| File name: | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe |
| Full analysis: | https://app.any.run/tasks/58222211-4172-4983-b7bf-4242ddcc3053 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 16, 2024, 22:43:19 |
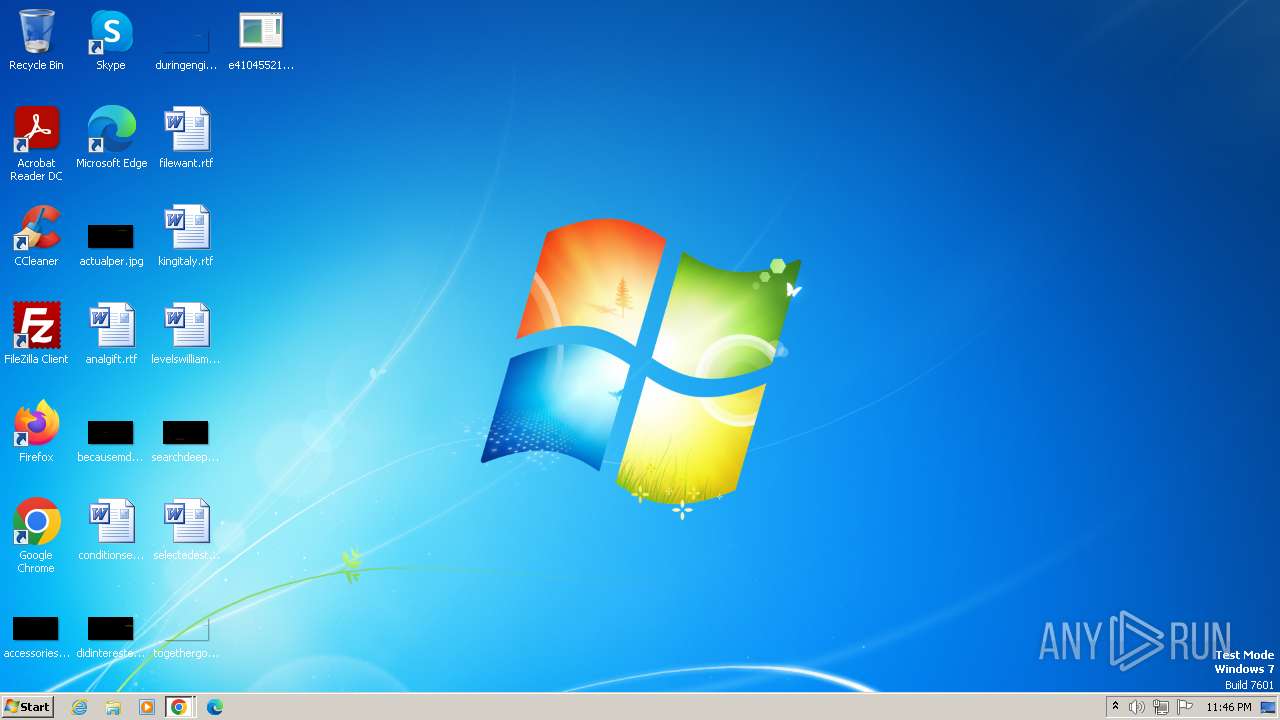
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2D3DEDB2538610C2AF373BDF3DBB43E0 |
| SHA1: | 91E42FF78F871AD624BAE2F2699B31F0FFE9A288 |
| SHA256: | E41045521E18B87BA80073F2FDEED4E848255D276C3F1FC3D670B24EE2321D11 |
| SSDEEP: | 49152:36WNkebmEFhOHGo4uh68QqyxBXSCXPGms1lw3F0YmKDSd0ujsE58Vq84wE8hnHkv:q4kEm2O0uh68QqoBXSCXPGms1lw3F0Y0 |
MALICIOUS
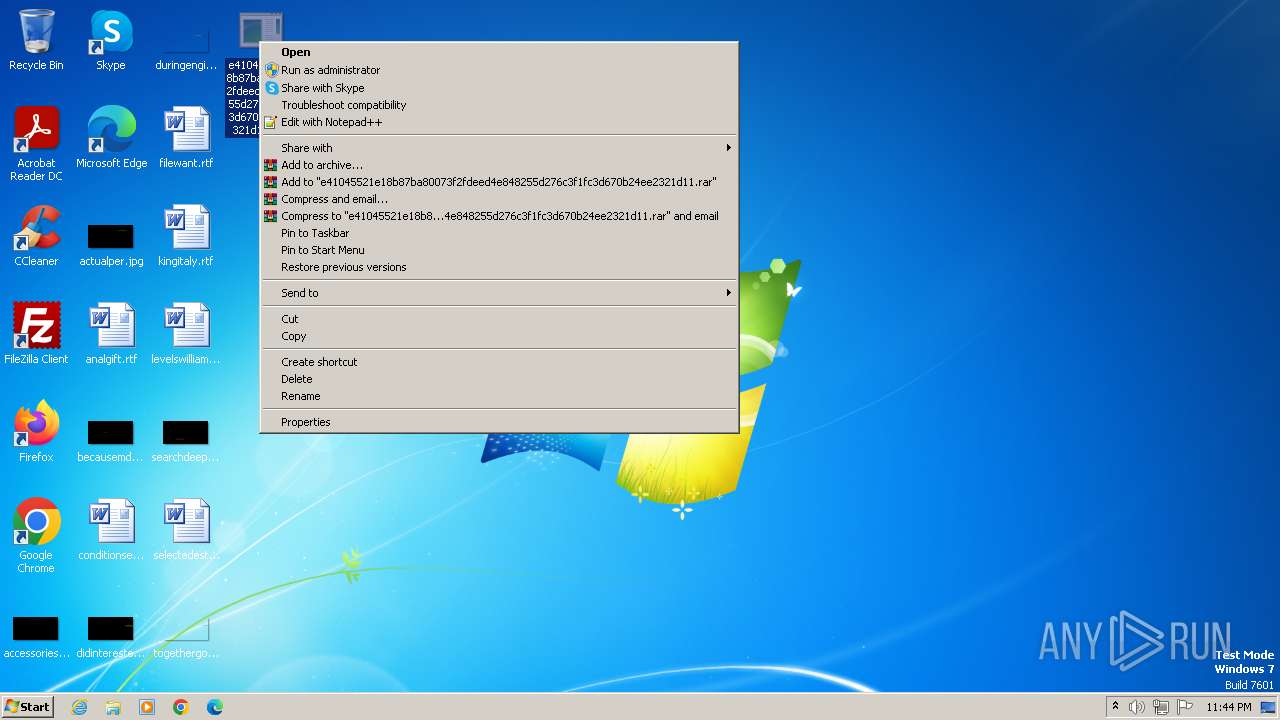
Drops the executable file immediately after the start
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3984)
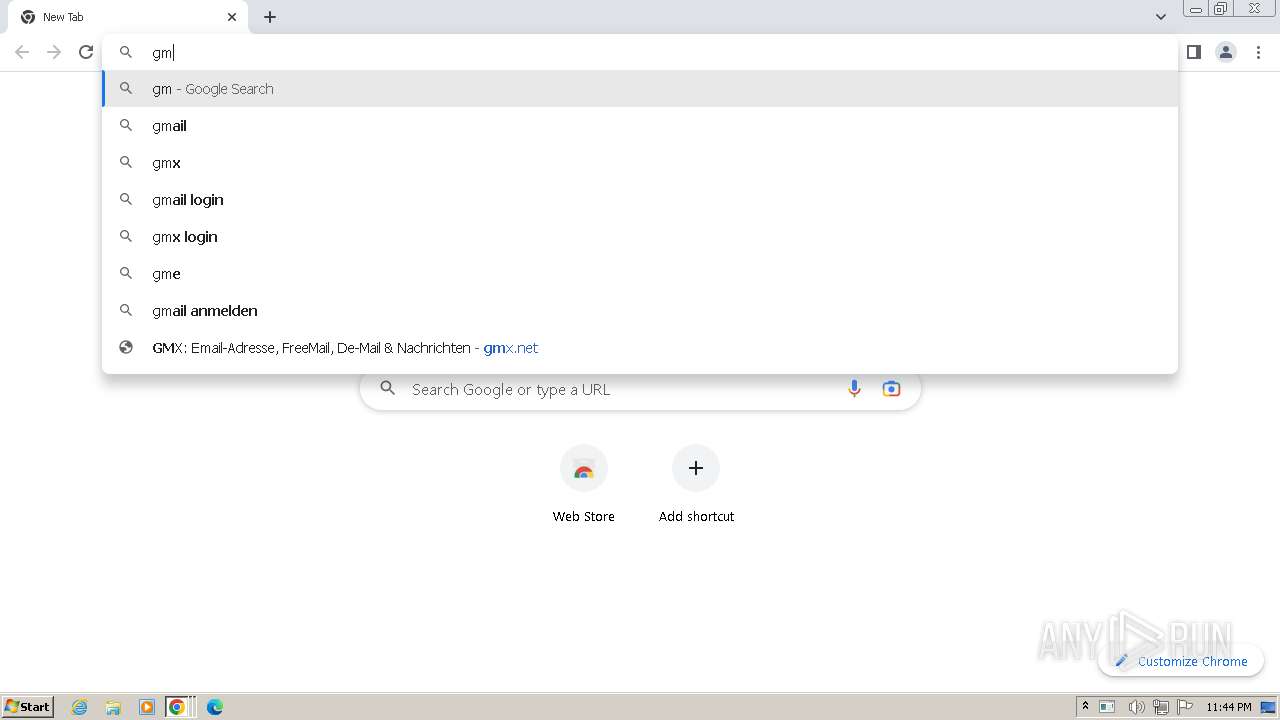
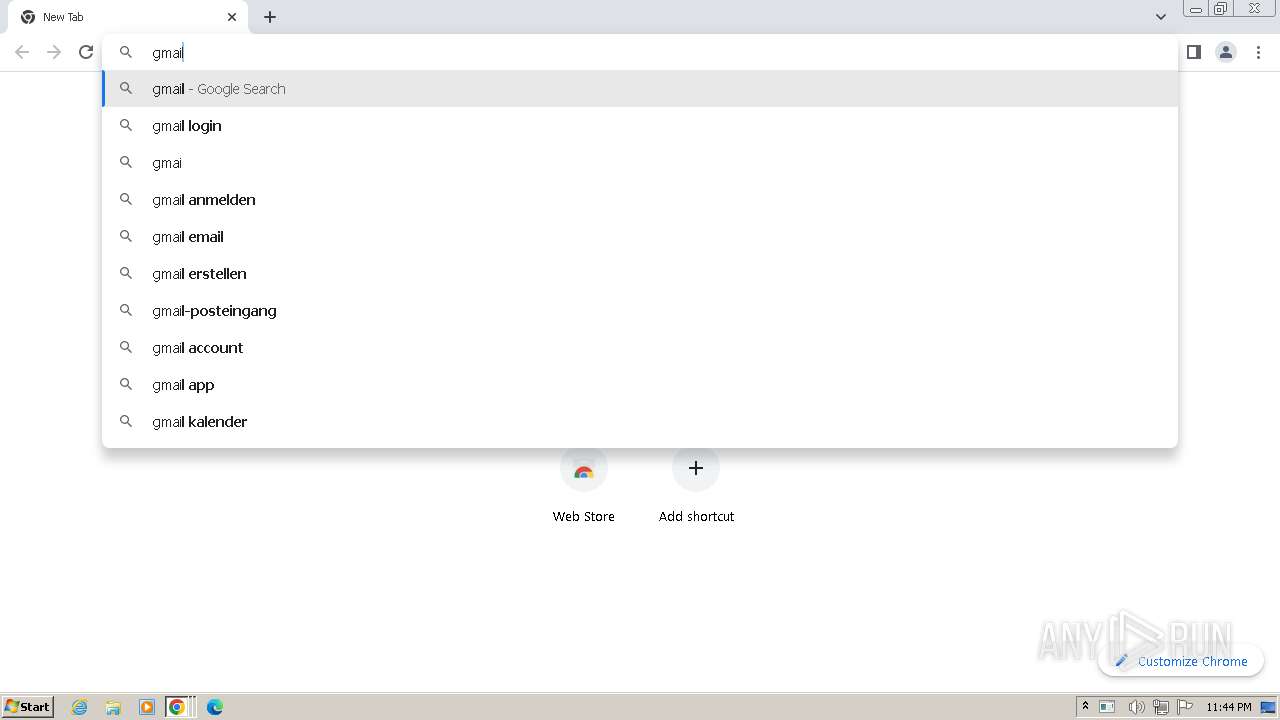
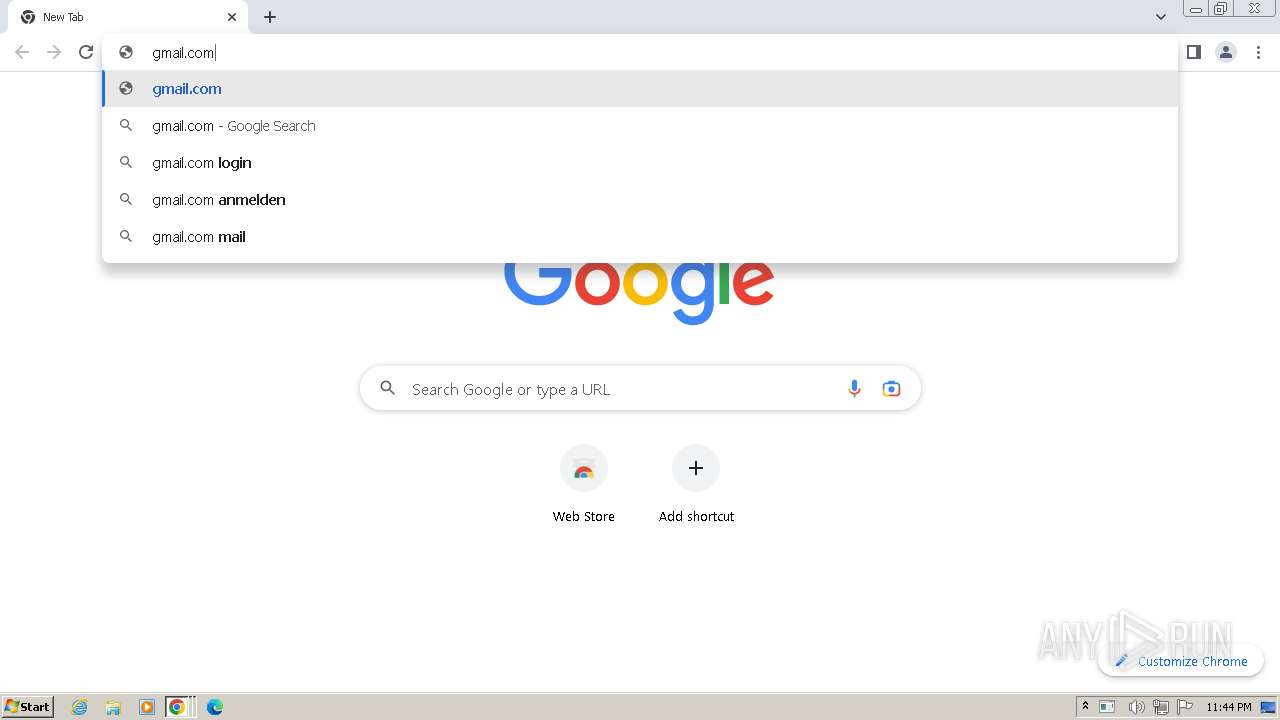
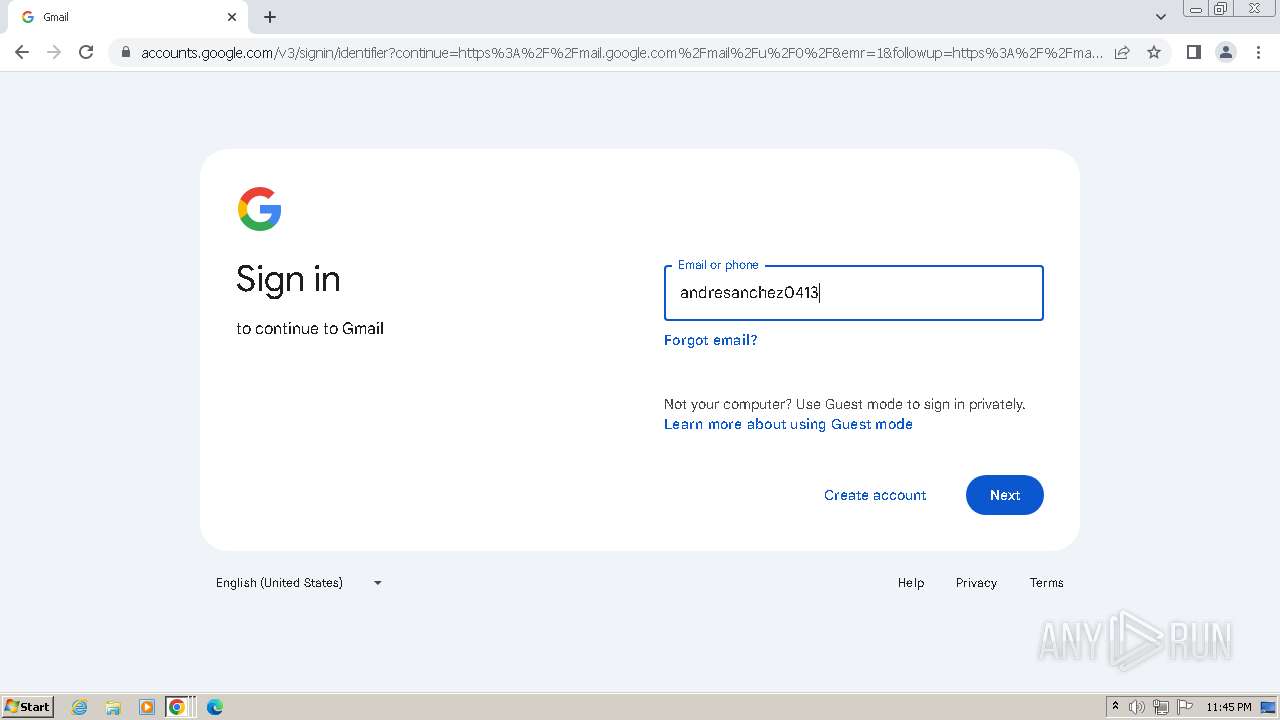
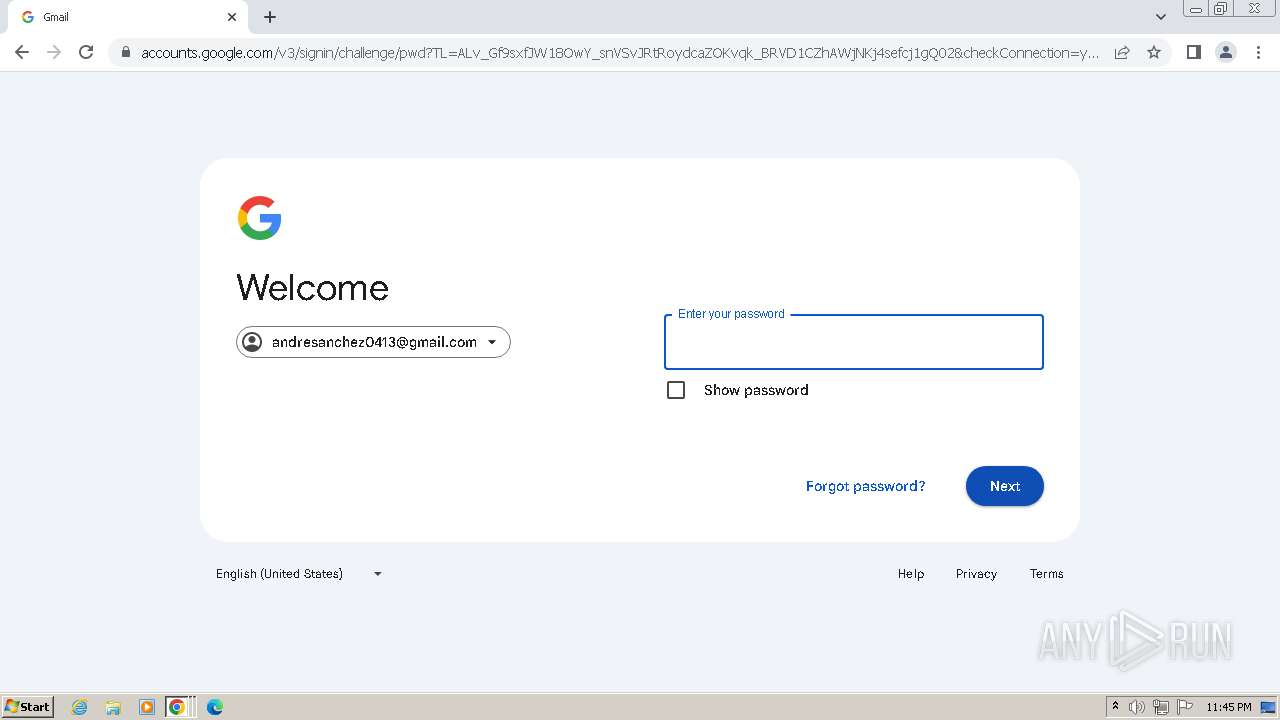
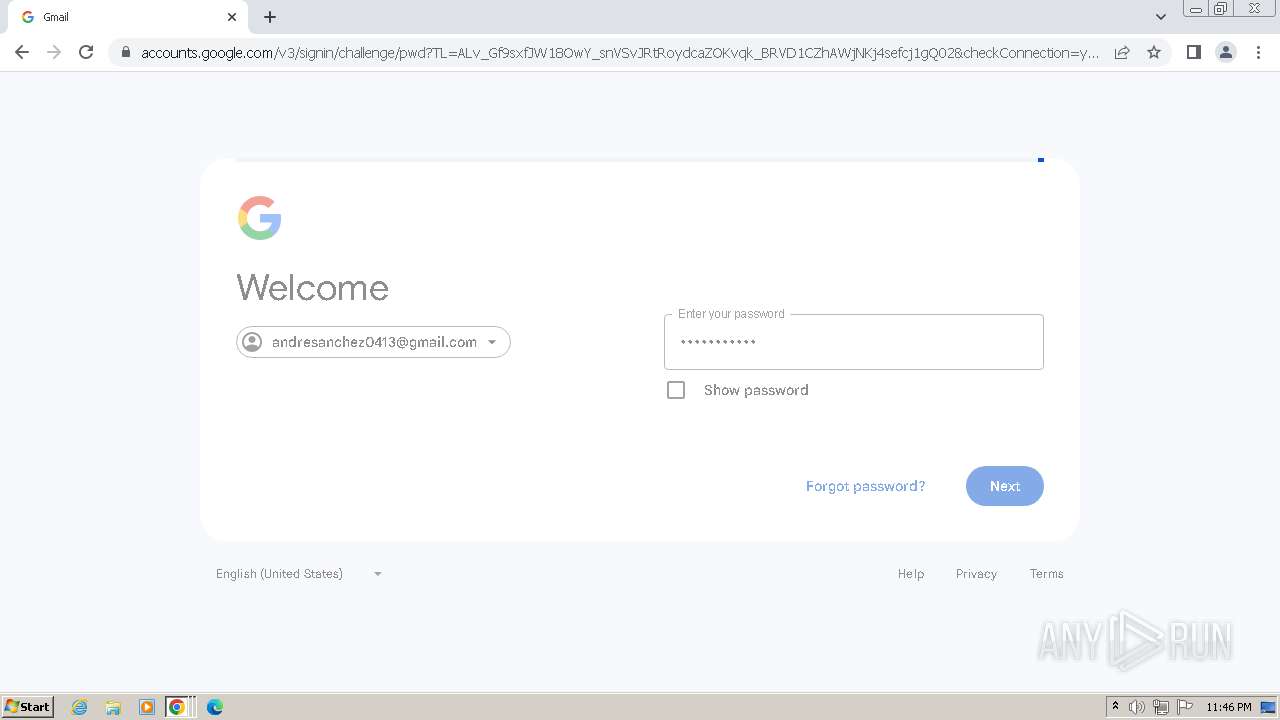
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1872)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1872)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 4052)
- RegSvcs.exe (PID: 2236)
AGENTTESLA has been detected (YARA)
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 4052)
Connects to the CnC server
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 2172)
AGENTTESLA has been detected (SURICATA)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 2172)
