| File name: | Ref1172020.iso |
| Full analysis: | https://app.any.run/tasks/14cc7465-def9-402d-9692-b72277cca050 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 17, 2020, 19:59:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
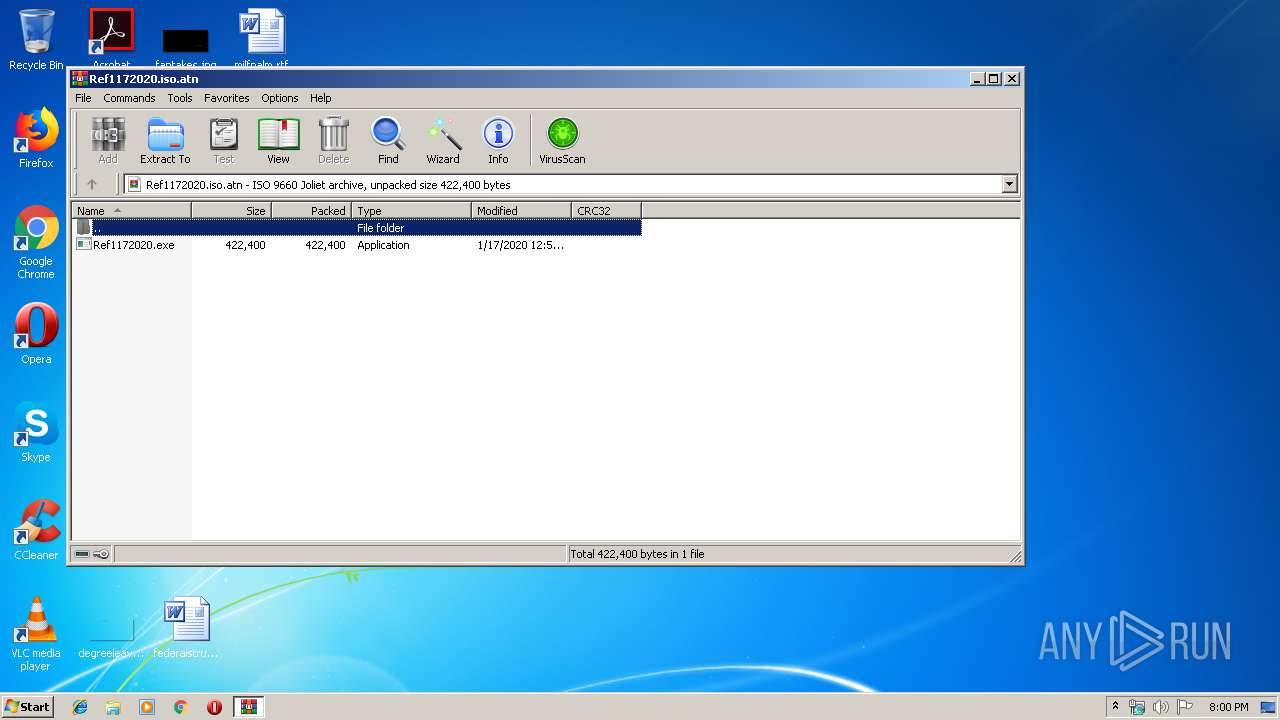
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data '20200117_022851' |
| MD5: | 6394A1531D3B7C9C3DFDEB99A2B7835A |
| SHA1: | 4F0E443CBB751CA448E2A9085A31486D821B71C9 |
| SHA256: | E24F21CC129146143A403E7E3E70E881071E78BFB59D49C8784172CB4AD1F80A |
| SSDEEP: | 12288:czcgQc0XiaYYb8QUfIkanIfONuPDzzmON6:Qzax7KCnMcuva4 |
MALICIOUS
Application was dropped or rewritten from another process
- Ref1172020.exe (PID: 1972)
- mjwxh0prwtldex.exe (PID: 1648)
