| download: | / |
| Full analysis: | https://app.any.run/tasks/72a899d6-c8cf-40e3-b614-2e8c25875847 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
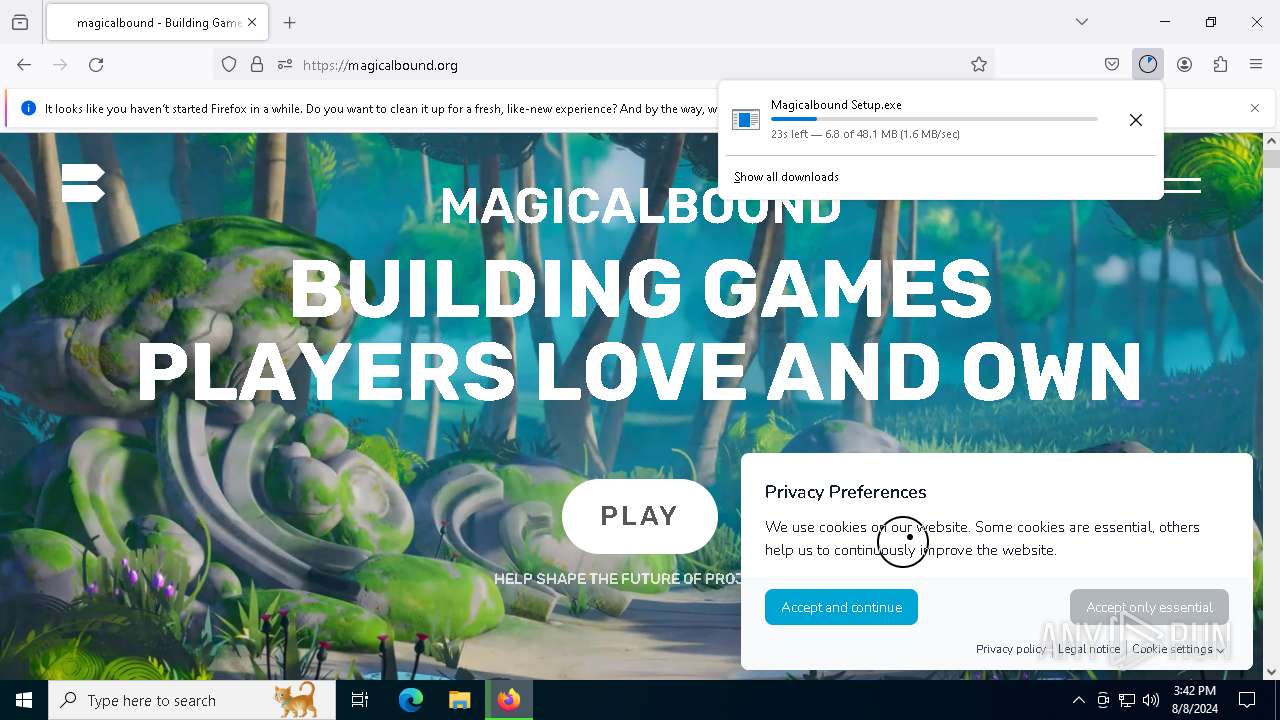
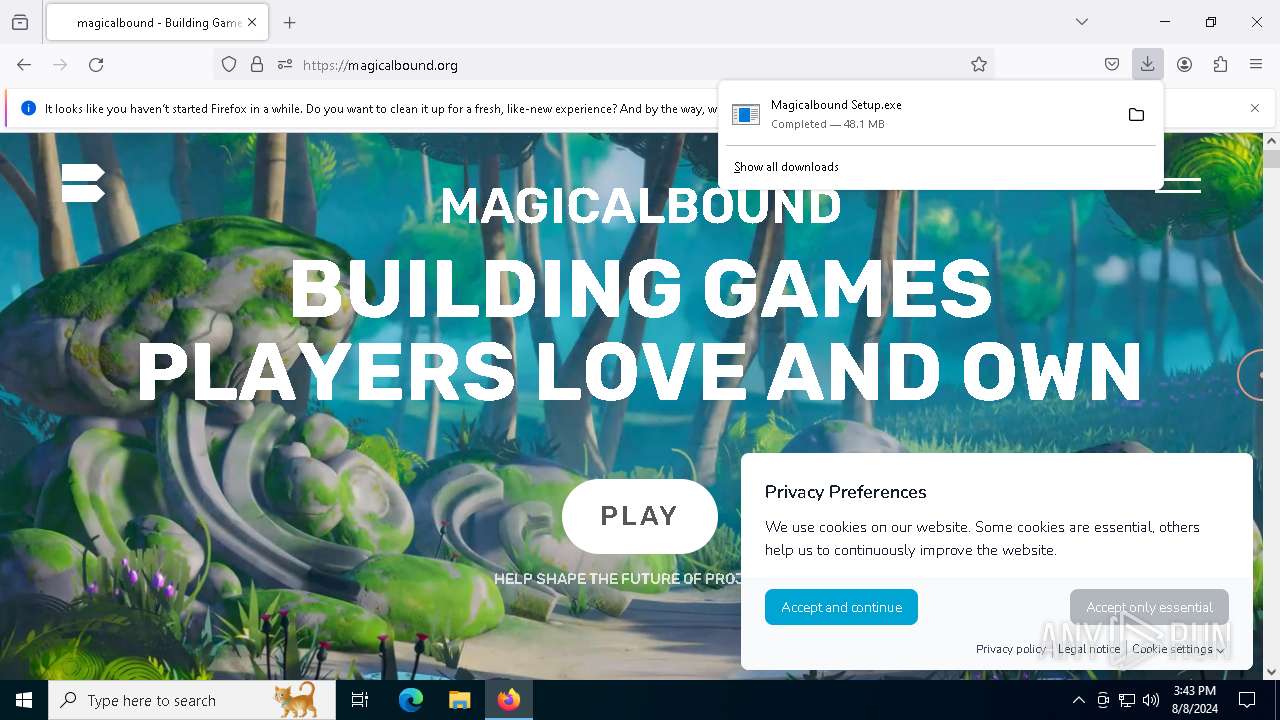
| Analysis date: | August 08, 2024, 15:42:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with very long lines (472) |
| MD5: | 676D3095C1A63E5C3B9F830EB3219A7C |
| SHA1: | 8583641FD94B477FAE43E568E81415FDD05E751A |
| SHA256: | DF5A133C13AC7839794665A641982E88F3C276A464FA02168B3B9BD4F9A4781D |
| SSDEEP: | 1536:jgvuVUfvhmF1GR2OP/nHtDyfC9rbHbpvRGHPfficsw8qW/6tGSKc1emGSKc1ePiR:f2vIF1GR2OP/nHtDyfCJGHPfficsw8qD |
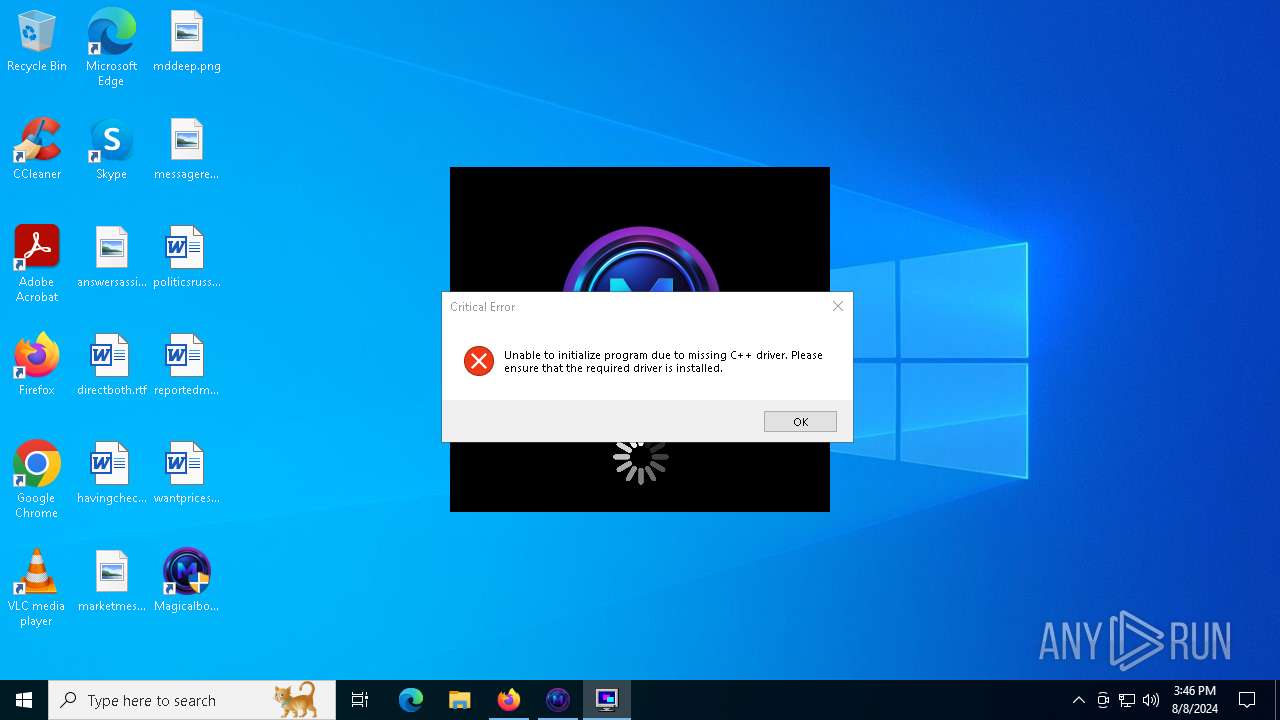
MALICIOUS
Adds path to the Windows Defender exclusion list
- Magicalbound.exe (PID: 5504)
STEALC has been detected (YARA)
- explorer.exe (PID: 4060)
Connects to the CnC server
- explorer.exe (PID: 4060)
Stealers network behavior
- explorer.exe (PID: 4060)
- OOBE-Maintenance.exe (PID: 7336)
STEALC has been detected (SURICATA)
- explorer.exe (PID: 4060)
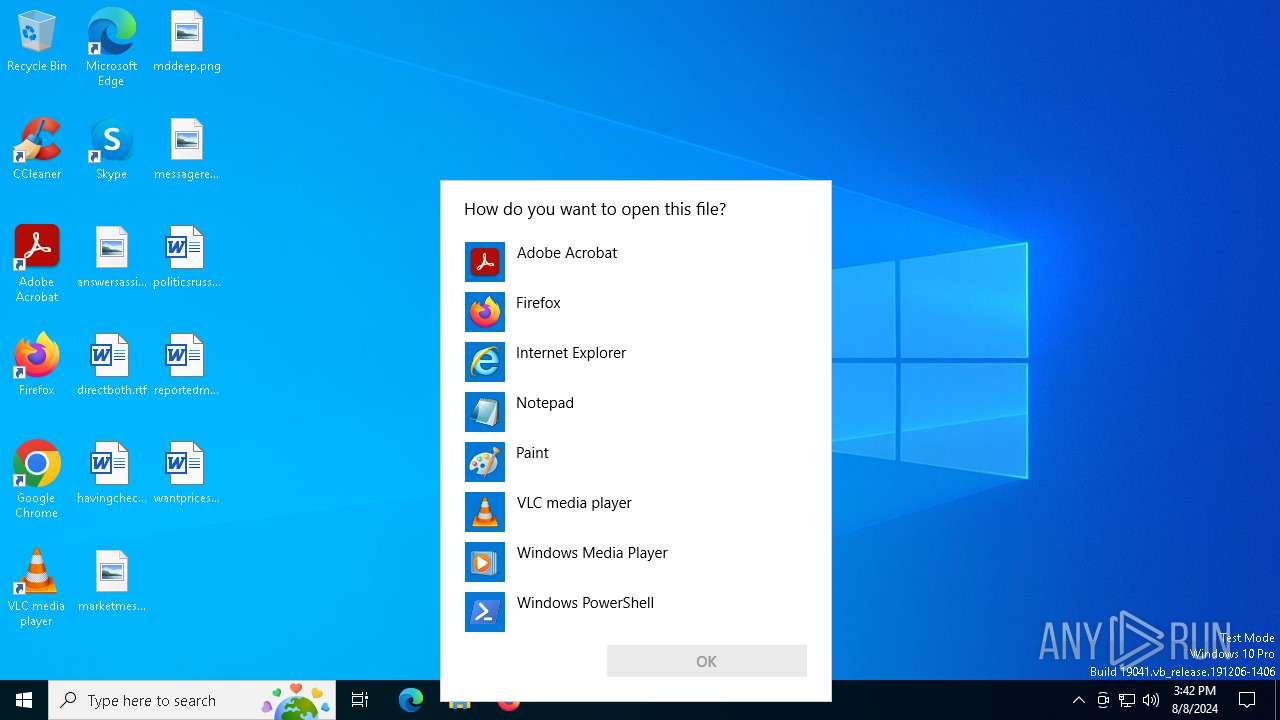
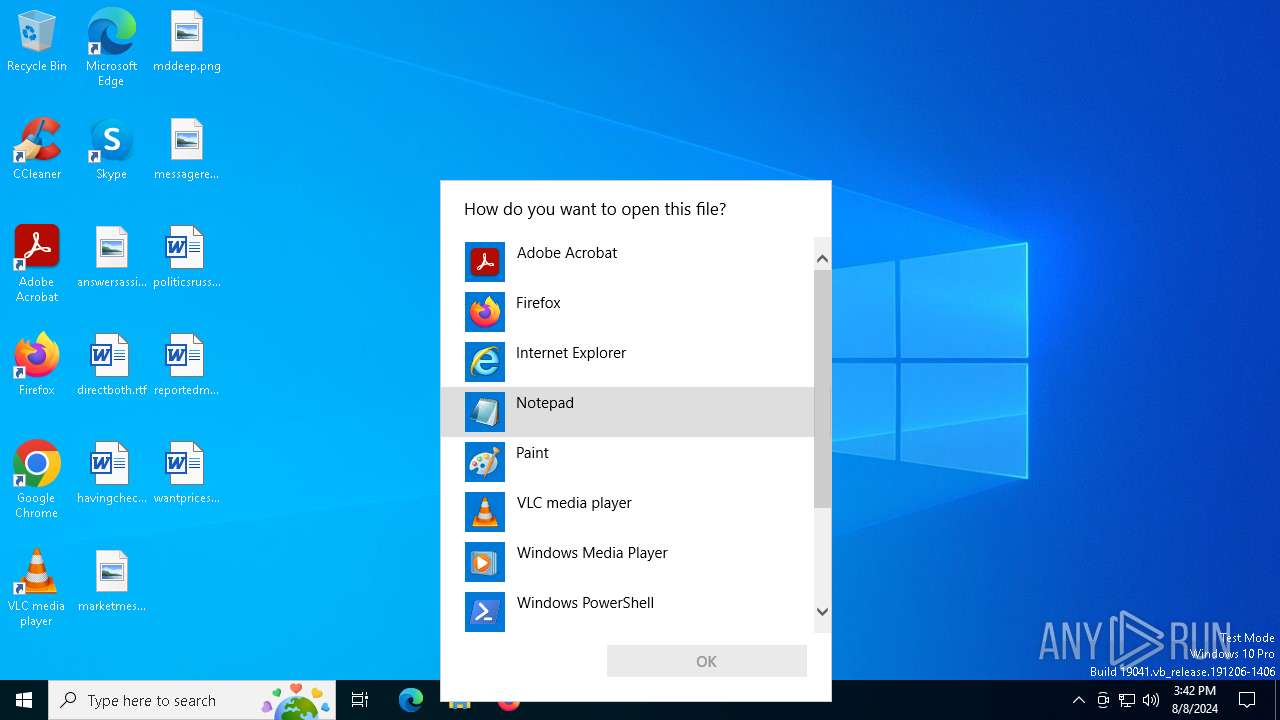
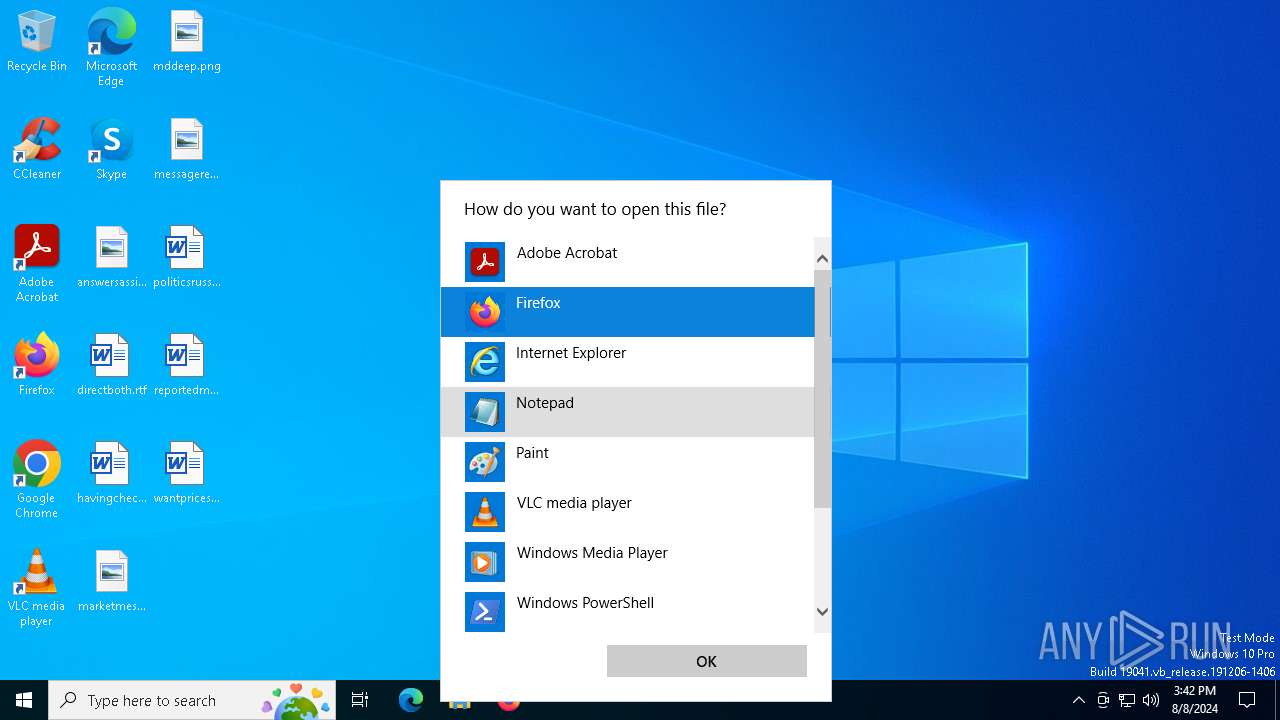
RHADAMANTHYS has been detected (SURICATA)
- OpenWith.exe (PID: 7224)
- OOBE-Maintenance.exe (PID: 7336)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 7336)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 7336)
SUSPICIOUS
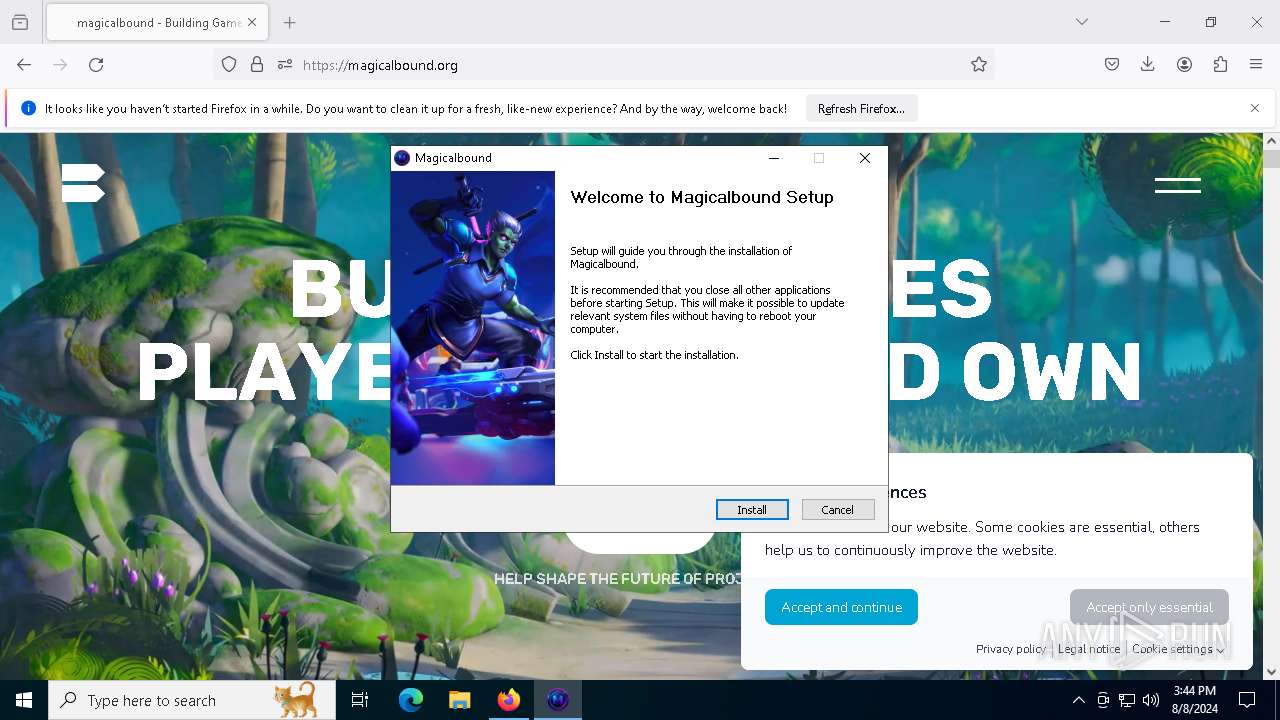
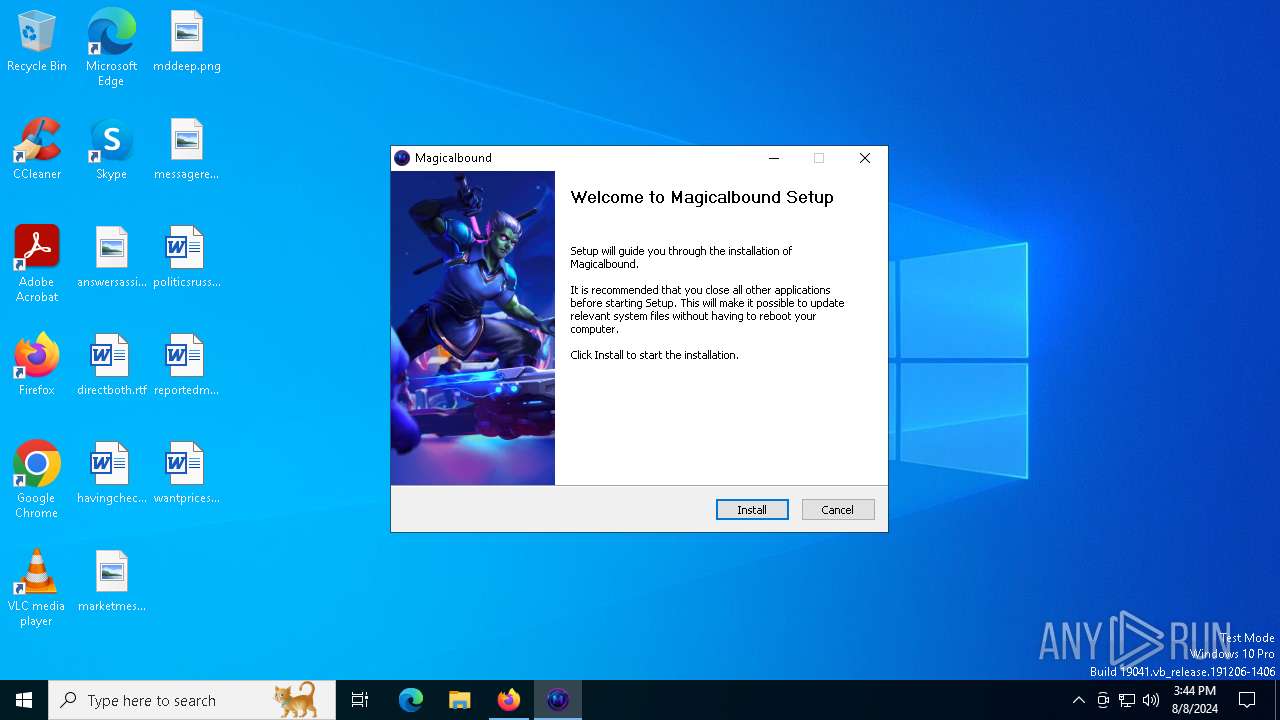
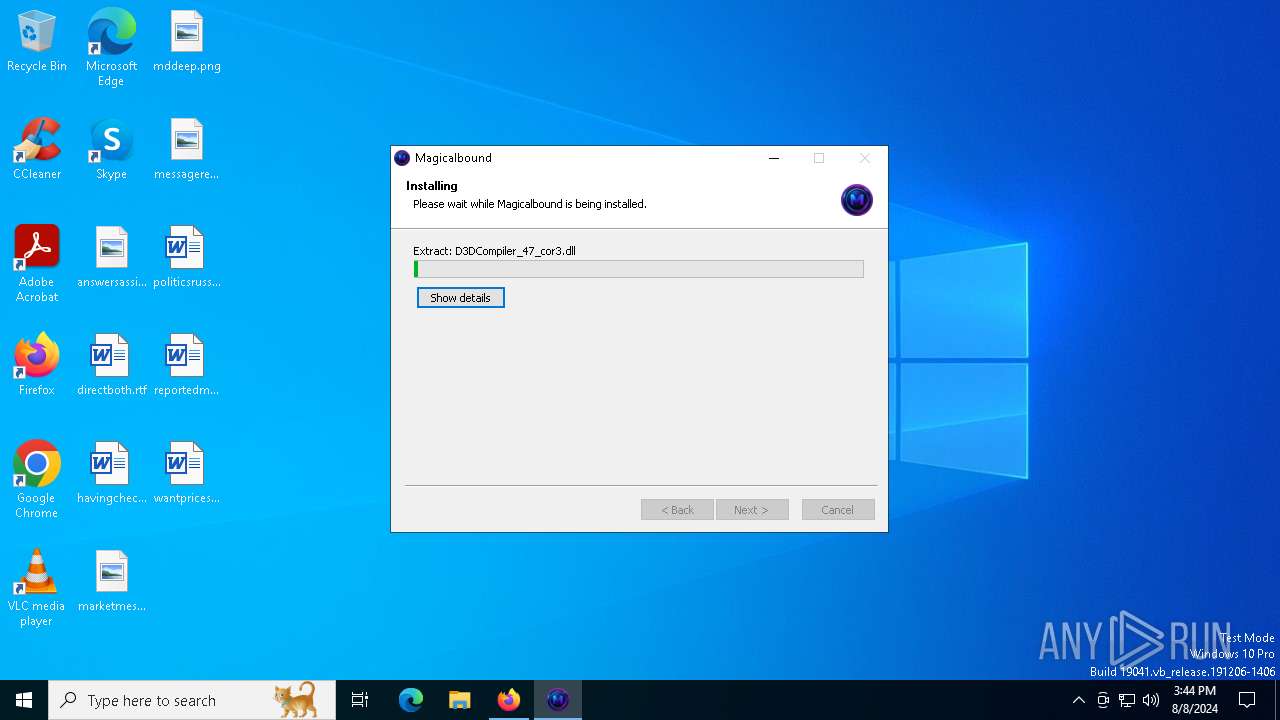
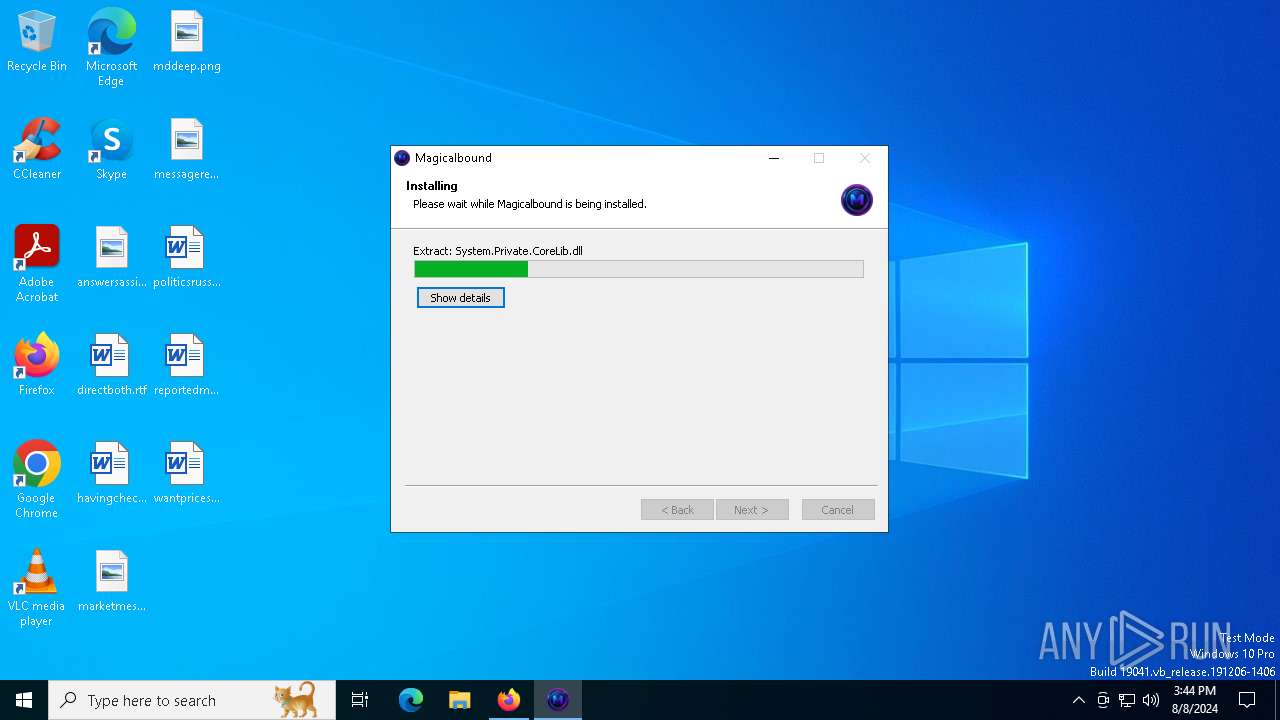
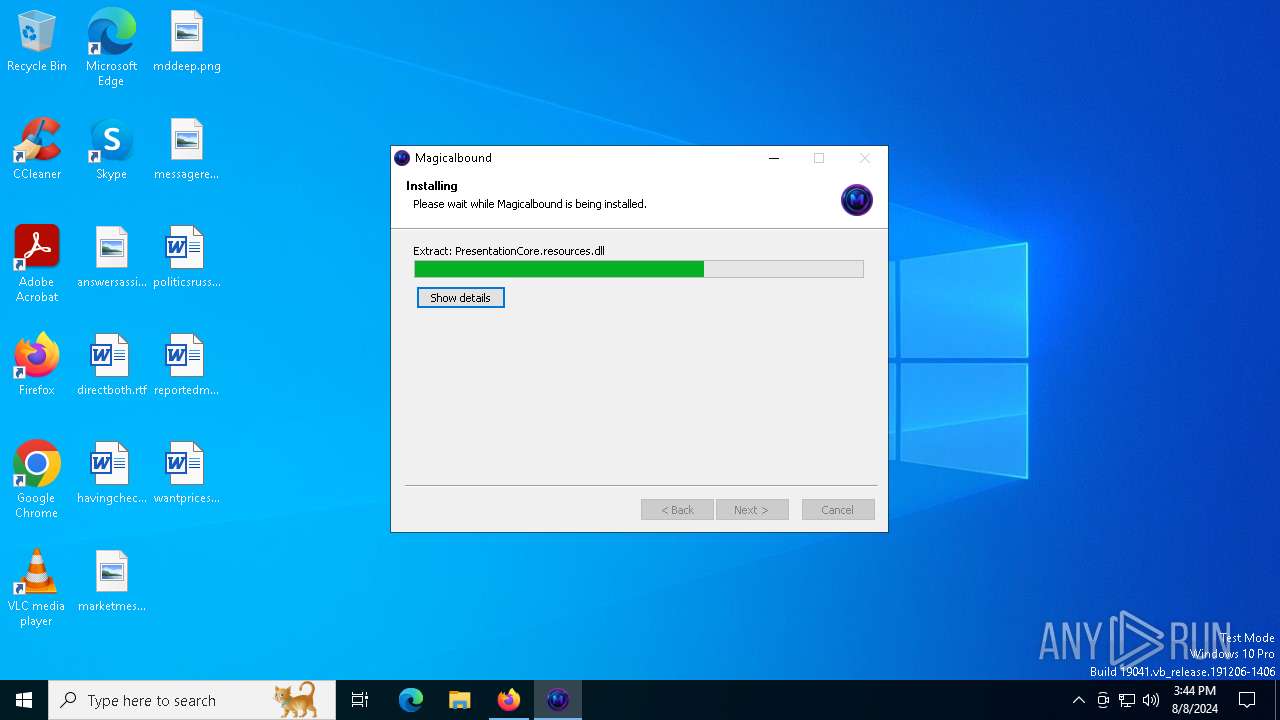
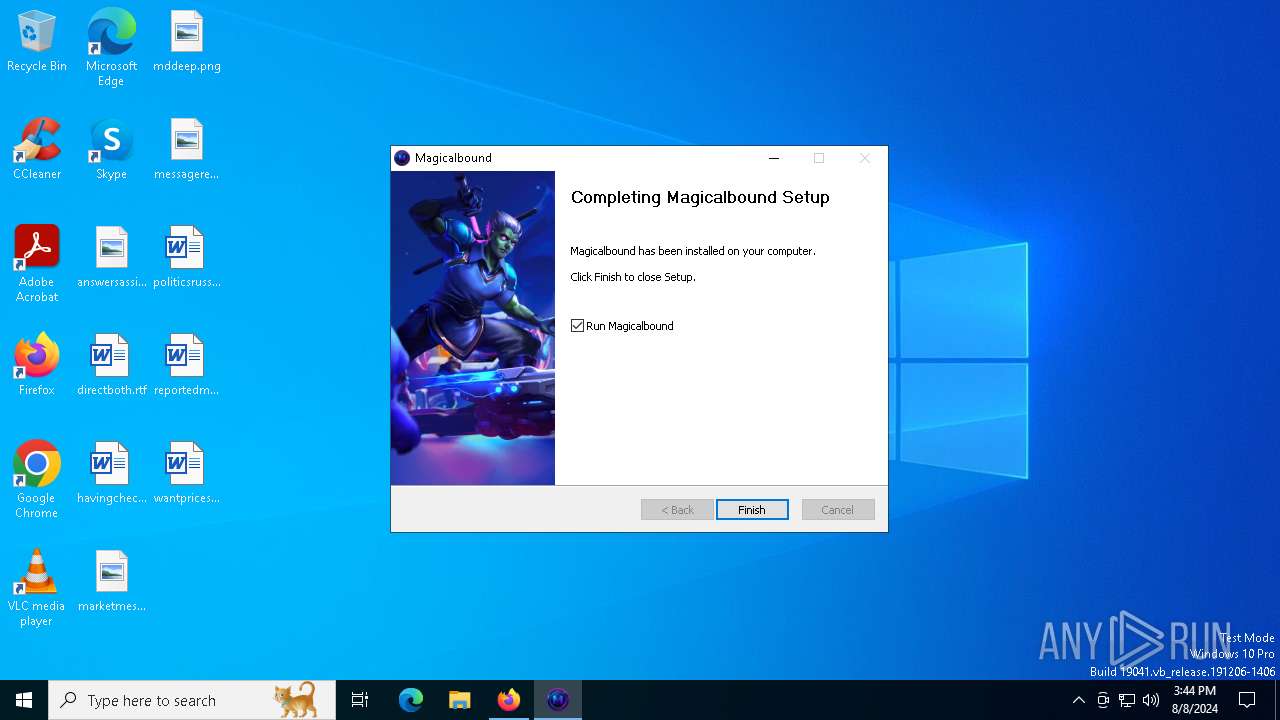
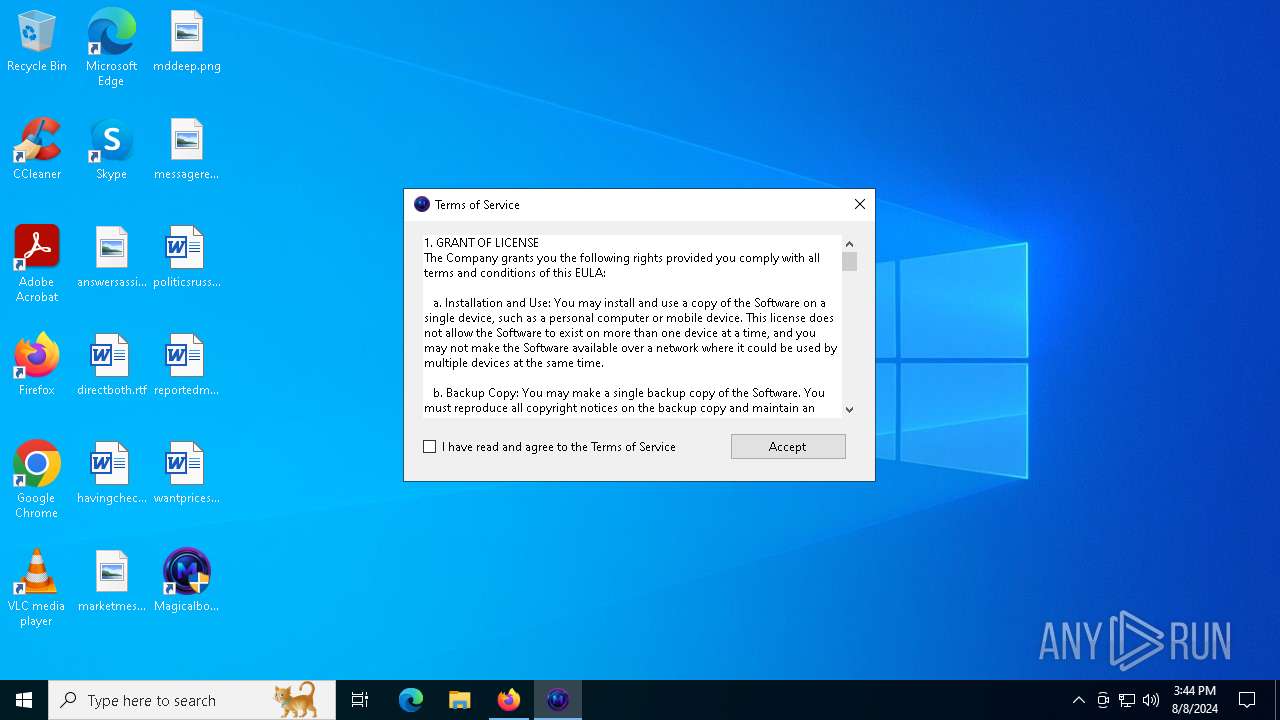
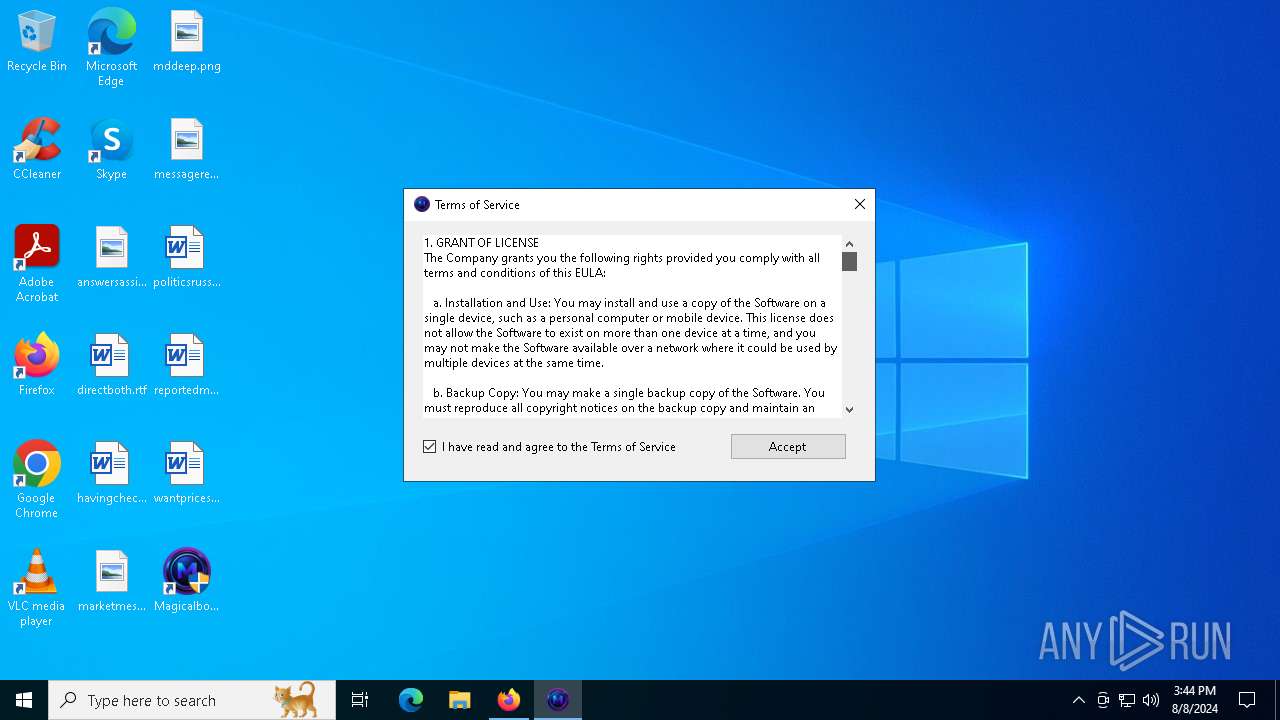
