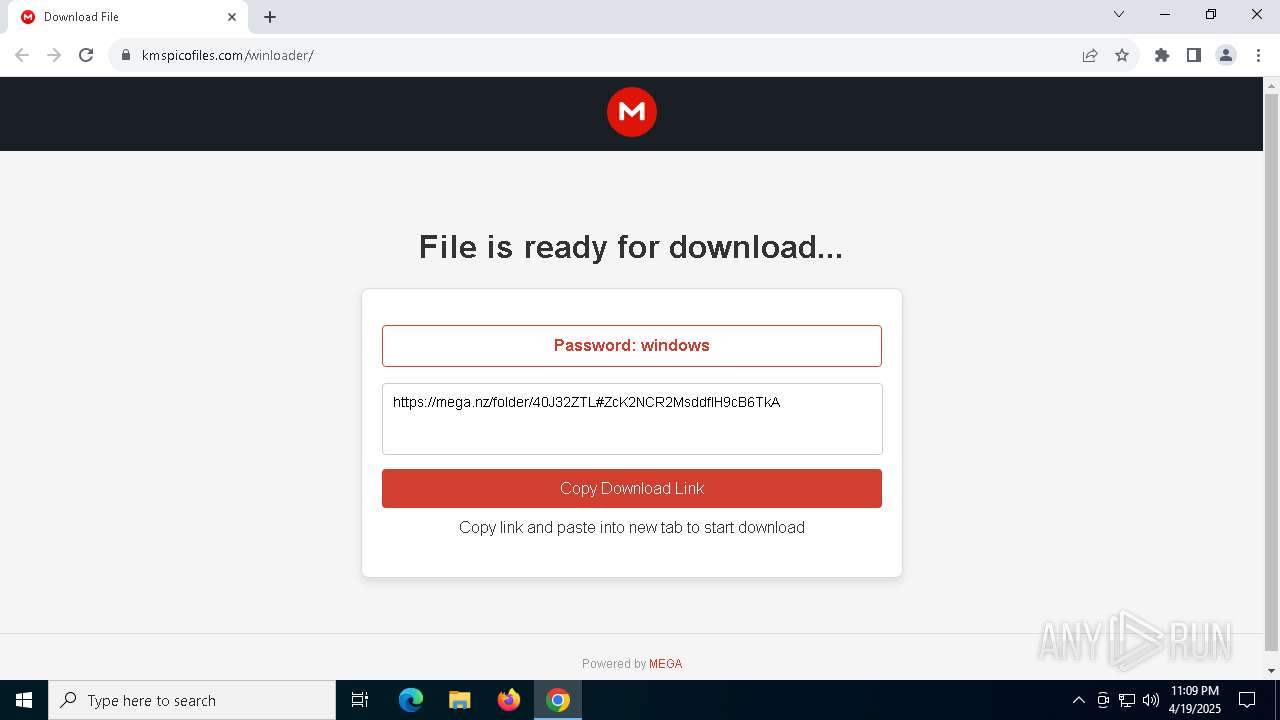
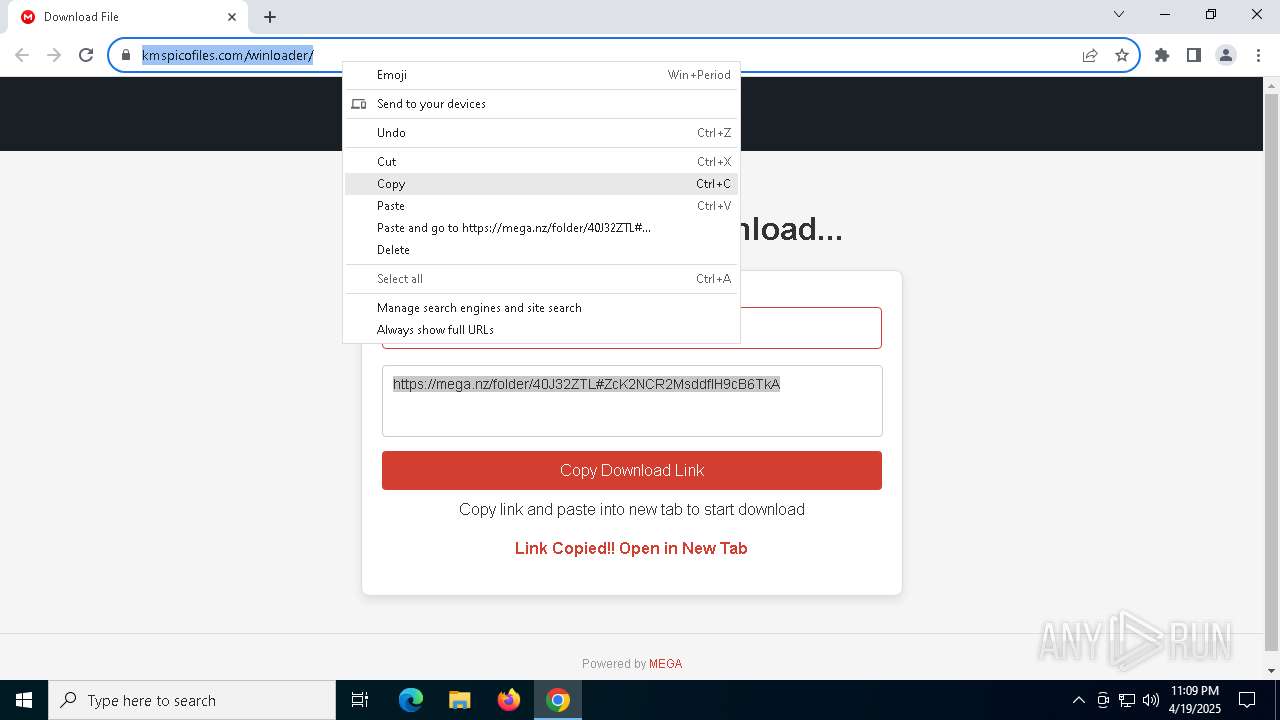
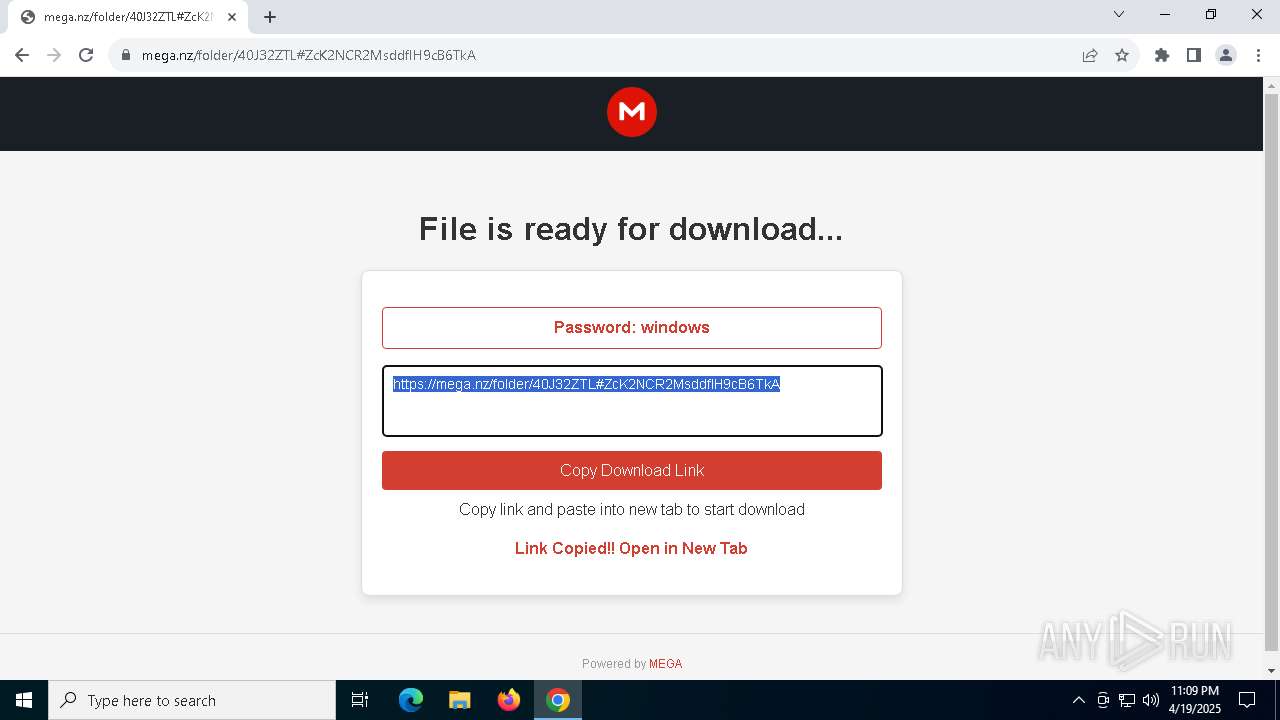
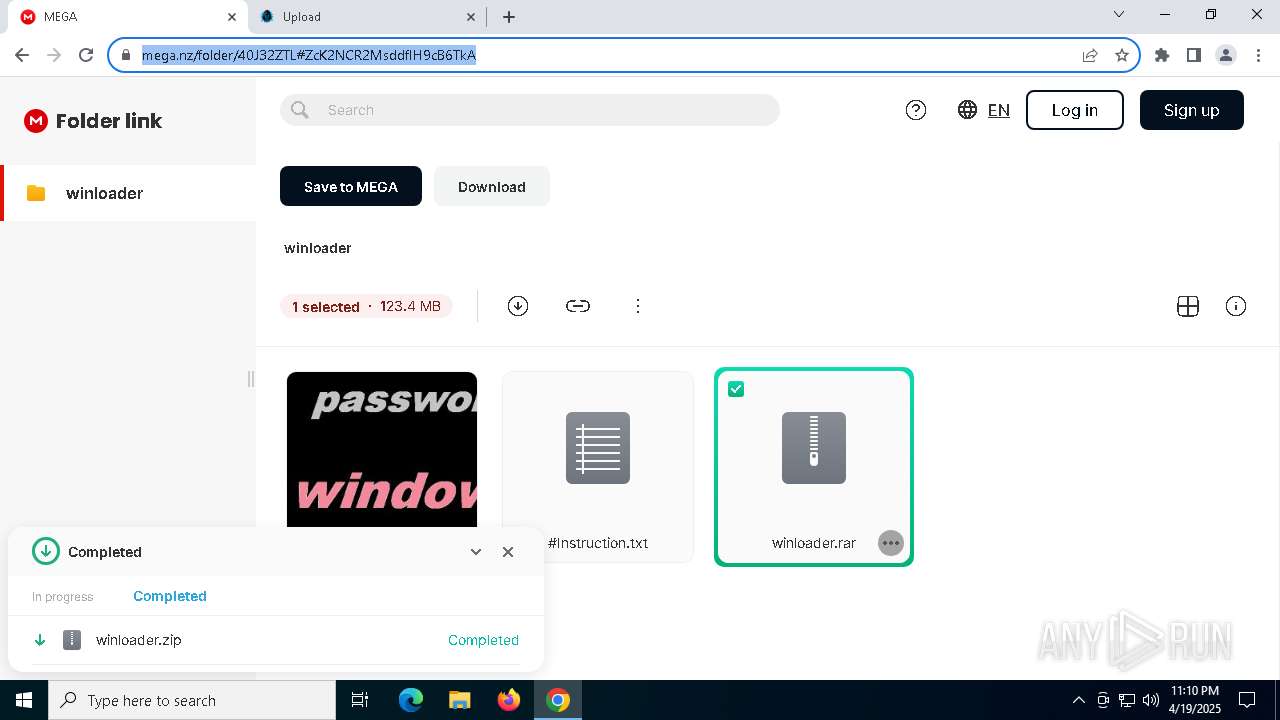
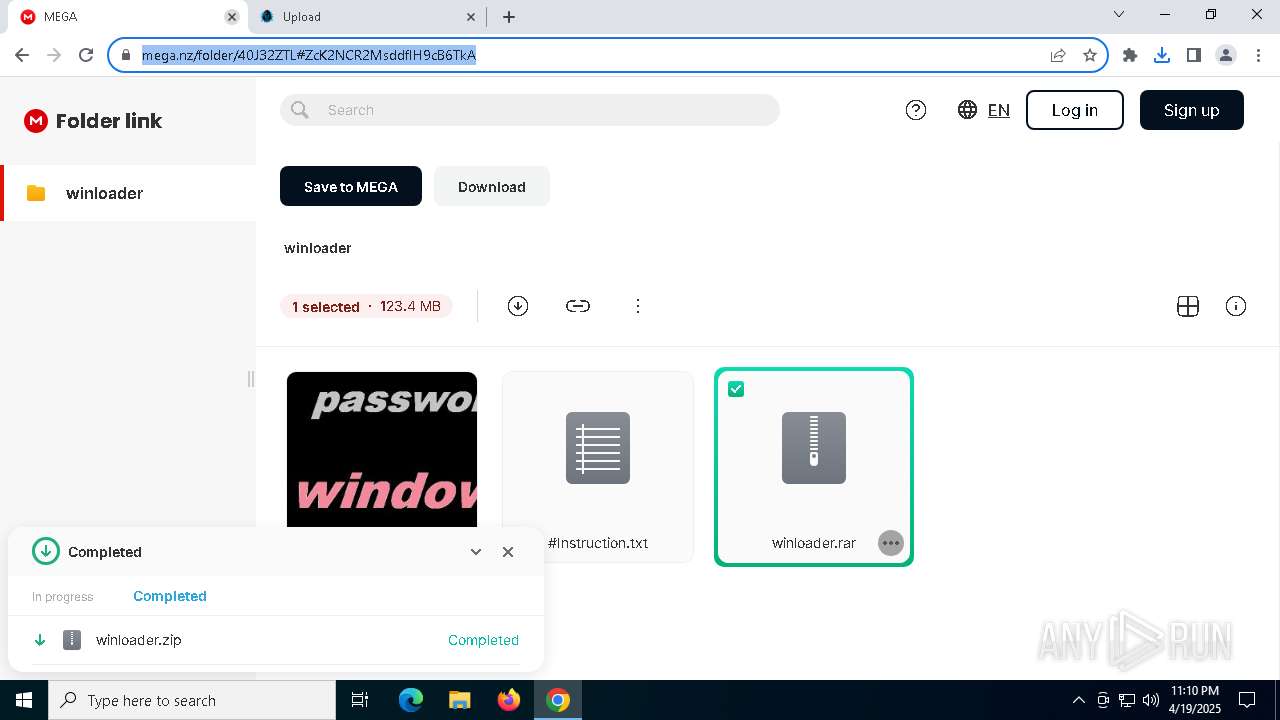
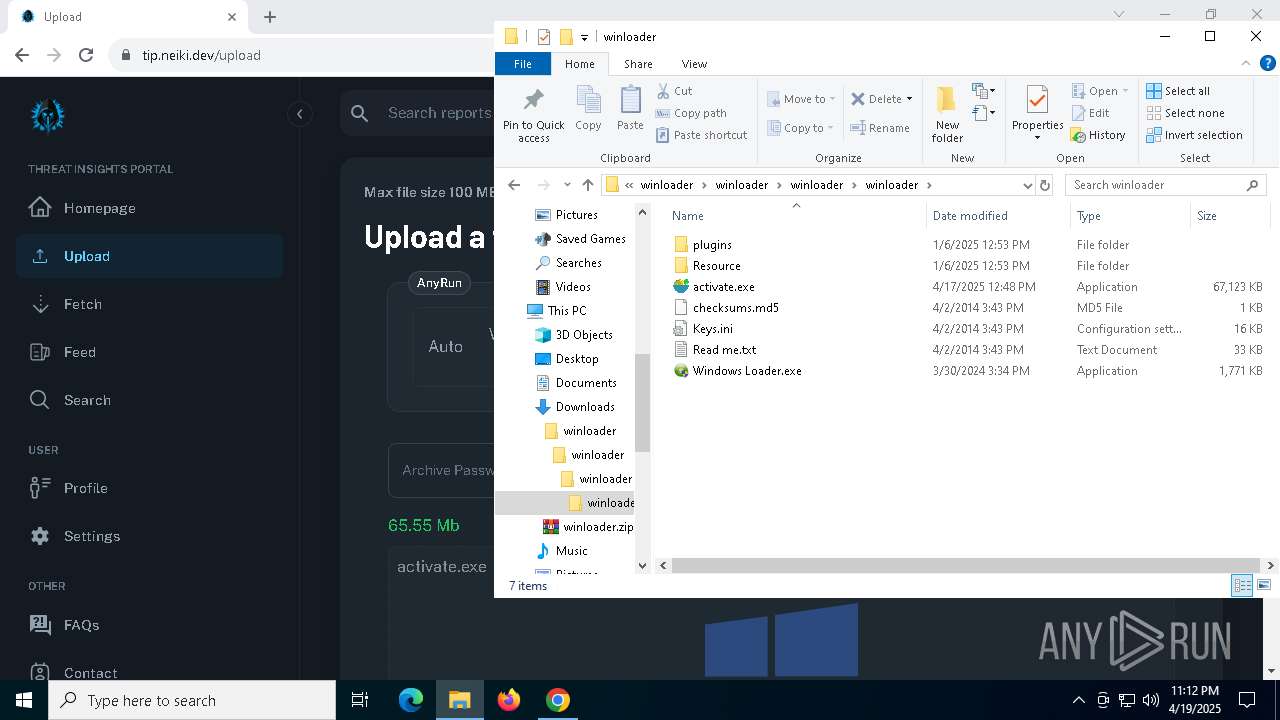
| URL: | https://oficial-kmspico.org/windows-loader/ |
| Full analysis: | https://app.any.run/tasks/c431ef99-af98-4037-9c99-17083d7192b6 |
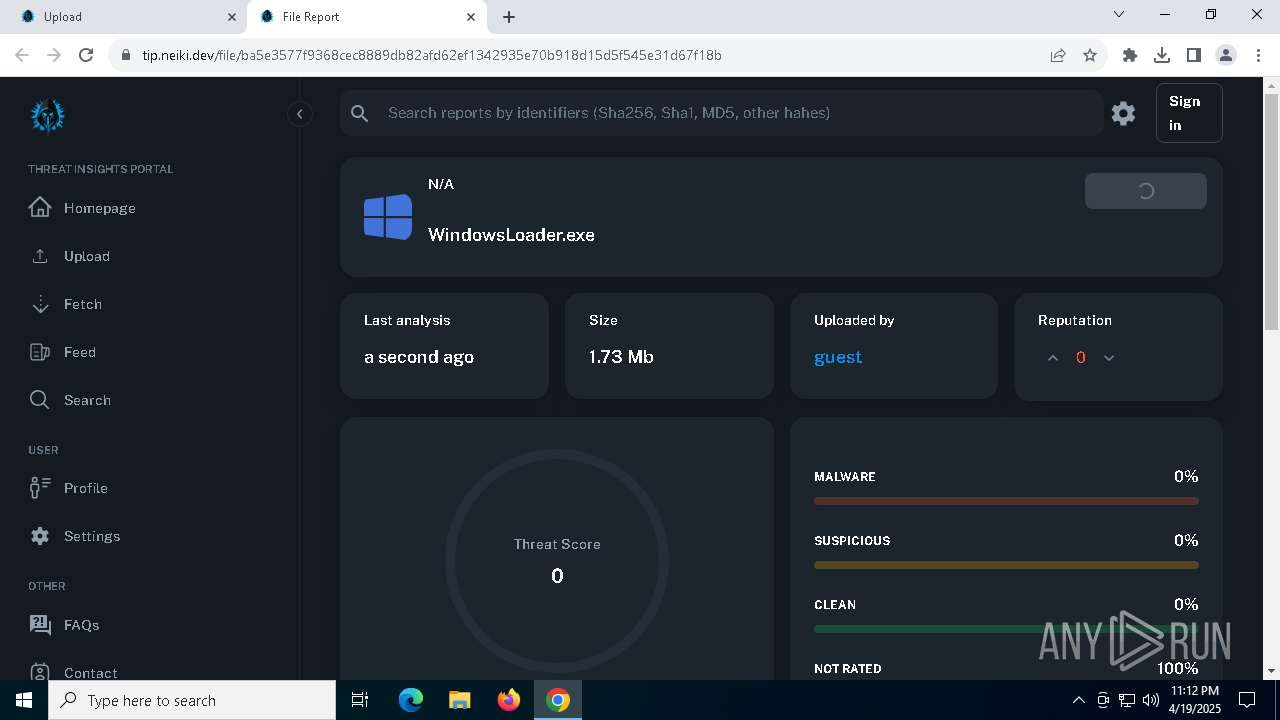
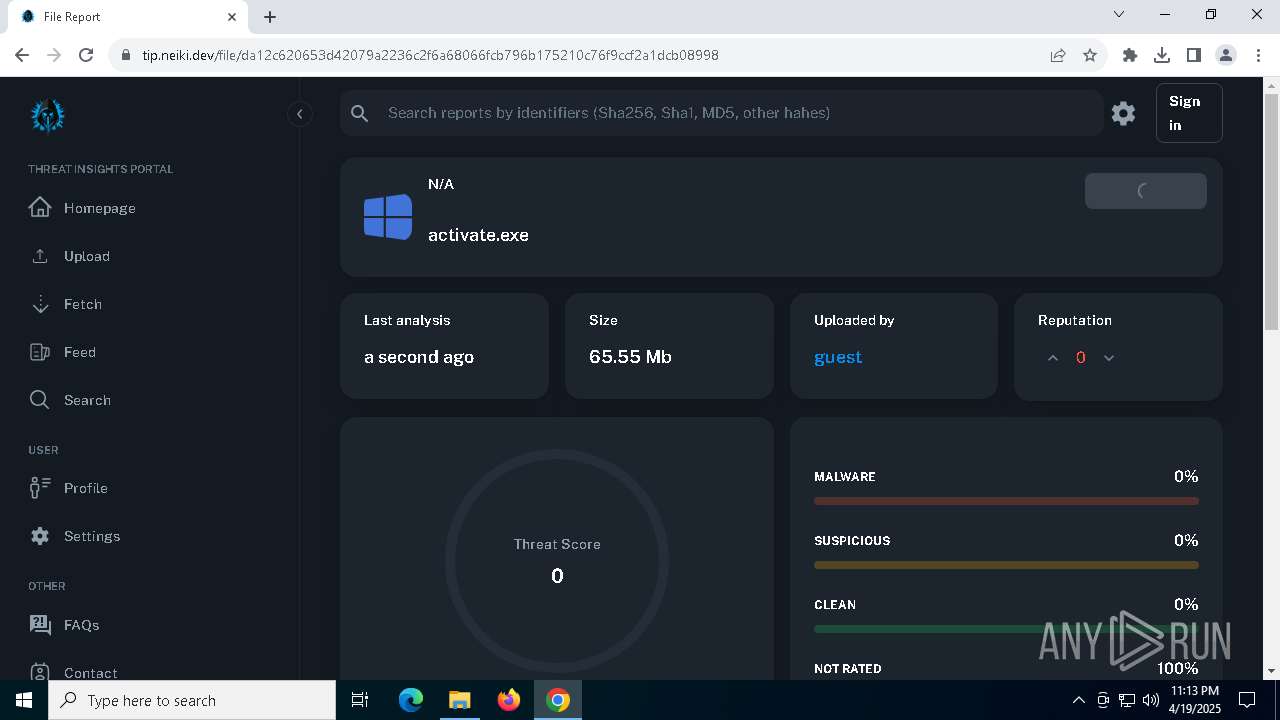
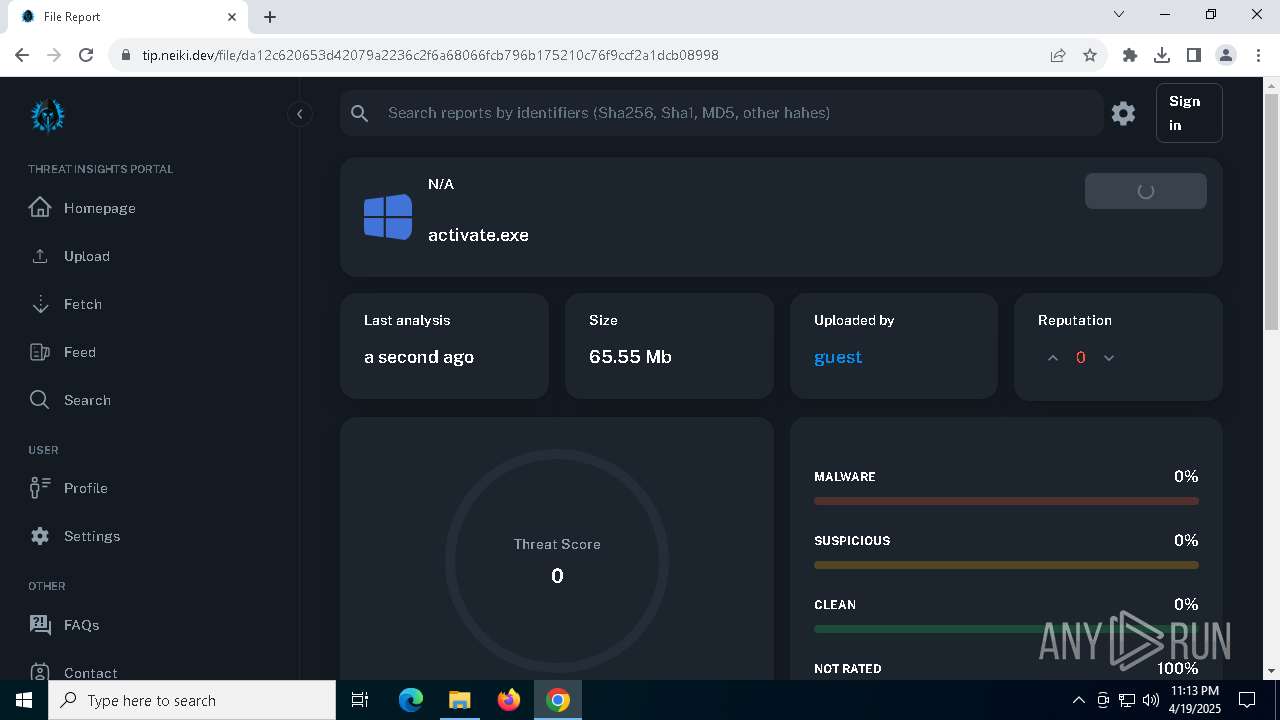
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
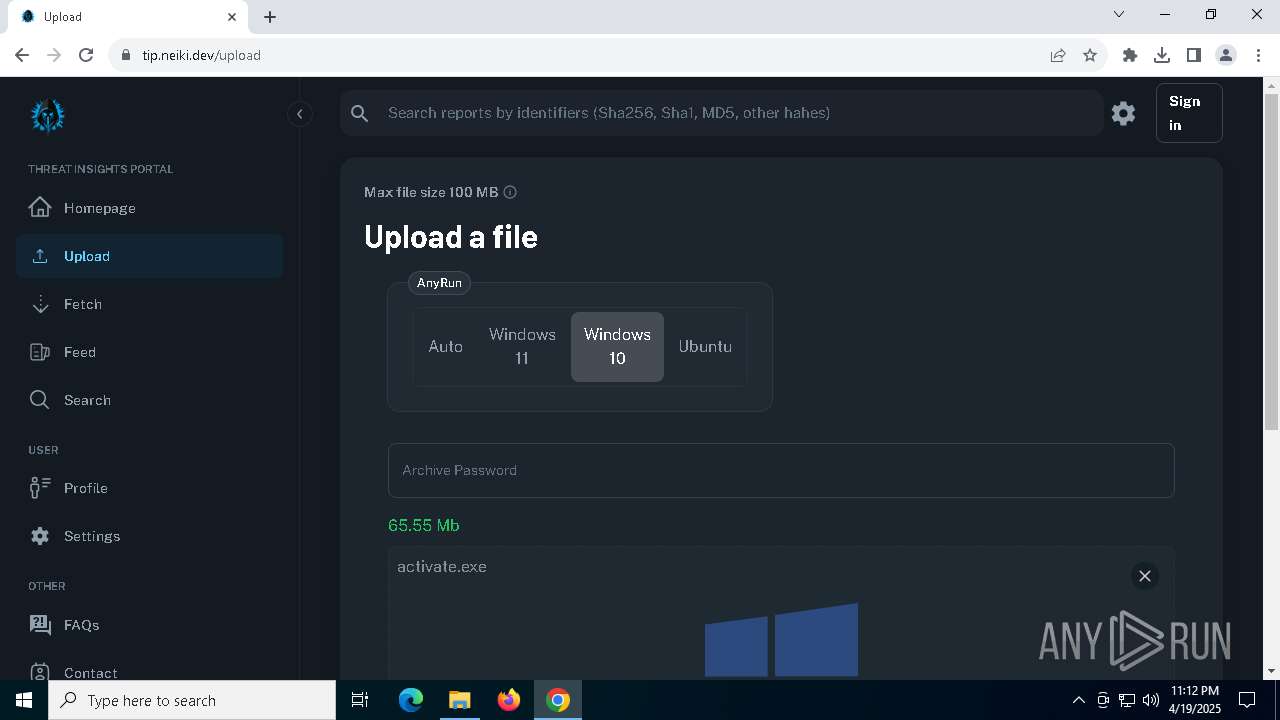
| Analysis date: | April 19, 2025, 23:09:03 |
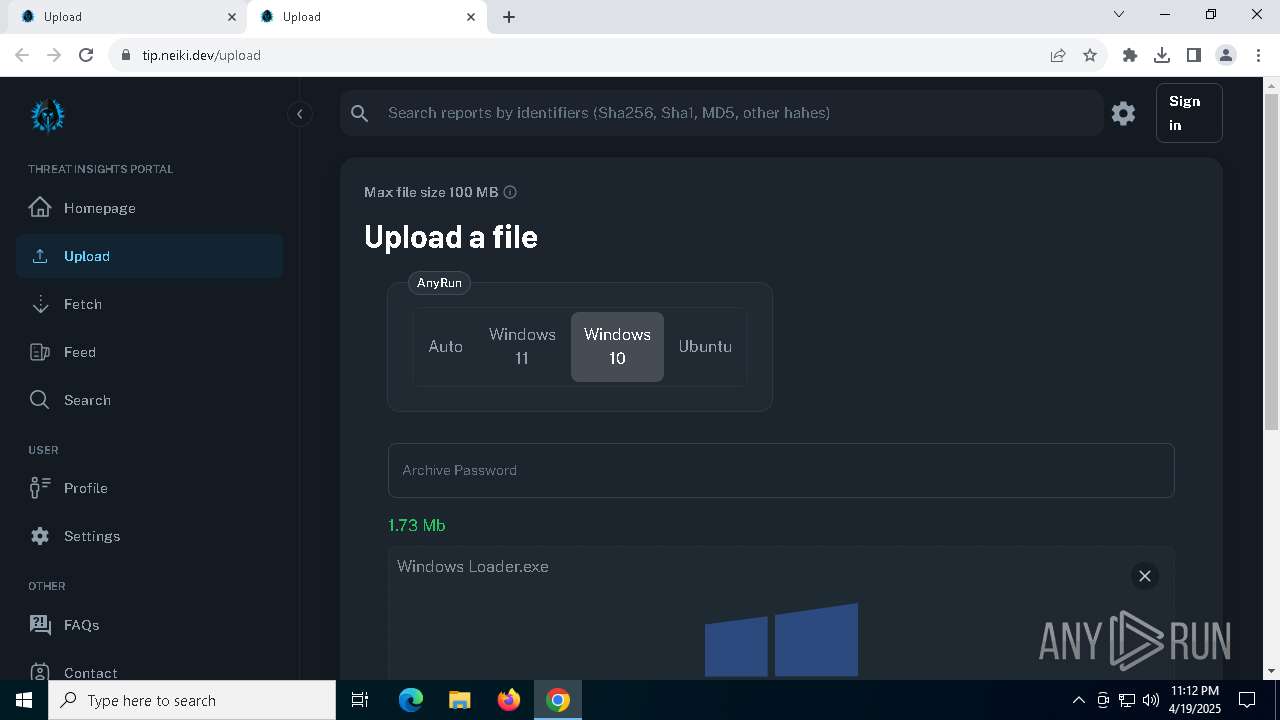
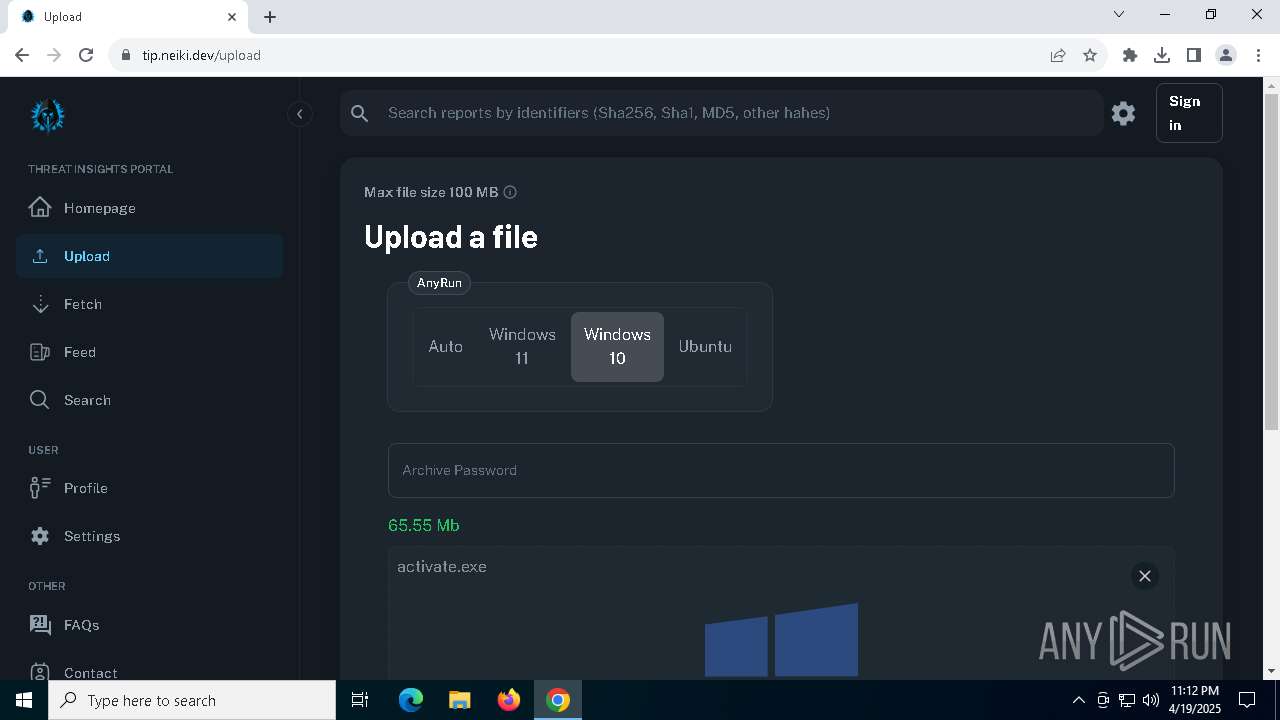
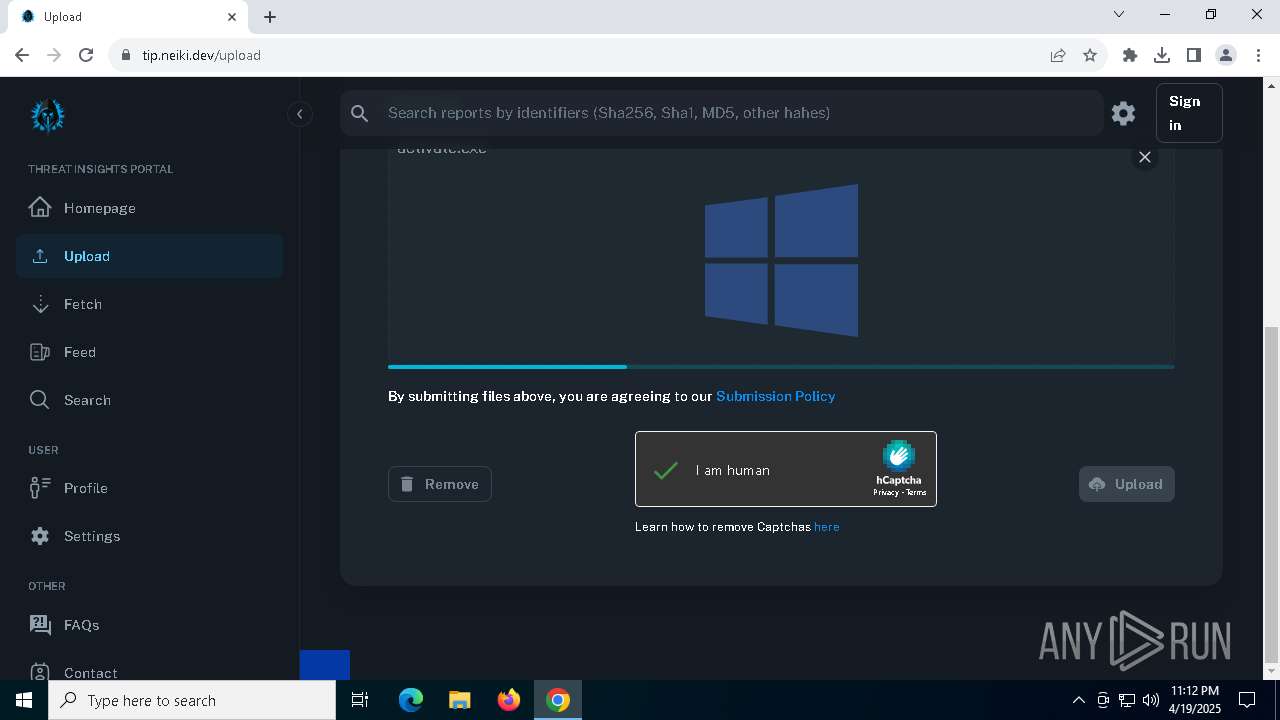
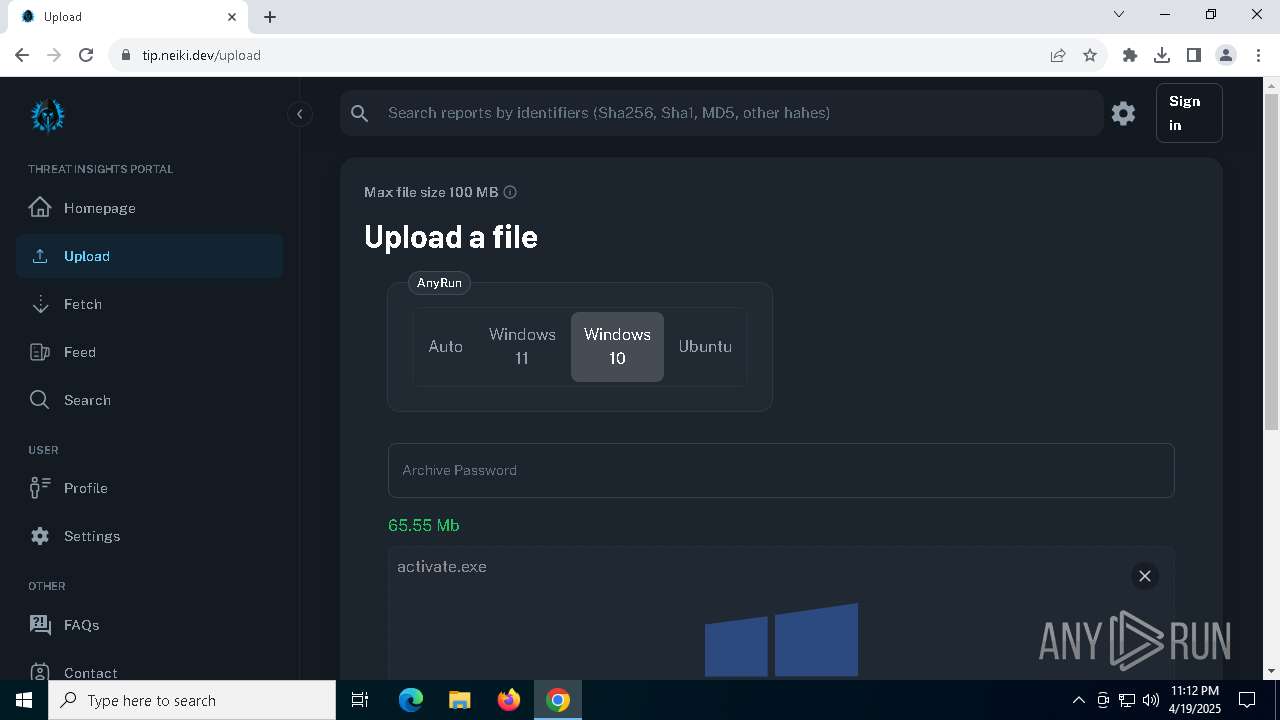
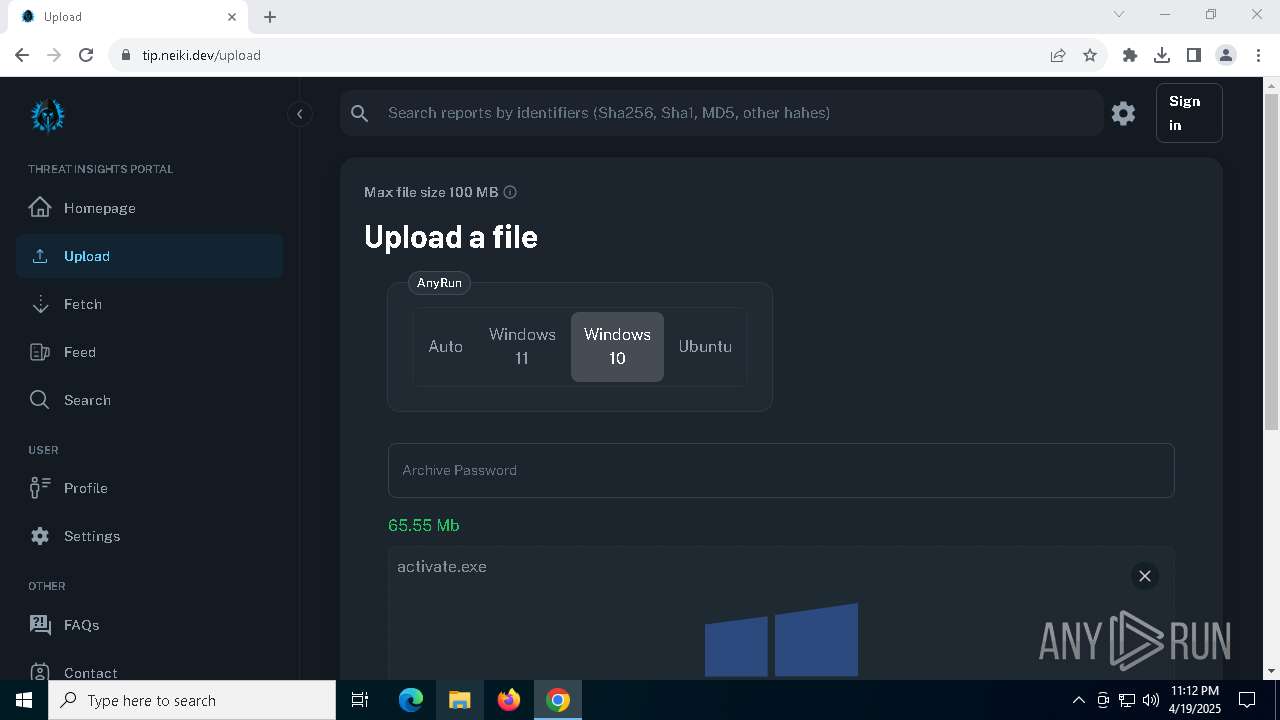
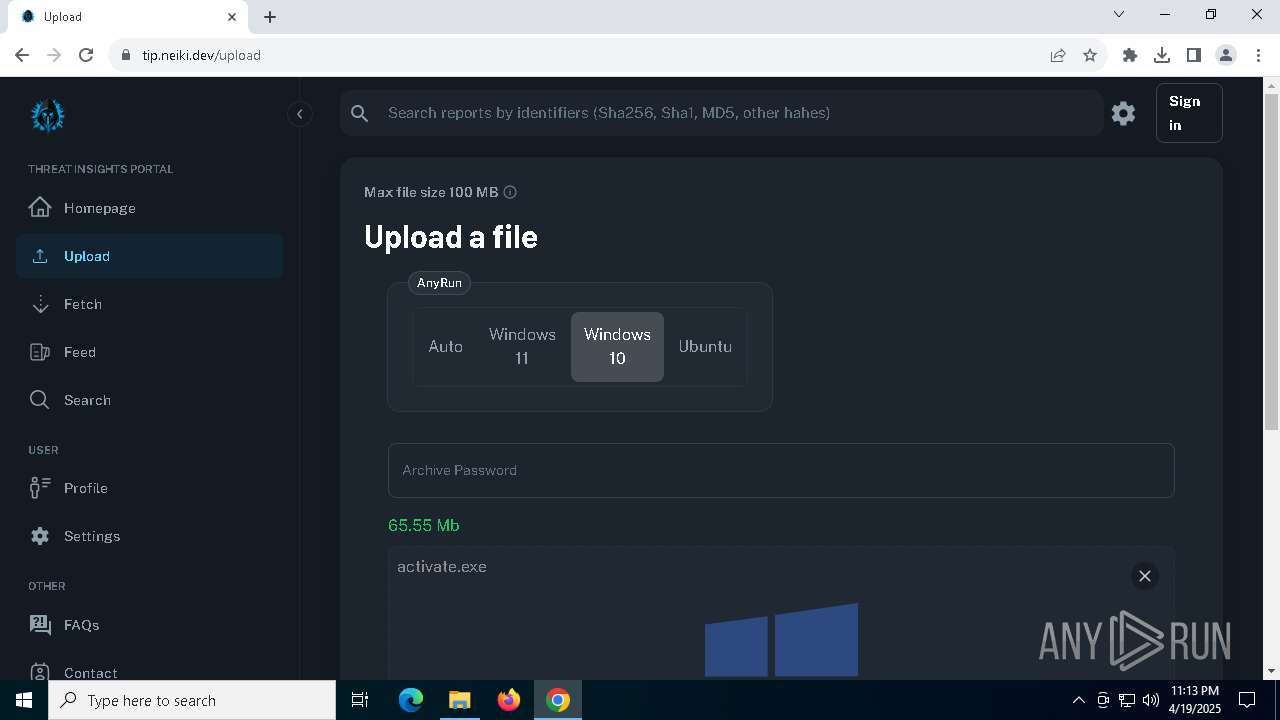
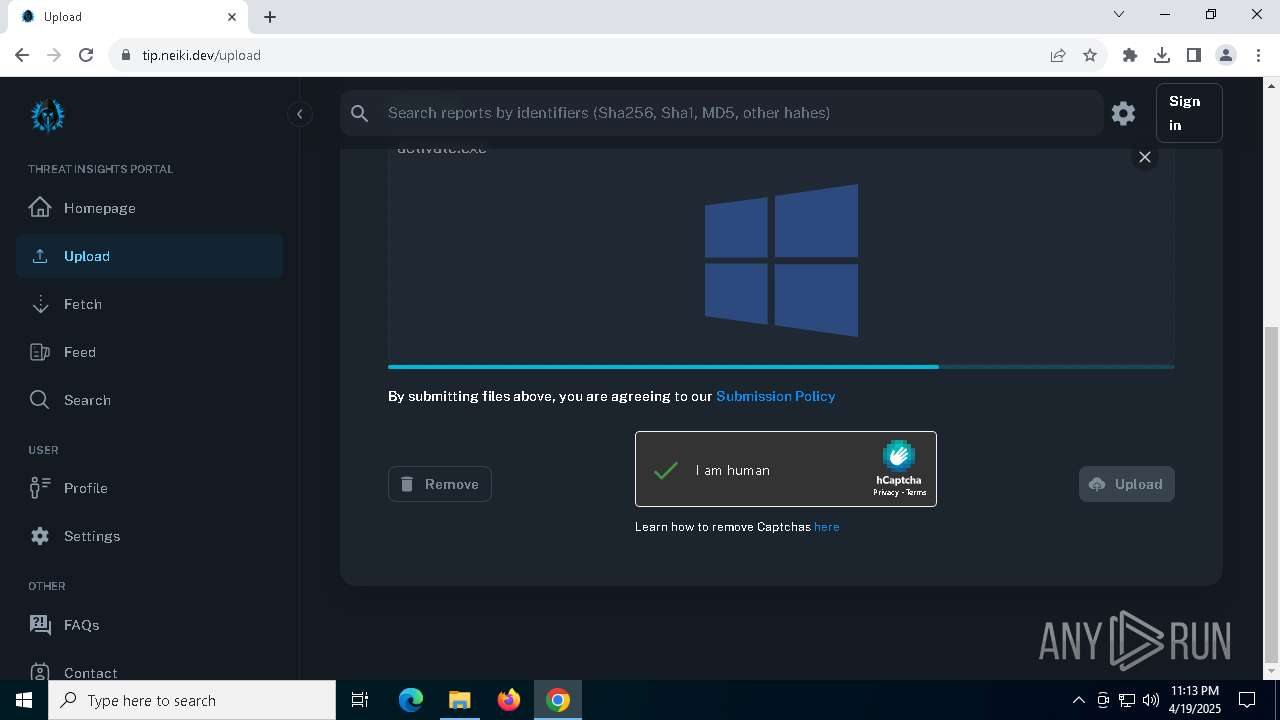
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
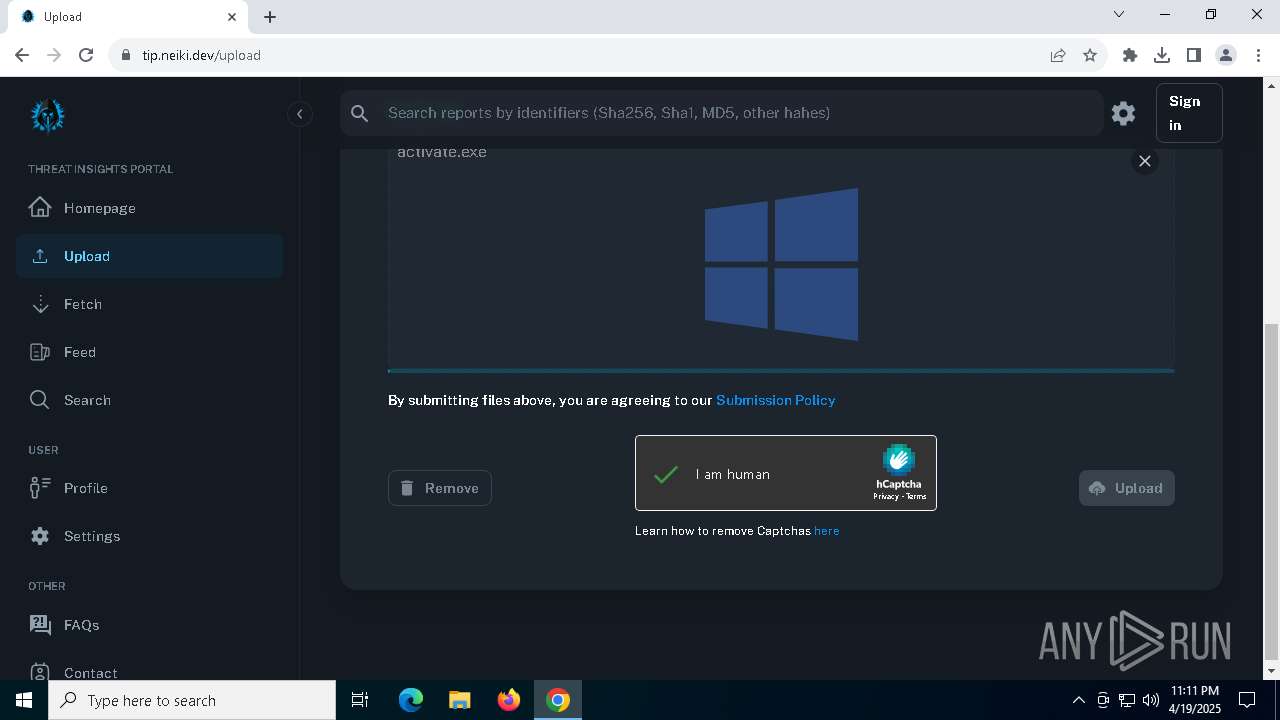
| MD5: | 990EDDD61738374B8900354408FD8F7D |
| SHA1: | D5939D497158D5828CD04652241B83EE78CA9DA2 |
| SHA256: | E4552D545DF757570ECE2CFEE24DAE57C2C8CFE88EFA06DDF1B6E0154D0313AE |
| SSDEEP: | 3:N8Ksgz4yyK:2Ks7u |
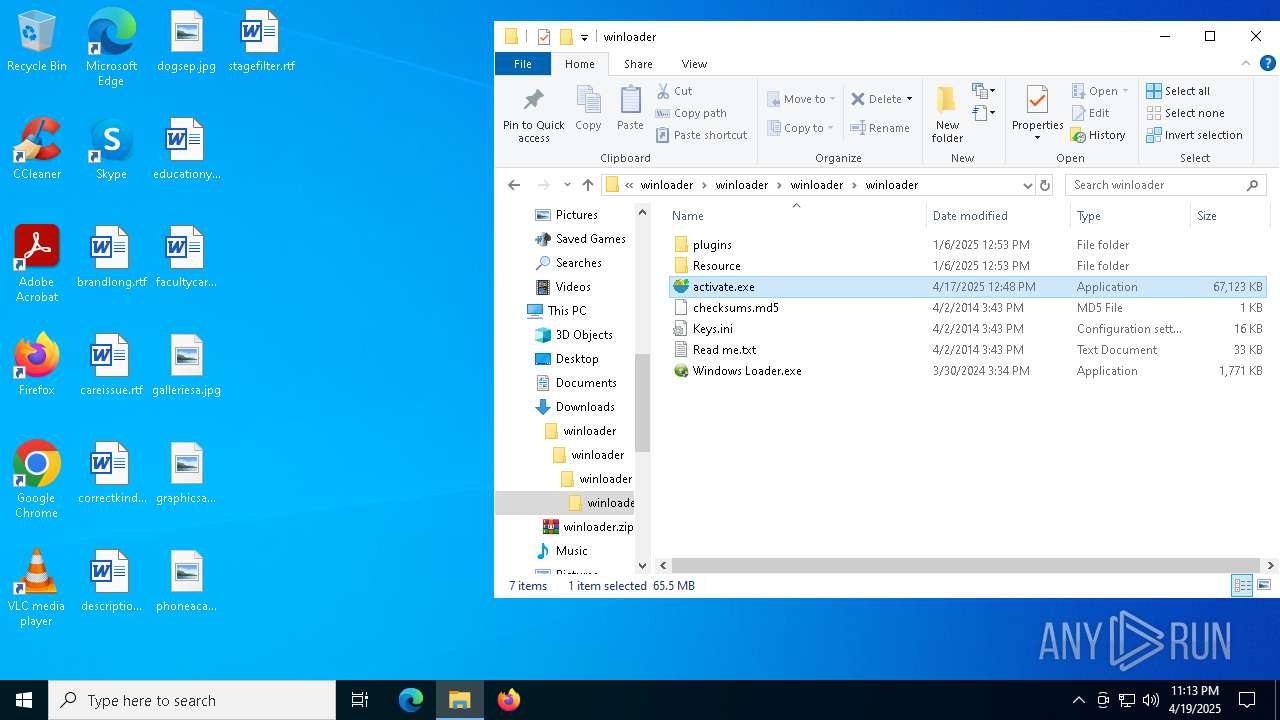
MALICIOUS
GENERIC has been found (auto)
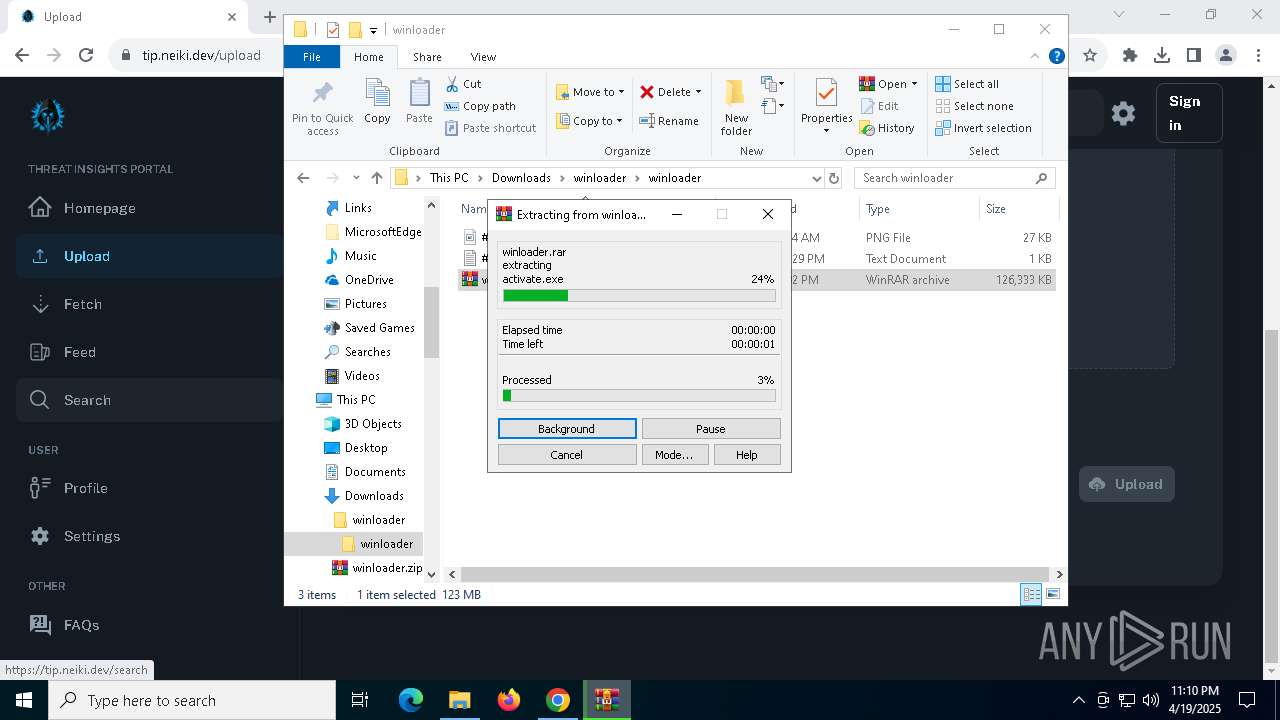
