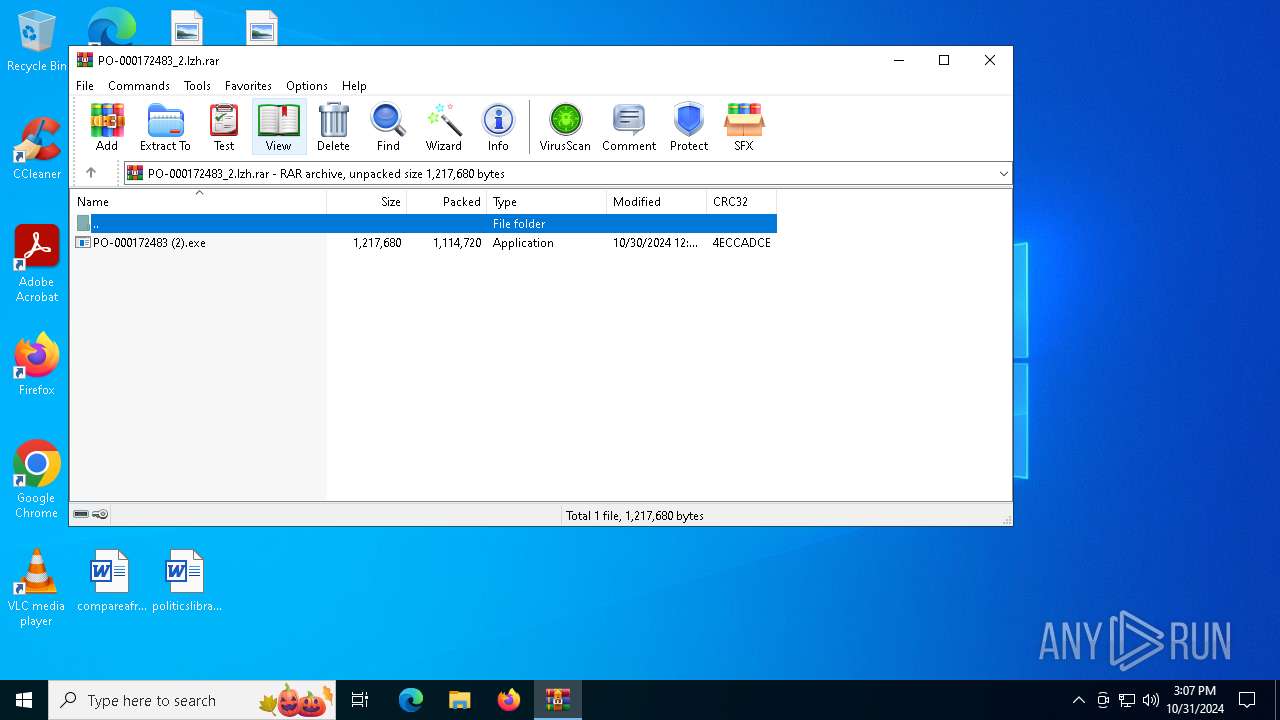
| File name: | PO-000172483_2.lzh |
| Full analysis: | https://app.any.run/tasks/42697e38-9214-490d-a109-f3b7ba526992 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 31, 2024, 15:06:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
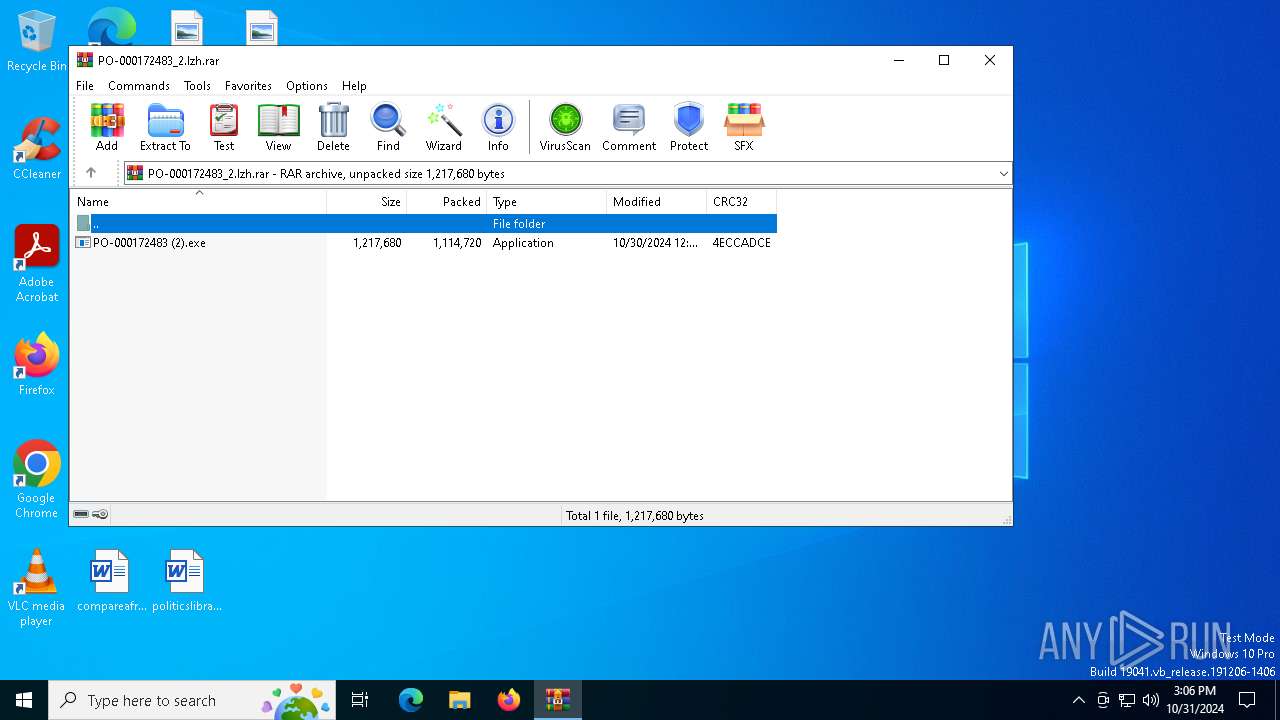
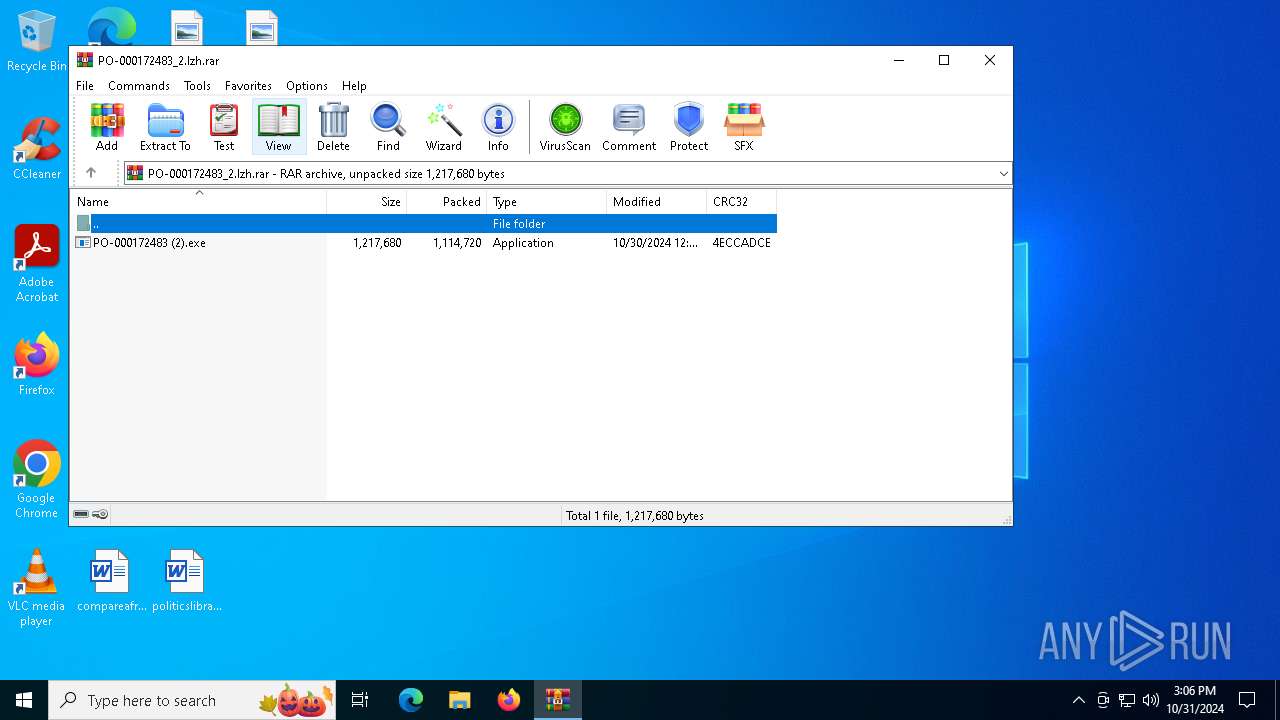
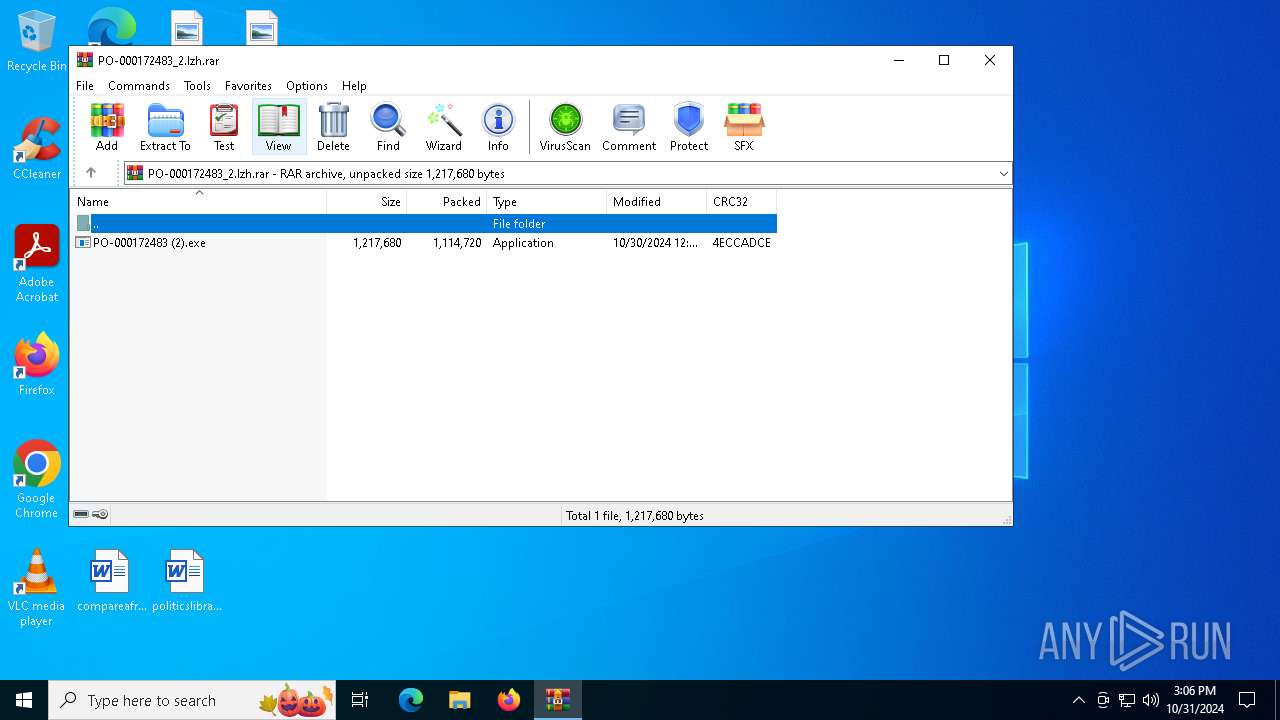
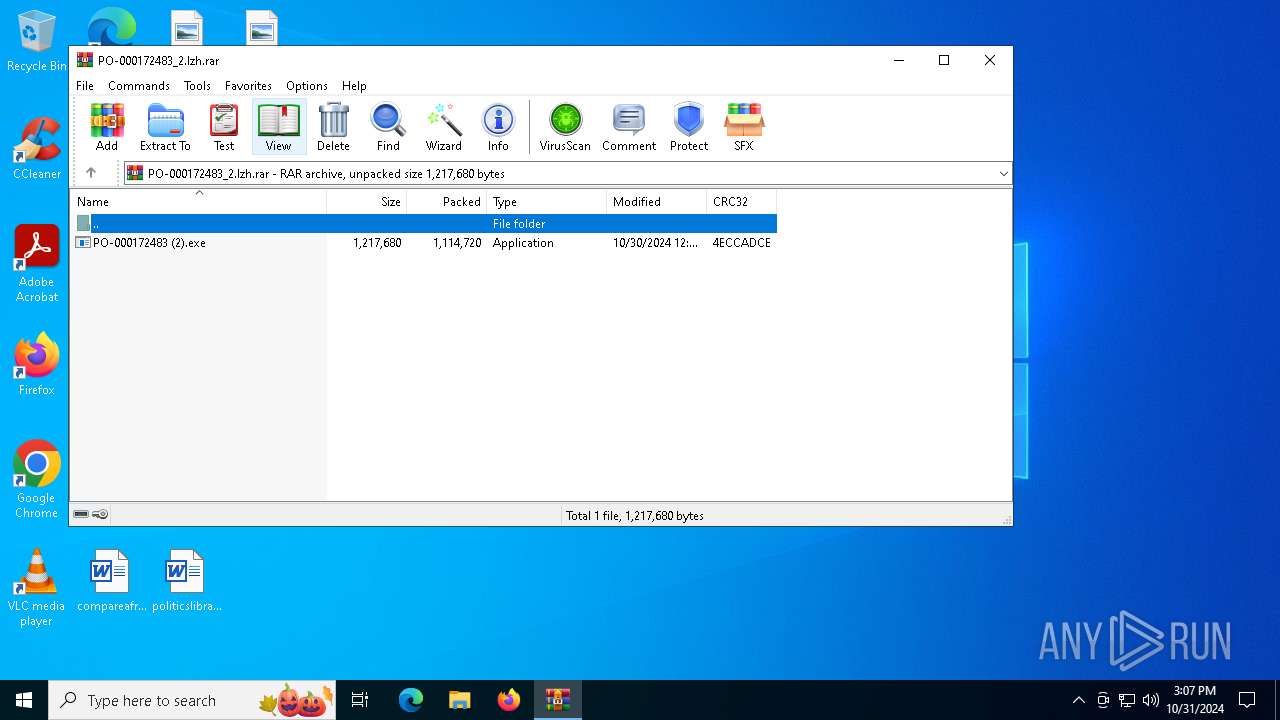
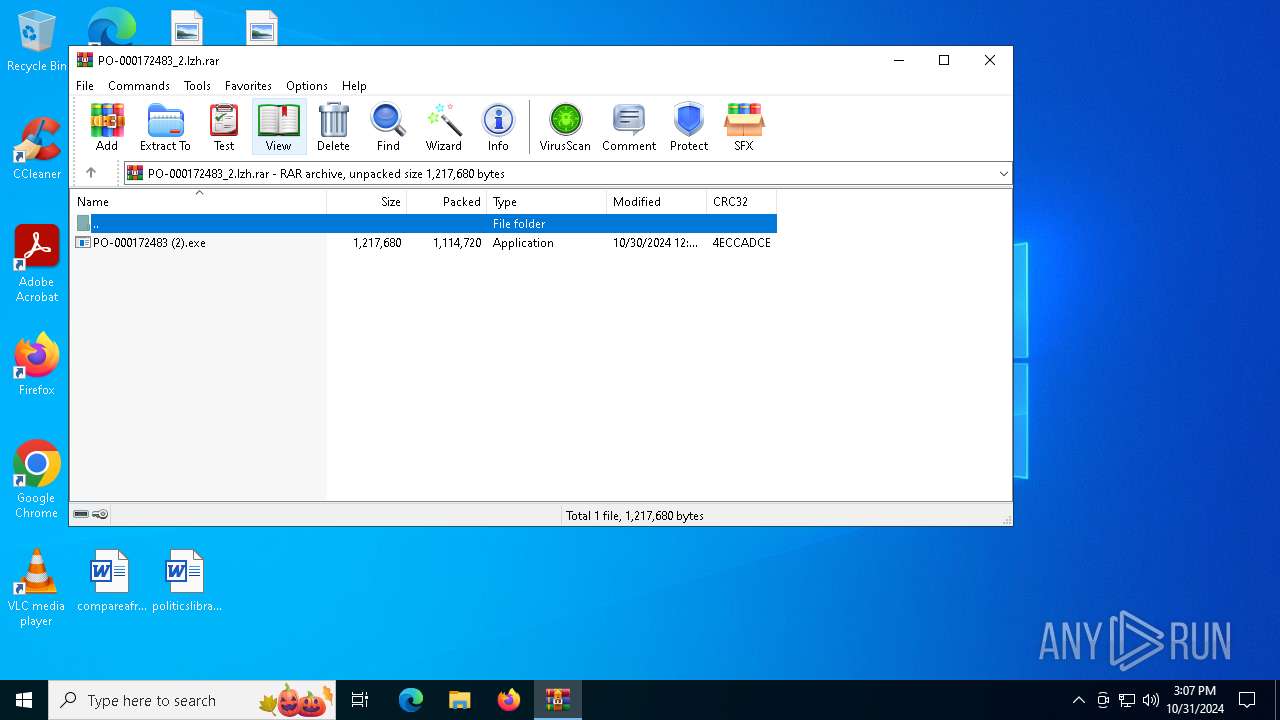
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C549C07DC8291DF4D2653F904E3E9309 |
| SHA1: | 38C5EEE99CB1F70A5851E429F17F4BFE3BB99A03 |
| SHA256: | E186576FA4B633B6396E563BA2565B95E3B0A8BDB42C4BFC9A4CAF1E948A9AF5 |
| SSDEEP: | 49152:mvd7Bvgv4jpiOEN5YvdfAZBixr/yVnJ2mrytkRHAIJgZMRdFvr7e9fAD9uvKl8vf:mv3piOE7YvJAZBipOdrytugkRdJqW9aR |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6224)
