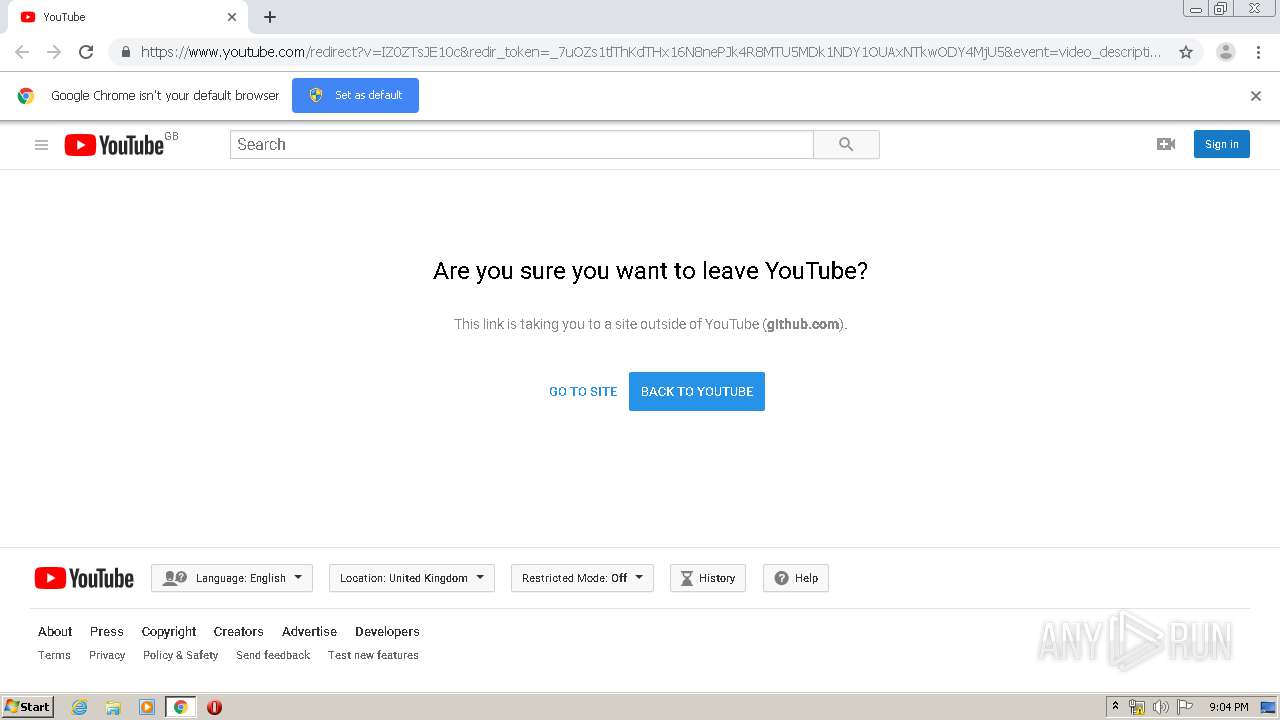
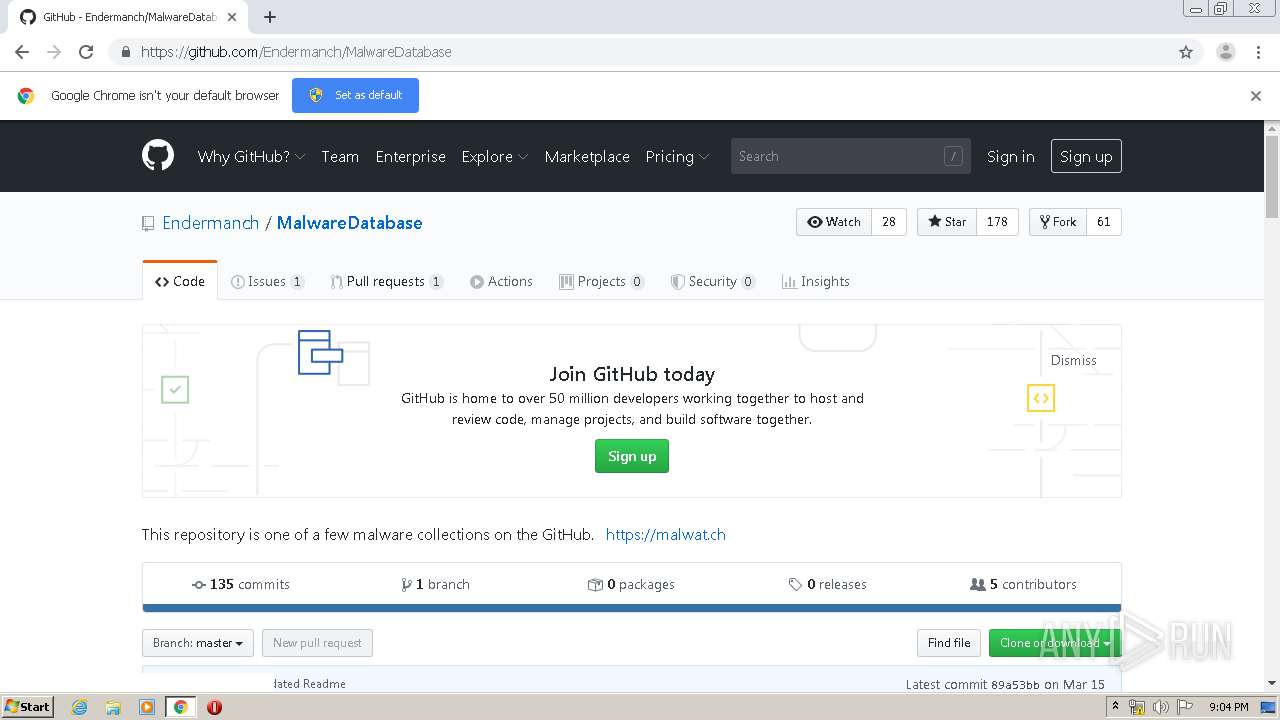
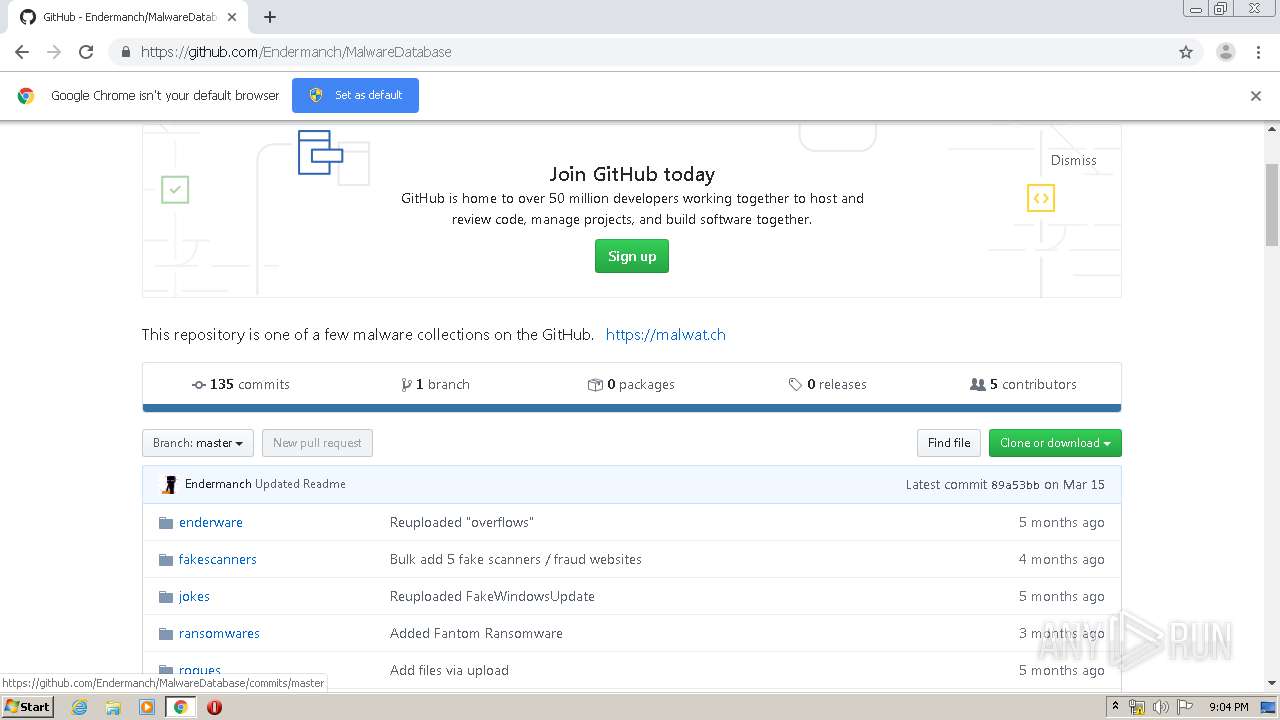
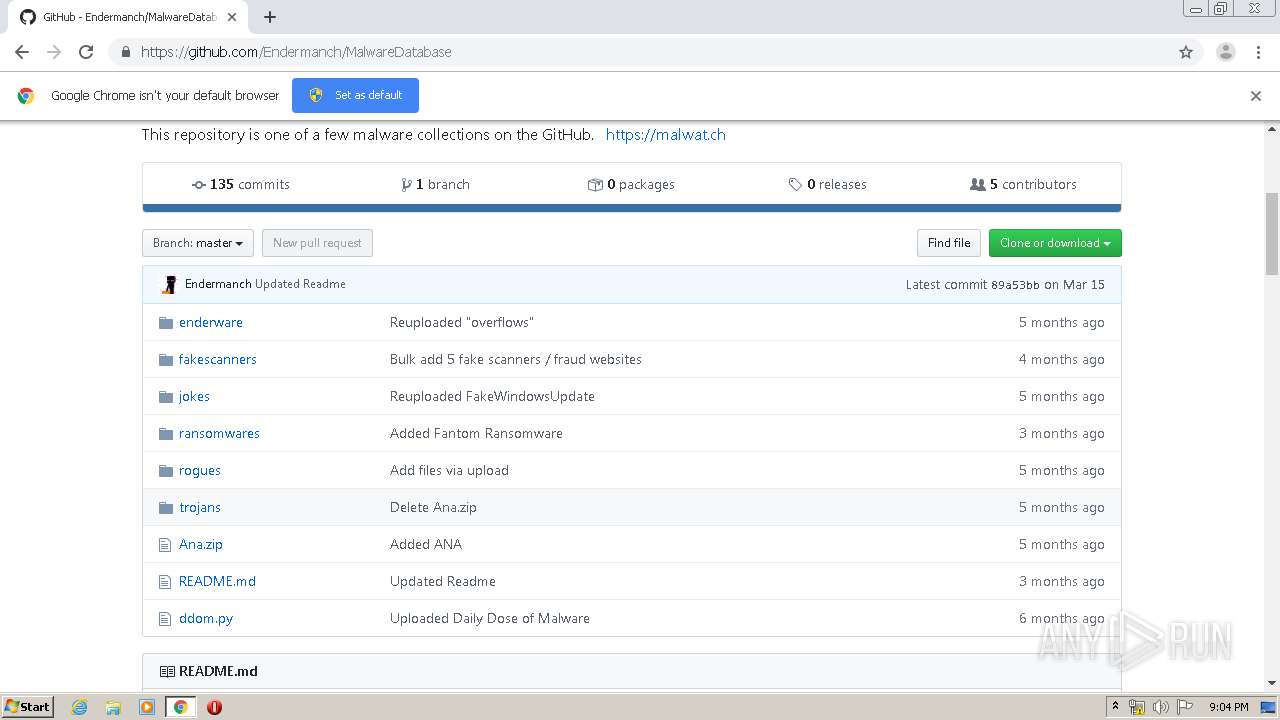
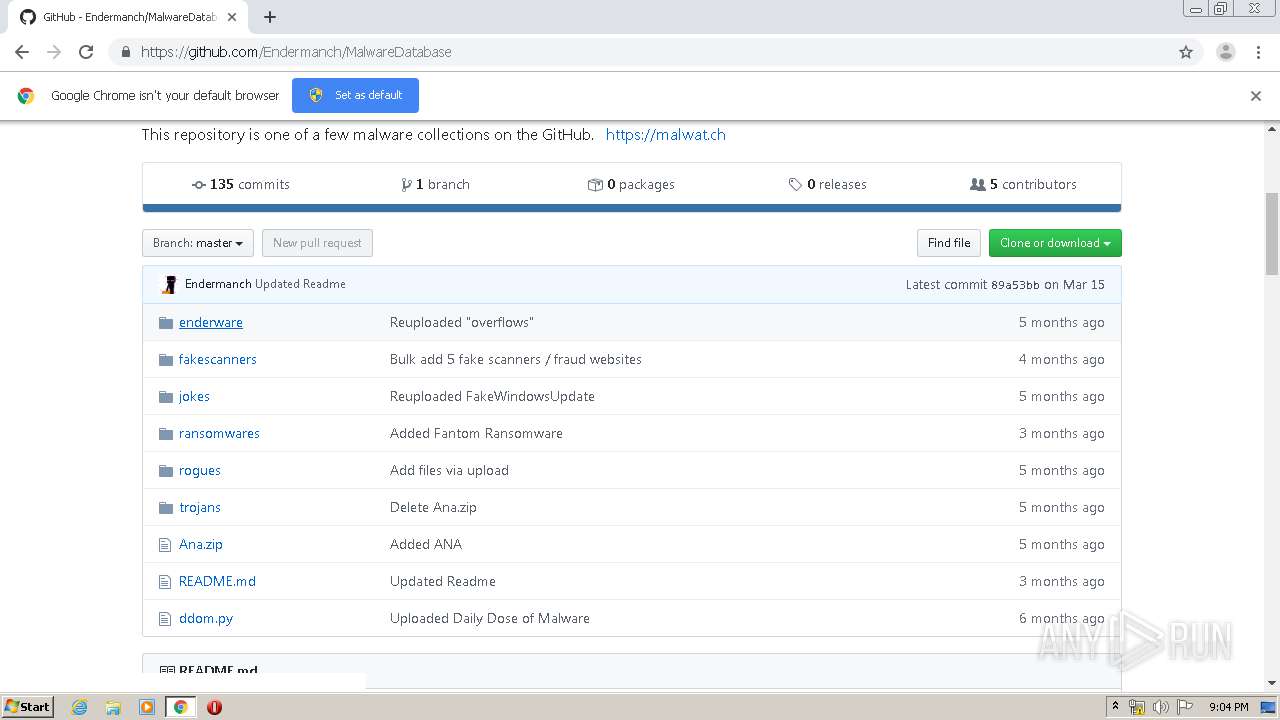
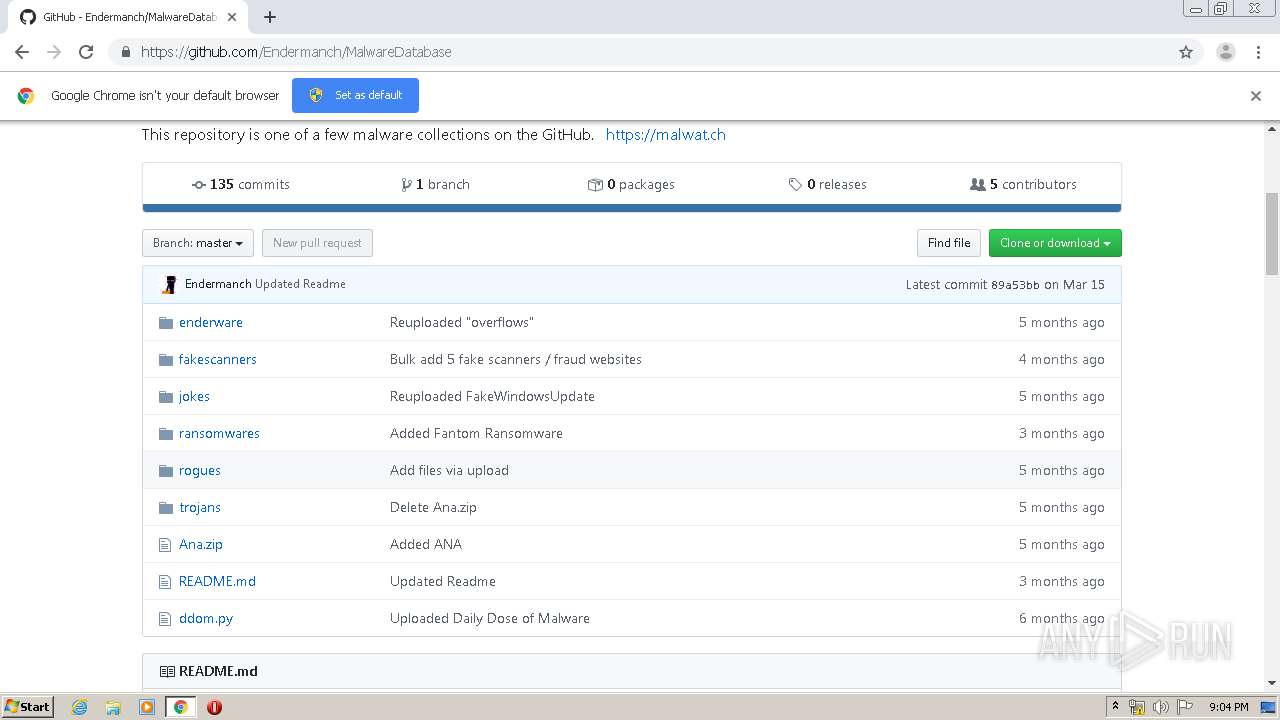
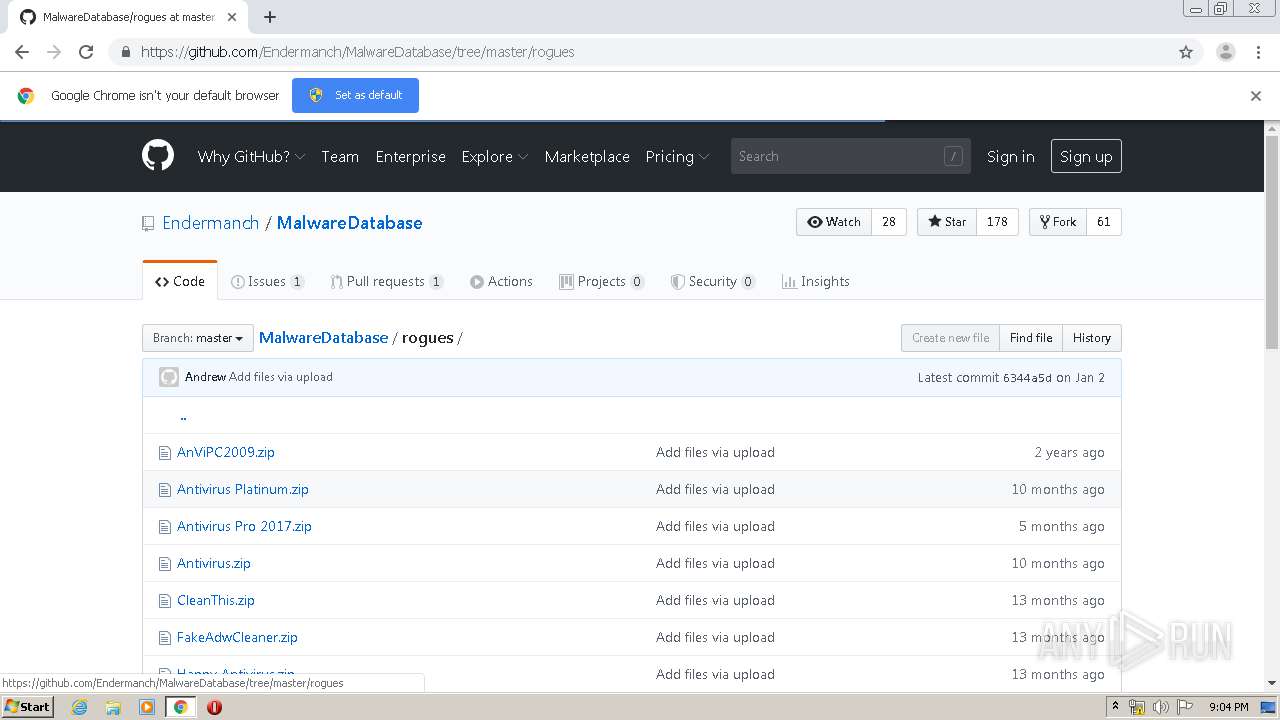
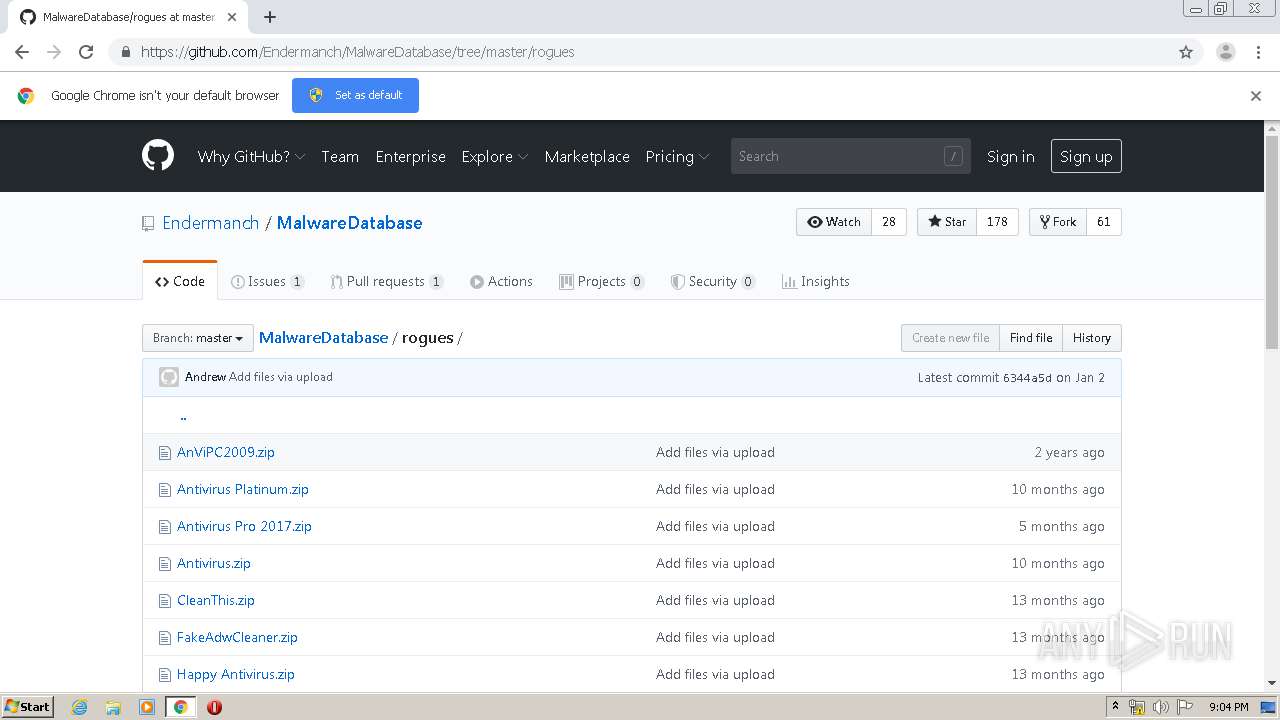
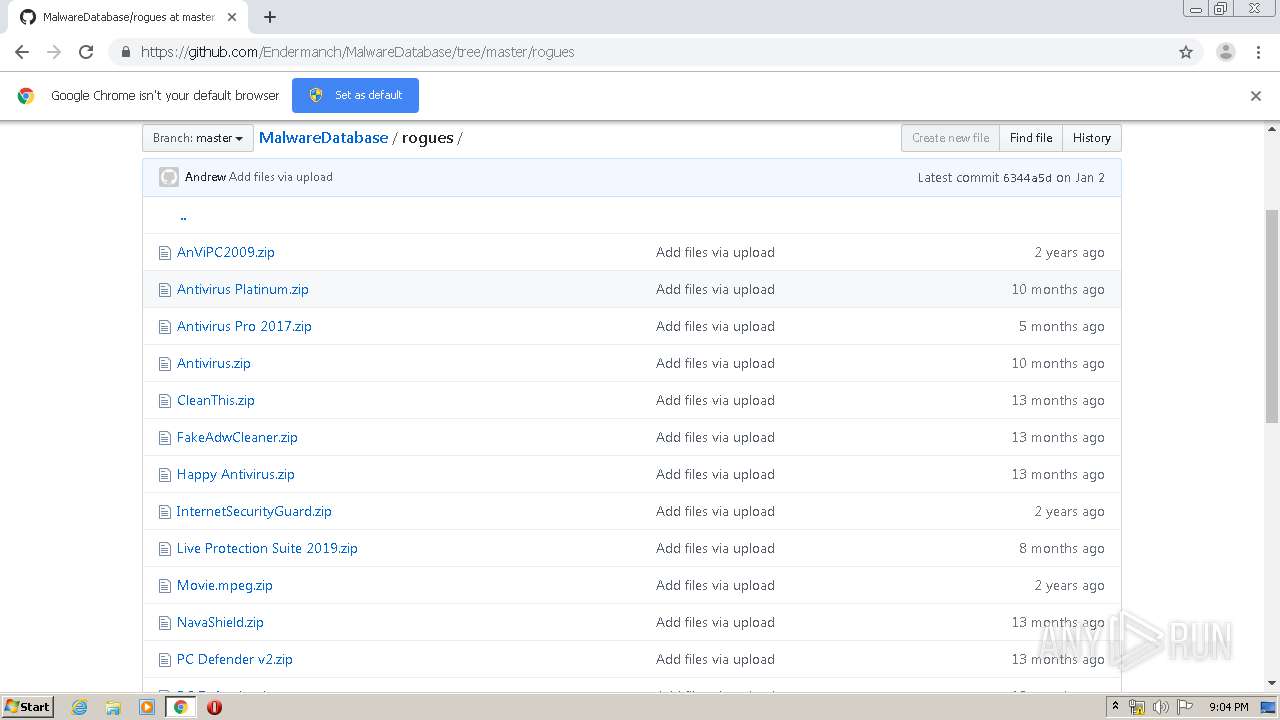
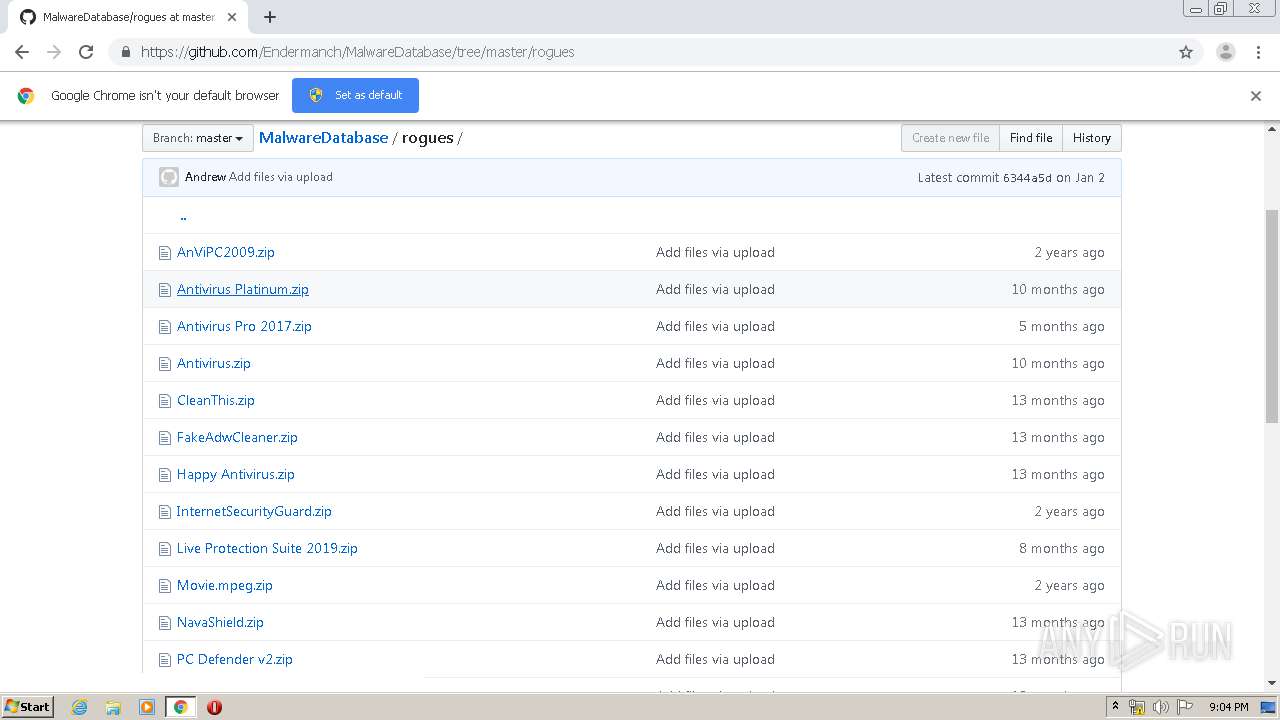
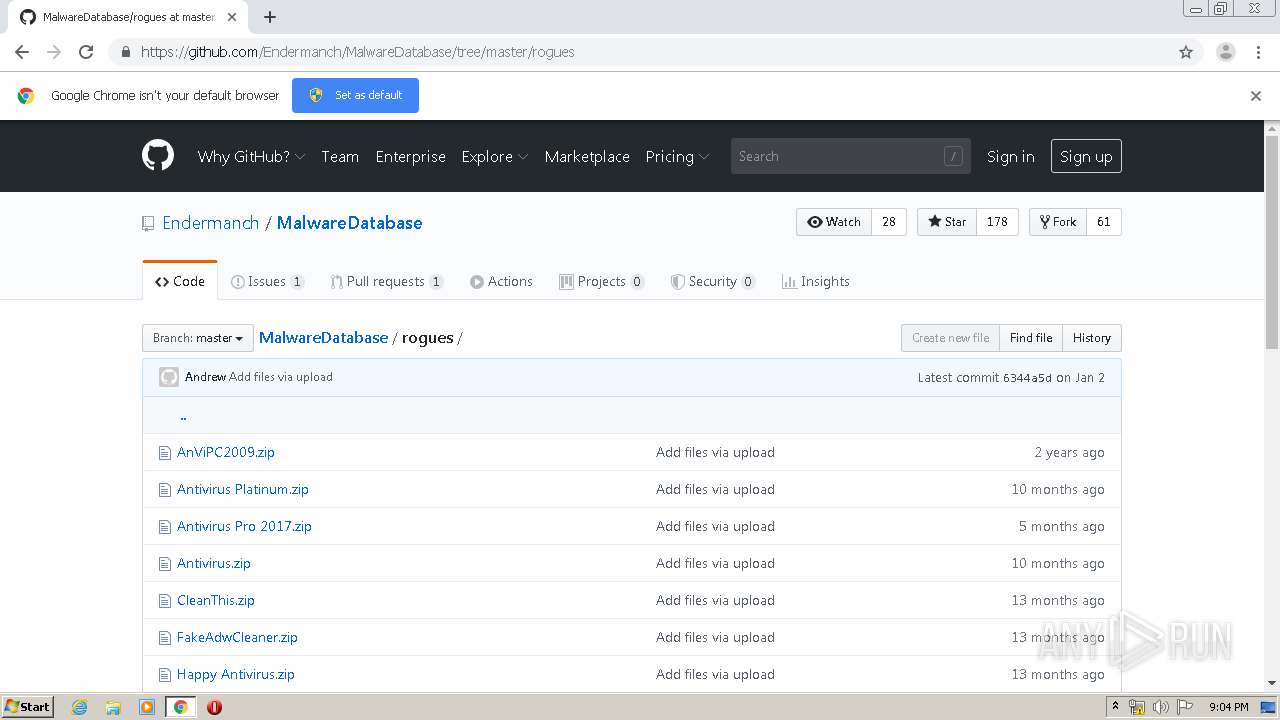
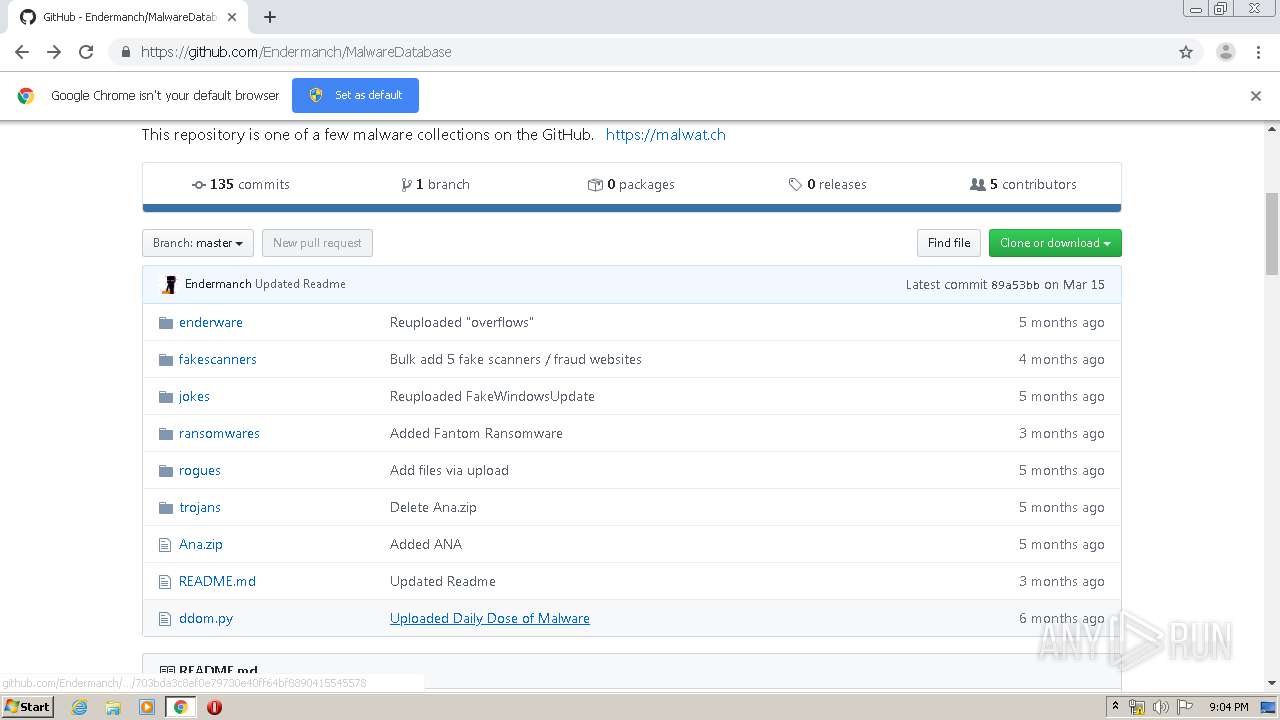
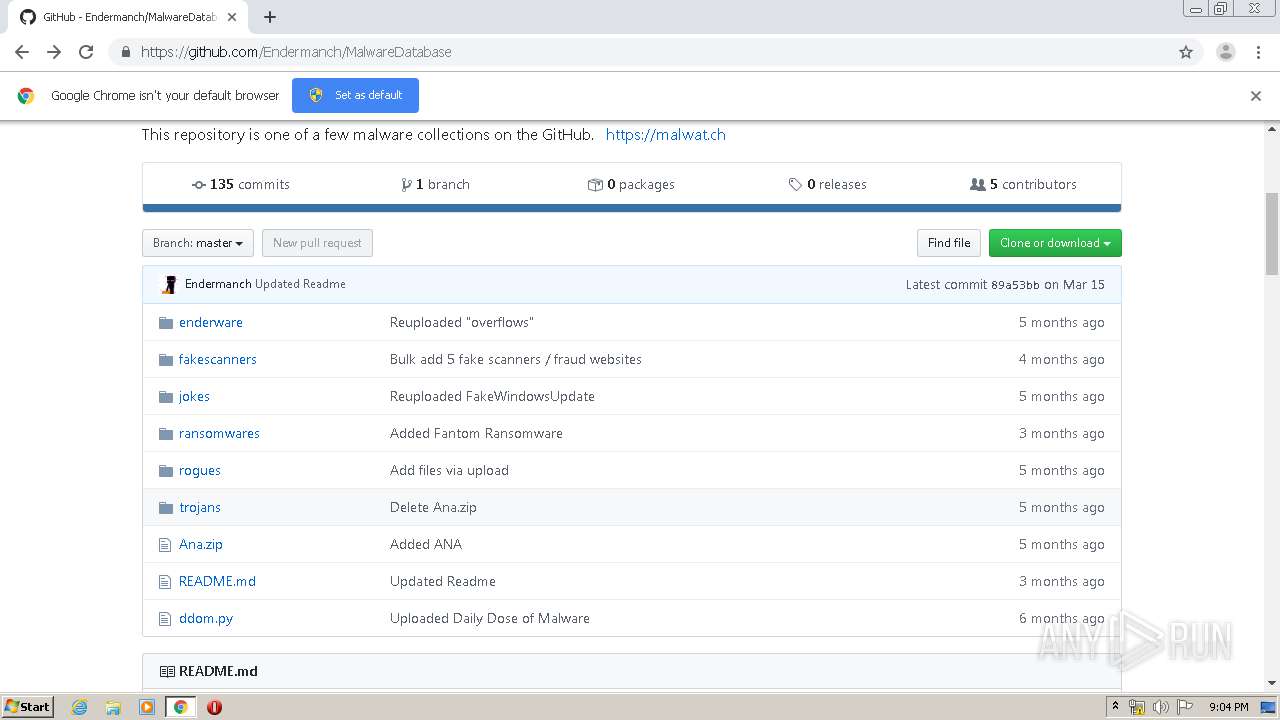
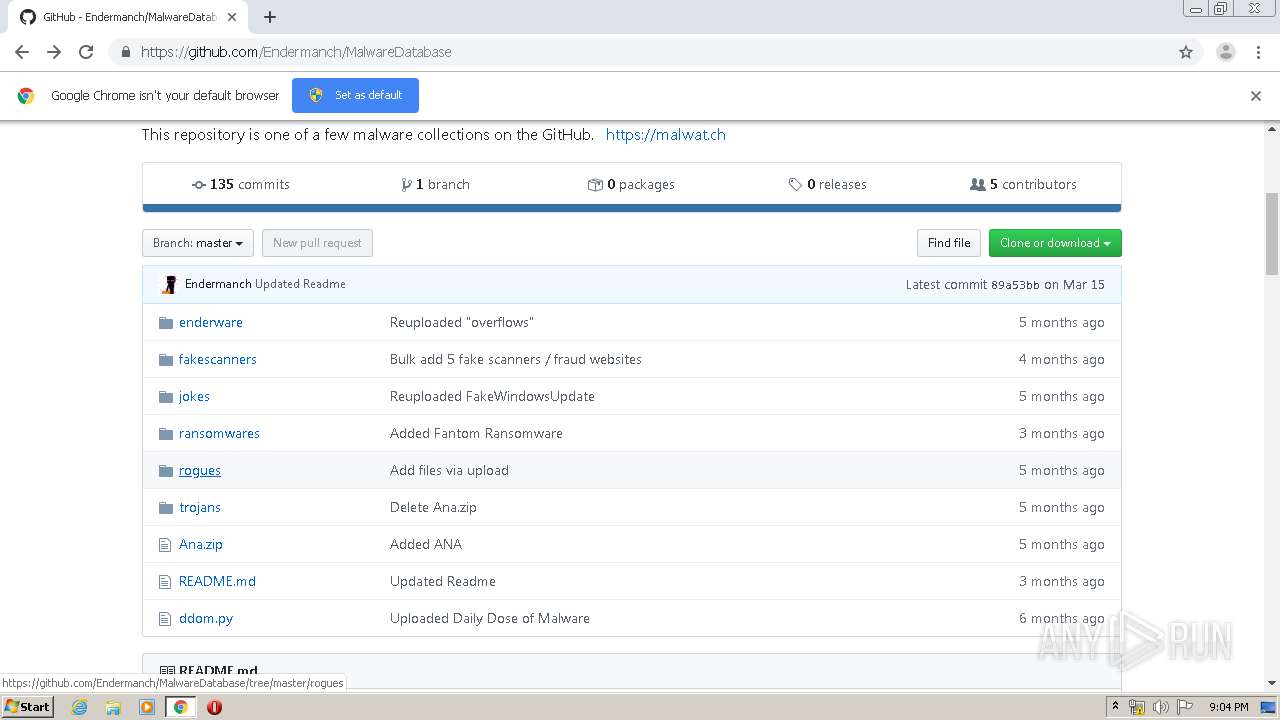
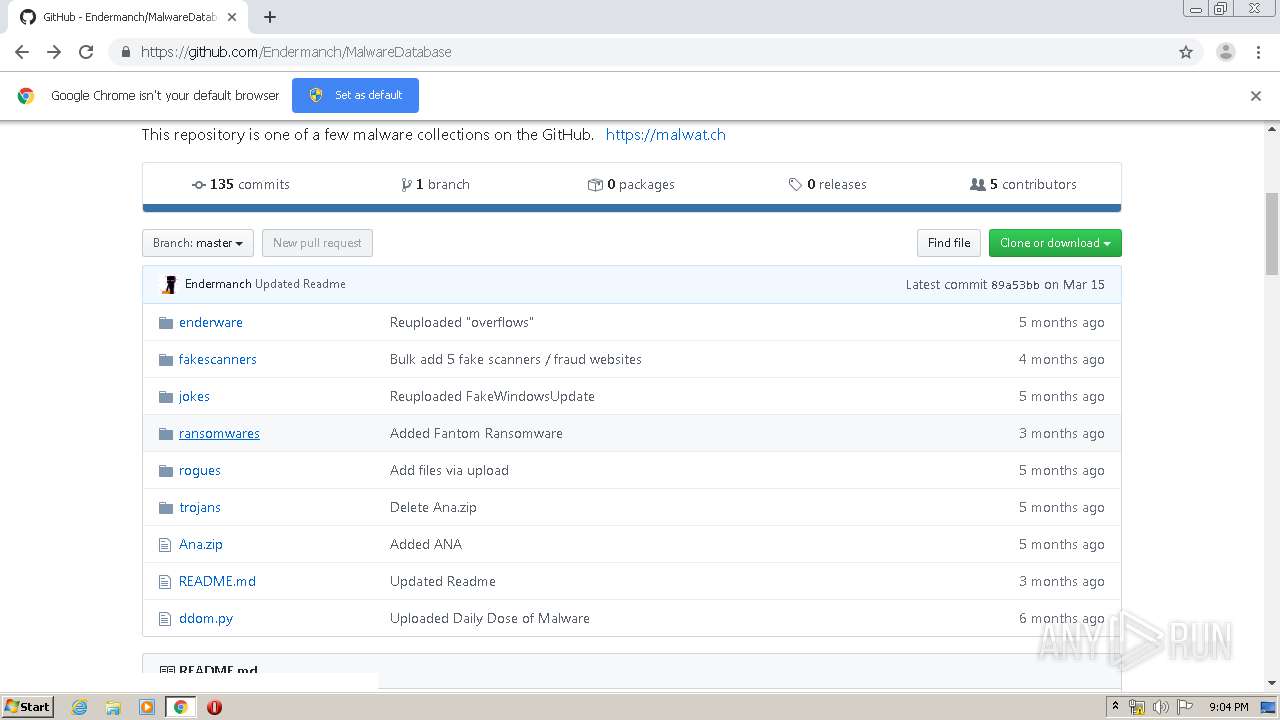
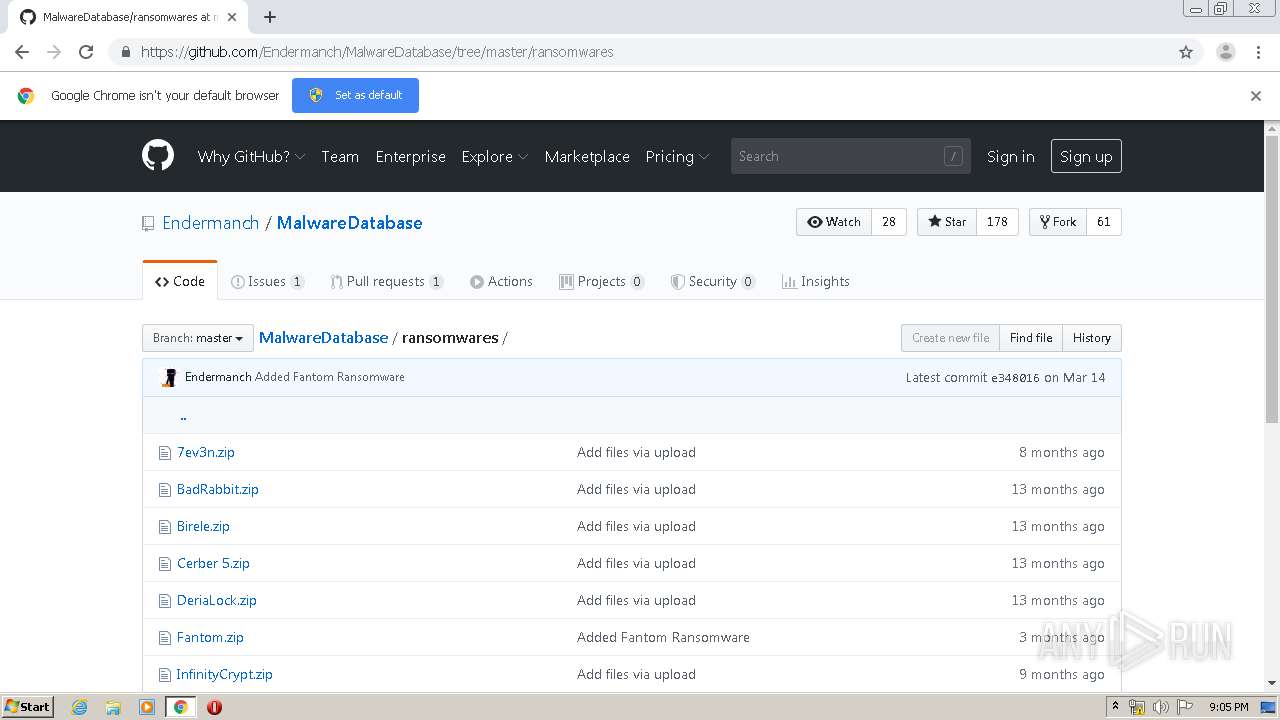
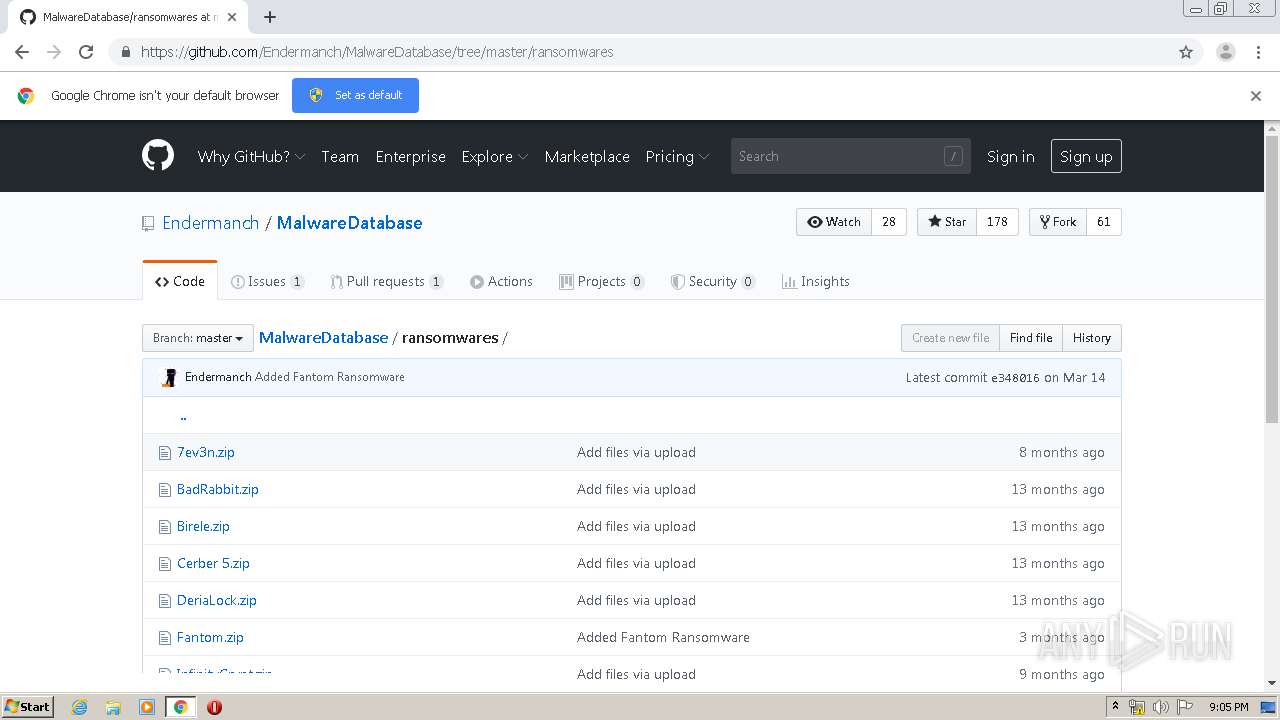
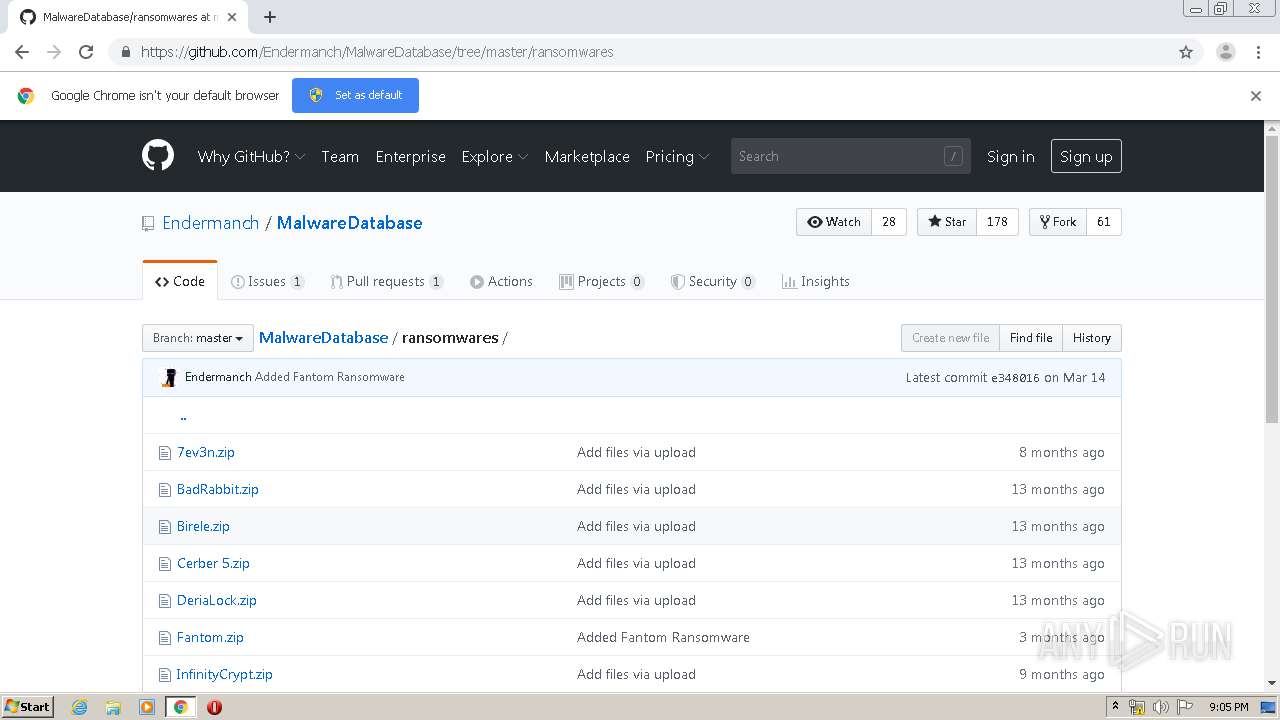
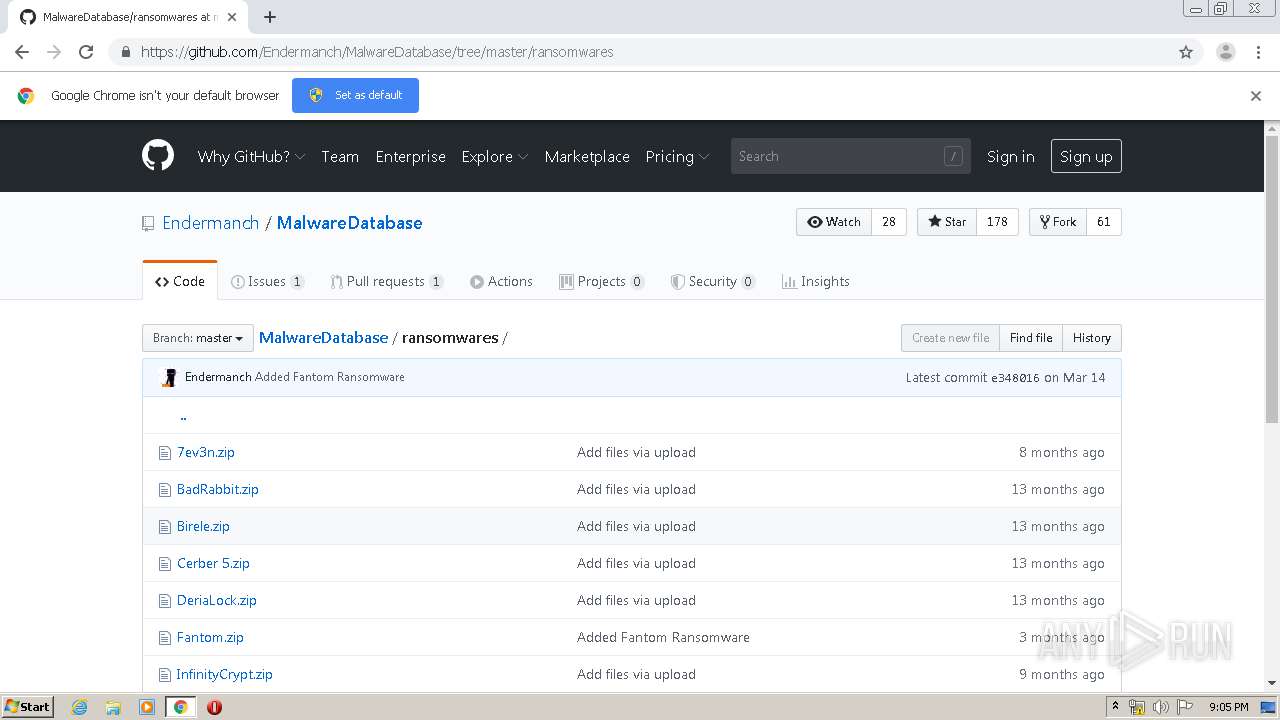
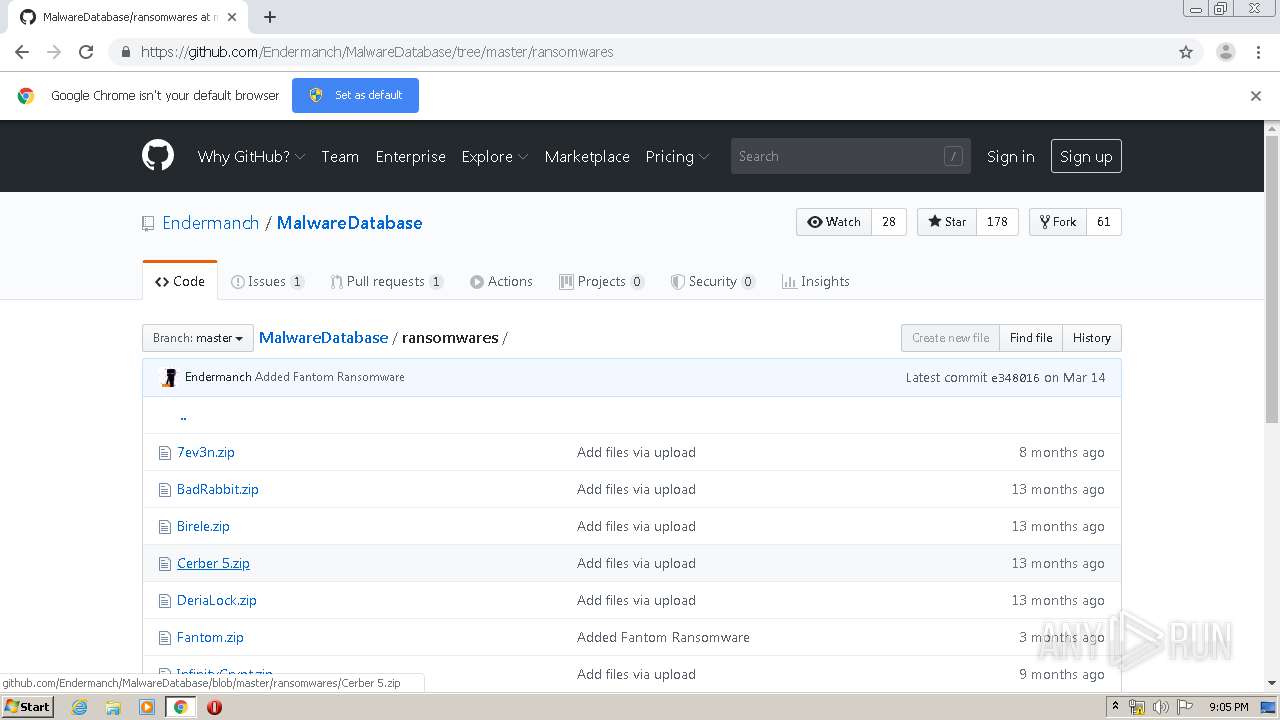
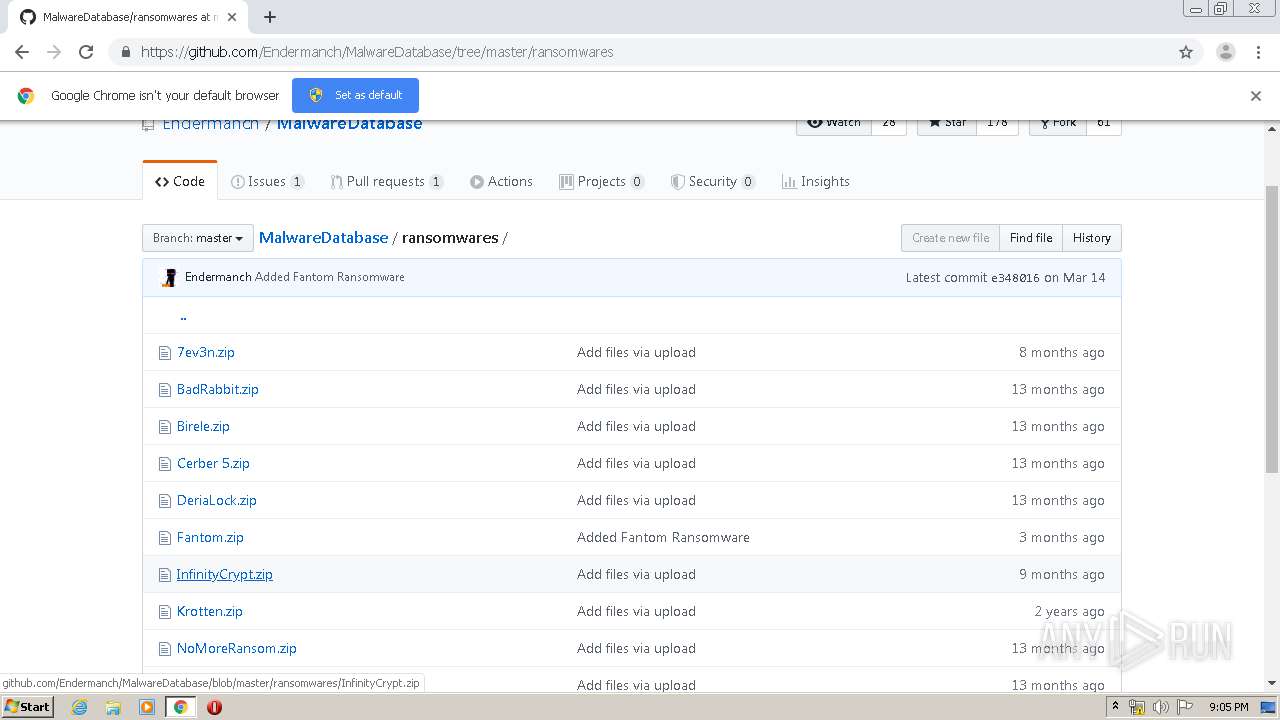
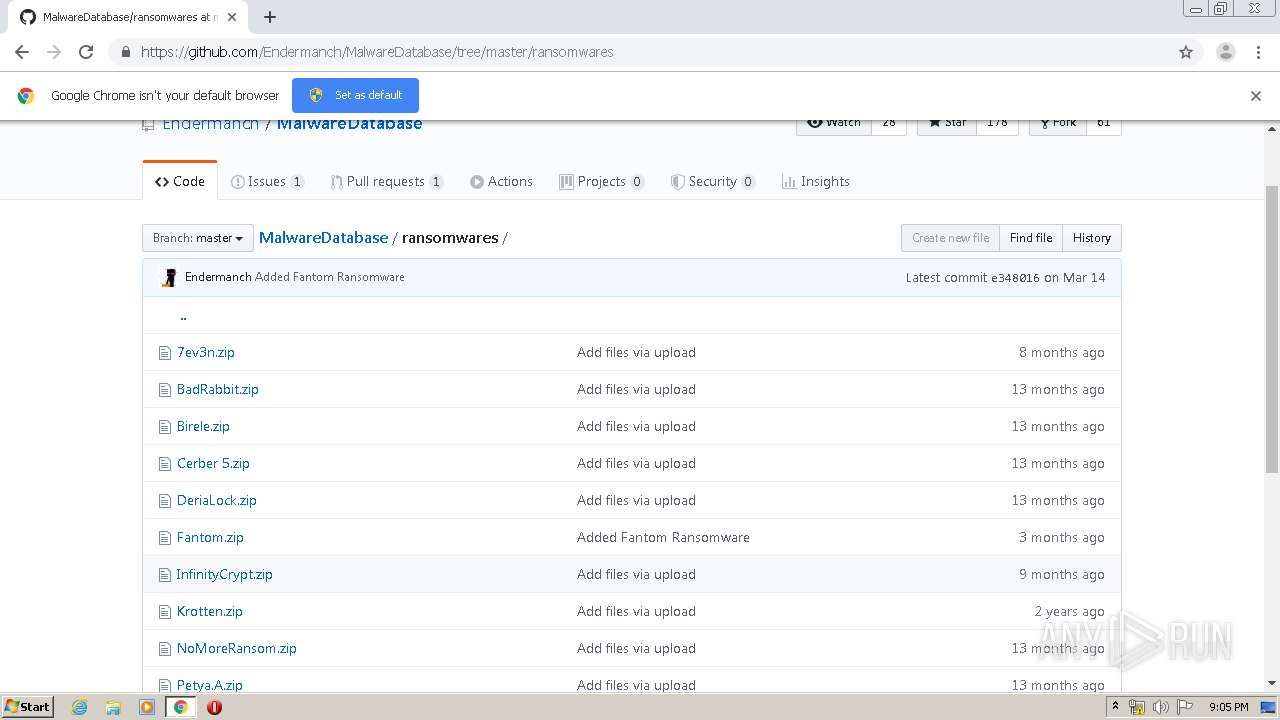
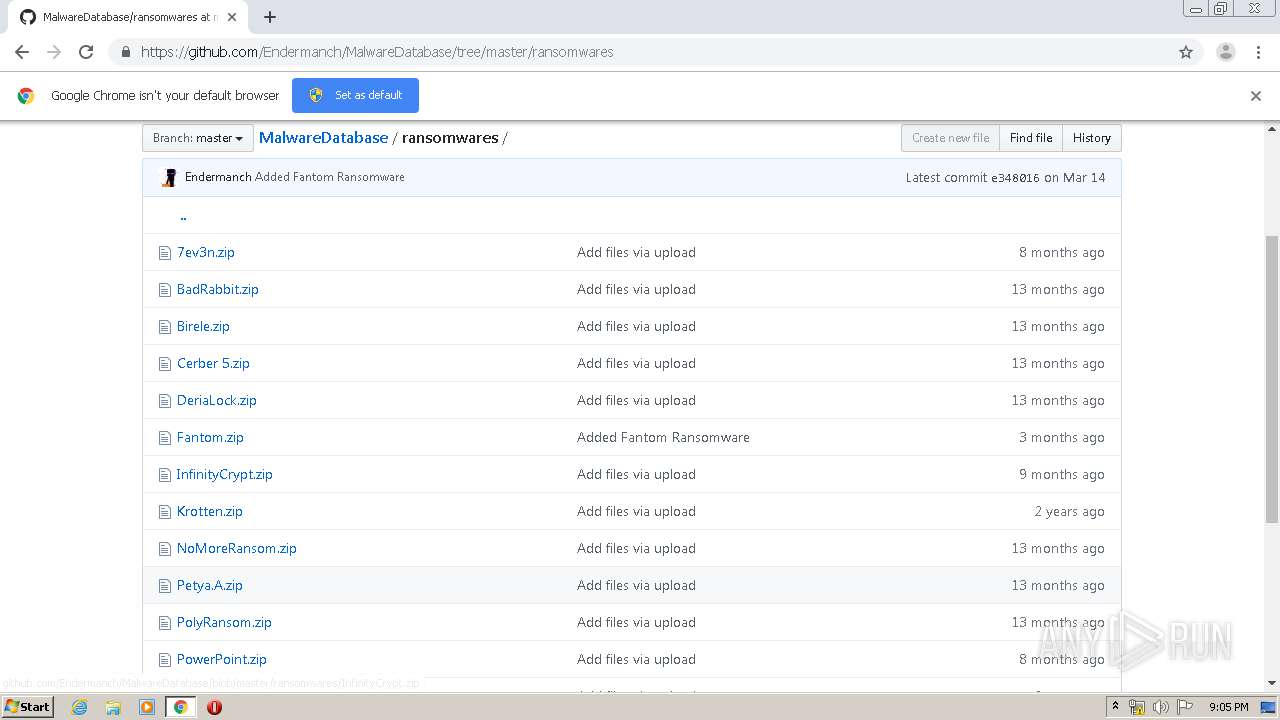
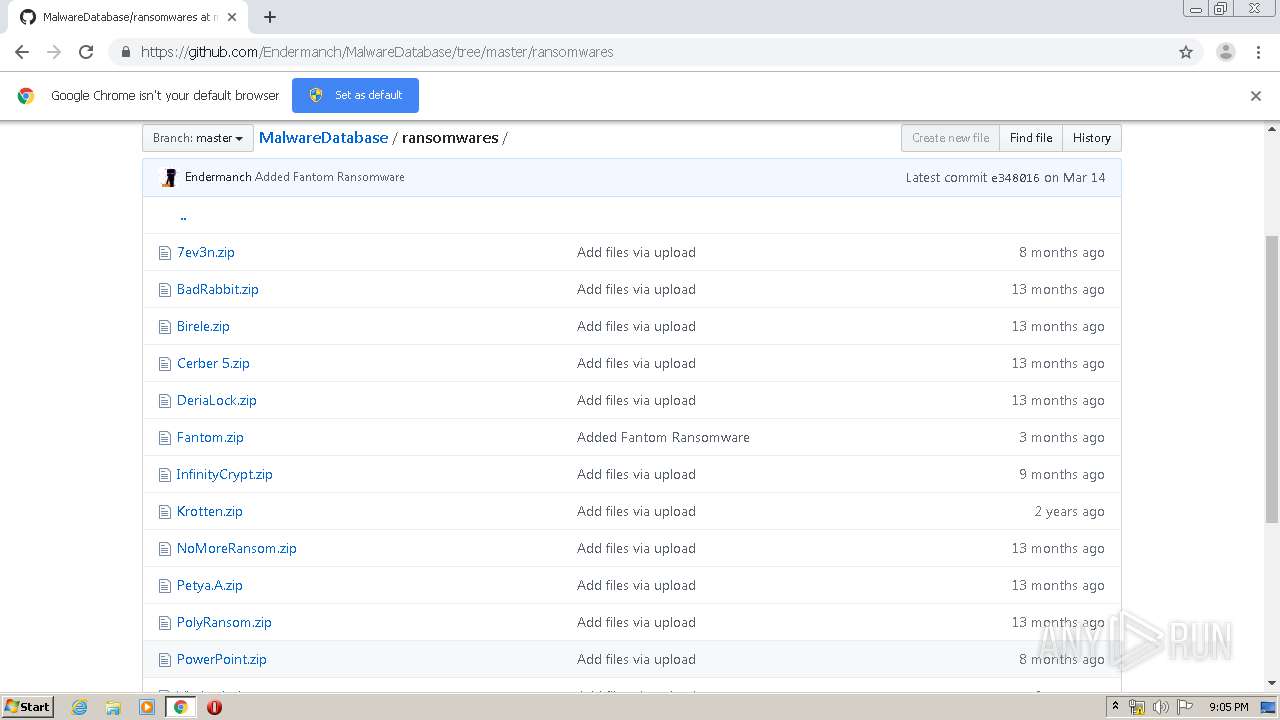
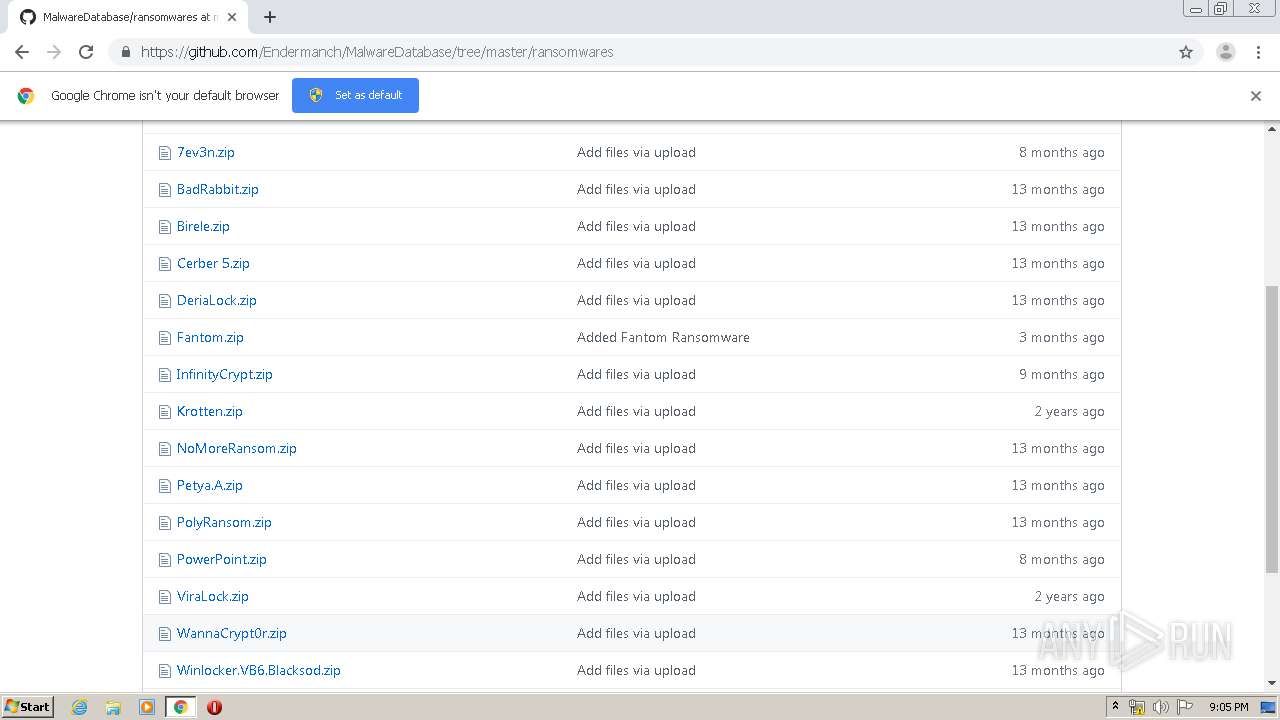
