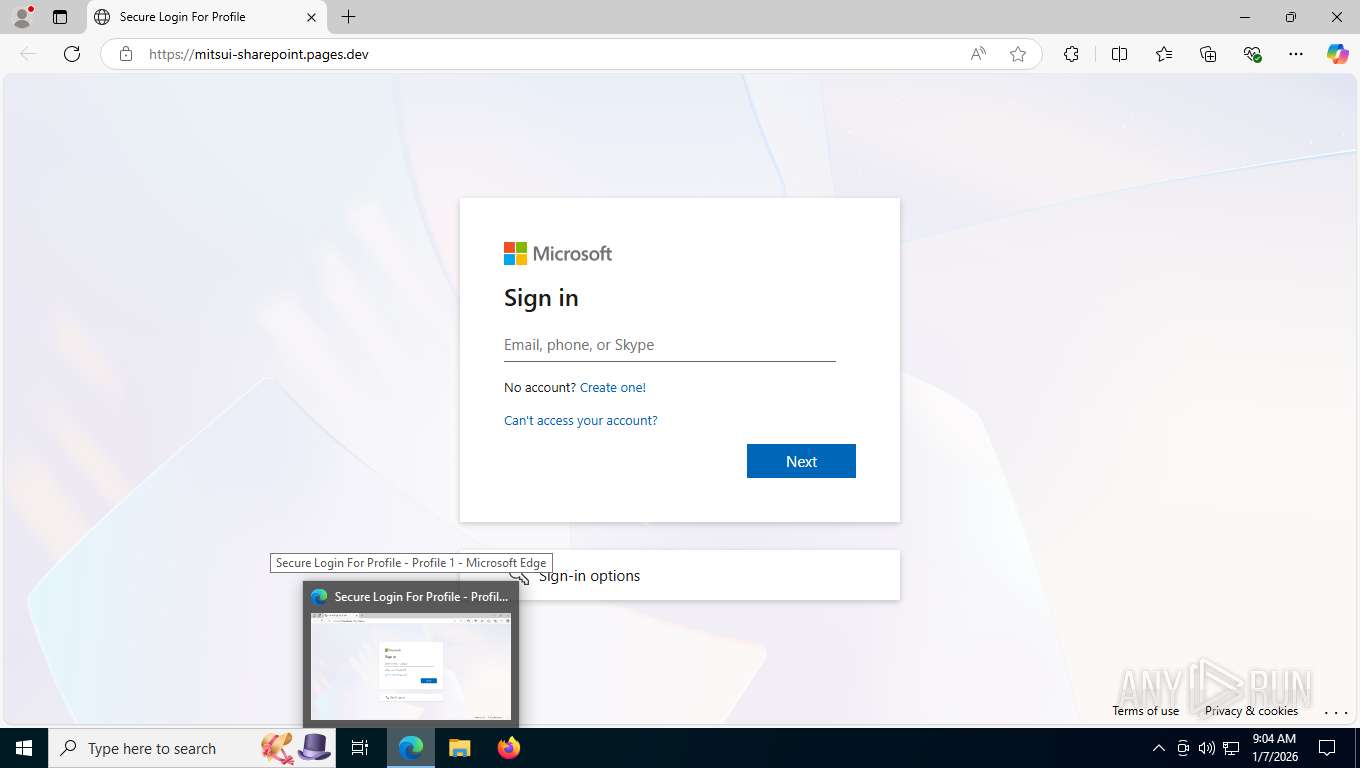
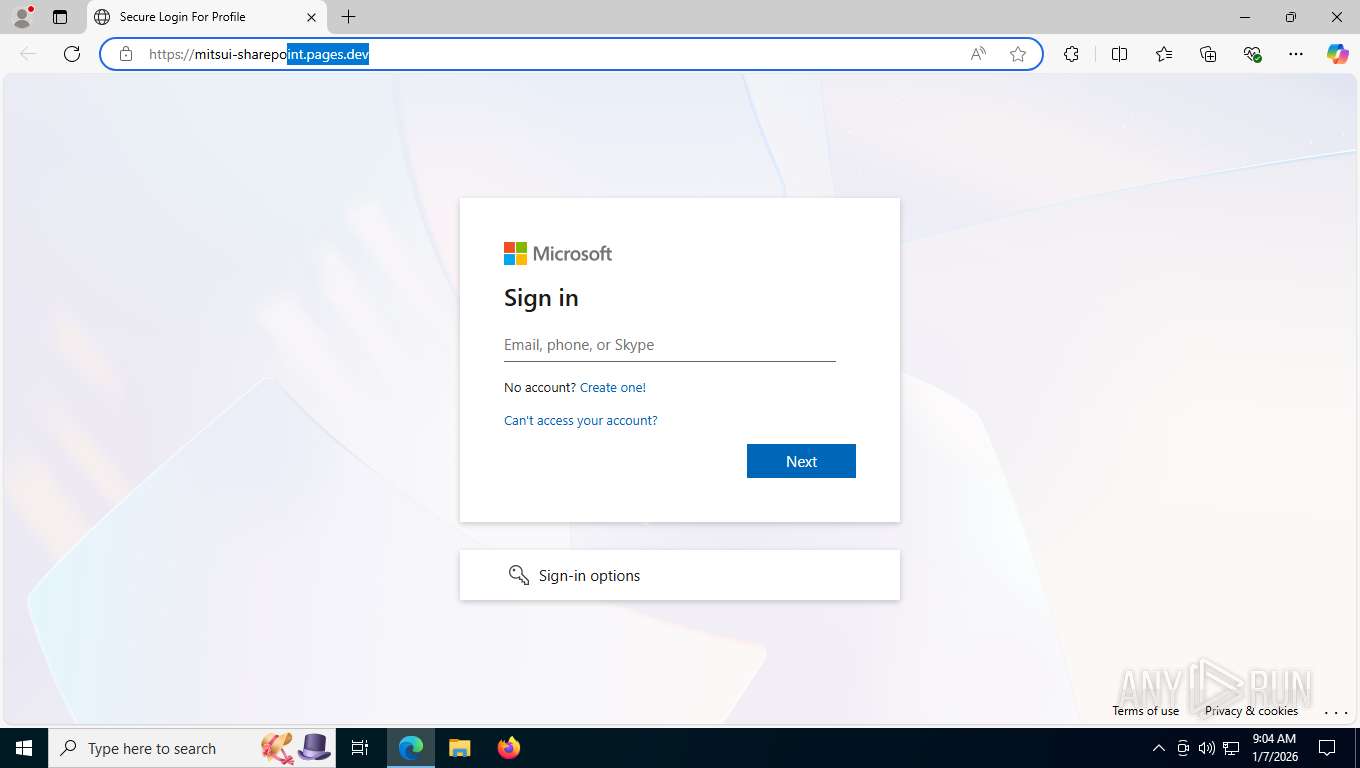
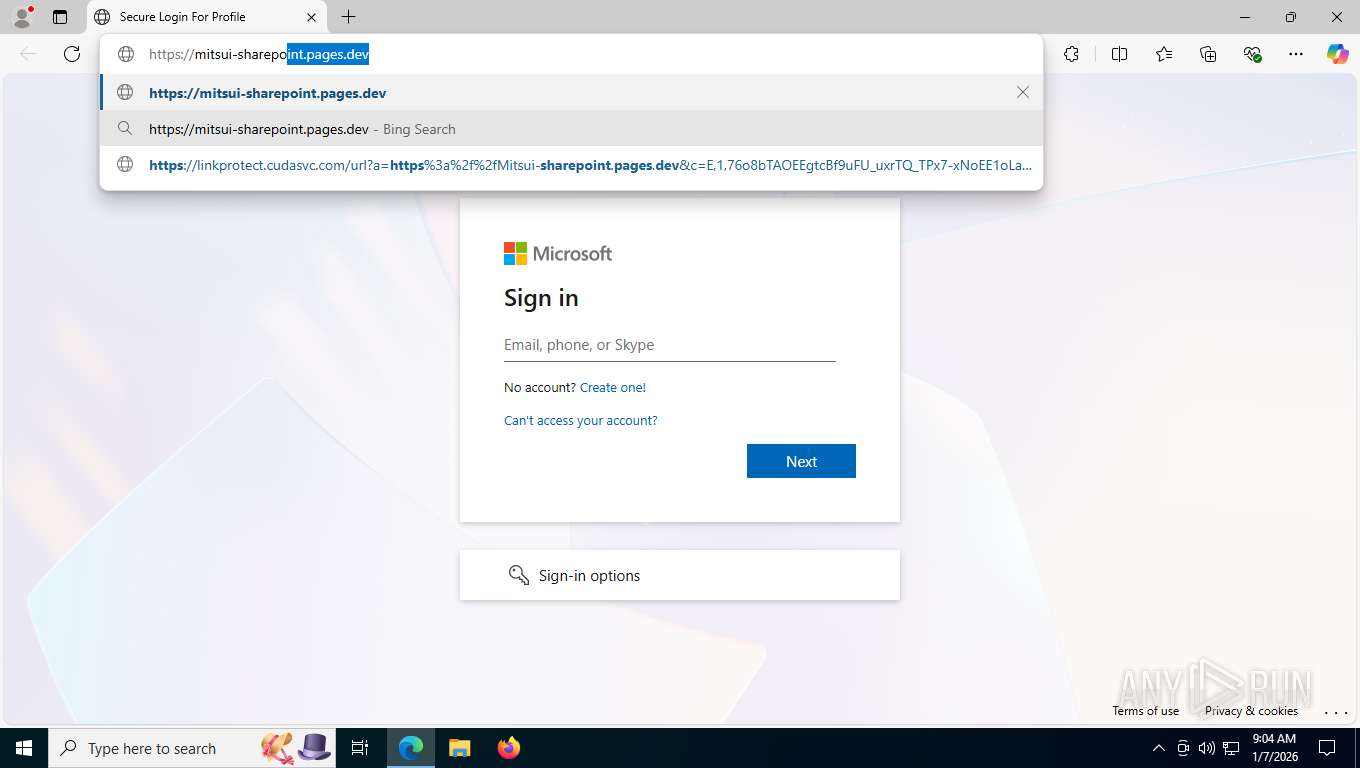
| URL: | https://linkprotect.cudasvc.com/url?a=https%3a%2f%2fMitsui-sharepoint.pages.dev&c=E,1,76o8bTAOEEgtcBf9uFU_uxrTQ_TPx7-xNoEE1oLa9nGXCndzL8kbj1rAP6WNCkNkhC6bMOdJpGvqN_uA77tbynTfKI2ItZ5o3wa1z0pygdKvd7mkGxKi5TwF1A,,&typo=1&ancr_add=1 |
| Full analysis: | https://app.any.run/tasks/b3624827-0b9e-44cc-bd96-06edc71ad668 |
| Verdict: | Malicious activity |
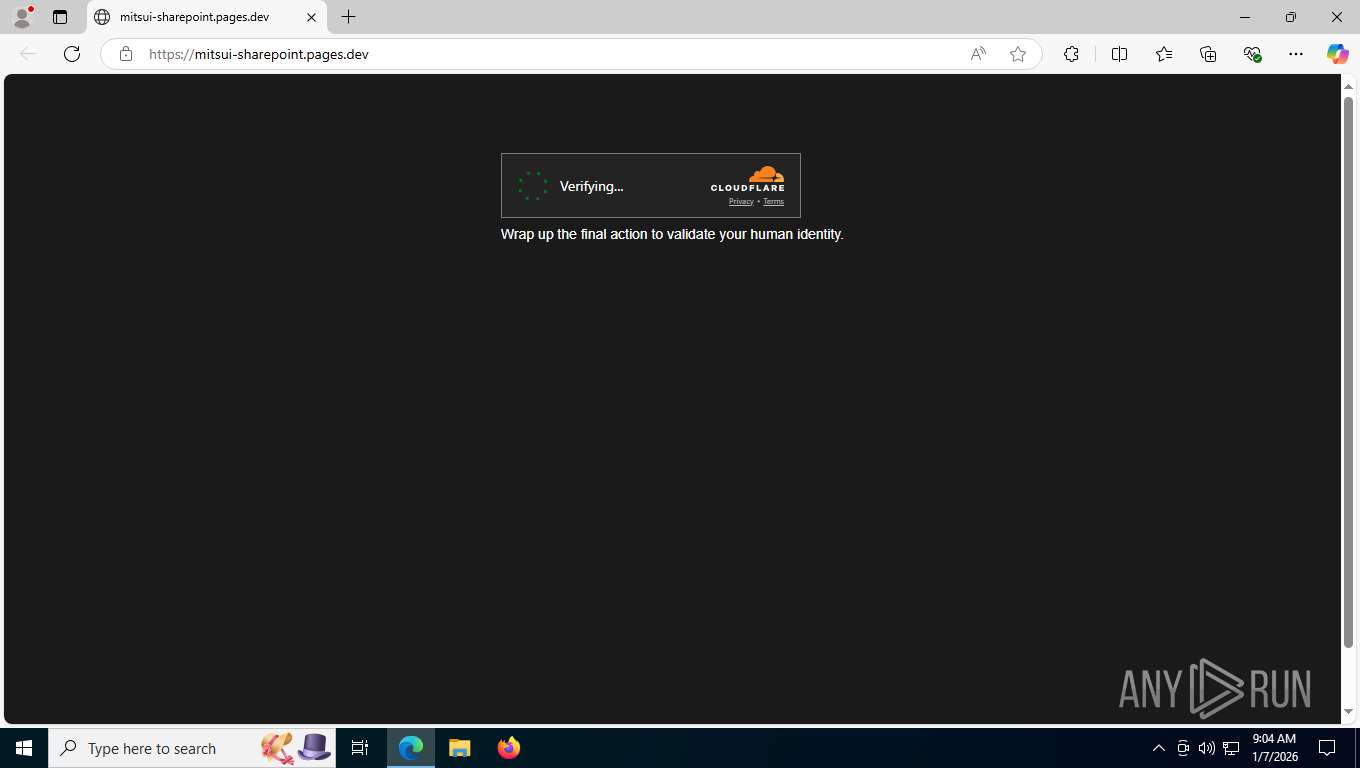
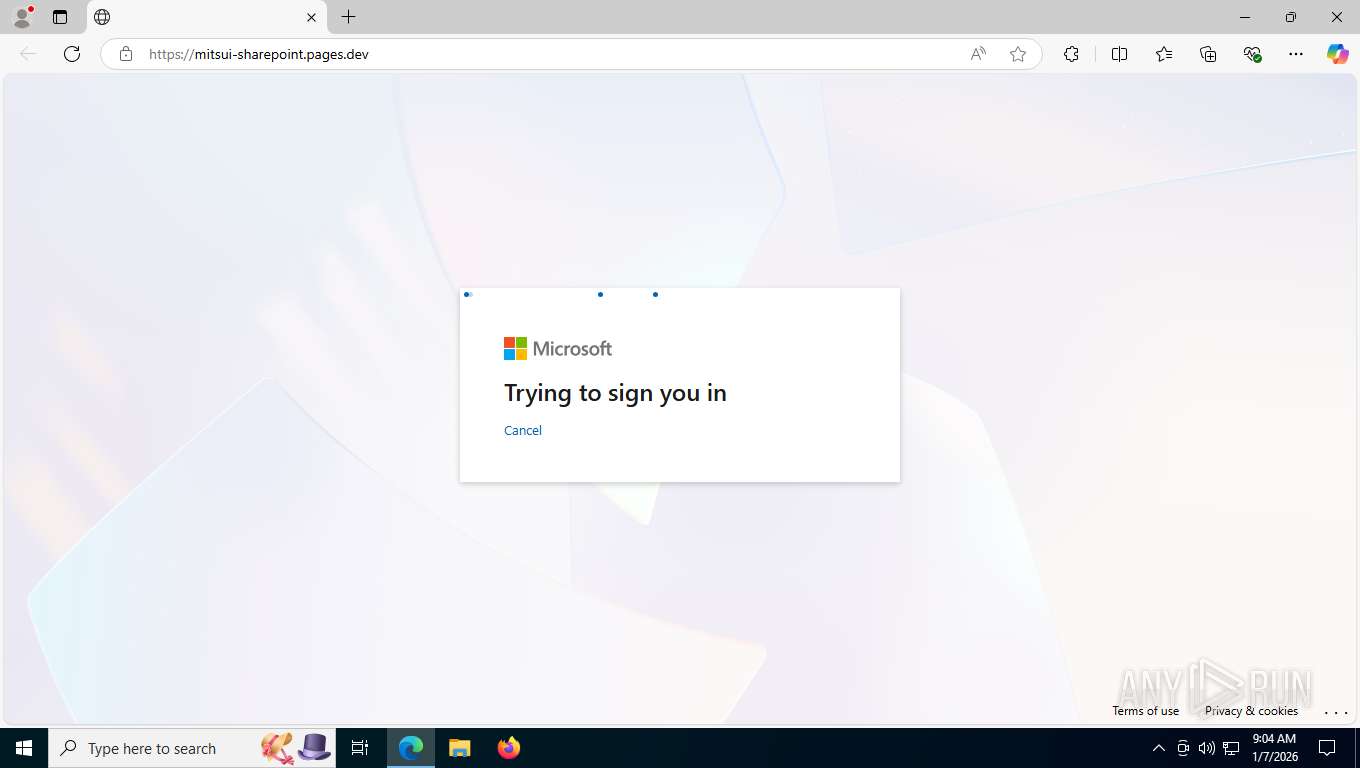
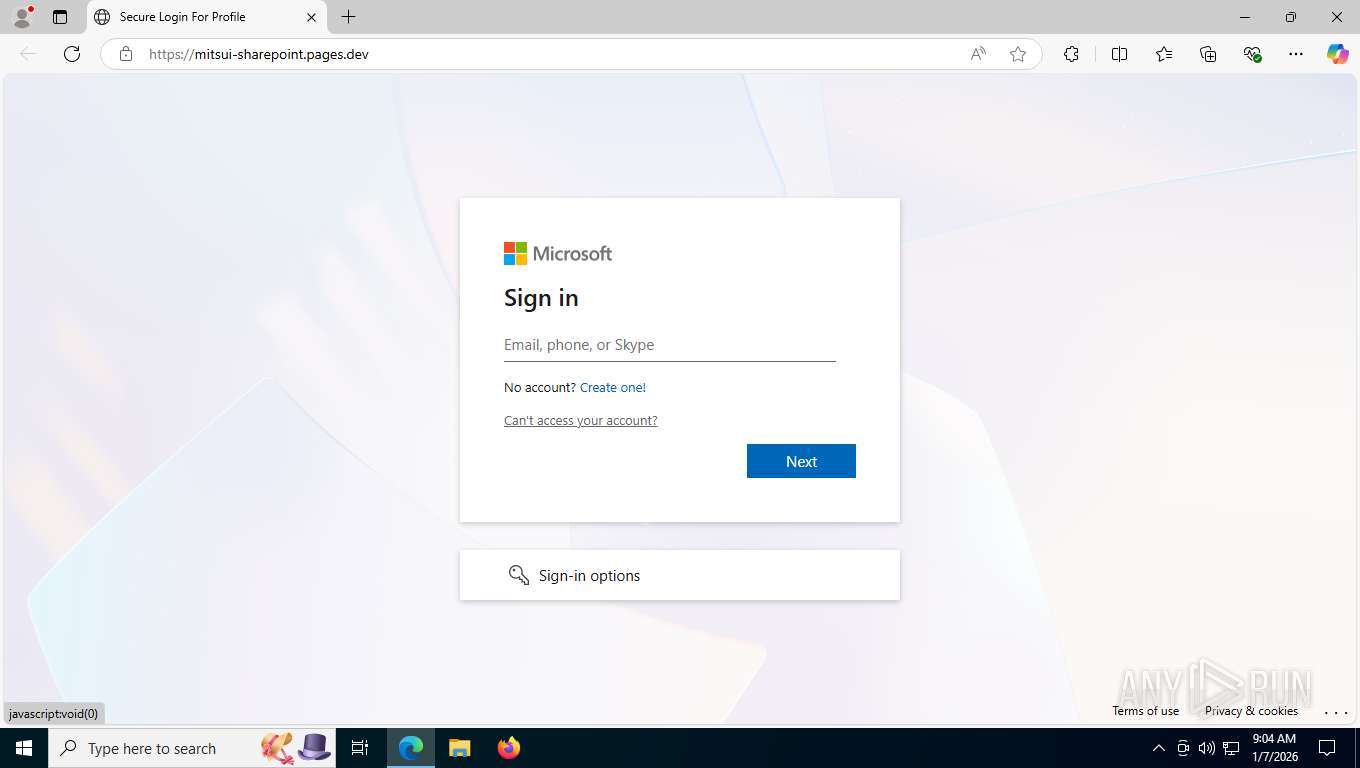
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | January 07, 2026, 14:04:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 54F66C166C5332605F751AD34DE1A8A8 |
| SHA1: | 3742BF54E208391FE7E025DF8E183D79F32E42FD |
| SHA256: | E1F7F96A30170A6518AA093B2913DF27D034E8A0A059F6C18EE622C386DA81A2 |
| SSDEEP: | 6:2MBts8MTBoAgAQE1AqIP1fr7geI5TO8pLhGlnZgb:2MtMRg3xr7qhB2Zgb |
MALICIOUS
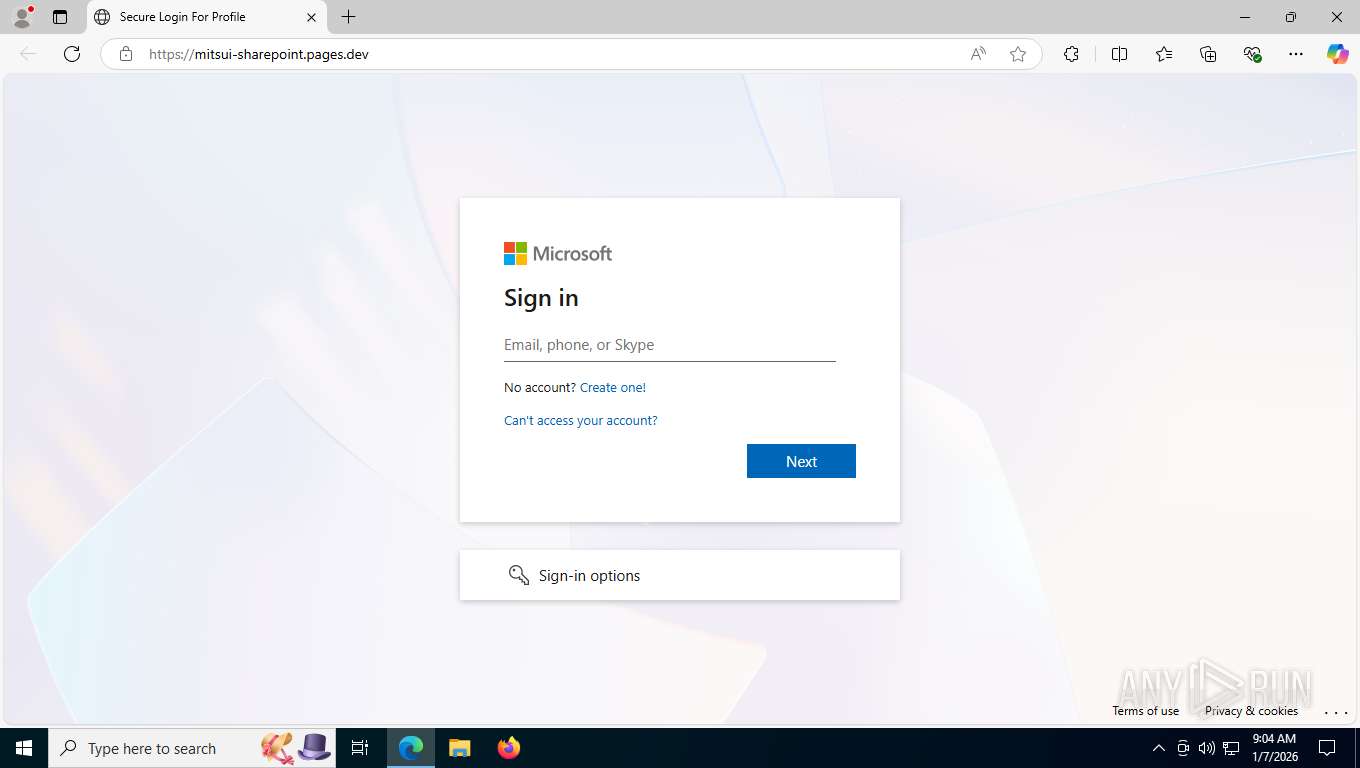
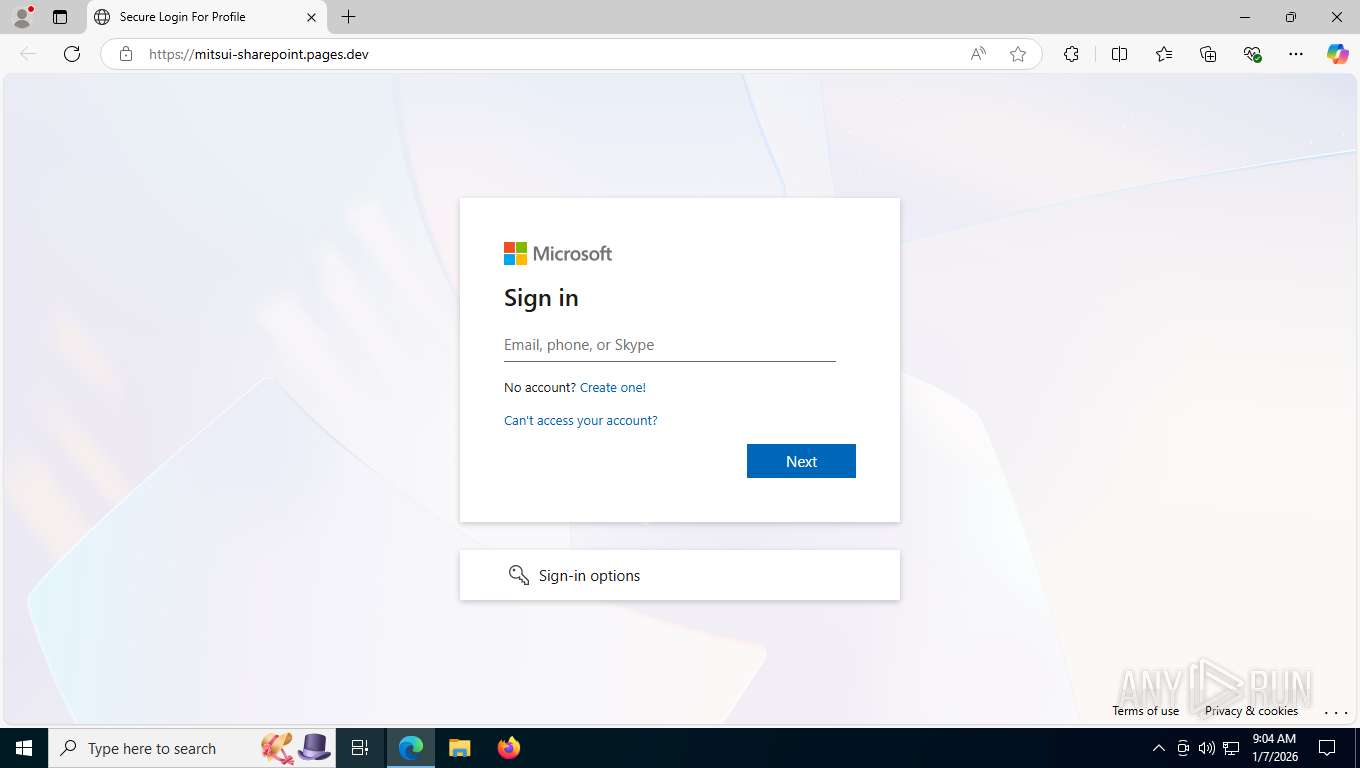
Tycoon 2FA phishing kit has been detected
- msedge.exe (PID: 7484)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7820)