SUSPICIOUS
Connects to FTP
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Accesses Microsoft Outlook profiles
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1872)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Reads the Internet Settings
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Connects to unusual port
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 4052)
The process connected to a server suspected of theft
- RegSvcs.exe (PID: 4000)
INFO
Checks supported languages
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3984)
- RegSvcs.exe (PID: 4000)
- wmpnscfg.exe (PID: 112)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2044)
- RegSvcs.exe (PID: 1872)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2312)
- RegSvcs.exe (PID: 1764)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1660)
- RegSvcs.exe (PID: 1620)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1812)
- RegSvcs.exe (PID: 1824)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1804)
- RegSvcs.exe (PID: 2172)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3772)
- RegSvcs.exe (PID: 3684)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2656)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3020)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3480)
- RegSvcs.exe (PID: 2236)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3780)
- RegSvcs.exe (PID: 4052)
Reads mouse settings
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3984)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2044)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2312)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1660)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1812)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1804)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3772)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2656)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3020)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3480)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3780)
Reads Environment values
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1872)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1872)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Reads the computer name
- RegSvcs.exe (PID: 4000)
- wmpnscfg.exe (PID: 112)
- RegSvcs.exe (PID: 1872)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
Create files in a temporary directory
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3984)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2044)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2312)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1660)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1812)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1804)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3772)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2656)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3020)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3480)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3780)
