| File name: | vpn.jar |
| Full analysis: | https://app.any.run/tasks/bb669793-e560-4502-aa73-48d97b228379 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | April 23, 2019, 08:39:10 |
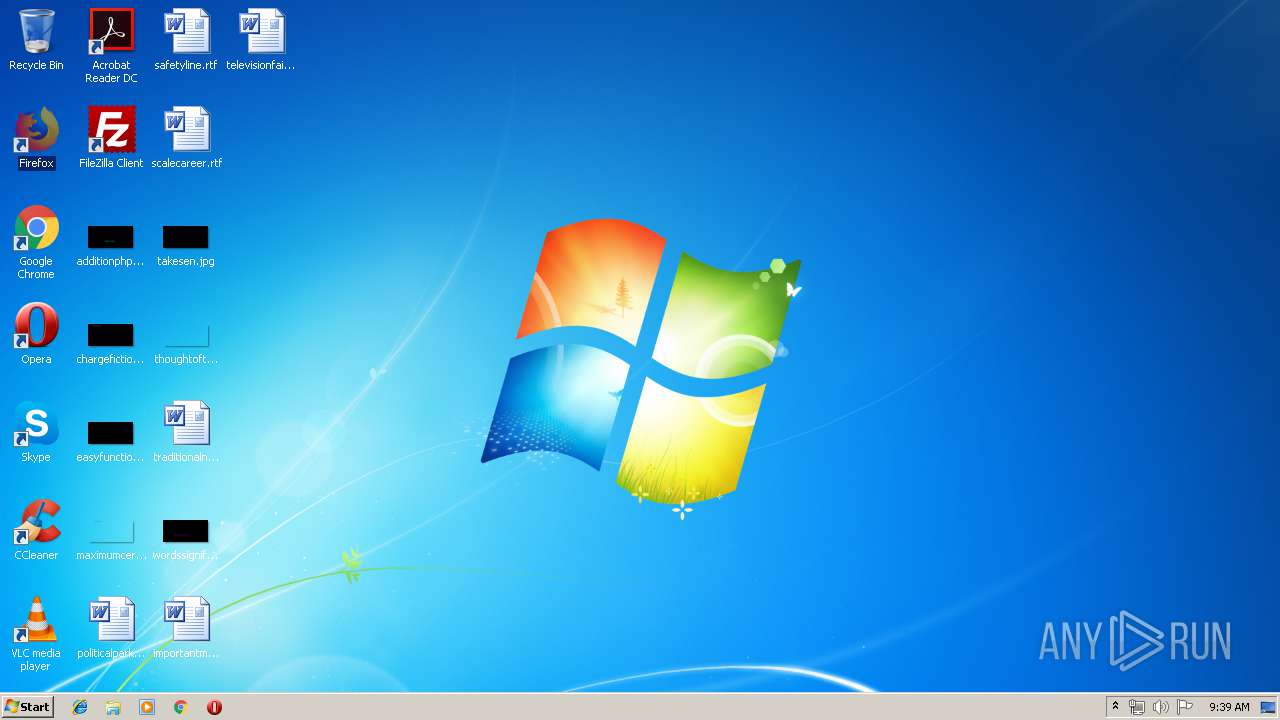
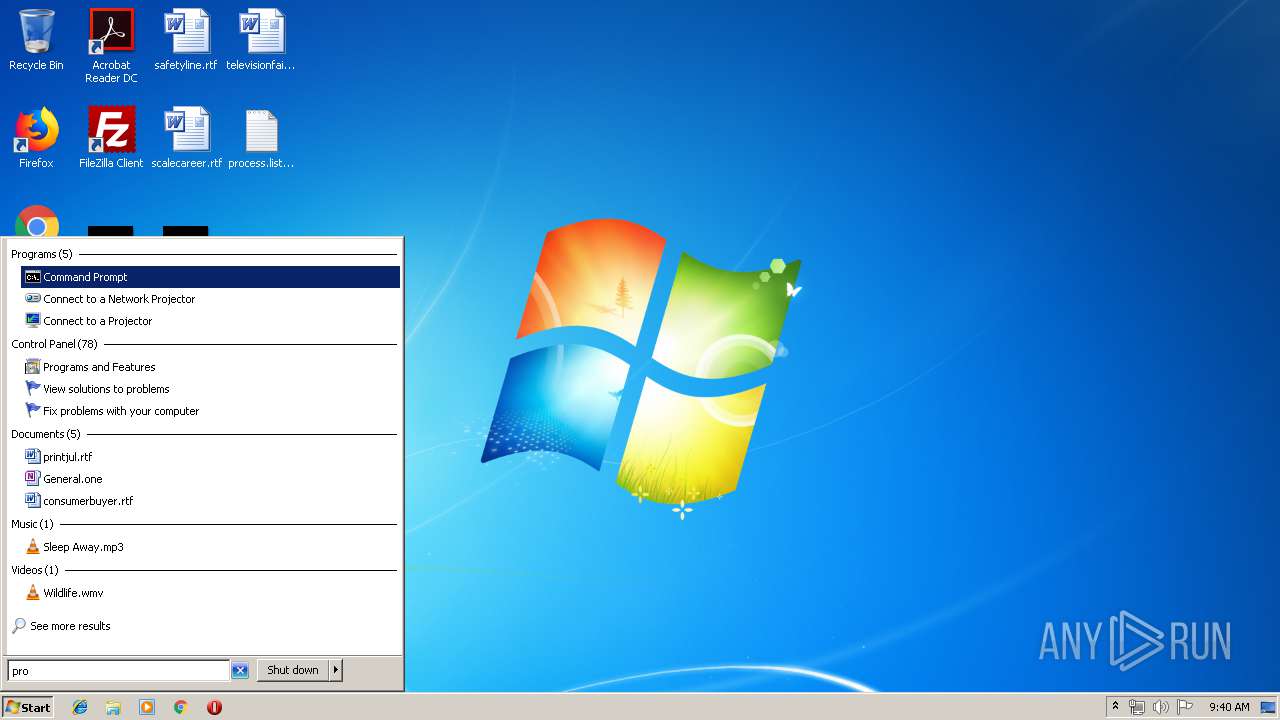
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | B5F5F5BDFC6A7C848FC5BEE504D3B6D1 |
| SHA1: | E22B417F57DE09485BFAA8B158182C6C8D6DD11D |
| SHA256: | DE7D1957F4813AF3120C95B2999686067C124F9DB540EBF29C8EF3FF299FA3FF |
| SSDEEP: | 768:hIqFc+bYjbINzVRi1D5Fk02KYl0O1ZxmFdr948hi8h/mQtgkDAO4ezL1TRqnBKGW:hPJVzezOHidrS8hsKgqlHCnBKG5793S |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 296)
- reg.exe (PID: 712)
ADWIND was detected
- javaw.exe (PID: 2256)
Connects to CnC server
- javaw.exe (PID: 2256)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2176)