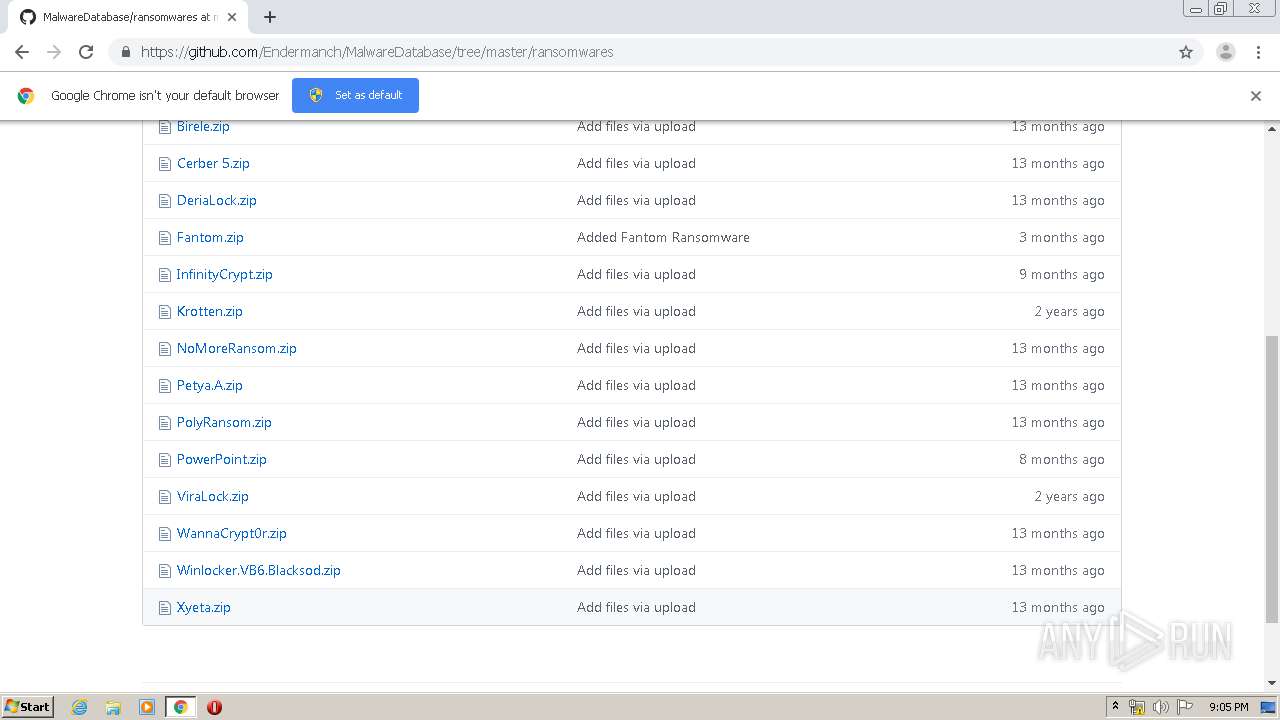
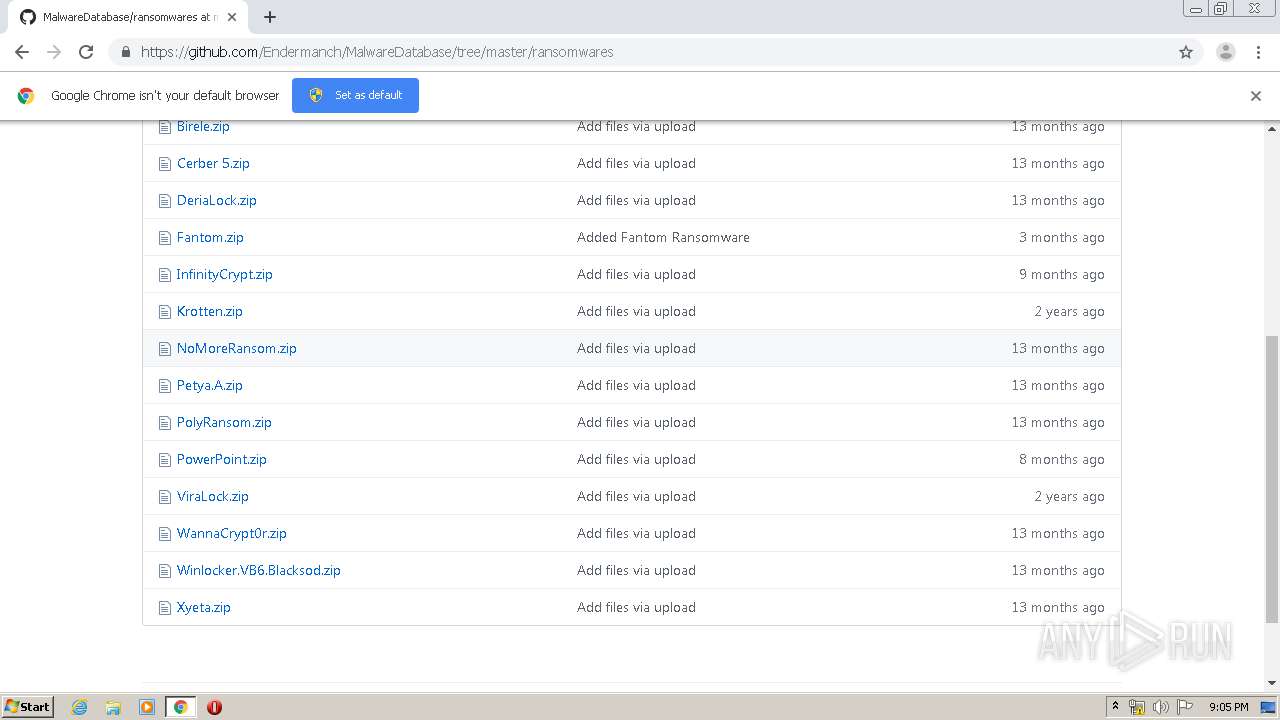
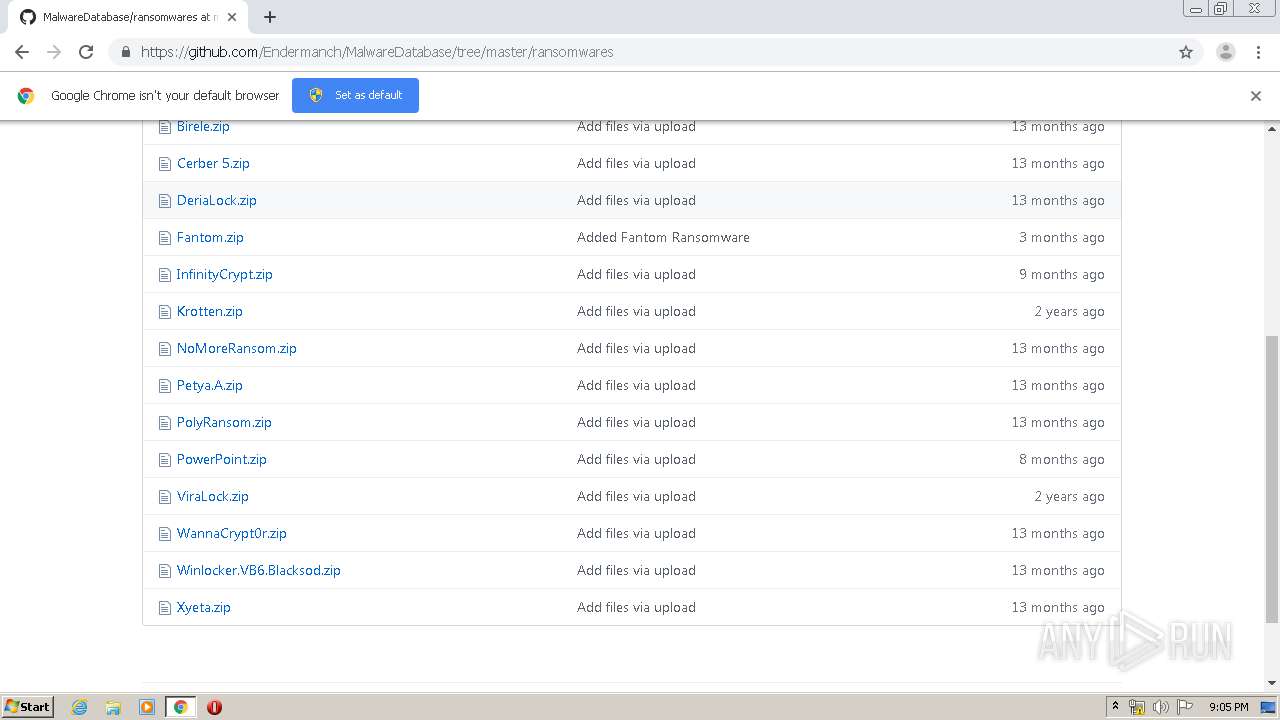
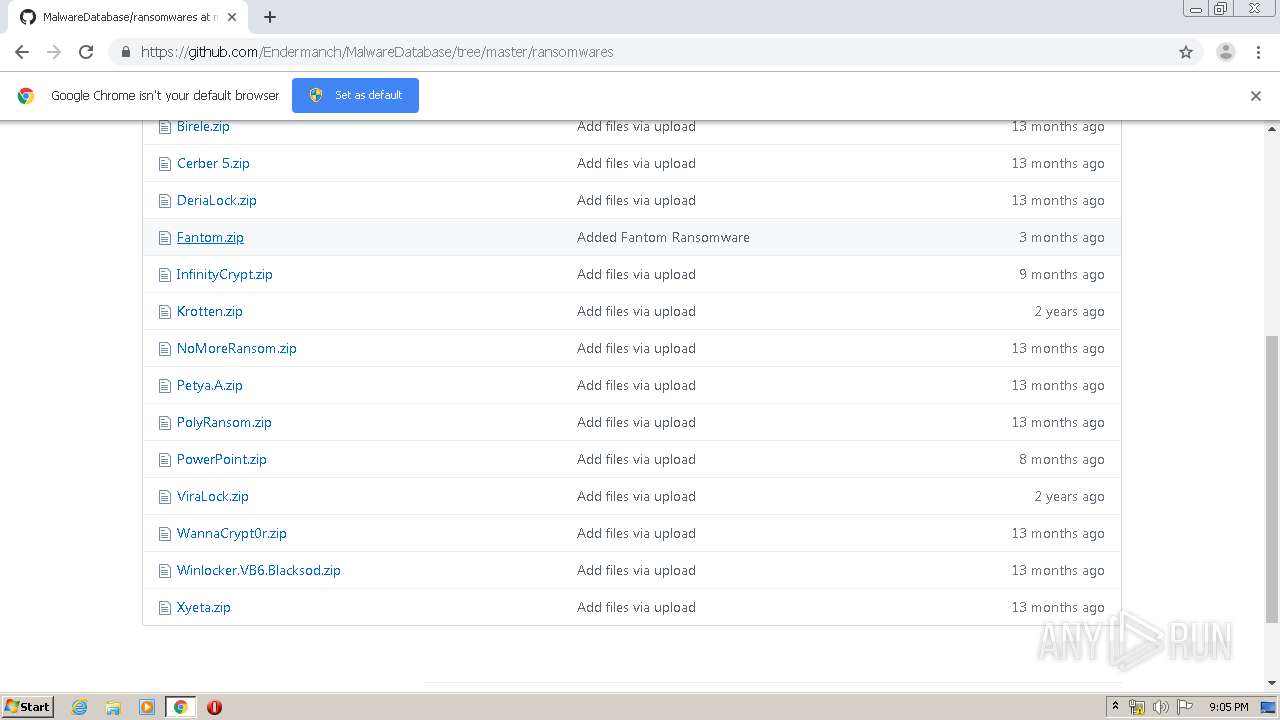
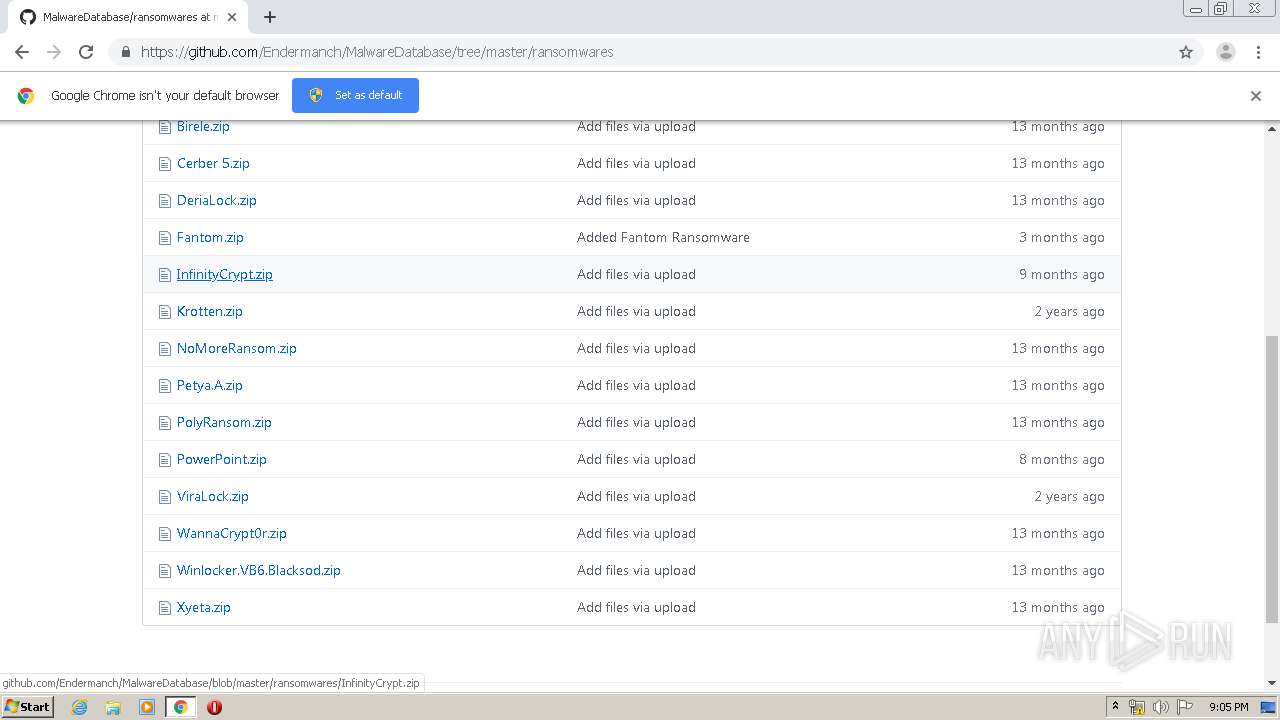
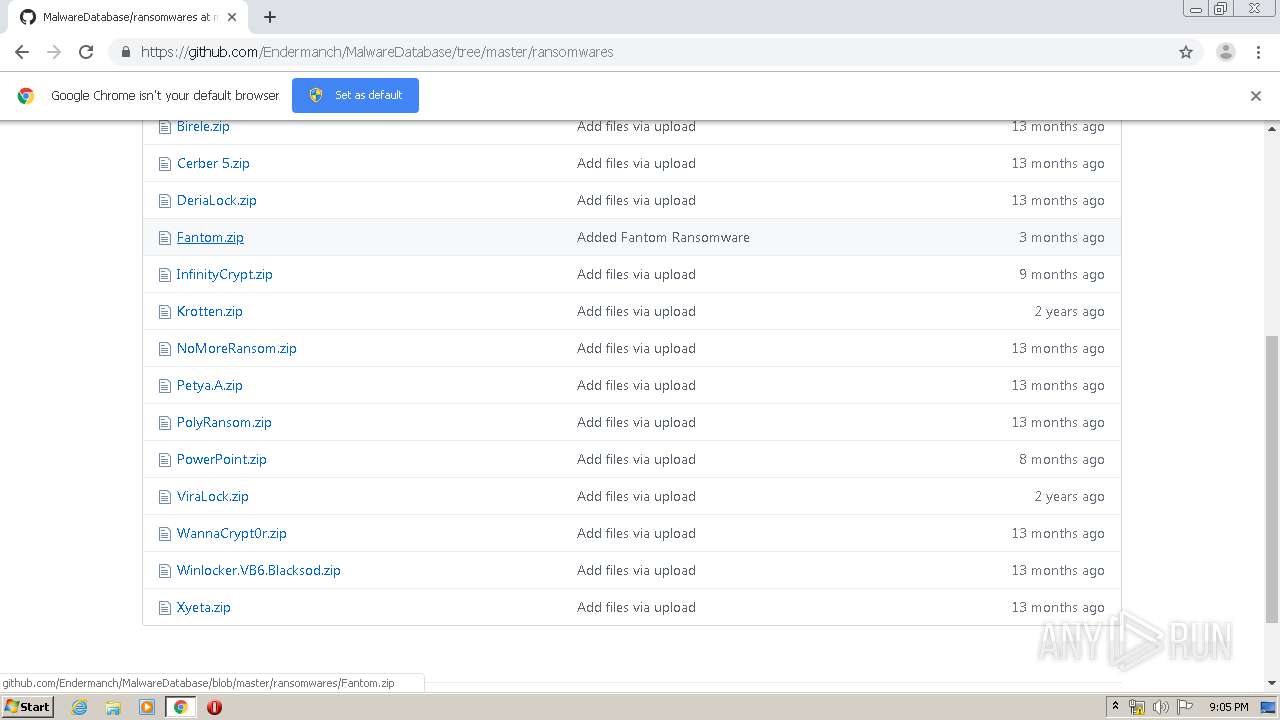
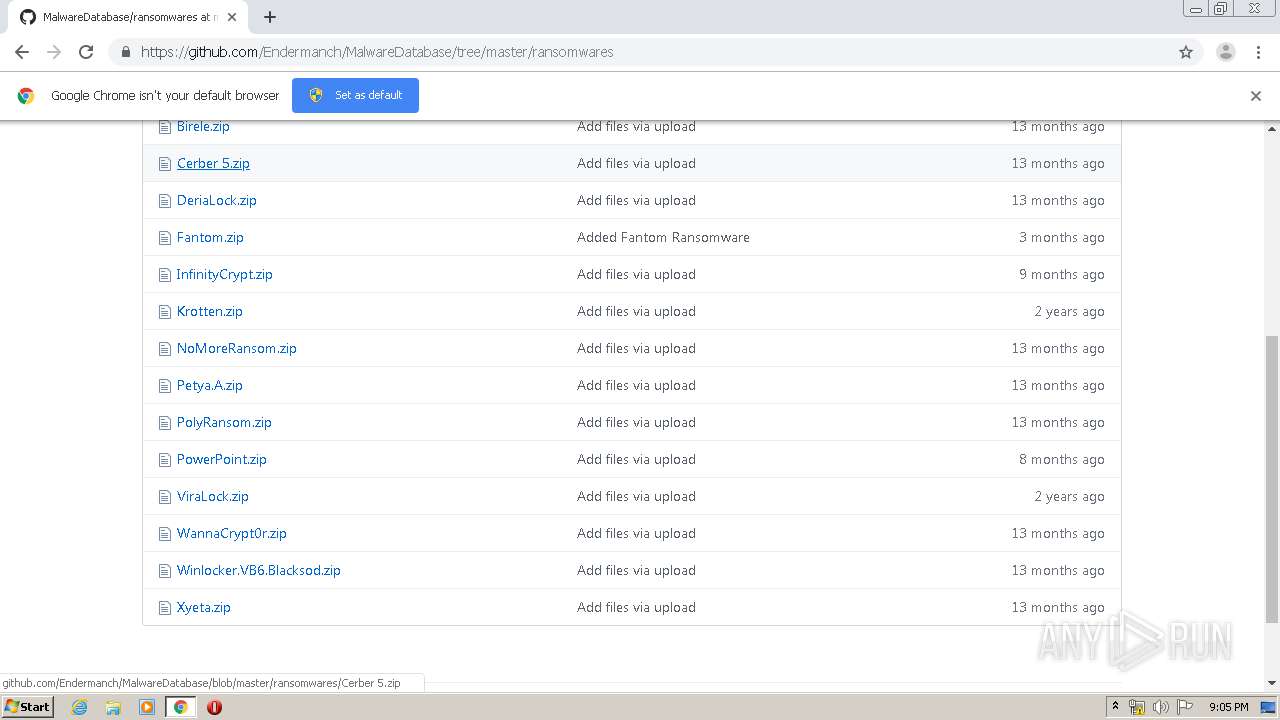
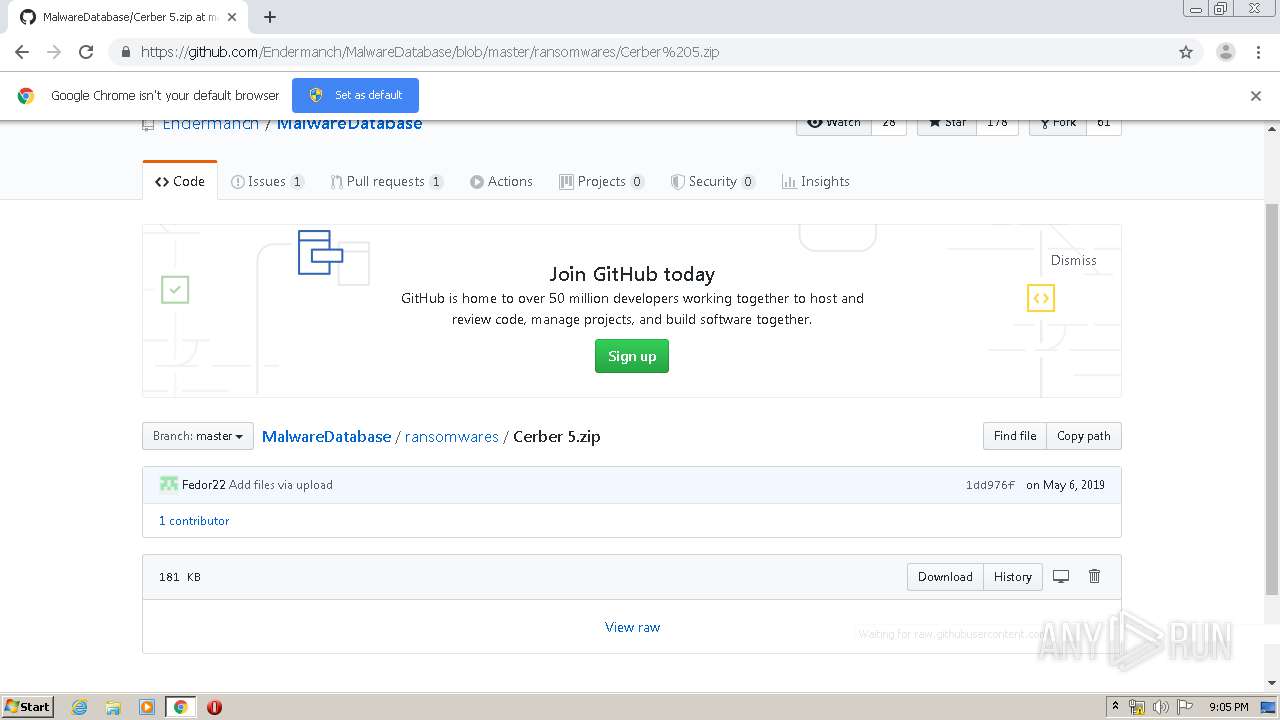
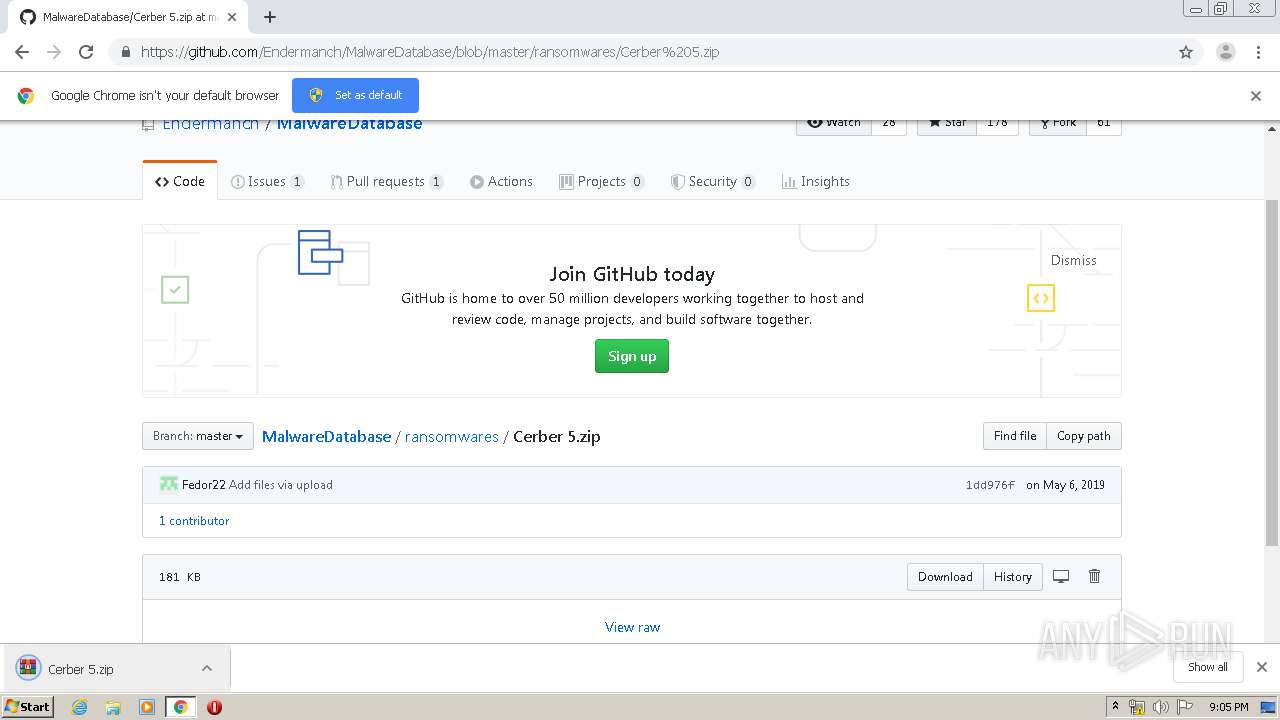
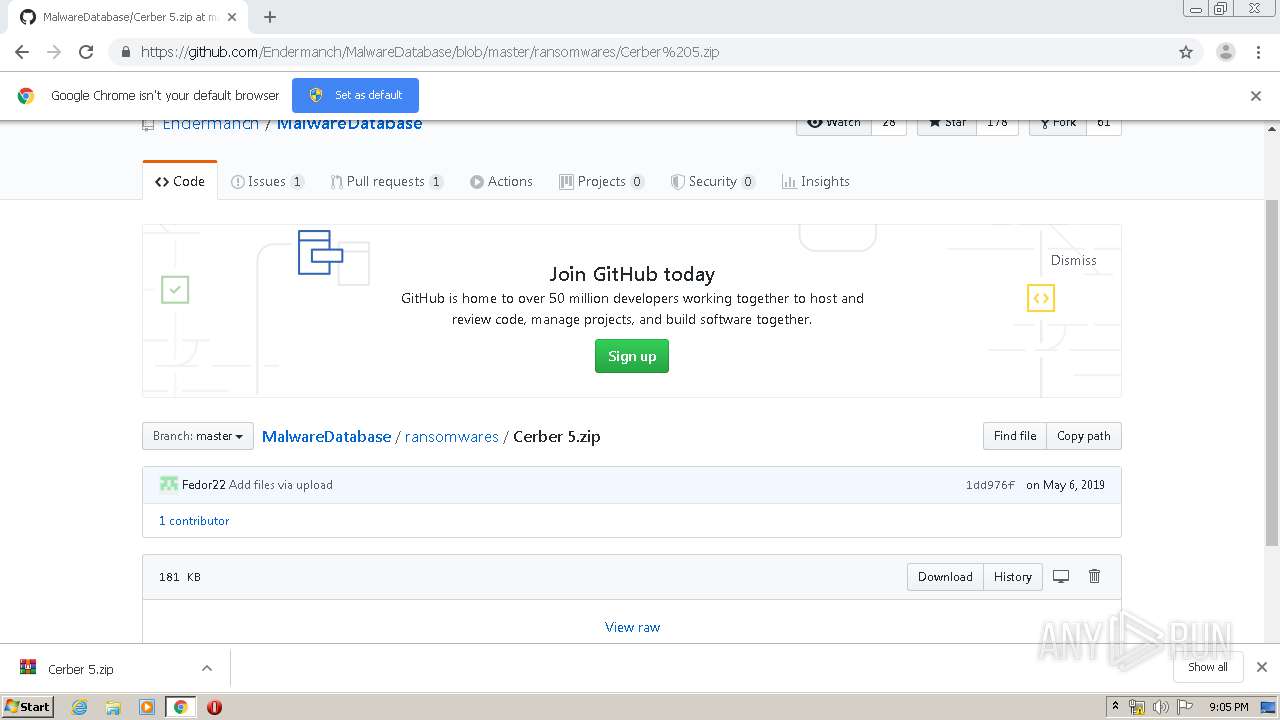
| URL: | https://www.youtube.com/redirect?v=IZ0ZTsJE10c&redir_token=_7uOZs1tlThKdTHx16N8nePJk4R8MTU5MDk1NDY1OUAxNTkwODY4MjU5&event=video_description&q=https%3A%2F%2Fgithub.com%2FEndermanch%2FMalwareDatabase |
| Full analysis: | https://app.any.run/tasks/b70fb83a-810b-4443-8bbd-803453a4c18b |
| Verdict: | Malicious activity |
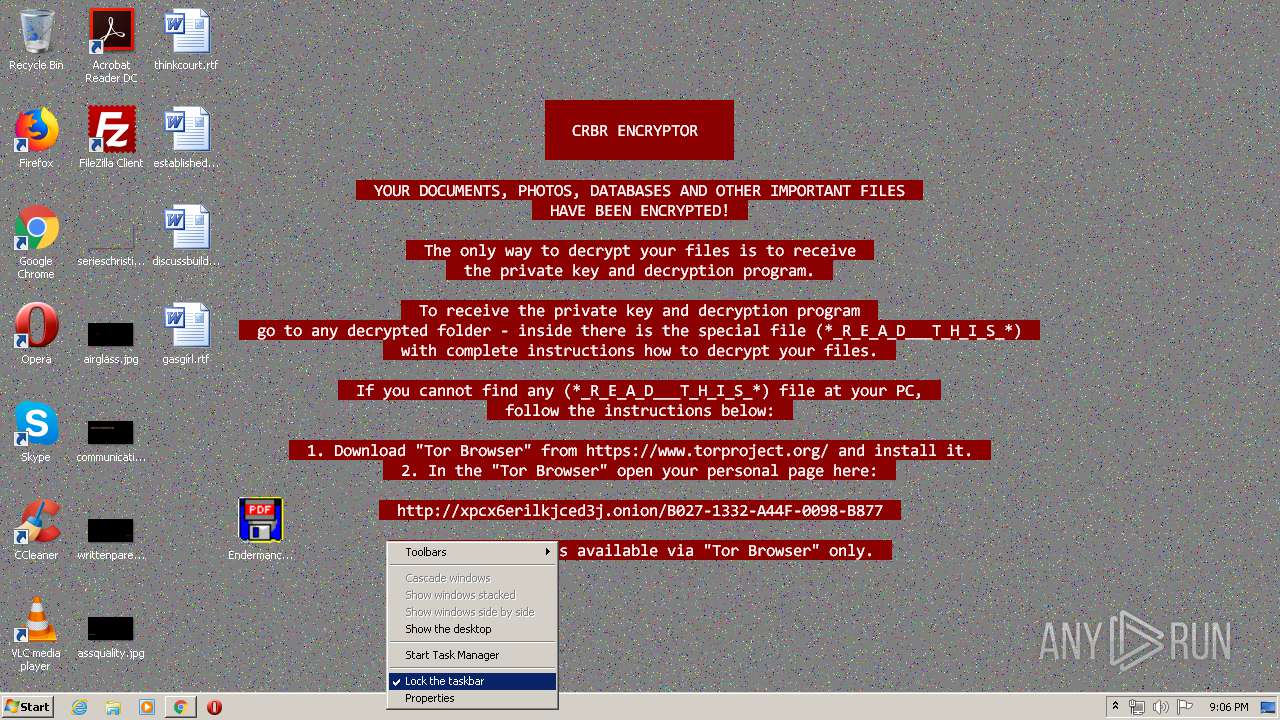
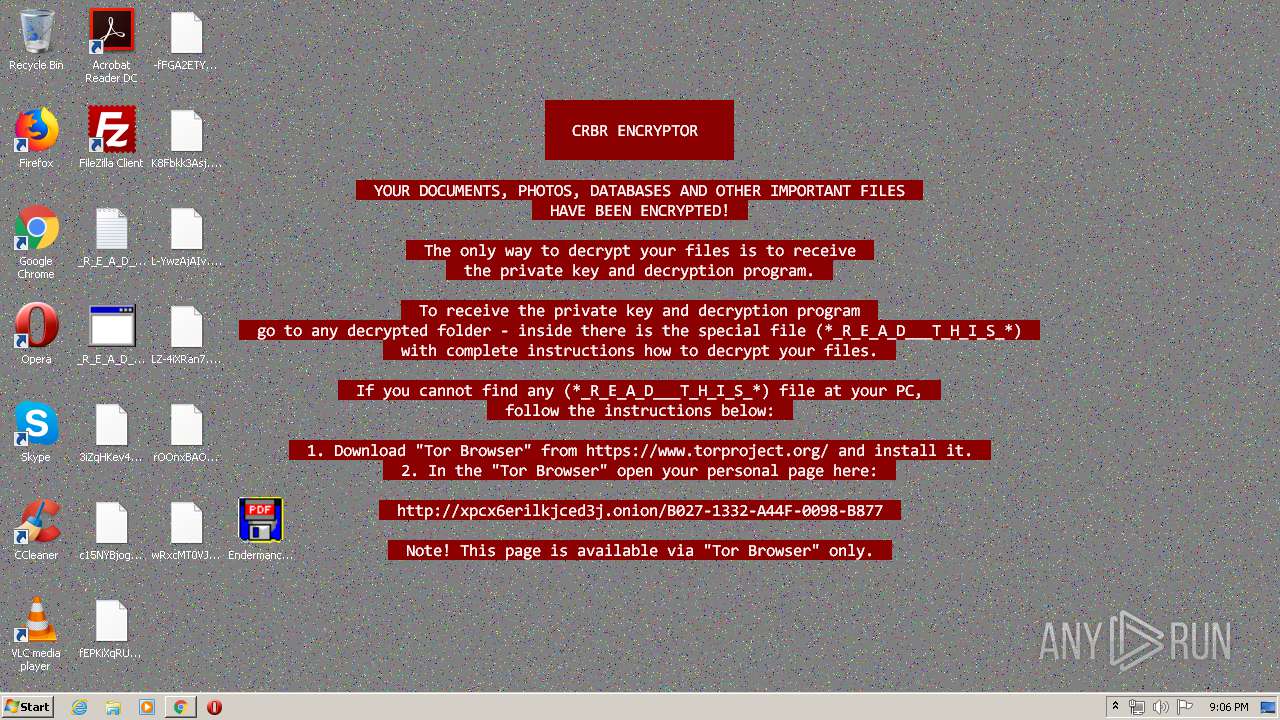
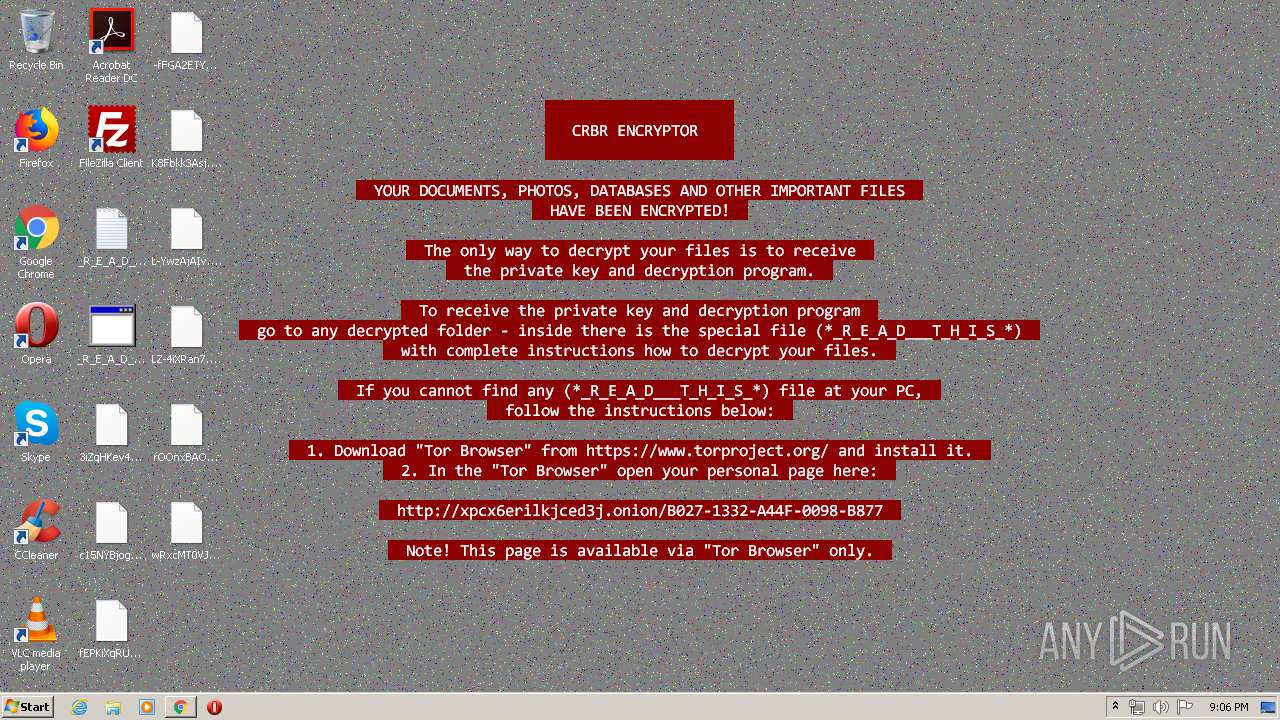
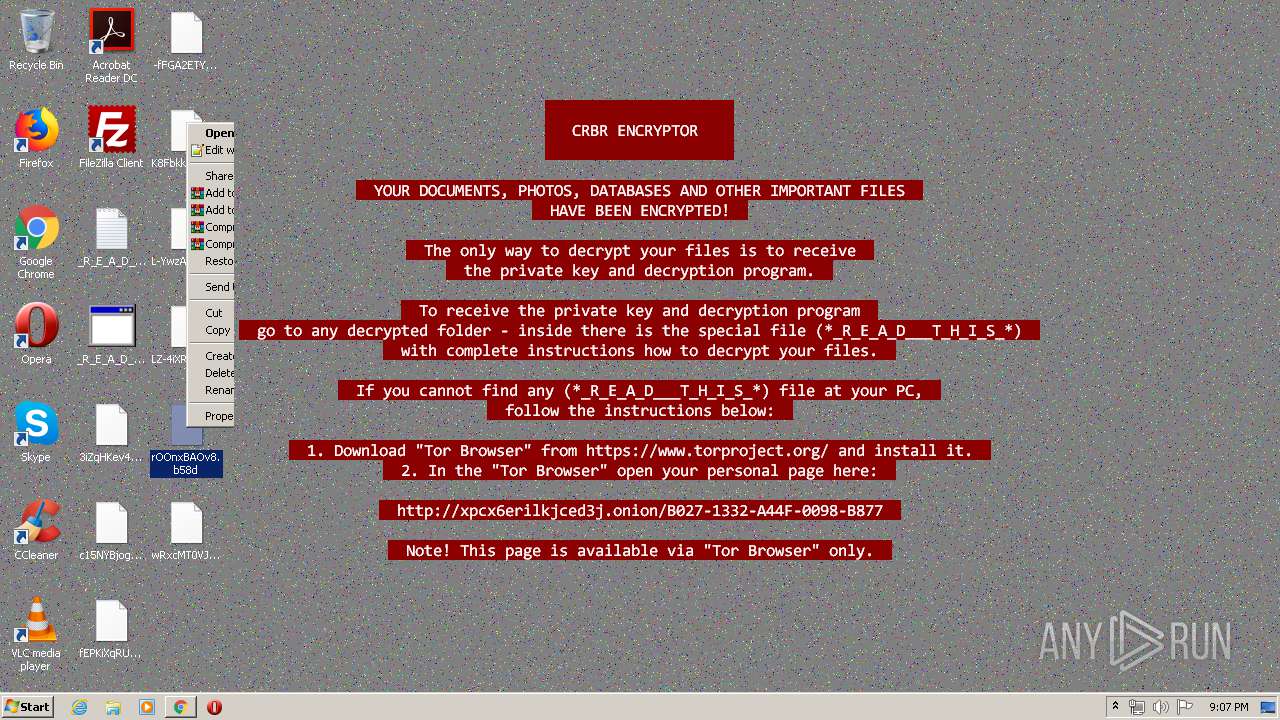
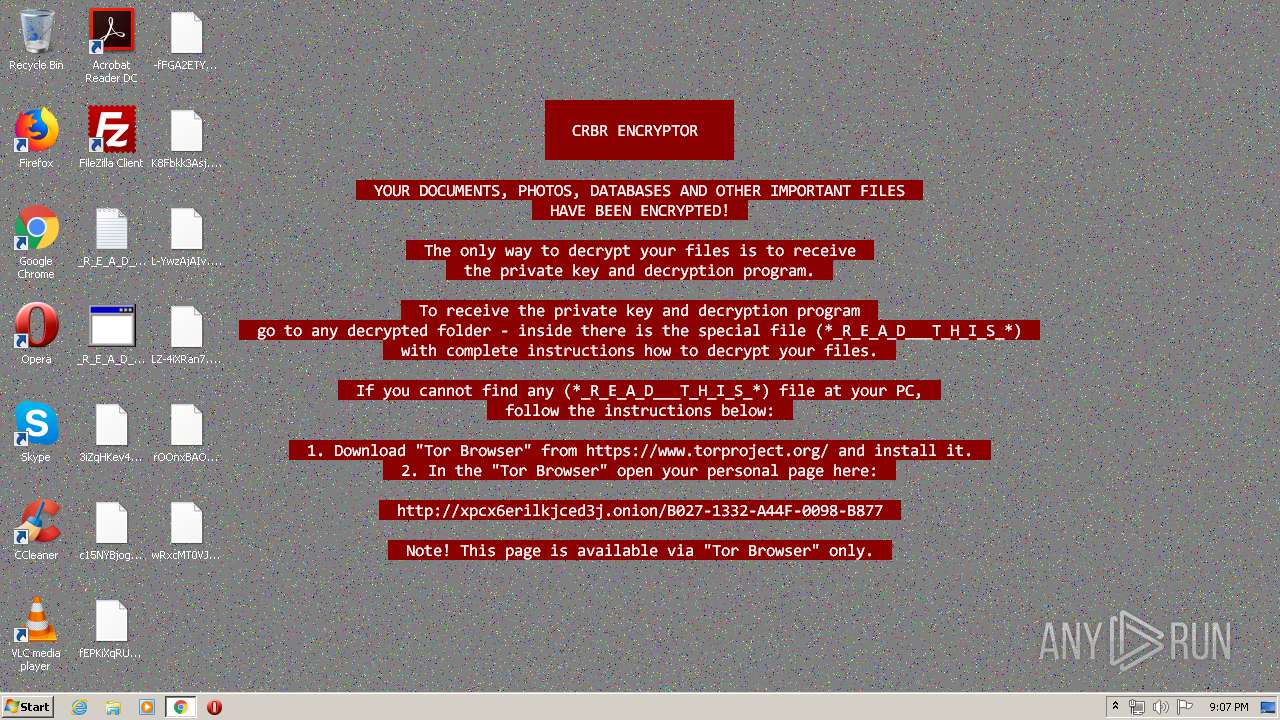
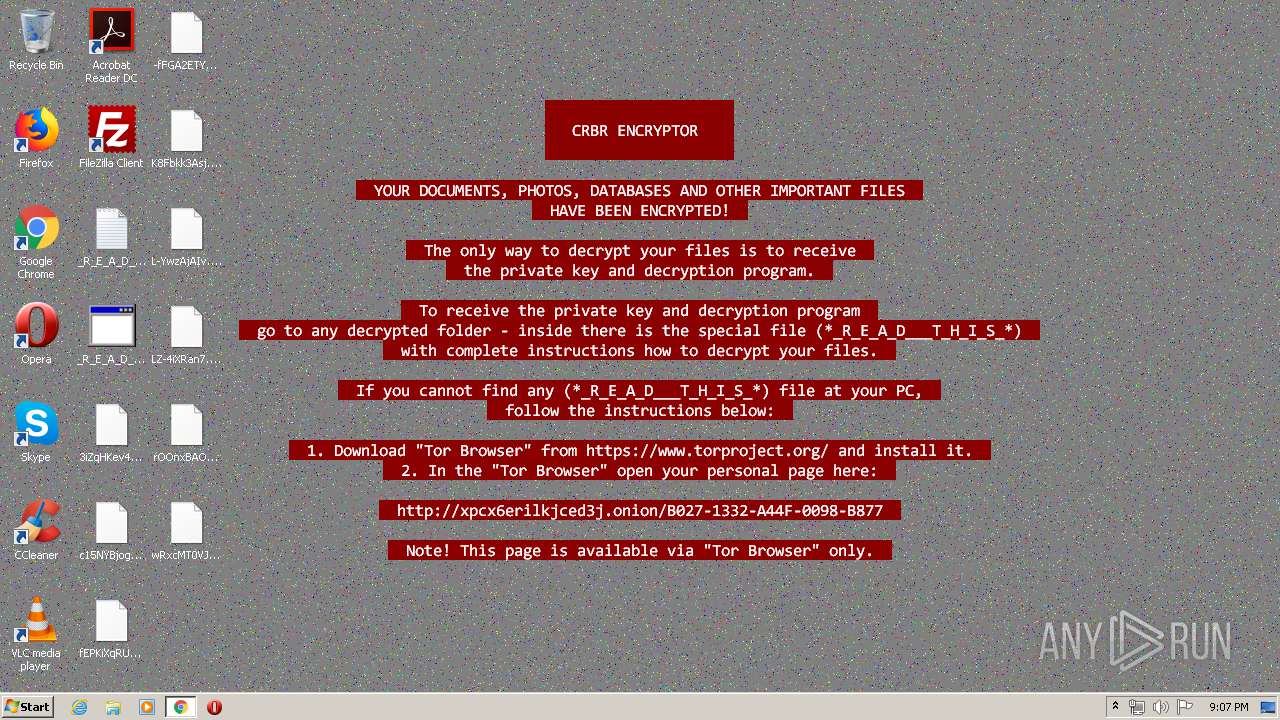
| Threats: | Cerber is a Ransomware-as-a-Service (RaaS) that appeared in 2016, spread quickly and has been evolving since. It became well-known for its file encryption, offline capabilities, and sophisticated evasion techniques. It primarily targets enterprises, financial institutions, and government entities, encrypting their data and demanding ransom payments in Bitcoin. It also targets everyday users encrypting personal files (photos, documents) with the risk of their permanent loss. |
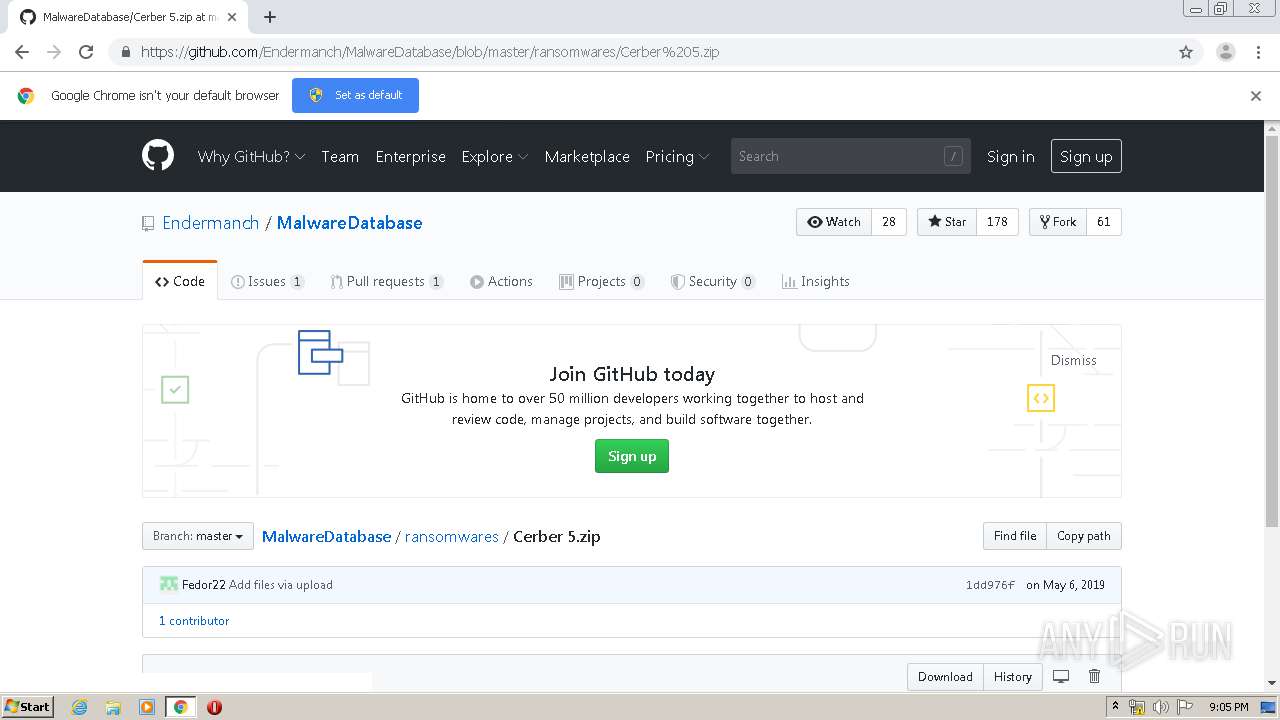
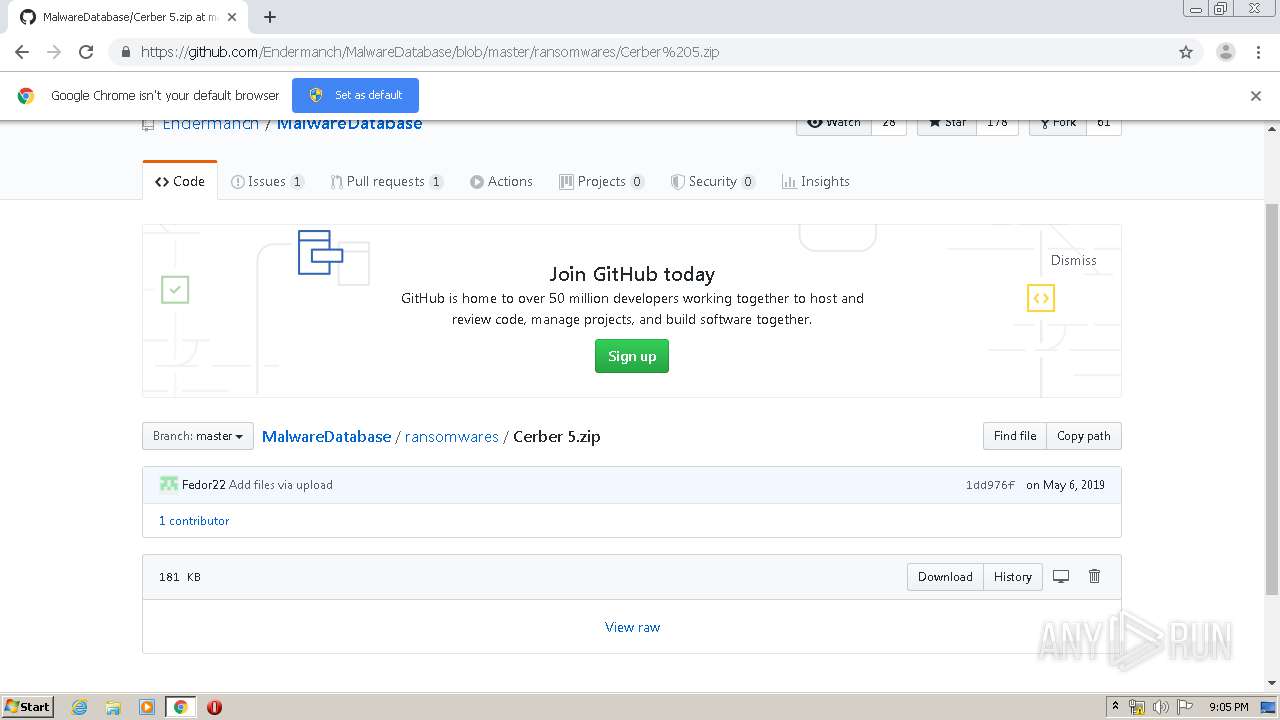
| Analysis date: | May 30, 2020, 20:04:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1842C0BB6651A27BE7EF31C362DA6471 |
| SHA1: | C526B88EE39B61B58D9F71BA82FF72B660DE6607 |
| SHA256: | DEA1CF4ED7BA65D2E67768811534C7B6E7AD63852F2CEB1177E967DBC04AF599 |
| SSDEEP: | 6:2OLUxGKU6gMTx/6OMoRqwkdkURL5z8YKLAMH:2jG9QF/6OMoRQd9QYkH |
MALICIOUS
Application was dropped or rewritten from another process
- Endermanch@Cerber5.exe (PID: 2484)
Actions looks like stealing of personal data
- Endermanch@Cerber5.exe (PID: 2484)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2716)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2144)
Starts CMD.EXE for self-deleting
- Endermanch@Cerber5.exe (PID: 2484)
Starts MSHTA.EXE for opening HTA or HTMLS files
- Endermanch@Cerber5.exe (PID: 2484)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2716)
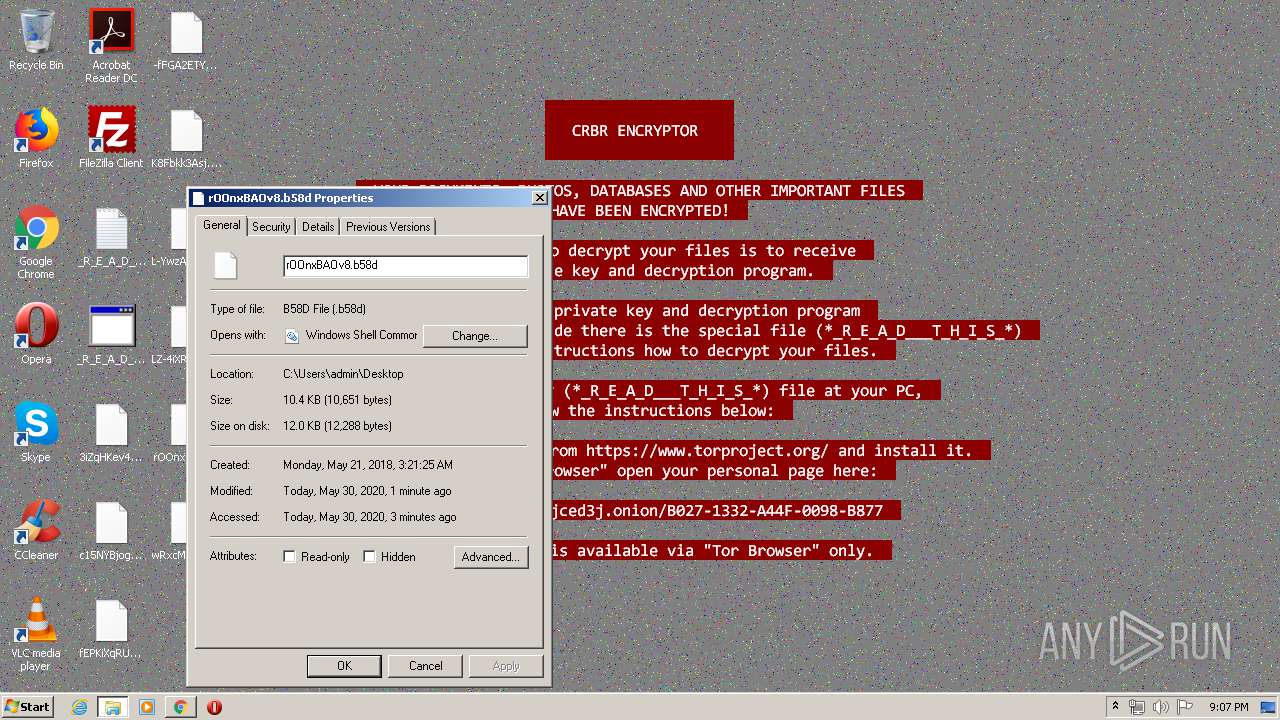
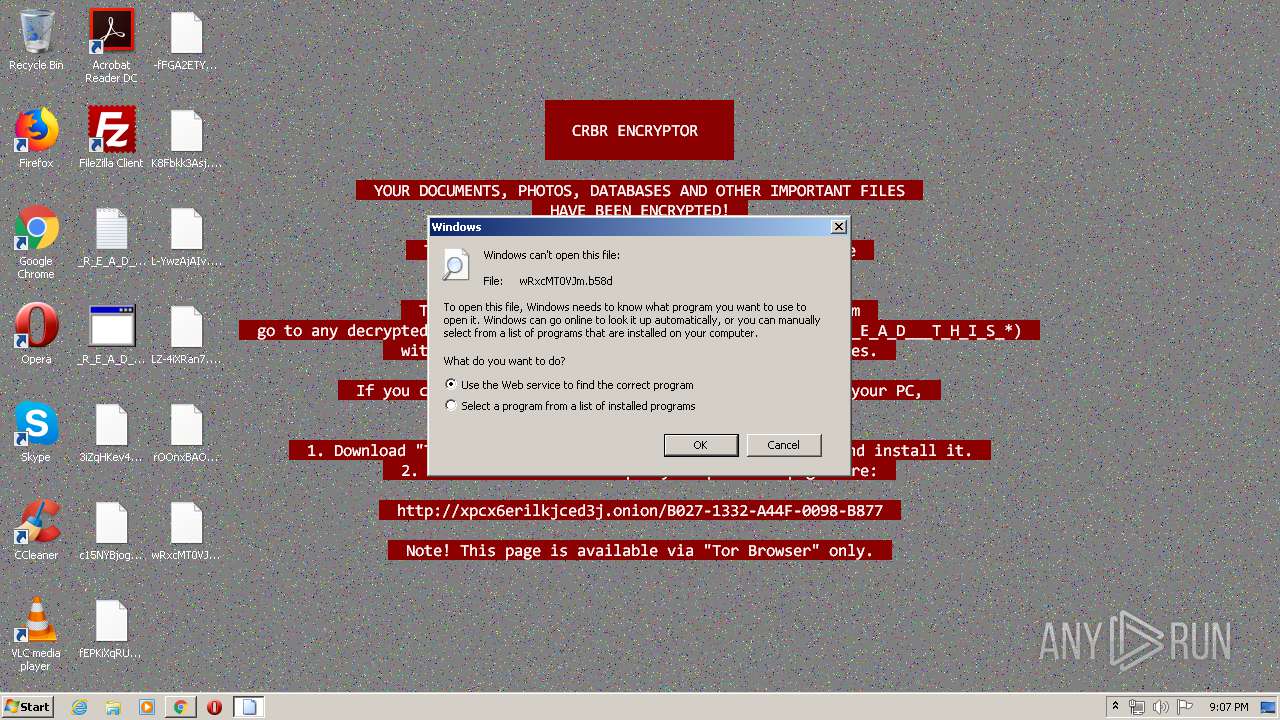
Creates files in the user directory
- Endermanch@Cerber5.exe (PID: 2484)
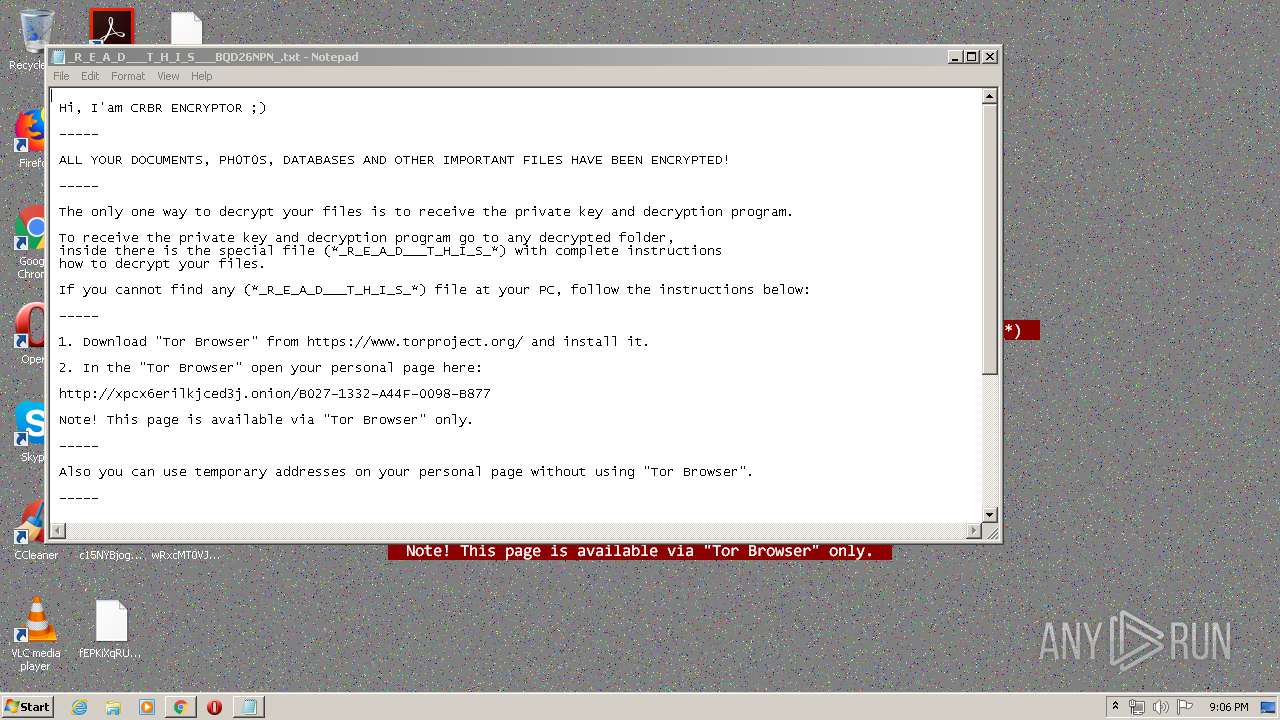
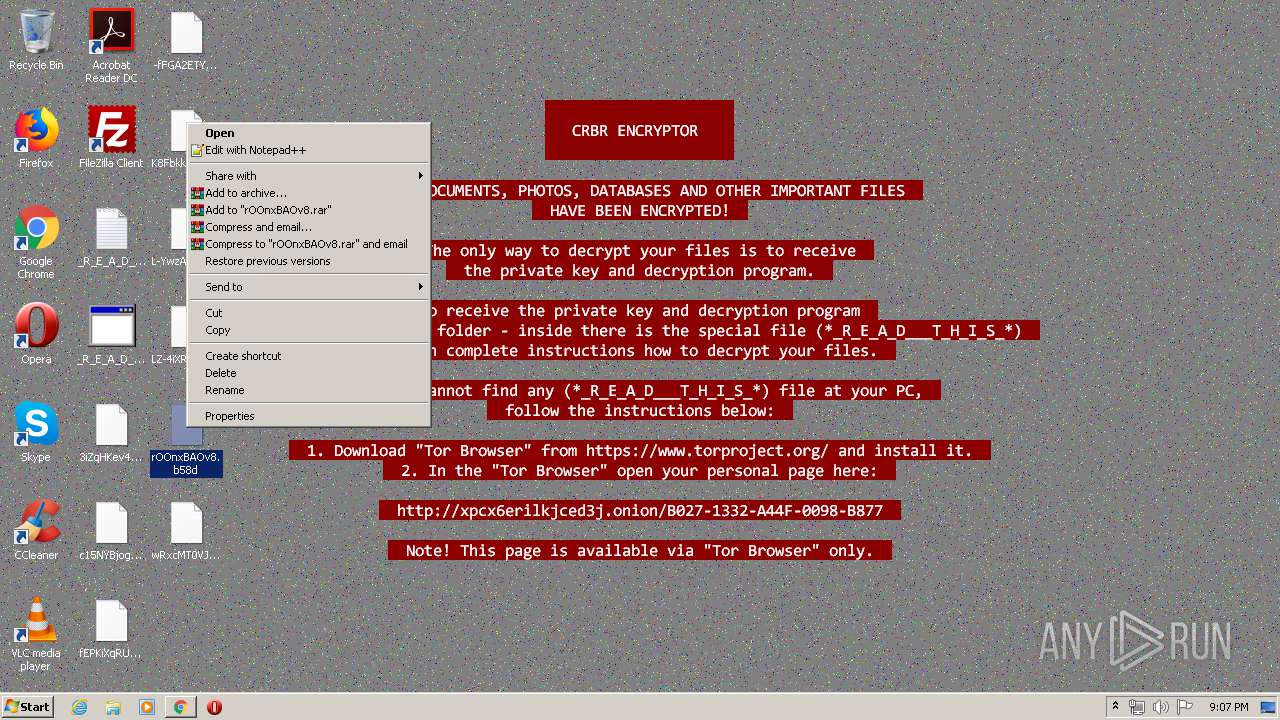
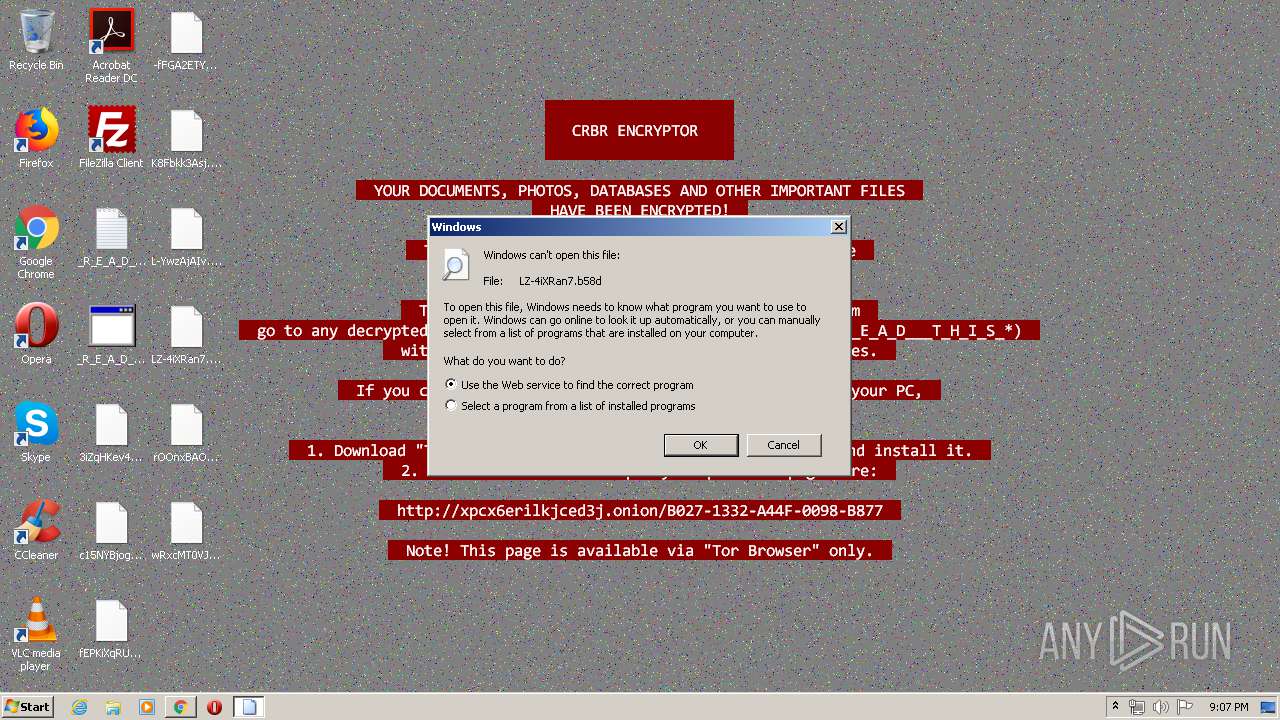
Creates files like Ransomware instruction
- Endermanch@Cerber5.exe (PID: 2484)
Starts CMD.EXE for commands execution
- Endermanch@Cerber5.exe (PID: 2484)
INFO
Application launched itself
- chrome.exe (PID: 2144)
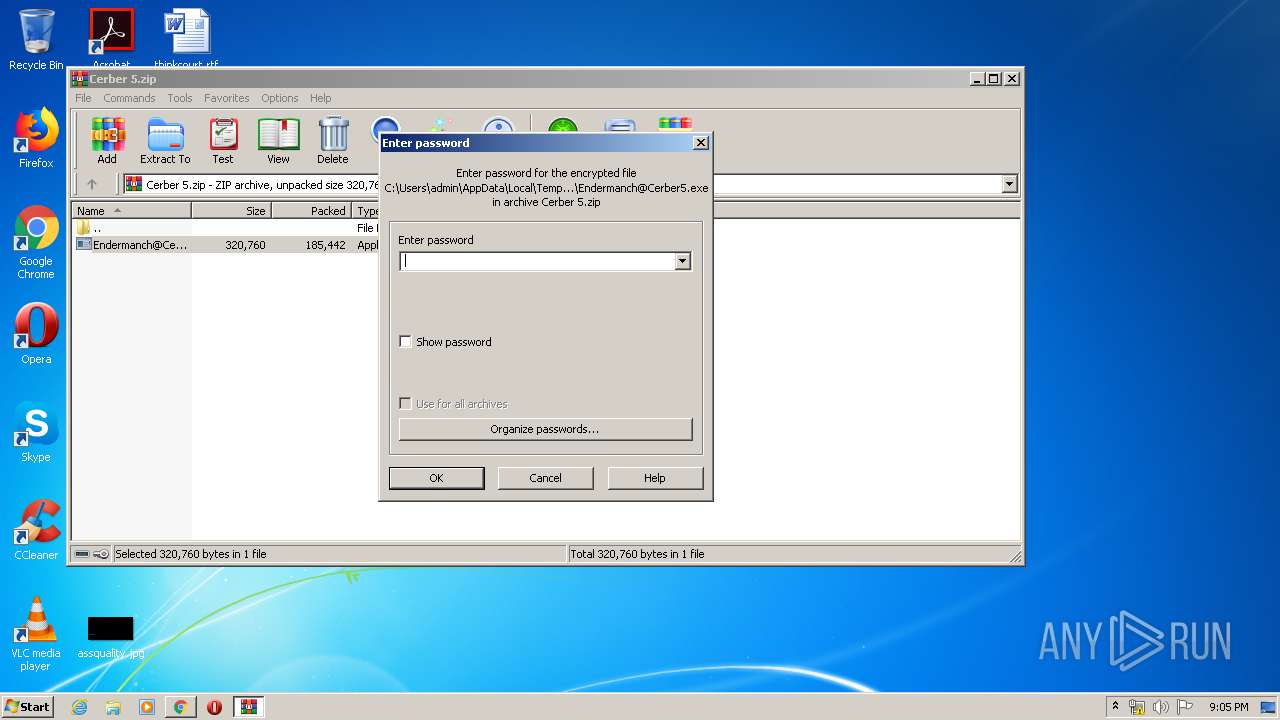
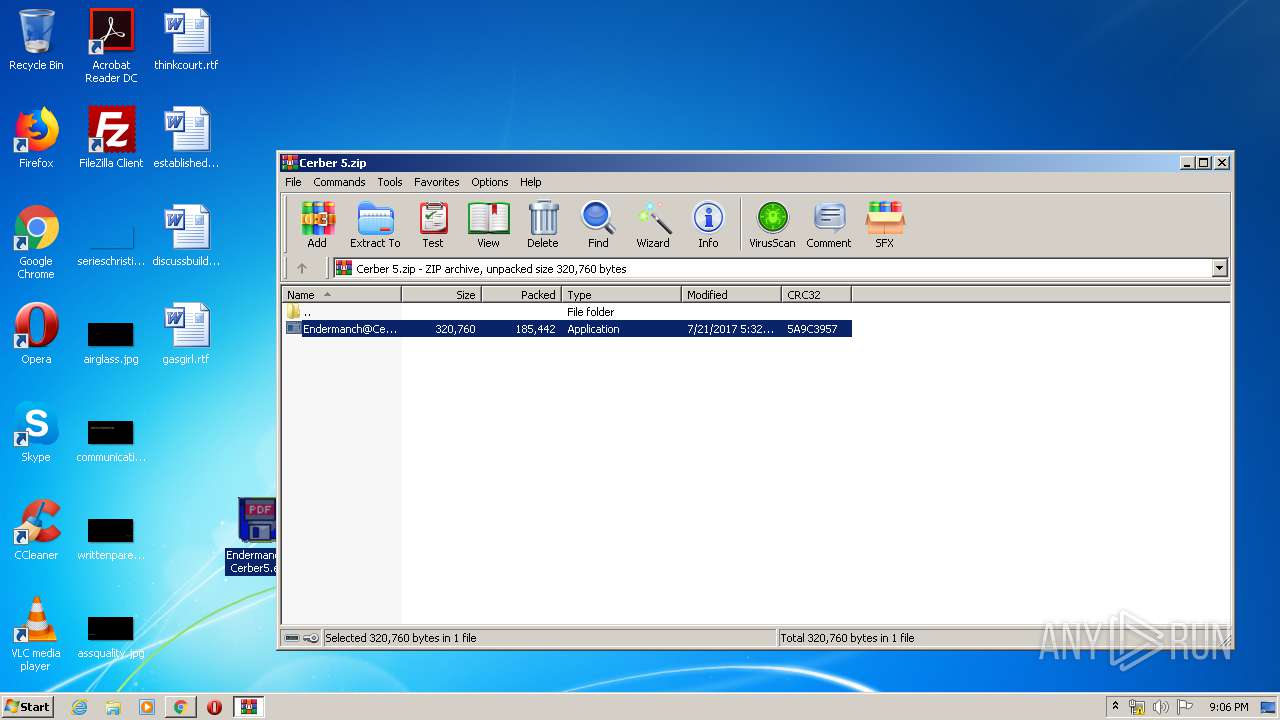
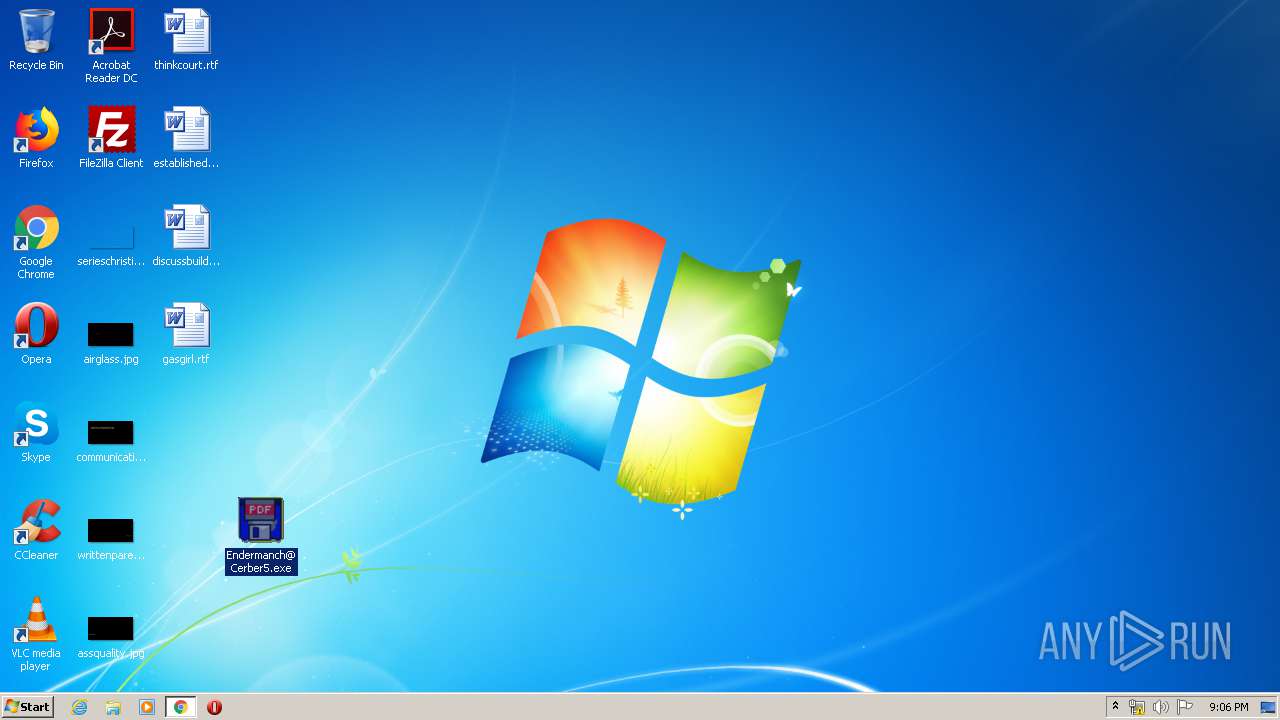
Manual execution by user
- Endermanch@Cerber5.exe (PID: 2484)
- mshta.exe (PID: 2088)
- rundll32.exe (PID: 3640)
- rundll32.exe (PID: 4036)
- taskmgr.exe (PID: 3024)
Reads the hosts file
- chrome.exe (PID: 2144)
- chrome.exe (PID: 332)
Reads Internet Cache Settings
- chrome.exe (PID: 2144)
Dropped object may contain TOR URL's
- Endermanch@Cerber5.exe (PID: 2484)
Reads internet explorer settings
- mshta.exe (PID: 2728)
- mshta.exe (PID: 2088)
Reads settings of System Certificates
- chrome.exe (PID: 332)
Dropped object may contain Bitcoin addresses
- Endermanch@Cerber5.exe (PID: 2484)
Dropped object may contain URL to Tor Browser
- Endermanch@Cerber5.exe (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
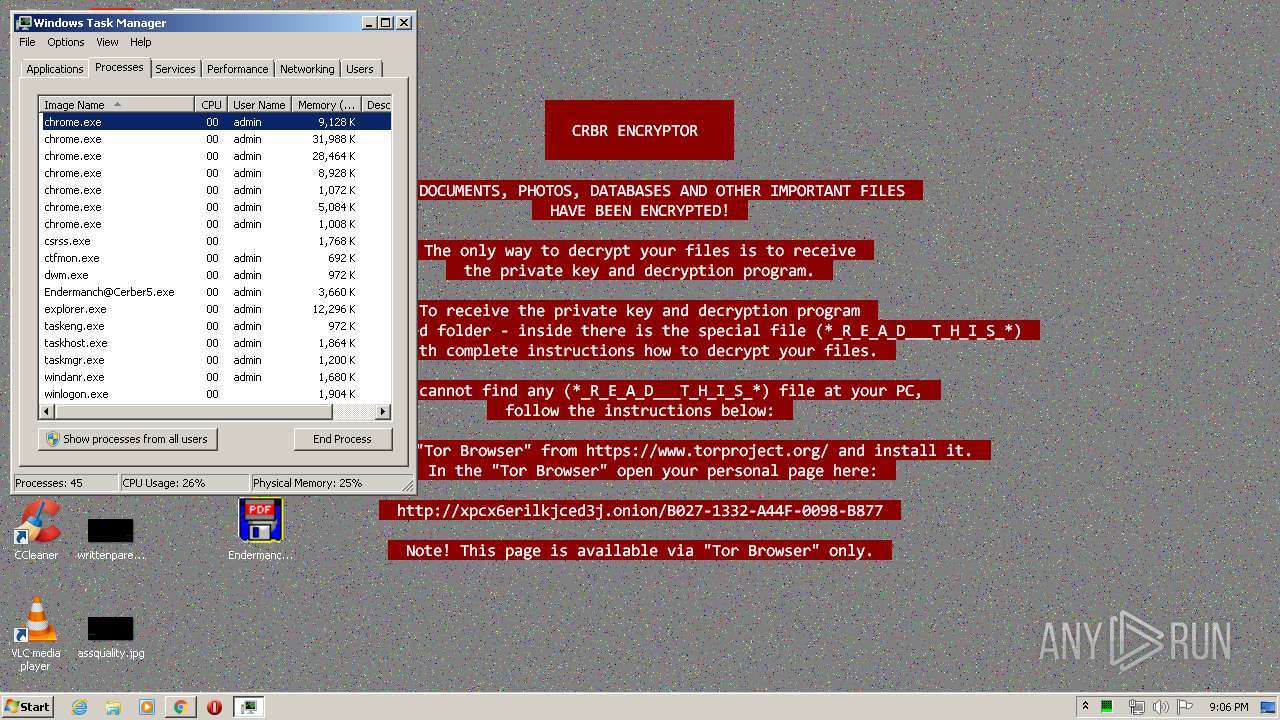
Total processes
82
Monitored processes
40
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13604737190679641353 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16547764687608889148 --mojo-platform-channel-handle=2792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5535672093779482053 --mojo-platform-channel-handle=2804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9606670536779825153 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
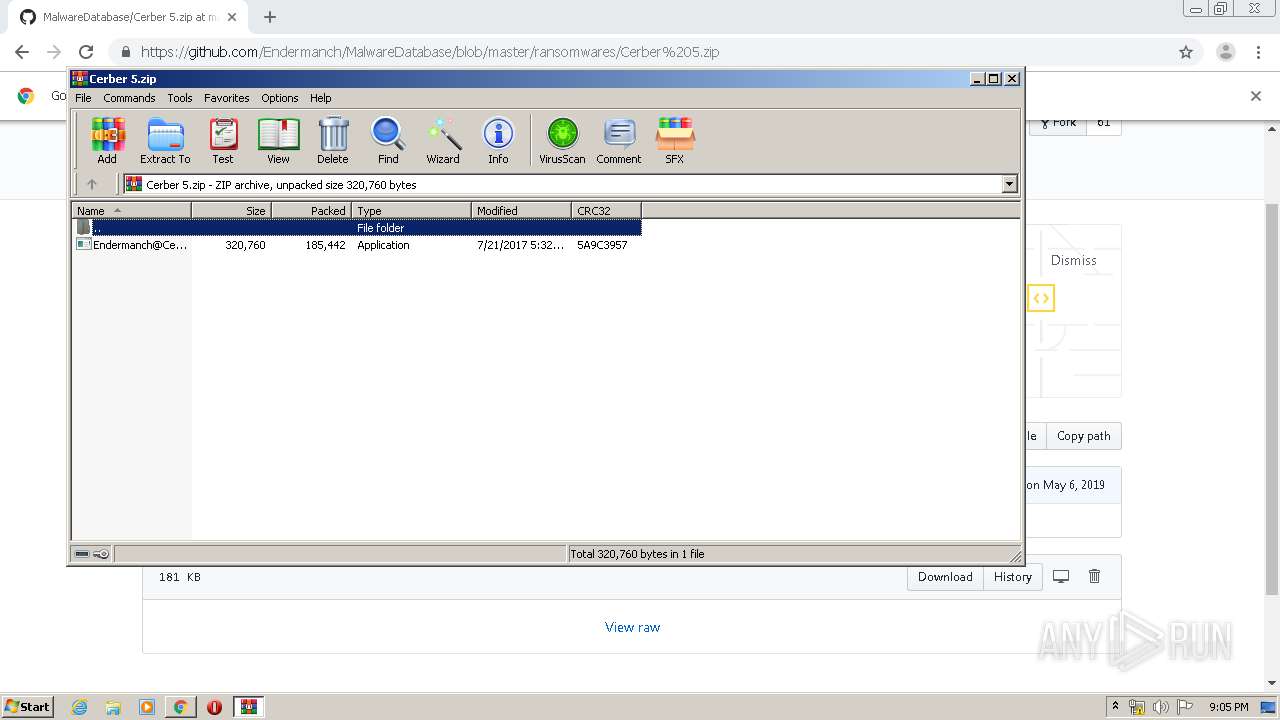
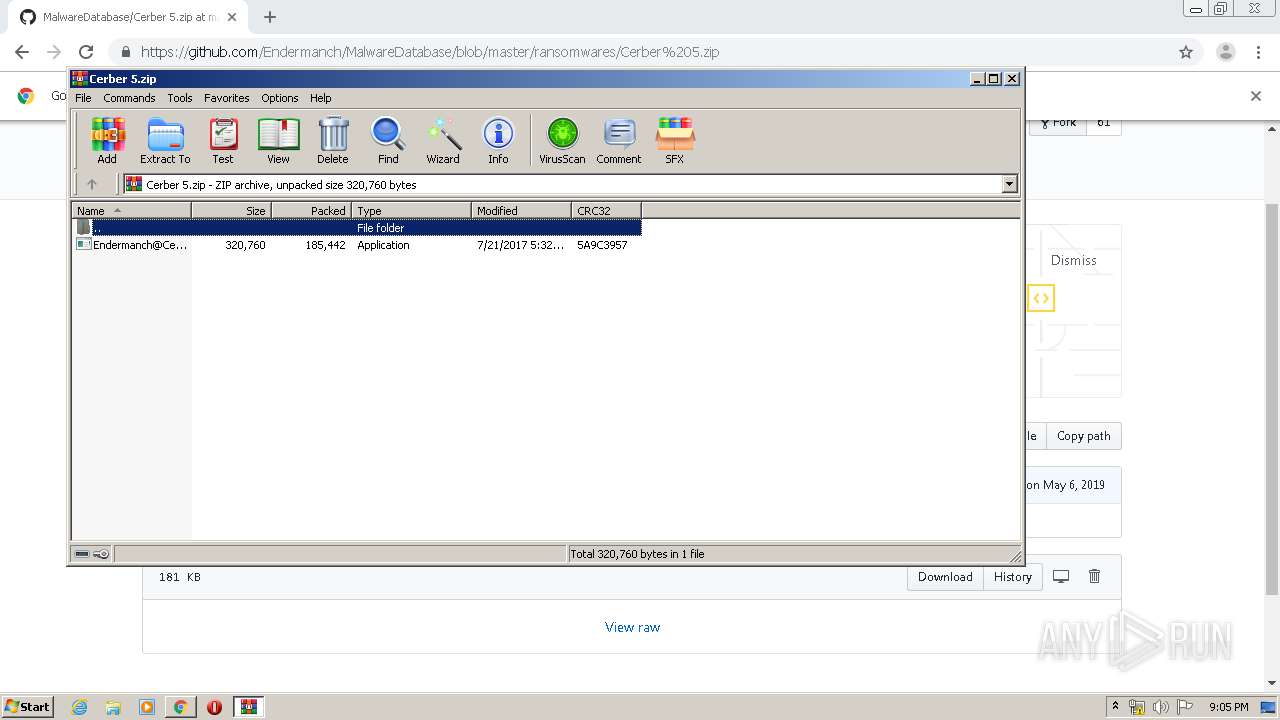
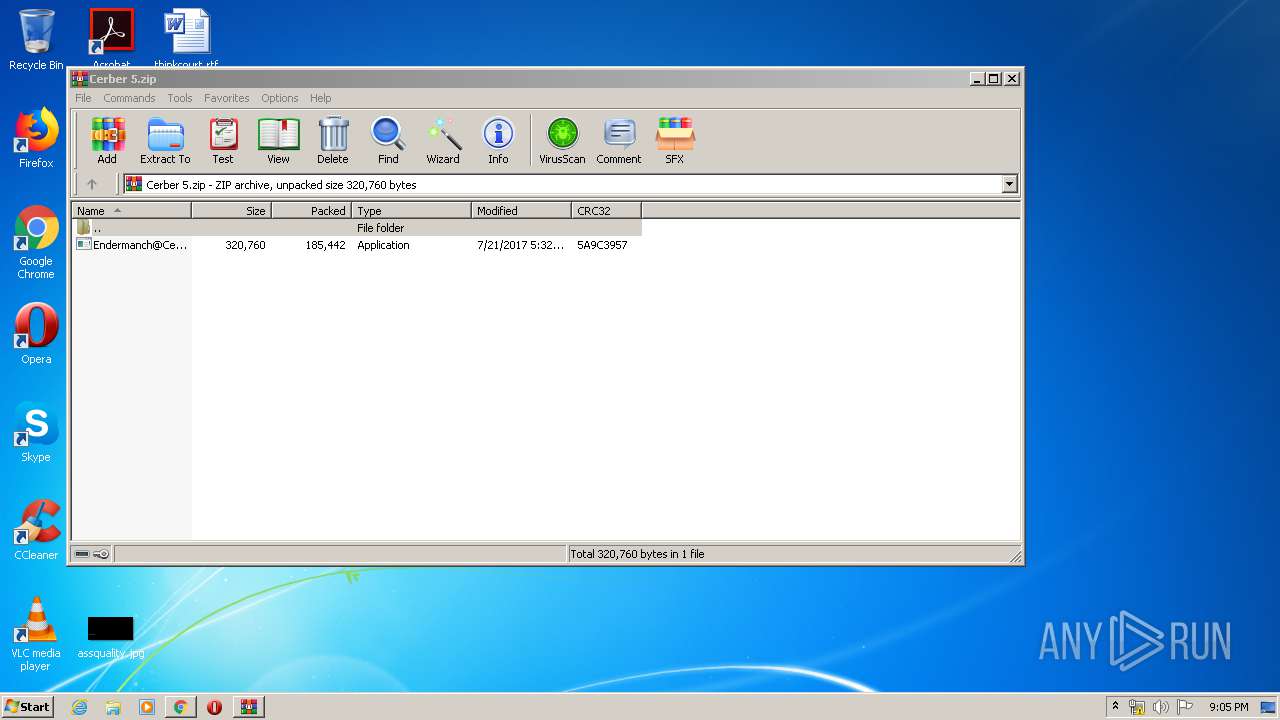
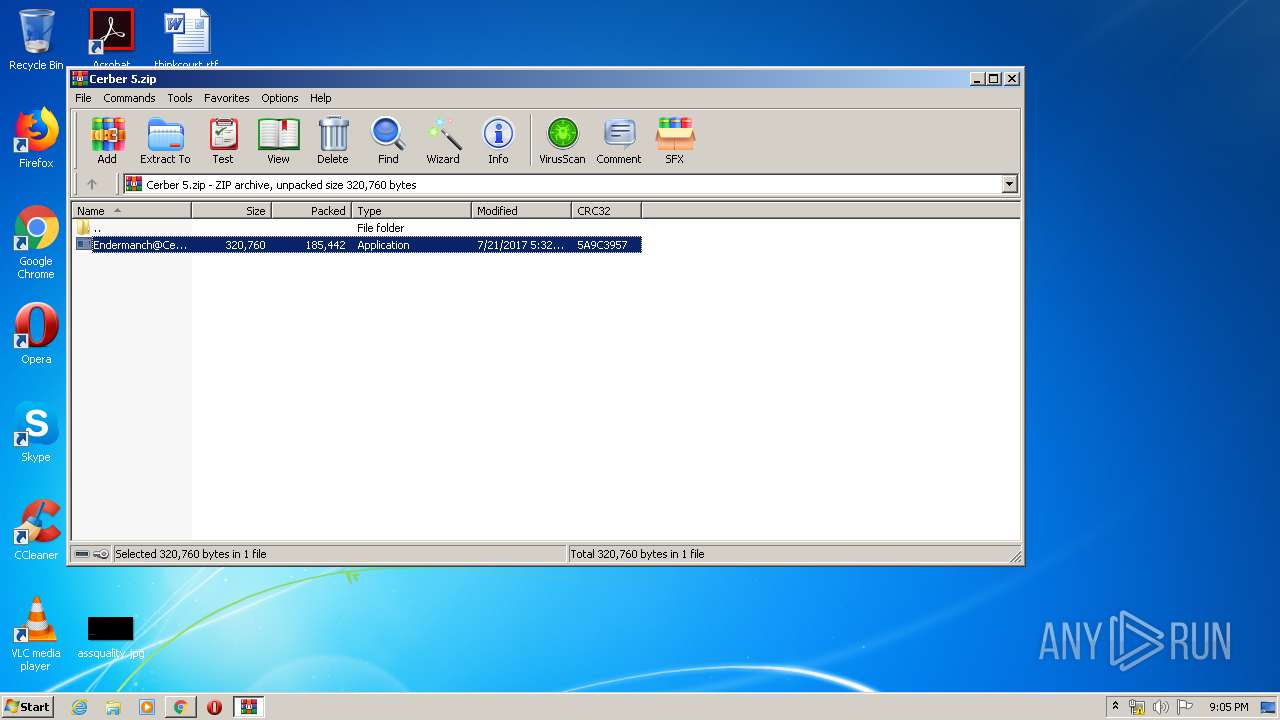
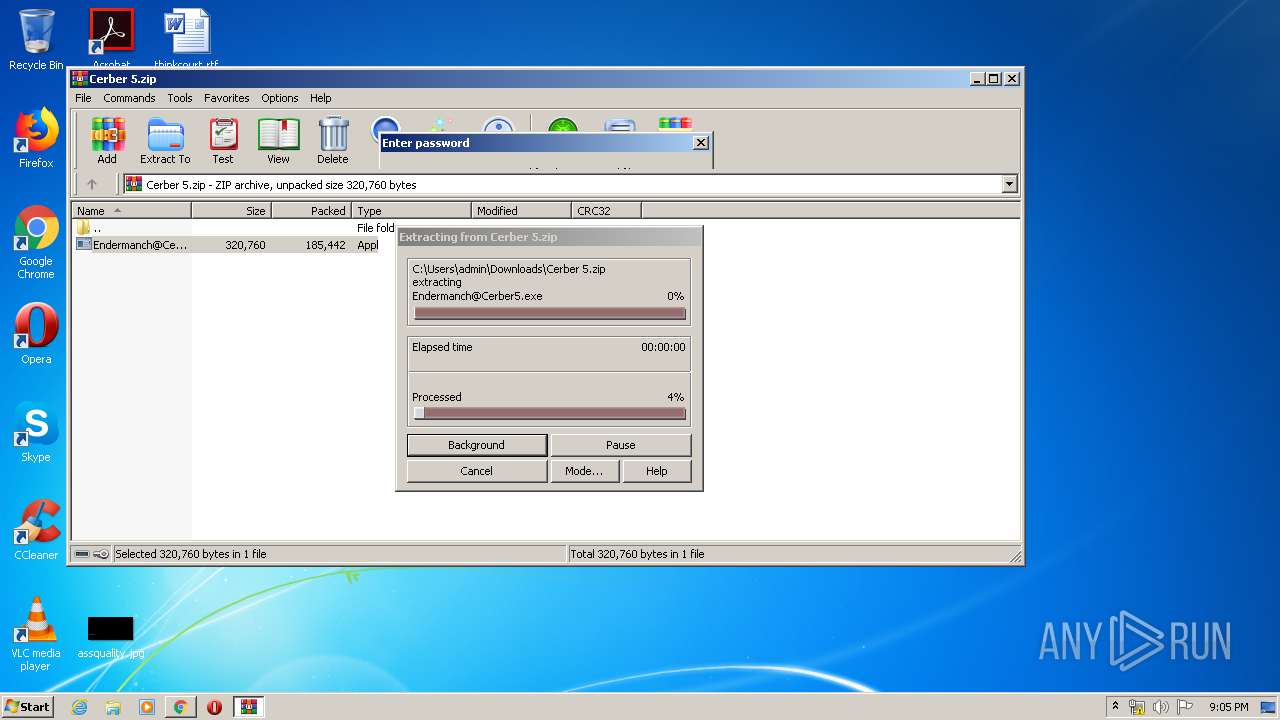
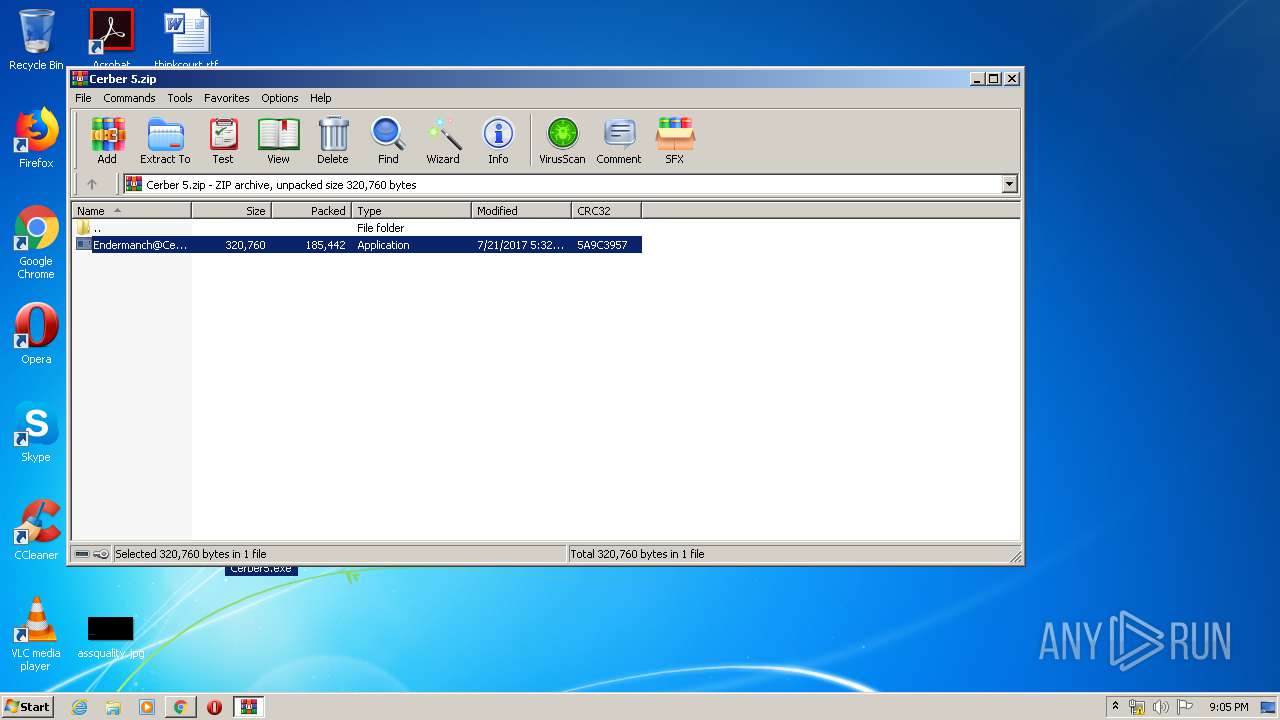
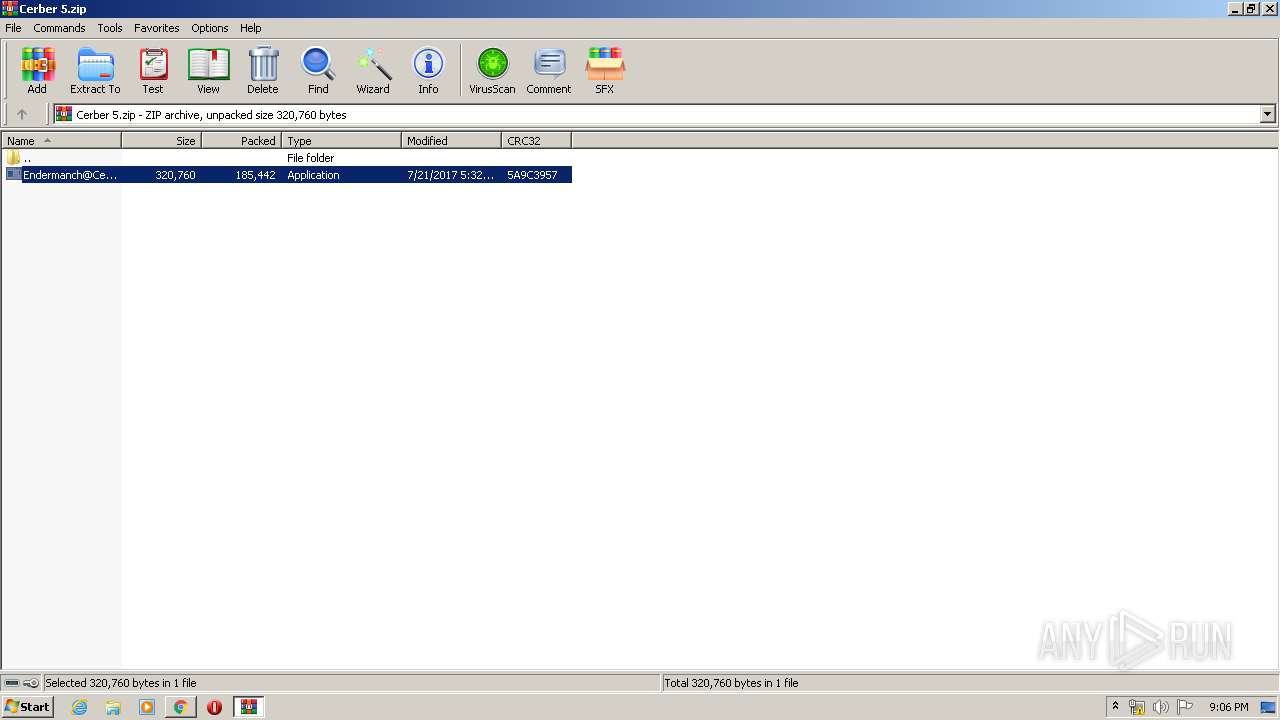
| 1516 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Cerber 5.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16079412104951237787 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=194539745336182300 --mojo-platform-channel-handle=2776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10735321627018308150 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\_R_E_A_D___T_H_I_S___I35C0JV0_.hta" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6827685861628947965,18259736318454210513,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12876795560418229955 --mojo-platform-channel-handle=728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 996
Read events
1 848
Write events
143
Delete events
5
Modification events
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2144-13235342665559750 |
Value: 259 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2144) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
44
Text files
218
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED2BC4A-860.pma | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\908400bd-aef2-4746-8e32-209b05db3a3b.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12ac26.TMP | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF12ac74.TMP | text | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12ae68.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
2 207
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
332 | chrome.exe | GET | 200 | 74.125.4.203:80 | http://r5---sn-aigzrner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.217.117.39&mm=28&mn=sn-aigzrner&ms=nvh&mt=1590868332&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
332 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
332 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
332 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.39&mm=28&mn=sn-aigzrney&ms=nvh&mt=1590868332&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
332 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 172.217.21.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 172.217.18.174:443 | clients4.google.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 216.58.210.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
332 | chrome.exe | 185.199.109.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
332 | chrome.exe | 140.82.118.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients4.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
github.com |
| malicious |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET TROJAN Ransomware/Cerber Checkin M3 (12) |