Connects to the CnC server
- WinRAR.exe (PID: 6224)
FORMBOOK has been detected (SURICATA)
- WinRAR.exe (PID: 6224)
SUSPICIOUS
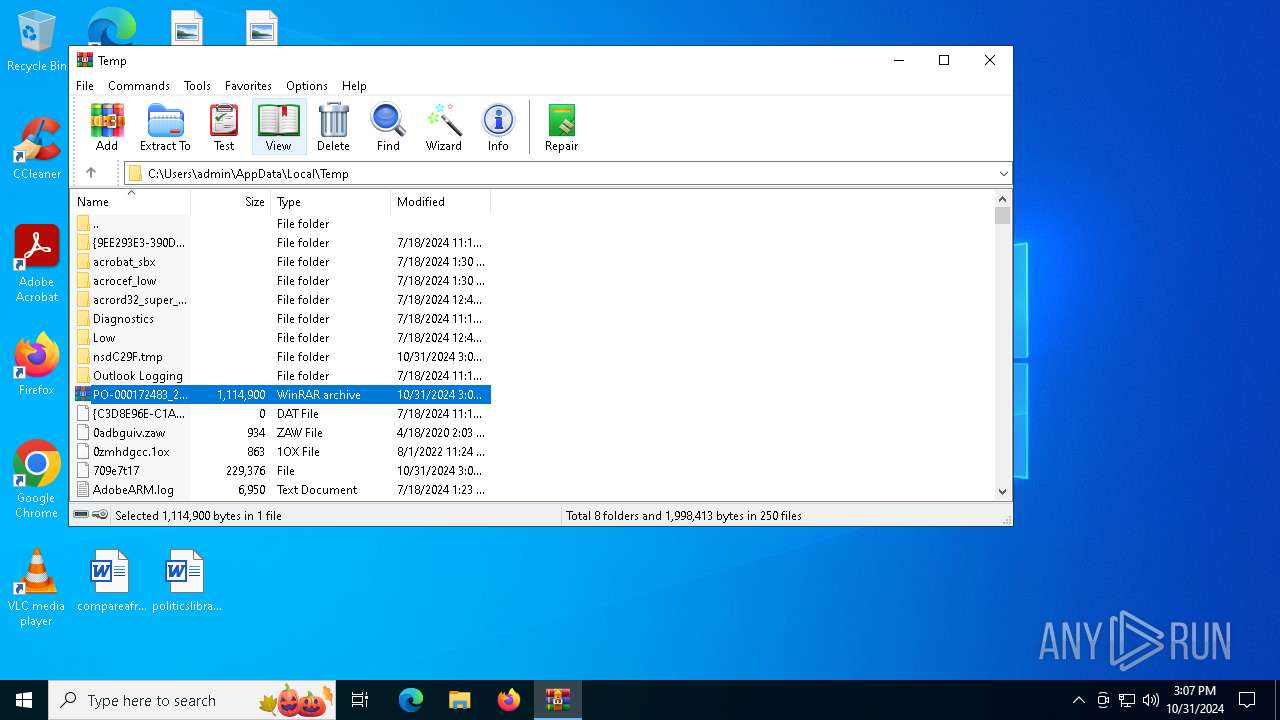
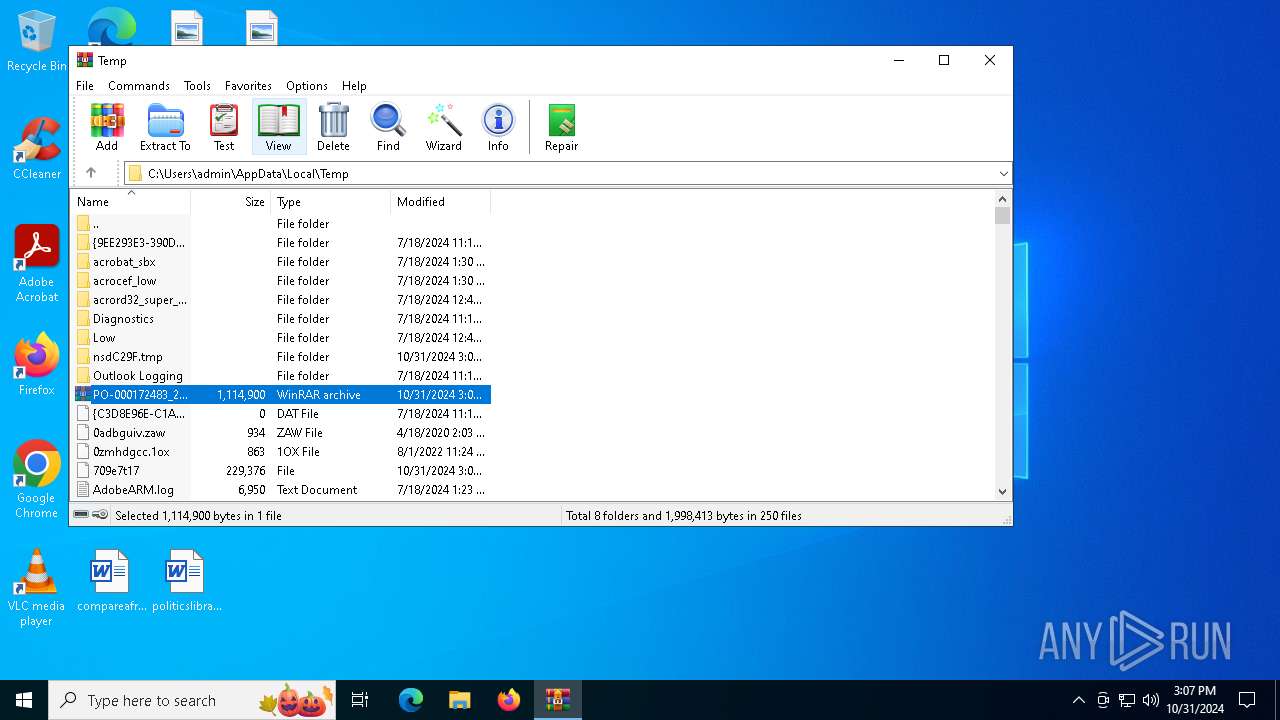
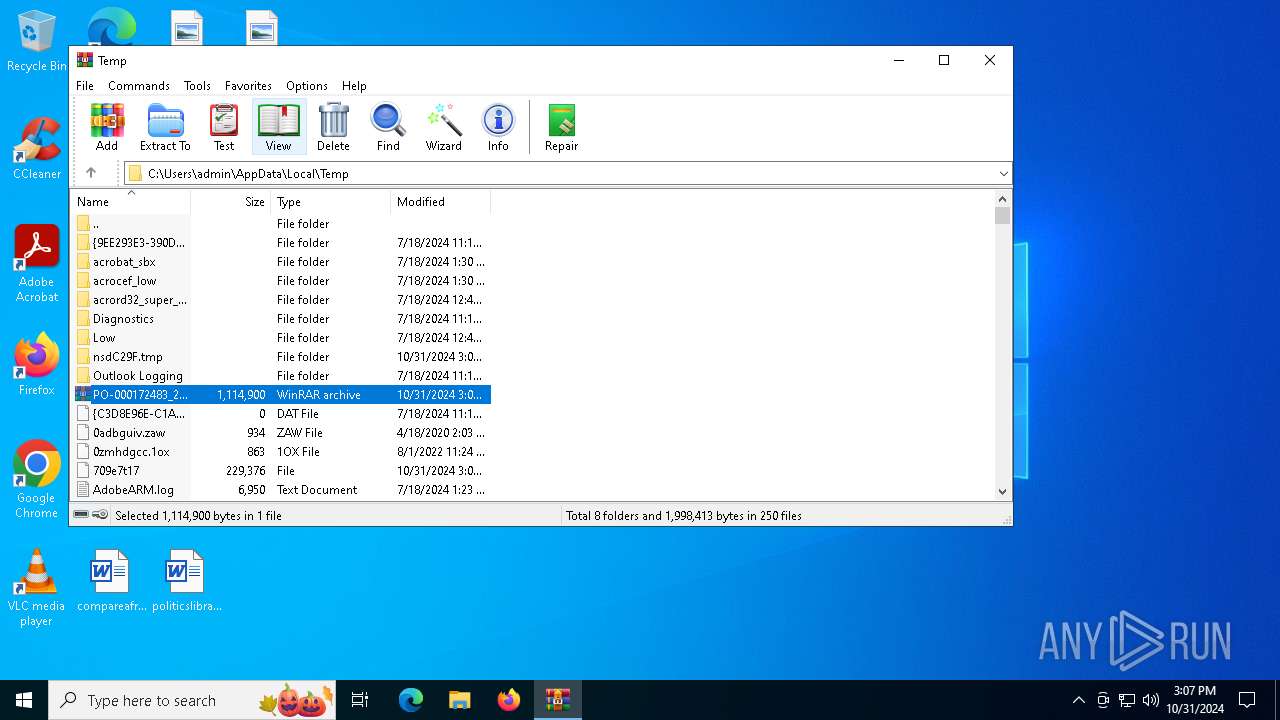
Malware-specific behavior (creating "System.dll" in Temp)
- PO-000172483 (2).exe (PID: 6472)
Application launched itself
- PO-000172483 (2).exe (PID: 6472)
Executable content was dropped or overwritten
- PO-000172483 (2).exe (PID: 6472)
Suspicious use of NETSH.EXE
- WinRAR.exe (PID: 6224)
Contacting a server suspected of hosting an CnC
- WinRAR.exe (PID: 6224)
INFO
Manual execution by a user
- PO-000172483 (2).exe (PID: 6472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 1114720 |
| UncompressedSize: | 1217680 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | PO-000172483 (2).exe |
Total processes
134
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5240 | "C:\Windows\SysWOW64\netsh.exe" | C:\Windows\SysWOW64\netsh.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6124 | "C:\Users\admin\Desktop\PO-000172483 (2).exe" | C:\Users\admin\Desktop\PO-000172483 (2).exe | PO-000172483 (2).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: screamer slounge Exit code: 0 Modules
| |||||||||||||||
| 6224 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\PO-000172483_2.lzh.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6472 | "C:\Users\admin\Desktop\PO-000172483 (2).exe" | C:\Users\admin\Desktop\PO-000172483 (2).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: screamer slounge Exit code: 0 Modules
| |||||||||||||||
| 7132 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | netsh.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
19 009
Read events
18 663
Write events
346
Delete events
0
Modification events
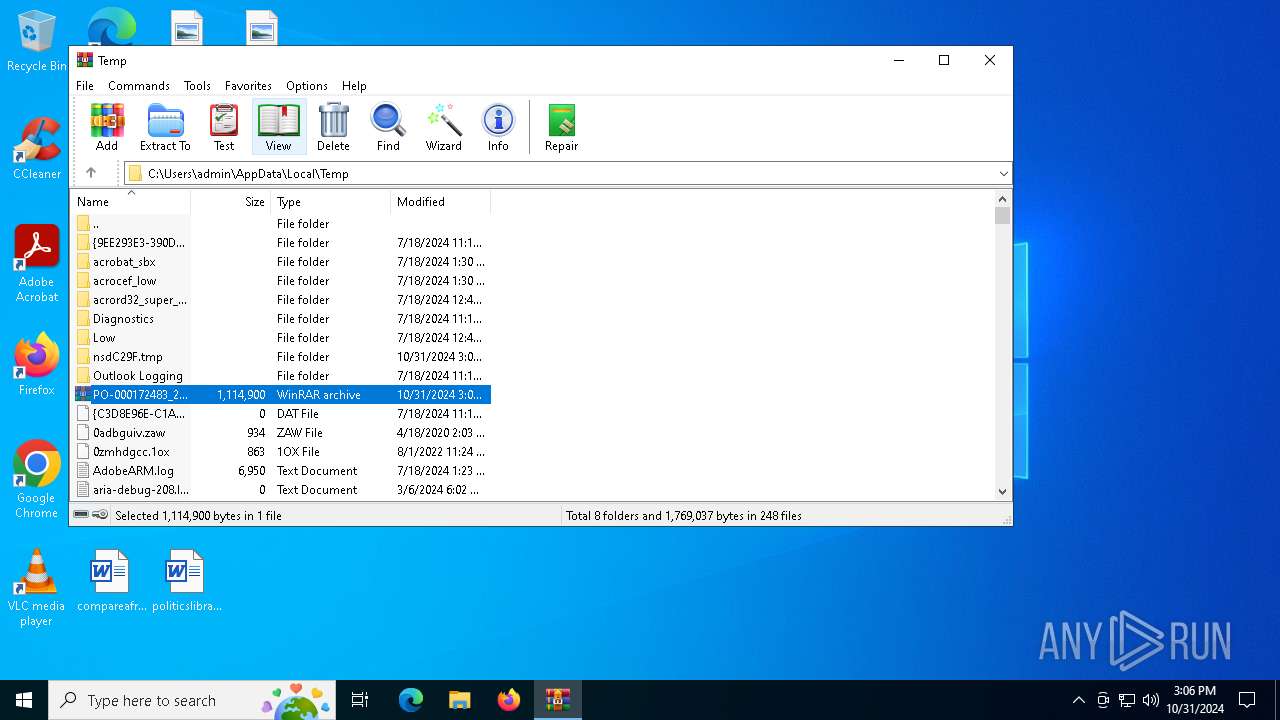
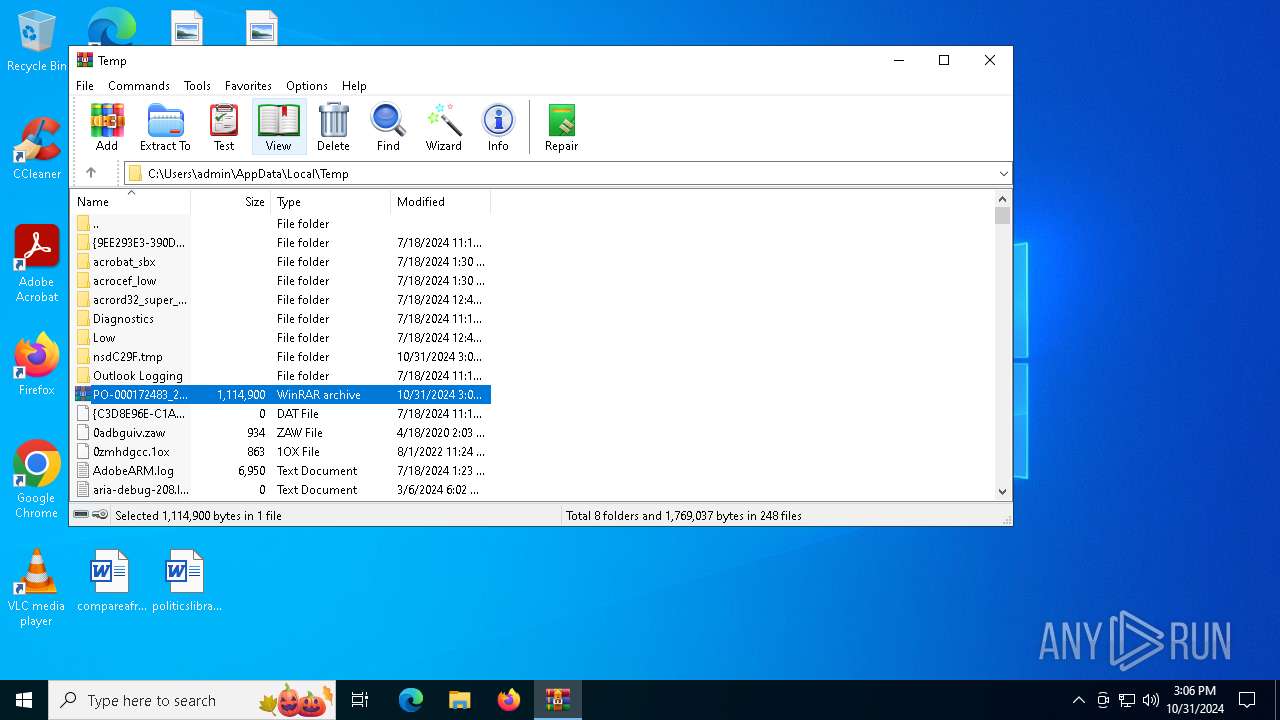
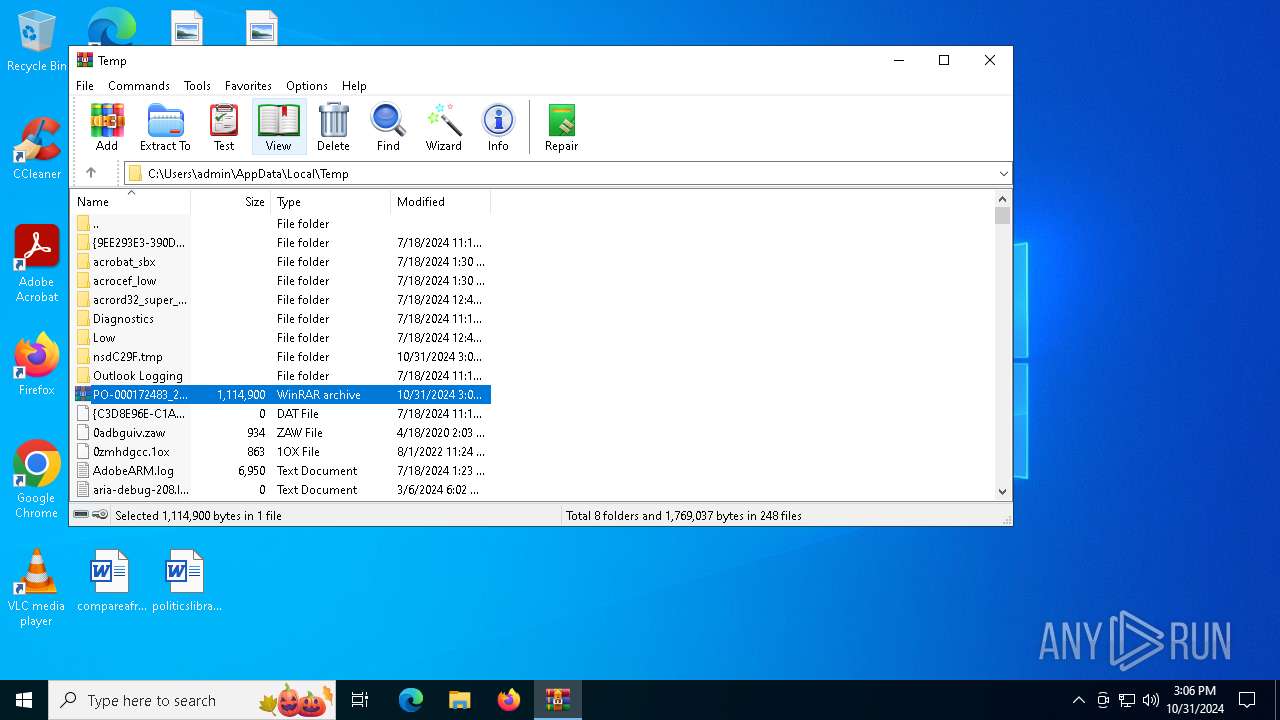
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PO-000172483_2.lzh.rar | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6472) PO-000172483 (2).exe | Key: | HKEY_CURRENT_USER\Zoofulvin68\Uninstall\brevbrere |
| Operation: | write | Name: | aircondition |
Value: 1 | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6224) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
1
Suspicious files
18
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6124 | PO-000172483 (2).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4FA45AE1010E09657982D8D28B3BD38E_CC847C1C687BCB4C6B5074DF051D733B | binary | |
MD5:C604DAFA27DC20FB1A0769CC882516E8 | SHA256:514705FD6E613F0E1ACF40648970EACC1791416A816EDBC2E5A4E10E1F95F068 | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Woodsmen\regill.ful | binary | |
MD5:B4FB425BAF217F31E91AAB39ABF66DCD | SHA256:4BC57A47B82B63EC20B393F65F3585EB81FE3F7748229CD19DEC8FE8A41D67C3 | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Proprietrer.bet | binary | |
MD5:0B62328C4966F6B879B3C13B7FBD9C0D | SHA256:645C325F62AF720972466322B09A7E396E46D8E640B138D582374B68D763A3A7 | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Ephemerality.Die | binary | |
MD5:4C350ACEE2817C711EBFD92A5B717772 | SHA256:22343C3DEDB52143B9B2E12FD783042710CD0B43B1B69E820356513F08C3DCFF | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Woodsmen\boyaus.rom | binary | |
MD5:F130EC3095DBECEDC791D8C58A59040C | SHA256:A56351ED69A301F5D9D89B6530280B7A85F998A806E1648911C37B6983BA9426 | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Woodsmen\gear.dra | binary | |
MD5:53FF1A157920AE92C9BF891D453D6B65 | SHA256:FAD1B5E641DC44B5A51048470D4E0FB47664CF2B994CEA24304495D99323B9DE | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Woodsmen\sortlistningens.txt | text | |
MD5:46003C65AA12A0EBE55662F0141186DC | SHA256:2EA079DEDE1B356842C5F5E0751B5E2B6565FDED65DAFB59A73D170C002ABB27 | |||
| 6124 | PO-000172483 (2).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:07A169FB8FD95D078244E3C731093347 | SHA256:0FE08EFAD3E0FB24A688CA2470790AC3BECBE71ED685EFB07A30AB52E0319C56 | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\overlays\besvangredes\Woodsmen\jagtfalk.ill | binary | |
MD5:169115C751DDA5E021E8C86E8454B26D | SHA256:ACCD4911D88E808AED4A2AA27394628C62574810B0B47977B7103A246FDF2A10 | |||
| 6472 | PO-000172483 (2).exe | C:\Users\admin\AppData\Local\Temp\nsdC29F.tmp\System.dll | executable | |
MD5:D6F54D2CEFDF58836805796F55BFC846 | SHA256:F917AEF484D1FBB4D723B2E2D3045CB6F5F664E61FBB3D5C577BD1C215DE55D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
66
DNS requests
33
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6124 | PO-000172483 (2).exe | GET | 200 | 172.217.16.131:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDzySkSNBgXtBKLijHUmMxR | unknown | — | — | whitelisted |
6124 | PO-000172483 (2).exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
6124 | PO-000172483 (2).exe | GET | 200 | 172.217.16.131:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACECt1gF5RMj4mChEciVJIkog%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6124 | PO-000172483 (2).exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4072 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6112 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7056 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4360 | SearchApp.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2076 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2076 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4360 | SearchApp.exe | 2.23.209.175:443 | th.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
drive.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6224 | WinRAR.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6224 | WinRAR.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6224 | WinRAR.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) M5 |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6224 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
10 ETPRO signatures available at the full report