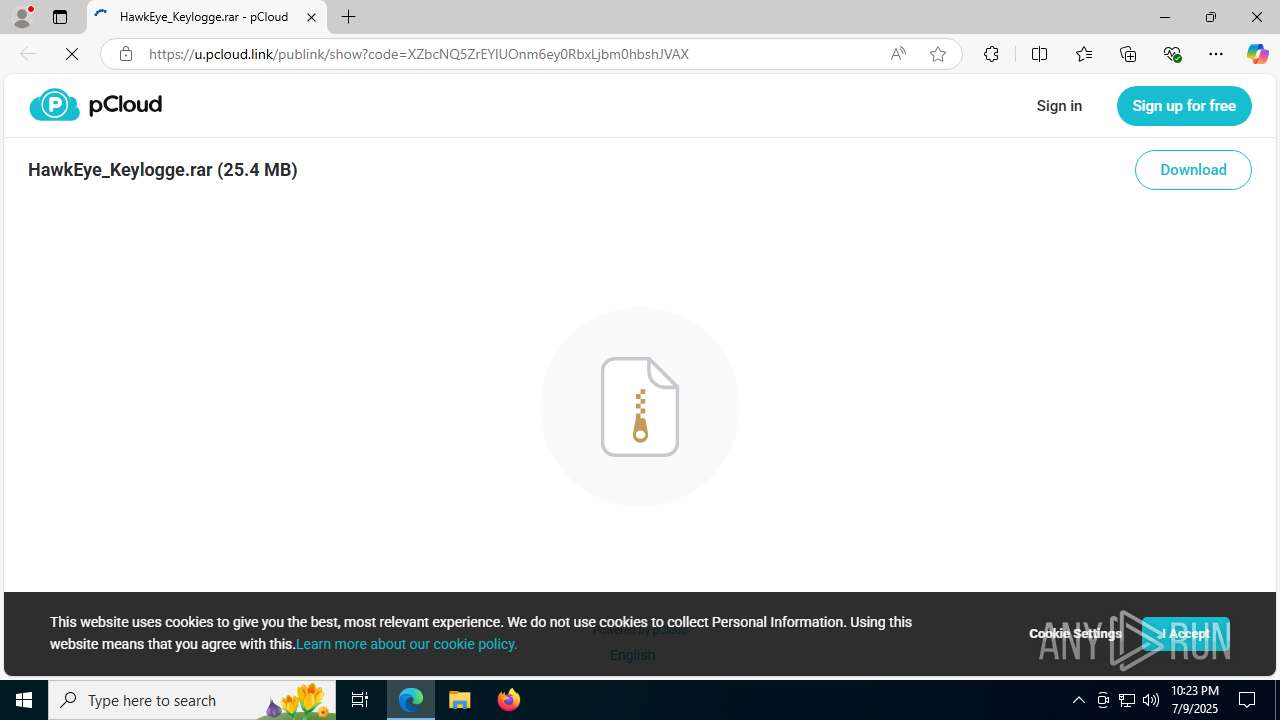
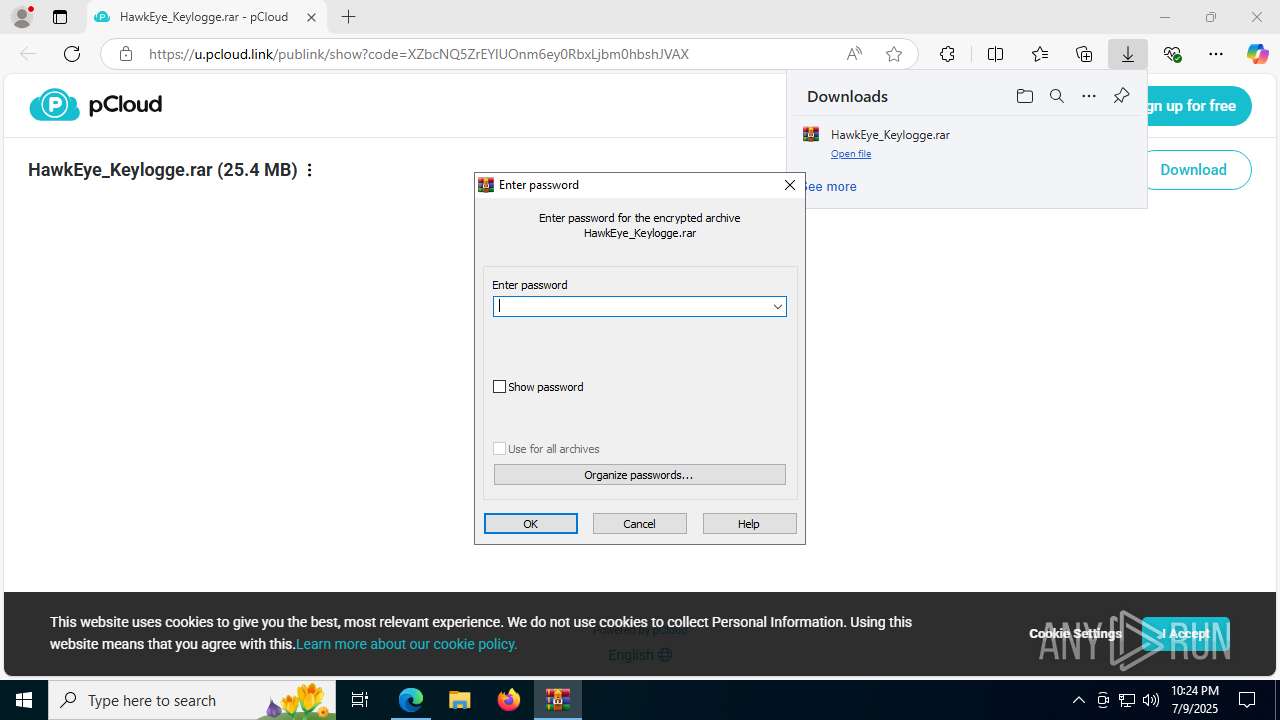
| URL: | https://u.pcloud.link/publink/show?code=XZbcNQ5ZrEYlUOnm6ey0RbxLjbm0hbshJVAX |
| Full analysis: | https://app.any.run/tasks/05a991a1-5054-4555-97af-e4dc3186d1fe |
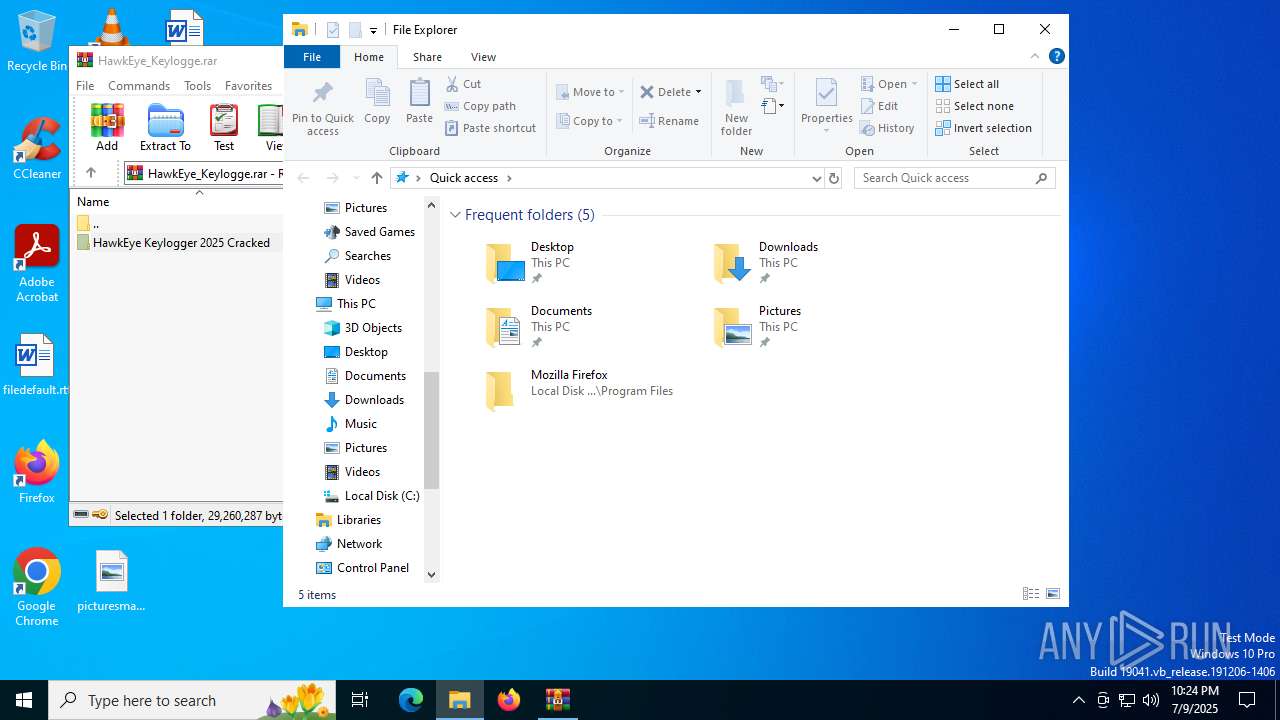
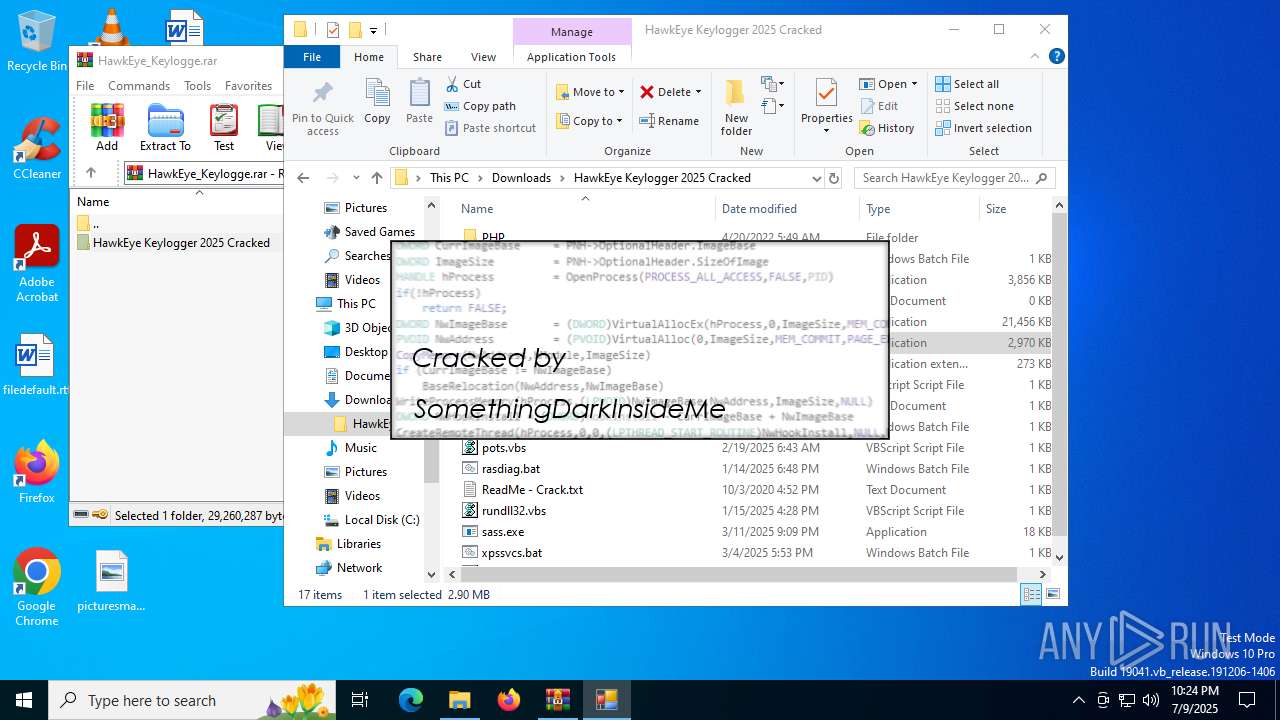
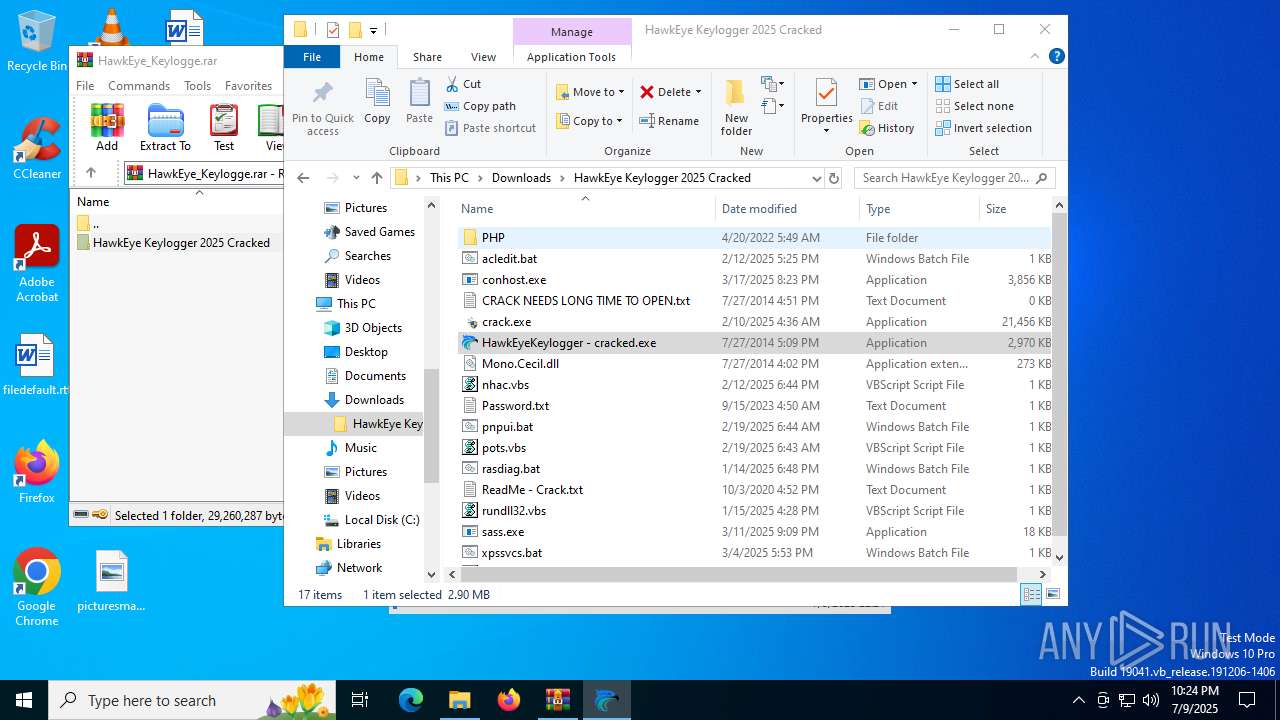
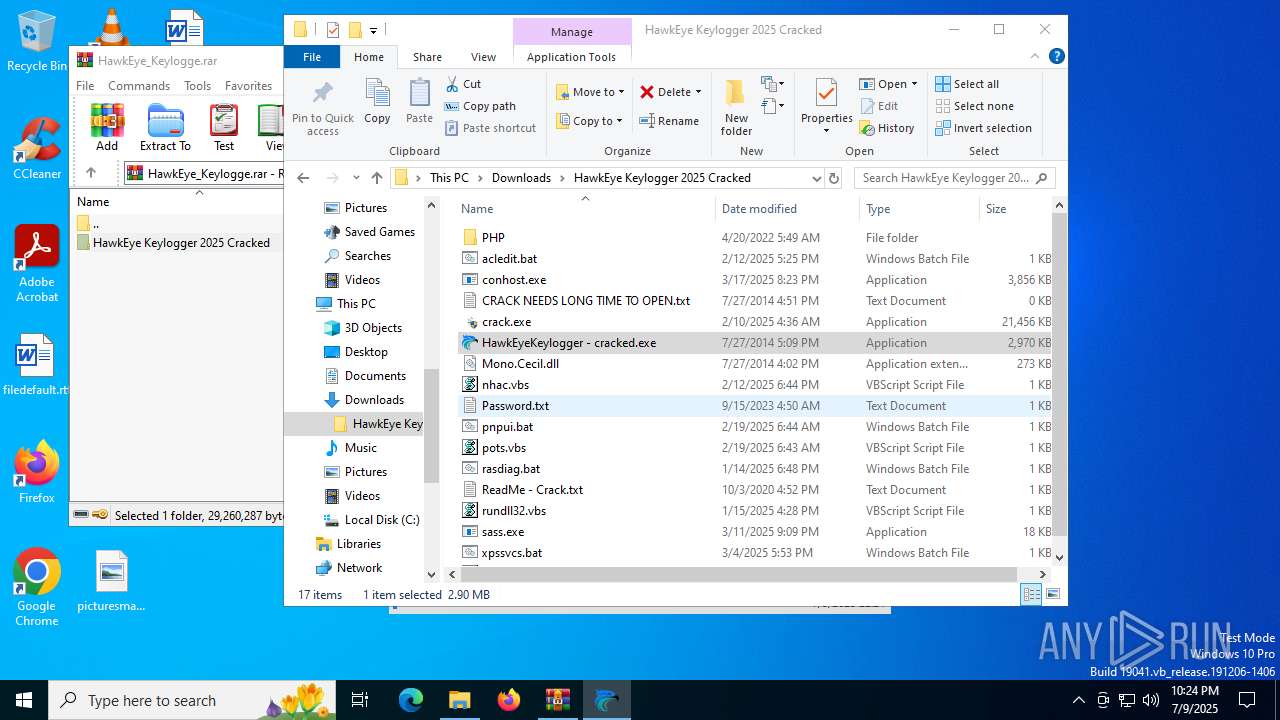
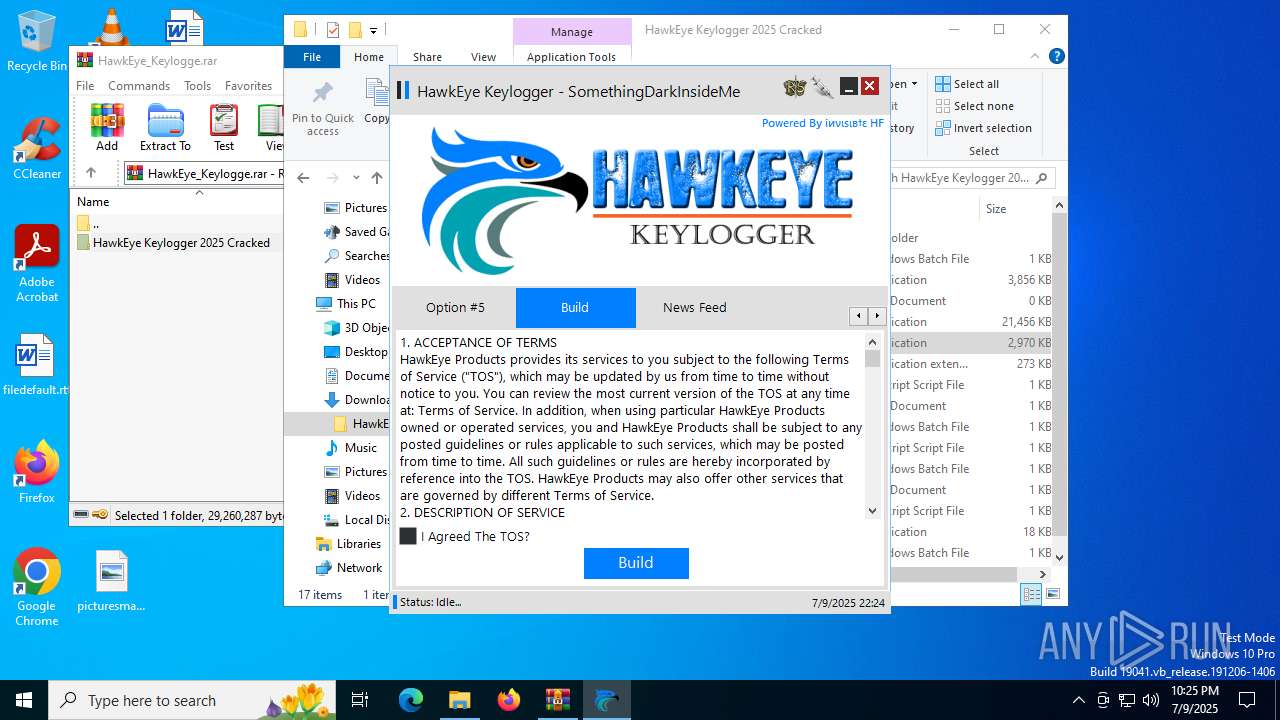
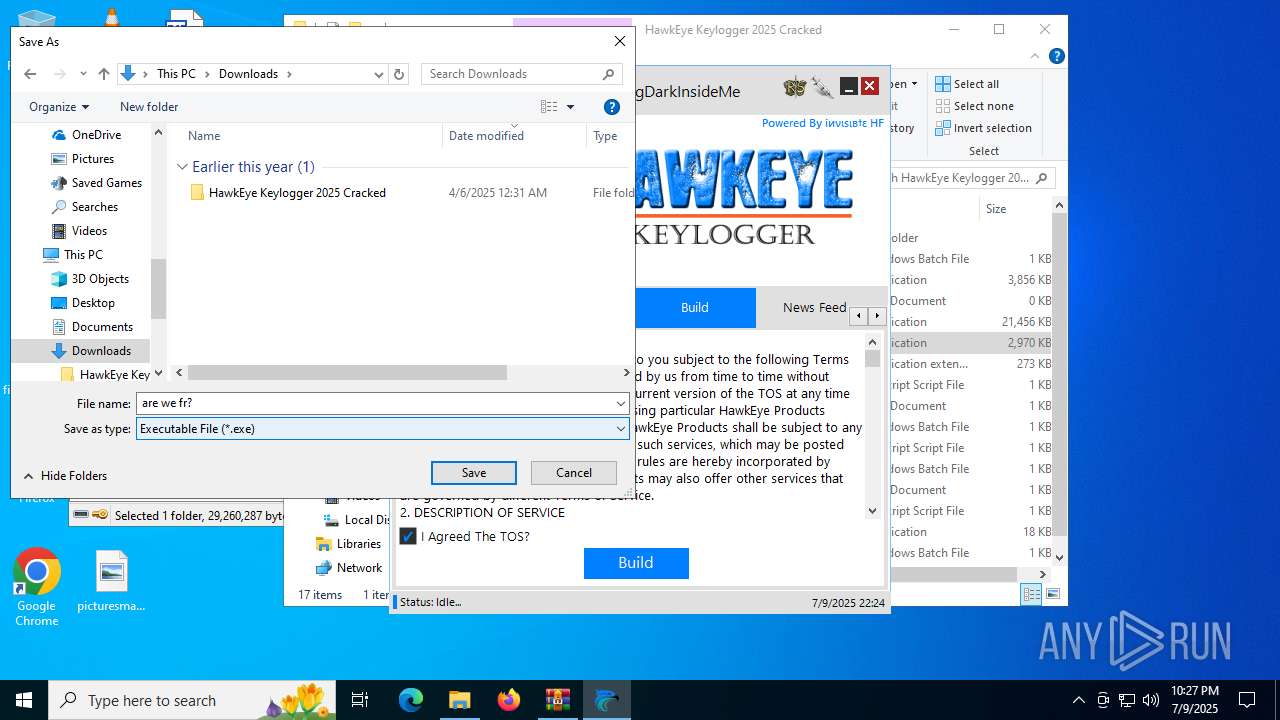
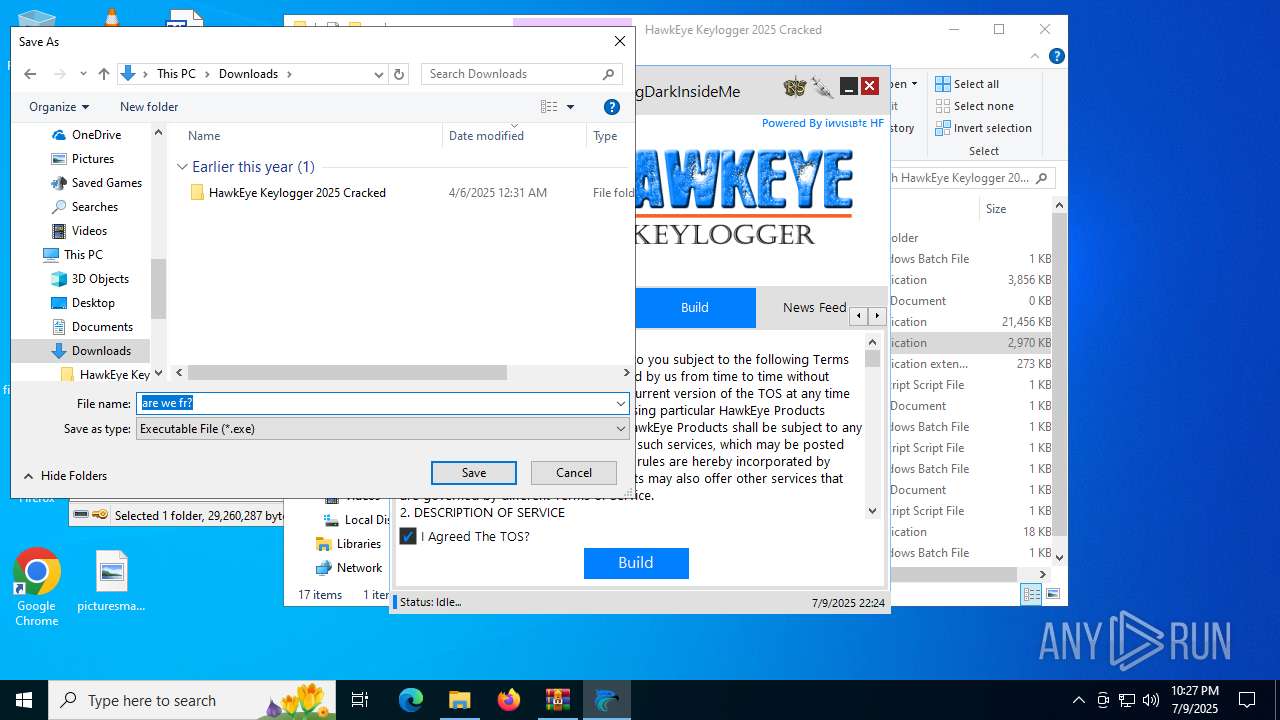
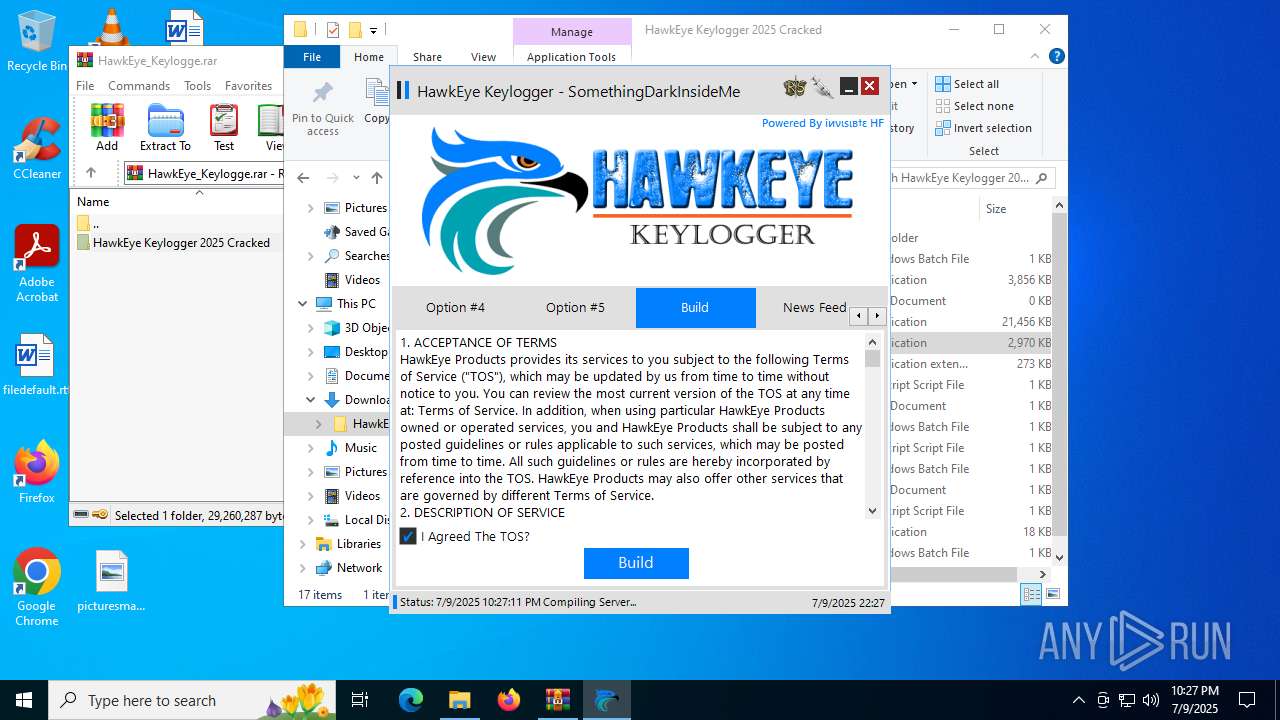
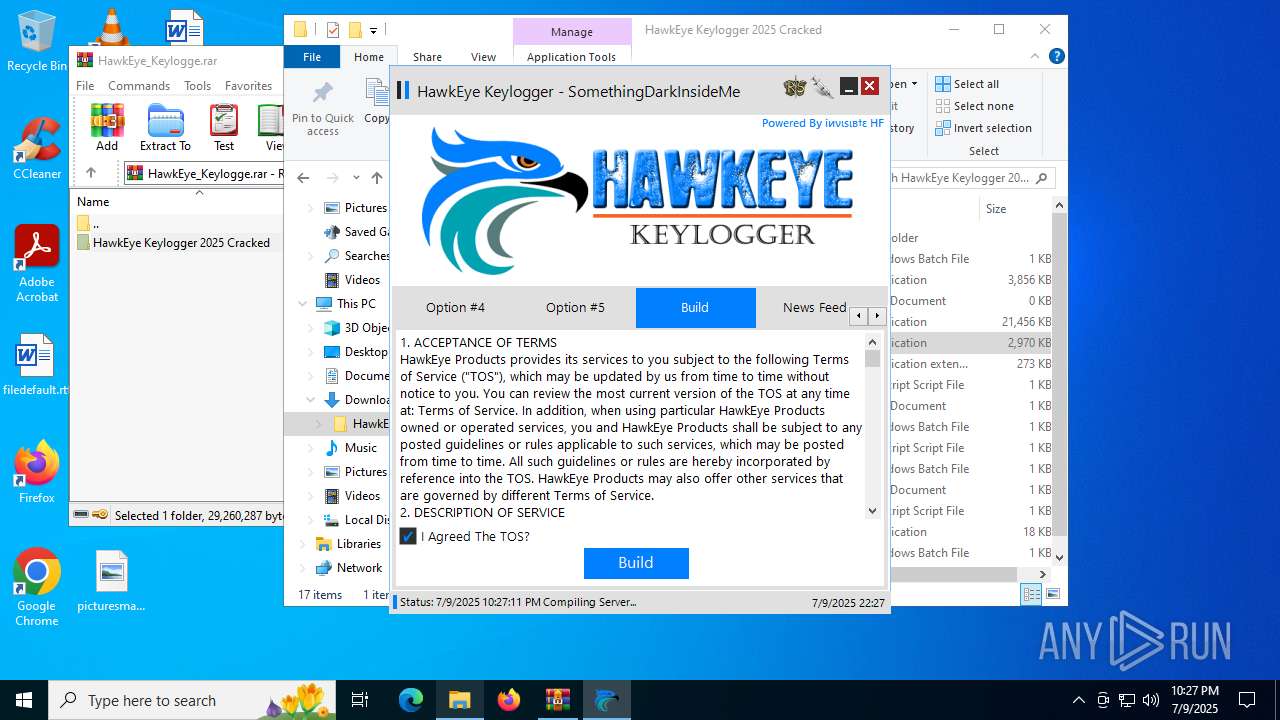
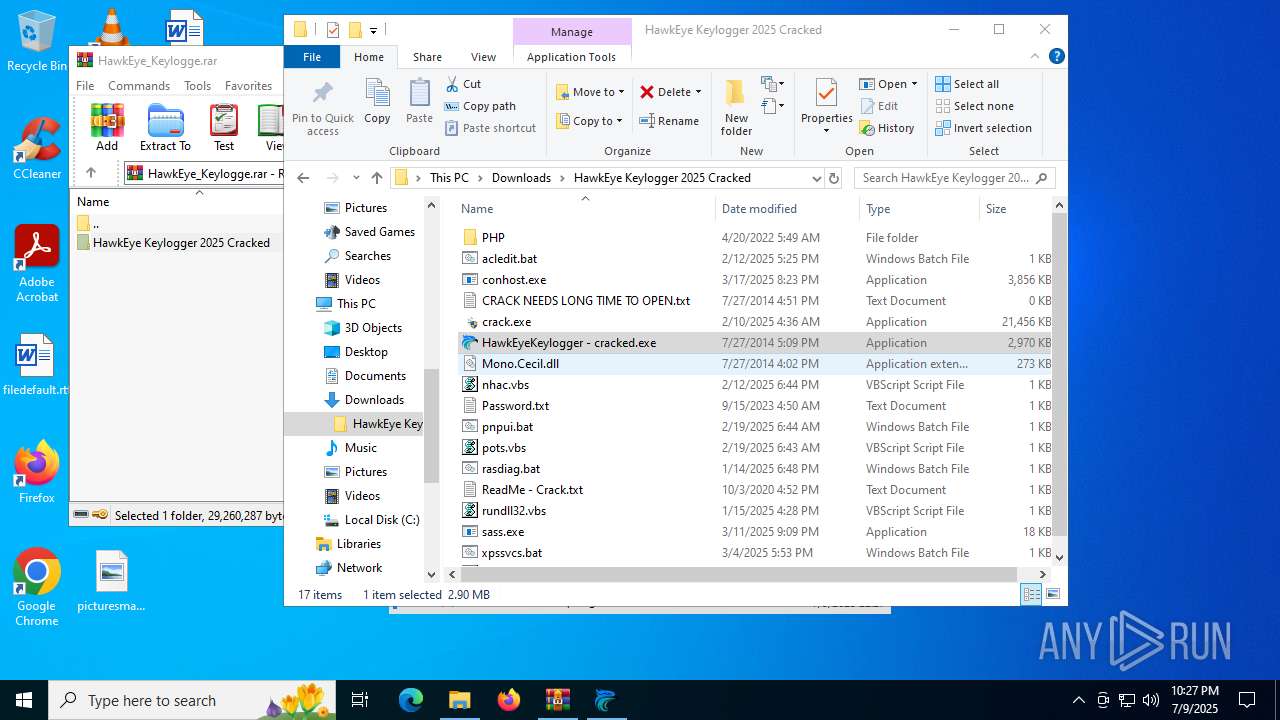
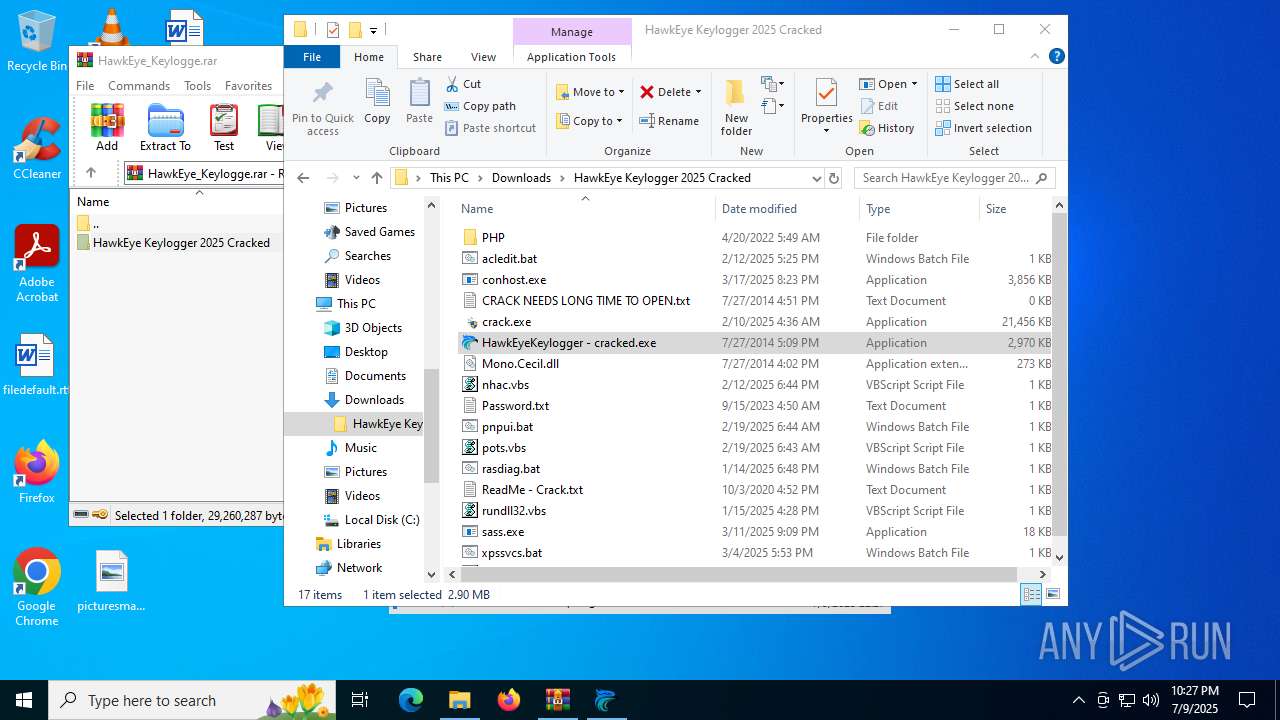
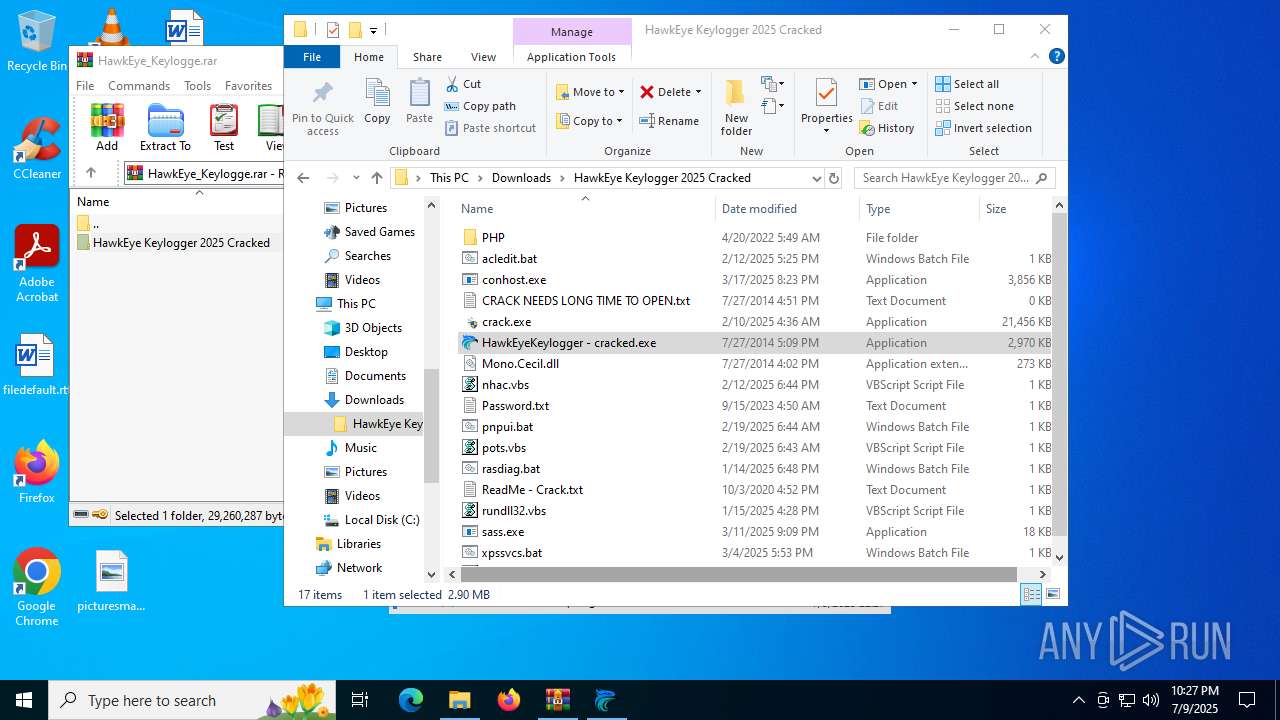
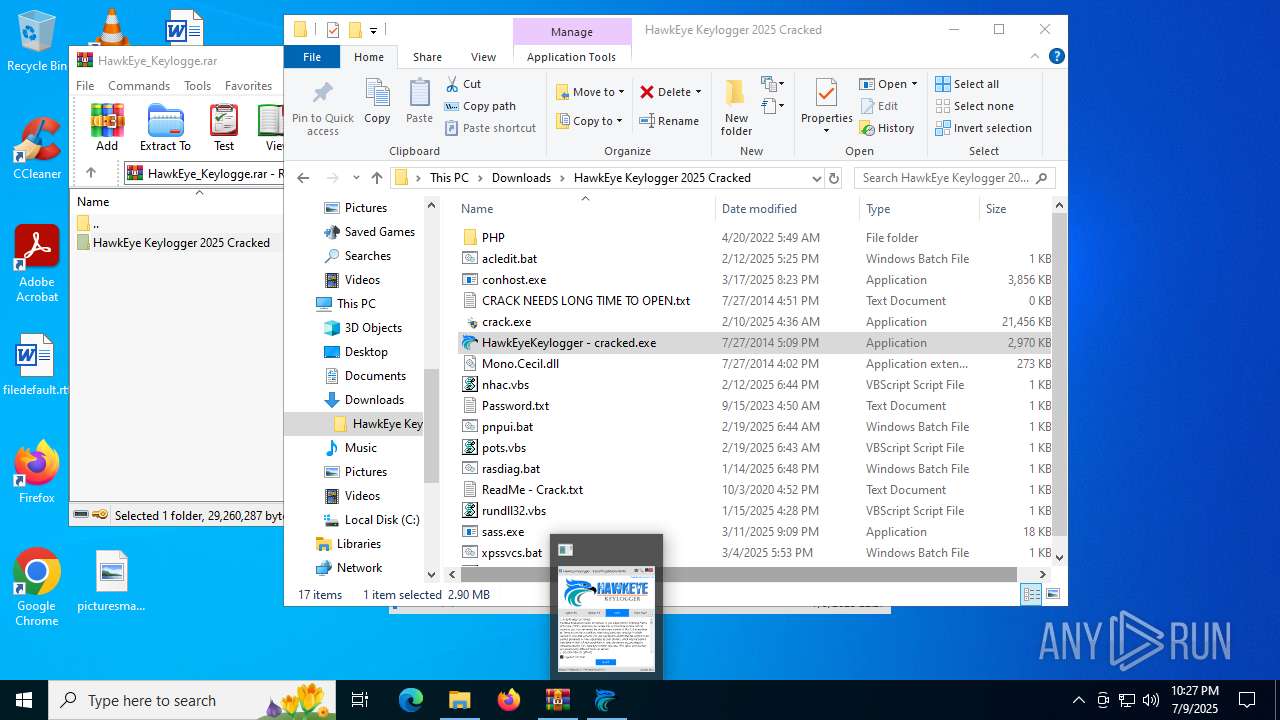
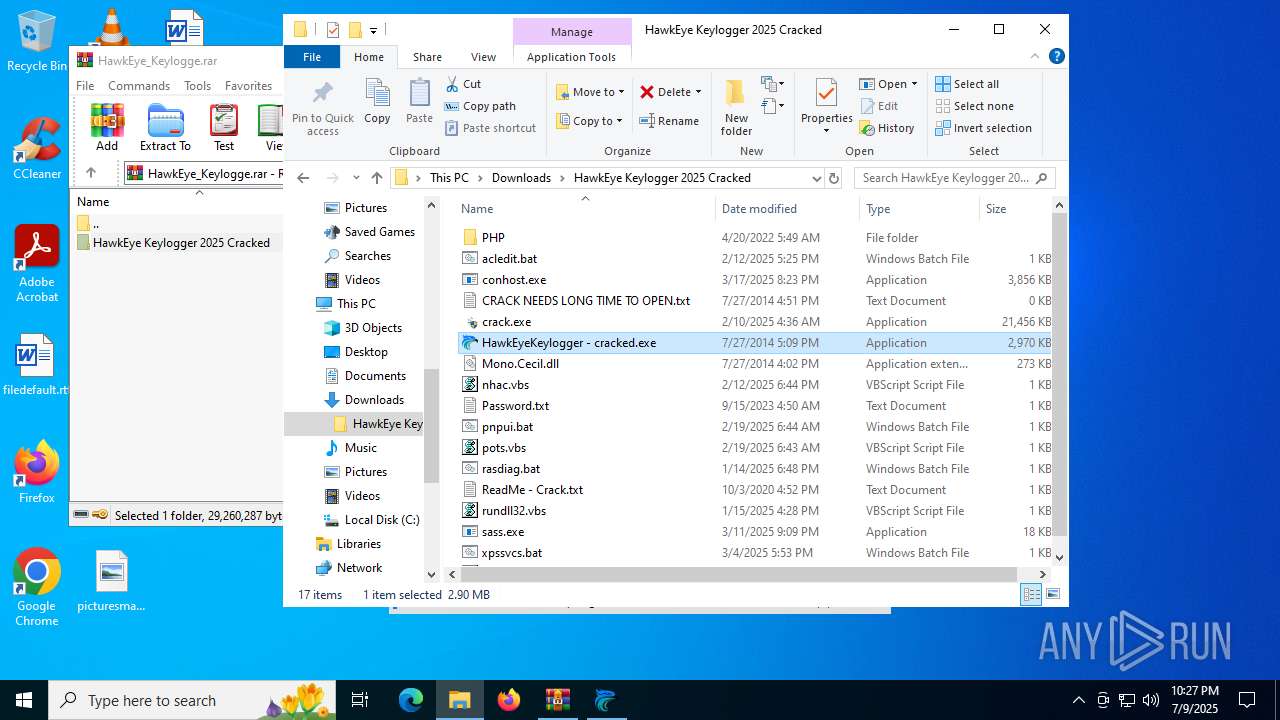
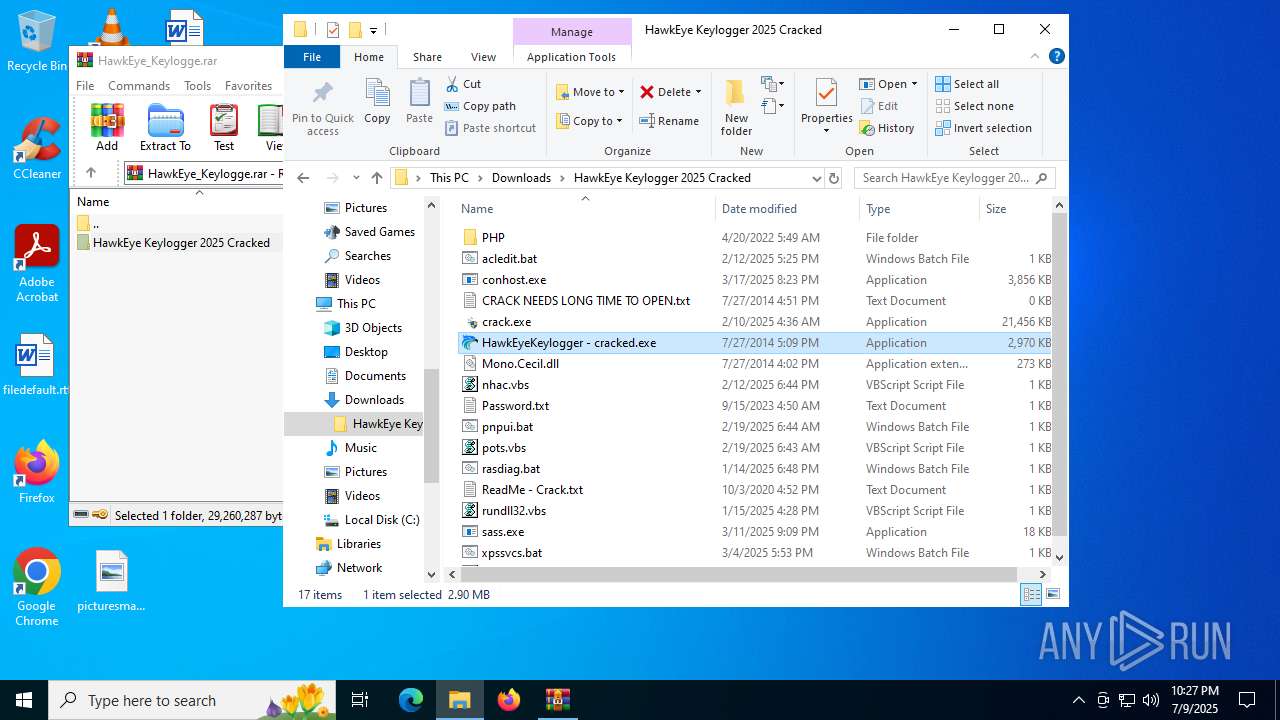
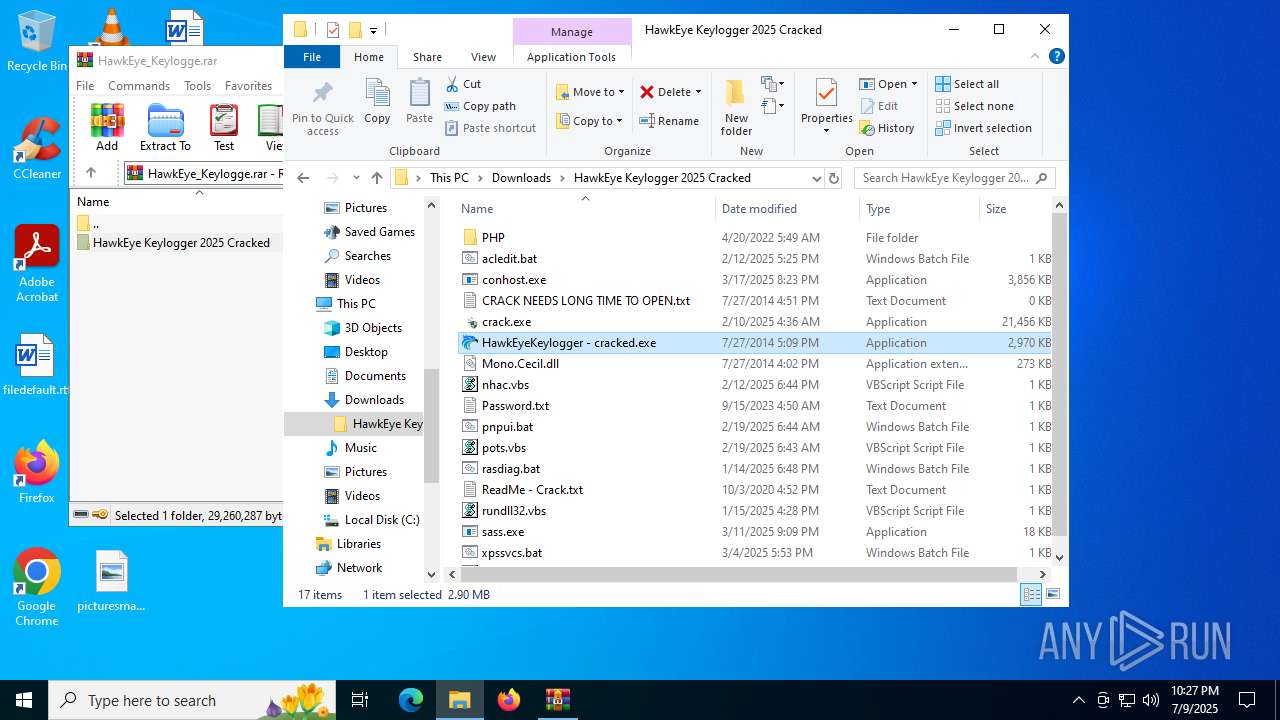
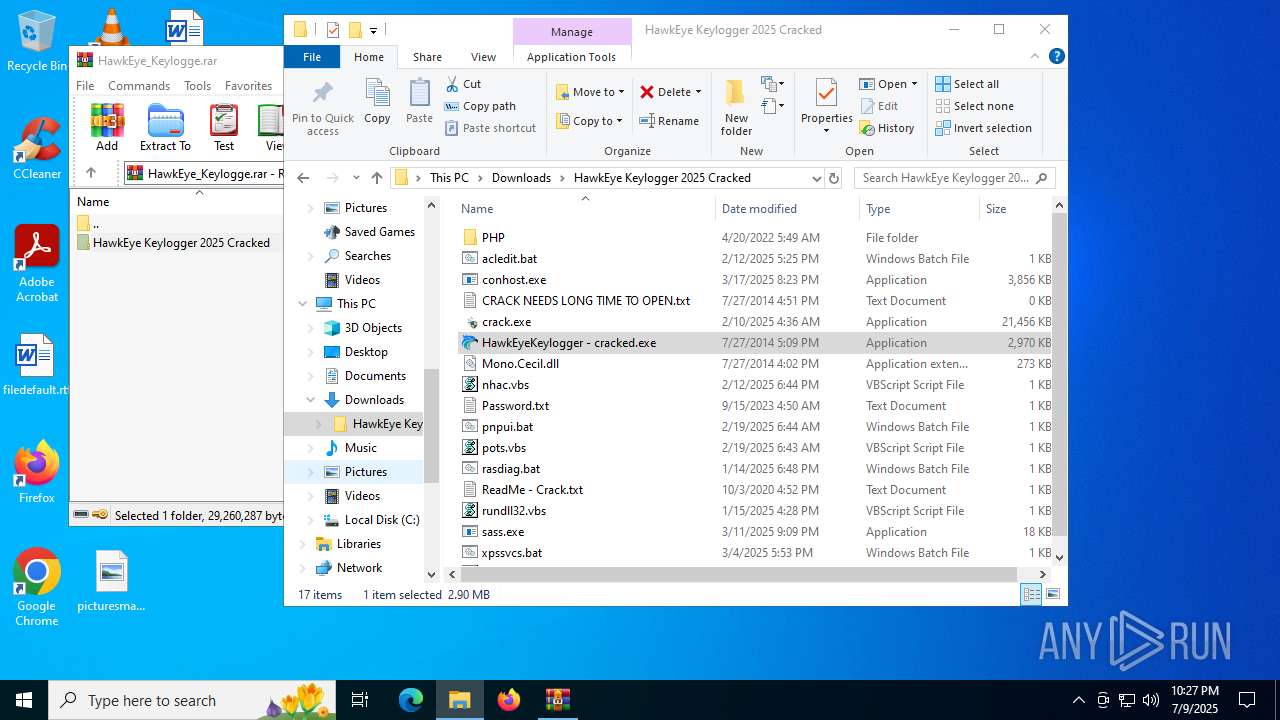
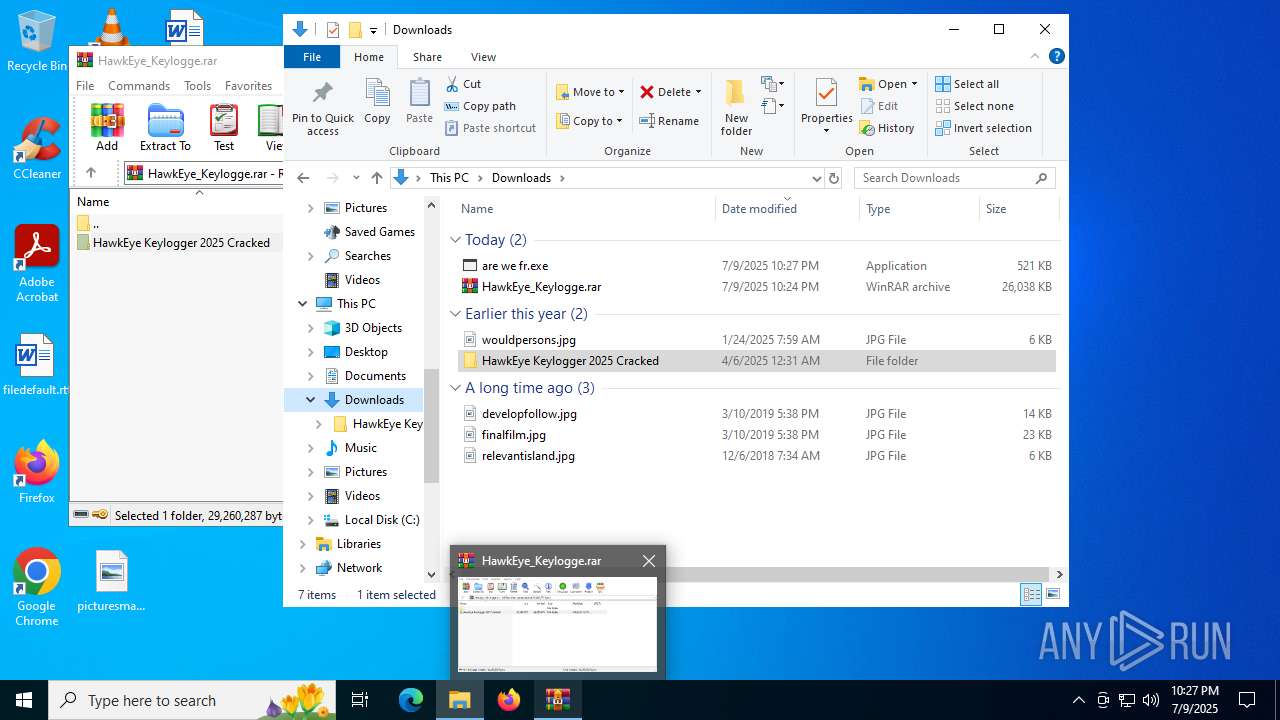
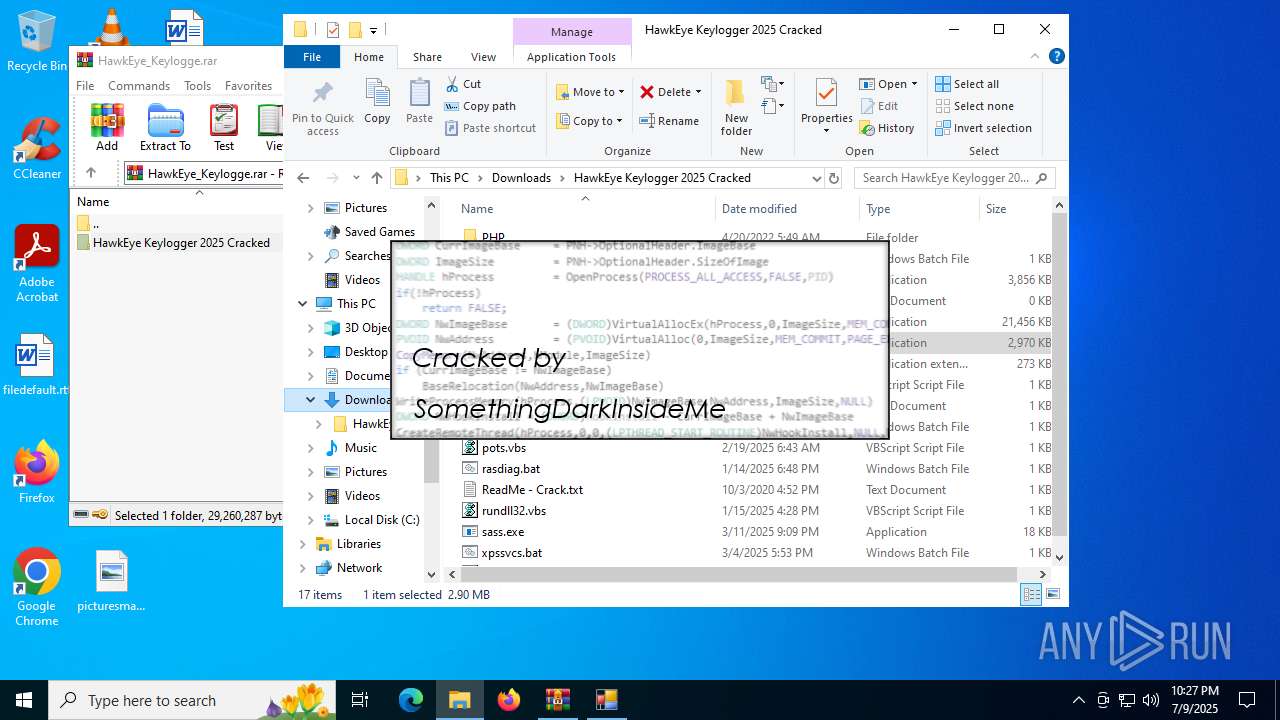
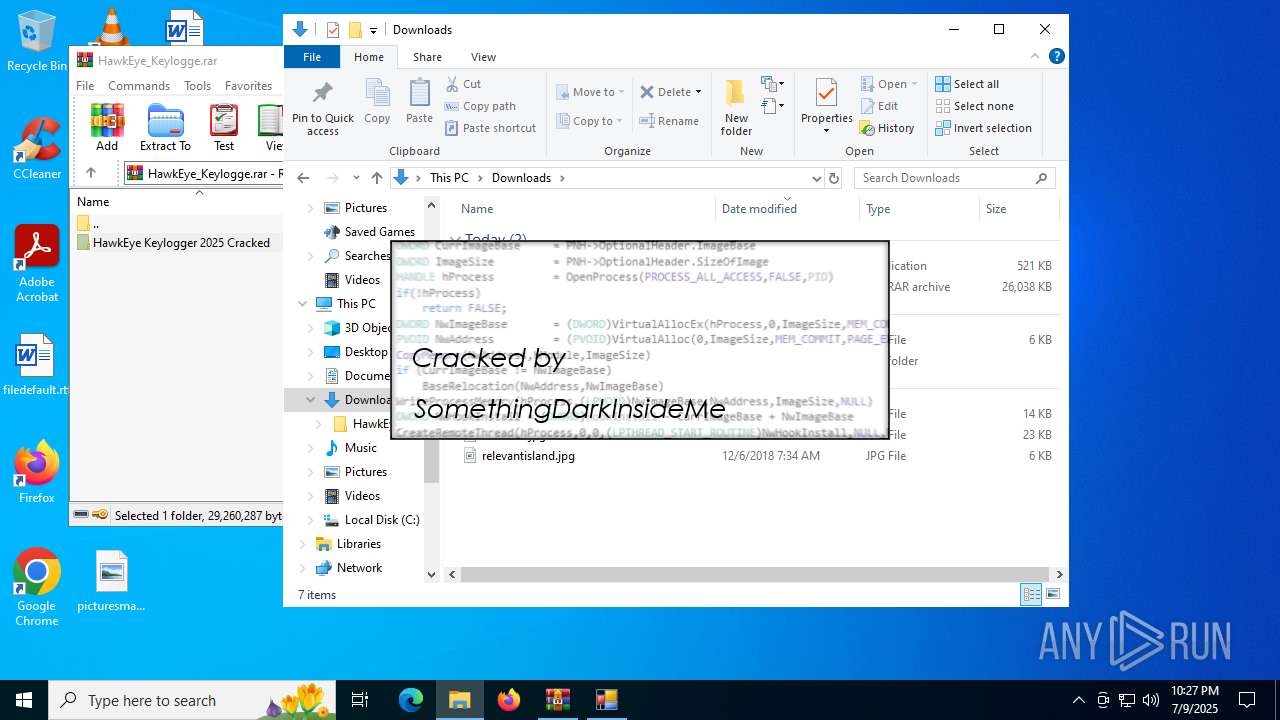
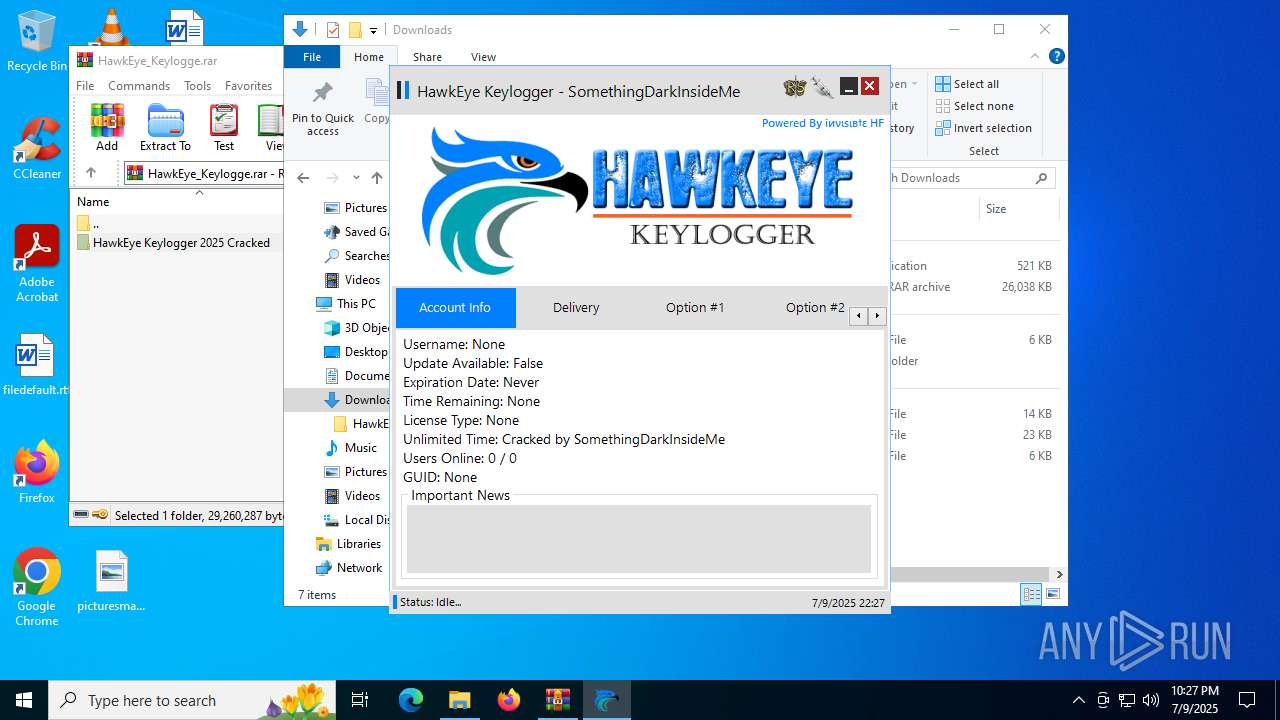
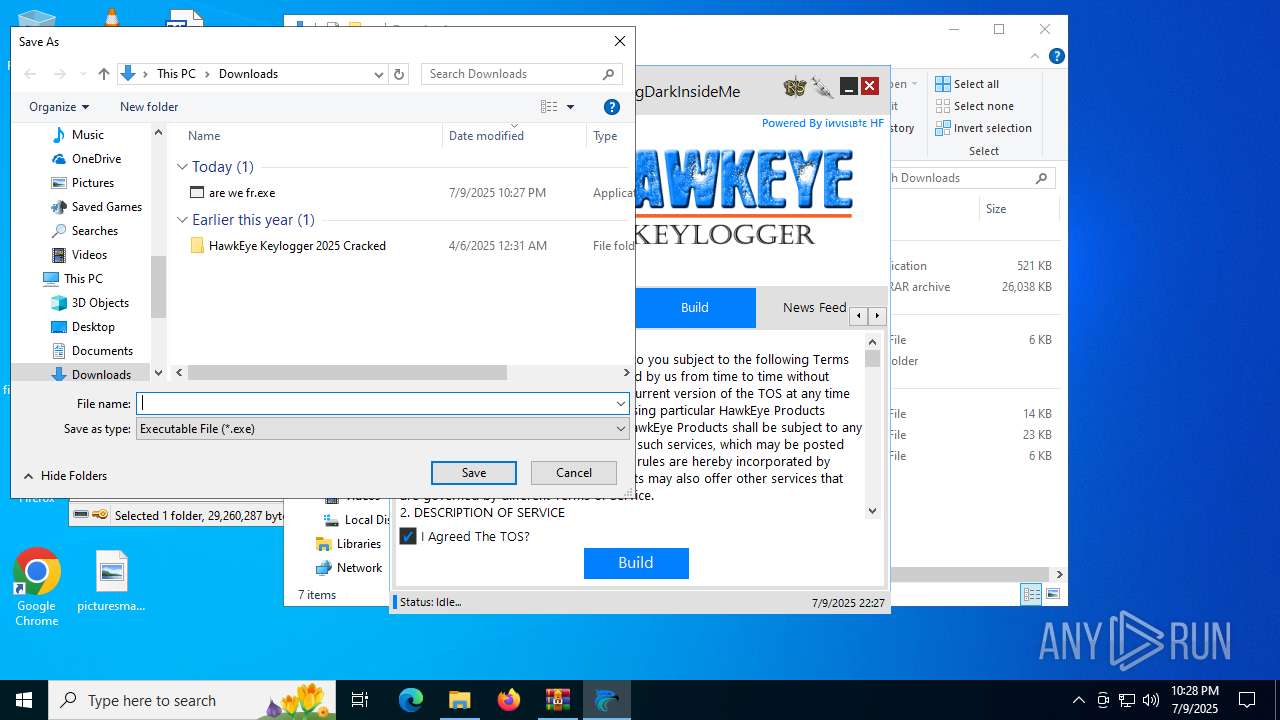
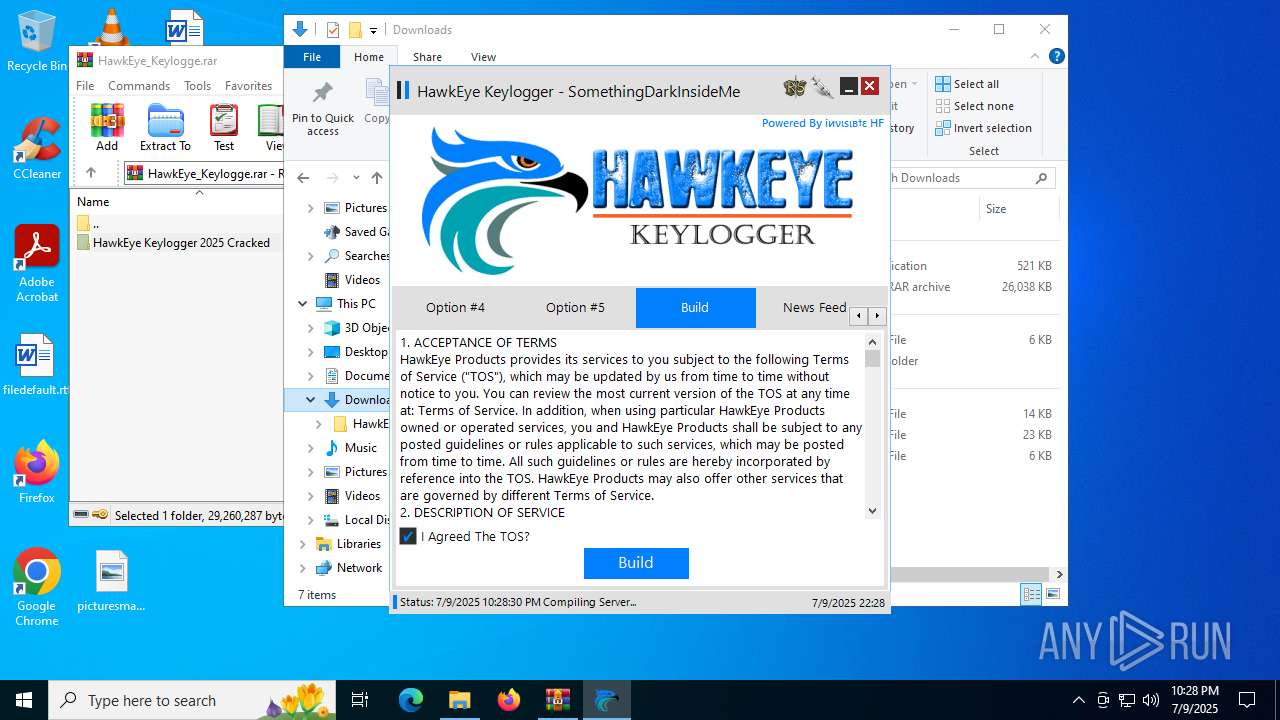
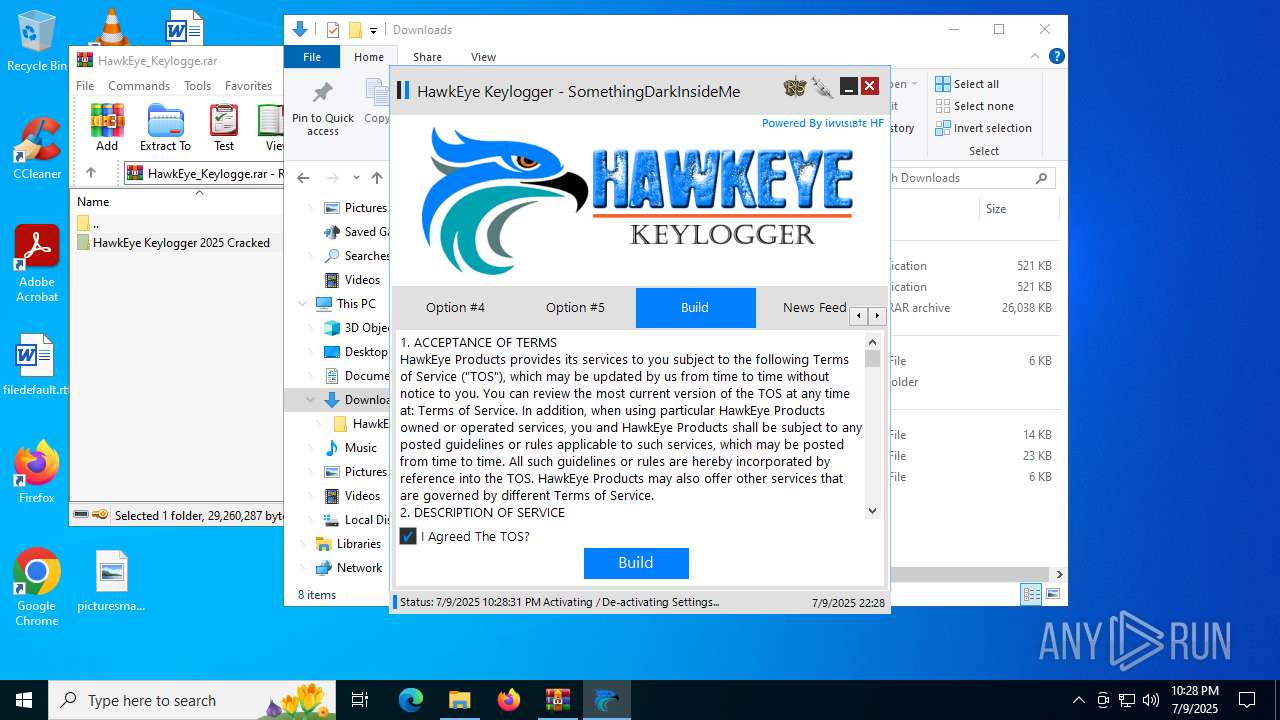
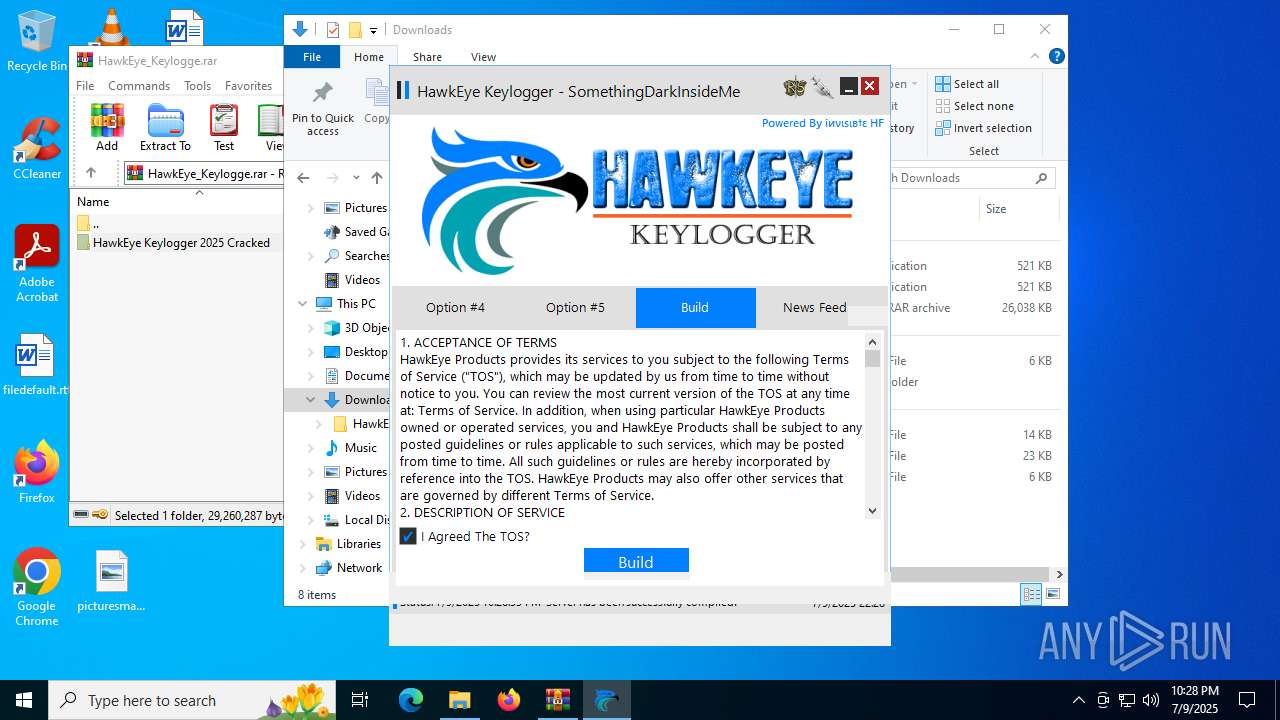
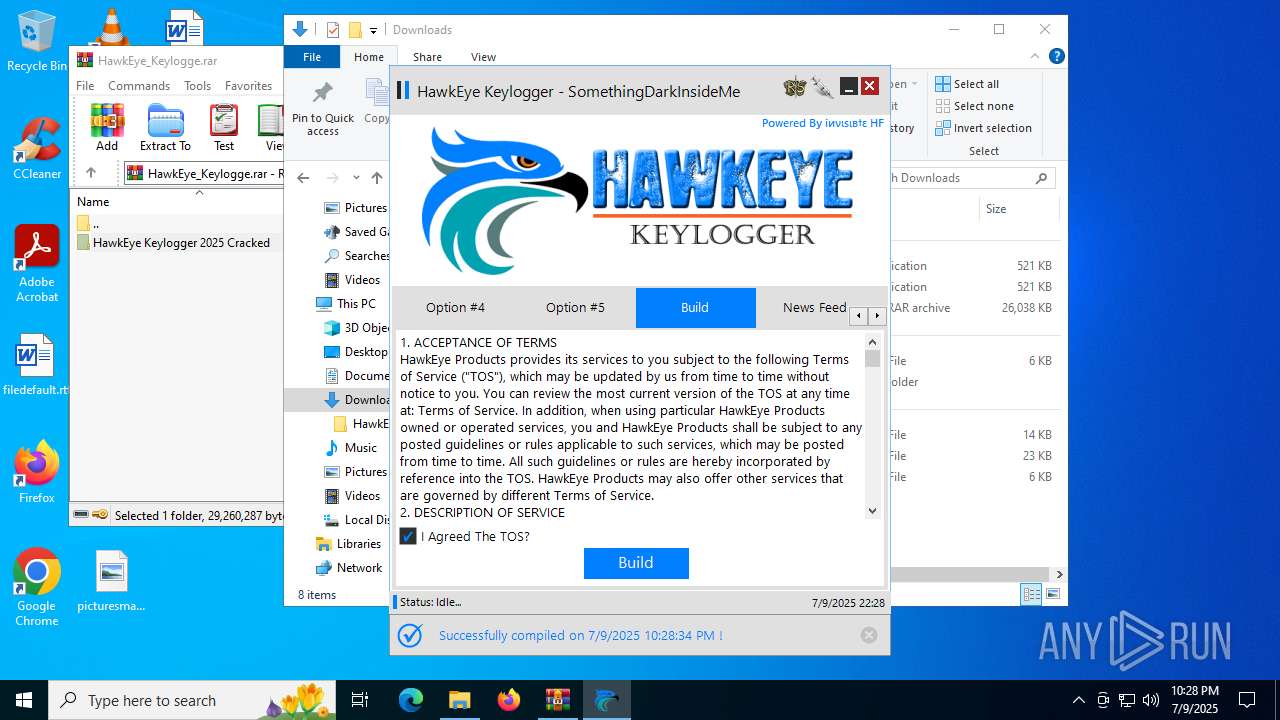
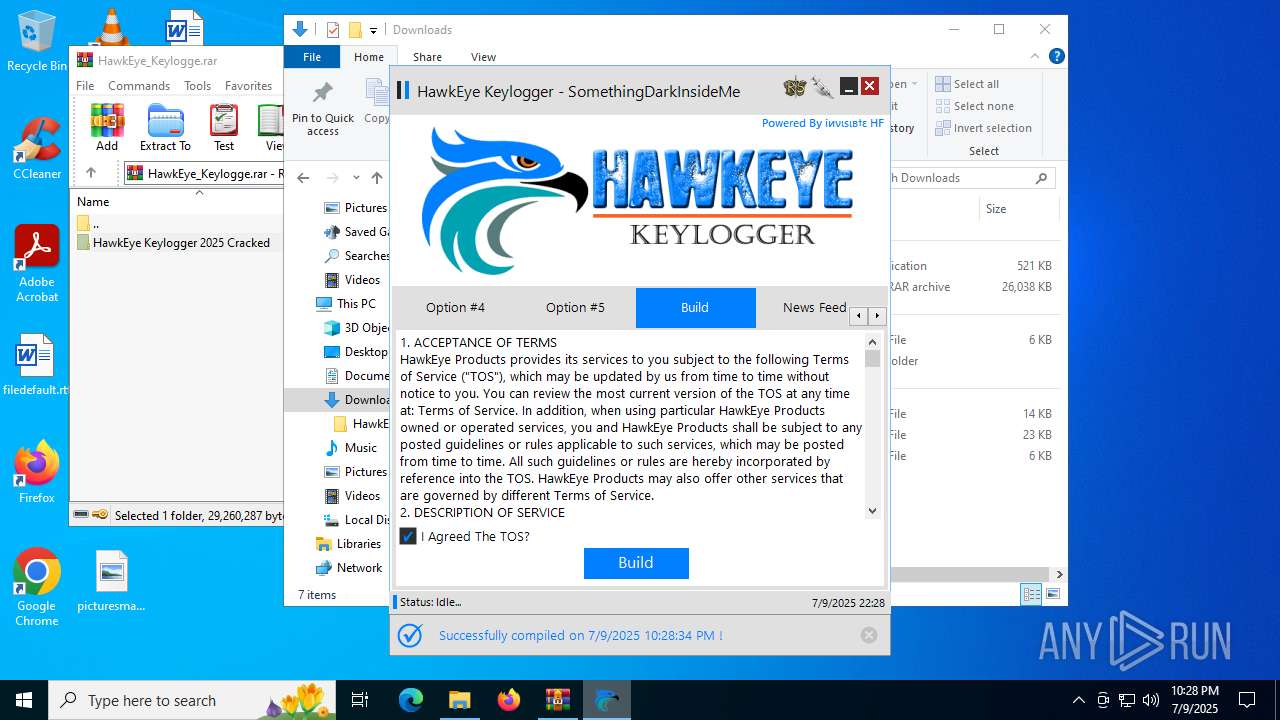
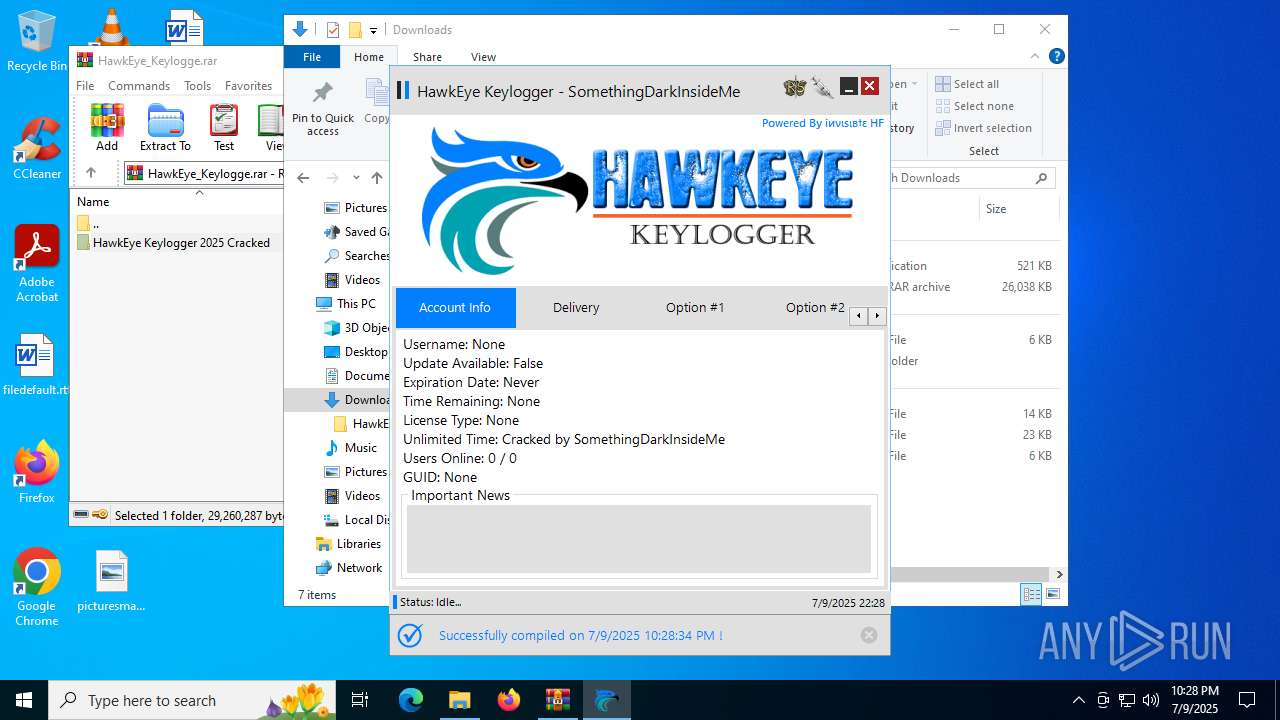
| Verdict: | Malicious activity |
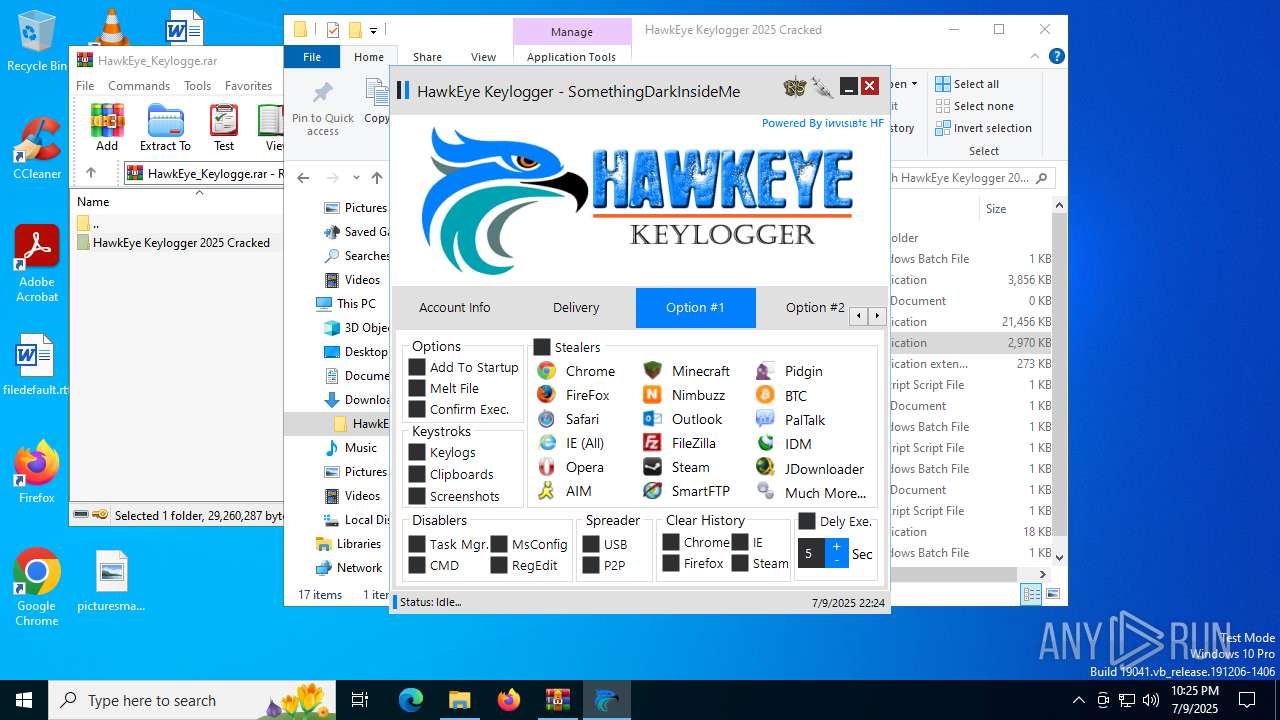
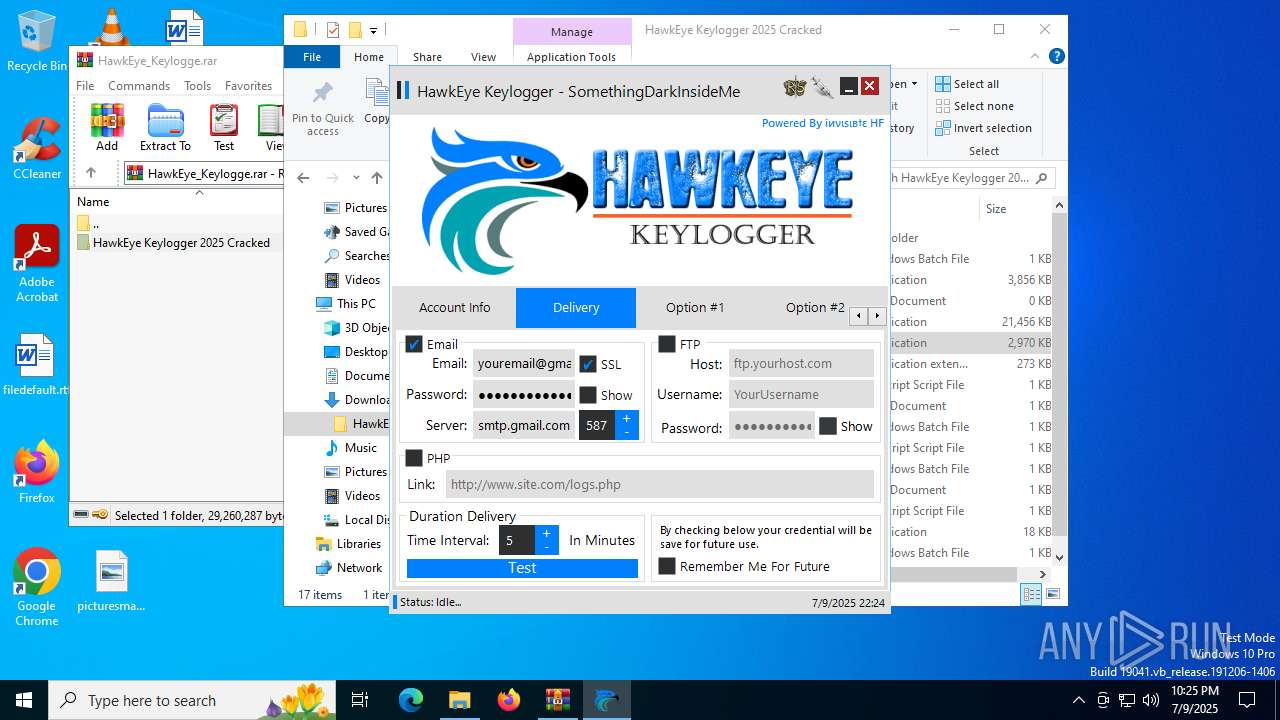
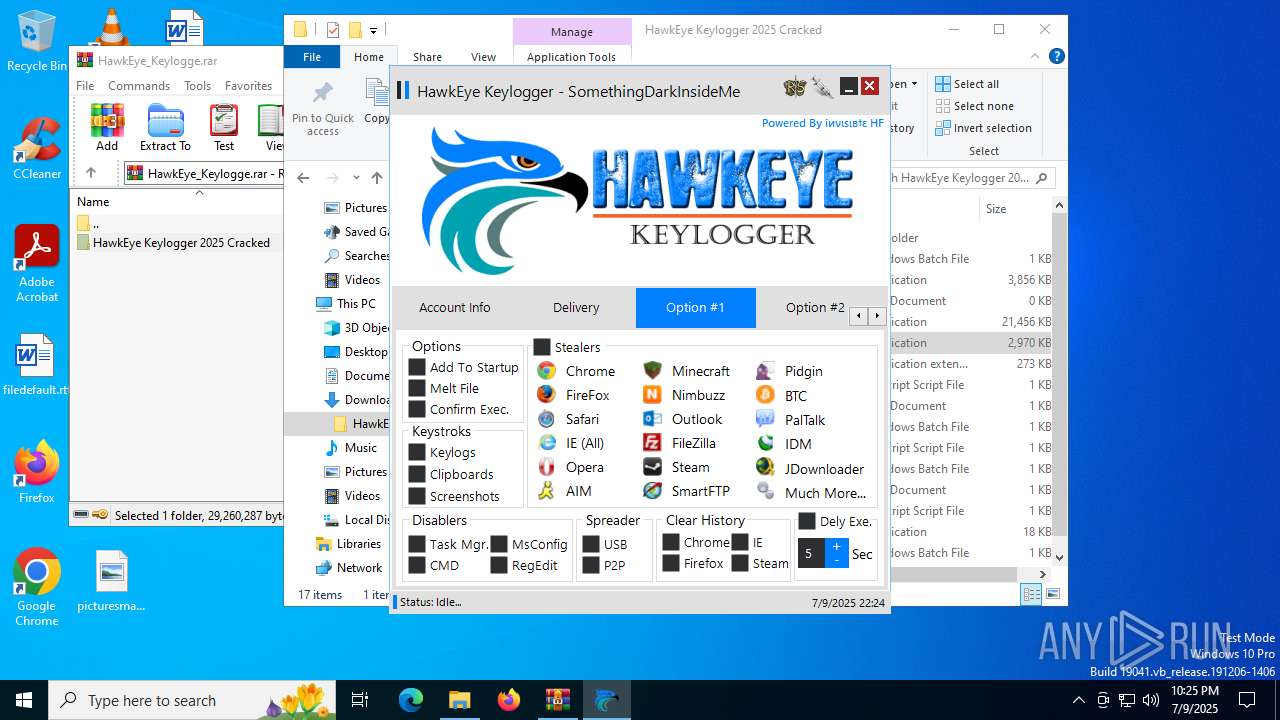
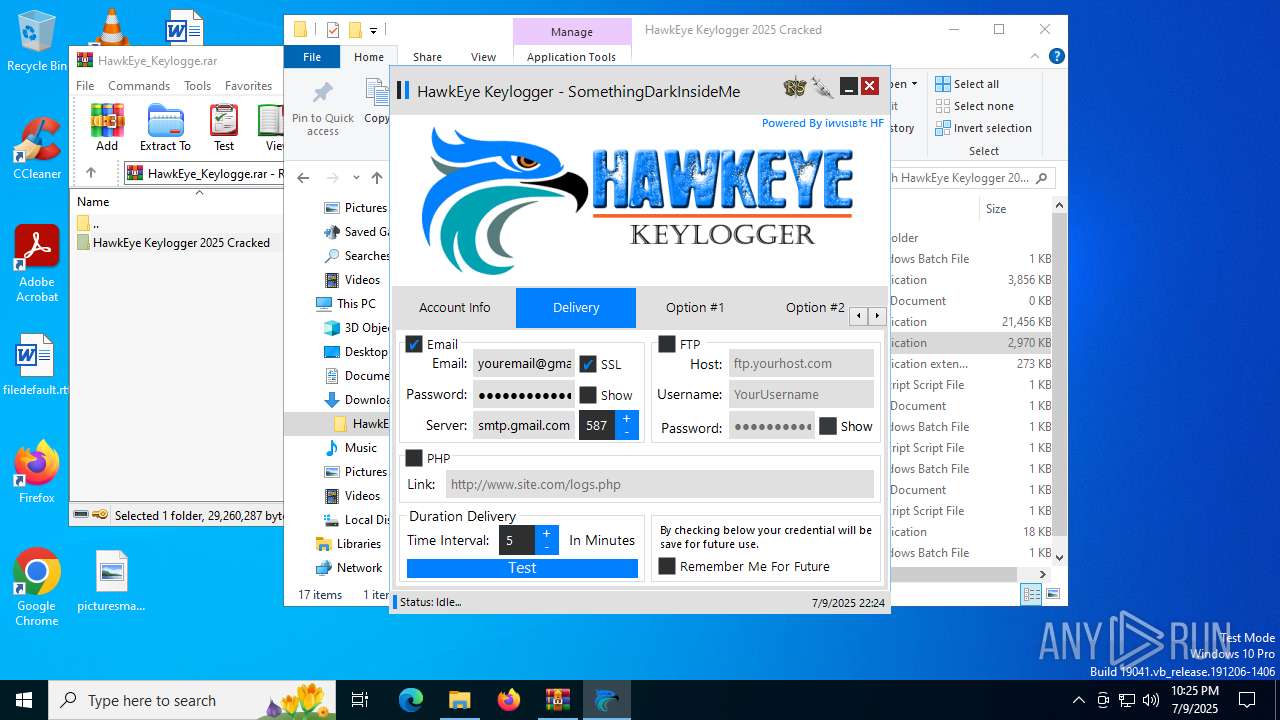
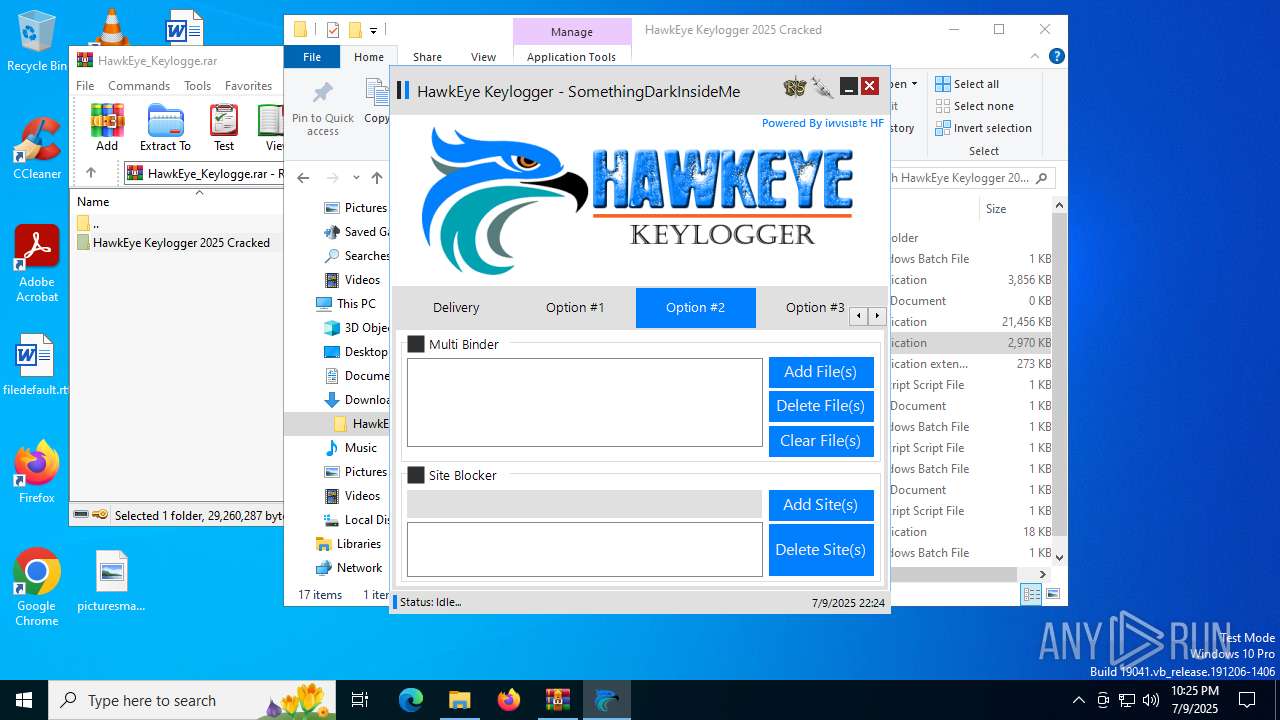
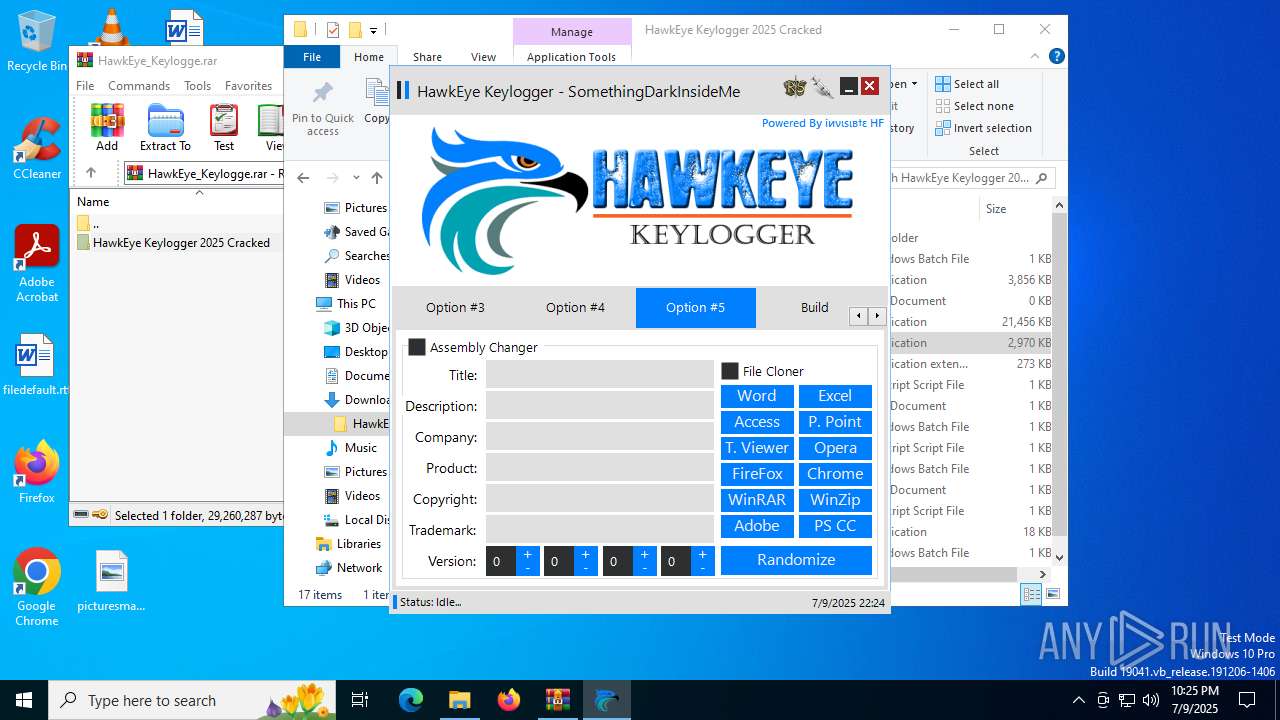
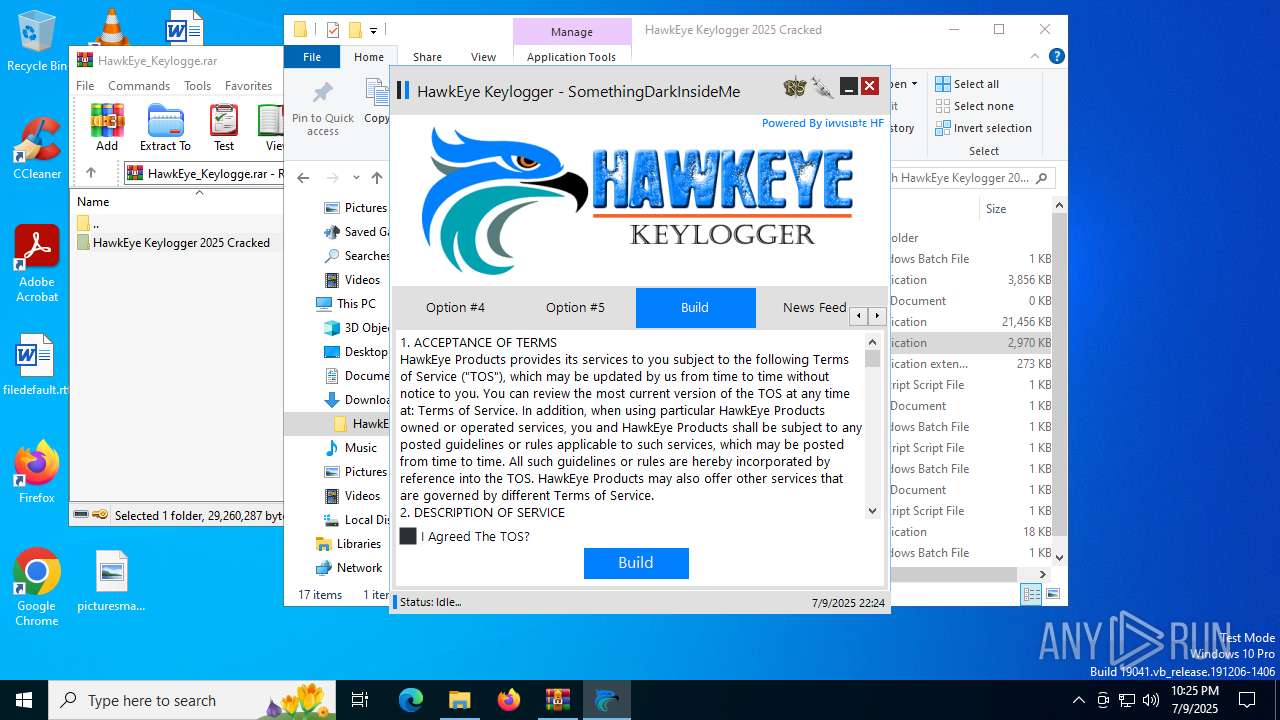
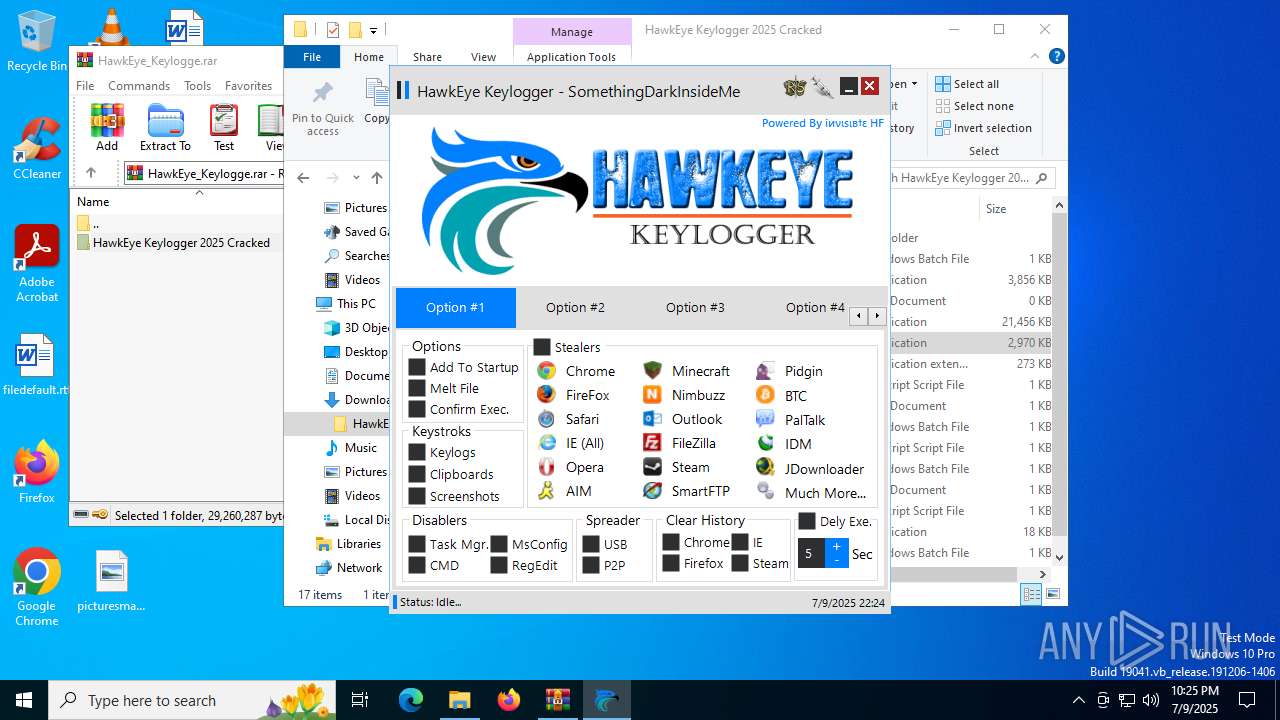
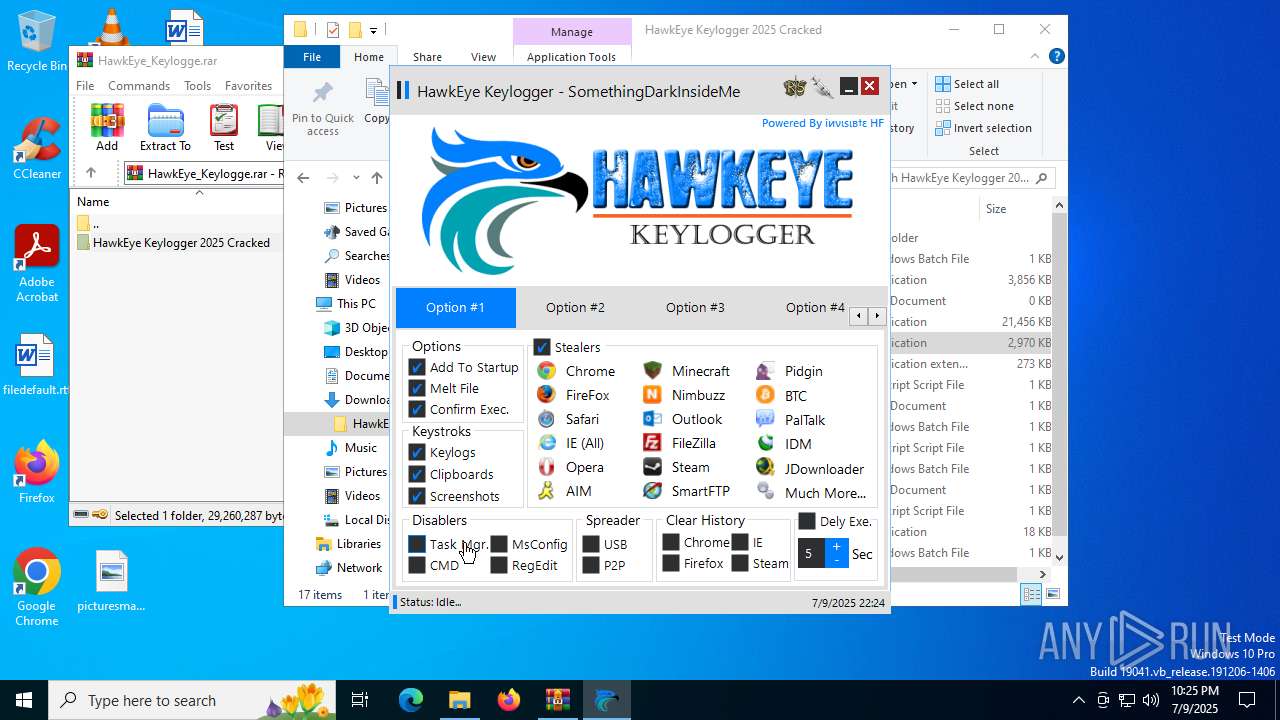
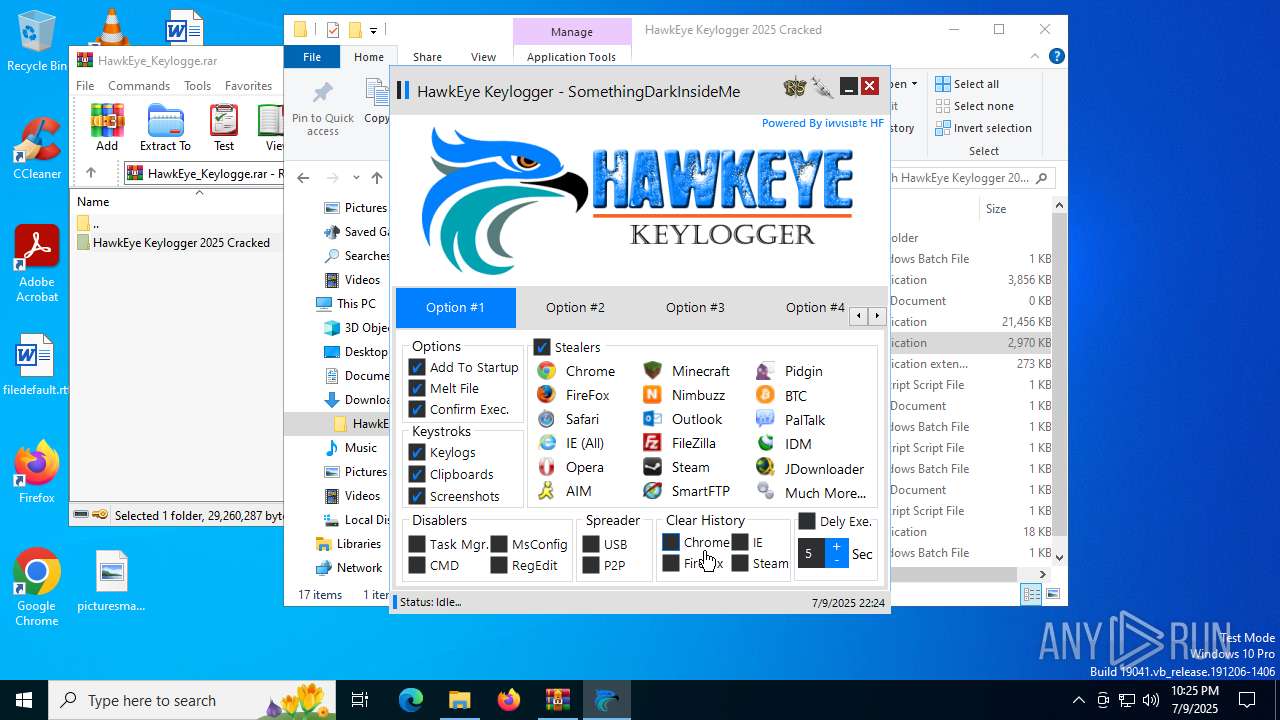
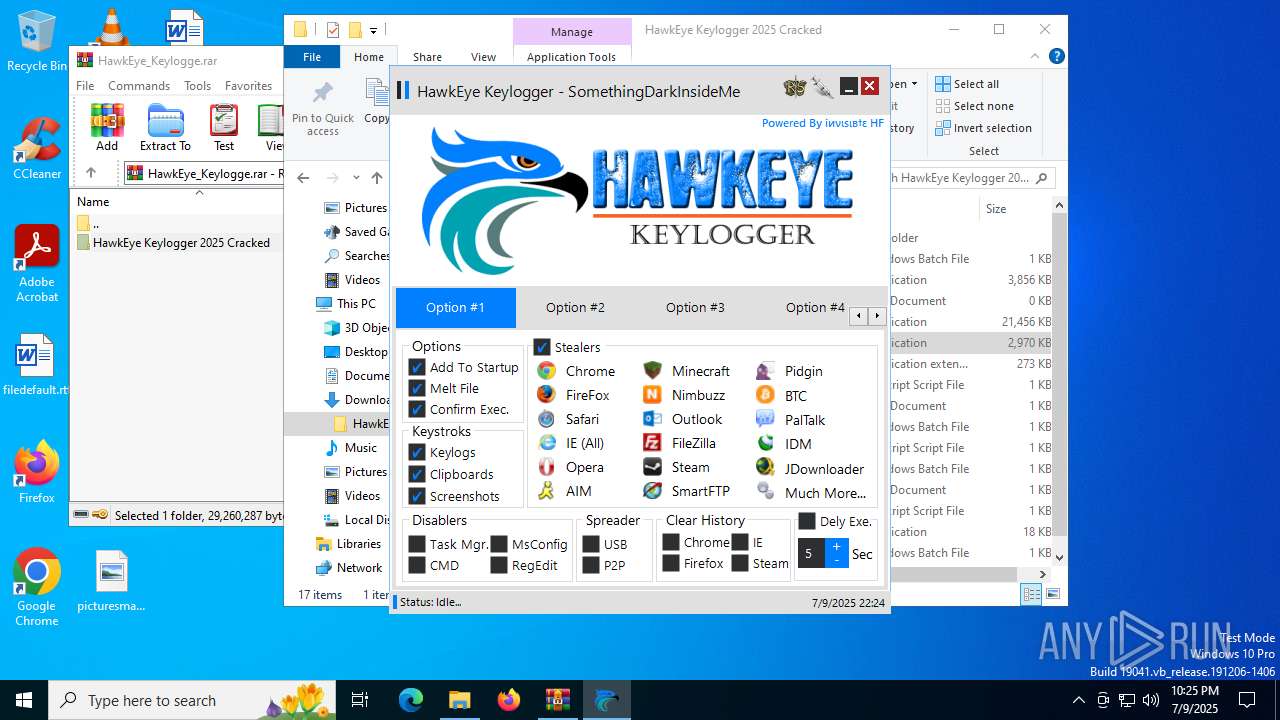
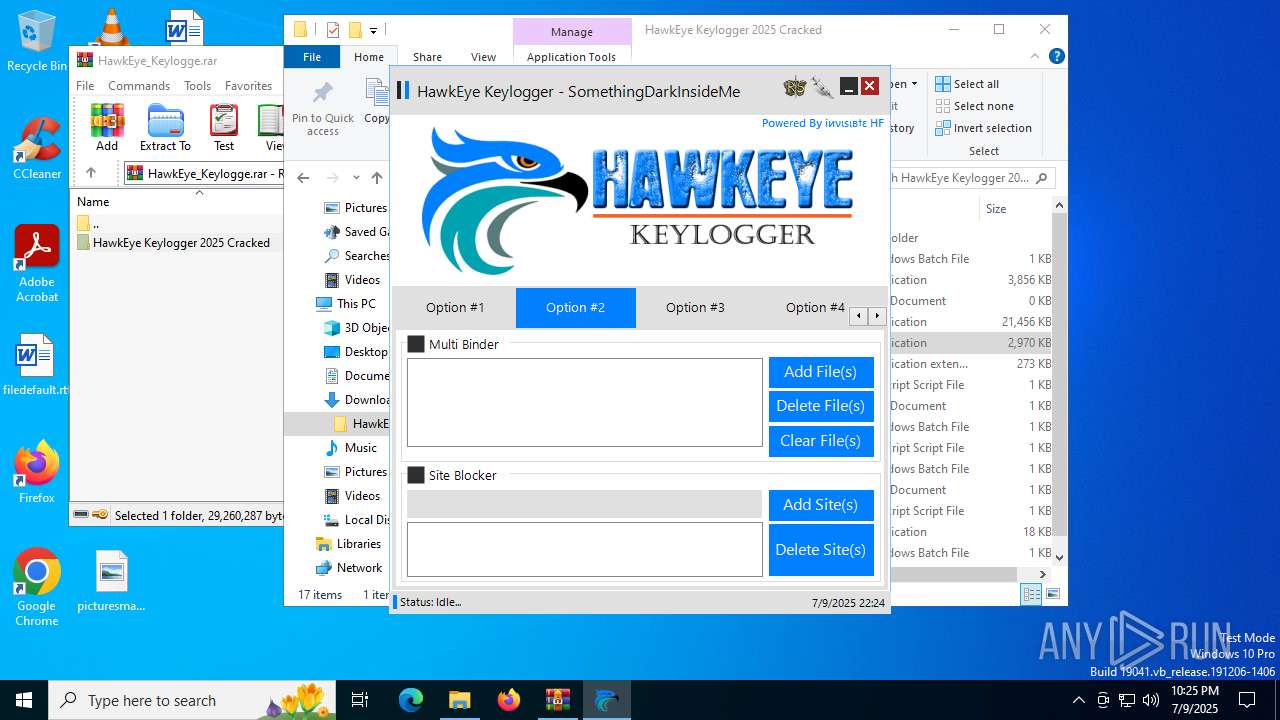
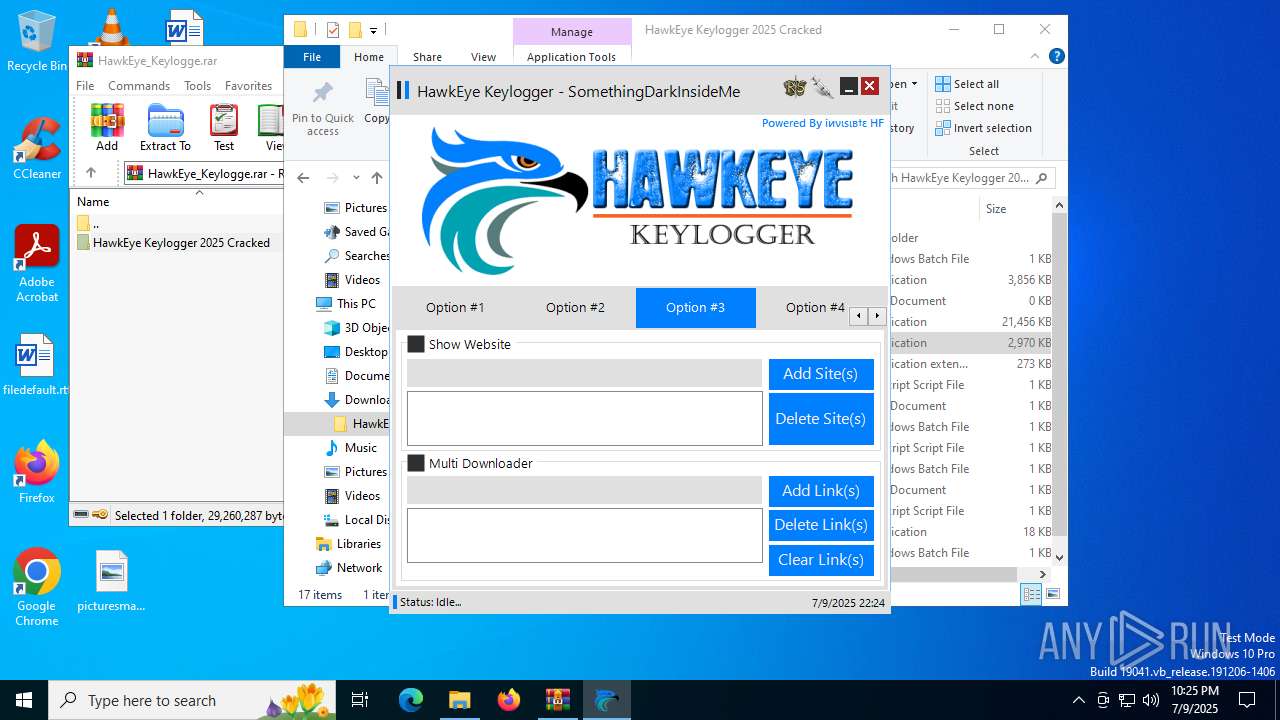
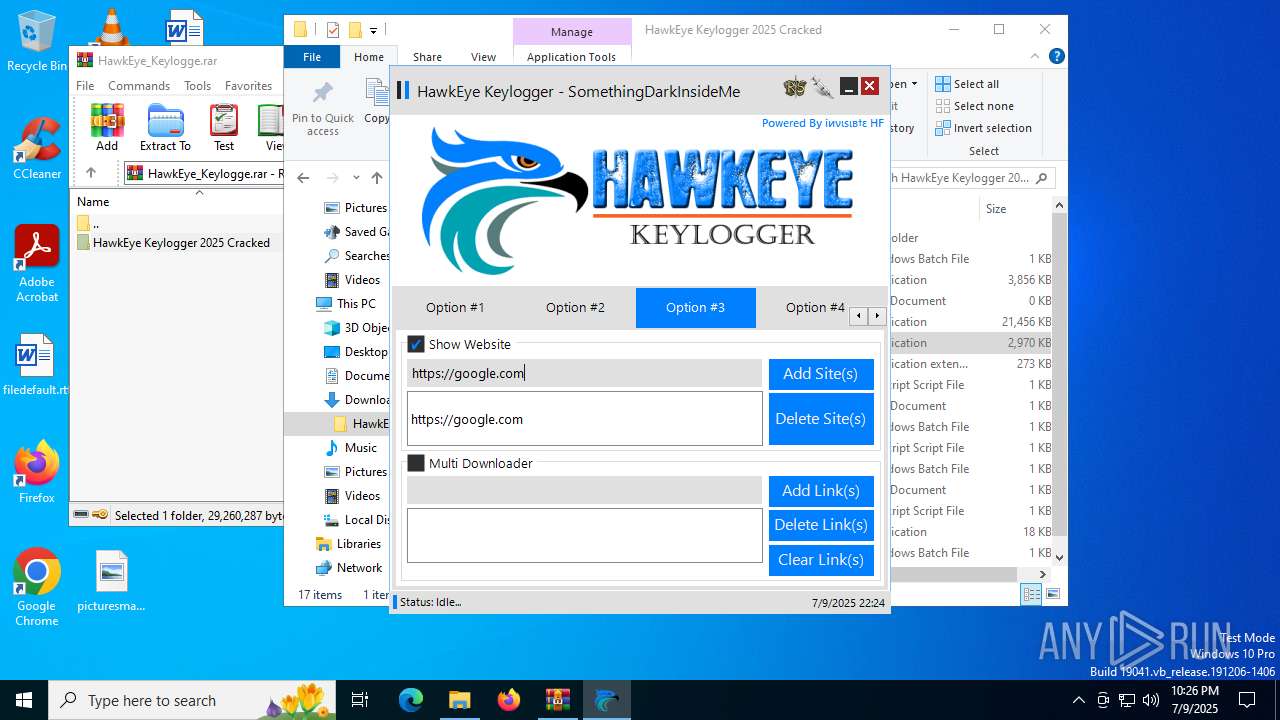
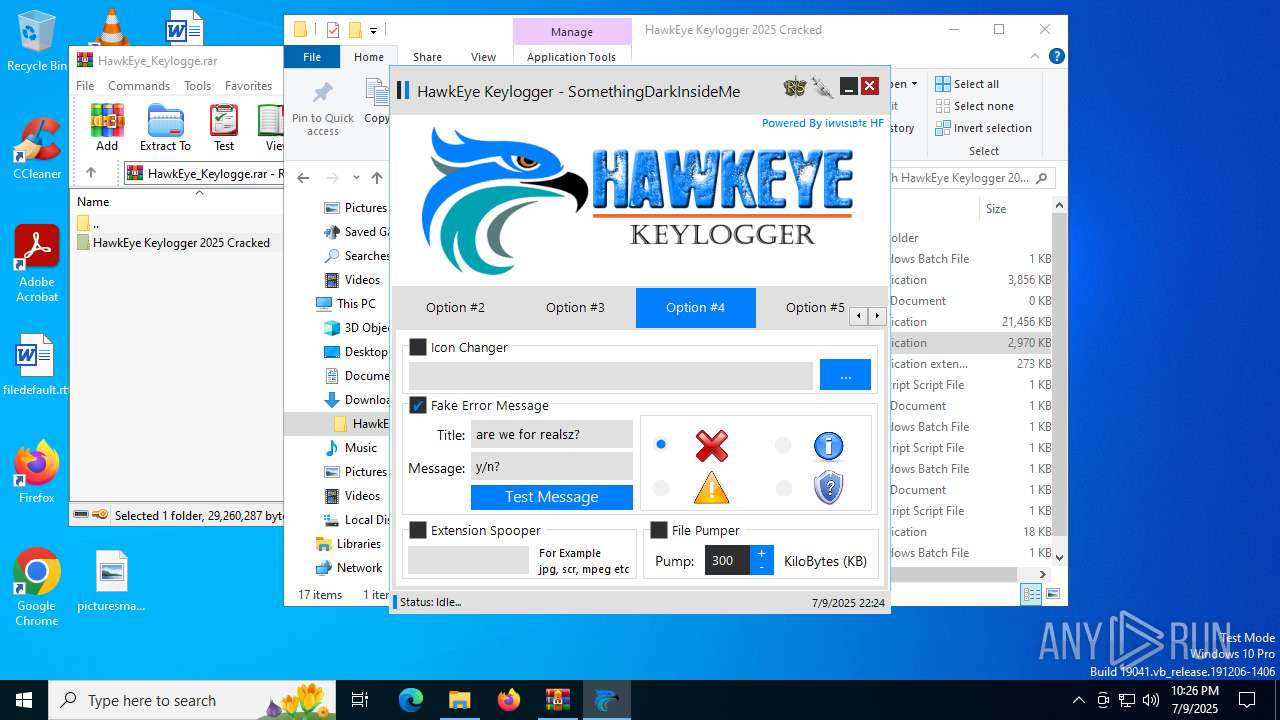
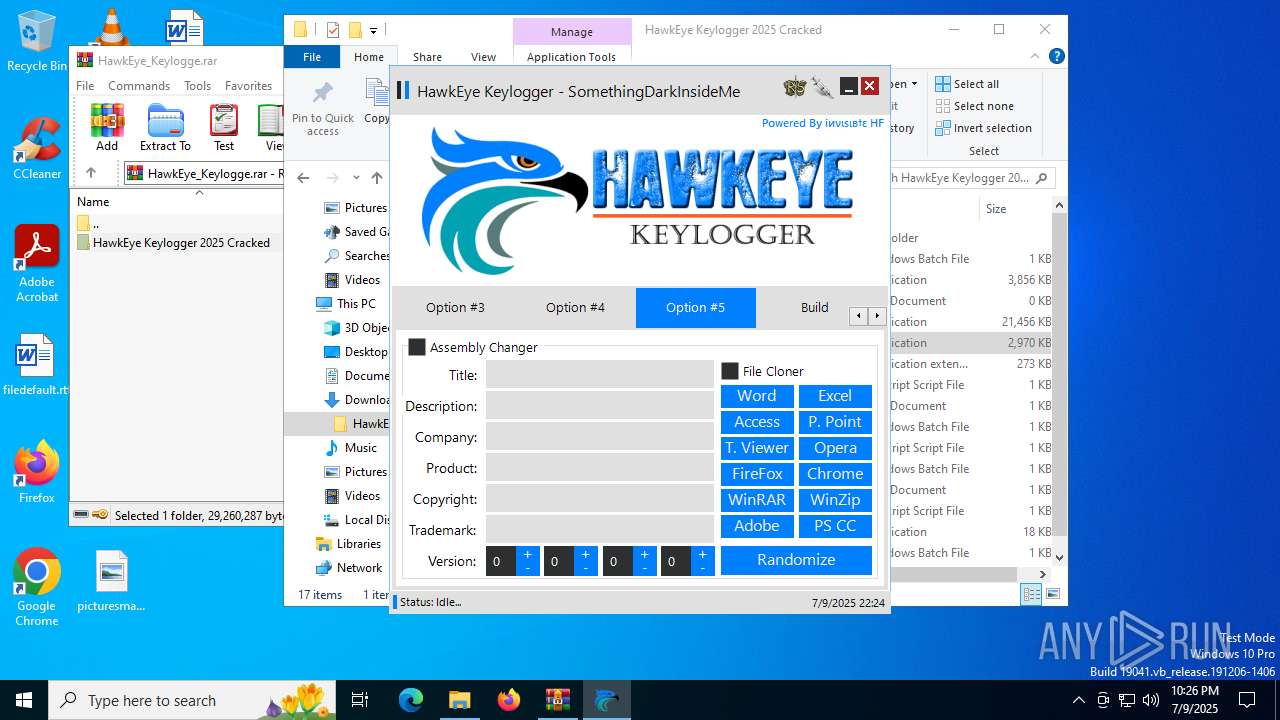
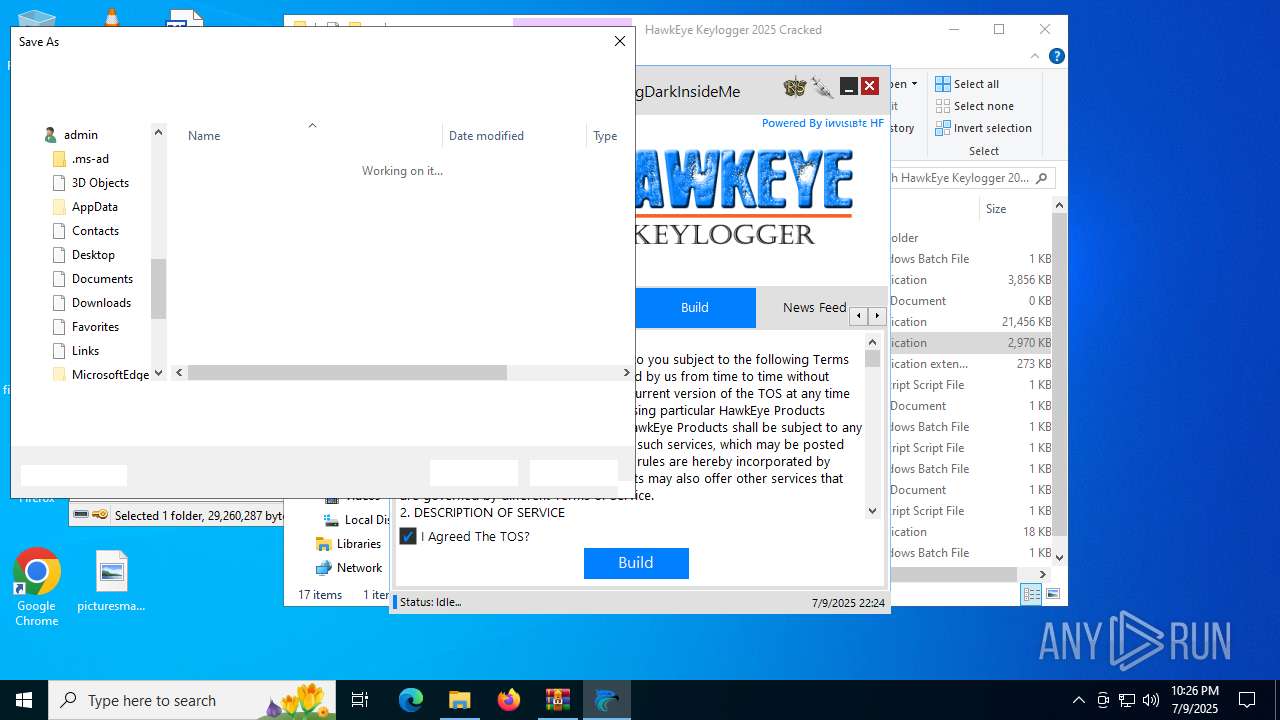
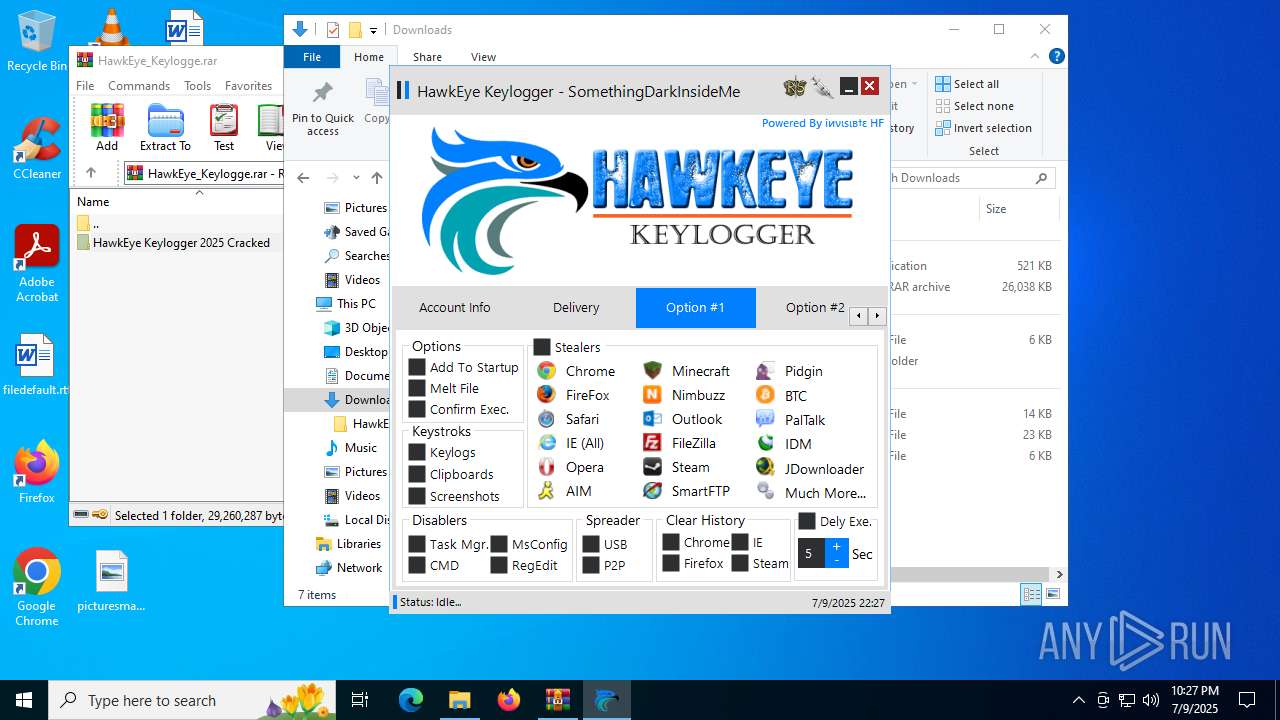
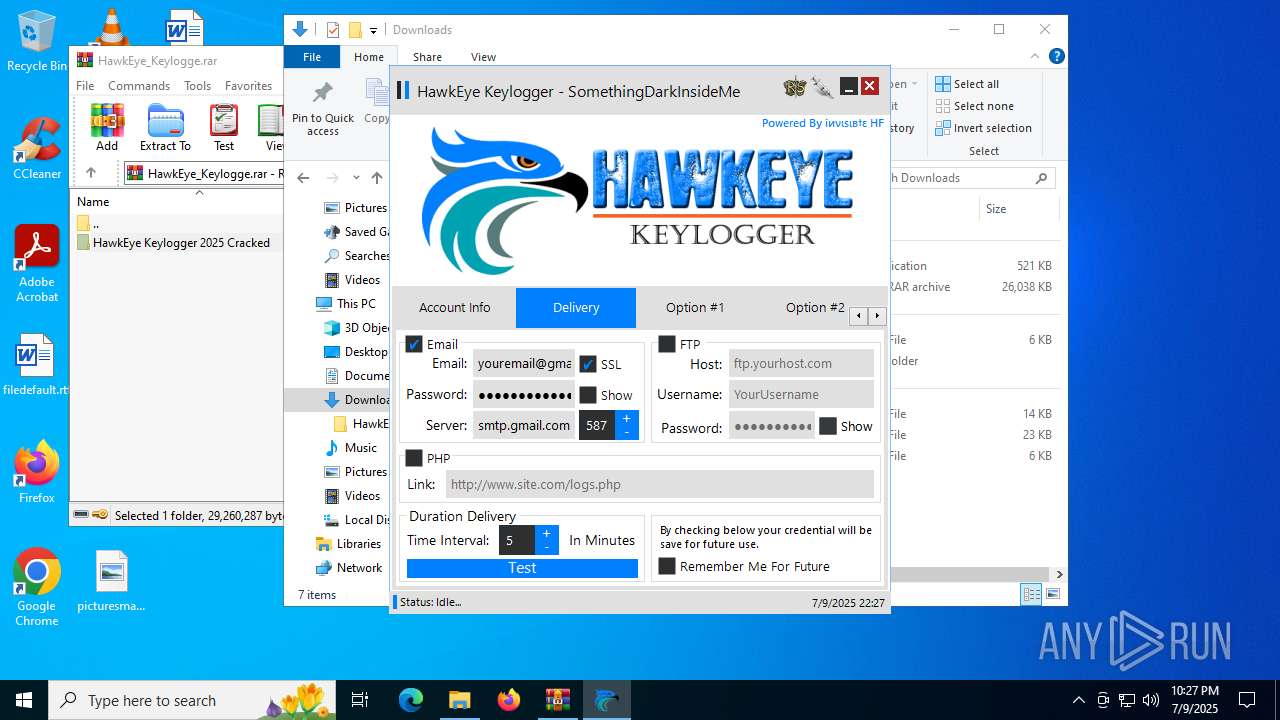
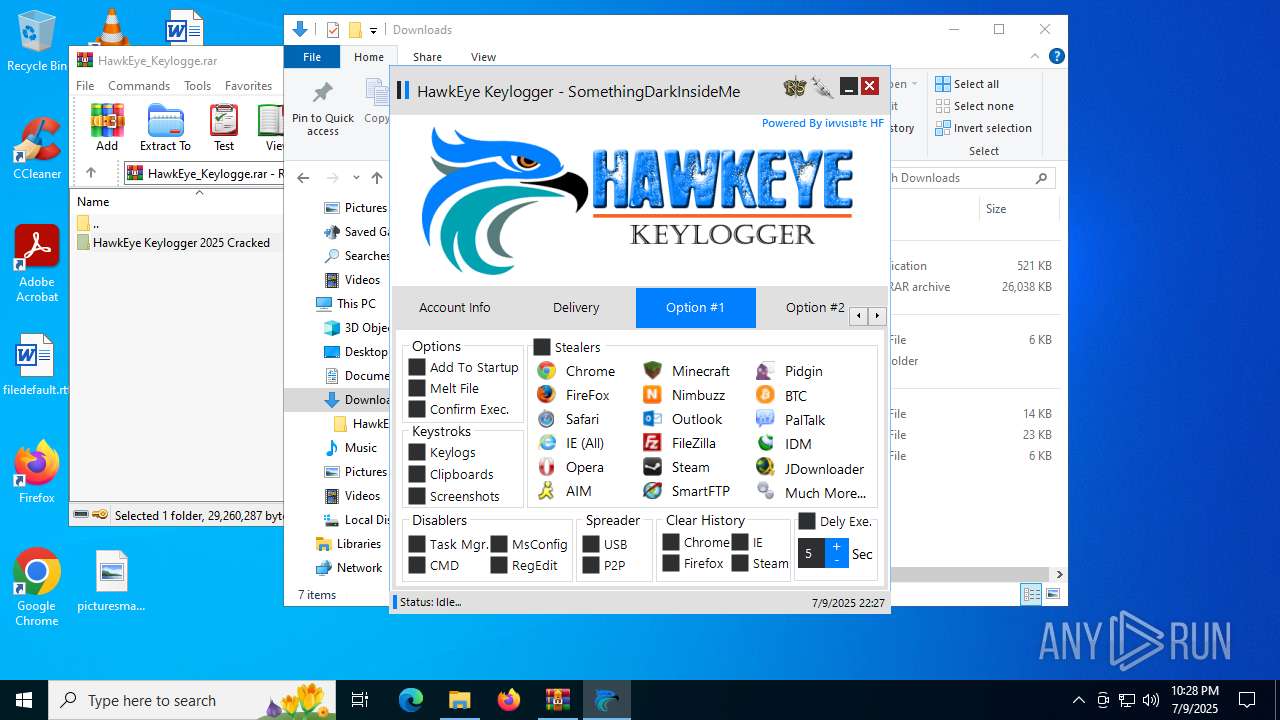
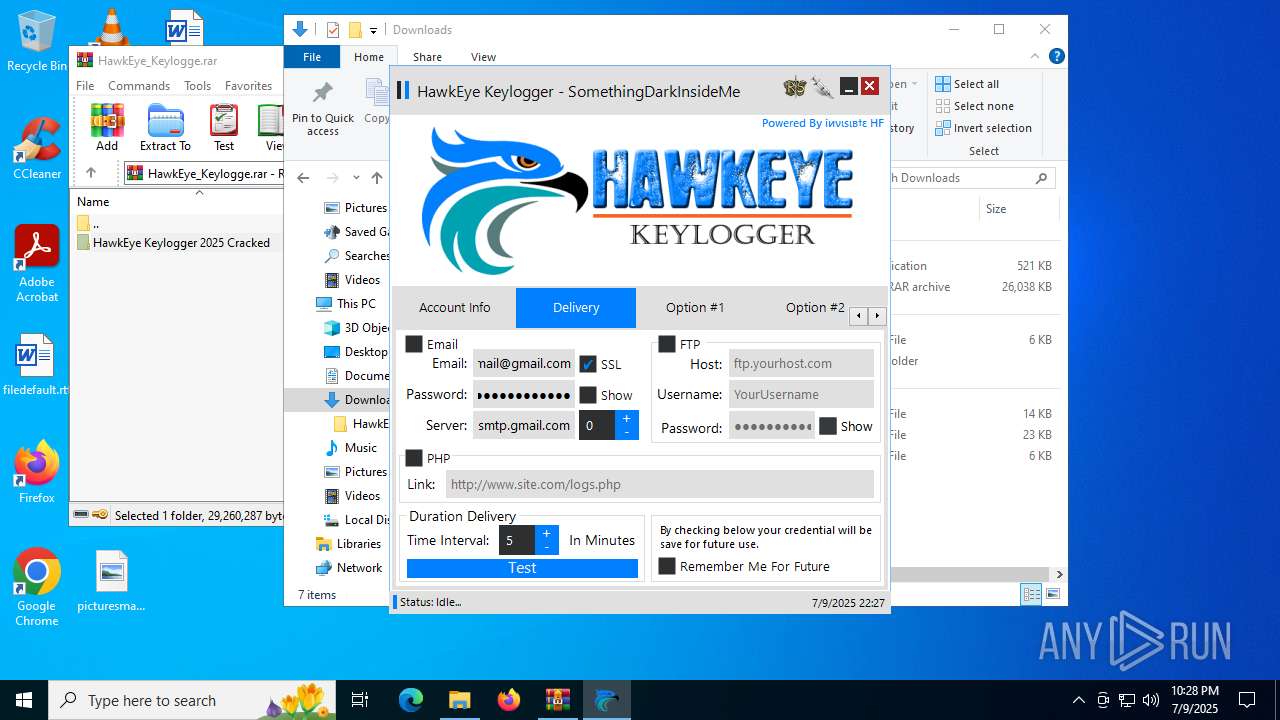
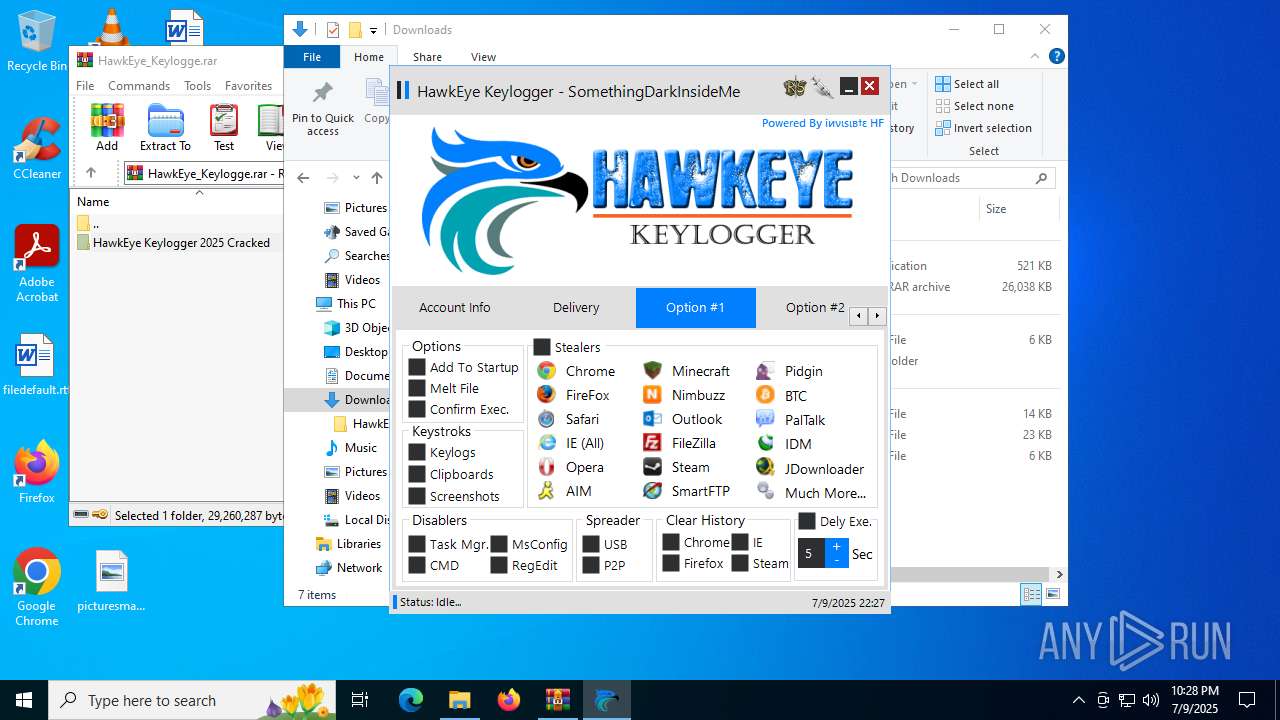
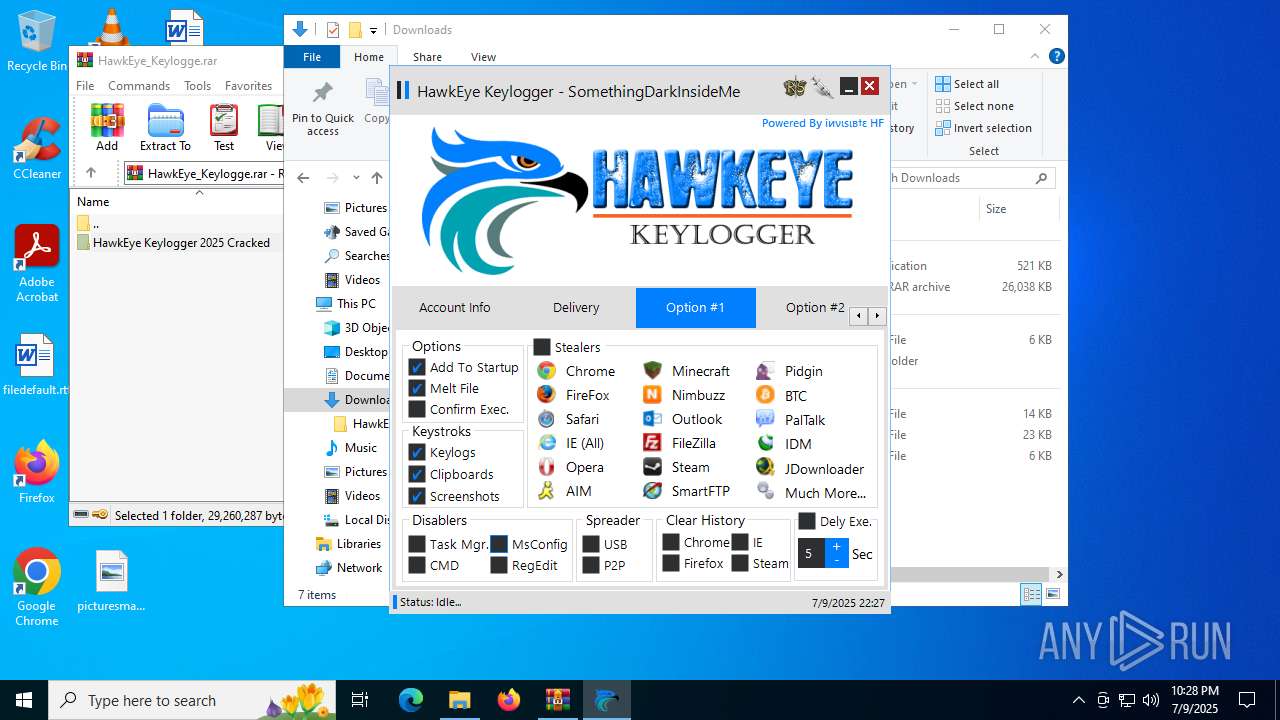
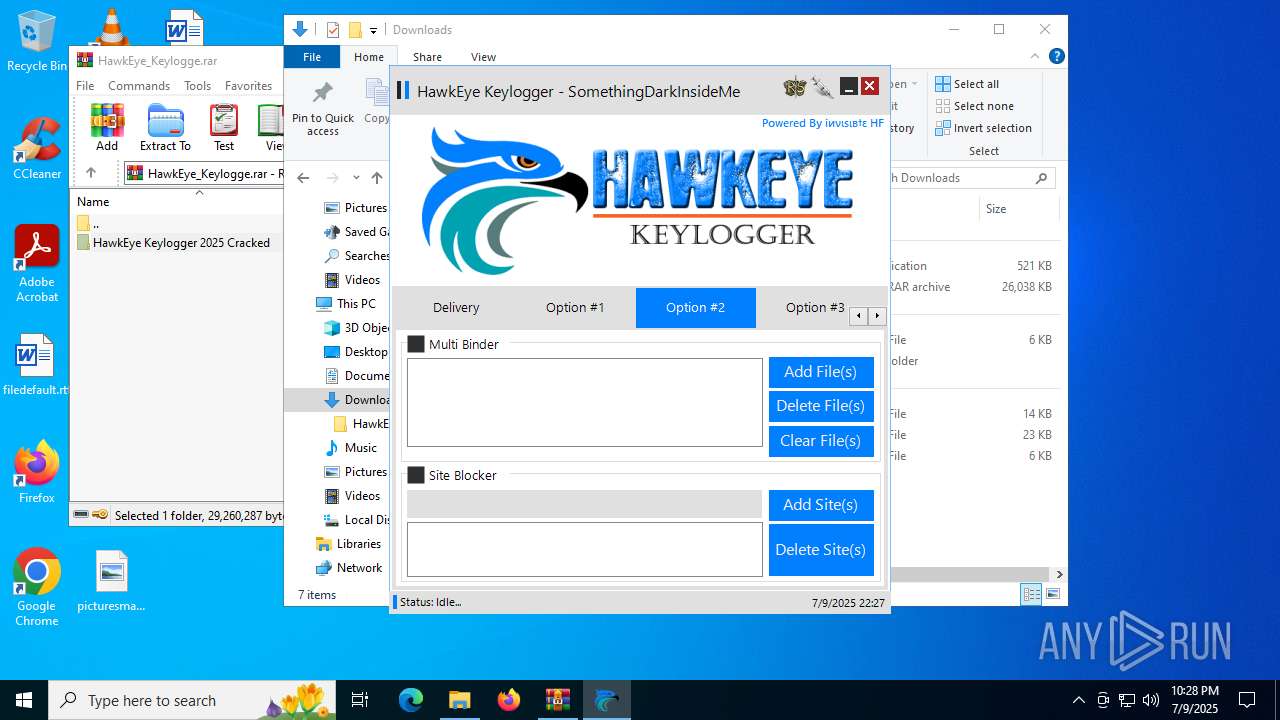
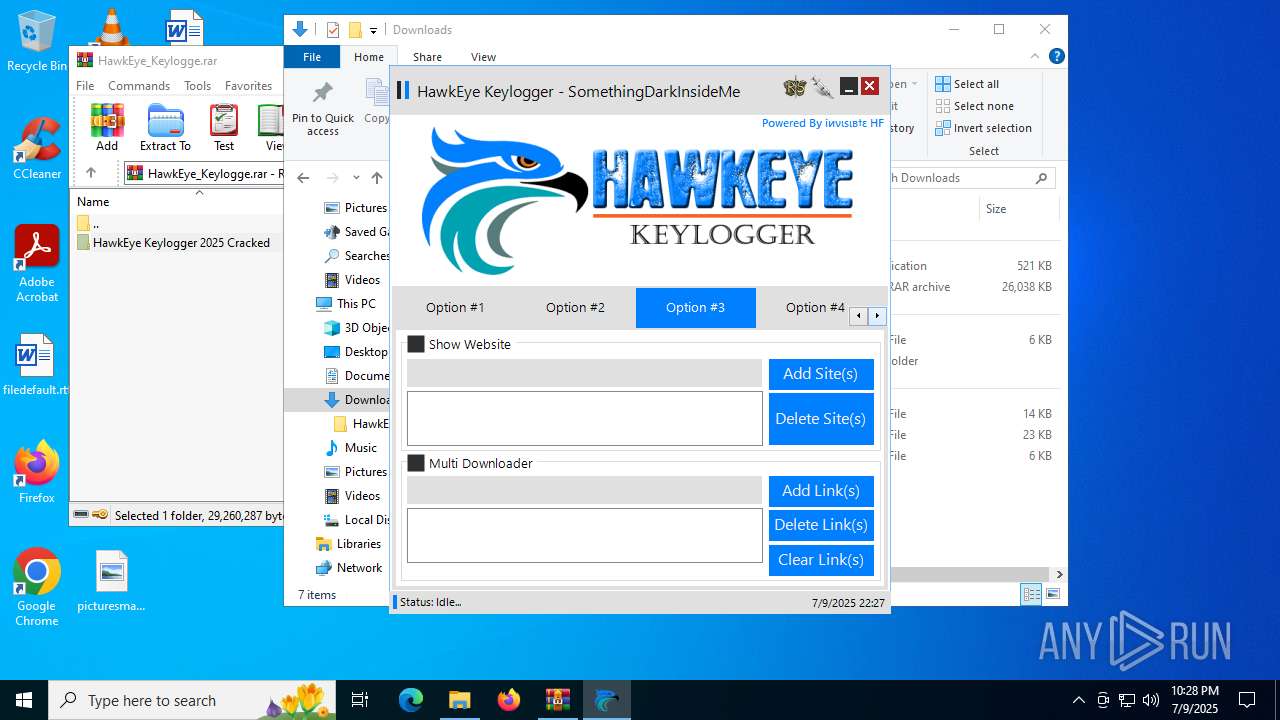
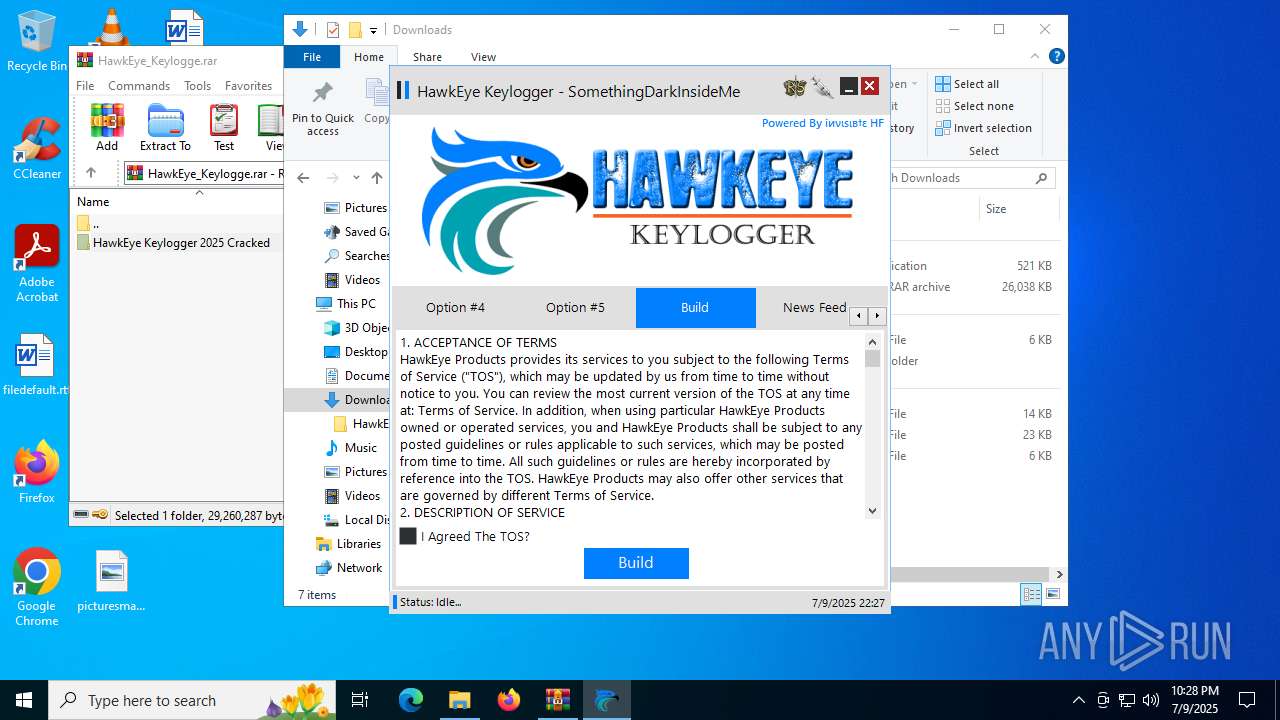
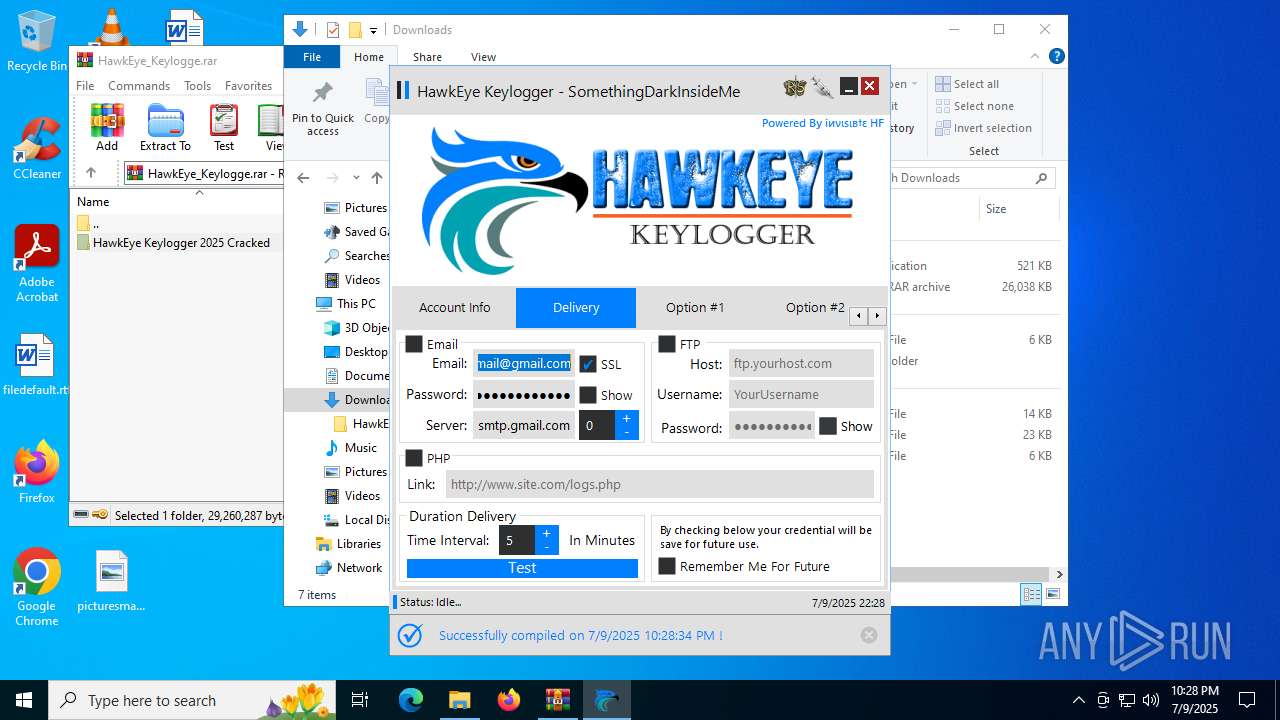
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | July 09, 2025, 22:23:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 725F013F2F14BE206C48501B821BD4DD |
| SHA1: | 7A5F52475EC58D2FFFD00750EEBFF9AF94D7B5D1 |
| SHA256: | E1B64C537BFF38F7E92F1EB04D416044FC7432312C6F038621110609FD553A50 |
| SSDEEP: | 3:N8sVnLoHCok8V/whHdhHQHWR0:2sCiopEdQWR0 |
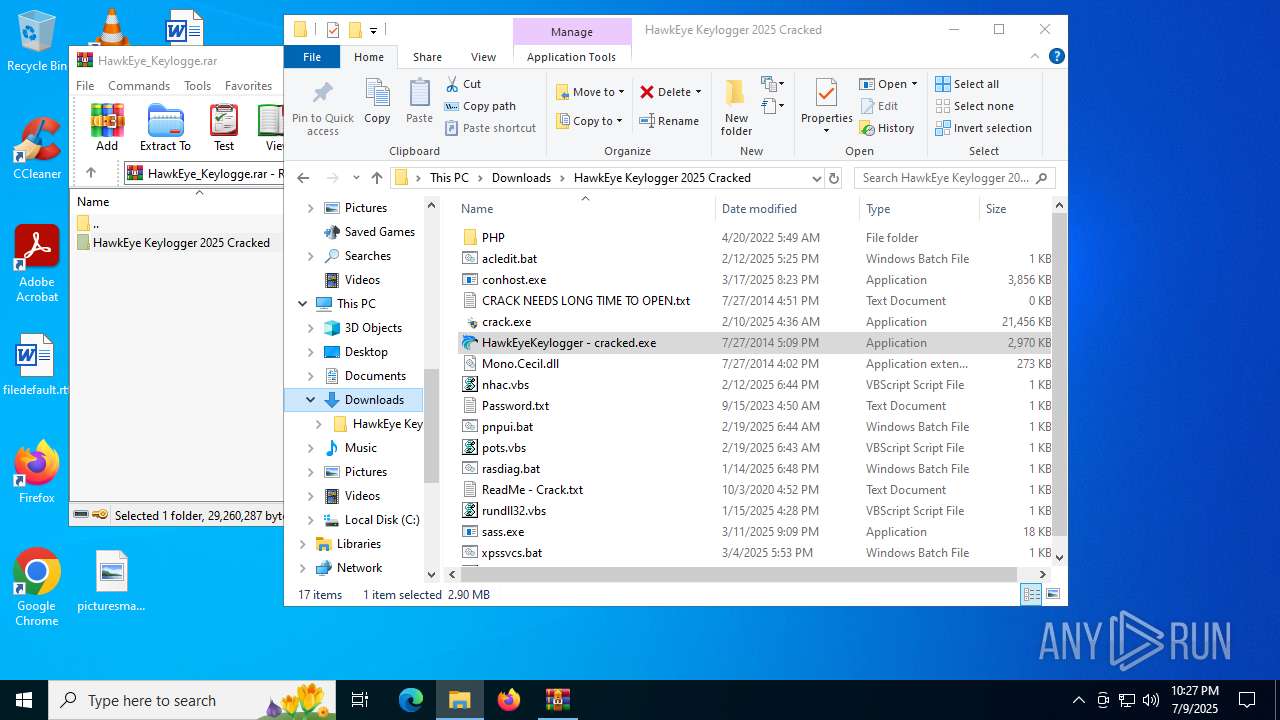
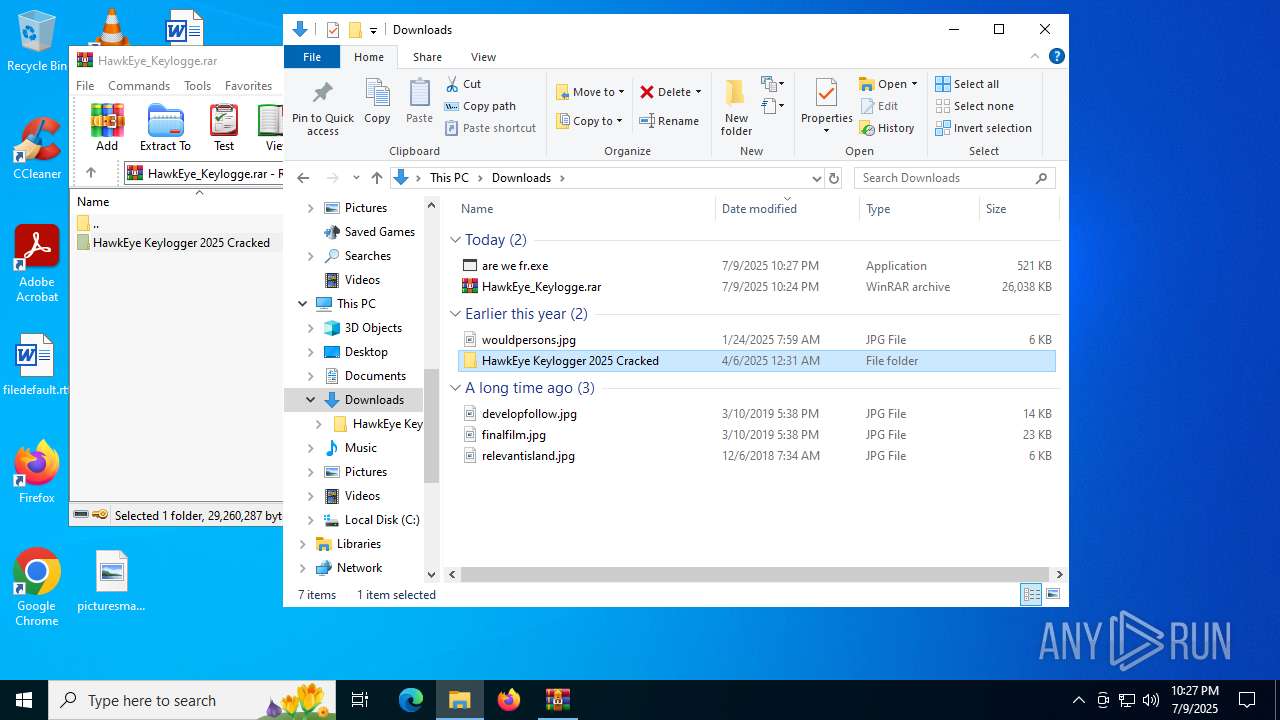
MALICIOUS
MAIL PASSSVIEW has been detected
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
HAWKEYE has been detected (YARA)
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
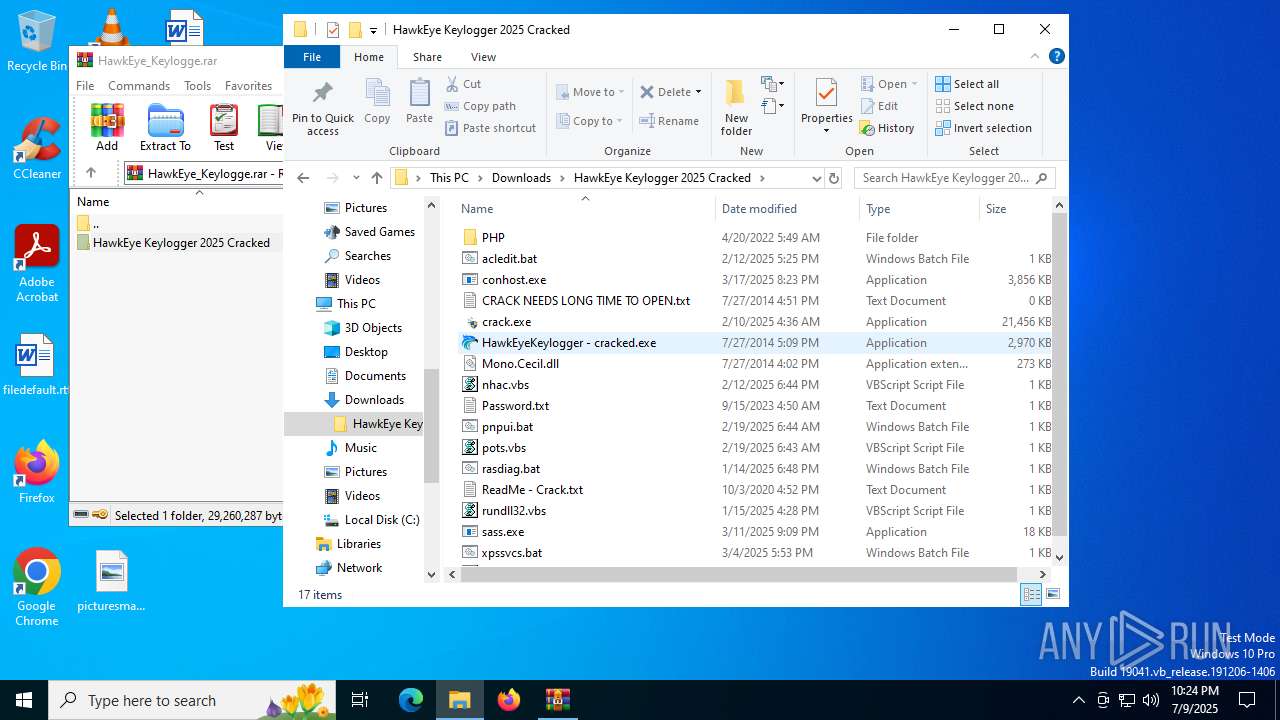
Changes the autorun value in the registry
- Windows Update.exe (PID: 7708)
Actions looks like stealing of personal data
- vbc.exe (PID: 7064)
SUSPICIOUS
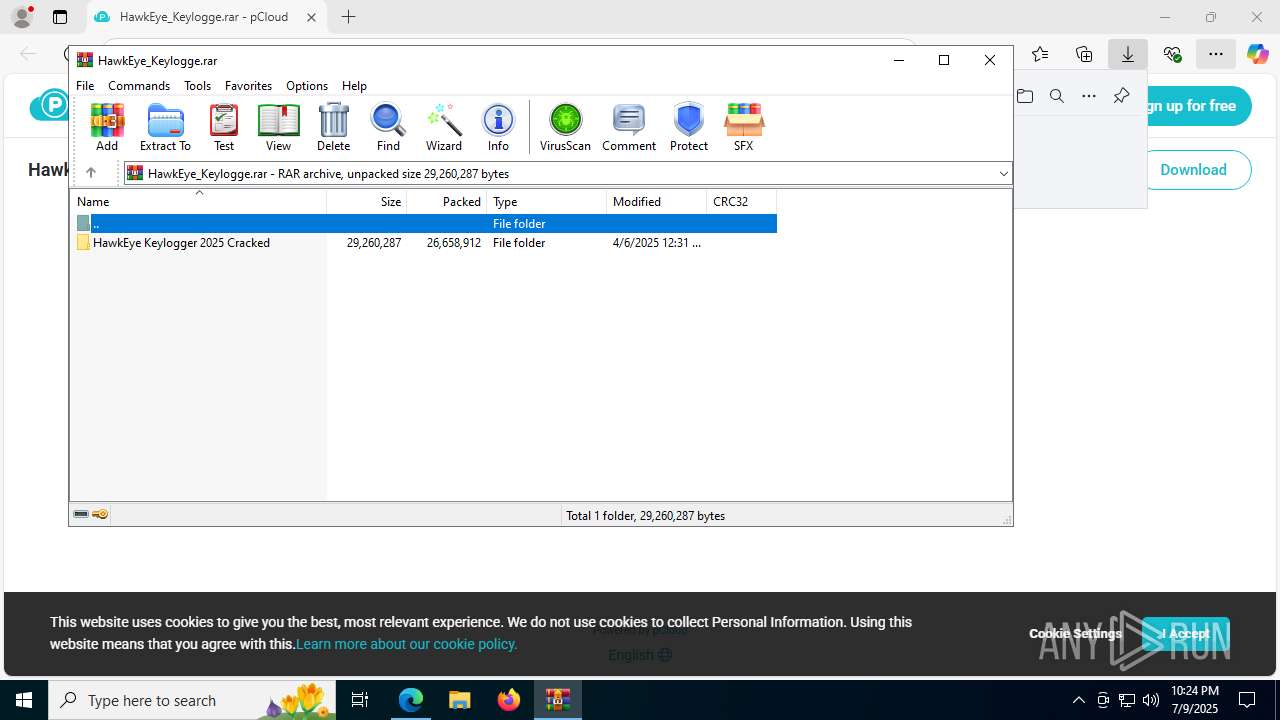
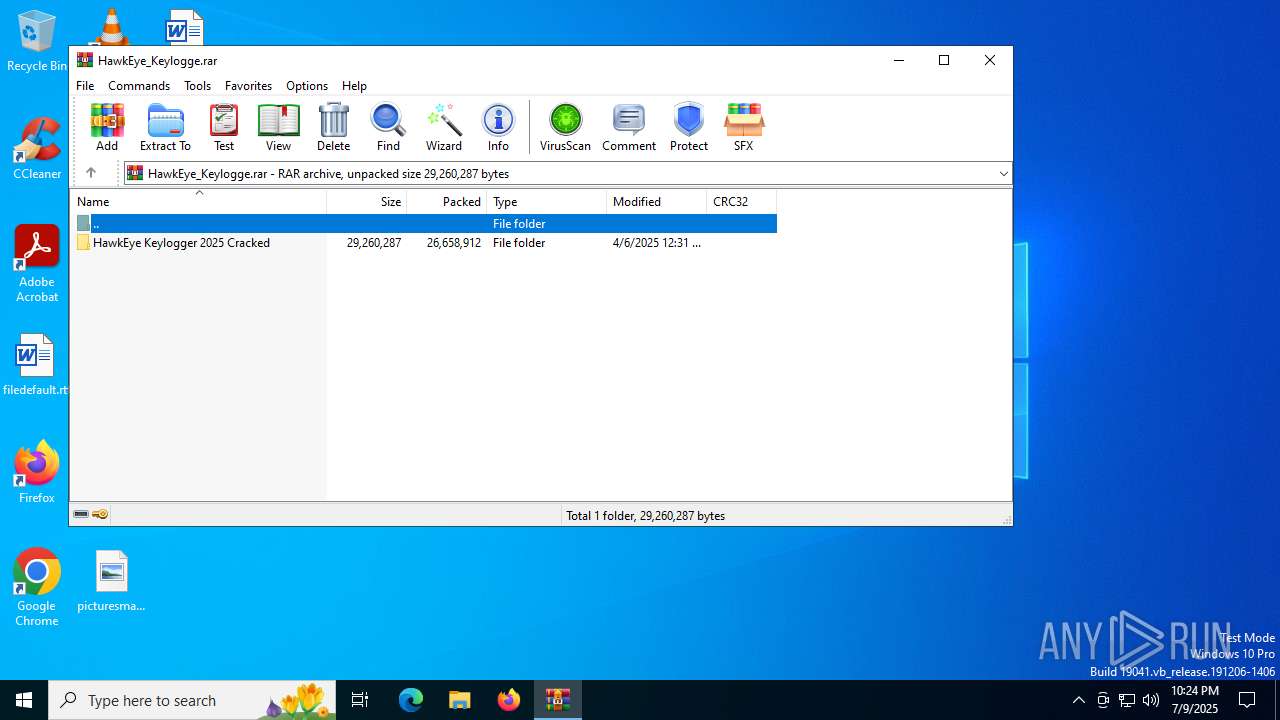
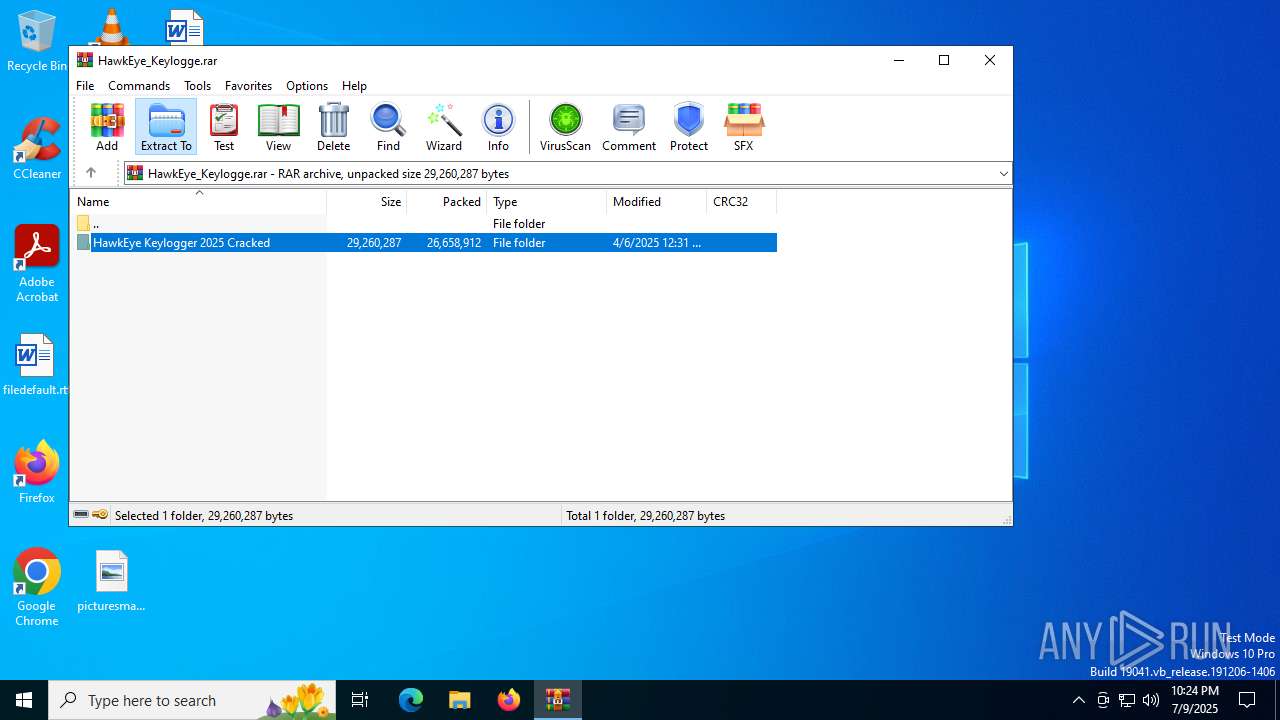
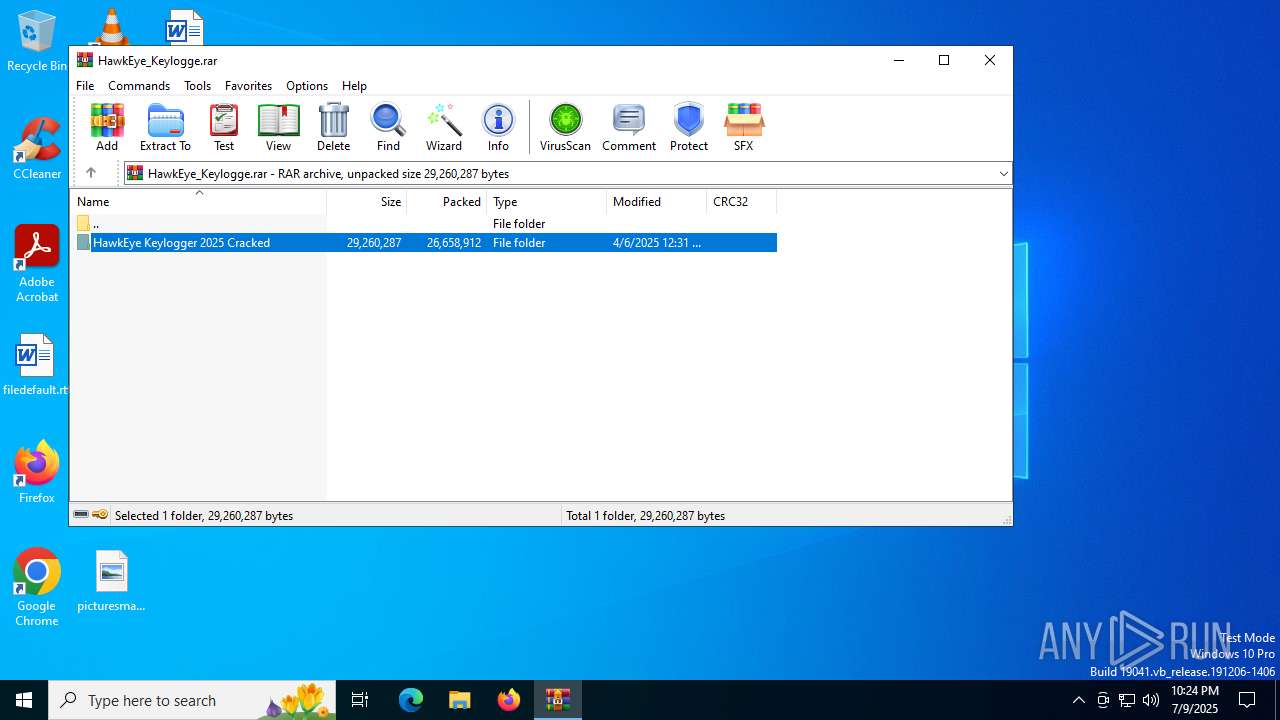
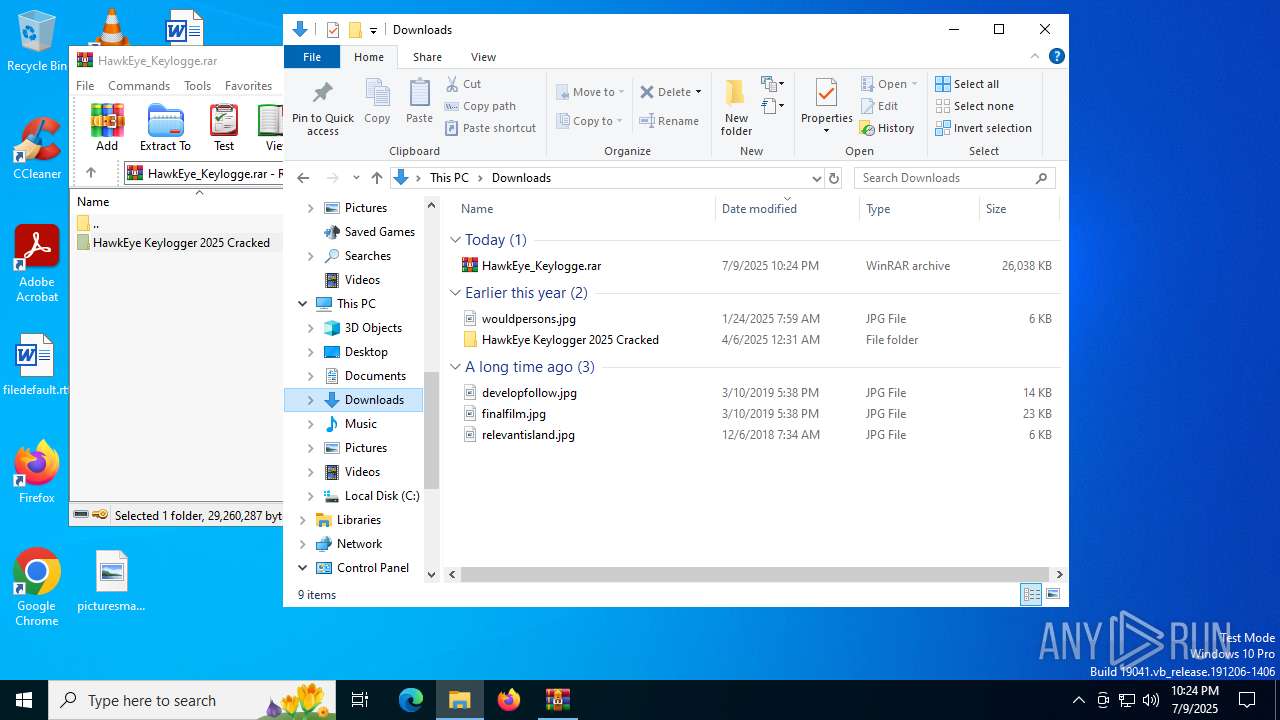
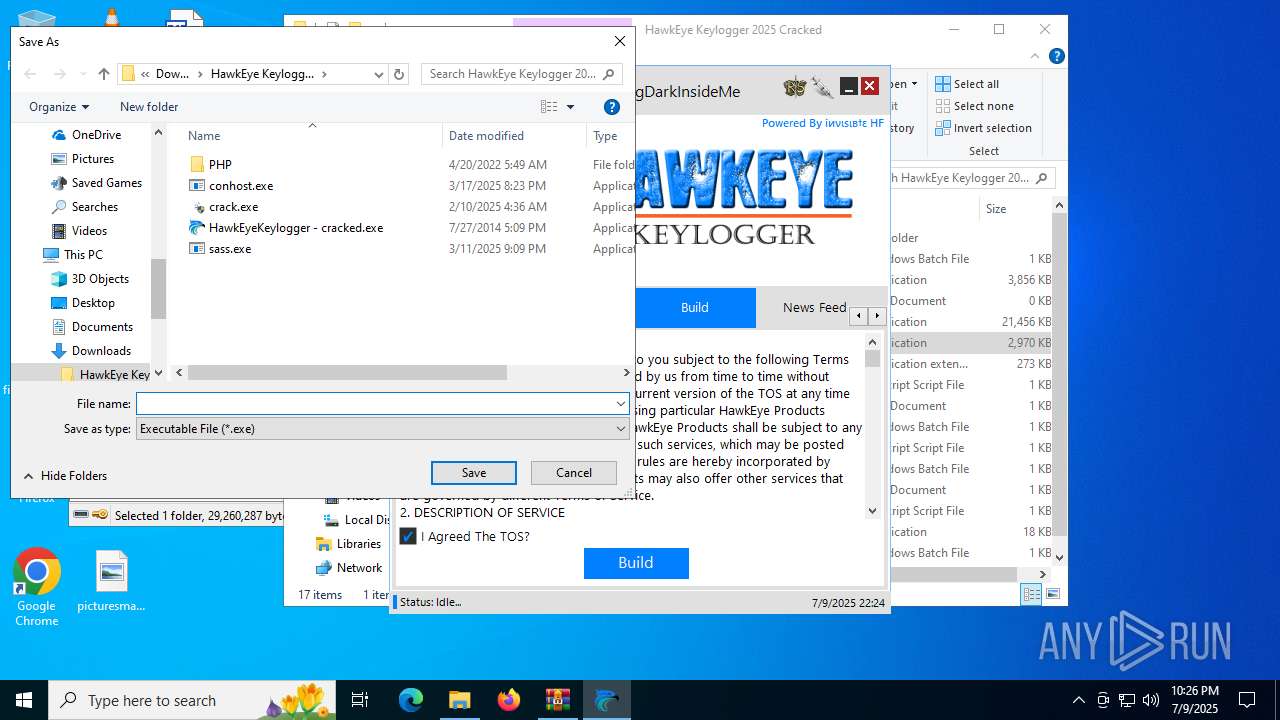
The process creates files with name similar to system file names
- WinRAR.exe (PID: 1564)
Application launched itself
- updater.exe (PID: 5104)
The process executes via Task Scheduler
- updater.exe (PID: 5104)
Reads security settings of Internet Explorer
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- yo.exe (PID: 7624)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
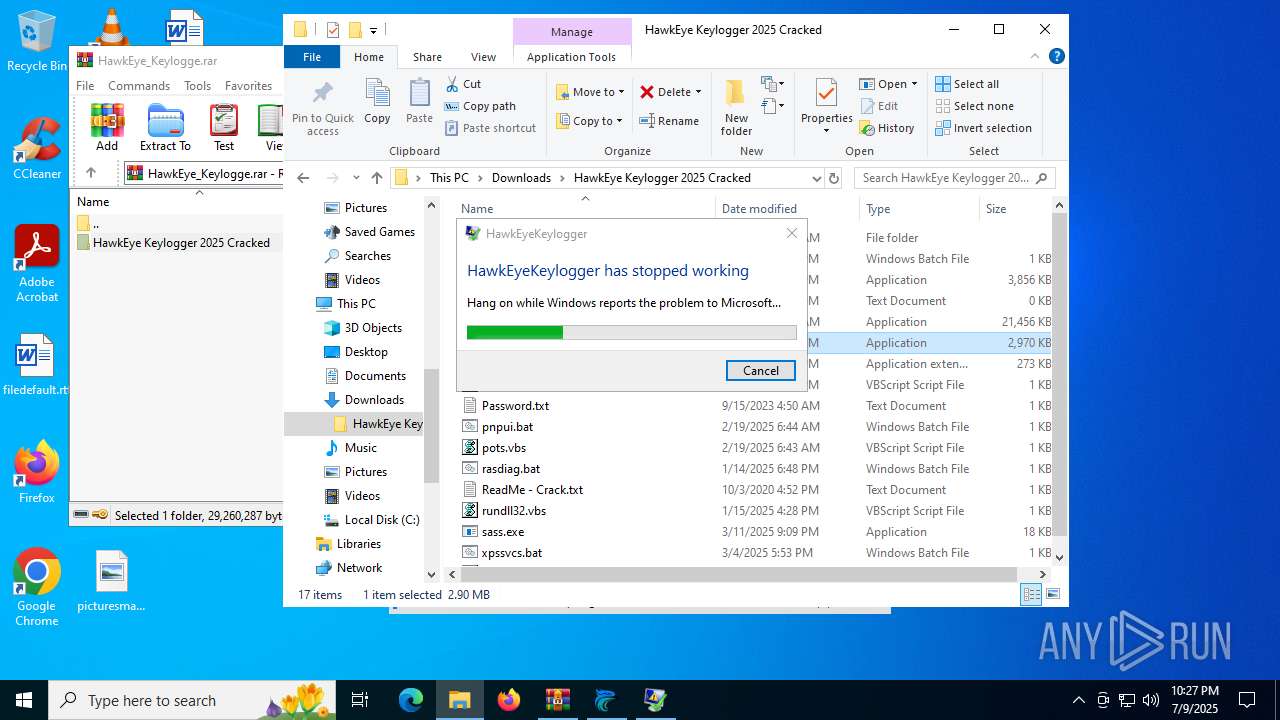
Executes application which crashes
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- HawkEyeKeylogger - cracked.exe (PID: 7996)
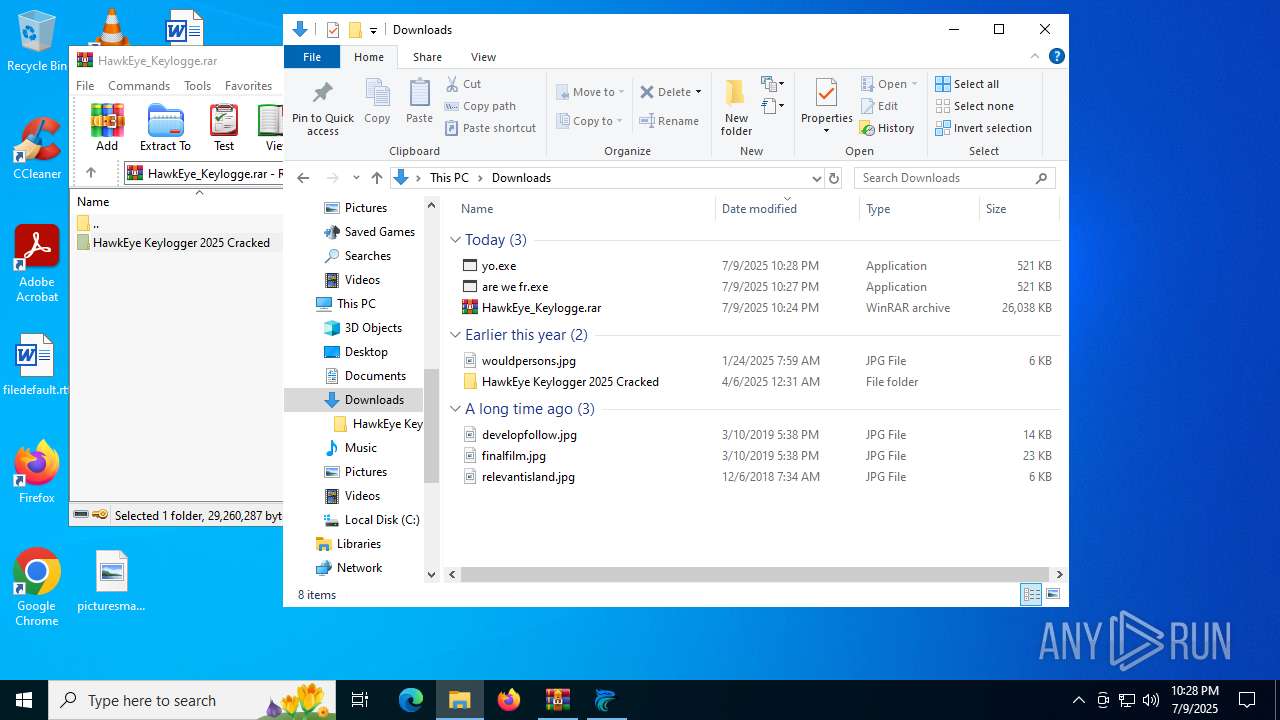
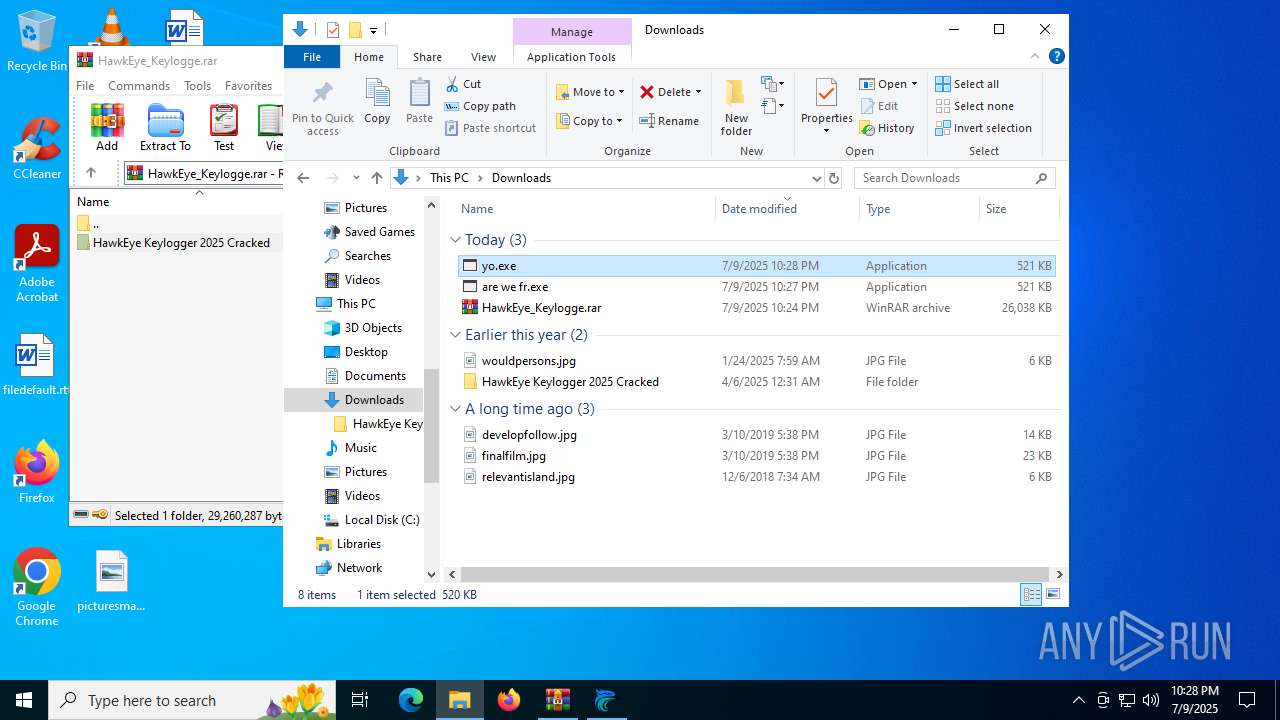
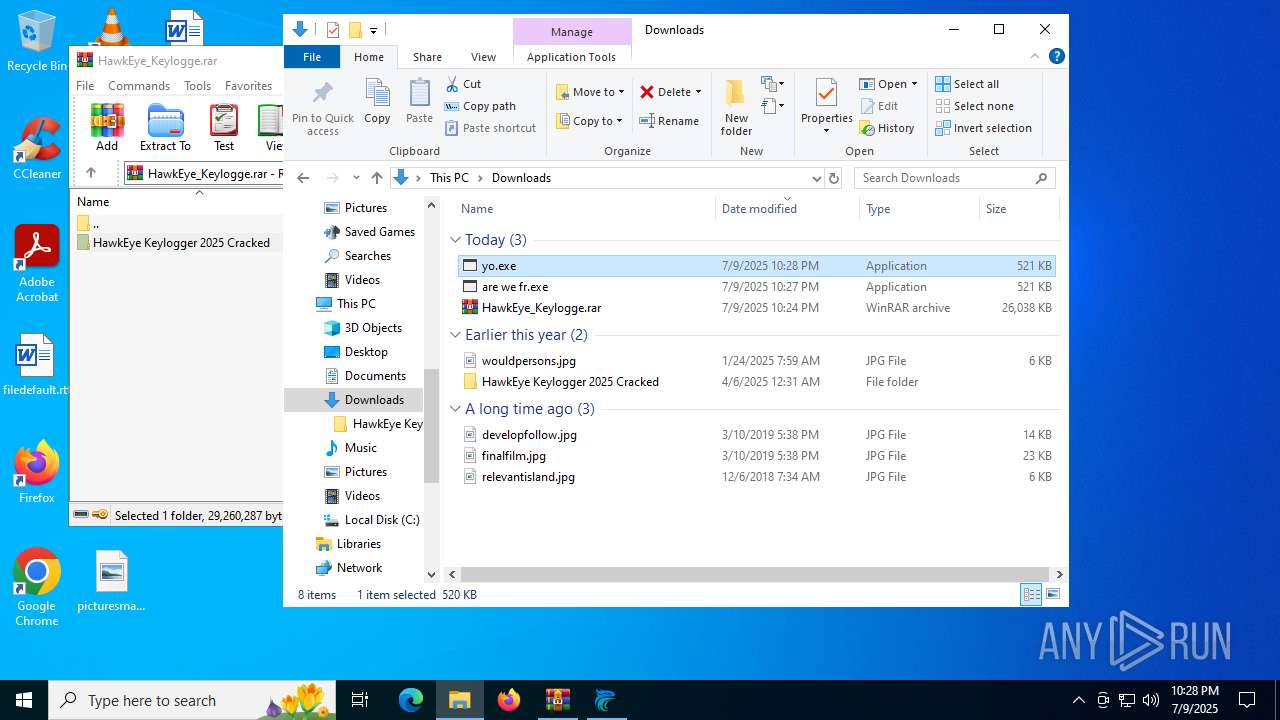
Executable content was dropped or overwritten
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- yo.exe (PID: 7624)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
- Windows Update.exe (PID: 7708)
Probably fake Windows Update file has been dropped
- yo.exe (PID: 7624)
The process executes VB scripts
- Windows Update.exe (PID: 7708)
Checks for external IP
- svchost.exe (PID: 2200)
- Windows Update.exe (PID: 7708)
Starts itself from another location
- yo.exe (PID: 7624)
Probably fake Windows Update
- Windows Update.exe (PID: 7708)
INFO
Checks supported languages
- identity_helper.exe (PID: 7992)
- identity_helper.exe (PID: 7284)
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- updater.exe (PID: 5104)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
- updater.exe (PID: 620)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- yo.exe (PID: 7624)
- vbc.exe (PID: 7064)
- Windows Update.exe (PID: 7708)
- vbc.exe (PID: 5028)
Application launched itself
- msedge.exe (PID: 1800)
- msedge.exe (PID: 5460)
Reads Environment values
- identity_helper.exe (PID: 7992)
- identity_helper.exe (PID: 7284)
Reads the computer name
- identity_helper.exe (PID: 7992)
- identity_helper.exe (PID: 7284)
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- updater.exe (PID: 5104)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- yo.exe (PID: 7624)
- vbc.exe (PID: 7064)
- Windows Update.exe (PID: 7708)
- vbc.exe (PID: 5028)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1800)
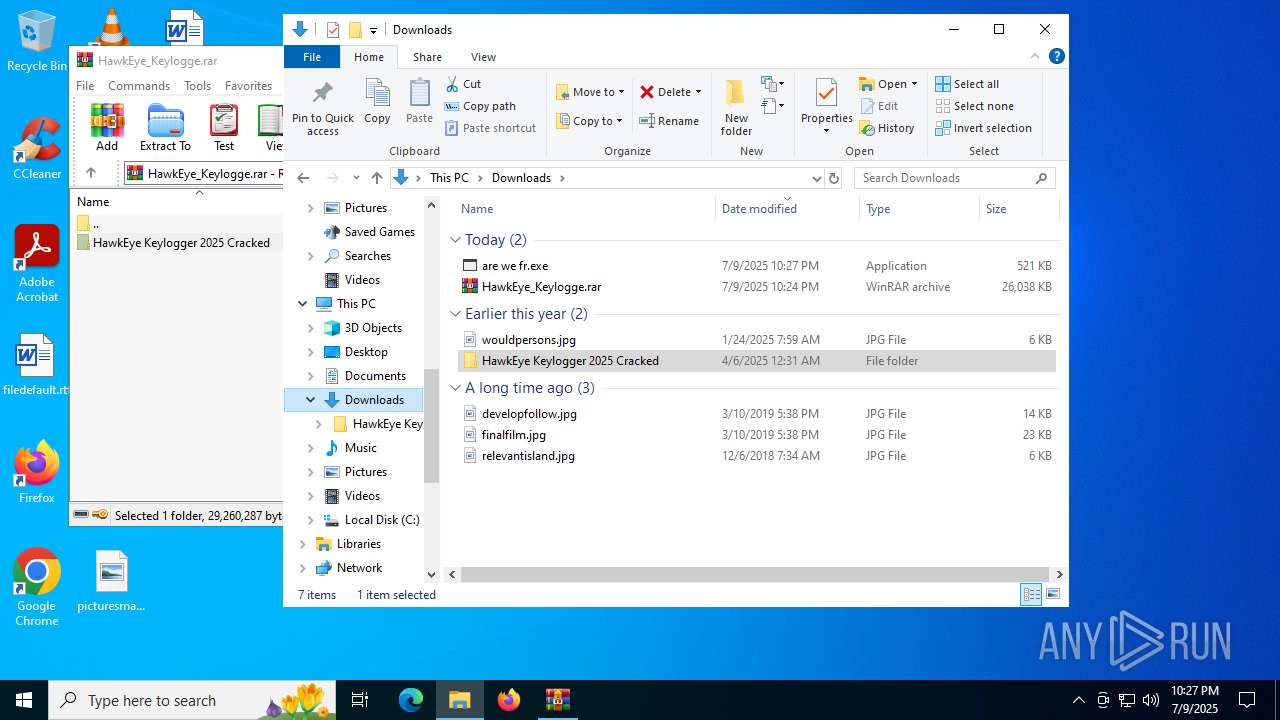
Manual execution by a user
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- yo.exe (PID: 7624)
Reads the machine GUID from the registry
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
- yo.exe (PID: 7624)
- Windows Update.exe (PID: 7708)
- vbc.exe (PID: 5028)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1564)
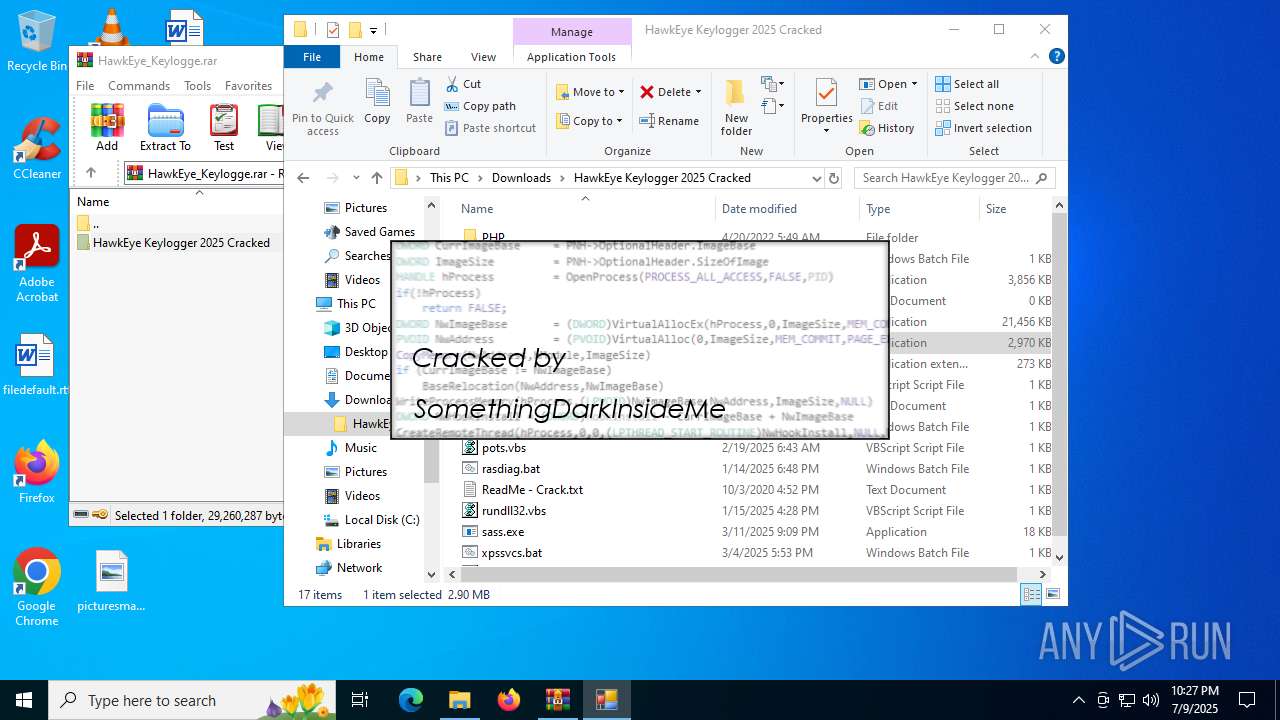
Compiled with Borland Delphi (YARA)
- HawkEyeKeylogger - cracked.exe (PID: 7996)
- HawkEyeKeylogger - cracked.exe (PID: 7396)
- HawkEyeKeylogger - cracked.exe (PID: 7884)
Reads the software policy settings
- slui.exe (PID: 7212)
- WerFault.exe (PID: 8004)
Checks proxy server information
- slui.exe (PID: 7212)
- WerFault.exe (PID: 8004)
- Windows Update.exe (PID: 7708)
Process checks whether UAC notifications are on
- updater.exe (PID: 5104)
Creates files or folders in the user directory
- WerFault.exe (PID: 6772)
- WerFault.exe (PID: 8004)
- yo.exe (PID: 7624)
- Windows Update.exe (PID: 7708)
Create files in a temporary directory
- yo.exe (PID: 7624)
- vbc.exe (PID: 5028)
- vbc.exe (PID: 7064)
Disables trace logs
- Windows Update.exe (PID: 7708)
Launching a file from a Registry key
- Windows Update.exe (PID: 7708)
Process checks computer location settings
- yo.exe (PID: 7624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
61
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2792,i,15786196772968255106,3078829853313436552,262144 --variations-seed-version --mojo-platform-channel-handle=2732 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2a8,0x2ac,0x2b0,0x284,0x2b4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4844,i,15157044404646100420,15809654537427720395,262144 --variations-seed-version --mojo-platform-channel-handle=3896 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2324,i,15786196772968255106,3078829853313436552,262144 --variations-seed-version --mojo-platform-channel-handle=2292 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
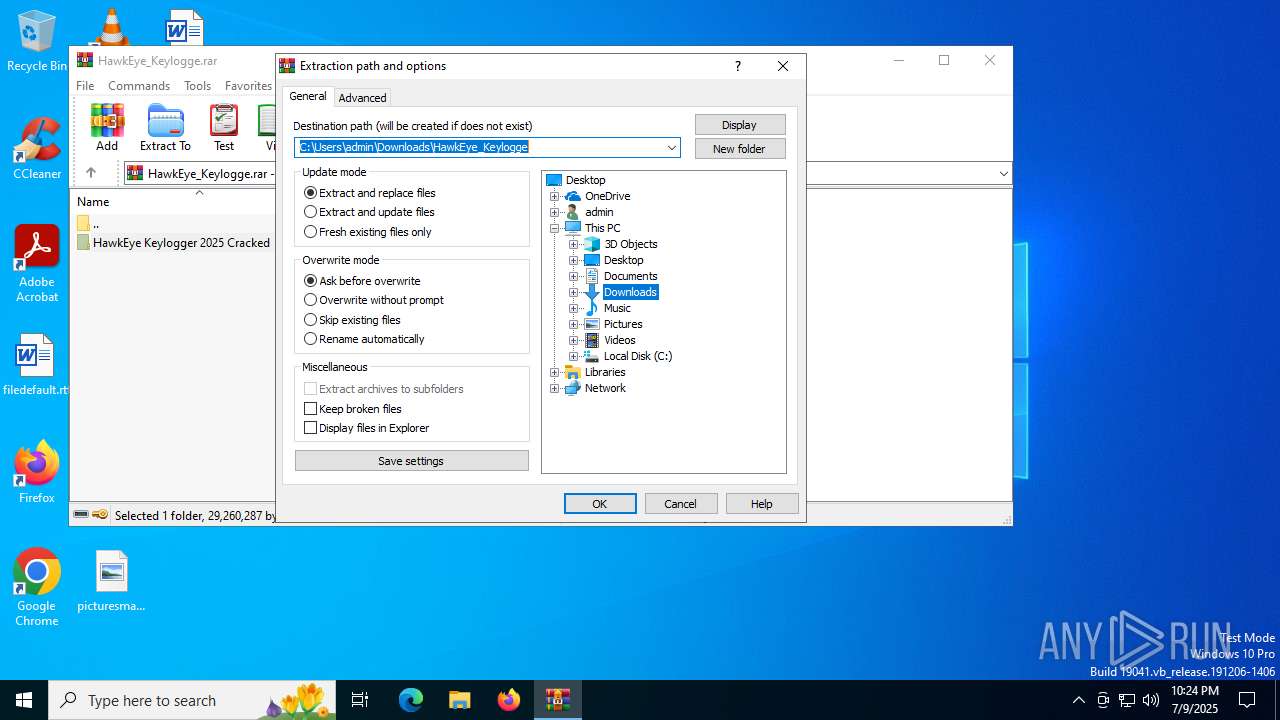
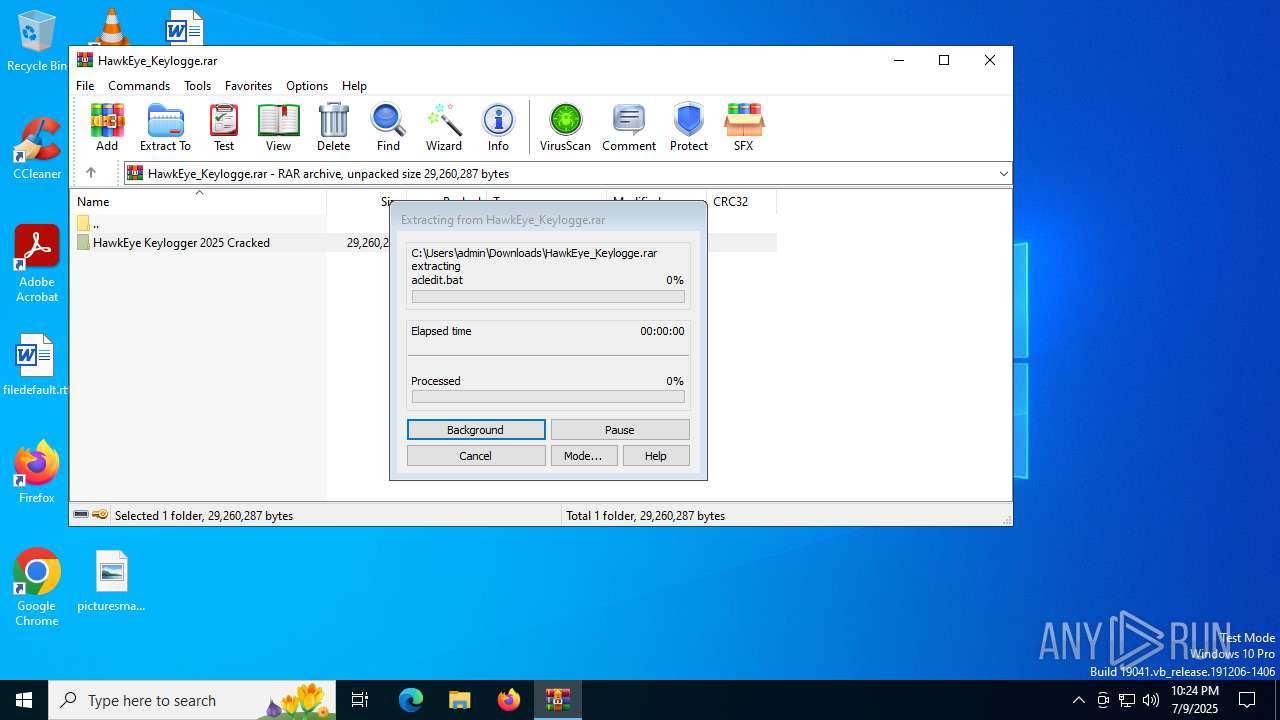
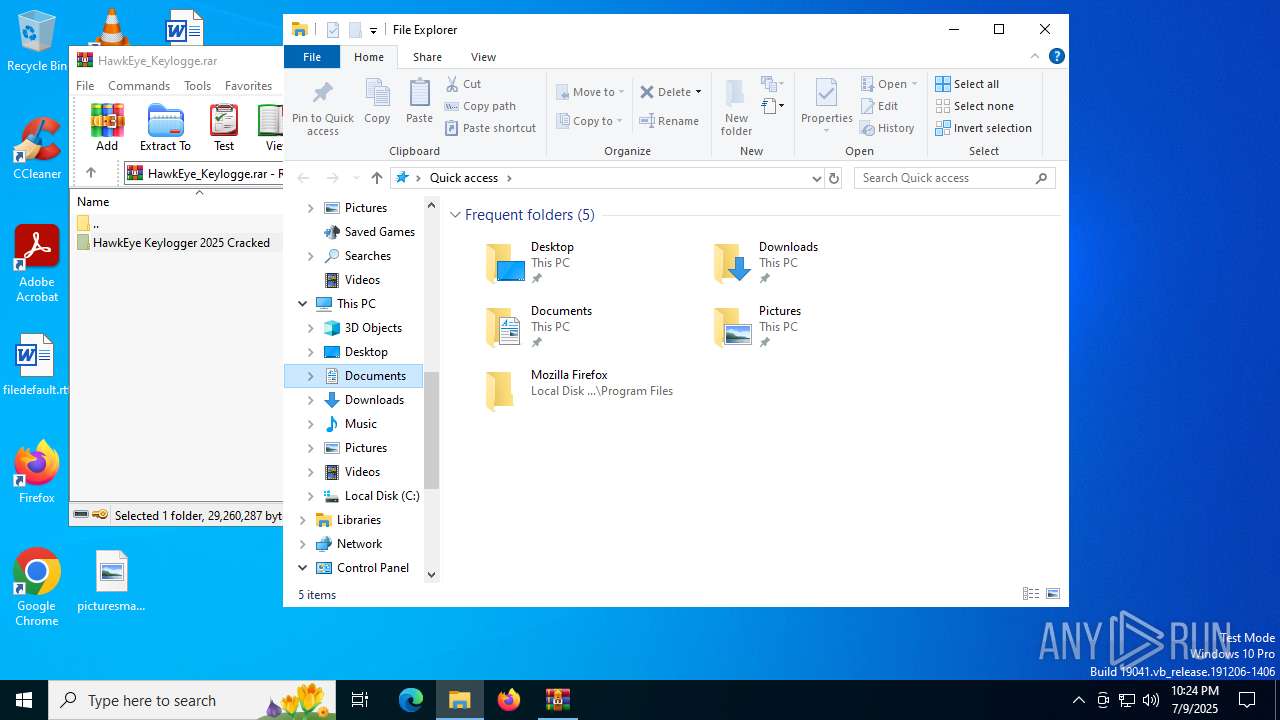
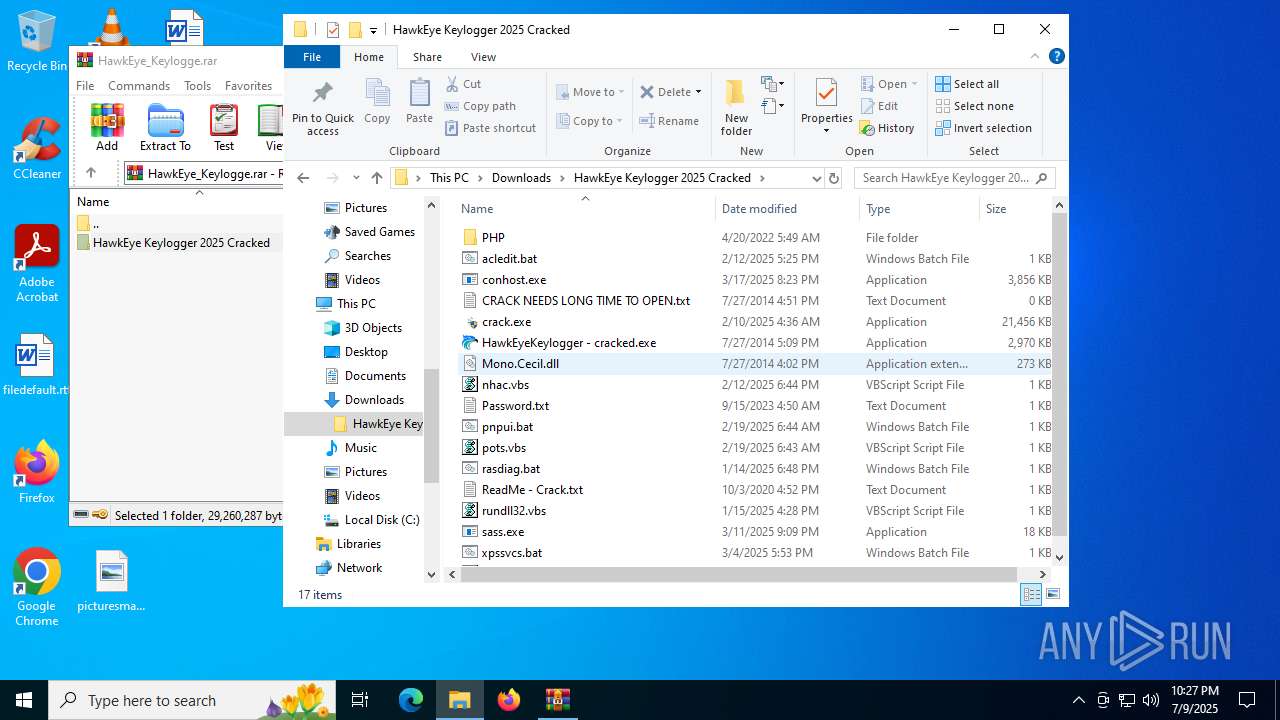
| 1564 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\HawkEye_Keylogge.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://u.pcloud.link/publink/show?code=XZbcNQ5ZrEYlUOnm6ey0RbxLjbm0hbshJVAX" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2724,i,15157044404646100420,15809654537427720395,262144 --variations-seed-version --mojo-platform-channel-handle=5112 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43c5f208,0x7ffc43c5f214,0x7ffc43c5f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2300,i,15786196772968255106,3078829853313436552,262144 --variations-seed-version --mojo-platform-channel-handle=2464 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
30 965
Read events
30 792
Write events
157
Delete events
16
Modification events
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CE7ADFD01C982F00 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {53918FD6-CC4D-47C3-B3FC-B5BDD059E7A3} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D57E3562-A1FC-4067-9E50-475845DD4C57} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {58D31623-F3E6-4D59-A3E9-8619A22E5454} | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 99D061D11C982F00 | |||
| (PID) Process: | (1800) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
12
Suspicious files
322
Text files
132
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175999.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1759a9.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1759a9.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1759b8.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1759c8.TMP | — | |
MD5:— | SHA256:— | |||
| 1800 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
99
DNS requests
94
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/03b2d981-4f59-42a6-8f9a-a2b6278a0020?P1=1752696336&P2=404&P3=2&P4=P6GjKkhBMzPT8mlhNaCYCL%2fL1vLnosqvRUWhZHGF9viak%2b5xE9CsRNcZfqjBWdZo7wcCVOdaDNjY6ZQtl%2bktpg%3d%3d | unknown | — | — | whitelisted |
2160 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6b853aed-57d0-44a7-b8d5-4cdd01a61f64?P1=1752703647&P2=404&P3=2&P4=mwF2Hn5LGcd5Xgavg%2f%2f0mCVBomM%2fI5U04ES4AoUCAnVynPMoqpwm8408tAfIl5j6ar6qu59Whyiz26Vpb0LCoA%3d%3d | unknown | — | — | whitelisted |
2160 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/03b2d981-4f59-42a6-8f9a-a2b6278a0020?P1=1752696336&P2=404&P3=2&P4=P6GjKkhBMzPT8mlhNaCYCL%2fL1vLnosqvRUWhZHGF9viak%2b5xE9CsRNcZfqjBWdZo7wcCVOdaDNjY6ZQtl%2bktpg%3d%3d | unknown | — | — | whitelisted |
2664 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:s6adpbx2Eo7zCrirhhWljJsMCiFufCR1Tb64GYuosdw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.181:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3944 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6412 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6412 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4860 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2664 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2664 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2664 | msedge.exe | 74.120.8.110:443 | u.pcloud.link | LEMURIACO | US | suspicious |
2664 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2664 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
u.pcloud.link |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pcdn-u.pcloud.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2664 | msedge.exe | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed in DNS Lookup (pcloud .com) |
2664 | msedge.exe | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed in DNS Lookup (pcloud .com) |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2664 | msedge.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |