| File name: | Samples and Enquiries.exe |
| Full analysis: | https://app.any.run/tasks/4f848017-cc14-4691-817c-d6c28b2556cf |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | October 14, 2019, 19:59:15 |
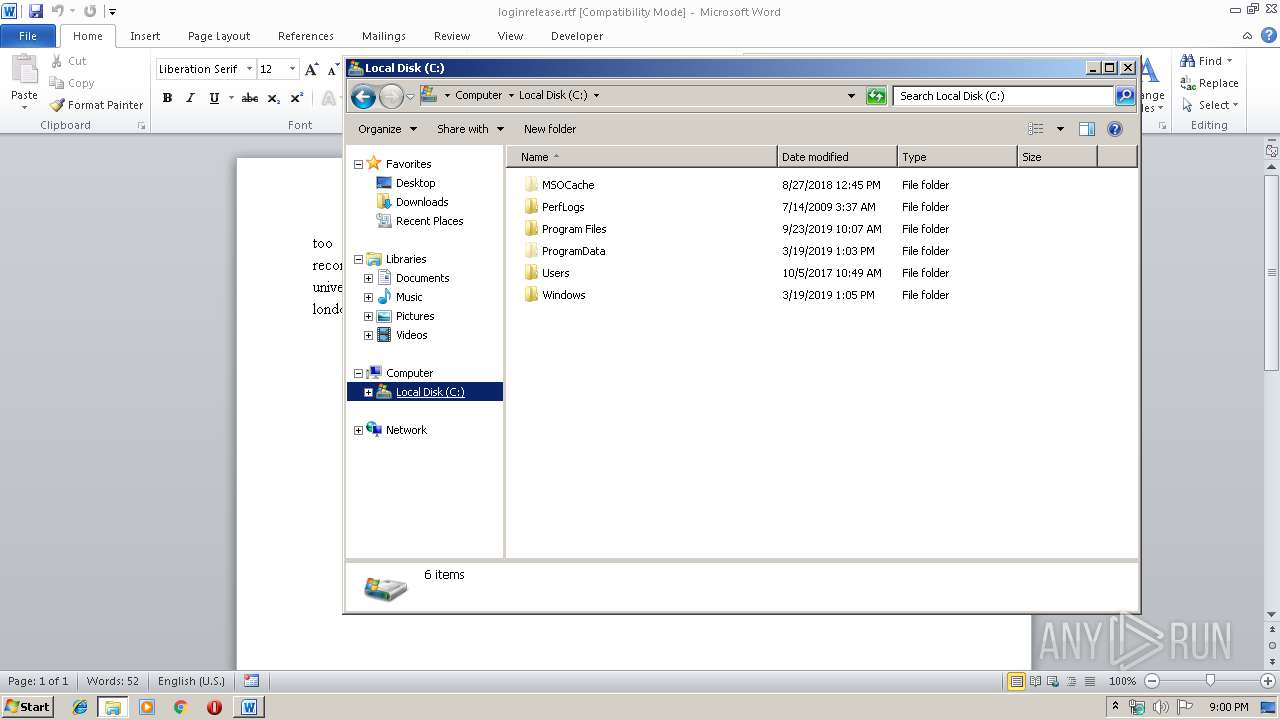
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 499E717756349E038B824DC9CCBF640E |
| SHA1: | FF1ACD16AF1F856B91117C176D15CBD2F674D96C |
| SHA256: | DE52D0C2FE133D9D39B41FE50C361FC0E404DB1564B287723290E5BED26ACEC1 |
| SSDEEP: | 12288:EkLJnjCb2WuCgRACKCkD40JSXluuSSXgAe:EkLc6WuCgRACKFJSXluu5N |
MALICIOUS
Changes the autorun value in the registry
- Samples and Enquiries.exe (PID: 4080)
AGENTTESLA was detected
- Samples and Enquiries.exe (PID: 4080)
Actions looks like stealing of personal data
