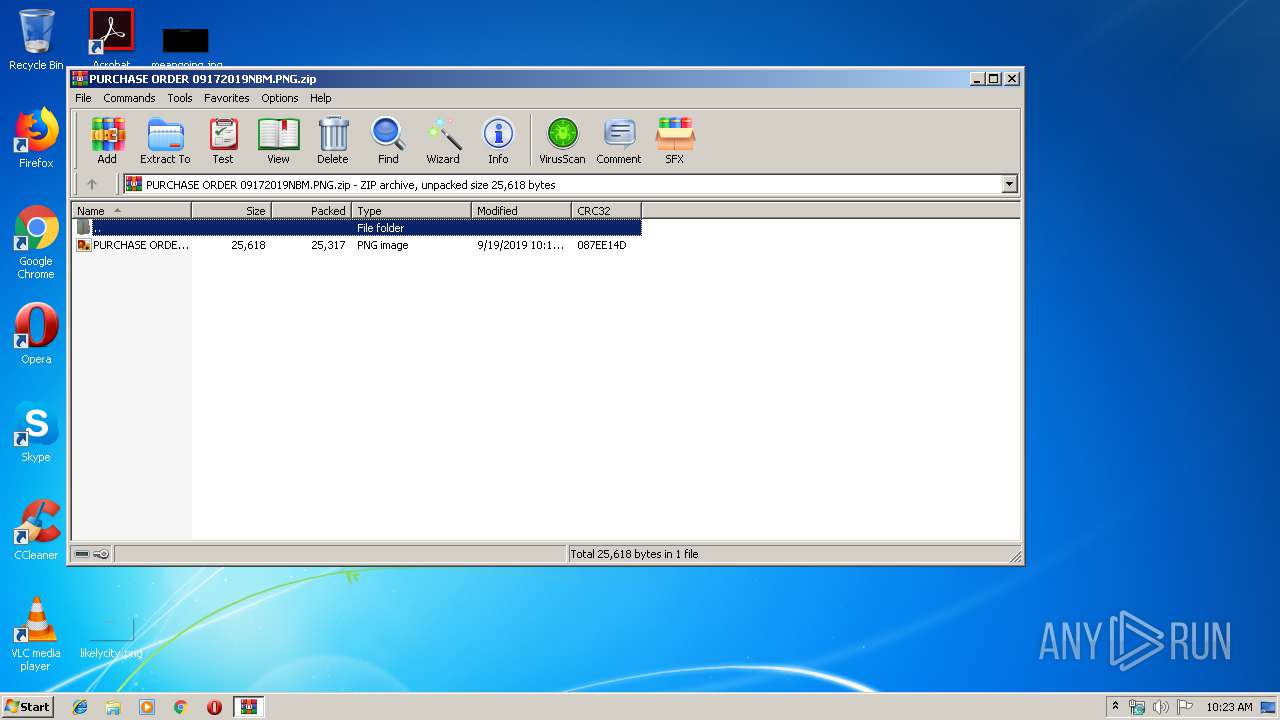
| File name: | PURCHASE ORDER 09172019NBM.PNG.zip |
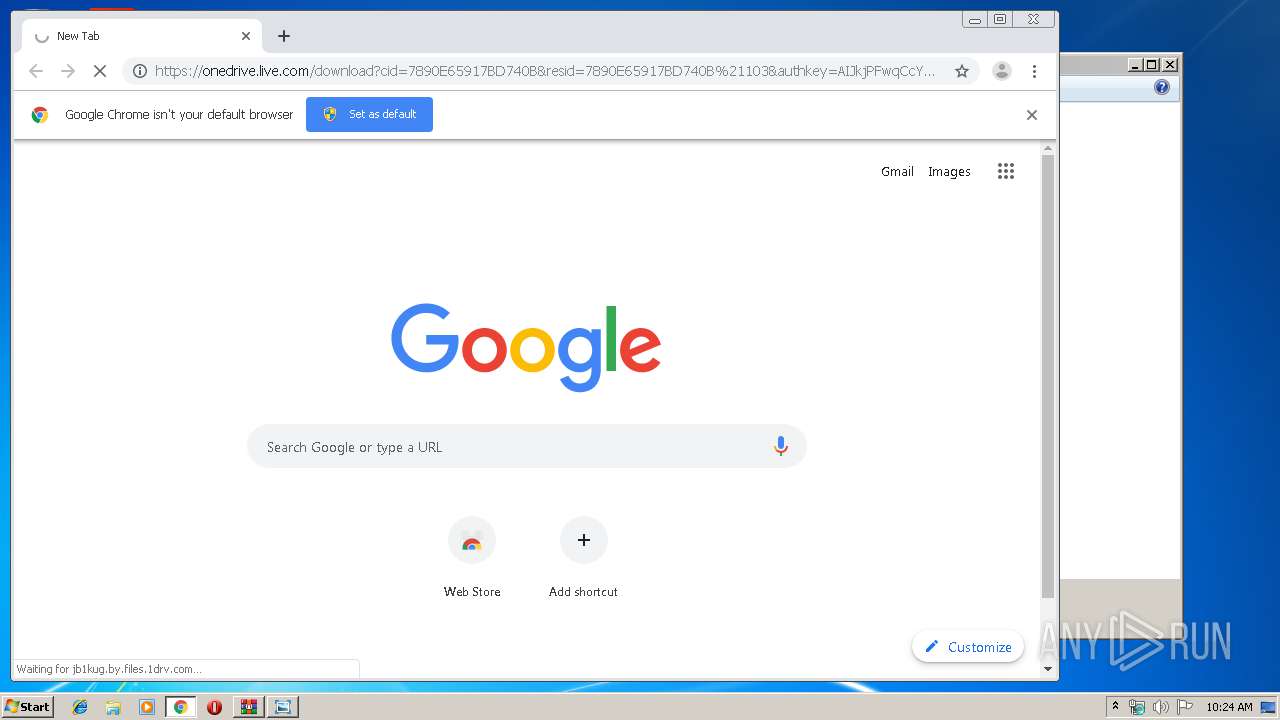
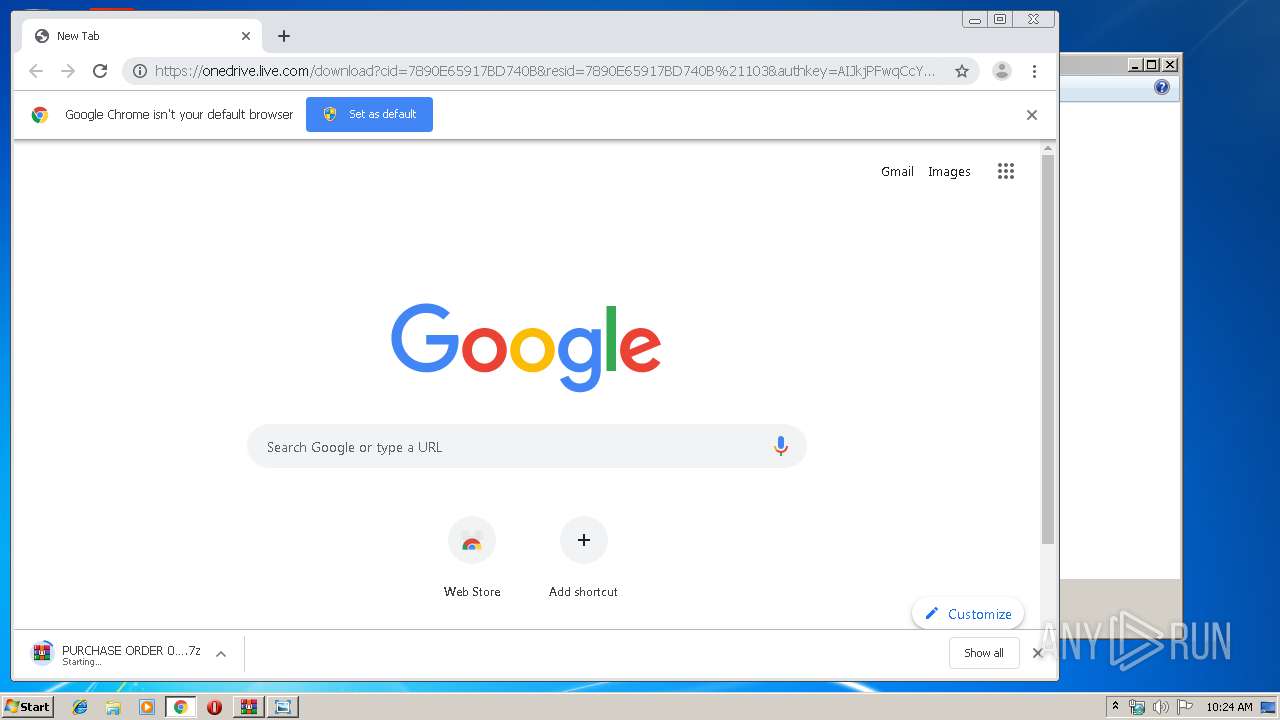
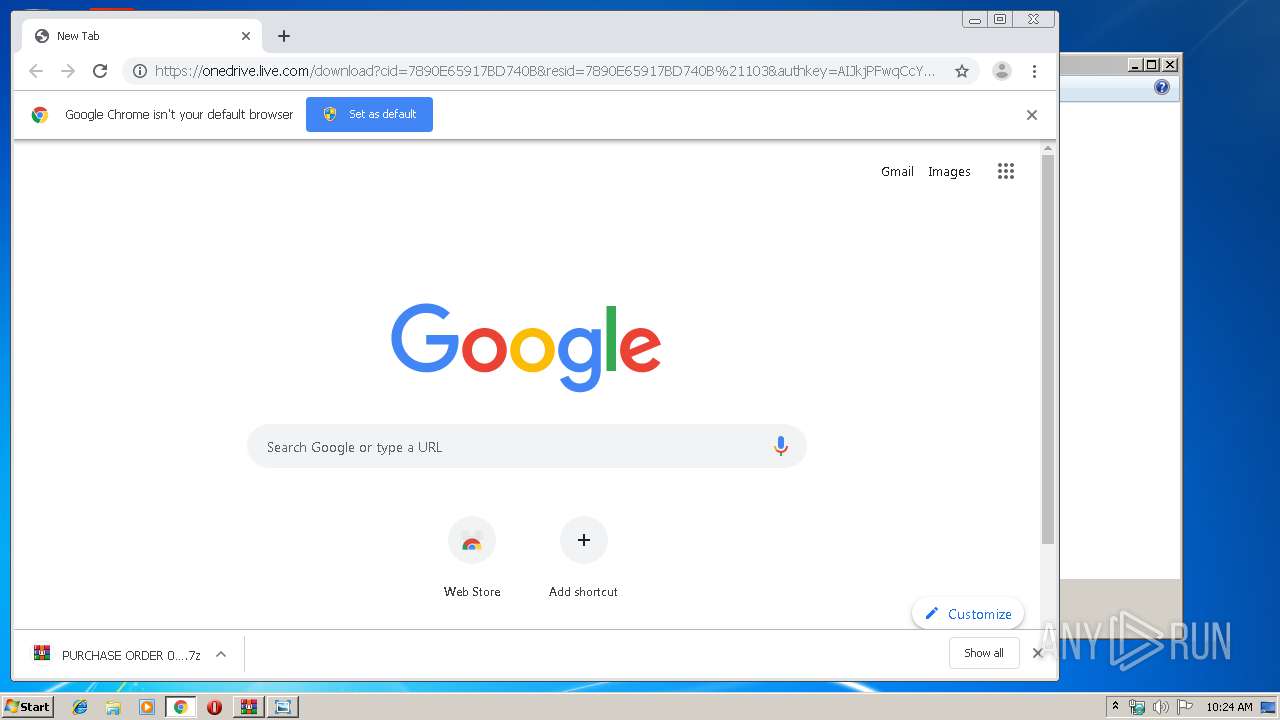
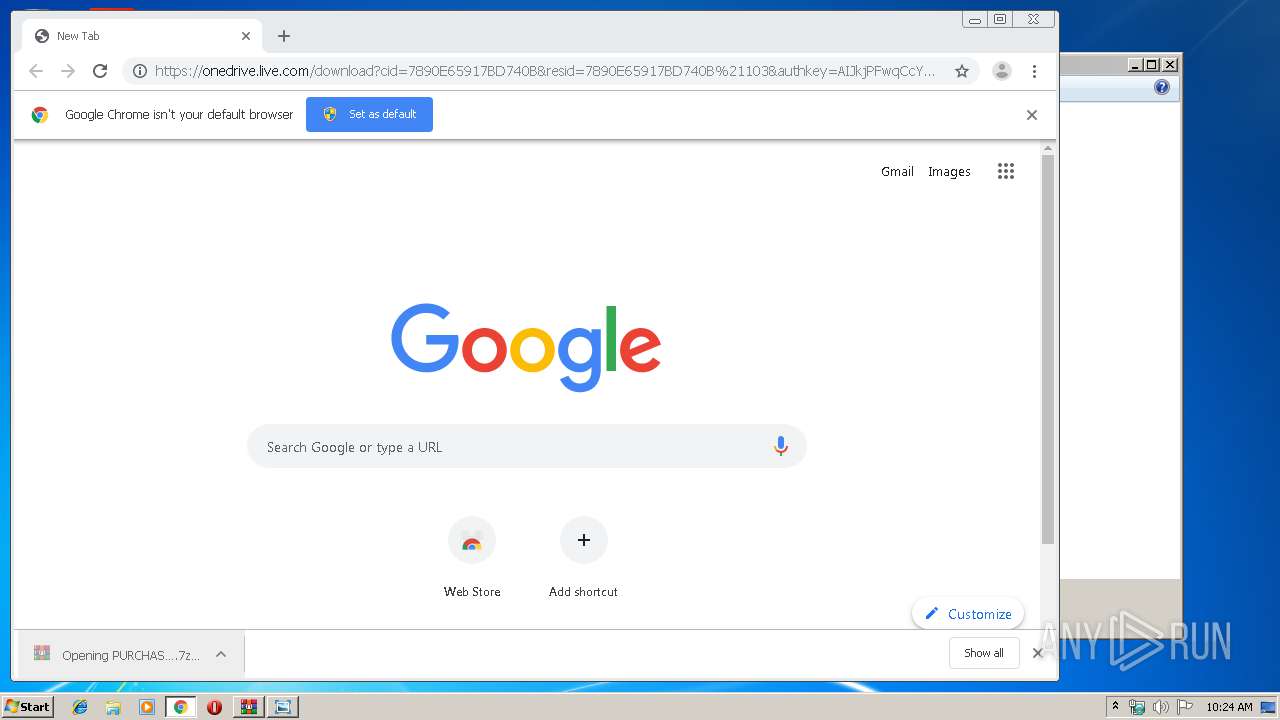
| Full analysis: | https://app.any.run/tasks/c53894ad-858c-4c2e-8af1-f9817a395a3a |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 19, 2019, 09:23:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E0DC172E9F60C8833DED74E6A87BEFB0 |
| SHA1: | 34331962C509274377483A0E241FD620136B6363 |
| SHA256: | E0355A9243AF49341100B38935D9FF4E7EEE63762A63175DDF2B46C1CC4BE4A8 |
| SSDEEP: | 768:UCZkiJAZG0DVT4q5z1lhHLHA8KKCBqz8C+dZ:5ZjIG4TxBZrg8KVBEj+b |
MALICIOUS
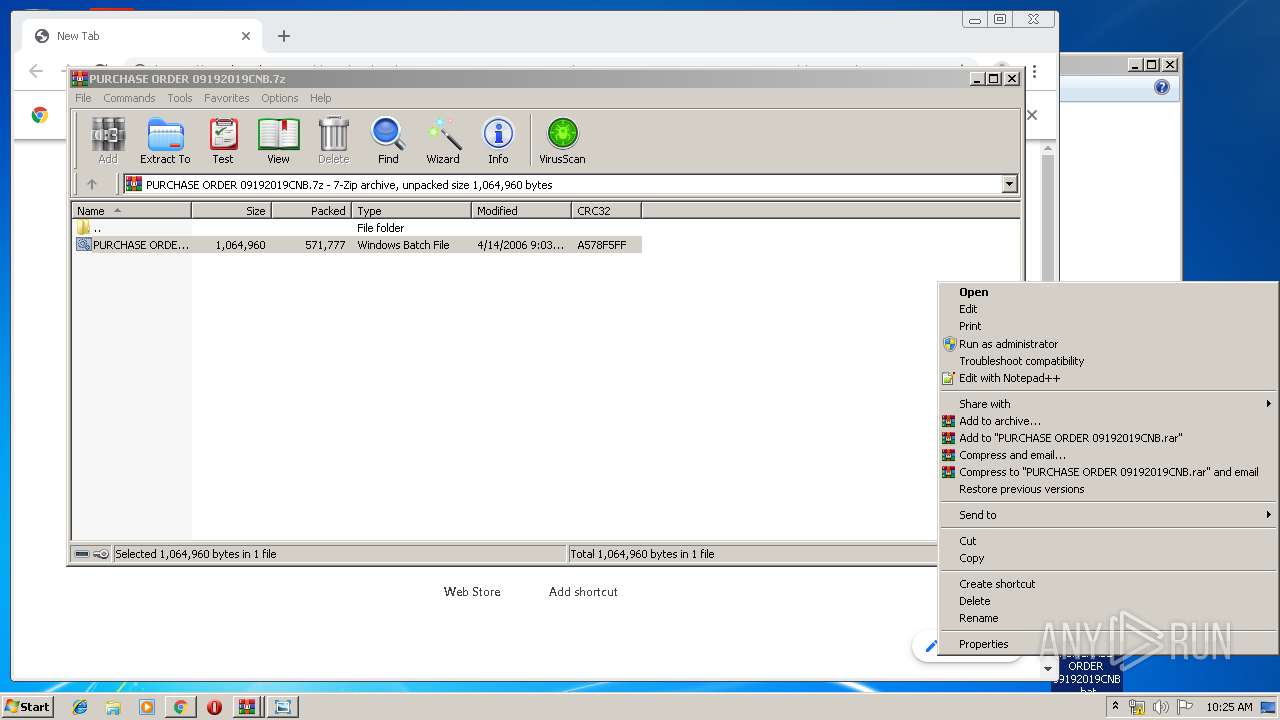
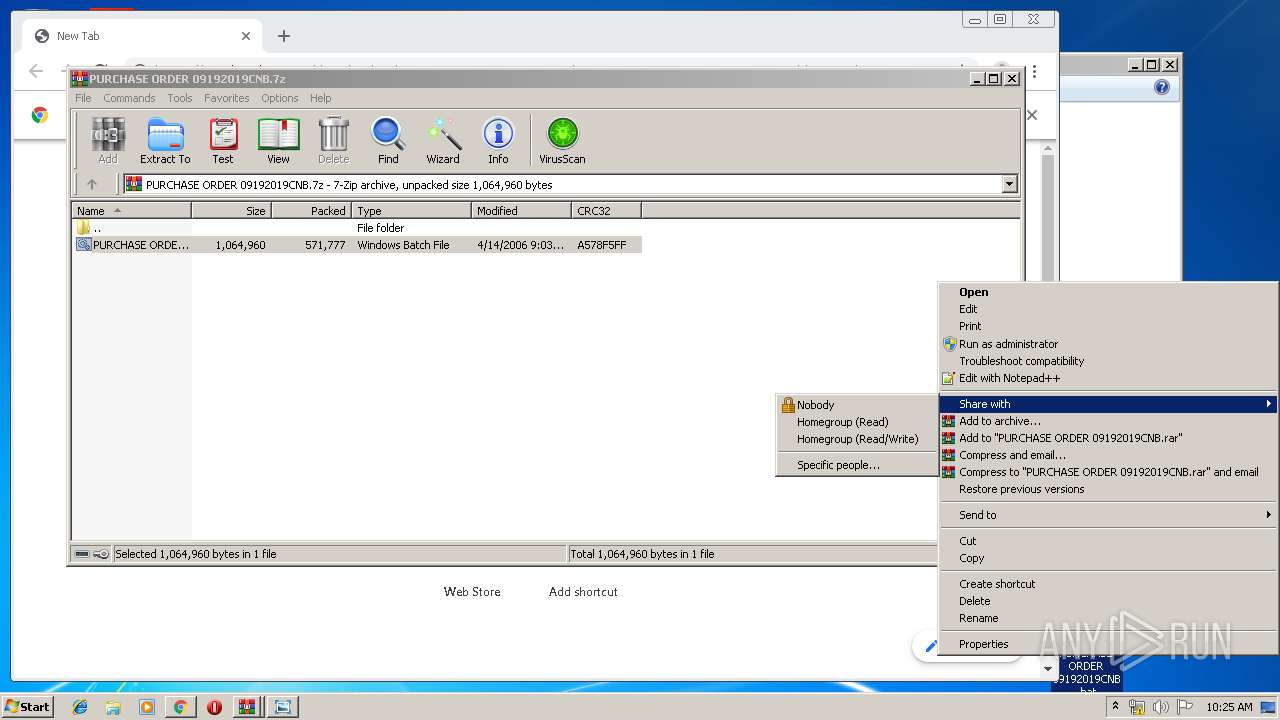
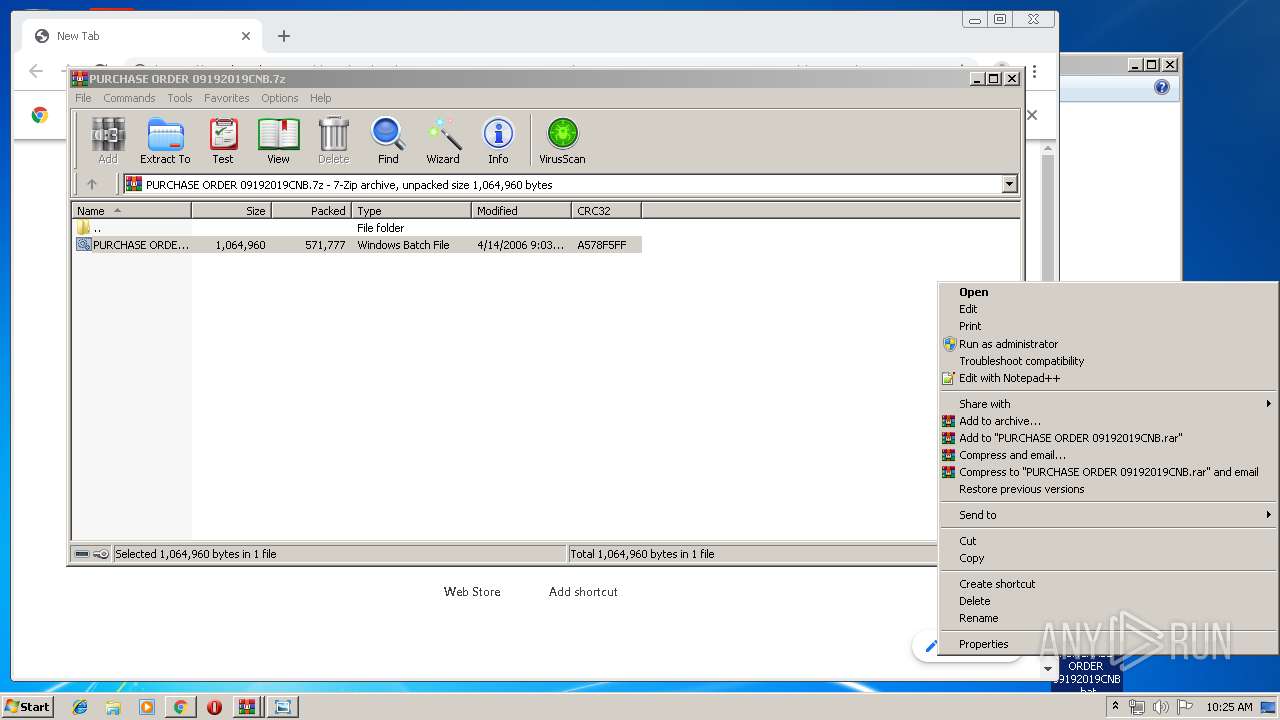
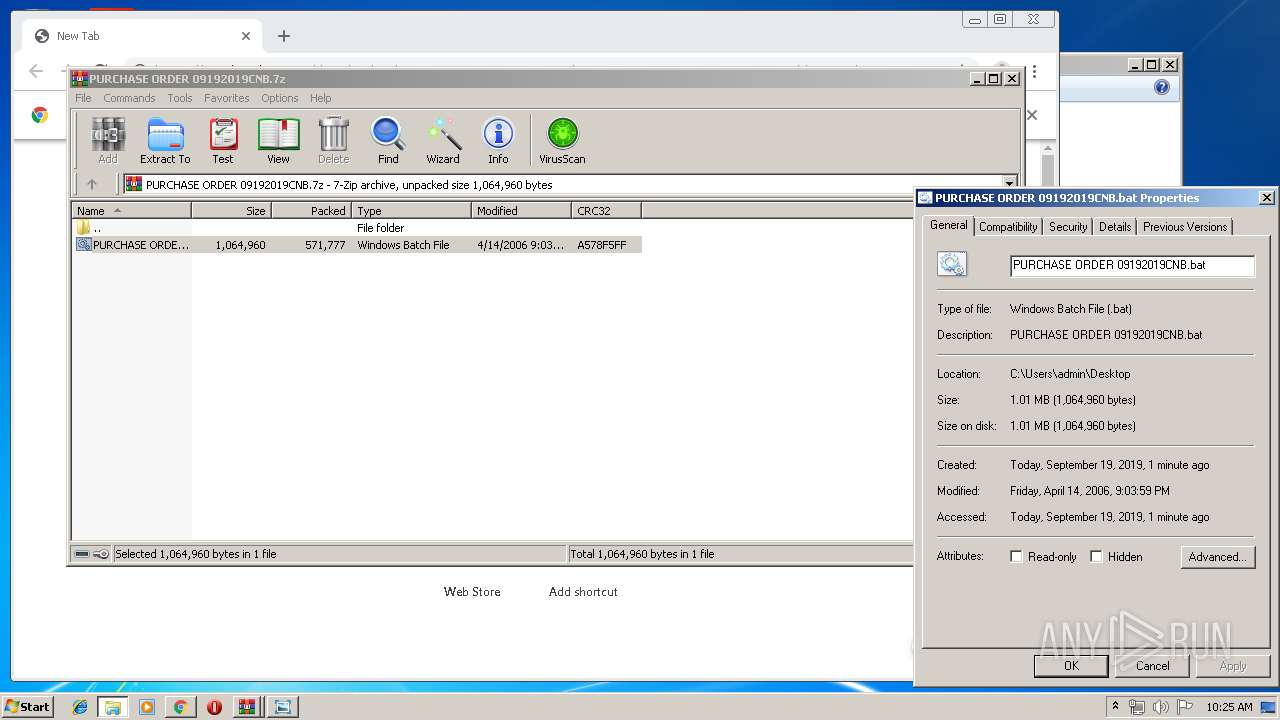
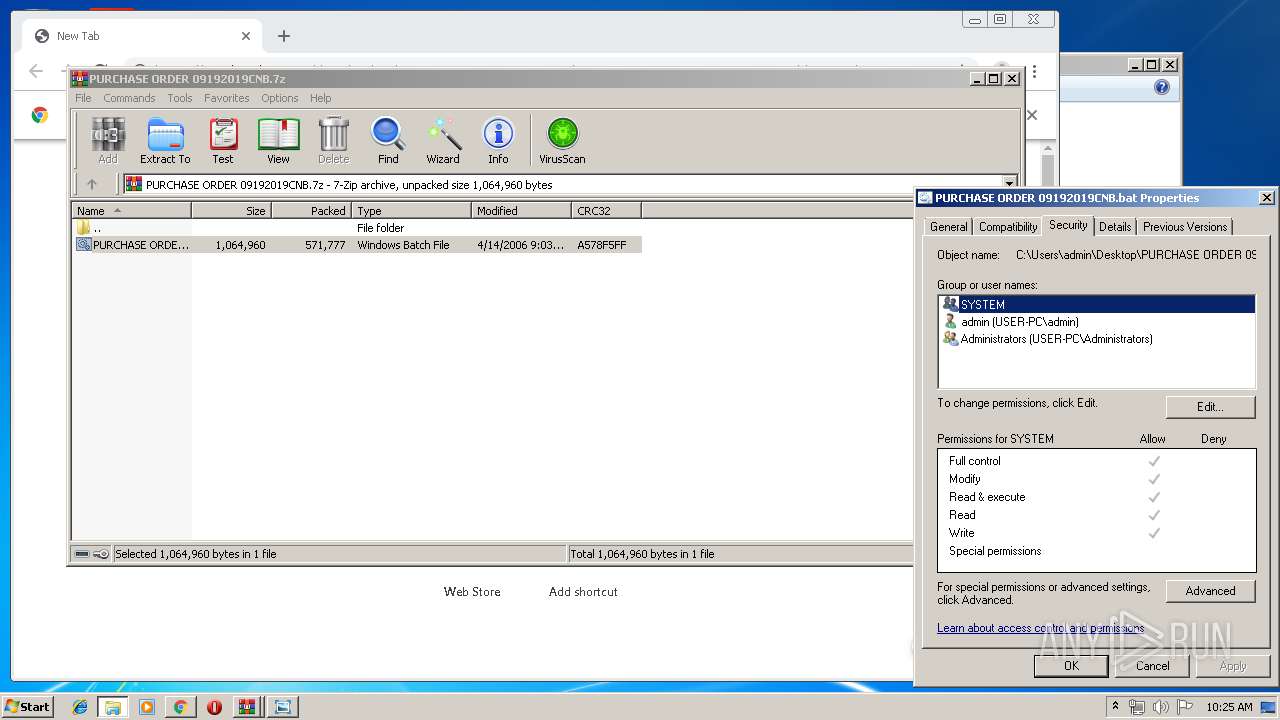
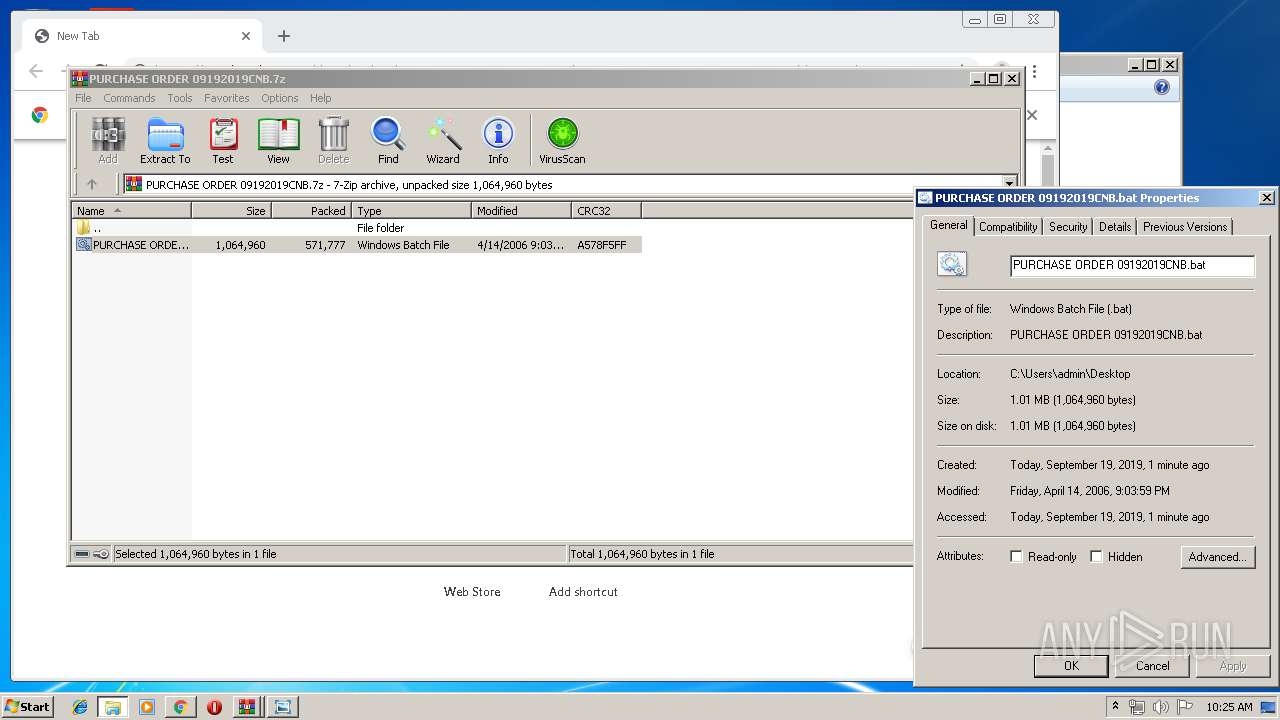
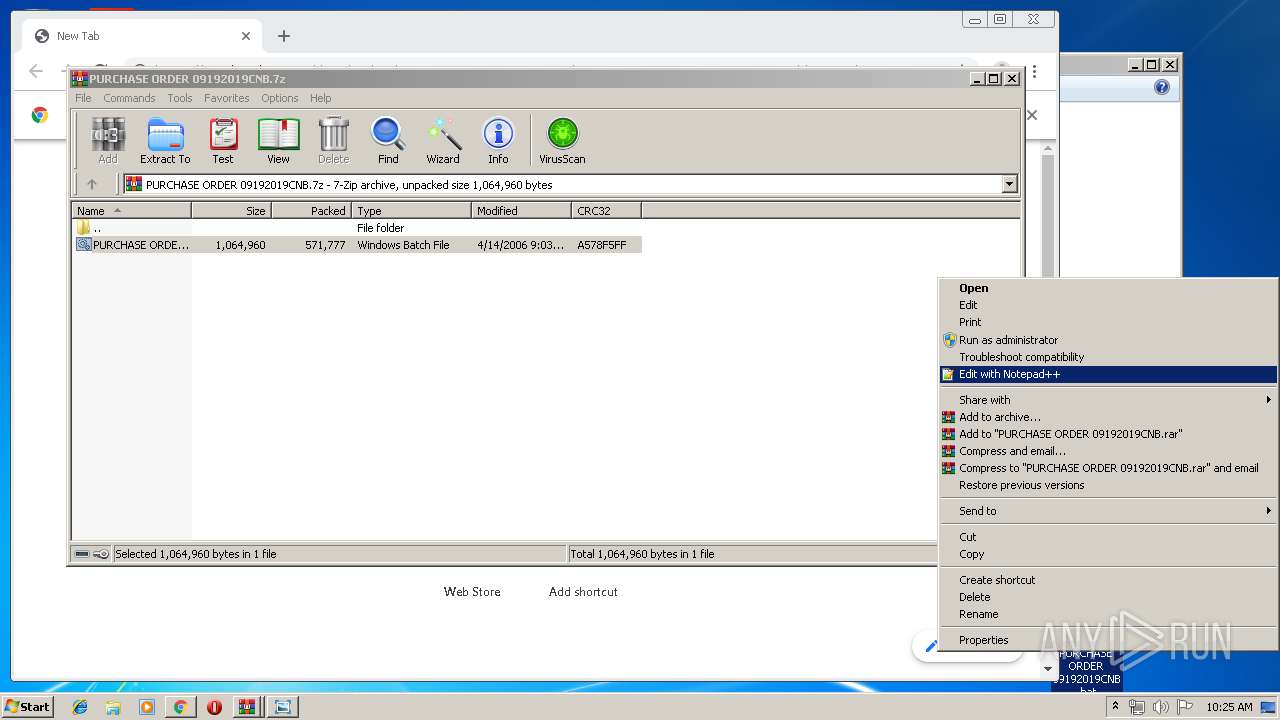
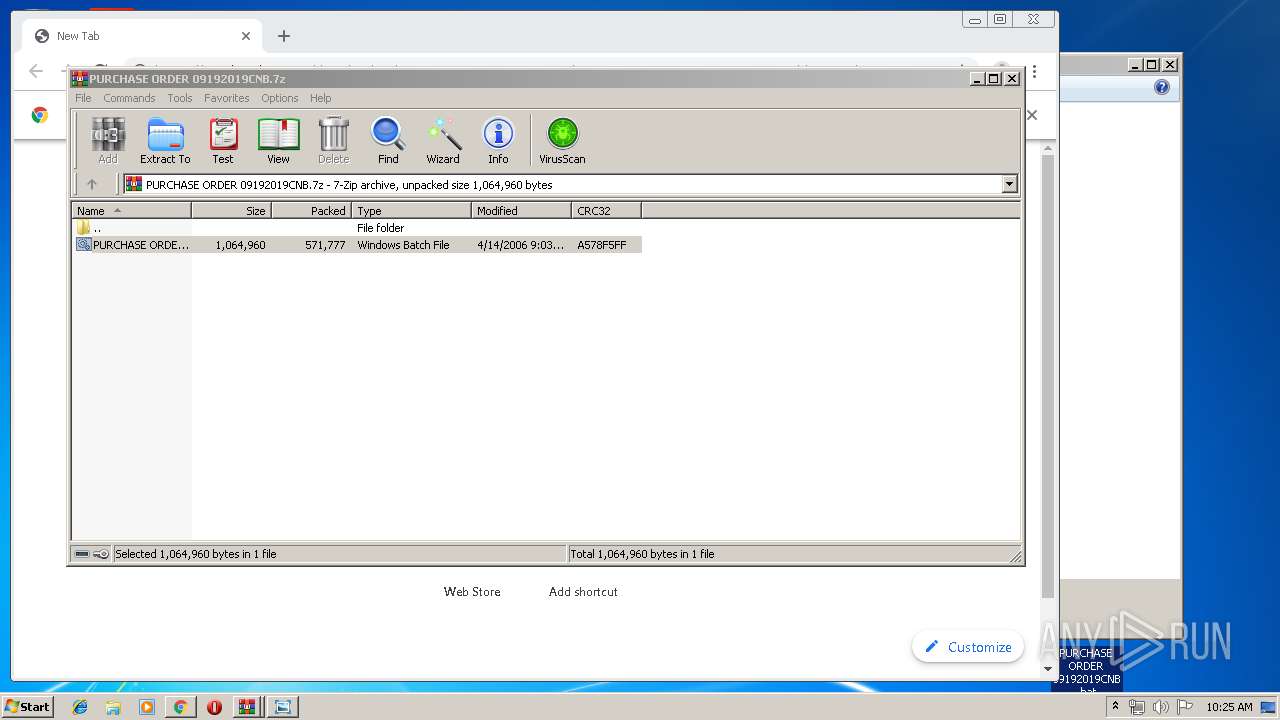
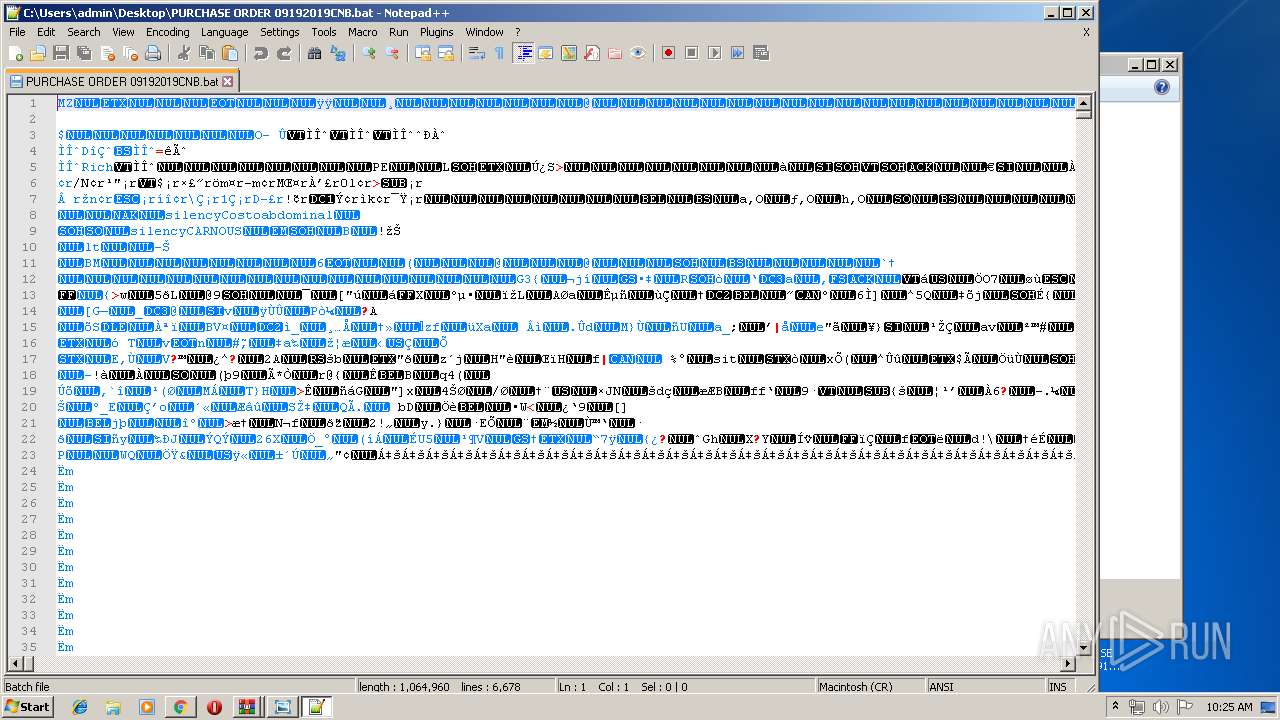
Application was dropped or rewritten from another process
- PURCHASE ORDER 09192019CNB.bat (PID: 2836)
- PURCHASE ORDER 09192019CNB.bat (PID: 2424)
- taskngrr.exe (PID: 2304)
NANOCORE was detected
- taskngrr.exe (PID: 2304)
Changes the autorun value in the registry
- taskngrr.exe (PID: 2304)
- PURCHASE ORDER 09192019CNB.bat (PID: 2424)
Connects to CnC server
- taskngrr.exe (PID: 2304)
AGENTTESLA was detected
- PURCHASE ORDER 09192019CNB.bat (PID: 2424)
Actions looks like stealing of personal data
- PURCHASE ORDER 09192019CNB.bat (PID: 2424)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3660)
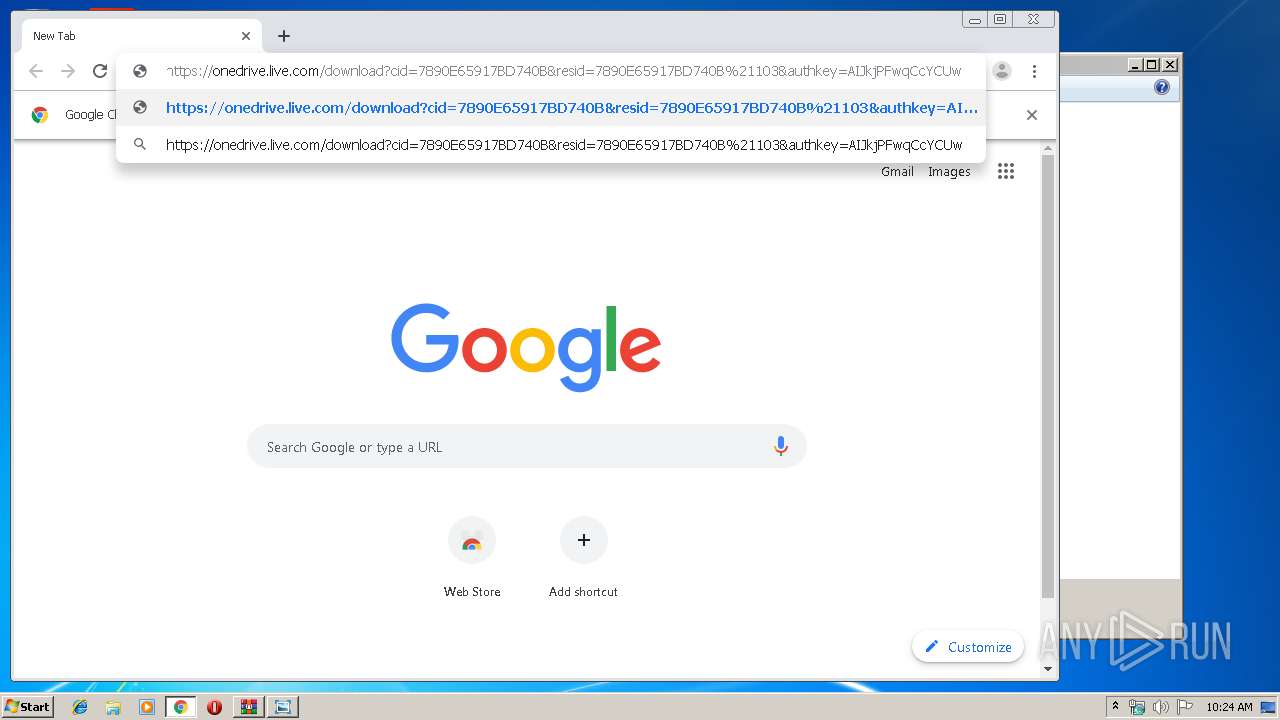
Modifies files in Chrome extension folder
- chrome.exe (PID: 3204)
Executable content was dropped or overwritten
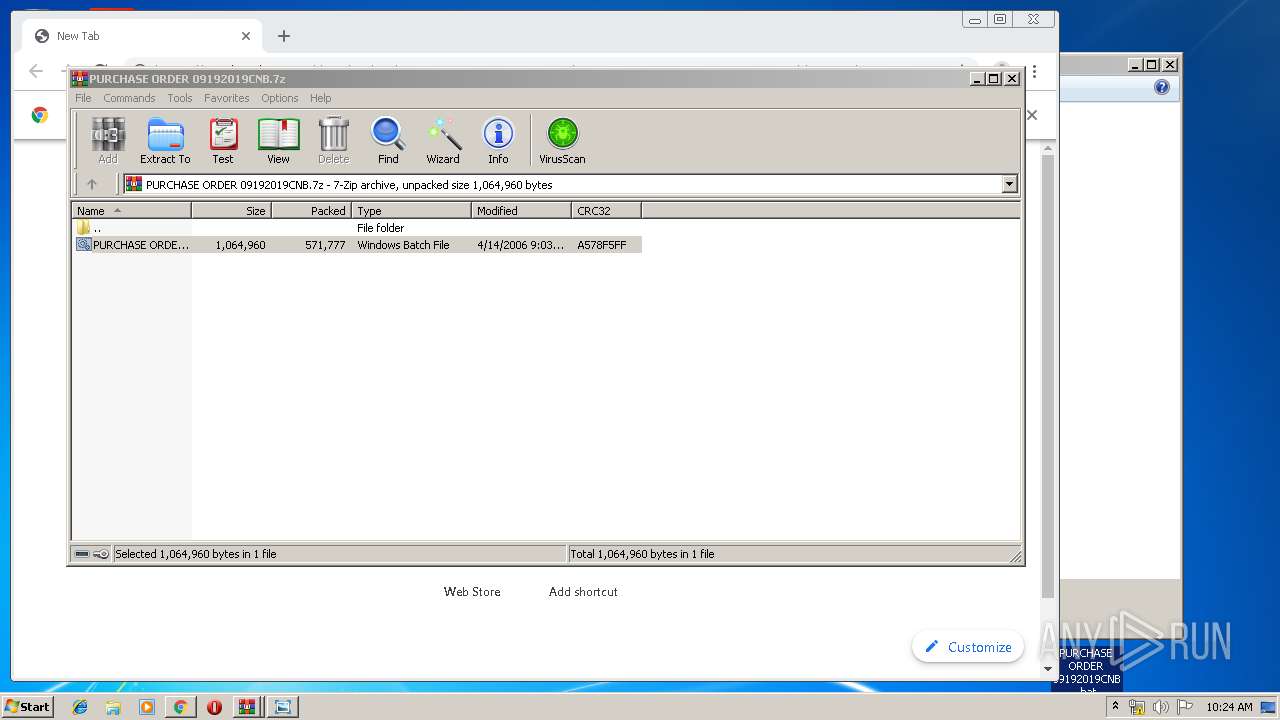
- PURCHASE ORDER 09192019CNB.bat (PID: 2836)
- taskngrr.exe (PID: 2304)
Creates files in the user directory
- taskngrr.exe (PID: 2304)
- notepad++.exe (PID: 408)
Application launched itself
- PURCHASE ORDER 09192019CNB.bat (PID: 2836)
Starts application with an unusual extension
- PURCHASE ORDER 09192019CNB.bat (PID: 2836)
Checks for external IP
- PURCHASE ORDER 09192019CNB.bat (PID: 2424)
INFO
Reads the hosts file
- chrome.exe (PID: 3204)
- chrome.exe (PID: 2848)
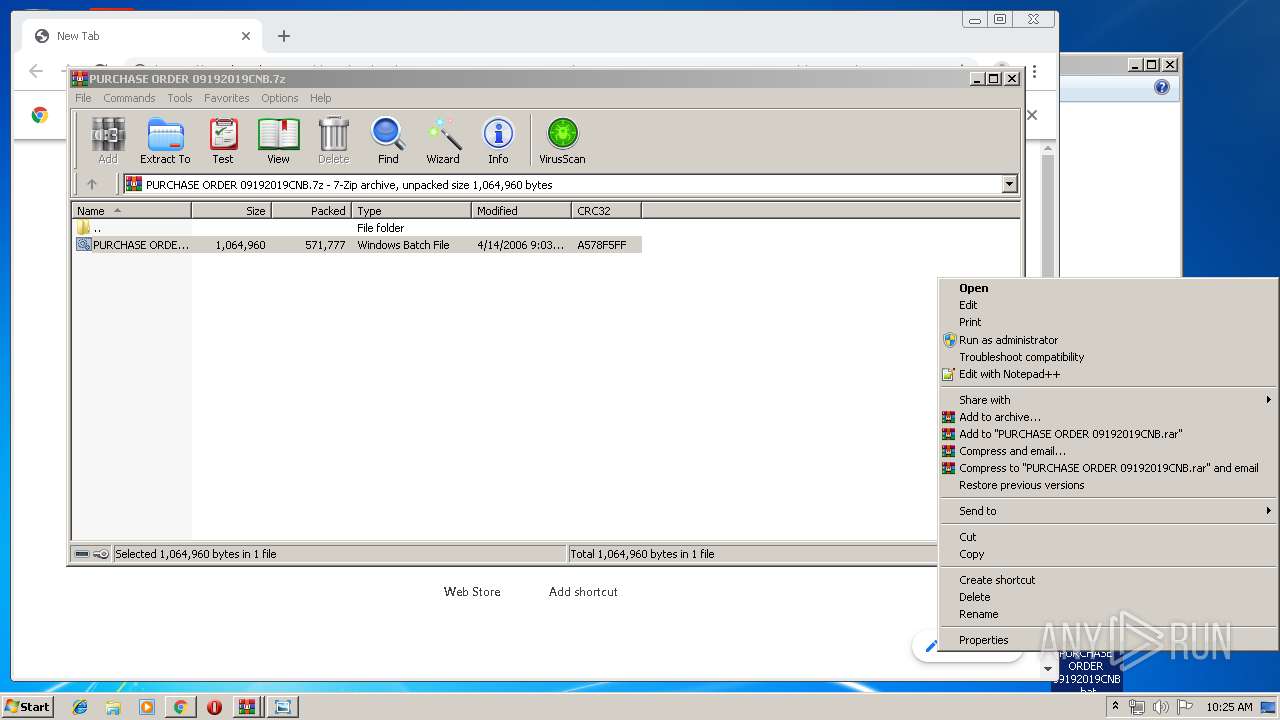
Manual execution by user
- chrome.exe (PID: 3204)
- PURCHASE ORDER 09192019CNB.bat (PID: 2836)
- notepad++.exe (PID: 408)
Reads Internet Cache Settings
- chrome.exe (PID: 3204)
Application launched itself
- chrome.exe (PID: 3204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:19 09:12:01 |
| ZipCRC: | 0x087ee14d |
| ZipCompressedSize: | 25317 |
| ZipUncompressedSize: | 25618 |
| ZipFileName: | PURCHASE ORDER 09172019NBM.PNG |
Total processes
71
Monitored processes
34
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,9339460074037799769,7354158770159437845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16386408942212063632 --mojo-platform-channel-handle=4132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\PURCHASE ORDER 09192019CNB.bat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
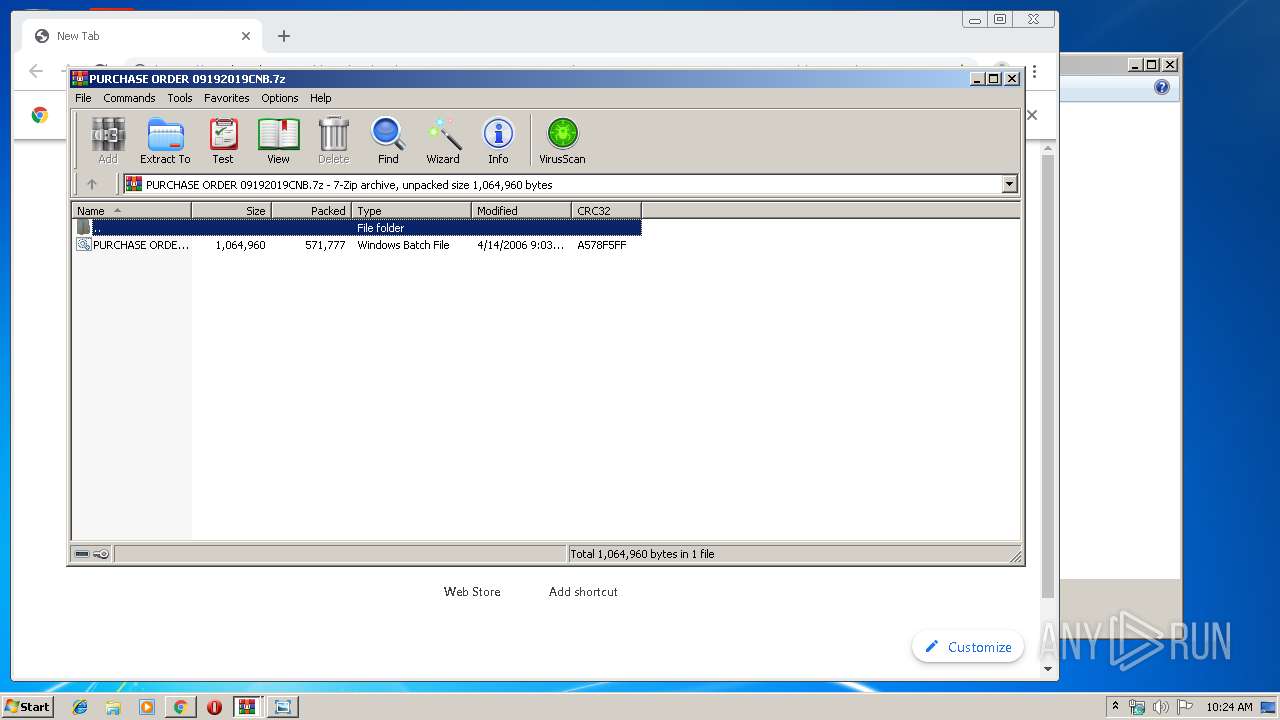
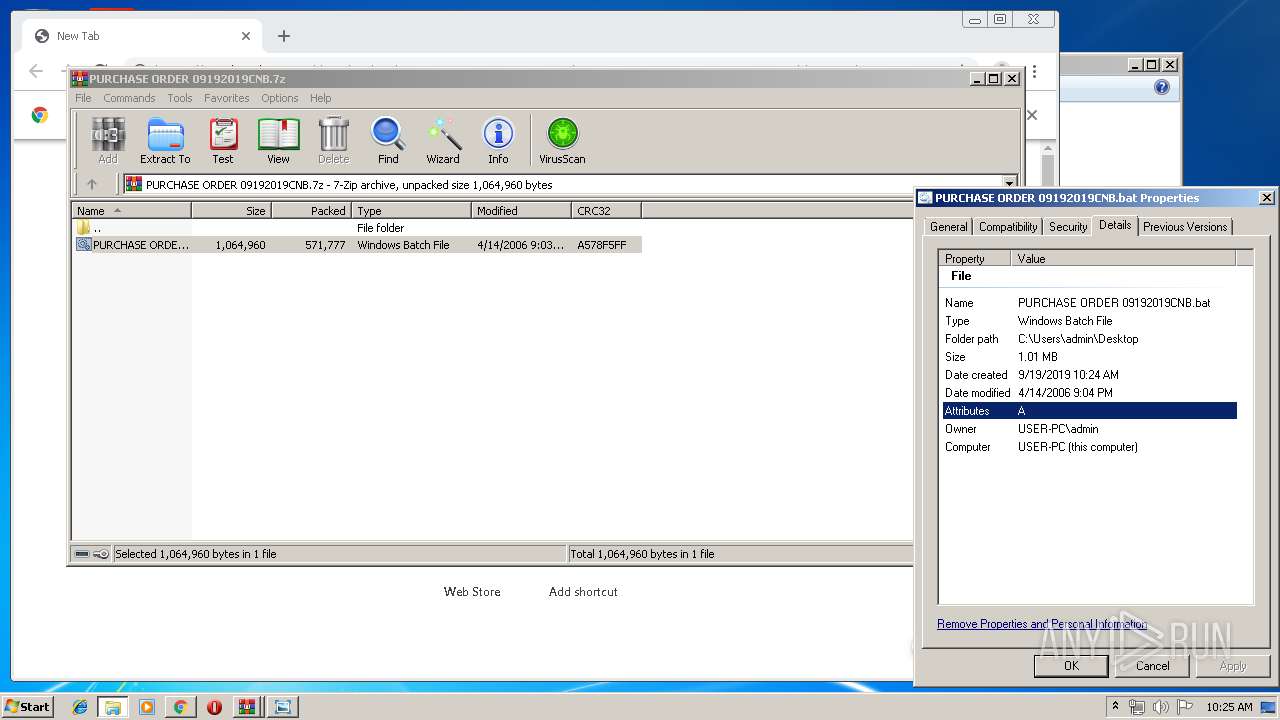
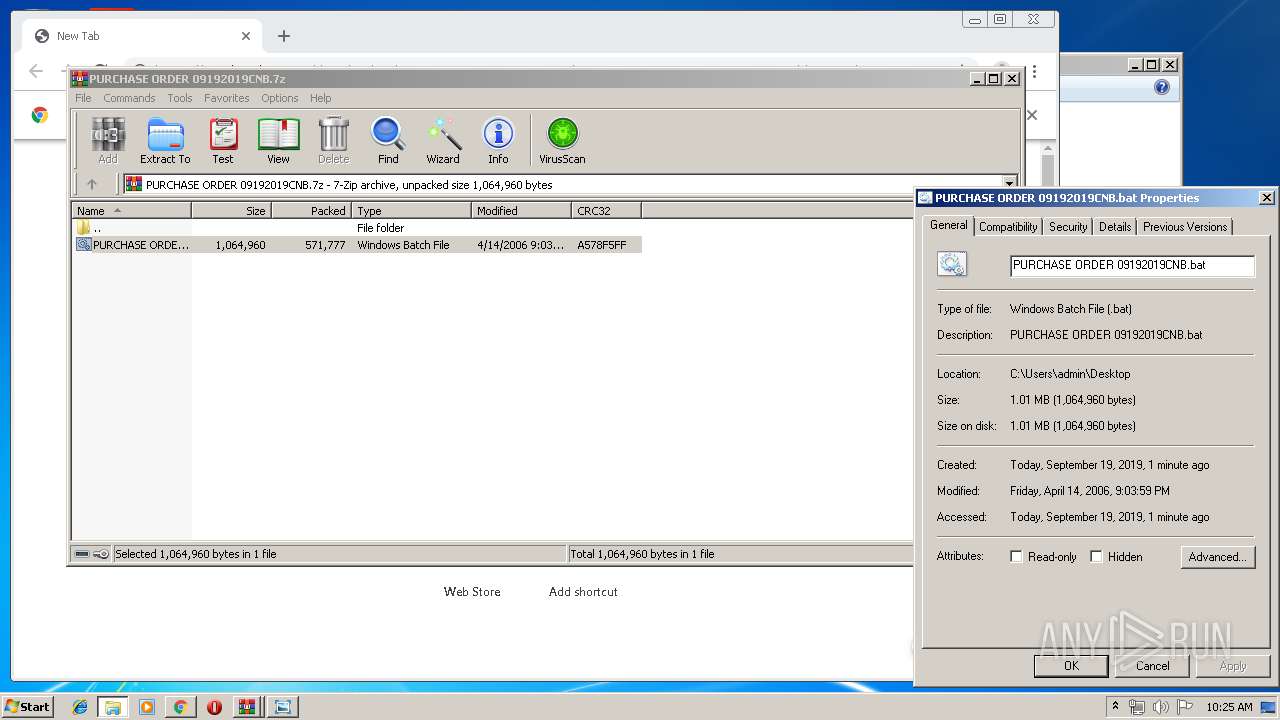
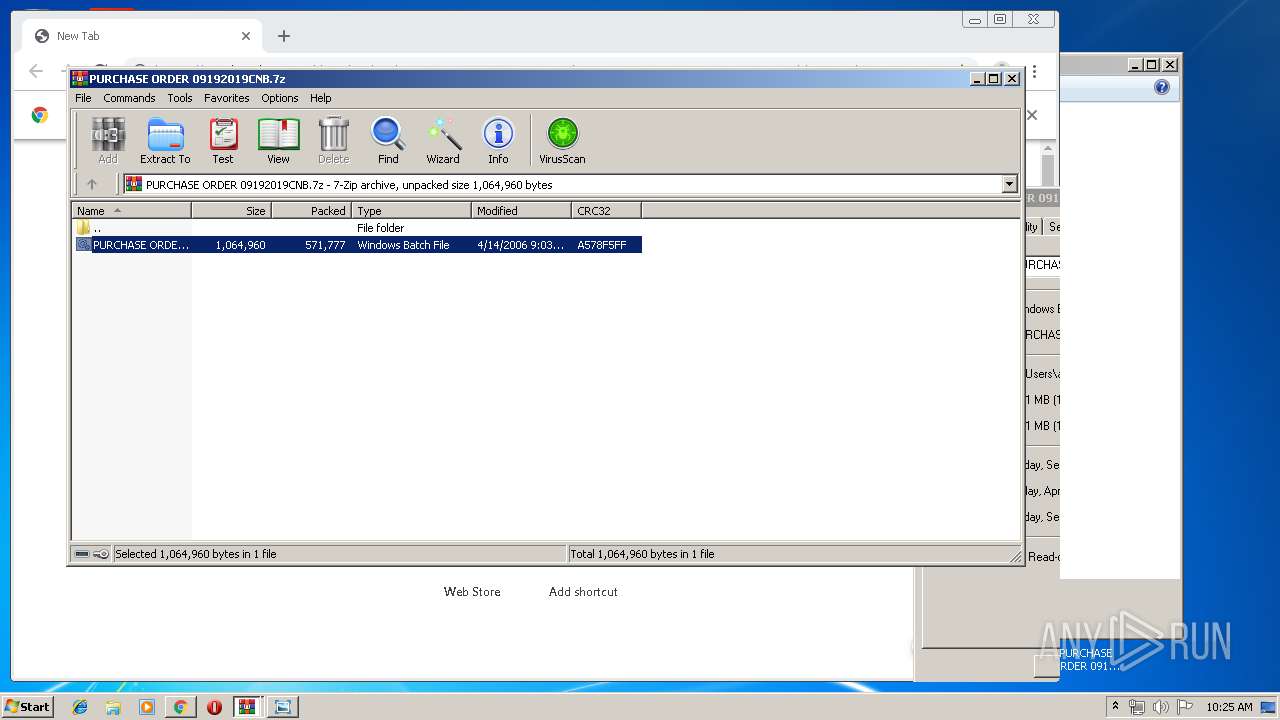
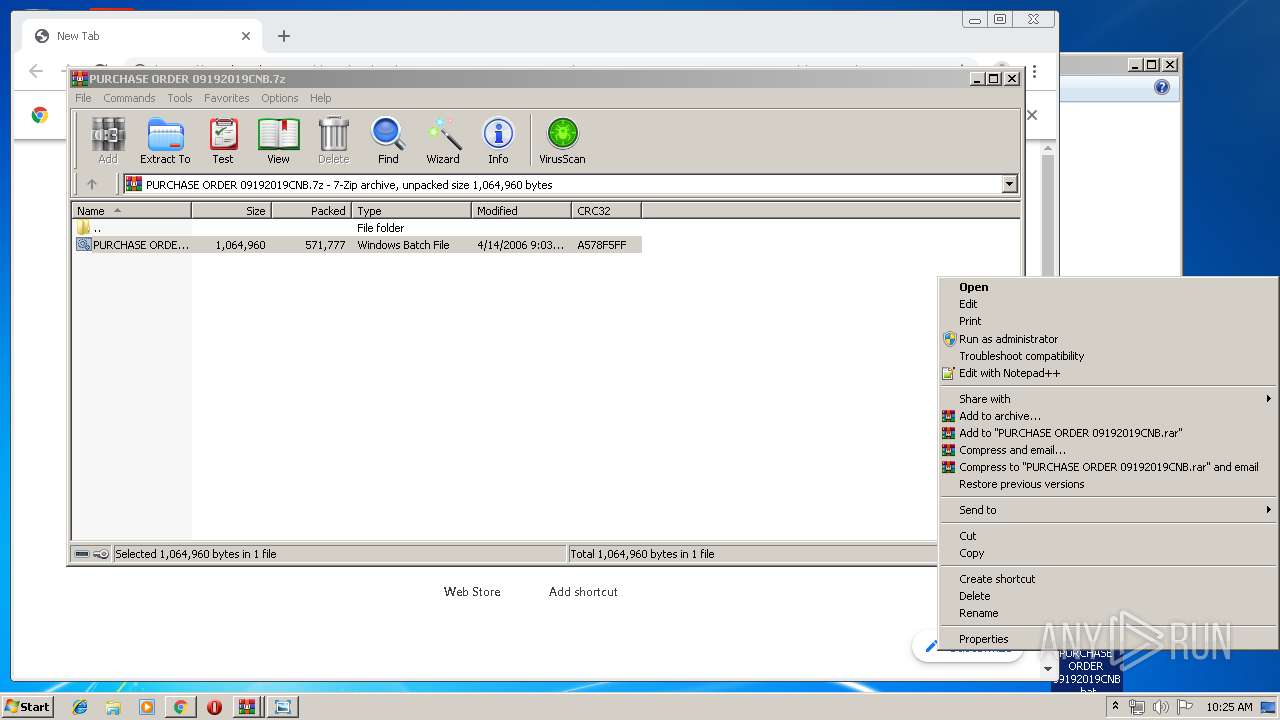
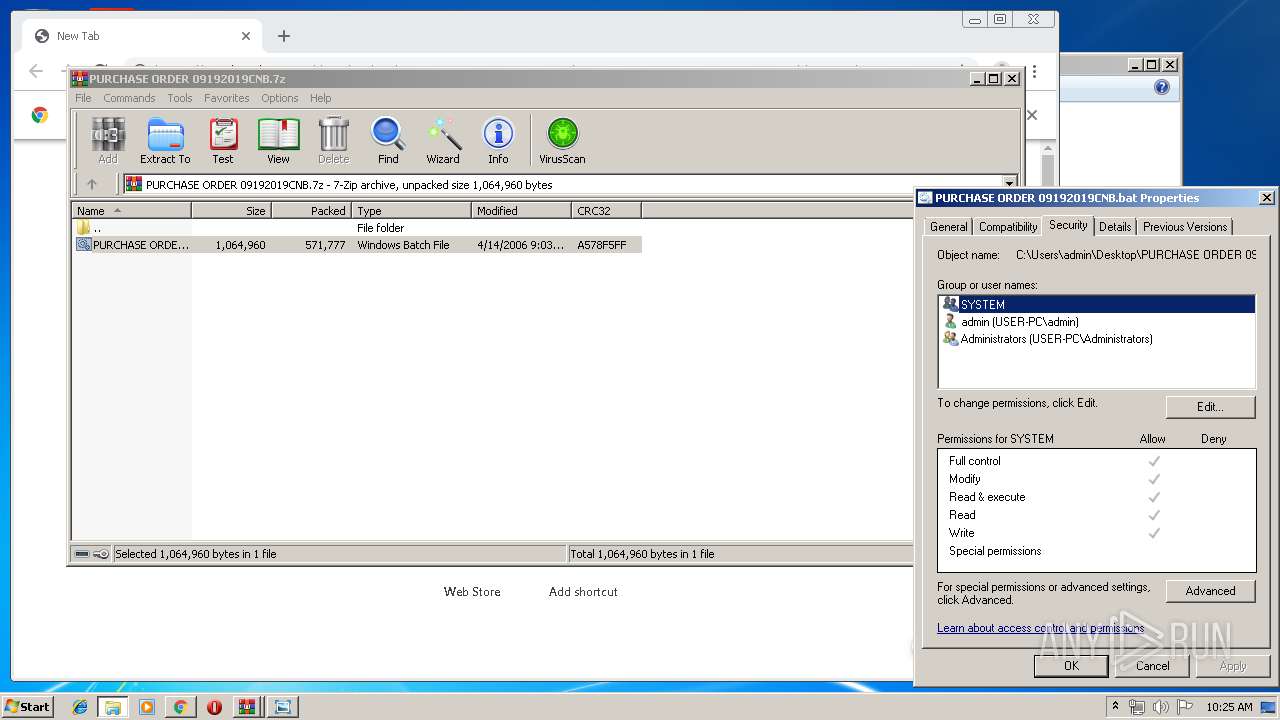
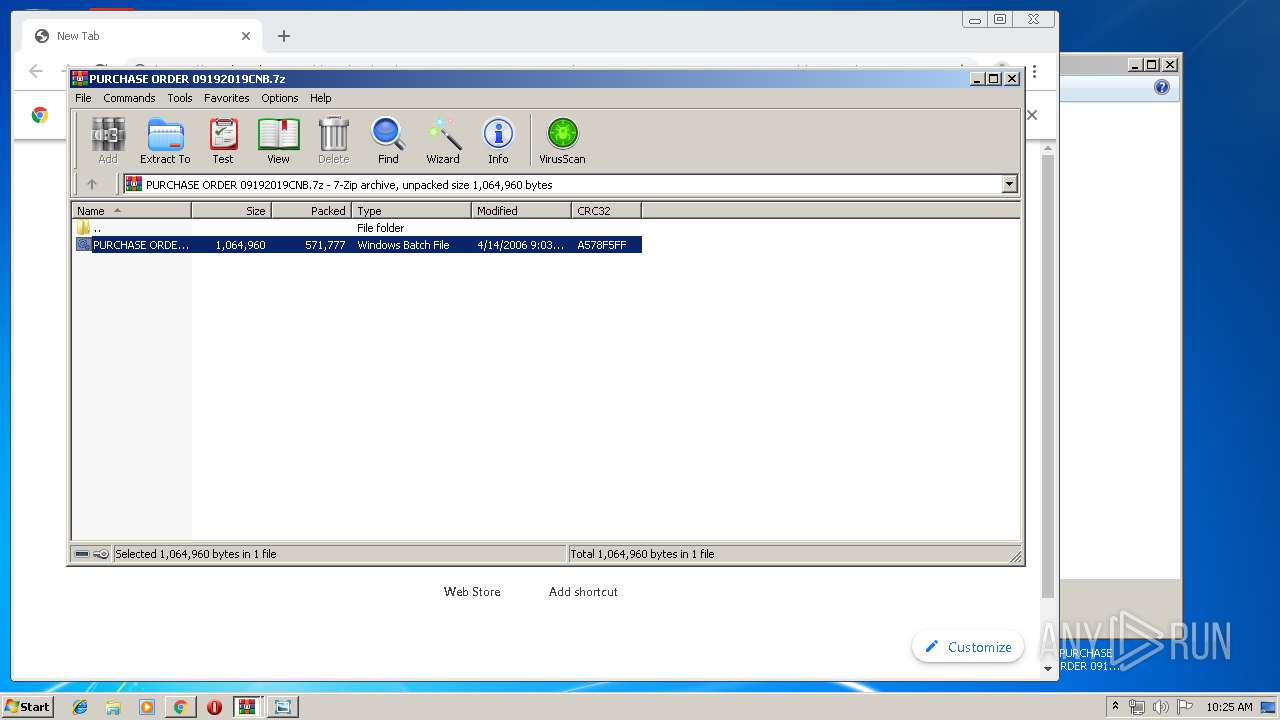
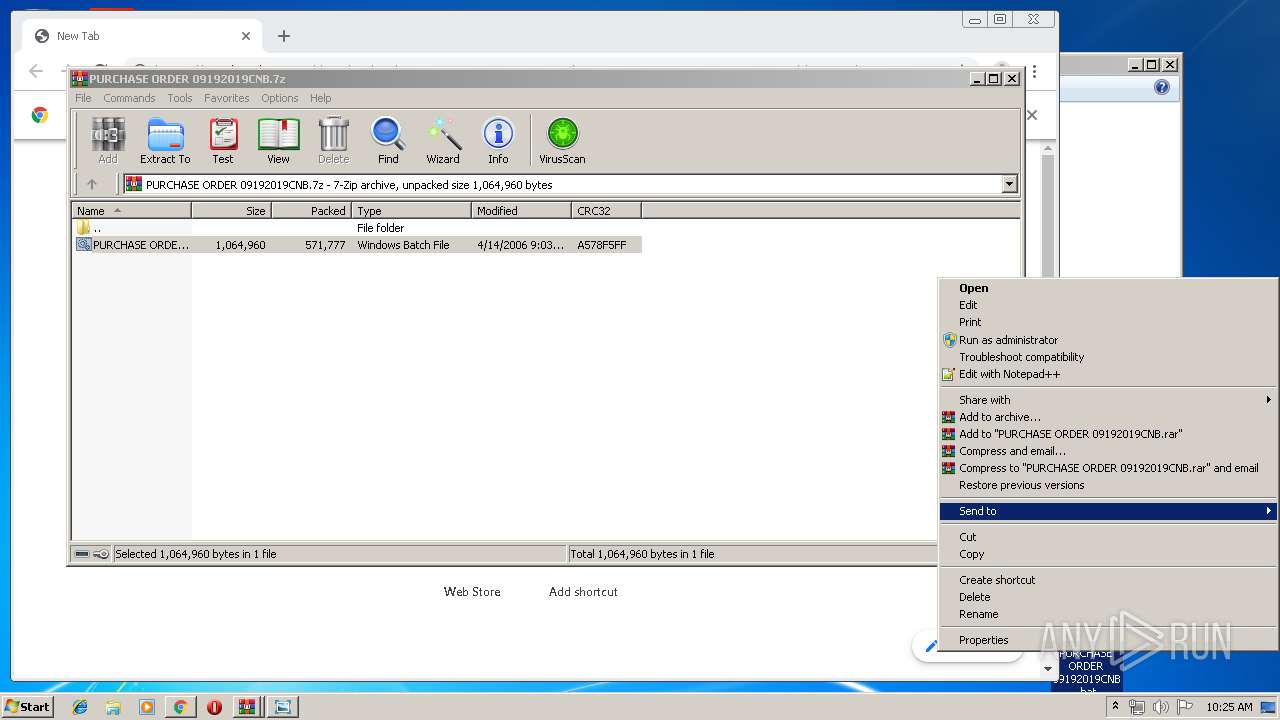
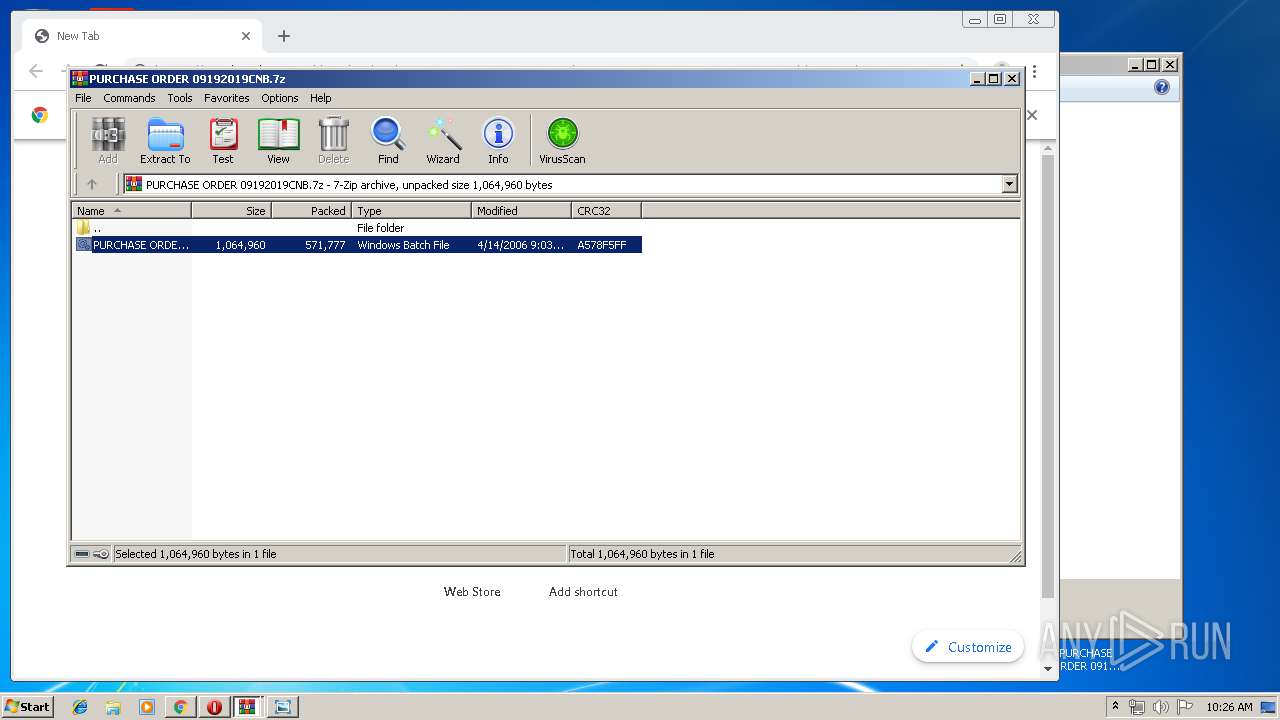
| 976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\PURCHASE ORDER 09192019CNB.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,9339460074037799769,7354158770159437845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12896198603361386255 --mojo-platform-channel-handle=3336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,9339460074037799769,7354158770159437845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11143739899183727051 --mojo-platform-channel-handle=3452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,9339460074037799769,7354158770159437845,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3926037495540655712 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,9339460074037799769,7354158770159437845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3942278699592851626 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2304 | "C:\Users\admin\AppData\Local\Temp\taskngrr.exe" | C:\Users\admin\AppData\Local\Temp\taskngrr.exe | PURCHASE ORDER 09192019CNB.bat | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\Desktop\PURCHASE ORDER 09192019CNB.bat" | C:\Users\admin\Desktop\PURCHASE ORDER 09192019CNB.bat | PURCHASE ORDER 09192019CNB.bat | ||||||||||||
User: admin Company: silencydecan Integrity Level: MEDIUM Exit code: 0 Version: 8.09.0009 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,9339460074037799769,7354158770159437845,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16343756859672559201 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 403
Read events
2 249
Write events
149
Delete events
5
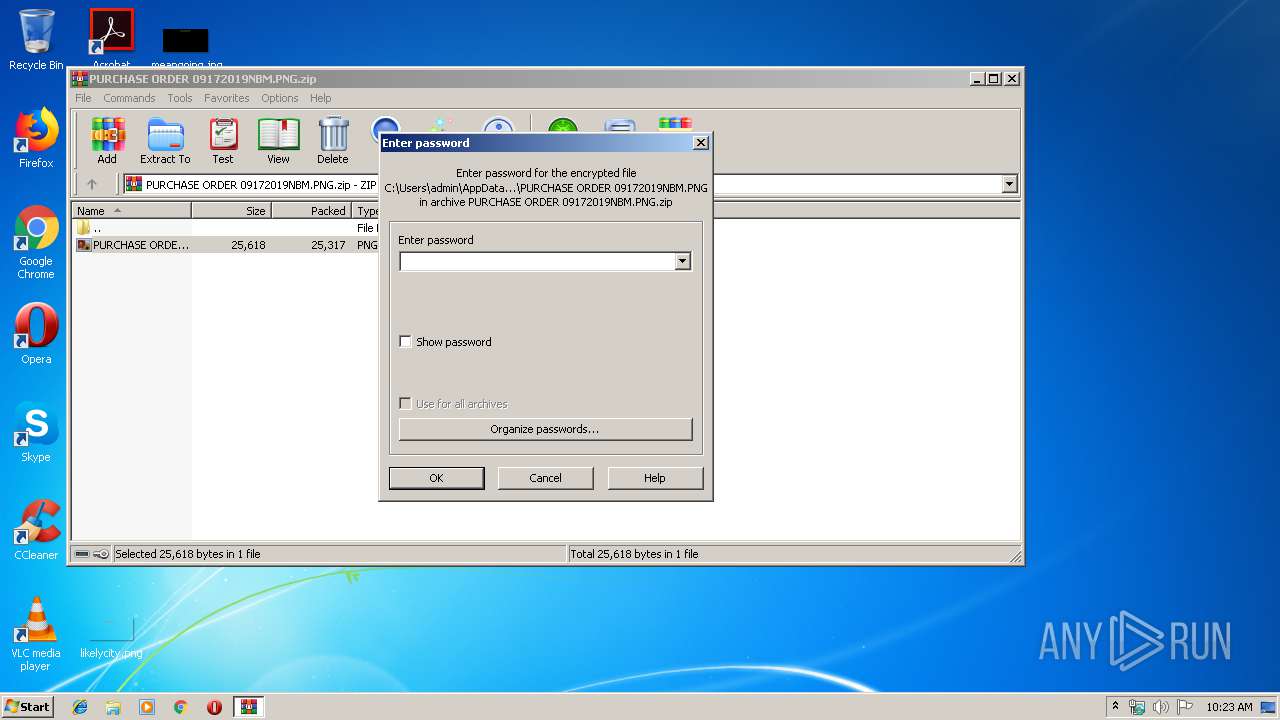
Modification events
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PURCHASE ORDER 09172019NBM.PNG.zip | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3660) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
Executable files
2
Suspicious files
29
Text files
191
Unknown types
6
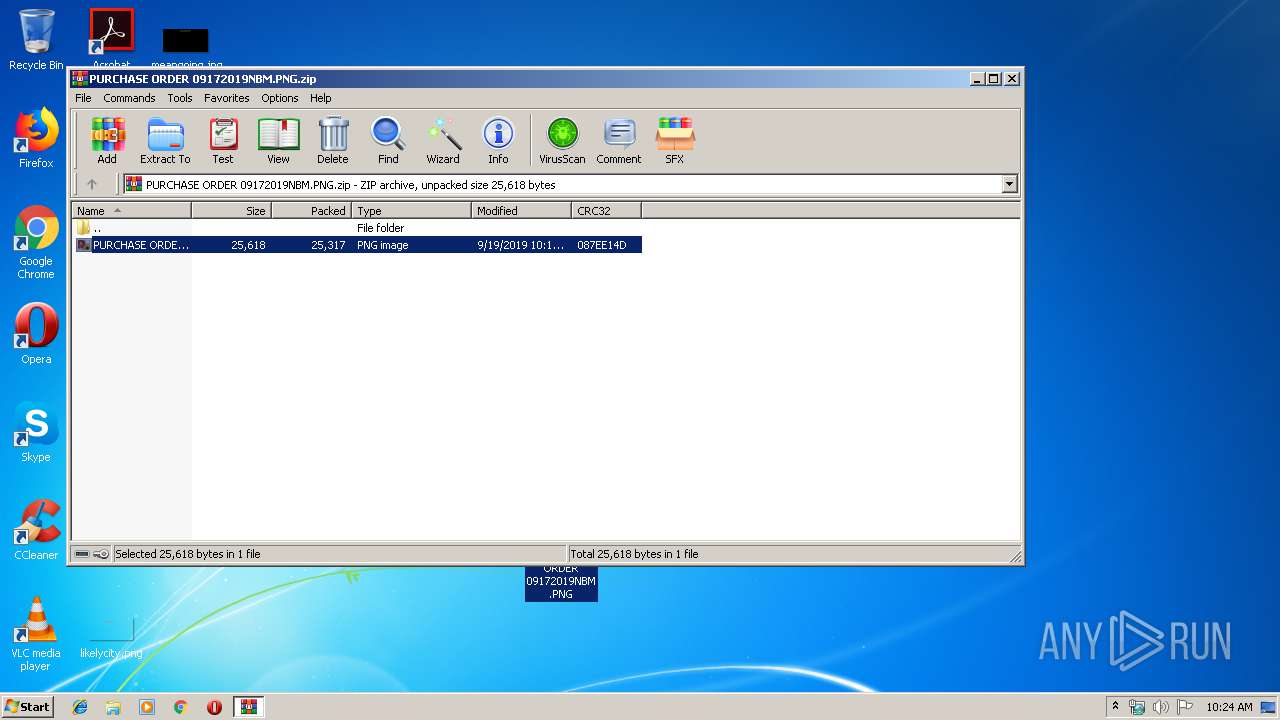
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF17104c.TMP | — | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\820468a4-63c7-45d2-bc19-03bf6805dc50.tmp | — | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3536.4091\PURCHASE ORDER 09172019NBM.PNG | image | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF170ffd.TMP | text | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
27
DNS requests
23
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2424 | PURCHASE ORDER 09192019CNB.bat | GET | 200 | 3.224.145.145:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2848 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2848 | chrome.exe | GET | 200 | 74.125.104.104:80 | http://r2---sn-2gb7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.187.165.52&mm=28&mn=sn-2gb7sn7k&ms=nvh&mt=1568885002&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2304 | taskngrr.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 60B |
2304 | taskngrr.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
2304 | taskngrr.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
2304 | taskngrr.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
2304 | taskngrr.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
2304 | taskngrr.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
2304 | taskngrr.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
2304 | taskngrr.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
2304 | taskngrr.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
2304 | taskngrr.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
33 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|