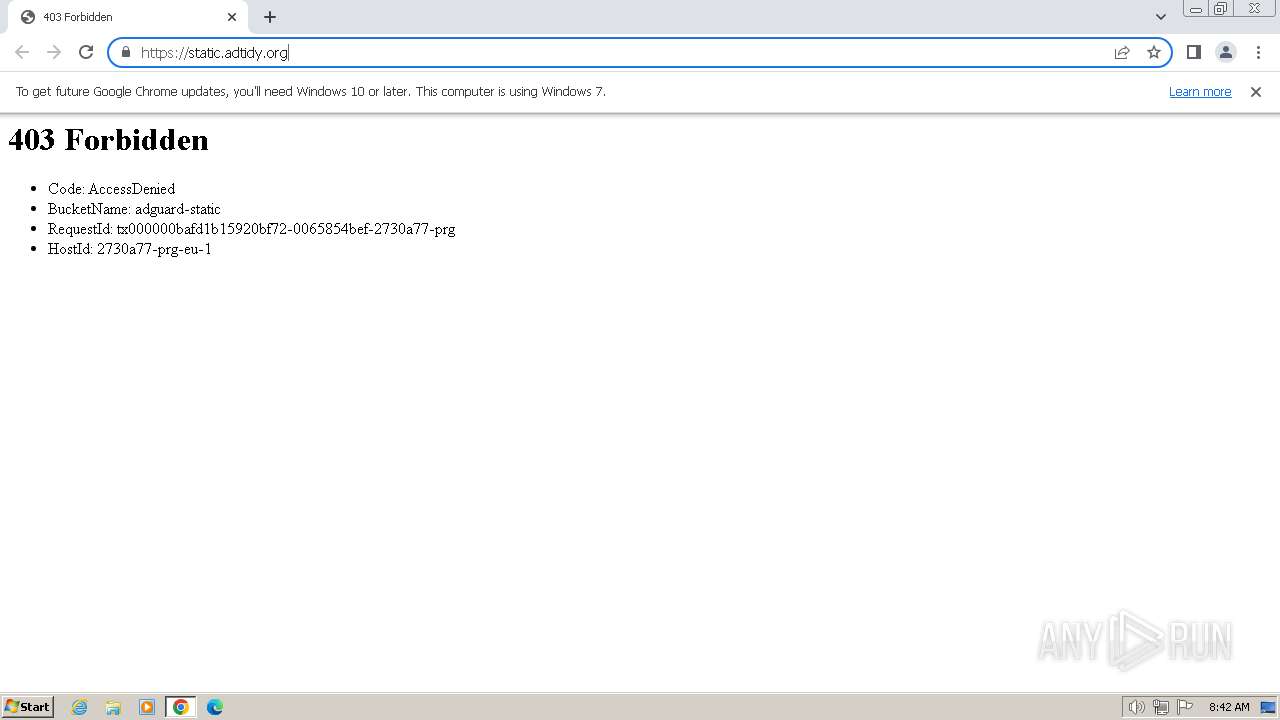
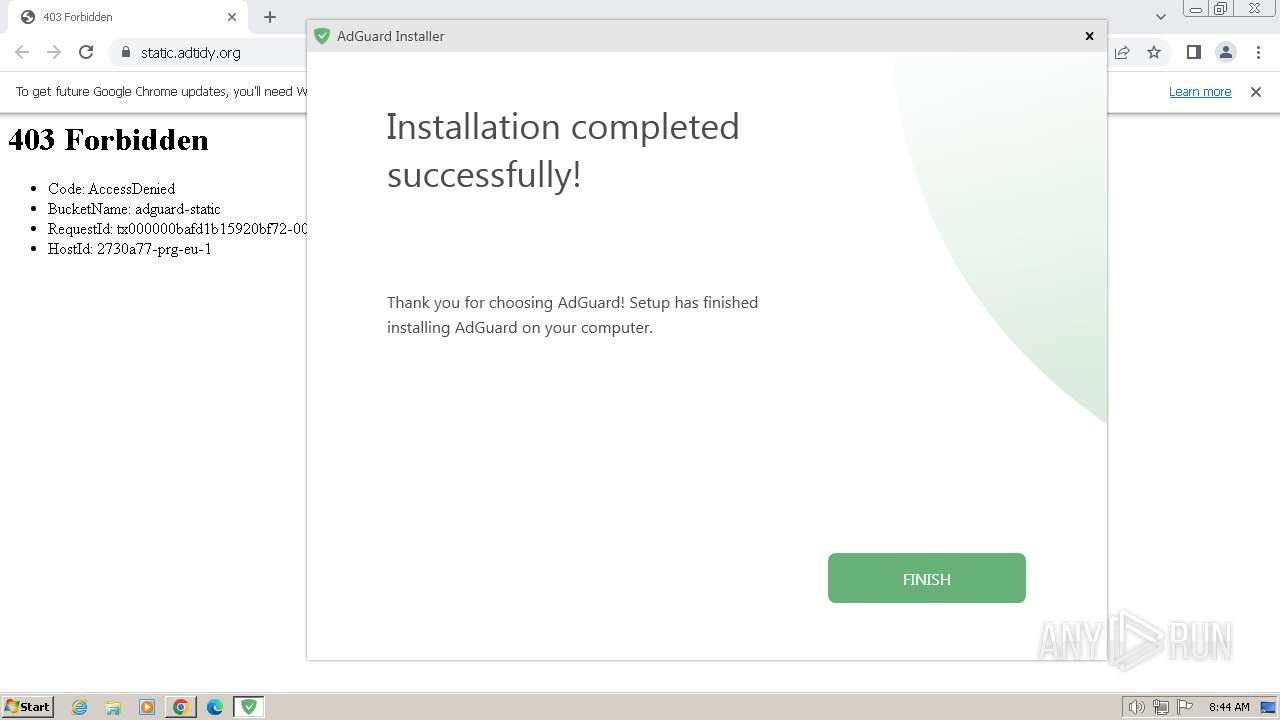
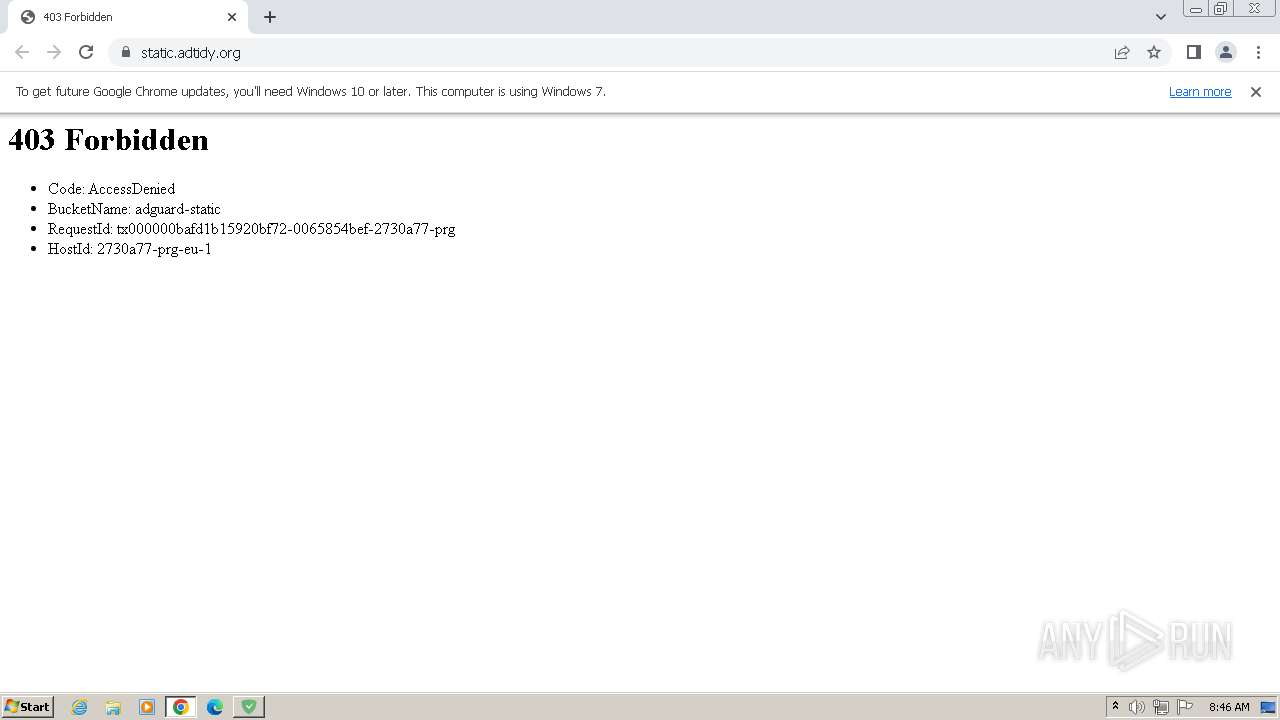
| URL: | static.adtidy.org |
| Full analysis: | https://app.any.run/tasks/7d3c8433-b793-40a3-9a30-a2f8dffe6e09 |
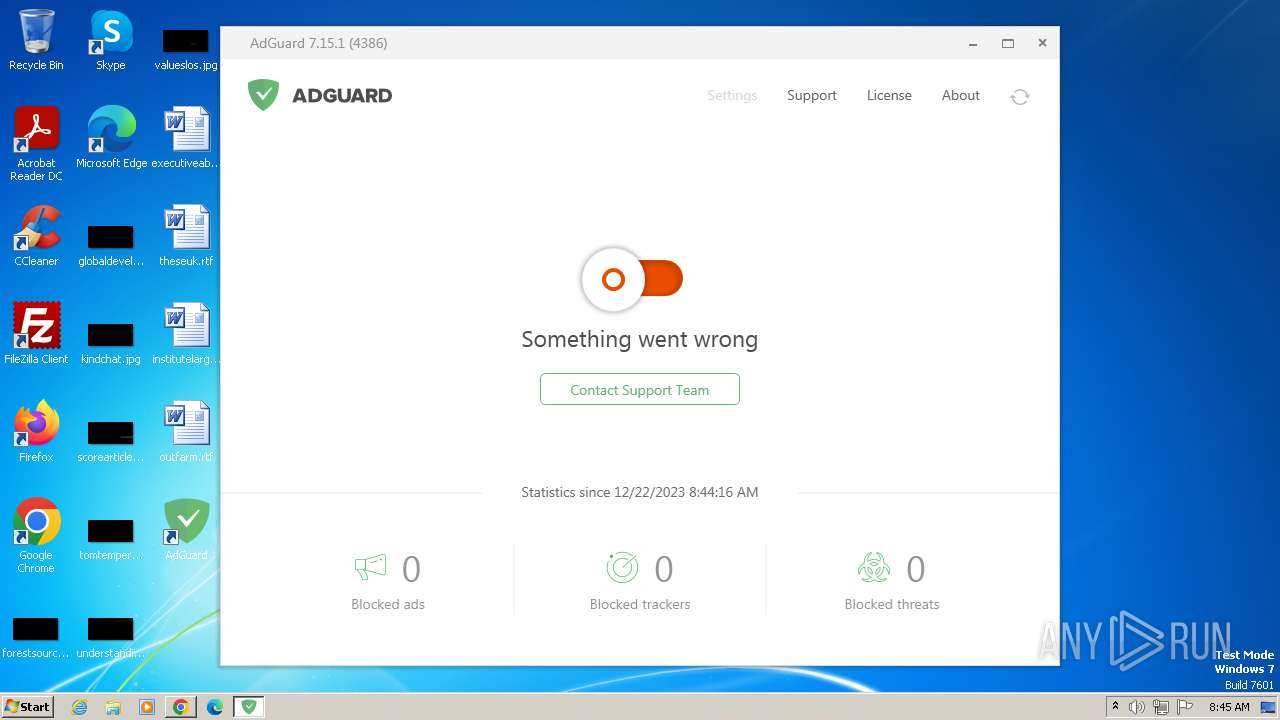
| Verdict: | Malicious activity |
| Threats: | Pikabot is a trojan malware with a focus on loader capabilities. Pikabot is also used for other activities, such as executing commands on the infected system. The earlier versions of the malware made use of extensive code obfuscation to evade detection. Upon infection, it collects system information and sends it to command-and-control servers. |
| Analysis date: | December 22, 2023, 08:42:10 |
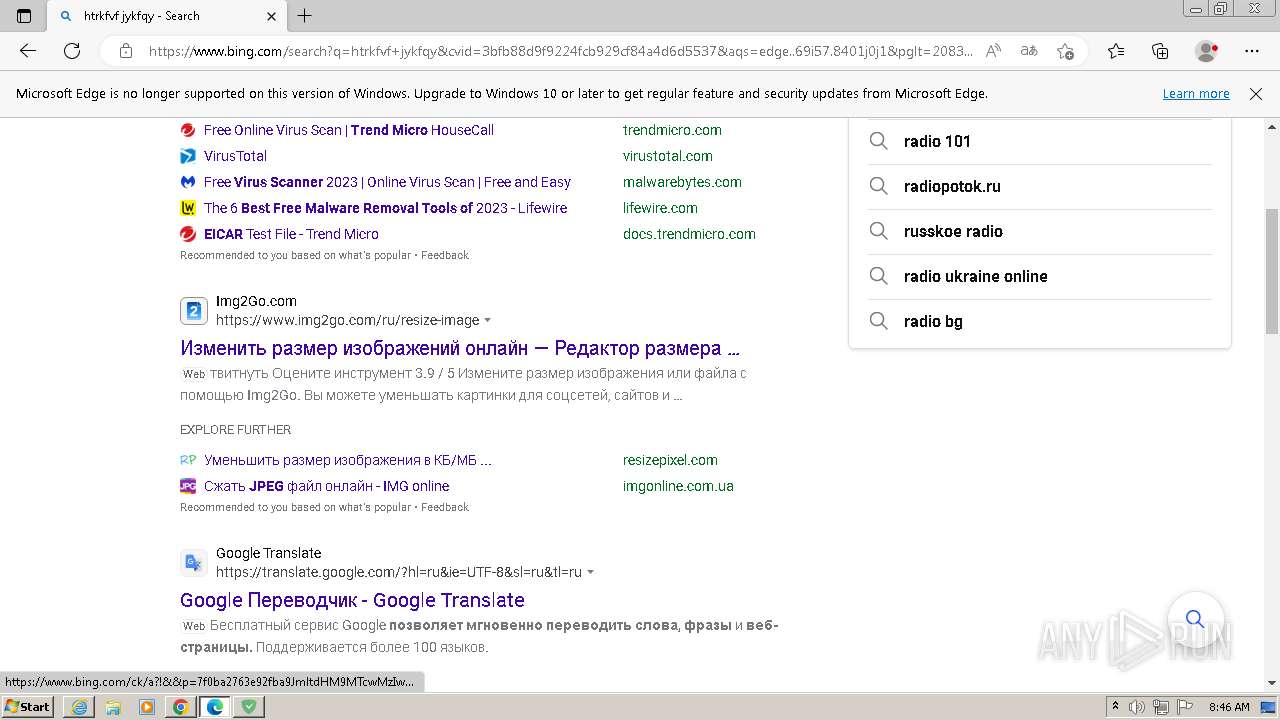
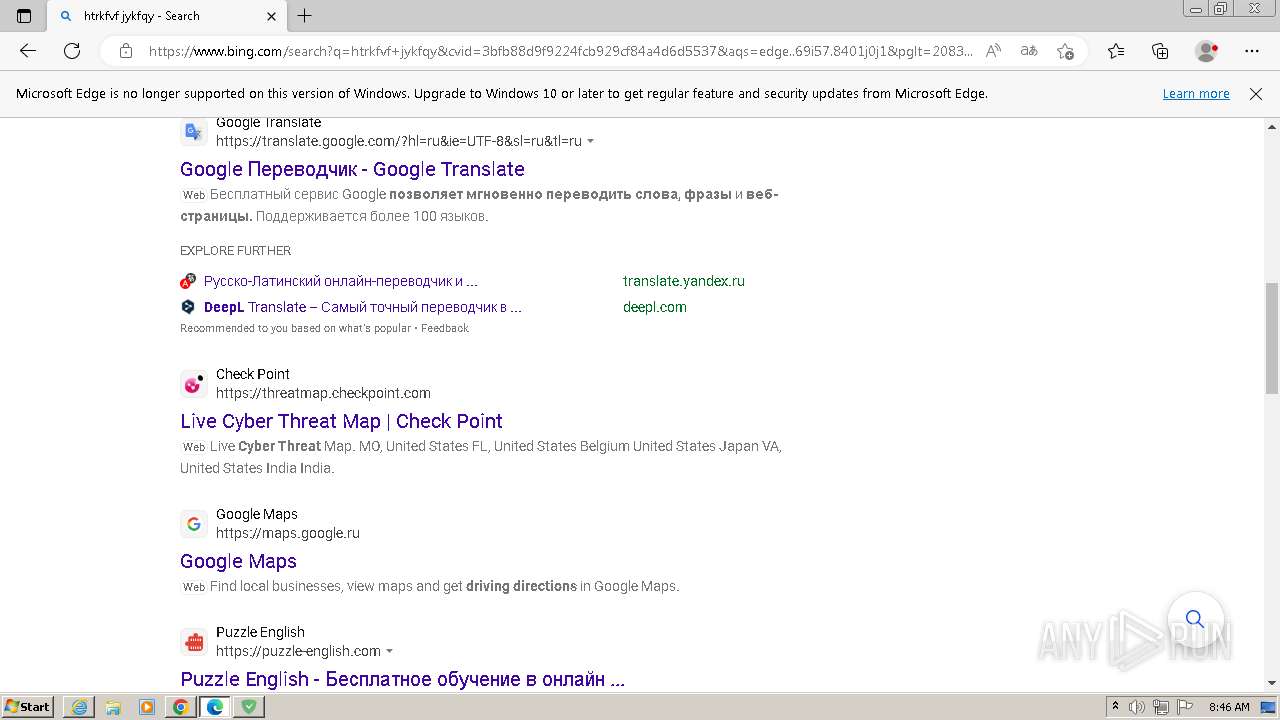
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2C7D9E4B636EBFE03BF20AFC277C0690 |
| SHA1: | 094D98DB651B5C38CDA240A3C42835A35E679A81 |
| SHA256: | DF57E40E6C11FDBE718E9D9E2737962BC92E61C2EE9EF2029CDCF2695D5A7B65 |
| SSDEEP: | 3:NrMgXC:1MgXC |
MALICIOUS
Pikabot has been detected
- rundll32.exe (PID: 4064)
- rundll32.exe (PID: 3884)
- rundll32.exe (PID: 2160)
- rundll32.exe (PID: 4044)
- rundll32.exe (PID: 1388)
- rundll32.exe (PID: 2828)
Starts NET.EXE for service management
- cmd.exe (PID: 2924)
- net.exe (PID: 2808)
Creates a writable file in the system directory
- AdguardSvc.exe (PID: 2396)
- Adguard.Tools.exe (PID: 3876)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3724)
SUSPICIOUS
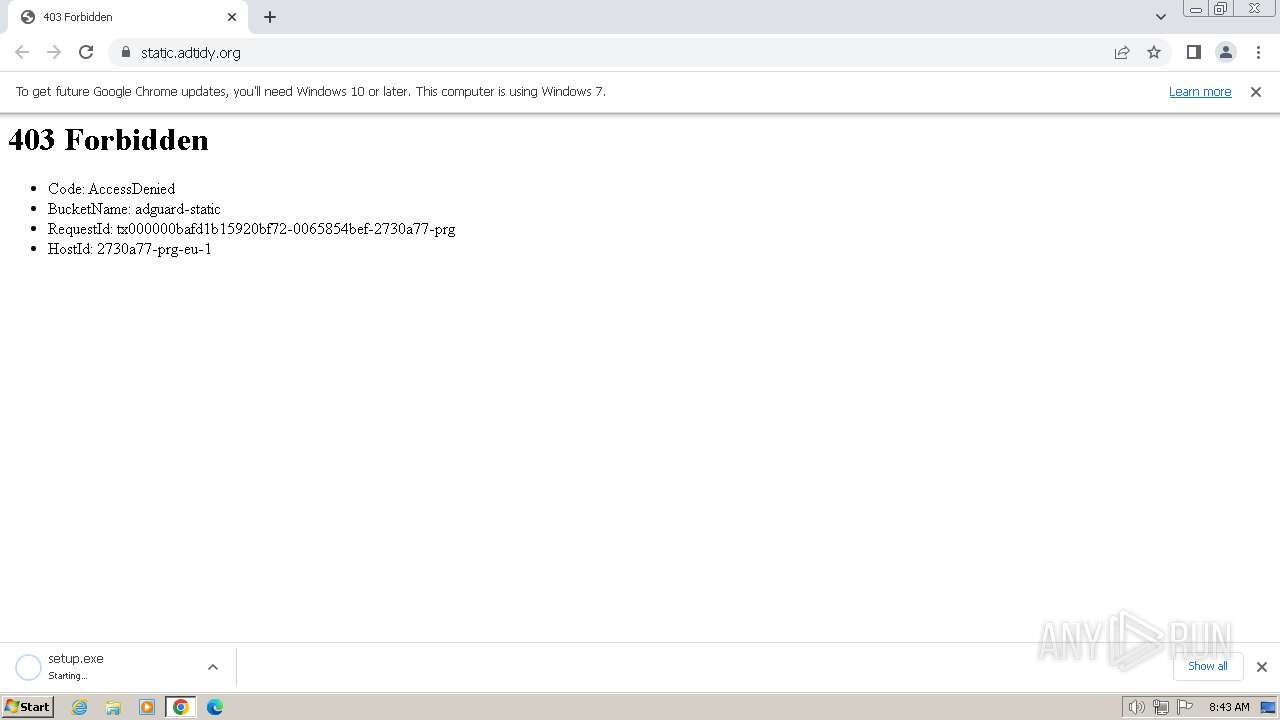
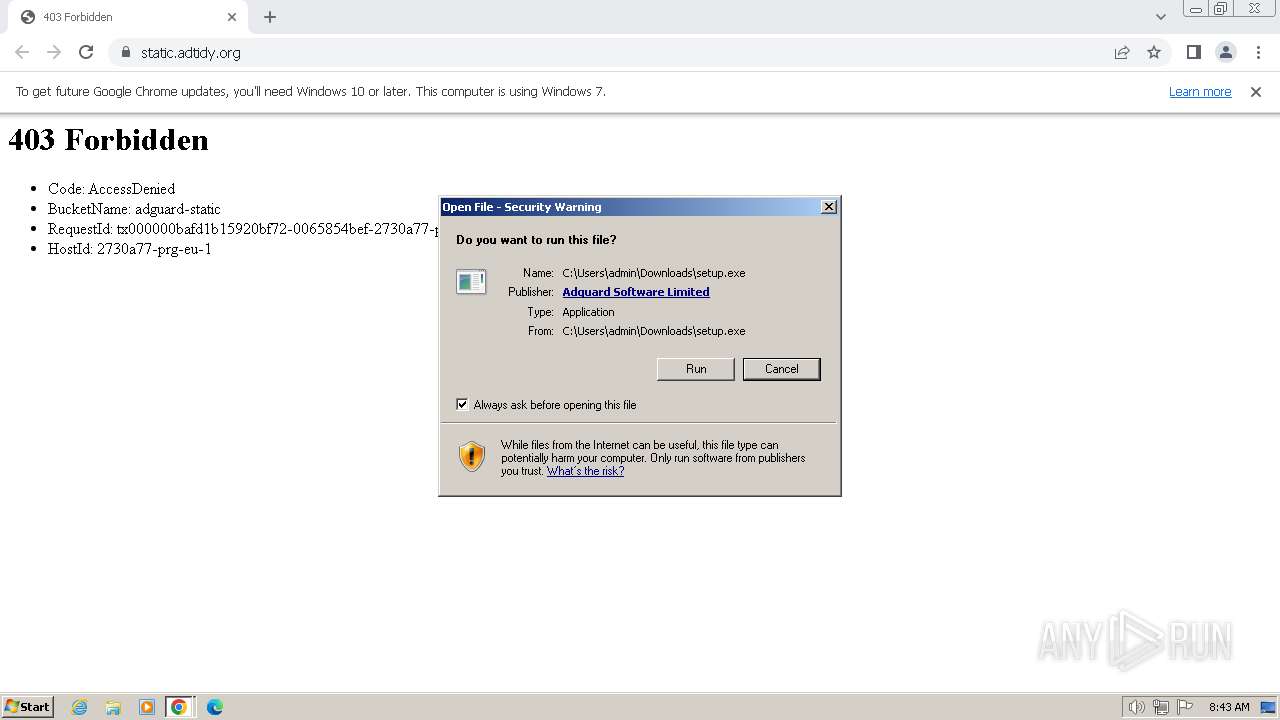
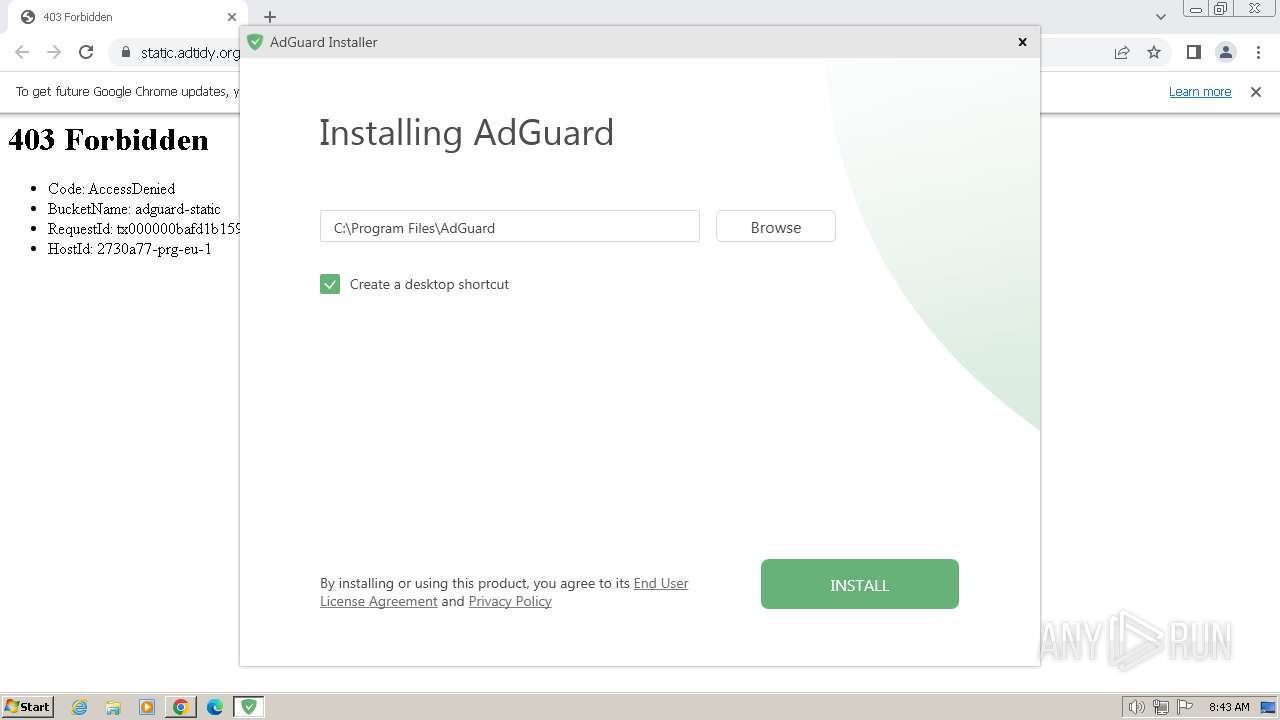
The process creates files with name similar to system file names
- setup.exe (PID: 3216)
- msiexec.exe (PID: 3084)
Searches for installed software
- adgSetup.exe (PID: 3328)
- setup.exe (PID: 3216)
Checks Windows Trust Settings
- msiexec.exe (PID: 3084)
- AdguardSvc.exe (PID: 2396)
- AdguardSvc.exe (PID: 1432)
- AdguardSvc.exe (PID: 3772)
Reads settings of System Certificates
- setup.exe (PID: 3216)
Reads the Internet Settings
- setup.exe (PID: 3216)
- Adguard.exe (PID: 900)
Process requests binary or script from the Internet
- setup.exe (PID: 3216)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 3684)
Adds/modifies Windows certificates
- msiexec.exe (PID: 3084)
- AdguardSvc.exe (PID: 2396)
- AdguardSvc.exe (PID: 3772)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 1388)
- AdguardSvc.exe (PID: 2396)
- AdguardSvc.exe (PID: 3772)
Drops a system driver (possible attempt to evade defenses)
- AdguardSvc.exe (PID: 2396)
- Adguard.Tools.exe (PID: 3876)
Starts SC.EXE for service management
- setup.exe (PID: 3216)
- AdguardSvc.exe (PID: 2396)
- Adguard.exe (PID: 900)
- AdguardSvc.exe (PID: 3772)
Creates a software uninstall entry
- adgSetup.exe (PID: 3328)
Creates files in the driver directory
- AdguardSvc.exe (PID: 2396)
- Adguard.Tools.exe (PID: 3876)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 3524)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 3492)
- cmd.exe (PID: 3852)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3084)
INFO
The process uses the downloaded file
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1776)
Create files in a temporary directory
- setup.exe (PID: 2656)
- setup.exe (PID: 3216)
- adgSetup.exe (PID: 3328)
- msiexec.exe (PID: 3084)
Drops the executable file immediately after the start
- chrome.exe (PID: 1776)
- setup.exe (PID: 2656)
- setup.exe (PID: 3216)
- adgSetup.exe (PID: 3328)
- chrome.exe (PID: 3908)
- rundll32.exe (PID: 4064)
- rundll32.exe (PID: 3884)
- rundll32.exe (PID: 2160)
- rundll32.exe (PID: 4044)
- rundll32.exe (PID: 1388)
- AdguardSvc.exe (PID: 2396)
- msiexec.exe (PID: 3084)
- rundll32.exe (PID: 2828)
- Adguard.Tools.exe (PID: 3876)
- chrome.exe (PID: 1876)
Checks supported languages
- setup.exe (PID: 3216)
- setup.exe (PID: 2656)
- adgSetup.exe (PID: 3328)
- msiexec.exe (PID: 3084)
- msiexec.exe (PID: 3684)
- msiexec.exe (PID: 2448)
- AdguardSvc.exe (PID: 2396)
- Adguard.BrowserExtensionHost.exe (PID: 4040)
- Adguard.exe (PID: 900)
- Adguard.Tools.exe (PID: 3268)
- Adguard.Tools.exe (PID: 3876)
- AdguardSvc.exe (PID: 1432)
- AdguardNetReg.exe (PID: 3932)
- AdguardSvc.exe (PID: 3772)
- Adguard.BrowserExtensionHost.exe (PID: 3104)
- Adguard.Tools.exe (PID: 3080)
Process drops legitimate windows executable
- setup.exe (PID: 3216)
- msiexec.exe (PID: 3084)
Reads the computer name
- setup.exe (PID: 3216)
- adgSetup.exe (PID: 3328)
- msiexec.exe (PID: 3084)
- msiexec.exe (PID: 3684)
- msiexec.exe (PID: 2448)
- AdguardSvc.exe (PID: 2396)
- Adguard.BrowserExtensionHost.exe (PID: 4040)
- Adguard.exe (PID: 900)
- Adguard.Tools.exe (PID: 3268)
- Adguard.Tools.exe (PID: 3876)
- AdguardSvc.exe (PID: 1432)
- AdguardNetReg.exe (PID: 3932)
- AdguardSvc.exe (PID: 3772)
- Adguard.BrowserExtensionHost.exe (PID: 3104)
- Adguard.Tools.exe (PID: 3080)
Reads the machine GUID from the registry
- setup.exe (PID: 3216)
- msiexec.exe (PID: 3084)
- msiexec.exe (PID: 3684)
- msiexec.exe (PID: 2448)
- AdguardSvc.exe (PID: 2396)
- Adguard.BrowserExtensionHost.exe (PID: 4040)
- Adguard.exe (PID: 900)
- Adguard.Tools.exe (PID: 3268)
- Adguard.Tools.exe (PID: 3876)
- AdguardSvc.exe (PID: 1432)
- AdguardSvc.exe (PID: 3772)
- Adguard.BrowserExtensionHost.exe (PID: 3104)
- Adguard.Tools.exe (PID: 3080)
- adgSetup.exe (PID: 3328)
Starts itself from another location
- setup.exe (PID: 3216)
Creates files in the program directory
- adgSetup.exe (PID: 3328)
- setup.exe (PID: 3216)
- AdguardSvc.exe (PID: 2396)
- Adguard.BrowserExtensionHost.exe (PID: 4040)
- Adguard.exe (PID: 900)
- Adguard.Tools.exe (PID: 3268)
- AdguardSvc.exe (PID: 1432)
- AdguardNetReg.exe (PID: 3932)
- Adguard.Tools.exe (PID: 3876)
- AdguardSvc.exe (PID: 3772)
- Adguard.BrowserExtensionHost.exe (PID: 3104)
- Adguard.Tools.exe (PID: 3080)
Reads Environment values
- setup.exe (PID: 3216)
- AdguardSvc.exe (PID: 2396)
- Adguard.exe (PID: 900)
- AdguardSvc.exe (PID: 3772)
Application launched itself
- chrome.exe (PID: 1776)
- msiexec.exe (PID: 3084)
- iexplore.exe (PID: 3260)
- msedge.exe (PID: 568)
Dropped object may contain TOR URL's
- msiexec.exe (PID: 3084)
- AdguardSvc.exe (PID: 2396)
Executes as Windows Service
- AdguardSvc.exe (PID: 2396)
- AdguardSvc.exe (PID: 1432)
- AdguardSvc.exe (PID: 3772)
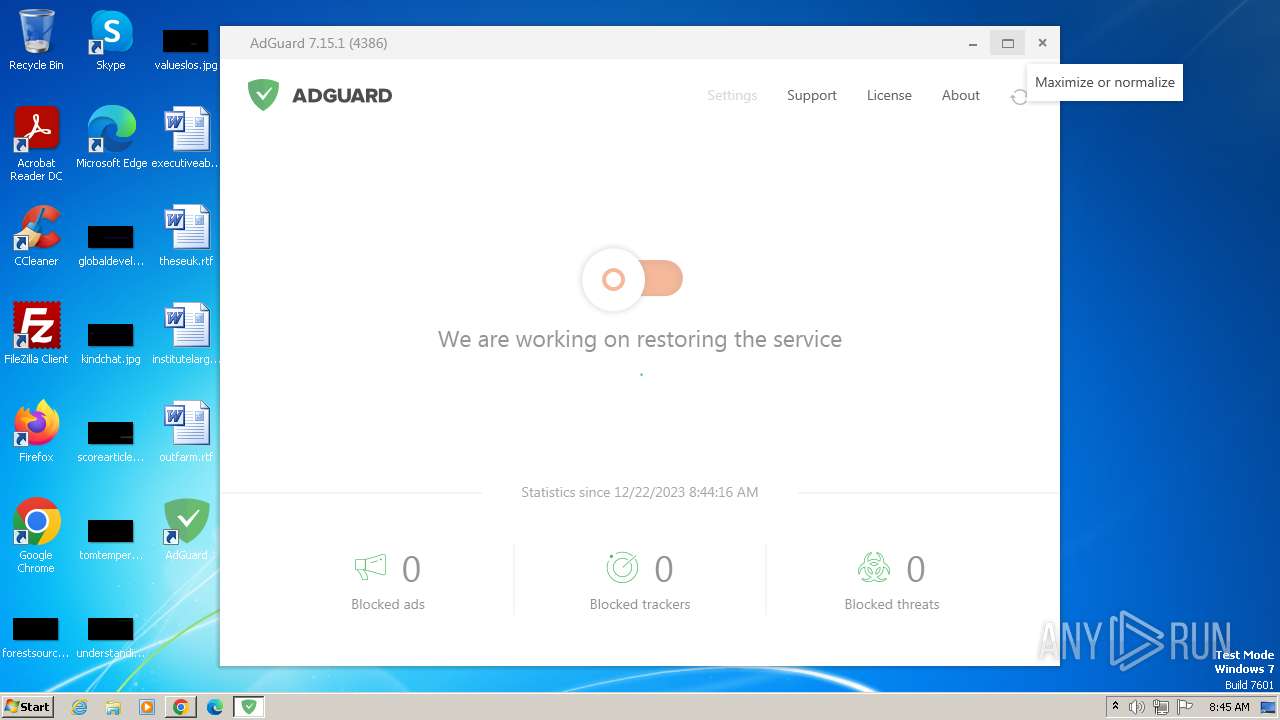
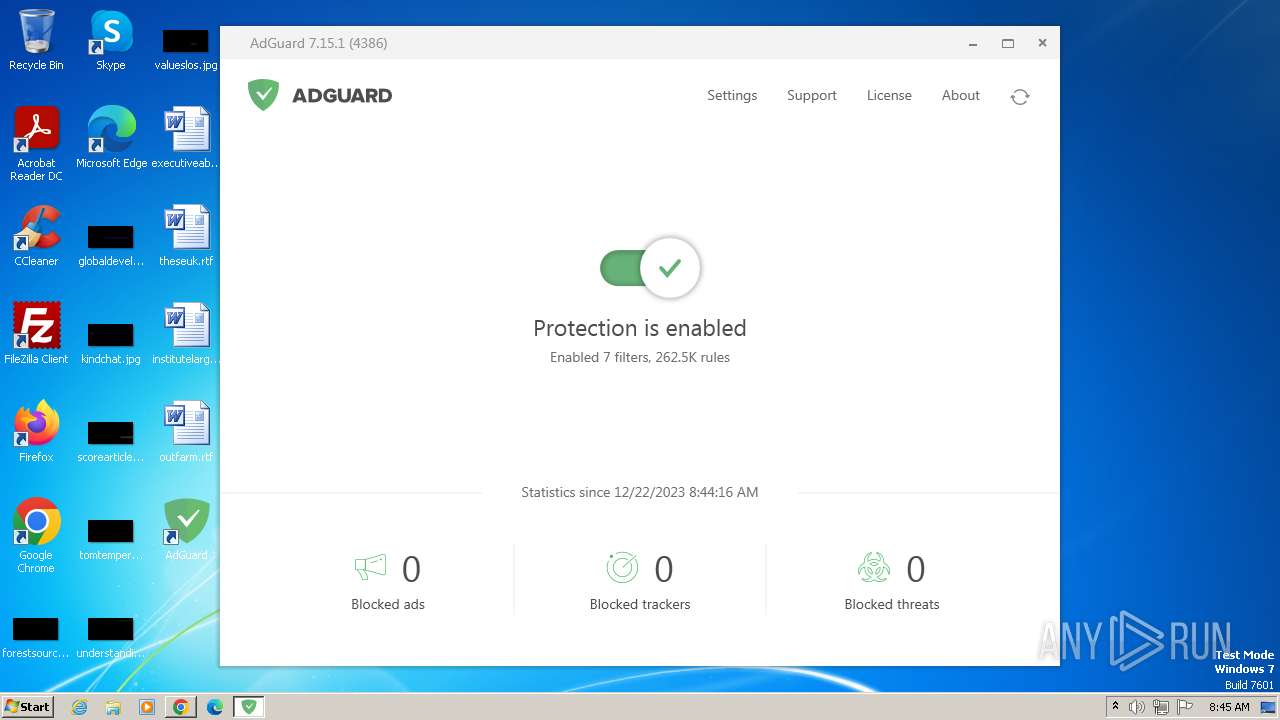
Manual execution by a user
- Adguard.exe (PID: 900)
- iexplore.exe (PID: 3260)
- msedge.exe (PID: 568)
Creates files or folders in the user directory
- Adguard.exe (PID: 900)
Reads CPU info
- Adguard.exe (PID: 900)
Checks proxy server information
- Adguard.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
152
Monitored processes
91
Malicious processes
12
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "sc" sdshow "Adguard Service" | C:\Windows\System32\sc.exe | — | AdguardSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1084 --field-trial-handle=1156,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1456 --field-trial-handle=1156,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4032 --field-trial-handle=1356,i,2202363202171558327,11087125959484523726,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2960 --field-trial-handle=1156,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3268 --field-trial-handle=1156,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\AdGuard\Adguard.exe" | C:\Program Files\AdGuard\Adguard.exe | explorer.exe | ||||||||||||
User: admin Company: Adguard Software Limited Integrity Level: MEDIUM Description: AdGuard for Windows Exit code: 0 Version: 7.15.4386.0 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=4188 --field-trial-handle=1156,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "ie4uinit.exe" -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
65 563
Read events
65 106
Write events
437
Delete events
20
Modification events
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
241
Suspicious files
804
Text files
190
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe1529.TMP | — | |
MD5:— | SHA256:— | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe1549.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe1bc1.TMP | — | |
MD5:— | SHA256:— | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFe1885.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 1776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFe2d93.TMP | — | |
MD5:— | SHA256:— | |||
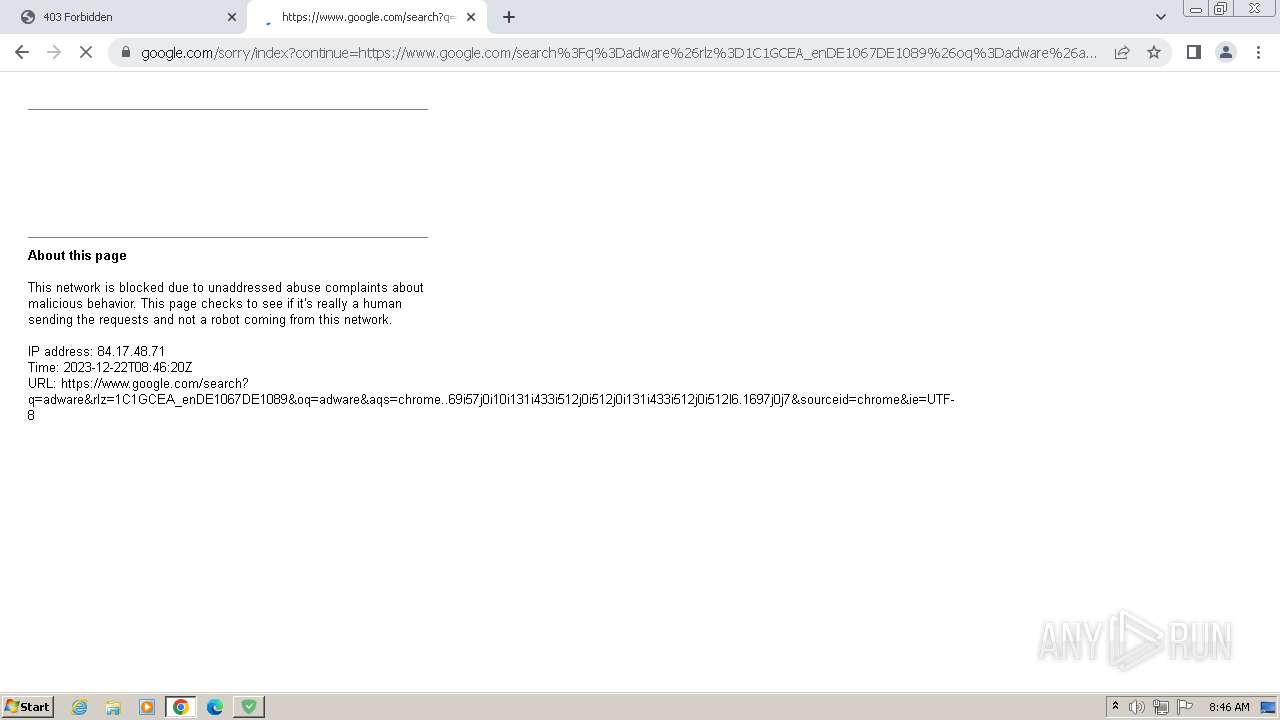
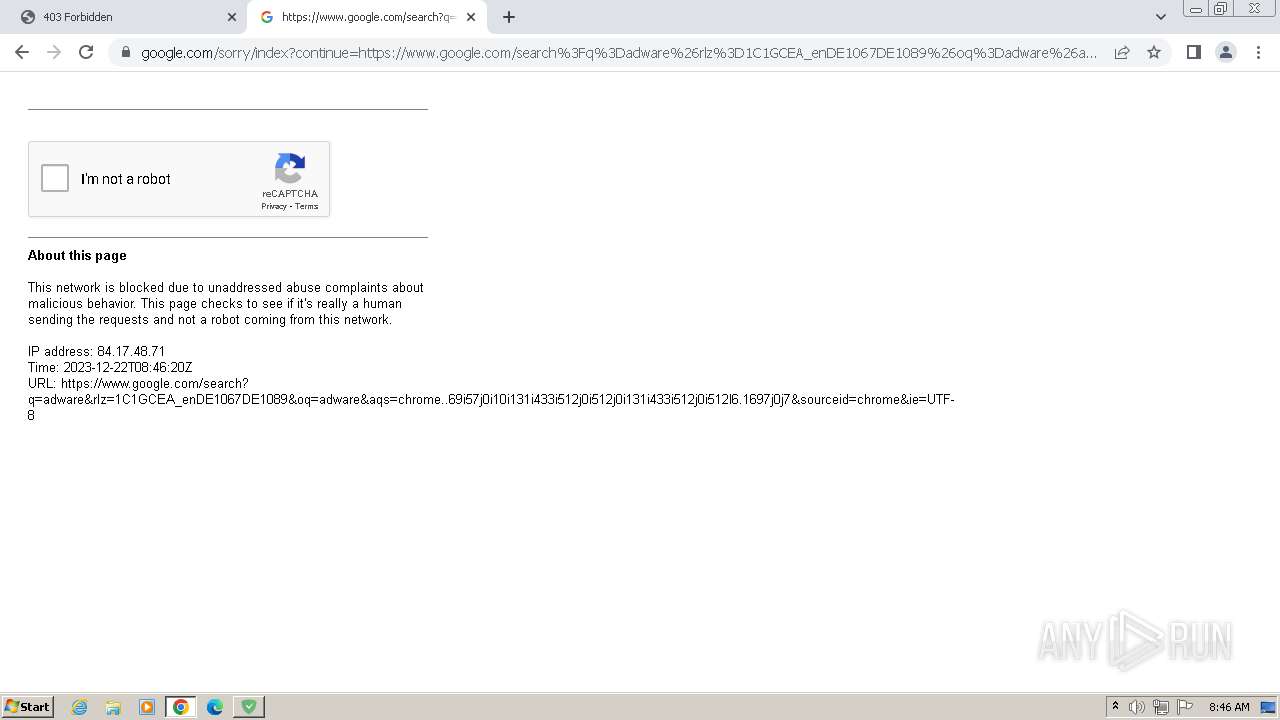
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
117
DNS requests
117
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1044 | chrome.exe | GET | 301 | 195.181.175.16:80 | http://static.adtidy.org/ | DE | html | 772 b | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 6.36 Kb | unknown |
3216 | setup.exe | GET | 301 | 195.181.170.18:80 | http://static.adguard.com/installer.v1.0.json | DE | html | 772 b | unknown |
— | — | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b57000d84e8d590f | DE | compressed | 65.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.59 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 8.23 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 8.39 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 18.5 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 34.4 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1044 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | unknown |
1044 | chrome.exe | 195.181.175.16:80 | static.adtidy.org | Datacamp Limited | DE | unknown |
1776 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1044 | chrome.exe | 195.181.175.16:443 | static.adtidy.org | Datacamp Limited | DE | unknown |
1044 | chrome.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
1776 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1044 | chrome.exe | 172.217.18.10:443 | www.googleapis.com | GOOGLE | US | whitelisted |
1044 | chrome.exe | 142.250.74.195:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
static.adtidy.org |
| unknown |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
time.windows.com |
| whitelisted |
static.adguard.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2396 | AdguardSvc.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2396 | AdguardSvc.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3772 | AdguardSvc.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3772 | AdguardSvc.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3772 | AdguardSvc.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
AdguardSvc.exe | SQLite error (5): database is locked
|