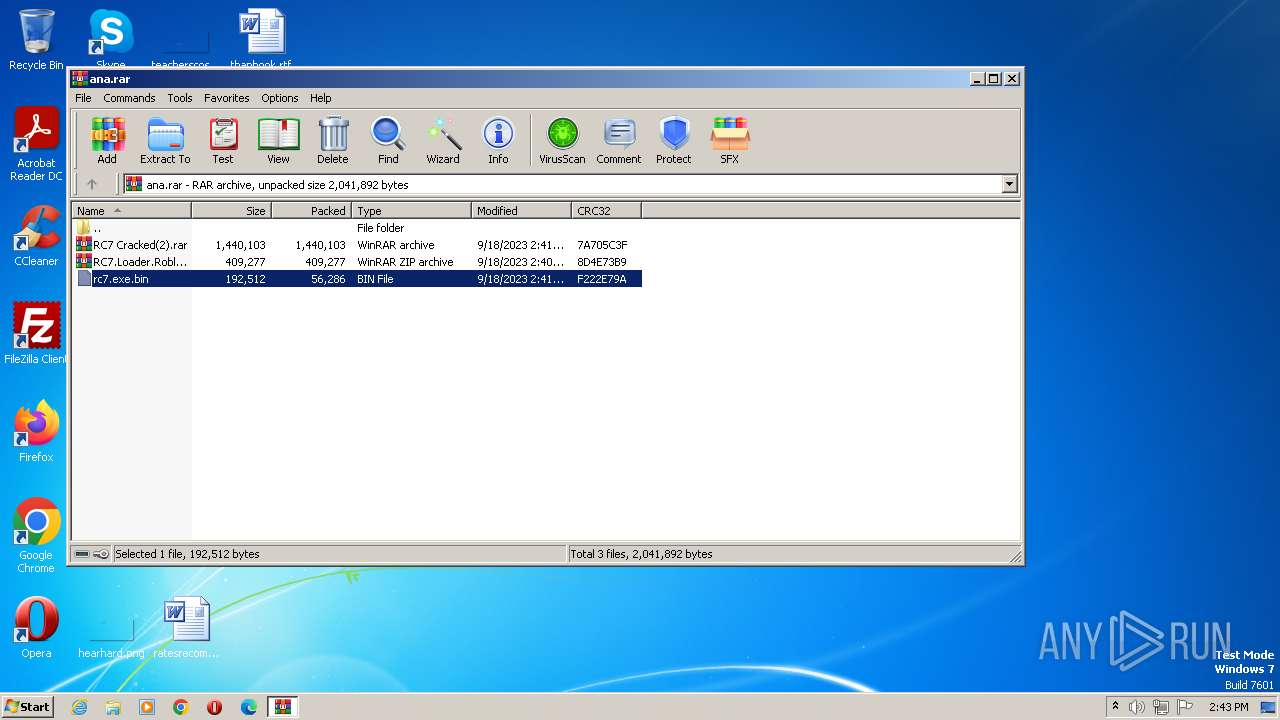
| File name: | ana.rar |
| Full analysis: | https://app.any.run/tasks/5629d807-33e7-4ba5-bf17-425ebadd292f |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | September 18, 2023, 13:43:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 14CCCFDFE51C91DA9A39F5C1C65289FA |
| SHA1: | 369870FF2189543C66CBA3CCA3F452558A6056B0 |
| SHA256: | E3BD75EEAFE4523A3E106BE47C414226260814E49AE1E639599DDFFF9E71F96F |
| SSDEEP: | 49152:Xe2WLhQ5nDesP5bSJeDyEipmAMfhkARliU983:XuQn7xS0Dn41MfQ |
MALICIOUS
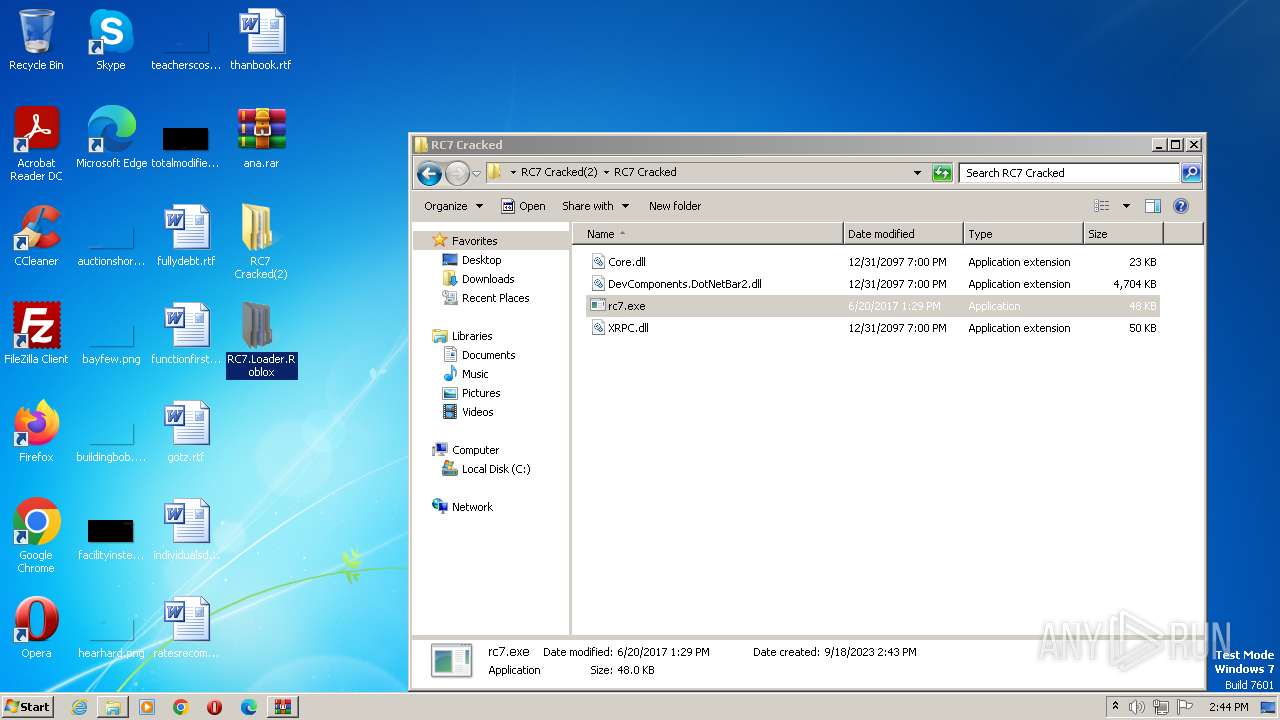
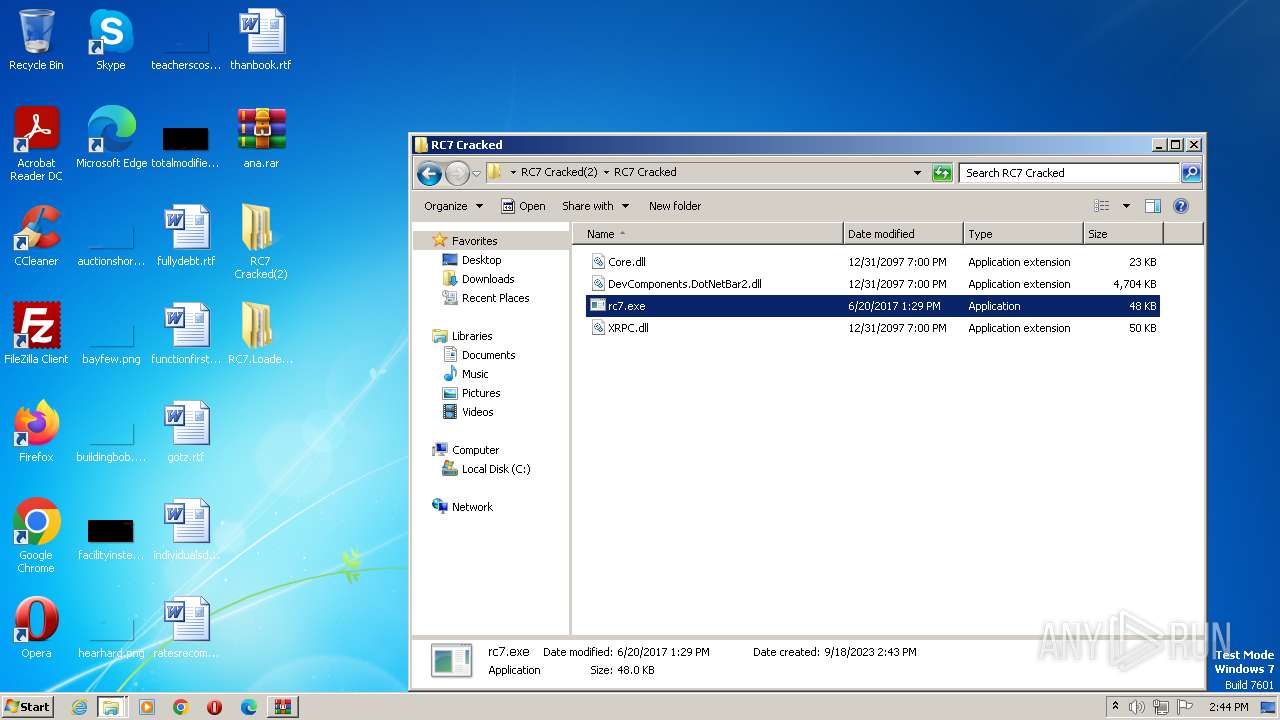
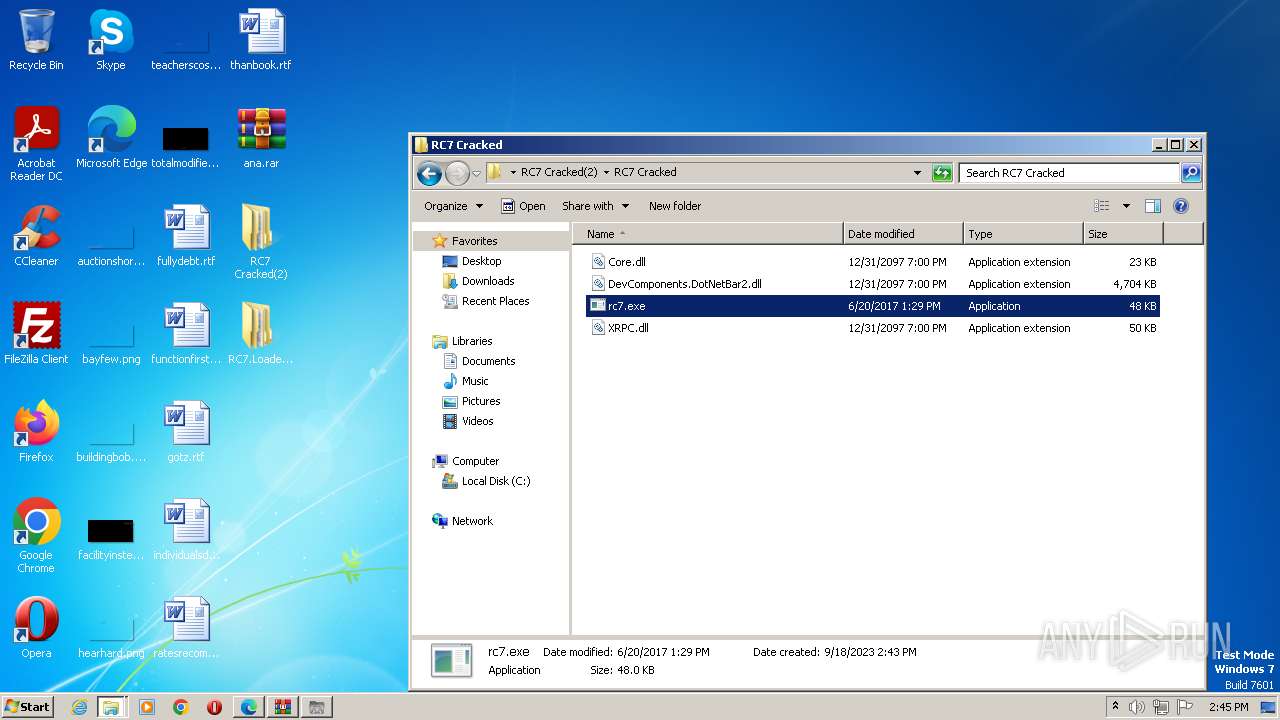
Application was dropped or rewritten from another process
- rc7.exe (PID: 3636)
- rc7.exe (PID: 3444)
- rc7.exe (PID: 752)
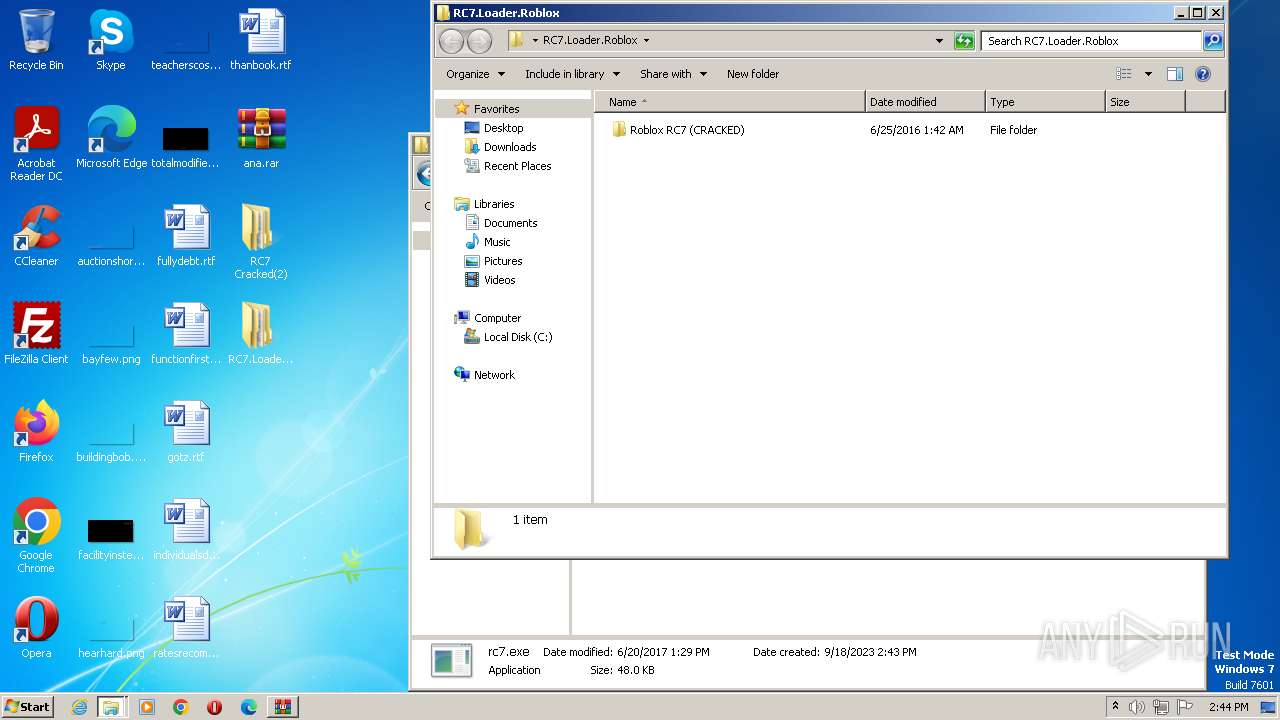
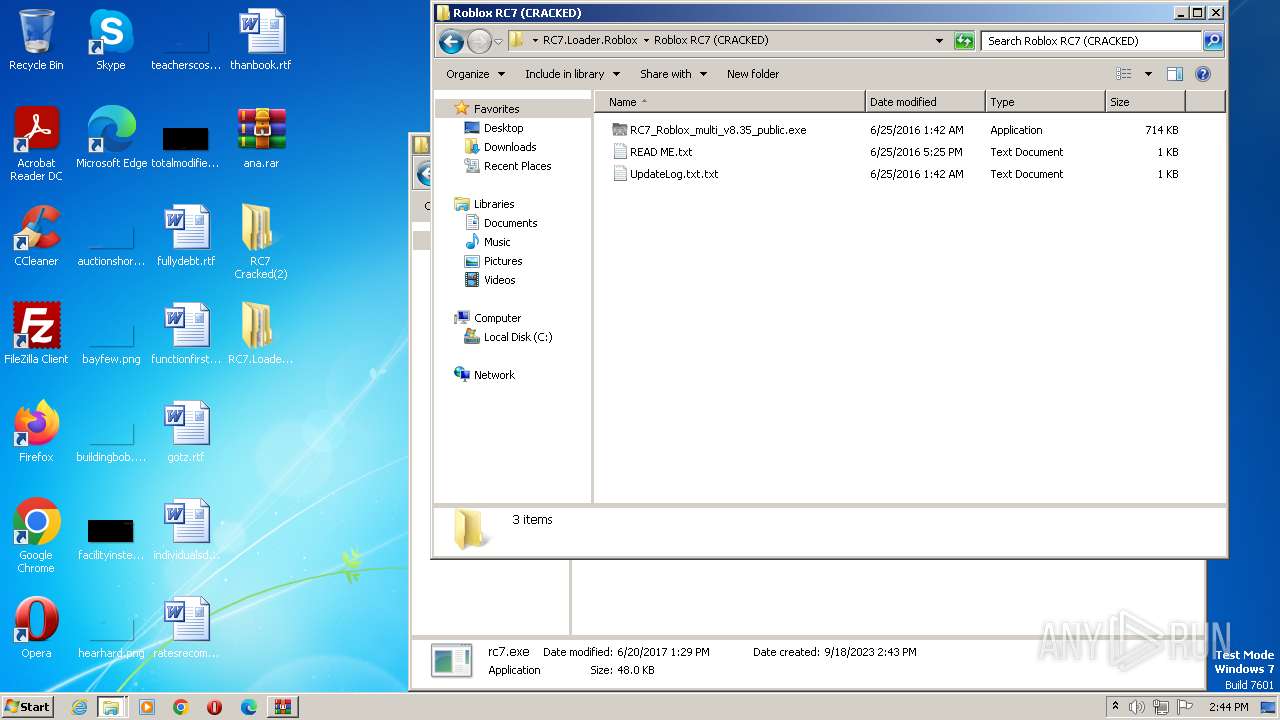
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- System.exe.exe (PID: 3888)
- RGHsetup.exe (PID: 3640)
- RGHsetup.exe (PID: 1908)
HAWKEYE detected by memory dumps
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
NJRAT detected by memory dumps
- System.exe.exe (PID: 3888)
Actions looks like stealing of personal data
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- vbc.exe (PID: 2716)
- vbc.exe (PID: 3752)
Create files in the Startup directory
- RGHsetup.exe (PID: 1908)
Changes appearance of the Explorer extensions
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
Steals credentials from Web Browsers
- vbc.exe (PID: 3752)
Changes the autorun value in the registry
- RGHsetup.exe (PID: 1908)
Steals credentials
- vbc.exe (PID: 3752)
Uses NirSoft utilities to collect credentials
- vbc.exe (PID: 3752)
NjRAT is detected
- RGHsetup.exe (PID: 1908)
SUSPICIOUS
Reads the Internet Settings
- rc7.exe (PID: 3636)
- rc7.exe (PID: 3444)
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- System.exe.exe (PID: 3888)
- rc7.exe (PID: 752)
Application launched itself
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
Starts itself from another location
- System.exe.exe (PID: 3888)
- rc7.exe (PID: 752)
The process creates files with name similar to system file names
- rc7.exe (PID: 752)
Connects to SMTP port
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
The process executes VB scripts
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
Uses NETSH.EXE to add a firewall rule or allowed programs
- RGHsetup.exe (PID: 1908)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3752)
Connects to unusual port
- RGHsetup.exe (PID: 1908)
Accesses Microsoft Outlook profiles
- vbc.exe (PID: 2716)
INFO
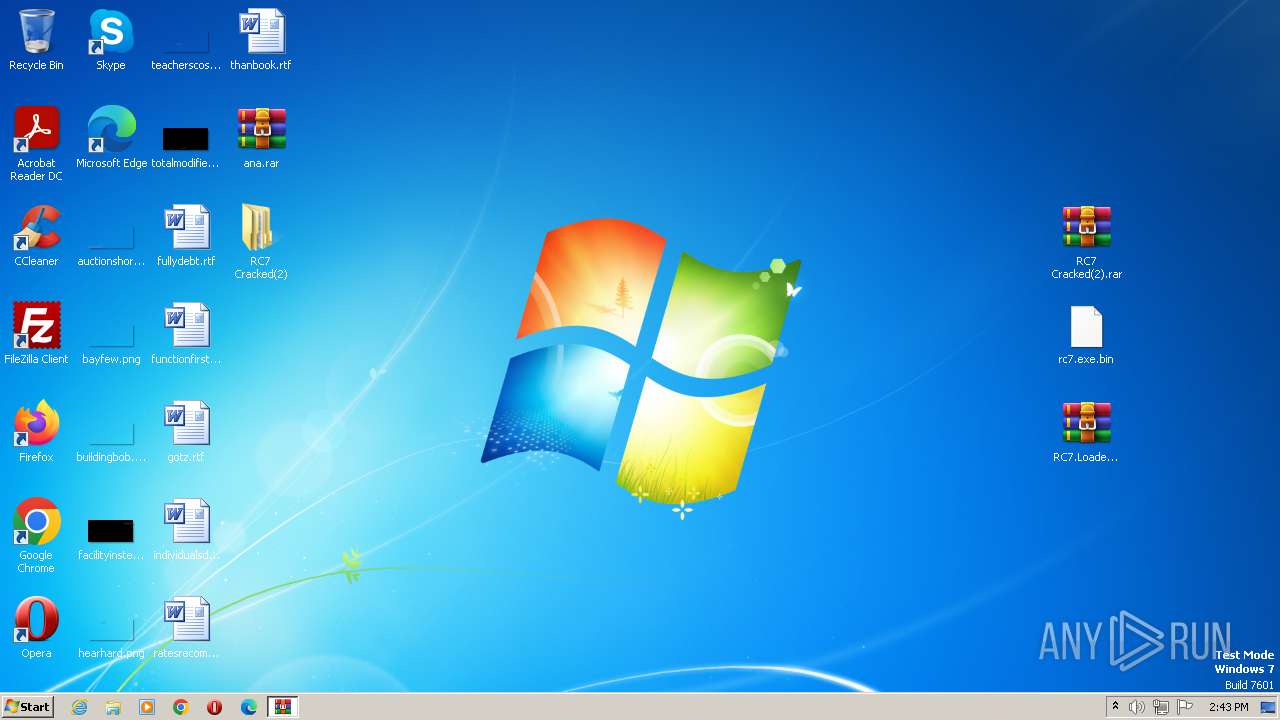
Manual execution by a user
- rc7.exe (PID: 3636)
- WinRAR.exe (PID: 2992)
- WinRAR.exe (PID: 3252)
- rc7.exe (PID: 3444)
- rc7.exe (PID: 752)
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- msedge.exe (PID: 2544)
Checks supported languages
- rc7.exe (PID: 3636)
- rc7.exe (PID: 3444)
- rc7.exe (PID: 752)
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- RGHsetup.exe (PID: 1908)
- System.exe.exe (PID: 3888)
- vbc.exe (PID: 2716)
- vbc.exe (PID: 3752)
Reads the computer name
- rc7.exe (PID: 3444)
- rc7.exe (PID: 3636)
- rc7.exe (PID: 752)
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- System.exe.exe (PID: 3888)
- RGHsetup.exe (PID: 1908)
- vbc.exe (PID: 2716)
- vbc.exe (PID: 3752)
Reads Environment values
- rc7.exe (PID: 3636)
- rc7.exe (PID: 3444)
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- RGHsetup.exe (PID: 1908)
Reads the machine GUID from the registry
- rc7.exe (PID: 3444)
- rc7.exe (PID: 3636)
- rc7.exe (PID: 752)
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- RC7_Roblox_multi_v8.35_public.exe (PID: 980)
- System.exe.exe (PID: 3888)
- RGHsetup.exe (PID: 1908)
- vbc.exe (PID: 3752)
Create files in a temporary directory
- rc7.exe (PID: 752)
- RGHsetup.exe (PID: 1908)
- System.exe.exe (PID: 3888)
- vbc.exe (PID: 3752)
- vbc.exe (PID: 2716)
Creates files or folders in the user directory
- RC7_Roblox_multi_v8.35_public.exe (PID: 2304)
- RGHsetup.exe (PID: 1908)
Application launched itself
- msedge.exe (PID: 1992)
- msedge.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Hawkeye
(PID) Process(2304) RC7_Roblox_multi_v8.35_public.exe
encryptedemailstringytdylanplays@mail.com
encryptedpassstringmoeder2420
encryptedsmtpstringsmtp.mail.com
portstring587
timerstring600000000
fakemgrstringThe application failed to initialize properly (0xc0000135)
encryptedftphostftp.host.com
encryptedftpuserusername
encryptedftppasspassword
encryptedphplinkhttp://www.DeceptiveEngineering.com/path/logs.php
useemailyesemail
useftpnoftp
usephpnophp
delaytime0
cleariedontclearie
clearffclearff
binderbindfiles
downloaderdownloadfiles
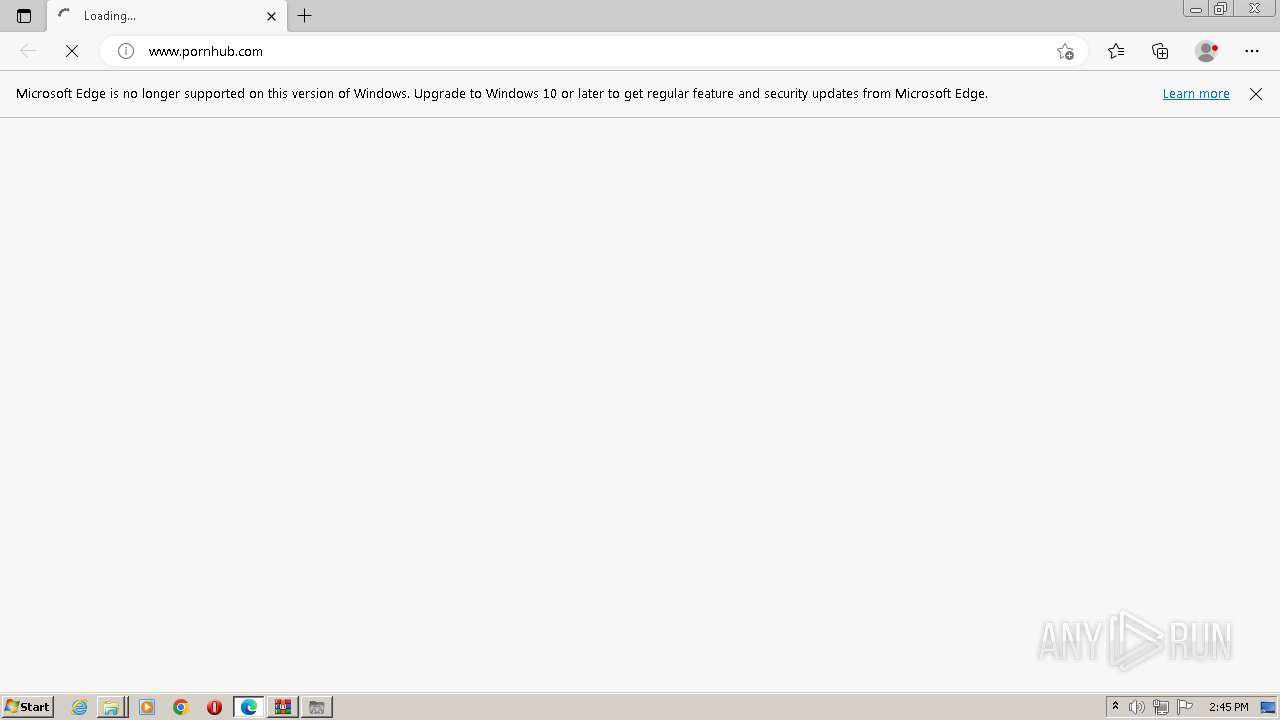
websitevisitorwww.pornhub.com/||
websiteblockerhtttp://youtube.com||http://store.steampowered.com/||steampowered.com||
AdminRightsAdminRights
notifynotify
DisableSSLDisableSSL
fakerrorfakeerror
startupDisablestartup
screenyscreeny
clipclip
TaskManagerTaskManager
loggerlogger
stealersstealers
meltDisablemelt
regreg
cmdcmd
misconfigmsconfig
spreadersspreaders
steamsteam
NjRat
(PID) Process(3888) System.exe.exe
C265.129.96.197
Ports2324
BotnetScammer
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\589bcd23d8efcc0c8745b31b96671f01
Splitter|'|'|
Version0.7d
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
84
Monitored processes
37
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3784 --field-trial-handle=1292,i,10683794422296475207,16156166003990069064,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1312 --field-trial-handle=1336,i,6733229737979116885,8134325718125196687,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3636 --field-trial-handle=1292,i,10683794422296475207,16156166003990069064,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
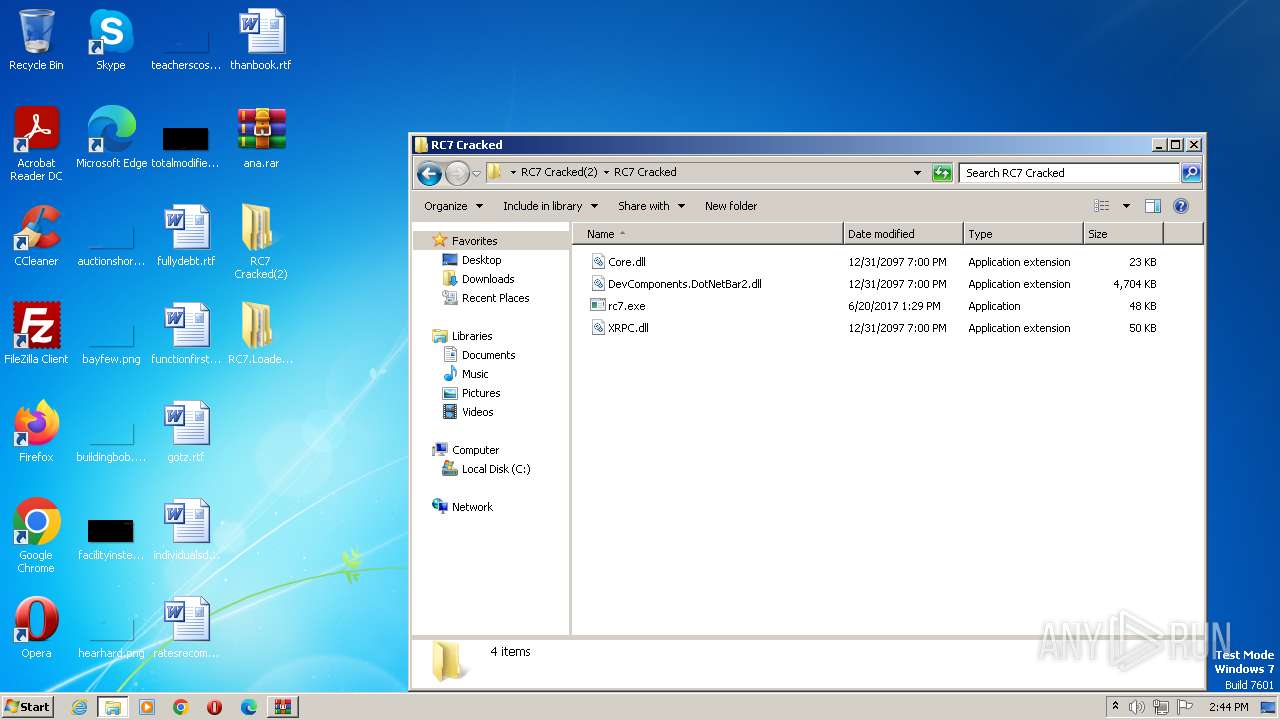
| 752 | "C:\Users\admin\Desktop\RC7 Cracked(2)\RC7 Cracked\rc7.exe" | C:\Users\admin\Desktop\RC7 Cracked(2)\RC7 Cracked\rc7.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1432 --field-trial-handle=1336,i,6733229737979116885,8134325718125196687,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 980 | "C:\Users\admin\Desktop\RC7.Loader.Roblox\Roblox RC7 (CRACKED)\RC7_Roblox_multi_v8.35_public.exe" | C:\Users\admin\Desktop\RC7.Loader.Roblox\Roblox RC7 (CRACKED)\RC7_Roblox_multi_v8.35_public.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2564 --field-trial-handle=1292,i,10683794422296475207,16156166003990069064,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6546f598,0x6546f5a8,0x6546f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2532 --field-trial-handle=1292,i,10683794422296475207,16156166003990069064,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3884 --field-trial-handle=1292,i,10683794422296475207,16156166003990069064,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
9 152
Read events
8 924
Write events
227
Delete events
1
Modification events
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
10
Suspicious files
26
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3652.11509\RC7.Loader.Roblox.zip | compressed | |
MD5:40ACEC92CD1367F856282DA61A390B86 | SHA256:76117126967A23E504393FD1EFDA3DC94AC9D93E59E9CEBF72C4DB7A53551B15 | |||
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3652.11509\rc7.exe.bin | executable | |
MD5:54A6DE9117B9B627FE53244891C77425 | SHA256:E62FEAC8C097A48457124882574F212E1BF61CB8F15CFAC1301C86FDE3039D56 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\RC7 Cracked(2)\RC7 Cracked\XRPC.dll | executable | |
MD5:F4B9DC07DBB55B31F6DBC96CC28F22A1 | SHA256:E29374583FDD82F23B3304AA29934E2F33BD5061E886D4279A013A194E17DC65 | |||
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3652.11509\RC7 Cracked(2).rar | compressed | |
MD5:ED7FB9E8BAE924B6142D0131A3C70DD5 | SHA256:8A39C43E42470ED2D16D33FA0E8D0F07B6CD7BBBA587A1119C68D75DFBF6B719 | |||
| 1992 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:6BBE1BFA3A9FEDA71E860D7BEE338526 | SHA256:A7D313A5230EA1B2C67C3ACDC75D66F87D214E760AEBD7B2228A9EEBBAB5C897 | |||
| 1992 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1908 | RGHsetup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\589bcd23d8efcc0c8745b31b96671f01.exe | executable | |
MD5:07F0C03DD5EE7510D1F8BDEC18C59991 | SHA256:3ABCE06E1906705B91D8F7DD1FE31373CA75CE8965DC0D434BCEE7A359E1DFF2 | |||
| 2304 | RC7_Roblox_multi_v8.35_public.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:20C1D6AD5E5BFE66F84669D052E4CA06 | SHA256:5CDD2E73818F6C2C173E38164341B64437AD60B9F25AEFE6BAB2F079F4F6CFD4 | |||
| 2612 | msedge.exe | — | ||
MD5:— | SHA256:— | |||
| 752 | rc7.exe | C:\Users\admin\AppData\Local\Temp\System.exe.exe | executable | |
MD5:07F0C03DD5EE7510D1F8BDEC18C59991 | SHA256:3ABCE06E1906705B91D8F7DD1FE31373CA75CE8965DC0D434BCEE7A359E1DFF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
36
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2736 | msedge.exe | GET | 301 | 66.254.114.41:80 | http://www.pornhub.com/ | unknown | — | — | unknown |
2736 | msedge.exe | GET | 204 | 13.107.6.158:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2304 | RC7_Roblox_multi_v8.35_public.exe | 104.16.155.36:80 | whatismyipaddress.com | CLOUDFLARENET | — | shared |
2304 | RC7_Roblox_multi_v8.35_public.exe | 104.16.154.36:80 | whatismyipaddress.com | CLOUDFLARENET | — | shared |
2304 | RC7_Roblox_multi_v8.35_public.exe | 74.208.5.15:587 | smtp.mail.com | IONOS SE | US | unknown |
2544 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1908 | RGHsetup.exe | 65.129.96.197:2324 | — | CENTURYLINK-US-LEGACY-QWEST | US | unknown |
2736 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2736 | msedge.exe | 20.31.42.83:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pharahhack.x10host.com |
| unknown |
whatismyipaddress.com |
| shared |
dns.msftncsi.com |
| shared |
smtp.mail.com |
| shared |
config.edge.skype.com |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
www.pornhub.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |