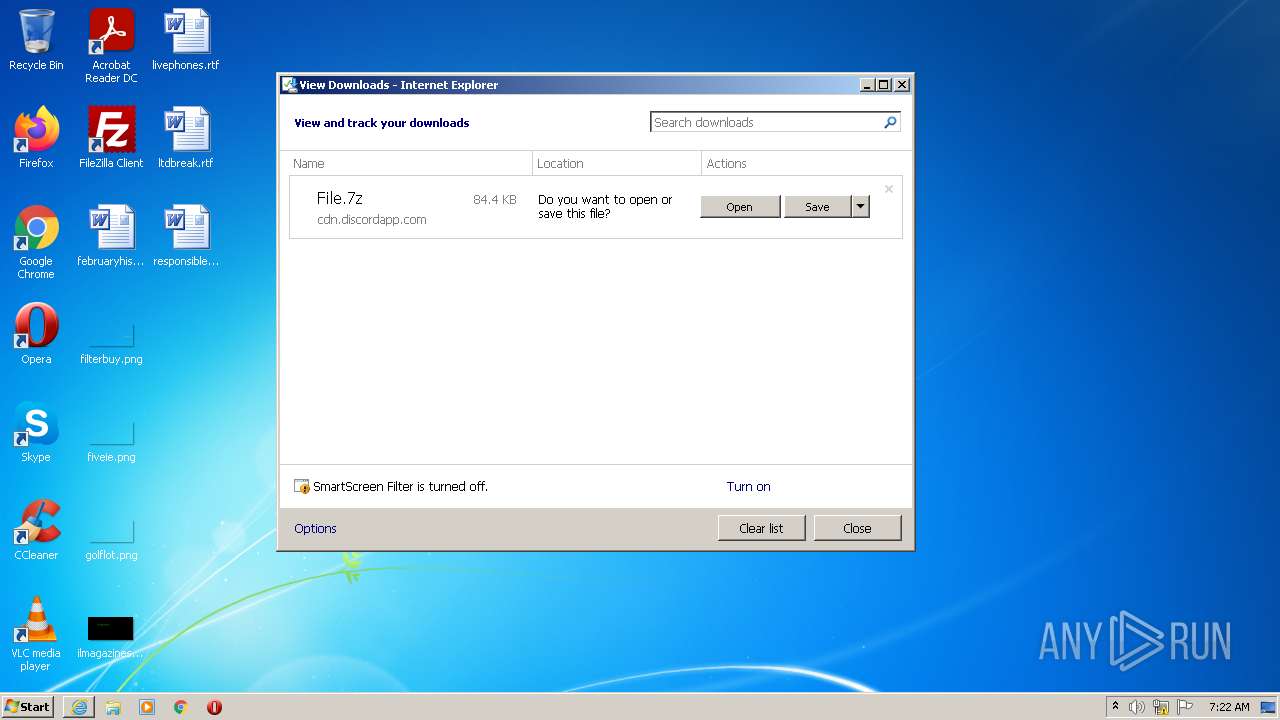
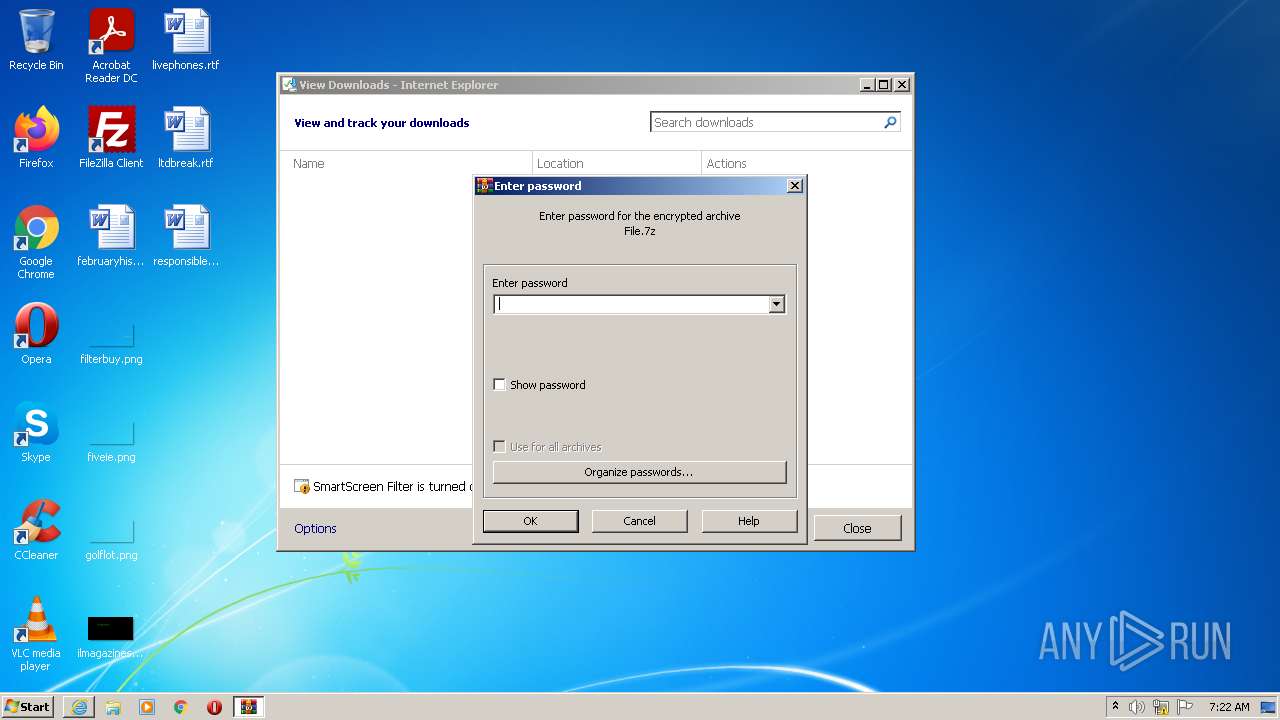
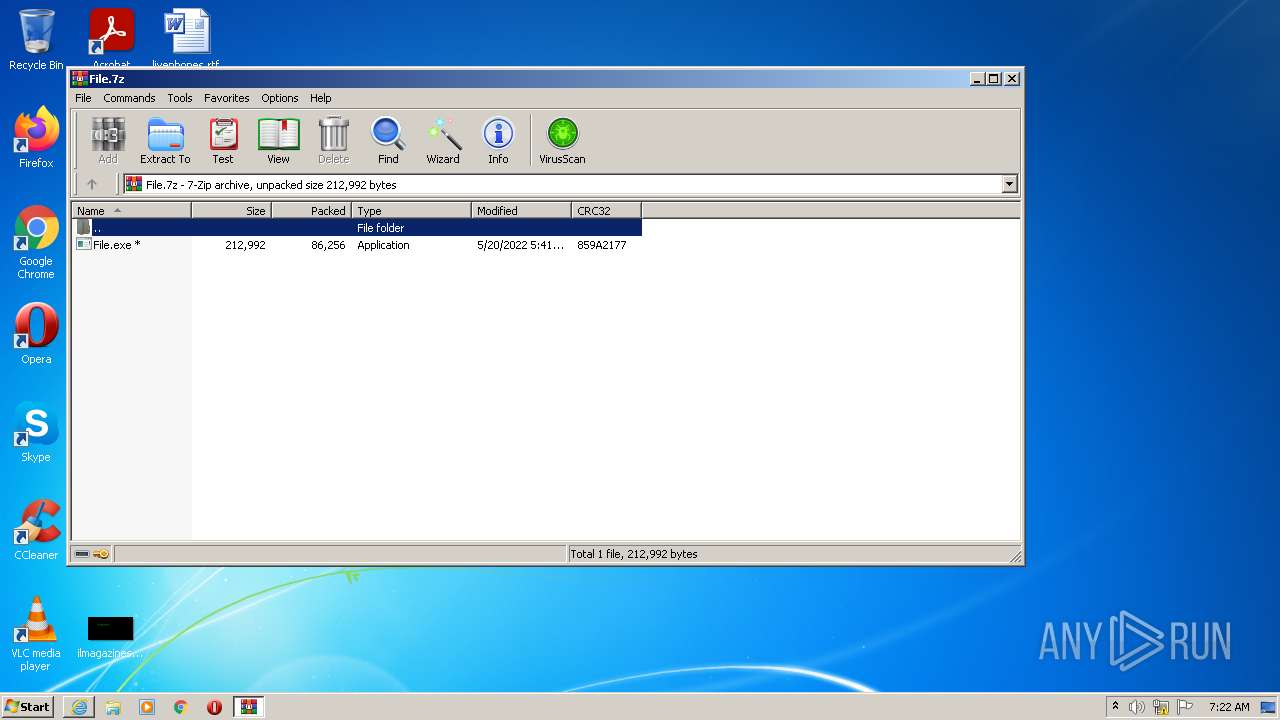
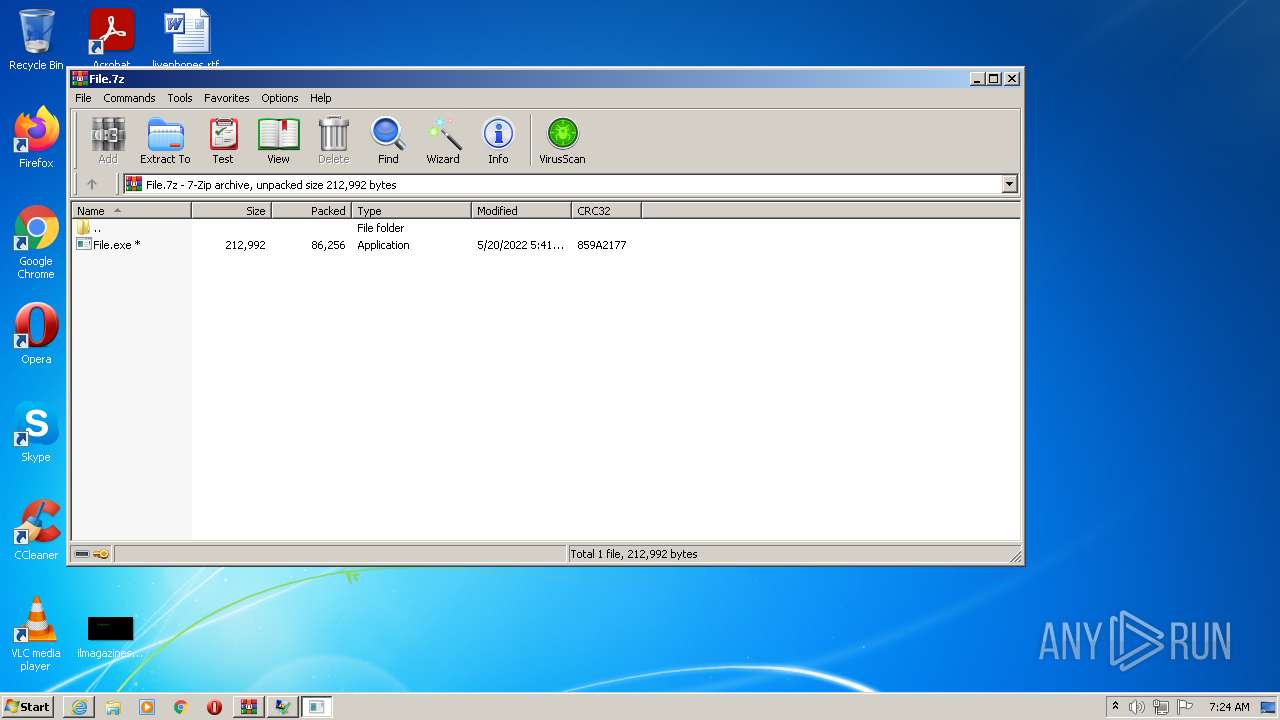
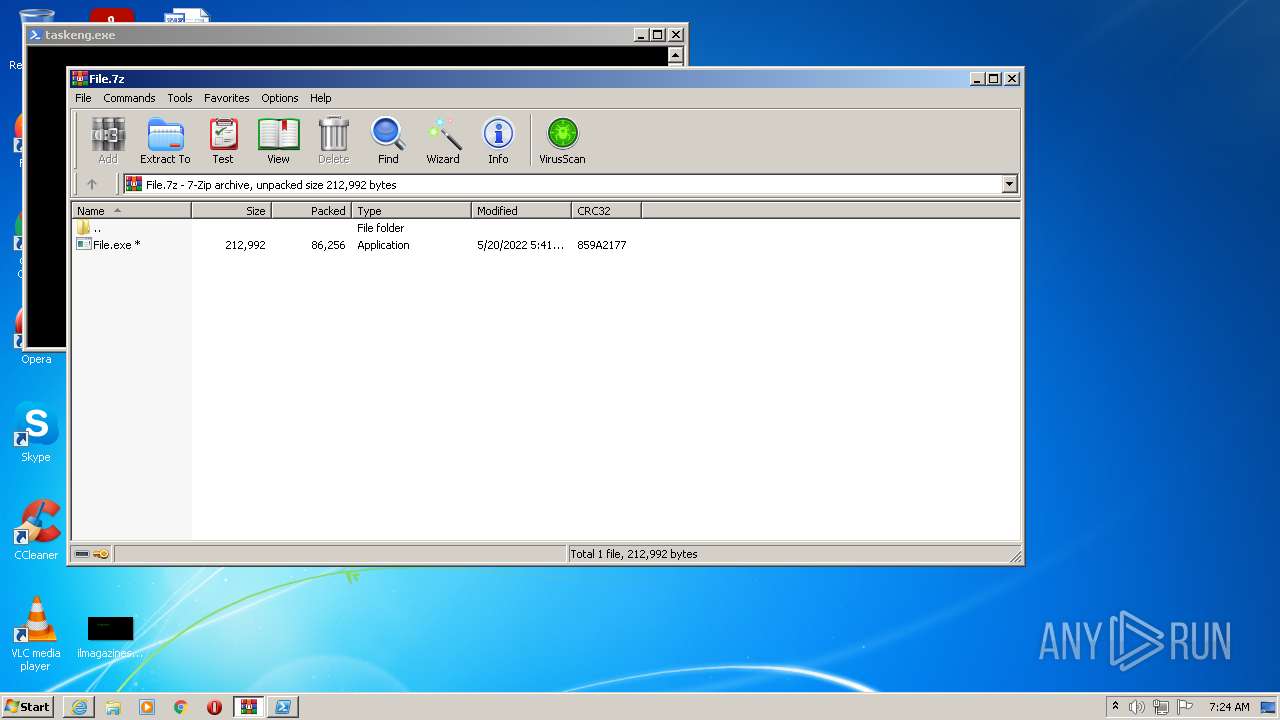
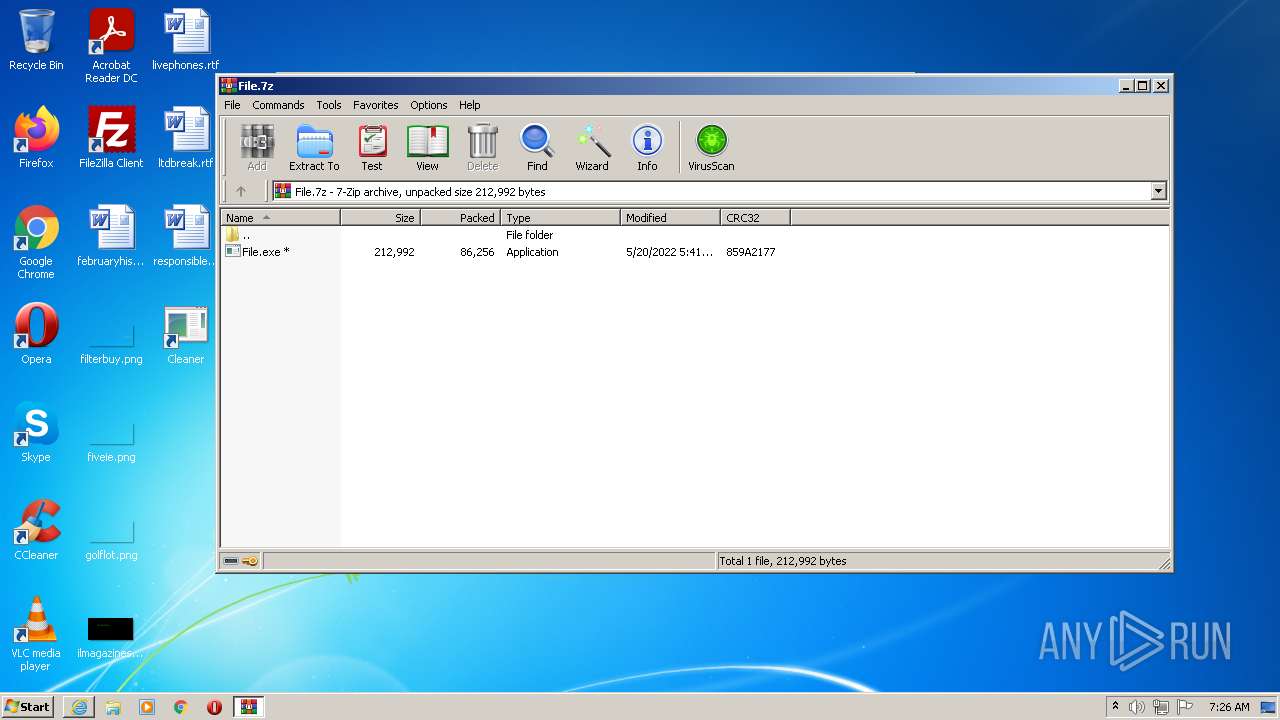
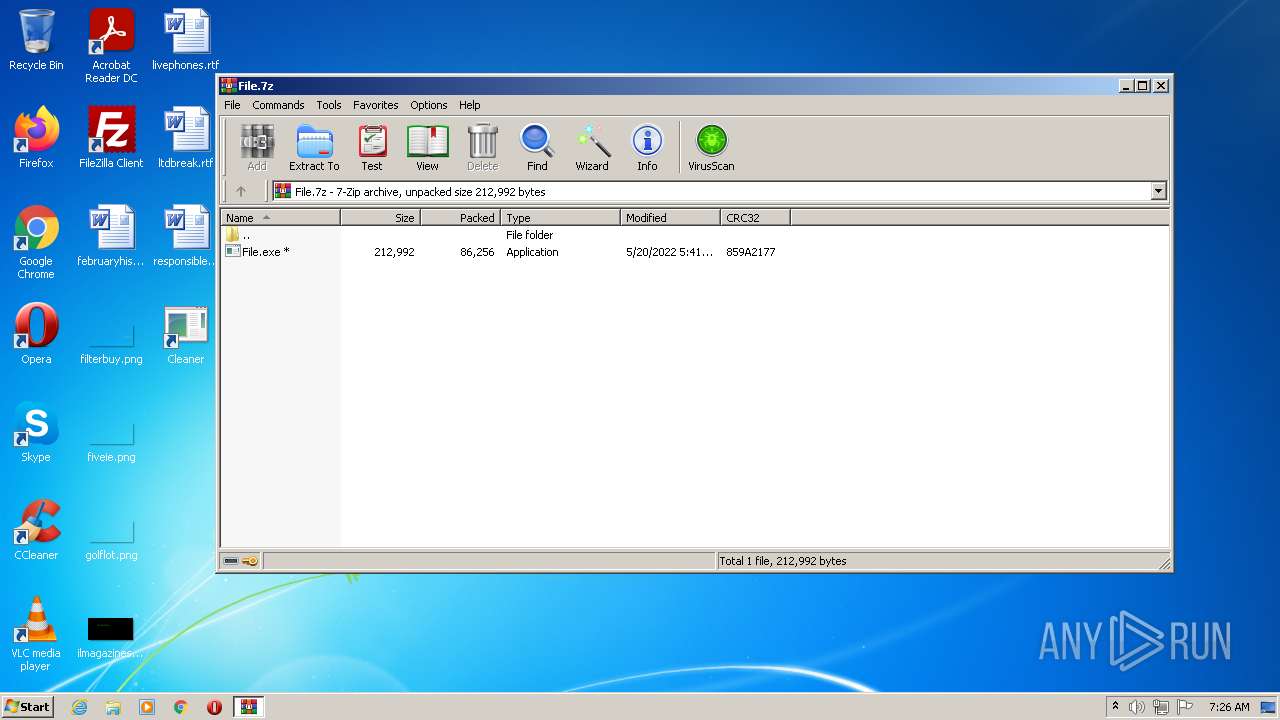
| URL: | https://cdn.discordapp.com/attachments/972462409266655305/977438551669108766/File.7z?file=181.zip |
| Full analysis: | https://app.any.run/tasks/1366a8a3-7aaa-44c1-ad3e-9d5882eea485 |
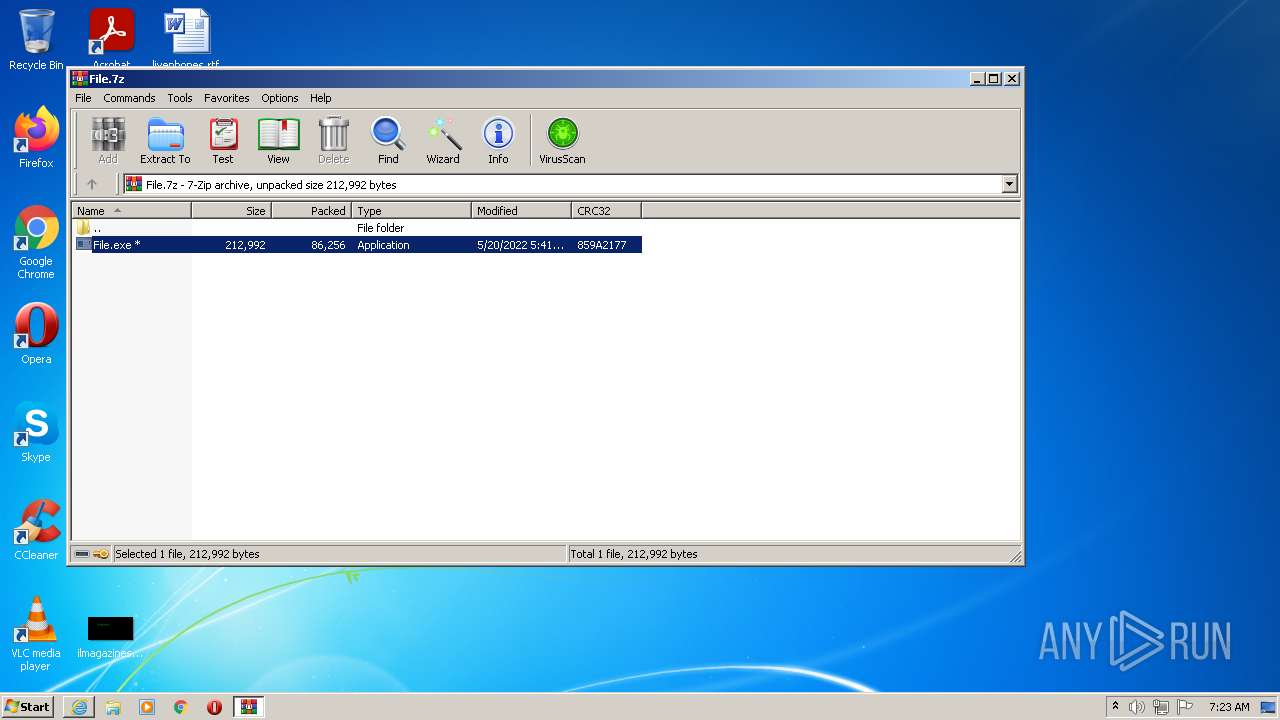
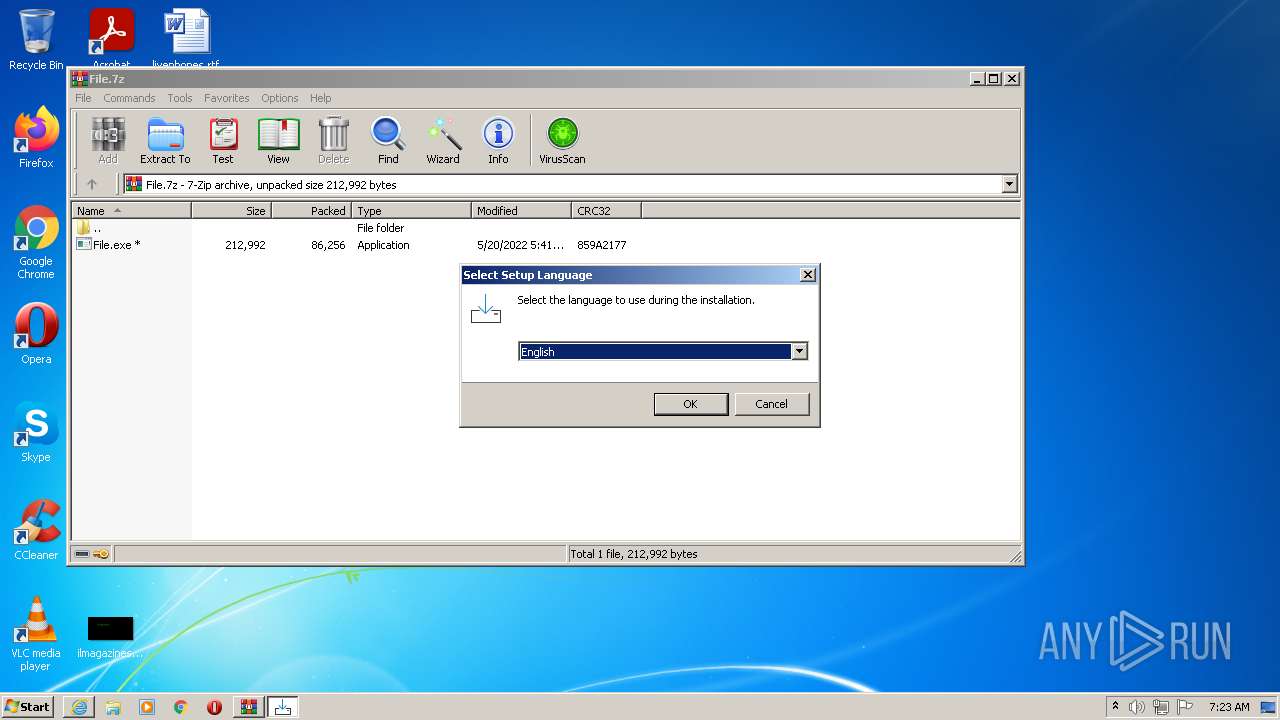
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 21, 2022, 06:22:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 46821FD3FF1E4E87DBA6BEC314D2F029 |
| SHA1: | 2615BB8D62A375881BDE41AA4999D6B4D874B1CE |
| SHA256: | E1C605EBC3E29A930CFC9504C0FCC6B705BE9983A893A8B5C0077FBC0705F930 |
| SSDEEP: | 3:N8cCWdy6//jB1VcrFWVfjiblB3gGjIAjIADn:2cry6XjD2lhB3x9jIADn |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 4032)
- File.exe (PID: 3152)
- NiceProcessX32.bmp.exe (PID: 2912)
- 13.php.exe (PID: 1832)
- cmd.exe (PID: 3916)
- Service.bmp.exe (PID: 3984)
- fxdd.bmp.exe (PID: 1000)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- mixinte2001.bmp.exe (PID: 4008)
- random.exe.exe (PID: 3272)
- real2001.bmp.exe (PID: 2268)
- test33.bmp.exe (PID: 1036)
- IQwqPtAU3c7.exe (PID: 2464)
- gYaqqhiDI.exe (PID: 2736)
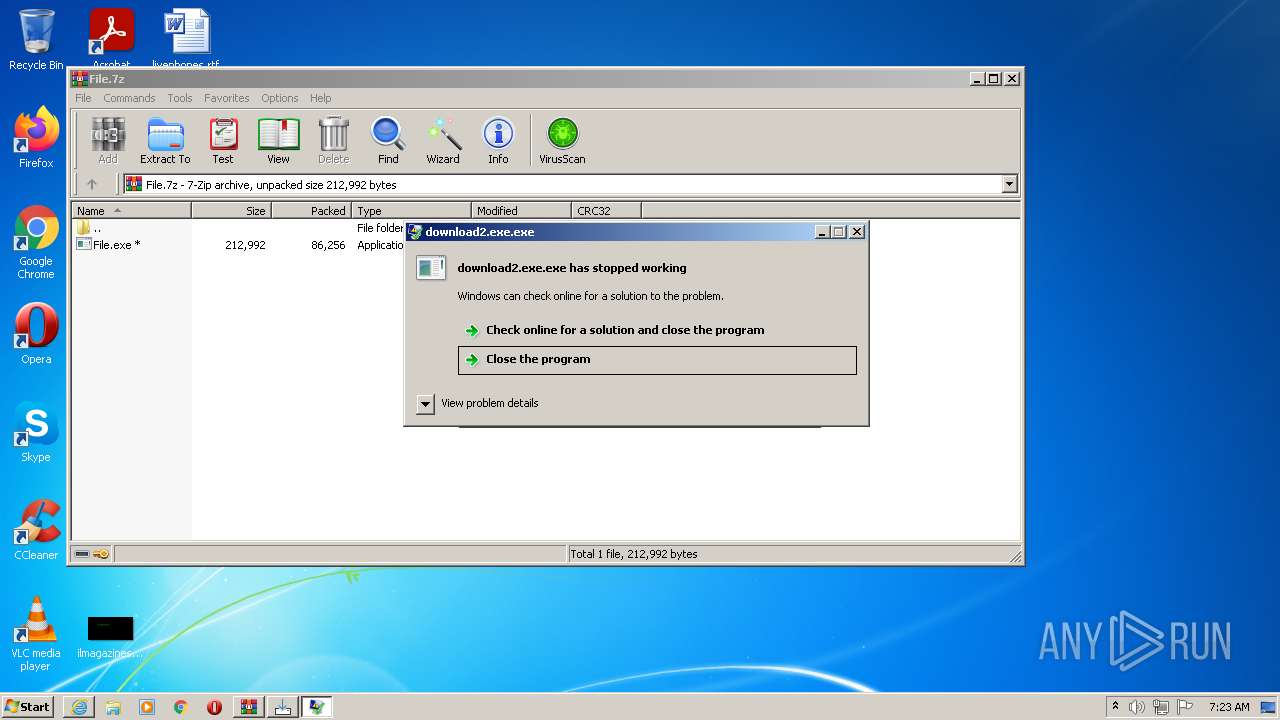
- download2.exe.exe (PID: 4084)
- utube2005.bmp.exe (PID: 3752)
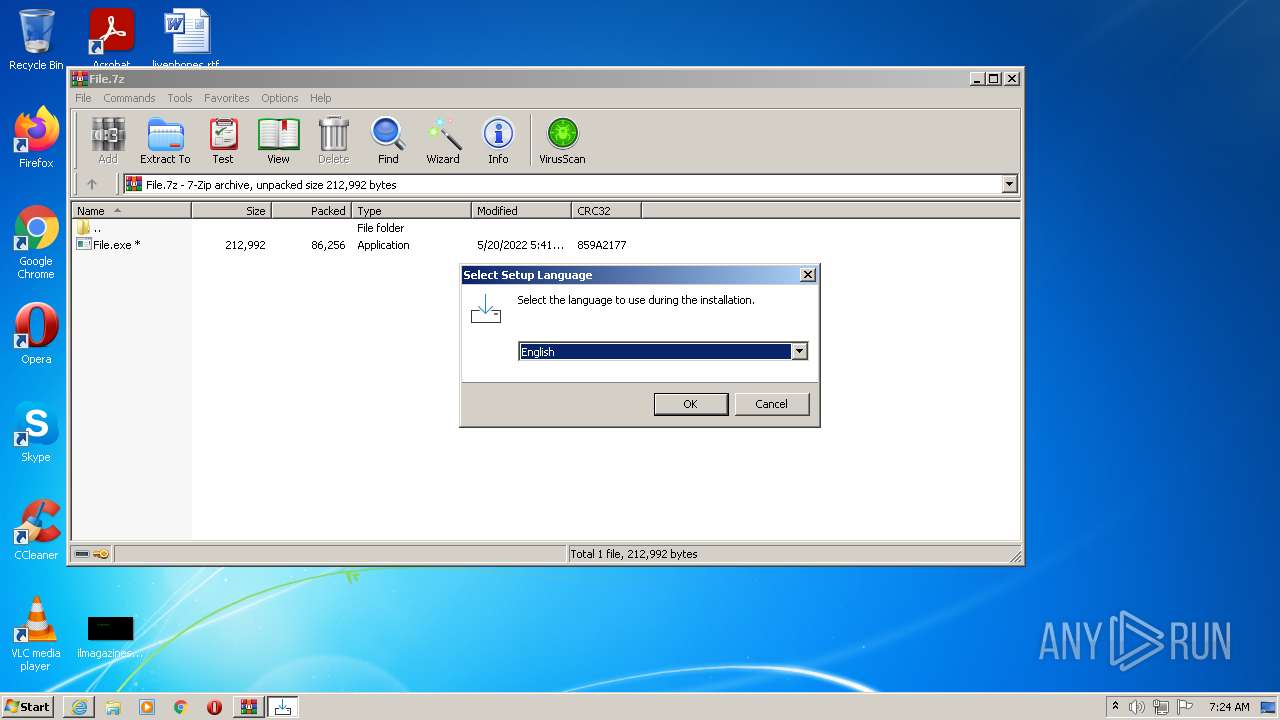
- setup.exe (PID: 3132)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- Install.exe (PID: 2208)
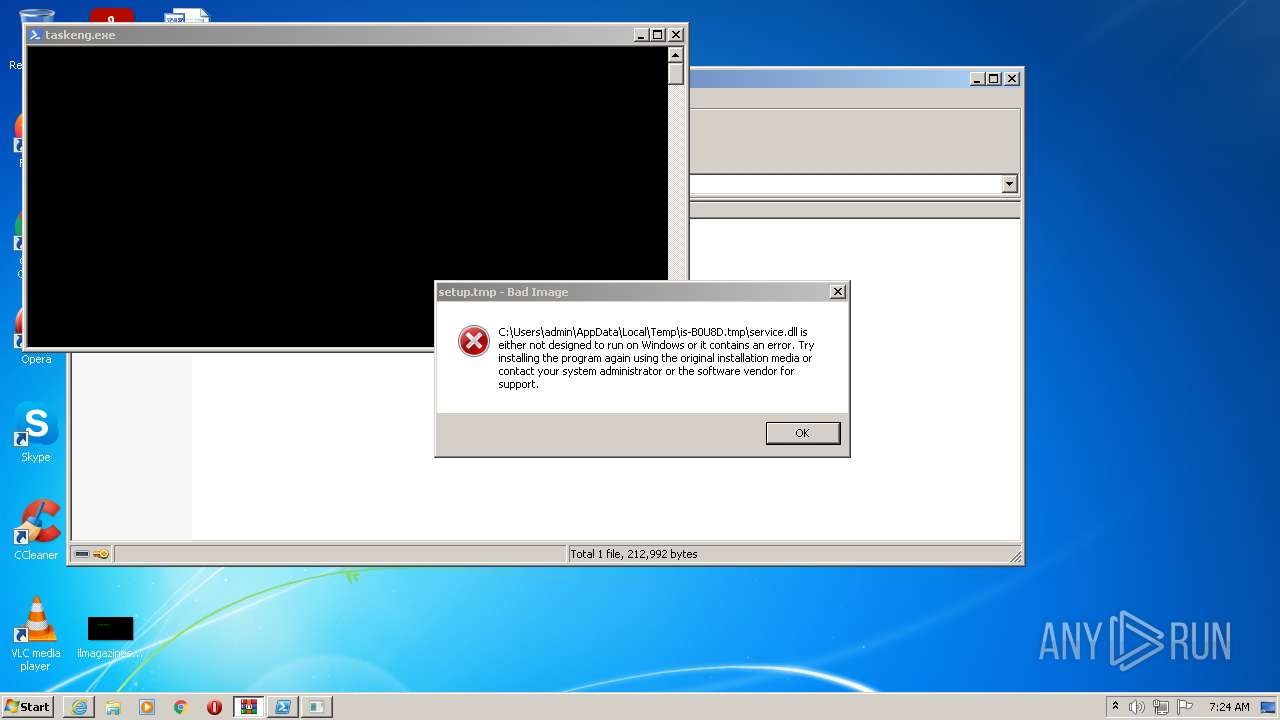
- setup.tmp (PID: 1256)
- setup.exe (PID: 3984)
- setup.tmp (PID: 3064)
- Congiunto.exe.pif (PID: 3480)
- orxds.exe (PID: 1208)
- GF6GB.exe (PID: 3316)
- build2.exe (PID: 2656)
- Install.exe (PID: 1808)
- Congiunto.exe.pif (PID: 3756)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- IsrGSPs.exe (PID: 5912)
- eCYGTdT.exe (PID: 4528)
Disables Windows Defender
- File.exe (PID: 3152)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
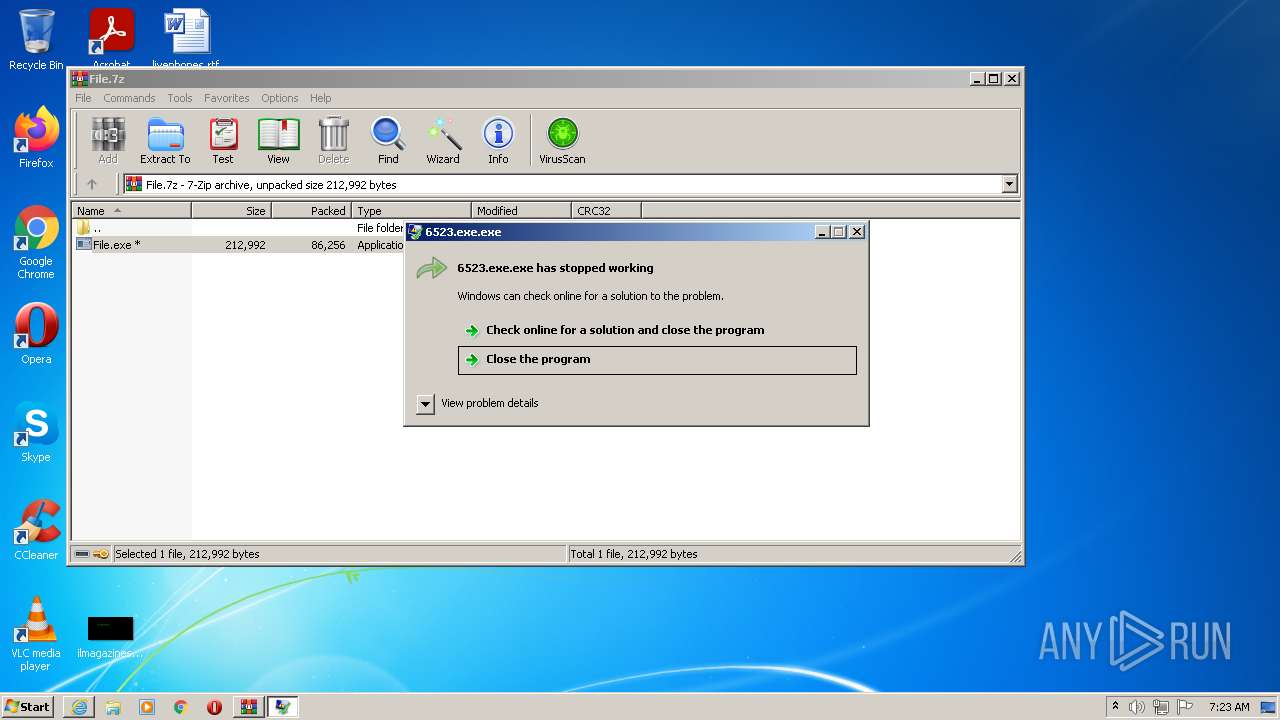
Application was dropped or rewritten from another process
- File.exe (PID: 3152)
- File.exe (PID: 116)
- NiceProcessX32.bmp.exe (PID: 2912)
- Service.bmp.exe (PID: 3984)
- SetupMEXX.exe.exe (PID: 2496)
- file1.exe.exe (PID: 1980)
- 13.php.exe (PID: 1832)
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- wam.exe.exe (PID: 1104)
- mxsfsaaa.exe (PID: 2428)
- 6523.exe.exe (PID: 2548)
- FJEfRXZ.exe.exe (PID: 1048)
- prolivv.bmp.exe (PID: 2336)
- test33.bmp.exe (PID: 3676)
- mixinte2001.bmp.exe (PID: 4008)
- real2001.bmp.exe (PID: 2268)
- olympteam_build_crypted_2.bmp.exe (PID: 2420)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
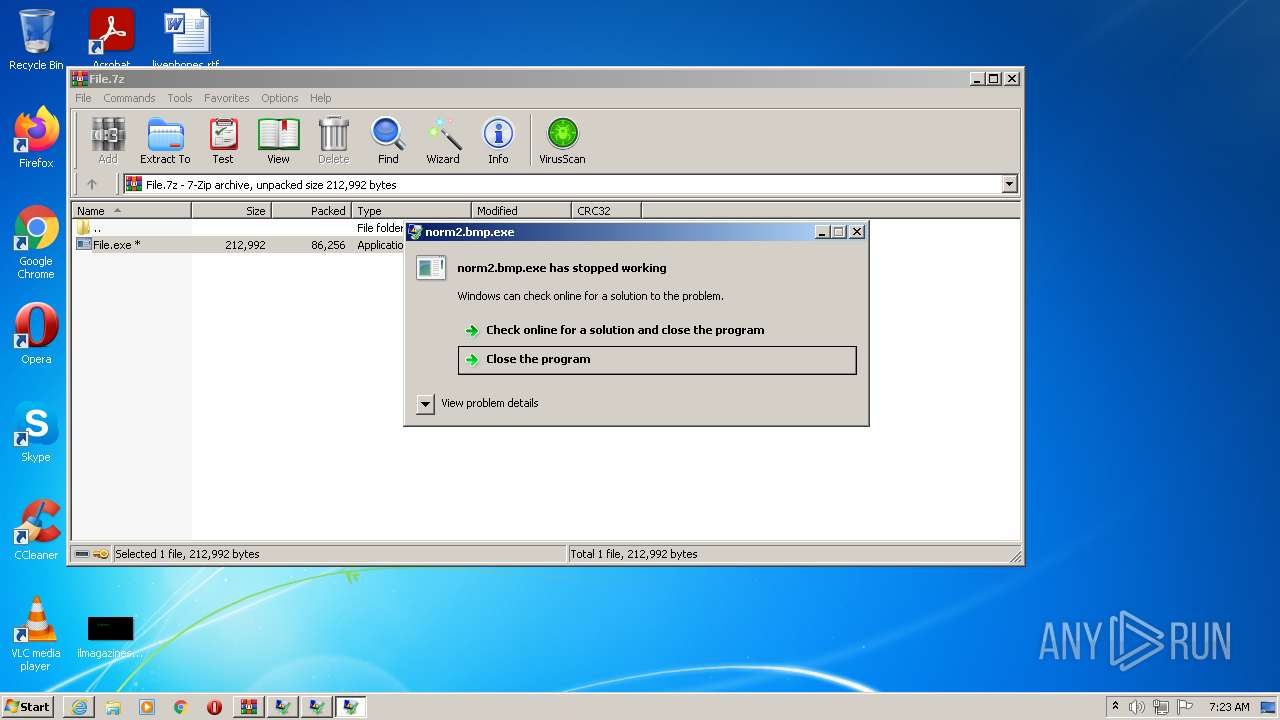
- norm2.bmp.exe (PID: 2552)
- lokes_1.bmp.exe (PID: 3928)
- fxdd.bmp.exe (PID: 1000)
- arabcode_crypted_3.bmp.exe (PID: 1224)
- unmatured.bmp.exe (PID: 2120)
- Fenix_7.bmp.exe (PID: 3744)
- ShortnessUnsol.bmp.exe (PID: 3108)
- orxds.exe (PID: 1208)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- NiceProcessX32.bmp.exe (PID: 2380)
- setup777.exe.exe (PID: 780)
- random.exe.exe (PID: 3272)
- test33.bmp.exe (PID: 3972)
- random.exe.exe (PID: 1972)
- mixinte2001.bmp.exe (PID: 2448)
- 0pbZ7.exe (PID: 3020)
- FJEfRXZ.exe.exe (PID: 4044)
- test33.bmp.exe (PID: 1036)
- IQwqPtAU3c7.exe (PID: 2464)
- search_hyperfs_310.exe.exe (PID: 2168)
- gYaqqhiDI.exe (PID: 2736)
- strongix.exe (PID: 2548)
- utube2005.bmp.exe (PID: 3752)
- ll.exe (PID: 2516)
- Install.exe (PID: 2208)
- ll.exe (PID: 1764)
- build2.exe (PID: 2664)
- H2506.exe (PID: 3244)
- download2.exe.exe (PID: 4084)
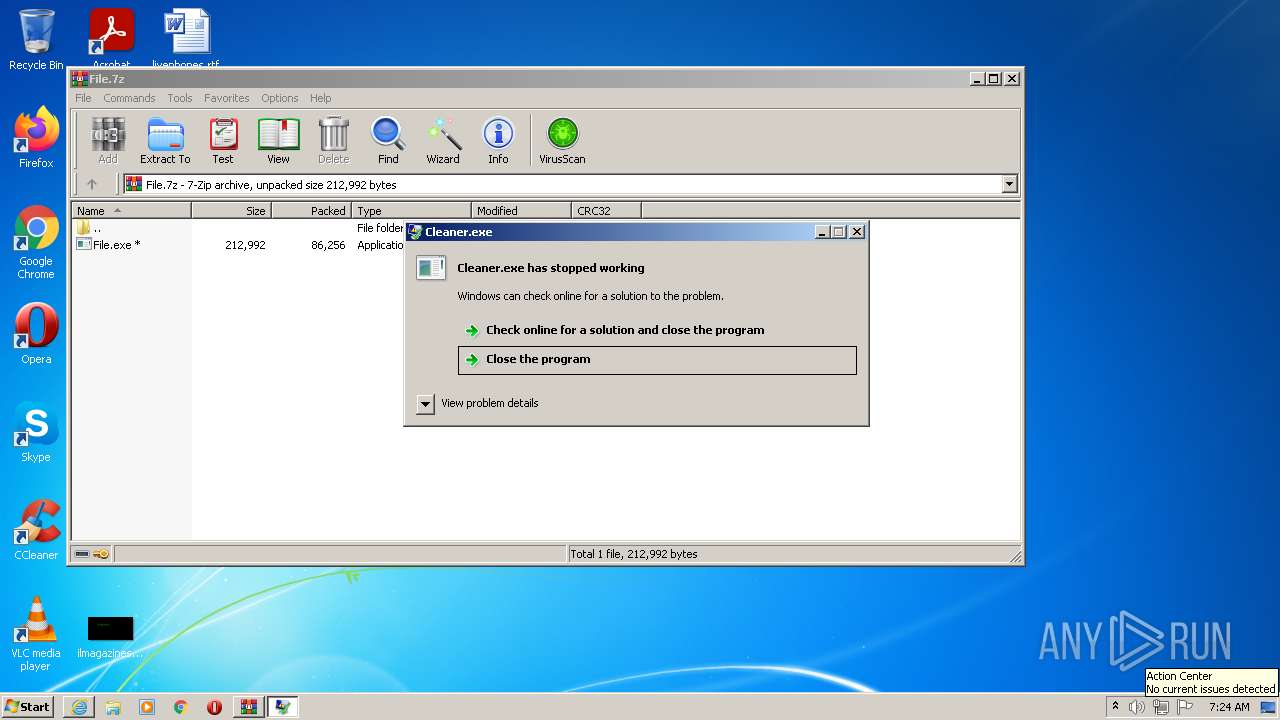
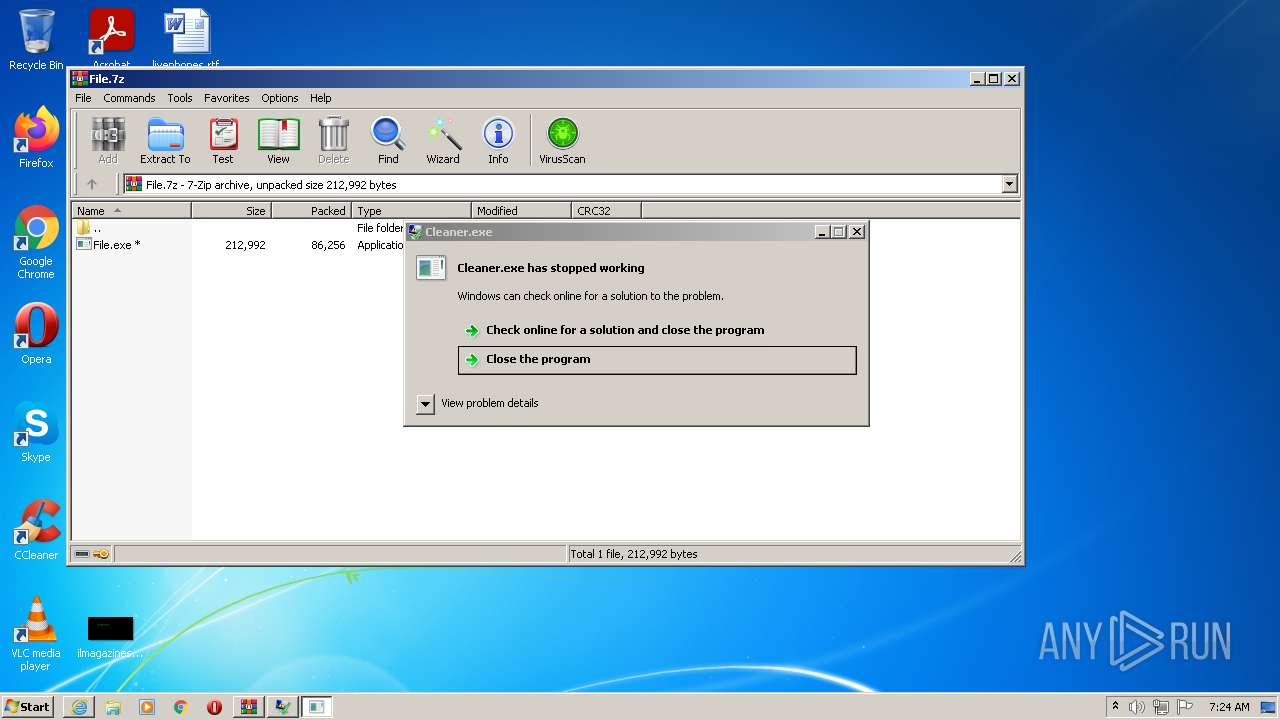
- Cleaner.exe (PID: 2416)
- setup331.exe (PID: 4092)
- Install.exe (PID: 1808)
- build2.exe (PID: 2656)
- InvisBrowser45856.exe (PID: 2064)
- setup.exe (PID: 3132)
- setup.exe (PID: 3984)
- Tabivuz.exe (PID: 1312)
- orxds.exe (PID: 3348)
- 1A2C2.exe (PID: 2124)
- GF6GB.exe (PID: 3316)
- 1K9D4.exe (PID: 1292)
- svmine.exe (PID: 3592)
- IsrGSPs.exe (PID: 5912)
- orxds.exe (PID: 5952)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- eCYGTdT.exe (PID: 4528)
- orxds.exe (PID: 4612)
- Cleaner.exe (PID: 4732)
Changes settings of System certificates
- File.exe (PID: 3152)
- Service.bmp.exe (PID: 3984)
- test33.bmp.exe (PID: 908)
- wam.exe.exe (PID: 1104)
- svchost.exe (PID: 2468)
SOCELARS was detected
- File.exe (PID: 3152)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
Connects to CnC server
- File.exe (PID: 3152)
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 916)
- AppLaunch.exe (PID: 3712)
- Service.bmp.exe (PID: 3984)
- SetupMEXX.exe.exe (PID: 2496)
- AppLaunch.exe (PID: 3564)
- Fenix_7.bmp.exe (PID: 3744)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- AppLaunch.exe (PID: 1600)
- orxds.exe (PID: 1208)
- lokes_1.bmp.exe (PID: 3928)
- ShortnessUnsol.bmp.exe (PID: 3108)
- svchost.exe (PID: 3296)
- strongix.exe (PID: 2548)
- H2506.exe (PID: 3244)
- rundll32.exe (PID: 5772)
- 1A2C2.exe (PID: 2124)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
REDLINE was detected
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 916)
- AppLaunch.exe (PID: 3712)
- SetupMEXX.exe.exe (PID: 2496)
- Fenix_7.bmp.exe (PID: 3744)
- AppLaunch.exe (PID: 3564)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- ShortnessUnsol.bmp.exe (PID: 3108)
- strongix.exe (PID: 2548)
- H2506.exe (PID: 3244)
- 1A2C2.exe (PID: 2124)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
Actions looks like stealing of personal data
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 3712)
- Fenix_7.bmp.exe (PID: 3744)
- ShortnessUnsol.bmp.exe (PID: 3108)
- AppLaunch.exe (PID: 916)
- SetupMEXX.exe.exe (PID: 2496)
- real2001.bmp.exe (PID: 2268)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- InvisBrowser45856.exe (PID: 2064)
- download2.exe.exe (PID: 4084)
- setup.tmp (PID: 1256)
- svchost.exe (PID: 2468)
- rundll32.exe (PID: 5772)
- build2.exe (PID: 2656)
- AppLaunch.exe (PID: 3564)
- H2506.exe (PID: 3244)
- strongix.exe (PID: 2548)
- 1A2C2.exe (PID: 2124)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- eCYGTdT.exe (PID: 4528)
Steals credentials from Web Browsers
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 3712)
- Fenix_7.bmp.exe (PID: 3744)
- ShortnessUnsol.bmp.exe (PID: 3108)
- real2001.bmp.exe (PID: 2268)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- svchost.exe (PID: 2468)
- build2.exe (PID: 2656)
- AppLaunch.exe (PID: 916)
- SetupMEXX.exe.exe (PID: 2496)
- 1A2C2.exe (PID: 2124)
- AppLaunch.exe (PID: 3564)
- strongix.exe (PID: 2548)
- H2506.exe (PID: 3244)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- eCYGTdT.exe (PID: 4528)
Changes the autorun value in the registry
- FJEfRXZ.exe.exe (PID: 1048)
- test33.bmp.exe (PID: 908)
- FJEfRXZ.exe.exe (PID: 4044)
- GF6GB.exe (PID: 3316)
Uses SVCHOST.EXE for hidden code execution
- mxsfsaaa.exe (PID: 2428)
- svchost.exe (PID: 2652)
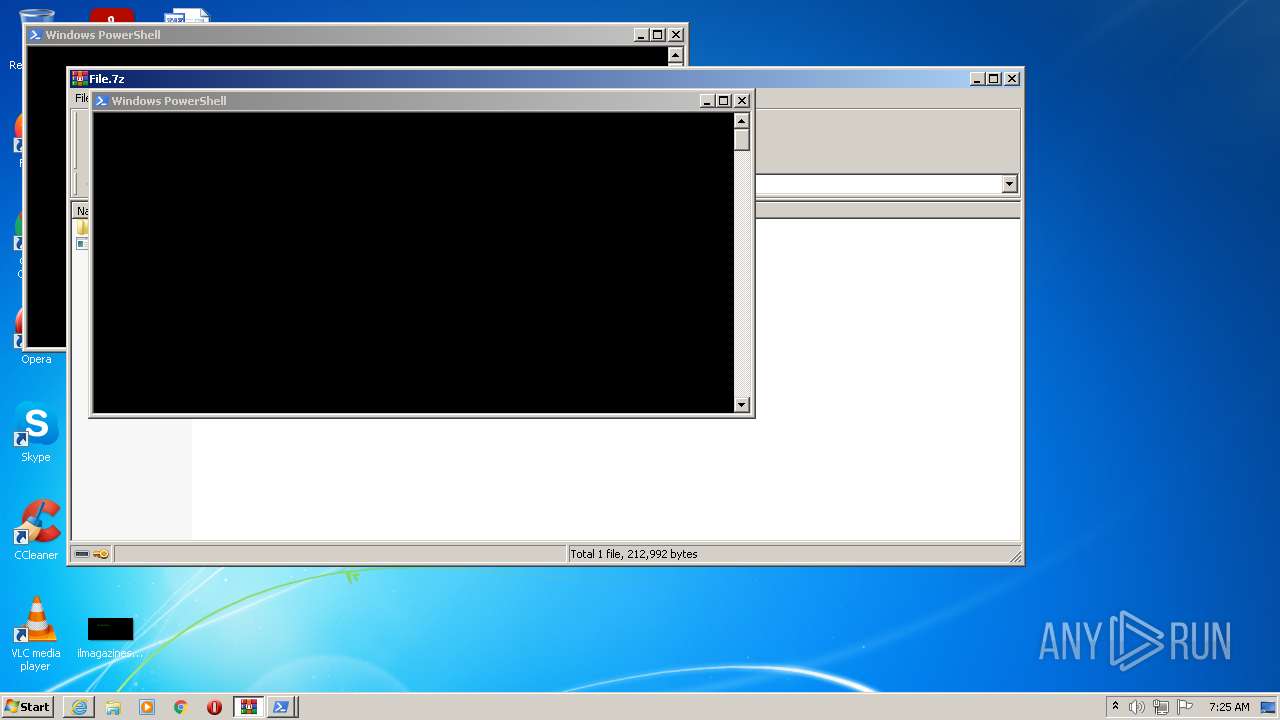
Runs app for hidden code execution
- cmd.exe (PID: 2144)
- cmd.exe (PID: 2844)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 4056)
- cmd.exe (PID: 2116)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 4056)
- cmd.exe (PID: 2116)
REDLINE detected by memory dumps
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 916)
- AppLaunch.exe (PID: 3712)
- norm2.bmp.exe (PID: 2552)
- AppLaunch.exe (PID: 2584)
- AppLaunch.exe (PID: 3564)
- AppLaunch.exe (PID: 1600)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
Uses Task Scheduler to run other applications
- Service.bmp.exe (PID: 3984)
- Service.bmp.exe (PID: 3984)
- orxds.exe (PID: 1208)
- cmd.exe (PID: 3584)
- Install.exe (PID: 1808)
- IsrGSPs.exe (PID: 5912)
- eCYGTdT.exe (PID: 4528)
- eCYGTdT.exe (PID: 4528)
- rundll32.EXE (PID: 2880)
TOFSEE detected by memory dumps
- svchost.exe (PID: 2652)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2632)
- schtasks.exe (PID: 2352)
- schtasks.exe (PID: 3220)
- test33.bmp.exe (PID: 908)
- test33.bmp.exe (PID: 1036)
- schtasks.exe (PID: 3048)
- schtasks.exe (PID: 4748)
- schtasks.exe (PID: 1760)
- schtasks.exe (PID: 5336)
- schtasks.exe (PID: 2804)
- schtasks.exe (PID: 3328)
- svchost.exe (PID: 872)
- schtasks.exe (PID: 1576)
- schtasks.exe (PID: 5900)
- schtasks.exe (PID: 4076)
- schtasks.exe (PID: 2052)
- schtasks.exe (PID: 5068)
- schtasks.exe (PID: 5368)
- schtasks.exe (PID: 4872)
- schtasks.exe (PID: 4568)
- schtasks.exe (PID: 5444)
- schtasks.exe (PID: 3620)
- schtasks.exe (PID: 2268)
- schtasks.exe (PID: 3048)
- schtasks.exe (PID: 4080)
Changes the Startup folder
- reg.exe (PID: 3992)
AMADEY was detected
- orxds.exe (PID: 1208)
AMADEY detected by memory dumps
- orxds.exe (PID: 1208)
- orxds.exe (PID: 3348)
Loads dropped or rewritten executable
- rundll32.exe (PID: 2172)
- real2001.bmp.exe (PID: 2268)
- Cleaner.exe (PID: 2416)
- rundll32.exe (PID: 3444)
- msiexec.exe (PID: 572)
- 13.php.exe (PID: 1832)
- conhost.exe (PID: 2952)
- conhost.exe (PID: 3912)
- build2.exe (PID: 2656)
- Service.bmp.exe (PID: 3984)
- cmd.exe (PID: 4000)
- DllHost.exe (PID: 832)
- reg.exe (PID: 3992)
- iexplore.exe (PID: 964)
- NiceProcessX32.bmp.exe (PID: 2912)
- svchost.exe (PID: 2468)
- DllHost.exe (PID: 148)
- test33.bmp.exe (PID: 1036)
- WerFault.exe (PID: 3608)
- DllHost.exe (PID: 2268)
- setup331.exe (PID: 4092)
- iexplore.exe (PID: 1332)
- fxdd.bmp.exe (PID: 1000)
- schtasks.exe (PID: 2352)
- File.exe (PID: 3152)
- AppLaunch.exe (PID: 3564)
- cmd.exe (PID: 3920)
- rrmix.exe.exe (PID: 2356)
- Offscum.exe.exe (PID: 2200)
- cmd.exe (PID: 2844)
- forfiles.exe (PID: 1024)
- file1.exe.exe (PID: 1980)
- search_hyperfs_310.exe.exe (PID: 2168)
- File.exe (PID: 116)
- schtasks.exe (PID: 4748)
- conhost.exe (PID: 3452)
- tasklist.exe (PID: 3136)
- cmd.exe (PID: 3980)
- WinRAR.exe (PID: 4032)
- sc.exe (PID: 3516)
- ntvdm.exe (PID: 3160)
- conhost.exe (PID: 4004)
- conhost.exe (PID: 3180)
- unmatured.bmp.exe (PID: 2120)
- Install.exe (PID: 1808)
- consent.exe (PID: 3044)
- conhost.exe (PID: 2348)
- DllHost.exe (PID: 3668)
- orxds.exe (PID: 3348)
- DllHost.exe (PID: 2288)
- Install.exe (PID: 2208)
- cmd.exe (PID: 3916)
- Congiunto.exe.pif (PID: 3756)
- mxsfsaaa.exe (PID: 2428)
- conhost.exe (PID: 2968)
- FJEfRXZ.exe.exe (PID: 1048)
- find.exe (PID: 3472)
- cmd.exe (PID: 3584)
- conhost.exe (PID: 2392)
- conhost.exe (PID: 3780)
- ll.exe (PID: 2516)
- cmd.exe (PID: 3120)
- findstr.exe (PID: 3068)
- svchost.exe (PID: 2652)
- mixinte2001.bmp.exe (PID: 2448)
- wmiprvse.exe (PID: 2852)
- svchost.exe (PID: 2420)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- conhost.exe (PID: 2580)
- AppLaunch.exe (PID: 2584)
- conhost.exe (PID: 2068)
- conhost.exe (PID: 3780)
- Fenix_7.bmp.exe (PID: 3744)
- cmd.exe (PID: 2768)
- schtasks.exe (PID: 3220)
- taskkill.exe (PID: 3088)
- ftp.exe (PID: 3636)
- conhost.exe (PID: 2340)
- DllHost.exe (PID: 3360)
- prolivv.bmp.exe (PID: 2336)
- AppLaunch.exe (PID: 3712)
- AppLaunch.exe (PID: 916)
- cmd.exe (PID: 2116)
- 6523.exe.exe (PID: 2548)
- cmd.exe (PID: 2144)
- schtasks.exe (PID: 2632)
- H2506.exe (PID: 3244)
- conhost.exe (PID: 4056)
- random.exe.exe (PID: 1972)
- IQwqPtAU3c7.exe (PID: 2464)
- control.exe (PID: 1340)
- find.exe (PID: 2528)
- ll.exe (PID: 1764)
- reg.exe (PID: 3132)
- arabcode_crypted_3.bmp.exe (PID: 1224)
- build2.exe (PID: 2664)
- SetupMEXX.exe.exe (PID: 2496)
- conhost.exe (PID: 852)
- cmd.exe (PID: 1556)
- norm2.bmp.exe (PID: 2552)
- DllHost.exe (PID: 2560)
- DllHost.exe (PID: 1812)
- find.exe (PID: 2724)
- orxds.exe (PID: 1208)
- taskkill.exe (PID: 2964)
- 1K9D4.exe (PID: 1292)
- findstr.exe (PID: 3364)
- FJEfRXZ.exe.exe (PID: 4044)
- svchost.exe (PID: 3296)
- netsh.exe (PID: 584)
- setup.exe (PID: 3132)
- tasklist.exe (PID: 3156)
- InvisBrowser45856.exe (PID: 2064)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- conhost.exe (PID: 2536)
- ShortnessUnsol.bmp.exe (PID: 3108)
- WerFault.exe (PID: 1760)
- DllHost.exe (PID: 2480)
- icacls.exe (PID: 3256)
- 1A2C2.exe (PID: 2124)
- mixinte2001.bmp.exe (PID: 4008)
- utube2005.bmp.exe (PID: 3752)
- find.exe (PID: 604)
- Congiunto.exe.pif (PID: 3480)
- olympteam_build_crypted_2.bmp.exe (PID: 2420)
- WerFault.exe (PID: 3912)
- WerFault.exe (PID: 2108)
- lokes_1.bmp.exe (PID: 3928)
- conhost.exe (PID: 3372)
- conhost.exe (PID: 3516)
- NiceProcessX32.bmp.exe (PID: 2380)
- SearchFilterHost.exe (PID: 1148)
- WerFault.exe (PID: 2248)
- conhost.exe (PID: 3176)
- DllHost.exe (PID: 2384)
- tasklist.exe (PID: 2680)
- test33.bmp.exe (PID: 908)
- DllHost.exe (PID: 2480)
- strongix.exe (PID: 2548)
- download2.exe.exe (PID: 4084)
- test33.bmp.exe (PID: 3676)
- random.exe.exe (PID: 3272)
- conhost.exe (PID: 3660)
- conhost.exe (PID: 2956)
- cmd.exe (PID: 2364)
- timeout.exe (PID: 3956)
- reg.exe (PID: 2696)
- cmd.exe (PID: 4056)
- rundll32.exe (PID: 2192)
- sc.exe (PID: 3372)
- tasklist.exe (PID: 3720)
- conhost.exe (PID: 456)
- PING.EXE (PID: 3484)
- conhost.exe (PID: 2964)
- schtasks.exe (PID: 3048)
- test33.bmp.exe (PID: 3972)
- sc.exe (PID: 3824)
- conhost.exe (PID: 3988)
- AppLaunch.exe (PID: 1600)
- setup.exe (PID: 3984)
- svchost.exe (PID: 148)
- setup777.exe.exe (PID: 780)
- forfiles.exe (PID: 2300)
- GF6GB.exe (PID: 3316)
- wam.exe.exe (PID: 1104)
- conhost.exe (PID: 3524)
- gYaqqhiDI.exe (PID: 2736)
- conhost.exe (PID: 4804)
- 0pbZ7.exe (PID: 3020)
- conhost.exe (PID: 2424)
- msiexec.exe (PID: 5684)
- conhost.exe (PID: 2760)
- PING.EXE (PID: 3668)
- ftp.exe (PID: 2476)
- DllHost.exe (PID: 4104)
- cmd.exe (PID: 752)
- conhost.exe (PID: 1544)
- taskkill.exe (PID: 1204)
- Tabivuz.exe (PID: 1312)
- conhost.exe (PID: 1384)
- schtasks.exe (PID: 1760)
- Congiunto.exe.pif (PID: 4816)
- powershell.EXE (PID: 5144)
- rundll32.exe (PID: 5772)
- conhost.exe (PID: 5424)
- DllHost.exe (PID: 2044)
- schtasks.exe (PID: 5336)
- conhost.exe (PID: 5360)
- conhost.exe (PID: 5912)
- schtasks.exe (PID: 5672)
- svmine.exe (PID: 3592)
- taskeng.exe (PID: 5784)
- orxds.exe (PID: 5952)
- IsrGSPs.exe (PID: 5912)
- schtasks.exe (PID: 2804)
- conhost.exe (PID: 1412)
- conhost.exe (PID: 1940)
- schtasks.exe (PID: 3328)
- powershell.EXE (PID: 4156)
- Congiunto.exe.pif (PID: 1540)
- conhost.exe (PID: 4360)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- gpupdate.exe (PID: 5808)
- conhost.exe (PID: 5876)
- gpscript.exe (PID: 4196)
- svchost.exe (PID: 5280)
- gpupdate.exe (PID: 5800)
- conhost.exe (PID: 6048)
- gpscript.exe (PID: 4068)
- schtasks.exe (PID: 1576)
- conhost.exe (PID: 5000)
- cmd.exe (PID: 4024)
- conhost.exe (PID: 4128)
- cmd.exe (PID: 5132)
- conhost.exe (PID: 2732)
- reg.exe (PID: 6032)
- cmd.exe (PID: 3812)
- conhost.exe (PID: 5240)
- reg.exe (PID: 5124)
- reg.exe (PID: 2164)
- conhost.exe (PID: 5440)
- conhost.exe (PID: 4228)
- conhost.exe (PID: 5768)
- reg.exe (PID: 5944)
- wscript.exe (PID: 5416)
- reg.exe (PID: 920)
- conhost.exe (PID: 3504)
- reg.exe (PID: 5996)
- reg.exe (PID: 4404)
- conhost.exe (PID: 3004)
- conhost.exe (PID: 1340)
- reg.exe (PID: 3432)
- reg.exe (PID: 2196)
- conhost.exe (PID: 2544)
- conhost.exe (PID: 2036)
- conhost.exe (PID: 3192)
- conhost.exe (PID: 4220)
- reg.exe (PID: 4300)
- reg.exe (PID: 1828)
- reg.exe (PID: 3048)
- reg.exe (PID: 1204)
- conhost.exe (PID: 4924)
- conhost.exe (PID: 2588)
- reg.exe (PID: 4888)
- conhost.exe (PID: 4744)
- reg.exe (PID: 2444)
- reg.exe (PID: 5460)
- conhost.exe (PID: 4312)
- reg.exe (PID: 5216)
- conhost.exe (PID: 940)
- reg.exe (PID: 4216)
- conhost.exe (PID: 3712)
- conhost.exe (PID: 5828)
- schtasks.exe (PID: 5900)
- schtasks.exe (PID: 3096)
- conhost.exe (PID: 2788)
- conhost.exe (PID: 2268)
- cmd.exe (PID: 4084)
- eCYGTdT.exe (PID: 4528)
- schtasks.exe (PID: 4076)
- conhost.exe (PID: 3352)
- reg.exe (PID: 1948)
- cmd.exe (PID: 4148)
- conhost.exe (PID: 2664)
- reg.exe (PID: 2336)
- schtasks.exe (PID: 4336)
- conhost.exe (PID: 4348)
- schtasks.exe (PID: 2052)
- conhost.exe (PID: 1856)
- conhost.exe (PID: 5084)
- schtasks.exe (PID: 5068)
- conhost.exe (PID: 5308)
- schtasks.exe (PID: 5444)
- conhost.exe (PID: 5188)
- schtasks.exe (PID: 4872)
- conhost.exe (PID: 2428)
- schtasks.exe (PID: 5368)
- DllHost.exe (PID: 5856)
- schtasks.exe (PID: 4568)
- schtasks.exe (PID: 3620)
- conhost.exe (PID: 5636)
- conhost.exe (PID: 3312)
- conhost.exe (PID: 1412)
- conhost.exe (PID: 4116)
- schtasks.exe (PID: 2268)
- cmd.exe (PID: 4236)
- conhost.exe (PID: 4876)
- schtasks.exe (PID: 4812)
- reg.exe (PID: 5876)
- schtasks.exe (PID: 3048)
- conhost.exe (PID: 4784)
- reg.exe (PID: 4448)
- cmd.exe (PID: 4484)
- conhost.exe (PID: 5336)
- conhost.exe (PID: 5240)
- rundll32.EXE (PID: 2880)
- schtasks.exe (PID: 4080)
- orxds.exe (PID: 4612)
- svchost.exe (PID: 1204)
- WerFault.exe (PID: 2020)
- Cleaner.exe (PID: 4732)
- DllHost.exe (PID: 1576)
- opera.exe (PID: 5440)
Application was injected by another process
- svchost.exe (PID: 872)
Runs injected code in another process
- rundll32.exe (PID: 2172)
- rundll32.exe (PID: 3444)
Stealing of credential data
- real2001.bmp.exe (PID: 2268)
- InvisBrowser45856.exe (PID: 2064)
- svchost.exe (PID: 2468)
- build2.exe (PID: 2656)
STOP was detected
- test33.bmp.exe (PID: 1036)
MINER was detected
- svchost.exe (PID: 3296)
TOFSEE was detected
- svchost.exe (PID: 2652)
Modifies exclusions in Windows Defender
- svchost.exe (PID: 2652)
- reg.exe (PID: 5124)
- reg.exe (PID: 920)
- reg.exe (PID: 5944)
- reg.exe (PID: 2164)
- reg.exe (PID: 4404)
- reg.exe (PID: 3048)
- reg.exe (PID: 5996)
- reg.exe (PID: 3432)
- reg.exe (PID: 2196)
Loads the Task Scheduler DLL interface
- schtasks.exe (PID: 5672)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4336)
- schtasks.exe (PID: 4812)
Modifies files in Chrome extension folder
- eCYGTdT.exe (PID: 4528)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 964)
Checks supported languages
- WinRAR.exe (PID: 4032)
- File.exe (PID: 3152)
- NiceProcessX32.bmp.exe (PID: 2912)
- Service.bmp.exe (PID: 3984)
- Offscum.exe.exe (PID: 2200)
- SetupMEXX.exe.exe (PID: 2496)
- rrmix.exe.exe (PID: 2356)
- 13.php.exe (PID: 1832)
- conhost.exe (PID: 2760)
- file1.exe.exe (PID: 1980)
- wam.exe.exe (PID: 1104)
- conhost.exe (PID: 2392)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3916)
- conhost.exe (PID: 4056)
- wmiprvse.exe (PID: 2852)
- conhost.exe (PID: 3524)
- conhost.exe (PID: 3780)
- 6523.exe.exe (PID: 2548)
- conhost.exe (PID: 4004)
- mxsfsaaa.exe (PID: 2428)
- FJEfRXZ.exe.exe (PID: 1048)
- conhost.exe (PID: 3176)
- conhost.exe (PID: 3660)
- conhost.exe (PID: 3988)
- conhost.exe (PID: 2068)
- prolivv.bmp.exe (PID: 2336)
- cmd.exe (PID: 2144)
- AppLaunch.exe (PID: 916)
- cmd.exe (PID: 4056)
- AppLaunch.exe (PID: 3712)
- Congiunto.exe.pif (PID: 3480)
- test33.bmp.exe (PID: 3676)
- mixinte2001.bmp.exe (PID: 4008)
- real2001.bmp.exe (PID: 2268)
- conhost.exe (PID: 2536)
- norm2.bmp.exe (PID: 2552)
- fxdd.bmp.exe (PID: 1000)
- lokes_1.bmp.exe (PID: 3928)
- olympteam_build_crypted_2.bmp.exe (PID: 2420)
- conhost.exe (PID: 3780)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- conhost.exe (PID: 852)
- test33.bmp.exe (PID: 908)
- arabcode_crypted_3.bmp.exe (PID: 1224)
- conhost.exe (PID: 456)
- unmatured.bmp.exe (PID: 2120)
- conhost.exe (PID: 3452)
- ShortnessUnsol.bmp.exe (PID: 3108)
- Fenix_7.bmp.exe (PID: 3744)
- AppLaunch.exe (PID: 2584)
- AppLaunch.exe (PID: 3564)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- conhost.exe (PID: 3180)
- orxds.exe (PID: 1208)
- conhost.exe (PID: 2348)
- AppLaunch.exe (PID: 1600)
- cmd.exe (PID: 4000)
- conhost.exe (PID: 2968)
- NiceProcessX32.bmp.exe (PID: 2380)
- setup777.exe.exe (PID: 780)
- random.exe.exe (PID: 1972)
- random.exe.exe (PID: 3272)
- test33.bmp.exe (PID: 3972)
- 0pbZ7.exe (PID: 3020)
- FJEfRXZ.exe.exe (PID: 4044)
- mixinte2001.bmp.exe (PID: 2448)
- conhost.exe (PID: 3372)
- conhost.exe (PID: 2952)
- cmd.exe (PID: 2844)
- test33.bmp.exe (PID: 1036)
- search_hyperfs_310.exe.exe (PID: 2168)
- IQwqPtAU3c7.exe (PID: 2464)
- cmd.exe (PID: 2116)
- gYaqqhiDI.exe (PID: 2736)
- Congiunto.exe.pif (PID: 3756)
- utube2005.bmp.exe (PID: 3752)
- strongix.exe (PID: 2548)
- conhost.exe (PID: 2956)
- download2.exe.exe (PID: 4084)
- cmd.exe (PID: 3584)
- InvisBrowser45856.exe (PID: 2064)
- setup331.exe (PID: 4092)
- ll.exe (PID: 1764)
- ll.exe (PID: 2516)
- Install.exe (PID: 2208)
- setup.exe (PID: 3132)
- build2.exe (PID: 2664)
- setup.tmp (PID: 1256)
- H2506.exe (PID: 3244)
- conhost.exe (PID: 2964)
- Install.exe (PID: 1808)
- cmd.exe (PID: 2768)
- Cleaner.exe (PID: 2416)
- cmd.exe (PID: 3980)
- conhost.exe (PID: 2580)
- cmd.exe (PID: 3920)
- conhost.exe (PID: 2340)
- orxds.exe (PID: 3348)
- build2.exe (PID: 2656)
- setup.exe (PID: 3984)
- setup.tmp (PID: 3064)
- 1A2C2.exe (PID: 2124)
- GF6GB.exe (PID: 3316)
- 1K9D4.exe (PID: 1292)
- conhost.exe (PID: 3516)
- conhost.exe (PID: 3912)
- conhost.exe (PID: 2424)
- conhost.exe (PID: 4804)
- conhost.exe (PID: 1544)
- cmd.exe (PID: 752)
- Congiunto.exe.pif (PID: 4816)
- conhost.exe (PID: 1384)
- powershell.EXE (PID: 5144)
- conhost.exe (PID: 5424)
- conhost.exe (PID: 5360)
- conhost.exe (PID: 5912)
- Tabivuz.exe (PID: 1312)
- svmine.exe (PID: 3592)
- IsrGSPs.exe (PID: 5912)
- conhost.exe (PID: 1412)
- orxds.exe (PID: 5952)
- Congiunto.exe.pif (PID: 1540)
- conhost.exe (PID: 4360)
- powershell.EXE (PID: 4156)
- conhost.exe (PID: 1940)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- conhost.exe (PID: 5876)
- conhost.exe (PID: 6048)
- conhost.exe (PID: 5000)
- conhost.exe (PID: 4128)
- conhost.exe (PID: 2732)
- cmd.exe (PID: 3812)
- conhost.exe (PID: 5240)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 5132)
- conhost.exe (PID: 5440)
- conhost.exe (PID: 5768)
- conhost.exe (PID: 4228)
- wscript.exe (PID: 5416)
- conhost.exe (PID: 3004)
- conhost.exe (PID: 1340)
- conhost.exe (PID: 3504)
- conhost.exe (PID: 2544)
- conhost.exe (PID: 2036)
- conhost.exe (PID: 3192)
- conhost.exe (PID: 4220)
- conhost.exe (PID: 4924)
- conhost.exe (PID: 940)
- conhost.exe (PID: 4744)
- conhost.exe (PID: 2588)
- conhost.exe (PID: 3712)
- conhost.exe (PID: 4312)
- conhost.exe (PID: 5828)
- conhost.exe (PID: 2788)
- conhost.exe (PID: 3352)
- conhost.exe (PID: 2268)
- eCYGTdT.exe (PID: 4528)
- cmd.exe (PID: 4148)
- cmd.exe (PID: 4084)
- conhost.exe (PID: 2664)
- conhost.exe (PID: 4348)
- conhost.exe (PID: 1856)
- conhost.exe (PID: 5084)
- conhost.exe (PID: 5188)
- conhost.exe (PID: 5308)
- conhost.exe (PID: 2428)
- conhost.exe (PID: 3312)
- conhost.exe (PID: 4116)
- conhost.exe (PID: 5636)
- conhost.exe (PID: 1412)
- cmd.exe (PID: 4236)
- conhost.exe (PID: 4876)
- conhost.exe (PID: 4784)
- cmd.exe (PID: 4484)
- conhost.exe (PID: 5336)
- conhost.exe (PID: 5240)
- orxds.exe (PID: 4612)
- Cleaner.exe (PID: 4732)
Reads the computer name
- WinRAR.exe (PID: 4032)
- File.exe (PID: 3152)
- Service.bmp.exe (PID: 3984)
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- 13.php.exe (PID: 1832)
- wam.exe.exe (PID: 1104)
- wmiprvse.exe (PID: 2852)
- mxsfsaaa.exe (PID: 2428)
- AppLaunch.exe (PID: 916)
- AppLaunch.exe (PID: 3712)
- Congiunto.exe.pif (PID: 3480)
- norm2.bmp.exe (PID: 2552)
- SetupMEXX.exe.exe (PID: 2496)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- Fenix_7.bmp.exe (PID: 3744)
- AppLaunch.exe (PID: 3564)
- AppLaunch.exe (PID: 2584)
- fxdd.bmp.exe (PID: 1000)
- orxds.exe (PID: 1208)
- AppLaunch.exe (PID: 1600)
- mixinte2001.bmp.exe (PID: 4008)
- setup777.exe.exe (PID: 780)
- real2001.bmp.exe (PID: 2268)
- lokes_1.bmp.exe (PID: 3928)
- 0pbZ7.exe (PID: 3020)
- random.exe.exe (PID: 1972)
- random.exe.exe (PID: 3272)
- test33.bmp.exe (PID: 1036)
- search_hyperfs_310.exe.exe (PID: 2168)
- ShortnessUnsol.bmp.exe (PID: 3108)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- Congiunto.exe.pif (PID: 3756)
- IQwqPtAU3c7.exe (PID: 2464)
- gYaqqhiDI.exe (PID: 2736)
- download2.exe.exe (PID: 4084)
- setup331.exe (PID: 4092)
- InvisBrowser45856.exe (PID: 2064)
- ll.exe (PID: 1764)
- ll.exe (PID: 2516)
- setup.tmp (PID: 1256)
- Cleaner.exe (PID: 2416)
- Install.exe (PID: 1808)
- build2.exe (PID: 2656)
- mixinte2001.bmp.exe (PID: 2448)
- setup.tmp (PID: 3064)
- 1K9D4.exe (PID: 1292)
- strongix.exe (PID: 2548)
- GF6GB.exe (PID: 3316)
- orxds.exe (PID: 3348)
- H2506.exe (PID: 3244)
- powershell.EXE (PID: 5144)
- 1A2C2.exe (PID: 2124)
- orxds.exe (PID: 5952)
- powershell.EXE (PID: 4156)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- wscript.exe (PID: 5416)
- eCYGTdT.exe (PID: 4528)
- Cleaner.exe (PID: 4732)
- orxds.exe (PID: 4612)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4032)
- File.exe (PID: 3152)
- NiceProcessX32.bmp.exe (PID: 2912)
- 13.php.exe (PID: 1832)
- cmd.exe (PID: 3916)
- Service.bmp.exe (PID: 3984)
- fxdd.bmp.exe (PID: 1000)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- mixinte2001.bmp.exe (PID: 4008)
- random.exe.exe (PID: 3272)
- real2001.bmp.exe (PID: 2268)
- IQwqPtAU3c7.exe (PID: 2464)
- gYaqqhiDI.exe (PID: 2736)
- download2.exe.exe (PID: 4084)
- utube2005.bmp.exe (PID: 3752)
- test33.bmp.exe (PID: 1036)
- setup.exe (PID: 3132)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- Install.exe (PID: 2208)
- setup.tmp (PID: 1256)
- setup.exe (PID: 3984)
- setup.tmp (PID: 3064)
- Congiunto.exe.pif (PID: 3480)
- orxds.exe (PID: 1208)
- GF6GB.exe (PID: 3316)
- build2.exe (PID: 2656)
- Install.exe (PID: 1808)
- Congiunto.exe.pif (PID: 3756)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- IsrGSPs.exe (PID: 5912)
- eCYGTdT.exe (PID: 4528)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 4032)
- File.exe (PID: 3152)
- NiceProcessX32.bmp.exe (PID: 2912)
- 13.php.exe (PID: 1832)
- cmd.exe (PID: 3916)
- Service.bmp.exe (PID: 3984)
- fxdd.bmp.exe (PID: 1000)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- mixinte2001.bmp.exe (PID: 4008)
- random.exe.exe (PID: 3272)
- real2001.bmp.exe (PID: 2268)
- test33.bmp.exe (PID: 1036)
- IQwqPtAU3c7.exe (PID: 2464)
- gYaqqhiDI.exe (PID: 2736)
- download2.exe.exe (PID: 4084)
- utube2005.bmp.exe (PID: 3752)
- setup.exe (PID: 3132)
- TrdngAnlzr22649.exe.exe (PID: 2660)
- Install.exe (PID: 2208)
- setup.tmp (PID: 1256)
- setup.exe (PID: 3984)
- setup.tmp (PID: 3064)
- Congiunto.exe.pif (PID: 3480)
- orxds.exe (PID: 1208)
- GF6GB.exe (PID: 3316)
- build2.exe (PID: 2656)
- Install.exe (PID: 1808)
- Congiunto.exe.pif (PID: 3756)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- IsrGSPs.exe (PID: 5912)
- eCYGTdT.exe (PID: 4528)
Adds / modifies Windows certificates
- File.exe (PID: 3152)
- Service.bmp.exe (PID: 3984)
- test33.bmp.exe (PID: 908)
- wam.exe.exe (PID: 1104)
Checks for external IP
- File.exe (PID: 3152)
- Service.bmp.exe (PID: 3984)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- svchost.exe (PID: 2468)
Starts CMD.EXE for commands execution
- 13.php.exe (PID: 1832)
- FJEfRXZ.exe.exe (PID: 1048)
- cmd.exe (PID: 2144)
- orxds.exe (PID: 1208)
- FJEfRXZ.exe.exe (PID: 4044)
- cmd.exe (PID: 2844)
- gYaqqhiDI.exe (PID: 2736)
- real2001.bmp.exe (PID: 2268)
- mixinte2001.bmp.exe (PID: 4008)
- forfiles.exe (PID: 2300)
- forfiles.exe (PID: 1024)
- mixinte2001.bmp.exe (PID: 2448)
- IsrGSPs.exe (PID: 5912)
- eCYGTdT.exe (PID: 4528)
Reads Environment values
- Offscum.exe.exe (PID: 2200)
- netsh.exe (PID: 584)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 916)
- AppLaunch.exe (PID: 3712)
- wam.exe.exe (PID: 1104)
- AppLaunch.exe (PID: 1600)
- SetupMEXX.exe.exe (PID: 2496)
- AppLaunch.exe (PID: 3564)
- Fenix_7.bmp.exe (PID: 3744)
- IQwqPtAU3c7.exe (PID: 2464)
- ShortnessUnsol.bmp.exe (PID: 3108)
- gYaqqhiDI.exe (PID: 2736)
- lokes_1.bmp.exe (PID: 3928)
- real2001.bmp.exe (PID: 2268)
- Cleaner.exe (PID: 2416)
- GF6GB.exe (PID: 3316)
- build2.exe (PID: 2656)
- H2506.exe (PID: 3244)
- strongix.exe (PID: 2548)
- 1A2C2.exe (PID: 2124)
- InvisBrowser45856.exe (PID: 2064)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- Cleaner.exe (PID: 4732)
Starts SC.EXE for service management
- 13.php.exe (PID: 1832)
Reads the cookies of Google Chrome
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 3712)
- Fenix_7.bmp.exe (PID: 3744)
- ShortnessUnsol.bmp.exe (PID: 3108)
- gYaqqhiDI.exe (PID: 2736)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
Searches for installed software
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- Fenix_7.bmp.exe (PID: 3744)
- real2001.bmp.exe (PID: 2268)
- AppLaunch.exe (PID: 3564)
- gYaqqhiDI.exe (PID: 2736)
- svchost.exe (PID: 2468)
- build2.exe (PID: 2656)
- AppLaunch.exe (PID: 3712)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- ShortnessUnsol.bmp.exe (PID: 3108)
- strongix.exe (PID: 2548)
- SetupMEXX.exe.exe (PID: 2496)
- AppLaunch.exe (PID: 916)
- H2506.exe (PID: 3244)
- InvisBrowser45856.exe (PID: 2064)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
- 1A2C2.exe (PID: 2124)
Reads CPU info
- wmiprvse.exe (PID: 2852)
- IQwqPtAU3c7.exe (PID: 2464)
- real2001.bmp.exe (PID: 2268)
- gYaqqhiDI.exe (PID: 2736)
- build2.exe (PID: 2656)
- InvisBrowser45856.exe (PID: 2064)
Reads the cookies of Mozilla Firefox
- Offscum.exe.exe (PID: 2200)
- rrmix.exe.exe (PID: 2356)
- AppLaunch.exe (PID: 3712)
- Fenix_7.bmp.exe (PID: 3744)
- ShortnessUnsol.bmp.exe (PID: 3108)
- AppLaunch.exe (PID: 1600)
- lokes_1.bmp.exe (PID: 3928)
- AppLaunch.exe (PID: 916)
- SetupMEXX.exe.exe (PID: 2496)
- 1A2C2.exe (PID: 2124)
- strongix.exe (PID: 2548)
- AppLaunch.exe (PID: 3564)
- H2506.exe (PID: 3244)
- 9817bcdf33322e8fbc1670e731c76126.exe (PID: 3248)
Executed as Windows Service
- mxsfsaaa.exe (PID: 2428)
Uses NETSH.EXE for network configuration
- 13.php.exe (PID: 1832)
Application launched itself
- cmd.exe (PID: 2144)
- test33.bmp.exe (PID: 3676)
- test33.bmp.exe (PID: 908)
- random.exe.exe (PID: 1972)
- cmd.exe (PID: 2844)
- test33.bmp.exe (PID: 3972)
- ll.exe (PID: 1764)
- build2.exe (PID: 2664)
- svchost.exe (PID: 2652)
- Congiunto.exe.pif (PID: 3480)
- Congiunto.exe.pif (PID: 3756)
Creates or modifies windows services
- svchost.exe (PID: 2652)
Reads Windows Product ID
- wmiprvse.exe (PID: 2852)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 4056)
- cmd.exe (PID: 2116)
Reads the Windows organization settings
- wmiprvse.exe (PID: 2852)
- setup.tmp (PID: 1256)
- setup.tmp (PID: 3064)
Starts application with an unusual extension
- cmd.exe (PID: 4056)
- cmd.exe (PID: 2116)
- Congiunto.exe.pif (PID: 3480)
- Congiunto.exe.pif (PID: 3756)
Reads Windows owner or organization settings
- wmiprvse.exe (PID: 2852)
- setup.tmp (PID: 1256)
- setup.tmp (PID: 3064)
Reads the date of Windows installation
- wmiprvse.exe (PID: 2852)
- powershell.EXE (PID: 5144)
- powershell.EXE (PID: 4156)
Reads mouse settings
- Congiunto.exe.pif (PID: 3480)
- Congiunto.exe.pif (PID: 3756)
- Tabivuz.exe (PID: 1312)
Creates files in the program directory
- Service.bmp.exe (PID: 3984)
- WerFault.exe (PID: 3912)
- WerFault.exe (PID: 3608)
- WerFault.exe (PID: 2248)
- real2001.bmp.exe (PID: 2268)
- WerFault.exe (PID: 1760)
- WerFault.exe (PID: 2108)
- build2.exe (PID: 2656)
- svchost.exe (PID: 872)
- eCYGTdT.exe (PID: 4528)
Creates a directory in Program Files
- Service.bmp.exe (PID: 3984)
- eCYGTdT.exe (PID: 4528)
Creates files in the Windows directory
- svchost.exe (PID: 872)
- svchost.exe (PID: 2652)
- svchost.exe (PID: 2468)
- schtasks.exe (PID: 5672)
- cmd.exe (PID: 3812)
- IsrGSPs.exe (PID: 5912)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4336)
- eCYGTdT.exe (PID: 4528)
- schtasks.exe (PID: 4812)
Starts itself from another location
- fxdd.bmp.exe (PID: 1000)
- utube2005.bmp.exe (PID: 3752)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 4000)
- cmd.exe (PID: 3120)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 5132)
- wscript.exe (PID: 5416)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 4148)
- cmd.exe (PID: 4236)
- cmd.exe (PID: 4484)
Uses ICACLS.EXE to modify access control list
- test33.bmp.exe (PID: 908)
Creates files in the user directory
- mixinte2001.bmp.exe (PID: 4008)
- real2001.bmp.exe (PID: 2268)
- IQwqPtAU3c7.exe (PID: 2464)
- gYaqqhiDI.exe (PID: 2736)
- svchost.exe (PID: 2468)
- orxds.exe (PID: 1208)
- GF6GB.exe (PID: 3316)
- powershell.EXE (PID: 5144)
- powershell.EXE (PID: 4156)
- eCYGTdT.exe (PID: 4528)
Removes files from Windows directory
- svchost.exe (PID: 872)
- IsrGSPs.exe (PID: 5912)
Executed via WMI
- rundll32.exe (PID: 2172)
- rundll32.exe (PID: 3444)
Uses RUNDLL32.EXE to load library
- wmiprvse.exe (PID: 2852)
- control.exe (PID: 1340)
- orxds.exe (PID: 1208)
- taskeng.exe (PID: 5784)
Executes application which crashes
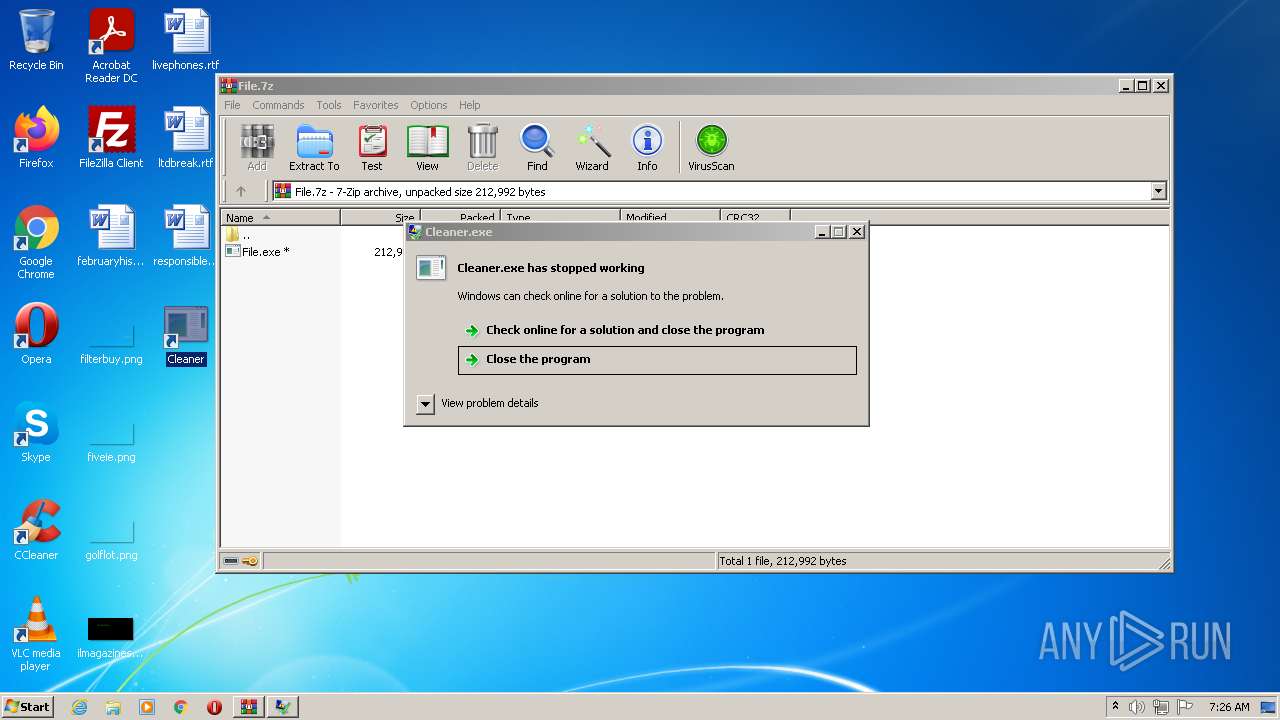
- TrdngAnlzr22649.exe.exe (PID: 2660)
Loads DLL from Mozilla Firefox
- InvisBrowser45856.exe (PID: 2064)
Starts CMD.EXE for self-deleting
- real2001.bmp.exe (PID: 2268)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3920)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 752)
Executed via Task Scheduler
- Tabivuz.exe (PID: 1312)
- orxds.exe (PID: 3348)
- powershell.EXE (PID: 5144)
- IsrGSPs.exe (PID: 5912)
- orxds.exe (PID: 5952)
- powershell.EXE (PID: 4156)
- orxds.exe (PID: 4612)
Reads default file associations for system extensions
- setup331.exe (PID: 4092)
Executes PowerShell scripts
- powershell.EXE (PID: 5144)
- powershell.EXE (PID: 4156)
Executes scripts
- IsrGSPs.exe (PID: 5912)
Creates a software uninstall entry
- eCYGTdT.exe (PID: 4528)
INFO
Checks supported languages
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 964)
- DllHost.exe (PID: 148)
- consent.exe (PID: 3044)
- DllHost.exe (PID: 2268)
- DllHost.exe (PID: 832)
- DllHost.exe (PID: 2288)
- sc.exe (PID: 3516)
- sc.exe (PID: 3824)
- sc.exe (PID: 3372)
- netsh.exe (PID: 584)
- ftp.exe (PID: 3636)
- svchost.exe (PID: 2652)
- tasklist.exe (PID: 3156)
- find.exe (PID: 2724)
- PING.EXE (PID: 3484)
- find.exe (PID: 2528)
- findstr.exe (PID: 3364)
- tasklist.exe (PID: 2680)
- svchost.exe (PID: 148)
- WerFault.exe (PID: 2248)
- DllHost.exe (PID: 2480)
- WerFault.exe (PID: 3608)
- schtasks.exe (PID: 2632)
- schtasks.exe (PID: 2352)
- svchost.exe (PID: 872)
- DllHost.exe (PID: 3360)
- schtasks.exe (PID: 3220)
- reg.exe (PID: 3992)
- DllHost.exe (PID: 2560)
- icacls.exe (PID: 3256)
- WerFault.exe (PID: 3912)
- DllHost.exe (PID: 2480)
- ftp.exe (PID: 2476)
- find.exe (PID: 3472)
- tasklist.exe (PID: 3720)
- find.exe (PID: 604)
- tasklist.exe (PID: 3136)
- svchost.exe (PID: 2468)
- rundll32.exe (PID: 2172)
- findstr.exe (PID: 3068)
- PING.EXE (PID: 3668)
- DllHost.exe (PID: 2384)
- schtasks.exe (PID: 3048)
- msiexec.exe (PID: 572)
- ntvdm.exe (PID: 3160)
- WerFault.exe (PID: 1760)
- taskkill.exe (PID: 3088)
- taskkill.exe (PID: 2964)
- DllHost.exe (PID: 3668)