- javaw.exe (PID: 2256)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2176)
- javaw.exe (PID: 2256)
Creates files in the user directory
- javaw.exe (PID: 2176)
- javaw.exe (PID: 2256)
Writes to a desktop.ini file (may be used to cloak folders)
- javaw.exe (PID: 2176)
Application launched itself
- javaw.exe (PID: 2176)
Executes JAVA applets
- javaw.exe (PID: 2176)
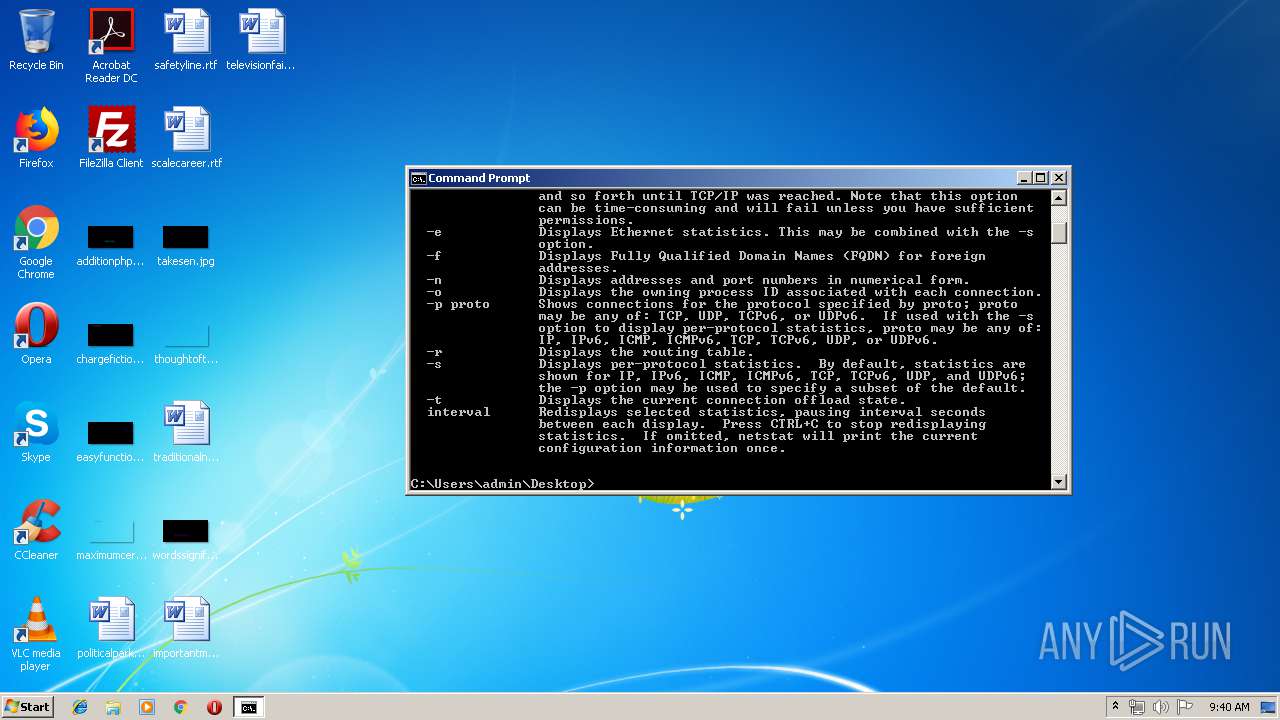
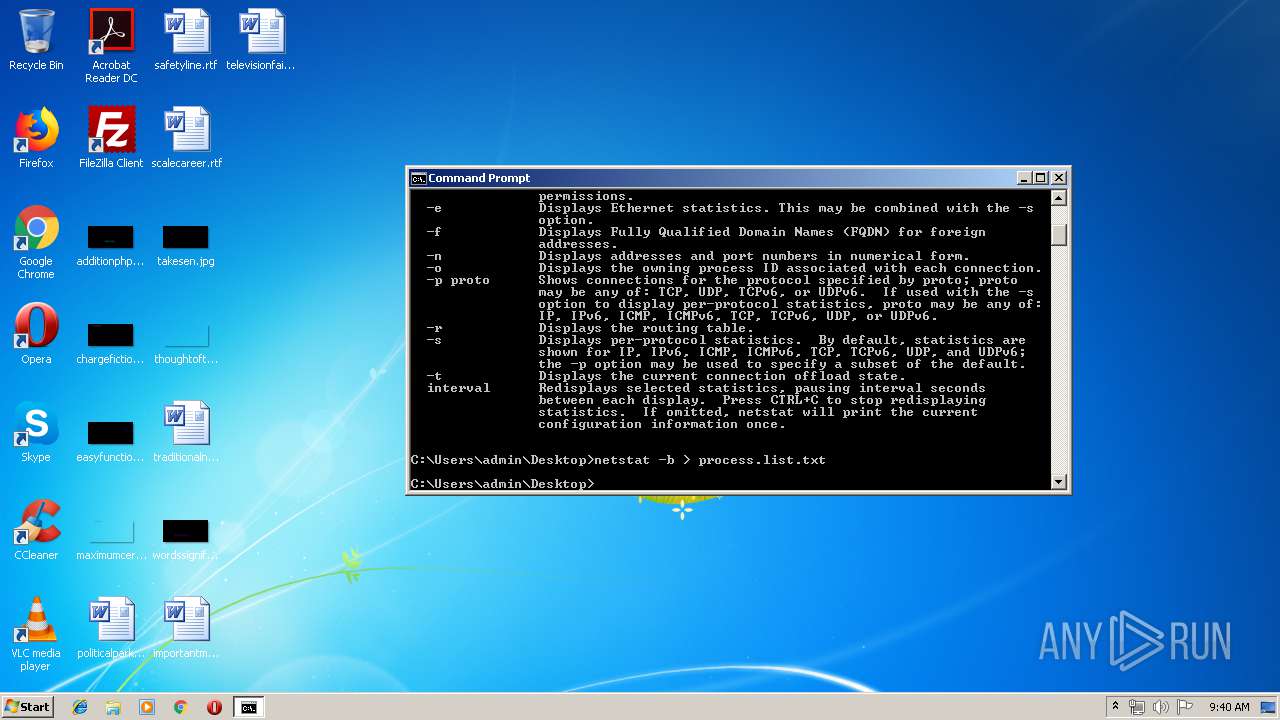
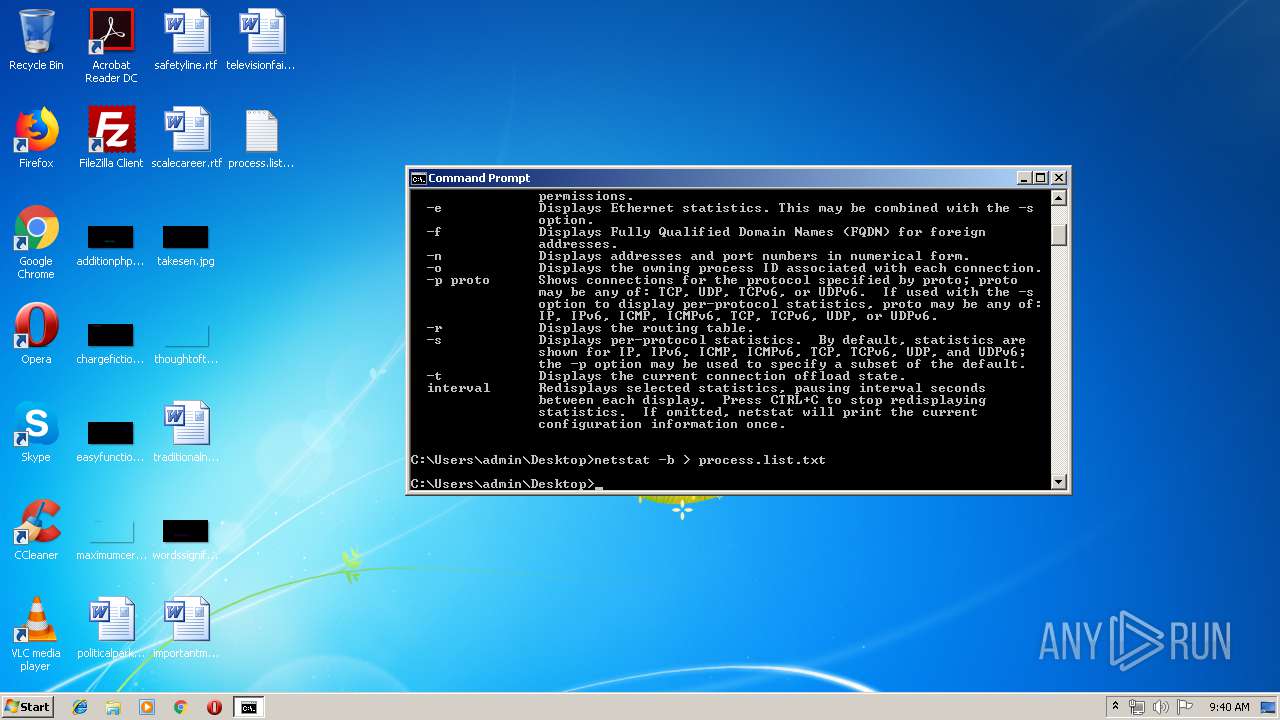
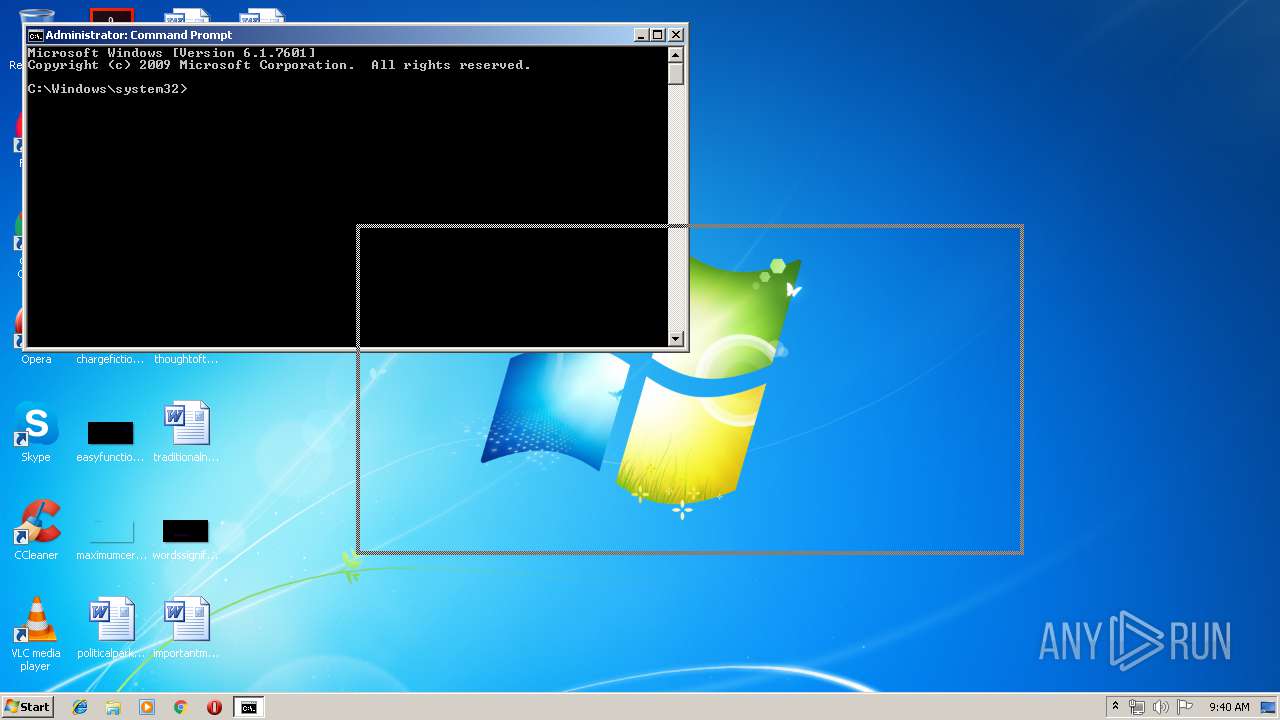
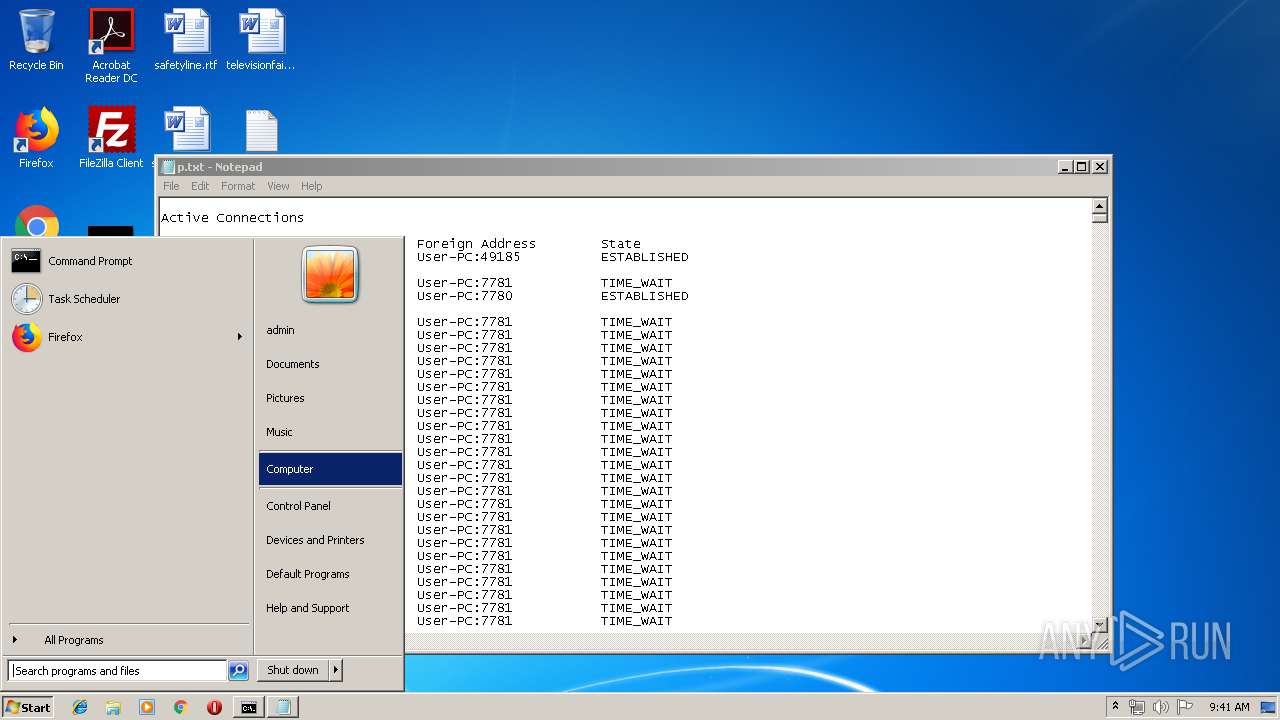
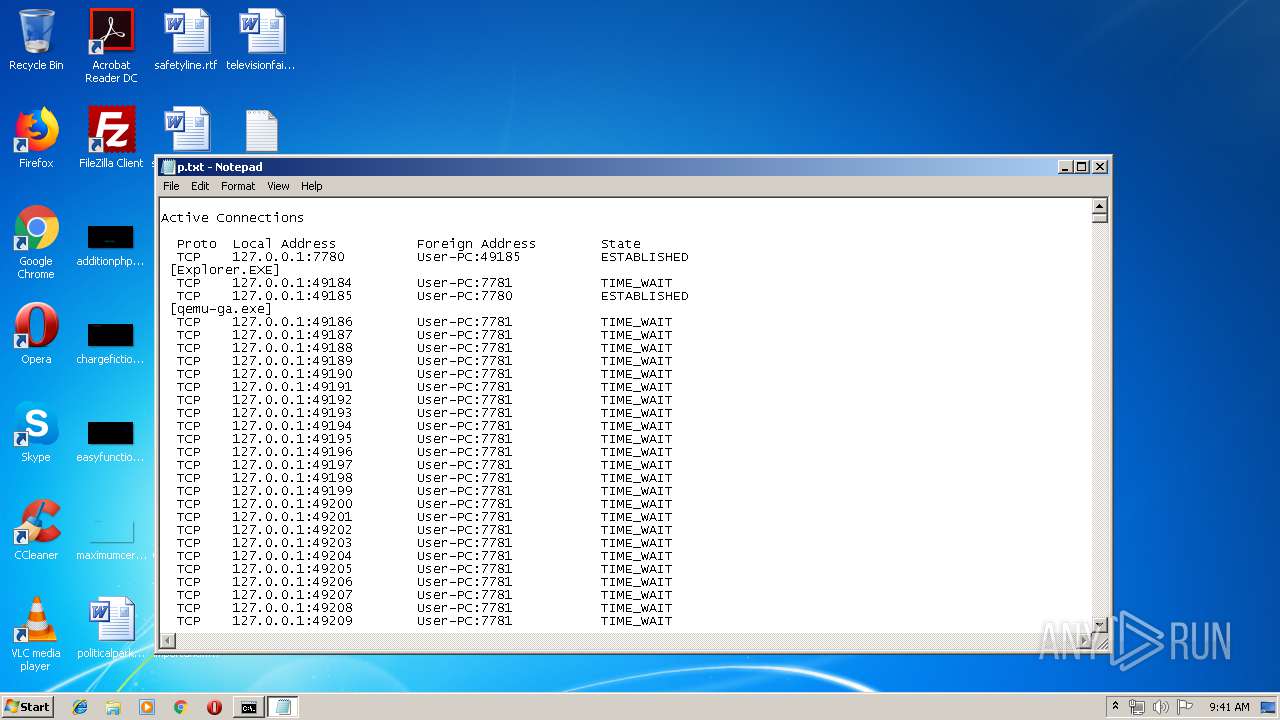
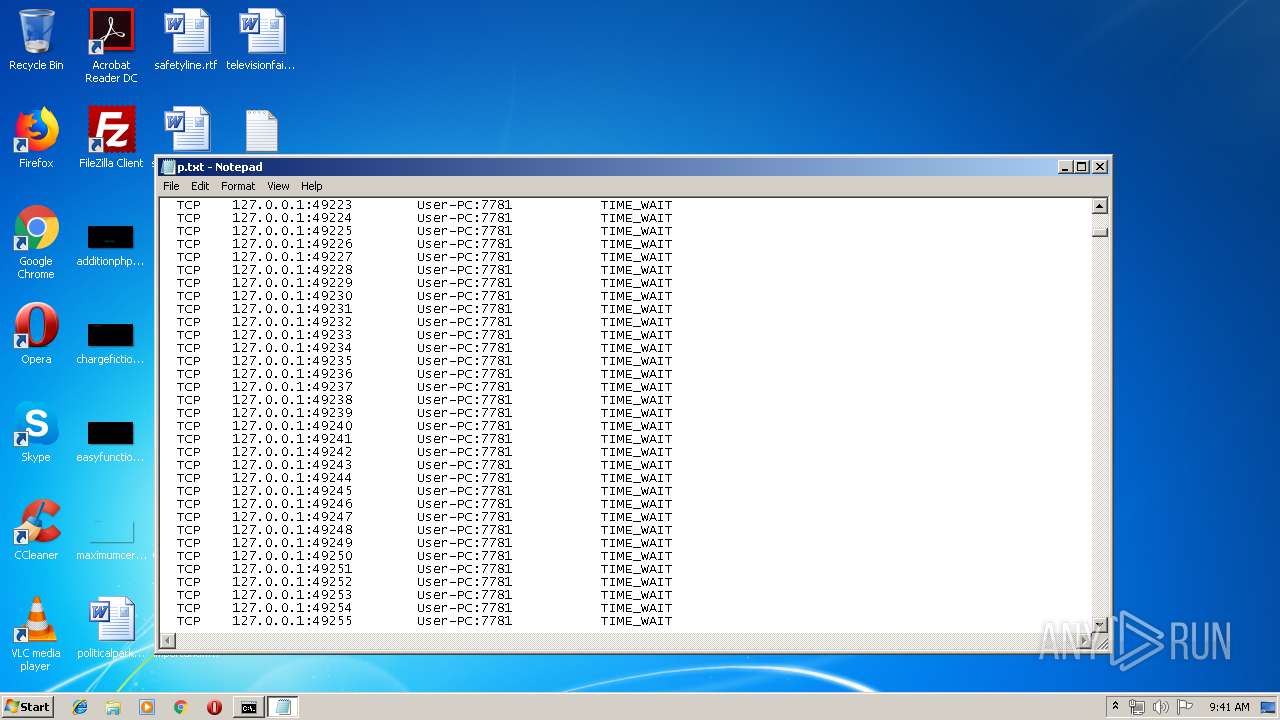
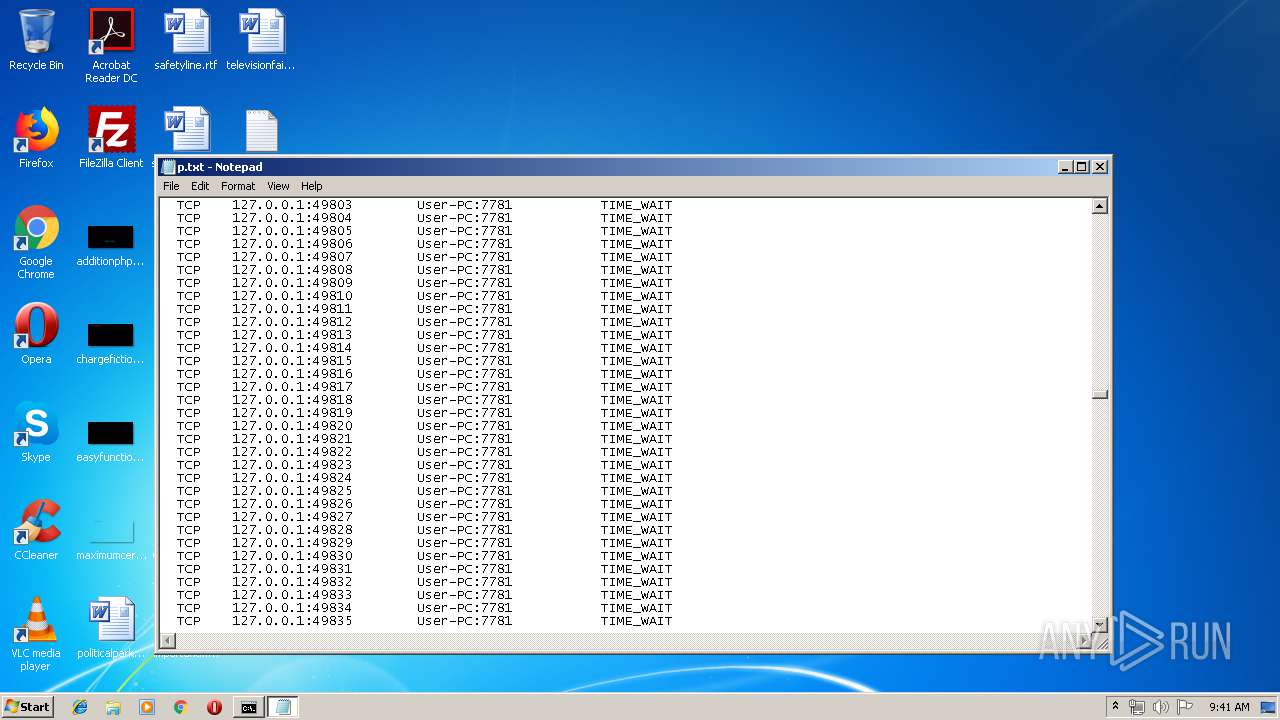
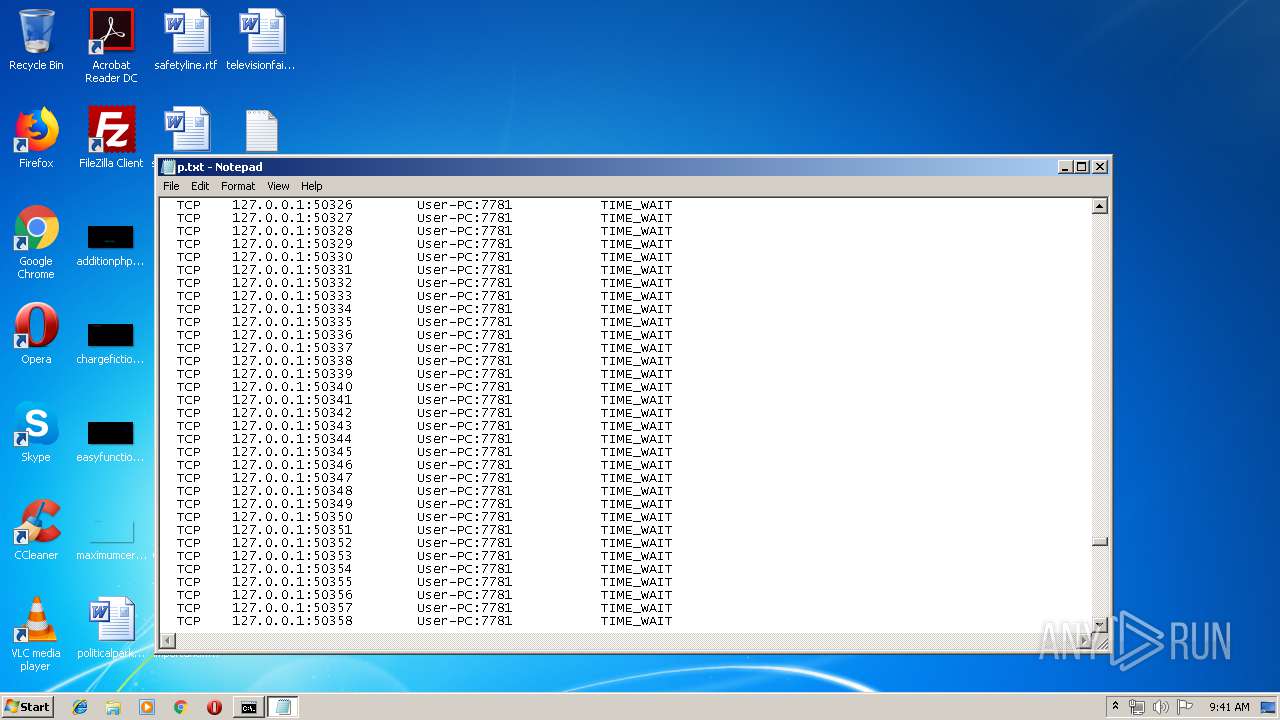
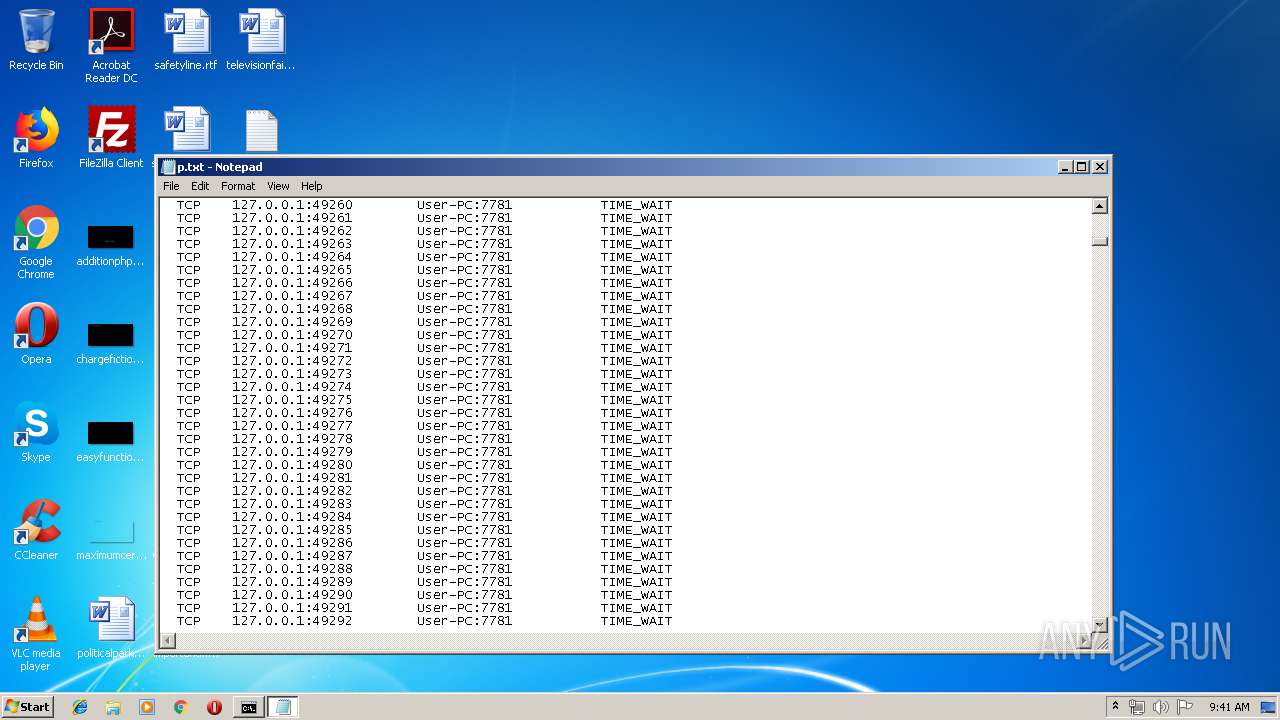
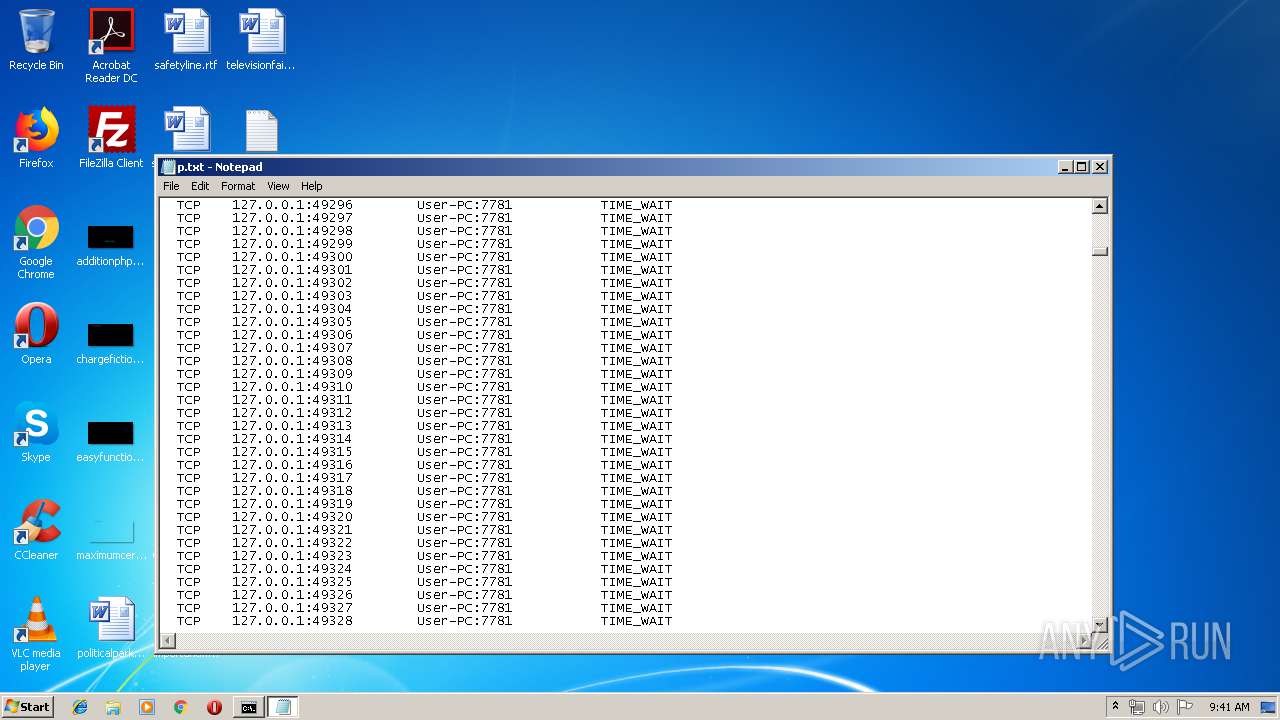
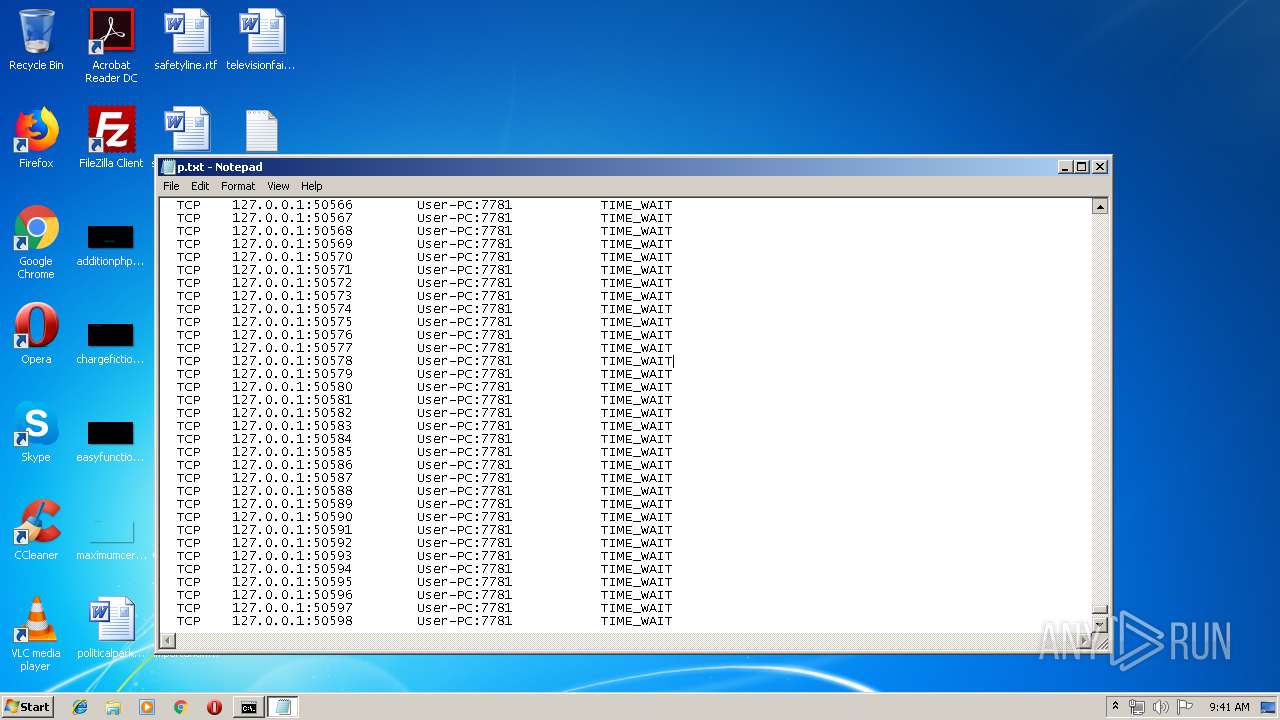
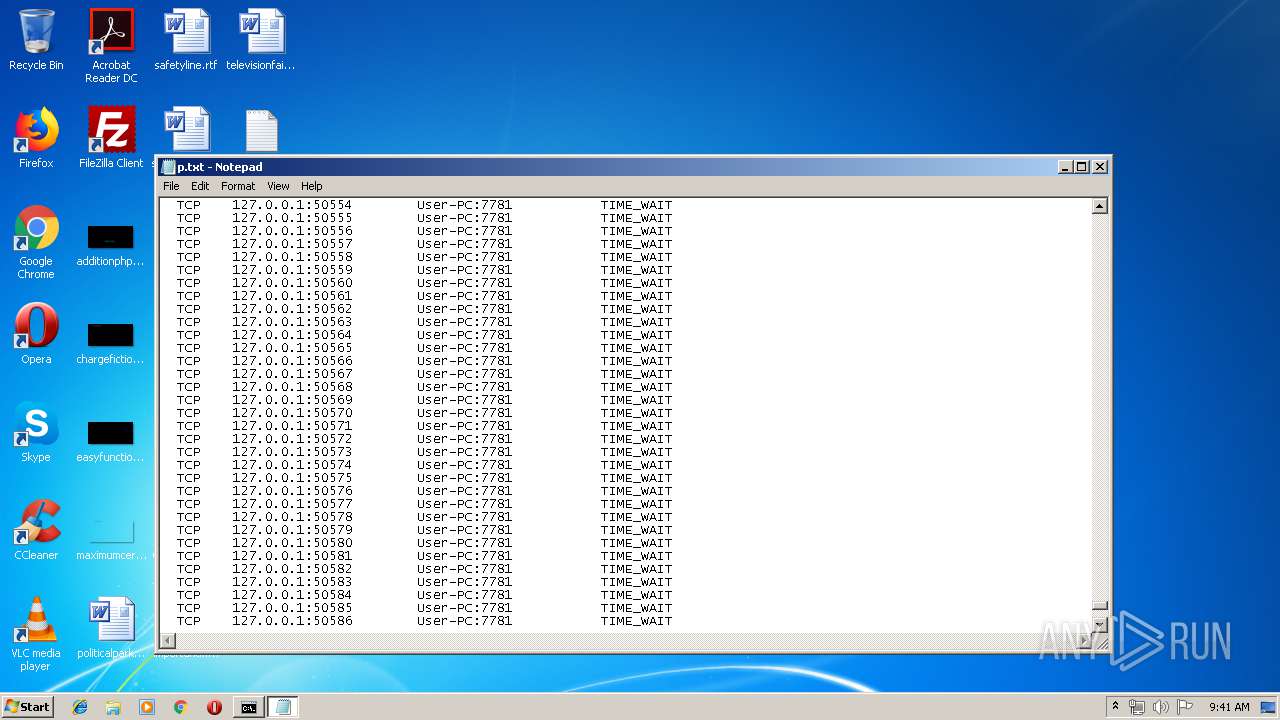
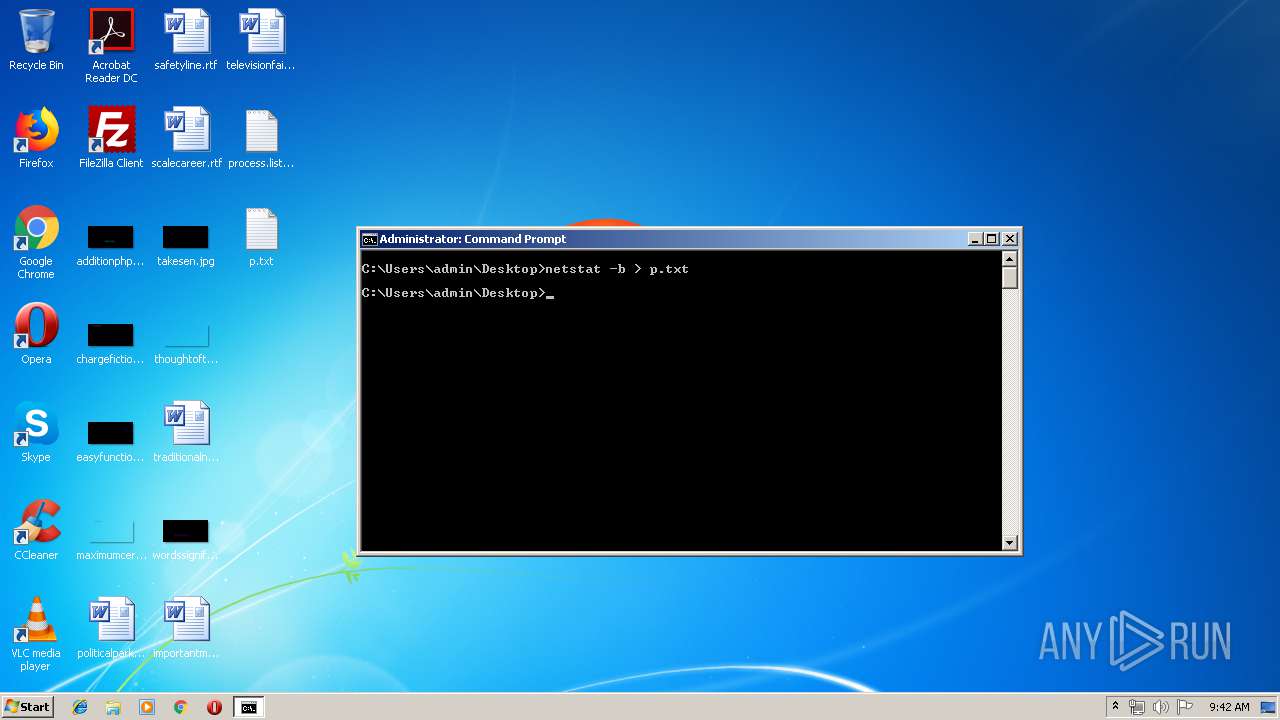
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3988)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:12 01:16:10 |
| ZipCRC: | 0x2446e170 |
| ZipCompressedSize: | 166 |
| ZipUncompressedSize: | 211 |
| ZipFileName: | META-INF/MANIFEST.MF |
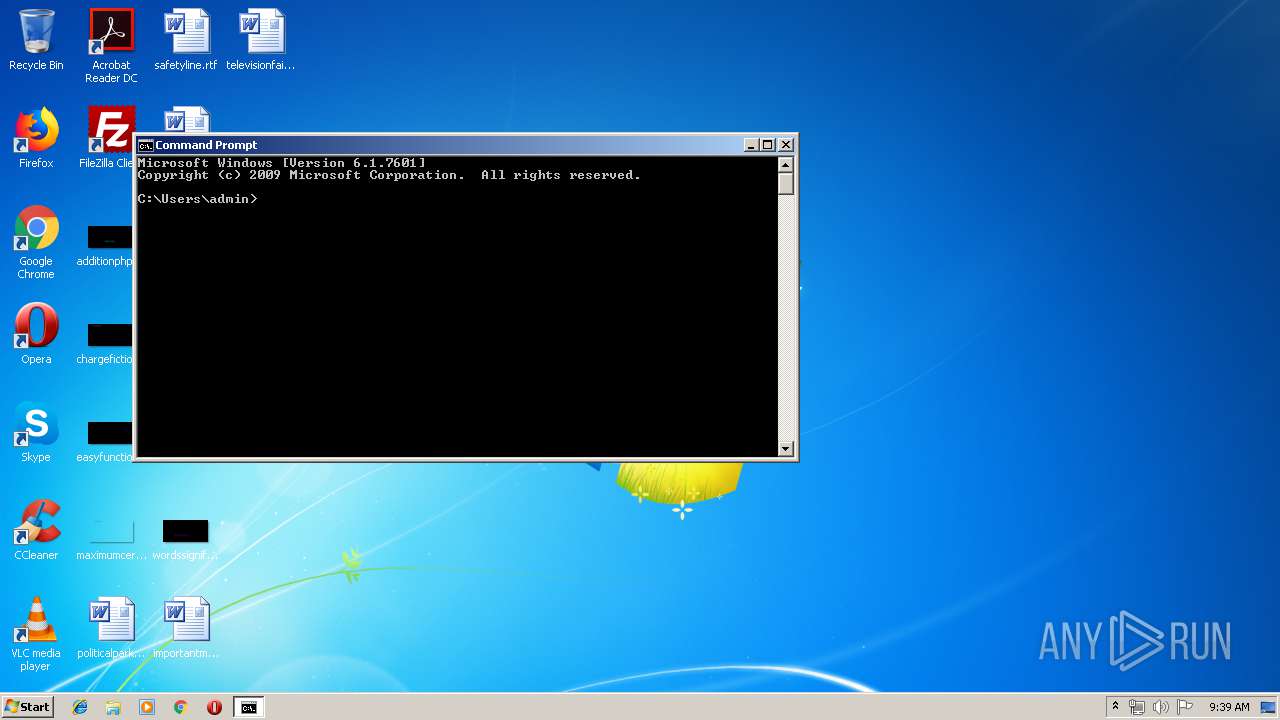
Total processes
64
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v asdasdasd /t REG_SZ /d "\"C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe\" -jar \"C:\Users\admin\AppData\Roaming\asdasd\asda.jar\"" /f | C:\Windows\system32\reg.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | attrib +s +h +r "C:\Users\admin\AppData\Roaming\asdasd" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v asdasdasd /t REG_SZ /d "\"C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe\" -jar \"C:\Users\admin\AppData\Roaming\asdasd\asda.jar\"" /f | C:\Windows\system32\reg.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1212 | attrib +s +h +r "C:\Users\admin\AppData\Roaming\asdasd\*.*" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
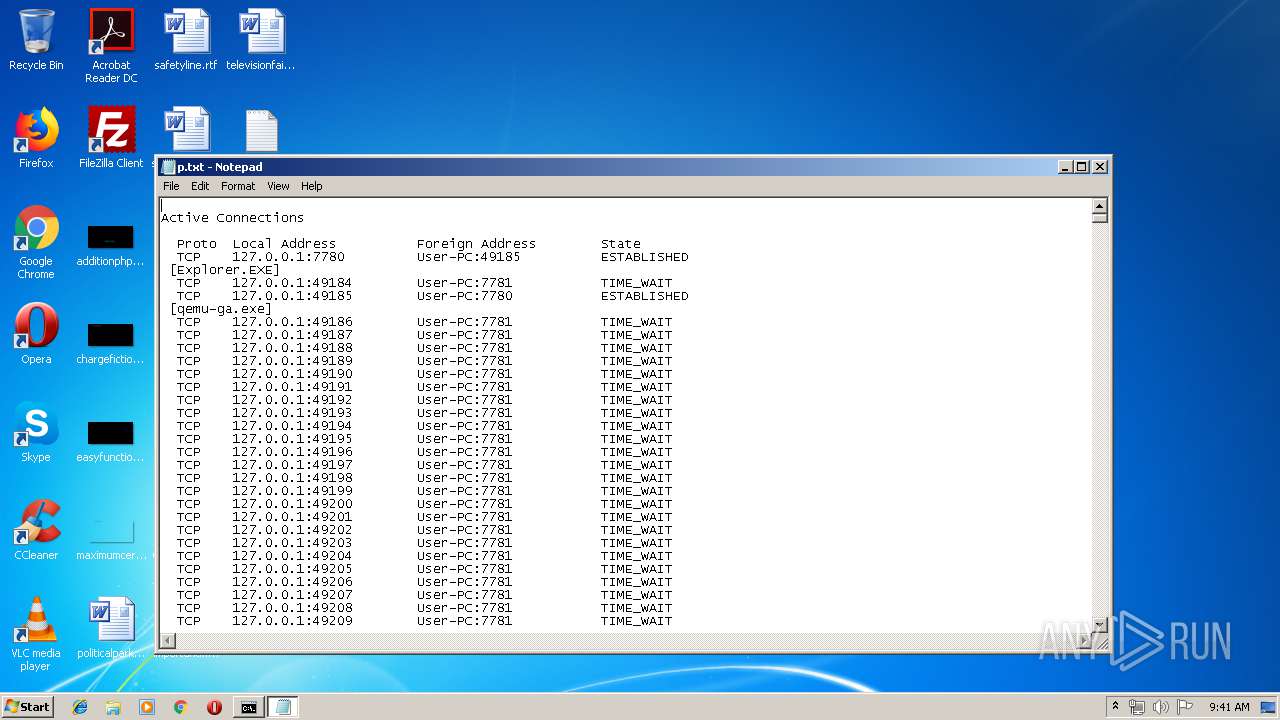
| 1336 | netstat | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
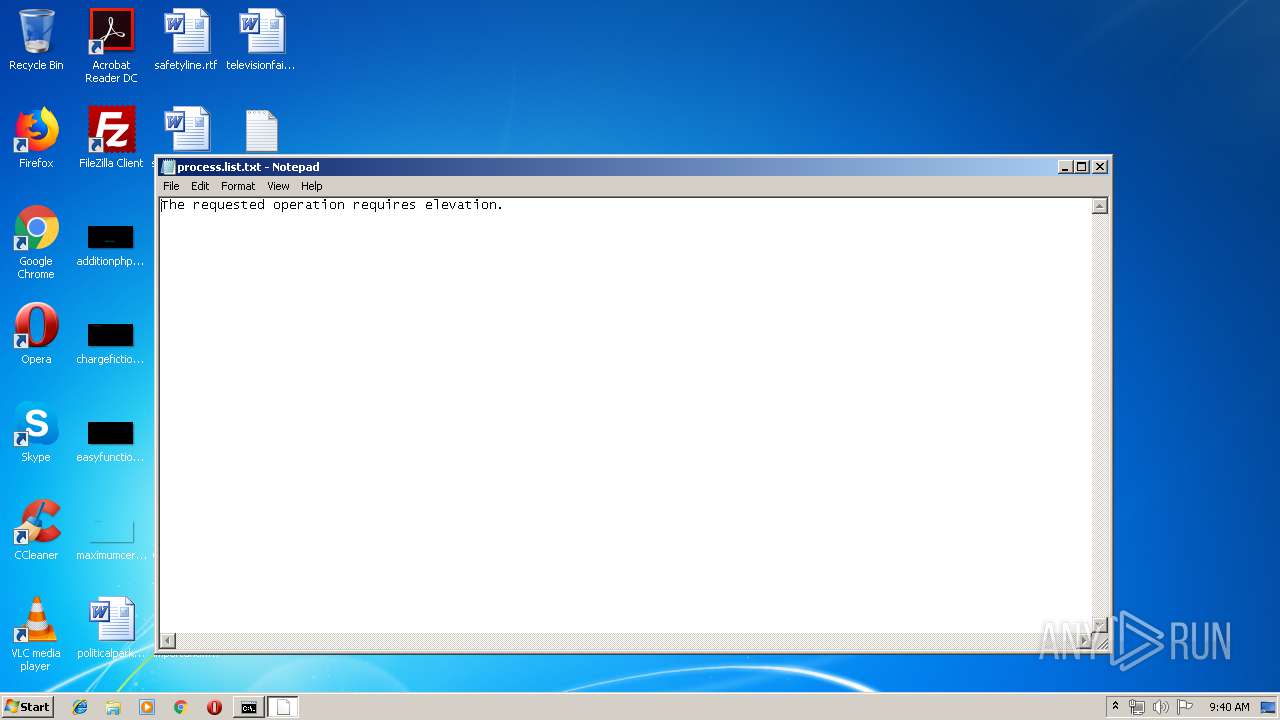
| 1680 | netstat -b | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1708 | reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Run /v asdasdasd /t REG_SZ /d "\"C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe\" -jar \"C:\Users\admin\AppData\Roaming\asdasd\asda.jar\"" /f | C:\Windows\system32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | attrib +H C:\Users\admin\.Plugins3 | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\p.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\vpn.jar.zip" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
88
Read events
79
Write events
9
Delete events
0
Modification events
| (PID) Process: | (296) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | asdasdasd |
Value: "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\asdasd\asda.jar" | |||
| (PID) Process: | (712) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | asdasdasd |
Value: "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\asdasd\asda.jar" | |||
| (PID) Process: | (2256) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3160) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 154 | |||
| (PID) Process: | (3160) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 154 | |||
| (PID) Process: | (3160) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3160) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (2796) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (1336) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
Executable files
1
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2256 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6815405426922097212.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2176 | javaw.exe | C:\Users\admin\AppData\Roaming\asdasd\asda.jar | java | |
MD5:— | SHA256:— | |||
| 2256 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3988 | cmd.exe | C:\Users\admin\Desktop\p.txt | text | |
MD5:— | SHA256:— | |||
| 2256 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 2176 | javaw.exe | C:\Users\admin\AppData\Roaming\asdasd\Desktop.ini | ini | |
MD5:E783BDD20A976EAEAAE1FF4624487420 | SHA256:2F65FA9C7ED712F493782ABF91467F869419A2F8B5ADF23B44019C08190FA3F3 | |||
| 3976 | cmd.exe | C:\Users\admin\Desktop\process.list.txt | text | |
MD5:C2E6B5D39145E5BBE26732EB5D5751BF | SHA256:1551E9D7B168BADE0FC637EBF41C052D4F8112EBFF60DAD9B00CAE4C1C82648B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
8
Threats
18
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2256 | javaw.exe | 54.38.61.62:1505 | — | OVH SAS | FR | malicious |
2256 | javaw.exe | 54.38.61.62:1506 | — | OVH SAS | FR | malicious |
— | — | 93.184.220.29:137 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.16.41.2:137 | — | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
112.186.16.2.in-addr.arpa |
| unknown |
37.159.32.13.in-addr.arpa |
| unknown |
29.220.184.93.in-addr.arpa |
| unknown |
2.41.16.104.in-addr.arpa |
| unknown |
74.22.217.172.in-addr.arpa |
| unknown |
227.168.217.172.in-addr.arpa |
| unknown |
238.21.217.172.in-addr.arpa |
| unknown |
62.61.38.54.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible JavaRAT(Qarallax/QRat) 4byte TCP serialization java stream |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.QRat.gen |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible JavaRAT(Qarallax/QRat) 4byte TCP serialization java stream |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible JavaRAT(Qarallax/QRat) 4byte TCP serialization java stream |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible JavaRAT(Qarallax/QRat) 4byte TCP serialization java stream |
2256 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible JavaRAT(Qarallax/QRat) 4byte TCP serialization java stream |
1 ETPRO signatures available at the full report