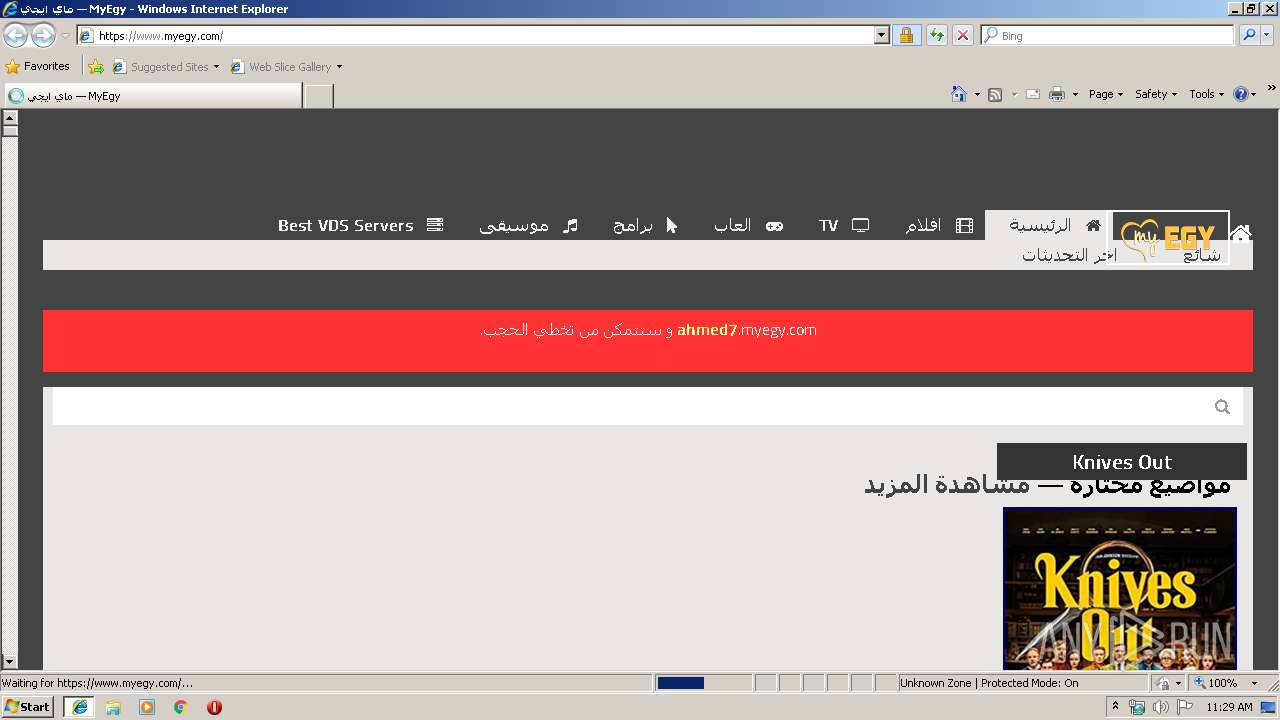
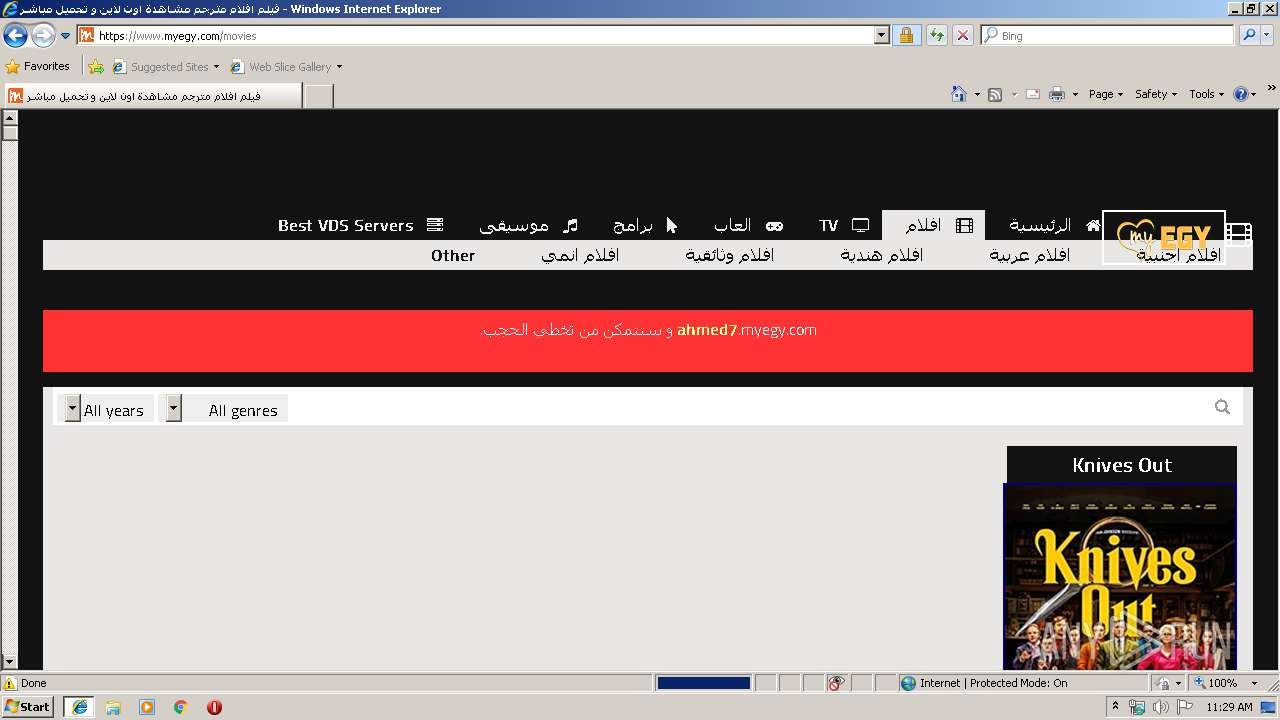
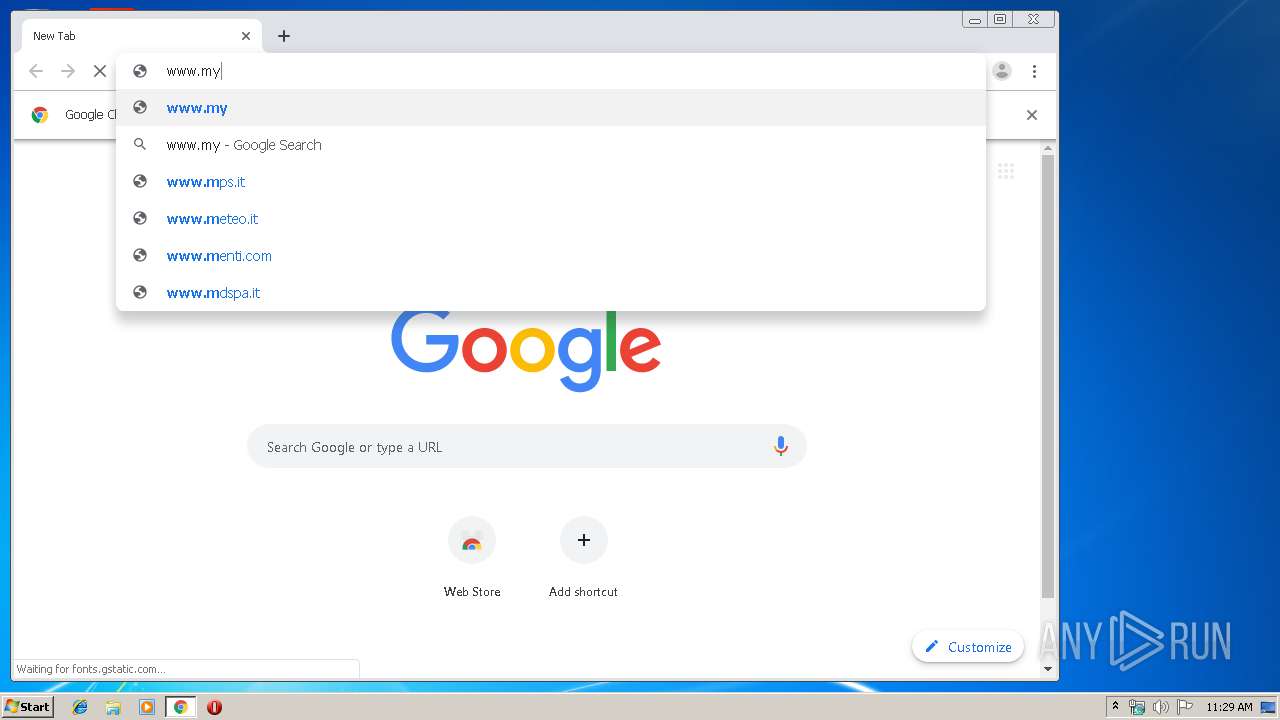
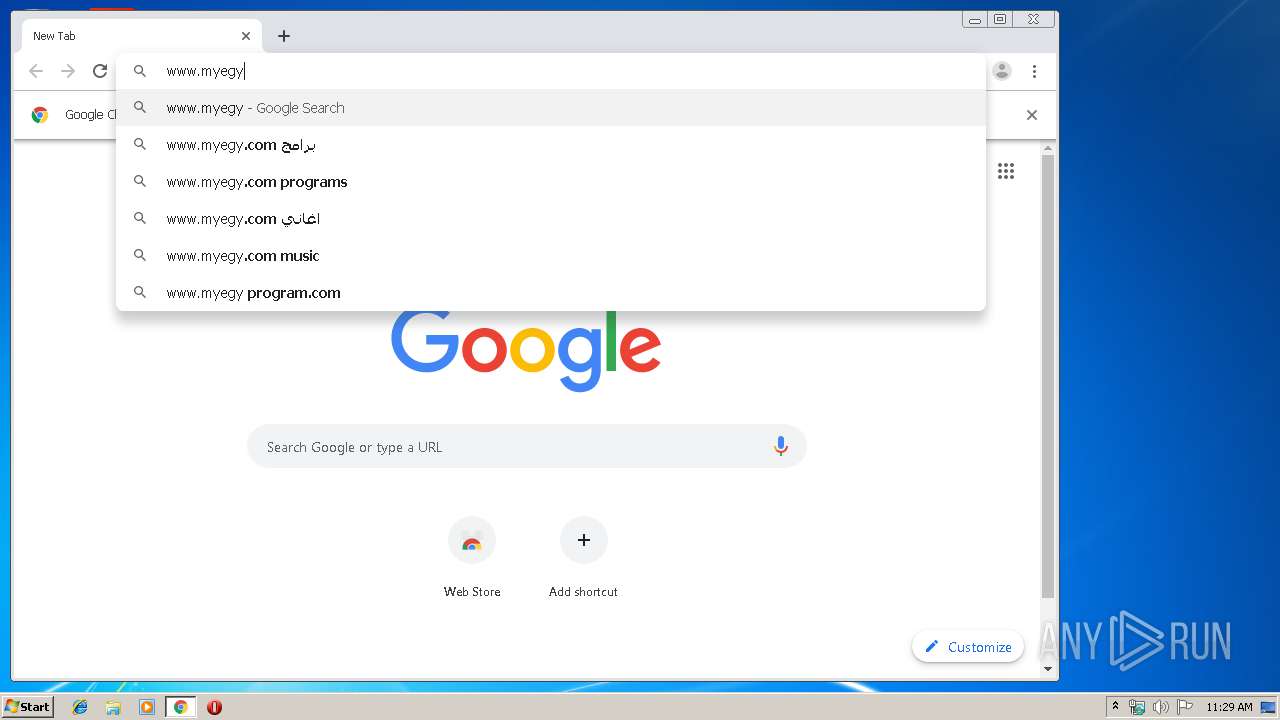
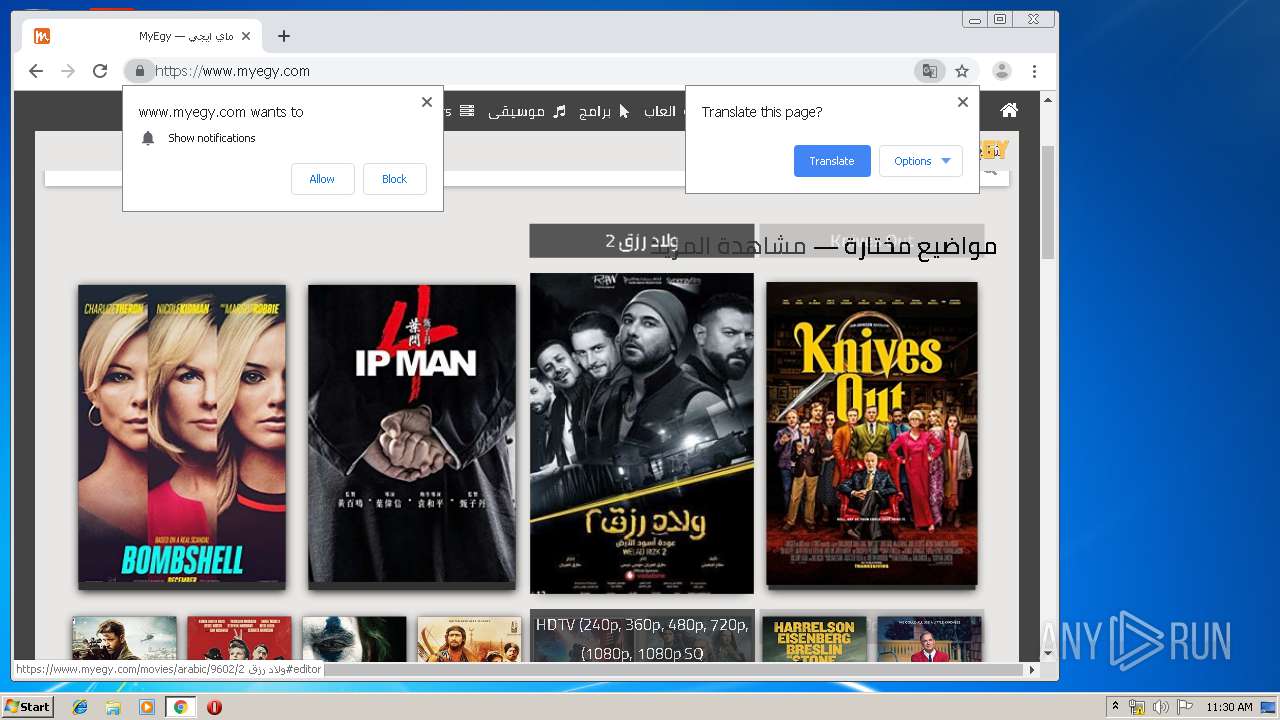
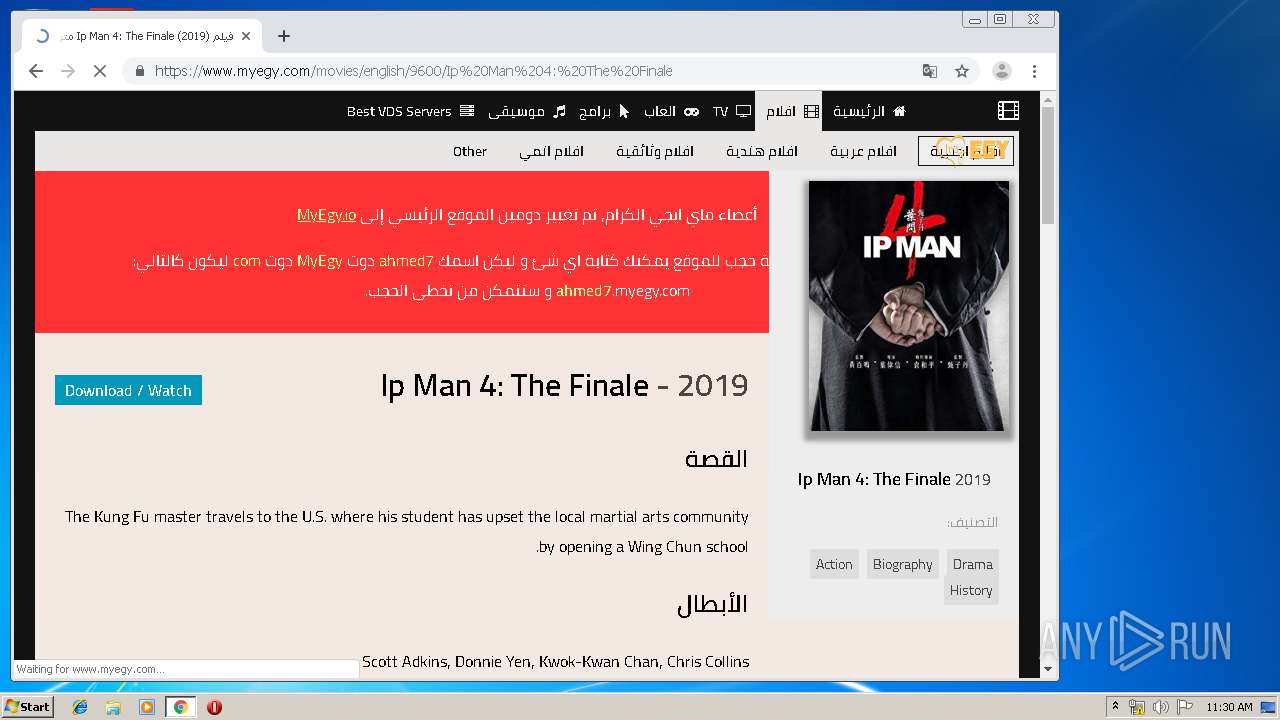
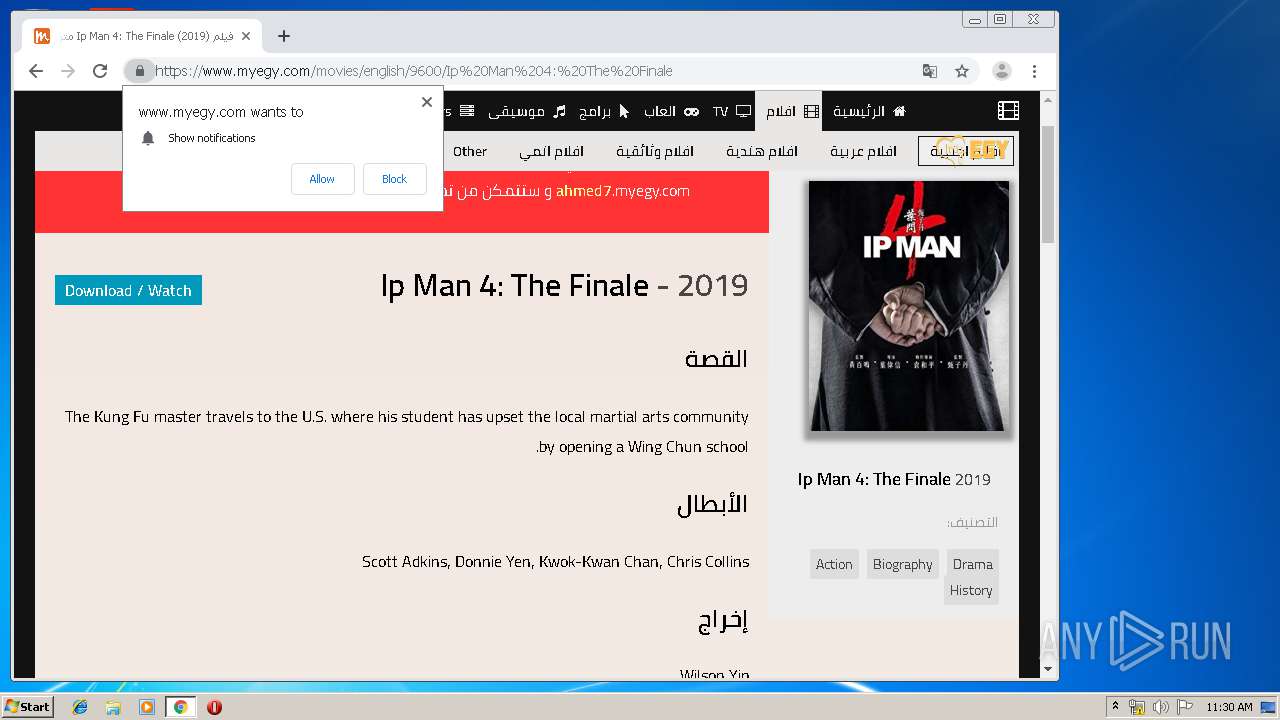
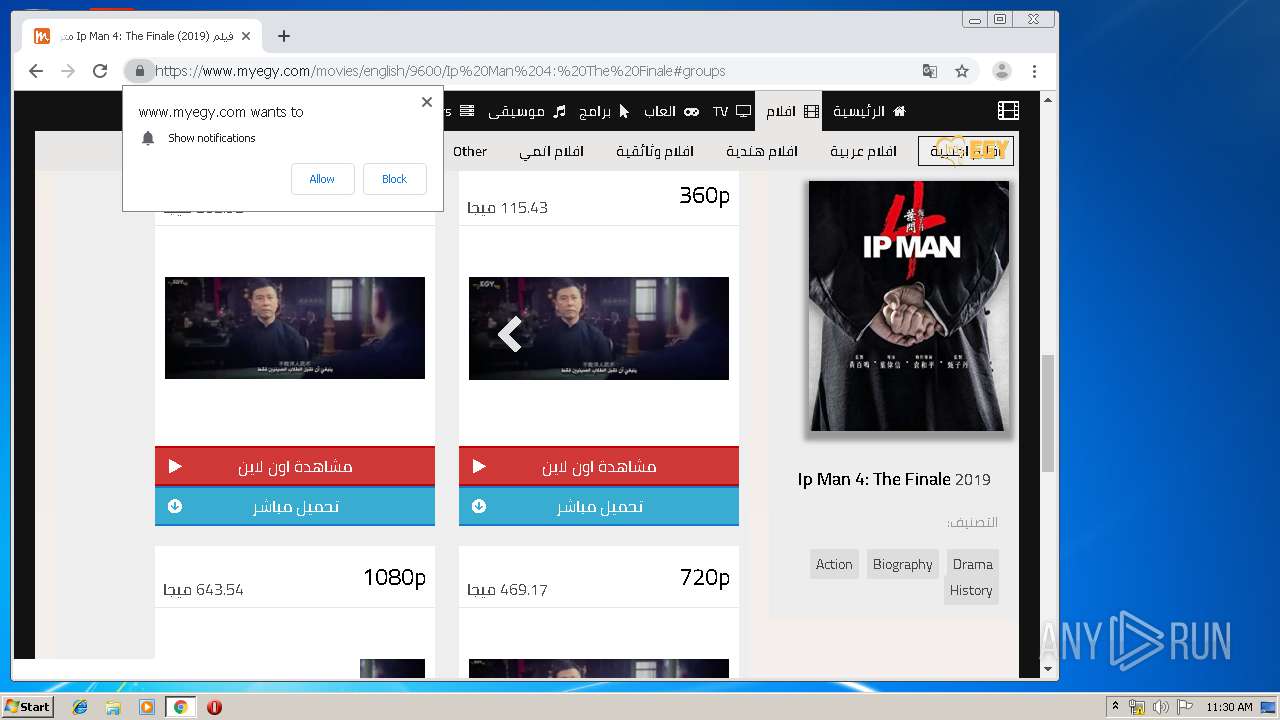
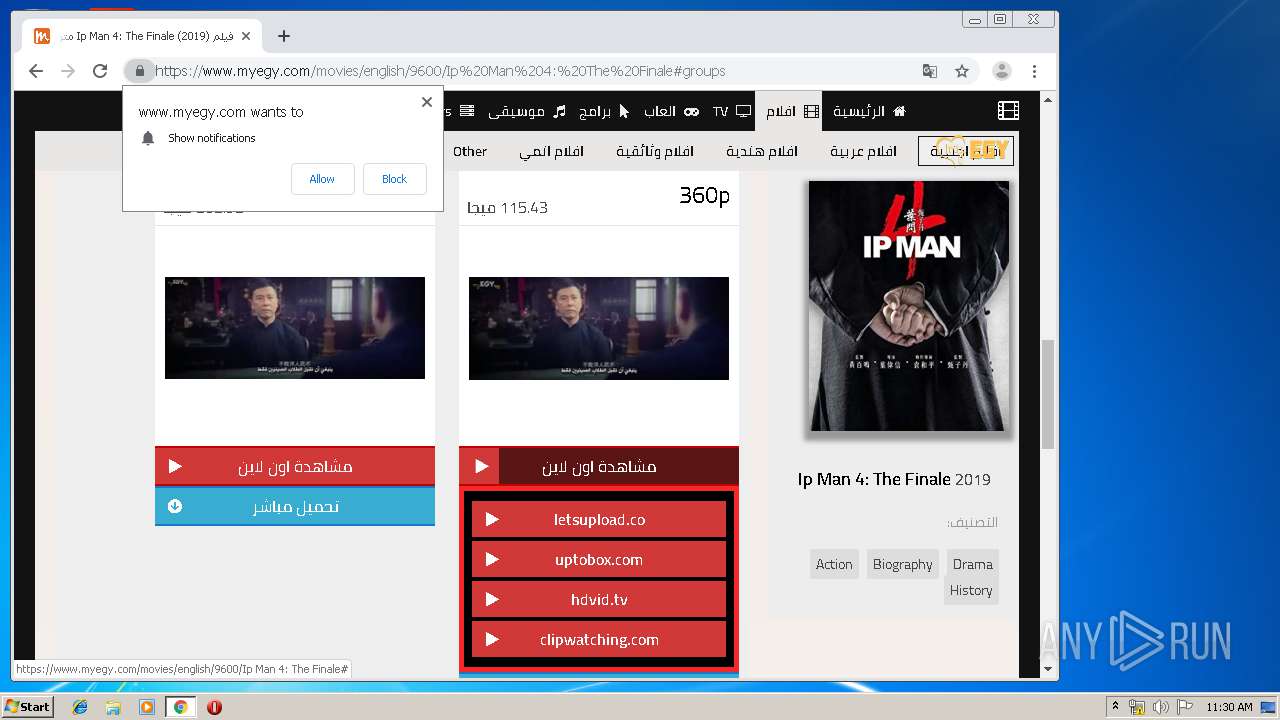
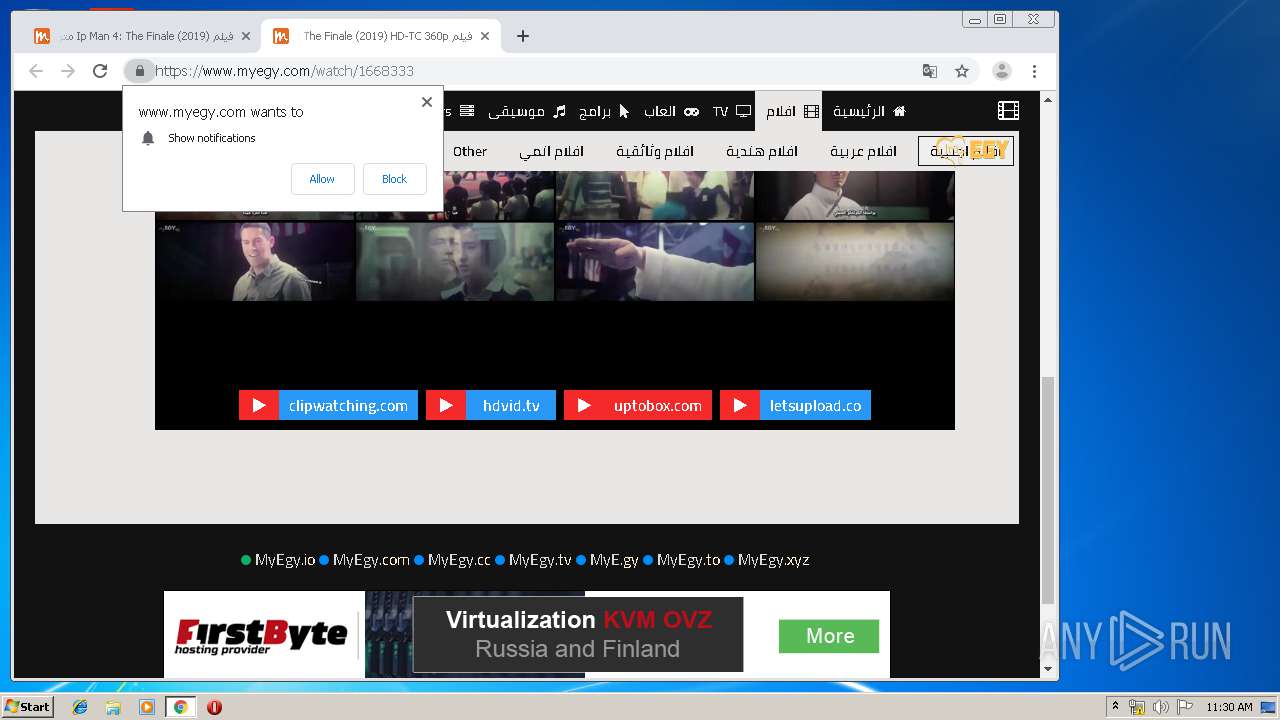
| URL: | https://www.myegy.com |
| Full analysis: | https://app.any.run/tasks/18a72ccc-471c-4b56-a71c-2d429545c61d |
| Verdict: | Malicious activity |
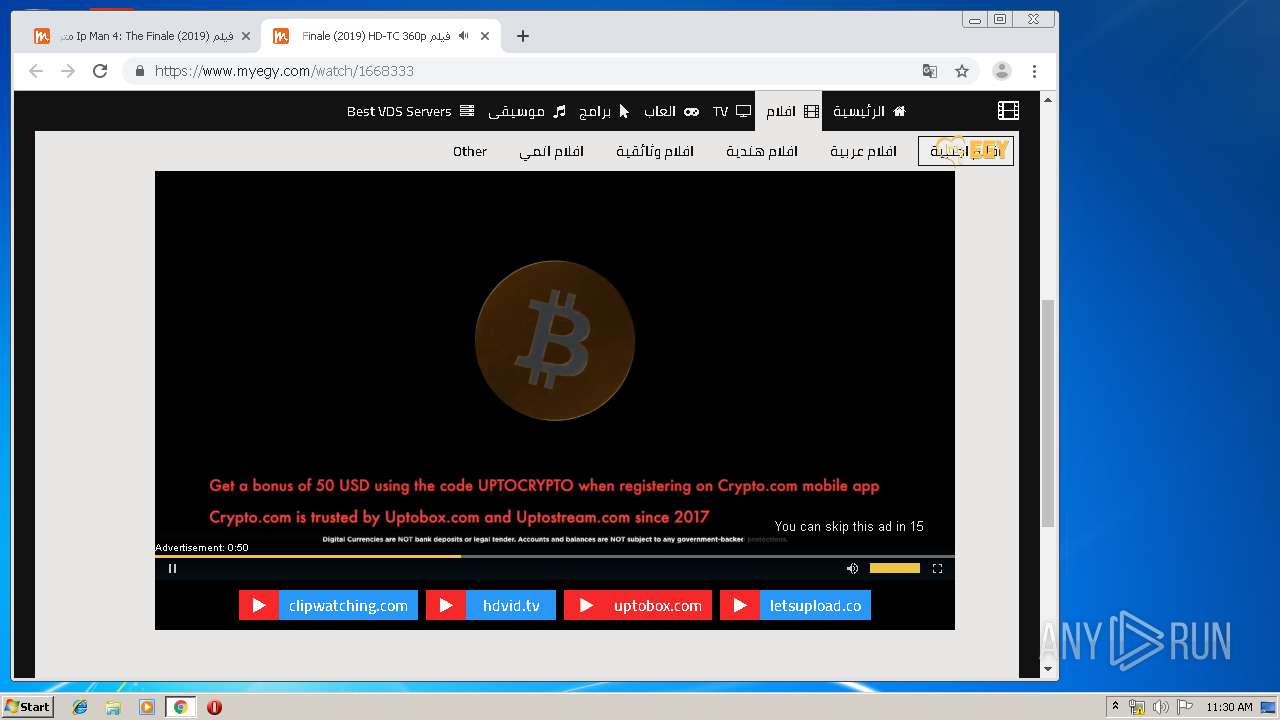
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
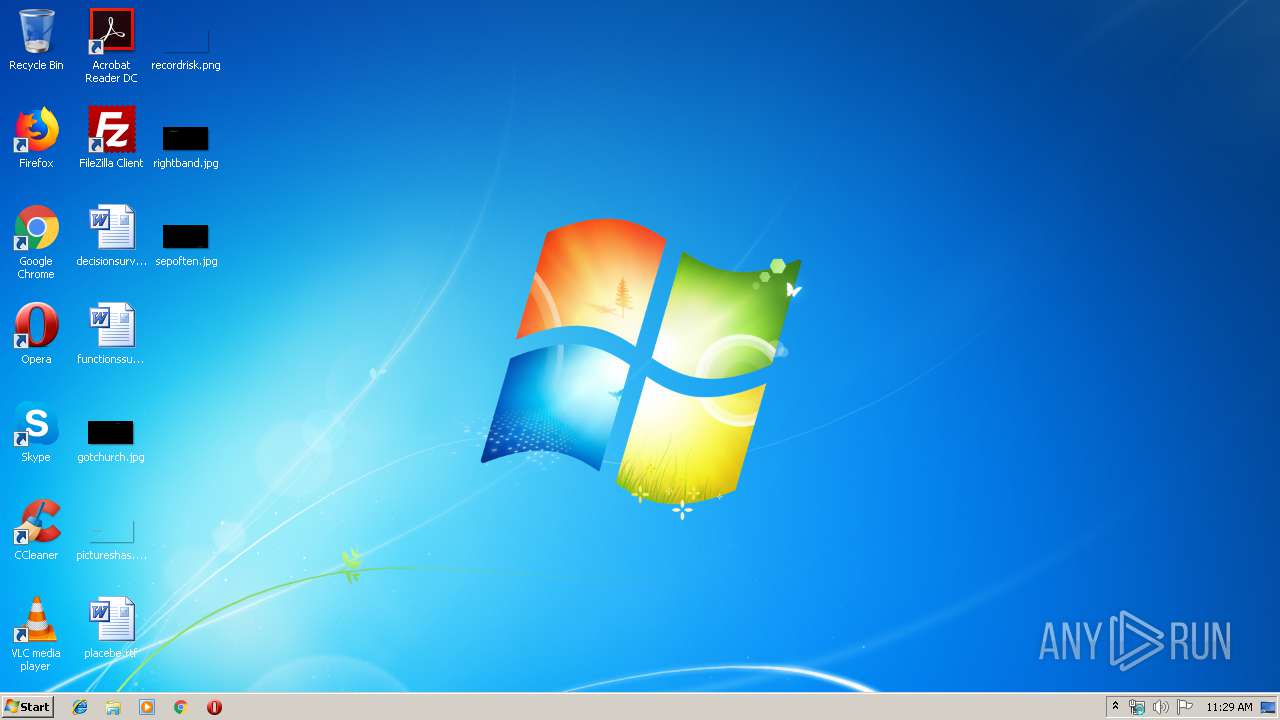
| Analysis date: | December 26, 2019, 11:28:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 56317D50E95FB5F15CA4607BADE5E274 |