Fake Microsoft Authentication Page has been detected
- msedge.exe (PID: 7484)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- msedge.exe (PID: 7484)
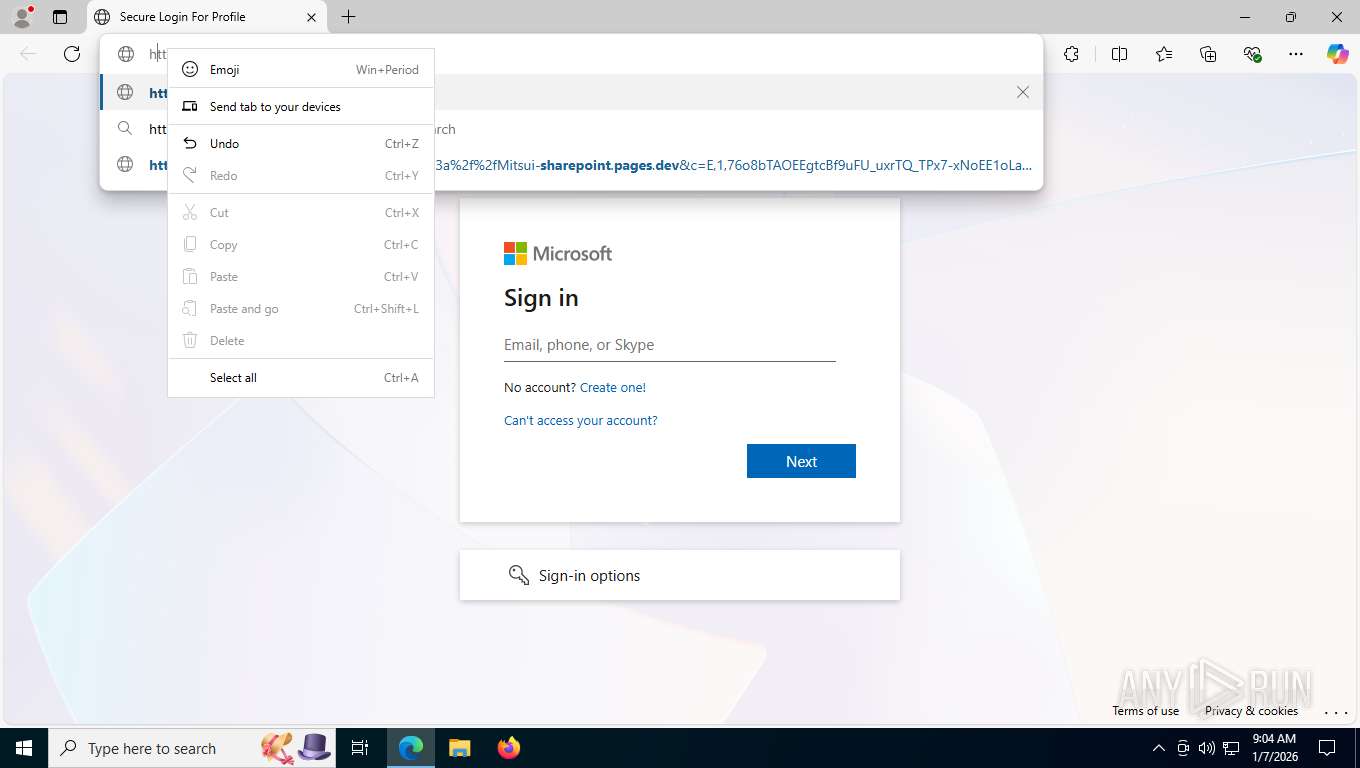
Context menu (right-click) prevention is present
- msedge.exe (PID: 7484)
Checks supported languages
- identity_helper.exe (PID: 7204)
- TextInputHost.exe (PID: 9164)
Reads the computer name
- TextInputHost.exe (PID: 9164)
- identity_helper.exe (PID: 7204)
Reads Environment values
- identity_helper.exe (PID: 7204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
170
Monitored processes
26
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5504,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=5408 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5768,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=5836 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5408 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5760,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=5764 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5852,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=6300 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6204,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=6332 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6892 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6508,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=6556 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 7088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5140,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=5176 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 7204 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6508,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=6556 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 7236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5300,i,16102558954099743178,9192025961129723529,262144 --variations-seed-version --mojo-platform-channel-handle=4536 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
1 227
Read events
1 223
Write events
3
Delete events
1
Modification events
| (PID) Process: | (9164) TextInputHost.exe | Key: | \REGISTRY\A\{3021a009-2457-28b5-67a3-cf33a622dc95}\LocalState |
| Operation: | write | Name: | CategorySetMRU_CategorySet.ExpressiveEmoji.Common |
Value: 300009003DD80ADE0A00300009003DD802DE0A00300009003ED823DD0A003000090064270A00300009003DD80DDE0A00300009003DD812DE0A00300009003DD84CDC0A00300009003DD818DE0A00300009003DD895DC0A00300009003DD801DE0A00300009003DD84DDC0A00300009003DD84CDE0A00300009003ED826DD0D2040260FFE0A00300009003ED826DD0D2042260FFE0A00300009003ED837DD0D2040260FFE0A00300009003ED837DD0D2042260FFE0A00300009000C270A00300009003ED81EDD0A00300009003DD809DE0A00300009003DD80EDE0A00300009003CD8B6DF0A00300009003DD822DE0A00300009003DD896DC0A00300009003DD81CDE0A00300009003DD84FDC0A00300009003DD88BDC0A00300009003CD839DF0A00300009003CD889DF0A00300009003CD882DF0A00300009003ED833DD0A00300009003DD831DC0D203DD864DC0A00300009003DD831DC0D203CD8CDDF0A00300009003DD831DC0D203DD8BBDC0A00300009003DD831DC0D203DD809DC0A00300009003DD831DC0D203DD853DC0A00300009003DD831DC0D203DD880DE0A003000090014270A00300009003DD840DC0A00300009003DD803DE0A003000090028270A00300009003DD806DE0A00300009003ED814DD0A00300009003ED822DD0A00300009003CD881DF0000E3636294DE7FDC01 | |||
| (PID) Process: | (9164) TextInputHost.exe | Key: | \REGISTRY\A\{3021a009-2457-28b5-67a3-cf33a622dc95}\LocalState |
| Operation: | write | Name: | CategorySetMRU_CategorySet.Kaomoji.Common |
Value: 3000090028004127B400E1256000412729000A00300009002800CF252700E1252700CF2529000A0030000900702528002A00B000BD25B0002A0029006F250A003000090006262A003A0020002E0061FF2E0020006F0028006722BD25662229006F0020002E0061FF2E003A002A0006260A003000090028002A002F00C9033CFF2A0029000A003000090028005E002F002F002F005E0029000A00300009003A002D0029000A00300009005E005F005E000A00300009003A002D0044000A0030000900DA140F16E2150A003000090028002C252C254FFE2C252C2529000A0030000900A50C5F00A50C0A0030000900A00C5F00A00C0A003000090028006F25B000A125B00009FF6F2535FE20003B2501253B250A003000090028002000B40065FF65FF290089FF28002E005F002E00600029000A00300009003C0F200064302000D5255F00D52520003D0F64300A00300009002800C90243FEC90229000A0030000900280022205F00222029000A00300009003A002D0028000A00300009003A002D0050000A00300009003B002D0029000A00300009002800200022205F00222029003E001023A0252D00A0250A003000090028001023A0255F00A02529000A003000090028001E269FFFEE309FFF29001E260A00300009001C2628009FFFEE309FFF1C2629000A00300009002800AC003F20AC0029000A00300009002800AC005F00AC00200029000A0030000900AF005C005F002800C43029005F002F00AF000A0030000900280054005F00540029000A0030000900280099225F0099223B0029000000D1FB6394DE7FDC01 | |||
