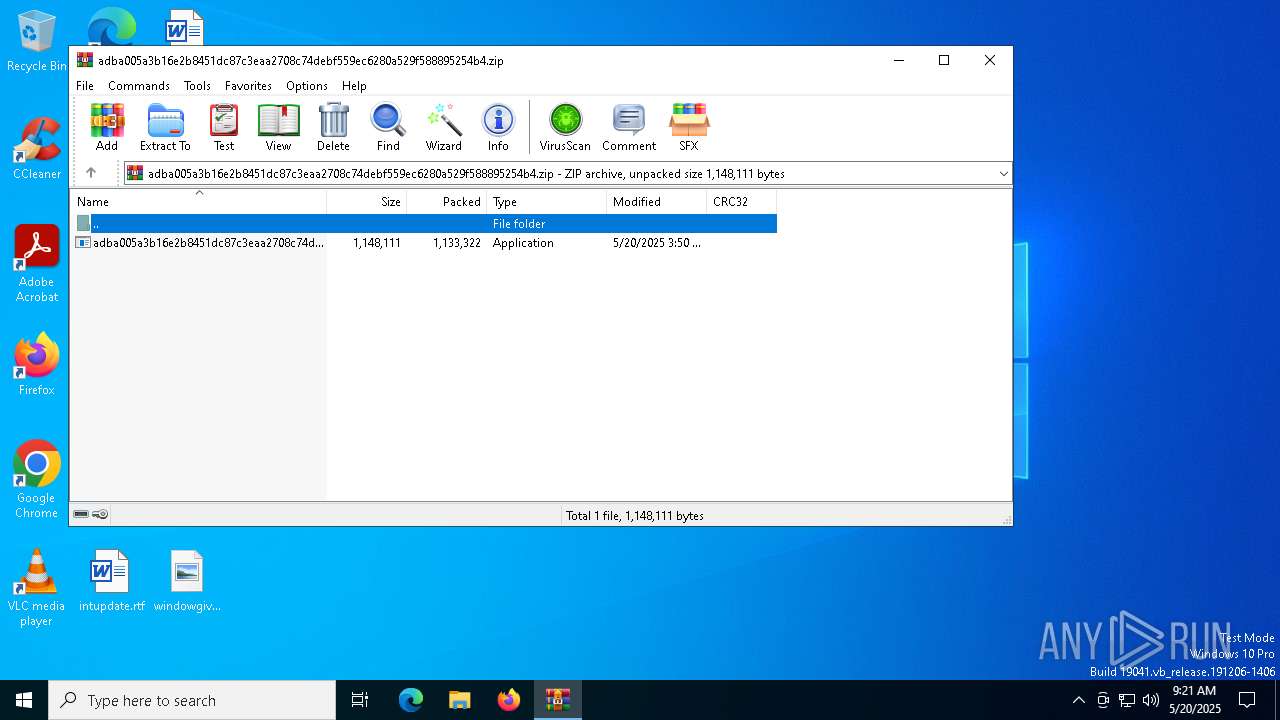
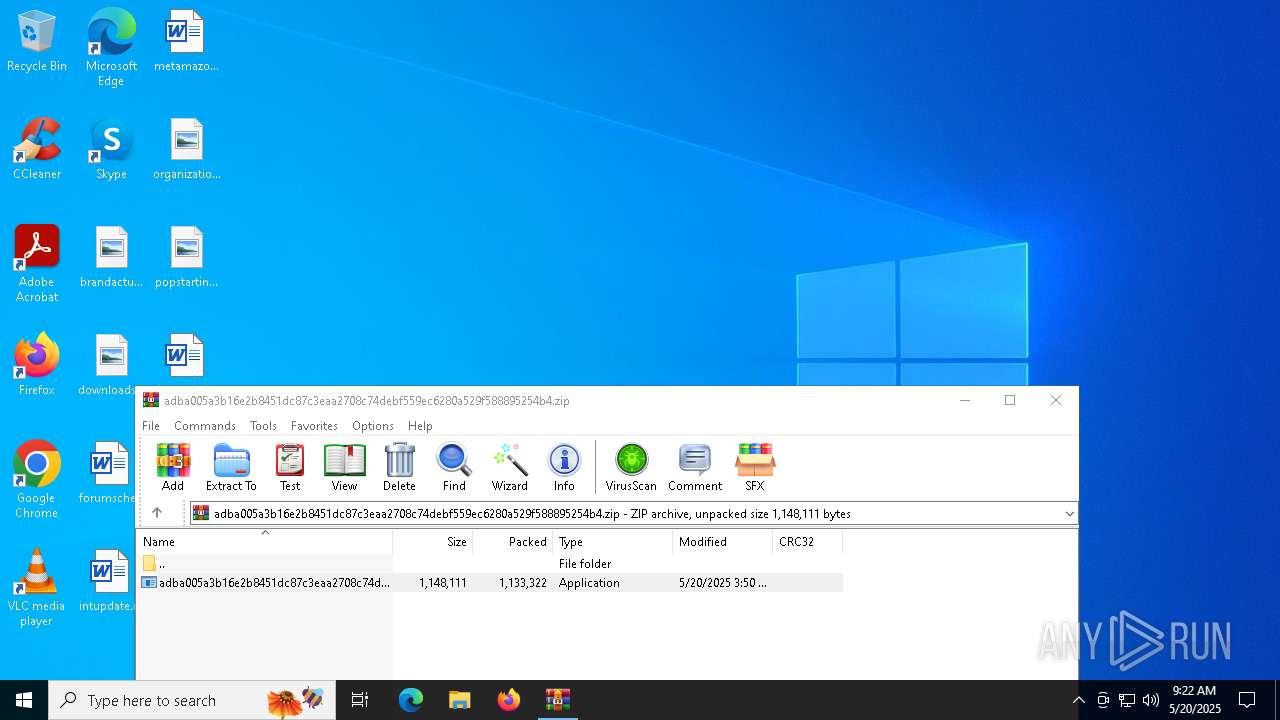
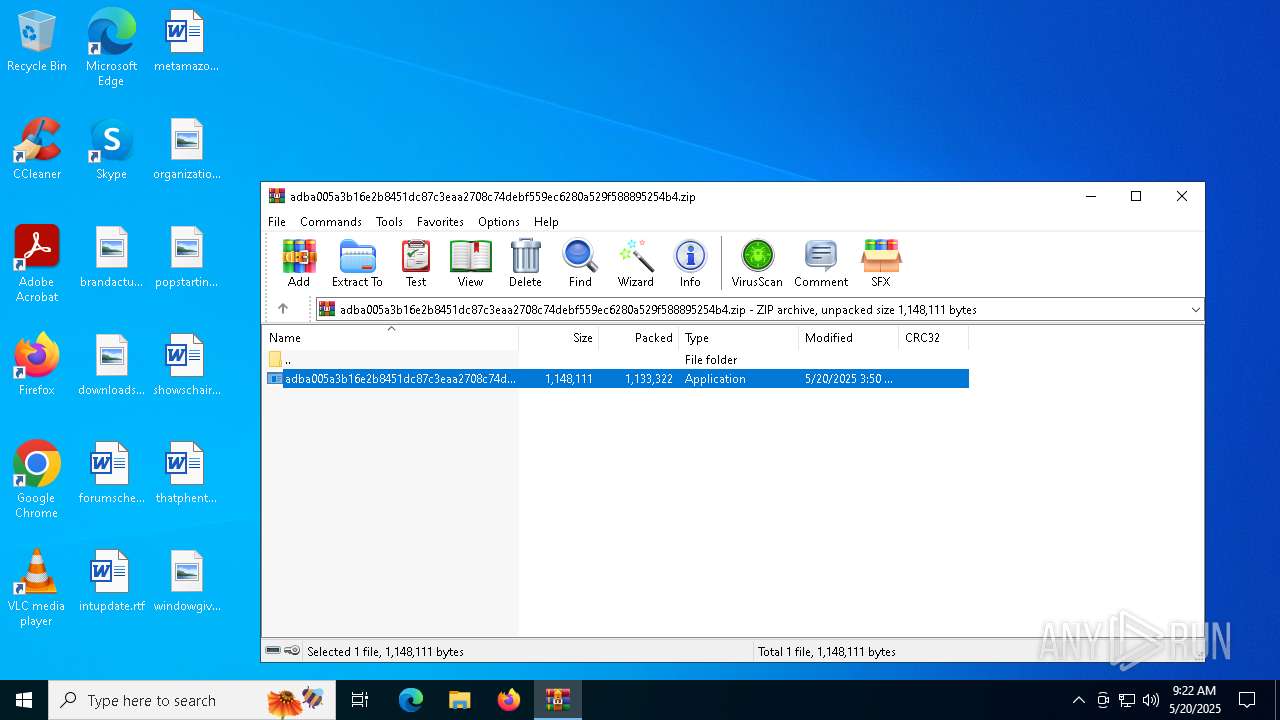
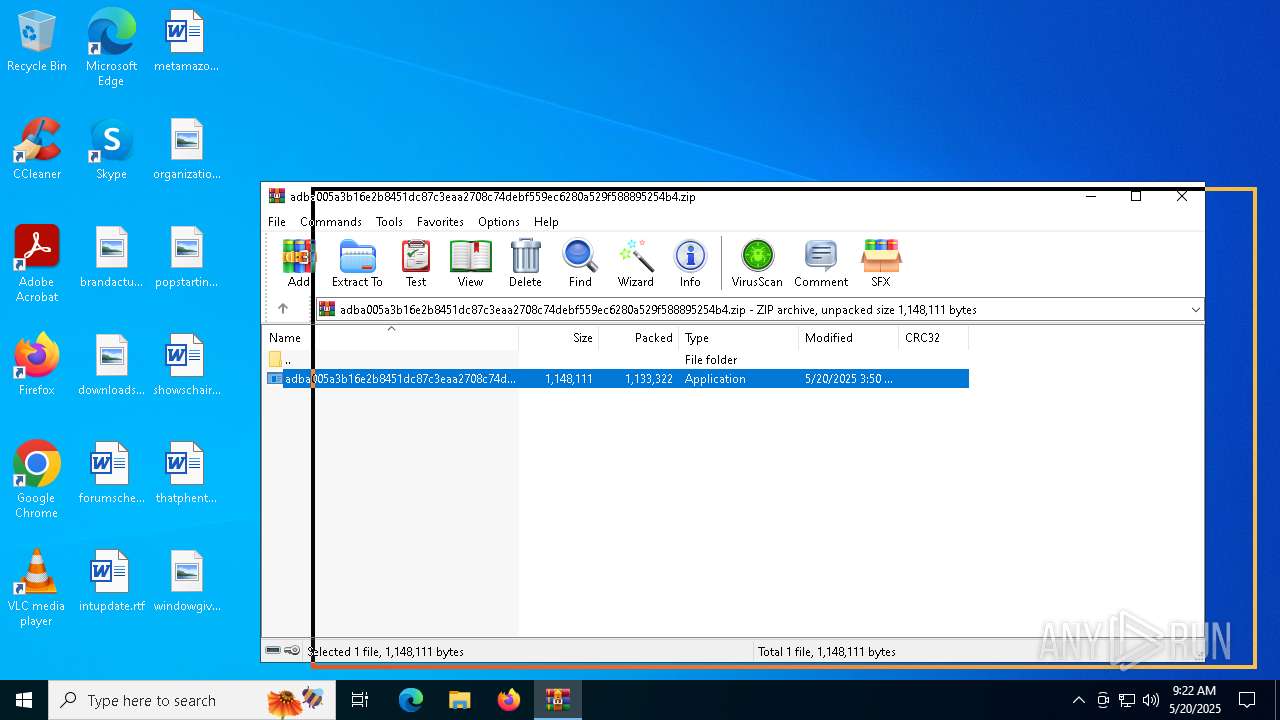
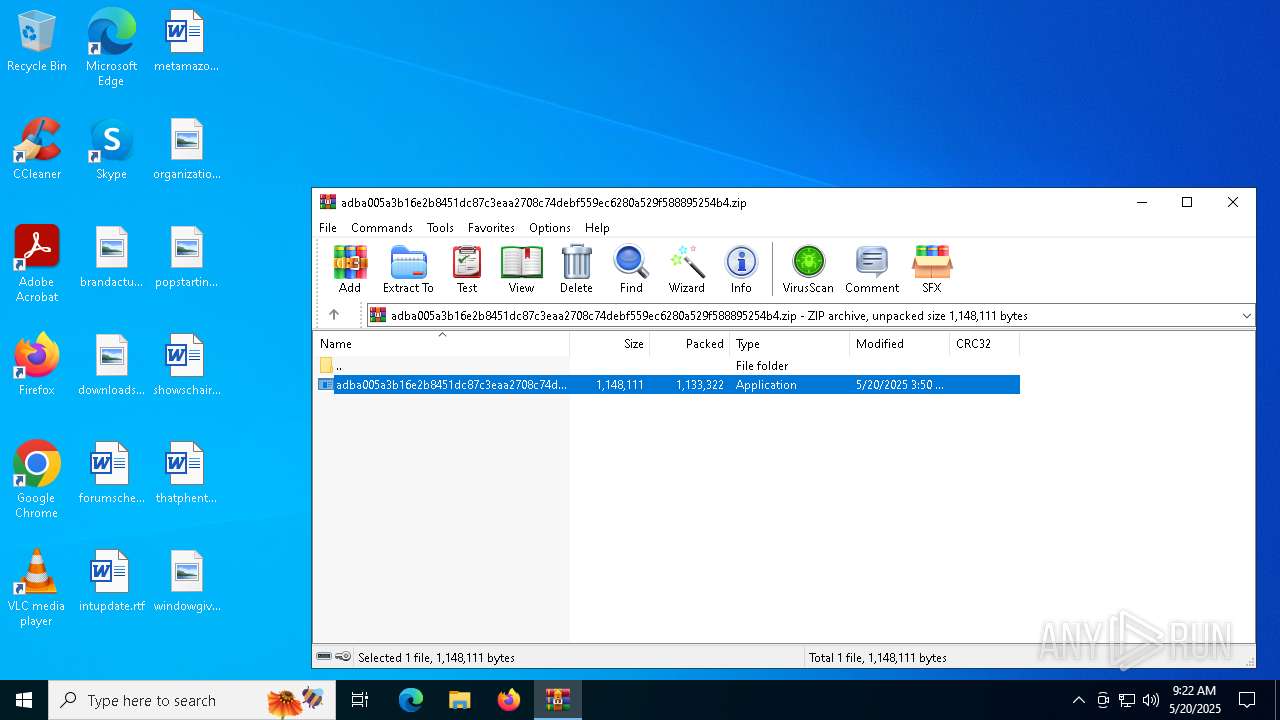
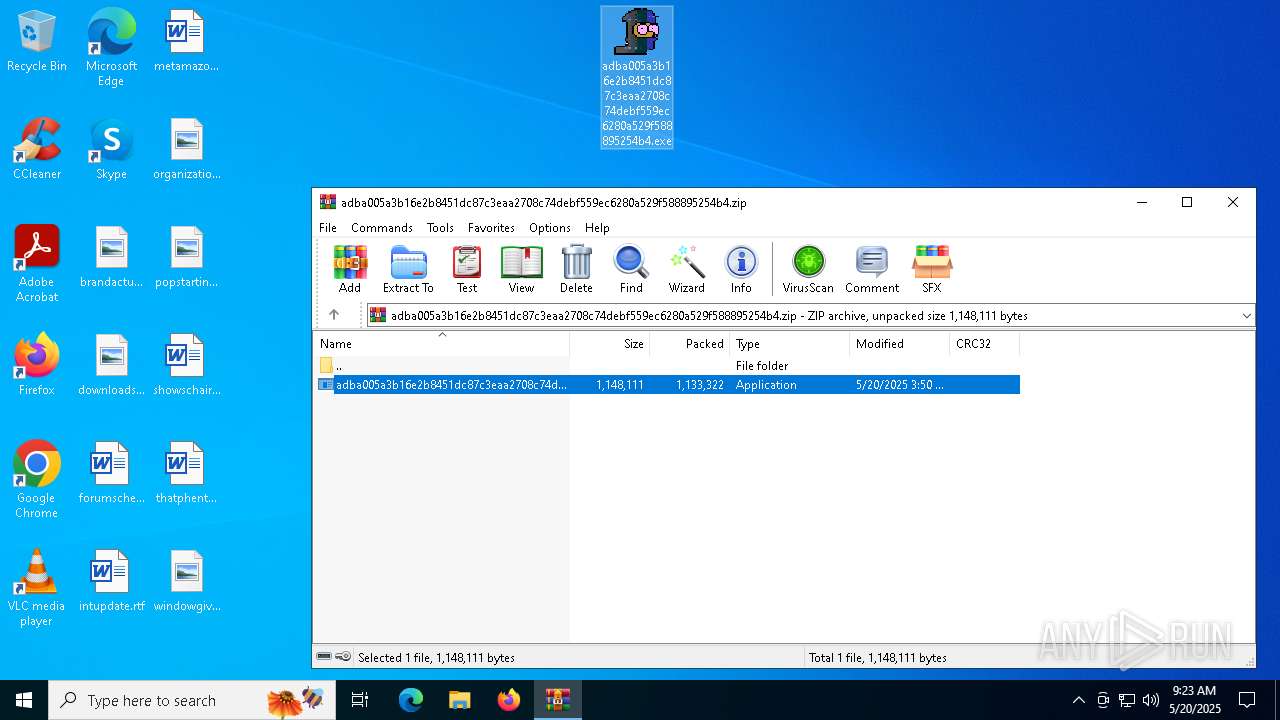
| File name: | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.zip |
| Full analysis: | https://app.any.run/tasks/bb5491f7-8632-4e9d-a706-effa5b00c2be |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | May 20, 2025, 09:21:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
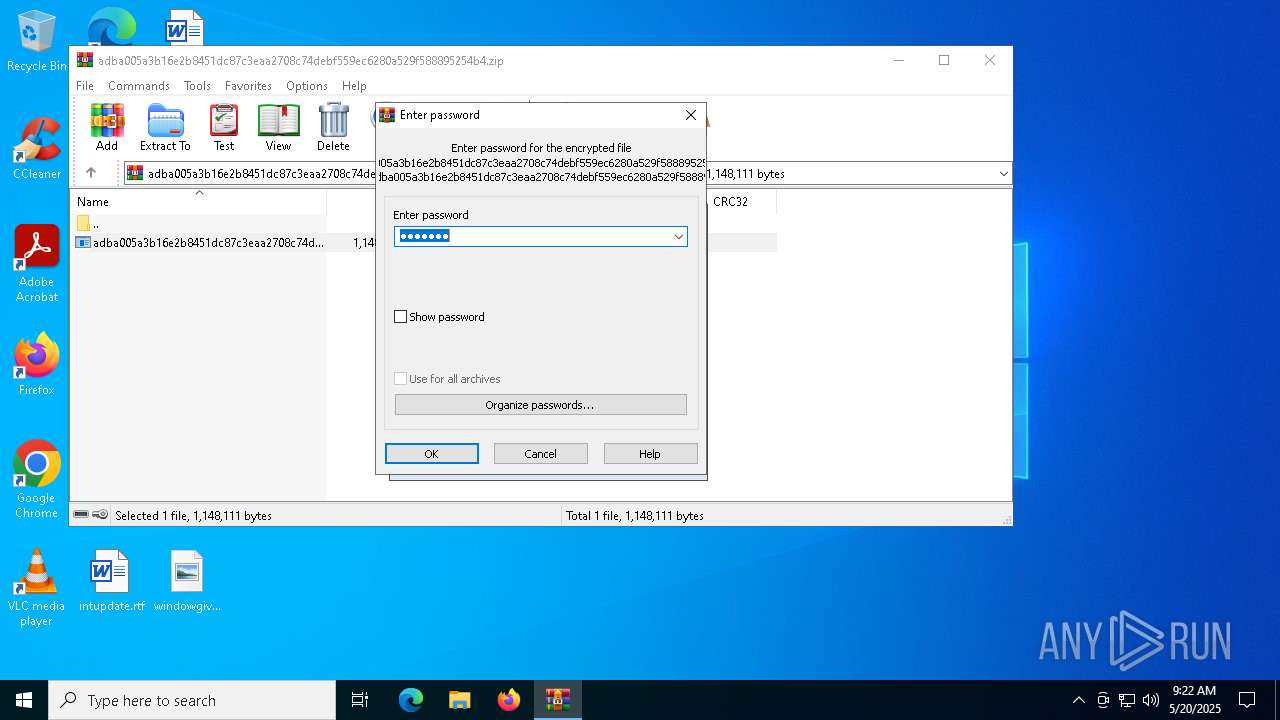
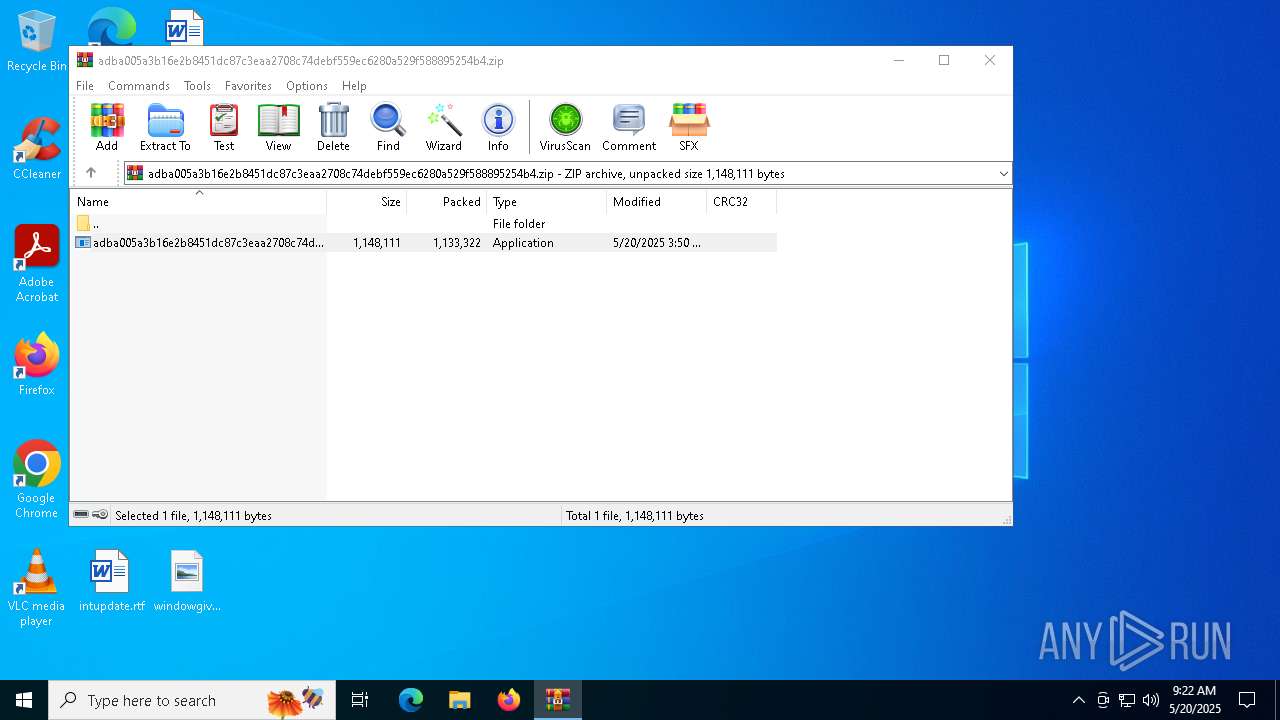
| MIME: | application/zip |
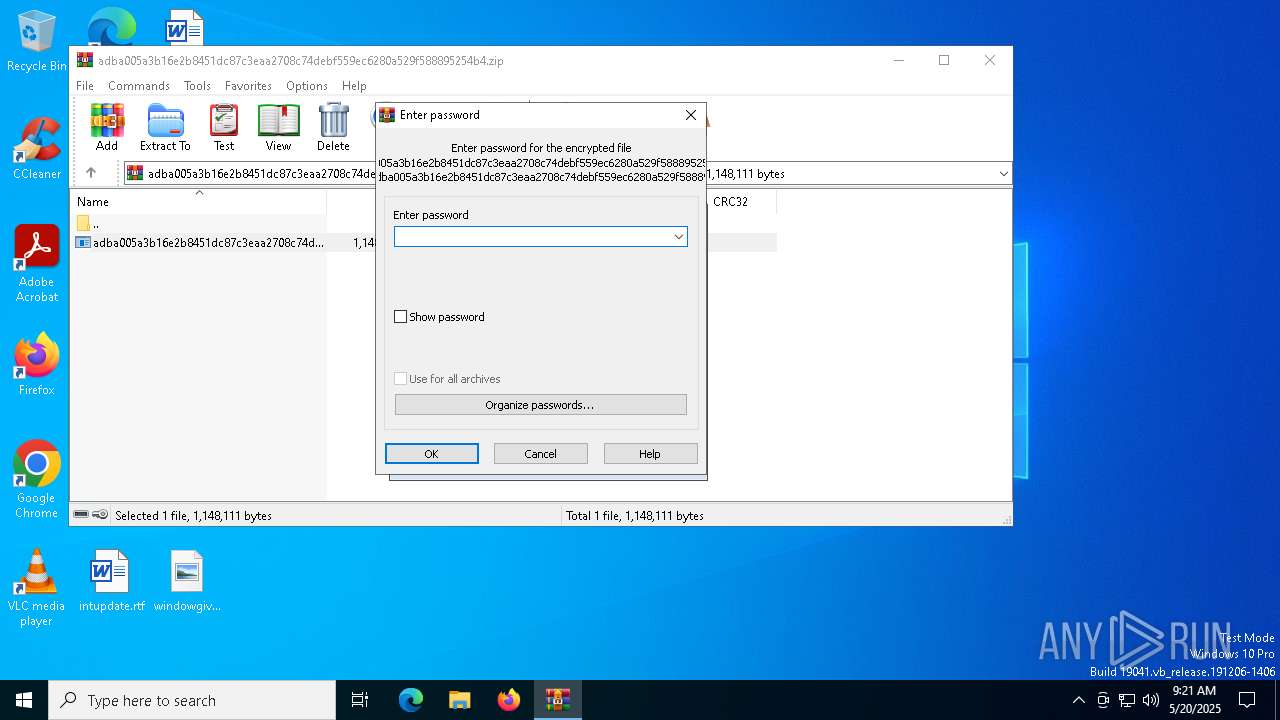
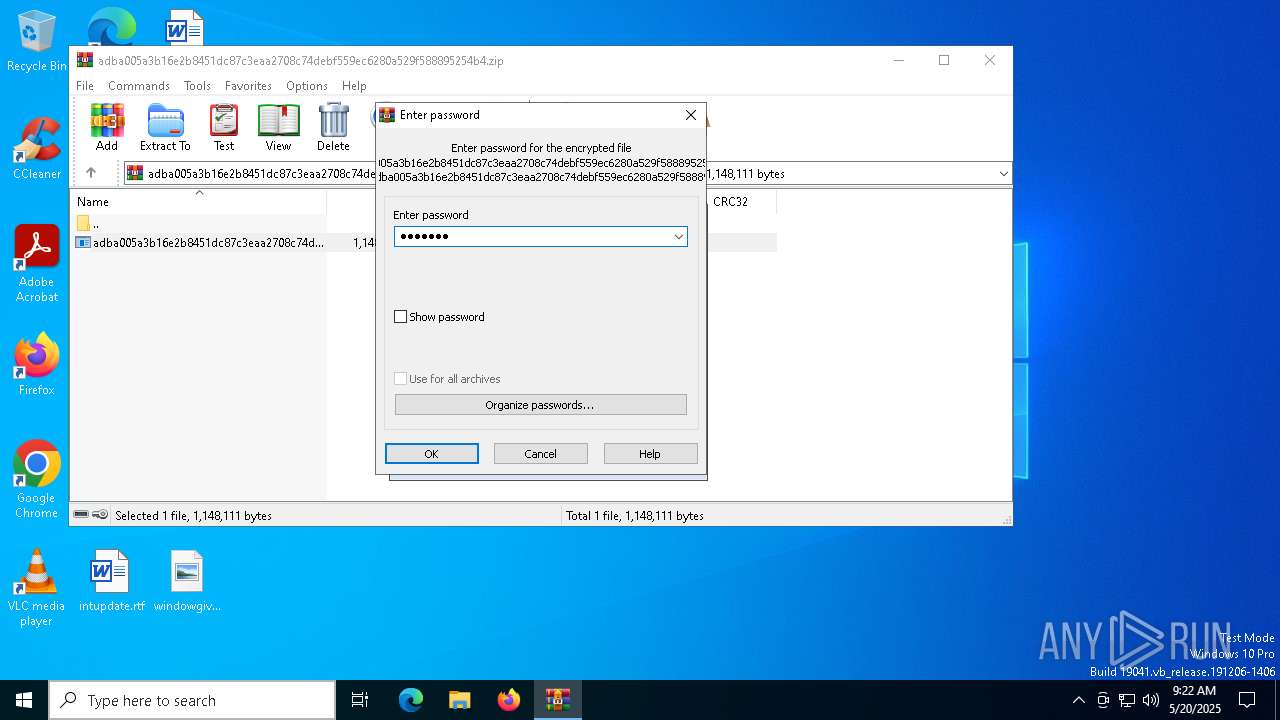
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | D92CD3908B883C21336897816FA43F29 |
| SHA1: | EF3AAB5A5AA49DF23EFC07546921CA1BA6F69685 |
| SHA256: | E360F2CB375027BF0AF5FB2B850B9BD67ED5B1AE5DA9018A917DB93BB6AE44AF |
| SSDEEP: | 49152:zMlGndvcb0IP6d1bGMb5u06qTWUXU4xcV4l1VlFvdSx3e4CoTiDbG3s0/GOSHqWC:wEnCb0IPsu0BT7U4a4lzrvdMCop3saeK |
MALICIOUS
REMCOS has been detected (YARA)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
REMCOS has been detected
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
GULOADER has been detected (YARA)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
REMCOS mutex has been found
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
REMCOS has been detected (SURICATA)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
GULOADER SHELLCODE has been detected (YARA)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
Application launched itself
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
Executable content was dropped or overwritten
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7176)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
The process creates files with name similar to system file names
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
There is functionality for taking screenshot (YARA)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
Contacting a server suspected of hosting an CnC
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
Connects to unusual port
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
INFO
Checks supported languages
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
Create files in a temporary directory
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
Creates files or folders in the user directory
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
The sample compiled with english language support
- WinRAR.exe (PID: 7176)
Reads the computer name
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 2108)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
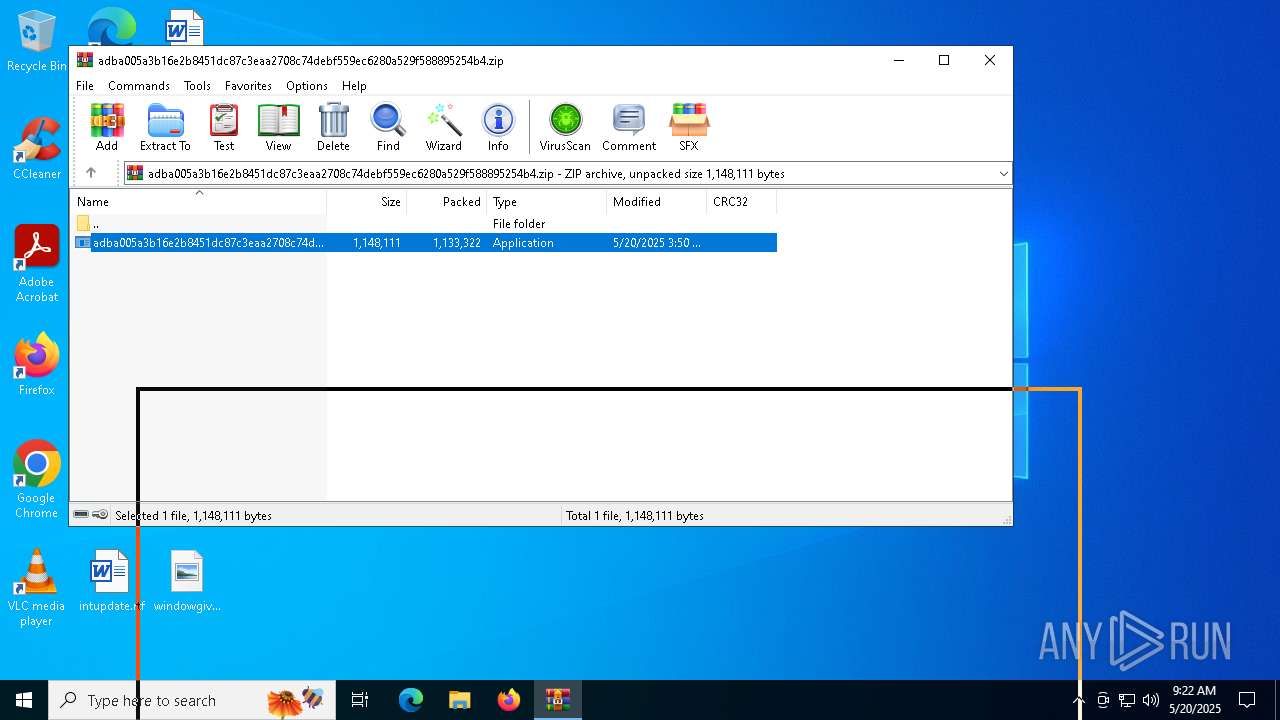
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7176)
Checks proxy server information
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
- slui.exe (PID: 7344)
Reads the machine GUID from the registry
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
Reads the software policy settings
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7384)
- slui.exe (PID: 7344)
Creates files in the program directory
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 5512)
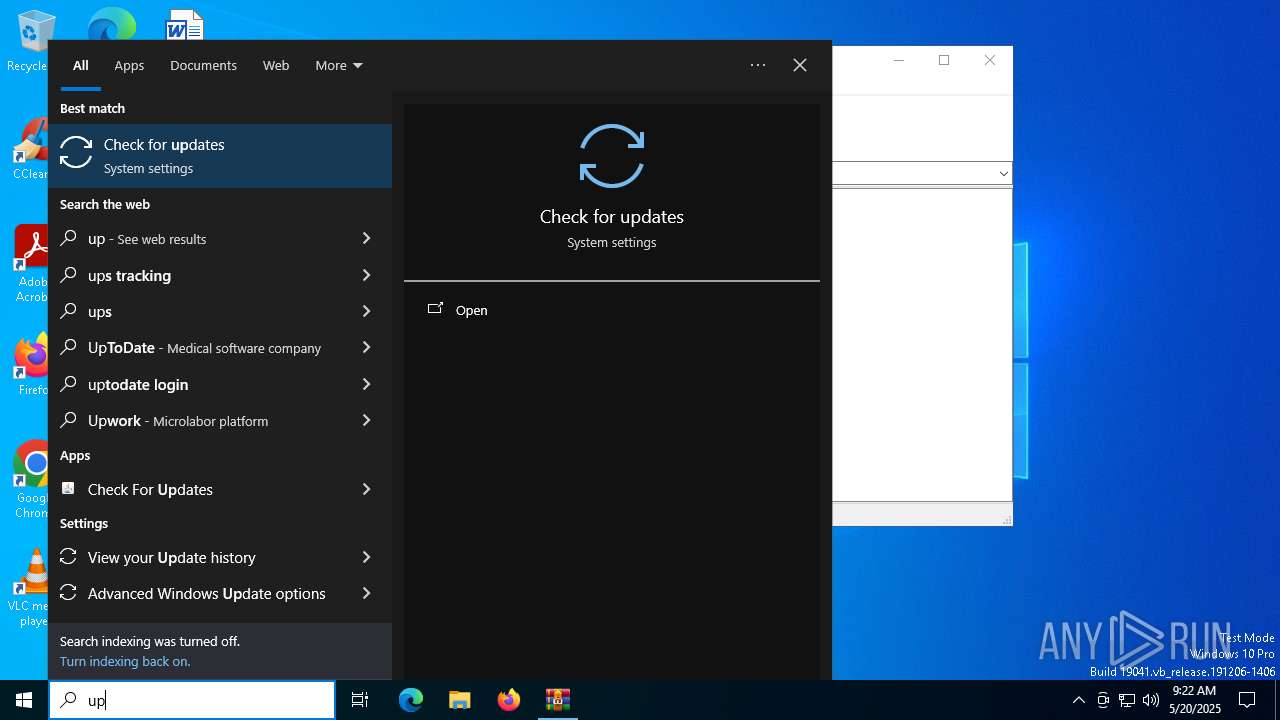
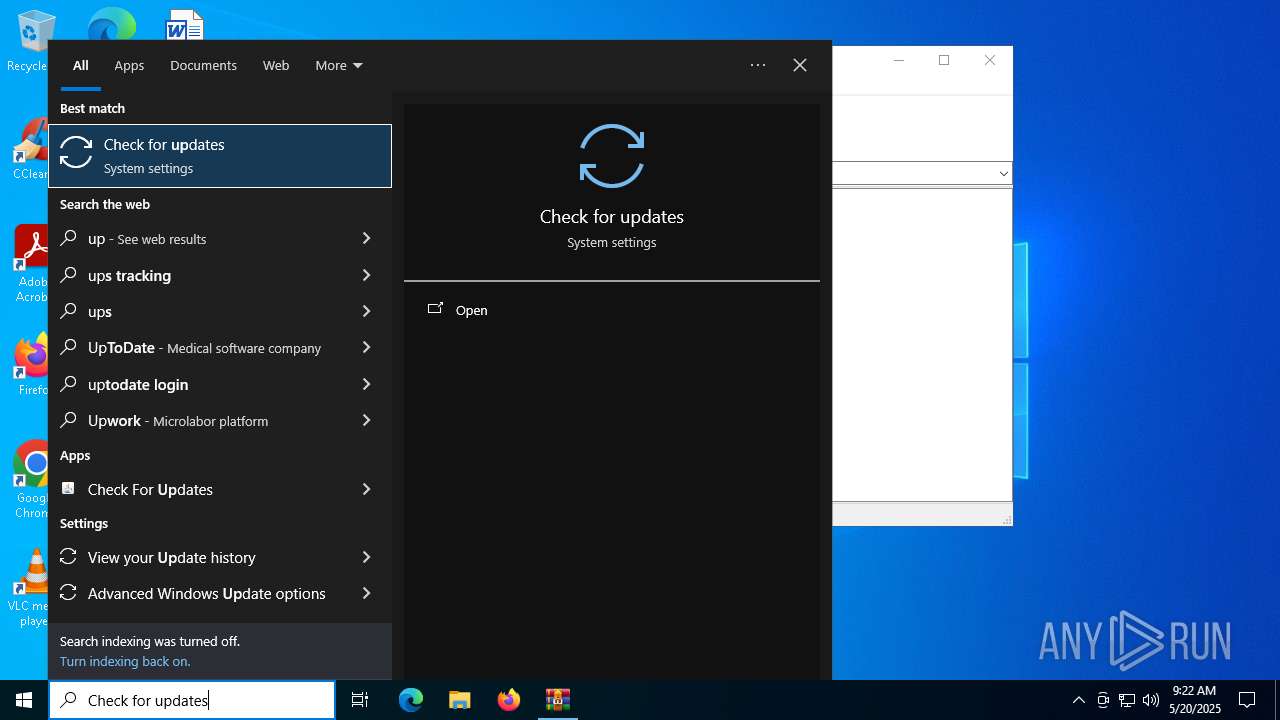
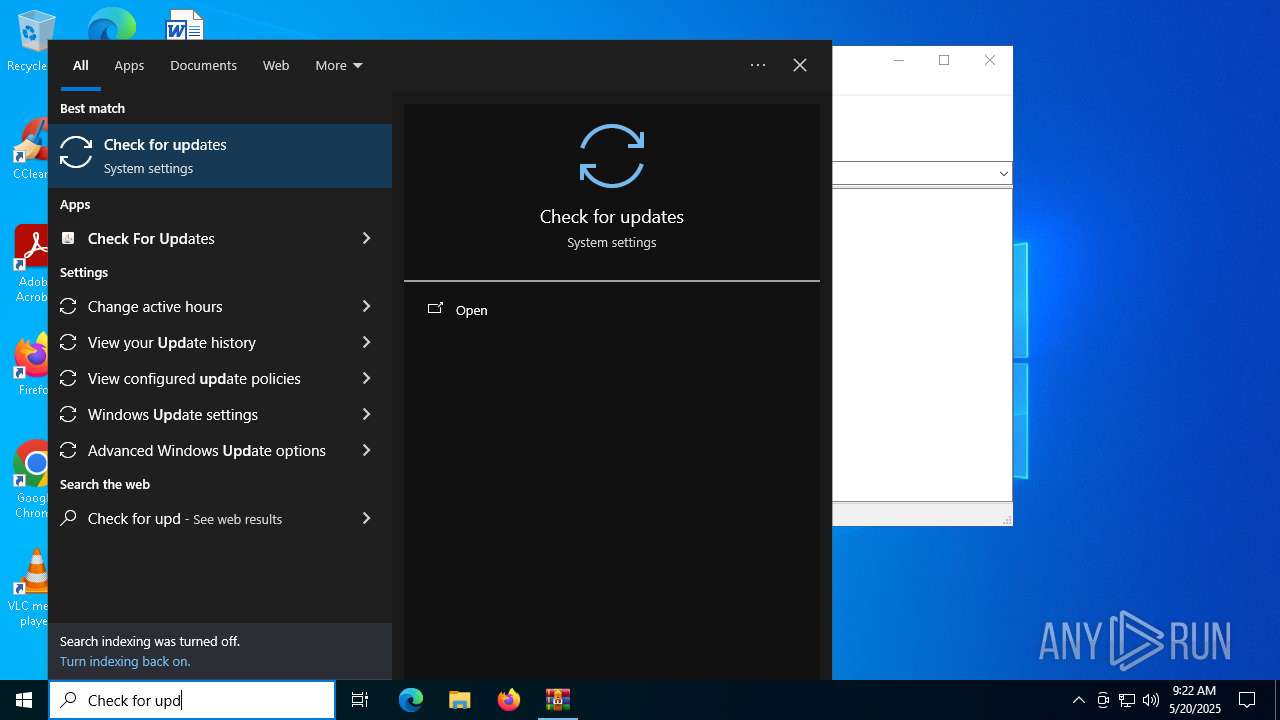
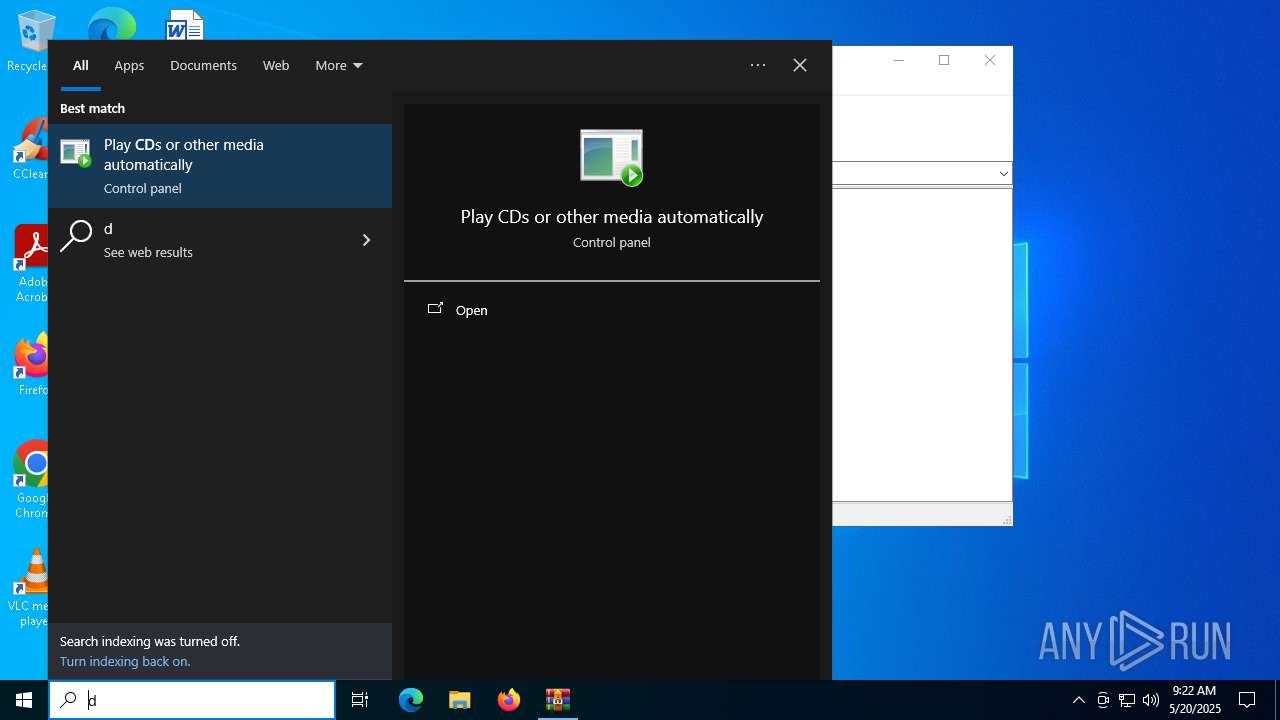
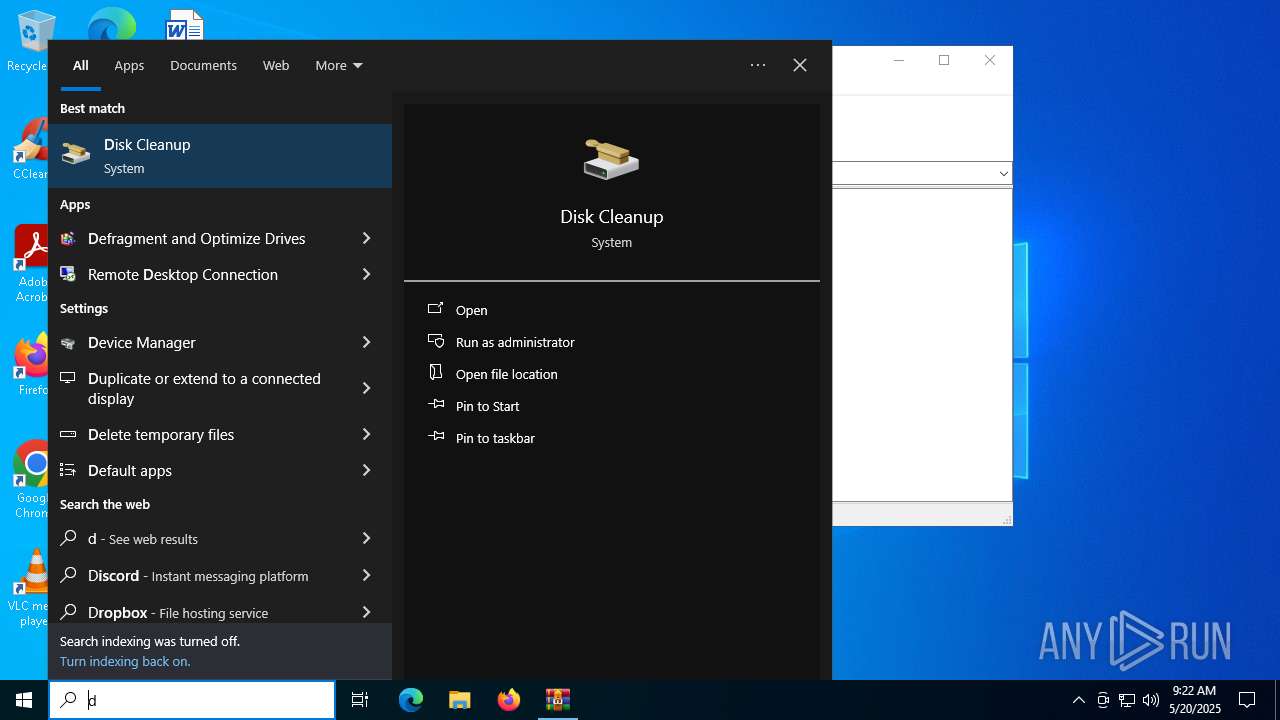
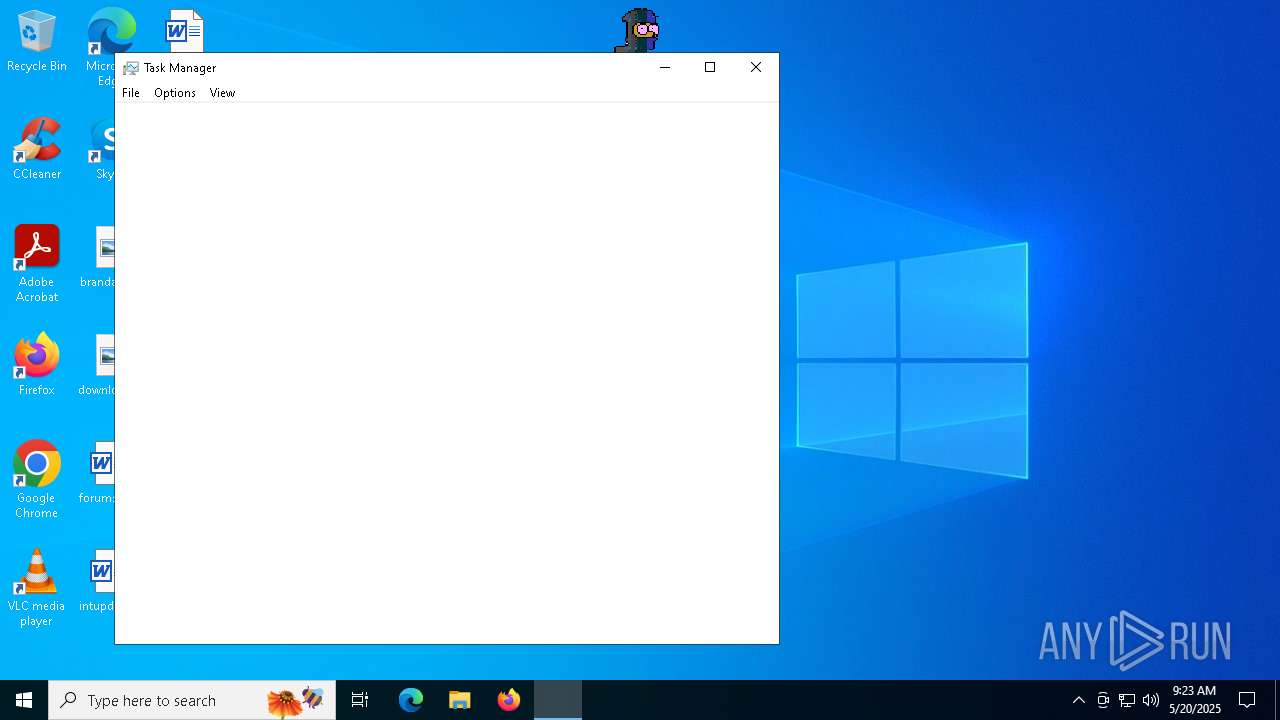
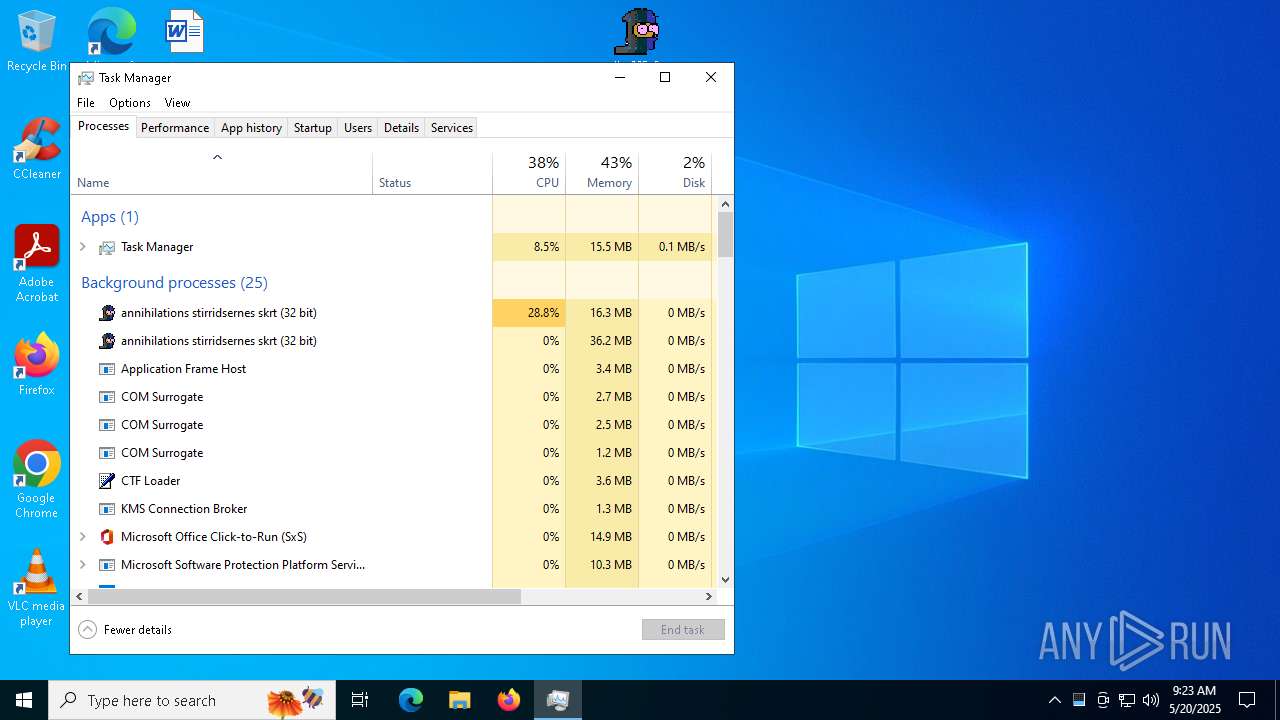
Manual execution by a user
- adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe (PID: 7476)
- Taskmgr.exe (PID: 7416)
- Taskmgr.exe (PID: 728)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:20 03:50:22 |
| ZipCRC: | 0x2c449fd3 |
| ZipCompressedSize: | 1133322 |
| ZipUncompressedSize: | 1148111 |
| ZipFileName: | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe |
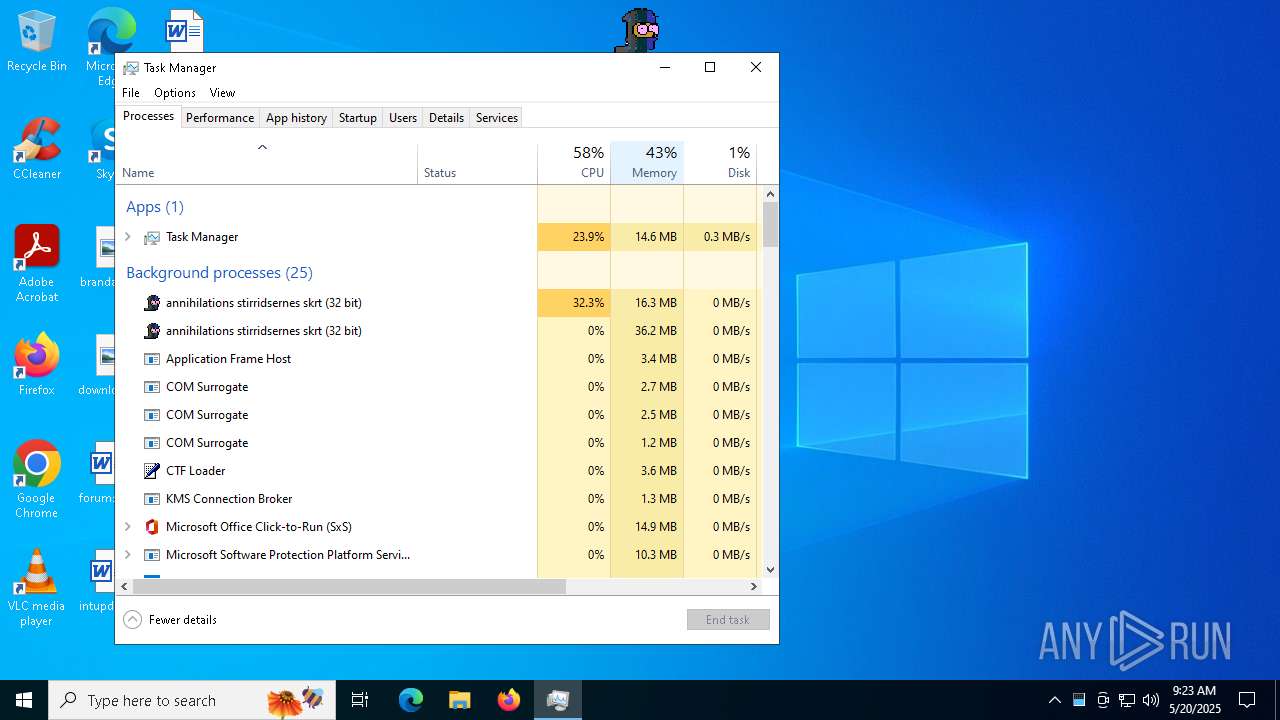
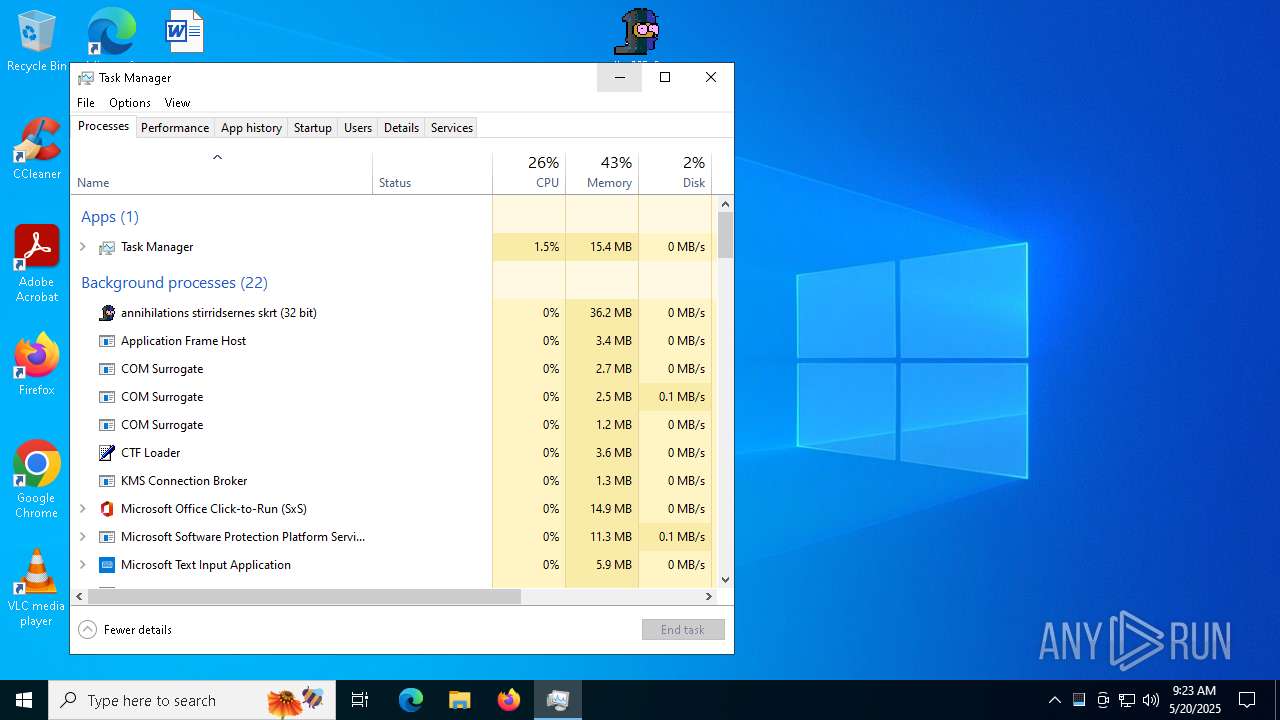
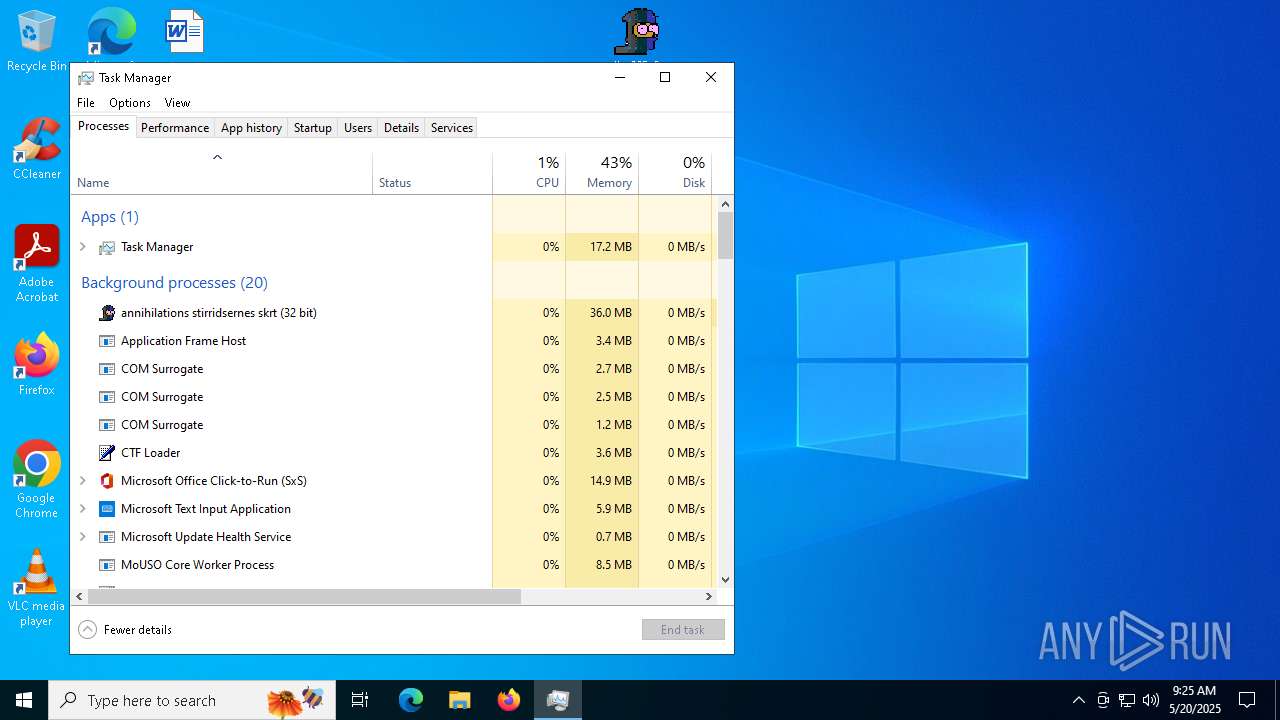
Total processes
145
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7176.22861\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb7176.22861\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | WinRAR.exe | ||||||||||||
User: admin Company: deltagne Integrity Level: MEDIUM Description: annihilations stirridsernes skrt Exit code: 0 Modules
| |||||||||||||||
| 5512 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7176.22861\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb7176.22861\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | ||||||||||||
User: admin Company: deltagne Integrity Level: MEDIUM Description: annihilations stirridsernes skrt Modules
| |||||||||||||||
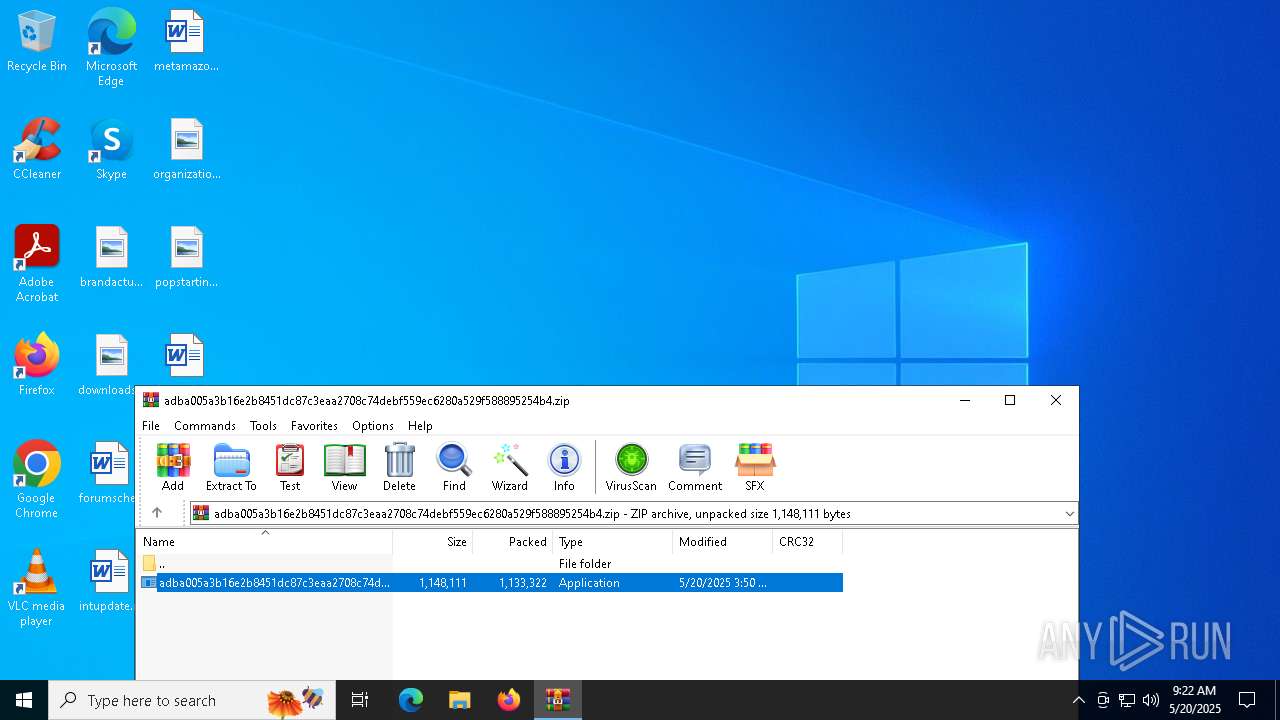
| 7176 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7344 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7384 | "C:\Users\admin\Desktop\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe" | C:\Users\admin\Desktop\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | ||||||||||||
User: admin Company: deltagne Integrity Level: MEDIUM Description: annihilations stirridsernes skrt Exit code: 2 Modules
| |||||||||||||||
| 7416 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7476 | "C:\Users\admin\Desktop\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe" | C:\Users\admin\Desktop\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | explorer.exe | ||||||||||||
User: admin Company: deltagne Integrity Level: MEDIUM Description: annihilations stirridsernes skrt Exit code: 0 Modules
| |||||||||||||||
Total events
5 666
Read events
5 616
Write events
49
Delete events
1
Modification events
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.zip | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
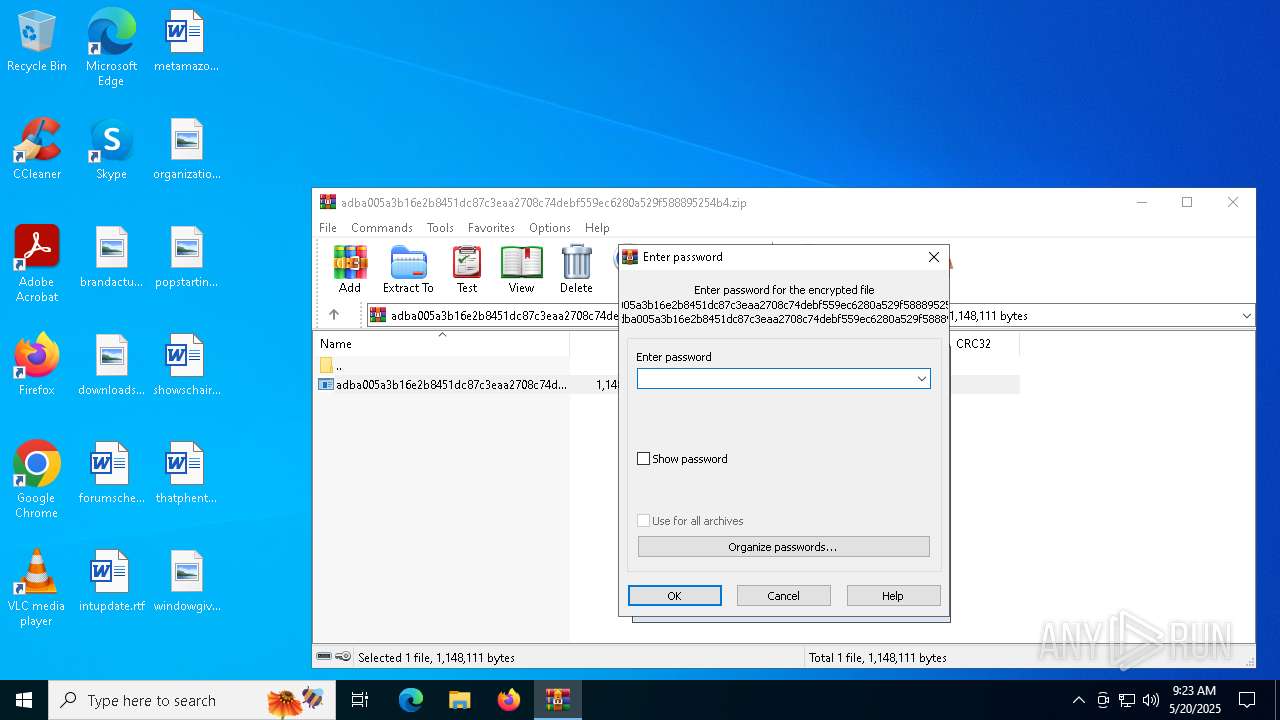
| (PID) Process: | (7176) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2108) adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | Key: | HKEY_CURRENT_USER\ureteral\neaf\Pilaw |
| Operation: | write | Name: | baltser |
Value: FF98047B | |||
Executable files
4
Suspicious files
11
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\tacmahack\Orbicularis71.fas | — | |
MD5:— | SHA256:— | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\tacmahack\doublehorned.spo | — | |
MD5:— | SHA256:— | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\tacmahack\hailse.bra | — | |
MD5:— | SHA256:— | |||
| 7176 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7176.22861\adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | executable | |
MD5:1A0E3B24A57F31C796ADFD22860E0BCF | SHA256:ADBA005A3B16E2B8451DC87C3EAA2708C74DEBF559EC6280A529F588895254B4 | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\tacmahack\Raining.txt | text | |
MD5:354BF4B937D7DFAB7EC8BEF501EBAA96 | SHA256:EE959DBCB8C8C29F58E4049BDE644B7F881E2CA22BA193A31208FA91DC2E247A | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\Gitterpunkternes.Par | binary | |
MD5:D94DCED5CA4981AAAEC31AE51F60B28E | SHA256:2E060D9B66B764B8272162713EC731661930FB92CA110028351E545629D30F1C | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\Medspillers225.hor | binary | |
MD5:74D47FFA9CA4322D5F8E53A009020A89 | SHA256:80E3E8B2D2E037F60401D0A524B0C1A68A53909818FA763BC91A7D7B57CBFDAB | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\tacmahack\Coimplicate.Tek | binary | |
MD5:493AAAAC2B29A385DB68DA8A40DBABAC | SHA256:356C4BA4E538325ECD3A1DCF75EDFCDF05D788C5F0CAE99D5A78440FA8E5A4DA | |||
| 2108 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\Roaming\Faktureringerne\tacmahack\Timingfejl.txt | text | |
MD5:894E81C971E12097000CC34CA0F48836 | SHA256:B73B724E105B24519A8E8FB499B915698F17C156A010353FA9B0741F13313948 | |||
| 5512 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:74B5C4429ED9760658689459C1511D79 | SHA256:21F982AF66A7A13C96A48C6E76BE459450DE0EA6F14CAE9695CF3BB4896642A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
42
DNS requests
25
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5512 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5512 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
5512 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
5512 | adba005a3b16e2b8451dc87c3eaa2708c74debf559ec6280a529f588895254b4.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |