| File name: | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506 |
| Full analysis: | https://app.any.run/tasks/e2581d27-41ac-405b-a4b6-581db286a4f2 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | March 09, 2021, 10:50:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D0A55DC67D9242C250F810DB5064DDBF |
| SHA1: | 2DC6E85B6FC4E1094A6BA1692723145A705132F4 |
| SHA256: | E339981B82EFC66E4F2A7B420ADA708C21A0A0A036DF459438FE5D215500028B |
| SSDEEP: | 1536:ZAUnCawT81GxSzu/LVSNKuS38xBxu0I3uxEu3cL3K81S/Y+I38Gm8nK9KuxIgR0k:Cqn1GxSzu/LVSNKuS38xBxu0I3uxEu3Z |
MALICIOUS
Known privilege escalation attack
- DllHost.exe (PID: 1880)
UAC/LUA settings modification
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
Steals credentials from Web Browsers
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
Connects to CnC server
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
LOKIBOT was detected
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
Actions looks like stealing of personal data
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
SUSPICIOUS
Checks supported languages
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
- cmd.exe (PID: 3080)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
- powershell.exe (PID: 2072)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2536)
- cmd.exe (PID: 3920)
Creates files in the Windows directory
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
Executed via COM
- DllHost.exe (PID: 1880)
Executes PowerShell scripts
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
Reads the computer name
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
- powershell.exe (PID: 2072)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
Starts application with an unusual extension
- DllHost.exe (PID: 1880)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
Reads the date of Windows installation
- powershell.exe (PID: 2072)
Starts CMD.EXE for commands execution
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
Creates files in the user directory
- powershell.exe (PID: 2072)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
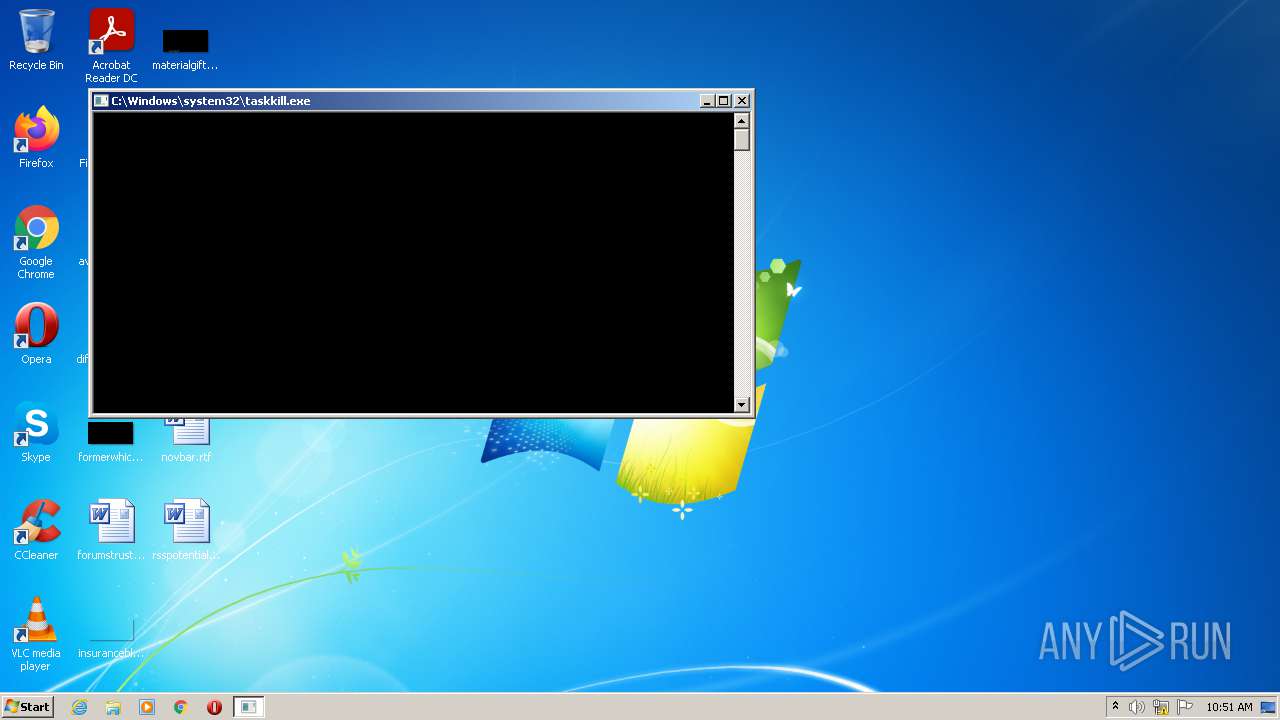
Uses TASKKILL.EXE to kill process
- DllHost.exe (PID: 1880)
Application launched itself
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
Loads DLL from Mozilla Firefox
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
Creates files in the program directory
- DllHost.exe (PID: 1880)
Executable content was dropped or overwritten
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
Drops a file with too old compile date
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2380)
Reads Environment values
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
INFO
Checks supported languages
- cmstp.exe (PID: 1120)
- DllHost.exe (PID: 1880)
- taskkill.exe (PID: 2552)
- timeout.exe (PID: 3036)
- timeout.exe (PID: 3748)
Reads settings of System Certificates
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
Reads the computer name
- cmstp.exe (PID: 1120)
- DllHost.exe (PID: 1880)
- taskkill.exe (PID: 2552)
Checks Windows Trust Settings
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 928)
- SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (43.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (21.7) |
| .exe | | | Win32 Executable (generic) (14.8) |
| .exe | | | Win16/32 Executable Delphi generic (6.8) |
| .exe | | | Generic Win/DOS Executable (6.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2049:12:16 08:54:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 76800 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14b5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.5.2 |
| ProductVersionNumber: | 5.2.6.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | IPHostEntry |
| CompanyName: | XmlSchemaProviderAttribute |
| FileDescription: | EventLog |
| FileVersion: | 1.6.5.2 |
| InternalName: | PaintEventArgs.exe |
| LegalCopyright: | 2019 SetPredefined |
| LegalTrademarks: | StringBuffer |
| OriginalFileName: | PaintEventArgs.exe |
| ProductName: | PaintEventArgs |
| ProductVersion: | 5.2.6.1 |
| AssemblyVersion: | 5.2.6.1 |
| Guid: | eaf5202c-78e2-4fad-9fb5-691bf8010eb7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Nov-1913 01:26:38 |
| Detected languages: |
|
| Comments: | IPHostEntry |
| CompanyName: | XmlSchemaProviderAttribute |
| FileDescription: | EventLog |
| FileVersion: | 1.6.5.2 |
| InternalName: | PaintEventArgs.exe |
| LegalCopyright: | 2019 SetPredefined |
| LegalTrademarks: | StringBuffer |
| OriginalFilename: | PaintEventArgs.exe |
| ProductName: | PaintEventArgs |
| ProductVersion: | 5.2.6.1 |
| Assembly Version: | 5.2.6.1 |
| Guid: | eaf5202c-78e2-4fad-9fb5-691bf8010eb7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Nov-1913 01:26:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00012B64 | 0x00012C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73538 |
.rsrc | 0x00016000 | 0x00000458 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.96675 |
.reloc | 0x00018000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.4616 | 1024 | Latin 1 / Western European | English - United States | RT_VERSION |
Imports
mscoree.dll |
Total processes
52
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | DllHost.exe | ||||||||||||
User: admin Company: XmlSchemaProviderAttribute Integrity Level: HIGH Description: EventLog Exit code: 1 Version: 1.6.5.2 Modules
| |||||||||||||||
| 1120 | "c:\windows\system32\cmstp.exe" /au C:\windows\temp\sseta53t.inf | c:\windows\system32\cmstp.exe | — | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 1 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1880 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | ||||||||||||
User: admin Company: XmlSchemaProviderAttribute Integrity Level: HIGH Description: EventLog Exit code: 0 Version: 1.6.5.2 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | — | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | |||||||||||
User: admin Company: XmlSchemaProviderAttribute Integrity Level: MEDIUM Description: EventLog Exit code: 0 Version: 1.6.5.2 Modules
| |||||||||||||||
| 2552 | taskkill /IM cmstp.exe /F | C:\Windows\system32\taskkill.exe | — | DllHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr" /S | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Explorer.EXE | ||||||||||||
User: admin Company: XmlSchemaProviderAttribute Integrity Level: MEDIUM Description: EventLog Exit code: 1 Version: 1.6.5.2 Modules
| |||||||||||||||
| 3036 | timeout 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Windows\System32\cmd.exe" /c timeout 1 | C:\Windows\System32\cmd.exe | — | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
10 187
Read events
10 065
Write events
122
Delete events
0
Modification events
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\168\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SecuriteInfo_RASMANCS |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SecuriteInfo_RASMANCS |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SecuriteInfo_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SecuriteInfo_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2688) SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\SecuriteInfo_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
6
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\windows\temp\sseta53t.inf | ini | |
MD5:— | SHA256:— | |||
| 928 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\Local\Temp\Cab5665.tmp | compressed | |
MD5:— | SHA256:— | |||
| 928 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PB2Q9ENFEQFGHLAQ12A1.temp | binary | |
MD5:— | SHA256:— | |||
| 928 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 1880 | DllHost.exe | C:\Windows\INF\setupapi.app.log | ini | |
MD5:— | SHA256:— | |||
| 2688 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\Local\XmlSchemaProviderAttribut\SecuriteInfo.com.Trojan.W_Url_elhzih0cvearjpjgrqp55i5s0i1f0e3s\1.823.463.491\cyjjspex.newcfg | xml | |
MD5:— | SHA256:— | |||
| 928 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\Local\Temp\Tar5666.tmp | cat | |
MD5:— | SHA256:— | |||
| 2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
4
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2688 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | GET | 200 | 172.67.174.240:80 | http://liverpoolofcfanclub.com/liverpool-fc-news/features/steven-gerrard-liverpool-future-dalglish--goal-923C431637A0113E5F0A2FAD0D1A4D74.html | US | html | 1.18 Mb | malicious |
2688 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | GET | 200 | 172.67.174.240:80 | http://liverpoolofcfanclub.com/liverpool-fc-news/features/steven-gerrard-liverpool-future-dalglish--goal-F0C57E7F0992E9869D56B6A454993147.html | US | html | 918 Kb | malicious |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | POST | 404 | 185.208.180.121:80 | http://becharnise.ir/fb9/fre.php | IR | text | 15 b | malicious |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | POST | 404 | 185.208.180.121:80 | http://becharnise.ir/fb9/fre.php | IR | binary | 23 b | malicious |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | POST | 404 | 185.208.180.121:80 | http://becharnise.ir/fb9/fre.php | IR | text | 15 b | malicious |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | POST | 404 | 185.208.180.121:80 | http://becharnise.ir/fb9/fre.php | IR | binary | 23 b | malicious |
928 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | GET | 200 | 8.248.135.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e34c97fc553345c5 | US | compressed | 57.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | 172.67.174.240:80 | liverpoolofcfanclub.com | — | US | suspicious |
2688 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
928 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | 8.248.135.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | 185.208.180.121:80 | becharnise.ir | Tahlilgran Karbin Ertebat Parsa Co. Ltd. | IR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
liverpoolofcfanclub.com |
| malicious |
becharnise.ir |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | MALWARE [PTsecurity] Loki/Pony Bot Artifact Check-in |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | MALWARE [PTsecurity] Loki/Pony Bot Artifact Check-in |
2380 | SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | rgCgwRdeQDxDkCUqtbVWin
|
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | nBipEZhmBICcmSOHAxpGOVlwgV |
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | saPQrsLFTOCbCVJxYvgpilDXN |
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | sGjuESlsDGSLWzlhrmLHvWsLqjlOdRzWf |
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | ABLgHhyGWMjJIaKulKYiblj |
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | AUqVHVRmRFoJWpOlgY
|
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | HOL OLOL OLOLO
|
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | HOL OLOL OLOLO
|
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | HOL OLOL OLOLO
|
SecuriteInfo.com.Trojan.Win32.Save.a.25010.10506.scr | HOL OLOL OLOLO
|