| SHA1: | C21A7BBCFC13F90CB4C7C2E7FE4DF76F3A05ACEE |
| SHA256: | E3EA584AD2DBA886ED5FFEACF7764D88DF0AFA10FC0554A0FE8549C8876AD418 |
| SSDEEP: | 3:N8DSLmLGT:2OLmLGT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1036)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2444)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2580)
Reads Internet Cache Settings
- iexplore.exe (PID: 3360)
Reads internet explorer settings
- iexplore.exe (PID: 3360)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1036)
- iexplore.exe (PID: 3360)
- iexplore.exe (PID: 2580)
Application launched itself
- iexplore.exe (PID: 2580)
- chrome.exe (PID: 2444)
Changes settings of System certificates
- iexplore.exe (PID: 2580)
Reads the hosts file
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2644)
Reads settings of System Certificates
- iexplore.exe (PID: 2580)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2580)
Manual execution by user
- chrome.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
37
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=115839736205525646 --mojo-platform-channel-handle=3660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2033102044096474095 --mojo-platform-channel-handle=4700 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6674651175140967828 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4171567388551324204 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8809185728743116092 --mojo-platform-channel-handle=3712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13516590813655399209 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2273880880766541917 --mojo-platform-channel-handle=3644 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15213207219073085630 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,9127899591205206410,1001684846811438716,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5266157079380431885 --mojo-platform-channel-handle=3268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 096
Read events
928
Write events
161
Delete events
7
Modification events
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F06C0871-27D2-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C0004001A000B001D000D005E00 | |||
Executable files
0
Suspicious files
82
Text files
473
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.myegy[1].txt | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UOPUHSTP\myegy_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:F0FE59A50842E40AAF0CC4E328D2BCB5 | SHA256:5AAFF5B782F895007409E5528C943DDBA8A7416FE091A79B095066E93090C93A | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:EC0A1BA9AB866CA2D3C06CEC6CEE0242 | SHA256:C116C0CA3D4D86AE7A93F5ACE18C40ACEC57CEA9134F510C72ED42BA1454087F | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\R2IF01GY\css[1].txt | text | |
MD5:12E66265C588C28F0E8D93D14E933277 | SHA256:B37ACEB05BEC2F5A08272FDF8116C566EF323AD0A2C848152FD548E424036AED | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\200NXADF\SLXGc1nY6HkvalIhTp8[1].eot | eot | |
MD5:A46DBB9C1FB3BA444F6E2D1ECD76507B | SHA256:8E16BF323CAD965CF08E0D95B6741FA685DA758E0C0F3258BA1E443FA3932366 | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\200NXADF\trumbowyg.min.!20160306231200[1].css | text | |
MD5:3D2B15EC4AE31C0AF48DCFBAC2C5AC2A | SHA256:C33618476CAB7103529EF7BA4D5012F35D97E8E27C0F57A0F654284F545B2F39 | |||
| 3360 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:246C36C0277A6EF3BE1E6C41E290F6A6 | SHA256:1FC2928B63422B172EDAA709A4C9F59E80A3EBDF80EBAC44F5DC0EBAE4D19577 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
83
DNS requests
47
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2644 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
2644 | chrome.exe | GET | 200 | 95.101.72.131:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.4 Kb | whitelisted |
2644 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
2644 | chrome.exe | GET | 200 | 13.35.254.176:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2580 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2644 | chrome.exe | GET | 200 | 74.125.13.7:80 | http://r2---sn-hgn7yn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.183.105.219&mm=28&mn=sn-hgn7yn76&ms=nvh&mt=1577359756&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2644 | chrome.exe | GET | 301 | 104.31.15.161:80 | http://www.myegy.com/ | US | — | — | shared |
2644 | chrome.exe | GET | 200 | 173.194.164.42:80 | http://r5---sn-hgn7rnee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.105.219&mm=28&mn=sn-hgn7rnee&ms=nvh&mt=1577359756&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3360 | iexplore.exe | 104.31.14.161:443 | www.myegy.com | Cloudflare Inc | US | unknown |
2580 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3360 | iexplore.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 64.233.184.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3360 | iexplore.exe | 104.18.50.29:443 | myegy.io | Cloudflare Inc | US | unknown |
2644 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2580 | iexplore.exe | 104.31.14.161:443 | www.myegy.com | Cloudflare Inc | US | unknown |
2644 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 74.125.13.7:80 | r2---sn-hgn7yn76.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.myegy.com |
| unknown |
www.bing.com |
| whitelisted |
sdk.truepush.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
myegy.io |
| unknown |
stats.g.doubleclick.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
2 ETPRO signatures available at the full report