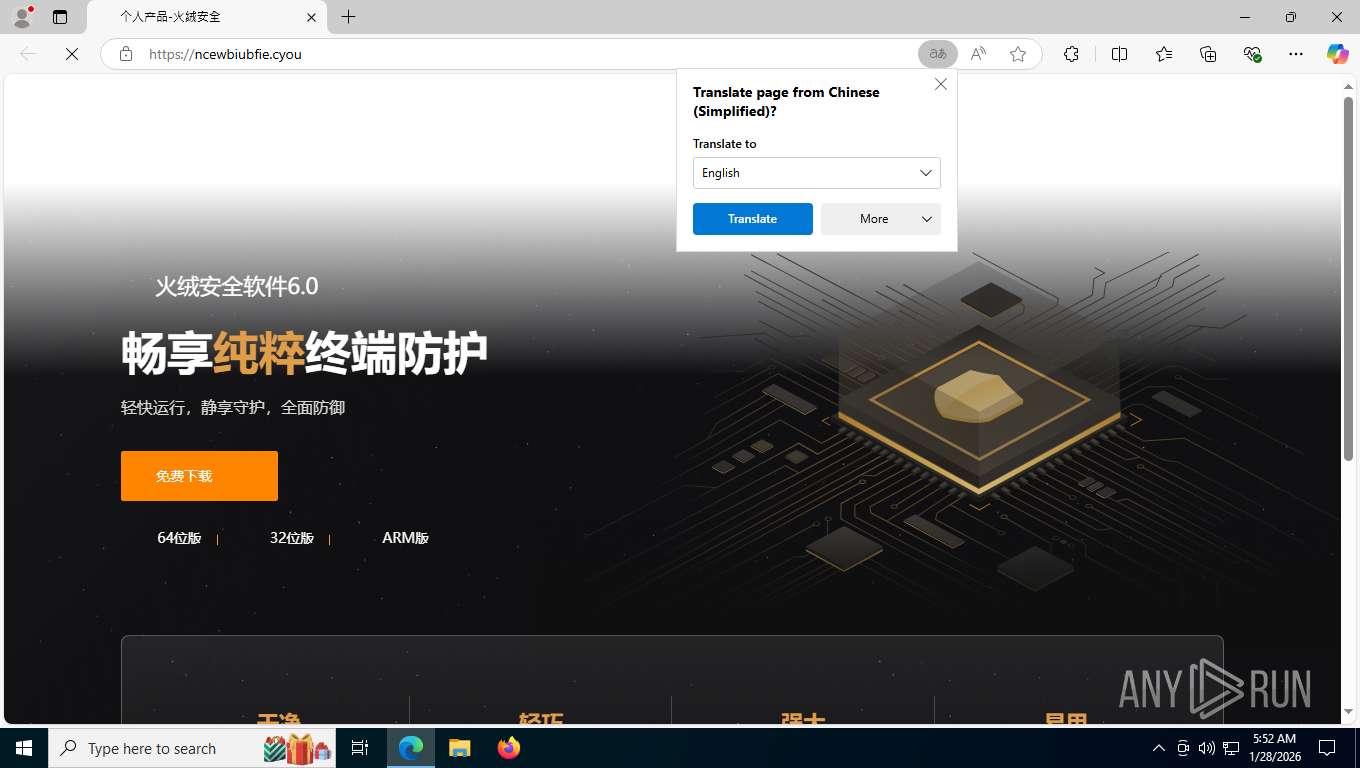
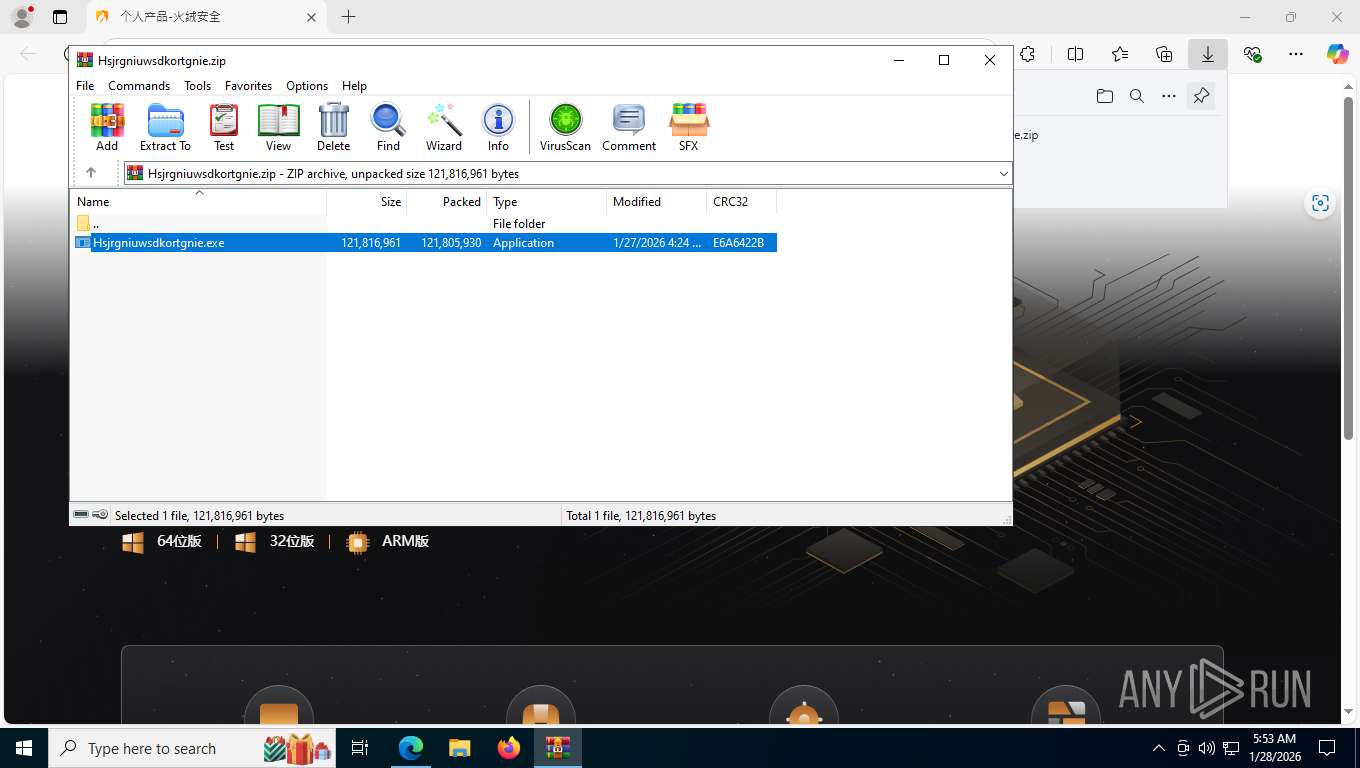
| URL: | https://ncewbiubfie.cyou/ |
| Full analysis: | https://app.any.run/tasks/a8d14f19-f3fb-42cd-b103-7a06eb1546c6 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | January 28, 2026, 10:52:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6D12DEC30ABFF5E9054CBD09C0BC66BB |
| SHA1: | 093BF7B33D04BD5982AC3C63D8207F0C276FEB80 |
| SHA256: | E0158F2464DCC01620FF1EB15EB45533CCCA9FB425A2F47DD4CB4C3F9F930C5B |
| SSDEEP: | 3:N8kMuLLKn:2A+n |
MALICIOUS
Connects to the CnC server
- rundll32.exe (PID: 5520)
VALLEYRAT has been detected
- rundll32.exe (PID: 5520)
SILVERFOX has been detected (SURICATA)
- rundll32.exe (PID: 5520)
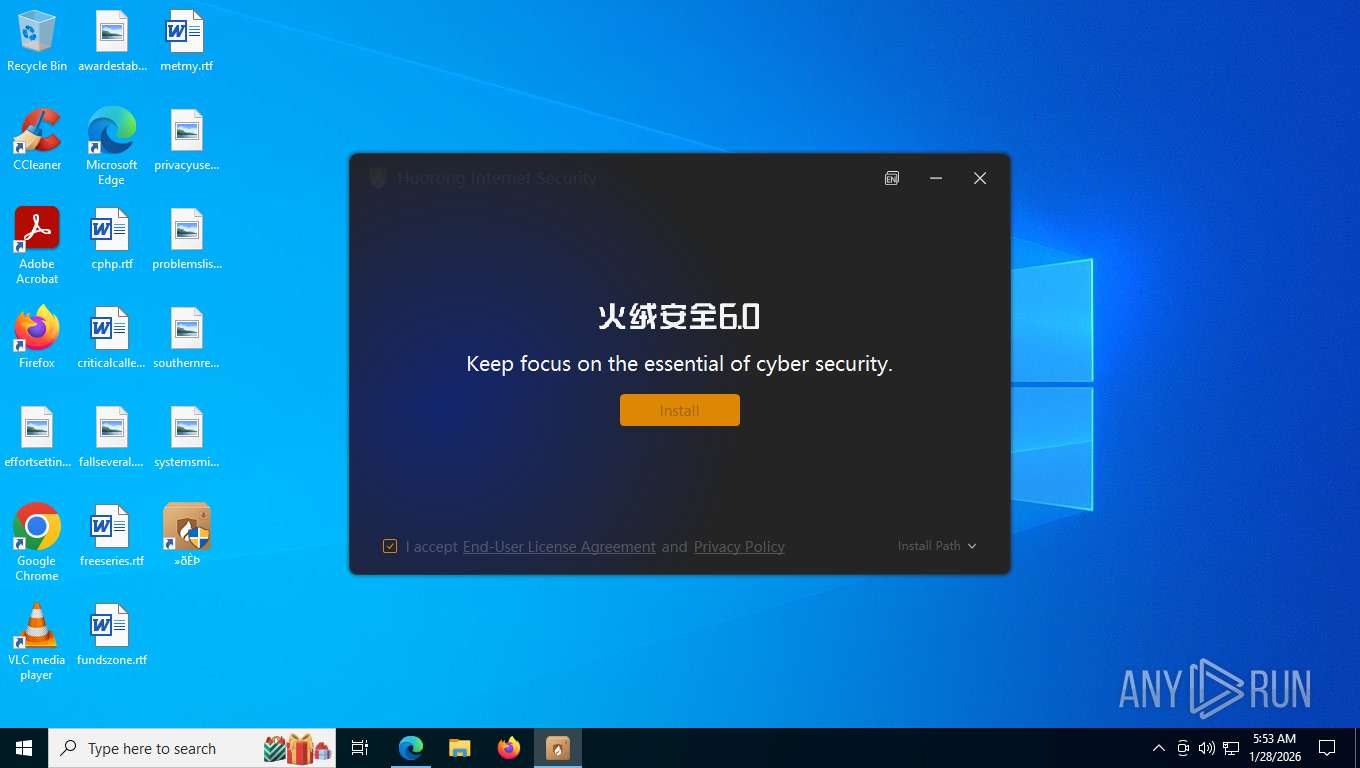
Executing a file with an untrusted certificate
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Changes the autorun value in the registry
- HRUpdate.exe (PID: 3796)
Registers / Runs the DLL via REGSVR32.EXE
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Potential DLL hijacking behavior detected
- regsvr32.exe (PID: 5148)
- regsvr32.exe (PID: 8492)
- regsvr32.exe (PID: 2336)
- regsvr32.exe (PID: 2780)
- regsvr32.exe (PID: 7228)
- regsvr32.exe (PID: 5872)
Proxy execution via Explorer
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
SUSPICIOUS
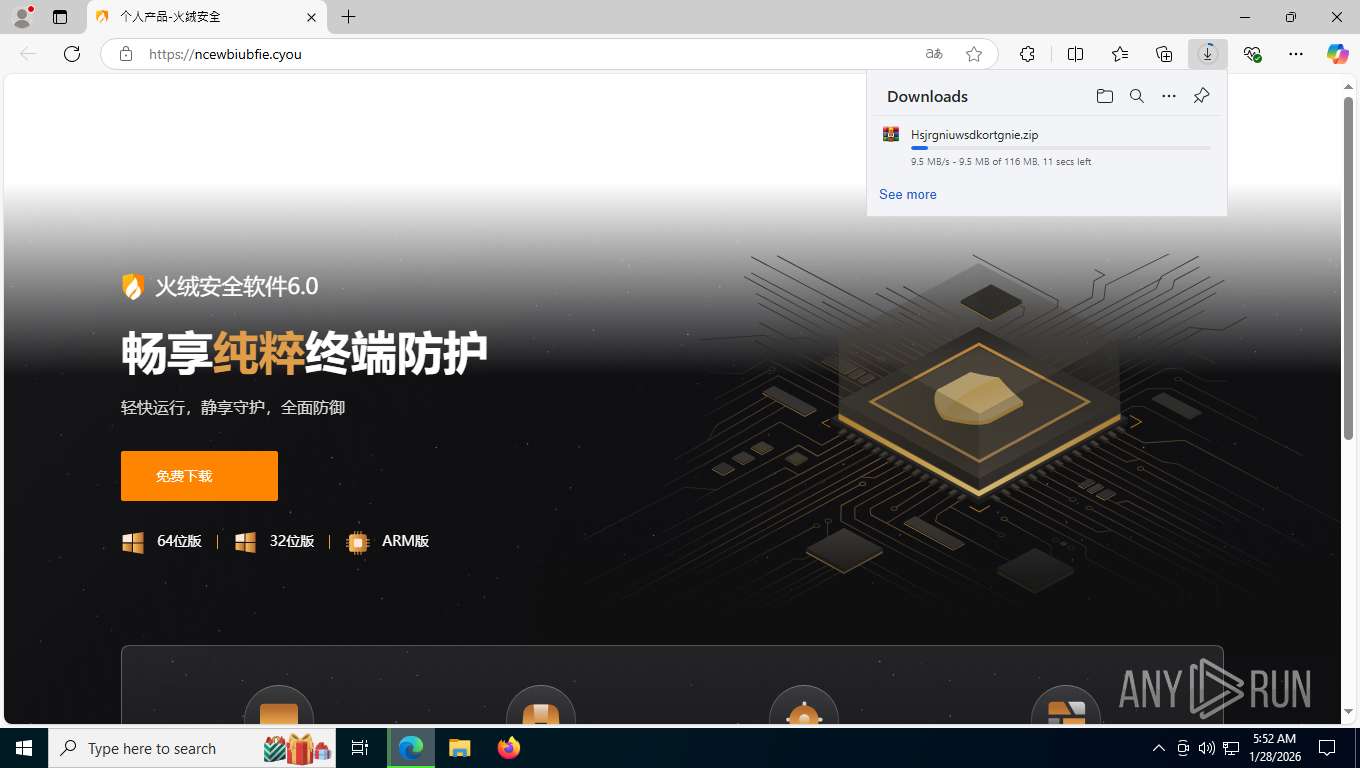
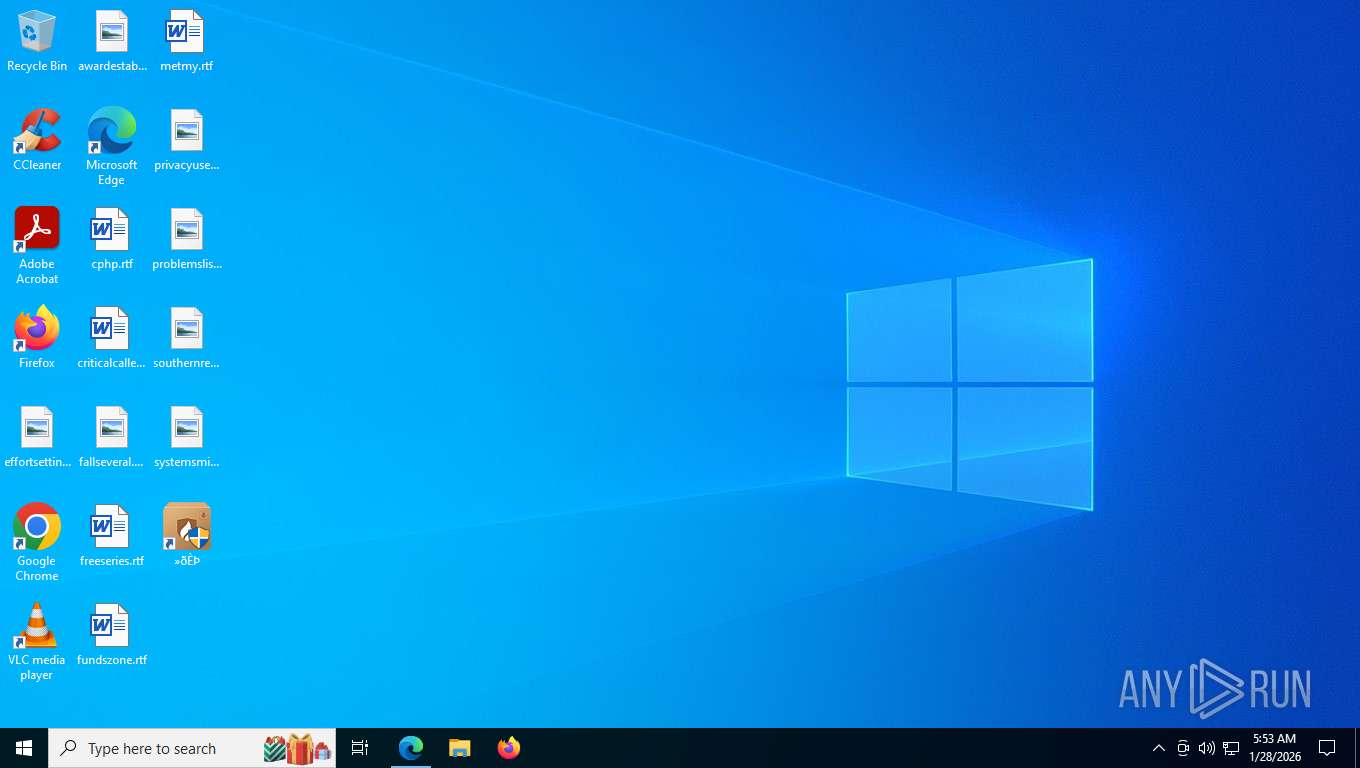
The process creates files with name similar to system file names
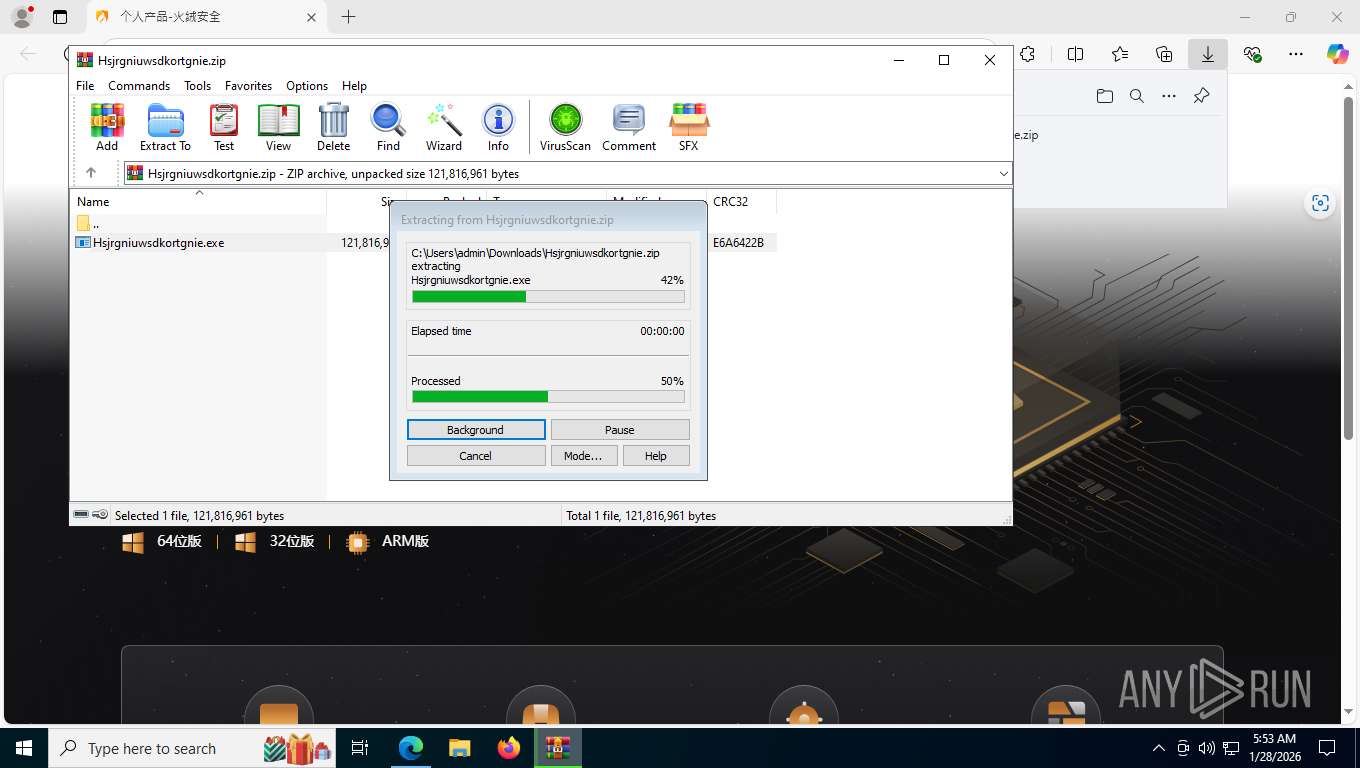
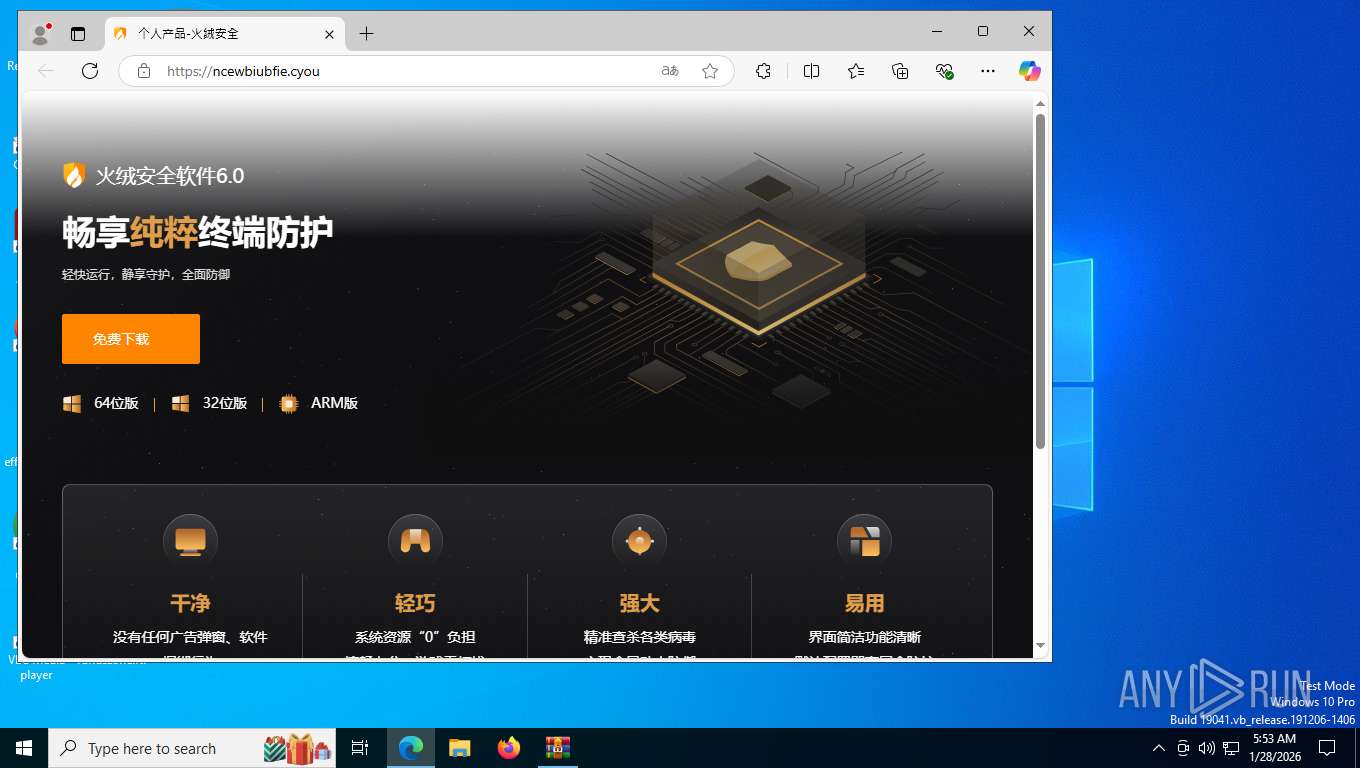
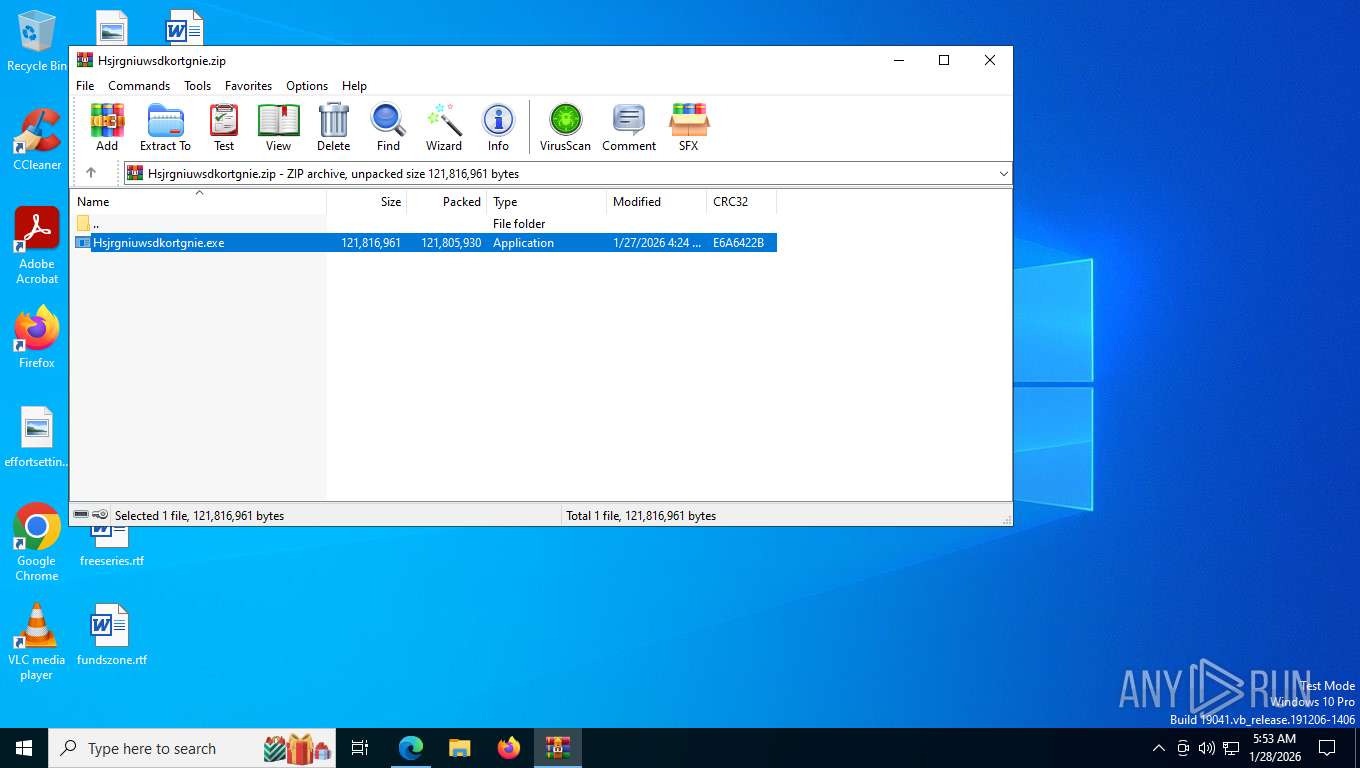
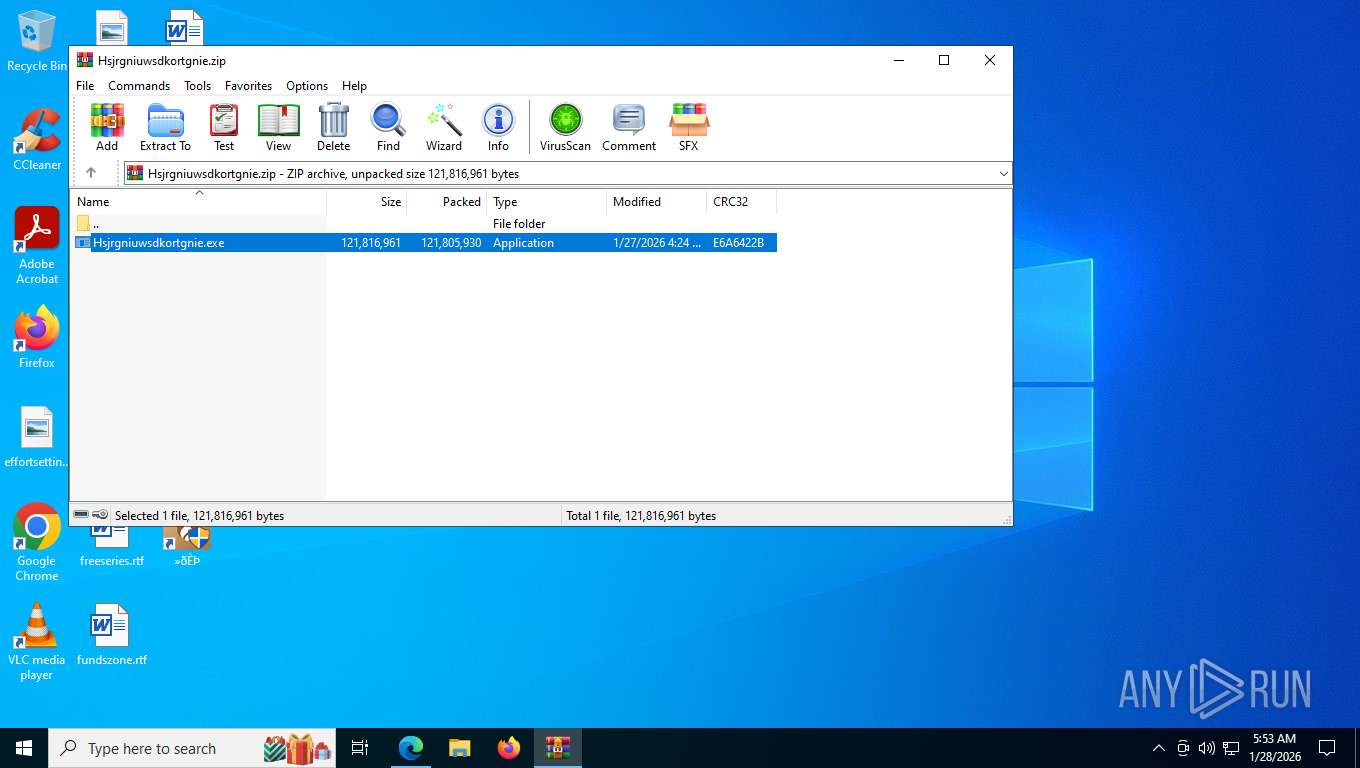
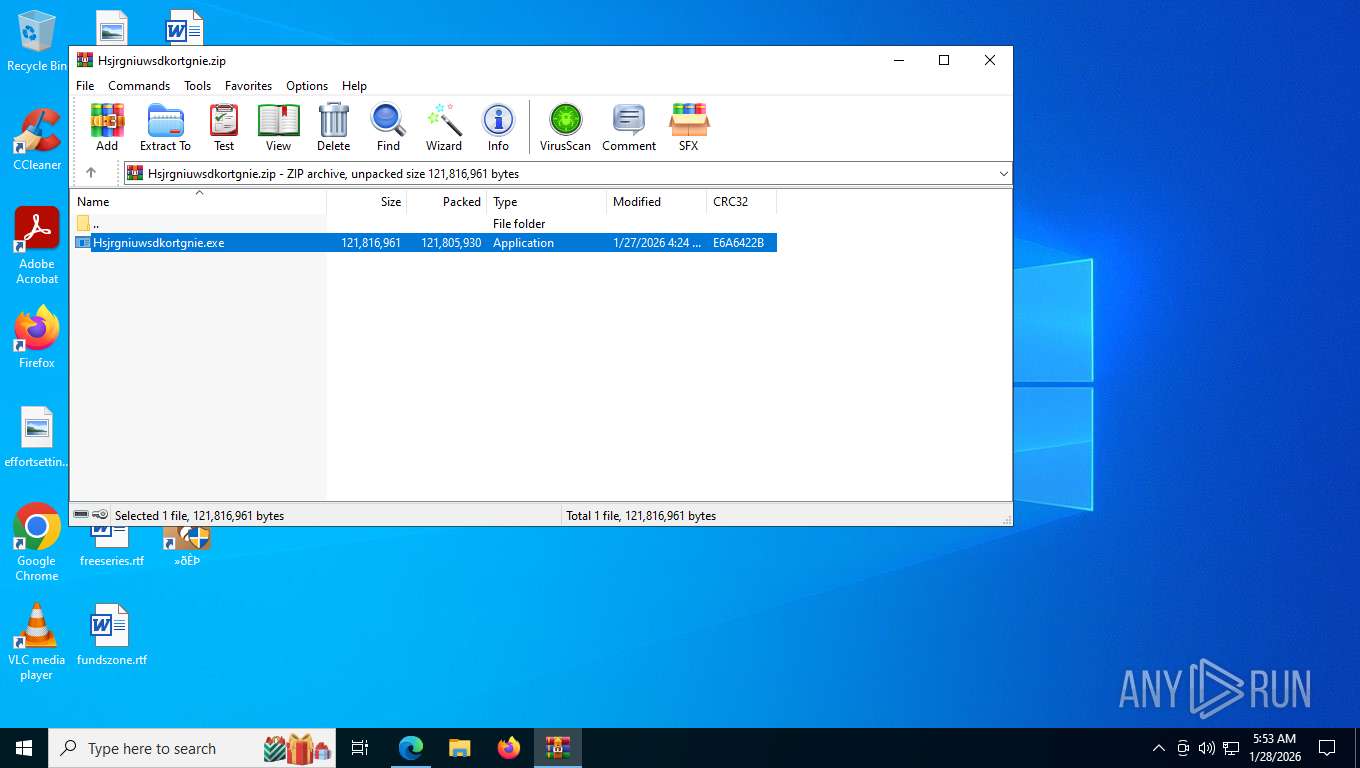
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
The process drops C-runtime libraries
- XLGame.exe (PID: 5496)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
Executable content was dropped or overwritten
- XLGame.exe (PID: 5496)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
Process drops legitimate windows executable
- XLGame.exe (PID: 5496)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
Malware-specific behavior (creating "System.dll" in Temp)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
Contacting a server suspected of hosting an CnC
- rundll32.exe (PID: 5520)
Searches for installed software
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- dllhost.exe (PID: 8096)
- HRUpdate.exe (PID: 4544)
The process executes via Task Scheduler
- XLGame.exe (PID: 7472)
Executes as Windows Service
- VSSVC.exe (PID: 6948)
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
- wsctrlsvc.exe (PID: 8556)
Creates or modifies Windows services
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Drops a system driver (possible attempt to evade defenses)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
Creates files in the driver directory
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
Found regular expressions for crypto-addresses (YARA)
- rundll32.exe (PID: 5520)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 8288)
- regsvr32.exe (PID: 7416)
- regsvr32.exe (PID: 676)
- regsvr32.exe (PID: 6912)
Read startup parameters
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Reads the date of Windows installation
- HRUpdate.exe (PID: 3796)
- HipsMain.exe (PID: 6396)
Reads Microsoft Outlook installation path
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 876)
INFO
Application launched itself
- msedge.exe (PID: 2600)
Checks supported languages
- identity_helper.exe (PID: 3092)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- XLGame.exe (PID: 5496)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- XLGame.exe (PID: 7472)
- LocalUpgrade.exe (PID: 8960)
- DB5Upgrade.exe (PID: 8752)
- HRUpdate.exe (PID: 3796)
- HipsDaemon.exe (PID: 9056)
- wsctrl.exe (PID: 8888)
- HipsTray.exe (PID: 5700)
- HipsTray.exe (PID: 756)
- DB5Upgrade.exe (PID: 8712)
- HipsTray.exe (PID: 6936)
- HipsTray.exe (PID: 8496)
- HipsTray.exe (PID: 4936)
- HipsDaemon.exe (PID: 4008)
- HRUpdate.exe (PID: 4544)
- HipsTray.exe (PID: 8040)
- HipsTray.exe (PID: 3536)
- wsctrl.exe (PID: 6444)
- wsctrlsvc.exe (PID: 8556)
- wsctrl.exe (PID: 4784)
- HipsMain.exe (PID: 6396)
- HipsMain.exe (PID: 2708)
- HipsTray.exe (PID: 5752)
- HipsTray.exe (PID: 4684)
Reads Environment values
- identity_helper.exe (PID: 3092)
Reads the computer name
- identity_helper.exe (PID: 3092)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- XLGame.exe (PID: 5496)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- HRUpdate.exe (PID: 3796)
- HipsDaemon.exe (PID: 9056)
- wsctrl.exe (PID: 8888)
- HipsTray.exe (PID: 756)
- HipsTray.exe (PID: 8496)
- HipsDaemon.exe (PID: 4008)
- HRUpdate.exe (PID: 4544)
- wsctrl.exe (PID: 6444)
- wsctrlsvc.exe (PID: 8556)
- wsctrl.exe (PID: 4784)
- HipsMain.exe (PID: 2708)
- HipsMain.exe (PID: 6396)
Drops script file
- msedge.exe (PID: 2600)
- msedge.exe (PID: 5708)
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3040)
- HRUpdate.exe (PID: 3796)
- explorer.exe (PID: 1876)
- HipsMain.exe (PID: 6396)
Creates files or folders in the user directory
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
Create files in a temporary directory
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- DB5Upgrade.exe (PID: 8752)
- LocalUpgrade.exe (PID: 8960)
- HipsMain.exe (PID: 6396)
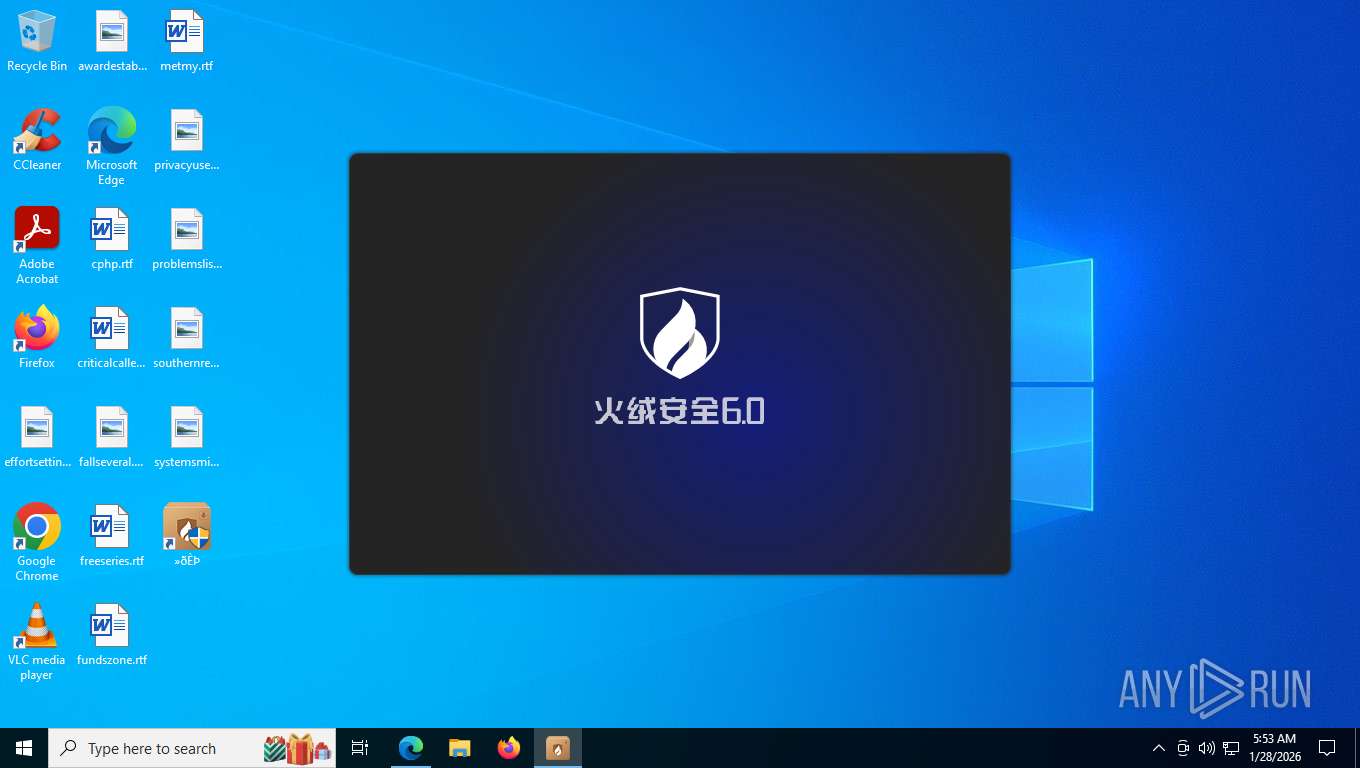
The sample compiled with chinese language support
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- XLGame.exe (PID: 5496)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
The sample compiled with english language support
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- XLGame.exe (PID: 5496)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
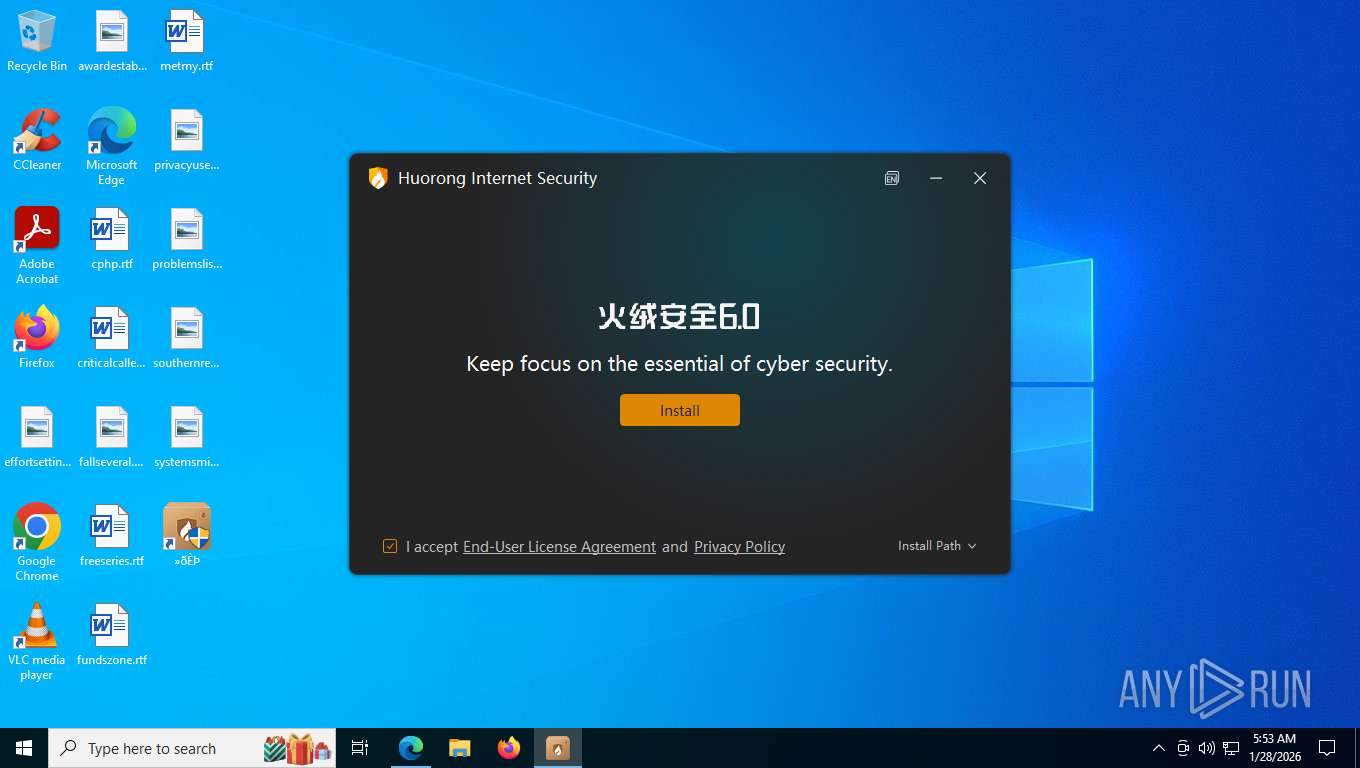
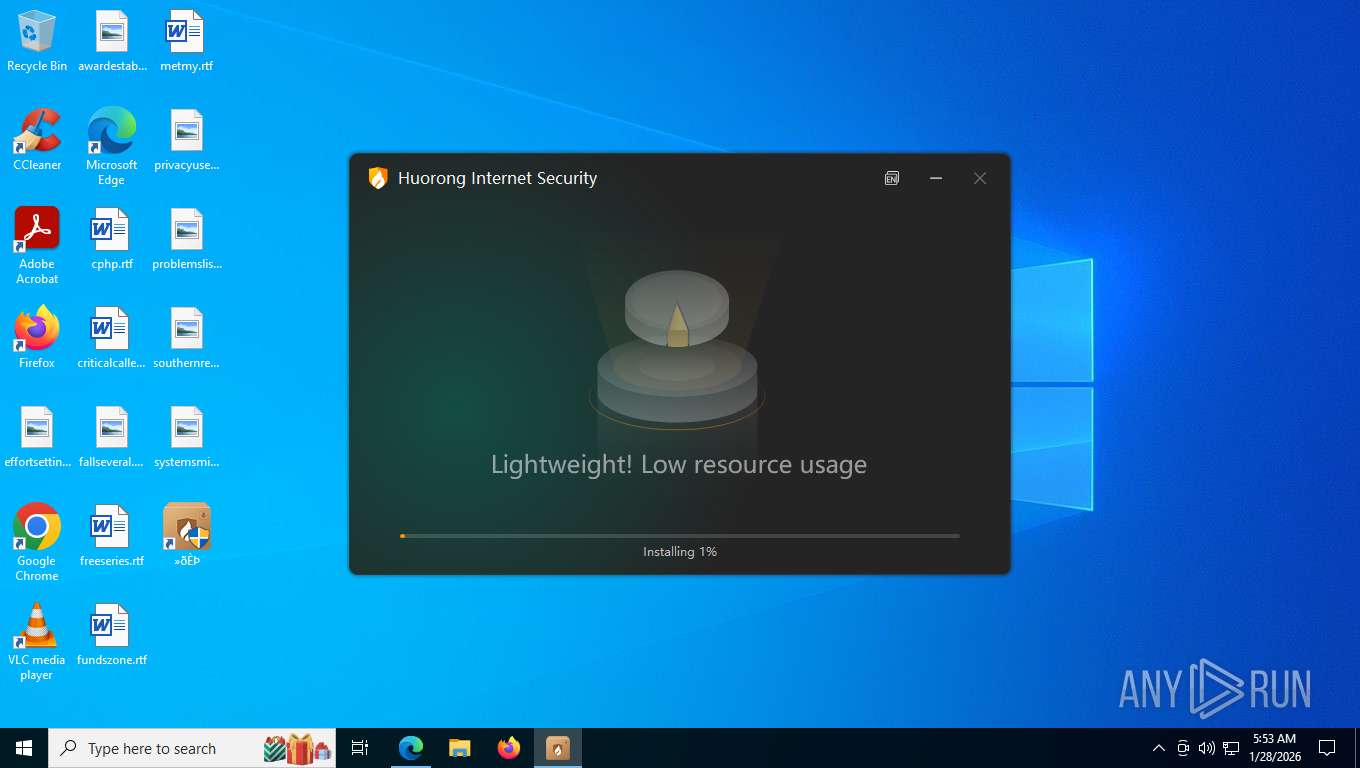
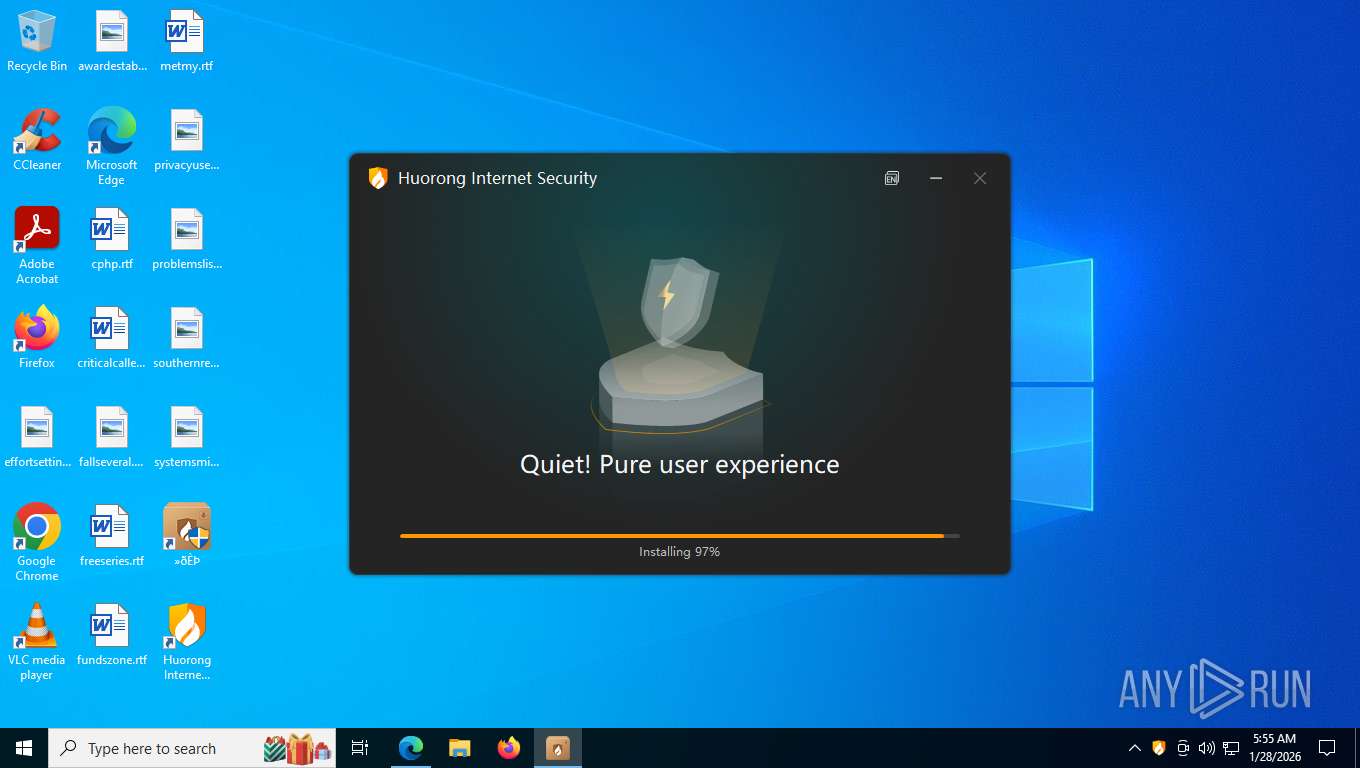
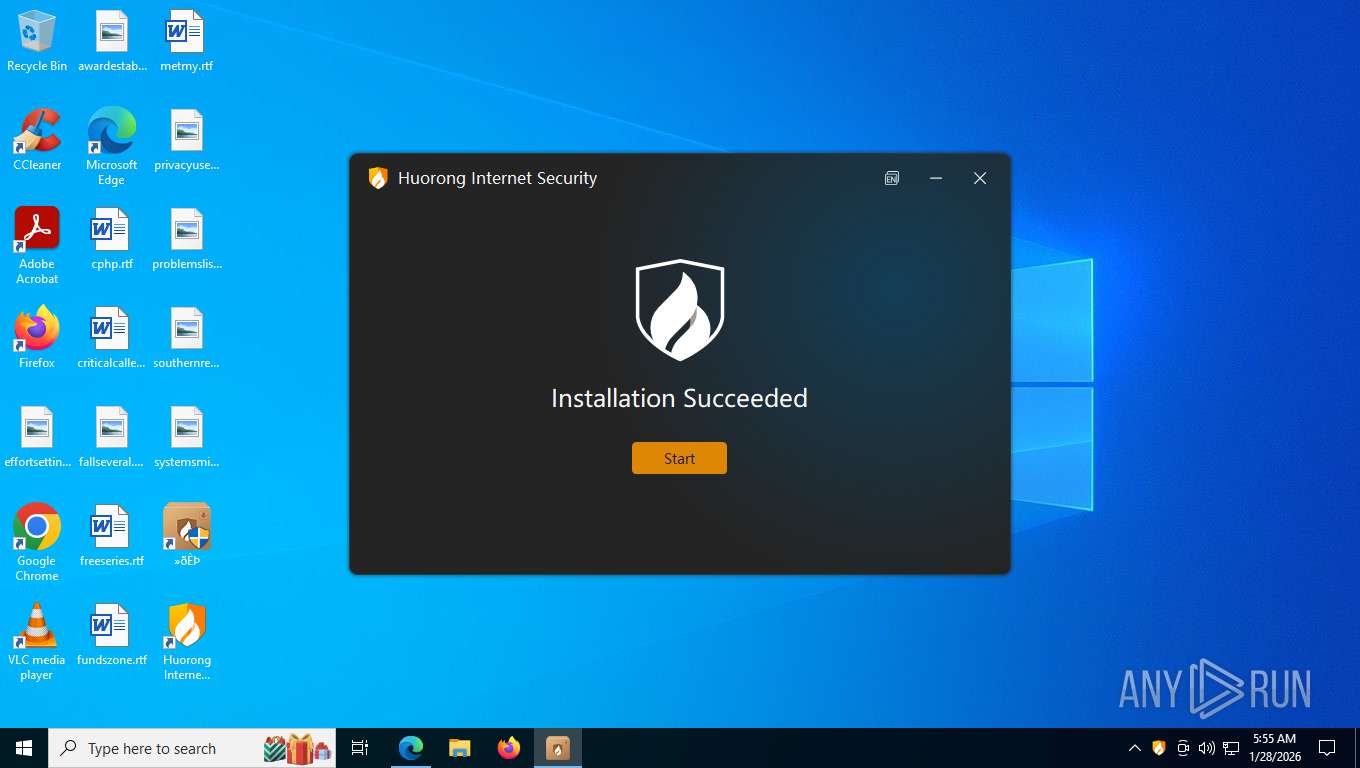
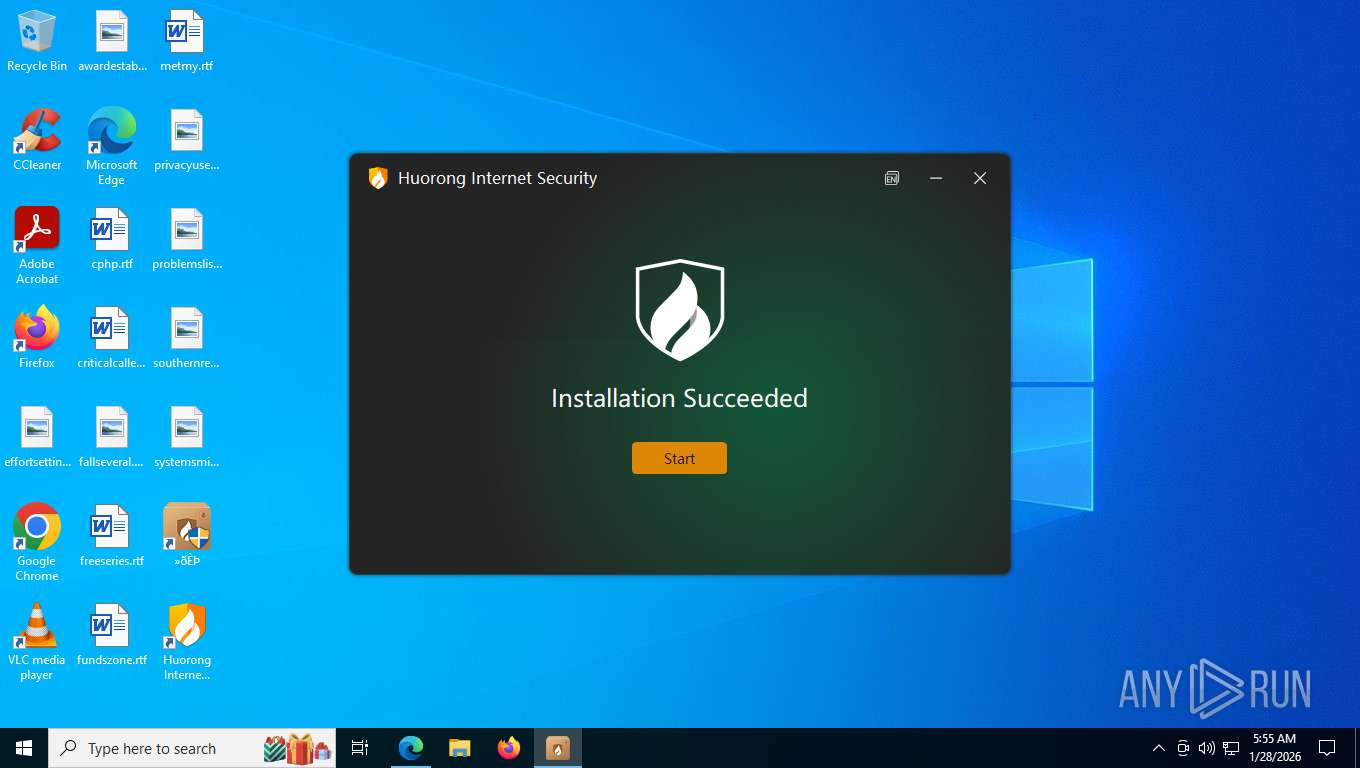
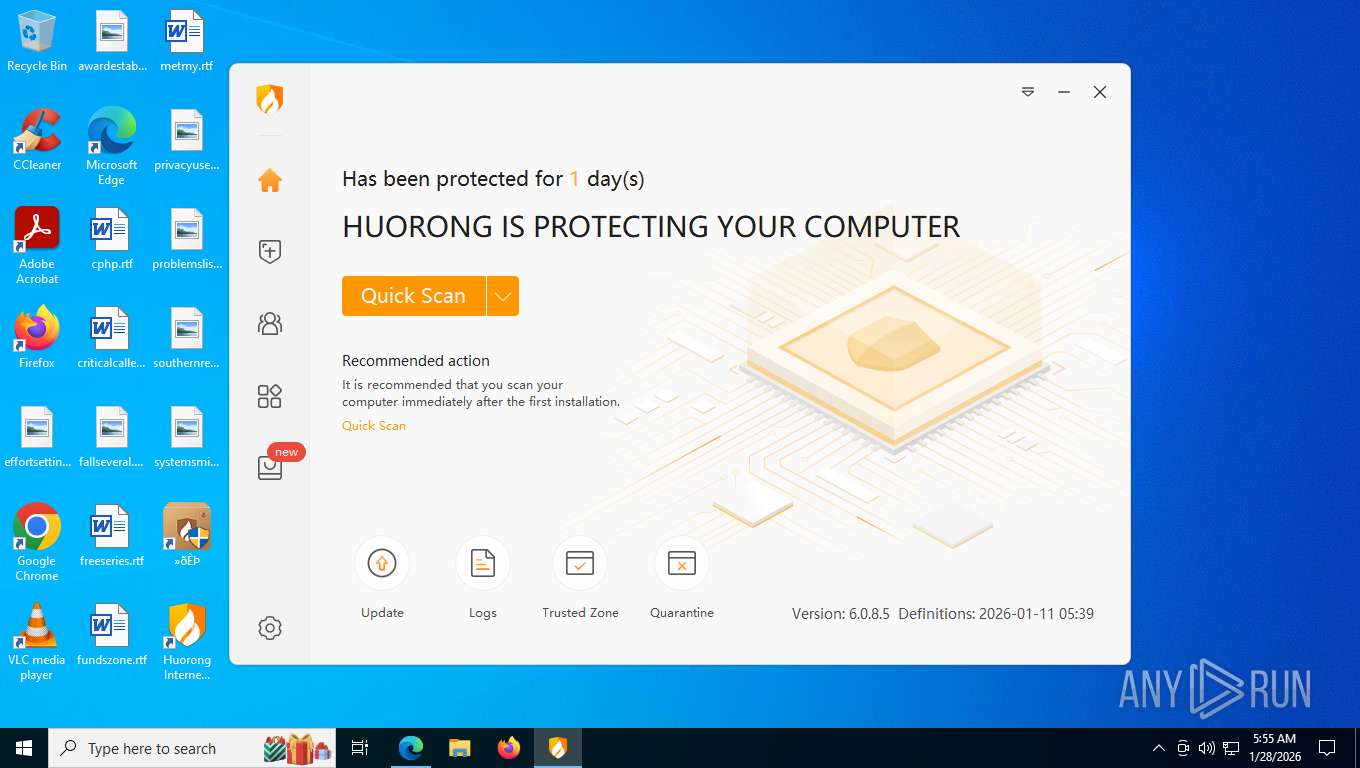
Manual execution by a user
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 4544)
- HipsMain.exe (PID: 6396)
- HipsTray.exe (PID: 4684)
Reads the machine GUID from the registry
- XLGame.exe (PID: 5496)
- XLGame.exe (PID: 7472)
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
- HRUpdate.exe (PID: 4544)
- HipsMain.exe (PID: 6396)
There is functionality for taking screenshot (YARA)
- Hsjrgniuwsdkortgnie.exe (PID: 6536)
- rundll32.exe (PID: 5520)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
Creates files in the program directory
- rundll32.exe (PID: 5520)
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- LocalUpgrade.exe (PID: 8960)
- HRUpdate.exe (PID: 3796)
- HipsDaemon.exe (PID: 9056)
- HipsTray.exe (PID: 756)
- HipsTray.exe (PID: 8496)
- HipsDaemon.exe (PID: 4008)
- HipsMain.exe (PID: 6396)
Manages system restore points
- SrTasks.exe (PID: 8276)
Checks proxy server information
- slui.exe (PID: 5112)
Process checks computer location settings
- HRUpdate.exe (PID: 3796)
- HipsMain.exe (PID: 6396)
Launching a file from a Registry key
- HRUpdate.exe (PID: 3796)
Creates a software uninstall entry
- sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe (PID: 272)
- HRUpdate.exe (PID: 4544)
Reads the time zone
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Reads CPU info
- HipsDaemon.exe (PID: 9056)
- HipsDaemon.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
255
Monitored processes
91
Malicious processes
12
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
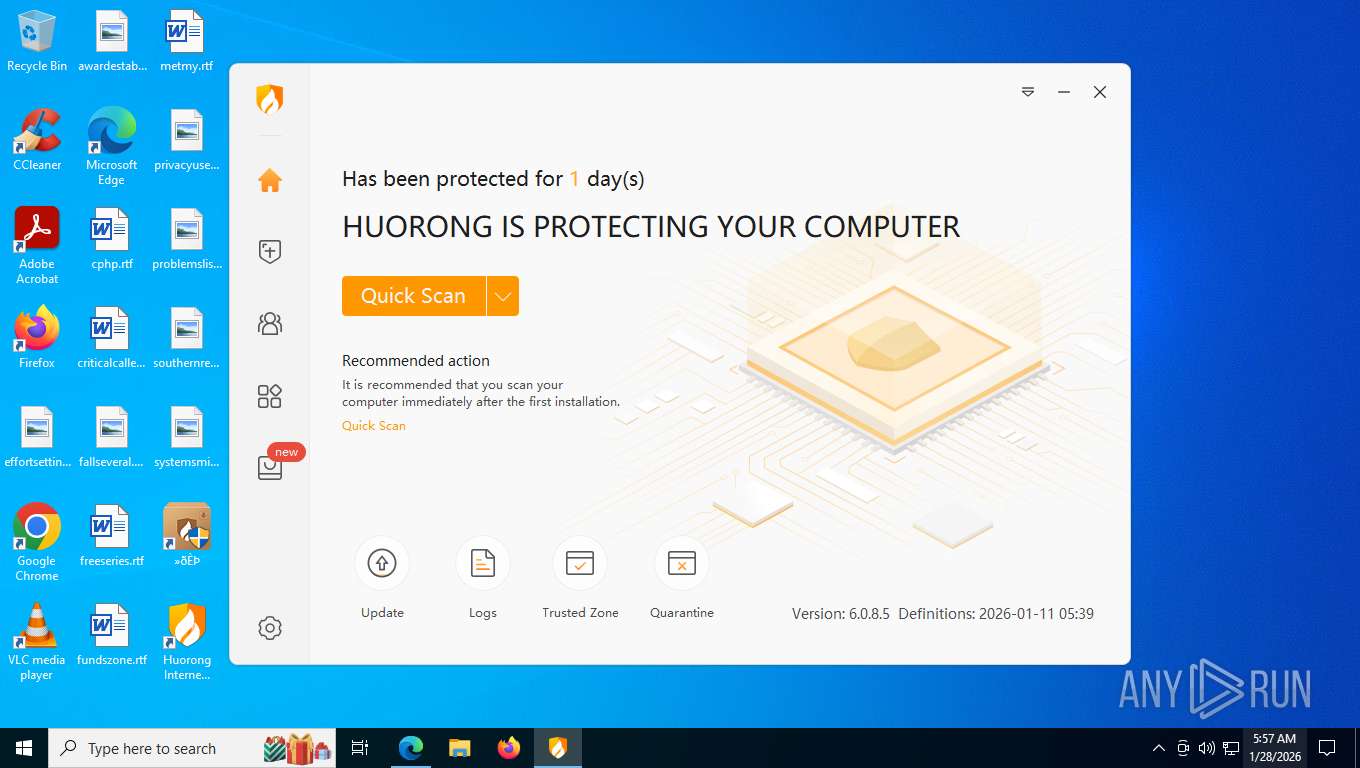
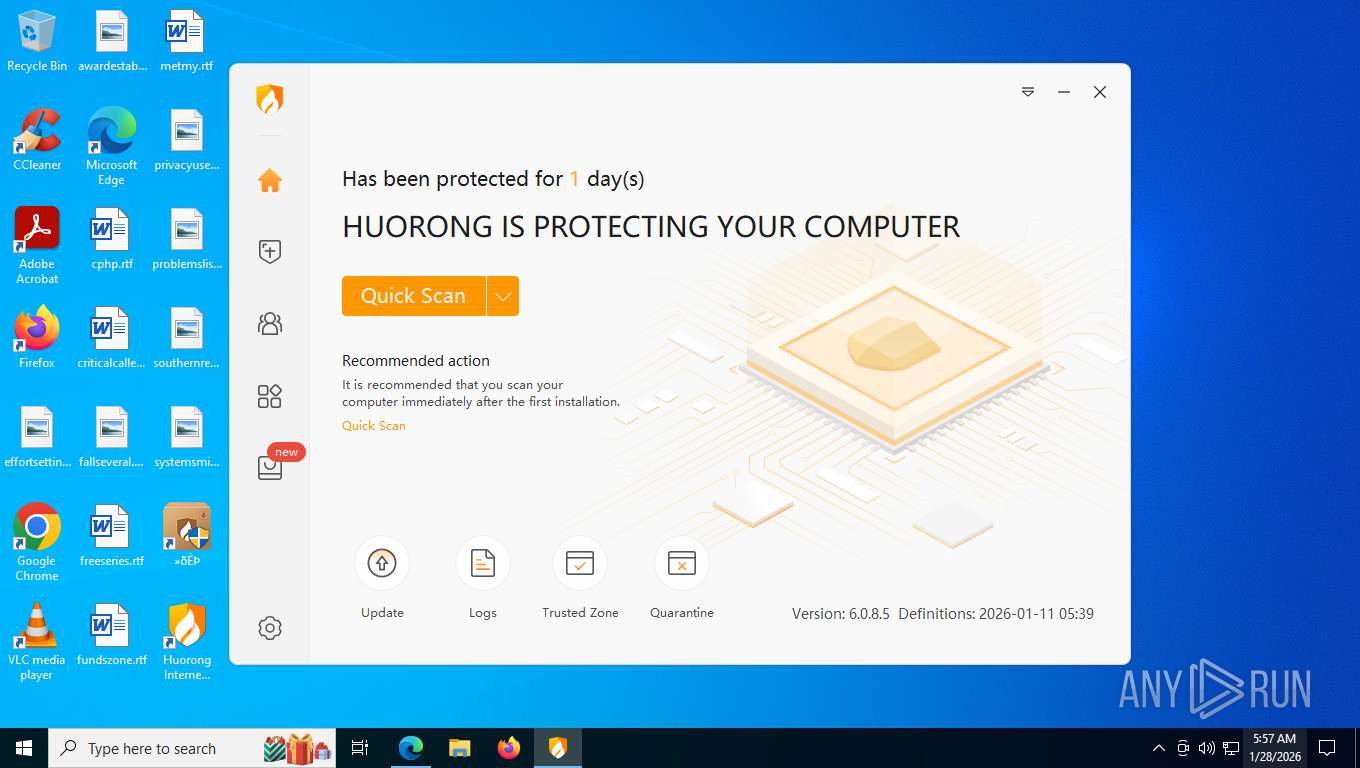
| 272 | "C:\Users\admin\AppData\Roaming\sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe" | C:\Users\admin\AppData\Roaming\sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe | explorer.exe | ||||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Internet Security Exit code: 0 Version: 6.0.8.5 Modules
| |||||||||||||||
| 676 | /s "C:\Program Files\Huorong\Sysdiag\bin\x86\HRShell.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | "C:\Program Files\Huorong\Sysdiag\\bin\HipsTray.exe" | C:\Program Files\Huorong\Sysdiag\bin\HipsTray.exe | — | HipsDaemon.exe | |||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: MEDIUM Description: Huorong Internet Security Tray Exit code: 0 Version: 6,0,0,0 Modules
| |||||||||||||||
| 876 | "C:\WINDOWS\explorer.exe" "C:\Program Files\Huorong\Sysdiag\bin\HipsMain.exe" | C:\Windows\explorer.exe | — | sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.22566\Hsjrgniuwsdkortgnie.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3040.22566\Hsjrgniuwsdkortgnie.exe | — | WinRAR.exe | |||||||||||
User: admin Company: HUORONG Integrity Level: MEDIUM Description: HUORONGR Exit code: 3221226540 Version: 3.7.13.8 Modules
| |||||||||||||||
| 1792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5312,i,4632105426236380209,6875513971876071339,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5252 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1876 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | C:\WINDOWS\system32\regsvr32 /s "C:\Program Files\Huorong\Sysdiag\bin\x86\HrShredShell.dll" | C:\Windows\System32\regsvr32.exe | — | sysdiag-all-x64-6.0.8.5-2026.01.11.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6036,i,4632105426236380209,6875513971876071339,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4384 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2256 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6768,i,4632105426236380209,6875513971876071339,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6740 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
2 220
Read events
2 212
Write events
8
Delete events
0
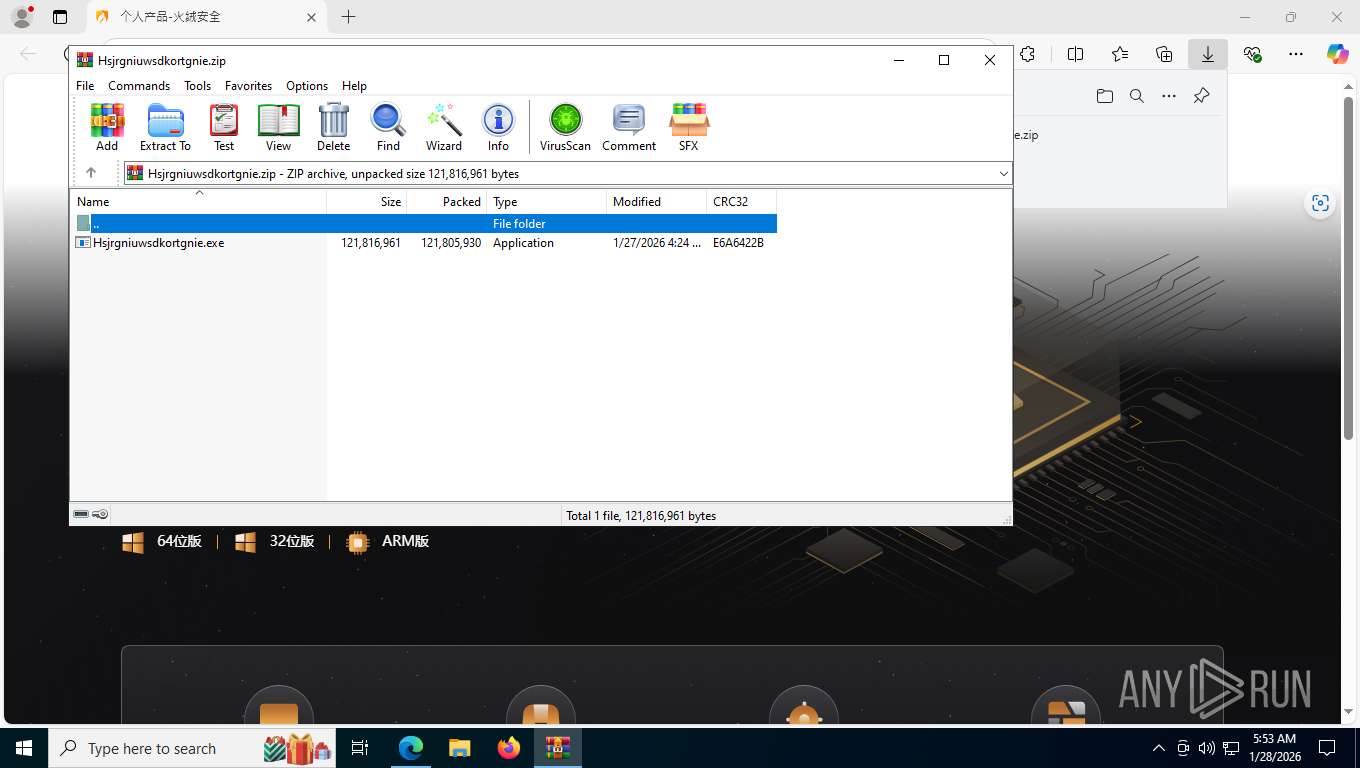
Modification events
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Hsjrgniuwsdkortgnie.zip | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
94
Suspicious files
1 029
Text files
350
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1b4497.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1b4497.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1b4497.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1b44a6.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1b44d5.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
145
TCP/UDP connections
173
DNS requests
92
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8648 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
8648 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.87 Kb | whitelisted |
8648 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Nm4WkrDV8En2l6SNhlLNYU9AHjDIfBYkYOKAOEyo4NM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
8648 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
8648 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | binary | 82 b | whitelisted |
8648 | msedge.exe | GET | 200 | 206.238.40.60:443 | https://ncewbiubfie.cyou/ | unknown | html | 115 Kb | unknown |
8648 | msedge.exe | GET | 200 | 206.238.40.60:443 | https://ncewbiubfie.cyou/%E4%B8%AA%E4%BA%BA%E4%BA%A7%E5%93%81-%E7%81%AB%E7%BB%92%E5%AE%89%E5%85%A8_files/iconfont.css | unknown | text | 917 b | unknown |
8648 | msedge.exe | GET | 200 | 206.238.40.60:443 | https://ncewbiubfie.cyou/%E4%B8%AA%E4%BA%BA%E4%BA%A7%E5%93%81-%E7%81%AB%E7%BB%92%E5%AE%89%E5%85%A8_files/public.css | unknown | text | 95.5 Kb | unknown |
8648 | msedge.exe | GET | 200 | 206.238.40.60:443 | https://ncewbiubfie.cyou/%E4%B8%AA%E4%BA%BA%E4%BA%A7%E5%93%81-%E7%81%AB%E7%BB%92%E5%AE%89%E5%85%A8_files/main.css | unknown | text | 128 Kb | unknown |
8648 | msedge.exe | GET | 200 | 206.238.40.60:443 | https://ncewbiubfie.cyou/%E4%B8%AA%E4%BA%BA%E4%BA%A7%E5%93%81-%E7%81%AB%E7%BB%92%E5%AE%89%E5%85%A8_files/base-v3.0.min.css | unknown | text | 19.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.204.147:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7768 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3500 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8648 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8648 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8648 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8648 | msedge.exe | 206.238.40.60:443 | ncewbiubfie.cyou | TERAEXCH | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ncewbiubfie.cyou |
| malicious |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
cdn-www.huorong.cn |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | INFO [ANY.RUN] Replicated HTML Page observed (saved from) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
8648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
8648 | msedge.exe | Misc activity | ET INFO Observed Cloudflare R2 Public Bucket (r2 .dev) Domain in TLS SNI |
8648 | msedge.exe | Misc activity | ET INFO Observed Cloudflare R2 Public Bucket (r2 .dev) Domain in TLS SNI |
8648 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
8648 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare R2 Public Bucket (r2 .dev) Domain |
8648 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
8648 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare R2 Public Bucket (r2 .dev) Domain |
Process | Message |
|---|---|
regsvr32.exe | DllUnregisterServer |
regsvr32.exe | DllUnregisterServer |
regsvr32.exe | DllUnregisterServer |
regsvr32.exe | DllUnregisterServer |
regsvr32.exe | DllUnregisterServer |
regsvr32.exe | DllUnregisterServer |