Disables trace logs
- RegSvcs.exe (PID: 4000)
- RegSvcs.exe (PID: 1764)
- RegSvcs.exe (PID: 1620)
- RegSvcs.exe (PID: 1824)
- RegSvcs.exe (PID: 2172)
- RegSvcs.exe (PID: 3684)
- RegSvcs.exe (PID: 2456)
- RegSvcs.exe (PID: 2644)
- RegSvcs.exe (PID: 2236)
- RegSvcs.exe (PID: 4052)
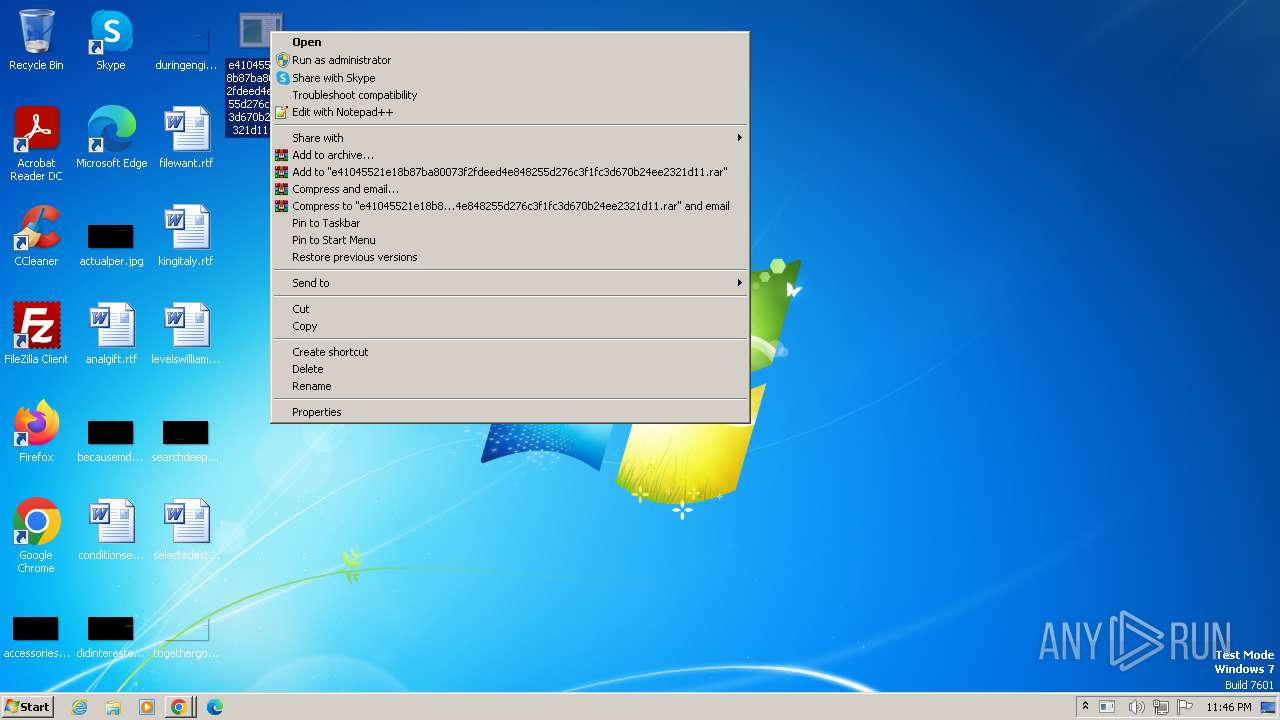
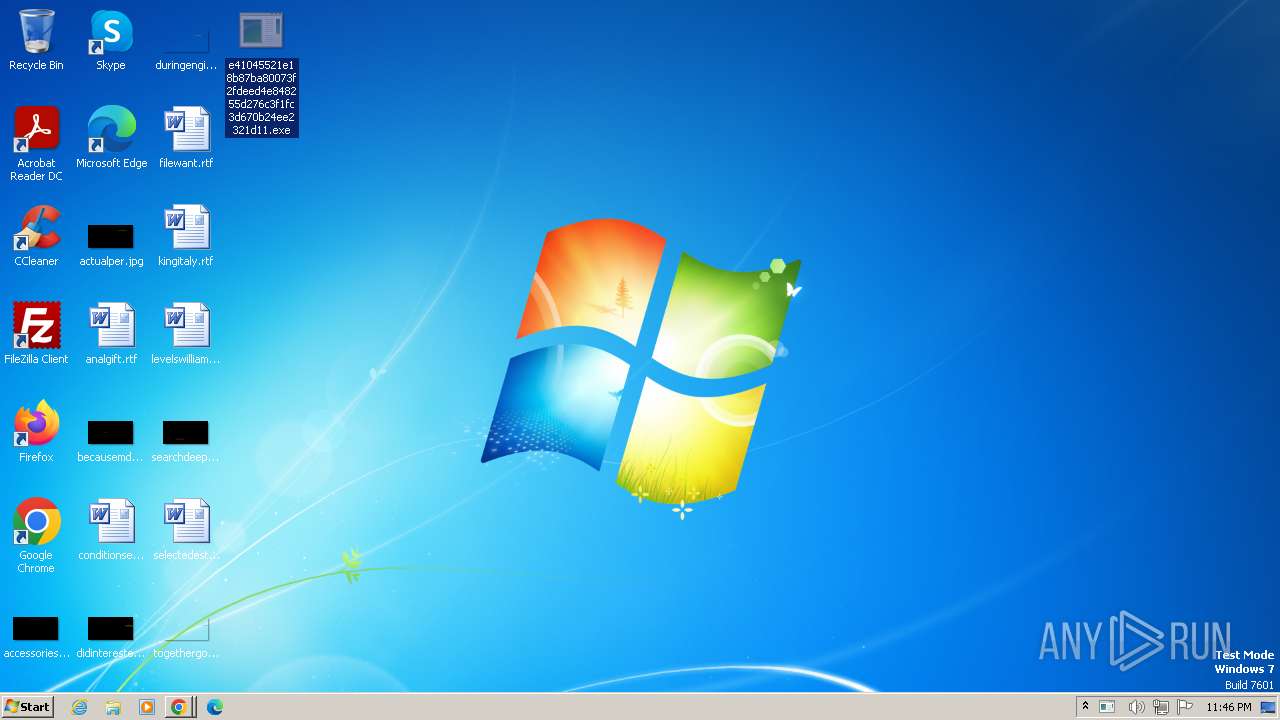
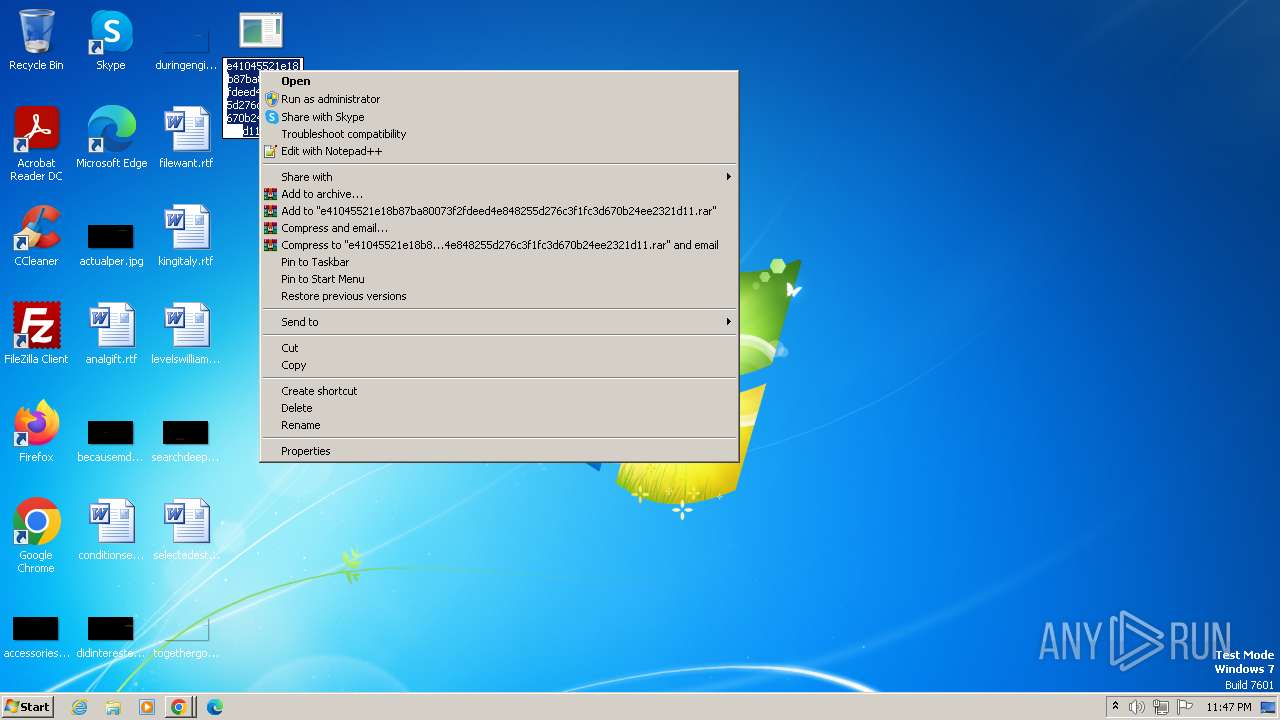
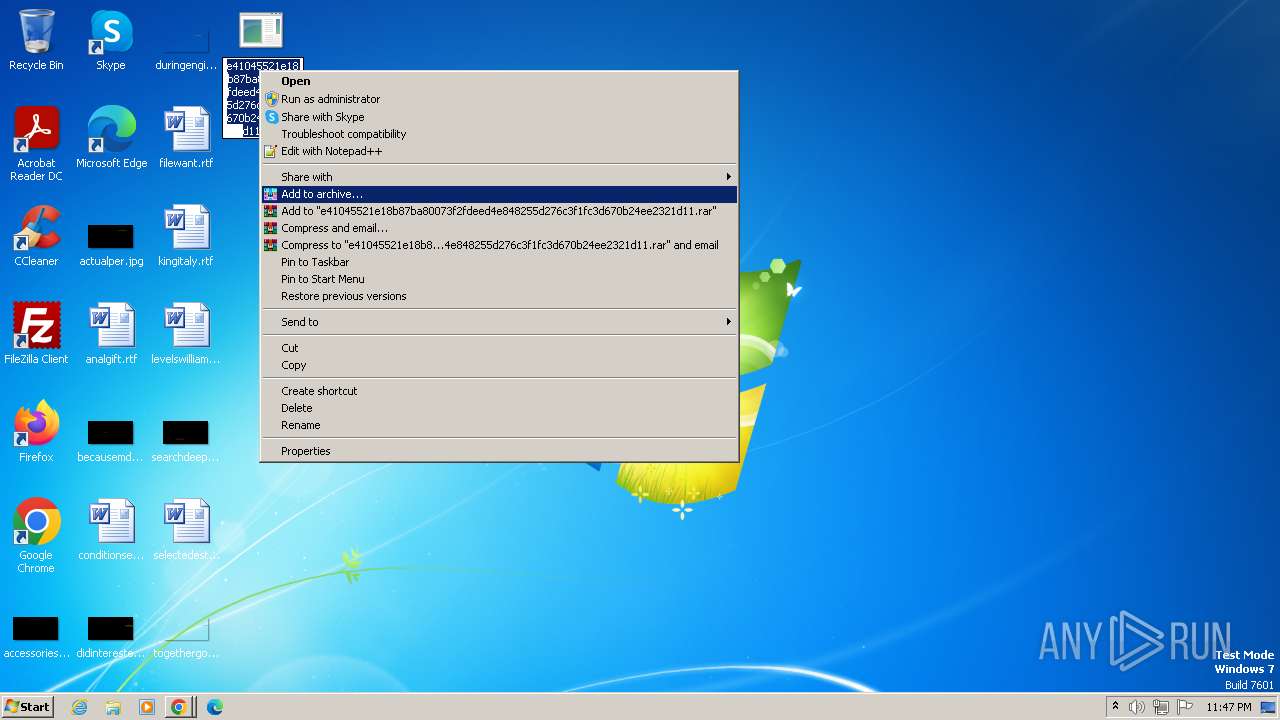
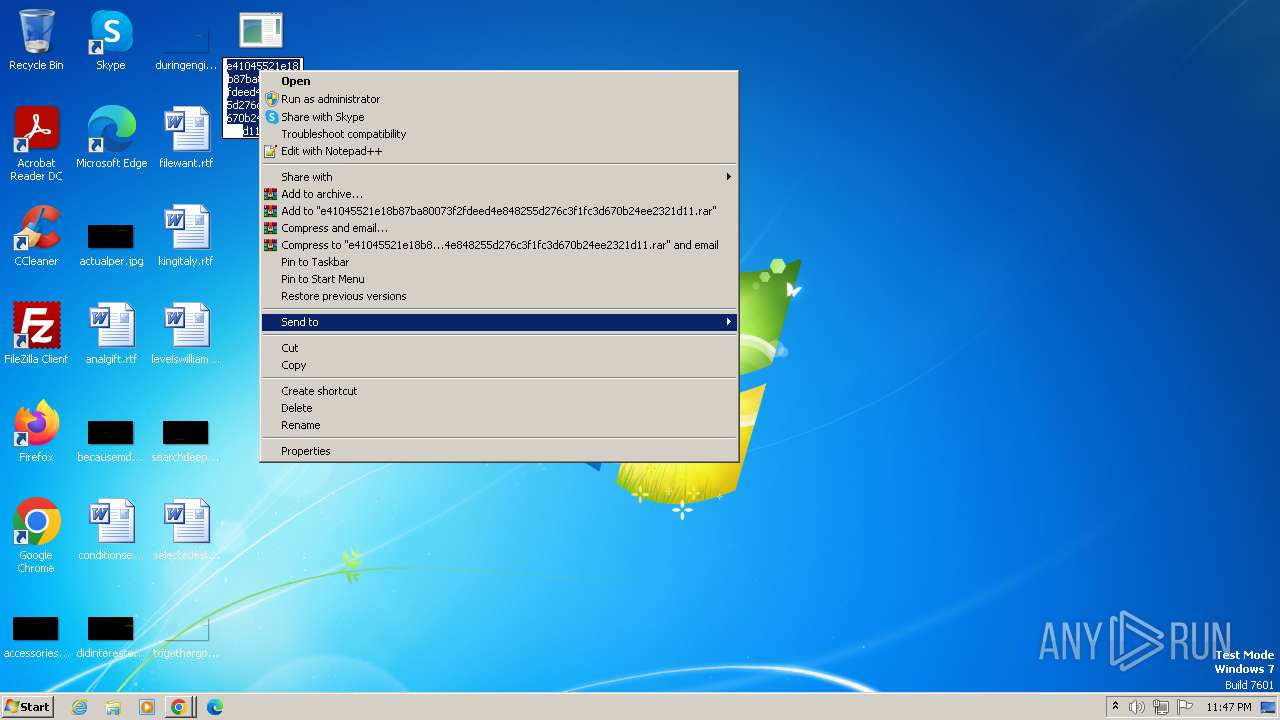
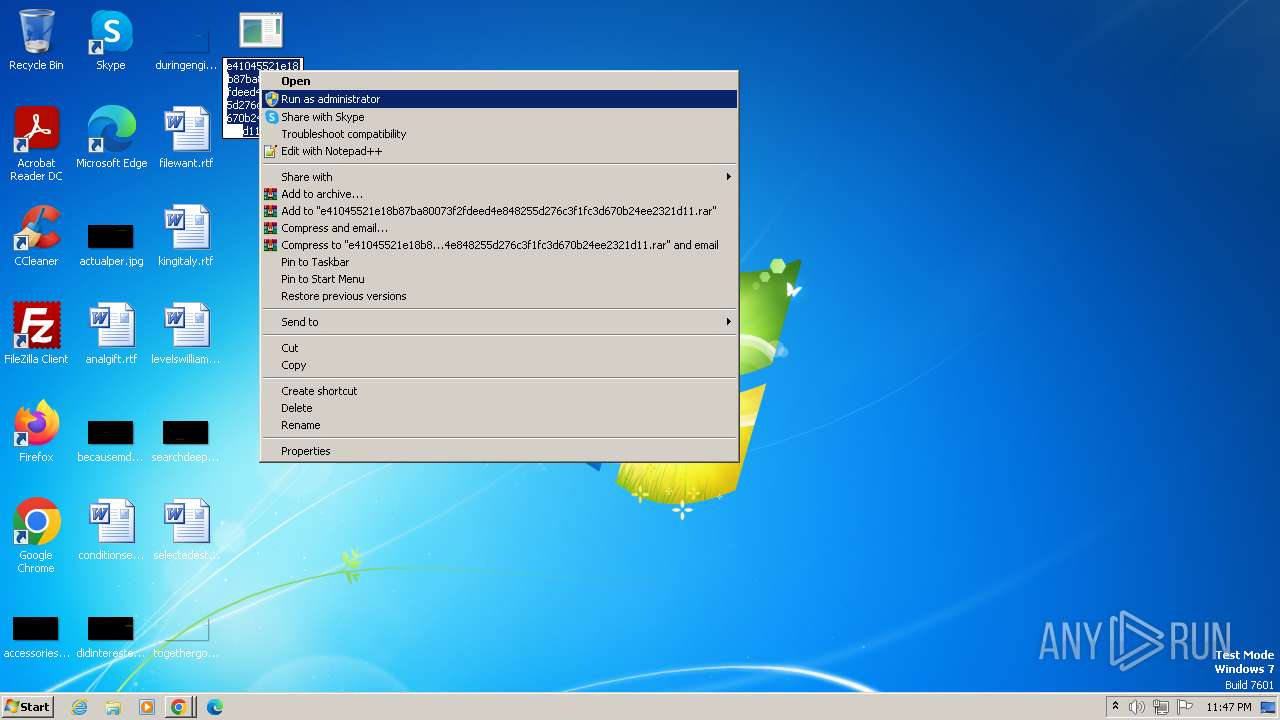
Manual execution by a user
- wmpnscfg.exe (PID: 112)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2044)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2312)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1660)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1812)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 1804)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 924)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3772)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 2656)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3020)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3480)
- e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe (PID: 3780)
Application launched itself
- chrome.exe (PID: 2512)
- chrome.exe (PID: 924)
- chrome.exe (PID: 2452)
Executable content was dropped or overwritten
