| File name: | 2.ps1 |
| Full analysis: | https://app.any.run/tasks/5e0482f0-dd5f-4ab6-903b-c1611f13f92c |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | January 20, 2022, 20:39:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | FD854C4DE72CCA89BDA6EC7362CB8047 |
| SHA1: | CBC87F189AD4FE16808C3B718720852A16437A2C |
| SHA256: | E219E04F6DDD3EA4A3C3F5DD9251D1E86EA820694246F7E73695427ECEF1E4D6 |
| SSDEEP: | 6144:wWHEnPX+KPg7Ppxbu9d6fnmDVR7YFNQ+UUXd2Jdf6KlPhkXsKwiQ/DaKLP50lu1J:y |
MALICIOUS
REMCOS was detected
- RegAsm.exe (PID: 3876)
Loads dropped or rewritten executable
- powershell.exe (PID: 3052)
SUSPICIOUS
Reads the computer name
- powershell.exe (PID: 3052)
- RegAsm.exe (PID: 3876)
Drops a file that was compiled in debug mode
- powershell.exe (PID: 3052)
Reads the date of Windows installation
- powershell.exe (PID: 3052)
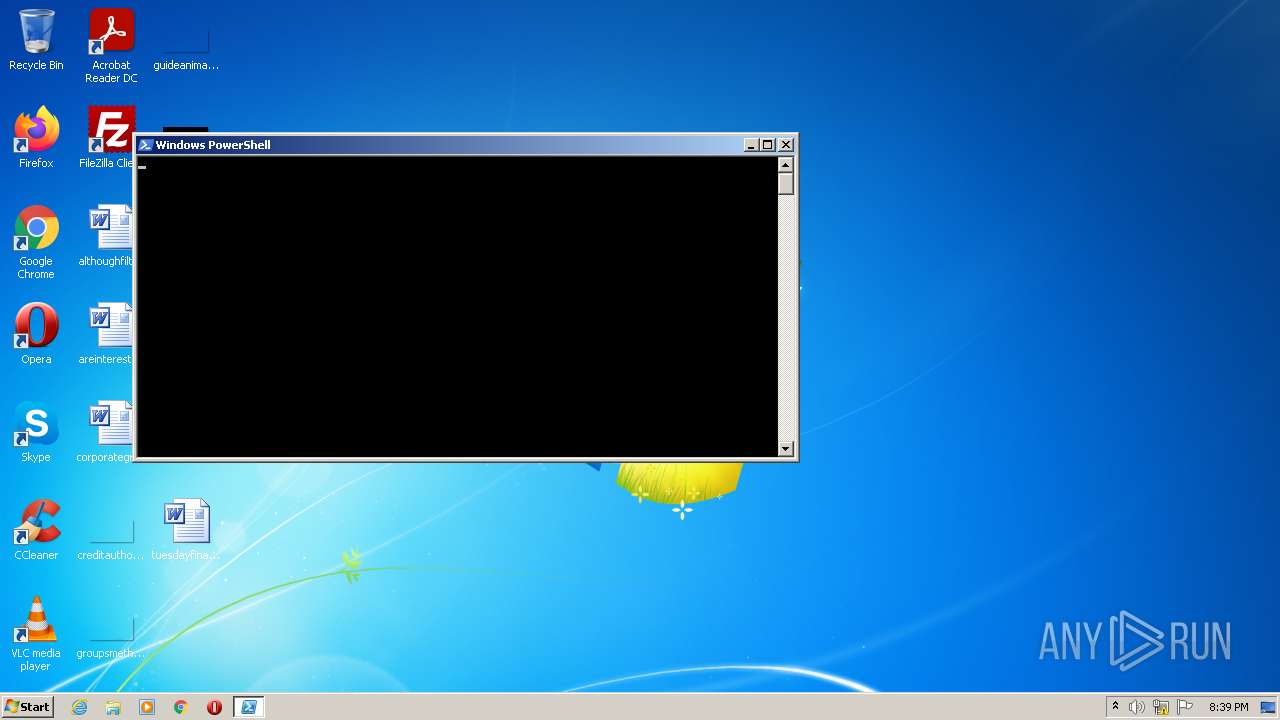
PowerShell script executed
- powershell.exe (PID: 3052)
Checks supported languages
- powershell.exe (PID: 3052)
- RegAsm.exe (PID: 3876)
Creates files in the user directory
- powershell.exe (PID: 3052)
- RegAsm.exe (PID: 3876)
Executable content was dropped or overwritten
- powershell.exe (PID: 3052)
Reads Environment values
- RegAsm.exe (PID: 3876)
Writes files like Keylogger logs
- RegAsm.exe (PID: 3876)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\2.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3876 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
2 796
Read events
2 718
Write events
78
Delete events
0
Modification events
| (PID) Process: | (3052) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3052) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3052) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3052) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3052) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3876) RegAsm.exe | Key: | HKEY_CURRENT_USER\Software\JANBUILD-STZUMV |
| Operation: | write | Name: | exepath |
Value: 740C637515544928E4DF95F93076DDC988002584295522DCEC645B3F4627C86A4C383D2EEA9C1DC4F9449FC614F9DB692AEB05223E84956009D1E5A0EBD902EF78D6BA58543DB0147C7F8B1BCCECD5EB2BA9356D6F7C5B2B96D3084510C669F1D84838E21BC69DFA5B9A2A4F404983587596 | |||
| (PID) Process: | (3876) RegAsm.exe | Key: | HKEY_CURRENT_USER\Software\JANBUILD-STZUMV |
| Operation: | write | Name: | licence |
Value: FDA2A20782EBD0A0B1004D41F9A29296 | |||
Executable files
2
Suspicious files
6
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:633630D4B472E897D6FE7BDB27290365 | SHA256:0598A41B7BB73CF24BBC7AA4D62A61997ACD589555C045DBFEE9D2F1E6008B32 | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF193791.TMP | binary | |
MD5:CCFCF369F751CE8DA0370D84E52A7EED | SHA256:53922490C3F5A04667EC3605A01AF2A4F4F265782D1BCA519F63ACAD413F2ED9 | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2F0HUFFJML0EUY20JRO1.temp | binary | |
MD5:633630D4B472E897D6FE7BDB27290365 | SHA256:0598A41B7BB73CF24BBC7AA4D62A61997ACD589555C045DBFEE9D2F1E6008B32 | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\e0e22da2-dbf8-4303-b7f9-7620a5e9f357\AgileDotNetRT.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
| 3876 | RegAsm.exe | C:\Users\admin\AppData\Roaming\JANBUILD\logs.dat | binary | |
MD5:644593583D2D646FB6C81798466601A1 | SHA256:FD98767F454CCFAD549C31DEAD052D53781124917A4C83A52F379744BE1ECB82 | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ac5c1527-e43f-46b1-9587-143b0e06e0d9\AgileDotNetRT.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\oslp5o4q.vyb.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\fxdexqao.pyf.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
94
DNS requests
99
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3876 | RegAsm.exe | 103.231.91.59:39207 | saptransmissions.dvrlists.com | Intergrid Group Pty Ltd | AU | malicious |
— | — | 103.231.91.59:39207 | saptransmissions.dvrlists.com | Intergrid Group Pty Ltd | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
saptransmissions.dvrlists.com |
| malicious |
dns.msftncsi.com |
| shared |