- Samples and Enquiries.exe (PID: 4080)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3160)
Application launched itself
- Samples and Enquiries.exe (PID: 2096)
Executable content was dropped or overwritten
- Samples and Enquiries.exe (PID: 4080)
Connects to SMTP port
- Samples and Enquiries.exe (PID: 4080)
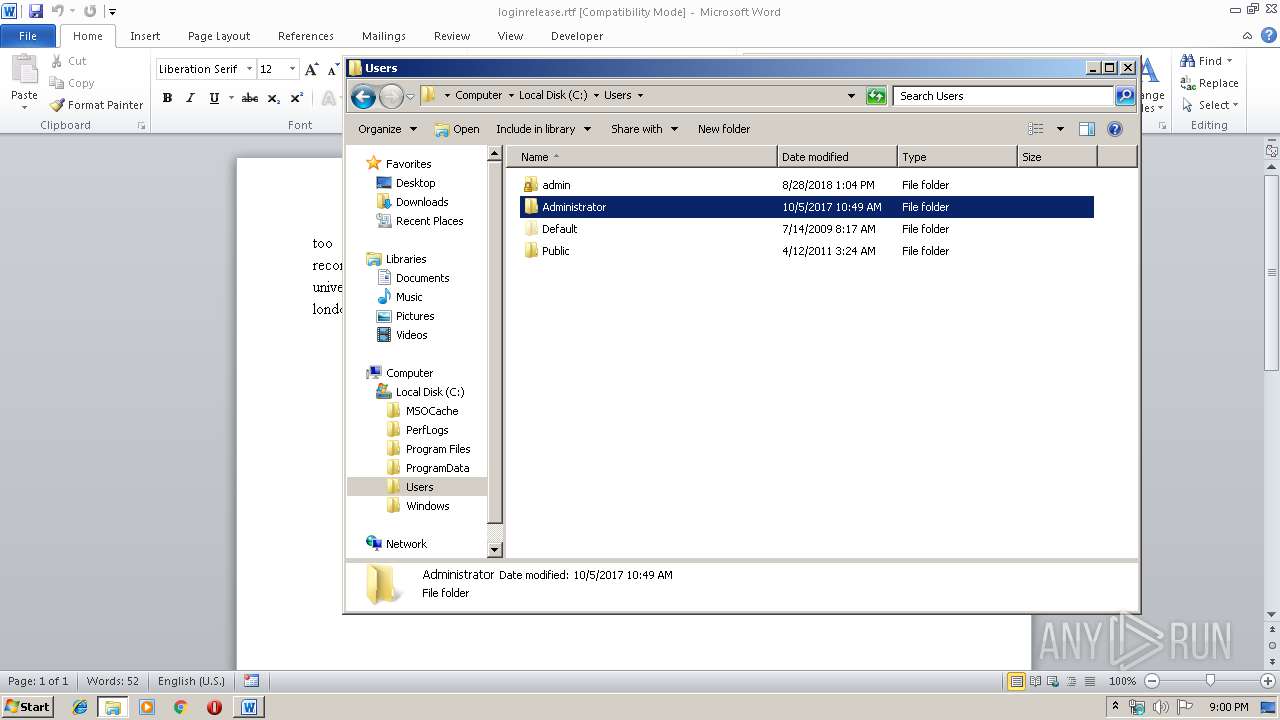
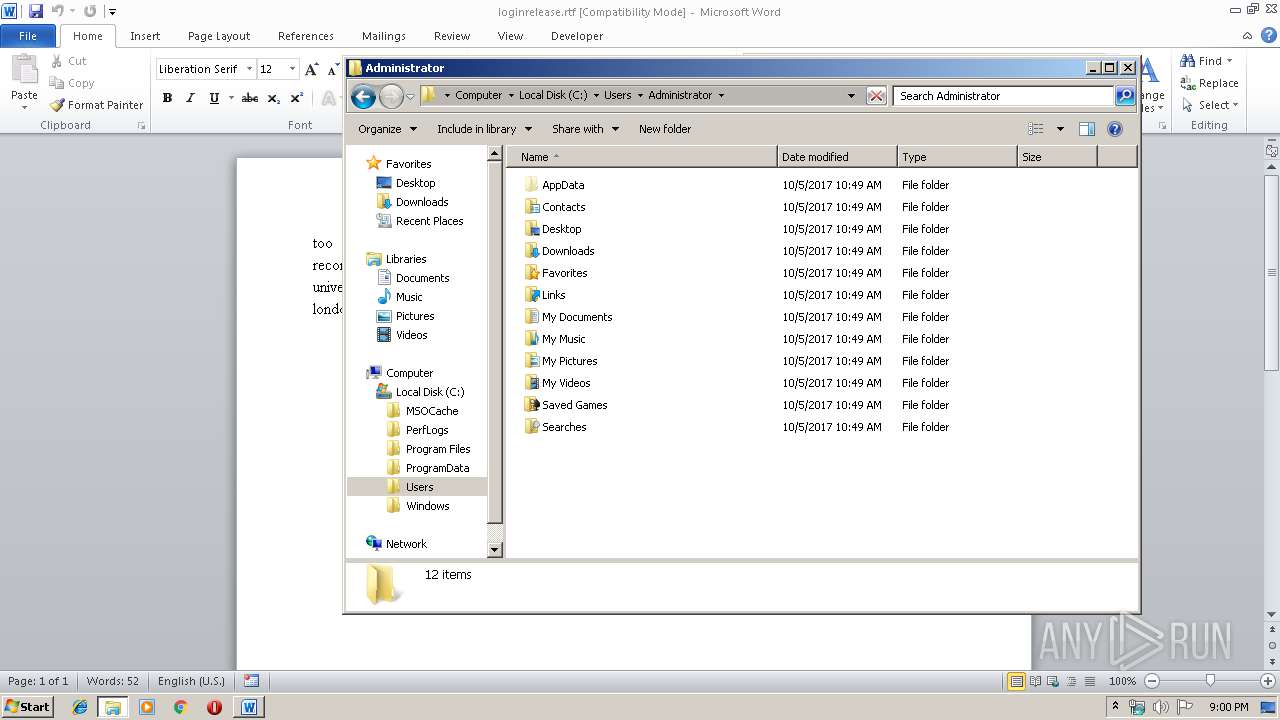
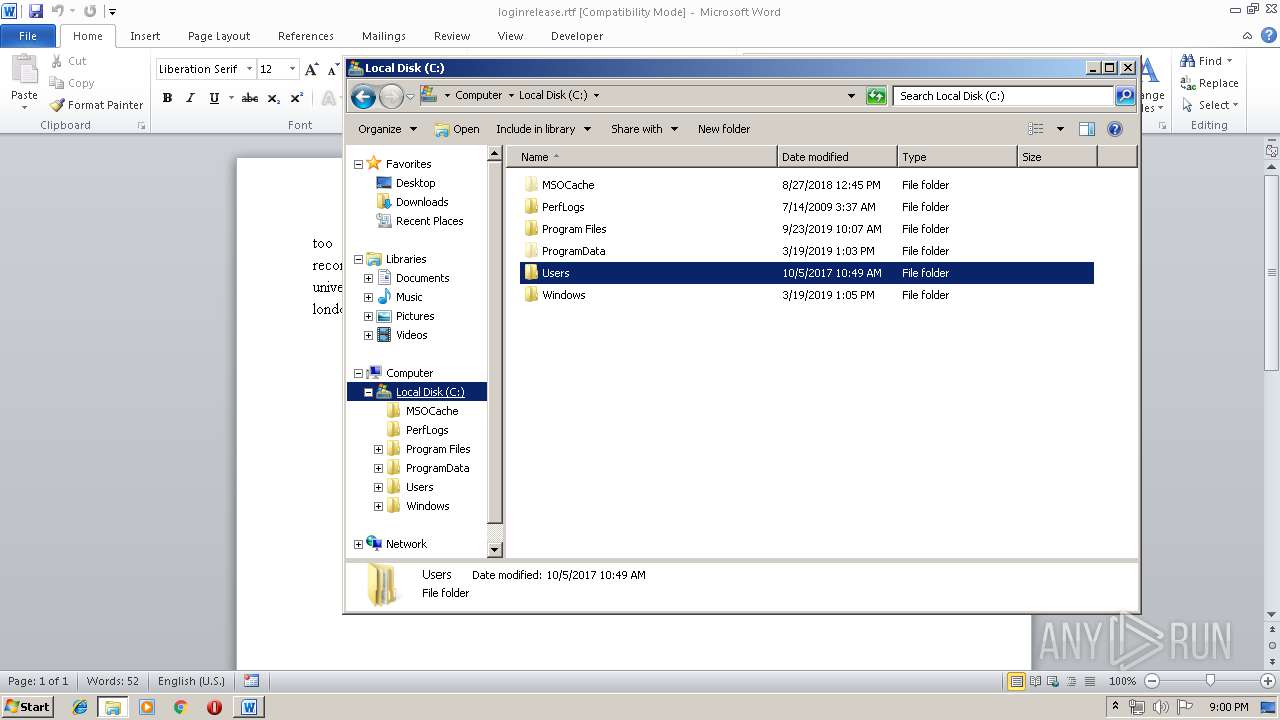
Creates files in the user directory
- Samples and Enquiries.exe (PID: 4080)
INFO
Manual execution by user
- WINWORD.EXE (PID: 3616)
- explorer.exe (PID: 1096)
Creates files in the user directory
- WINWORD.EXE (PID: 3616)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3616)
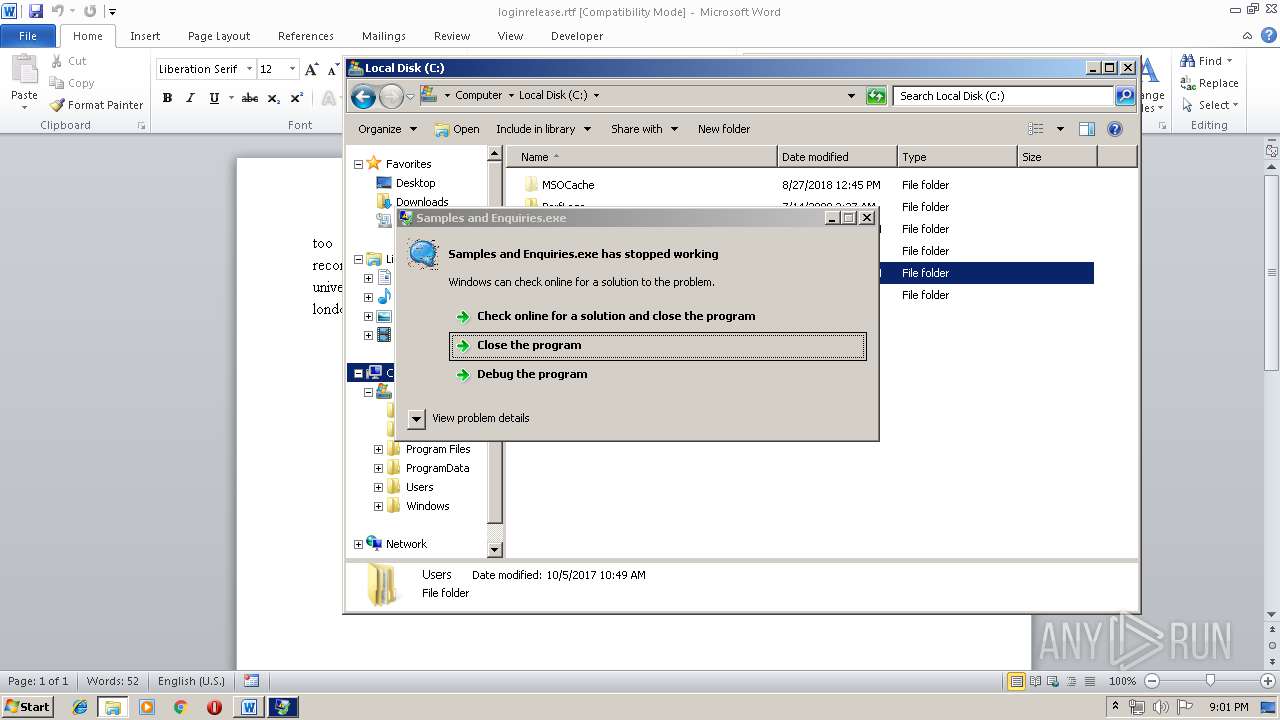
Application was crashed
- Samples and Enquiries.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:23 04:22:26+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 548864 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1334 |
| OSVersion: | 4 |
| ImageVersion: | 1.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.3 |
| ProductVersionNumber: | 1.1.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | AMmiccova |
| FileVersion: | 1.01.0003 |
| ProductVersion: | 1.01.0003 |
| InternalName: | GASas |
| OriginalFileName: | GASas.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Aug-2015 02:22:26 |
| Detected languages: |
|
| ProductName: | AMmiccova |
| FileVersion: | 1.01.0003 |
| ProductVersion: | 1.01.0003 |
| InternalName: | GASas |
| OriginalFilename: | GASas.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Aug-2015 02:22:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00085EC4 | 0x00086000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.06243 |
.data | 0x00087000 | 0x0000116C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00089000 | 0x00001D3C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96829 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.24049 | 484 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 3.6365 | 2664 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 5.98653 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 6.06042 | 1736 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
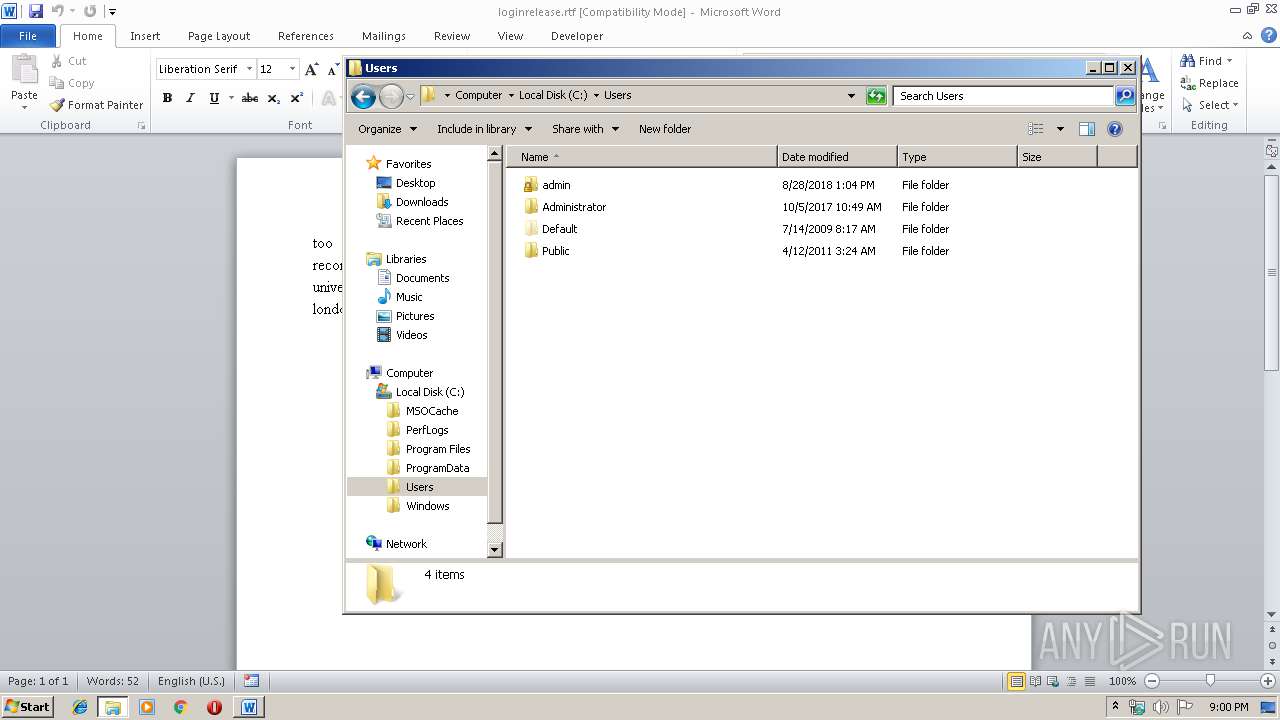
| 1096 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
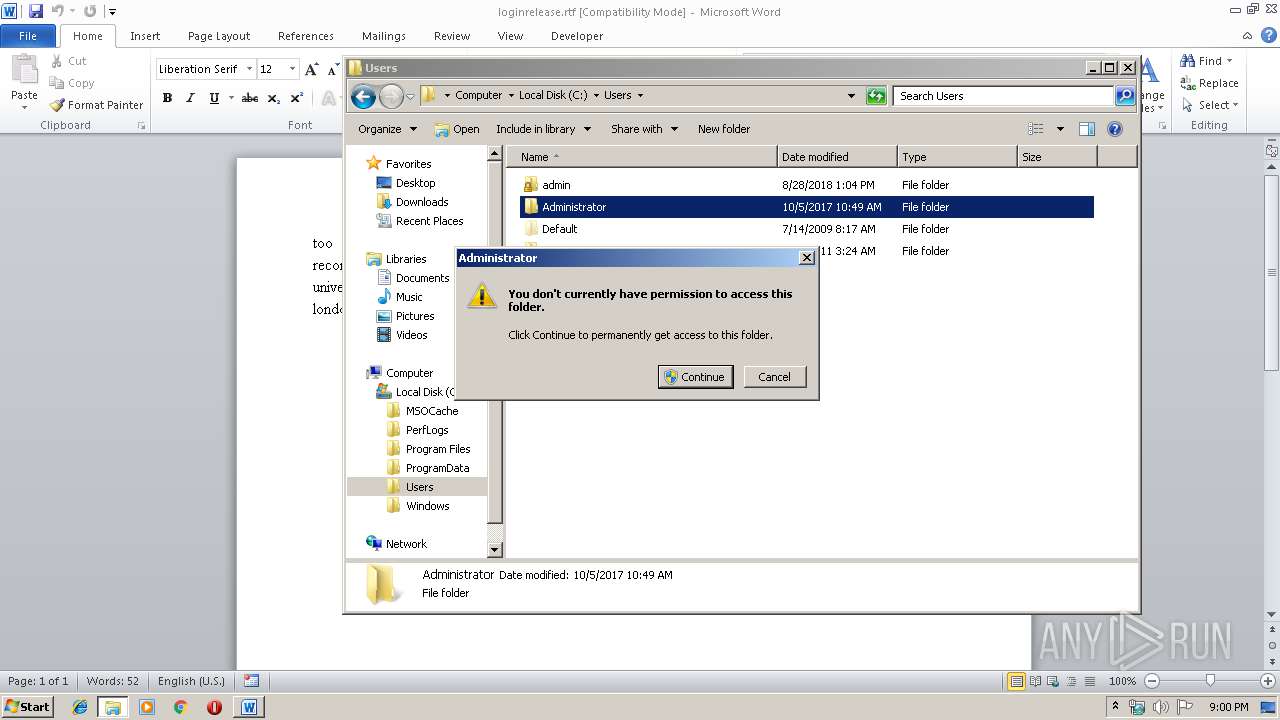
| 2096 | "C:\Users\admin\AppData\Local\Temp\Samples and Enquiries.exe" | C:\Users\admin\AppData\Local\Temp\Samples and Enquiries.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.01.0003 Modules
| |||||||||||||||
| 2608 | dw20.exe -x -s 1188 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | Samples and Enquiries.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3160 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
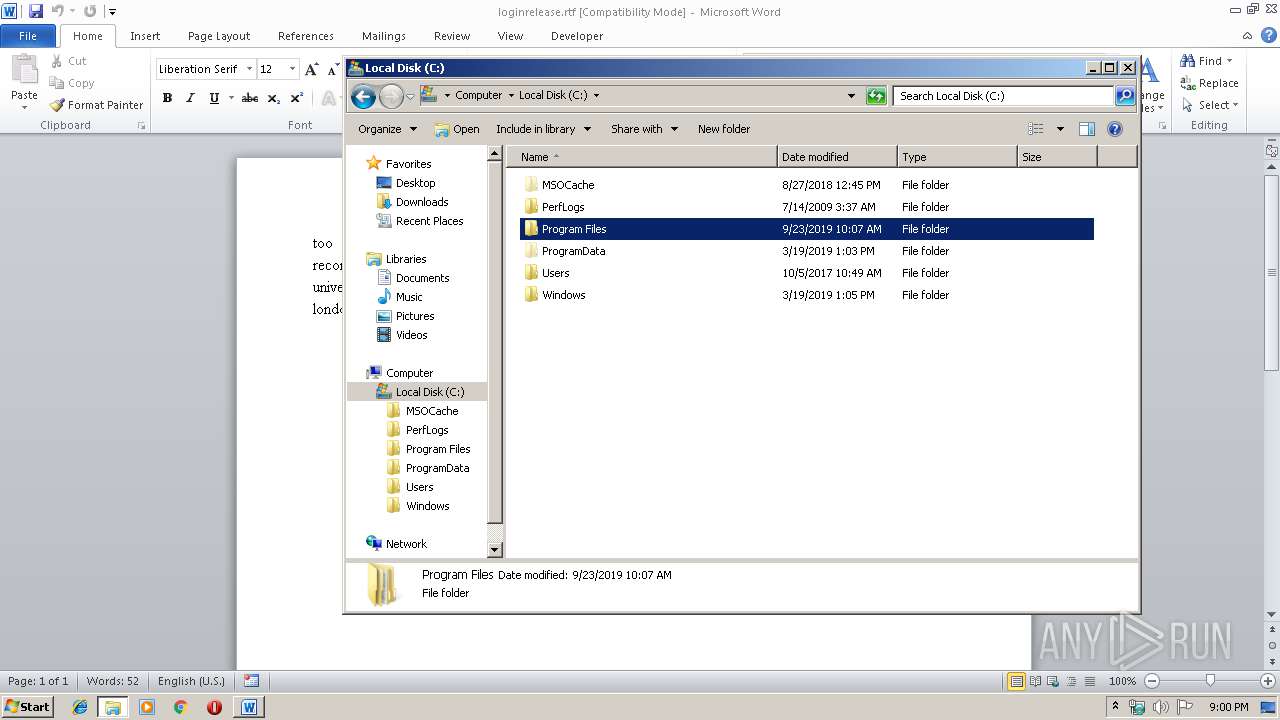
| 3616 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\loginrelease.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\Samples and Enquiries.exe" | C:\Users\admin\AppData\Local\Temp\Samples and Enquiries.exe | Samples and Enquiries.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.01.0003 Modules
| |||||||||||||||
Total events
1 454
Read events
771
Write events
548
Delete events
135
Modification events
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :ya |
Value: 3A796100200E0000010000000000000000000000 | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3616) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511935 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRCDBA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\Desktop\~$ginrelease.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\loginrelease.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3616 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 4080 | Samples and Enquiries.exe | C:\Users\admin\AppData\Roaming\MyApp\MyApp.exe | executable | |
MD5:— | SHA256:— | |||
| 4080 | Samples and Enquiries.exe | C:\Users\admin\AppData\Local\Temp\637066836427183360_c3a1dc1d-5dd5-47ae-8248-3a40e9765727.db | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | Samples and Enquiries.exe | 173.254.28.237:587 | mail.amethishipping.com | Unified Layer | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.amethishipping.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4080 | Samples and Enquiries.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |