| File name: | dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c |
| Full analysis: | https://app.any.run/tasks/82838662-afb1-45a4-82b4-7398117058e6 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 12, 2024, 14:16:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | D317EE086EBECCF5E01E002CA6B0EAD9 |
| SHA1: | 48E8C5846D9C67649B3C2FB8D76AA951828DD84E |
| SHA256: | DFDC0318F3DC5BA3F960B1F338B638CD9645856D2A2AF8AA33EA0F9979A9CA4C |
| SSDEEP: | 6144:OnBhwyNf9MLJOUgUKZRQXRLr13e+Y2I+uvecTIJNcj0OtAWz3:YwyNFMLJOOKq3e+Y2I+CyJTOx |
MALICIOUS
Connects to the CnC server
- Dctooux.exe (PID: 6308)
AMADEY has been detected (SURICATA)
- Dctooux.exe (PID: 6308)
AMADEY has been detected (YARA)
- Dctooux.exe (PID: 6308)
SUSPICIOUS
Executable content was dropped or overwritten
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
Reads security settings of Internet Explorer
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
- Dctooux.exe (PID: 6308)
Starts itself from another location
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
Contacting a server suspected of hosting an CnC
- Dctooux.exe (PID: 6308)
Process requests binary or script from the Internet
- Dctooux.exe (PID: 6308)
The process executes via Task Scheduler
- Dctooux.exe (PID: 6784)
- Dctooux.exe (PID: 6900)
INFO
Reads the computer name
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
- Dctooux.exe (PID: 6308)
Process checks computer location settings
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
- Dctooux.exe (PID: 6308)
Checks supported languages
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
- Dctooux.exe (PID: 6308)
- Dctooux.exe (PID: 6784)
The process uses the downloaded file
- dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe (PID: 6236)
Creates files or folders in the user directory
- Dctooux.exe (PID: 6308)
Create files in a temporary directory
- Dctooux.exe (PID: 6308)
Checks proxy server information
- Dctooux.exe (PID: 6308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(6308) Dctooux.exe
C2vitantgroup.com
URLhttp://vitantgroup.com/xmlrpc.php
Version4.18
Options
Drop directory431a343abc
Drop nameDctooux.exe
Strings (113)2016
cmd /C RMDIR /s/q
Comodo
st=s
=
\App
Norton
e1
AVG
" && timeout 1 && del
exe
2019
--
wb
DefaultSettings.YResolution
ProgramData\
:::
VideoID
Rem
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
http://
<d>
2022
Sophos
Programs
lv:
&unit=
------
Dctooux.exe
4.18
POST
%-lu
<c>
Content-Type: application/x-www-form-urlencoded
Doctor Web
\
id:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
360TotalSecurity
Startup
vitantgroup.com
431a343abc
"
Content-Type: application/octet-stream
Content-Type: multipart/form-data; boundary=----
cred.dll|clip.dll|
S-%lu-
rb
rundll32.exe
0123456789
GetNativeSystemInfo
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
" && ren
/xmlrpc.php
d1
ESET
vs:
"
------
sd:
WinDefender
dll
e0
%USERPROFILE%
Panda Security
SOFTWARE\Microsoft\Windows NT\CurrentVersion
cmd
-unicode-
shell32.dll
ProductName
&&
shutdown -s -t 0
|
/Plugins/
Bitdefender
\0000
Content-Disposition: form-data; name="data"; filename="
os:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
av:
-%lu
Avira
GET
Kaspersky Lab
#
ps1
-executionpolicy remotesigned -File "
DefaultSettings.XResolution
Powershell.exe
bi:
https://
random
pc:
un:
abcdefghijklmnopqrstuvwxyz0123456789-_
ar:
Main
"taskkill /f /im "
ComputerName
AVAST Software
SYSTEM\ControlSet001\Services\BasicDisplay\Video
r=
.jpg
CurrentBuild
og:
dm:
?scr=1
kernel32.dll
/k
&& Exit"
+++
rundll32
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:07 18:15:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 337408 |
| InitializedDataSize: | 114176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20be9 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
125
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6236 | "C:\Users\admin\Desktop\dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe" | C:\Users\admin\Desktop\dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6308 | "C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe" | C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe | dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(6308) Dctooux.exe C2vitantgroup.com URLhttp://vitantgroup.com/xmlrpc.php Version4.18 Options Drop directory431a343abc Drop nameDctooux.exe Strings (113)2016 cmd /C RMDIR /s/q Comodo st=s = \App Norton e1 AVG " && timeout 1 && del exe 2019 -- wb DefaultSettings.YResolution ProgramData\ ::: VideoID Rem SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce SOFTWARE\Microsoft\Windows\CurrentVersion\Run http:// <d> 2022 Sophos Programs lv: &unit= ------ Dctooux.exe 4.18 POST %-lu <c> Content-Type: application/x-www-form-urlencoded Doctor Web \ id: SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders 360TotalSecurity Startup vitantgroup.com 431a343abc "
Content-Type: application/octet-stream Content-Type: multipart/form-data; boundary=---- cred.dll|clip.dll| S-%lu- rb rundll32.exe 0123456789 GetNativeSystemInfo SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ " && ren /xmlrpc.php d1 ESET vs: " ------ sd: WinDefender dll e0 %USERPROFILE% Panda Security SOFTWARE\Microsoft\Windows NT\CurrentVersion cmd -unicode- shell32.dll ProductName && shutdown -s -t 0 | /Plugins/ Bitdefender \0000 Content-Disposition: form-data; name="data"; filename=" os: SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders av: -%lu Avira GET Kaspersky Lab # ps1 -executionpolicy remotesigned -File " DefaultSettings.XResolution Powershell.exe bi: https:// random pc: un: abcdefghijklmnopqrstuvwxyz0123456789-_ ar: Main "taskkill /f /im " ComputerName AVAST Software SYSTEM\ControlSet001\Services\BasicDisplay\Video r= .jpg CurrentBuild og: dm: ?scr=1 kernel32.dll /k && Exit" +++ rundll32 | |||||||||||||||
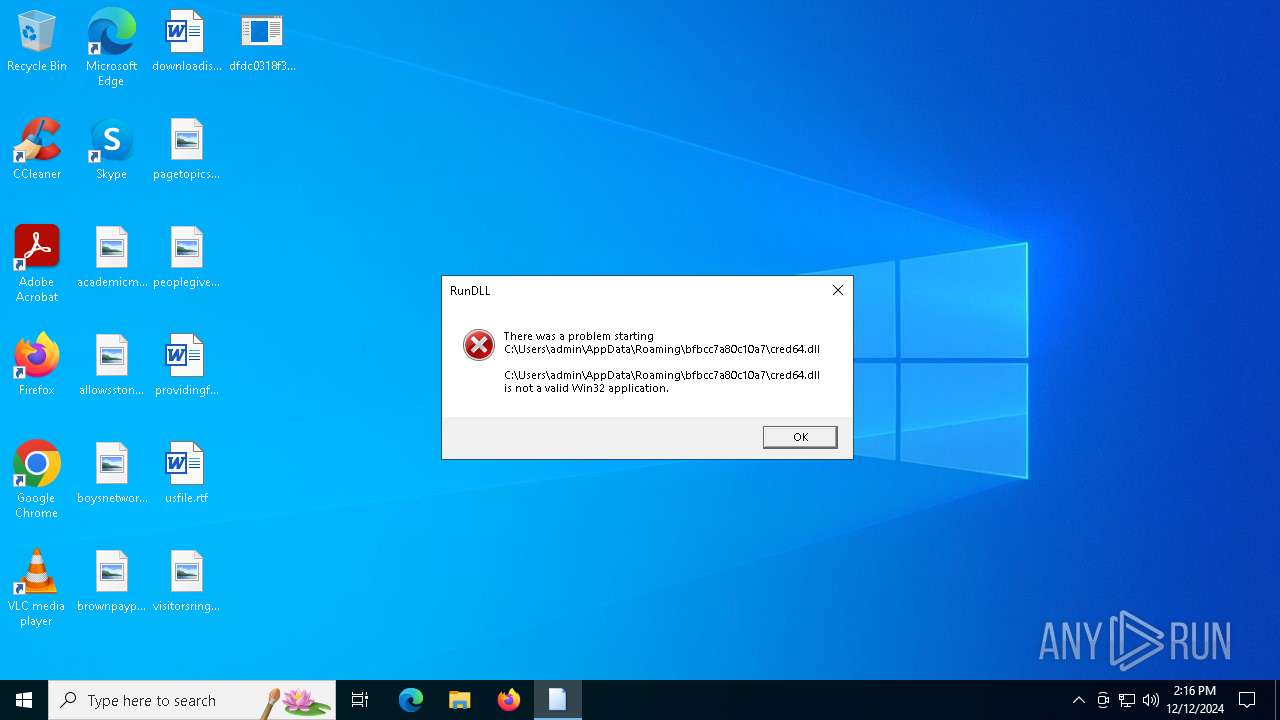
| 6716 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\bfbcc7a80c10a7\cred64.dll, Main | C:\Windows\SysWOW64\rundll32.exe | — | Dctooux.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
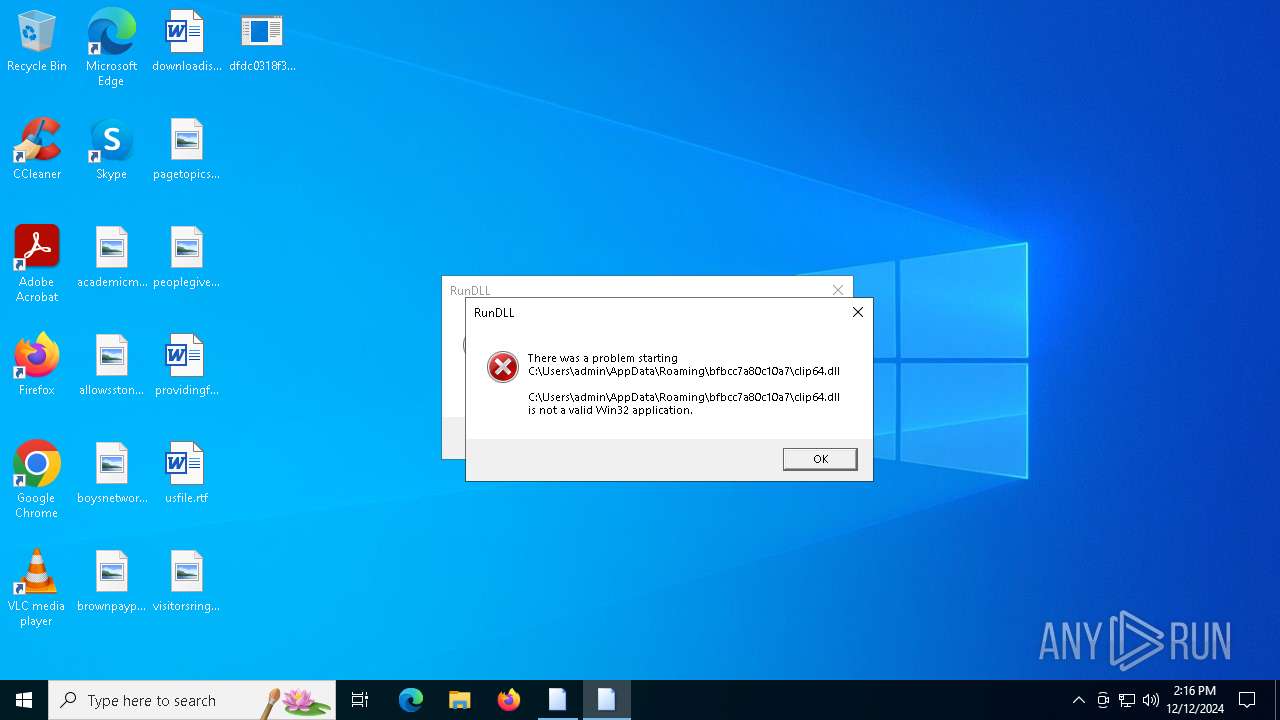
| 6756 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\bfbcc7a80c10a7\clip64.dll, Main | C:\Windows\SysWOW64\rundll32.exe | — | Dctooux.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6784 | "C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe" | C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6900 | "C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe" | C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 306
Read events
1 303
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6308) Dctooux.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6308) Dctooux.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6308) Dctooux.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6308 | Dctooux.exe | C:\Users\admin\AppData\Roaming\bfbcc7a80c10a7\clip64.dll | html | |
MD5:17F47E623CF388EA8FECB7DA0960A7F4 | SHA256:E6ED2B9BBA6CED4988B01976231CEBE36EF2649E7E803C875046456BE6612796 | |||
| 6308 | Dctooux.exe | C:\Users\admin\AppData\Roaming\bfbcc7a80c10a7\cred64.dll | html | |
MD5:B7B2ACDCDEE3AF9EEE03C7306149471F | SHA256:95327E18503CE4F7FF387DD092F32E0F86175799A5C5D7F5C088921918AB2A1E | |||
| 6236 | dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe | C:\Users\admin\AppData\Local\Temp\431a343abc\Dctooux.exe | executable | |
MD5:D317EE086EBECCF5E01E002CA6B0EAD9 | SHA256:DFDC0318F3DC5BA3F960B1F338B638CD9645856D2A2AF8AA33EA0F9979A9CA4C | |||
| 6236 | dfdc0318f3dc5ba3f960b1f338b638cd9645856d2a2af8aa33ea0f9979a9ca4c.exe | C:\Windows\Tasks\Dctooux.job | binary | |
MD5:9CA104752C386098FC45BE19DA520312 | SHA256:3D19B861FBDA19A78946E7B5BC554857E4ECC24C30F04383994FC0E2DFA51182 | |||
| 6308 | Dctooux.exe | C:\Users\admin\AppData\Local\Temp\693682860607 | image | |
MD5:7B172AC94F5395E9820D8AC6A40F53BE | SHA256:6C4CED4AC5D60AC56351001208F9E97BAAD9C7424D26BA54A7C64AD3A38B0E3E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
29
DNS requests
9
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6308 | Dctooux.exe | POST | 200 | 185.68.16.133:80 | http://vitantgroup.com/xmlrpc.php | unknown | — | — | malicious |
6072 | svchost.exe | GET | 200 | 2.16.164.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6308 | Dctooux.exe | POST | 200 | 185.68.16.133:80 | http://vitantgroup.com/xmlrpc.php?scr=1 | unknown | — | — | malicious |
2632 | RUXIMICS.exe | GET | 200 | 2.16.164.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6072 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6308 | Dctooux.exe | POST | 200 | 185.68.16.133:80 | http://vitantgroup.com/xmlrpc.php | unknown | — | — | malicious |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6308 | Dctooux.exe | GET | 404 | 185.68.16.133:80 | http://vitantgroup.com/Plugins/clip64.dll | unknown | — | — | malicious |
6308 | Dctooux.exe | POST | 200 | 185.68.16.133:80 | http://vitantgroup.com/xmlrpc.php?scr=1 | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6072 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2632 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.96.72:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.19.96.65:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6072 | svchost.exe | 2.16.164.58:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6308 | Dctooux.exe | 185.68.16.133:80 | vitantgroup.com | Hosting Ukraine LTD | UA | malicious |
4712 | MoUsoCoreWorker.exe | 2.16.164.58:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
vitantgroup.com |
| malicious |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6308 | Dctooux.exe | A Network Trojan was detected | ET MALWARE Amadey Bot Activity (POST) M1 |
6308 | Dctooux.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6308 | Dctooux.exe | A Network Trojan was detected | BOTNET [ANY.RUN] Amadey Clipper plugin download request |
6308 | Dctooux.exe | A Network Trojan was detected | ET MALWARE Amadey Bot Activity (POST) M1 |
6308 | Dctooux.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6308 | Dctooux.exe | A Network Trojan was detected | ET MALWARE Amadey Bot Activity (POST) M1 |
6308 | Dctooux.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
1 ETPRO signatures available at the full report