| File name: | now1_output44F3940.exe |
| Full analysis: | https://app.any.run/tasks/a0652f35-29b8-436d-843b-c1ce1a008645 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
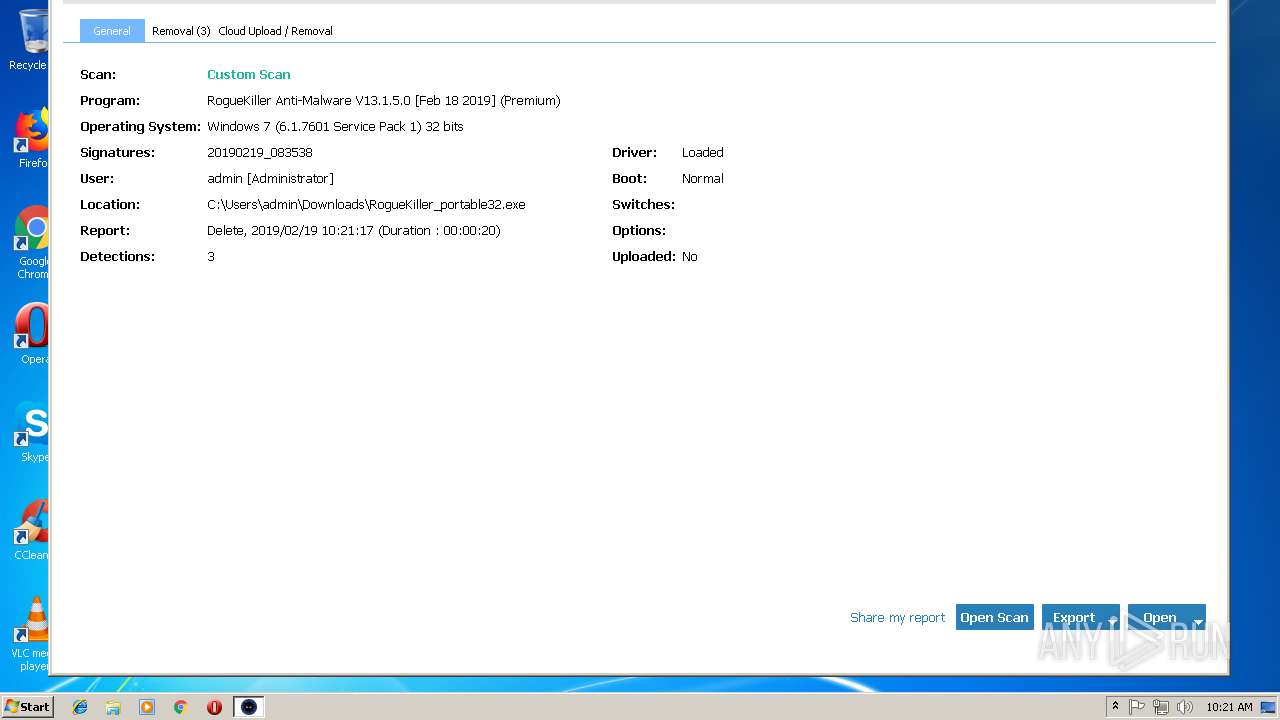
| Analysis date: | February 19, 2019, 10:17:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 44969C084396C1DB5E921F676553B497 |
| SHA1: | B7B3305213127131B4758B2DCBEF77D3F4908DDB |
| SHA256: | E2B184B9B1C3FEDBA26A1AF8D3004A5758A5AE68C4990397BEEC5C88D851DAFC |
| SSDEEP: | 6144:2/qePsJKObtaQI4JxmZ1GumeeeeeeeeeeEYeeeeeeeeeeh9J9gQIKFEXXXXXXXX0:2/qePsJKzQI4J0Z1KUGNDV8Muo |
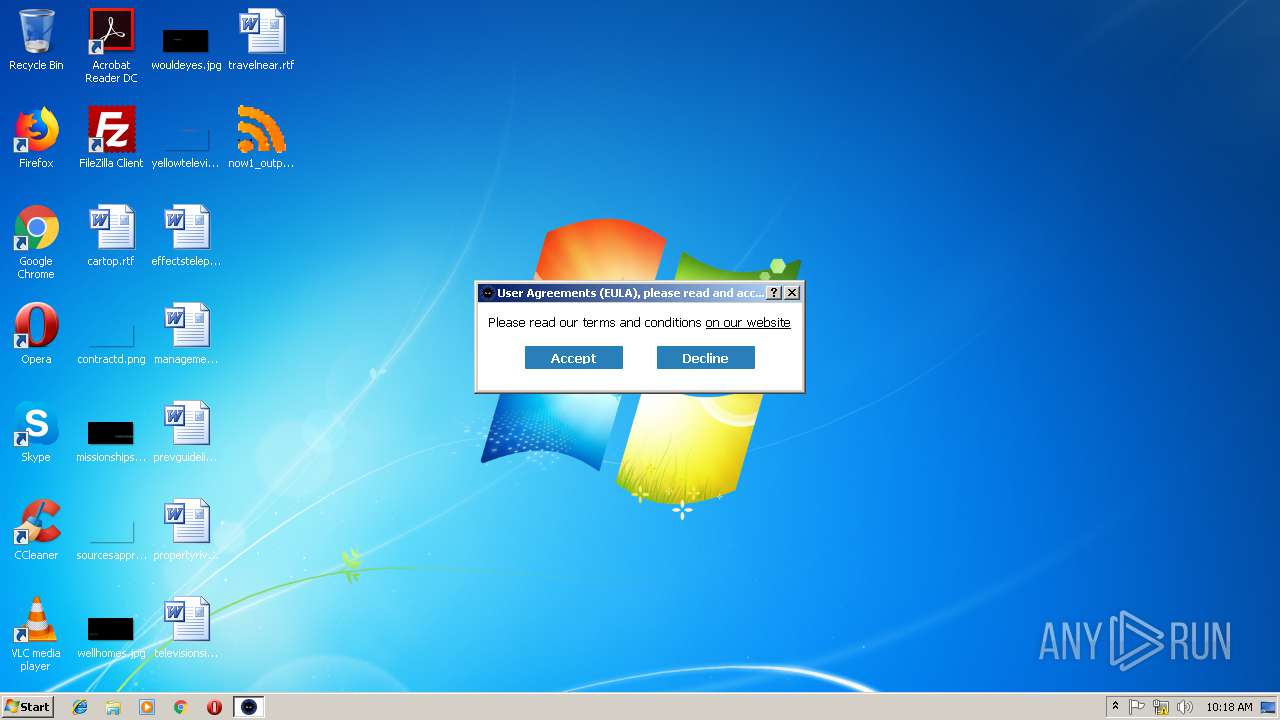
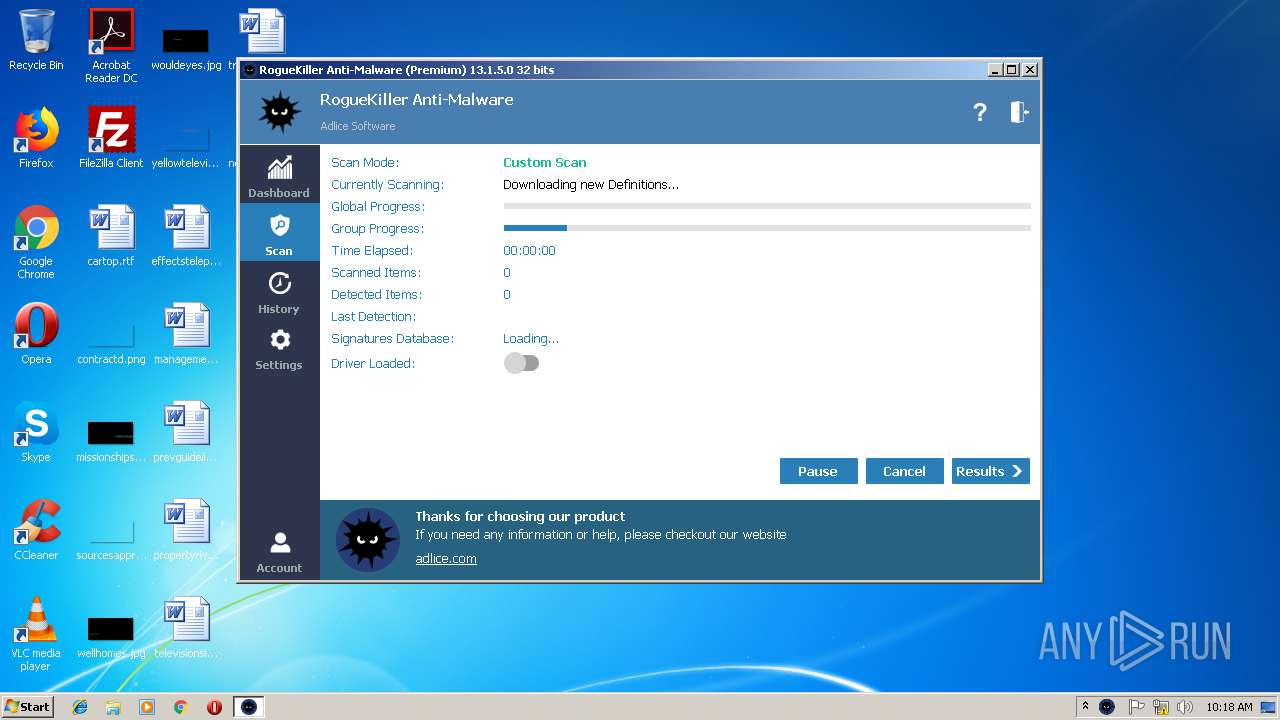
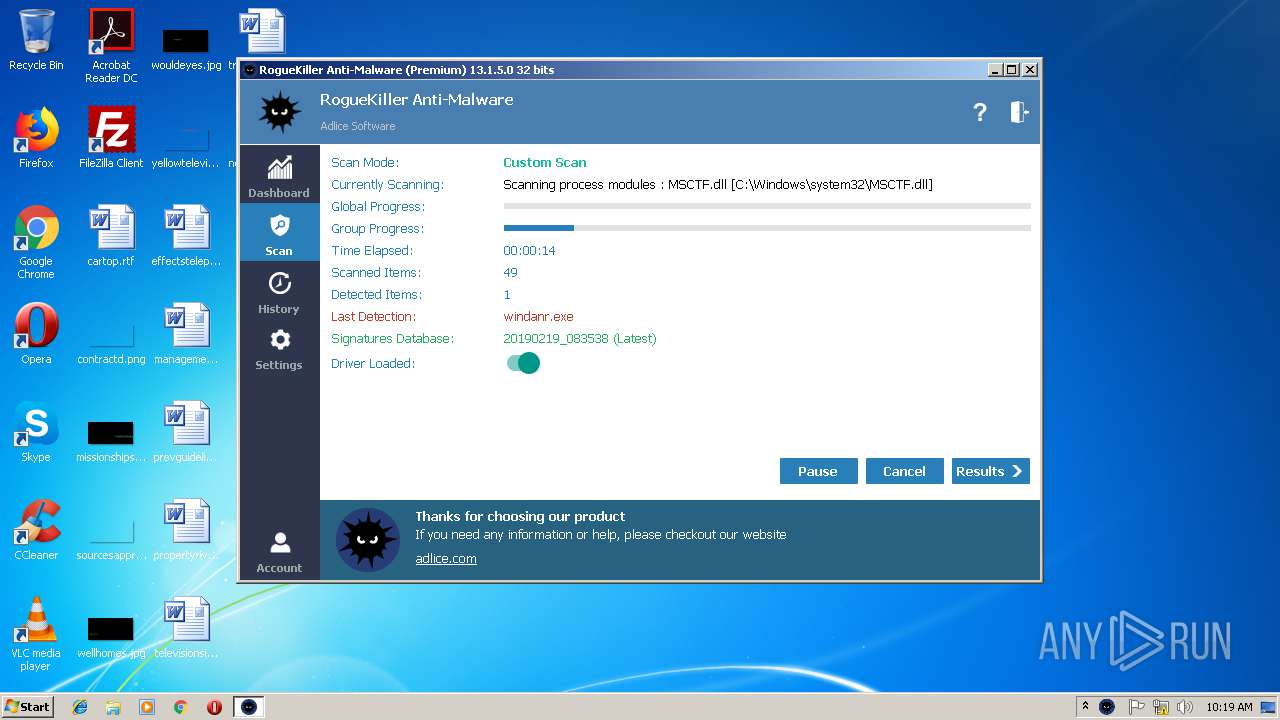
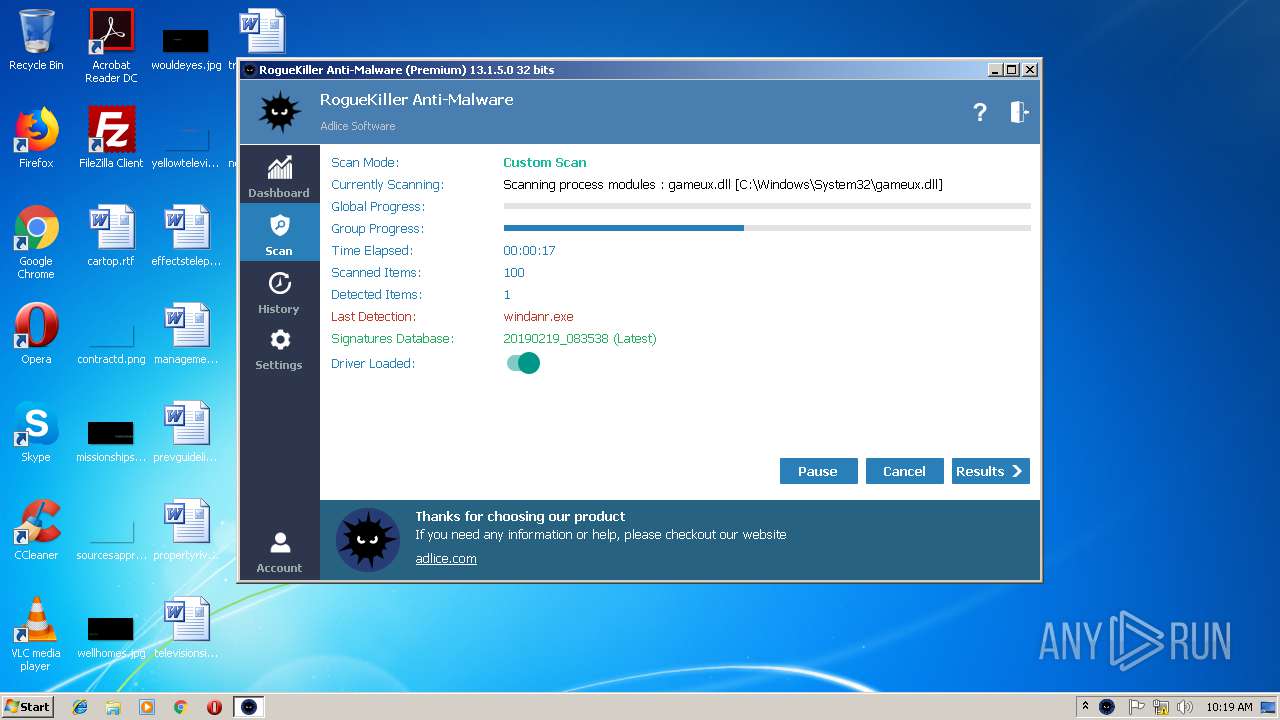
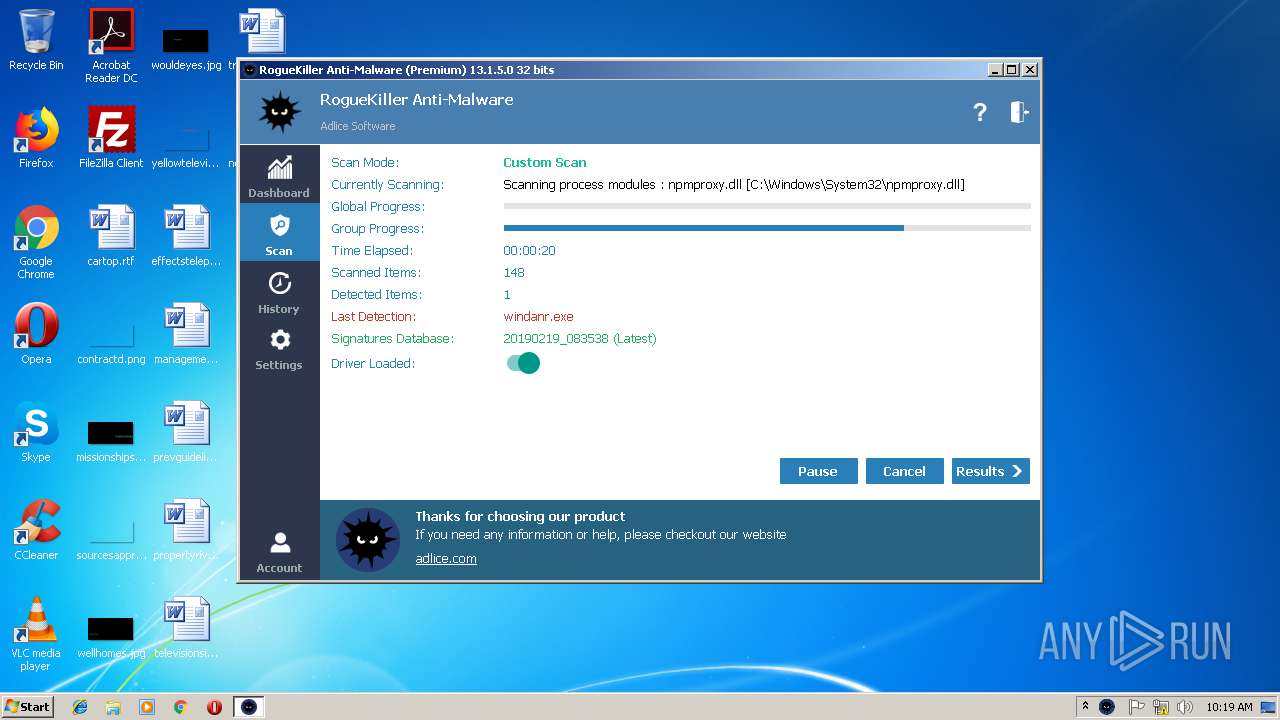
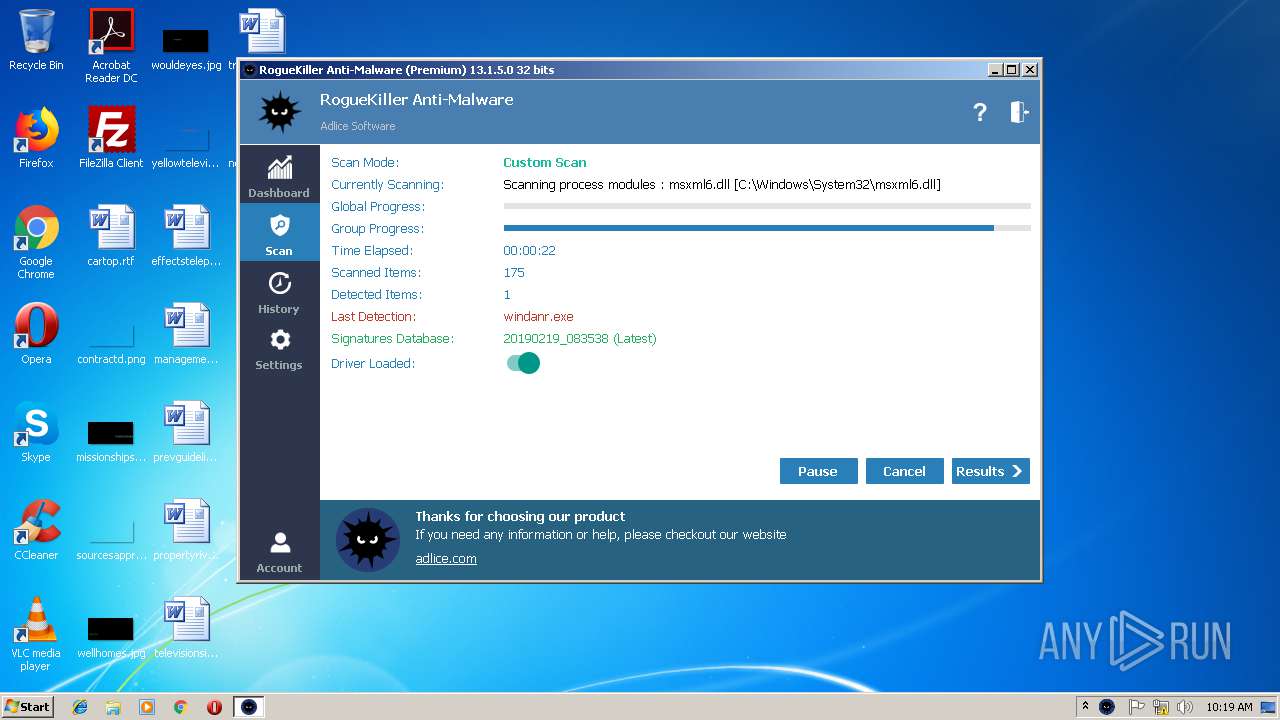
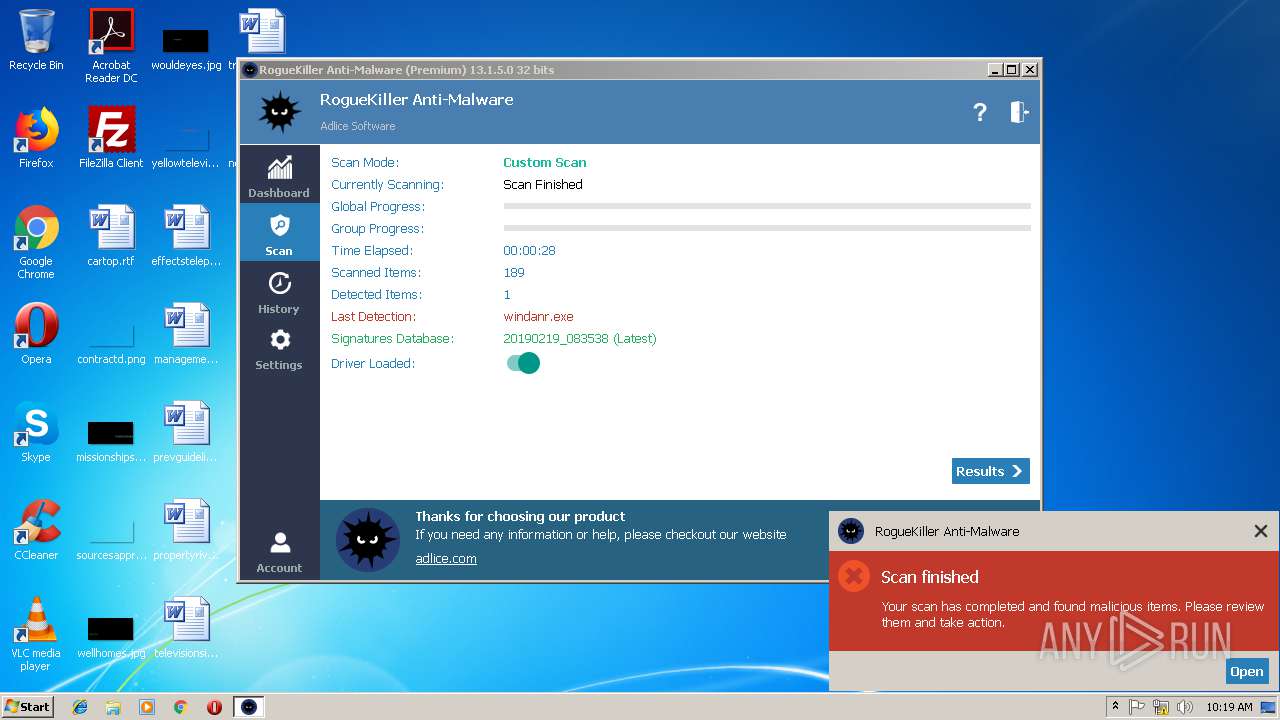
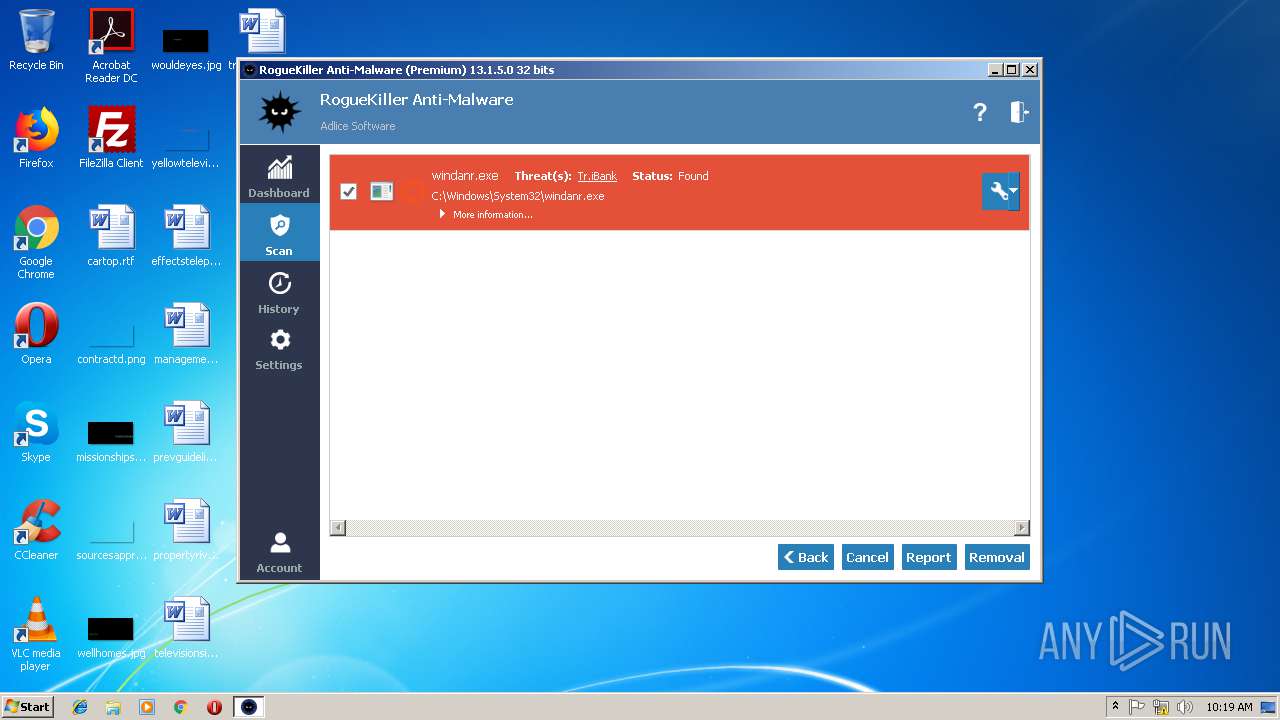
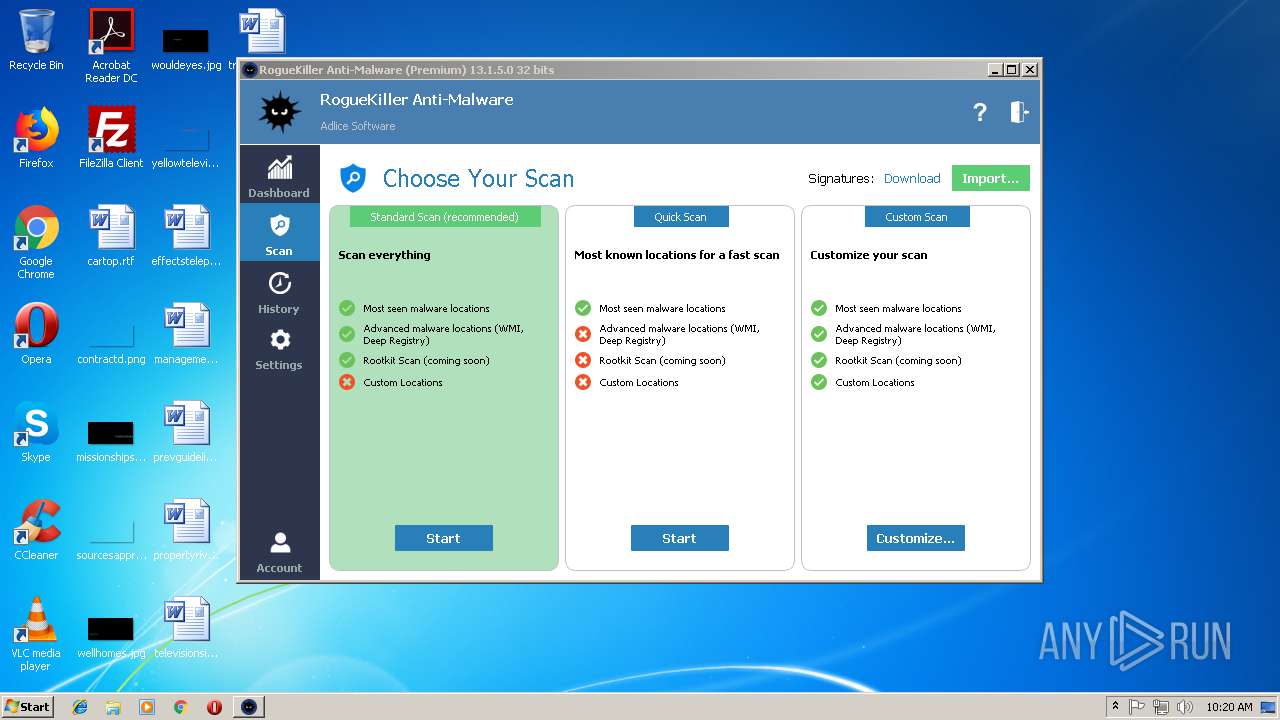
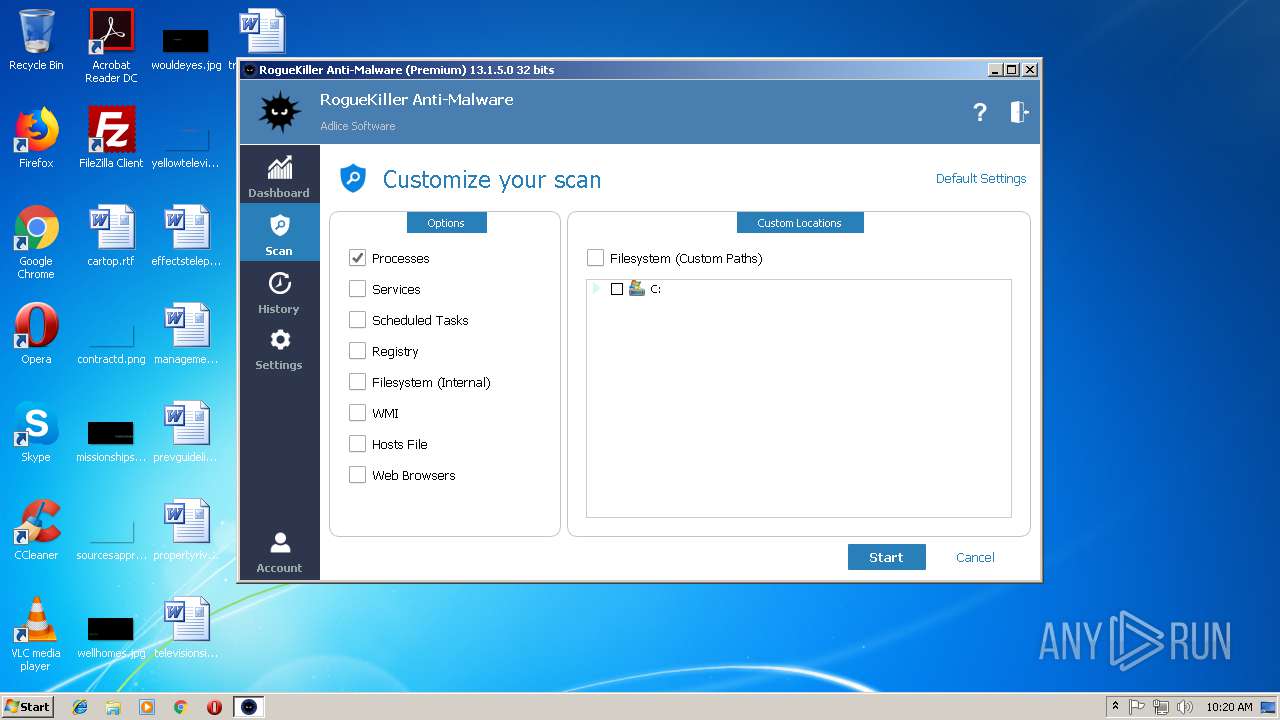
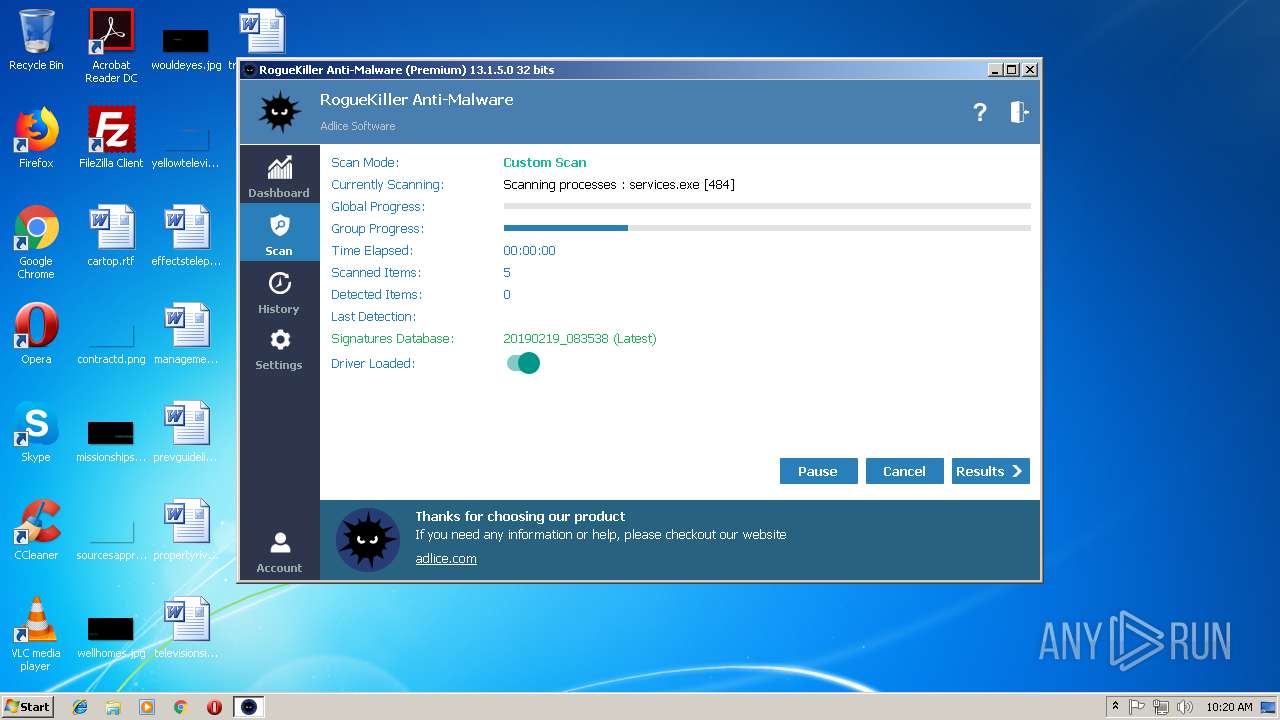
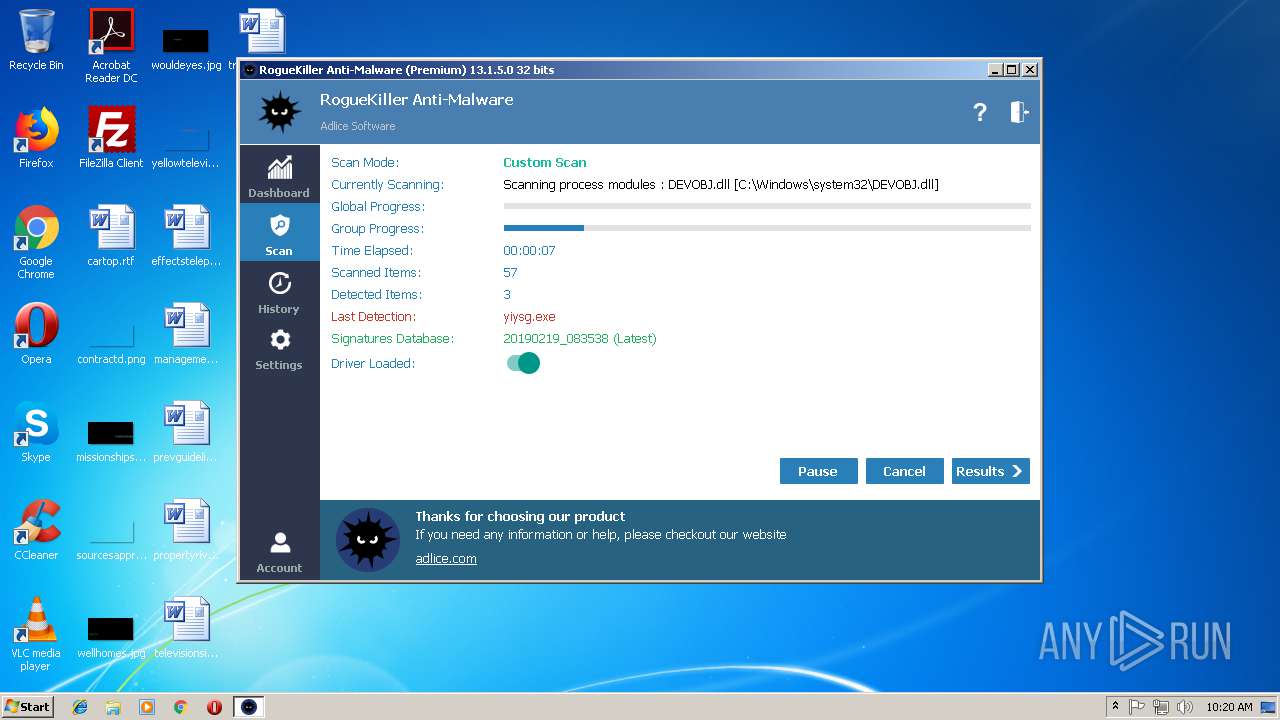
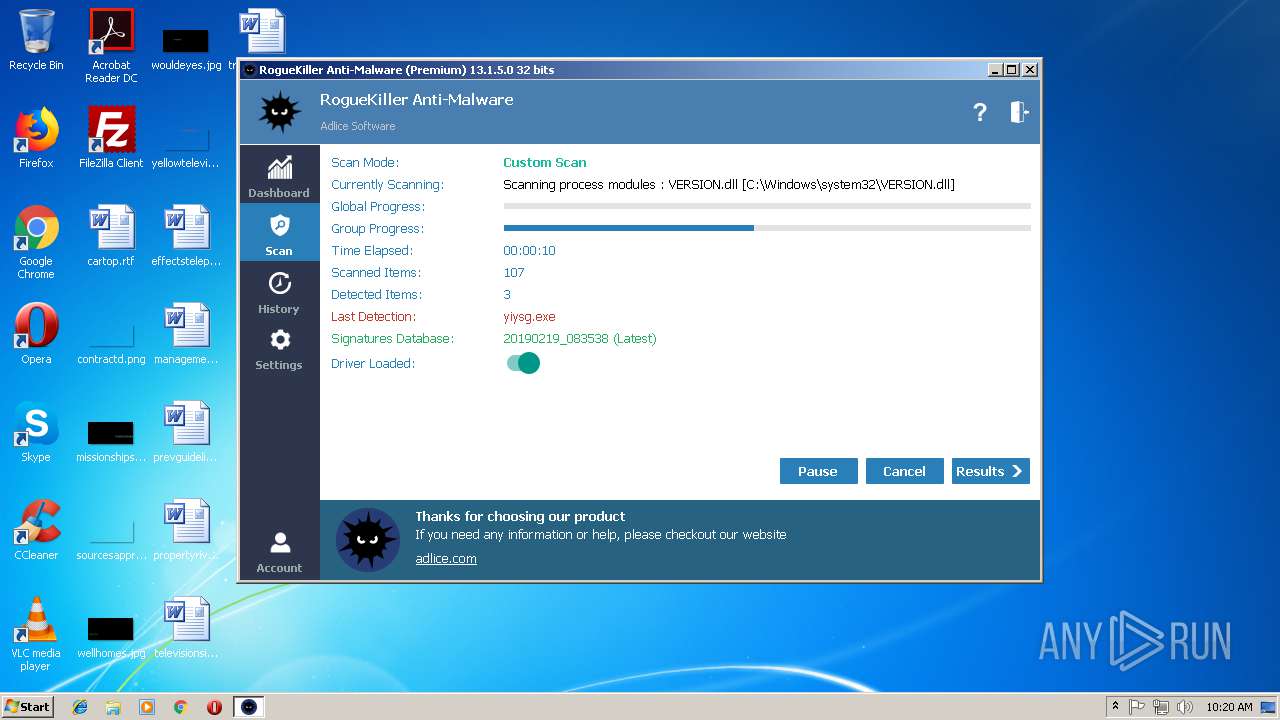
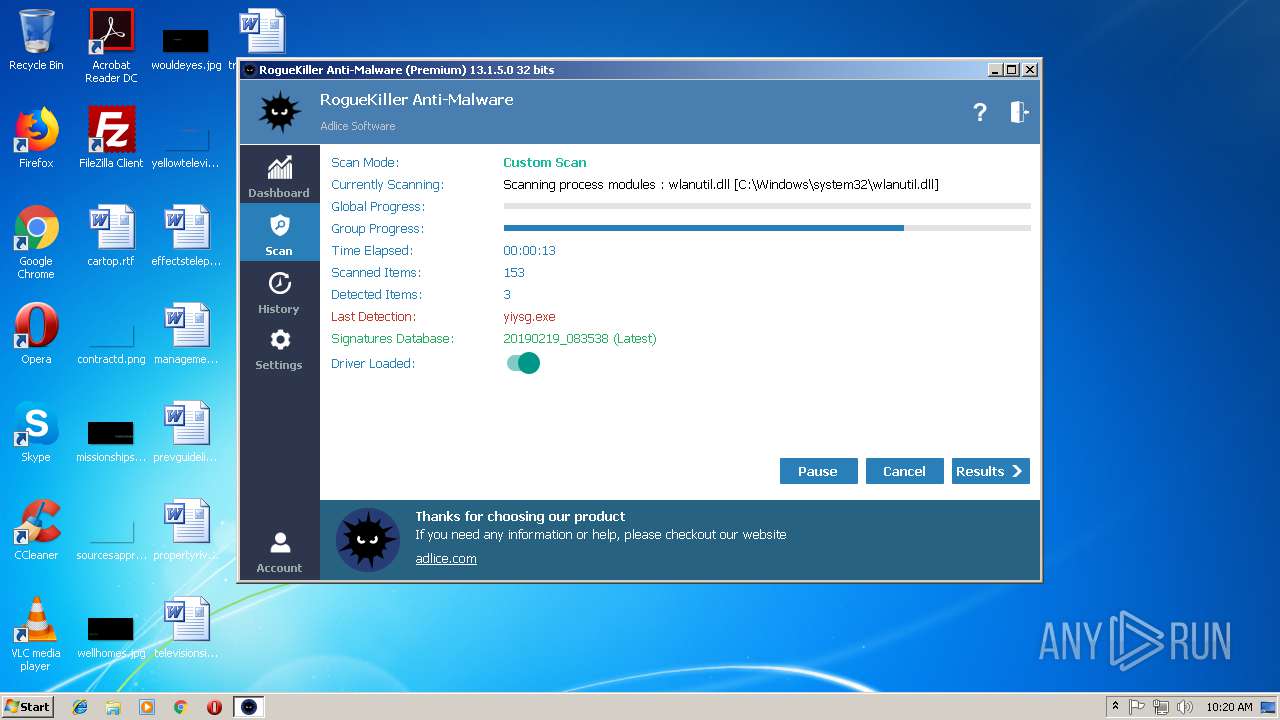
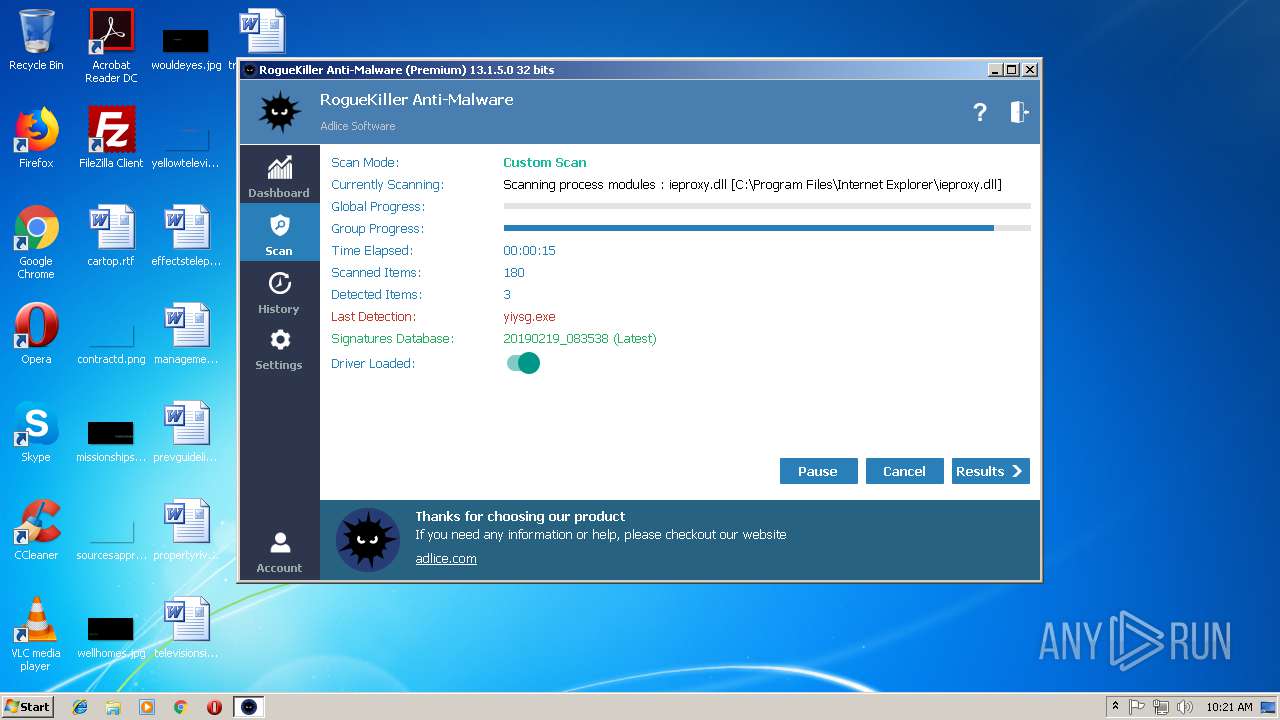
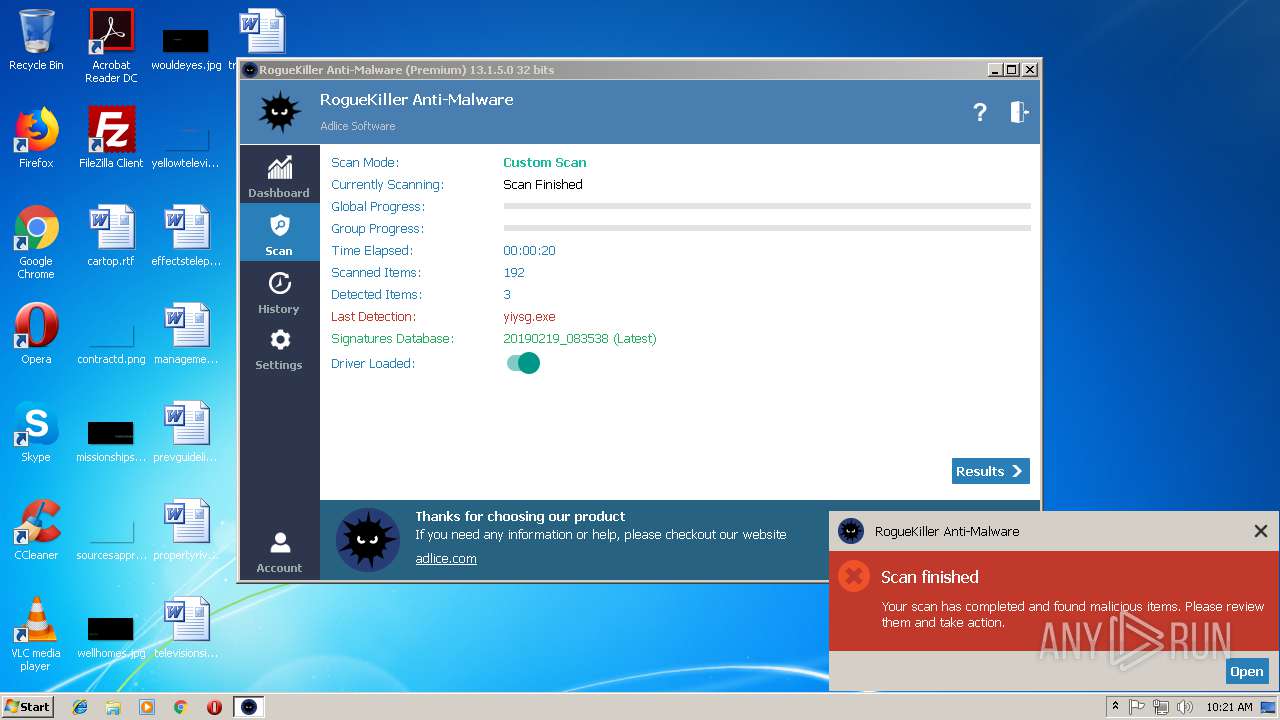
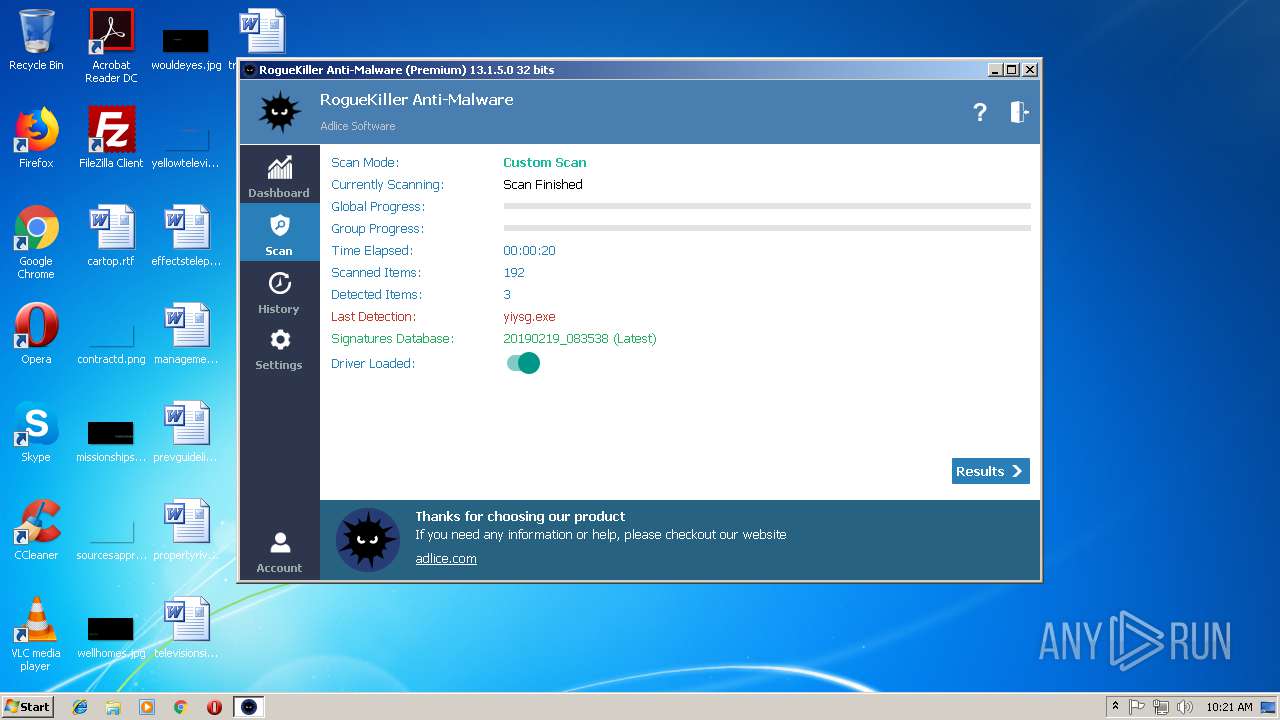
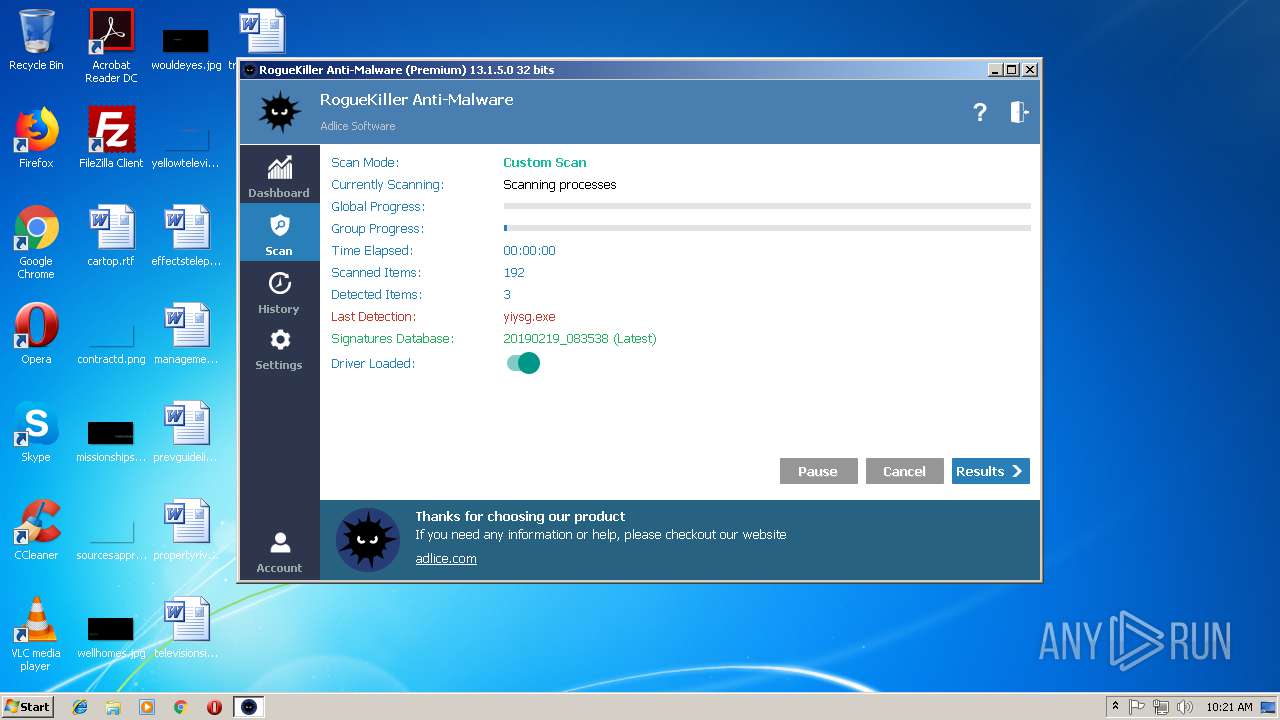
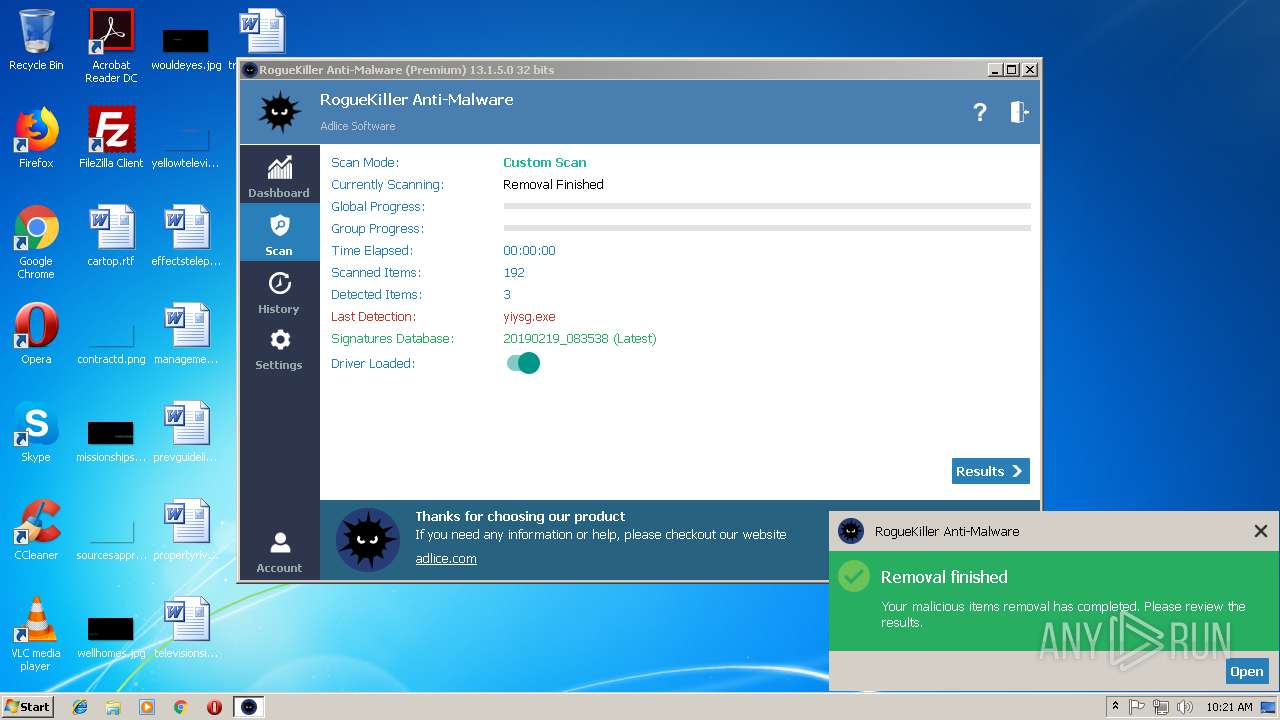
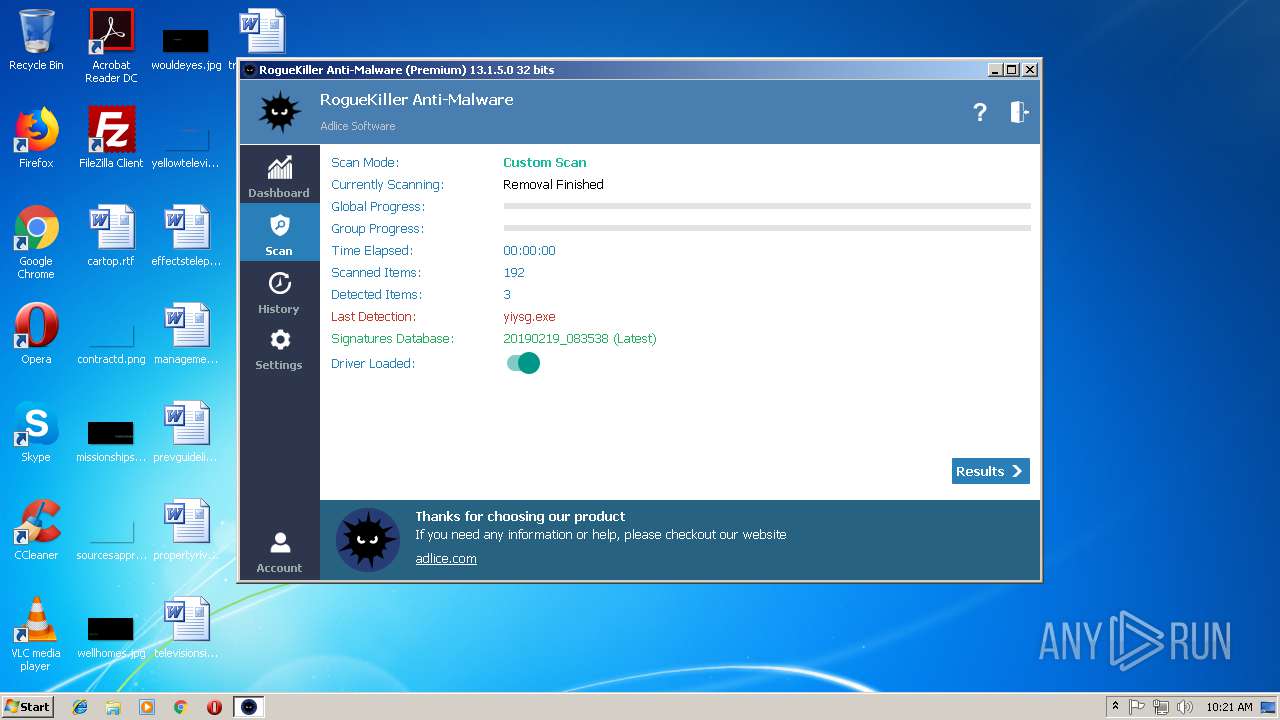
MALICIOUS
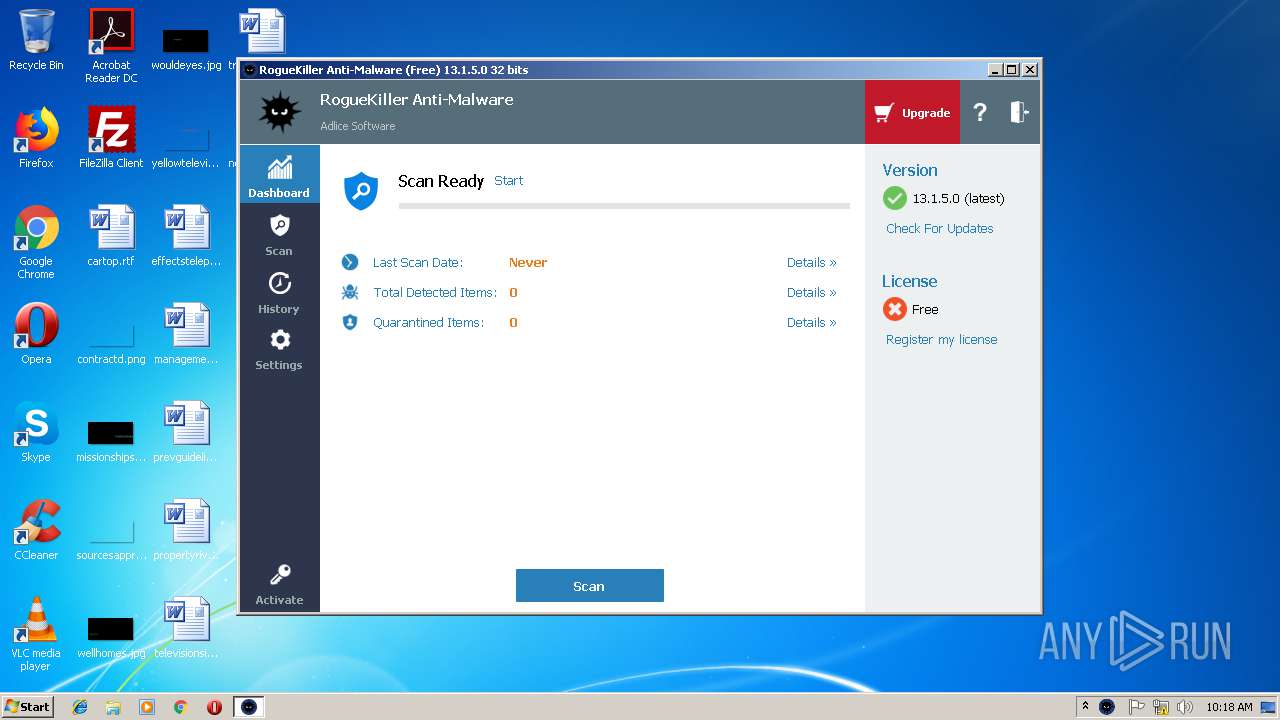
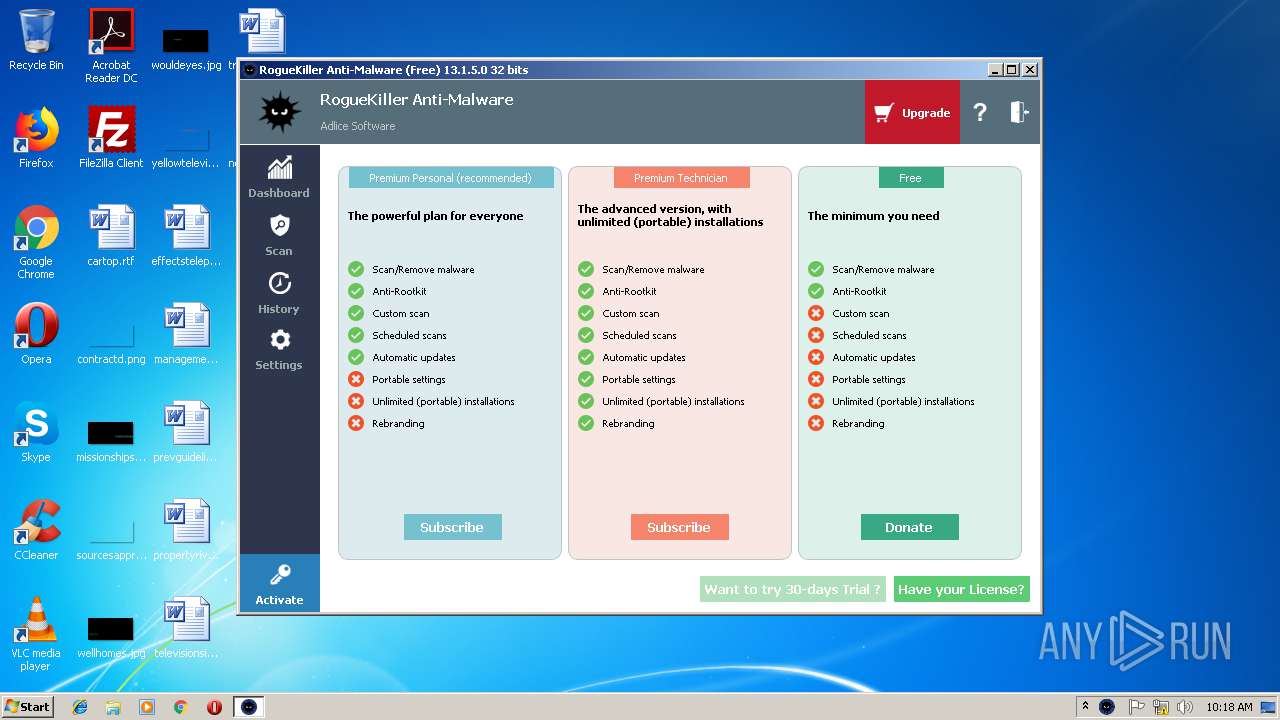
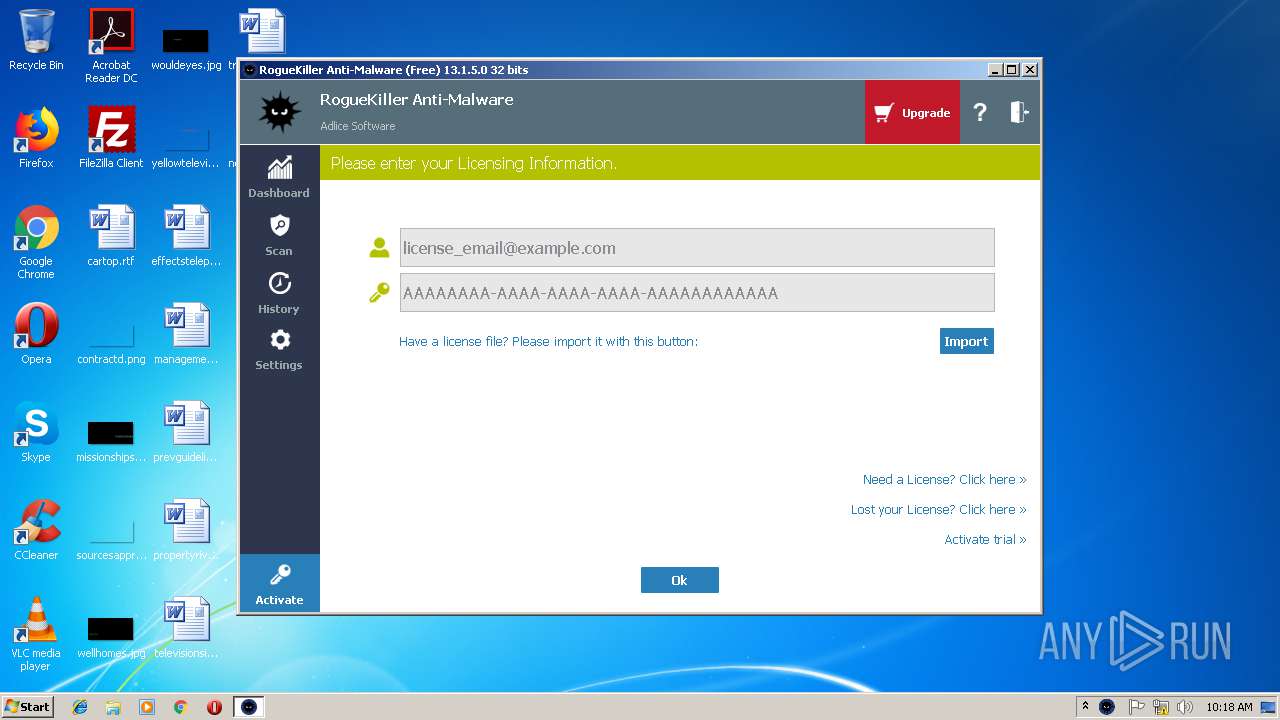
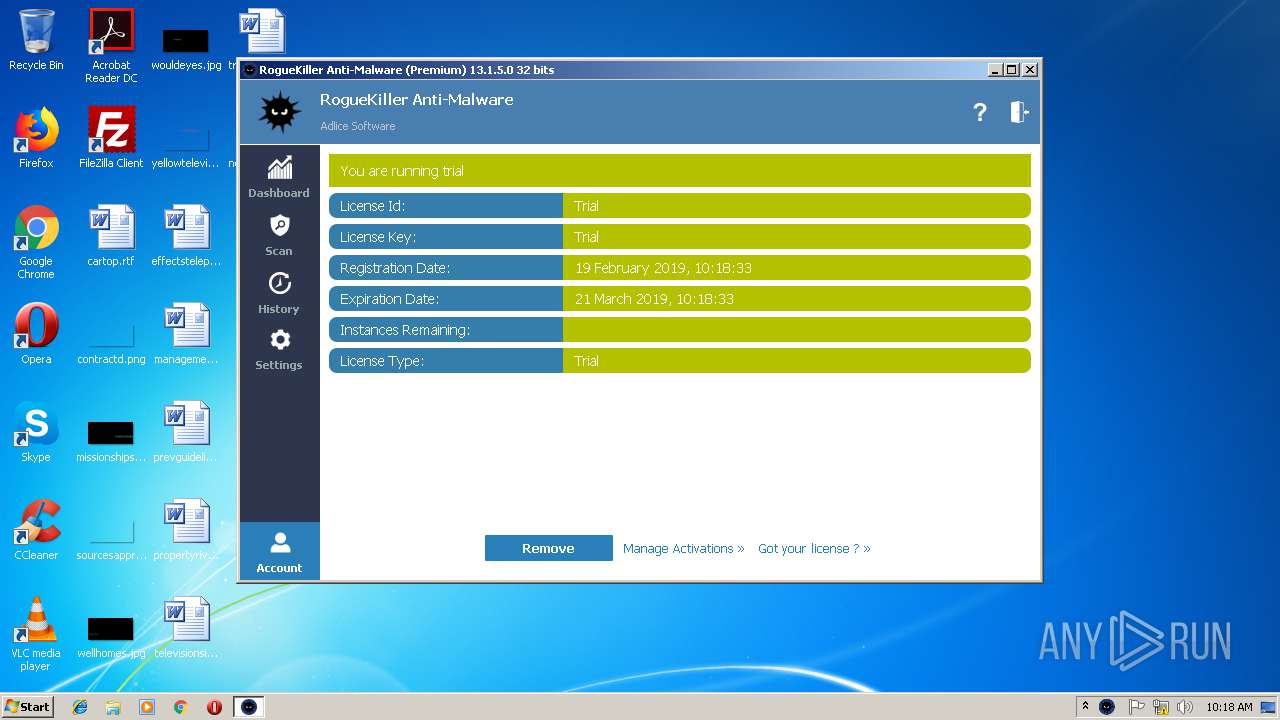
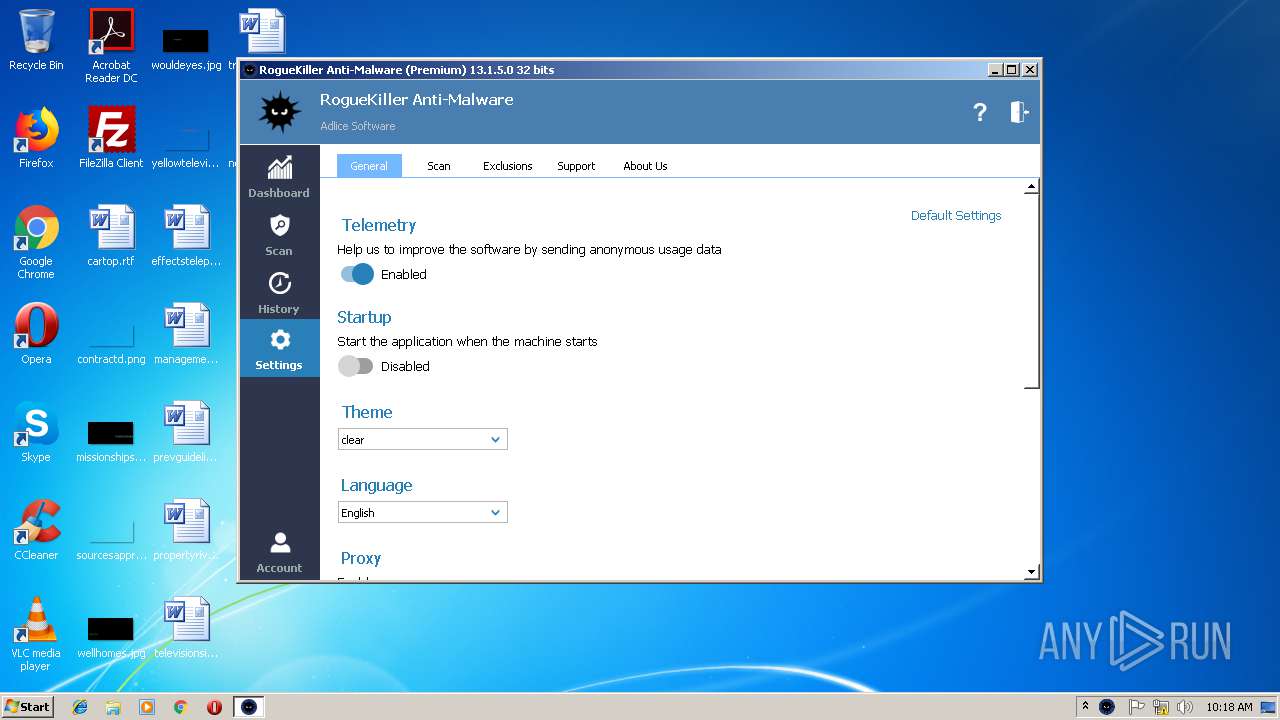
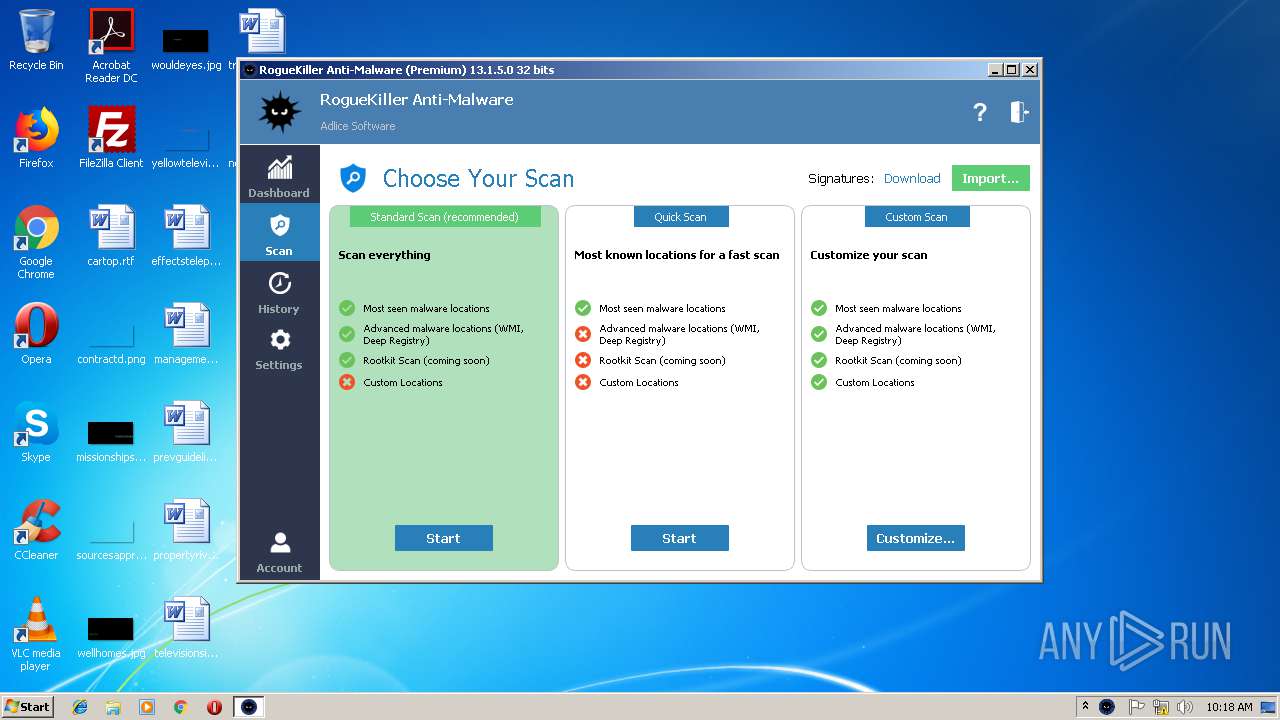
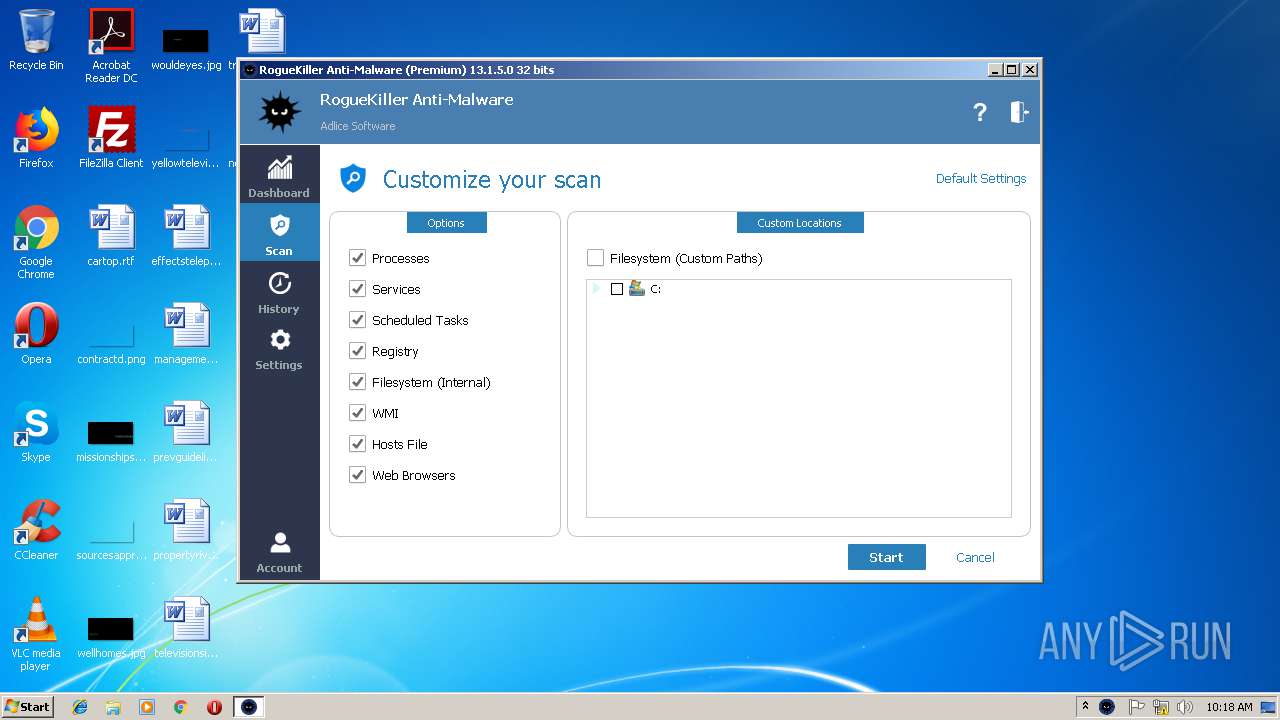
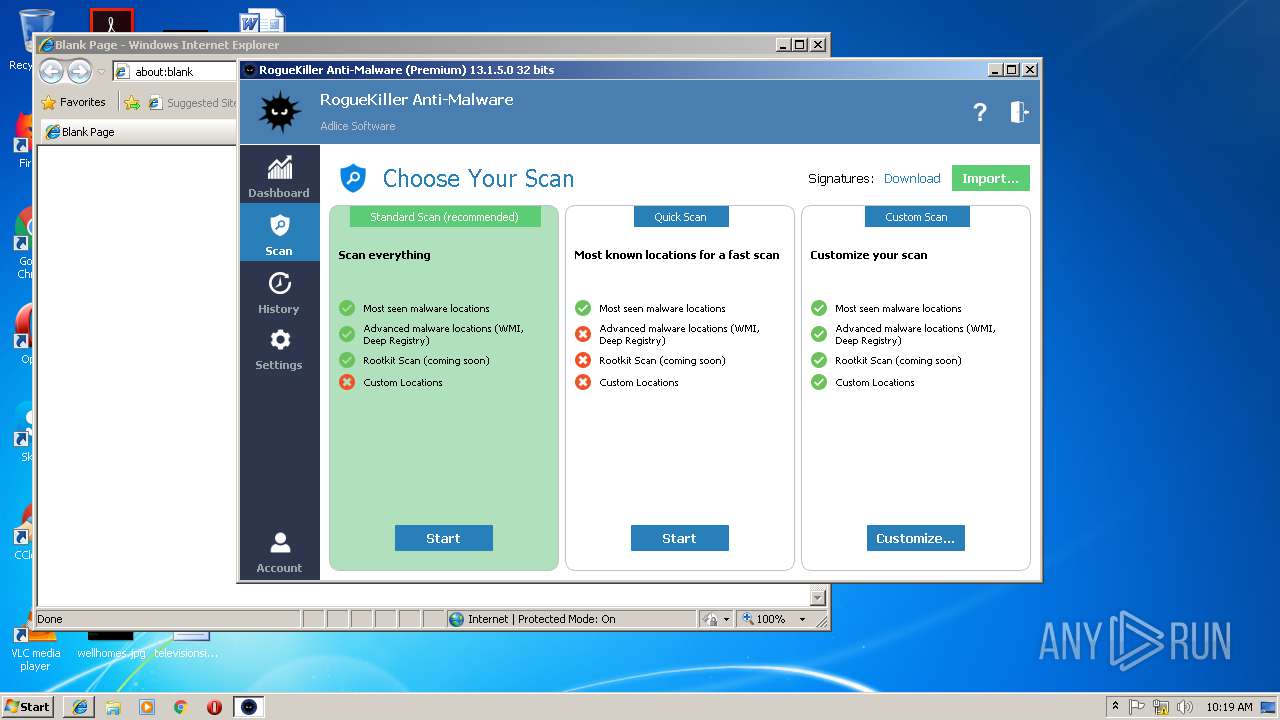
Application was dropped or rewritten from another process
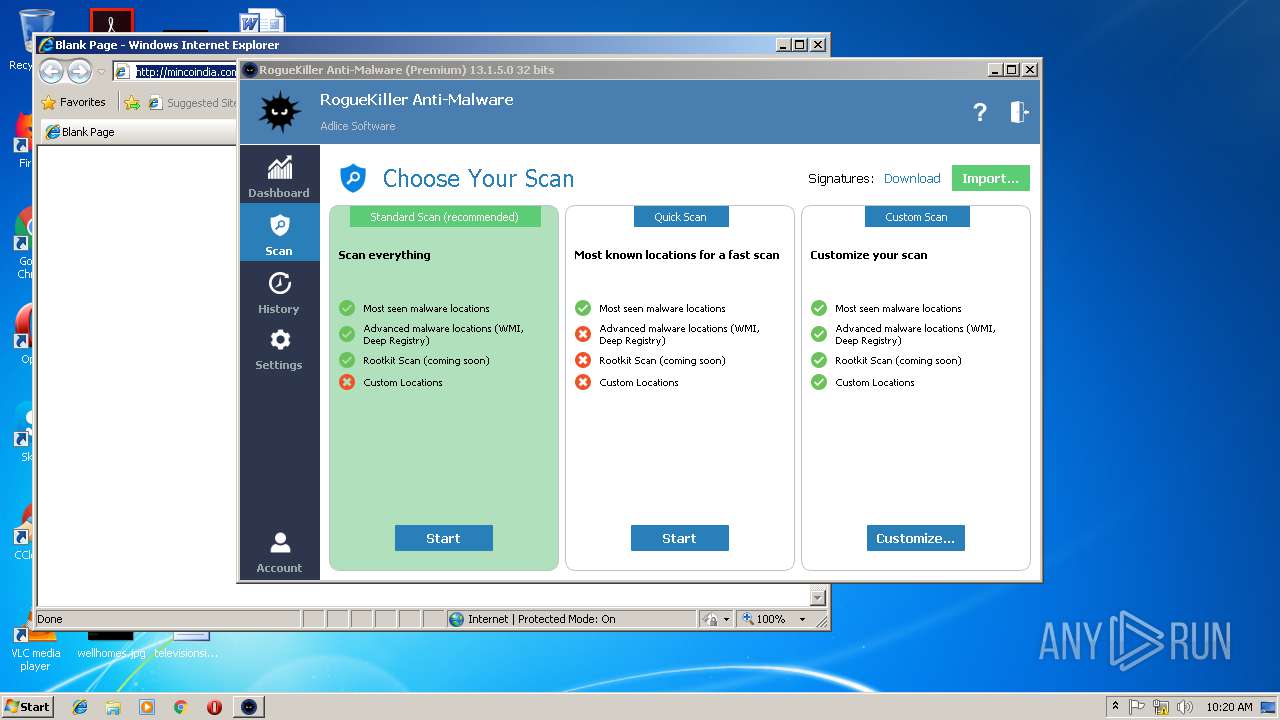
- RogueKiller_portable32.exe (PID: 2400)
- RogueKiller_portable32.exe (PID: 1816)
- fast[1].exe (PID: 1624)
- shd[1].exe (PID: 2660)
- images.exe (PID: 1912)
- 185979[1].exe (PID: 2812)
- images.exe (PID: 3656)
- yiysg.exe (PID: 3204)
- yiysg.exe (PID: 3084)
- shd[1].exe (PID: 3204)
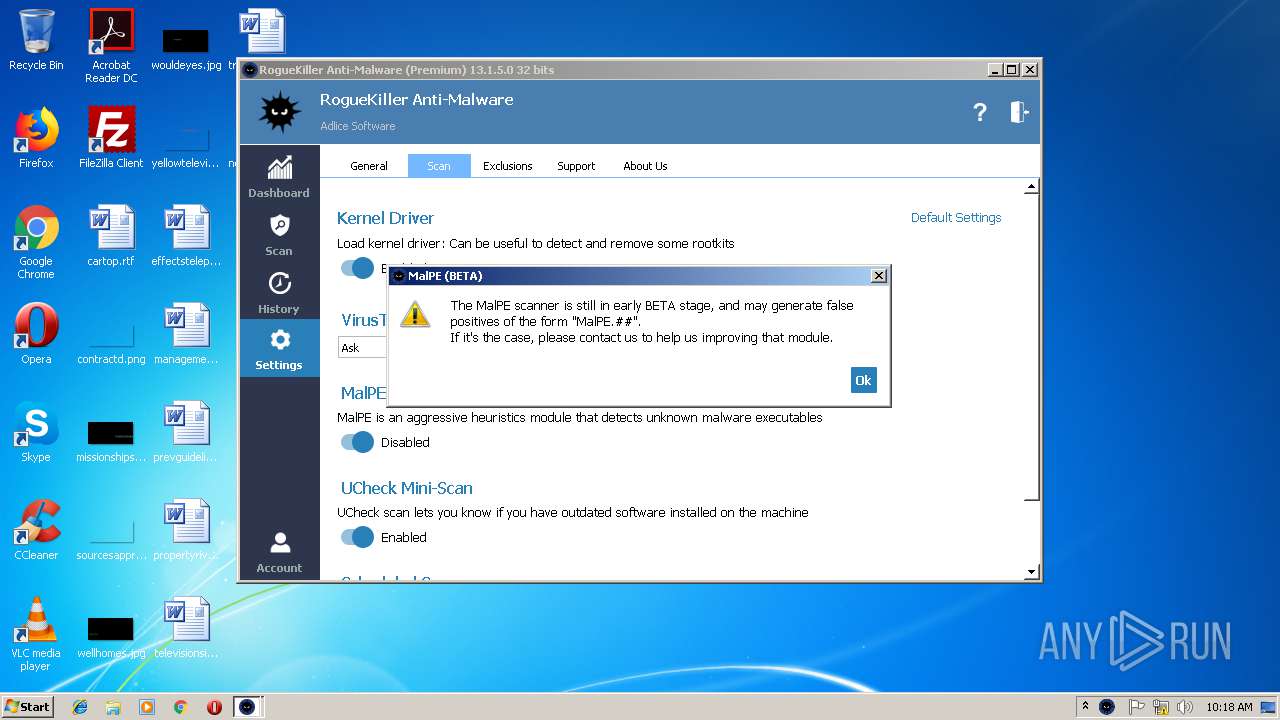
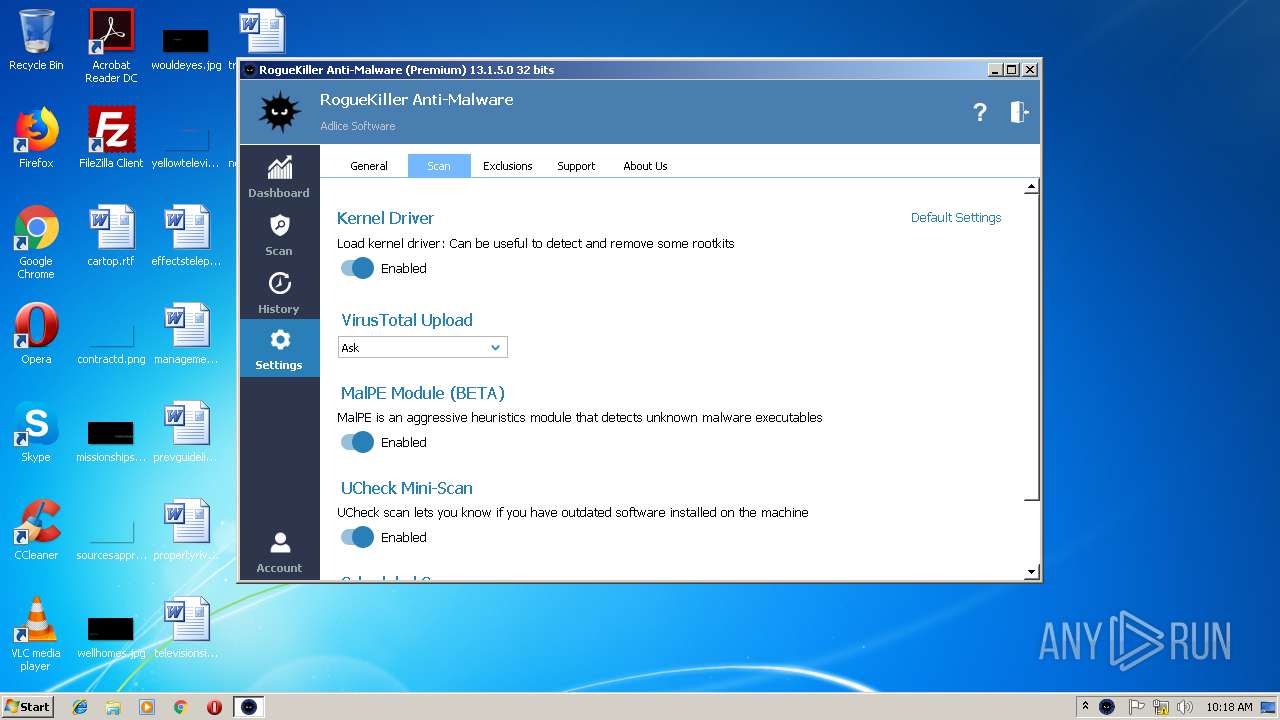
Loads the Task Scheduler DLL interface
- RogueKiller_portable32.exe (PID: 2400)
Loads the Task Scheduler COM API
- RogueKiller_portable32.exe (PID: 2400)
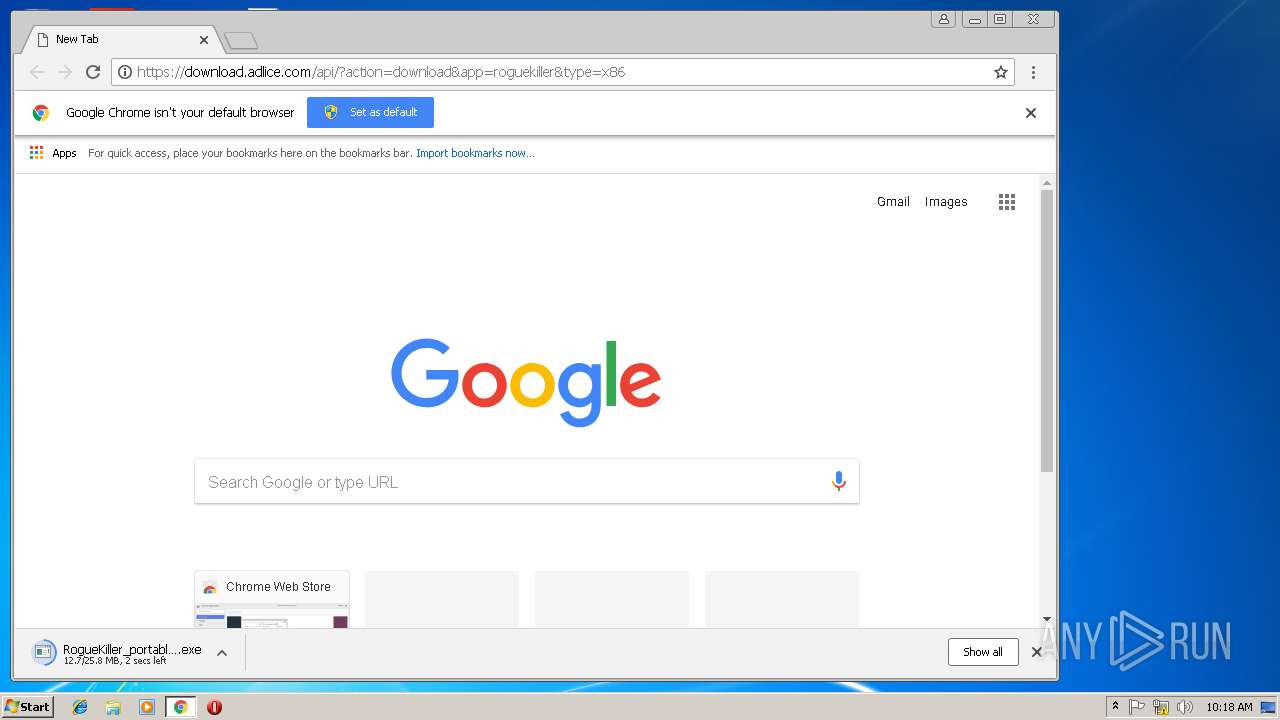
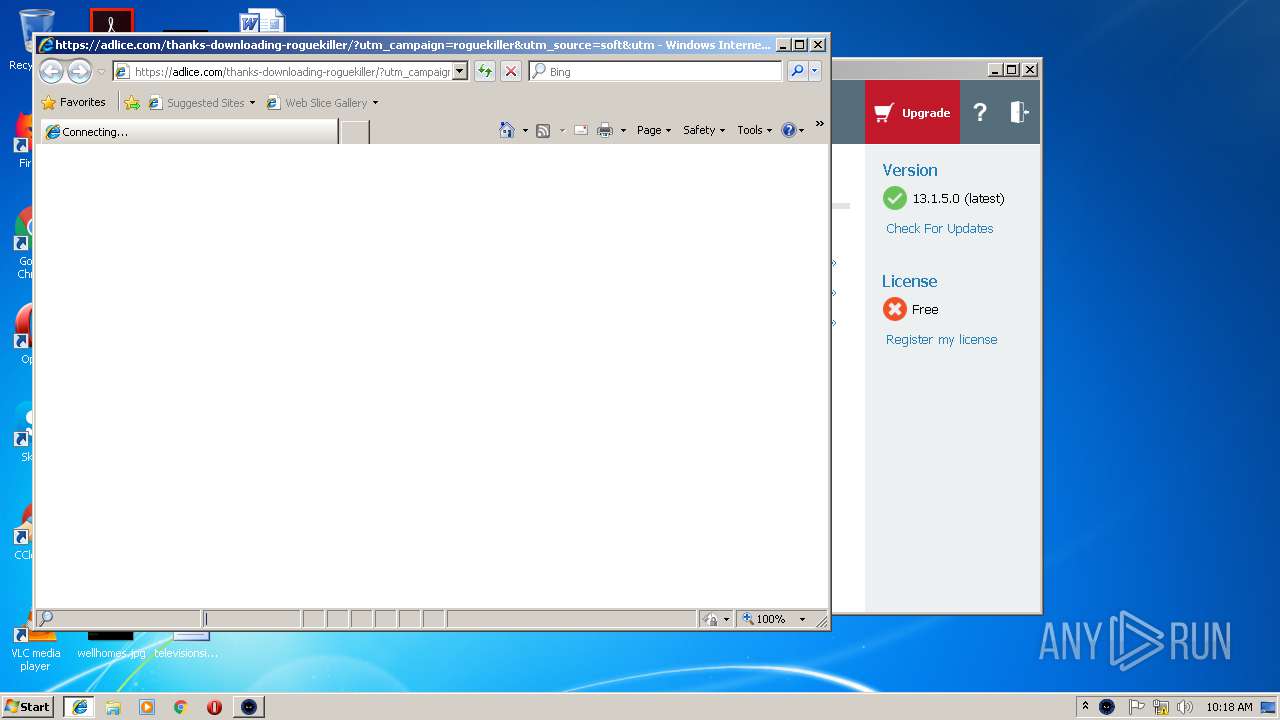
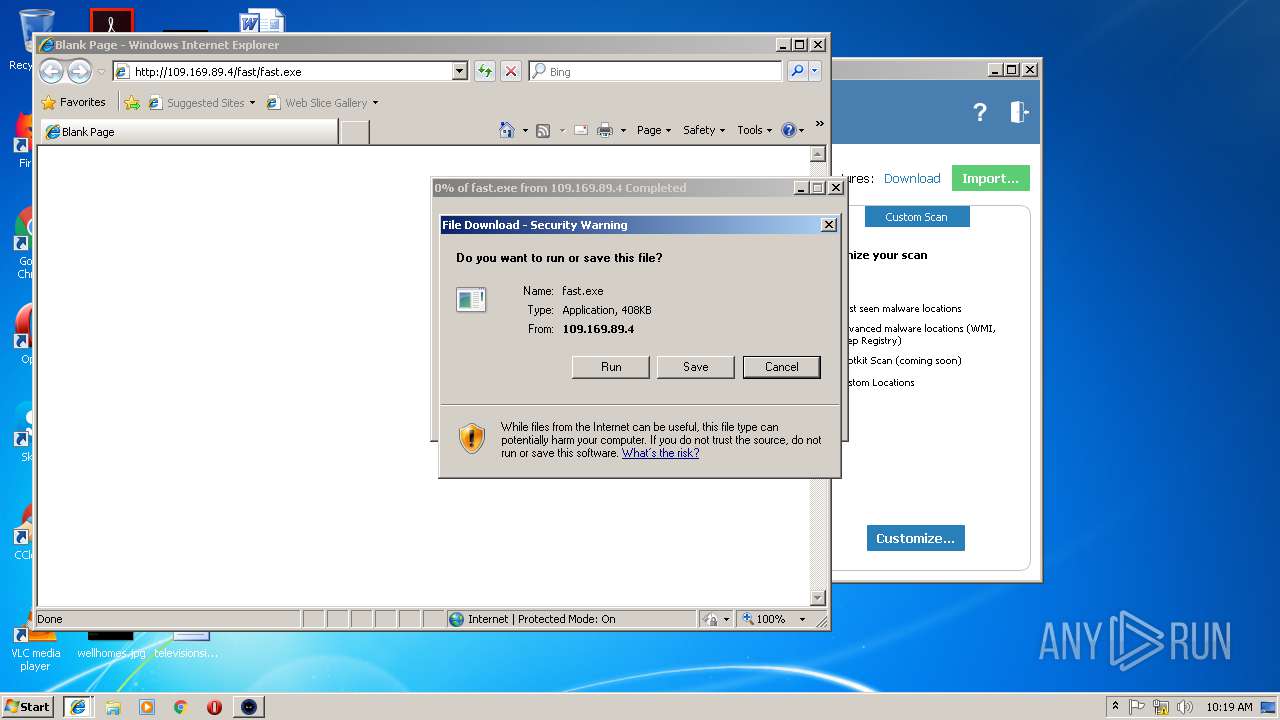
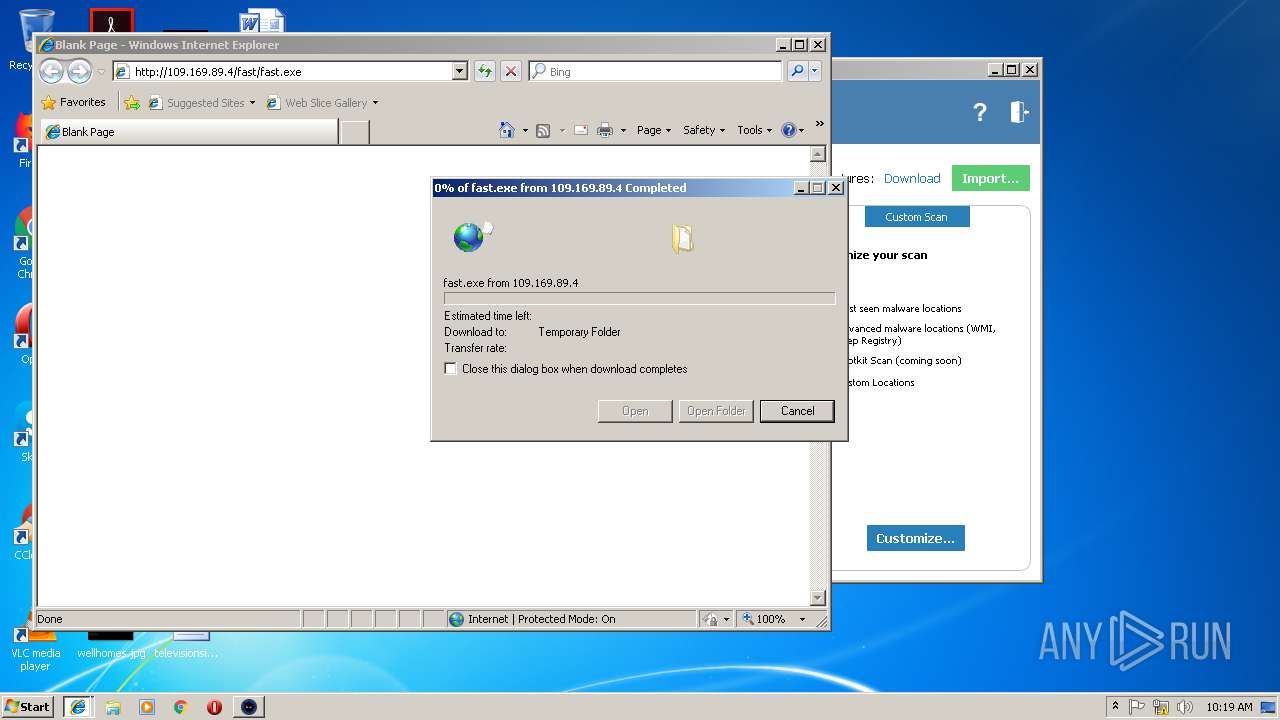
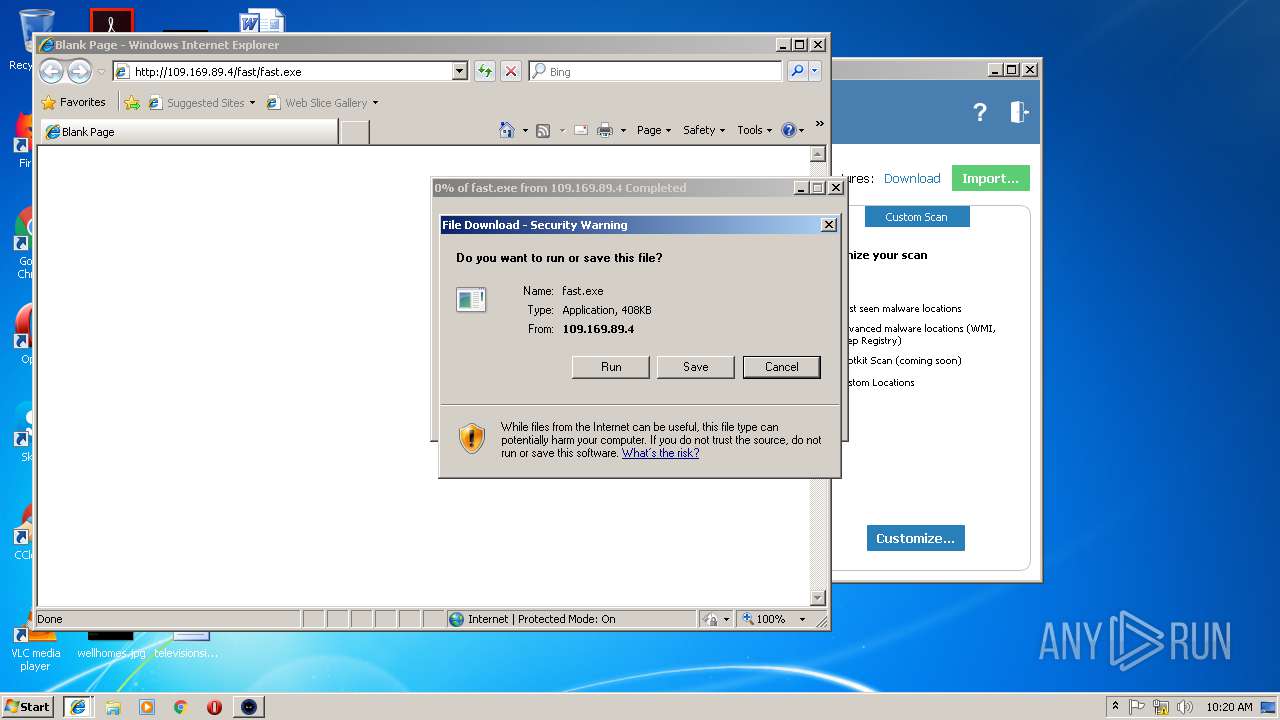
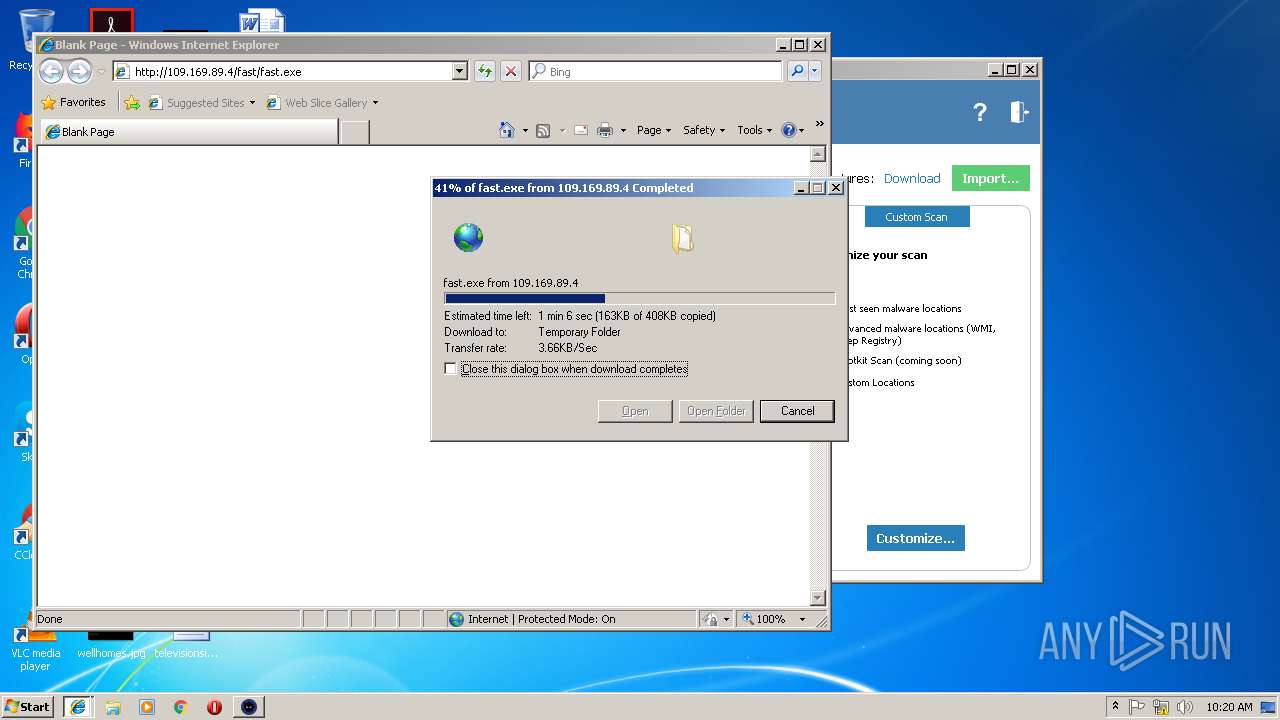
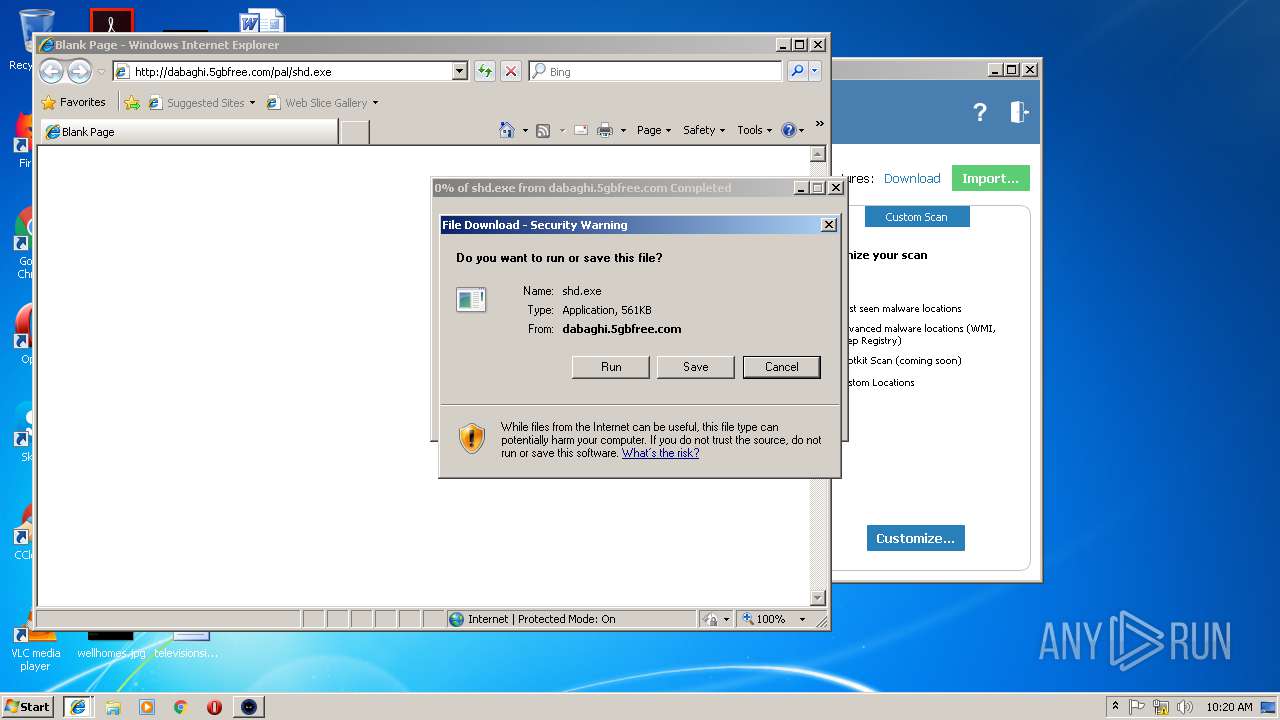
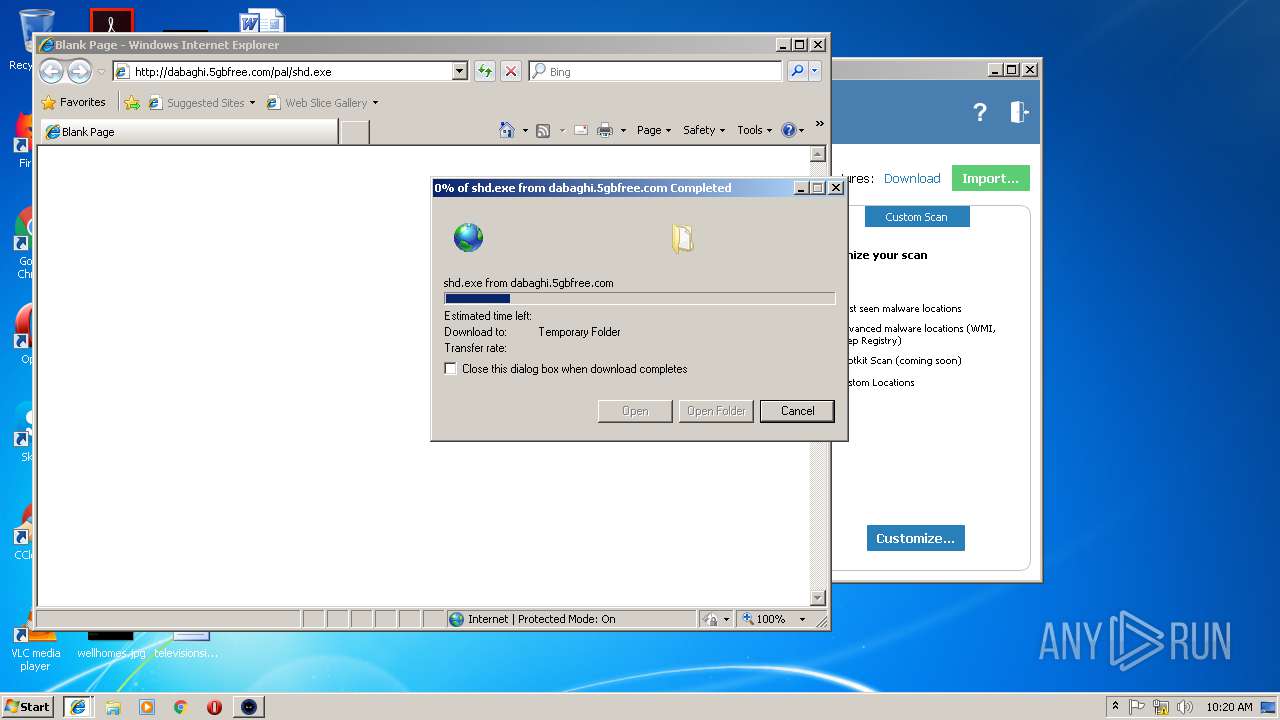
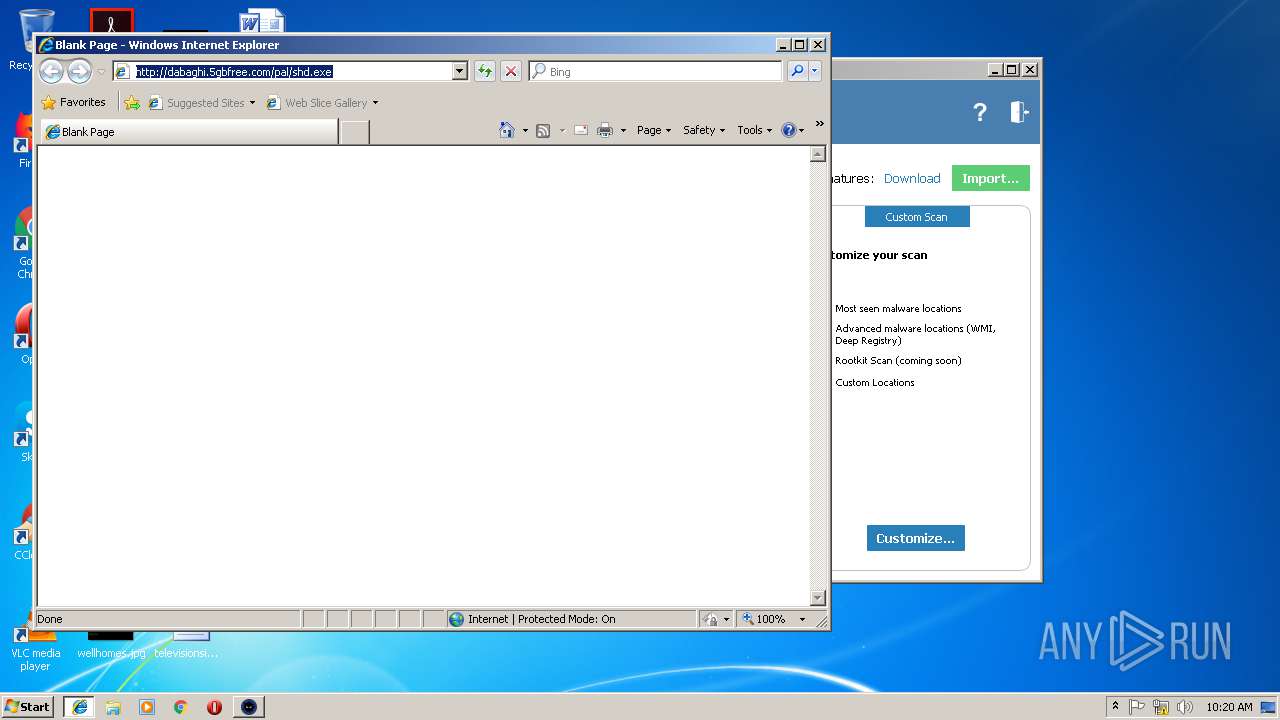
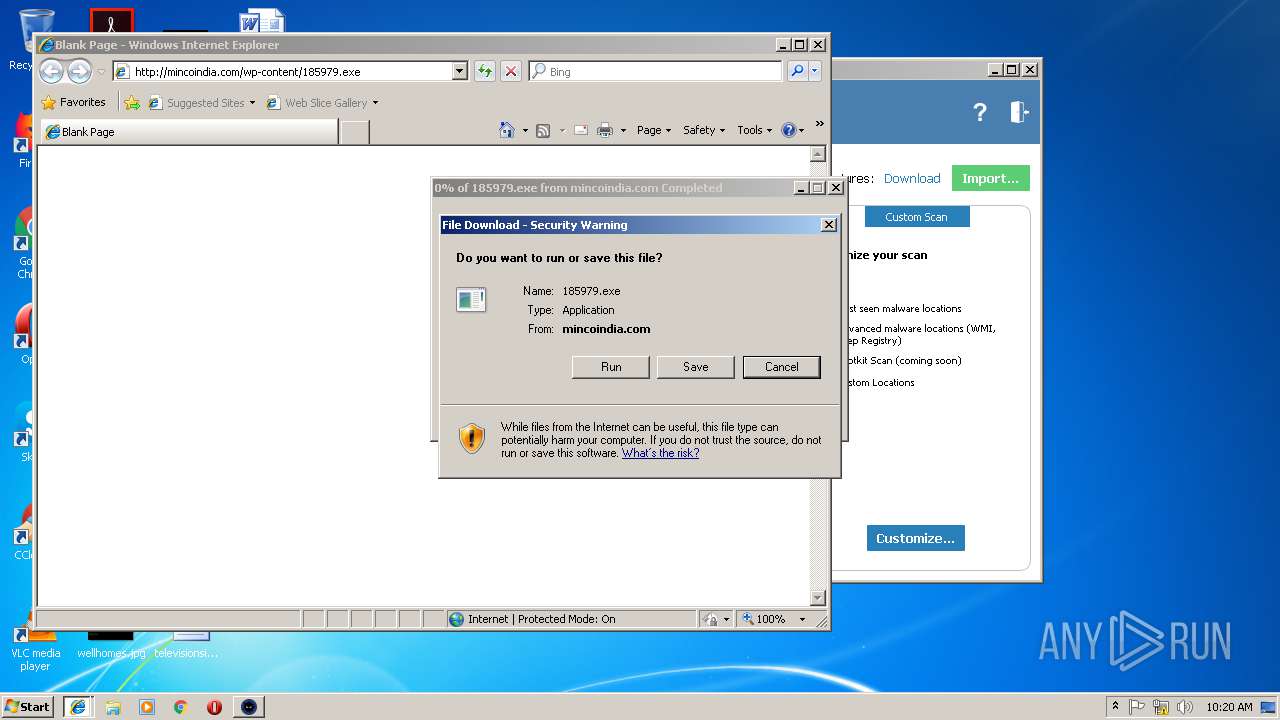
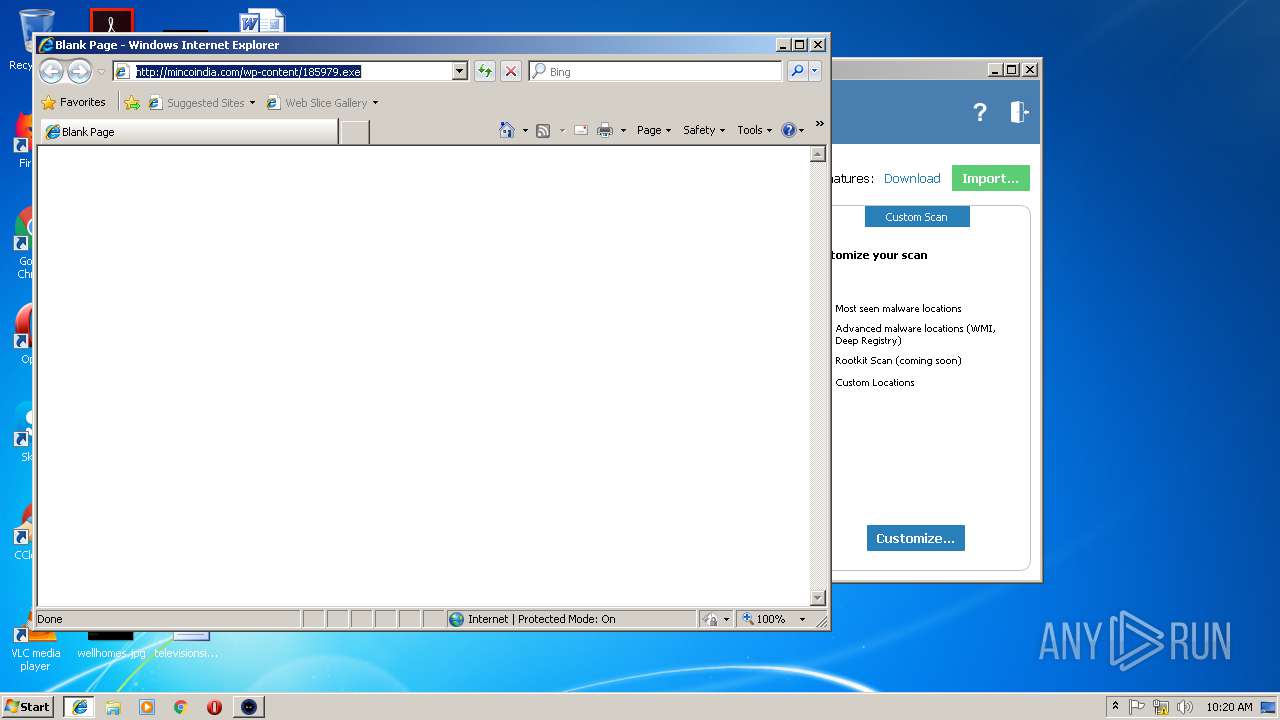
Downloads executable files from IP
- iexplore.exe (PID: 1300)
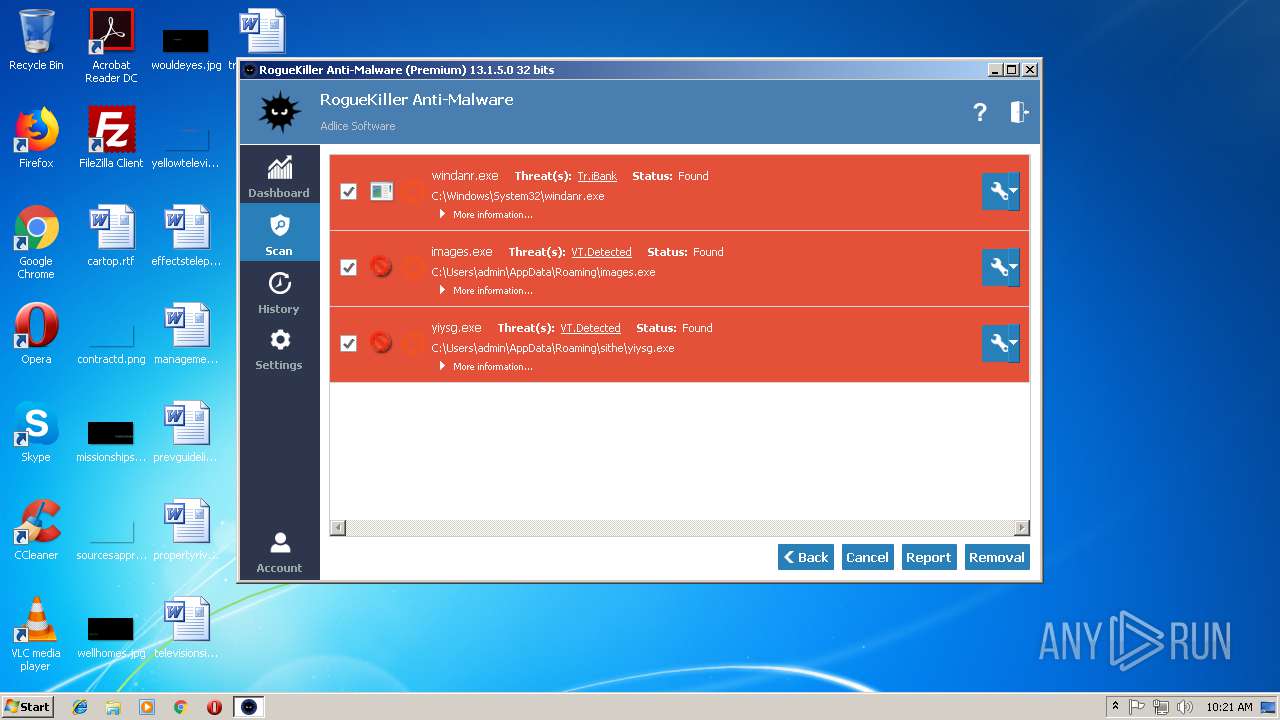
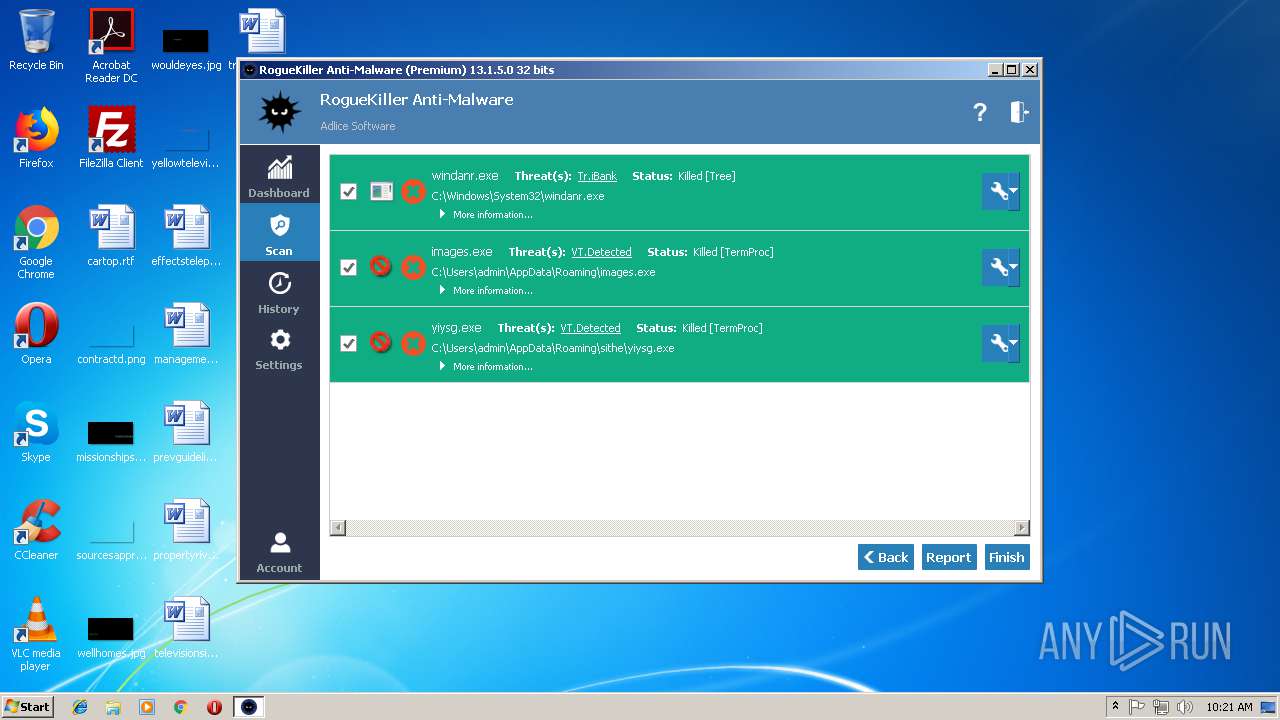
