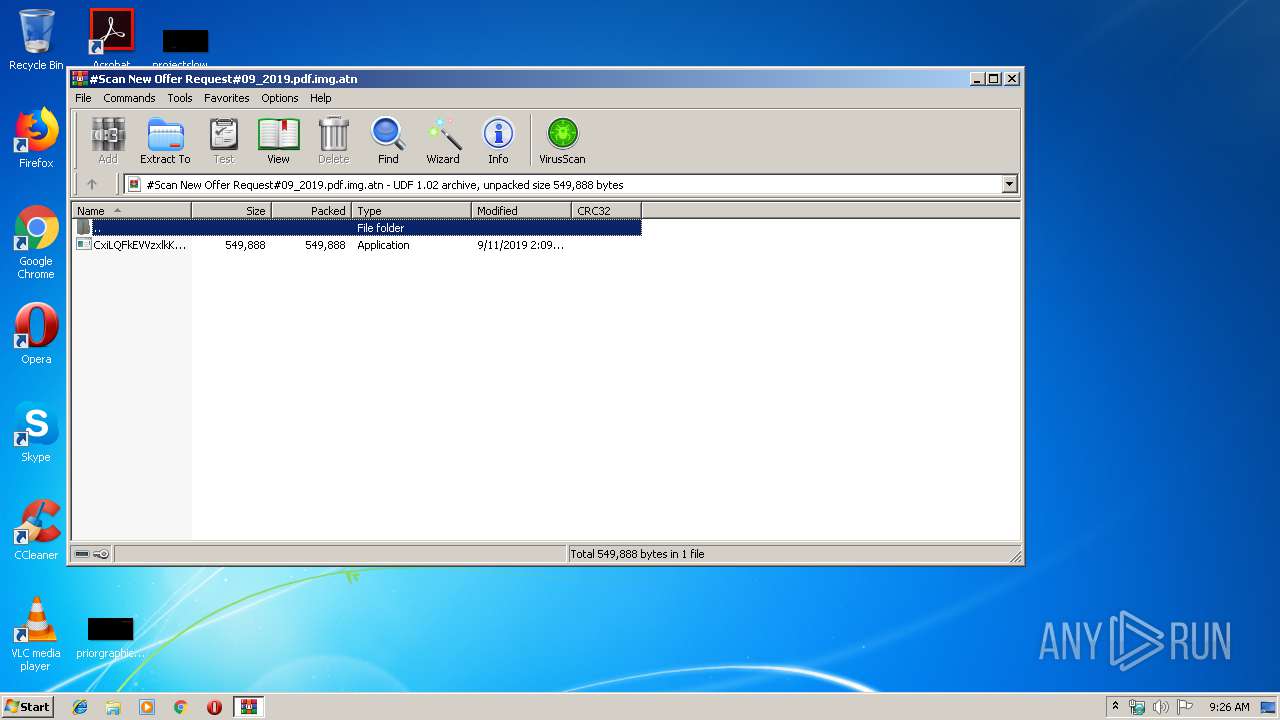
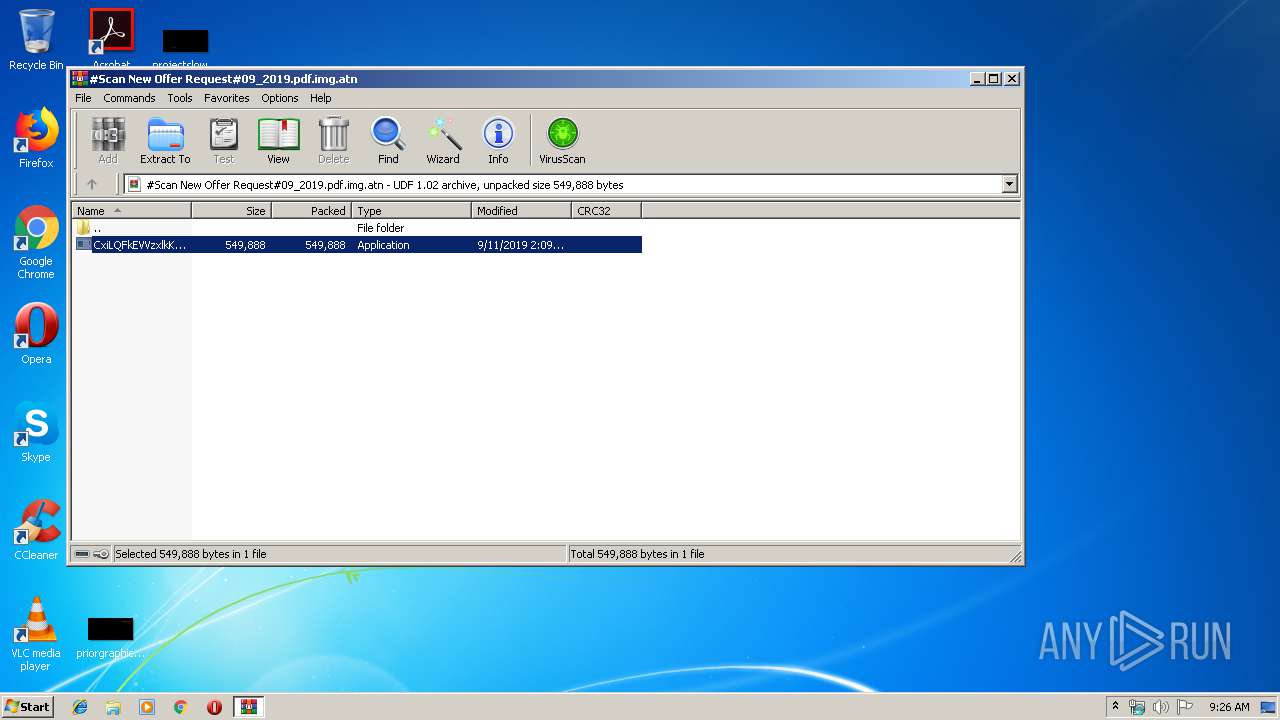
| File name: | #Scan New Offer Request#09_2019.pdf.img |
| Full analysis: | https://app.any.run/tasks/51419c8a-10bb-490a-909f-3ecb5f7ab4bb |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 11, 2019, 08:25:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | UDF filesystem data (version 1.5) 'ORDINARY_CRYPTED' |
| MD5: | BF0968ABBF2A4CA0D19D4C8540F27B5B |
| SHA1: | E955147680A7BDE9819537D7532B6F4125D72B79 |
| SHA256: | E21C78DDA1DBDB1473DA4D50F8985E736E9377AED1FA86C29533E5DA17BC9D61 |
| SSDEEP: | 12288:DLo9+xcaQYiDd4bWAzvBu33Dvim4g0uNISWNBgm+E9:3o9+qG/bWwpw3DvimP0g3IBgFE |
MALICIOUS
Application was dropped or rewritten from another process
- CxiLQFkEVVzxlkK.exe (PID: 3708)
- CxiLQFkEVVzxlkK.exe (PID: 3848)
Uses Task Scheduler to run other applications
- CxiLQFkEVVzxlkK.exe (PID: 3708)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1728)
AGENTTESLA was detected
- CxiLQFkEVVzxlkK.exe (PID: 3848)
Actions looks like stealing of personal data
- CxiLQFkEVVzxlkK.exe (PID: 3848)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2248)
- CxiLQFkEVVzxlkK.exe (PID: 3708)
Creates files in the user directory
- CxiLQFkEVVzxlkK.exe (PID: 3708)
- CxiLQFkEVVzxlkK.exe (PID: 3848)
Application launched itself
- CxiLQFkEVVzxlkK.exe (PID: 3708)
Reads the cookies of Google Chrome
- CxiLQFkEVVzxlkK.exe (PID: 3848)
Reads the cookies of Mozilla Firefox
- CxiLQFkEVVzxlkK.exe (PID: 3848)
Checks for external IP
- CxiLQFkEVVzxlkK.exe (PID: 3848)
INFO
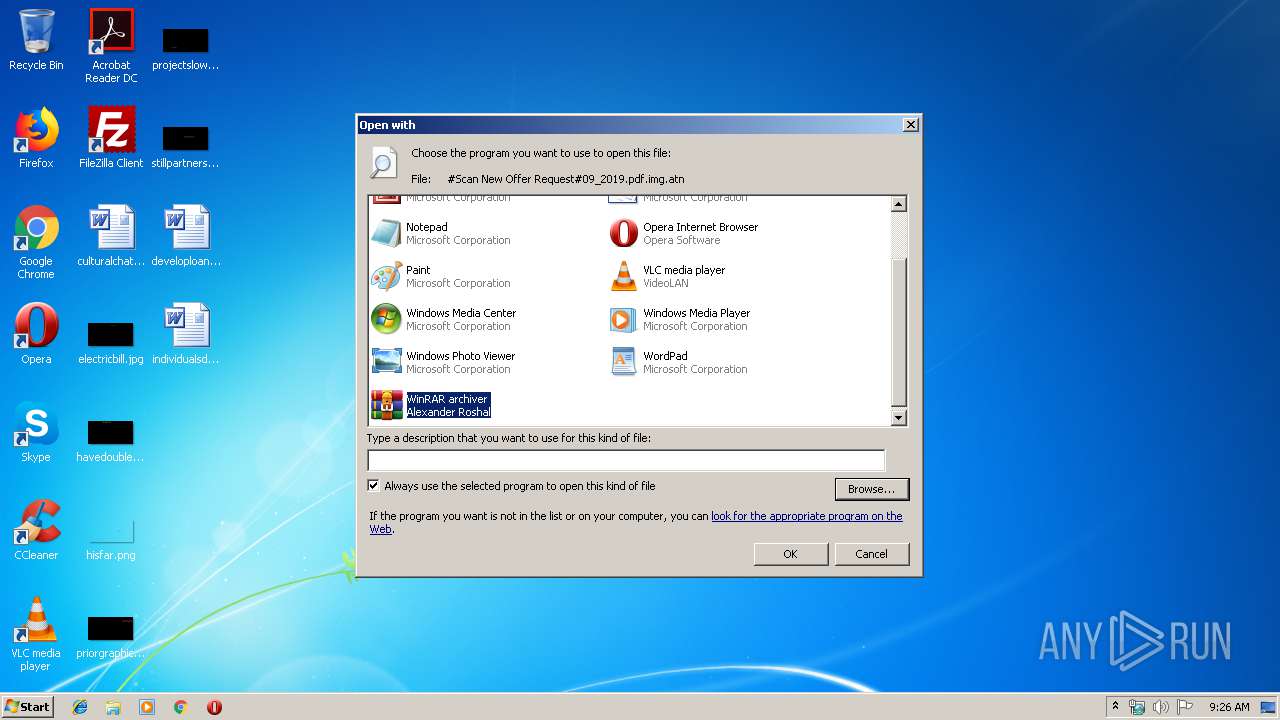
Modifies the open verb of a shell class
- rundll32.exe (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .atn | | | Photoshop Action (37.5) |
|---|---|---|
| .gmc | | | Game Music Creator Music (8.4) |
| .abr | | | Adobe PhotoShop Brush (7.5) |
EXIF
ISO
| VolumeName: | ORDINARY_CRYPTED |
|---|---|
| VolumeBlockCount: | 599 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2019:09:11 02:18:59+01:00 |
| VolumeSetName: | UNDEFINED |
| Software: | IMGBURN V2.5.8.0 - THE ULTIMATE IMAGE BURNER! |
| VolumeCreateDate: | 2019:09:11 02:18:59.00+01:00 |
| VolumeModifyDate: | 2019:09:11 02:18:59.00+01:00 |
Composite
| VolumeSize: | 1198 kB |
|---|
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1728 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\LURTjInTqI" /XML "C:\Users\admin\AppData\Local\Temp\tmpE791.tmp" | C:\Windows\System32\schtasks.exe | — | CxiLQFkEVVzxlkK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
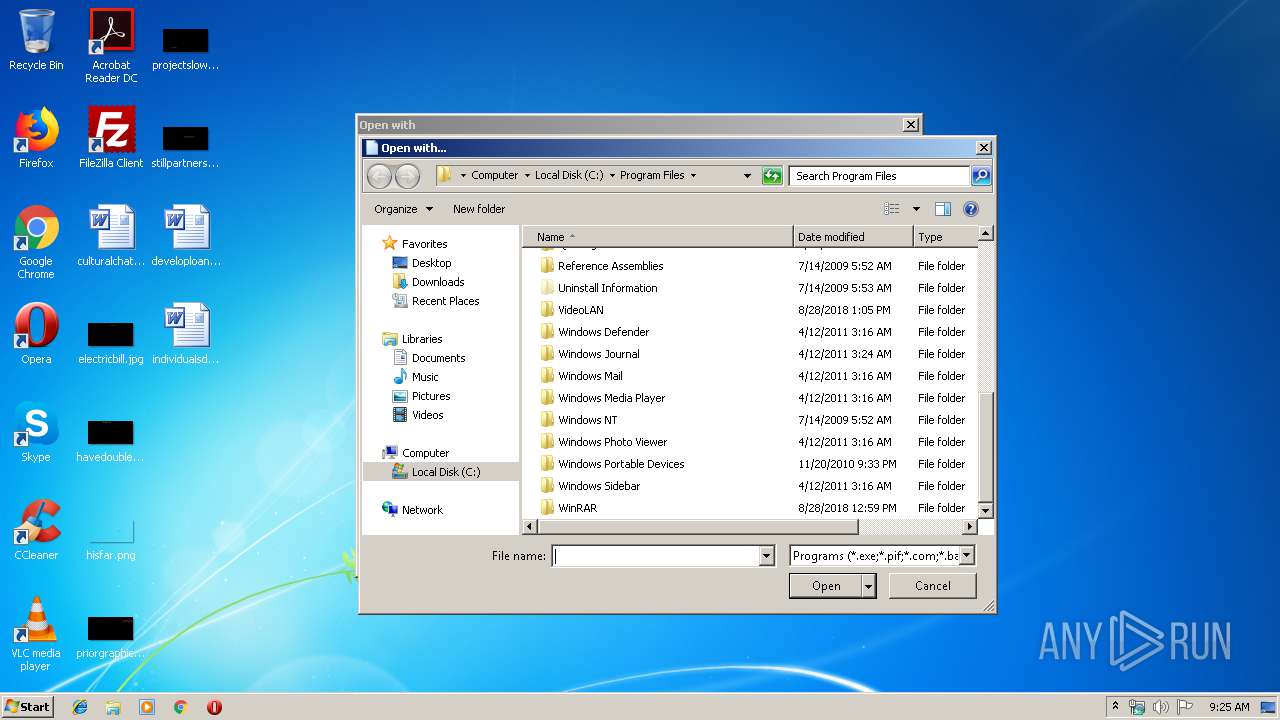
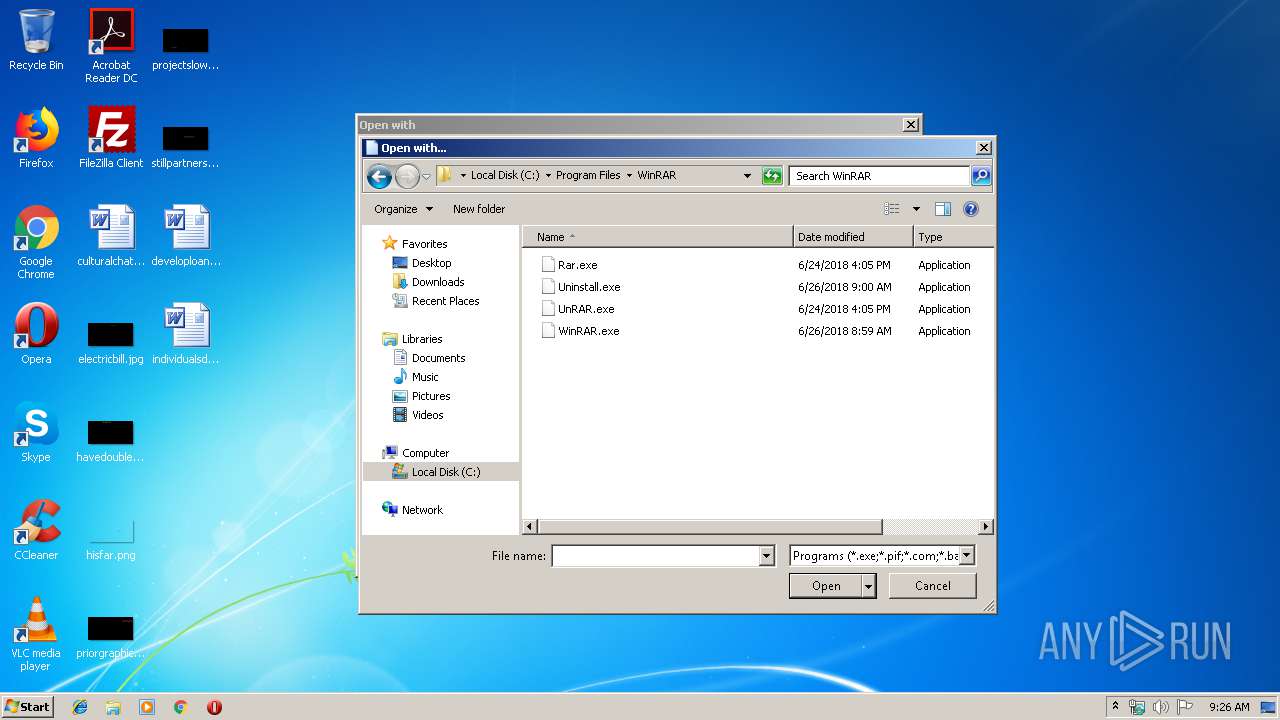
| 2248 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\#Scan New Offer Request#09_2019.pdf.img.atn" | C:\Program Files\WinRAR\WinRAR.exe | rundll32.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
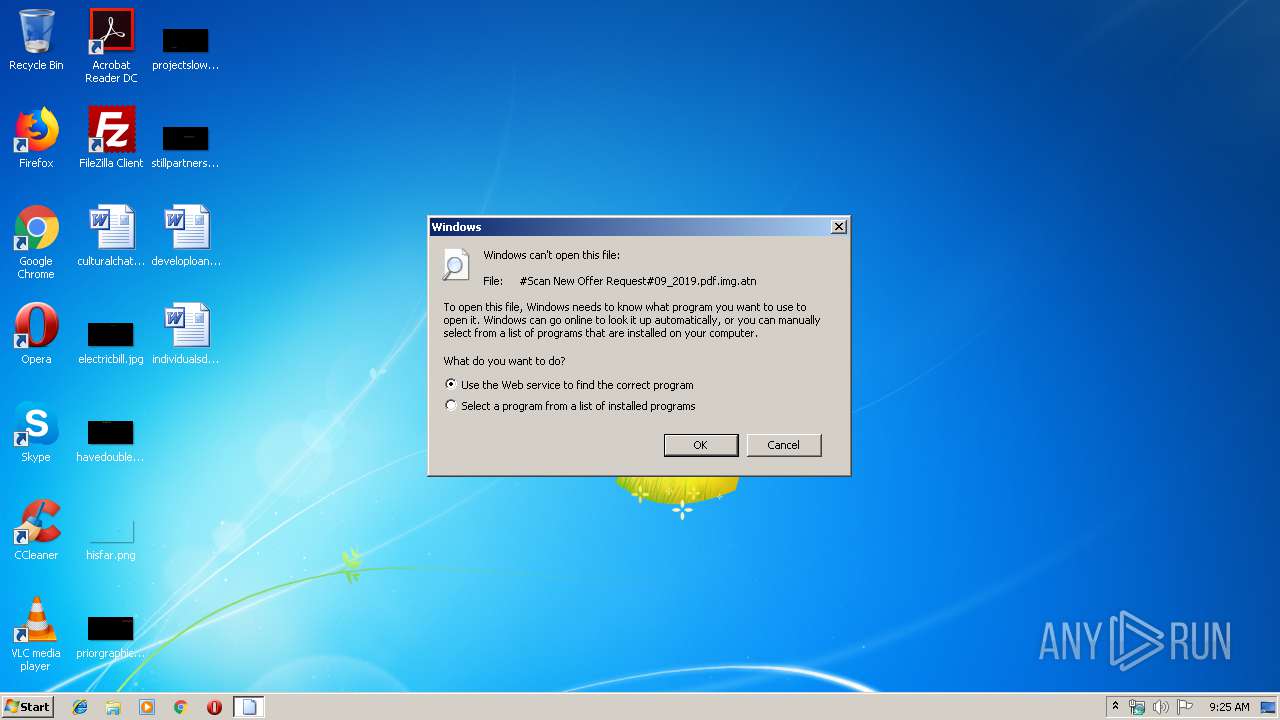
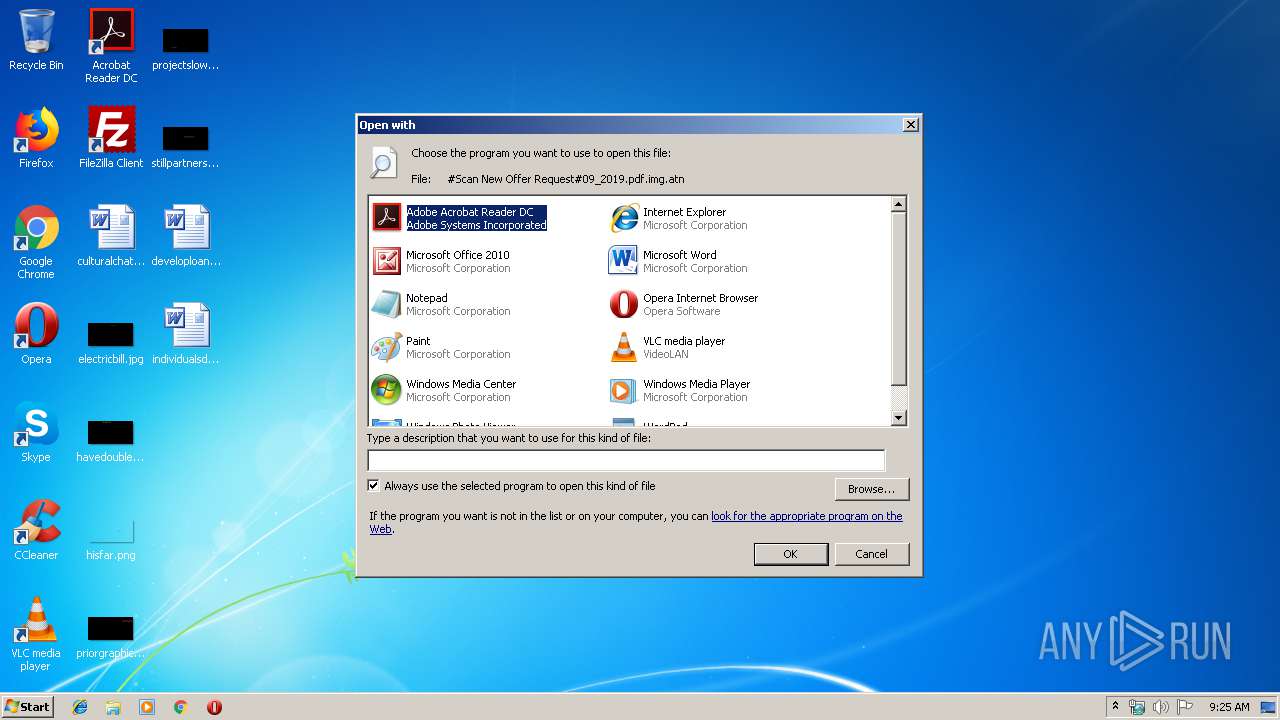
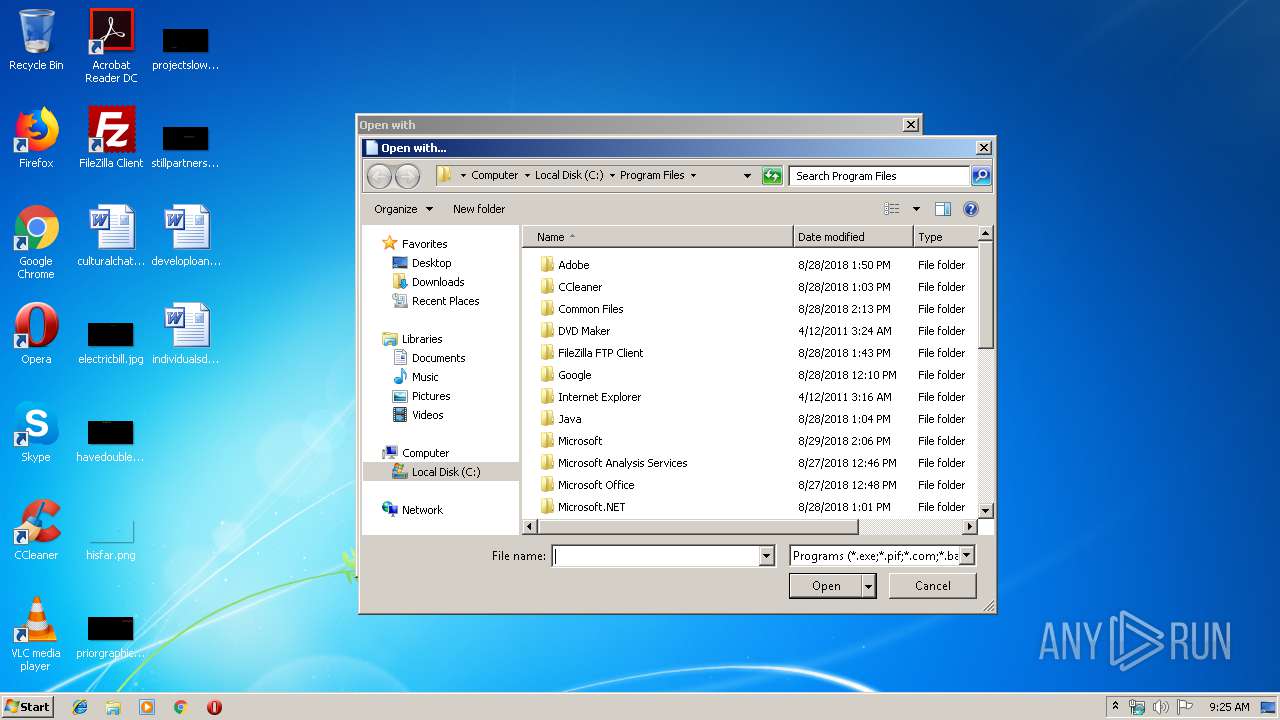
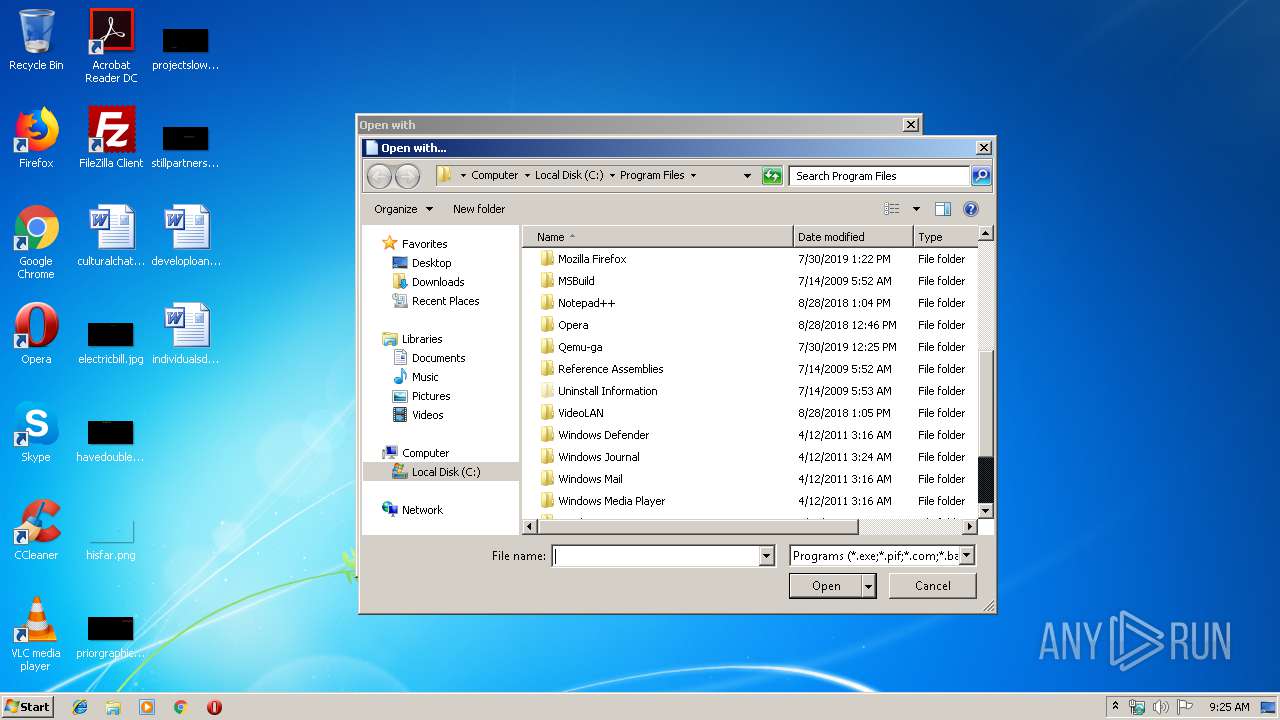
| 2884 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\#Scan New Offer Request#09_2019.pdf.img.atn | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.37912\CxiLQFkEVVzxlkK.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.37912\CxiLQFkEVVzxlkK.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NeuralNetworkFixer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3848 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.37912\CxiLQFkEVVzxlkK.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.37912\CxiLQFkEVVzxlkK.exe | CxiLQFkEVVzxlkK.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NeuralNetworkFixer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 328
Read events
1 161
Write events
166
Delete events
1
Modification events
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\35\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\1 |
| Operation: | write | Name: | 5 |
Value: 50003100000000001C4D655F100057696E52415200003A0008000400EFBE1C4DBC5E1C4D655F2A0000000AC1000000000C000000000000000000000000000000570069006E00520041005200000016000000 | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\1 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000400000003000000010000000000000002000000FFFFFFFF | |||
| (PID) Process: | (2884) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | CxiLQFkEVVzxlkK.exe | C:\Users\admin\AppData\Local\Temp\tmpE791.tmp | — | |
MD5:— | SHA256:— | |||
| 3848 | CxiLQFkEVVzxlkK.exe | C:\Users\admin\AppData\Roaming\wjvd20wg.1pu\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 3848 | CxiLQFkEVVzxlkK.exe | C:\Users\admin\AppData\Roaming\wjvd20wg.1pu\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 3848 | CxiLQFkEVVzxlkK.exe | C:\Users\admin\AppData\Roaming\wjvd20wg.1pu.zip | — | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.37912\CxiLQFkEVVzxlkK.exe | executable | |
MD5:— | SHA256:— | |||
| 3708 | CxiLQFkEVVzxlkK.exe | C:\Users\admin\AppData\Roaming\LURTjInTqI.exe | executable | |
MD5:— | SHA256:— | |||
| 3848 | CxiLQFkEVVzxlkK.exe | C:\Users\admin\AppData\Local\Temp\637037908528415000_38fe29bf-2bc9-42e7-9720-0efe31ca9a06.db | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3848 | CxiLQFkEVVzxlkK.exe | GET | 200 | 52.44.169.135:80 | http://checkip.amazonaws.com/ | US | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | CxiLQFkEVVzxlkK.exe | 52.44.169.135:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3848 | CxiLQFkEVVzxlkK.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2 ETPRO signatures available at the full report