- chrome.exe (PID: 2620)
- chrome.exe (PID: 4072)
Drops the executable file immediately after the start
- chrome.exe (PID: 2620)
- chrome.exe (PID: 4072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(4000) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(1764) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(1620) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(1824) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(2172) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(2456) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(2644) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(2236) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
(PID) Process(4052) RegSvcs.exe
Protocolftp
Hostftp://ftp.corpsa.net
Usernamevodooooo@corpsa.net
Password-E~O8rekW5UT
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:13 17:29:36+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 468992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
98
Monitored processes
58
Malicious processes
22
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=4084 --field-trial-handle=1104,i,5947118992204864583,18396916749048693583,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1548 --field-trial-handle=1104,i,5947118992204864583,18396916749048693583,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1620 | "C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.3761.0 built by: NET48REL1 Modules
AgentTesla(PID) Process(1620) RegSvcs.exe Protocolftp Hostftp://ftp.corpsa.net Usernamevodooooo@corpsa.net Password-E~O8rekW5UT | |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x68428b38,0x68428b48,0x68428b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe" | C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1764 | "C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.3761.0 built by: NET48REL1 Modules
AgentTesla(PID) Process(1764) RegSvcs.exe Protocolftp Hostftp://ftp.corpsa.net Usernamevodooooo@corpsa.net Password-E~O8rekW5UT | |||||||||||||||
| 1804 | "C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe" | C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe" | C:\Users\admin\Desktop\e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
27 669
Read events
27 555
Write events
113
Delete events
1
Modification events
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4000) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegSvcs_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
7
Suspicious files
810
Text files
55
Unknown types
211
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF114207.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1660 | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | C:\Users\admin\AppData\Local\Temp\autCE7D.tmp | binary | |
MD5:3E0CC456174CCDC79990253E8A8DDBA8 | SHA256:4C735C6A4E0C1FF6941309033AFEACCBB7741659DDB61EE811D54829574B2AD1 | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3984 | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | C:\Users\admin\AppData\Local\Temp\drawlingly | binary | |
MD5:65C58D4B7D28BBB685C37F13A11108F9 | SHA256:6EE59EE300378214DD810DD724F6C93F66C2FED55F3669F38C299AC708042356 | |||
| 2452 | chrome.exe | — | ||
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\cf644314-84af-424b-ba25-95852c7d511a.tmp | — | |
MD5:— | SHA256:— | |||
| 2044 | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | C:\Users\admin\AppData\Local\Temp\aut735D.tmp | binary | |
MD5:3E0CC456174CCDC79990253E8A8DDBA8 | SHA256:4C735C6A4E0C1FF6941309033AFEACCBB7741659DDB61EE811D54829574B2AD1 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Local State | — | |
MD5:— | SHA256:— | |||
| 3984 | e41045521e18b87ba80073f2fdeed4e848255d276c3f1fc3d670b24ee2321d11.exe | C:\Users\admin\AppData\Local\Temp\aut2F11.tmp | binary | |
MD5:3E0CC456174CCDC79990253E8A8DDBA8 | SHA256:4C735C6A4E0C1FF6941309033AFEACCBB7741659DDB61EE811D54829574B2AD1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
71
DNS requests
76
Threats
67
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4000 | RegSvcs.exe | 64.34.65.25:21 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
4000 | RegSvcs.exe | 64.34.65.25:54057 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
1764 | RegSvcs.exe | 64.34.65.25:21 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
1764 | RegSvcs.exe | 64.34.65.25:62674 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
1620 | RegSvcs.exe | 64.34.65.25:21 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
1620 | RegSvcs.exe | 64.34.65.25:50053 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
1824 | RegSvcs.exe | 64.34.65.25:21 | ftp.corpsa.net | COGECO-PEER1 | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ftp.corpsa.net |
| unknown |
clientservices.googleapis.com |
| whitelisted |
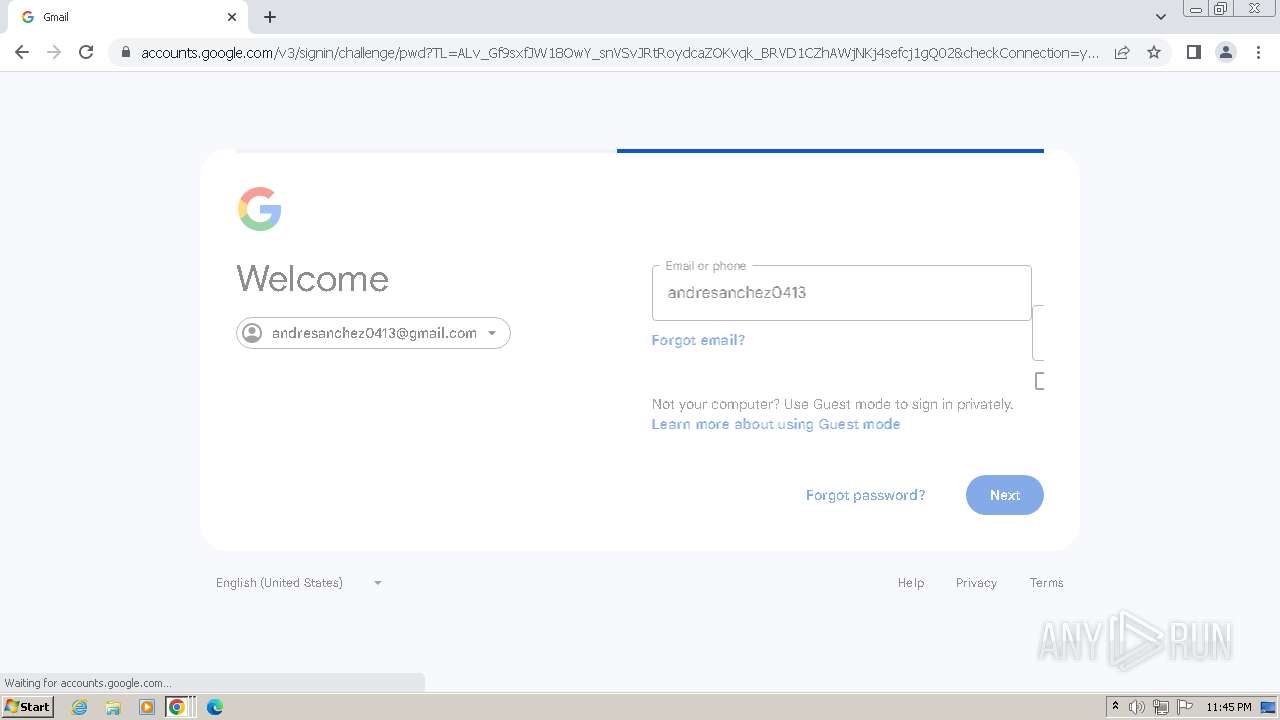
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| unknown |
encrypted-tbn0.gstatic.com |
| whitelisted |
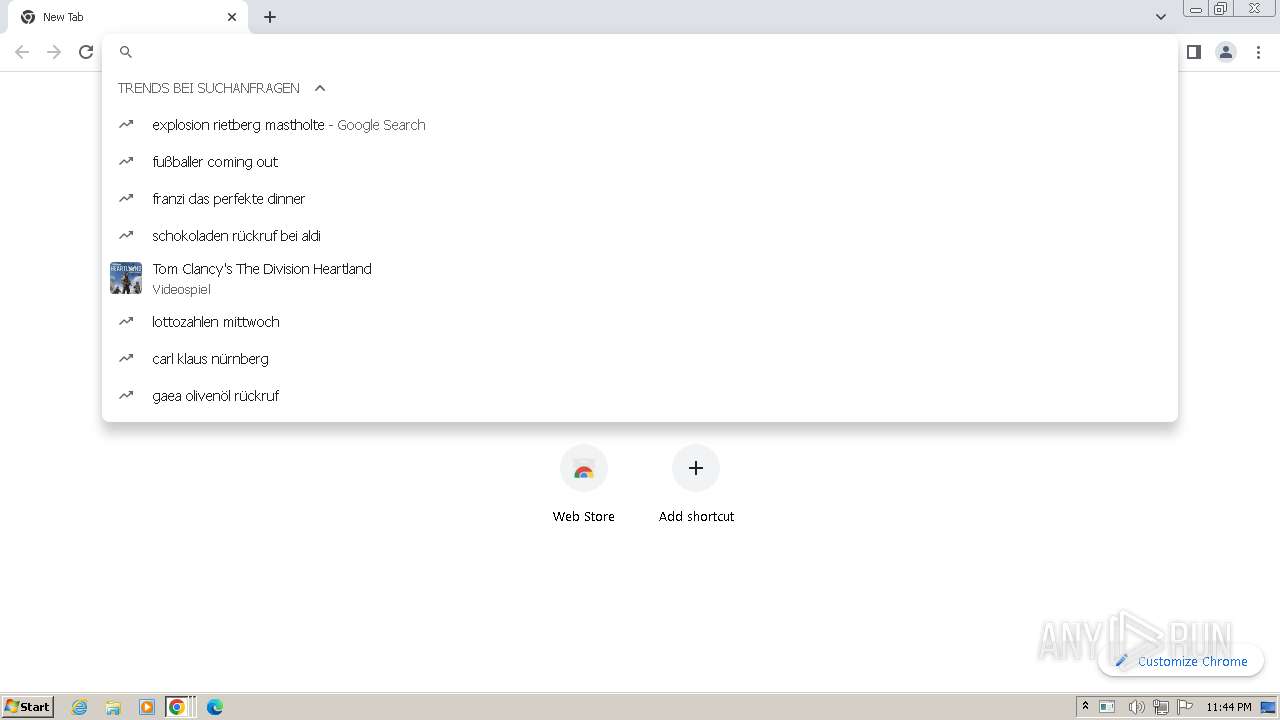
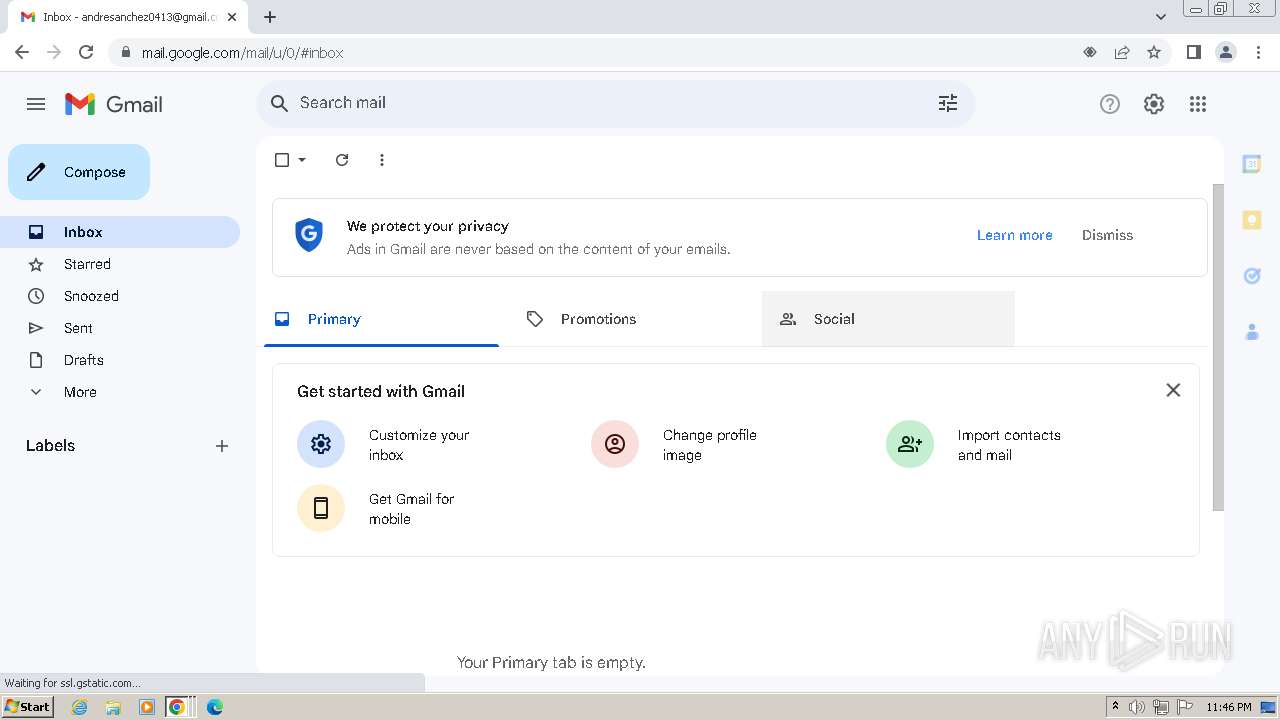
gmail.com |
| shared |
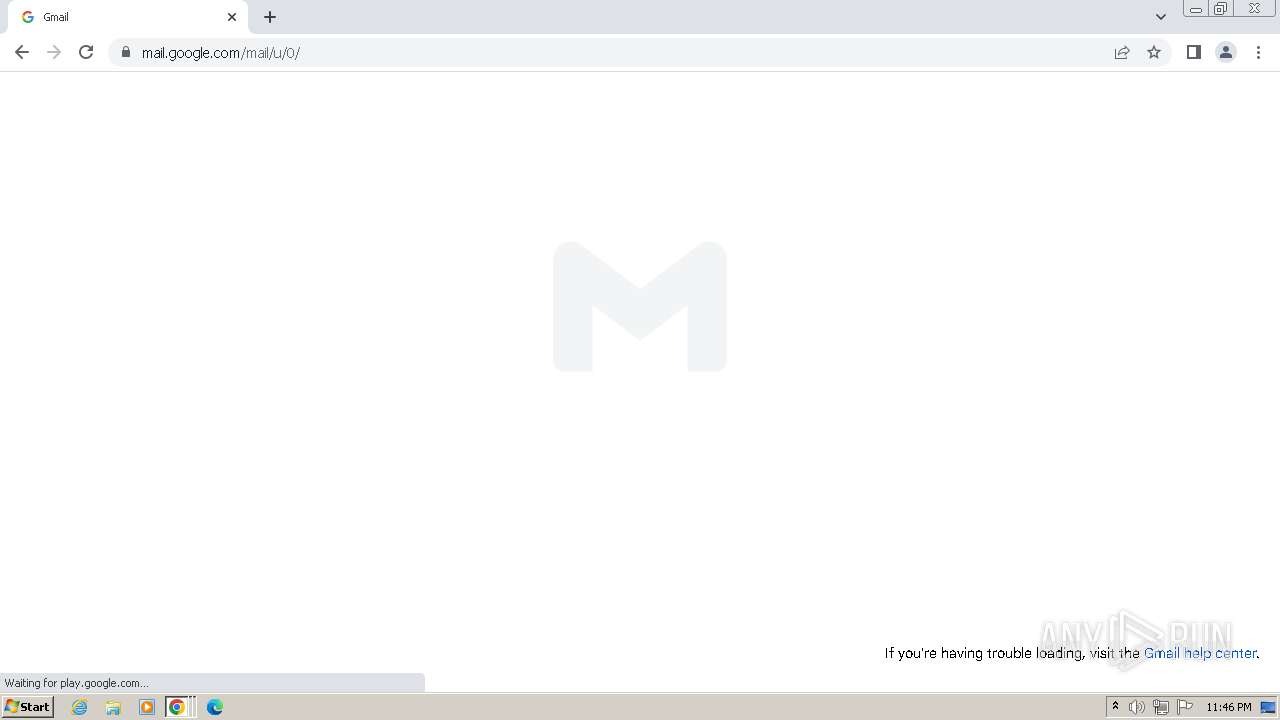
mail.google.com |
| shared |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4000 | RegSvcs.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
4000 | RegSvcs.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
4000 | RegSvcs.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
4000 | RegSvcs.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Clear Text Login Exfiltration Atempt |
4000 | RegSvcs.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Clear Text Password Exfiltration Atempt |
4000 | RegSvcs.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
— | — | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
— | — | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
— | — | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
— | — | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
18 ETPRO signatures available at the full report