| File name: | e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314 |
| Full analysis: | https://app.any.run/tasks/53210796-690e-4b22-99d8-9850bce60bab |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 15, 2025, 19:15:39 |
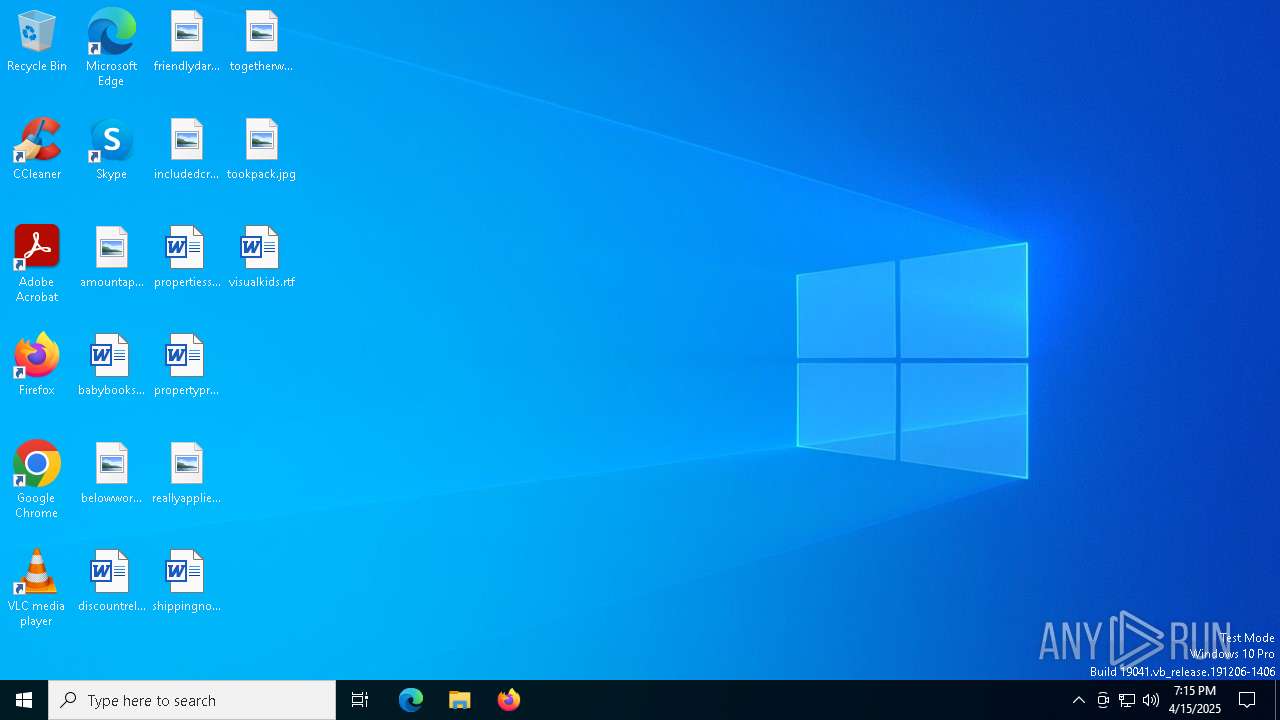
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 9C11C79449C9CA18FD07A4D08268E77D |
| SHA1: | 40A027CA3E7319DDB37D0548B24484458FB67402 |
| SHA256: | E2FD729DFE277C8D99FED9DBCEA85F3B97F8DF87855FCE053B68AF26627EB314 |
| SSDEEP: | 1536:IMWtYwbwgYm4QbzHHI4OUVbOOBLPw7RqBnbPXSmD0WJgvHdmjf+:IMWtYwbwgYm9HIGcqBnbPyWJg0m |
MALICIOUS
ASYNCRAT has been detected (MUTEX)
- e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe (PID: 7400)
ASYNCRAT has been detected (YARA)
- e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe (PID: 7400)
SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe (PID: 7400)
Checks supported languages
- e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe (PID: 7400)
Reads the machine GUID from the registry
- e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe (PID: 7400)
Checks proxy server information
- slui.exe (PID: 7640)
Reads the software policy settings
- slui.exe (PID: 7640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7400) e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe
C2 (1)a36e-78-175-182-33.ngrok-free.app
Ports (1)8080
Version0.5.7B
BotnetDefault
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPScq8/BwsXbQznkKm4pXTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjUwNDEzMDkyMjIxWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAOL/e/howoO4XI0hKpOtgaifCTQJOnFUWCv+z92Sm+jL7HFzP74fuv7d8rxI0L+vfqXX+jZ++w/A...
Server_SignaturekjB774ELGVA+AB4NMvIQ2qiD5tice3rmrK4Hk6SLE7m05RJLpoucYcdE1qHwWsp9Shk4ugbueW4ON+plrzUTyP/NKGG7Fb+XJFOpdHl2rnS4yMM/ZJunXEzHoViA0cm3iT+Vt9IDfyCwZLeohXMpqYAzt7rfF46jZ8K3bfTFJFFVd3Yr2NpVh9x4xkmw5Nv+QYJhCt3klw8tQD0iabJEAQF+ITuRZgnjHVu+ANonmSmMOygUeOEKOWk4/5KUmsyovlI+lS76CGvqJqZBG76iDPc0ol4BNgfY4sodeDcpKkH5...
Keys
AES4a03e9718bcb1149d13bef796bf24445e84cdcf730e68e352bdc7d4904b4f0c7
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:25 01:25:26+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 43008 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc72e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Stub.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Stub.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
120
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7400 | "C:\Users\admin\Desktop\e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe" | C:\Users\admin\Desktop\e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
AsyncRat(PID) Process(7400) e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe C2 (1)a36e-78-175-182-33.ngrok-free.app Ports (1)8080 Version0.5.7B BotnetDefault Options AutoRunfalse MutexAsyncMutex_6SI8OkPnk InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIIE8jCCAtqgAwIBAgIQAPScq8/BwsXbQznkKm4pXTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjUwNDEzMDkyMjIxWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAOL/e/howoO4XI0hKpOtgaifCTQJOnFUWCv+z92Sm+jL7HFzP74fuv7d8rxI0L+vfqXX+jZ++w/A... Server_SignaturekjB774ELGVA+AB4NMvIQ2qiD5tice3rmrK4Hk6SLE7m05RJLpoucYcdE1qHwWsp9Shk4ugbueW4ON+plrzUTyP/NKGG7Fb+XJFOpdHl2rnS4yMM/ZJunXEzHoViA0cm3iT+Vt9IDfyCwZLeohXMpqYAzt7rfF46jZ8K3bfTFJFFVd3Yr2NpVh9x4xkmw5Nv+QYJhCt3klw8tQD0iabJEAQF+ITuRZgnjHVu+ANonmSmMOygUeOEKOWk4/5KUmsyovlI+lS76CGvqJqZBG76iDPc0ol4BNgfY4sodeDcpKkH5... Keys AES4a03e9718bcb1149d13bef796bf24445e84cdcf730e68e352bdc7d4904b4f0c7 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 7640 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 788
Read events
3 788
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
27
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7400 | e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe | 3.124.142.205:8080 | a36e-78-175-182-33.ngrok-free.app | AMAZON-02 | DE | malicious |
6808 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7640 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7400 | e2fd729dfe277c8d99fed9dbcea85f3b97f8df87855fce053b68af26627eb314.exe | 18.158.249.75:8080 | a36e-78-175-182-33.ngrok-free.app | AMAZON-02 | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
a36e-78-175-182-33.ngrok-free.app |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Observed DNS Query to *.ngrok Domain (ngrok-free .app) |
2196 | svchost.exe | Misc activity | ET INFO Observed DNS Query to *.ngrok Domain (ngrok-free .app) |