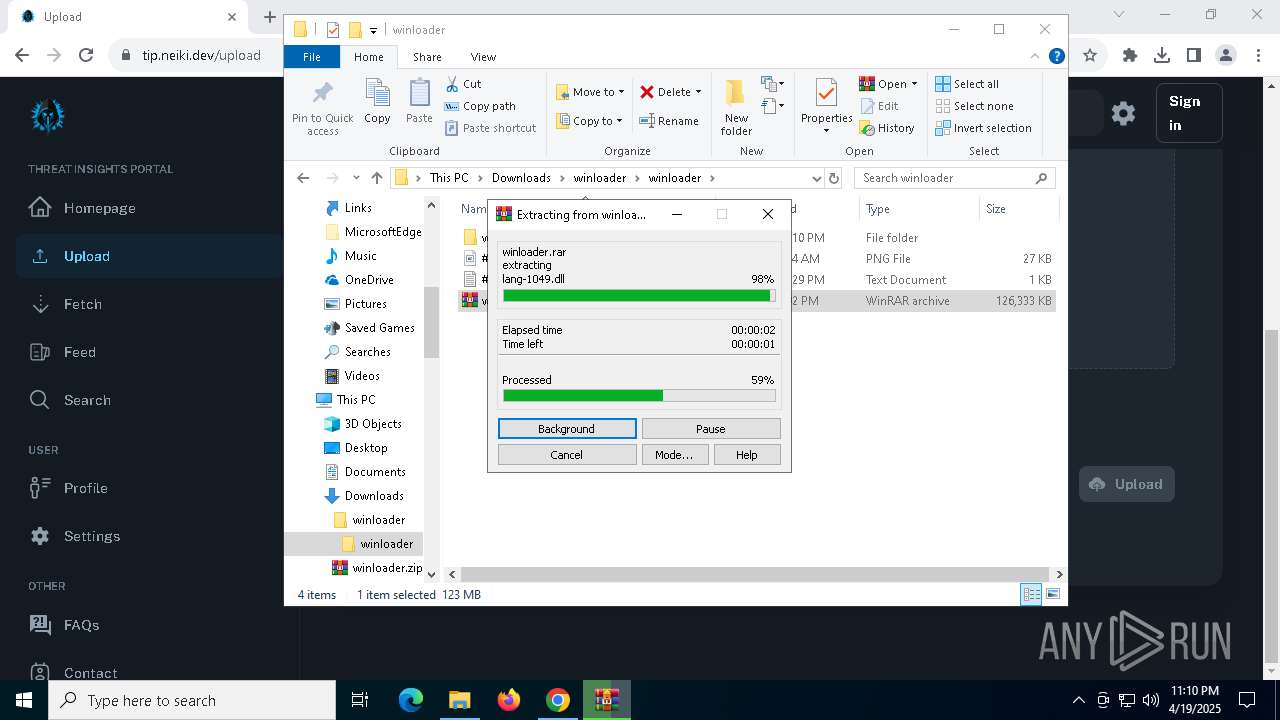
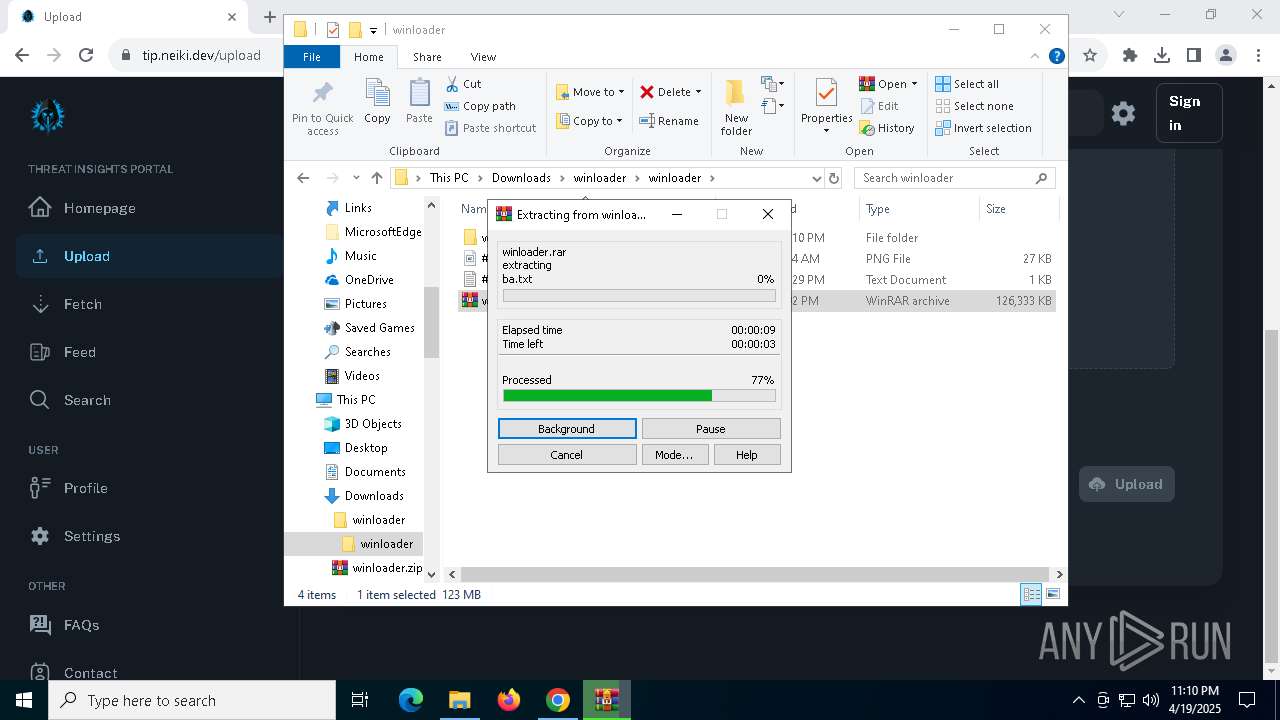
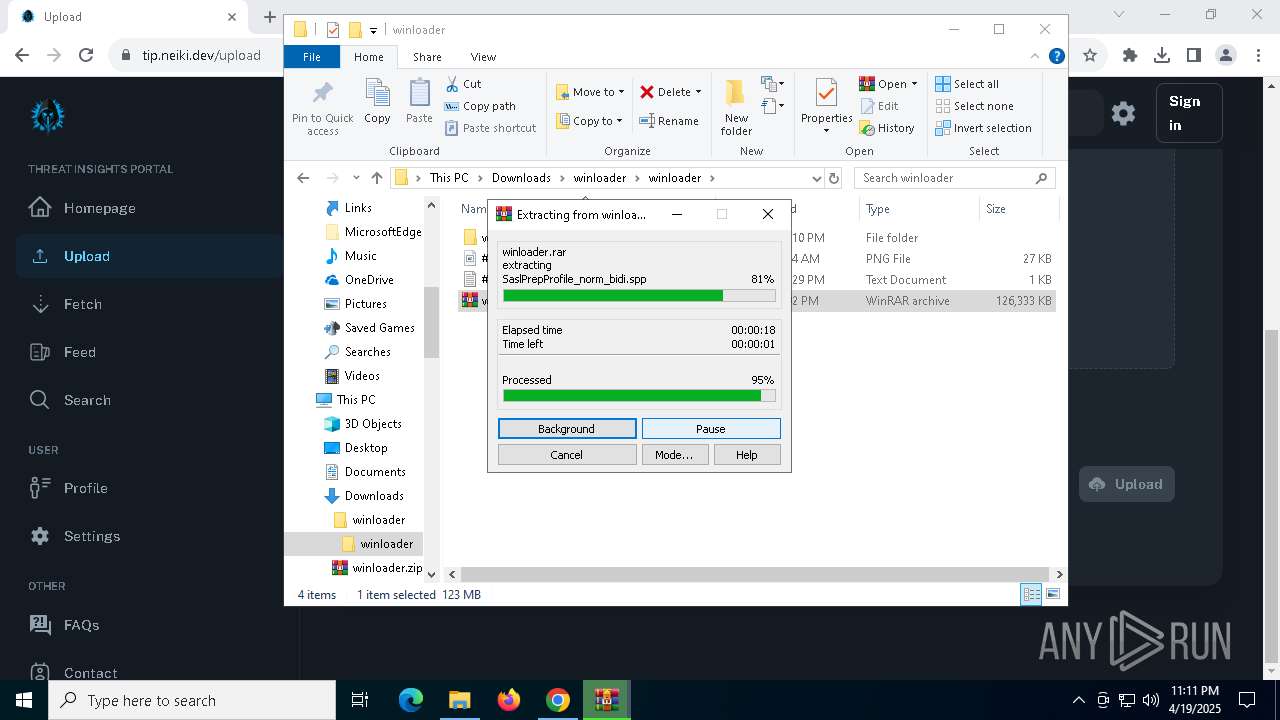
- WinRAR.exe (PID: 8144)
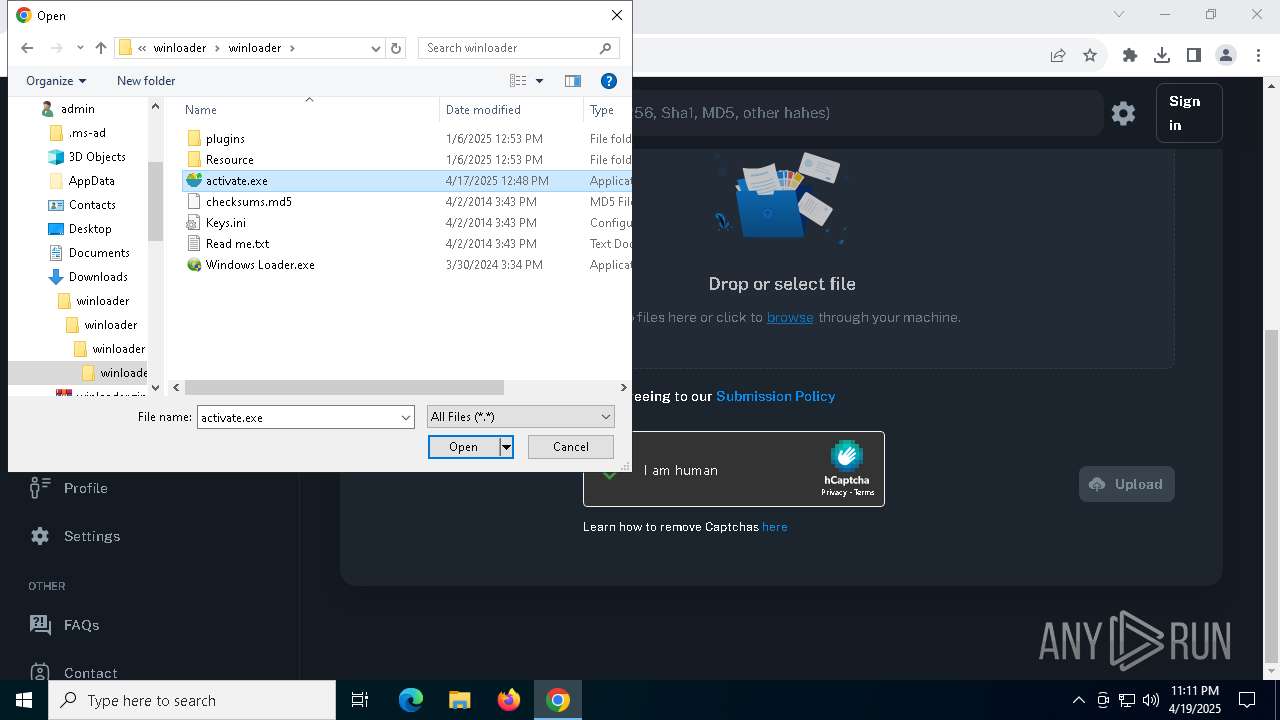
Executing a file with an untrusted certificate
- activate.exe (PID: 2656)
- activate.exe (PID: 7888)
- activate.exe (PID: 900)
Stealers network behavior
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- activate.exe (PID: 2656)
- activate.exe (PID: 900)
- activate.exe (PID: 7888)
Steals credentials from Web Browsers
- activate.exe (PID: 2656)
- activate.exe (PID: 900)
- activate.exe (PID: 7888)
Actions looks like stealing of personal data
- activate.exe (PID: 2656)
- activate.exe (PID: 7888)
- activate.exe (PID: 900)
LUMMA has been detected (YARA)
- activate.exe (PID: 2656)
Changes powershell execution policy (Bypass)
- activate.exe (PID: 900)
- activate.exe (PID: 2656)
- activate.exe (PID: 7888)
Bypass execution policy to execute commands
- powershell.exe (PID: 8104)
- powershell.exe (PID: 436)
- powershell.exe (PID: 7132)
SUSPICIOUS
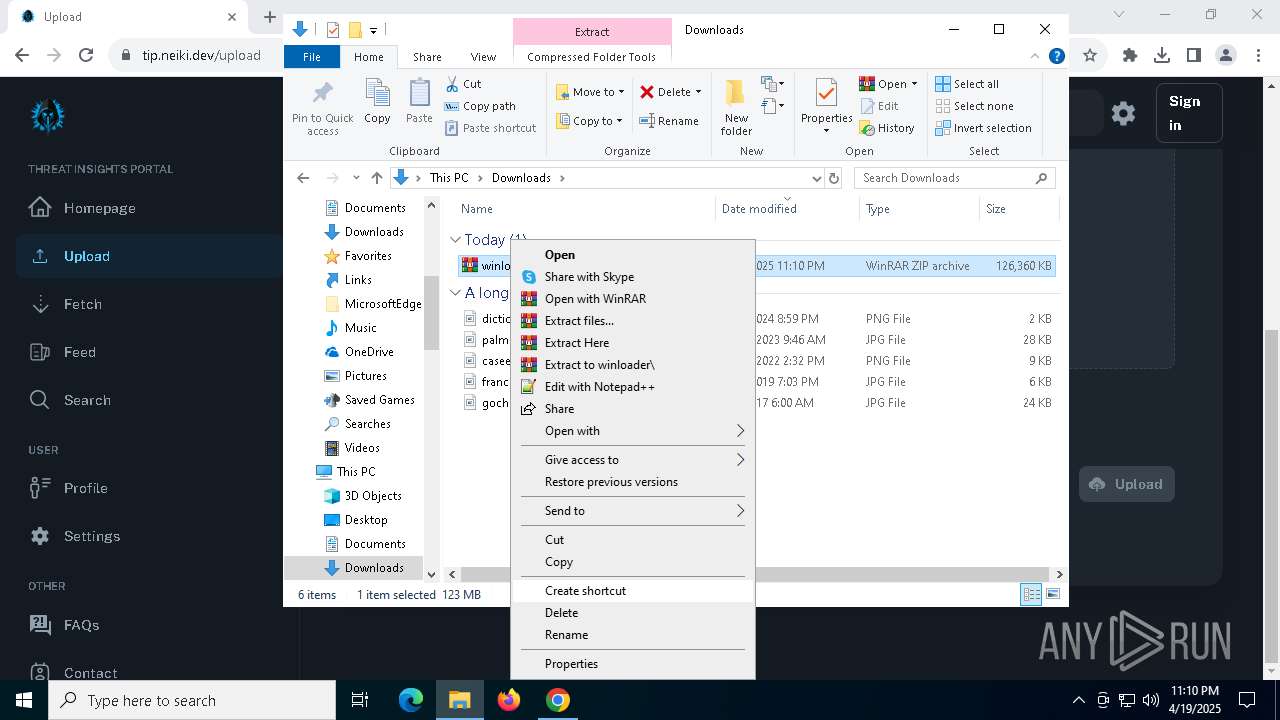
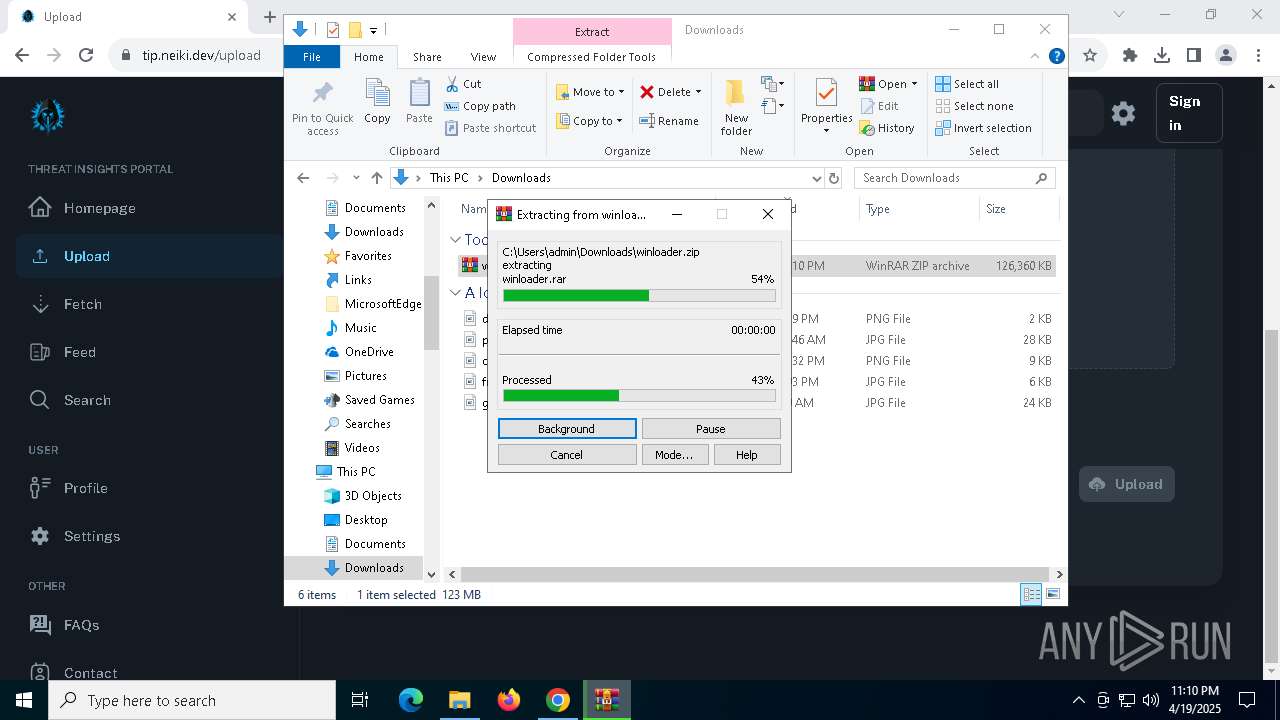
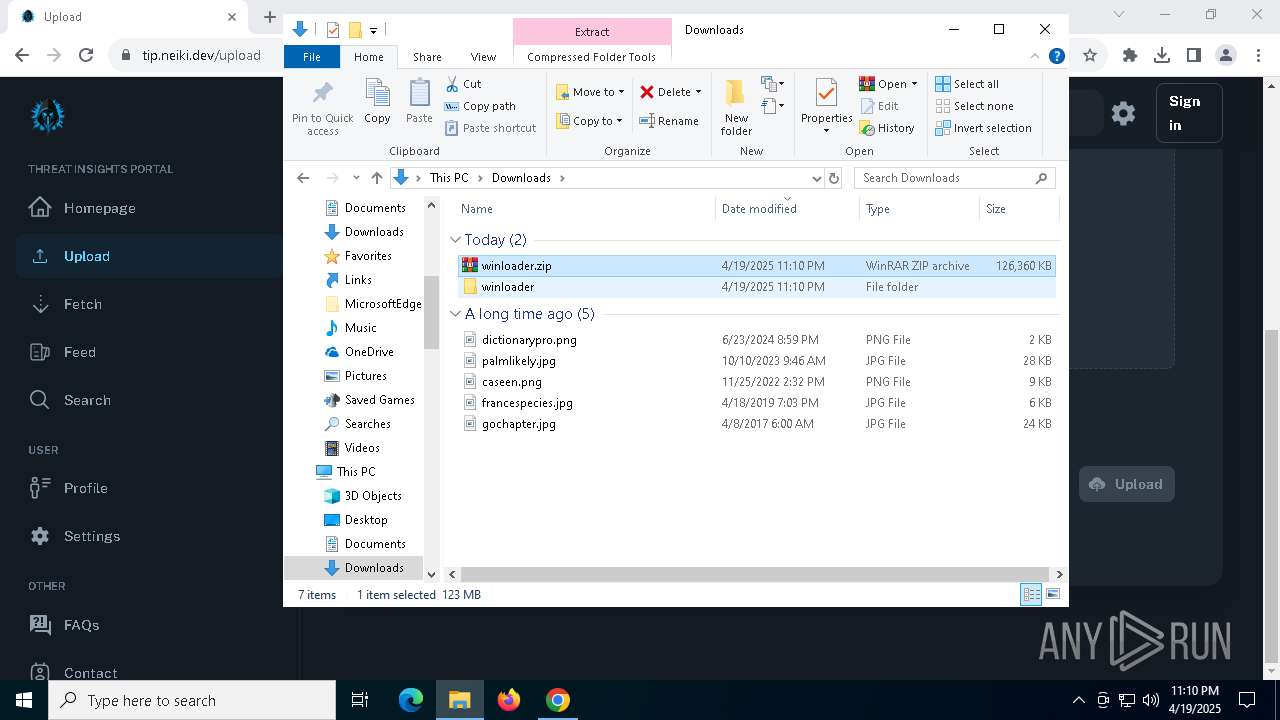
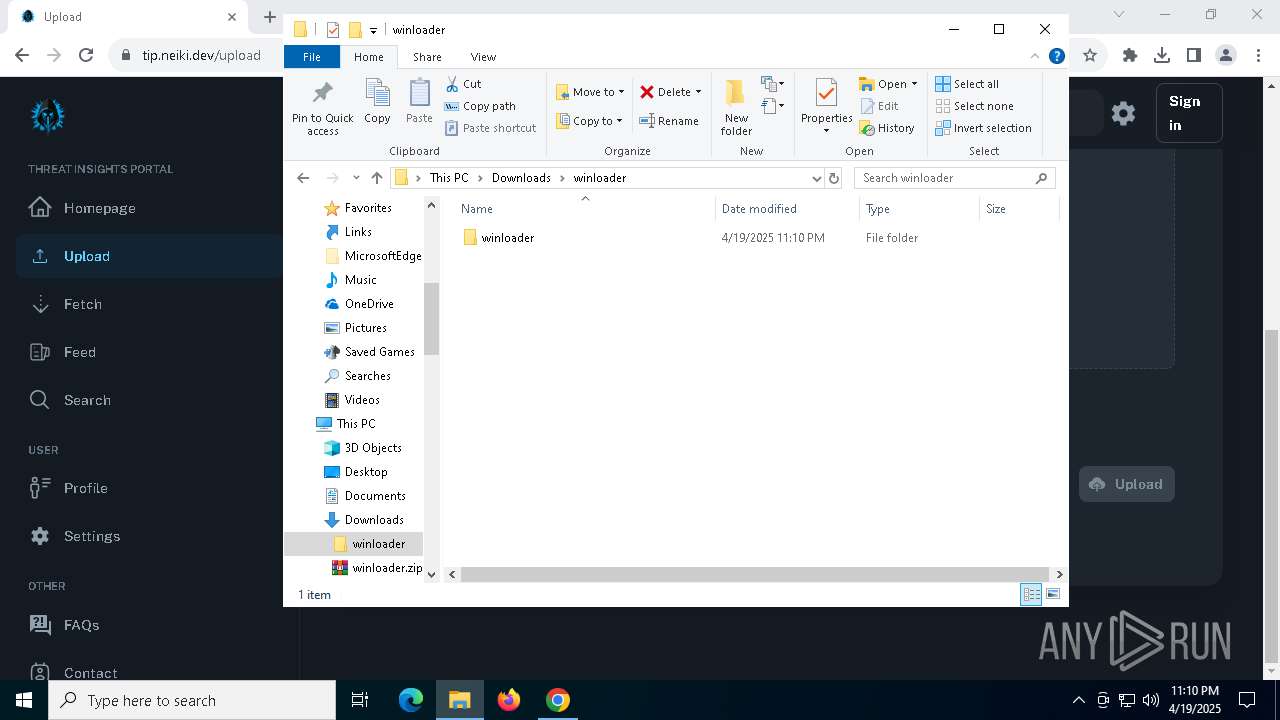
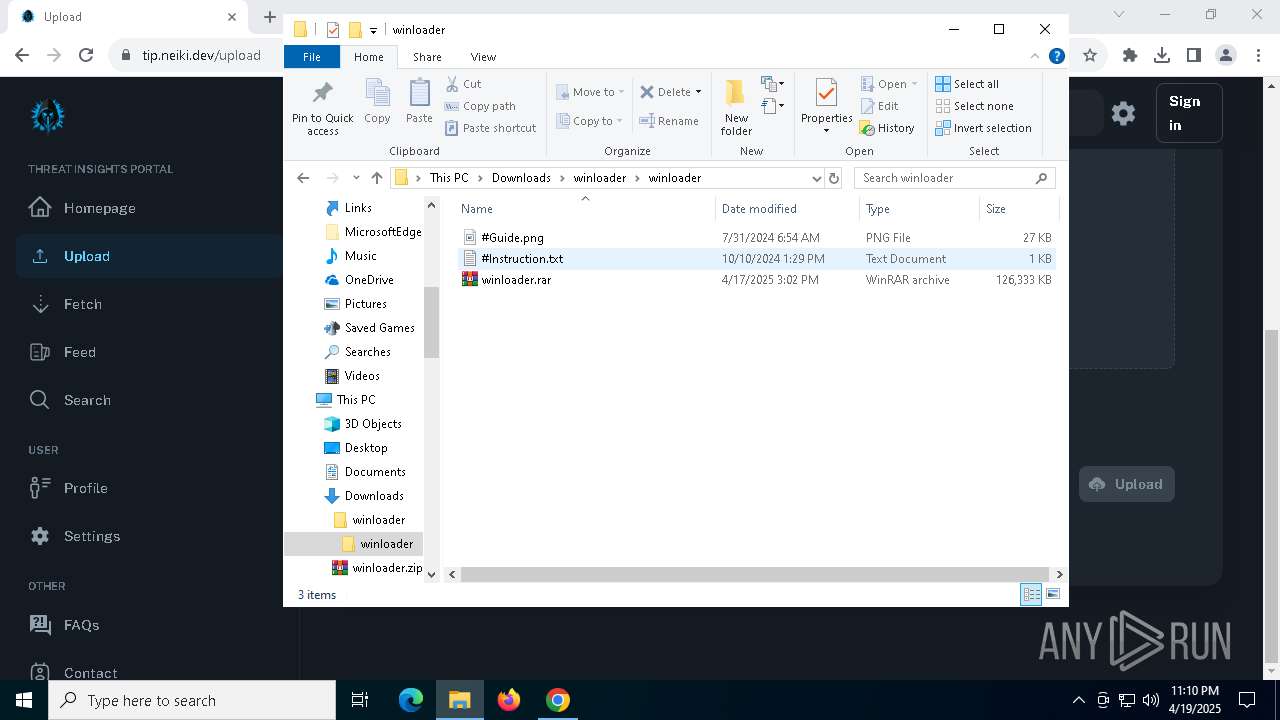
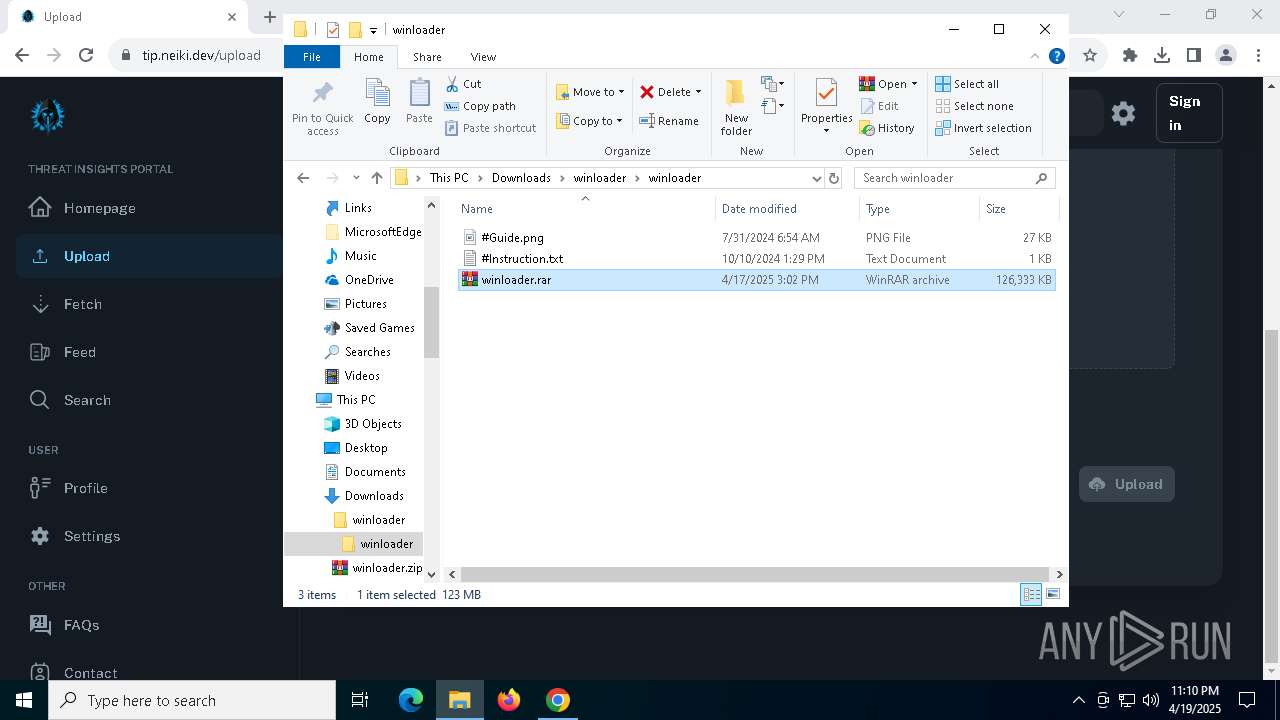
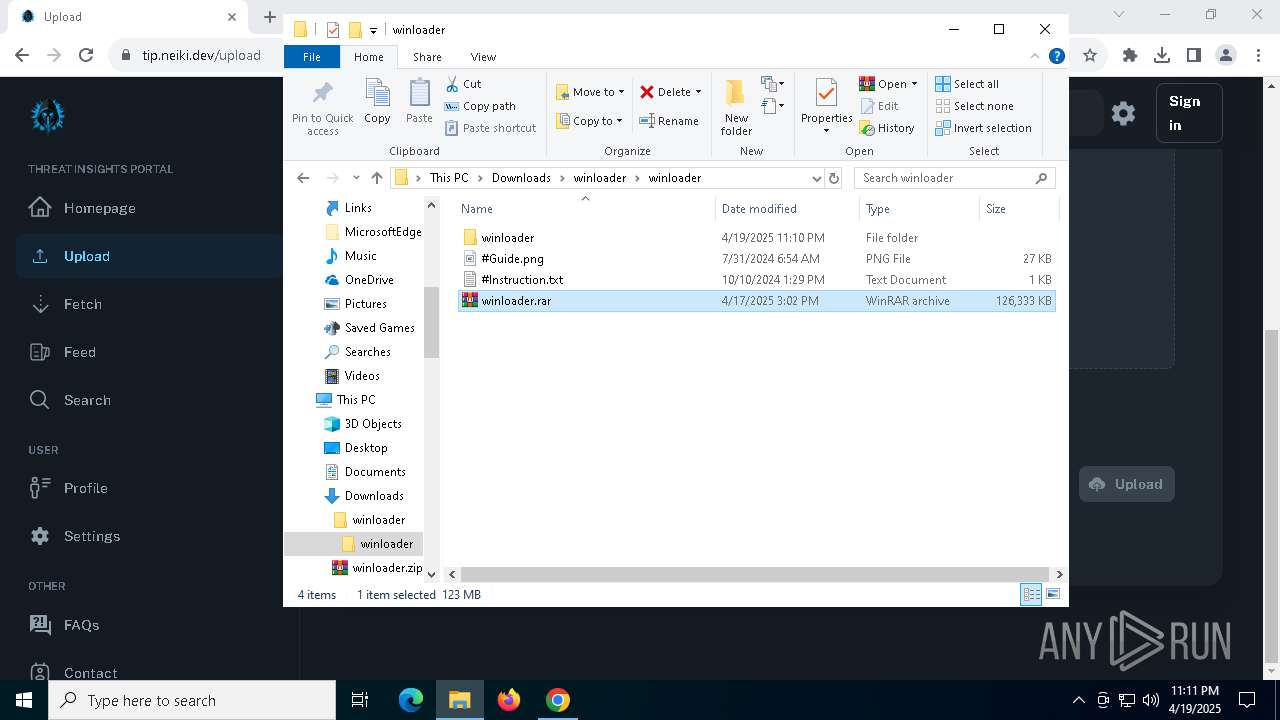
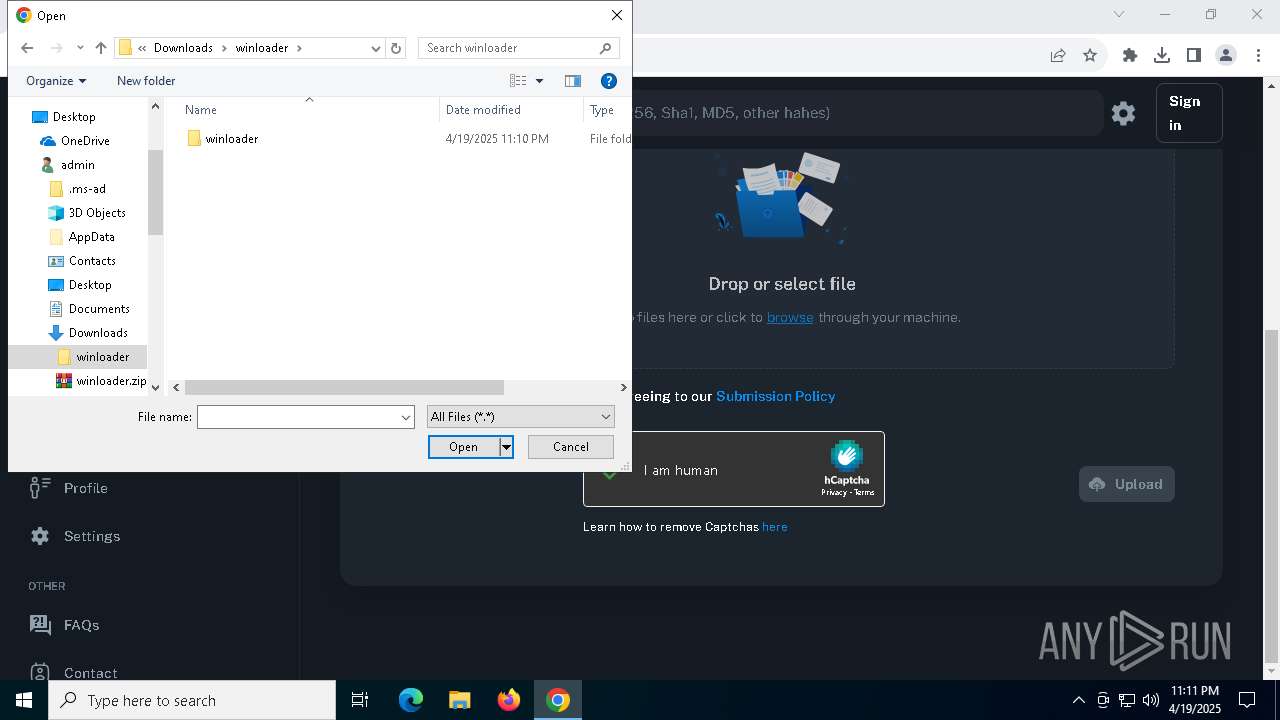
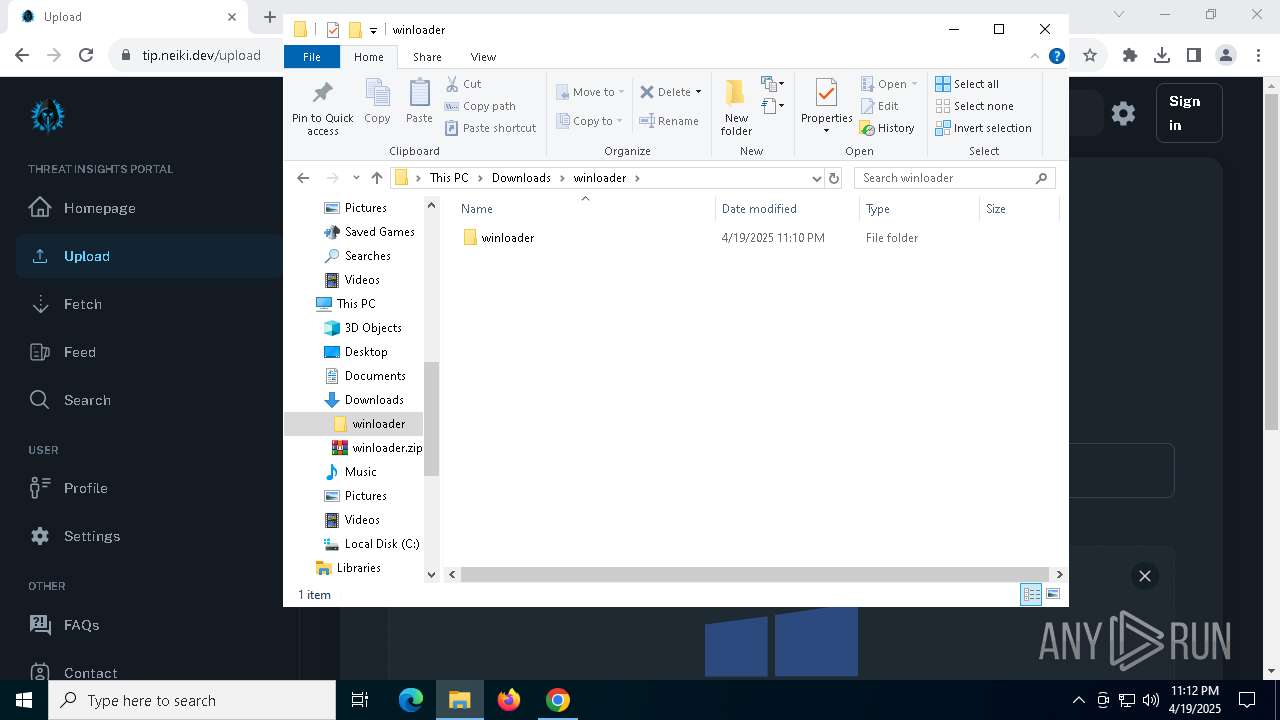
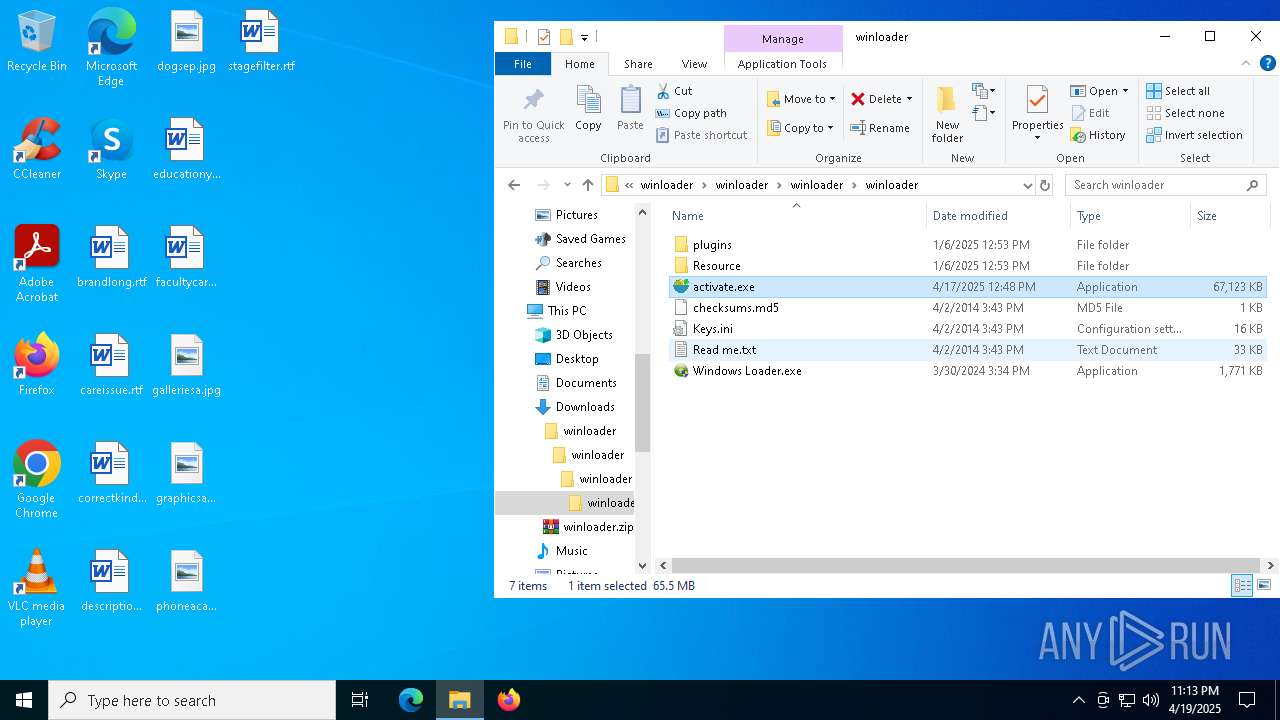
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8144)
Process drops legitimate windows executable
- WinRAR.exe (PID: 8144)
Reads security settings of Internet Explorer
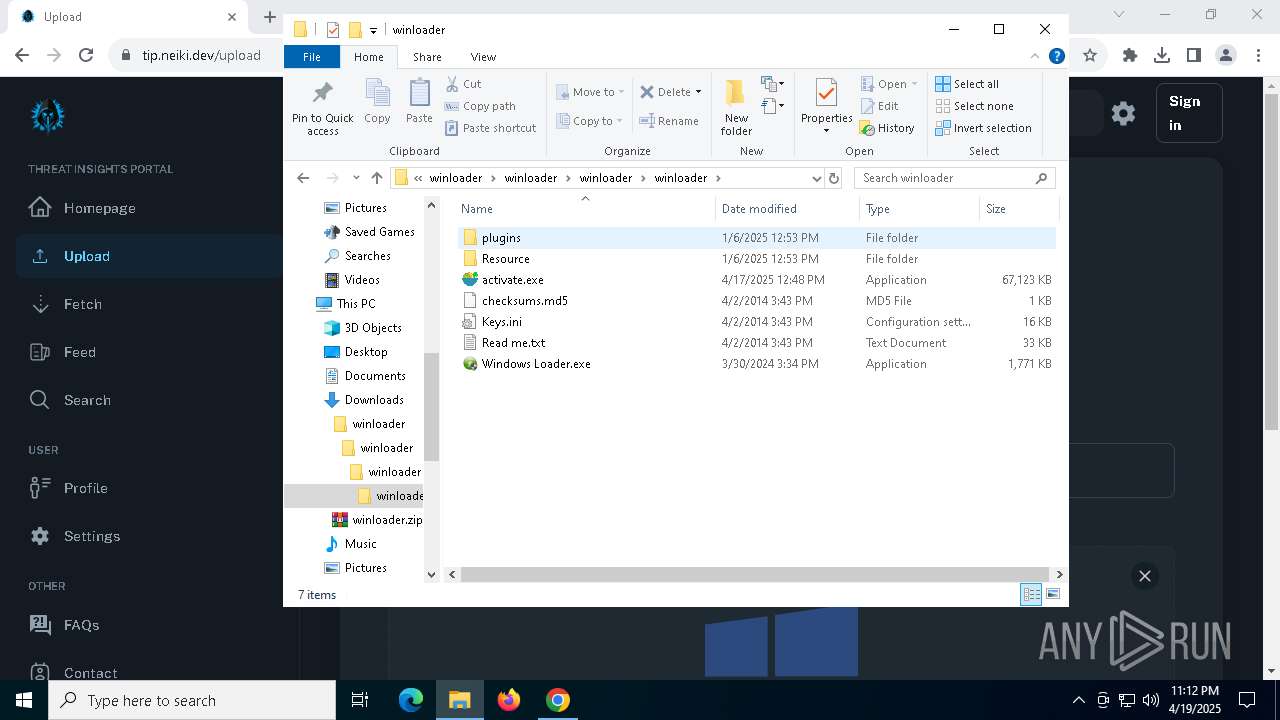
- Windows Loader.exe (PID: 5452)
- Windows Loader.exe (PID: 2616)
There is functionality for taking screenshot (YARA)
- activate.exe (PID: 2656)
- Windows Loader.exe (PID: 5452)
Searches for installed software
- activate.exe (PID: 900)
- activate.exe (PID: 2656)
- activate.exe (PID: 7888)
Starts POWERSHELL.EXE for commands execution
- activate.exe (PID: 900)
- activate.exe (PID: 7888)
- activate.exe (PID: 2656)
INFO
Application launched itself
- chrome.exe (PID: 896)
- firefox.exe (PID: 5176)
- firefox.exe (PID: 6488)
- msedge.exe (PID: 7948)
- msedge.exe (PID: 7756)
Reads the software policy settings
- slui.exe (PID: 7380)
- slui.exe (PID: 8088)
- activate.exe (PID: 2656)
- activate.exe (PID: 900)
- activate.exe (PID: 7888)
- powershell.exe (PID: 7132)
- powershell.exe (PID: 436)
- powershell.exe (PID: 8104)
Executable content was dropped or overwritten
- chrome.exe (PID: 7292)
- WinRAR.exe (PID: 8144)
The sample compiled with english language support
- WinRAR.exe (PID: 8144)
- chrome.exe (PID: 7292)
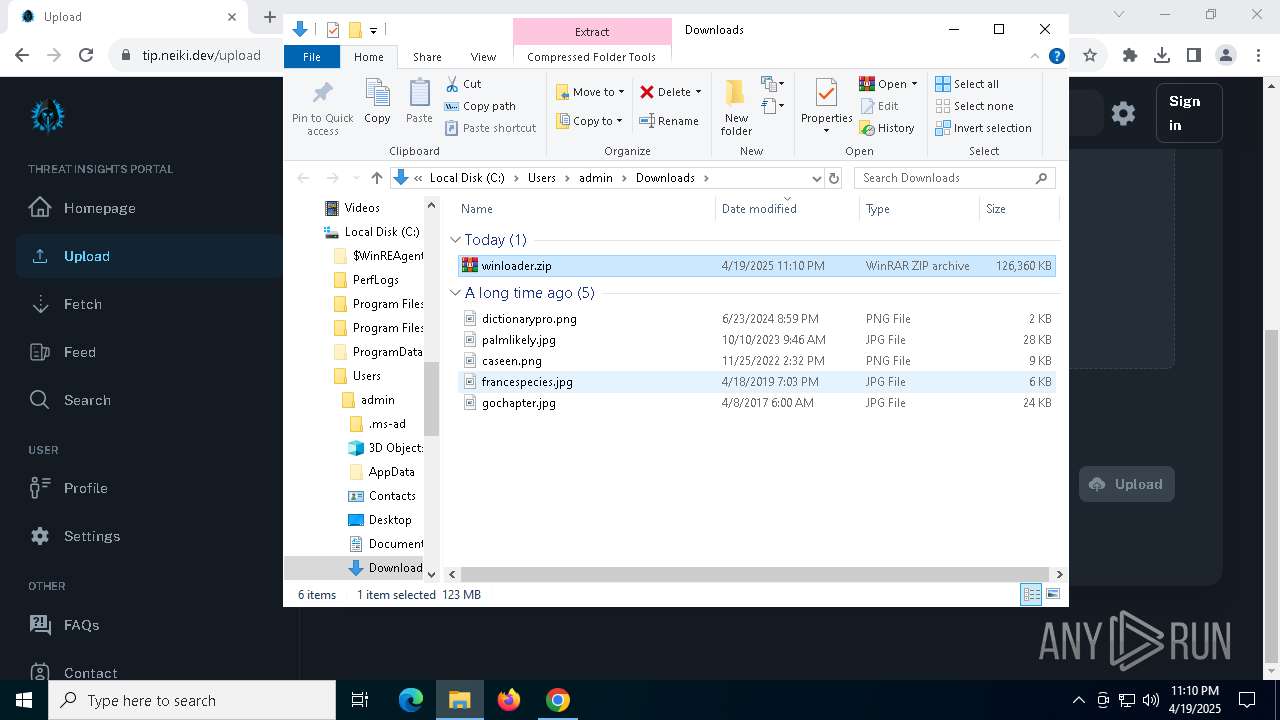
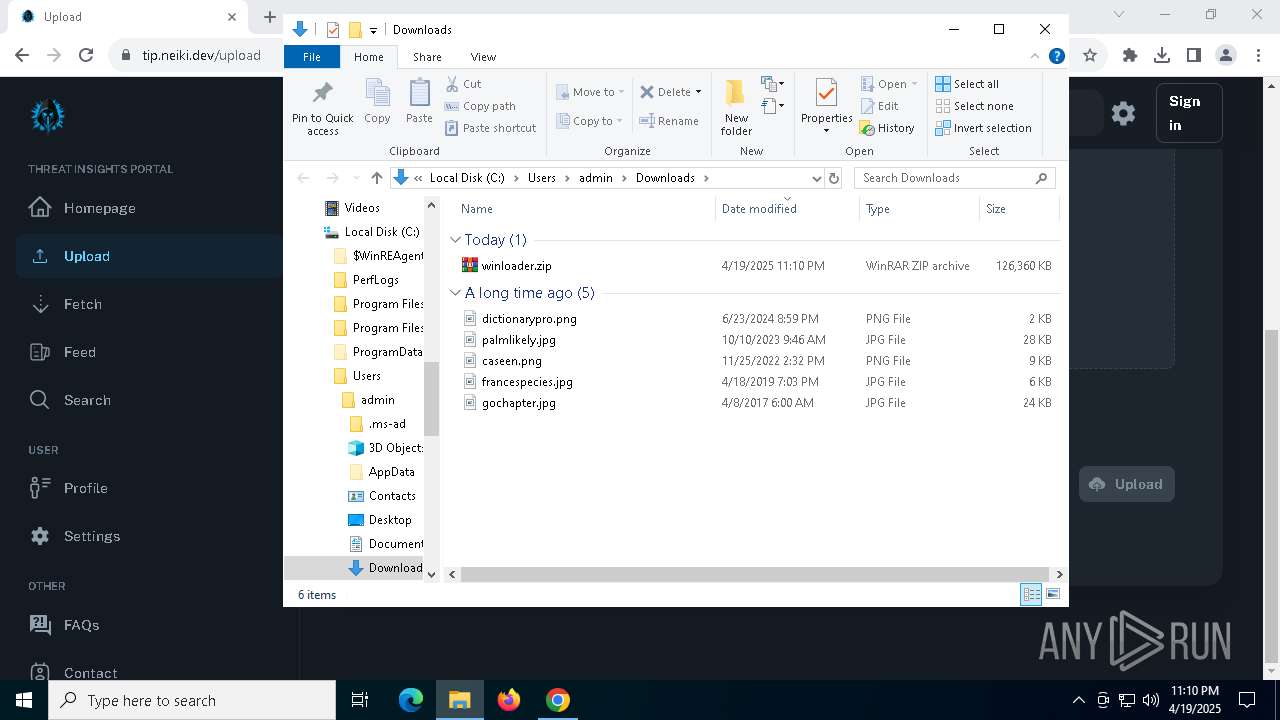
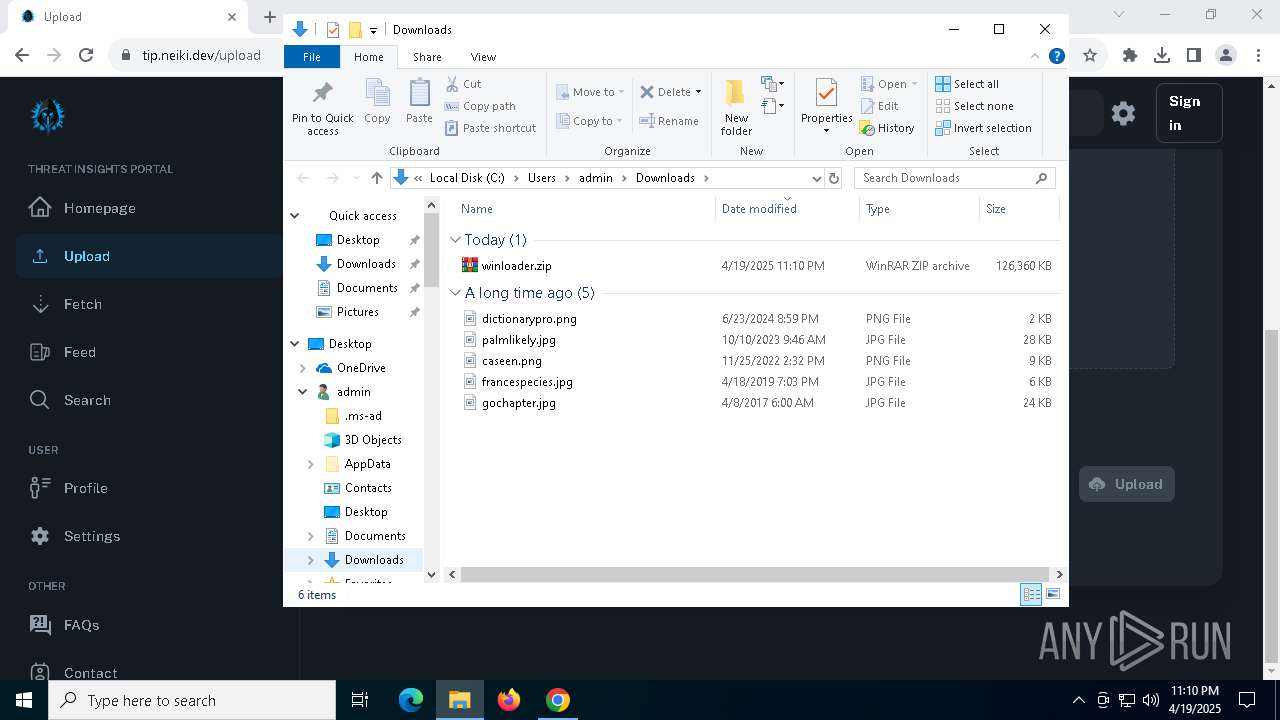
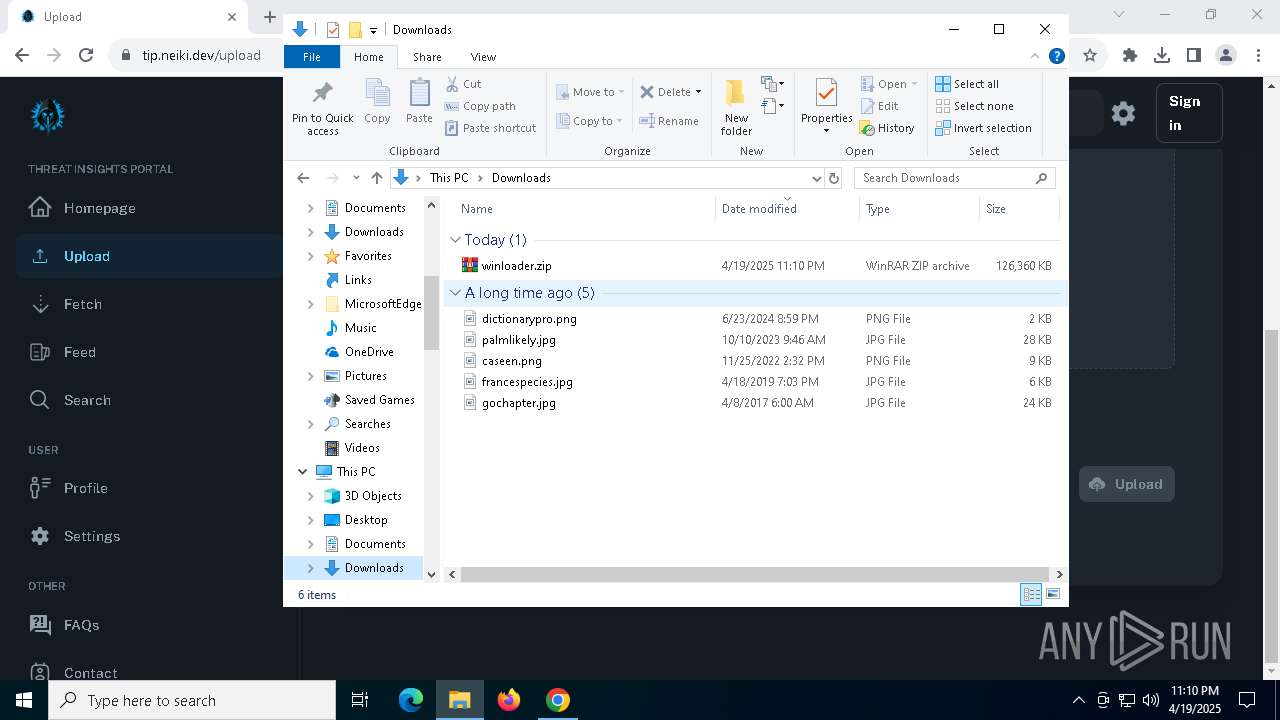
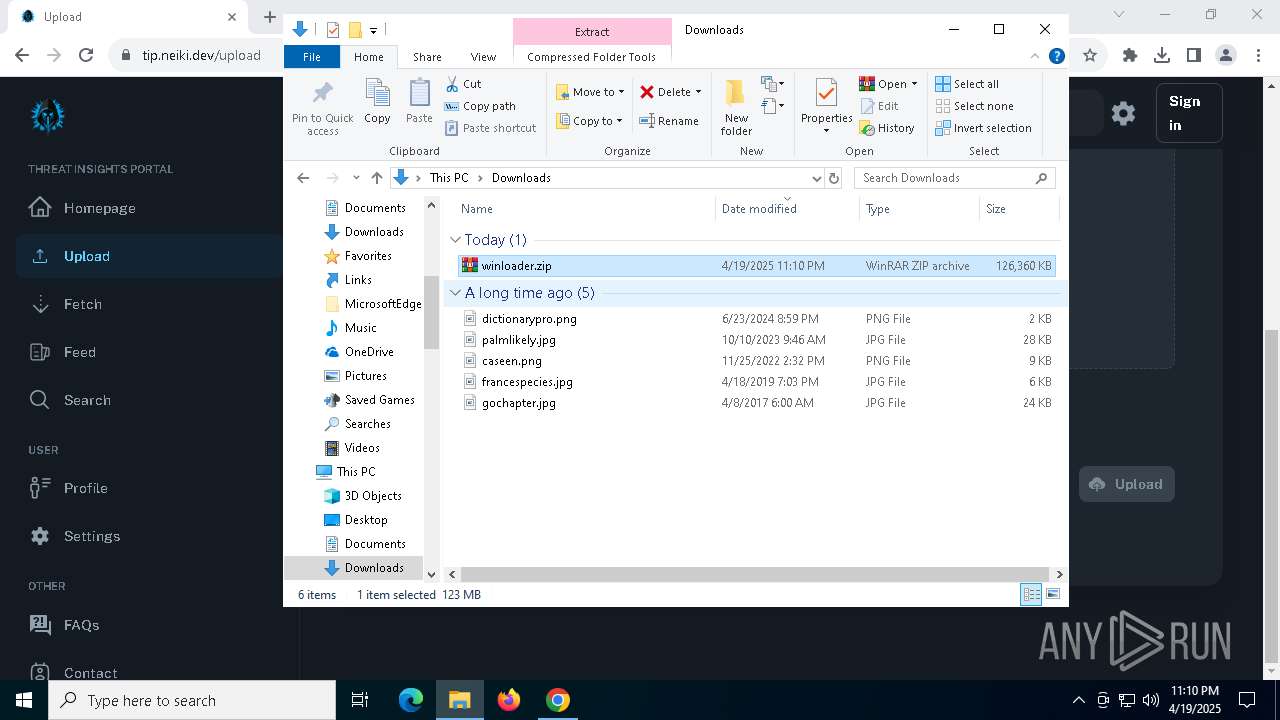
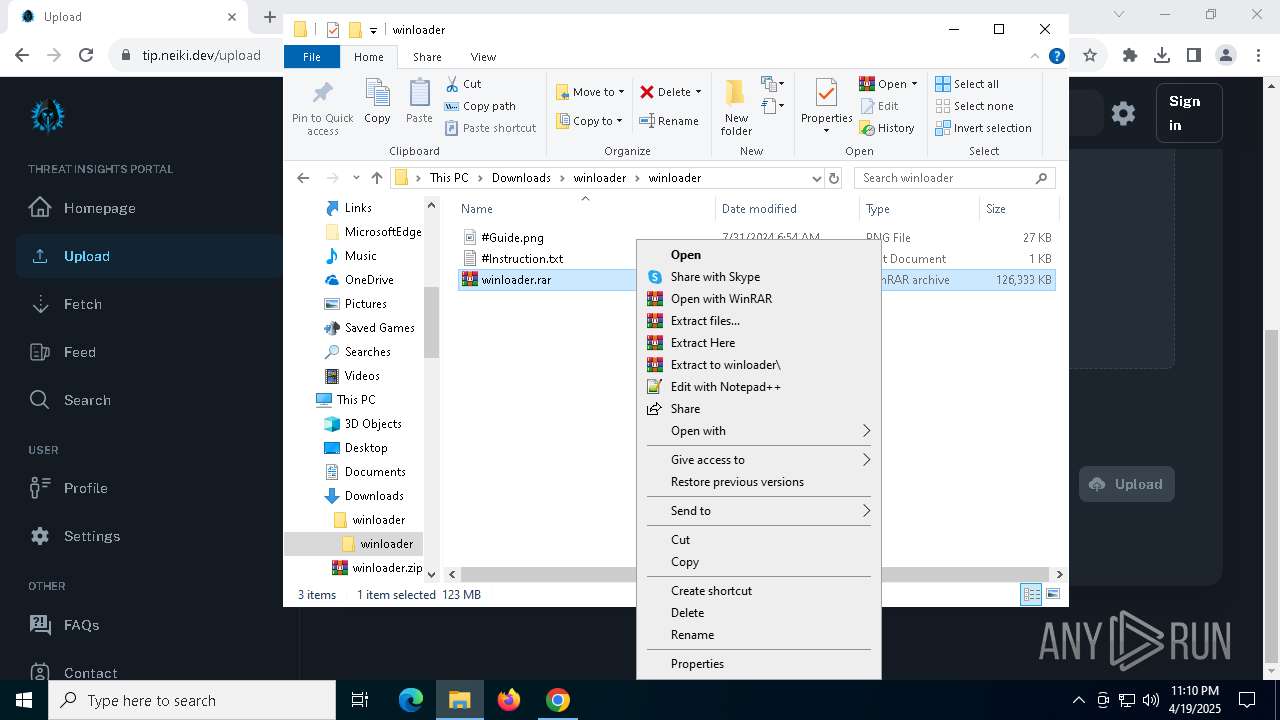
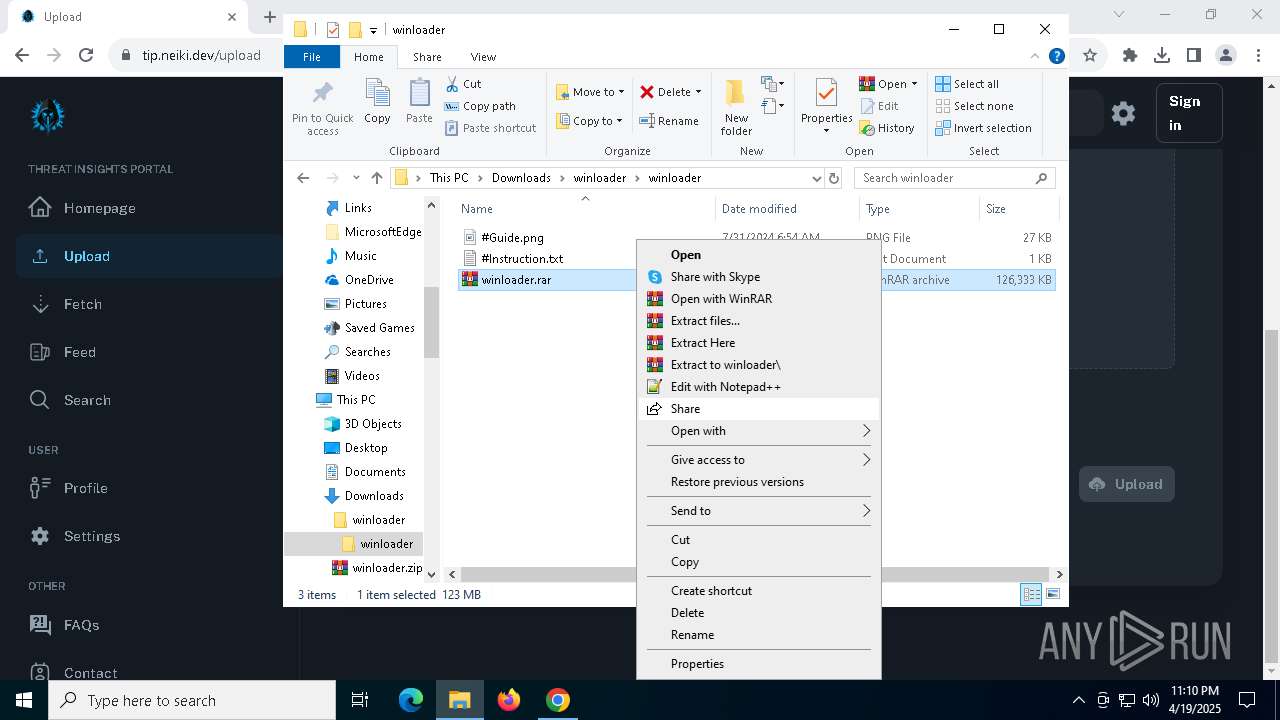
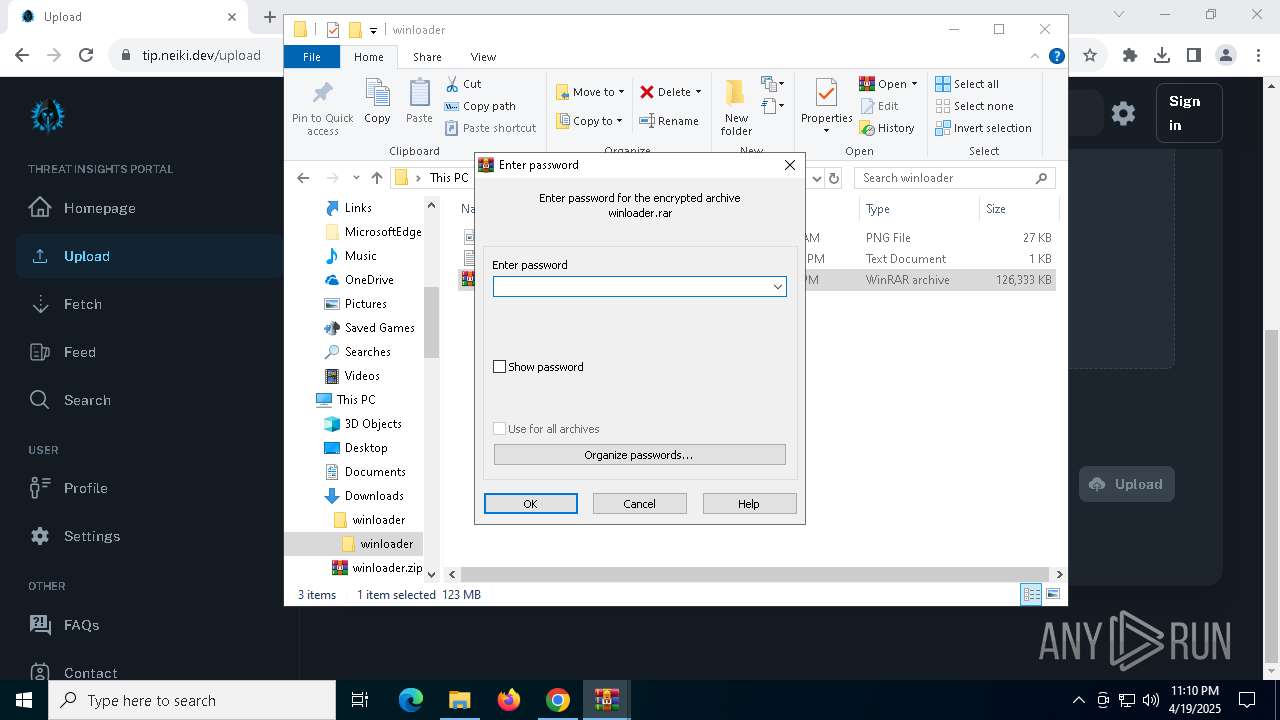
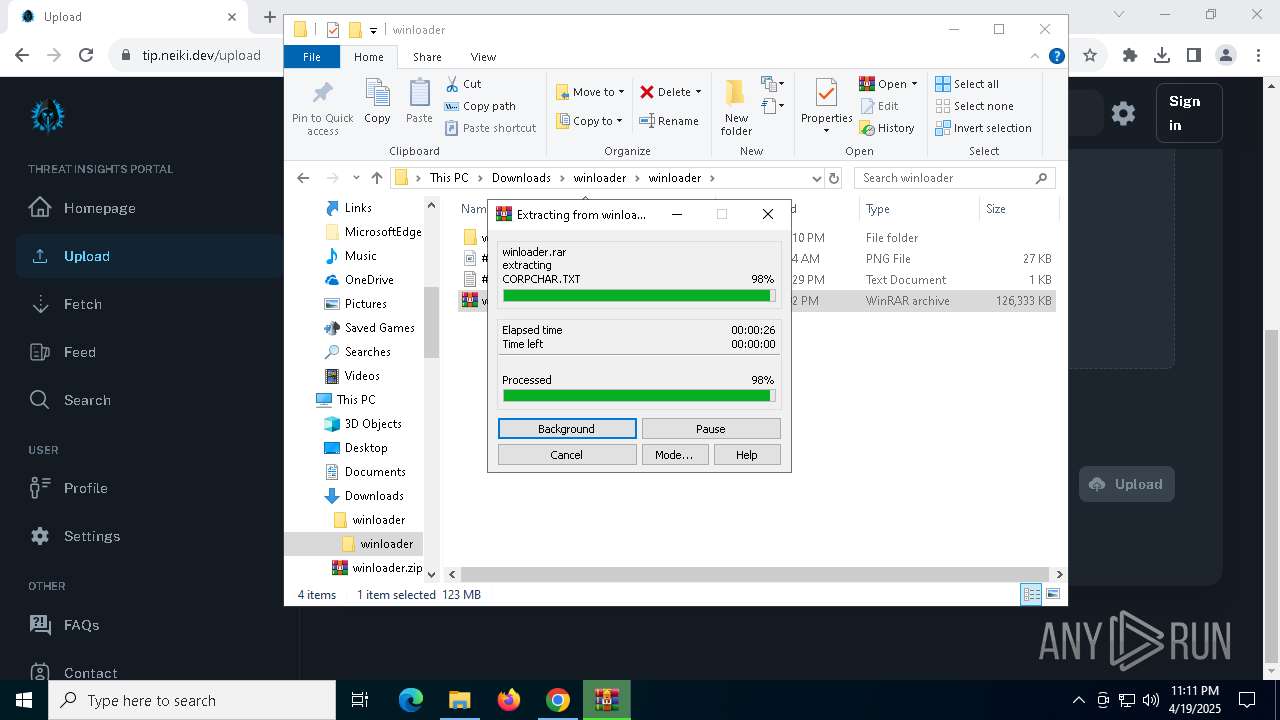
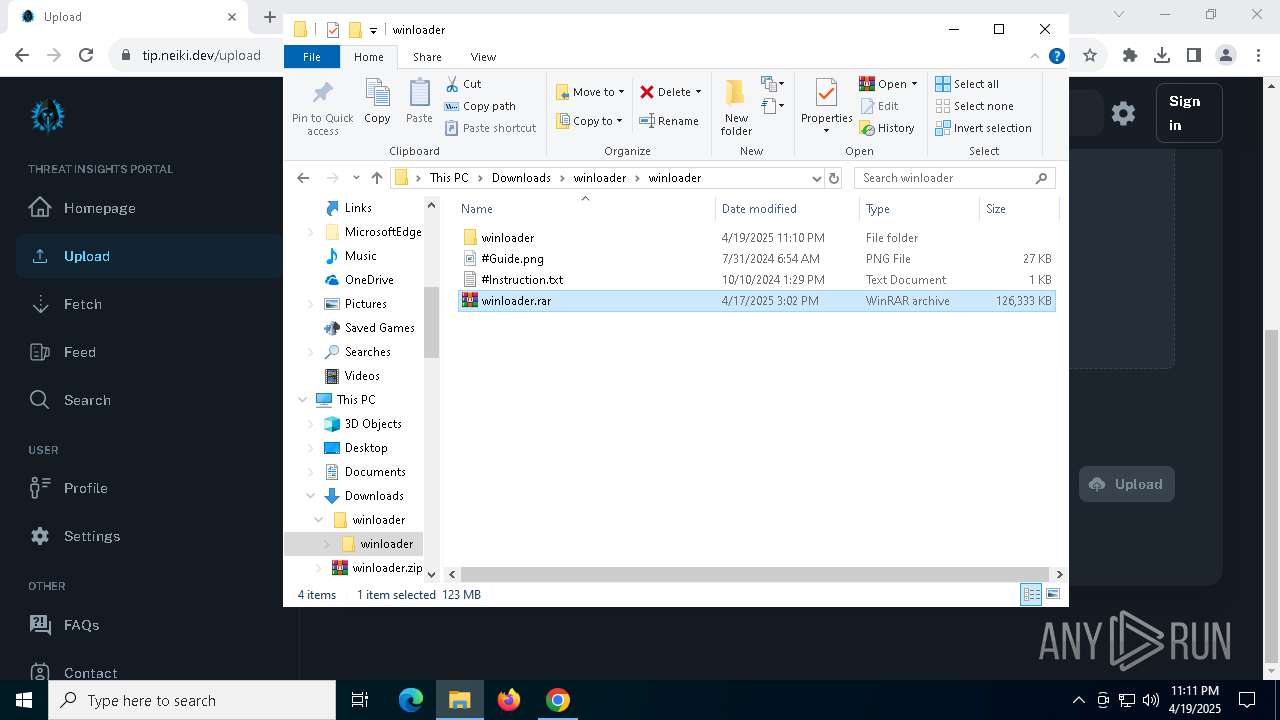
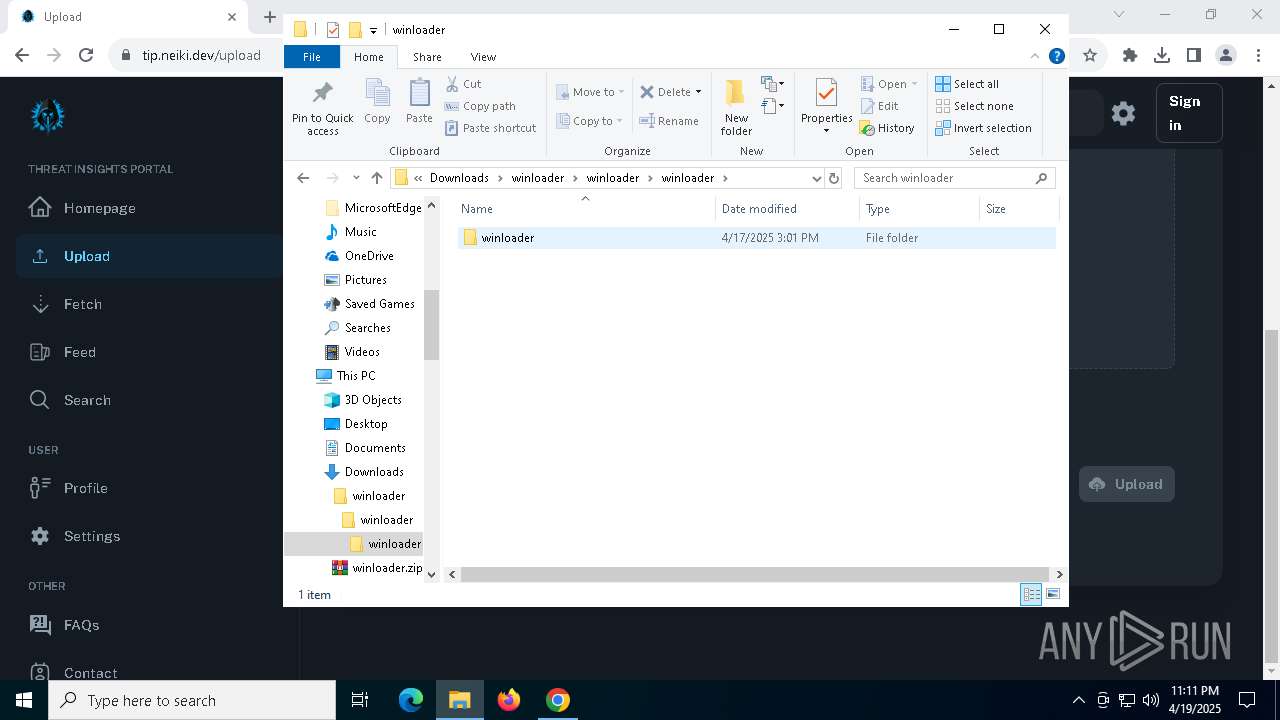
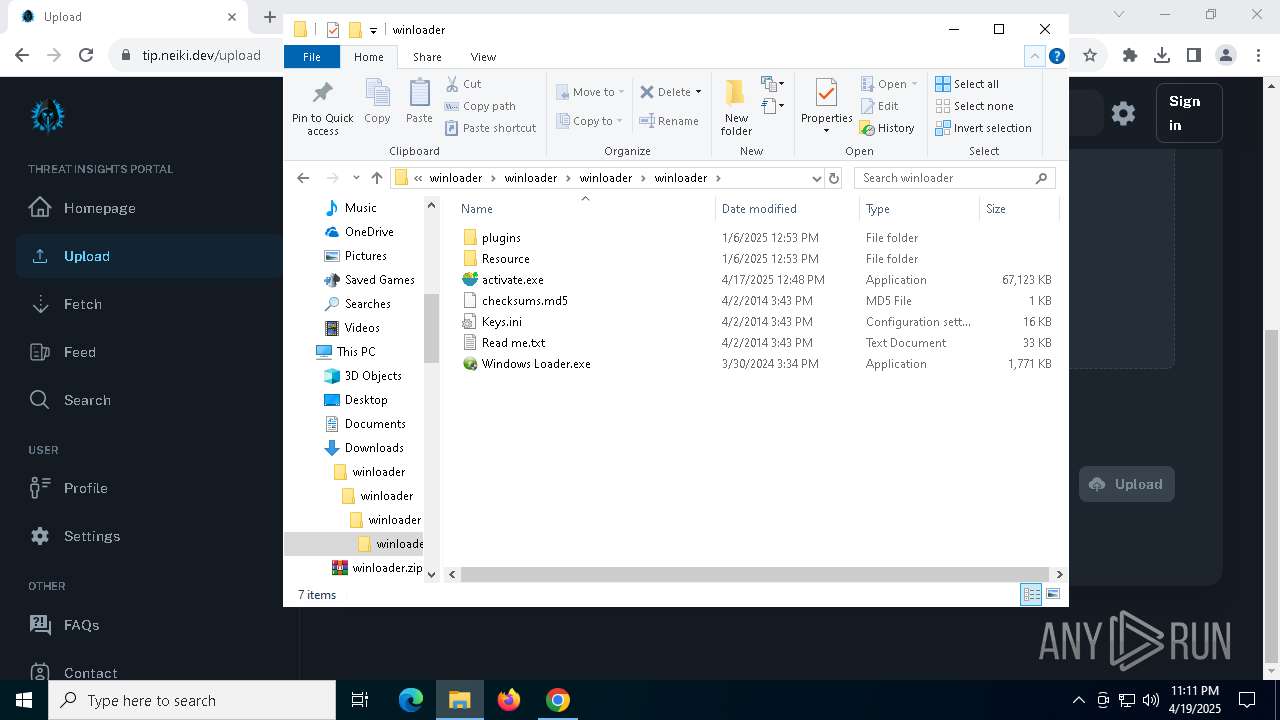
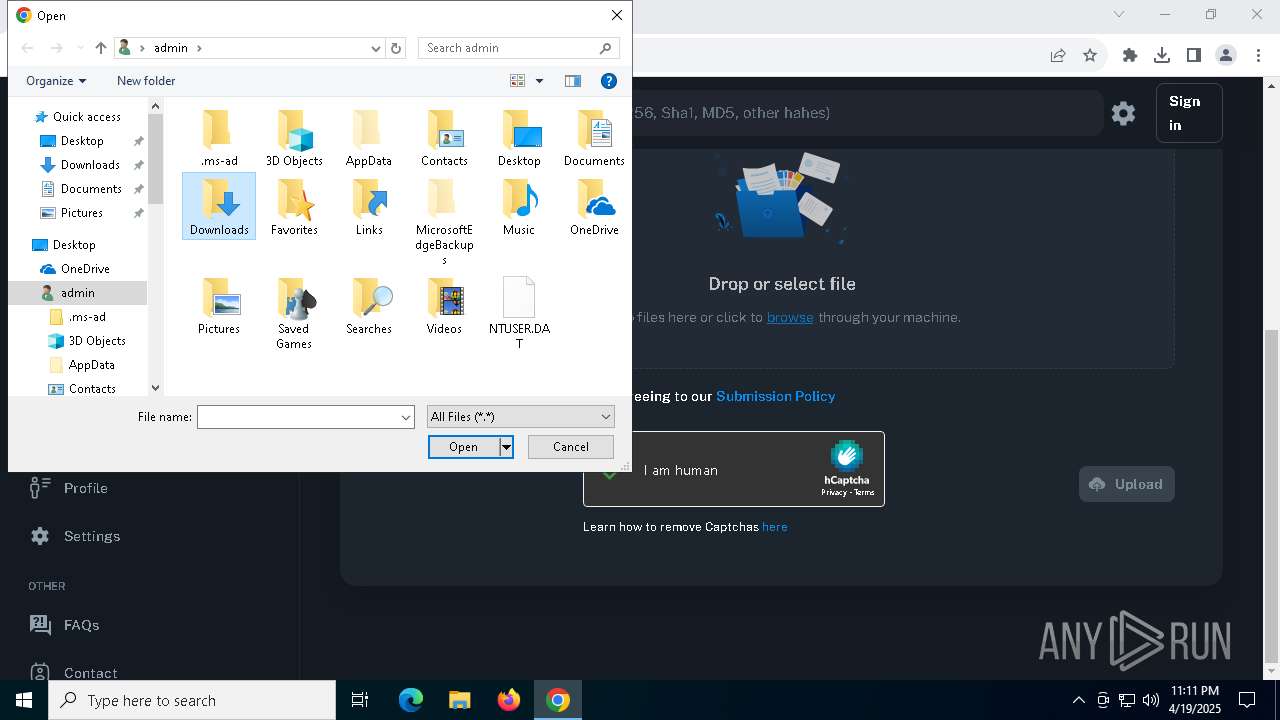
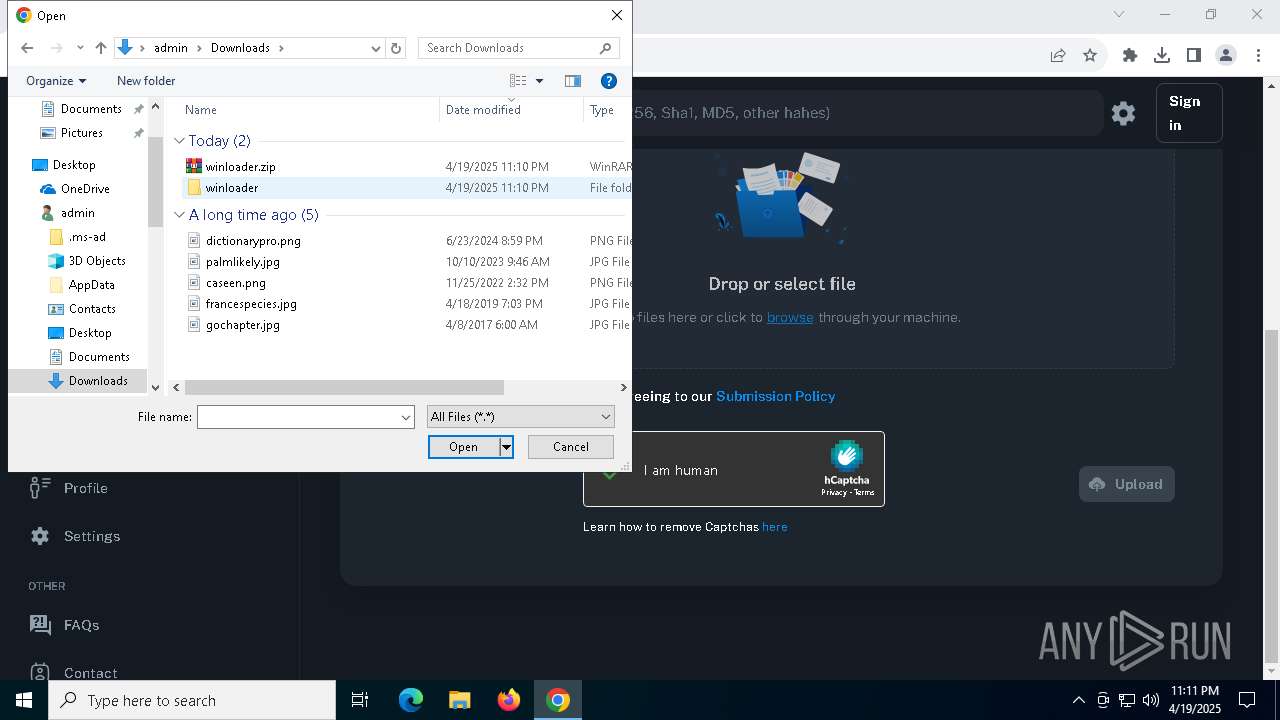
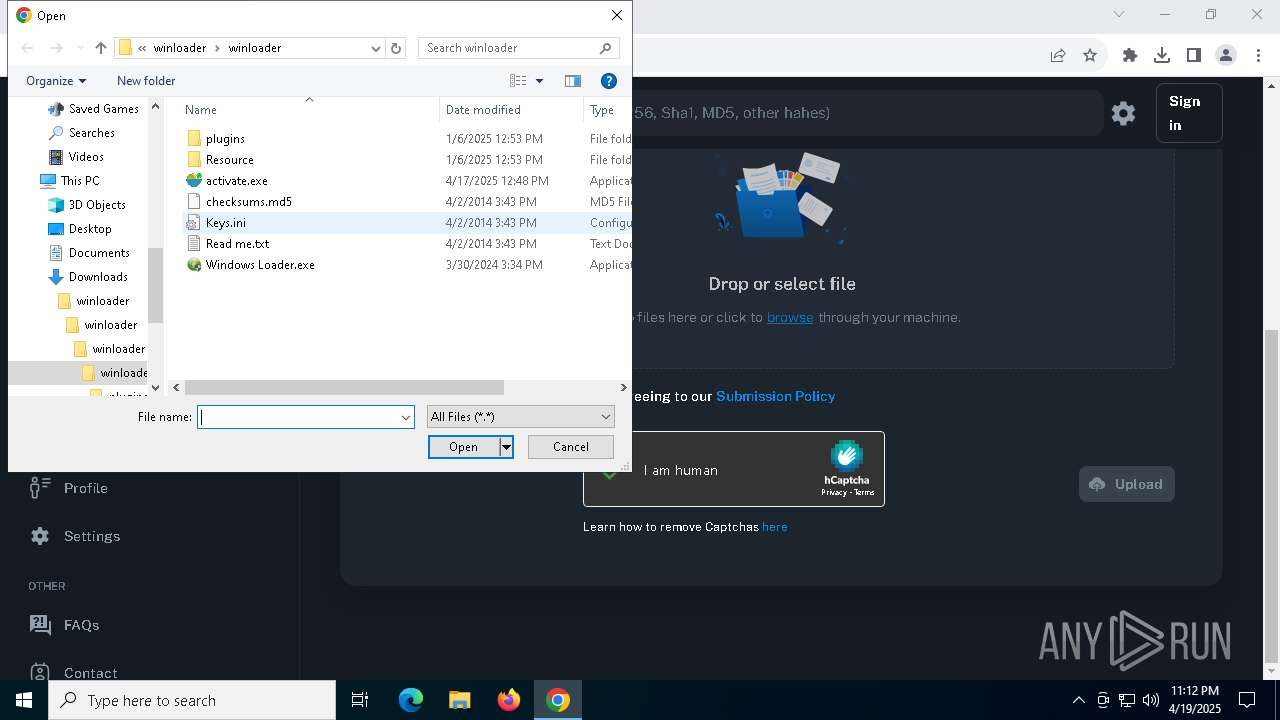
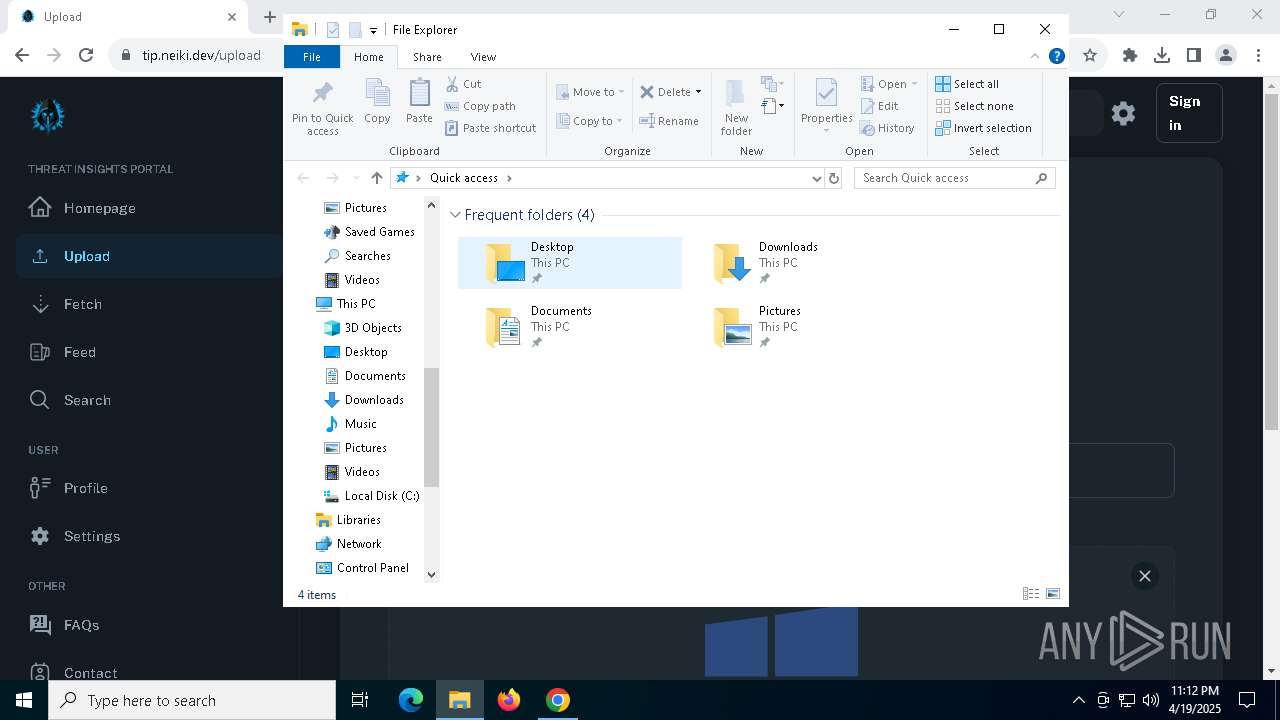
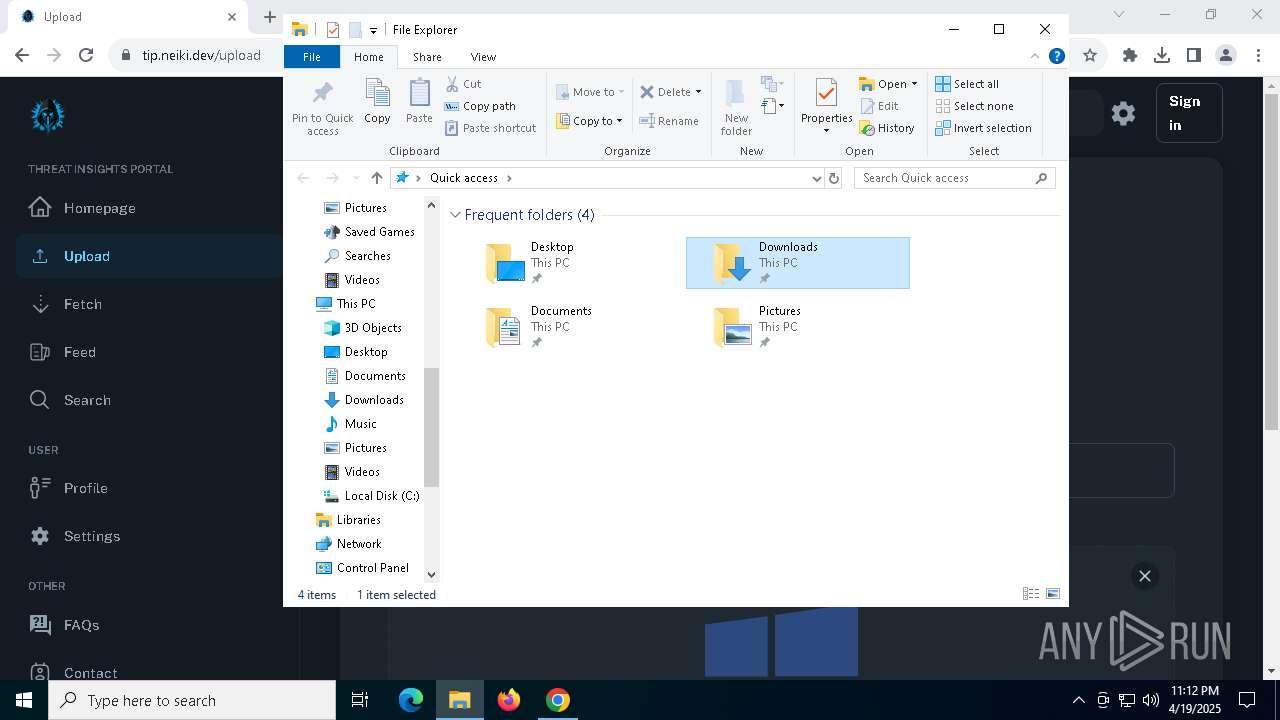
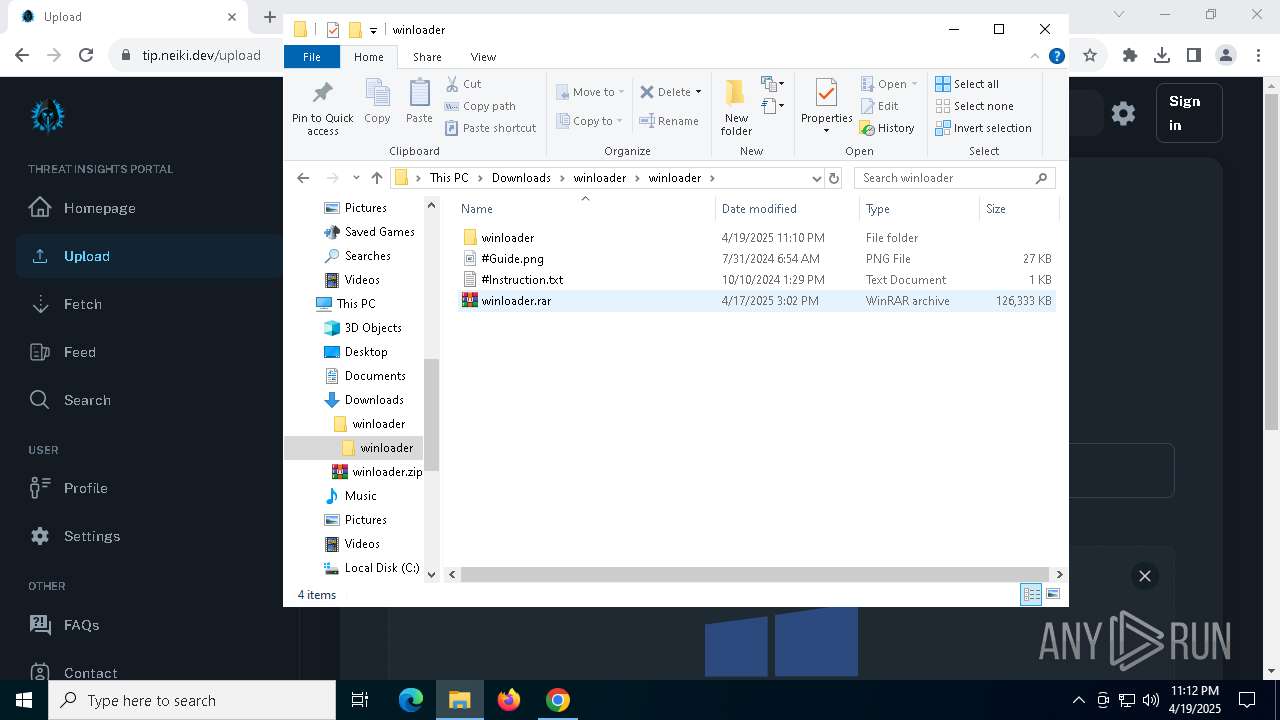
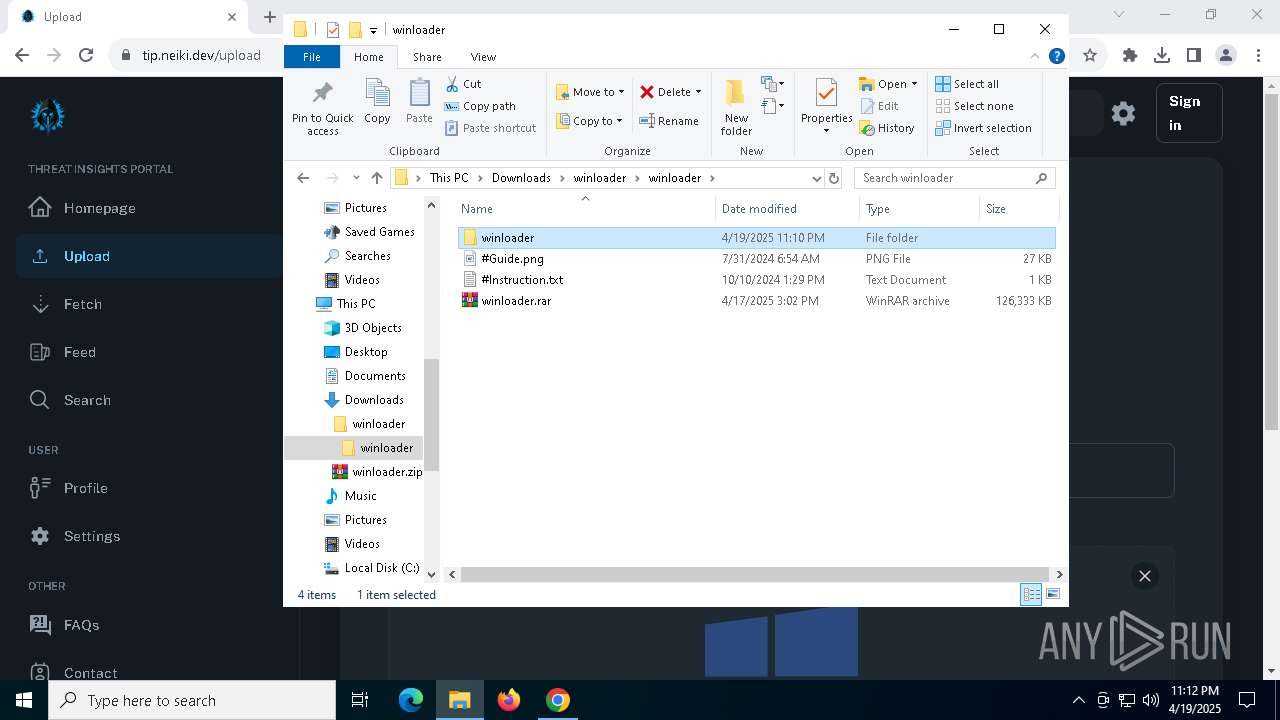
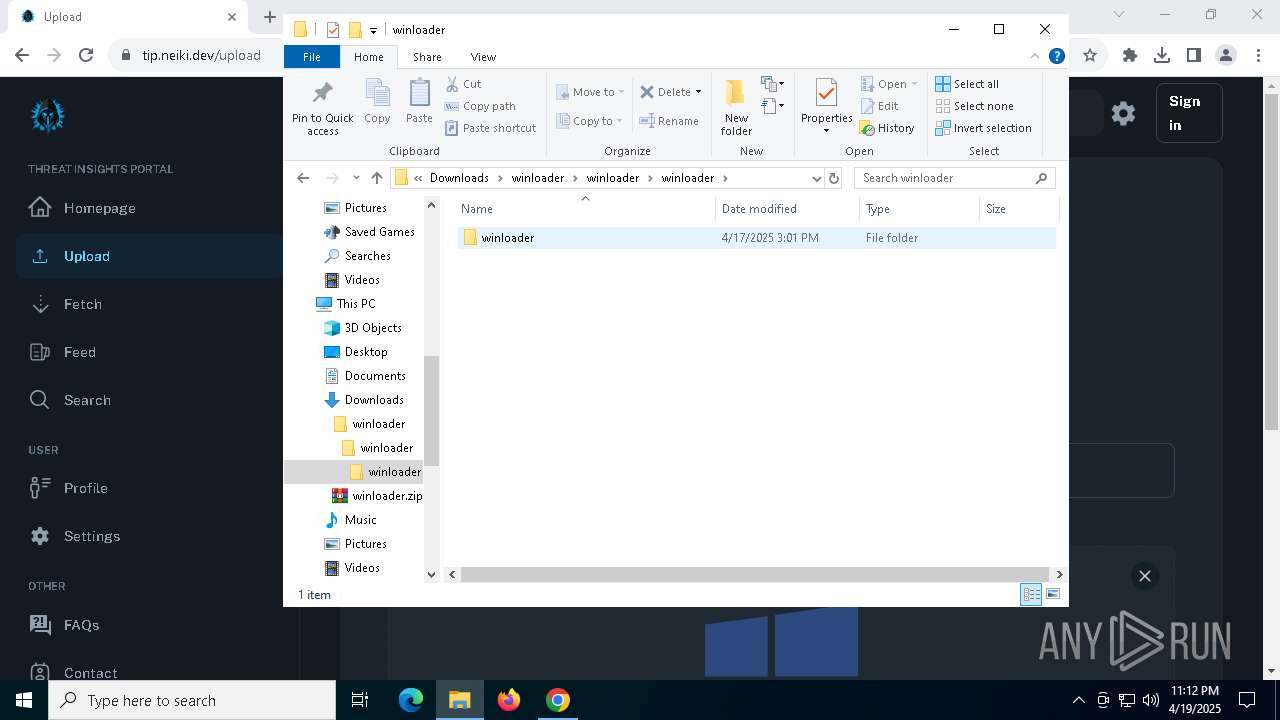
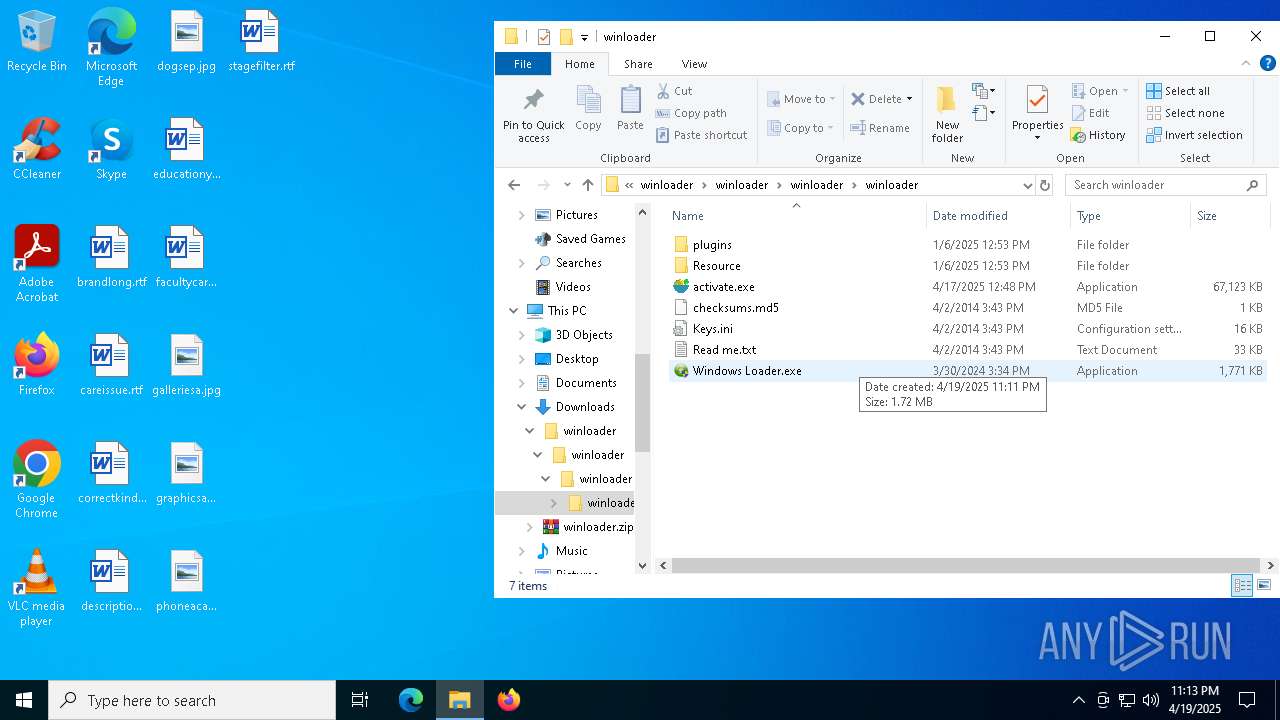
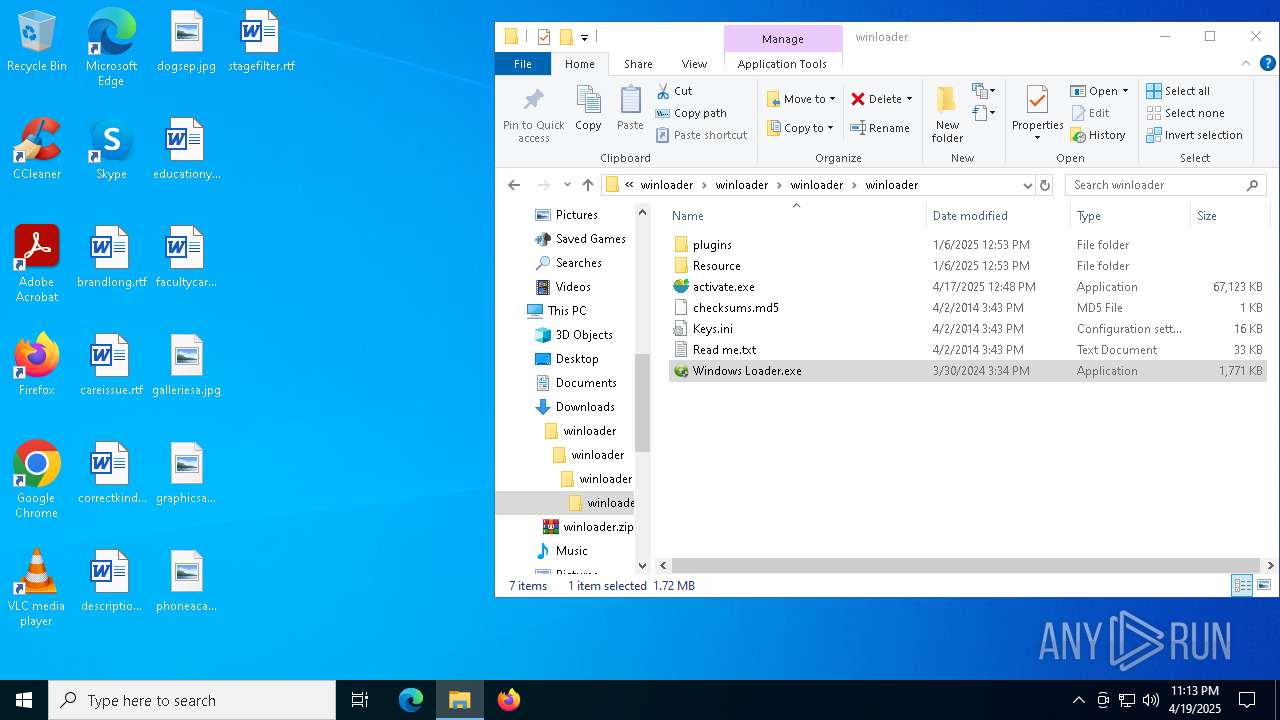
Manual execution by a user
- WinRAR.exe (PID: 8144)
- WinRAR.exe (PID: 5324)
- activate.exe (PID: 2656)
- Windows Loader.exe (PID: 2504)
- Windows Loader.exe (PID: 5452)
- Windows Loader.exe (PID: 2616)
- Windows Loader.exe (PID: 5132)
- msedge.exe (PID: 7948)
- firefox.exe (PID: 5176)
The sample compiled with chinese language support
- WinRAR.exe (PID: 8144)
The sample compiled with russian language support
- WinRAR.exe (PID: 8144)
Checks proxy server information
- slui.exe (PID: 8088)
Checks supported languages
- activate.exe (PID: 2656)
- Windows Loader.exe (PID: 2616)
- activate.exe (PID: 7888)
- activate.exe (PID: 900)
- Windows Loader.exe (PID: 5452)
Reads the computer name
- Windows Loader.exe (PID: 2616)
- Windows Loader.exe (PID: 5452)
- activate.exe (PID: 2656)
- activate.exe (PID: 7888)
- activate.exe (PID: 900)
Process checks computer location settings
- Windows Loader.exe (PID: 5452)
- Windows Loader.exe (PID: 2616)
Create files in a temporary directory
- powershell.exe (PID: 8104)
- powershell.exe (PID: 436)
- powershell.exe (PID: 7132)
Reads security settings of Internet Explorer
- powershell.exe (PID: 8104)
- powershell.exe (PID: 436)
- powershell.exe (PID: 7132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(2656) activate.exe
C2 (9)ferromny.digital/gwpd
oreheatq.live/gsopp
castmaxw.run/ganzde
steelgoy.run/pqowen
weldorae.digital/geds
advennture.top/GKsiio
smeltingt.run/giiaus
steelixr.live/aguiz
targett.top/dsANGt
Total processes
245
Monitored processes
103
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6192 --field-trial-handle=1840,i,6345948306723095321,12589665400820849089,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 436 | powershell -exec bypass <!DOCTYPE html> <html lang="en"> <head> <meta name="viewport" content="width=device-width, initial-scale=0.75, maximum-scale=1.0, user-scalable=yes" /> <meta http-equiv="Content-Type" content="text/html; charset=utf-8" /> <title>Pastebin.com - Not Found (#404)</title> </head> <body> <h1>Not Found (#404)</h1> <p>This page is no longer available. It has either expired, been removed by its creator, or removed by one of the Pastebin staff.</p> </body> </html> | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | activate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=4628 --field-trial-handle=2336,i,16945275497305483094,7911709020054753975,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2372 --field-trial-handle=2376,i,14561493431126066024,6143157488727599362,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://oficial-kmspico.org/windows-loader/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
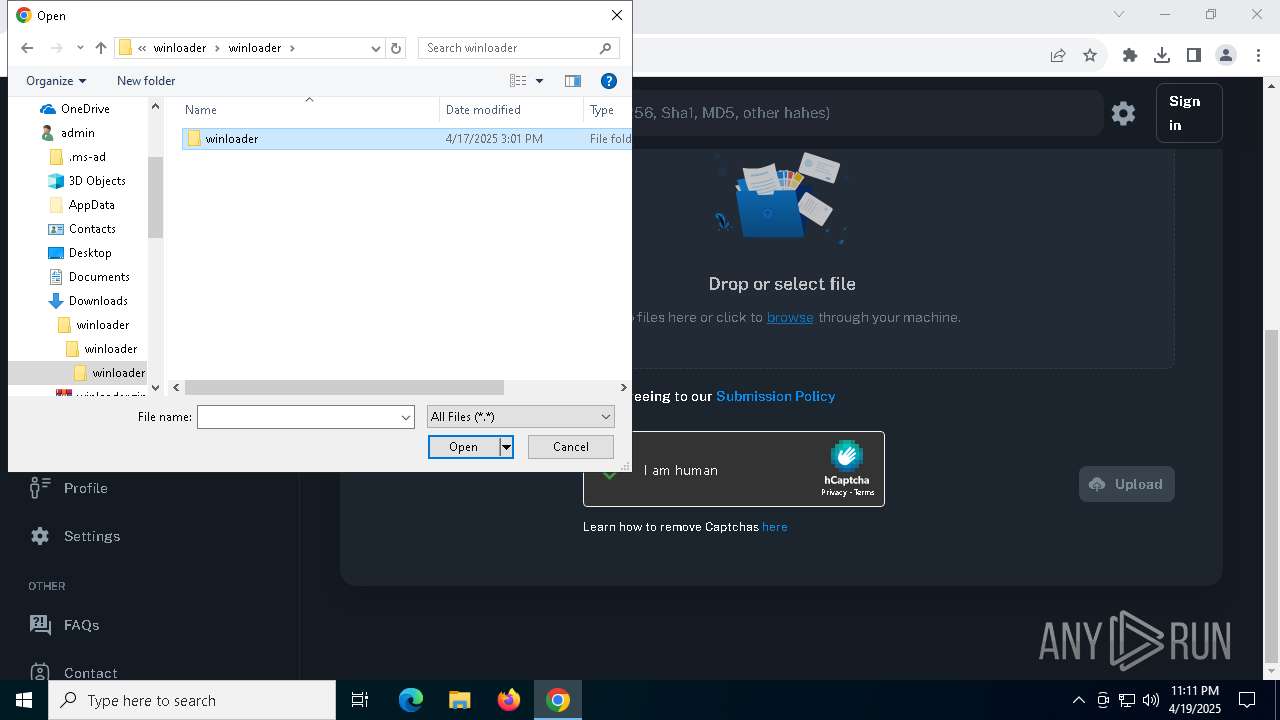
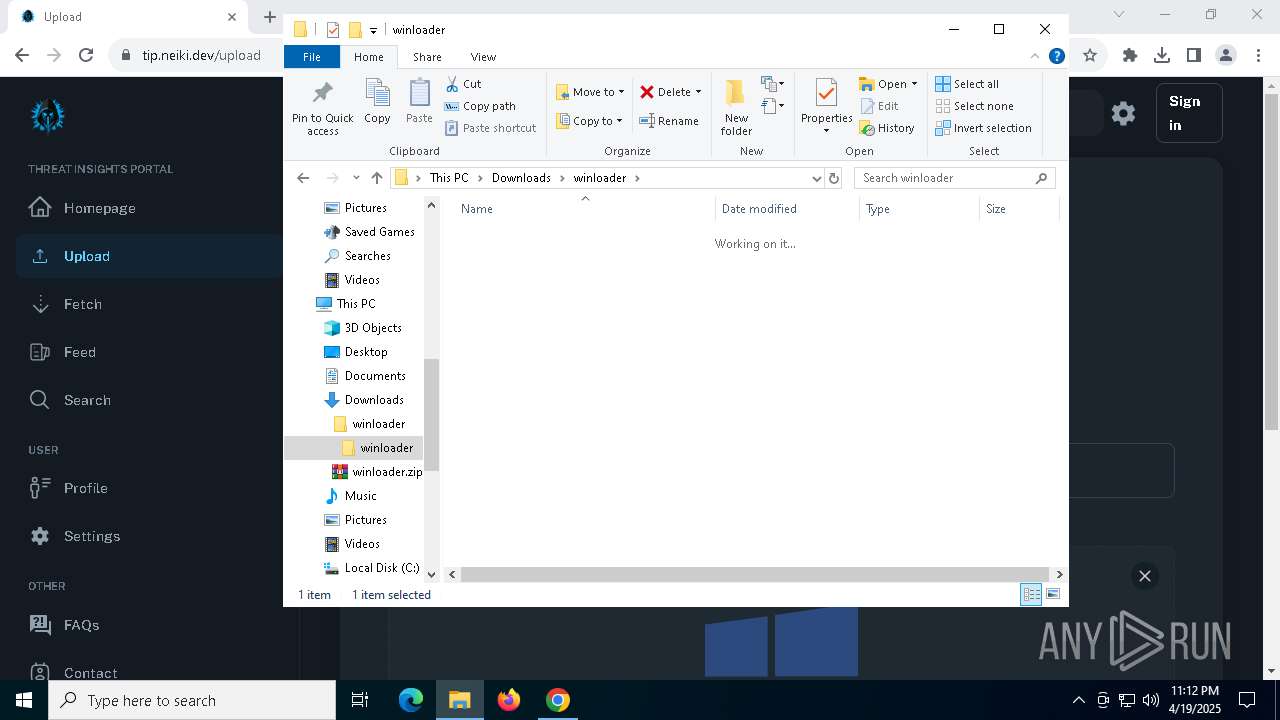
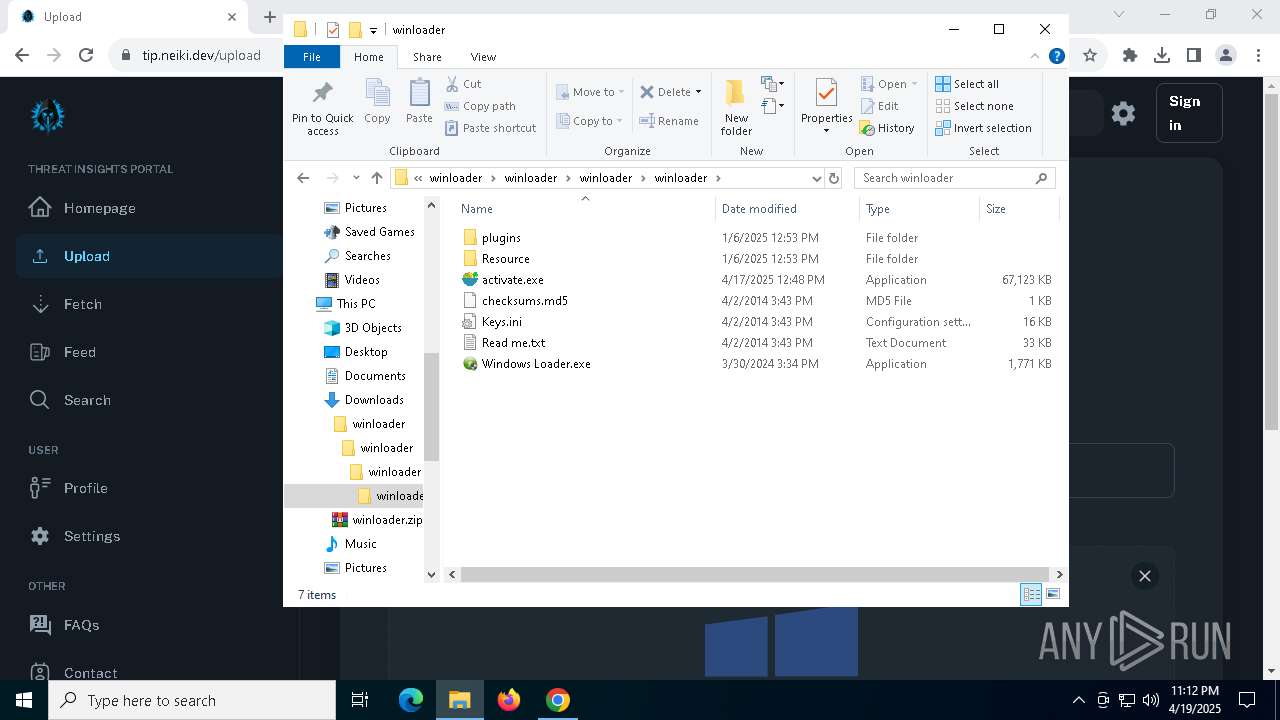
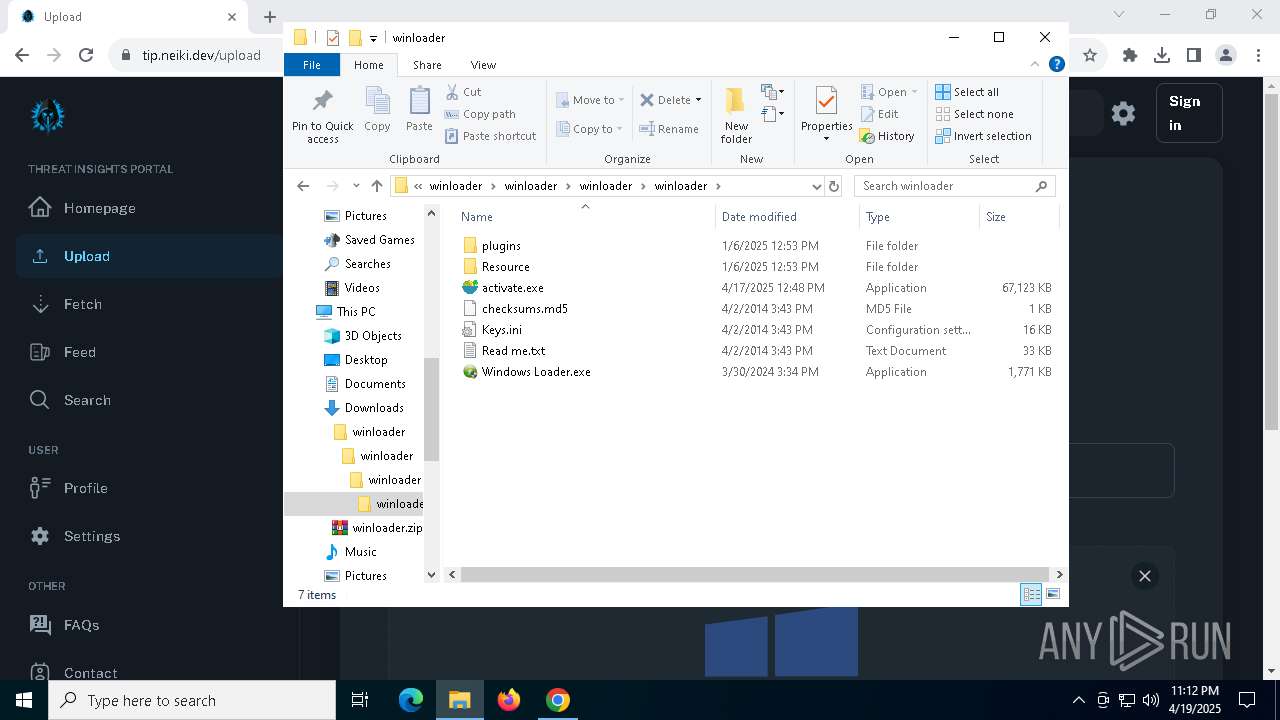
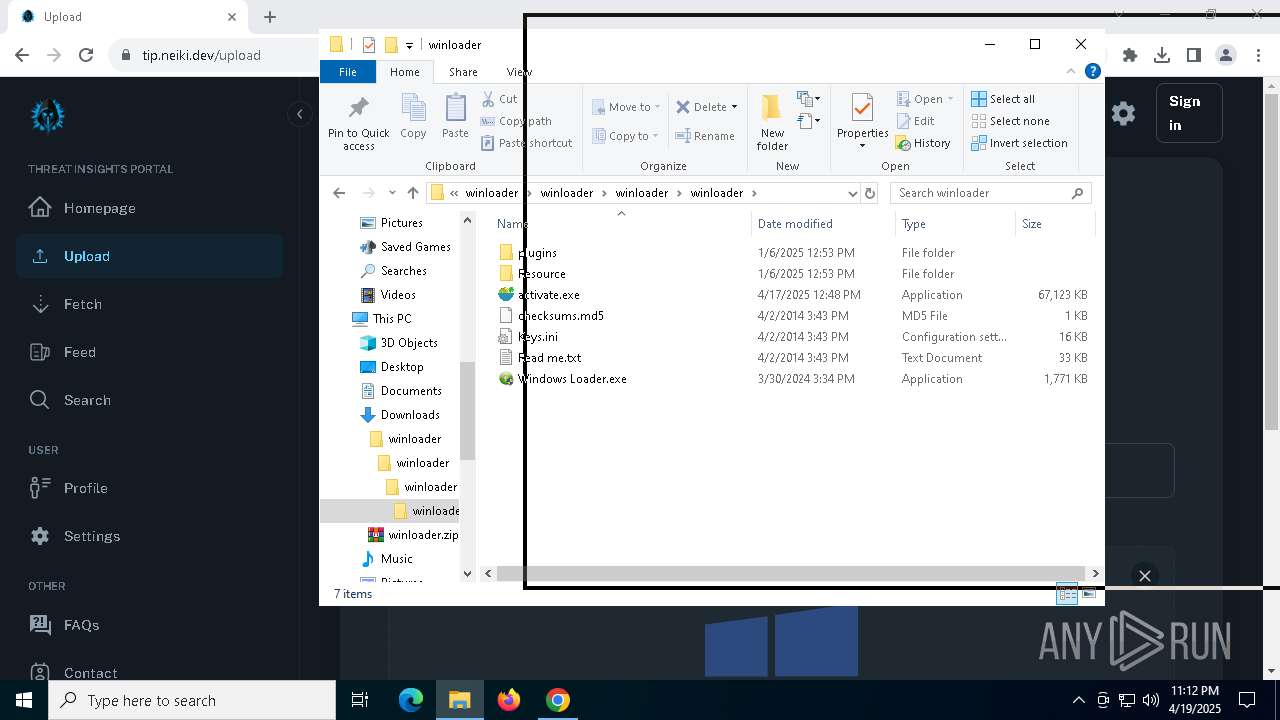
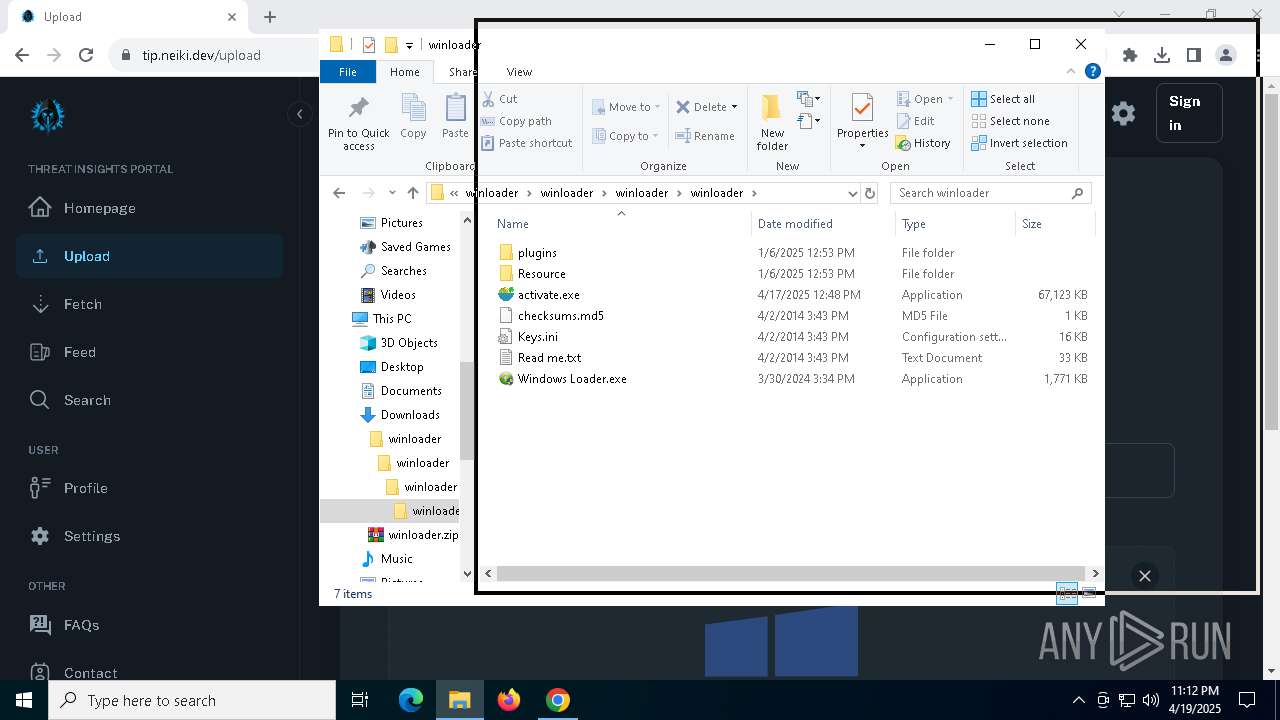
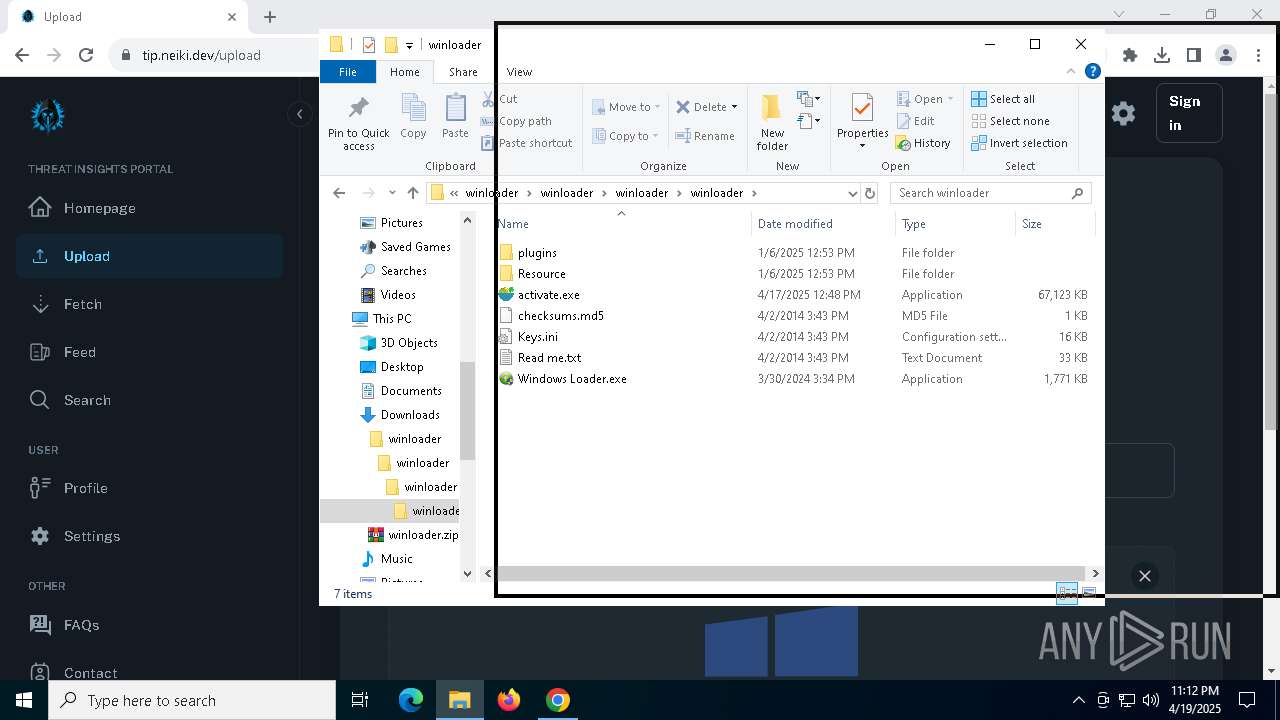
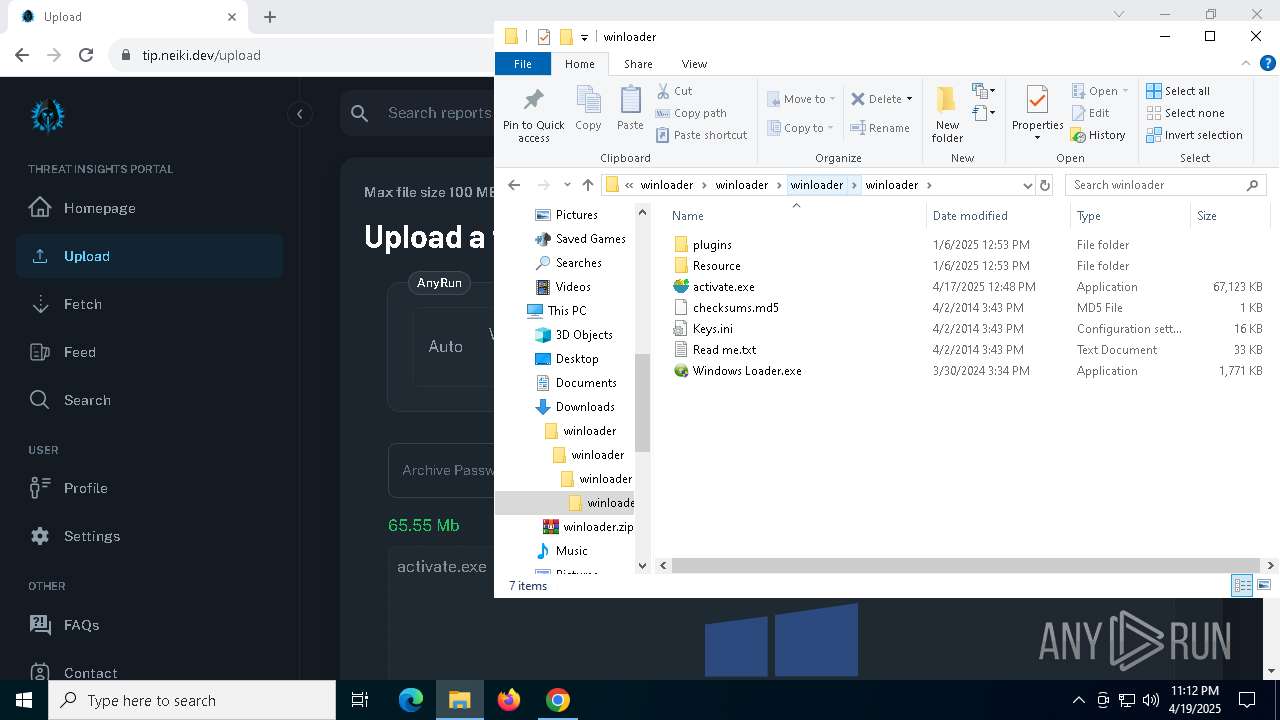
| 900 | "C:\Users\admin\Downloads\winloader\winloader\winloader\winloader\activate.exe" | C:\Users\admin\Downloads\winloader\winloader\winloader\winloader\activate.exe | Windows Loader.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: saladict Version: 3.0.8 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=3548 --field-trial-handle=1840,i,6345948306723095321,12589665400820849089,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5580 -childID 9 -isForBrowser -prefsHandle 4156 -prefMapHandle 4144 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {67d506bb-7780-4526-9a2b-d2b7c75781f4} 6488 "\\.\pipe\gecko-crash-server-pipe.6488" 28da90ba4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4836 -childID 4 -isForBrowser -prefsHandle 4704 -prefMapHandle 4628 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {58f129e8-7789-4685-9418-3d2b94c636b6} 6488 "\\.\pipe\gecko-crash-server-pipe.6488" 28da2f04a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=5520 --field-trial-handle=1840,i,6345948306723095321,12589665400820849089,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
60 952
Read events
60 618
Write events
296
Delete events
38
Modification events
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D45D8D3780B1DB01 | |||
Executable files
87
Suspicious files
682
Text files
656
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c1cb.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c1db.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
200
DNS requests
269
Threats
40
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7940 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2148 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7940 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2148 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2148 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2148 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2148 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2148 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7316 | chrome.exe | 104.21.48.1:443 | oficial-kmspico.org | CLOUDFLARENET | — | unknown |
896 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7316 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7316 | chrome.exe | 142.250.184.200:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7316 | chrome.exe | 88.212.201.198:443 | counter.yadro.ru | United Network LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
oficial-kmspico.org |
| unknown |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
s.gravatar.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
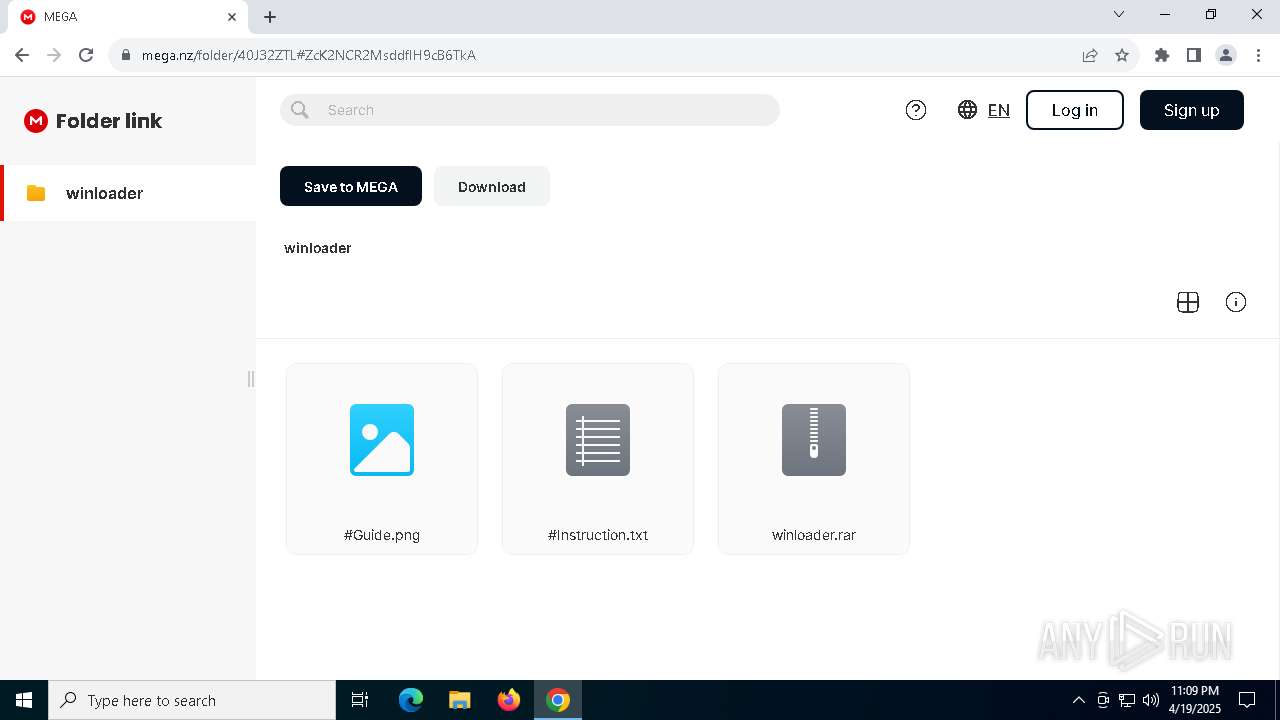
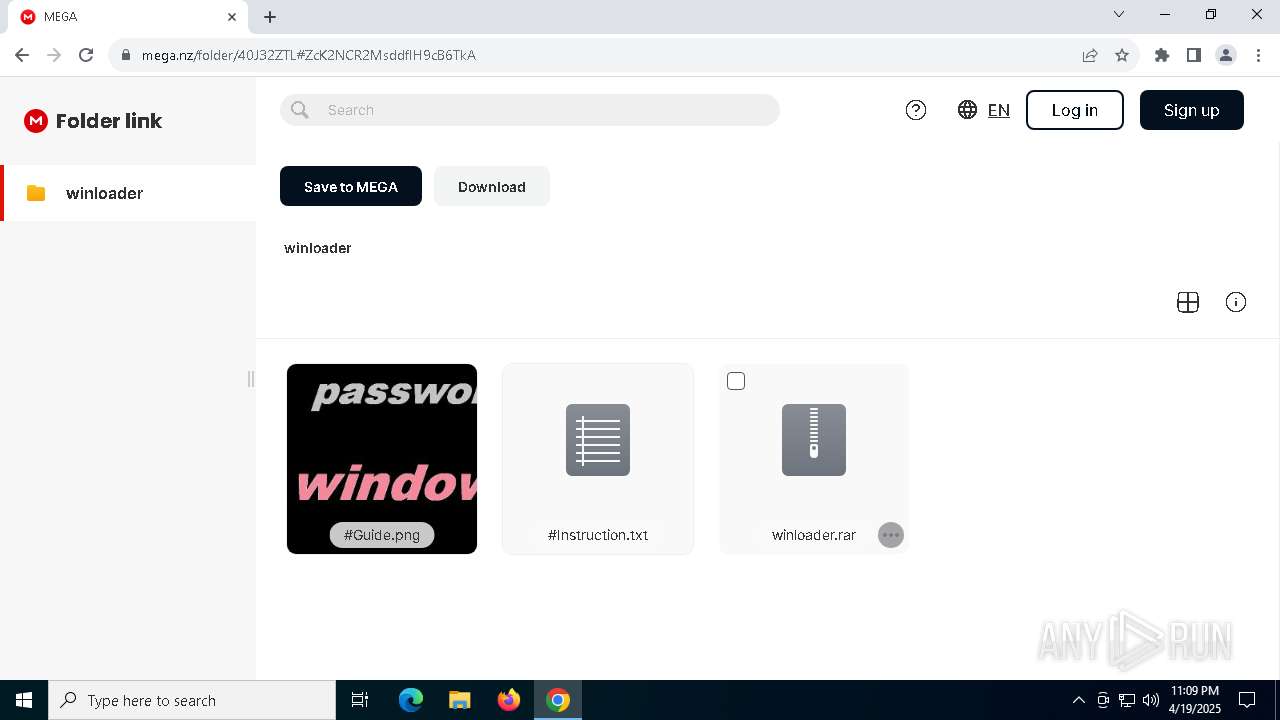
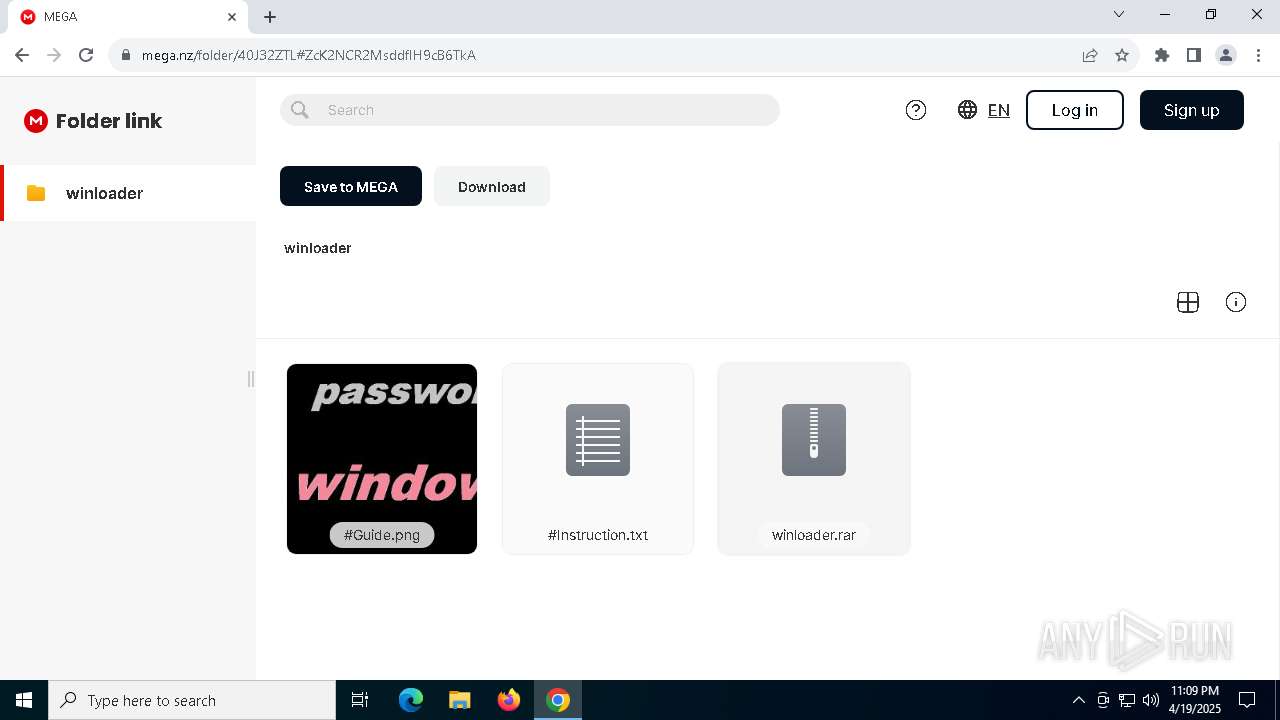
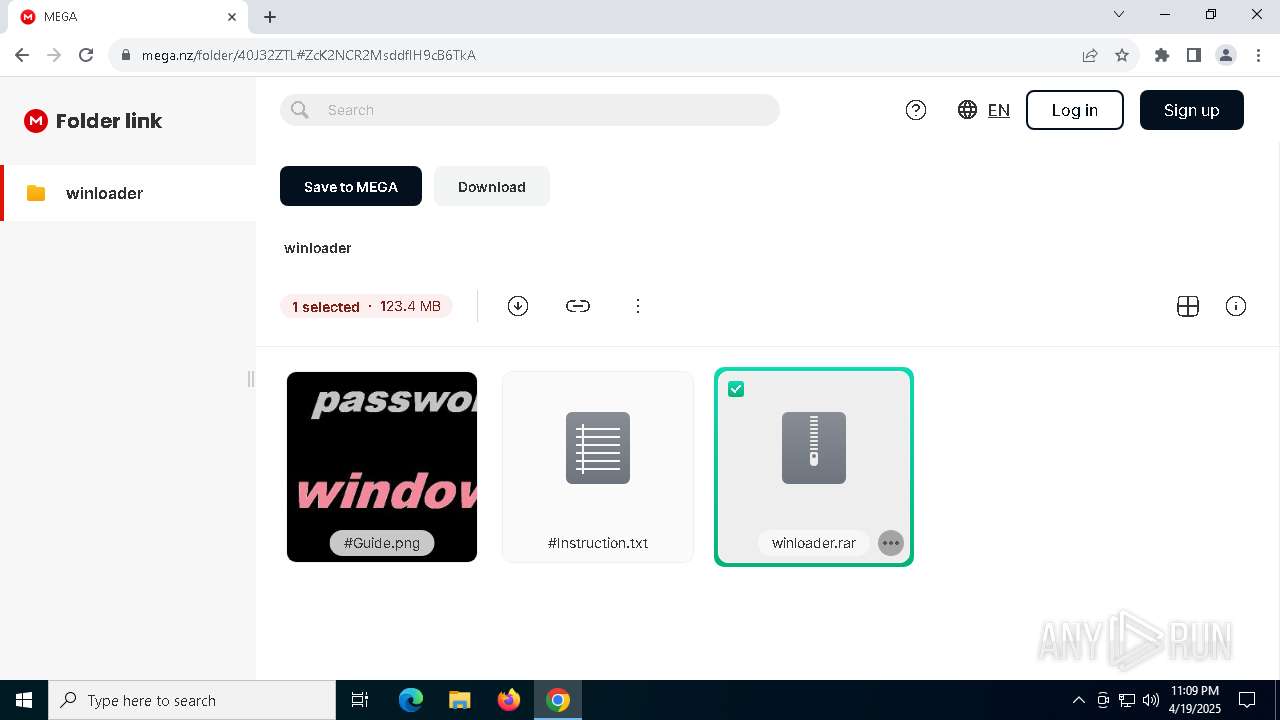
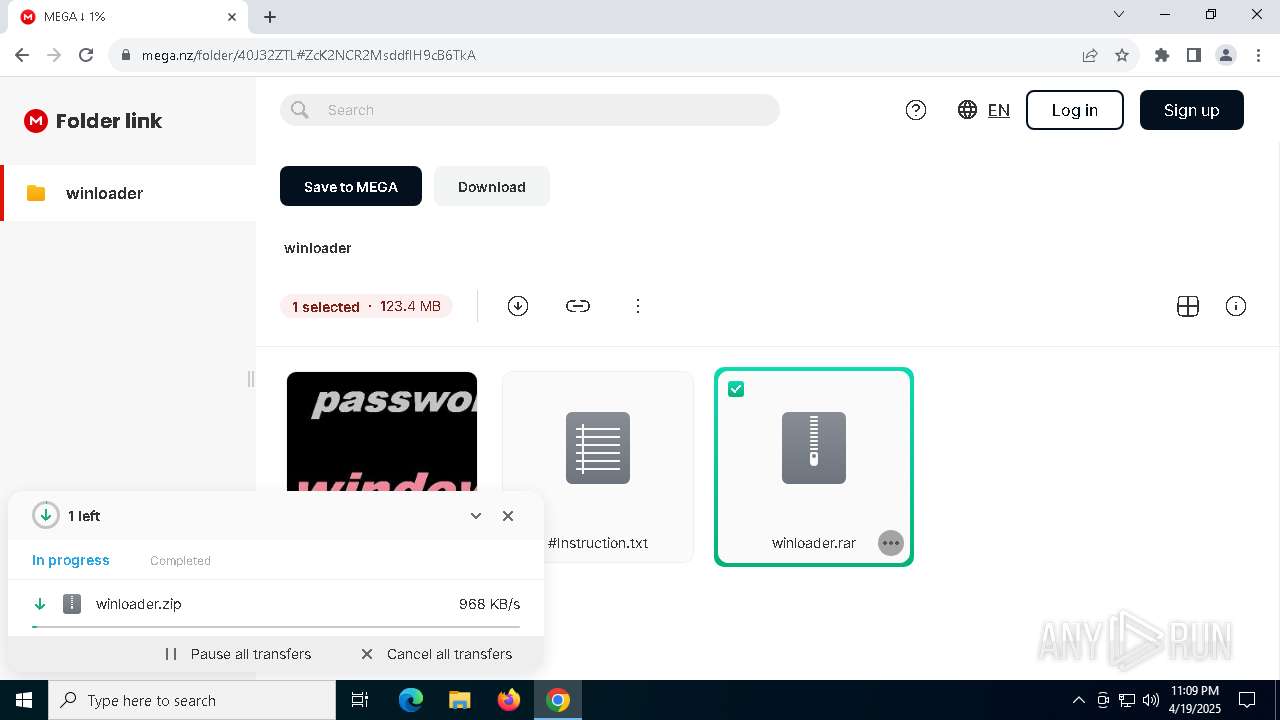
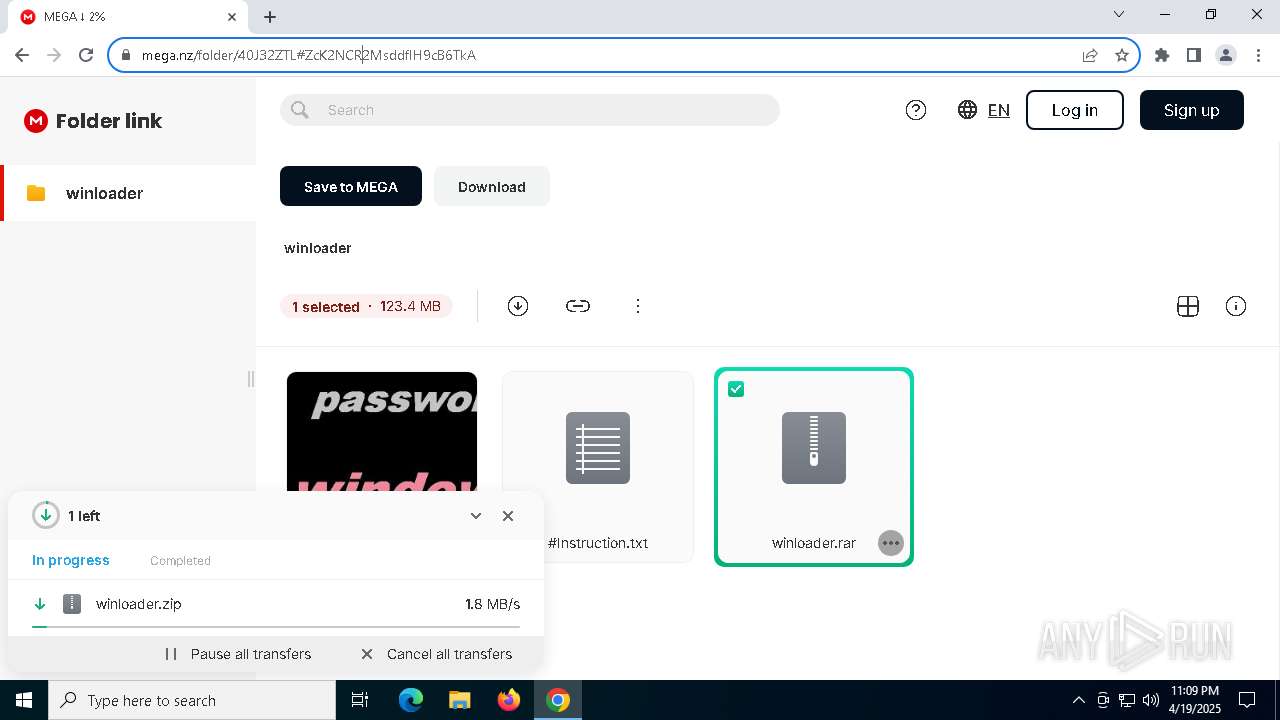
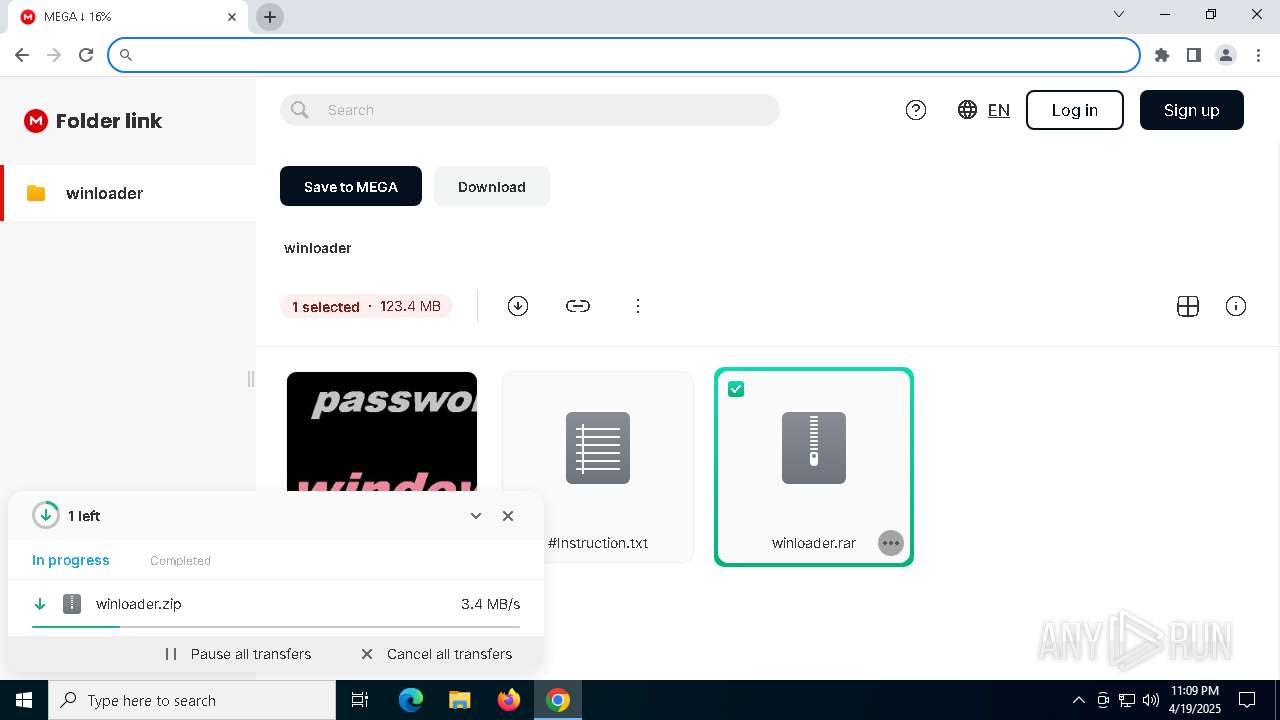
7316 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7316 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |