| File name: | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe |
| Full analysis: | https://app.any.run/tasks/a591447e-b8ee-498e-8a8e-b238fb879e0c |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | February 14, 2026, 14:24:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 0CC23421CAF3D074E69522B6D3584563 |
| SHA1: | BFE20E613F45FEDD72005E89903129B624C46FB5 |
| SHA256: | E35CBA2515F7B88501C1244EDD9CFA73023D0EB10503CF7156D12ABFA972C862 |
| SSDEEP: | 98304:aq58lL3Y8W+JlFB1R4R5D16ugdc1RMaHIQsVmqrALReXqaTqZwmguBdNY/h7Nrqj:G41mjzlfKl7wAsAtTr5h |
MALICIOUS
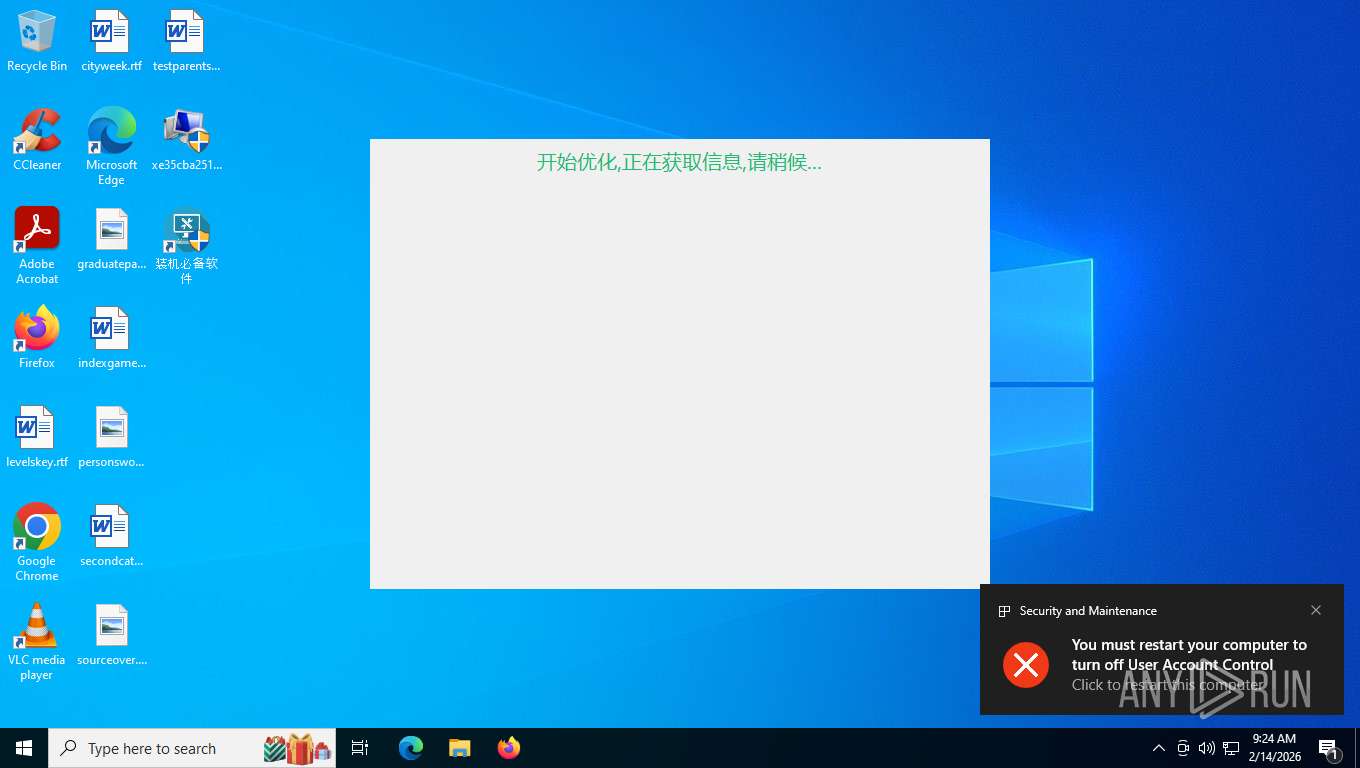
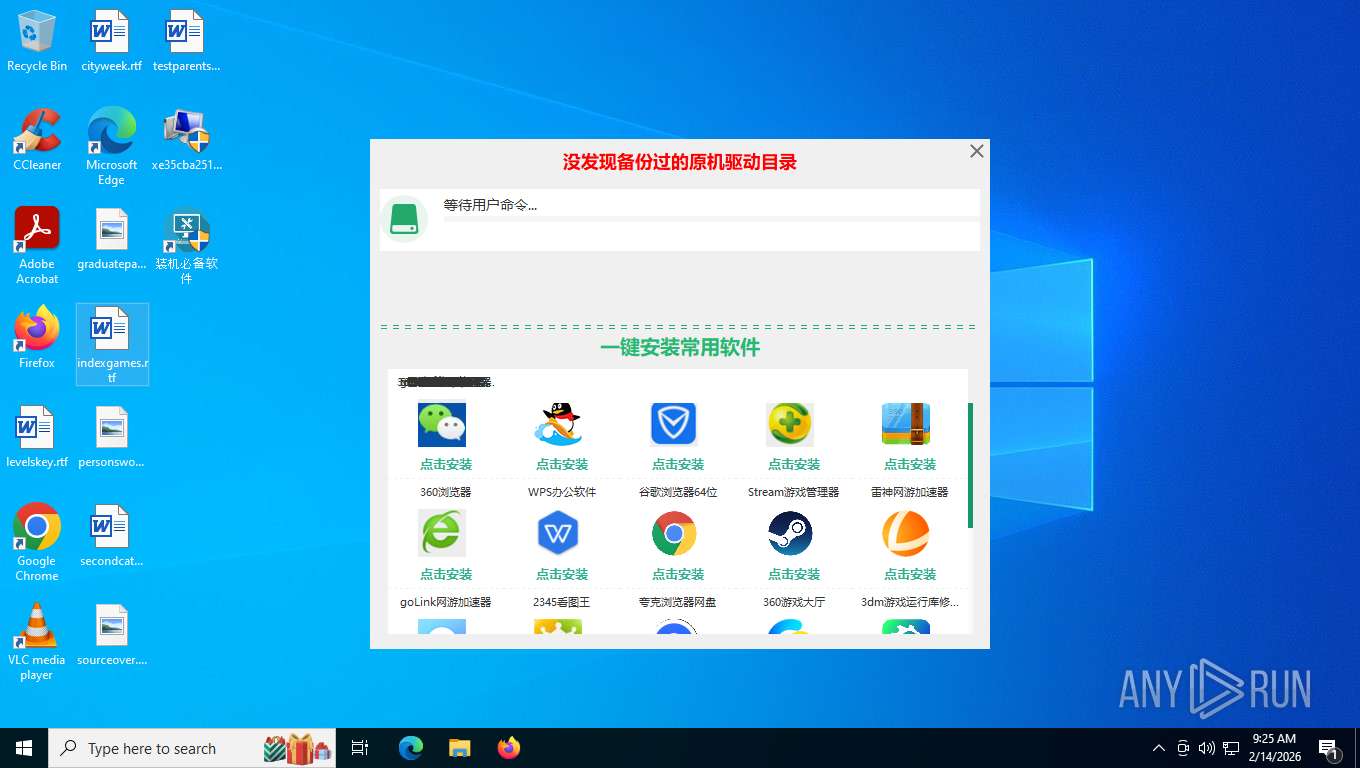
UAC/LUA settings modification
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Disables Windows Defender
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Executing a file with an untrusted certificate
- MiniThunderPlatform.exe (PID: 848)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Executable content was dropped or overwritten
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- easysoft.exe (PID: 476)
Process drops legitimate windows executable
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
The process drops C-runtime libraries
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 4540)
- cmd.exe (PID: 7668)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 8780)
- cmd.exe (PID: 4936)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 3212)
- cmd.exe (PID: 4364)
- cmd.exe (PID: 2608)
Starts CMD.EXE for commands execution
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Reads Microsoft Outlook installation path
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Reads Internet Explorer settings
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Contacting a server suspected of hosting an CnC
- MiniThunderPlatform.exe (PID: 848)
INFO
Reads the computer name
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- MiniThunderPlatform.exe (PID: 848)
- easysoft.exe (PID: 476)
Checks supported languages
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- easysoft.exe (PID: 476)
- MiniThunderPlatform.exe (PID: 848)
The sample compiled with chinese language support
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- easysoft.exe (PID: 476)
The sample compiled with english language support
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Create files in a temporary directory
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Reads the machine GUID from the registry
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- easysoft.exe (PID: 476)
- MiniThunderPlatform.exe (PID: 848)
Reads security settings of Internet Explorer
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- MiniThunderPlatform.exe (PID: 848)
Creates files in the program directory
- MiniThunderPlatform.exe (PID: 848)
- easysoft.exe (PID: 476)
Checks proxy server information
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
- MiniThunderPlatform.exe (PID: 848)
- slui.exe (PID: 1732)
Creates files or folders in the user directory
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Disables trace logs
- MiniThunderPlatform.exe (PID: 848)
Drops script file
- xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe (PID: 8732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:12:01 07:04:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3740672 |
| InitializedDataSize: | 15747072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x24d958 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.25.11.28 |
| ProductVersionNumber: | 8.25.11.28 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | 3012262930@qq.com |
| FileDescription: | 系统优化脚本 |
| FileVersion: | 8.25.11.28 |
| InternalName: | msdnloader.exe |
| LegalCopyright: | 3012262930@qq.com All rights reserved. |
| OriginalFileName: | msdnloader.exe |
| ProductName: | 系统优化脚本 |
| ProductVersion: | 8.25.11.28 |
Total processes
168
Monitored processes
30
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | netsh advfirewall firewall add rule name = "桌面调用工具" dir=in program = "C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\tools\aria2c.exe" action=allow protocol=tcp profile=public | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\easysoft.exe /oobesp | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\easysoft.exe | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | ||||||||||||
User: admin Company: 3012262930@qq.com Integrity Level: HIGH Description: 实用小软件管家 Exit code: 0 Version: 8.25.8.18 Modules
| |||||||||||||||
| 848 | "C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\MiniThunderPlatform.exe" -StartTP | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\MiniThunderPlatform.exe | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | ||||||||||||
User: admin Company: 深圳市迅雷网络技术有限公司 Integrity Level: HIGH Description: 360安全浏览器迅雷下载加速 Version: 3, 2, 1, 46 Modules
| |||||||||||||||
| 1732 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2608 | cmd /C netsh advfirewall firewall add rule name = "桌面调用工具" dir=in program = "C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\tools\aria2c.exe" action=allow | C:\Windows\SysWOW64\cmd.exe | — | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3212 | cmd /C netsh advfirewall firewall add rule name = "桌面调用工具" dir=in program = "C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\MiniThunderPlatform.exe" action=allow protocol=tcp profile=public | C:\Windows\SysWOW64\cmd.exe | — | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | netsh advfirewall firewall delete rule name = "桌面调用工具" | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
60 594
Read events
60 560
Write events
34
Delete events
0
Modification events
| (PID) Process: | (8732) xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (8732) xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (8732) xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (8732) xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | FilterAdministratorToken |
Value: 1 | |||
| (PID) Process: | (8732) xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (848) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (848) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (848) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (848) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (848) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
17
Suspicious files
9
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\atl71.dll | executable | |
MD5:79CB6457C81ADA9EB7F2087CE799AAA7 | SHA256:A68E1297FAE2BCF854B47FFA444F490353028DE1FA2CA713B6CF6CC5AA22B88A | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\locallist.ini | binary | |
MD5:C6AD5FFF8A0FA0D89CC6545113F44DC5 | SHA256:9C4C63EC20FD7271B16099EDD7DA4D5BE5ED3A6BCB78C9DF28FFD9773BF0EDDD | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\zlib1.dll | executable | |
MD5:89F6488524EAA3E5A66C5F34F3B92405 | SHA256:BD29D2B1F930E4B660ADF71606D1B9634188B7160A704A8D140CADAFB46E1E56 | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\id.dat | text | |
MD5:9F9B4BC7ADAFE3333ED2A292044449B4 | SHA256:C6233DE5D227E53209C6FDA197C77B23F32351DB234C1C1069C3ACB26686967F | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\msvcr71.dll | executable | |
MD5:CA2F560921B7B8BE1CF555A5A18D54C3 | SHA256:C4D4339DF314A27FF75A38967B7569D9962337B8D4CD4B0DB3ABA5FF72B2BFBB | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\image.zip | compressed | |
MD5:3BBB6DE5D8FFE5F21CB60C9B430C6D47 | SHA256:9C5D5046C31BBD5D548BC5424D2DC2E1F568D9F327ECD63C14F246892A5CA142 | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\XLBugReport.exe | executable | |
MD5:67C767470D0893C4A2E46BE84C9AFCBB | SHA256:64F8D68CC1CFC5B9CC182DF3BECF704AF93D0F1CC93EE59DBF682C75B6D4FFC0 | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\minizip.dll | executable | |
MD5:7FD4F79ACA0B09FD3A60841A47CA96E7 | SHA256:FC10C877E2BCFAB35758446A72A8DB704D8E8455470D65A6DE5492C10C8D6786 | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\XLBugHandler.dll | executable | |
MD5:92154E720998ACB6FA0F7BAD63309470 | SHA256:1845DF41DA539BCA264F59365BF7453B686B9098CC94CD0E2B9A20C74A561096 | |||
| 8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | C:\Users\admin\AppData\Local\Temp\45BUn24Yfv\download\MiniThunderPlatform.exe | executable | |
MD5:5761B0B1F4BA56EF156A8848D1C214CF | SHA256:F1A7A250356418E387D2827DD440B76326586621B4FDD837F8B327D16919827F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
169
TCP/UDP connections
107
DNS requests
47
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
876 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.128:443 | https://login.live.com/RST2.srf | unknown | text | 11.1 Kb | unknown |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.17:443 | https://login.live.com/RST2.srf | unknown | binary | 10.3 Kb | unknown |
— | — | POST | 200 | 40.126.31.128:443 | https://login.live.com/RST2.srf | unknown | text | 10.3 Kb | unknown |
8732 | xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | GET | 200 | 122.188.45.182:80 | http://jsy.newitboy.com/wllinfo/oemloader/oemjsy.dat | unknown | — | — | unknown |
— | — | POST | 200 | 20.190.160.17:443 | https://login.live.com/RST2.srf | unknown | text | 10.3 Kb | unknown |
— | — | POST | 204 | 2.16.106.207:443 | https://www.bing.com/threshold/xls.aspx?t=5&dl=1&wsbc=1 | unknown | — | — | unknown |
356 | svchost.exe | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | unknown | text | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
876 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
jsy.newitboy.com |
| malicious |
www.bing.com |
| whitelisted |
hgyyds.newitboy.com |
| unknown |
hub5pnc.hz.sandai.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
848 | MiniThunderPlatform.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] RAT:Win32/Generic outbound frame |
848 | MiniThunderPlatform.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Common RAT related JA3 hash observed |
848 | MiniThunderPlatform.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Common RAT related JA3 hash observed |
Process | Message |
|---|---|
xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | SeSecurityPrivilege1
|
xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | SeDebugPrivilege1
|
xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | SeRestorePrivilege1
|
xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | Sat Feb 14 09:24:35 2026
|
xe35cba2515f7b88501c1244edd9cfa73023d0eb10503cf7156d12abfa972c862.exe | SeTakeOwnershipPrivilege1
|