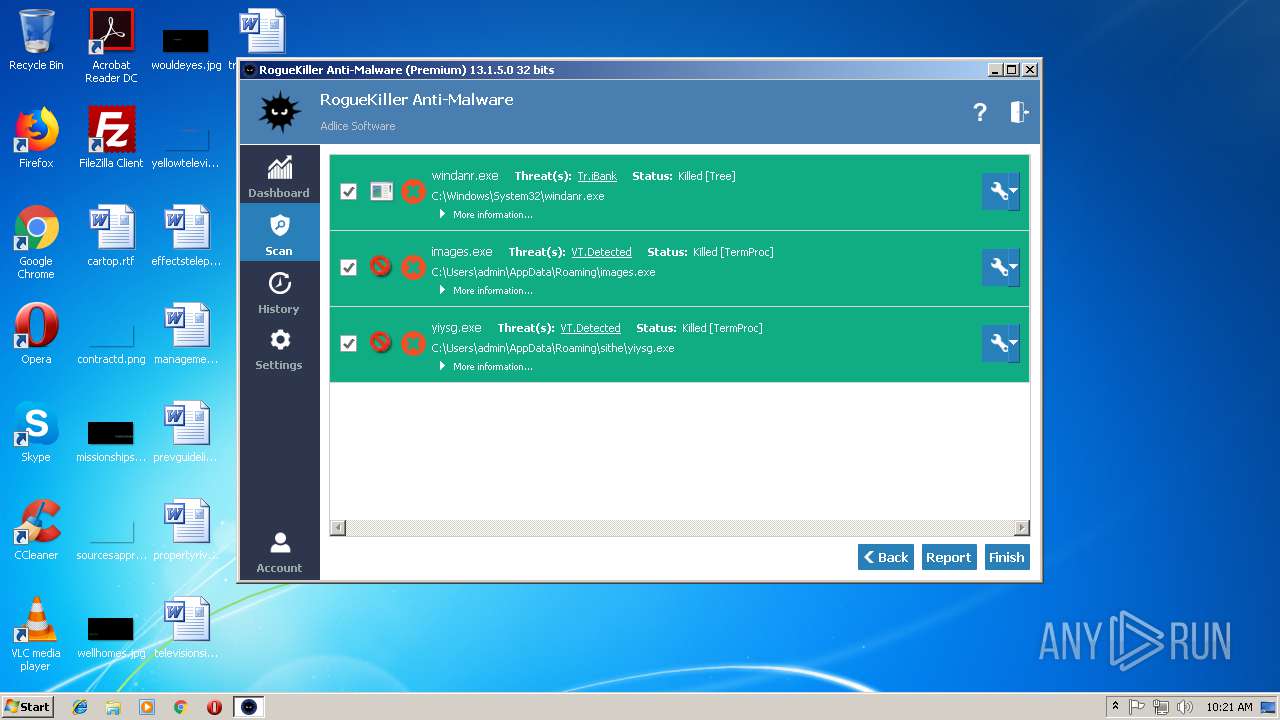
LOKIBOT was detected
- now1_output44F3940.exe (PID: 3132)
- yiysg.exe (PID: 3084)
Connects to CnC server
- now1_output44F3940.exe (PID: 3132)
- images.exe (PID: 3656)
- yiysg.exe (PID: 3084)
Detected artifacts of LokiBot
- now1_output44F3940.exe (PID: 3132)
Downloads executable files from the Internet
- iexplore.exe (PID: 1300)
Changes the autorun value in the registry
- shd[1].exe (PID: 3204)
Actions looks like stealing of personal data
- now1_output44F3940.exe (PID: 3132)
- yiysg.exe (PID: 3084)
AVEMARIA was detected
- images.exe (PID: 3656)
Writes to a start menu file
- yiysg.exe (PID: 3204)
SUSPICIOUS
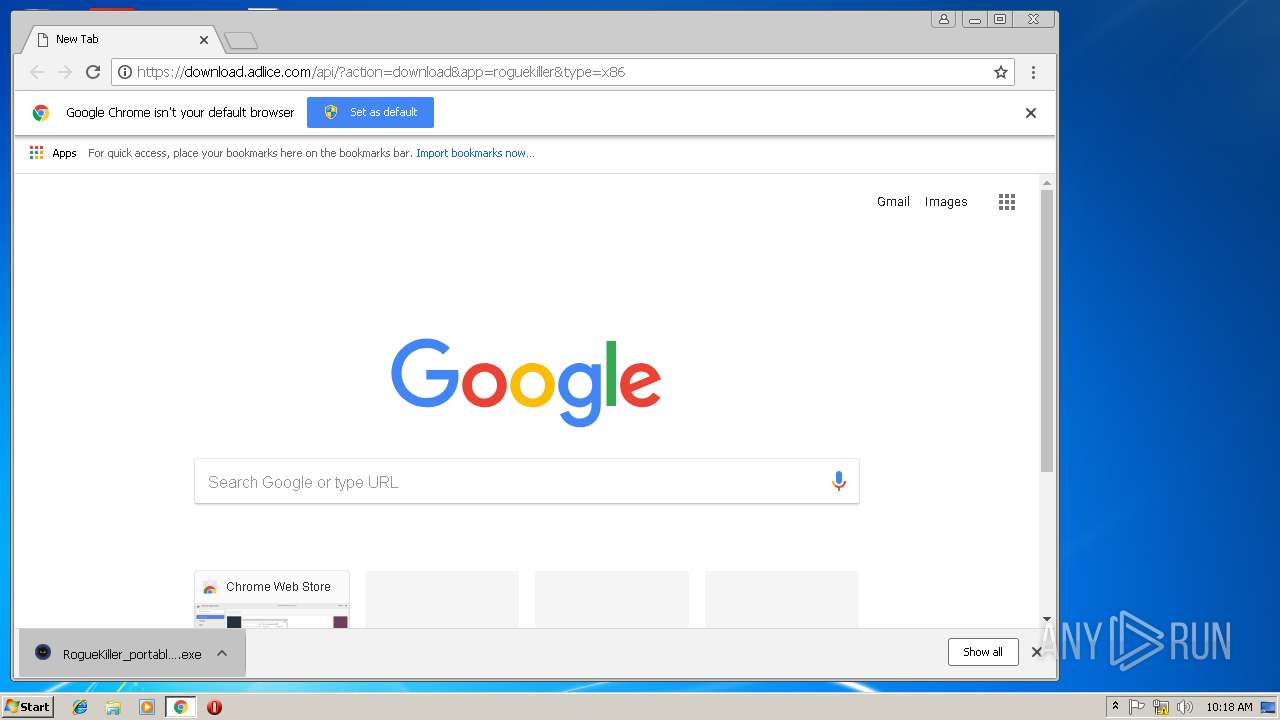
Executable content was dropped or overwritten
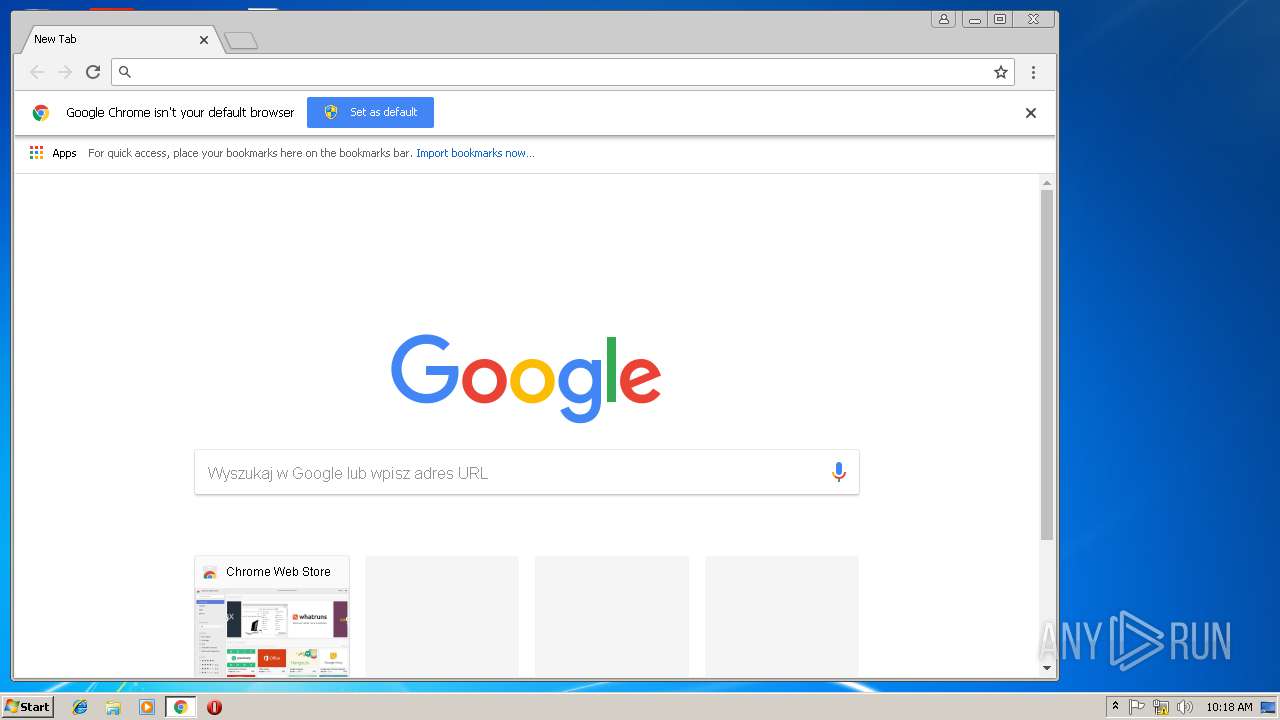
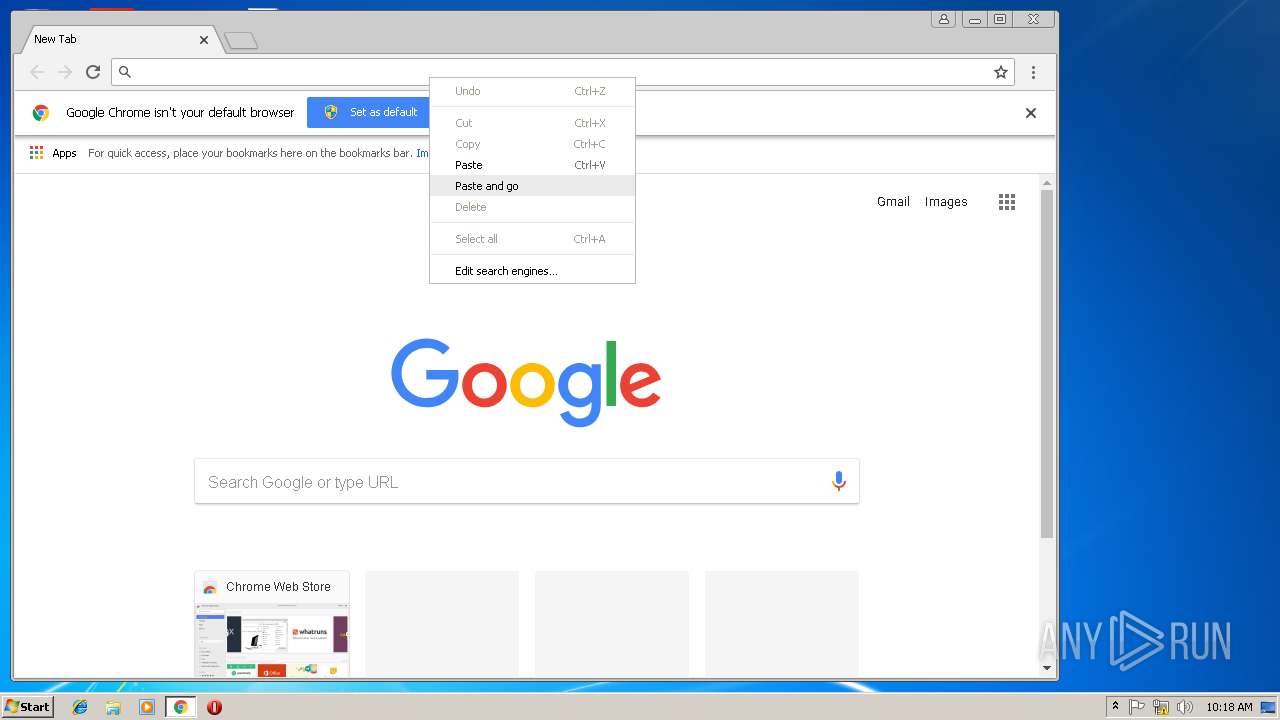
- chrome.exe (PID: 3508)
- RogueKiller_portable32.exe (PID: 2400)
- iexplore.exe (PID: 2608)
- now1_output44F3940.exe (PID: 3132)
- iexplore.exe (PID: 1300)
- shd[1].exe (PID: 3204)
- 185979[1].exe (PID: 2812)
Low-level read access rights to disk partition
- RogueKiller_portable32.exe (PID: 2400)
Creates files in the program directory
- RogueKiller_portable32.exe (PID: 2400)
Reads Internet Cache Settings
- RogueKiller_portable32.exe (PID: 2400)
Application launched itself
- now1_output44F3940.exe (PID: 3028)
- shd[1].exe (PID: 2660)
- images.exe (PID: 1912)
- yiysg.exe (PID: 3204)
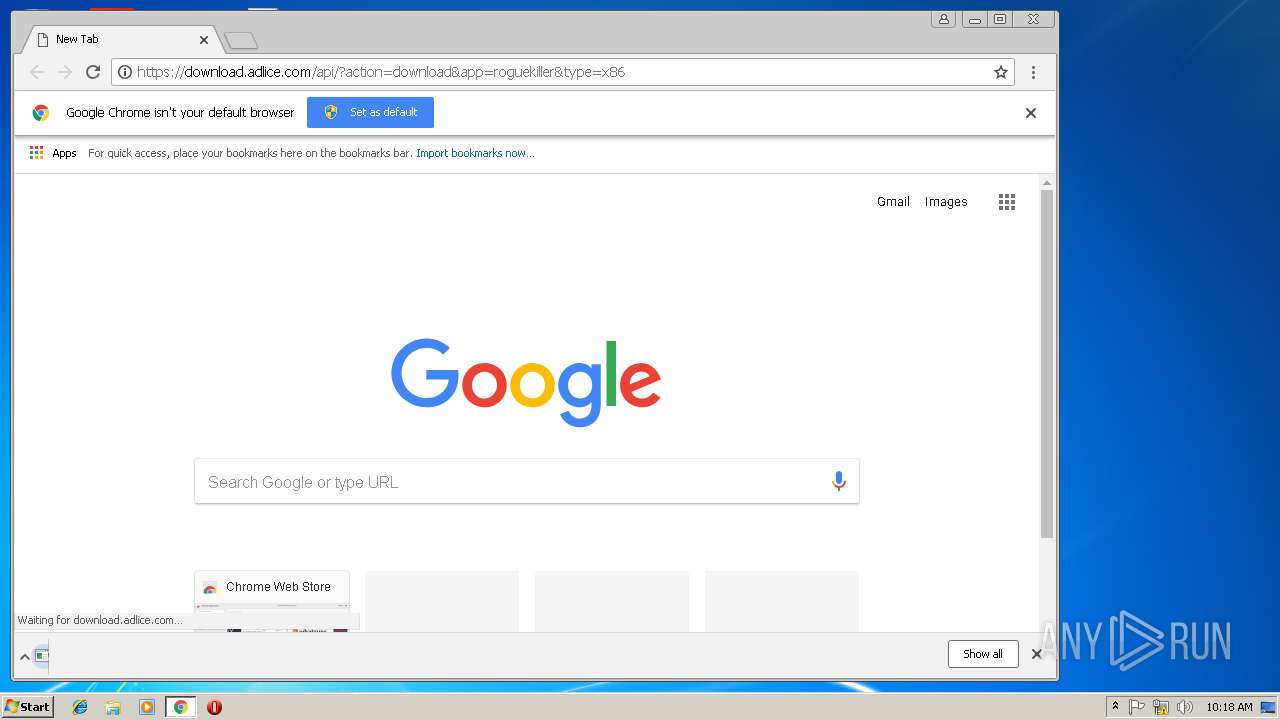
Starts Internet Explorer
- RogueKiller_portable32.exe (PID: 2400)
Creates files in the driver directory
- RogueKiller_portable32.exe (PID: 2400)
Creates files in the Windows directory
- RogueKiller_portable32.exe (PID: 2400)
Creates or modifies windows services
- RogueKiller_portable32.exe (PID: 2400)
Loads DLL from Mozilla Firefox
- now1_output44F3940.exe (PID: 3132)
- images.exe (PID: 3656)
- yiysg.exe (PID: 3084)
Creates files in the user directory
- now1_output44F3940.exe (PID: 3132)
- images.exe (PID: 3656)
- 185979[1].exe (PID: 2812)
- yiysg.exe (PID: 3204)
- yiysg.exe (PID: 3084)
- shd[1].exe (PID: 3204)
Starts CMD.EXE for commands execution
- wuapp.exe (PID: 3832)
Reads the machine GUID from the registry
- images.exe (PID: 3656)
Connects to unusual port
- images.exe (PID: 3656)
Starts itself from another location
- 185979[1].exe (PID: 2812)
Removes files from Windows directory
- RogueKiller_portable32.exe (PID: 2400)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3508)
- RogueKiller_portable32.exe (PID: 2400)
Application launched itself
- chrome.exe (PID: 3508)
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 2608)
Reads Internet Cache Settings
- chrome.exe (PID: 3508)
- iexplore.exe (PID: 1300)
- iexplore.exe (PID: 2608)
Changes internet zones settings
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 2608)
Reads internet explorer settings
- iexplore.exe (PID: 1300)
Creates files in the user directory
- iexplore.exe (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (69.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:05:30 00:01:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1024000 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12f4 |
| OSVersion: | 4 |
| ImageVersion: | 6.7 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.7.0.6 |
| ProductVersionNumber: | 6.7.0.6 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | stargazers2 |
| ProductName: | reluctance2 |
| FileVersion: | 6.07.0006 |
| ProductVersion: | 6.07.0006 |
| InternalName: | MAHOMET |
| OriginalFileName: | MAHOMET.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-May-2010 22:01:05 |
| Detected languages: |
|
| CompanyName: | stargazers2 |
| ProductName: | reluctance2 |
| FileVersion: | 6.07.0006 |
| ProductVersion: | 6.07.0006 |
| InternalName: | MAHOMET |
| OriginalFilename: | MAHOMET.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-May-2010 22:01:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000F9890 | 0x000FA000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96644 |
.data | 0x000FB000 | 0x00000B68 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000FC000 | 0x00001AC6 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.1438 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32858 | 552 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 3.22405 | 1736 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 2.58346 | 1384 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 3.67617 | 1864 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30004 | 3.43355 | 872 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
67
Monitored processes
28
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1300 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2608 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,18159128105085429570,15763300789824830251,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2BCC9812701E5D0A4D38162C1B078824 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1624 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\fast[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\fast[1].exe | — | iexplore.exe | |||||||||||
User: admin Company: PhIlIPS Integrity Level: MEDIUM Description: PIrIfORM LtD Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1816 | "C:\Users\admin\Downloads\RogueKiller_portable32.exe" | C:\Users\admin\Downloads\RogueKiller_portable32.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | — | shd[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5d00b0,0x6f5d00c0,0x6f5d00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3848 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,18159128105085429570,15763300789824830251,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5FE375F439AF6EC909A8986926349BA2 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5FE375F439AF6EC909A8986926349BA2 --renderer-client-id=6 --mojo-platform-channel-handle=3584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\Downloads\RogueKiller_portable32.exe" | C:\Users\admin\Downloads\RogueKiller_portable32.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 023
Read events
1 806
Write events
206
Delete events
11
Modification events
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3508-13195045088115875 |
Value: 259 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3508-13195045088115875 |
Value: 259 | |||
Executable files
14
Suspicious files
83
Text files
86
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0cc81e0a-4757-4d7e-a7cf-d7638aa155fe.tmp | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF19c7bb.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4b053cf9-b1e1-439e-a32c-b117ea7fa1c0.tmp | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19c6b1.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
49
DNS requests
31
Threats
53
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1300 | iexplore.exe | GET | — | 109.169.89.4:80 | http://109.169.89.4/fast/fast.exe | GB | — | — | suspicious |
2608 | iexplore.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | — | — | whitelisted |
1300 | iexplore.exe | GET | 200 | 107.180.27.166:80 | http://mincoindia.com/wp-content/185979.exe | US | executable | 314 Kb | malicious |
3084 | yiysg.exe | POST | — | 141.105.68.76:80 | http://n010tt.cf/playtime/playbook/onelove/fre.php | RU | — | — | malicious |
3132 | now1_output44F3940.exe | POST | 404 | 173.212.235.45:80 | http://martfire.gq/mart/five/fre.php | DE | html | 215 b | malicious |
1300 | iexplore.exe | GET | 200 | 209.90.88.136:80 | http://dabaghi.5gbfree.com/pal/shd.exe | US | executable | 561 Kb | suspicious |
1300 | iexplore.exe | GET | 200 | 109.169.89.4:80 | http://109.169.89.4/fast/fast.exe | GB | executable | 408 Kb | suspicious |
3848 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3508 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 216.58.205.227:443 | www.google.pl | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.pl |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
3132 | now1_output44F3940.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3132 | now1_output44F3940.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3132 | now1_output44F3940.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.gq domain |
3132 | now1_output44F3940.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3132 | now1_output44F3940.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3132 | now1_output44F3940.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3132 | now1_output44F3940.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3132 | now1_output44F3940.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3132 | now1_output44F3940.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.gq domain |
16 ETPRO signatures available at the full report
Process | Message |
|---|---|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|