| (PID) Process: | (9164) TextInputHost.exe | Key: | \REGISTRY\A\{3021a009-2457-28b5-67a3-cf33a622dc95}\LocalState |
| Operation: | delete value | Name: | CategorySetMRU_CategorySet.Symbols.Common |
Value: | |||
| (PID) Process: | (9164) TextInputHost.exe | Key: | \REGISTRY\A\{3021a009-2457-28b5-67a3-cf33a622dc95}\LocalState |
| Operation: | write | Name: | CurrentSkinTone |
Value: 00000000A7226494DE7FDC01 | |||
Executable files
0
Suspicious files
33
Text files
245
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe248.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe258.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe258.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfe258.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe258.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
80
DNS requests
81
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7820 | msedge.exe | GET | 302 | 104.18.95.41:443 | https://challenges.cloudflare.com/turnstile/v0/api.js?render=explicit | US | — | — | unknown |
7820 | msedge.exe | GET | 302 | 104.18.94.41:443 | https://challenges.cloudflare.com/turnstile/v0/api.js?render=explicit | US | — | — | unknown |
7820 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dKx5ic4PsmnECkKsgjw3tM_EQI8D4n01W1VZ3o71x0I&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
7820 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
7820 | msedge.exe | GET | 200 | 188.114.96.3:443 | https://mitsui-sharepoint.pages.dev/ | US | html | 128 Kb | unknown |
7820 | msedge.exe | GET | 302 | 18.158.233.156:443 | https://linkprotect.cudasvc.com/url?a=https%3a%2f%2fMitsui-sharepoint.pages.dev&c=E,1,76o8bTAOEEgtcBf9uFU_uxrTQ_TPx7-xNoEE1oLa9nGXCndzL8kbj1rAP6WNCkNkhC6bMOdJpGvqN_uA77tbynTfKI2ItZ5o3wa1z0pygdKvd7mkGxKi5TwF1A,,&typo=1&ancr_add=1 | US | html | 138 b | unknown |
7820 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7820 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7820 | msedge.exe | GET | 200 | 142.251.140.170:443 | https://fonts.googleapis.com/css2?family=Inter:wght@400;600&display=swap | US | text | 4.83 Kb | whitelisted |
7820 | msedge.exe | GET | 200 | 104.18.95.41:443 | https://challenges.cloudflare.com/turnstile/v0/b/88d68f5d5ea3/api.js | US | text | 48.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6788 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7820 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7820 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7820 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7820 | msedge.exe | 18.158.233.156:443 | linkprotect.cudasvc.com | AMAZON-02 | US | whitelisted |
7820 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
linkprotect.cudasvc.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
mitsui-sharepoint.pages.dev |
| unknown |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
7820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
7820 | msedge.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
7820 | msedge.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
7820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7820 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (challengepages) |
7820 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (challengepages) |
7820 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7820 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (challengepages) |