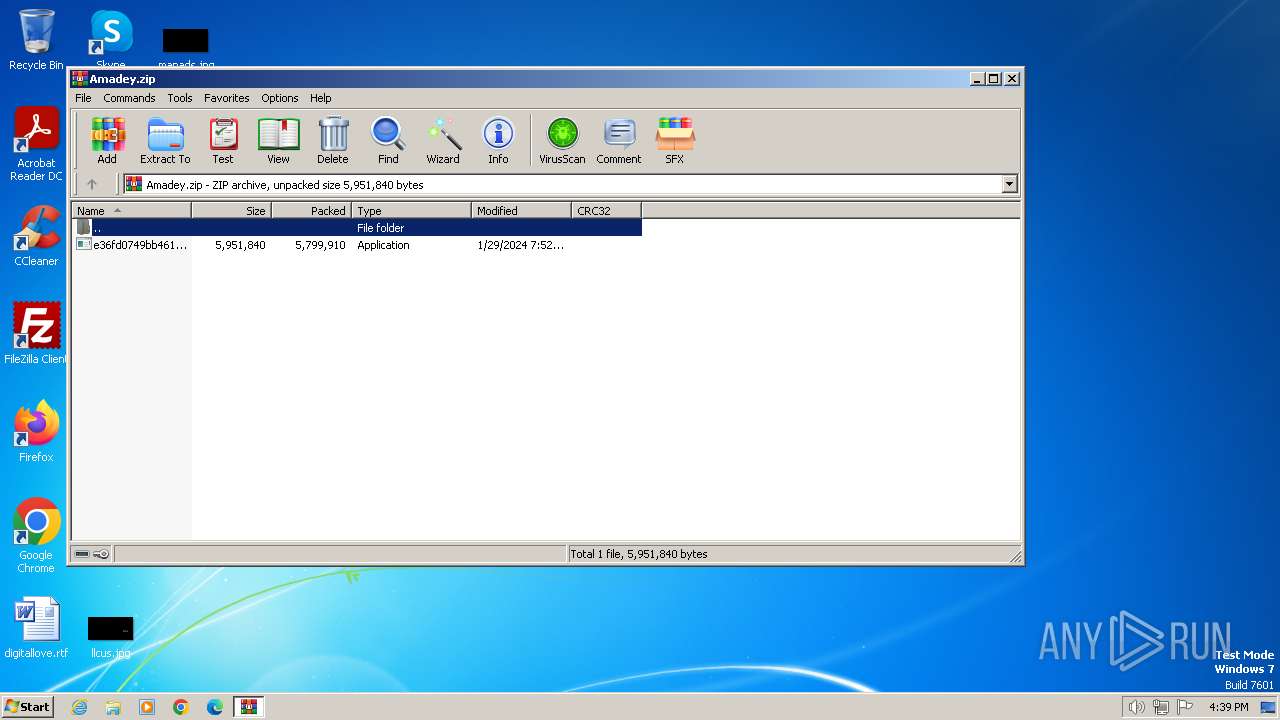
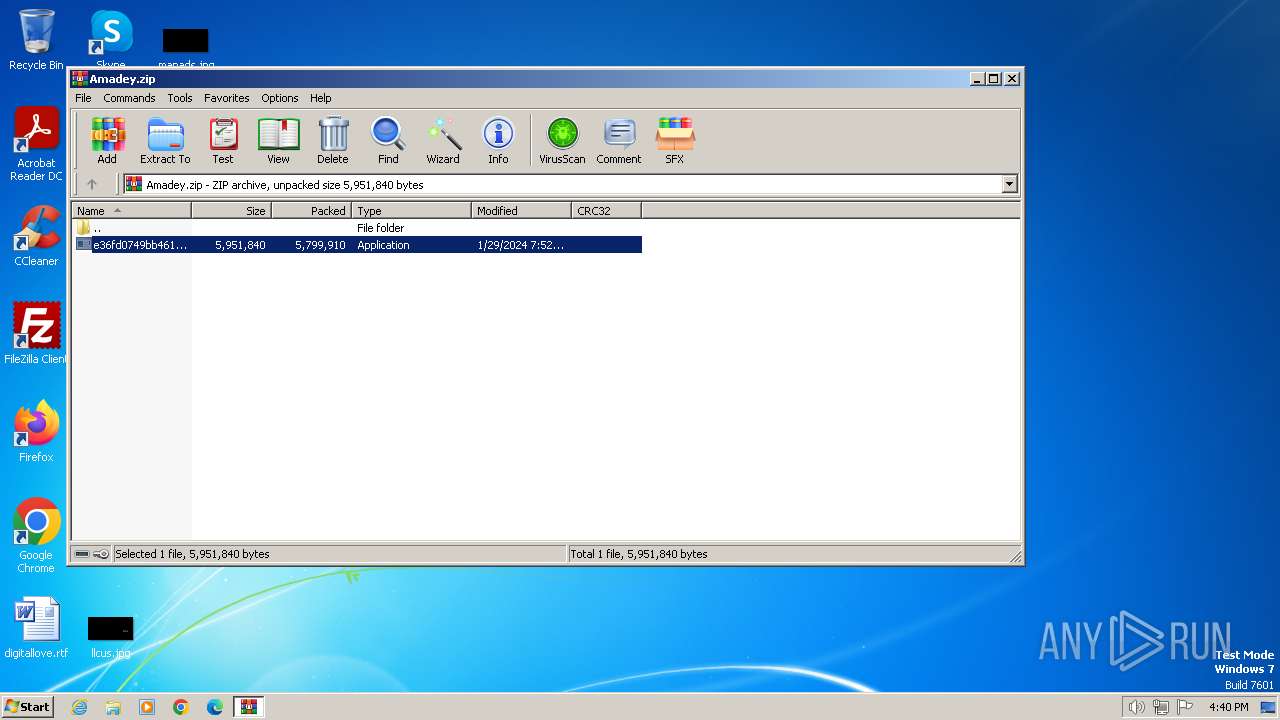
| File name: | Amadey.zip |
| Full analysis: | https://app.any.run/tasks/c4f14a3f-5445-4ffe-b565-5f9340149c74 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | February 09, 2024, 16:39:30 |
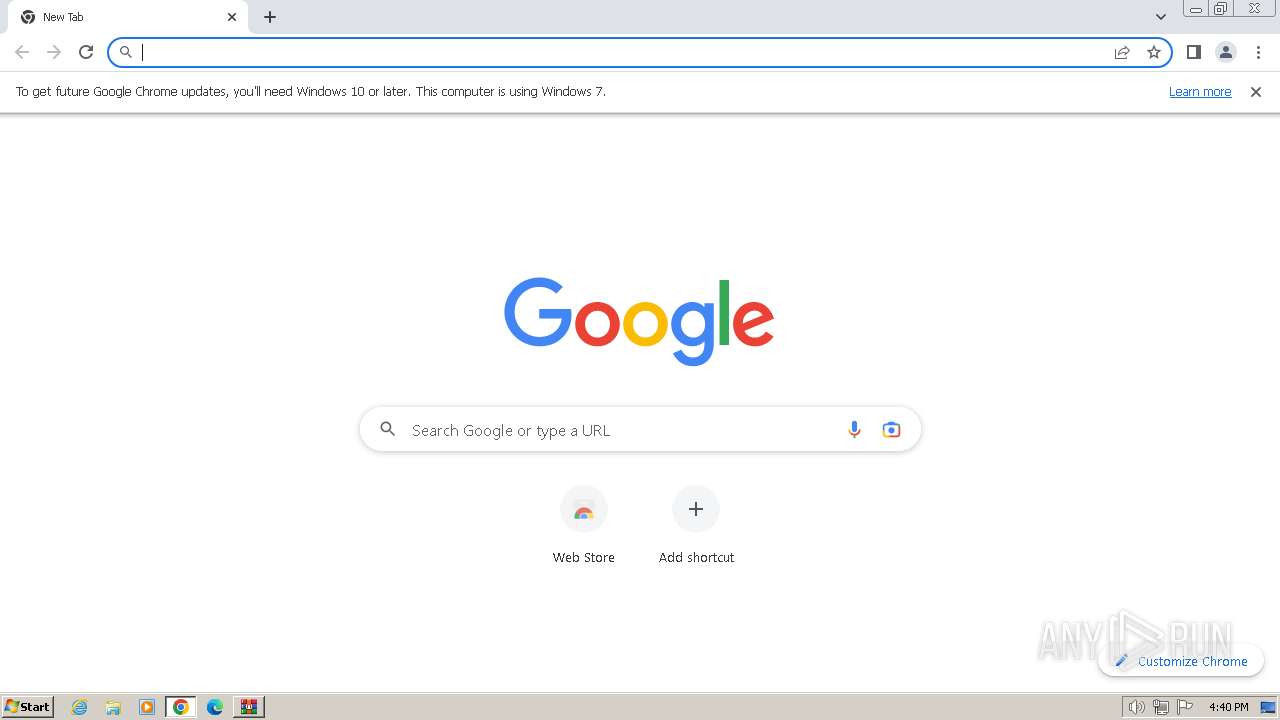
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
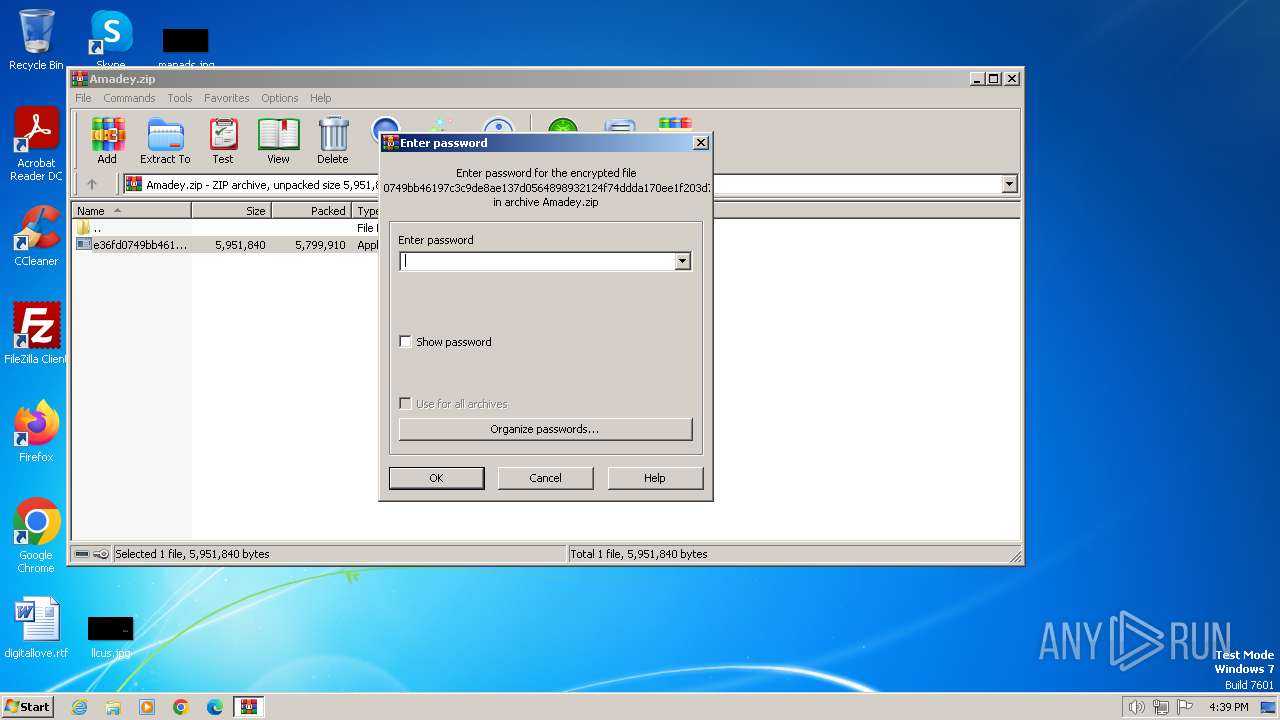
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | DAB5EFE9859A5B12FE00F4029DA6C3CB |
| SHA1: | C4B58A48D6618961EAEE6BC55C78D69DD7BC92E5 |
| SHA256: | DEA89F7CB29C4B385392AA46211C67605C7AAD51530A2CE8A7F24E5694BF9224 |
| SSDEEP: | 98304:DIMHtqmBSvt3krTNOlW2nWdsrFU3MMsRIYy84khdlPeH5HtXdwReJPWs46V/wcwT:ROFIGvnpIsmSw4fFHWH/o |
MALICIOUS
Changes the autorun value in the registry
- Utsysc.exe (PID: 3732)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3668)
- Utsysc.exe (PID: 3732)
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
Connects to the CnC server
- Utsysc.exe (PID: 3732)
- rundll32.exe (PID: 1696)
- rundll32.exe (PID: 2588)
AMADEY has been detected (SURICATA)
- Utsysc.exe (PID: 3732)
- rundll32.exe (PID: 1696)
- rundll32.exe (PID: 2588)
Steals credentials from Web Browsers
- rundll32.exe (PID: 1696)
Unusual connection from system programs
- rundll32.exe (PID: 1696)
- rundll32.exe (PID: 2588)
Actions looks like stealing of personal data
- rundll32.exe (PID: 1696)
SUSPICIOUS
Reads the Internet Settings
- Utsysc.exe (PID: 3732)
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
- rundll32.exe (PID: 1696)
- rundll32.exe (PID: 2588)
Reads security settings of Internet Explorer
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
- Utsysc.exe (PID: 3732)
- WinRAR.exe (PID: 3668)
Connects to the server without a host name
- Utsysc.exe (PID: 3732)
- rundll32.exe (PID: 2588)
Process requests binary or script from the Internet
- Utsysc.exe (PID: 3732)
Starts itself from another location
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
Executable content was dropped or overwritten
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
- Utsysc.exe (PID: 3732)
Starts POWERSHELL.EXE for commands execution
- rundll32.exe (PID: 1696)
Uses RUNDLL32.EXE to load library
- Utsysc.exe (PID: 3732)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 1696)
Uses NETSH.EXE to obtain data on the network
- rundll32.exe (PID: 1696)
Accesses Microsoft Outlook profiles
- rundll32.exe (PID: 1696)
INFO
Checks supported languages
- Utsysc.exe (PID: 3732)
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
Reads the computer name
- Utsysc.exe (PID: 3732)
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
Create files in a temporary directory
- Utsysc.exe (PID: 3732)
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
Checks proxy server information
- Utsysc.exe (PID: 3732)
- rundll32.exe (PID: 1696)
- rundll32.exe (PID: 2588)
Reads the machine GUID from the registry
- Utsysc.exe (PID: 3732)
- e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe (PID: 3972)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3668)
Creates files or folders in the user directory
- Utsysc.exe (PID: 3732)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 1696)
- rundll32.exe (PID: 2588)
Application launched itself
- chrome.exe (PID: 3776)
Manual execution by a user
- chrome.exe (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:01:29 07:52:10 |
| ZipCRC: | 0x1504441e |
| ZipCompressedSize: | 5799910 |
| ZipUncompressedSize: | 5951840 |
| ZipFileName: | e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe |
Total processes
59
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2116 --field-trial-handle=1160,i,1320336932810761098,10248675653920352427,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1348 | powershell -Command Compress-Archive -Path 'C:\Users\admin\AppData\Local\Temp\_Files_\' -DestinationPath 'C:\Users\admin\AppData\Local\Temp\302019708150_Desktop.zip' -CompressionLevel Optimal | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1696 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\cred.dll, Main | C:\Windows\System32\rundll32.exe | Utsysc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1140 --field-trial-handle=1160,i,1320336932810761098,10248675653920352427,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1528 --field-trial-handle=1160,i,1320336932810761098,10248675653920352427,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1612 --field-trial-handle=1160,i,1320336932810761098,10248675653920352427,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2588 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\clip.dll, Main | C:\Windows\System32\rundll32.exe | Utsysc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1316 --field-trial-handle=1160,i,1320336932810761098,10248675653920352427,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2648 | netsh wlan show profiles | C:\Windows\System32\netsh.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 638
Read events
14 398
Write events
216
Delete events
24
Modification events
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Amadey.zip | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
6
Suspicious files
21
Text files
29
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18a071.TMP | — | |
MD5:— | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3668.26768\e36fd0749bb46197c3c9de8ae137d0564898932124f74ddda170ee1f203d72d0.exe | executable | |
MD5:807D1D2867127684704CDCED73584329 | SHA256:E36FD0749BB46197C3C9DE8AE137D0564898932124F74DDDA170EE1F203D72D0 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18a081.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1348 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cesknmqk.5n4.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1348 | powershell.exe | C:\Users\admin\AppData\Local\Temp\302019708150_Desktop.zip | compressed | |
MD5:76CDB2BAD9582D23C1F6F4D868218D6C | SHA256:8739C76E681F900923B900C9DF0EF75CF421D39CABB54650C4B9AD19B6A76D85 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
15
DNS requests
8
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3732 | Utsysc.exe | POST | 200 | 185.172.128.5:80 | http://185.172.128.5/v8sjh3hs8/index.php | unknown | text | 7 b | unknown |
3732 | Utsysc.exe | GET | 200 | 185.172.128.5:80 | http://185.172.128.5/v8sjh3hs8/Plugins/cred.dll | unknown | executable | 1.03 Mb | unknown |
2588 | rundll32.exe | POST | 200 | 185.172.128.5:80 | http://185.172.128.5/v8sjh3hs8/index.php | unknown | text | 34 b | unknown |
3732 | Utsysc.exe | GET | 200 | 185.172.128.5:80 | http://185.172.128.5/v8sjh3hs8/Plugins/clip.dll | unknown | executable | 102 Kb | unknown |
1696 | rundll32.exe | POST | 200 | 185.172.128.5:80 | http://185.172.128.5/v8sjh3hs8/index.php | unknown | binary | 1 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3732 | Utsysc.exe | 185.172.128.5:80 | — | OOO Nadym Svyaz Service | RU | malicious |
1696 | rundll32.exe | 185.172.128.5:80 | — | OOO Nadym Svyaz Service | RU | malicious |
3776 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2592 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2592 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
2592 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
2588 | rundll32.exe | 185.172.128.5:80 | — | OOO Nadym Svyaz Service | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3732 | Utsysc.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
3732 | Utsysc.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .dll file with no User-Agent |
3732 | Utsysc.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Payload Request (GET) M2 |
3732 | Utsysc.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3732 | Utsysc.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1696 | rundll32.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
1696 | rundll32.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
3732 | Utsysc.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
3732 | Utsysc.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .dll file with no User-Agent |
3732 | Utsysc.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Payload Request (GET) M1 |
5 ETPRO signatures available at the full report