Drops the executable file immediately after the start
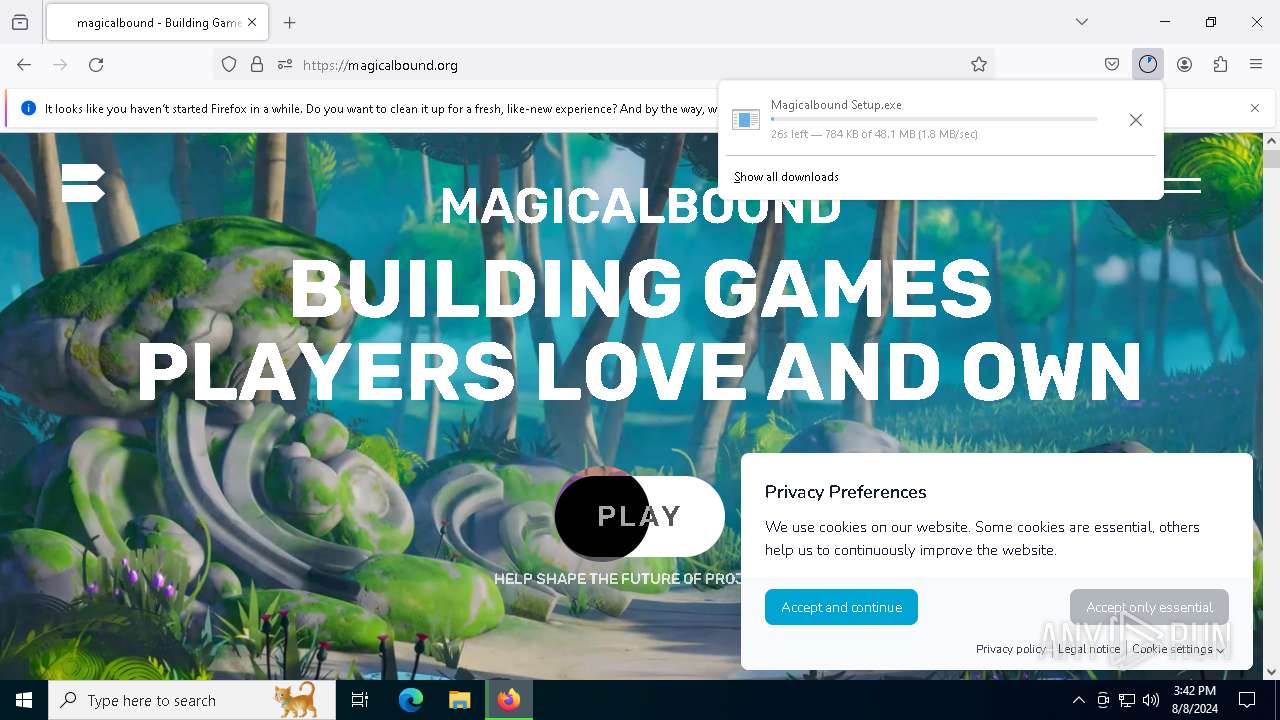
- Magicalbound Setup.exe (PID: 788)
- Magicalbound.exe (PID: 5504)
Executable content was dropped or overwritten
- Magicalbound Setup.exe (PID: 788)
- Magicalbound.exe (PID: 5504)
Checks for external IP
- svchost.exe (PID: 2256)
Process drops legitimate windows executable
- Magicalbound Setup.exe (PID: 788)
The process creates files with name similar to system file names
- Magicalbound Setup.exe (PID: 788)
The process drops C-runtime libraries
- Magicalbound Setup.exe (PID: 788)
Creates a software uninstall entry
- Magicalbound Setup.exe (PID: 788)
Starts POWERSHELL.EXE for commands execution
- Magicalbound.exe (PID: 5504)
Malware-specific behavior (creating "System.dll" in Temp)
- Magicalbound Setup.exe (PID: 788)
Script adds exclusion path to Windows Defender
- Magicalbound.exe (PID: 5504)
Starts CMD.EXE for commands execution
- snss1.exe (PID: 7868)
- snss2.exe (PID: 7956)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 4060)
- OpenWith.exe (PID: 7224)
- OOBE-Maintenance.exe (PID: 7336)
Connects to the server without a host name
- explorer.exe (PID: 4060)
Windows Defender mutex has been found
- explorer.exe (PID: 4060)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 7336)
Searches for installed software
- OOBE-Maintenance.exe (PID: 7336)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 7224)
INFO
Application launched itself
- firefox.exe (PID: 6752)
- firefox.exe (PID: 6788)
- firefox.exe (PID: 6828)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 6360)
- explorer.exe (PID: 4060)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6360)
- firefox.exe (PID: 6788)
Checks supported languages
- TextInputHost.exe (PID: 2468)
- Magicalbound Setup.exe (PID: 788)
- Magicalbound.exe (PID: 5504)
- snss1.exe (PID: 7868)
- snss2.exe (PID: 7956)
Executable content was dropped or overwritten
- firefox.exe (PID: 6788)
Reads the computer name
- TextInputHost.exe (PID: 2468)
- Magicalbound Setup.exe (PID: 788)
- Magicalbound.exe (PID: 5504)
- snss1.exe (PID: 7868)
- snss2.exe (PID: 7956)
The process uses the downloaded file
- firefox.exe (PID: 6788)
Create files in a temporary directory
- Magicalbound Setup.exe (PID: 788)
- Magicalbound.exe (PID: 5504)
- snss1.exe (PID: 7868)
- snss2.exe (PID: 7956)
Creates files in the program directory
- Magicalbound Setup.exe (PID: 788)
- Magicalbound.exe (PID: 5504)
Creates files or folders in the user directory
- Magicalbound Setup.exe (PID: 788)
- explorer.exe (PID: 4060)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 7472)
- powershell.exe (PID: 7552)
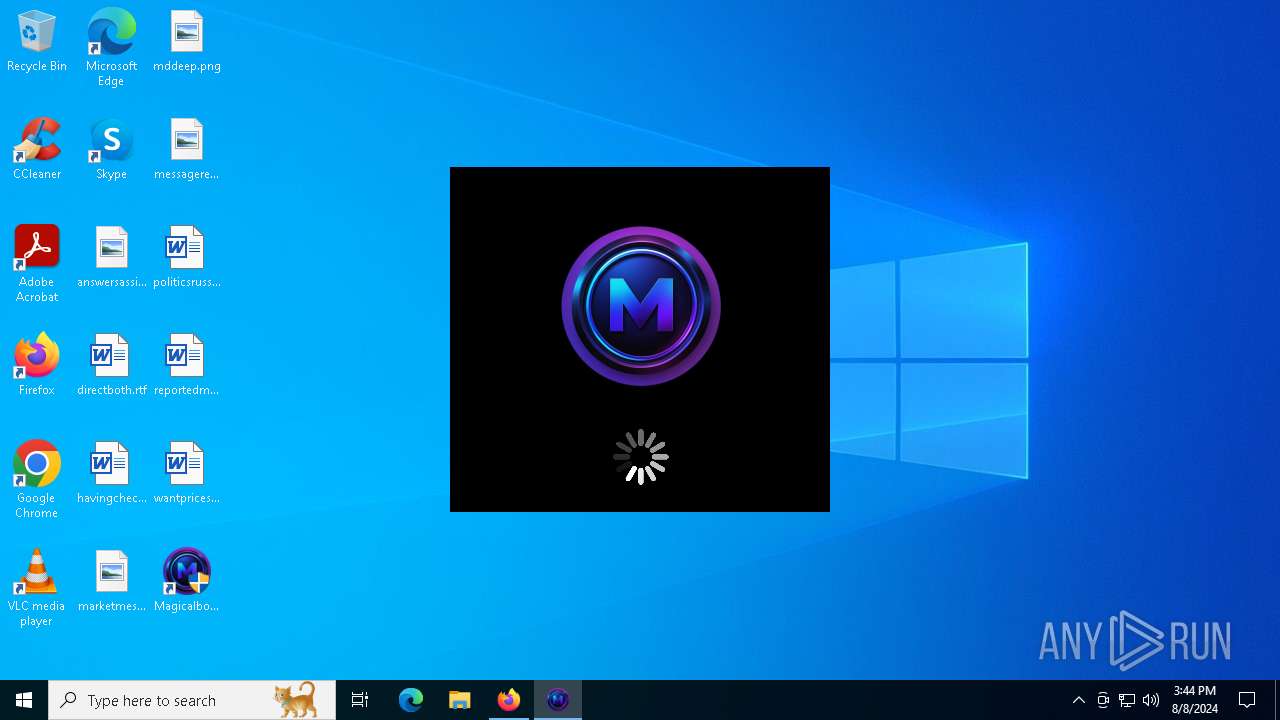
.NET Reactor protector has been detected
- Magicalbound.exe (PID: 5504)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7472)
- powershell.exe (PID: 7552)
Checks proxy server information
- Magicalbound.exe (PID: 5504)
- explorer.exe (PID: 4060)
Reads the software policy settings
- Magicalbound.exe (PID: 5504)
Reads Environment values
- snss1.exe (PID: 7868)
Manual execution by a user
- firefox.exe (PID: 6828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Stealc
(PID) Process(4060) explorer.exe
C2195.211.124.201
Strings (353)INSERT_KEY_HERE
21
08
20
24
GetProcAddress
LoadLibraryA
lstrcatA
OpenEventA
CreateEventA
CloseHandle
Sleep
GetUserDefaultLangID
VirtualAllocExNuma
VirtualFree
GetSystemInfo
VirtualAlloc
HeapAlloc
GetComputerNameA
lstrcpyA
GetProcessHeap
GetCurrentProcess
lstrlenA
ExitProcess
GlobalMemoryStatusEx
GetSystemTime
SystemTimeToFileTime
advapi32.dll
gdi32.dll
user32.dll
crypt32.dll
ntdll.dll
GetUserNameA
CreateDCA
GetDeviceCaps
ReleaseDC
CryptStringToBinaryA
sscanf
VMwareVMware
HAL9TH
JohnDoe
DISPLAY
%hu/%hu/%hu
http://195.211.124.201
markopolo
!|
/be7c600e19a47f1c.php
/a011f7f7085e3930/
magicalkebab4
GetEnvironmentVariableA
GetFileAttributesA
GlobalLock
HeapFree
GetFileSize
GlobalSize
CreateToolhelp32Snapshot
IsWow64Process
Process32Next
GetLocalTime
FreeLibrary
GetTimeZoneInformation
GetSystemPowerStatus
GetVolumeInformationA
GetWindowsDirectoryA
Process32First
GetLocaleInfoA
GetUserDefaultLocaleName
GetModuleFileNameA
DeleteFileA
FindNextFileA
LocalFree
FindClose
SetEnvironmentVariableA
LocalAlloc
GetFileSizeEx
ReadFile
SetFilePointer
WriteFile
CreateFileA
FindFirstFileA
CopyFileA
VirtualProtect
GetLogicalProcessorInformationEx
GetLastError
lstrcpynA
MultiByteToWideChar
GlobalFree
WideCharToMultiByte
GlobalAlloc
OpenProcess
TerminateProcess
GetCurrentProcessId
gdiplus.dll
ole32.dll
bcrypt.dll
wininet.dll
shlwapi.dll
shell32.dll
psapi.dll
rstrtmgr.dll
CreateCompatibleBitmap
SelectObject
BitBlt
DeleteObject
CreateCompatibleDC
GdipGetImageEncodersSize
GdipGetImageEncoders
GdipCreateBitmapFromHBITMAP
GdiplusStartup
GdiplusShutdown
GdipSaveImageToStream
GdipDisposeImage
GdipFree
GetHGlobalFromStream
CreateStreamOnHGlobal
CoUninitialize
CoInitialize
CoCreateInstance
BCryptGenerateSymmetricKey
BCryptCloseAlgorithmProvider
BCryptDecrypt
BCryptSetProperty
BCryptDestroyKey
BCryptOpenAlgorithmProvider
GetWindowRect
GetDesktopWindow
GetDC
CloseWindow
wsprintfA
EnumDisplayDevicesA
GetKeyboardLayoutList
CharToOemW
wsprintfW
RegQueryValueExA
RegEnumKeyExA
RegOpenKeyExA
RegCloseKey
RegEnumValueA
CryptBinaryToStringA
CryptUnprotectData
SHGetFolderPathA
ShellExecuteExA
InternetOpenUrlA
InternetConnectA
InternetCloseHandle
InternetOpenA
HttpSendRequestA
HttpOpenRequestA
InternetReadFile
InternetCrackUrlA
StrCmpCA
StrStrA
StrCmpCW
PathMatchSpecA
GetModuleFileNameExA
RmStartSession
RmRegisterResources
RmGetList
RmEndSession
sqlite3_open
sqlite3_prepare_v2
sqlite3_step
sqlite3_column_text
sqlite3_finalize
sqlite3_close
sqlite3_column_bytes
sqlite3_column_blob
encrypted_key
PATH
C:\ProgramData\nss3.dll
NSS_Init
NSS_Shutdown
PK11_GetInternalKeySlot
PK11_FreeSlot
PK11_Authenticate
PK11SDR_Decrypt
C:\ProgramData\
SELECT origin_url, username_value, password_value FROM logins
browser:
profile:
url:
login:
password:
Opera
OperaGX
Network
cookies
.txt
SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies
TRUE
FALSE
autofill
SELECT name, value FROM autofill
history
SELECT url FROM urls LIMIT 1000
cc
SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards
name:
month:
year:
card:
Cookies
Login Data
Web Data
History
logins.json
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
guid
SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies
SELECT fieldname, value FROM moz_formhistory
SELECT url FROM moz_places LIMIT 1000
cookies.sqlite
formhistory.sqlite
places.sqlite
plugins
Local Extension Settings
Sync Extension Settings
IndexedDB
Opera Stable
Opera GX Stable
CURRENT
chrome-extension_
_0.indexeddb.leveldb
Local State
profiles.ini
chrome
opera
firefox
wallets
%08lX%04lX%lu
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
x32
x64
%d/%d/%d %d:%d:%d
HARDWARE\DESCRIPTION\System\CentralProcessor\0
ProcessorNameString
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
DisplayName
DisplayVersion
Network Info:
- IP: IP?
- Country: ISO?
System Summary:
- HWID:
- OS:
- Architecture:
- UserName:
- Computer Name:
- Local Time:
- UTC:
- Language:
- Keyboards:
- Laptop:
- Running Path:
- CPU:
- Threads:
- Cores:
- RAM:
- Display Resolution:
- GPU:
User Agents:
Installed Apps:
All Users:
Current User:
Process List:
system_info.txt
freebl3.dll
mozglue.dll
msvcp140.dll
nss3.dll
softokn3.dll
vcruntime140.dll
\Temp\
.exe
runas
open
/c start
%DESKTOP%
%APPDATA%
%LOCALAPPDATA%
%USERPROFILE%
%DOCUMENTS%
%PROGRAMFILES%
%PROGRAMFILES_86%
%RECENT%
*.lnk
files
\discord\
\Local Storage\leveldb\CURRENT
\Local Storage\leveldb
\Telegram Desktop\
key_datas
D877F783D5D3EF8C*
map*
A7FDF864FBC10B77*
A92DAA6EA6F891F2*
F8806DD0C461824F*
Telegram
Tox
*.tox
*.ini
Password
Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\13.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\14.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\15.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\16.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
oftware\Microsoft\Windows Messaging Subsystem\Profiles\9375CFF0413111d3B88A00104B2A6676\
00000001
00000002
00000003
00000004
\Outlook\accounts.txt
Pidgin
\.purple\
accounts.xml
dQw4w9WgXcQ
token:
Software\Valve\Steam
SteamPath
\config\
ssfn*
config.vdf
DialogConfig.vdf
DialogConfigOverlay*.vdf
libraryfolders.vdf
loginusers.vdf
\Steam\
sqlite3.dll
browsers
done
soft
\Discord\tokens.txt
/c timeout /t 5 & del /f /q "
" & del "C:\ProgramData\*.dll"" & exit
C:\Windows\system32\cmd.exe
https
Content-Type: multipart/form-data; boundary=----
POST
HTTP/1.1
Content-Disposition: form-data; name="
hwid
build
token
file_name
file
message
ABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890
screenshot.jpg
EXIF
HTML
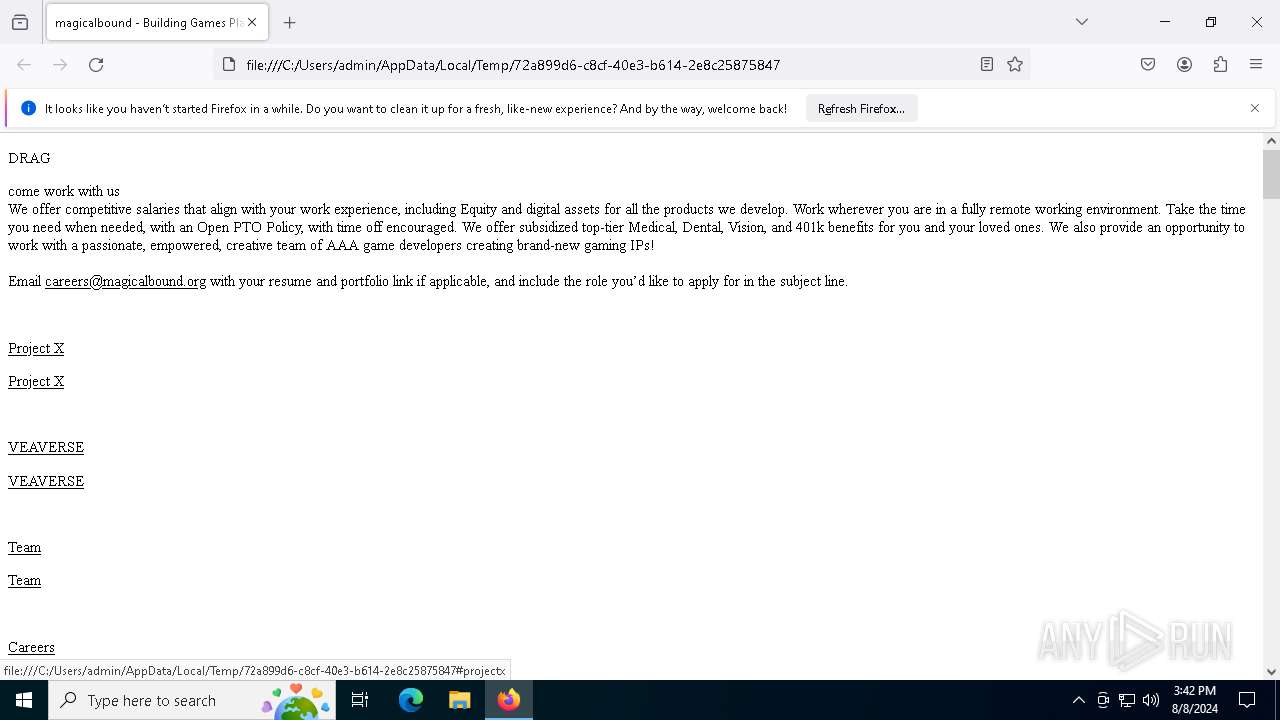
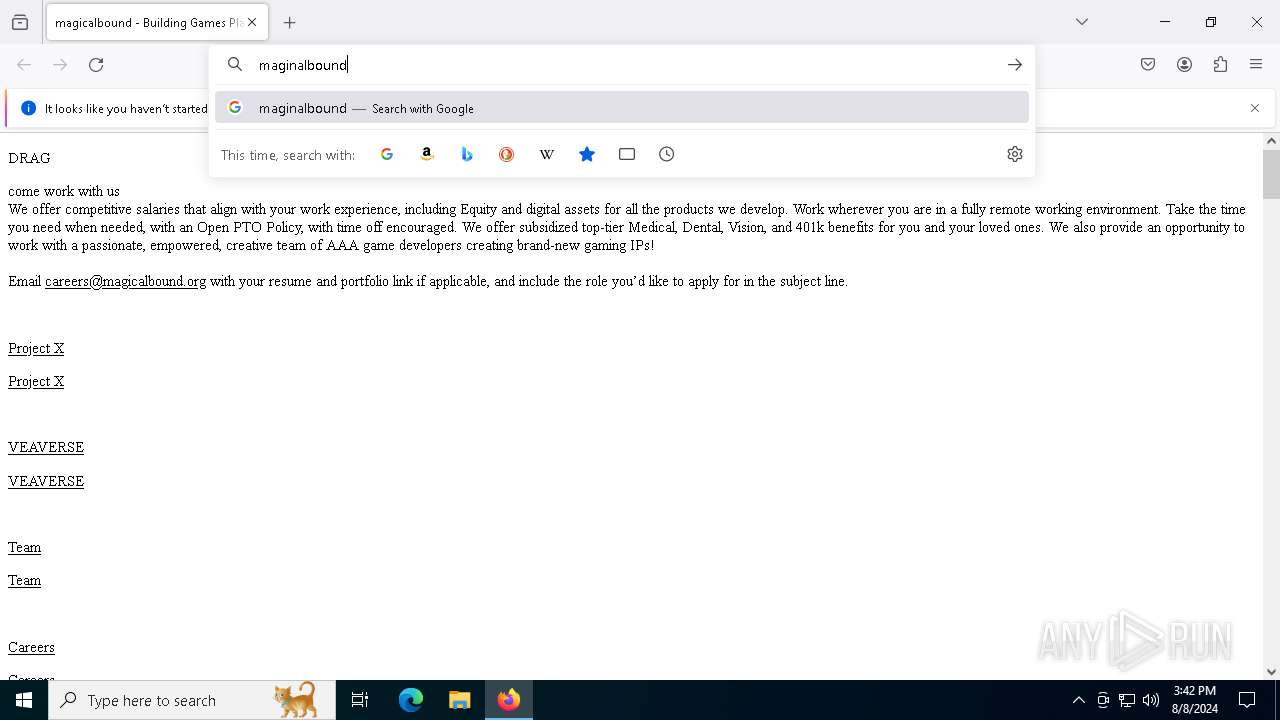
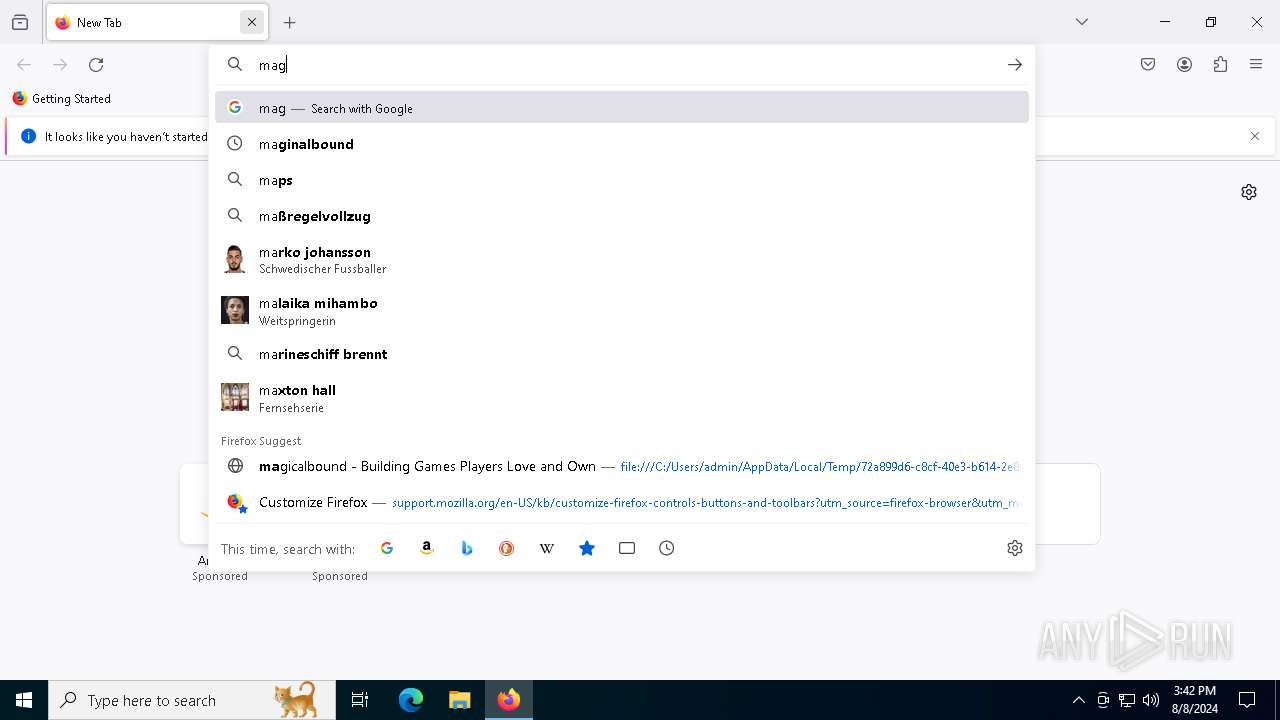
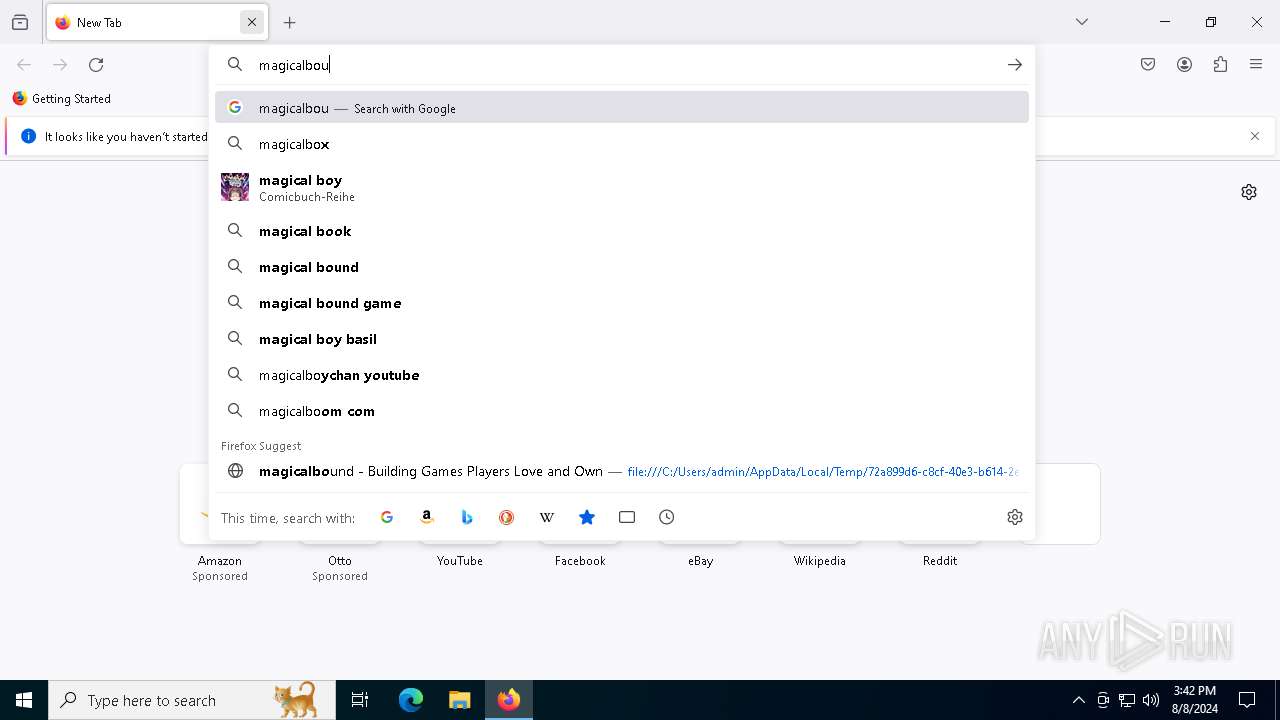
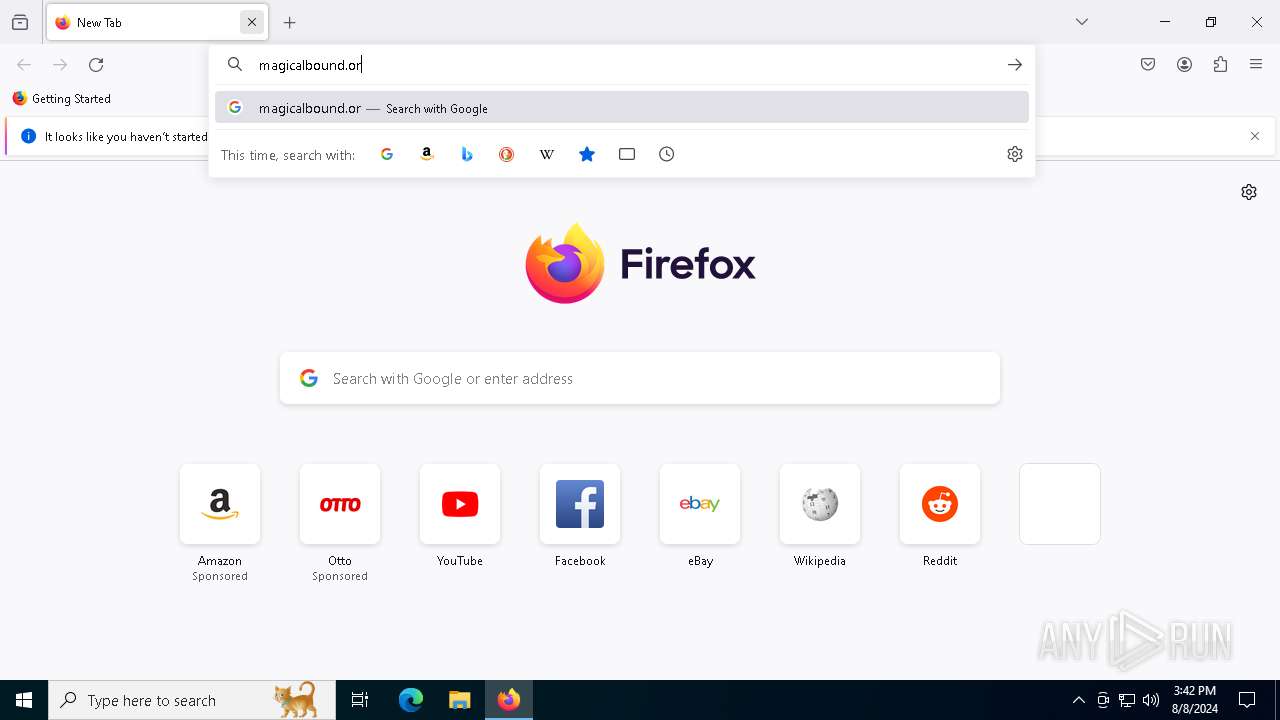
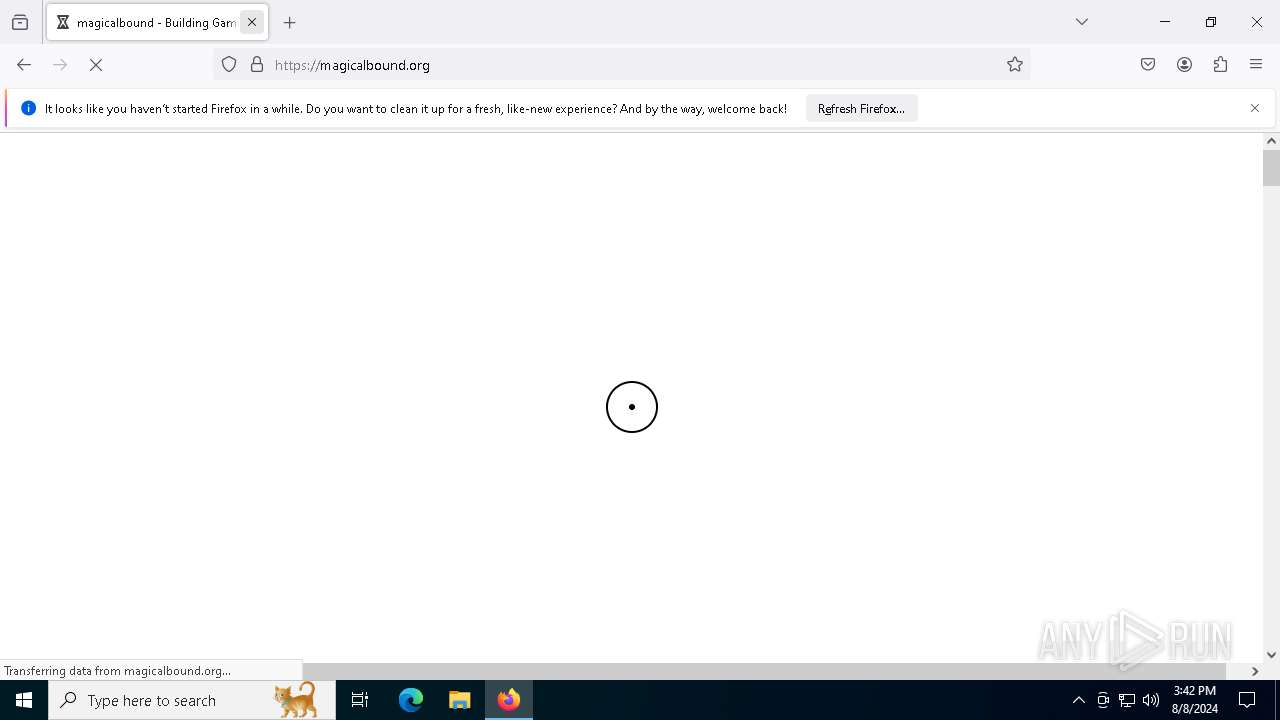
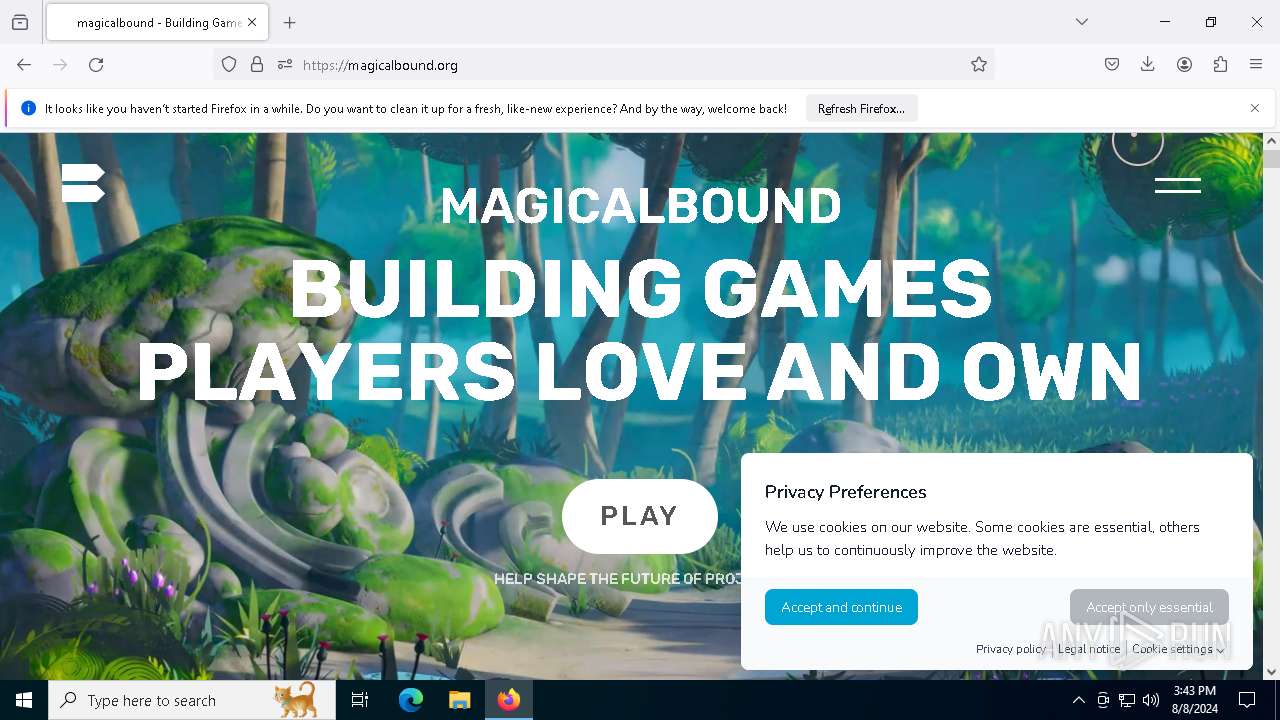
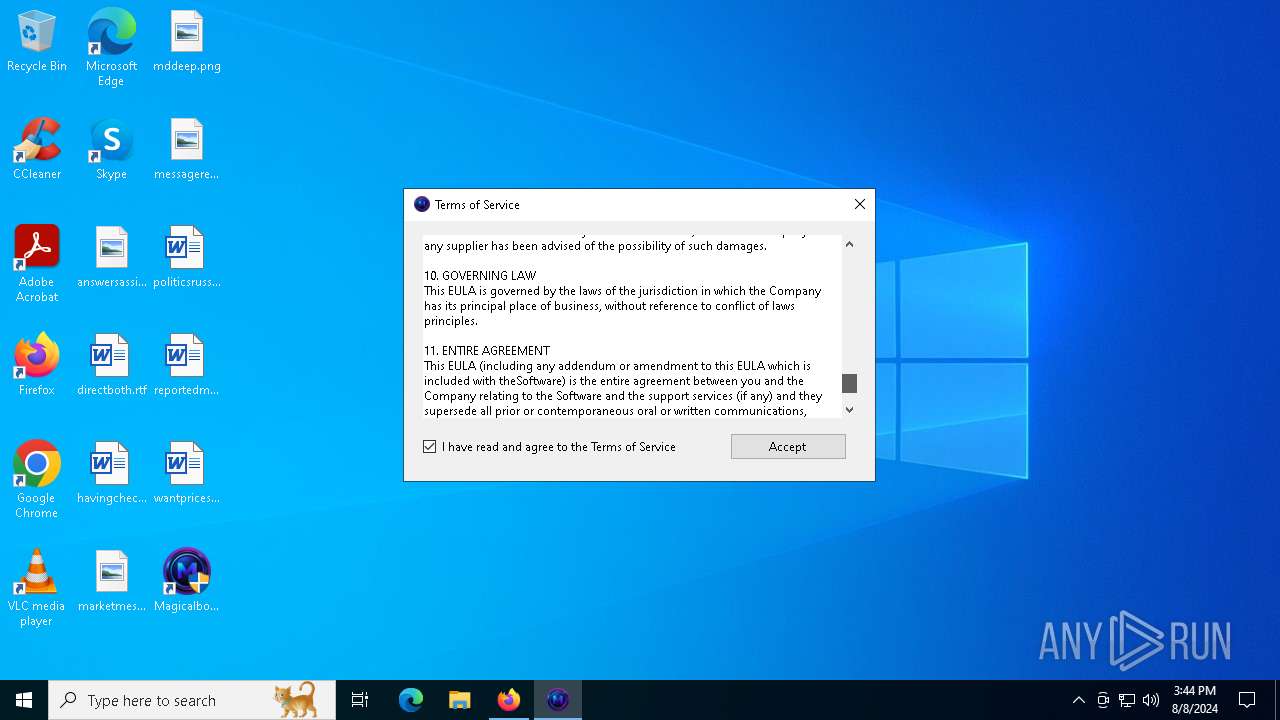
| Title: | magicalbound - Building Games Players Love and Own |
|---|---|
| Description: | magicalbound is on a mission to build memorable lifelong gaming communities that invite players into Heroic Stories, creating deep connections and positive life changes. Heroic stories are thrilling gameplay moments that bring players together and enrich players lives inside and outside the game. We believe blockchain technology will deepen these moments and enrich the player experience when paired with world-class gameplay. |
| TwitterCard: | summary_large_image |
| Viewport: | width=device-width, initial-scale=1 |
Total processes
184
Monitored processes
45
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7916 -childID 11 -isForBrowser -prefsHandle 7872 -prefMapHandle 7772 -prefsLen 32132 -prefMapSize 244343 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3e4f24f6-55d4-4e3c-b8aa-1fb09a9ea85d} 6788 "\\.\pipe\gecko-crash-server-pipe.6788" 24868159f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
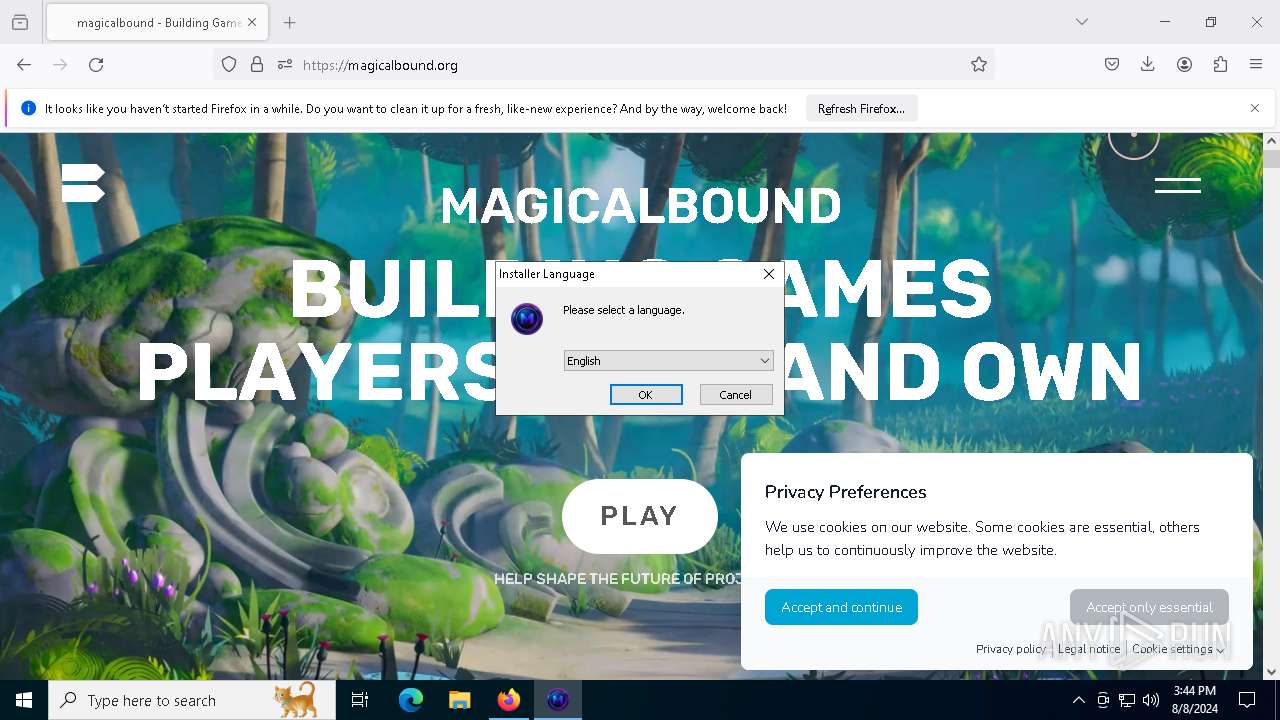
| 788 | "C:\Users\admin\Downloads\Magicalbound Setup.exe" | C:\Users\admin\Downloads\Magicalbound Setup.exe | firefox.exe | ||||||||||||
User: admin Company: Magicalbound Team Integrity Level: HIGH Description: Magicalbound Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6476 -childID 9 -isForBrowser -prefsHandle 5864 -prefMapHandle 7372 -prefsLen 32132 -prefMapSize 244343 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a97aac96-43d8-4291-92b6-643a26844abe} 6788 "\\.\pipe\gecko-crash-server-pipe.6788" 248674354d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6920 -childID 8 -isForBrowser -prefsHandle 6916 -prefMapHandle 6376 -prefsLen 31242 -prefMapSize 244343 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {fc3058e4-9e11-40be-aa1b-0860db9aff50} 6788 "\\.\pipe\gecko-crash-server-pipe.6788" 2486356b150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2468 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4716 -childID 2 -isForBrowser -prefsHandle 4768 -prefMapHandle 4764 -prefsLen 36263 -prefMapSize 244343 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {0588e773-ab15-44e7-961c-e8ef278993d6} 6788 "\\.\pipe\gecko-crash-server-pipe.6788" 24866595690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=3064 -parentBuildID 20240213221259 -sandboxingKind 1 -prefsHandle 6996 -prefMapHandle 6308 -prefsLen 34794 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {81b0fe3f-4187-49d0-aade-e52b7827f9ab} 6788 "\\.\pipe\gecko-crash-server-pipe.6788" 2486769d310 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5436 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4512 -prefMapHandle 5124 -prefsLen 36339 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {0e1d18ed-1e7b-4bac-b94e-f2eeb64a15fe} 6788 "\\.\pipe\gecko-crash-server-pipe.6788" 2486739e510 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
55 455
Read events
55 363
Write events
91
Delete events
1
Modification events
| (PID) Process: | (6360) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (6360) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
| (PID) Process: | (6360) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6360) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6360) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6360) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6752) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 33BE04CA00000000 | |||
| (PID) Process: | (6788) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 53DD05CA00000000 | |||
| (PID) Process: | (6788) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (6788) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
Executable files
472
Suspicious files
383
Text files
52
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:B8D99F07CFF04E91032D964F681E95D0 | SHA256:D9DFB80D07380A2C3D397B290EA730B399488013434341E53CF1DAB63B00C954 | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:3B75743DE2C9522B1018EDFCCF996781 | SHA256:E11BCD73194060FE5AB02E93B27F46FC29F76DB8BC6B0D31394EB6F7308A7B32 | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6788 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
184
DNS requests
230
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6788 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6788 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6788 | firefox.exe | POST | 200 | 95.101.54.209:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 95.101.54.128:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 142.250.186.67:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 95.101.54.128:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 142.250.186.67:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 95.101.54.128:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 95.101.54.209:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6788 | firefox.exe | POST | 200 | 95.101.54.209:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5040 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1860 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1860 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6788 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6788 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
6788 | firefox.exe | 216.58.206.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6788 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
6788 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
6788 | firefox.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
4060 | explorer.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Stealc HTTP POST Request |
4060 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
5 ETPRO signatures available at the full report