FORMBOOK was detected
- netsh.exe (PID: 3744)
- explorer.exe (PID: 352)
- Firefox.exe (PID: 1796)
Actions looks like stealing of personal data
- netsh.exe (PID: 3744)
Connects to CnC server
- explorer.exe (PID: 352)
Changes the autorun value in the registry
- netsh.exe (PID: 3744)
Stealing of credential data
- netsh.exe (PID: 3744)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 352)
Loads DLL from Mozilla Firefox
- netsh.exe (PID: 3744)
Executed via COM
- DllHost.exe (PID: 3660)
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 352)
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
- WinRAR.exe (PID: 1848)
- DllHost.exe (PID: 3660)
Starts CMD.EXE for commands execution
- netsh.exe (PID: 3744)
Creates files in the user directory
- netsh.exe (PID: 3744)
Creates files in the program directory
- DllHost.exe (PID: 3660)
INFO
Manual execution by user
- netsh.exe (PID: 3744)
Creates files in the user directory
- Firefox.exe (PID: 1796)
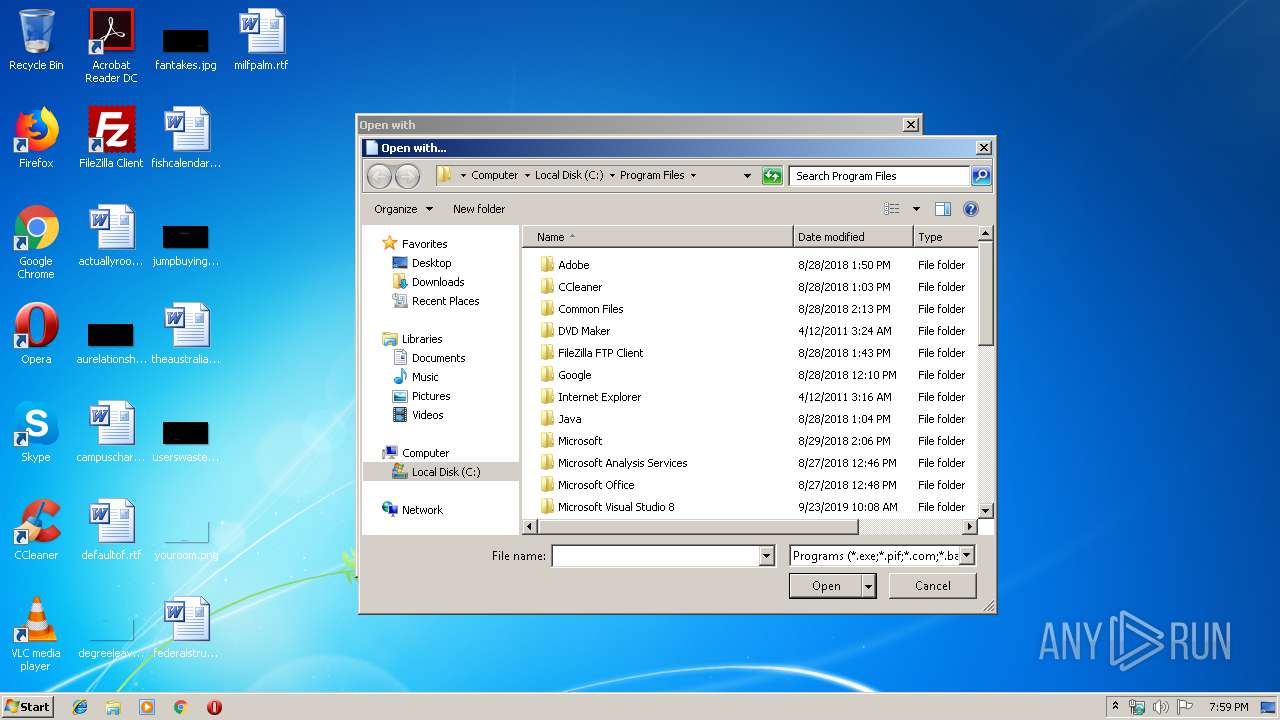
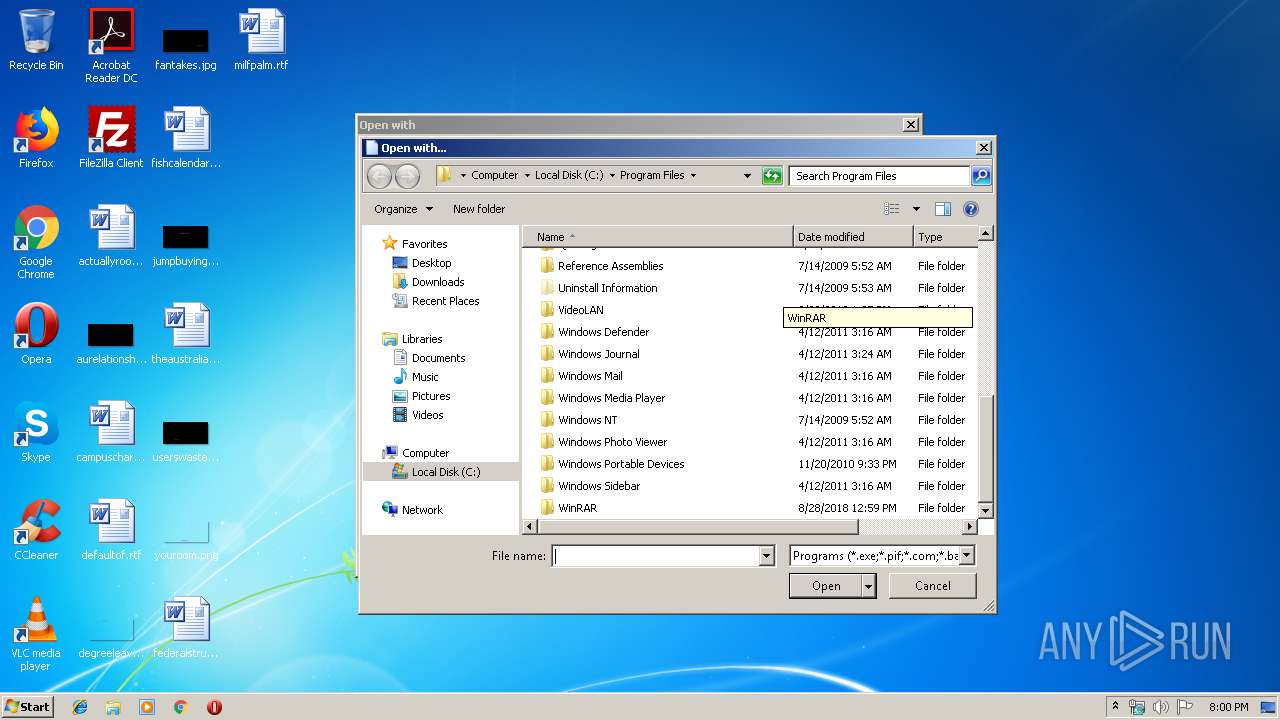
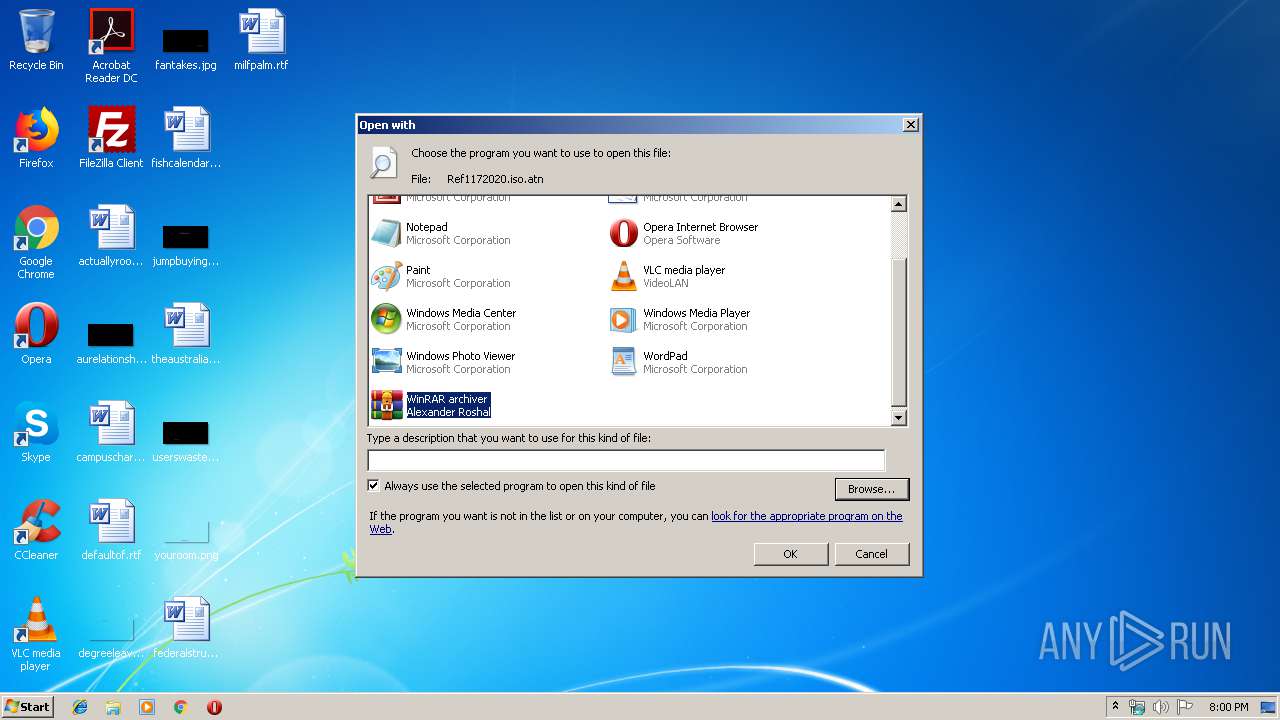
Modifies the open verb of a shell class
- rundll32.exe (PID: 2408)
Reads the hosts file
- netsh.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .atn | | | Photoshop Action (37.5) |
|---|---|---|
| .gmc | | | Game Music Creator Music (8.4) |
| .abr | | | Adobe PhotoShop Brush (7.5) |
EXIF
ISO
| System: | WIN32 |
|---|---|
| VolumeName: | 20200117_022851 |
| VolumeBlockCount: | 232 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 1970:01:01 01:00:00+01:00 |
| Software: | ULTRAISO V9.7 CD & DVD CREATOR, (C) EZB SYSTEMS, INC. |
| VolumeCreateDate: | 2020:01:17 02:29:42.00+01:00 |
| VolumeModifyDate: | 2020:01:17 02:29:42.00+01:00 |
Composite
| VolumeSize: | 464 kB |
|---|
Total processes
45
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa1848.22254\Ref1172020.exe" | C:\Windows\System32\cmd.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Pun0l\mjwxh0prwtldex.exe" | C:\Program Files\Pun0l\mjwxh0prwtldex.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | netsh.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
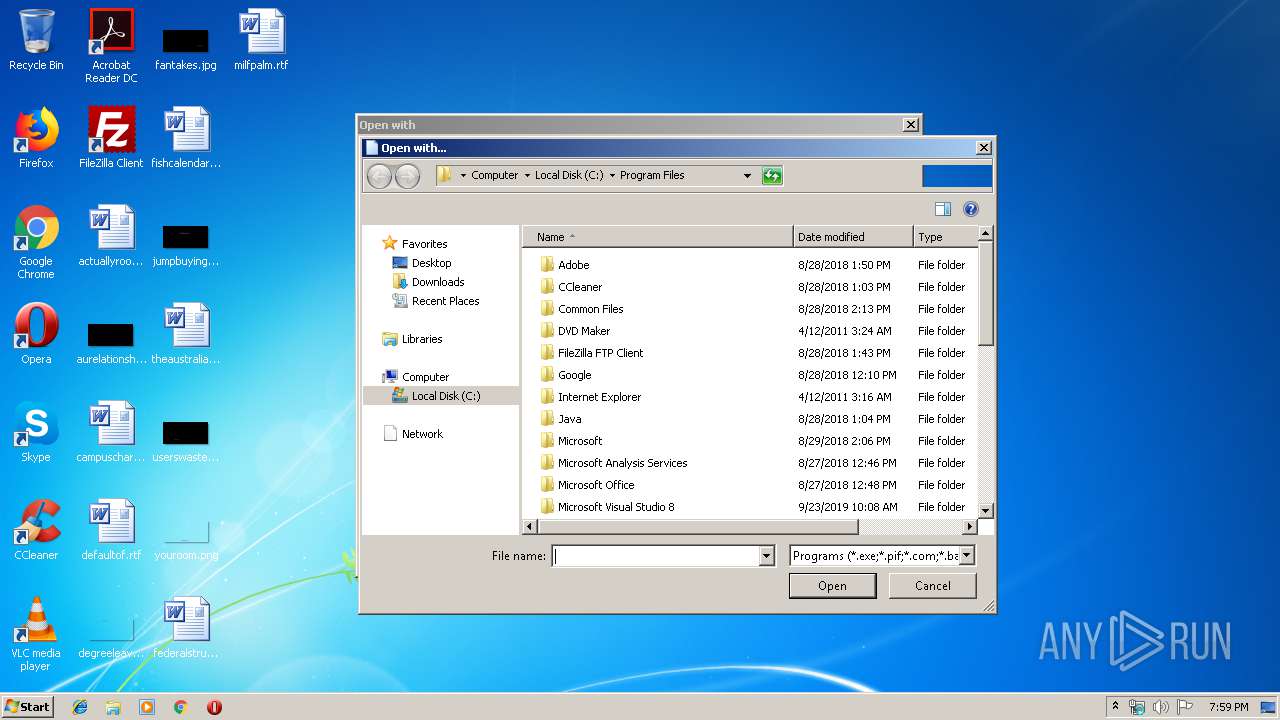
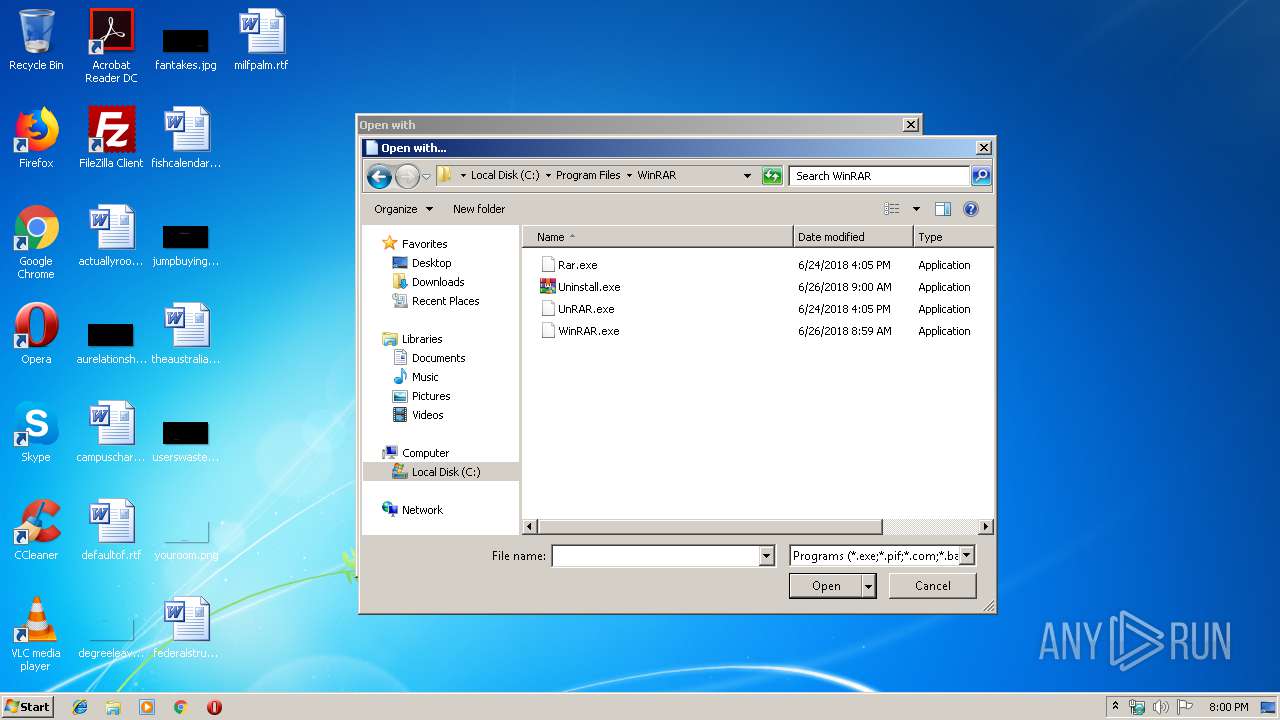
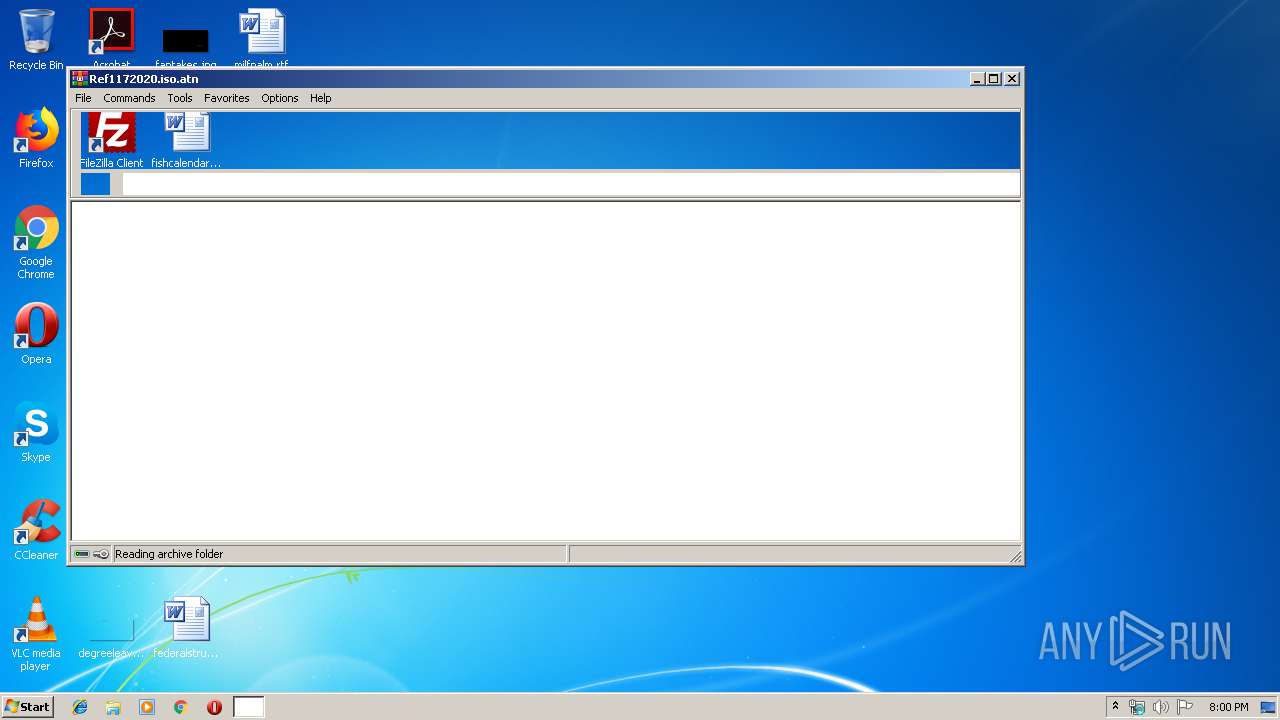
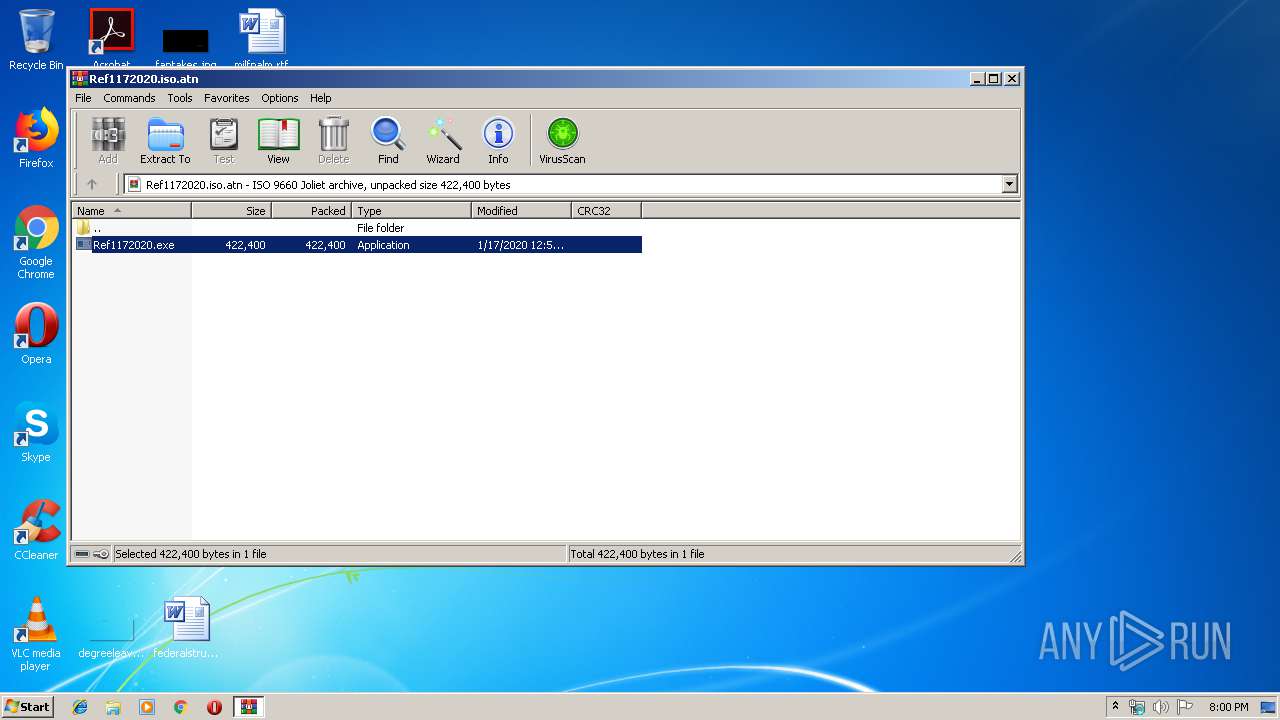
| 1848 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ref1172020.iso.atn" | C:\Program Files\WinRAR\WinRAR.exe | rundll32.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1848.22254\Ref1172020.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1848.22254\Ref1172020.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
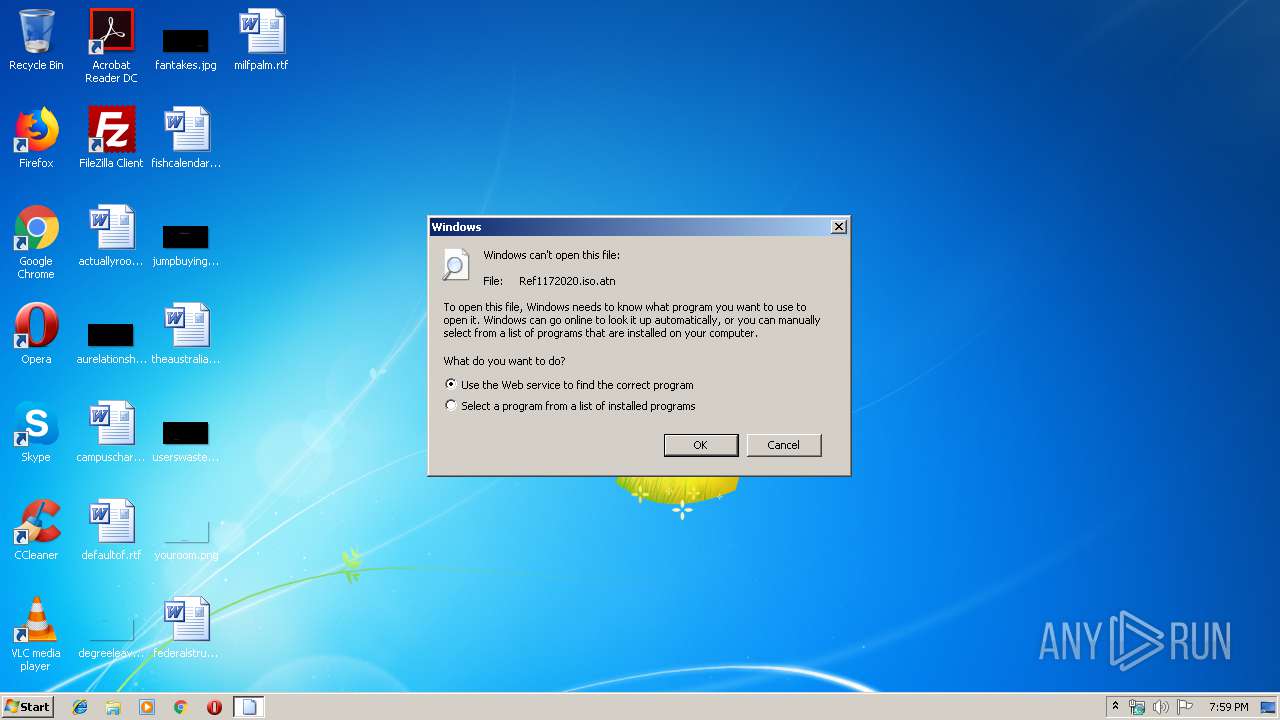
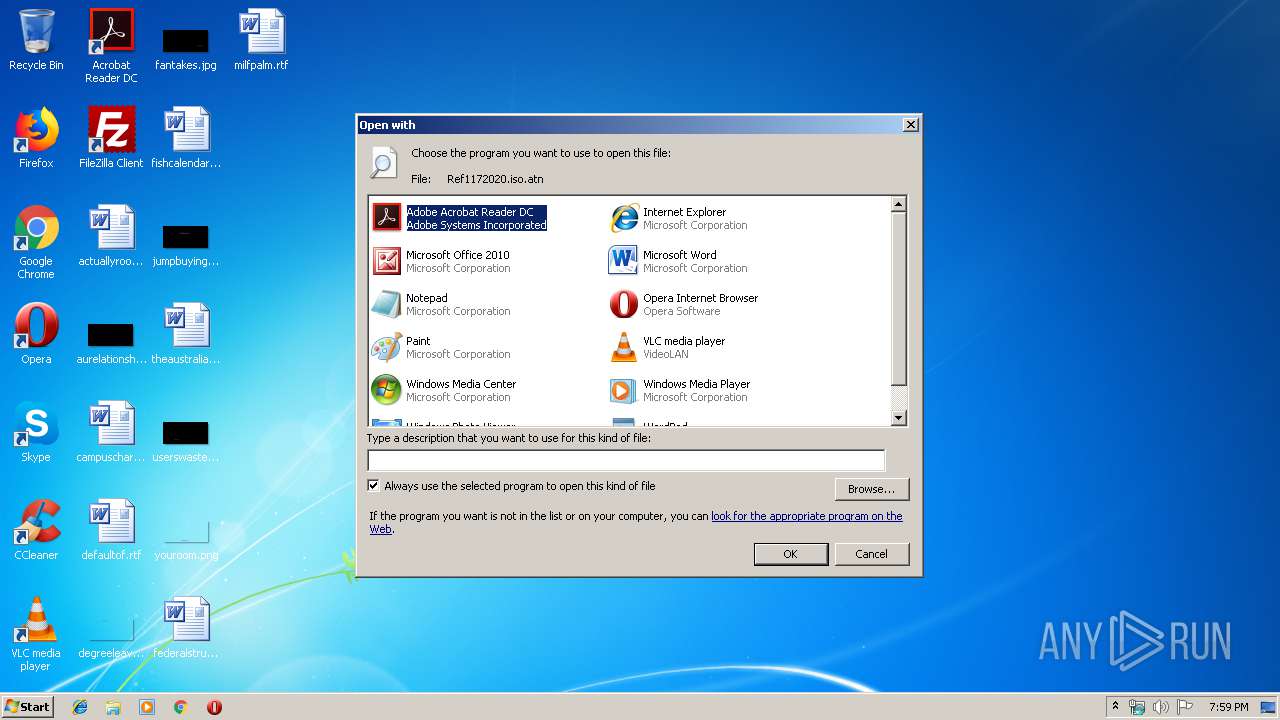
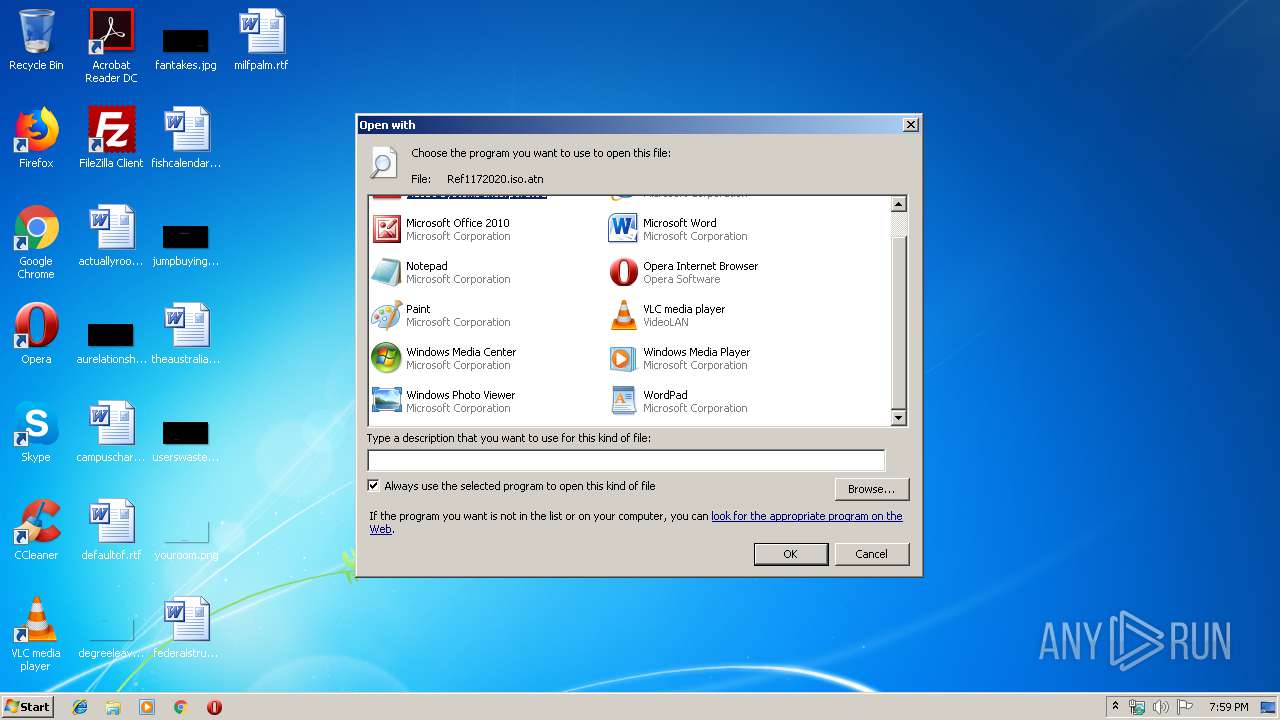
| 2408 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Ref1172020.iso.atn | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | "C:\Windows\System32\dwm.exe" | C:\Windows\System32\dwm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3744 | "C:\Windows\System32\netsh.exe" | C:\Windows\System32\netsh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 372
Read events
1 184
Write events
187
Delete events
1
Modification events
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2408) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
3
Suspicious files
74
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1848.22254\Ref1172020.exe | executable | |
MD5:— | SHA256:— | |||
| 3660 | DllHost.exe | C:\Program Files\Pun0l\mjwxh0prwtldex.exe | executable | |
MD5:— | SHA256:— | |||
| 1796 | Firefox.exe | C:\Users\admin\AppData\Roaming\4341Q-19\434logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Pun0l\mjwxh0prwtldex.exe | executable | |
MD5:— | SHA256:— | |||
| 3744 | netsh.exe | C:\Users\admin\AppData\Roaming\4341Q-19\434logrc.ini | binary | |
MD5:E03F207A7B9CFC4D877ED2EC64BE028E | SHA256:B17183098B6E349844A3151456EDF62C8E41B2348D2445A610C0FF1E29963067 | |||
| 3744 | netsh.exe | C:\Users\admin\AppData\Roaming\4341Q-19\434logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3744 | netsh.exe | C:\Users\admin\AppData\Roaming\4341Q-19\434logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 3744 | netsh.exe | C:\Users\admin\AppData\Roaming\4341Q-19\434logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | — | 184.168.131.241:80 | http://www.vehicledonation.online/t8a/?xPeDUfwp=Si1C7opdcowm2ssNfOaRn7JqGFiTLK5eUl0GrdkEDFAwIvXRIucl76YjVQLPdu+n75jswg==&9r8tQ=J4Nhp&sql=1 | US | — | — | malicious |
352 | explorer.exe | GET | 302 | 162.255.119.158:80 | http://www.radioncr.com/t8a/?xPeDUfwp=EX4jpGRwrA0kTfSIfzJ3pO5SiQ+780Sc9EsfU8ByvumfVfQJq5VUCclhIFa1SKpbrmgTEQ==&9r8tQ=J4Nhp | US | html | 172 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | explorer.exe | 184.168.131.241:80 | www.vehicledonation.online | GoDaddy.com, LLC | US | shared |
352 | explorer.exe | 162.255.119.158:80 | www.radioncr.com | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dmaestroshop.com |
| unknown |
www.radioncr.com |
| malicious |
www.vehicledonation.online |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
2 ETPRO signatures available at the full report