| File name: | vpn.jar |
| Full analysis: | https://app.any.run/tasks/1660765f-0081-493a-9a77-1e657312232d |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | April 23, 2019, 08:13:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | B5F5F5BDFC6A7C848FC5BEE504D3B6D1 |
| SHA1: | E22B417F57DE09485BFAA8B158182C6C8D6DD11D |
| SHA256: | DE7D1957F4813AF3120C95B2999686067C124F9DB540EBF29C8EF3FF299FA3FF |
| SSDEEP: | 768:hIqFc+bYjbINzVRi1D5Fk02KYl0O1ZxmFdr948hi8h/mQtgkDAO4ezL1TRqnBKGW:hPJVzezOHidrS8hsKgqlHCnBKG5793S |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 128)
- reg.exe (PID: 868)
Connects to CnC server
- javaw.exe (PID: 3660)
ADWIND was detected
- javaw.exe (PID: 3660)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2192)
- javaw.exe (PID: 3660)
Writes to a desktop.ini file (may be used to cloak folders)
- javaw.exe (PID: 2192)
Application launched itself
- javaw.exe (PID: 2192)
Creates files in the user directory
- javaw.exe (PID: 2192)
Executes JAVA applets
- javaw.exe (PID: 2192)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2192)
- javaw.exe (PID: 3660)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1472)
INFO
Application launched itself
- chrome.exe (PID: 1472)
Reads settings of System Certificates
- chrome.exe (PID: 1472)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:12 01:16:10 |
| ZipCRC: | 0x2446e170 |
| ZipCompressedSize: | 166 |
| ZipUncompressedSize: | 211 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
73
Monitored processes
36
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v asdasdasd /t REG_SZ /d "\"C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe\" -jar \"C:\Users\admin\AppData\Roaming\asdasd\asda.jar\"" /f | C:\Windows\system32\reg.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | attrib +s +h +r "C:\Users\admin\AppData\Roaming\asdasd" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f350f18,0x6f350f28,0x6f350f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 584 | reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Run /v asdasdasd /t REG_SZ /d "\"C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe\" -jar \"C:\Users\admin\AppData\Roaming\asdasd\asda.jar\"" /f | C:\Windows\system32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,14683362048179942783,14672339213252047911,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11527102288460546953 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11527102288460546953 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 868 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v asdasdasd /t REG_SZ /d "\"C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe\" -jar \"C:\Users\admin\AppData\Roaming\asdasd\asda.jar\"" /f | C:\Windows\system32\reg.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,14683362048179942783,14672339213252047911,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=762314297143069996 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,14683362048179942783,14672339213252047911,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9046147451036301076 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9046147451036301076 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,14683362048179942783,14672339213252047911,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11906157420494479481 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11906157420494479481 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | attrib +s +h +r "C:\Users\admin\AppData\Roaming\asdasd\*.*" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
606
Read events
501
Write events
100
Delete events
5
Modification events
| (PID) Process: | (128) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | asdasdasd |
Value: "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\asdasd\asda.jar" | |||
| (PID) Process: | (868) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | asdasdasd |
Value: "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\asdasd\asda.jar" | |||
| (PID) Process: | (3660) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (1472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1472-13200480867300625 |
Value: 259 | |||
| (PID) Process: | (1472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
Executable files
1
Suspicious files
75
Text files
201
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\897fcdce-c36e-4a04-ba7a-9904019e642a.tmp | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
37
DNS requests
17
Threats
7
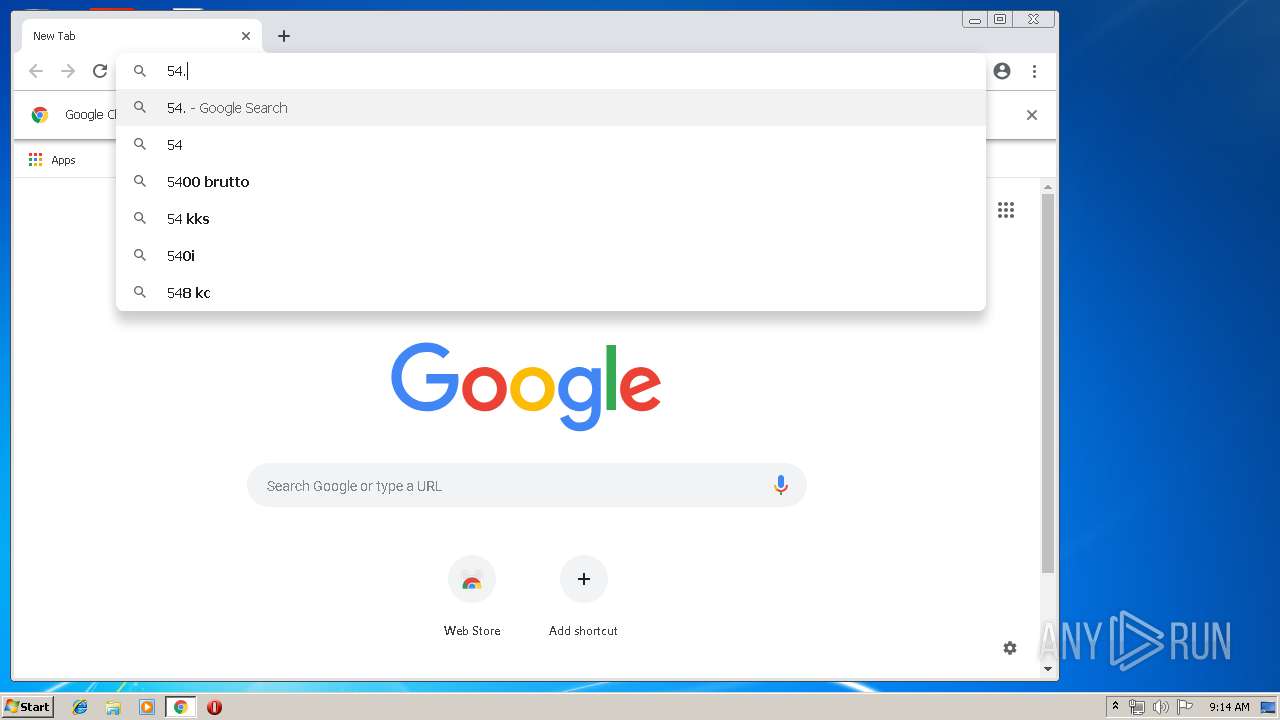
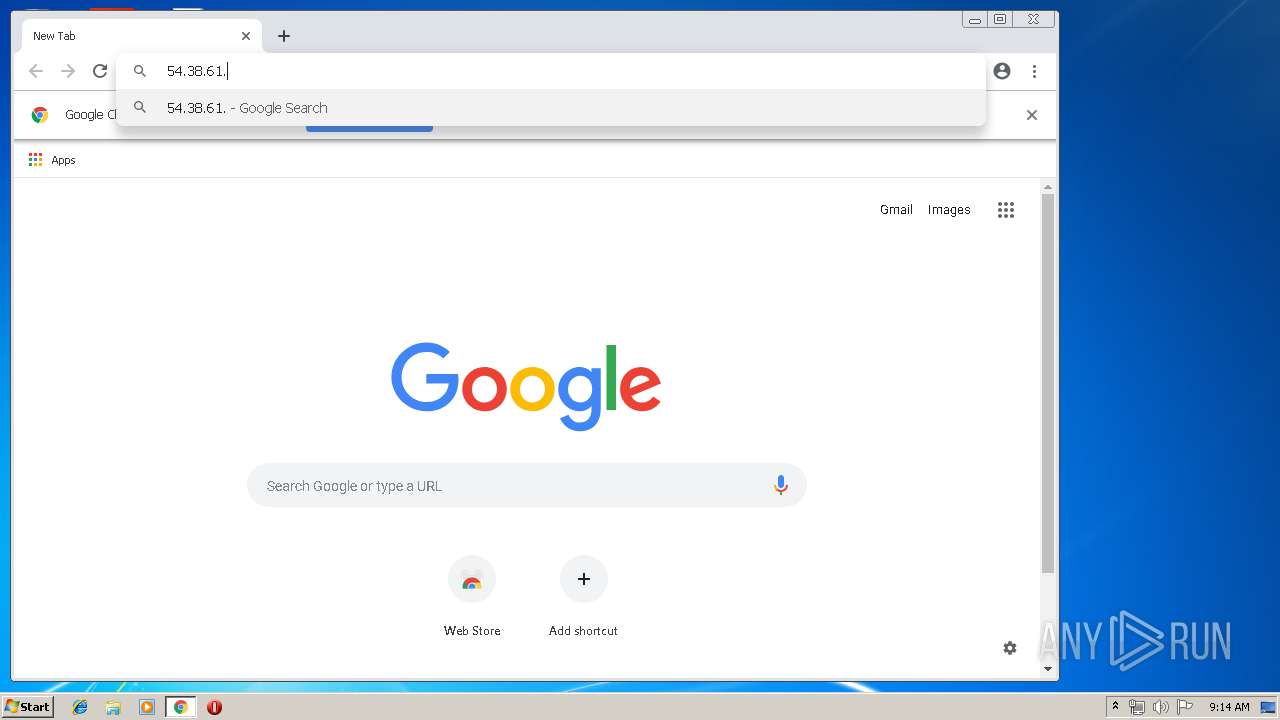
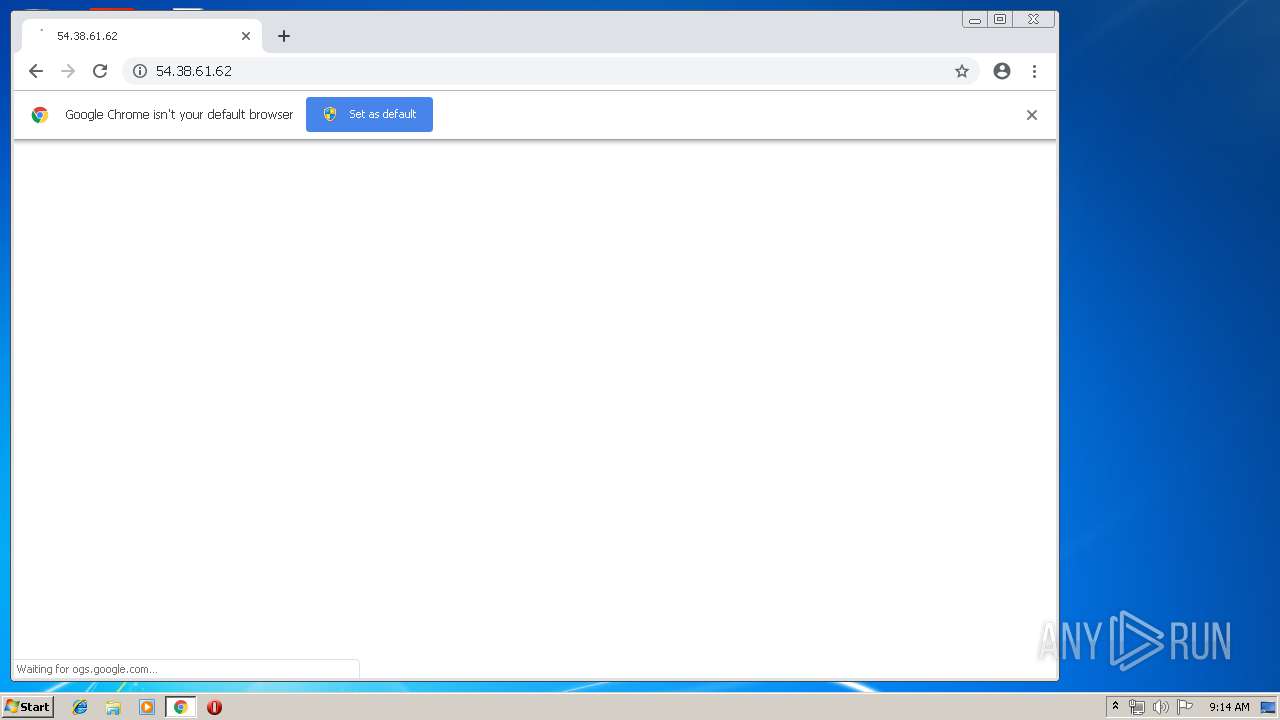
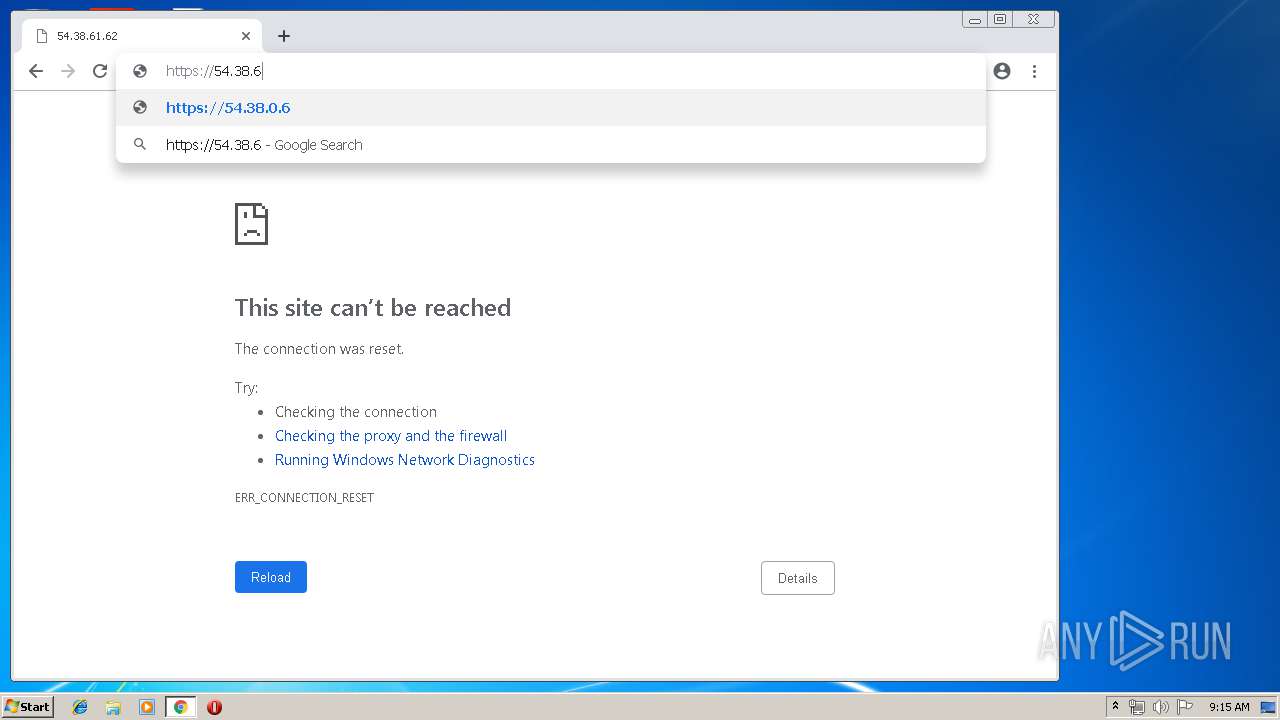
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1472 | chrome.exe | GET | — | 54.38.61.62:80 | http://54.38.61.62/ | FR | — | — | malicious |
1472 | chrome.exe | GET | — | 54.38.61.62:80 | http://54.38.61.62/ | FR | — | — | malicious |
1472 | chrome.exe | GET | — | 54.38.61.62:80 | http://54.38.61.62/ | FR | — | — | malicious |
1472 | chrome.exe | GET | — | 54.38.61.62:80 | http://54.38.61.62/ | FR | — | — | malicious |
1472 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
1472 | chrome.exe | GET | 200 | 194.9.25.78:80 | http://r3---sn-5uh5o-f5fs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.219.109&mm=28&mn=sn-5uh5o-f5fs&ms=nvh&mt=1556006690&mv=u&pl=24&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | javaw.exe | 54.38.61.62:1505 | ip62.ip-54-38-61.eu | OVH SAS | FR | malicious |
1472 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
1472 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.pl |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3660 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible JavaRAT(Qarallax/QRat) 4byte TCP serialization java stream |
3660 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.QRat.gen |
3660 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
3660 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
3660 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
3660 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adwind.RAT v.3.0 Check-in |
1 ETPRO signatures available at the full report