- SearchFilterHost.exe (PID: 1148)
- rundll32.exe (PID: 2192)
- WerFault.exe (PID: 2108)
- control.exe (PID: 1340)
- timeout.exe (PID: 3956)
- DllHost.exe (PID: 1812)
- svchost.exe (PID: 2420)
- forfiles.exe (PID: 2300)
- svchost.exe (PID: 3296)
- reg.exe (PID: 2696)
- rundll32.exe (PID: 3444)
- cmd.exe (PID: 3120)
- reg.exe (PID: 3132)
- cmd.exe (PID: 1556)
- forfiles.exe (PID: 1024)
- schtasks.exe (PID: 4748)
- msiexec.exe (PID: 5684)
- DllHost.exe (PID: 4104)
- taskkill.exe (PID: 1204)
- schtasks.exe (PID: 1760)
- rundll32.exe (PID: 5772)
- DllHost.exe (PID: 2044)
- schtasks.exe (PID: 5672)
- schtasks.exe (PID: 5336)
- taskeng.exe (PID: 5784)
- schtasks.exe (PID: 2804)
- schtasks.exe (PID: 3328)
- gpscript.exe (PID: 4068)
- gpscript.exe (PID: 4196)
- svchost.exe (PID: 5280)
- gpupdate.exe (PID: 5808)
- gpupdate.exe (PID: 5800)
- schtasks.exe (PID: 1576)
- reg.exe (PID: 5124)
- reg.exe (PID: 6032)
- reg.exe (PID: 920)
- reg.exe (PID: 2164)
- reg.exe (PID: 5944)
- reg.exe (PID: 4404)
- reg.exe (PID: 5996)
- reg.exe (PID: 3432)
- reg.exe (PID: 3048)
- reg.exe (PID: 4300)
- reg.exe (PID: 1828)
- reg.exe (PID: 4888)
- reg.exe (PID: 2444)
- reg.exe (PID: 1204)
- reg.exe (PID: 2196)
- reg.exe (PID: 5216)
- reg.exe (PID: 4216)
- schtasks.exe (PID: 5900)
- reg.exe (PID: 5460)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4076)
- reg.exe (PID: 2336)
- reg.exe (PID: 1948)
- schtasks.exe (PID: 4336)
- schtasks.exe (PID: 4872)
- schtasks.exe (PID: 5068)
- schtasks.exe (PID: 2052)
- schtasks.exe (PID: 5444)
- schtasks.exe (PID: 5368)
- DllHost.exe (PID: 5856)
- schtasks.exe (PID: 4568)
- schtasks.exe (PID: 4812)
- schtasks.exe (PID: 3620)
- schtasks.exe (PID: 2268)
- reg.exe (PID: 4448)
- reg.exe (PID: 5876)
- schtasks.exe (PID: 3048)
- rundll32.EXE (PID: 2880)
- schtasks.exe (PID: 4080)
- svchost.exe (PID: 1204)
- WerFault.exe (PID: 2020)
- DllHost.exe (PID: 1576)
- opera.exe (PID: 5440)
Reads the computer name
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 964)
- DllHost.exe (PID: 148)
- consent.exe (PID: 3044)
- DllHost.exe (PID: 2268)
- DllHost.exe (PID: 832)
- DllHost.exe (PID: 2288)
- sc.exe (PID: 3516)
- sc.exe (PID: 3824)
- sc.exe (PID: 3372)
- netsh.exe (PID: 584)
- ftp.exe (PID: 3636)
- svchost.exe (PID: 2652)
- tasklist.exe (PID: 3156)
- tasklist.exe (PID: 2680)
- PING.EXE (PID: 3484)
- svchost.exe (PID: 148)
- WerFault.exe (PID: 2248)
- DllHost.exe (PID: 2480)
- WerFault.exe (PID: 3608)
- schtasks.exe (PID: 2632)
- schtasks.exe (PID: 2352)
- DllHost.exe (PID: 3360)
- schtasks.exe (PID: 3220)
- DllHost.exe (PID: 2560)
- icacls.exe (PID: 3256)
- WerFault.exe (PID: 3912)
- DllHost.exe (PID: 2480)
- ftp.exe (PID: 2476)
- tasklist.exe (PID: 3720)
- rundll32.exe (PID: 2172)
- tasklist.exe (PID: 3136)
- svchost.exe (PID: 2468)
- PING.EXE (PID: 3668)
- DllHost.exe (PID: 2384)
- schtasks.exe (PID: 3048)
- WerFault.exe (PID: 1760)
- taskkill.exe (PID: 2964)
- taskkill.exe (PID: 3088)
- DllHost.exe (PID: 3668)
- SearchFilterHost.exe (PID: 1148)
- DllHost.exe (PID: 1812)
- WerFault.exe (PID: 2108)
- control.exe (PID: 1340)
- svchost.exe (PID: 3296)
- svchost.exe (PID: 2420)
- rundll32.exe (PID: 3444)
- schtasks.exe (PID: 4748)
- DllHost.exe (PID: 4104)
- taskkill.exe (PID: 1204)
- schtasks.exe (PID: 1760)
- rundll32.exe (PID: 5772)
- DllHost.exe (PID: 2044)
- schtasks.exe (PID: 5336)
- schtasks.exe (PID: 5672)
- taskeng.exe (PID: 5784)
- schtasks.exe (PID: 2804)
- schtasks.exe (PID: 3328)
- gpupdate.exe (PID: 5800)
- svchost.exe (PID: 5280)
- gpupdate.exe (PID: 5808)
- schtasks.exe (PID: 1576)
- schtasks.exe (PID: 5900)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4076)
- schtasks.exe (PID: 4336)
- schtasks.exe (PID: 5068)
- schtasks.exe (PID: 2052)
- schtasks.exe (PID: 5368)
- schtasks.exe (PID: 5444)
- schtasks.exe (PID: 4872)
- DllHost.exe (PID: 5856)
- schtasks.exe (PID: 4568)
- schtasks.exe (PID: 4812)
- schtasks.exe (PID: 3620)
- schtasks.exe (PID: 2268)
- schtasks.exe (PID: 3048)
- schtasks.exe (PID: 4080)
- rundll32.EXE (PID: 2880)
- DllHost.exe (PID: 1576)
- svchost.exe (PID: 1204)
- WerFault.exe (PID: 2020)
- opera.exe (PID: 5440)
Application launched itself
- iexplore.exe (PID: 1332)
Reads settings of System Certificates
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 964)
- File.exe (PID: 3152)
- Offscum.exe.exe (PID: 2200)
- Service.bmp.exe (PID: 3984)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- wam.exe.exe (PID: 1104)
- random.exe.exe (PID: 3272)
- real2001.bmp.exe (PID: 2268)
- test33.bmp.exe (PID: 1036)
- ll.exe (PID: 2516)
- svchost.exe (PID: 2468)
- build2.exe (PID: 2656)
- GF6GB.exe (PID: 3316)
- InvisBrowser45856.exe (PID: 2064)
- lokes_1.bmp.exe (PID: 3928)
- eCYGTdT.exe (PID: 4528)
Checks Windows Trust Settings
- iexplore.exe (PID: 964)
- iexplore.exe (PID: 1332)
- consent.exe (PID: 3044)
- File.exe (PID: 3152)
- test33.bmp.exe (PID: 908)
- hYZk5OKaJqjyyX5kRuSkitei.exe (PID: 2376)
- real2001.bmp.exe (PID: 2268)
- test33.bmp.exe (PID: 1036)
- svchost.exe (PID: 2468)
- build2.exe (PID: 2656)
- powershell.EXE (PID: 4156)
- powershell.EXE (PID: 5144)
- wscript.exe (PID: 5416)
- eCYGTdT.exe (PID: 4528)
Changes internet zones settings
- iexplore.exe (PID: 1332)
Reads internet explorer settings
- iexplore.exe (PID: 964)
Reads the date of Windows installation
- iexplore.exe (PID: 1332)
- opera.exe (PID: 5440)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1332)
Creates files in the user directory
- iexplore.exe (PID: 1332)
- opera.exe (PID: 5440)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1332)
Changes settings of System certificates
- iexplore.exe (PID: 1332)
Reads CPU info
- svchost.exe (PID: 2468)
Application was dropped or rewritten from another process
- setup.tmp (PID: 1256)
- setup.tmp (PID: 3064)
Loads dropped or rewritten executable
- setup.tmp (PID: 1256)
- setup.tmp (PID: 3064)
Creates a software uninstall entry
- setup.tmp (PID: 3064)
Manual execution by user
- Cleaner.exe (PID: 4732)
- opera.exe (PID: 5440)
Check for Java to be installed
- opera.exe (PID: 5440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(2356) rrmix.exe.exe
C2 (1)193.233.48.58:38989
BotnetRuzki
Err_msg
Auth_value80c38cc7772c328c028b0e4f42a3fac6
US (200)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
80c38cc7772c328c028b0e4f42a3fac6
Authorization
ns1
UNKNWON
GSYCFyEDJx0ZC11dIipaVhs2BhciLQVTGyNUUA==
ARw/WwxbBVo=
Trimming
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
System.Core, Version=3.5.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089
System.Security.Cryptography.AesCryptoServiceProvider
9b0kgil4ep7.rmtpkxubprxrd9
{11111-22222-10009-11111}
{11111-22222-50001-00000}
GetDelegateForFunctionPointer
v4wb21iq4l82.v4a44yl6tx
m_ptr
System.Reflection.RuntimeModule
m_pData
clrjit.dll
System.Reflection.ReflectionContext
__
file:///
Location
Find
ResourceA
Virtual
Alloc
Write
Process
Protect
Open
Close
Handle
kernel
32.dll
{11111-22222-10001-00001}
{11111-22222-10001-00002}
{11111-22222-20001-00001}
{11111-22222-20001-00002}
{11111-22222-40001-00001}
{11111-22222-40001-00002}
{11111-22222-50001-00001}
{11111-22222-50001-00002}
(PID) Process(916) AppLaunch.exe
C2 (1)91.211.251.186:41933
Botnetruz
Err_msg
Auth_valueb5178f81ea8830c13e88c402dccf09f0
US (165)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
b5178f81ea8830c13e88c402dccf09f0
Authorization
ns1
UNKNWON
GTUpAzgGIAsaCyVHOD9RCxklNUA7KCBGGxshSw==
NQ86QA==
Valvules
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
Network\
String
Replace
80
81
0.0.0.0
(PID) Process(3712) AppLaunch.exe
C2 (1)65.108.101.231:14648
BotnetSUSHI
Err_msg
Auth_value26bcdf6ae8358a98f24ebd4bd8ec3714
US (165)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
26bcdf6ae8358a98f24ebd4bd8ec3714
Authorization
ns1
UNKNWON
HA8lBygnMl0iDRcSPSFRCj4TK1EfMSFAKzcUVA==
B1QmJjY2GFQ=
Repressing
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
(PID) Process(2584) AppLaunch.exe
C2 (1)194.36.177.138:81
BotnetROK
Err_msg
Auth_value17f65f419822bba9db958b4ac6cc9f05
US (163)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
17f65f419822bba9db958b4ac6cc9f05
Authorization
ns1
UNKNWON
DzUMQCUaKEA/KCRUPhBEHT8JJVcoNCxN
FwpePA==
Bagpipers
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
Network\
String
Replace
80
81
0.0.0.0
(PID) Process(3564) AppLaunch.exe
C2 (1)185.215.113.24:15994
Botnet@humus228p
Err_msg
Auth_valuebb99a32fdff98741feb69d524760afae
US (165)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
bb99a32fdff98741feb69d524760afae
Authorization
ns1
UNKNWON
HCEIRTkHGA0hJ0EVHCEiATgHAEMiICBYHiE+SQ==
ADIHRRc1Bw8iHjxZMjRSSQ==
Quotum
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
(PID) Process(1600) AppLaunch.exe
C2 (1)193.124.22.34:19489
Botnetruz19489
Err_msg
Auth_value2b3af4bdf5e7f4f41faf1150d1660073
US (163)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
2b3af4bdf5e7f4f41faf1150d1660073
Authorization
ns1
UNKNWON
HzEdEyAPISsrNV0VKA1mHzgtAx0rBjRCJj1YWQ==
MQsgXyExD2IqMgJR
Reviled
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
Network\
String
Replace
80
81
0.0.0.0
(PID) Process(3248) 9817bcdf33322e8fbc1670e731c76126.exe
C2 (1)elew3le3lanle.freeddns.org:4633
Botnetn1k0y11
Err_msg
Auth_value5b8edd43c63faa6789619650019aee17
US (163)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Host
Port
:
User
Pass
cookies.sqlite
%USEDisposeRPROFILE%\AppDaDisposeta\LDisposeocal
Dispose
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrstring.EmptyyptOpestring.EmptynAlgorithmProvistring.Emptyder
string.Empty
BCruintyptCloseAlgorituinthmProvuintider
uint
BCrUnmanagedTypeyptDecrUnmanagedTypeypt
UnmanagedType
BCrbyte[]yptDesbyte[]troyKbyte[]ey
byte[]
BCpszPropertyryptGepszPropertytPropepszPropertyrty
pszProperty
BCEncodingryptSEncodingetPrEncodingoperEncodingty
Encoding
BCrbMasterKeyyptImbMasterKeyportKbMasterKeyey
bMasterKey
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
{0}
net.tcp://
/
localhost
5b8edd43c63faa6789619650019aee17
Authorization
ns1
UNKNWON
GTgfAgsMJwcpFyEUNzhDGi4gdgIEAzkaMzMhNgweWxkVBBdFDSs+FCIBVEk=
IQUhHCI+Agw+ElJa
Cognovits
Yandex\YaAddon
ToString
asf
*wallet*
ZmZuYmVsZmRvZWlvaGVua2ppYm5tYWRqaWVoamhhamJ8WW9yb2lXYWxsZXQKaWJuZWpkZmptbWtwY25scGVia2xtbmtvZW9paG9mZWN8VHJvbmxpbmsKamJkYW9jbmVpaWlubWpiamxnYWxoY2VsZ2Jlam1uaWR8TmlmdHlXYWxsZXQKbmtiaWhmYmVvZ2FlYW9laGxlZm5rb2RiZWZncGdrbm58TWV0YW1hc2sKYWZiY2JqcGJwZmFkbGttaG1jbGhrZWVvZG1hbWNmbGN8TWF0aFdhbGxldApobmZhbmtu...
_
T
e
l
gr
am
ex
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
Armenia
Azerbaijan
Belarus
Kazakhstan
Kyrgyzstan
Moldova
Tajikistan
Uzbekistan
Ukraine
Russia
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
Network\
String
Replace
80
81
0.0.0.0
Tofsee
(PID) Process(2652) svchost.exe
C2 (2)niflheimr.cn
jotunheim.name
Encrypted Strings (59)c:\Windows
\system32\
ImagePath
.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
MSConfig
/r
.exe
cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s
svchost.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
ConsentPromptBehaviorAdmin
PromptOnSecureDesktop
MSConfig
:.repos
USERPROFILE
\Local Settings:.repos
USERPROFILE
\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos
USERPROFILE
\wincookie.repos
TMP
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
SYSTEM\CurrentControlSet\services
ImagePath
SYSTEM\CurrentControlSet\services
SYSTEM\CurrentControlSet\services
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
.exe
qazwsxed
%s%i%i%i%i.bat
@echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0
svchost.exe
.exe
/u
USERPROFILE
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/d
/e
/d
/e
.exe
"%s" /u"%s"
USERPROFILE
.exe
USERPROFILE
USERPROFILE
ver=%d lid=%d
win=%X/%d sid=%s
rep=%s
Amadey
(PID) Process(1208) orxds.exe
C2 (1)185.215.113.38/f8dfksdj3/index.php
Version3.10
Strings (92)8c7aecc852
orxds.exe
SCHTASKS
/Create /SC MINUTE /MO 1 /TN
/TR "
" /F
/C REG ADD "HKCU\Software\Micro=oft\Windows\CurrentVersion\Expl9rer\User Shell Folders" /f /v S>artup /t REG_SZ /d
cmd
SOFTWARE\Microsoft\Windows\Curr/ntVersion\Explorer\Shell Folder=
Startup
/C REG ADD "HKCU\SOFTWARE\Micro=oft\Windows\CurrentVersion\RunO8ce" /f /v rem /t REG_SZ /d
"cmd /C RMDIR /s/q "
SOFTWARE\Microsoft\Windows\Curr/ntVersion\Run
rundll32
/Delete /TN "
powershell
-Command $action = New-Schedule.TaskAction -Execute '
'; $time = New-TimeSpan -Minute= 1; $trigger = New-ScheduledTas5Trigger -Once -At 0:00 -Repetit3onInterval $time; Register-Sche.uledTask -Action $action -Trigg/r $trigger -TaskName '
-Command $action = Unregister-S-heduledTask -TaskName '
-Confirm: $false
POST
GET
id=
&vs=
&sd=
&os=
&bi=
&ar=
&pc=
&un=
&dm=
&av=
&lv=
cred.dll|
Main
http://
https://
exe
dll
<c>
<d>
Plugins/
+++
&unit=
shell32.dll
kernel32.dll
GetNativeSystemInfo
ProgramData\
AVAST Software
Avira
Kaspersky Lab
ESET
Panda Security
Doctor Web
AVG
360TotalSecurity
Bitdefender
Norton
Sophos
Comodo
WinDefender
0123456789
Content-Type: multipart/form-da>a; boundary=----
------
?scr=1
.jpg
Content-Type: application/x-www÷form-urlencoded
SYSTEM\CurrentControlSet\Contro6\ComputerName\ComputerName
ComputerName
-unicode-
SYSTEM\CurrentControlSet\Contro6\UnitedVideo\CONTROL\VIDEO\
SYSTEM\ControlSet001\Services\B+sicDisplay\Video
VideoID
\0000
DefaultSettings.XResolution
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows NT\C?rrentVersion
ProductName
2019
2022
2016
CurrentBuild
cmd.exe
/c echo Y|CACLS "
" /P "
:N"
/c CACLS "
:R" /E
:F" /E
AppData
:::
rundll32.exe
(PID) Process(3348) orxds.exe
C2 (1)185.215.113.38/f8dfksdj3/index.php
Version3.10
Strings (92)8c7aecc852
orxds.exe
SCHTASKS
/Create /SC MINUTE /MO 1 /TN
/TR "
" /F
/C REG ADD "HKCU\Software\Micro=oft\Windows\CurrentVersion\Expl9rer\User Shell Folders" /f /v S>artup /t REG_SZ /d
cmd
SOFTWARE\Microsoft\Windows\Curr/ntVersion\Explorer\Shell Folder=
Startup
/C REG ADD "HKCU\SOFTWARE\Micro=oft\Windows\CurrentVersion\RunO8ce" /f /v rem /t REG_SZ /d
"cmd /C RMDIR /s/q "
SOFTWARE\Microsoft\Windows\Curr/ntVersion\Run
rundll32
/Delete /TN "
powershell
-Command $action = New-Schedule.TaskAction -Execute '
'; $time = New-TimeSpan -Minute= 1; $trigger = New-ScheduledTas5Trigger -Once -At 0:00 -Repetit3onInterval $time; Register-Sche.uledTask -Action $action -Trigg/r $trigger -TaskName '
-Command $action = Unregister-S-heduledTask -TaskName '
-Confirm: $false
POST
GET
id=
&vs=
&sd=
&os=
&bi=
&ar=
&pc=
&un=
&dm=
&av=
&lv=
cred.dll|
Main
http://
https://
exe
dll
<c>
<d>
Plugins/
+++
&unit=
shell32.dll
kernel32.dll
GetNativeSystemInfo
ProgramData\
AVAST Software
Avira
Kaspersky Lab
ESET
Panda Security
Doctor Web
AVG
360TotalSecurity
Bitdefender
Norton
Sophos
Comodo
WinDefender
0123456789
Content-Type: multipart/form-da>a; boundary=----
------
?scr=1
.jpg
Content-Type: application/x-www÷form-urlencoded
SYSTEM\CurrentControlSet\Contro6\ComputerName\ComputerName
ComputerName
-unicode-
SYSTEM\CurrentControlSet\Contro6\UnitedVideo\CONTROL\VIDEO\
SYSTEM\ControlSet001\Services\B+sicDisplay\Video
VideoID
\0000
DefaultSettings.XResolution
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows NT\C?rrentVersion
ProductName
2019
2022
2016
CurrentBuild
cmd.exe
/c echo Y|CACLS "
" /P "
:N"
/c CACLS "
:R" /E
:F" /E
AppData
:::
rundll32.exe
Total processes
337
Monitored processes
306
Malicious processes
121
Suspicious processes
50
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4032.31638\File.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4032.31638\File.exe | — | WinRAR.exe | |||||||||||
User: admin Company: ForceMin Integrity Level: MEDIUM Description: ForceMin Exit code: 3221226540 Version: 1.3.21001.2 Modules
| |||||||||||||||
| 148 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 148 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | \??\C:\Windows\system32\conhost.exe "-489118971-4459609-1275391461535746290-1986735221-708399636343974051785506568" | \??\C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 572 | "C:\Windows\System32\msiexec.exe" -y .\DKFg.kg | C:\Windows\System32\msiexec.exe | — | search_hyperfs_310.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 2147943514 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\system32\svchost.exe" enable=yes>nul | C:\Windows\System32\netsh.exe | — | 13.php.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | find /I /N "psuaservice.exe" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Windows\System32\cmd.exe" /c taskkill /im "mixinte2001.bmp.exe" /f & erase "C:\Users\admin\Pictures\Adobe Films\mixinte2001.bmp.exe" & exit | C:\Windows\System32\cmd.exe | — | mixinte2001.bmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 780 | "C:\Users\admin\Pictures\Adobe Films\setup777.exe.exe" | C:\Users\admin\Pictures\Adobe Films\setup777.exe.exe | — | hYZk5OKaJqjyyX5kRuSkitei.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 832 | C:\Windows\system32\DllHost.exe /Processid:{E10F6C3A-F1AE-4ADC-AA9D-2FE65525666E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
128 199
Read events
126 342
Write events
1 798
Delete events
59
Modification events
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 435232736 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960859 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 735392736 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960859 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
118
Suspicious files
135
Text files
168
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA3BACC2551A769D2.TMP | gmc | |
MD5:— | SHA256:— | |||
| 964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\File[1].7z | compressed | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\File.7z | compressed | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{610823CE-D8CE-11EC-8C9F-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\File.7z.6hl2w22.partial | compressed | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF359E22F839A7646C.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{579430FB-D8CE-11EC-8C9F-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
133
TCP/UDP connections
335
DNS requests
105
Threats
477
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | File.exe | HEAD | 200 | 45.144.225.57:80 | http://45.144.225.57/download/NiceProcessX32.bmp | unknown | — | — | malicious |
3152 | File.exe | HEAD | 200 | 193.233.48.74:80 | http://193.233.48.74/rrmix.exe | RU | — | — | suspicious |
3152 | File.exe | HEAD | 200 | 212.193.30.29:80 | http://212.193.30.29/WW/file1.exe | RU | — | — | malicious |
3152 | File.exe | HEAD | 404 | 212.193.30.29:80 | http://212.193.30.29/WW/file2.exe | RU | — | — | malicious |
3152 | File.exe | HEAD | 200 | 193.233.48.98:80 | http://193.233.48.98/Offscum.exe | RU | — | — | suspicious |
3152 | File.exe | HEAD | 200 | 193.106.191.190:80 | http://193.106.191.190/SetupMEXX.exe | RU | — | — | malicious |
3152 | File.exe | HEAD | 200 | 45.144.225.57:80 | http://45.144.225.57/download/Service.bmp | unknown | — | — | malicious |
3152 | File.exe | HEAD | 404 | 212.193.30.29:80 | http://212.193.30.29/WW/file4.exe | RU | — | — | malicious |
3152 | File.exe | HEAD | — | 31.41.244.81:80 | http://31.41.244.81:9080/13.php | RU | — | — | suspicious |
3152 | File.exe | GET | 200 | 212.193.30.21:80 | http://212.193.30.21/base/api/statistics.php | RU | binary | 94 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | File.exe | 31.41.244.81:80 | — | LLC DARNET | RU | suspicious |
3152 | File.exe | 193.233.48.74:80 | — | OOO FREEnet Group | RU | suspicious |
3152 | File.exe | 212.193.30.29:80 | — | — | RU | malicious |
3152 | File.exe | 193.106.191.190:80 | — | LLC Kras-Host | RU | malicious |
964 | iexplore.exe | 162.159.134.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
1332 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1332 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1332 | iexplore.exe | 95.140.236.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | whitelisted |
964 | iexplore.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
1332 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
pastebin.com |
| malicious |
ipinfo.io |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
964 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
964 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3152 | File.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3152 | File.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3152 | File.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3152 | File.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3152 | File.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3152 | File.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3152 | File.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3152 | File.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
214 ETPRO signatures available at the full report