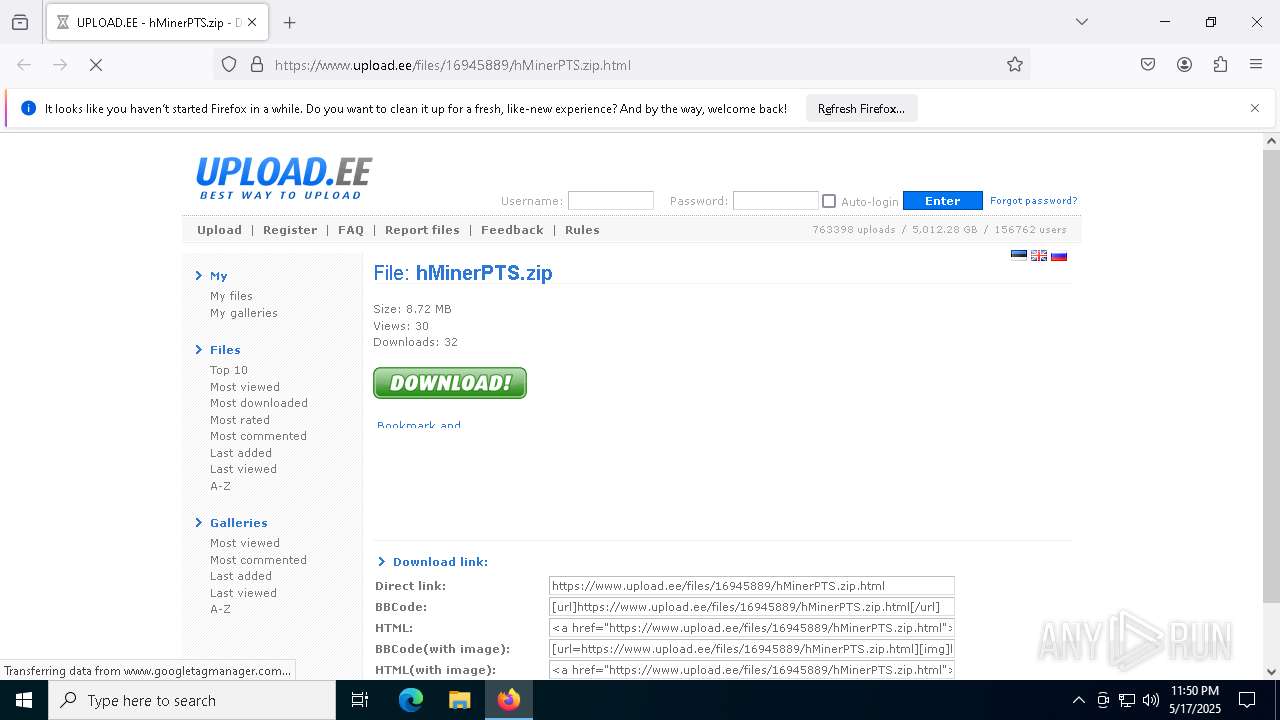
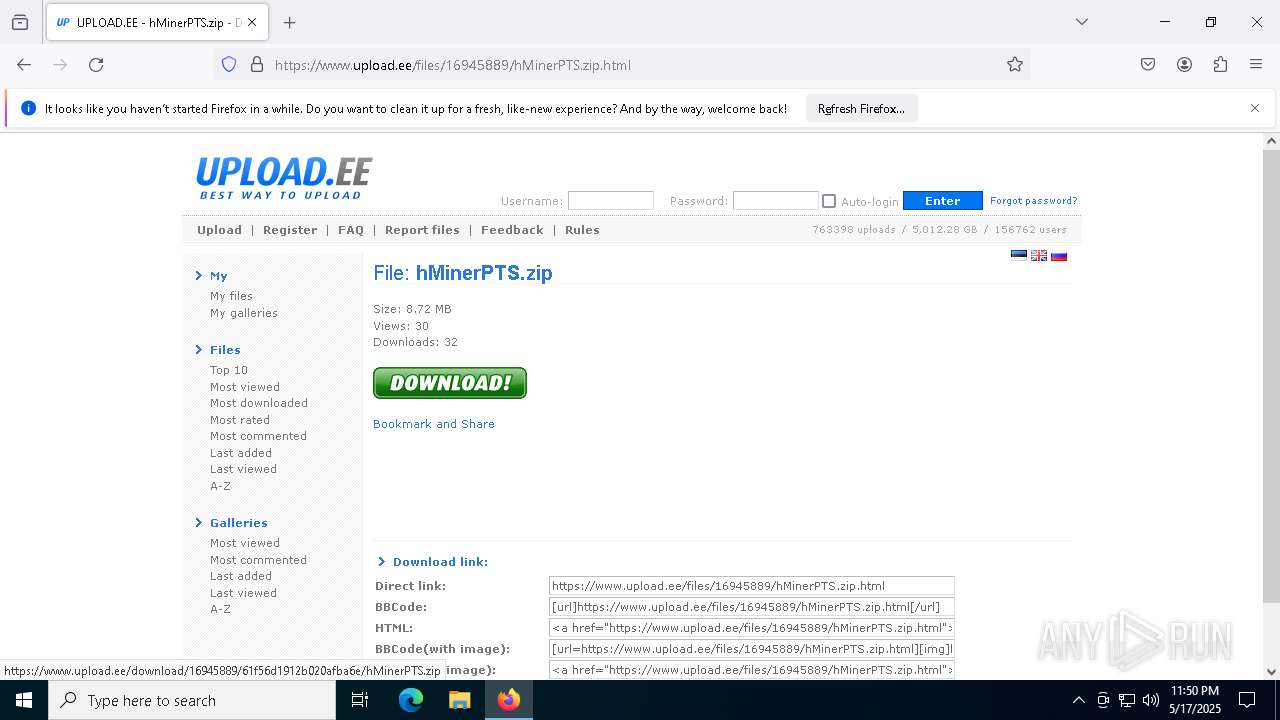
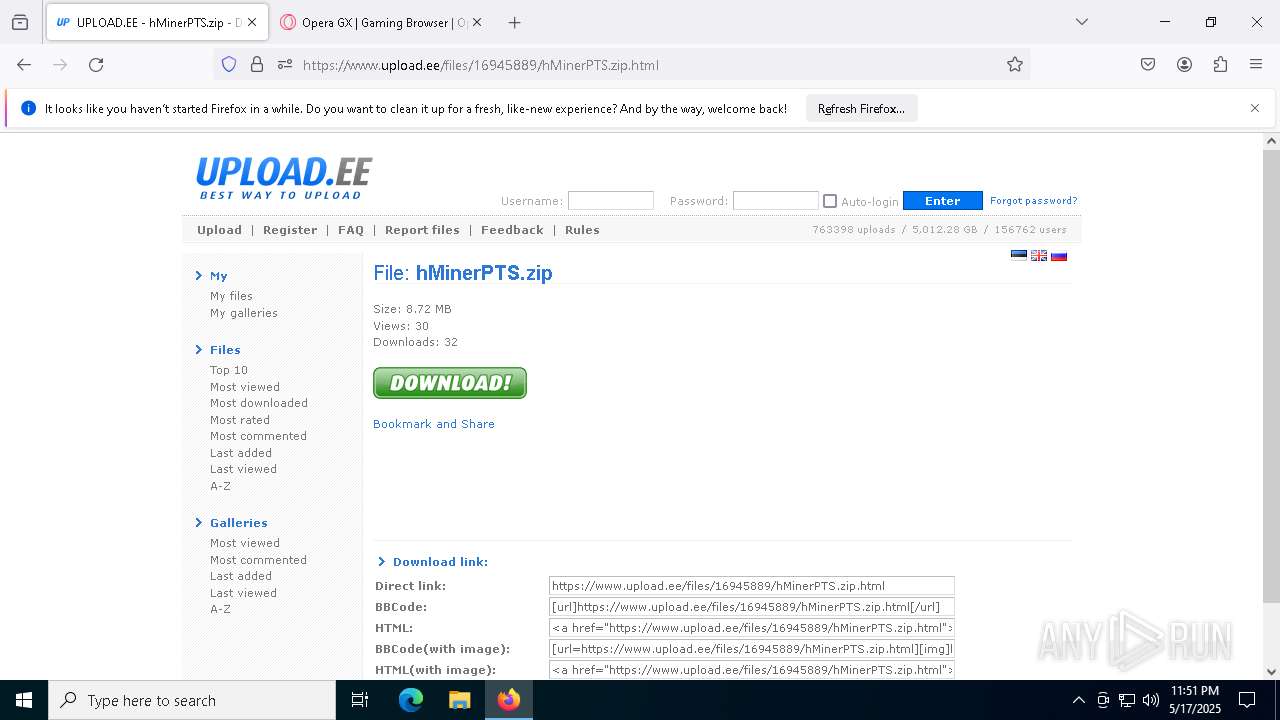
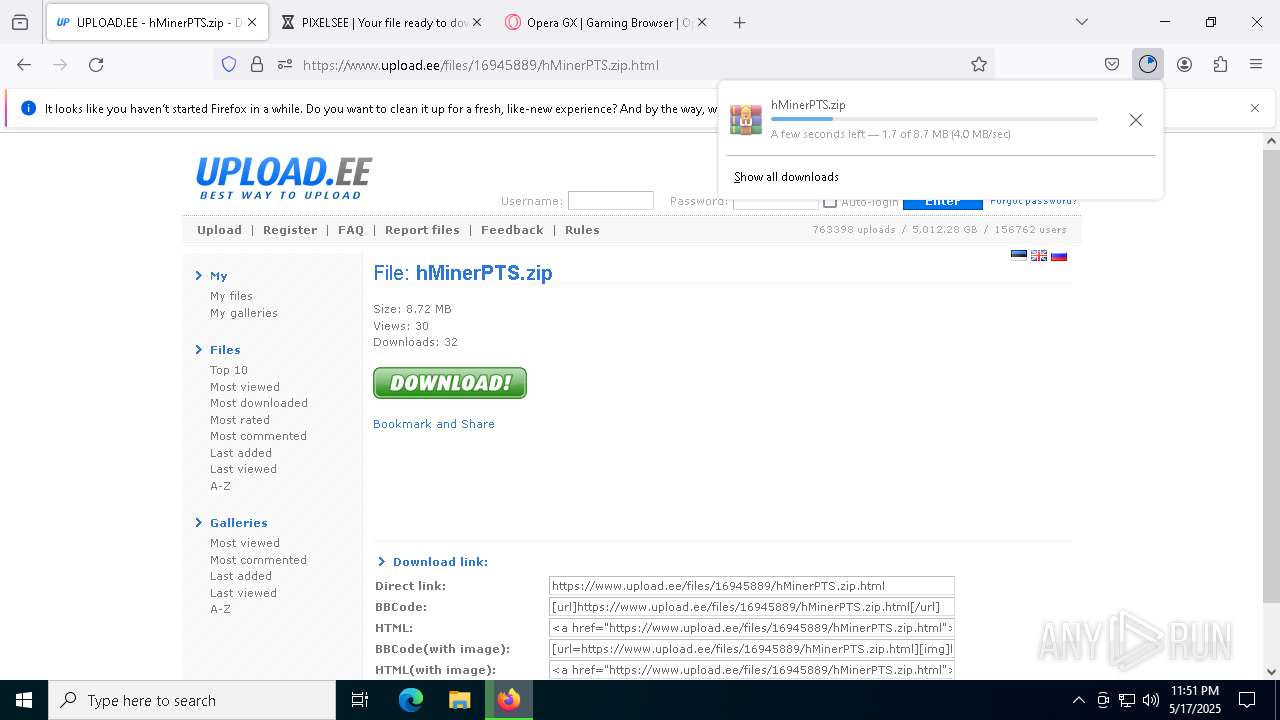
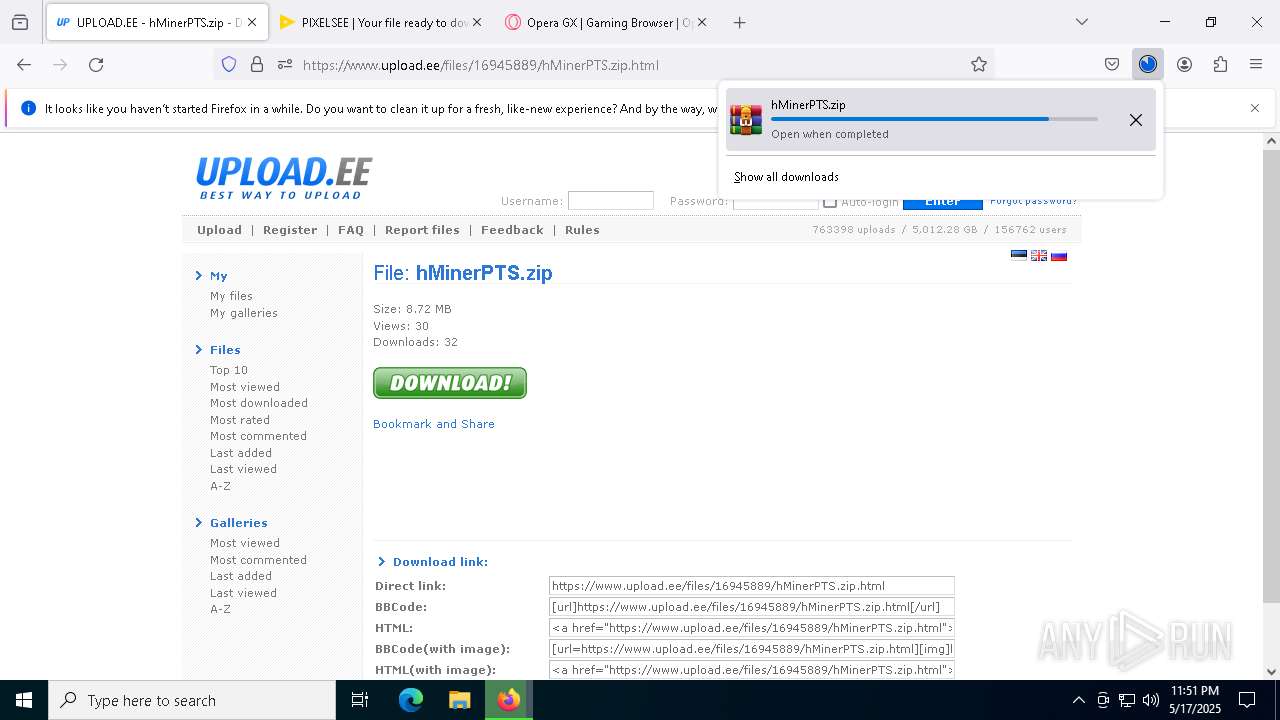
| URL: | https://www.upload.ee/files/16945889/hMinerPTS.zip.html |
| Full analysis: | https://app.any.run/tasks/426a8464-c202-41f9-9509-4a6450d949c2 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | May 17, 2025, 23:50:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8545A8738C43292ABA070E11B8A97F8F |
| SHA1: | 313B549D8463C1BAD4B9D859CEDB1FB3692D9039 |
| SHA256: | E09A7647B1787BB6B0B846396A165C4E56EC2A70656A3A266BB0E861540ED8AA |
| SSDEEP: | 3:N8DSLr7MJmUEItGscLQn:2OLr04I8LQn |
MALICIOUS
Executing a file with an untrusted certificate
- crack.exe (PID: 8384)
- crack.exe (PID: 1132)
- crack.exe (PID: 8692)
- crack.exe (PID: 9044)
Create files in the Startup directory
- Payload.exe (PID: 8524)
BlankGrabber has been detected
- crack.exe (PID: 8384)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7612)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3008)
- crack.exe (PID: 9044)
- cmd.exe (PID: 1812)
Changes Windows Defender settings
- cmd.exe (PID: 3008)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 1812)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7244)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7244)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7244)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7244)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7244)
Changes settings for real-time protection
- powershell.exe (PID: 7244)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6816)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7244)
Bypass execution policy to execute commands
- powershell.exe (PID: 8300)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 1452)
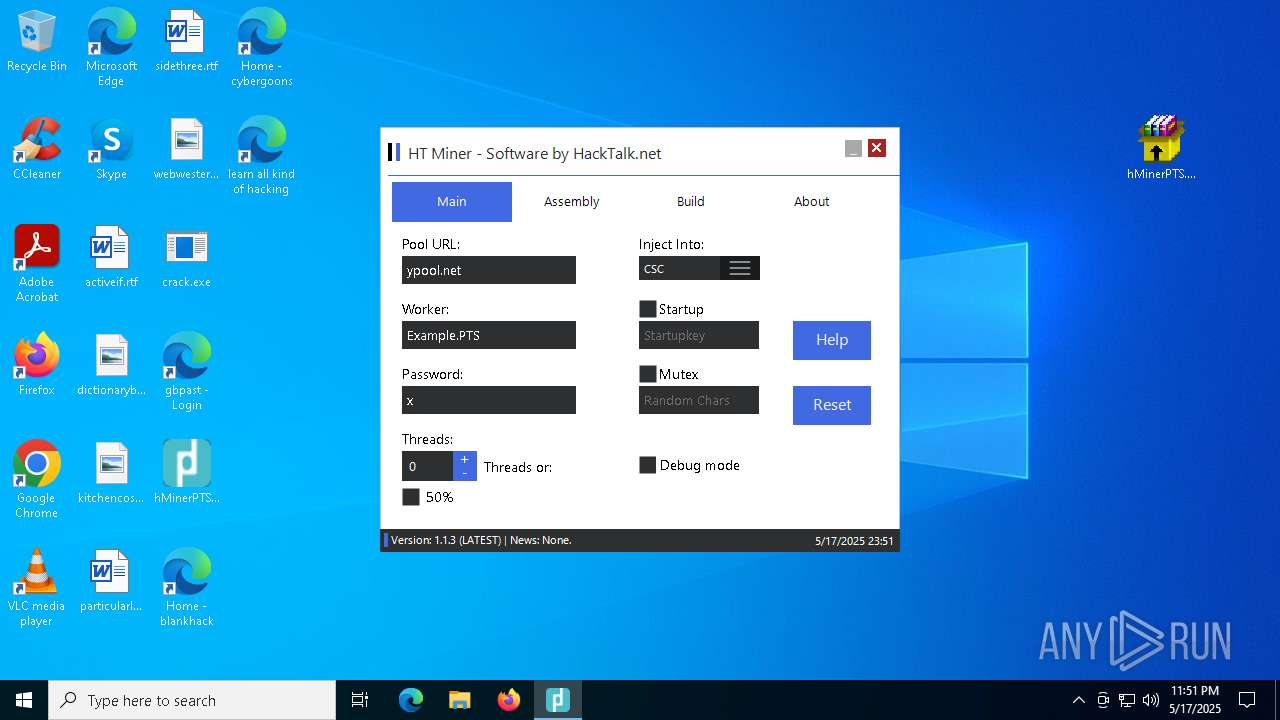
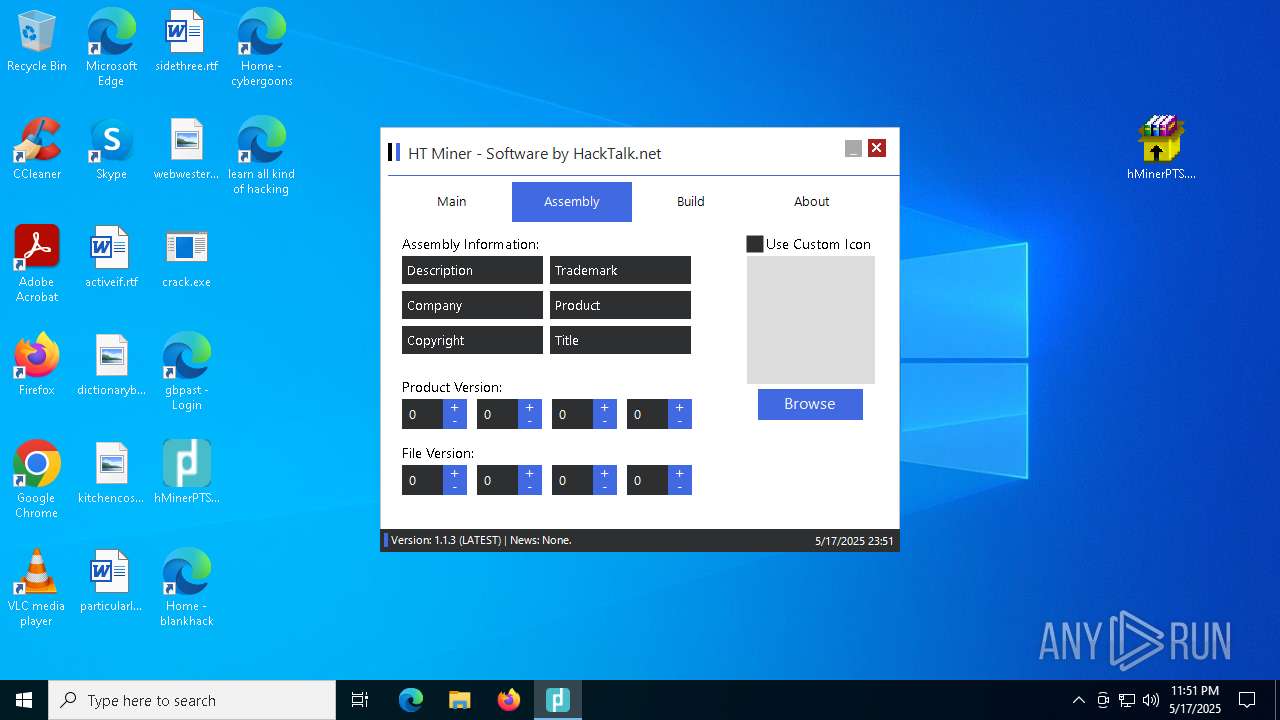
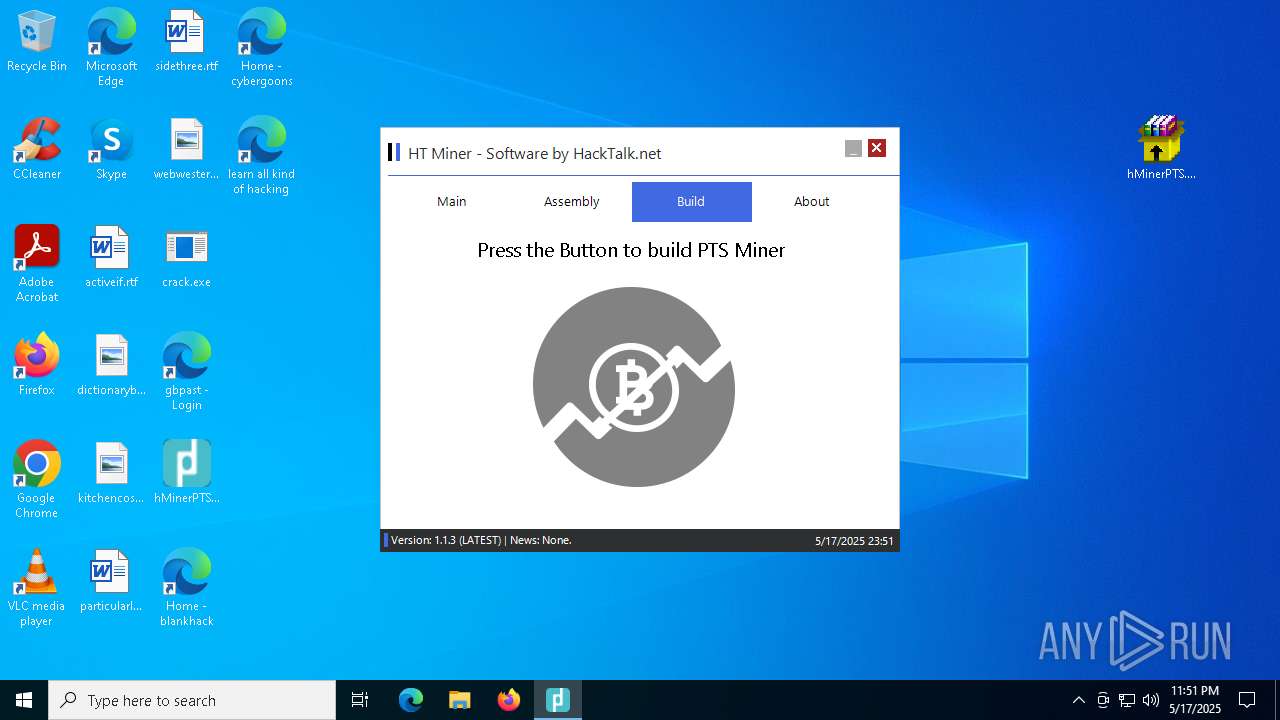
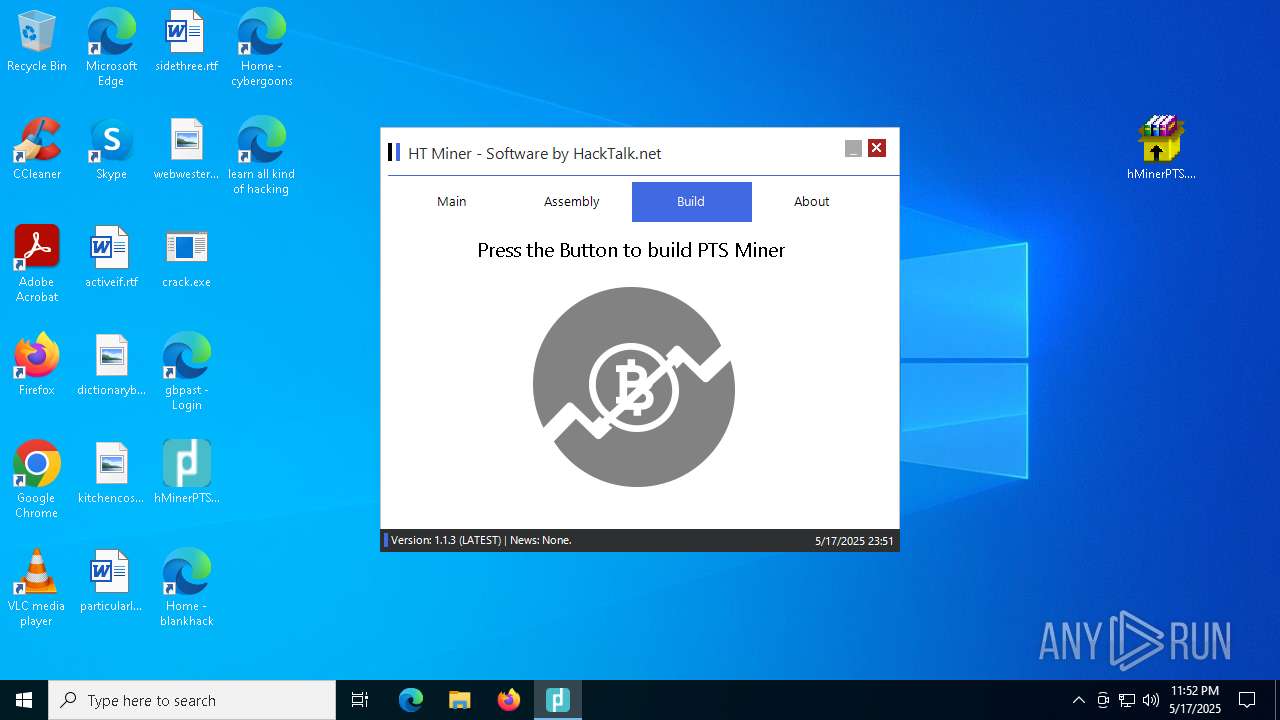
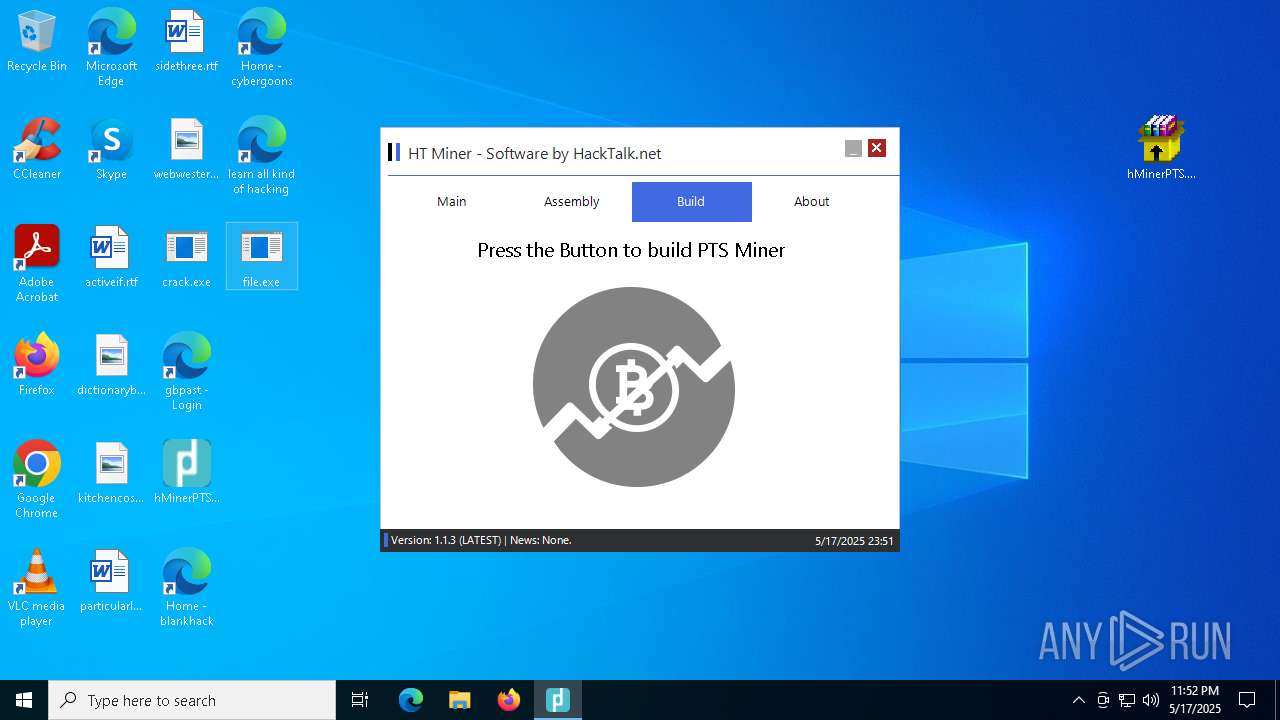
Starts Visual C# compiler
- file.exe (PID: 2240)
BLANKGRABBER has been detected (SURICATA)
- crack.exe (PID: 9044)
SUSPICIOUS
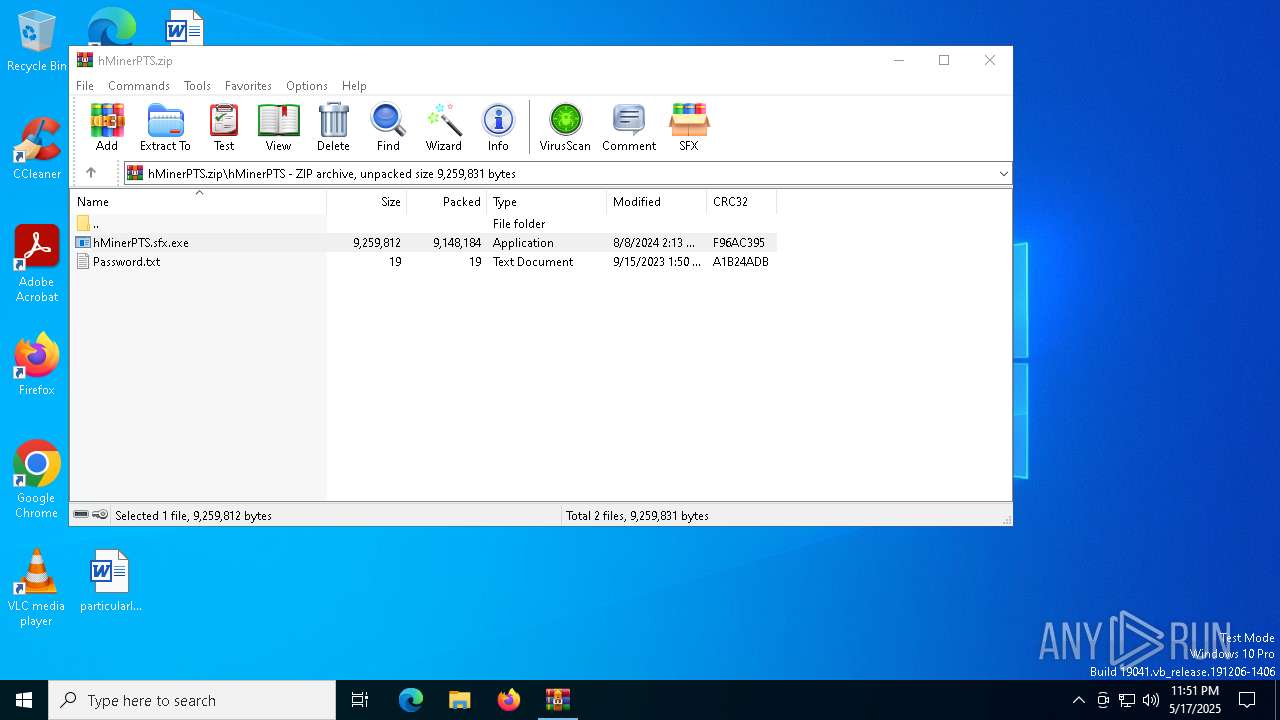
Reads security settings of Internet Explorer
- hMinerPTS.sfx.exe (PID: 3896)
- crack.exe (PID: 8220)
- crack.exe (PID: 1132)
Reads Microsoft Outlook installation path
- hMinerPTS.sfx.exe (PID: 3896)
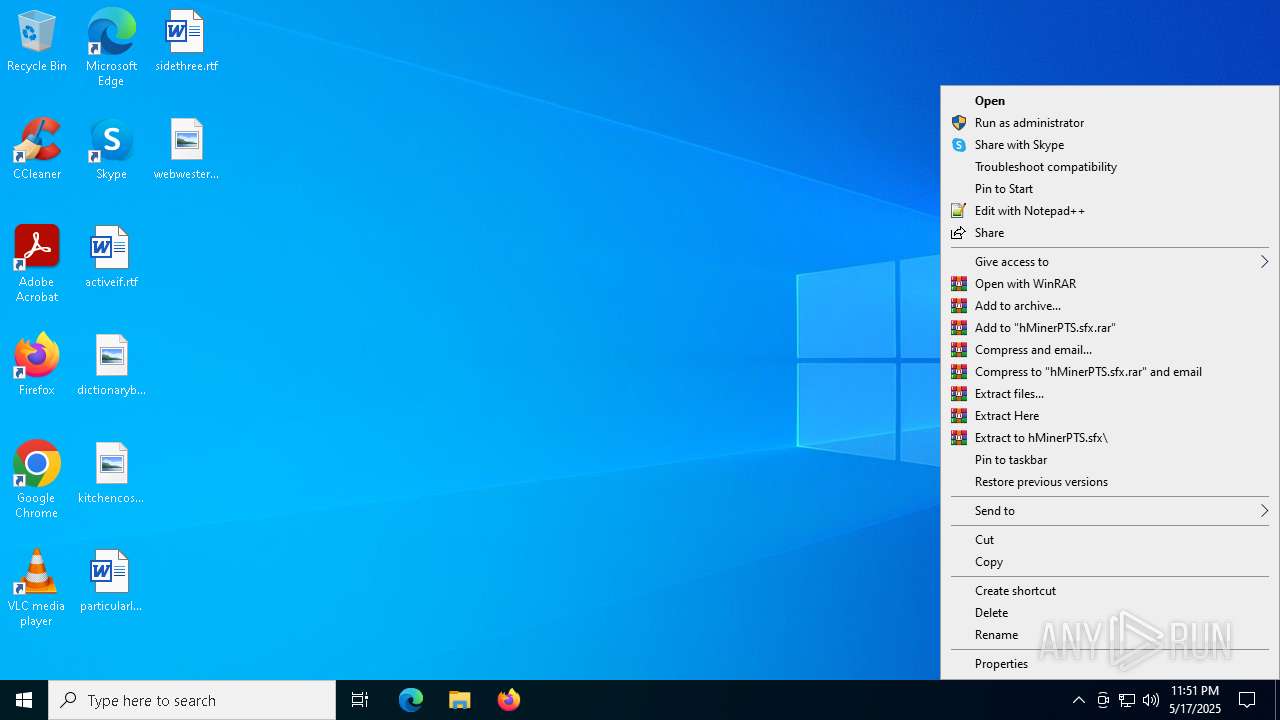
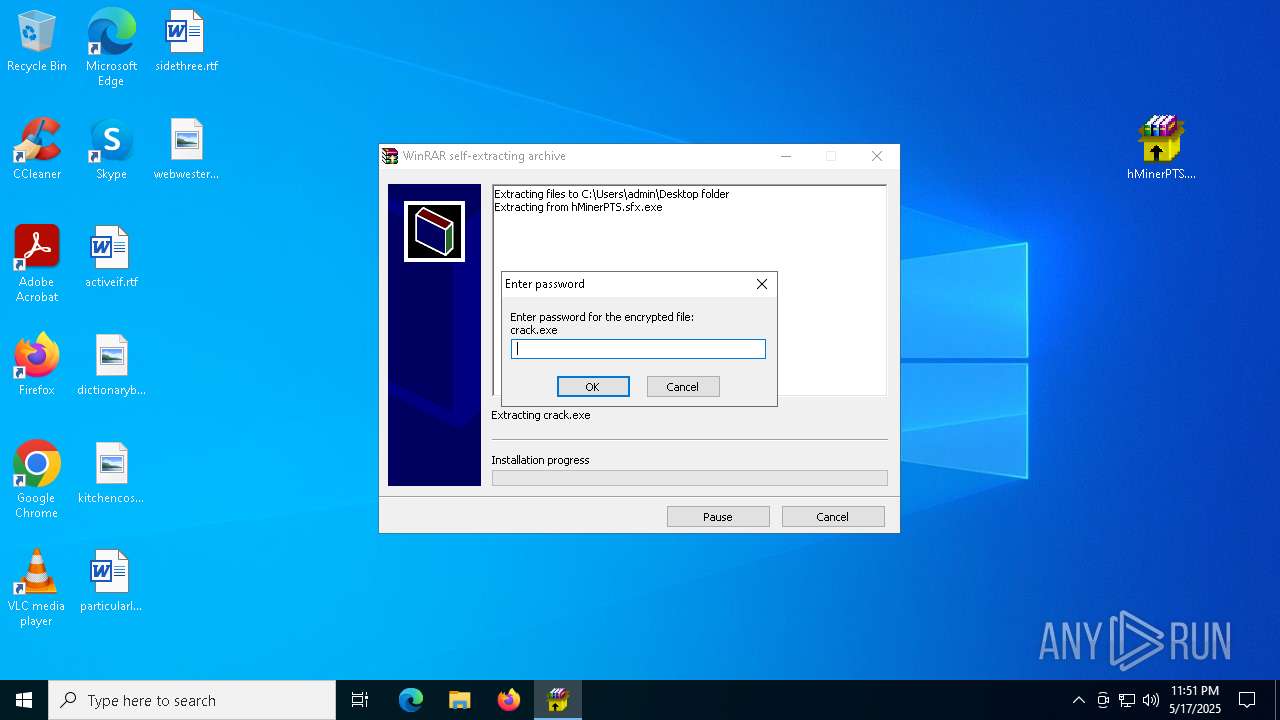
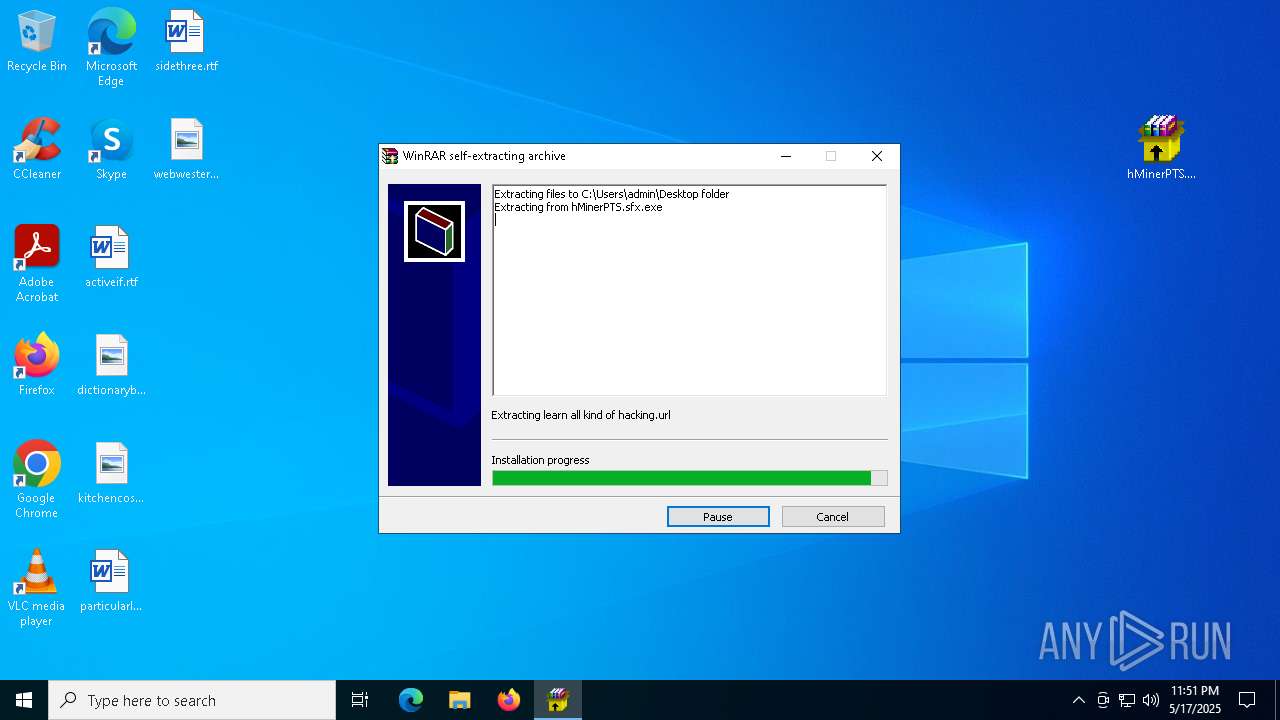
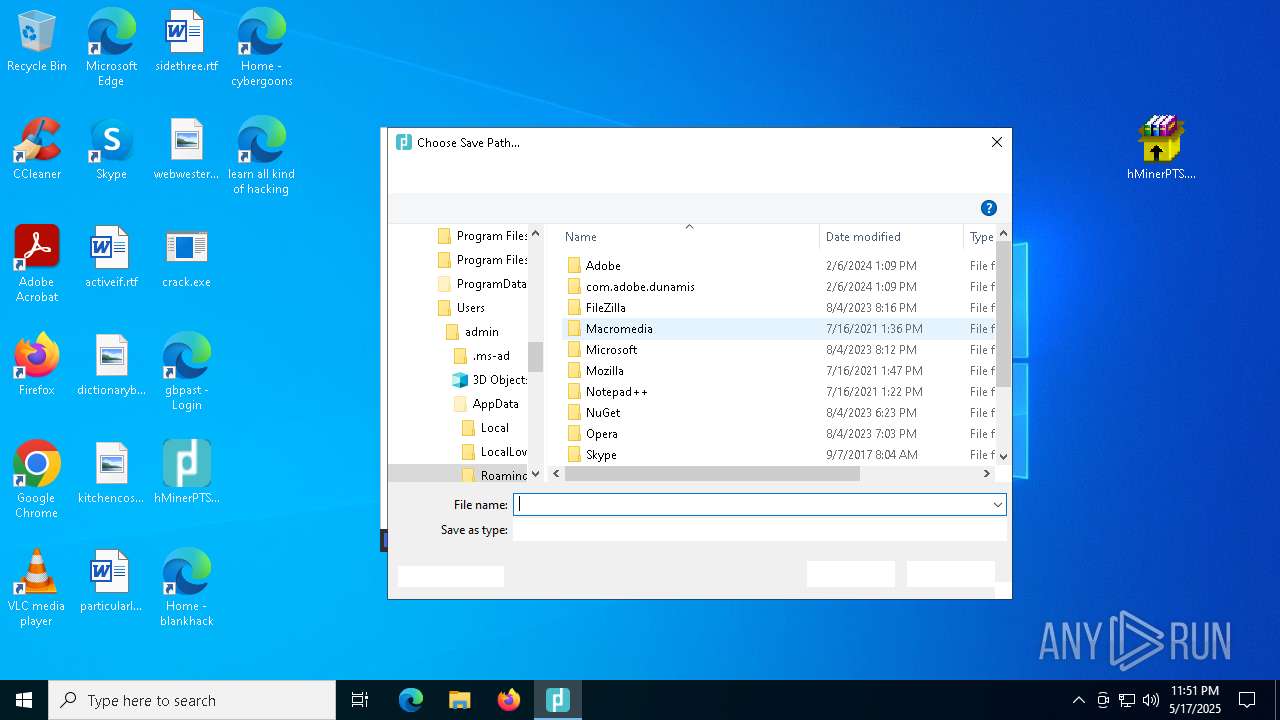
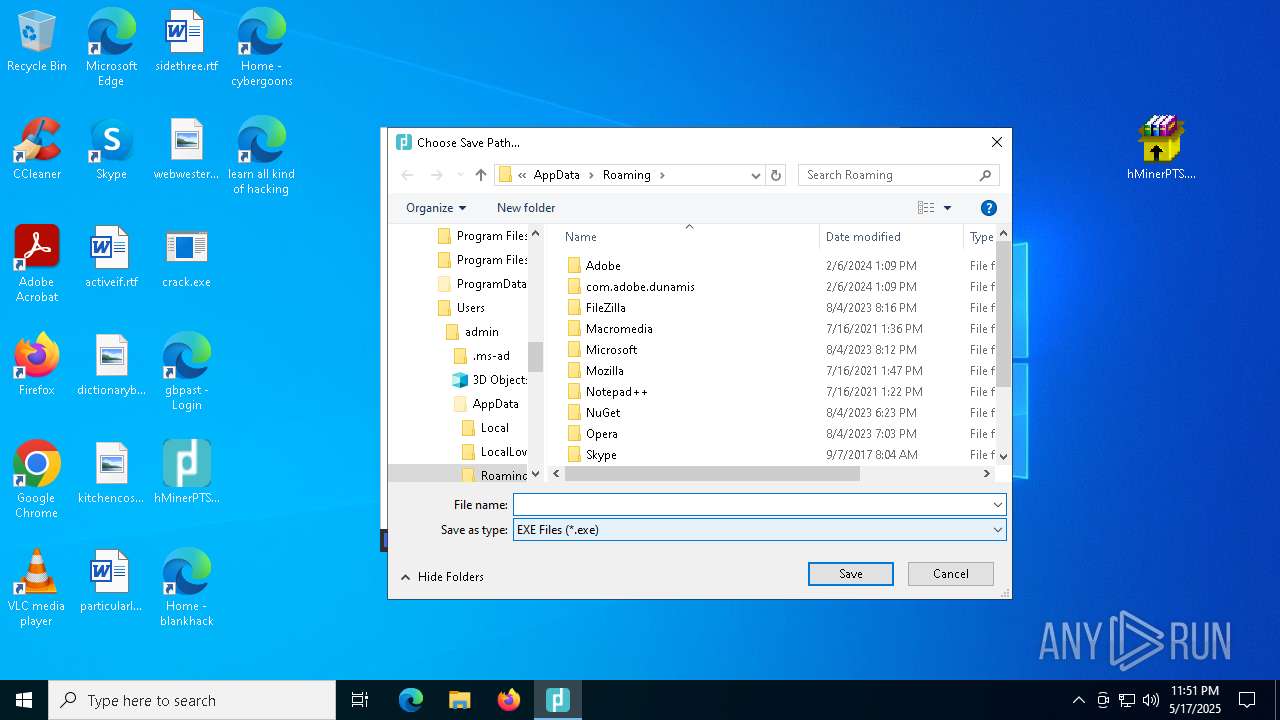
Executable content was dropped or overwritten
- hMinerPTS.sfx.exe (PID: 3896)
- crack.exe (PID: 8220)
- Payload.exe (PID: 8524)
- crack.exe (PID: 8384)
- crack.exe (PID: 8692)
- crack.exe (PID: 9044)
- hMinerPTS.exe (PID: 8648)
- csc.exe (PID: 6852)
- vbc.exe (PID: 7380)
Reads Internet Explorer settings
- hMinerPTS.sfx.exe (PID: 3896)
Starts POWERSHELL.EXE for commands execution
- crack.exe (PID: 8220)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 7252)
- cmd.exe (PID: 300)
- cmd.exe (PID: 6148)
BASE64 encoded PowerShell command has been detected
- crack.exe (PID: 8220)
- cmd.exe (PID: 6816)
Base64-obfuscated command line is found
- crack.exe (PID: 8220)
- cmd.exe (PID: 6816)
Starts a Microsoft application from unusual location
- crack.exe (PID: 8384)
- crack.exe (PID: 1132)
- crack.exe (PID: 8692)
- crack.exe (PID: 9044)
Process drops python dynamic module
- crack.exe (PID: 8384)
- crack.exe (PID: 8692)
Process drops legitimate windows executable
- crack.exe (PID: 8384)
- crack.exe (PID: 8220)
- crack.exe (PID: 8692)
- crack.exe (PID: 9044)
The process drops C-runtime libraries
- crack.exe (PID: 8384)
- crack.exe (PID: 8692)
Application launched itself
- crack.exe (PID: 8384)
- crack.exe (PID: 1132)
- crack.exe (PID: 8692)
Reads the date of Windows installation
- crack.exe (PID: 1132)
Found strings related to reading or modifying Windows Defender settings
- crack.exe (PID: 9044)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3008)
- cmd.exe (PID: 1812)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7612)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7612)
Starts CMD.EXE for commands execution
- crack.exe (PID: 9044)
Get information on the list of running processes
- cmd.exe (PID: 7780)
- crack.exe (PID: 9044)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 7332)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1184)
- cmd.exe (PID: 7468)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 8828)
Starts application with an unusual extension
- cmd.exe (PID: 8508)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 5868)
- cmd.exe (PID: 6108)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6816)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 8932)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 8884)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7260)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4112)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 5776)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6852)
Checks for external IP
- crack.exe (PID: 9044)
- svchost.exe (PID: 2196)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- crack.exe (PID: 9044)
The process executes VB scripts
- hMinerPTS.exe (PID: 8532)
INFO
Application launched itself
- firefox.exe (PID: 6668)
- firefox.exe (PID: 660)
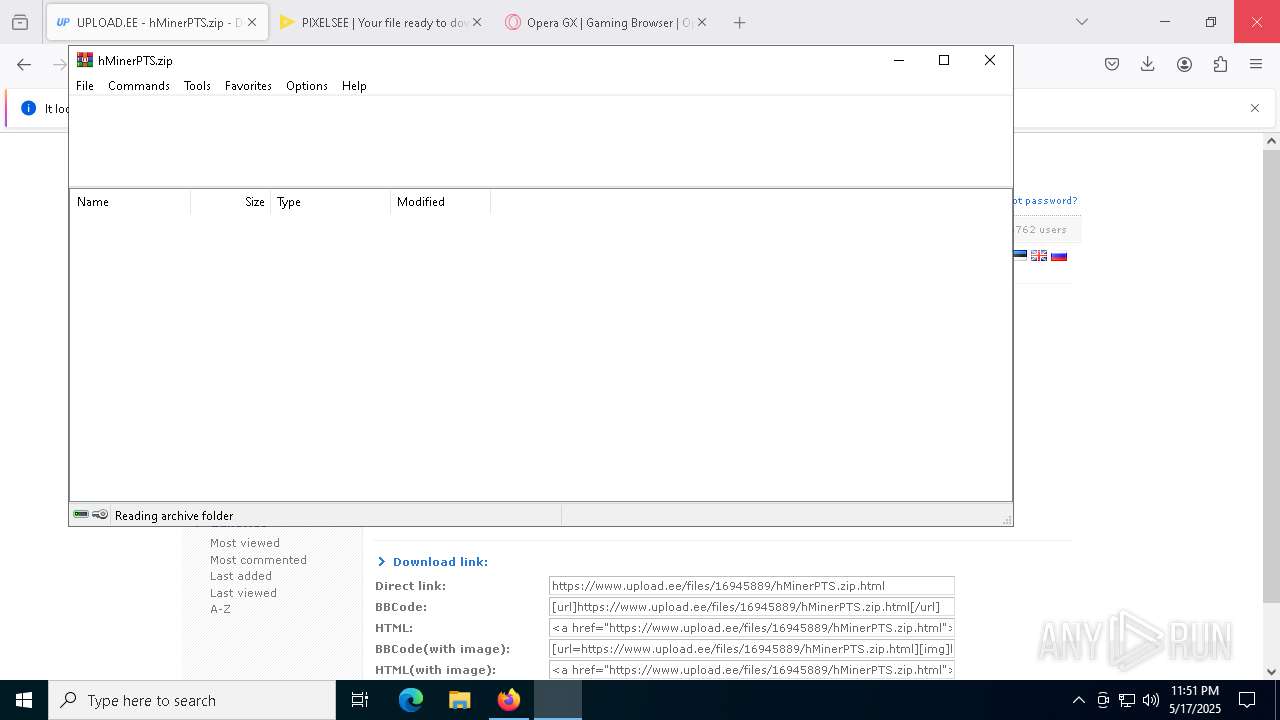
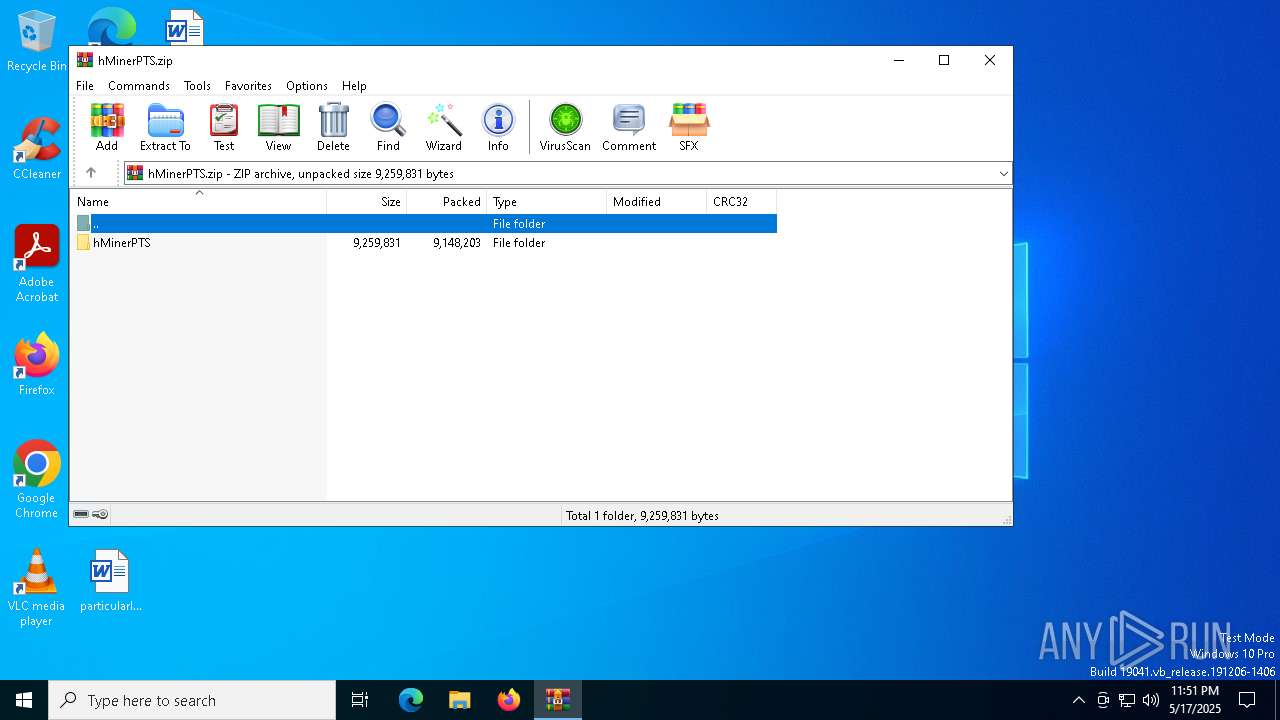
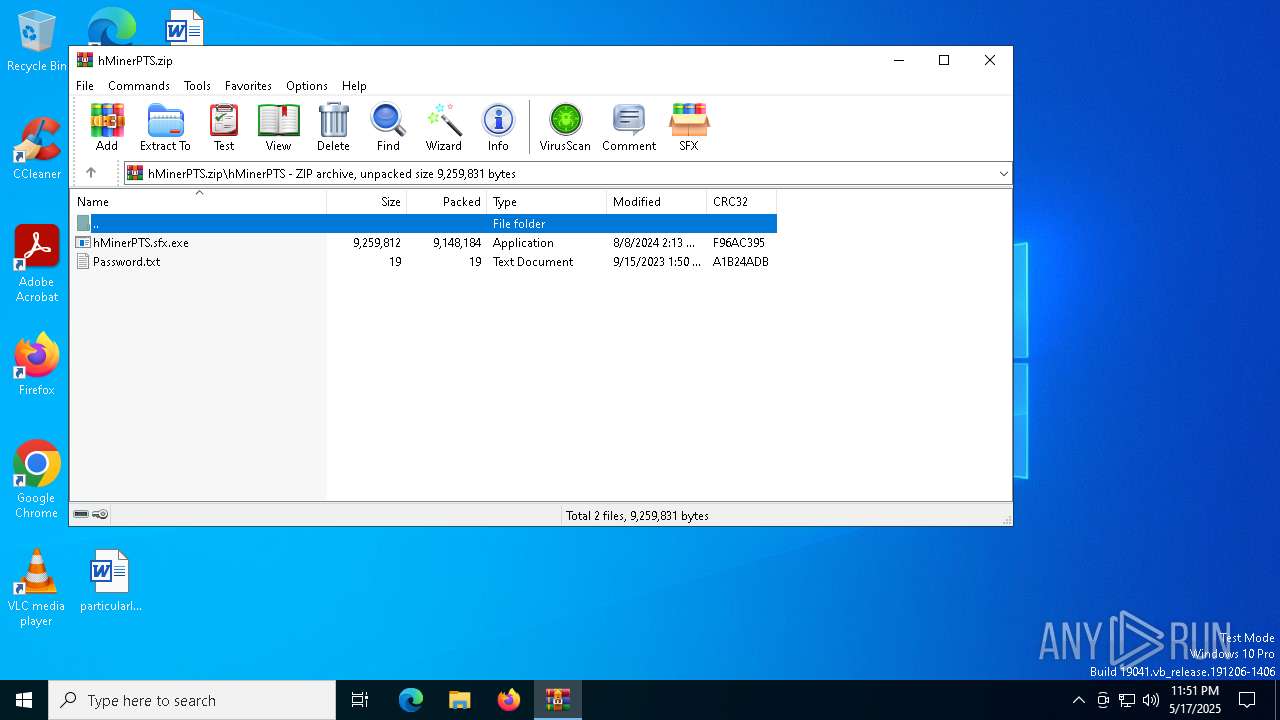
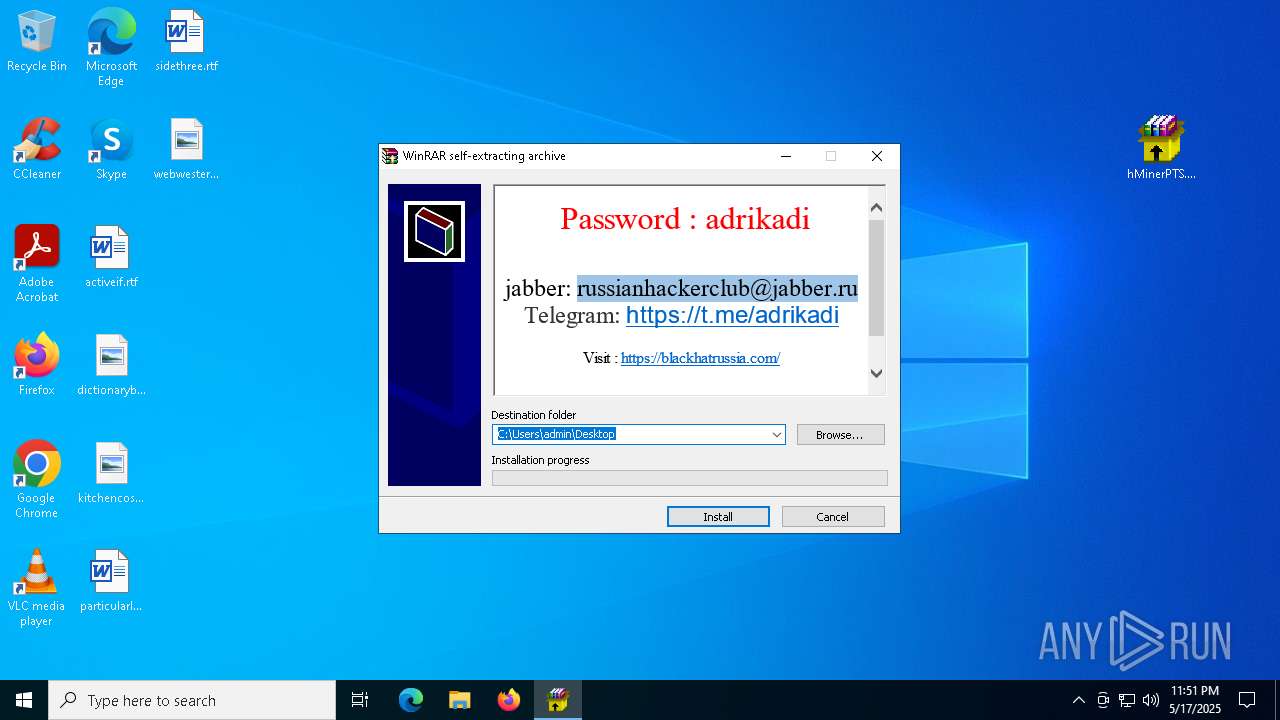
Manual execution by a user
- WinRAR.exe (PID: 1328)
- hMinerPTS.sfx.exe (PID: 3896)
- hMinerPTS.exe (PID: 8648)
- file.exe (PID: 2240)
Checks supported languages
- hMinerPTS.sfx.exe (PID: 3896)
- Payload.exe (PID: 8524)
- crack.exe (PID: 8220)
- crack.exe (PID: 8384)
- crack.exe (PID: 1132)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1328)
Checks proxy server information
- hMinerPTS.sfx.exe (PID: 3896)
Reads the computer name
- hMinerPTS.sfx.exe (PID: 3896)
- crack.exe (PID: 8220)
- Payload.exe (PID: 8524)
- crack.exe (PID: 8384)
- crack.exe (PID: 1132)
Process checks computer location settings
- hMinerPTS.sfx.exe (PID: 3896)
- crack.exe (PID: 8220)
- crack.exe (PID: 1132)
Create files in a temporary directory
- crack.exe (PID: 8220)
- crack.exe (PID: 8384)
- crack.exe (PID: 1132)
The sample compiled with english language support
- crack.exe (PID: 8220)
- crack.exe (PID: 8384)
- crack.exe (PID: 8692)
- crack.exe (PID: 9044)
Creates files or folders in the user directory
- Payload.exe (PID: 8524)
Reads the machine GUID from the registry
- Payload.exe (PID: 8524)
The Powershell gets current clipboard
- powershell.exe (PID: 7252)
Checks the directory tree
- tree.com (PID: 8304)
- tree.com (PID: 8884)
- tree.com (PID: 7436)
- tree.com (PID: 8904)
- tree.com (PID: 2136)
- tree.com (PID: 924)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- powershell.exe (PID: 8584)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 9048)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
262
Monitored processes
127
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY" | C:\Windows\System32\cmd.exe | — | crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://www.upload.ee/files/16945889/hMinerPTS.zip.html" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Temp\BtcStealer.exe" | C:\Users\admin\AppData\Local\Temp\BtcStealer.exe | — | hMinerPTS.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp2 Version: 1.0.0.0 Modules
| |||||||||||||||
| 920 | powershell Get-ItemPropertyValue -Path HKLM:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | tree /A /F | C:\Windows\System32\tree.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tree Walk Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5792 -childID 12 -isForBrowser -prefsHandle 5860 -prefMapHandle 6140 -prefsLen 31324 -prefMapSize 244583 -jsInitHandle 1200 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {04a48f60-a94f-48ab-9f81-1cecc6fb29a6} 6668 "\\.\pipe\gecko-crash-server-pipe.6668" 12c7664f850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Local\Temp\crack.exe" | C:\Users\admin\AppData\Local\Temp\crack.exe | — | crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MDMAgent Exit code: 0 Version: 10.0.22621.2506 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\WINDOWS\system32\cmd.exe /c "WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntivirusProduct Get displayName" | C:\Windows\System32\cmd.exe | — | crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | powershell Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2544 -childID 13 -isForBrowser -prefsHandle 764 -prefMapHandle 4040 -prefsLen 31324 -prefMapSize 244583 -jsInitHandle 1200 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7d63c2ae-9af1-489f-a0c6-d706d418af94} 6668 "\\.\pipe\gecko-crash-server-pipe.6668" 12c73113150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
84 404
Read events
84 303
Write events
97
Delete events
4
Modification events
| (PID) Process: | (6668) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\hMinerPTS.zip | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
125
Suspicious files
257
Text files
72
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:4006DDC2918B16C7EF5516C58373842B | SHA256:269EA23B77EDE0874628BD8611BCC5A3E87E0C44CA8A821C0D028B929D4F468F | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:CF89BF2D8A5104F008782353E042AA8D | SHA256:7203A54525BCD07566B1144DEA5C1ABFC9307871CCCD6961B9BB6A293783C9DB | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:7E6C85D29901961776E0815669CED7CD | SHA256:34978BD78DFC69A65C7920FB7D455EB13BFFB8C50574EB7421FDEF6EFD17F8BB | |||
| 6668 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:CB715D9CD550A89A5D405D80F9FE5DA8 | SHA256:59C22F0DC324C3BB01B1CE0B335160D54F187C108819A9D0923C6B3C9BEBF1A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
191
DNS requests
234
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6668 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6668 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6668 | firefox.exe | POST | 200 | 2.17.190.73:80 | http://status.rapidssl.com/ | unknown | — | — | whitelisted |
6668 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6668 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6668 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
6668 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6668 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4244 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6668 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
6668 | firefox.exe | 57.129.39.102:443 | www.upload.ee | — | FR | whitelisted |
6668 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6668 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.upload.ee |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2196 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
9044 | crack.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
9044 | crack.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |
9044 | crack.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |