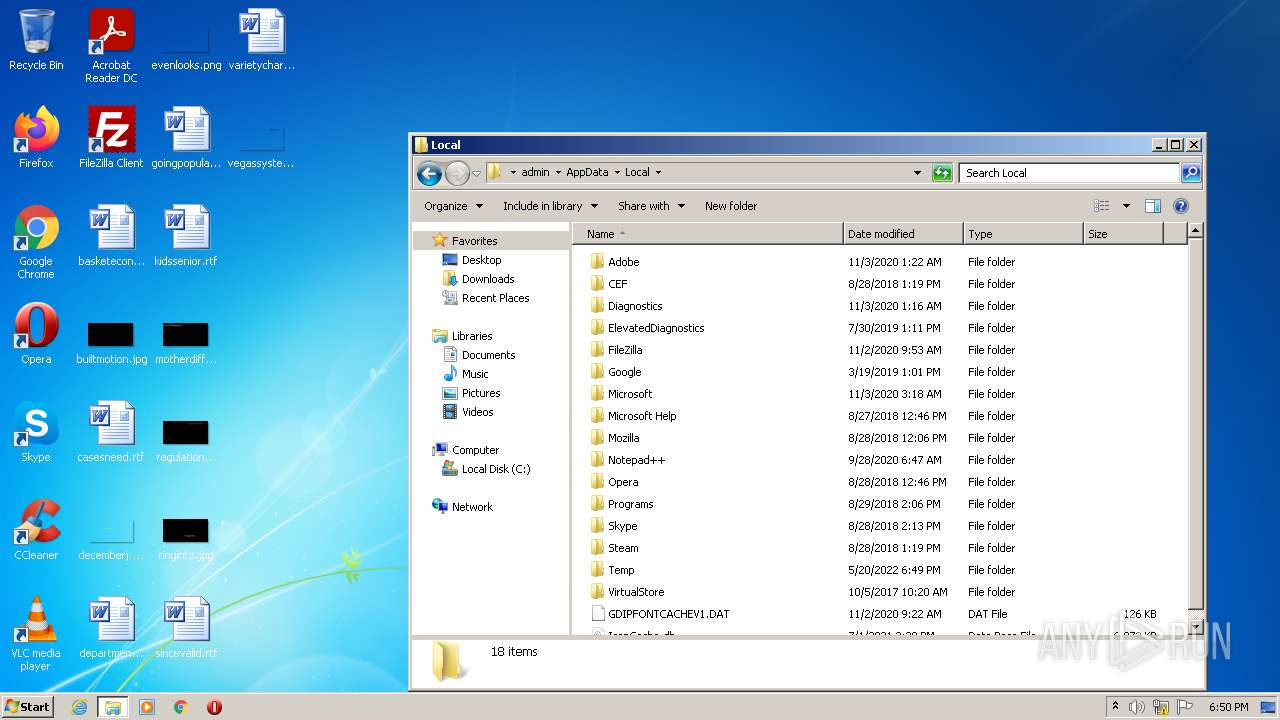
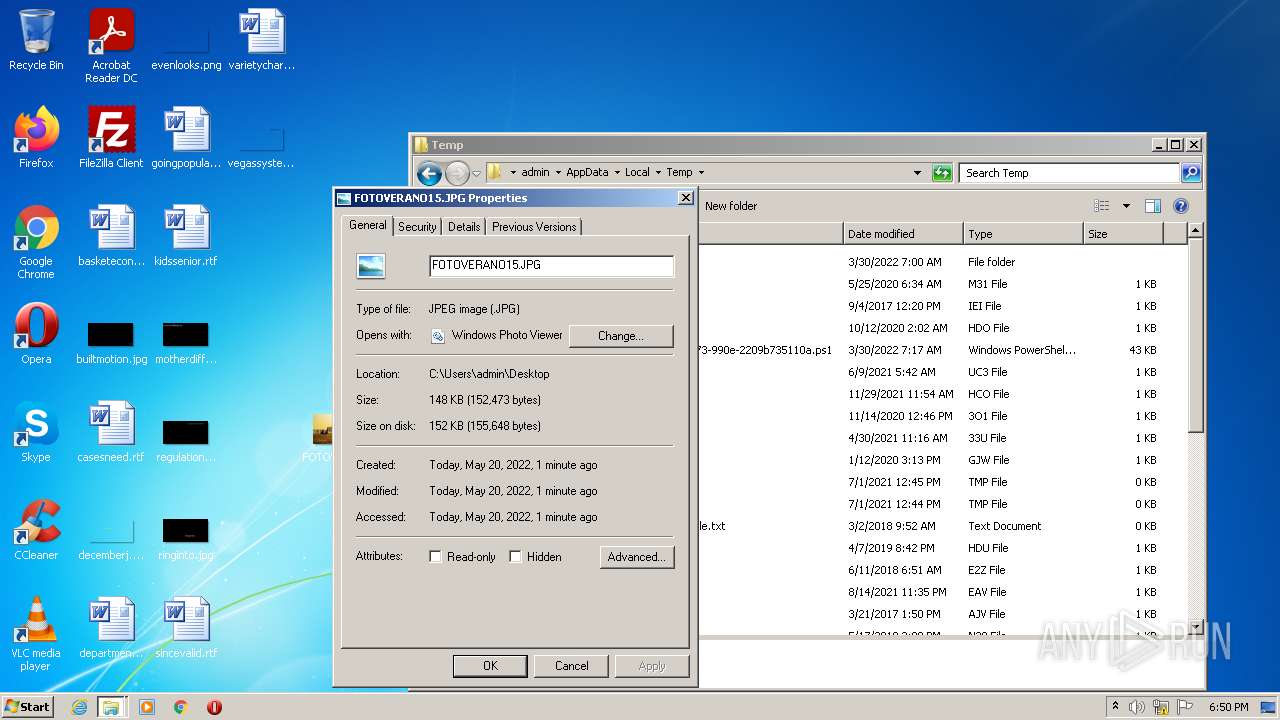
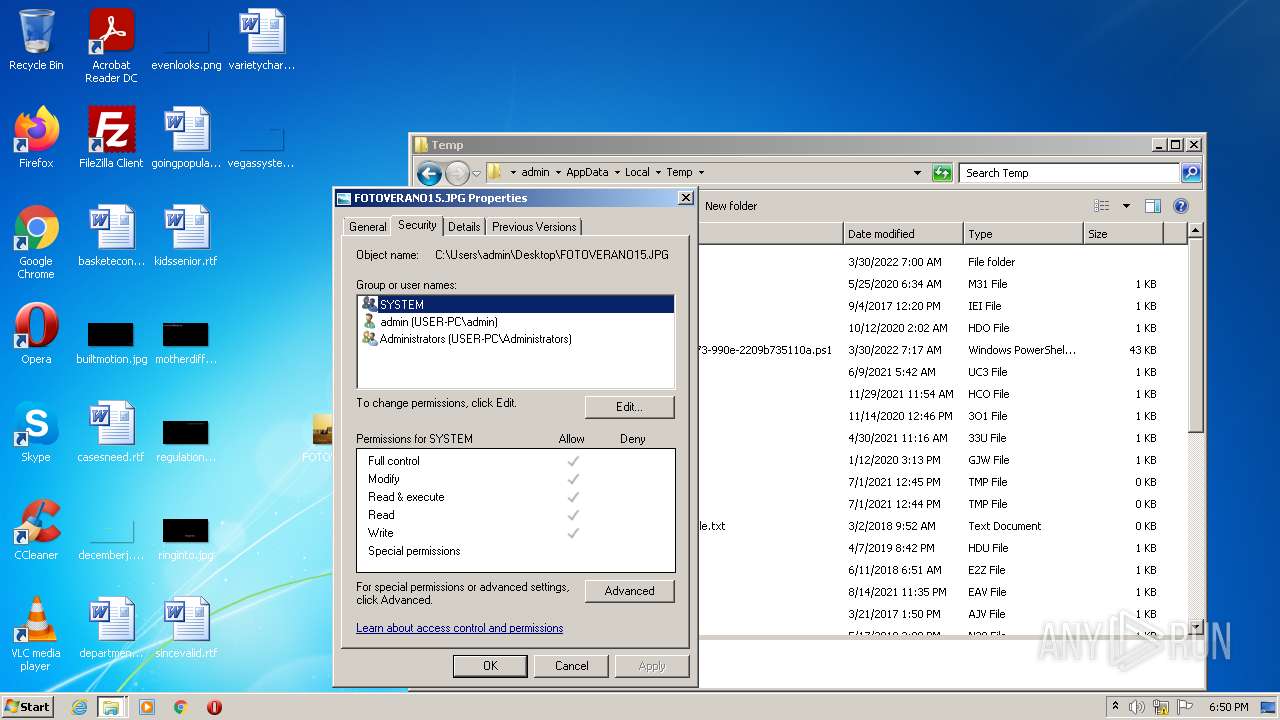
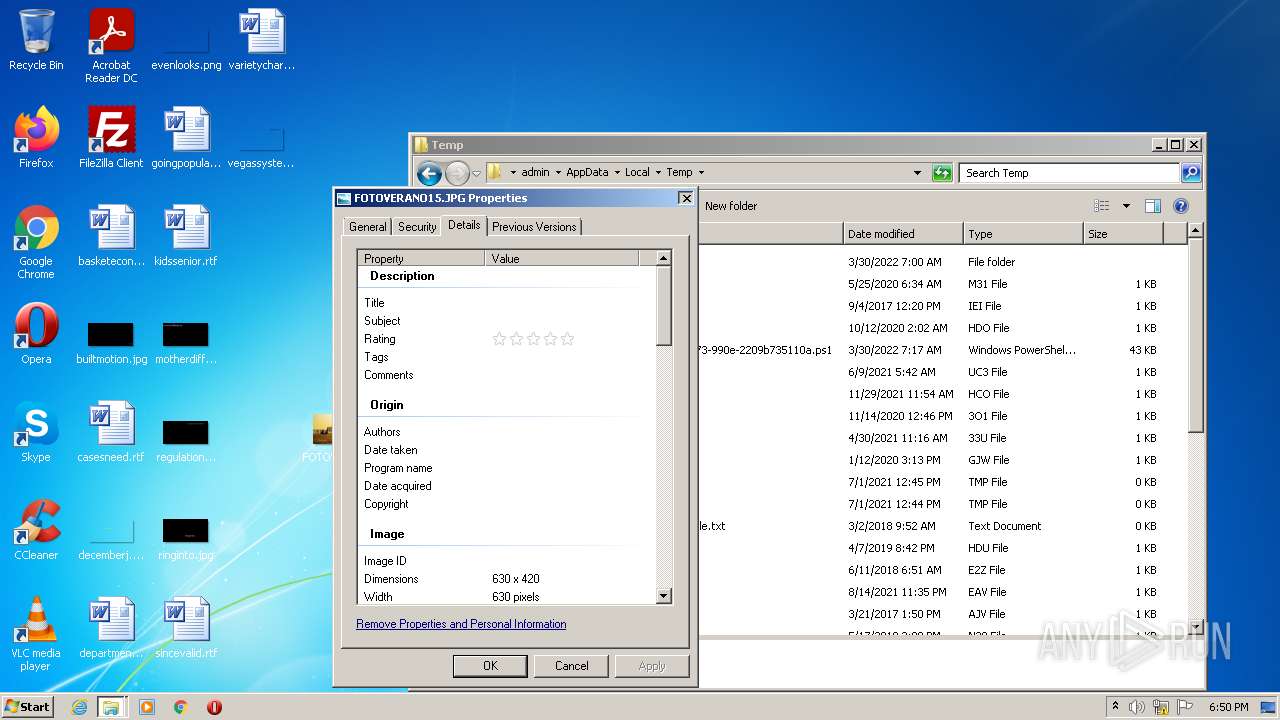
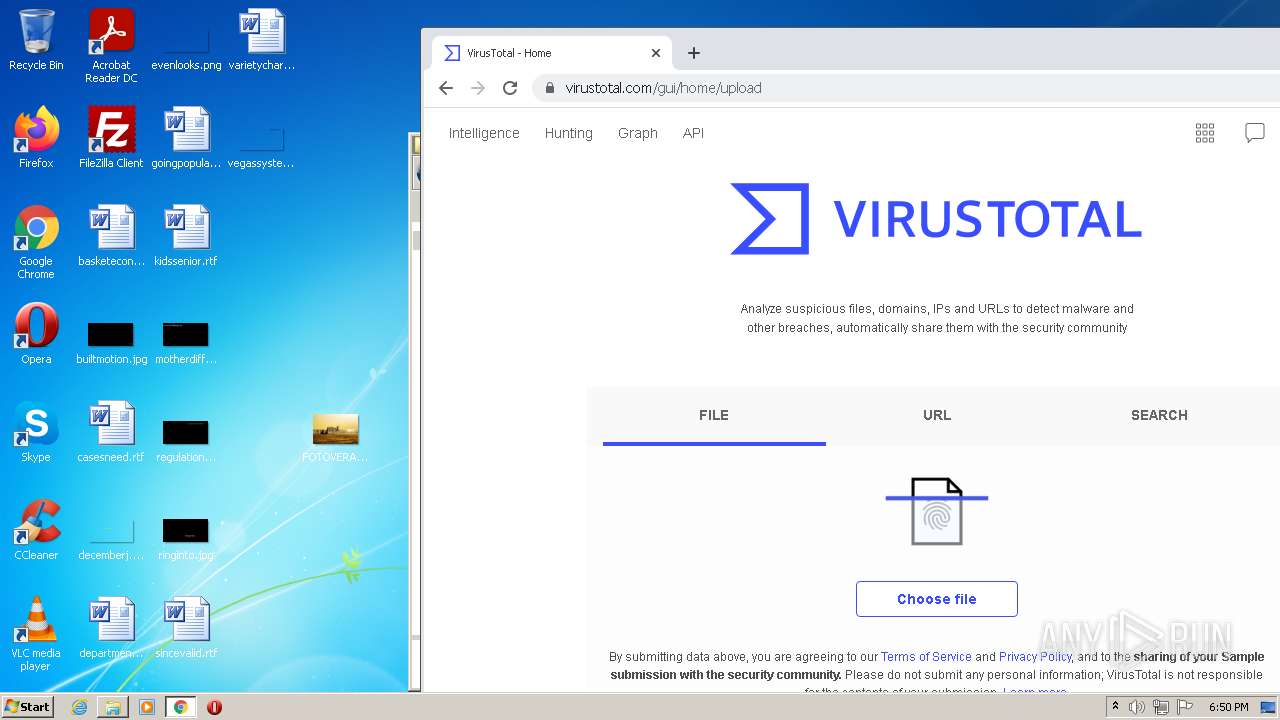
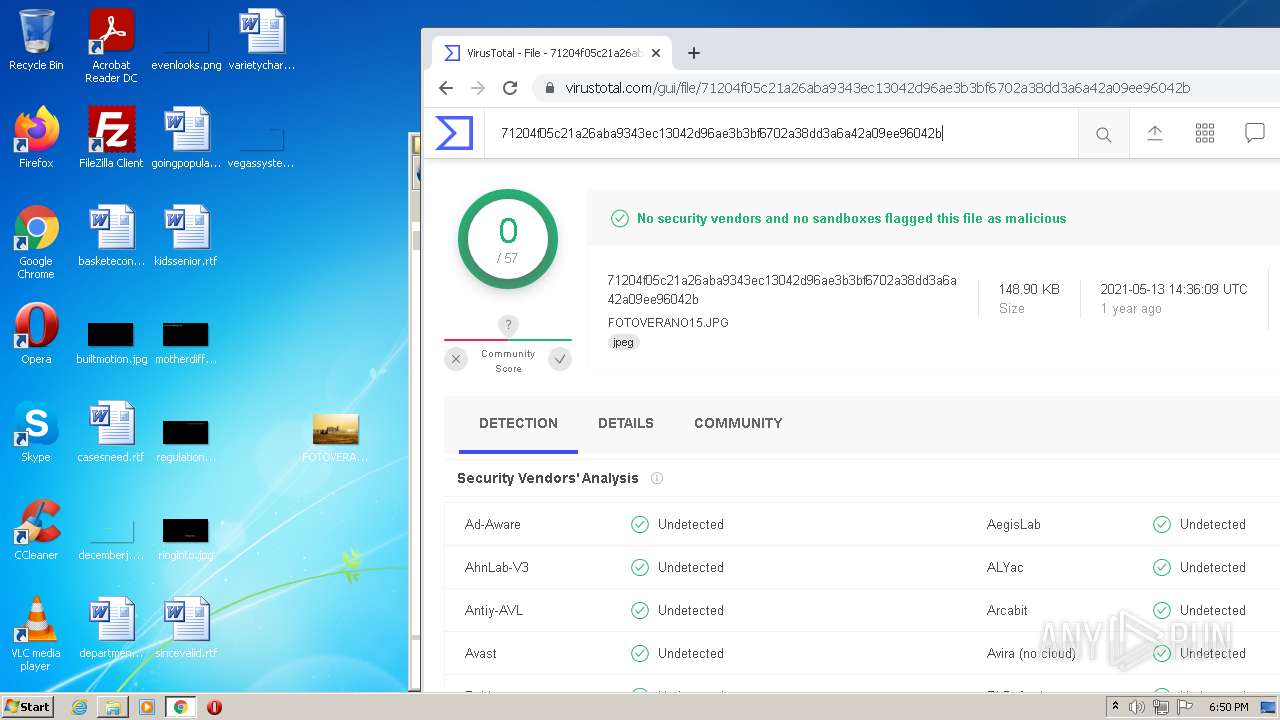
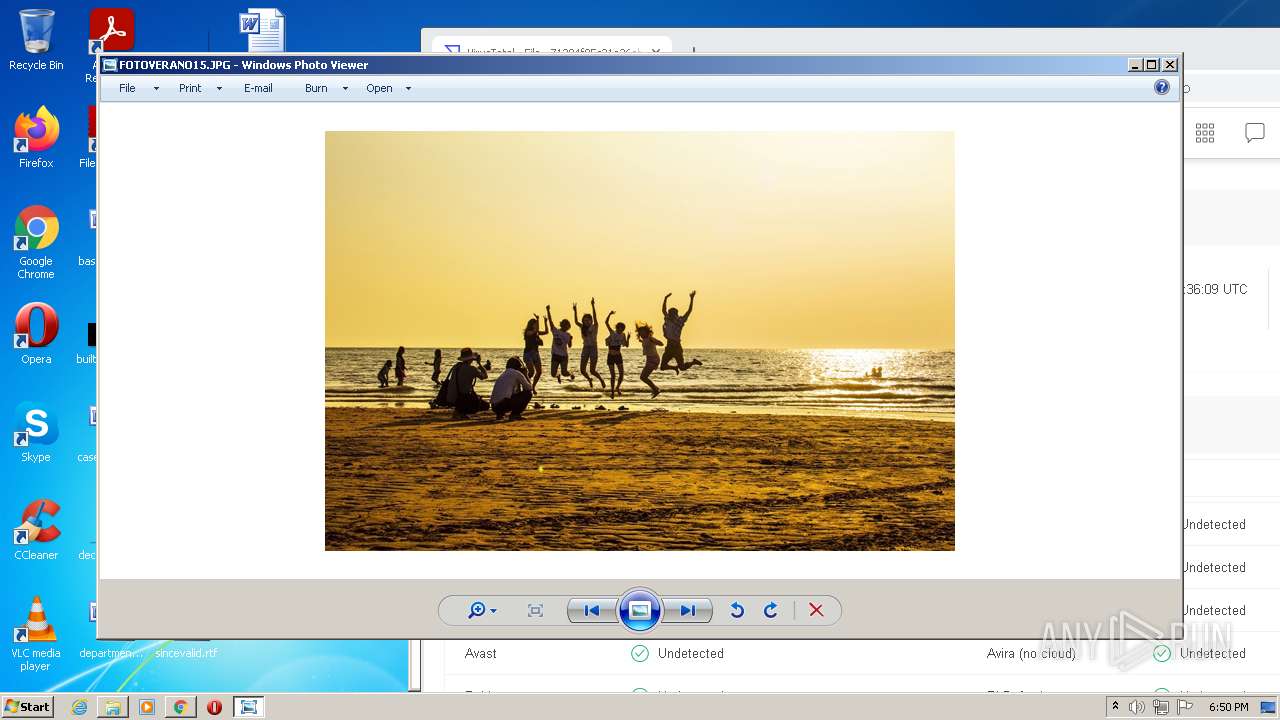
| File name: | FOTOVERANO15.scr |
| Full analysis: | https://app.any.run/tasks/44ae446e-265e-46ea-9c9d-0c766bf1e7c4 |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | May 20, 2022, 17:49:48 |
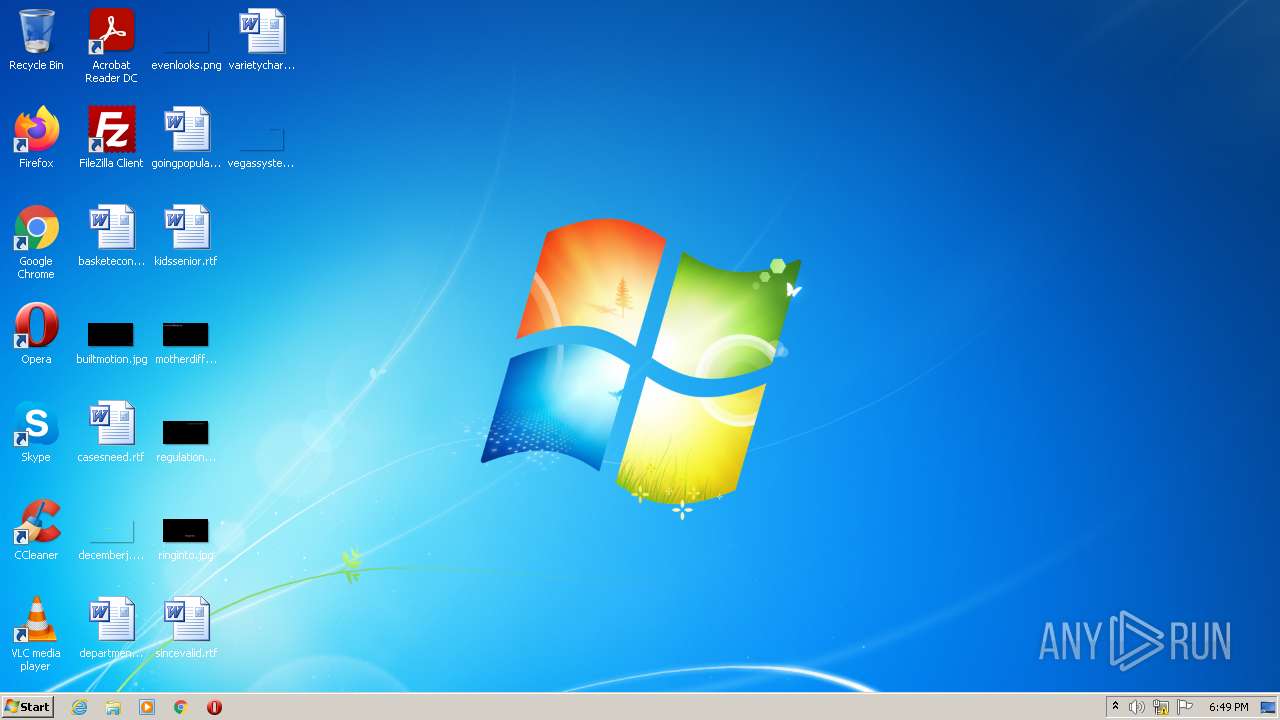
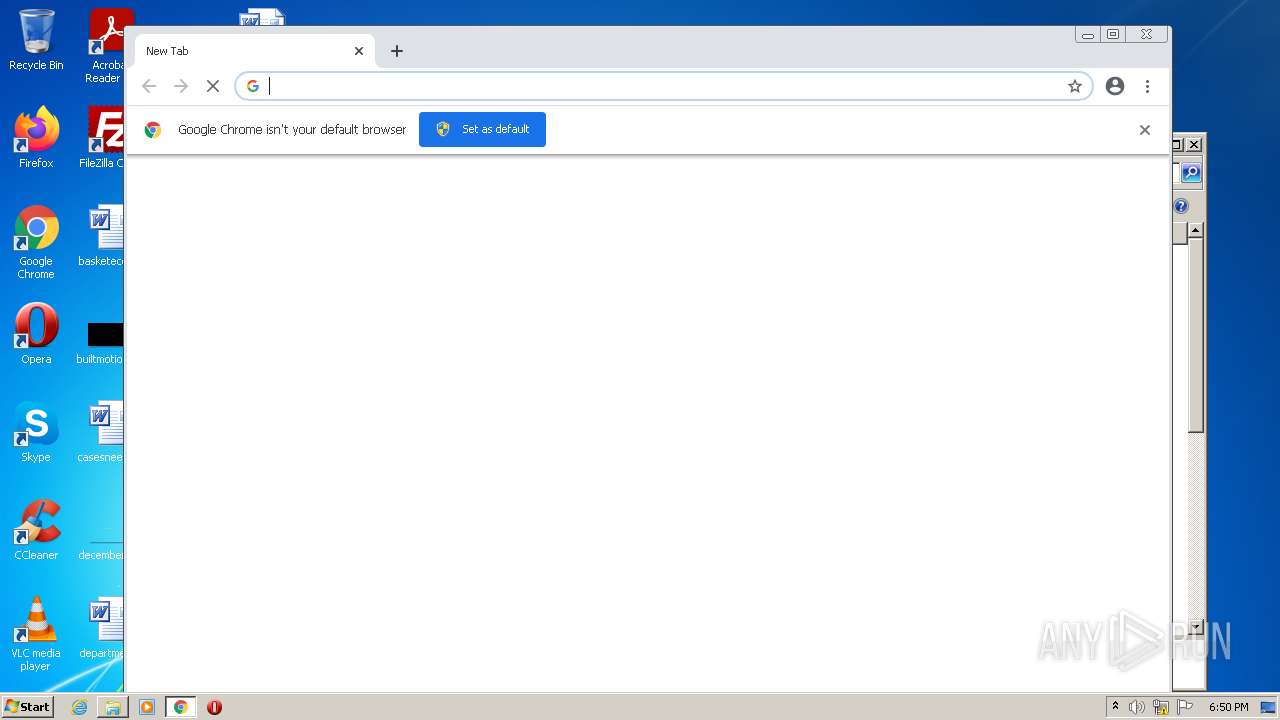
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EC692BDE91AD1C6E182843BC0A5C7E81 |
| SHA1: | 54996C1D4AEAF76855B7B73A323B74C191573863 |
| SHA256: | DE19D8EA2911FF7E337823576E214151AD4426206DB8E9EA9880778F2592F935 |
| SSDEEP: | 24576:aZ1xuVVjfFoynPaVBUR8f+kN10EBa10svzX:qQDgok30gW |
MALICIOUS
Drops executable file immediately after starts
- FOTOVERANO15.scr.exe (PID: 240)
Changes the autorun value in the registry
- iexplore.exe (PID: 3480)
- FOTOVERANO15.scr.exe (PID: 240)
- msdcsc.exe (PID: 1828)
Changes the login/logoff helper path in the registry
- FOTOVERANO15.scr.exe (PID: 240)
DARKCOMET detected by memory dumps
- iexplore.exe (PID: 3480)
SUSPICIOUS
Checks supported languages
- FOTOVERANO15.scr.exe (PID: 240)
- msdcsc.exe (PID: 1828)
Starts itself from another location
- FOTOVERANO15.scr.exe (PID: 240)
Executed via COM
- DllHost.exe (PID: 2360)
- DllHost.exe (PID: 2324)
Executable content was dropped or overwritten
- FOTOVERANO15.scr.exe (PID: 240)
Reads the computer name
- msdcsc.exe (PID: 1828)
- FOTOVERANO15.scr.exe (PID: 240)
Starts Internet Explorer
- msdcsc.exe (PID: 1828)
Drops a file with a compile date too recent
- FOTOVERANO15.scr.exe (PID: 240)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1828)
INFO
Checks supported languages
- DllHost.exe (PID: 2360)
- notepad.exe (PID: 2304)
- iexplore.exe (PID: 3480)
- notepad.exe (PID: 3800)
- verclsid.exe (PID: 3652)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 280)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 1036)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 3800)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3052)
- DllHost.exe (PID: 2324)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 1896)
Reads the computer name
- iexplore.exe (PID: 3480)
- DllHost.exe (PID: 2360)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 3052)
- DllHost.exe (PID: 2324)
- chrome.exe (PID: 2476)
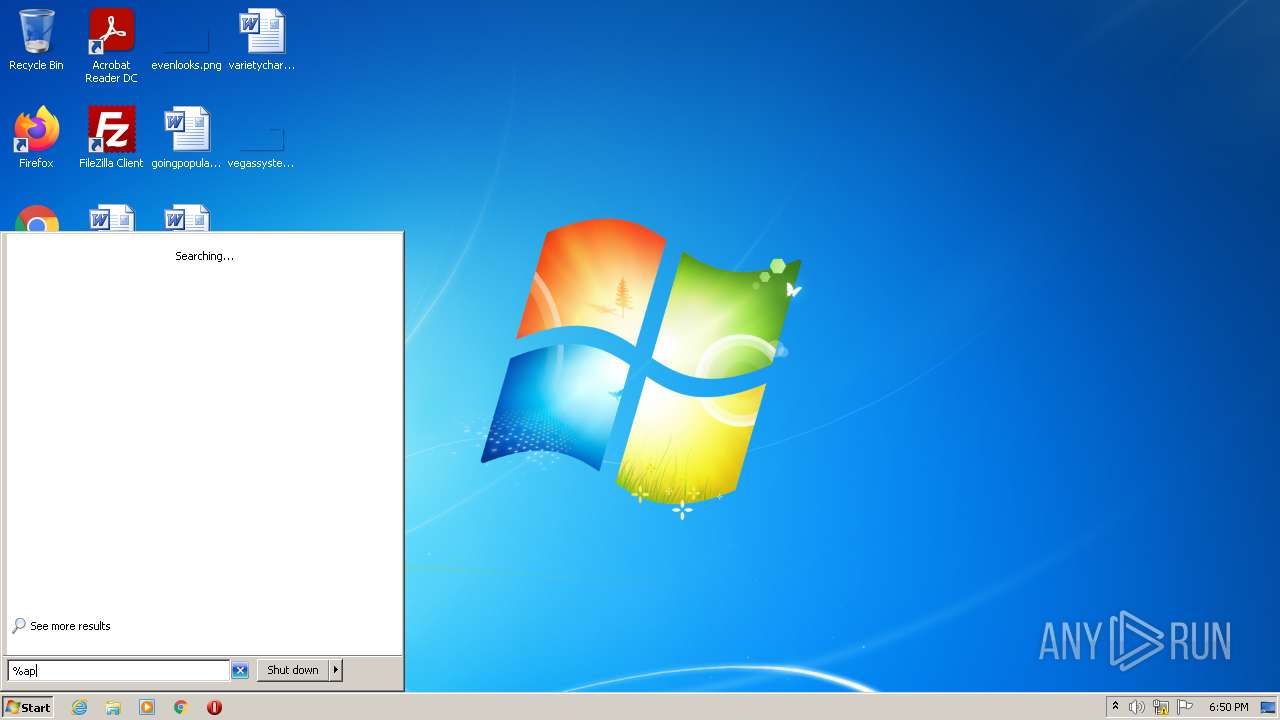
Manual execution by user
- verclsid.exe (PID: 3652)
- chrome.exe (PID: 1828)
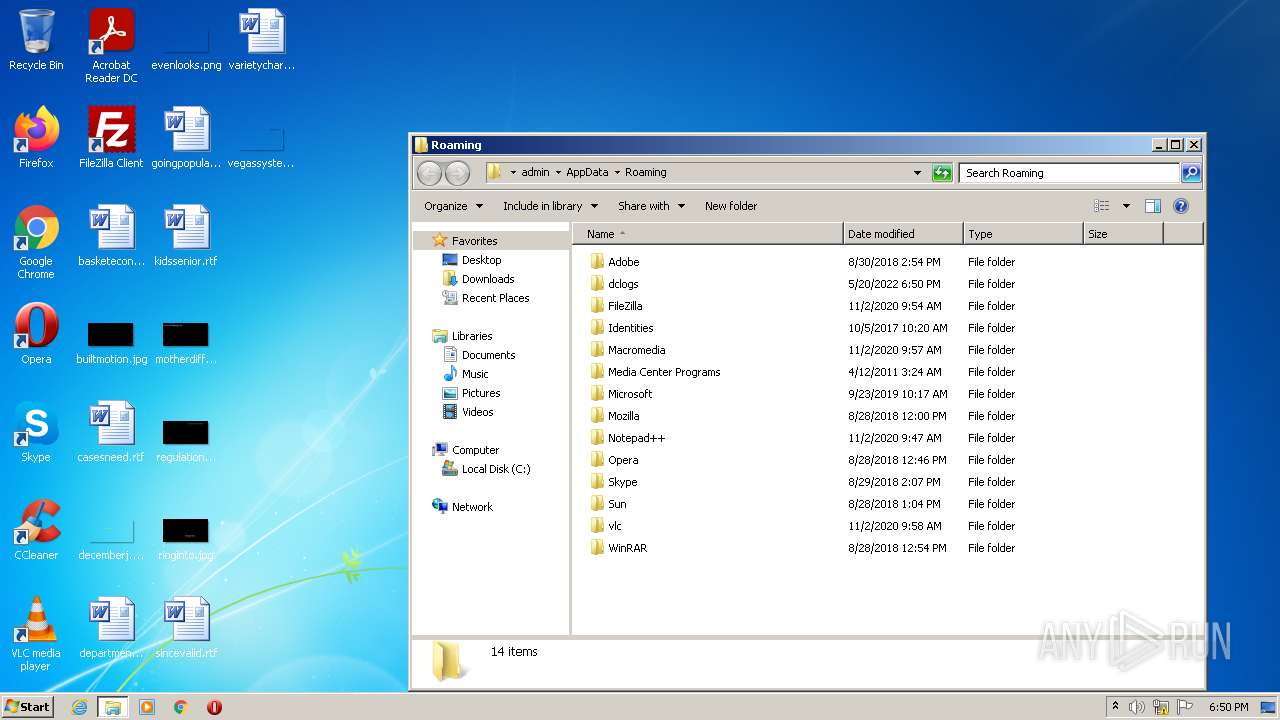
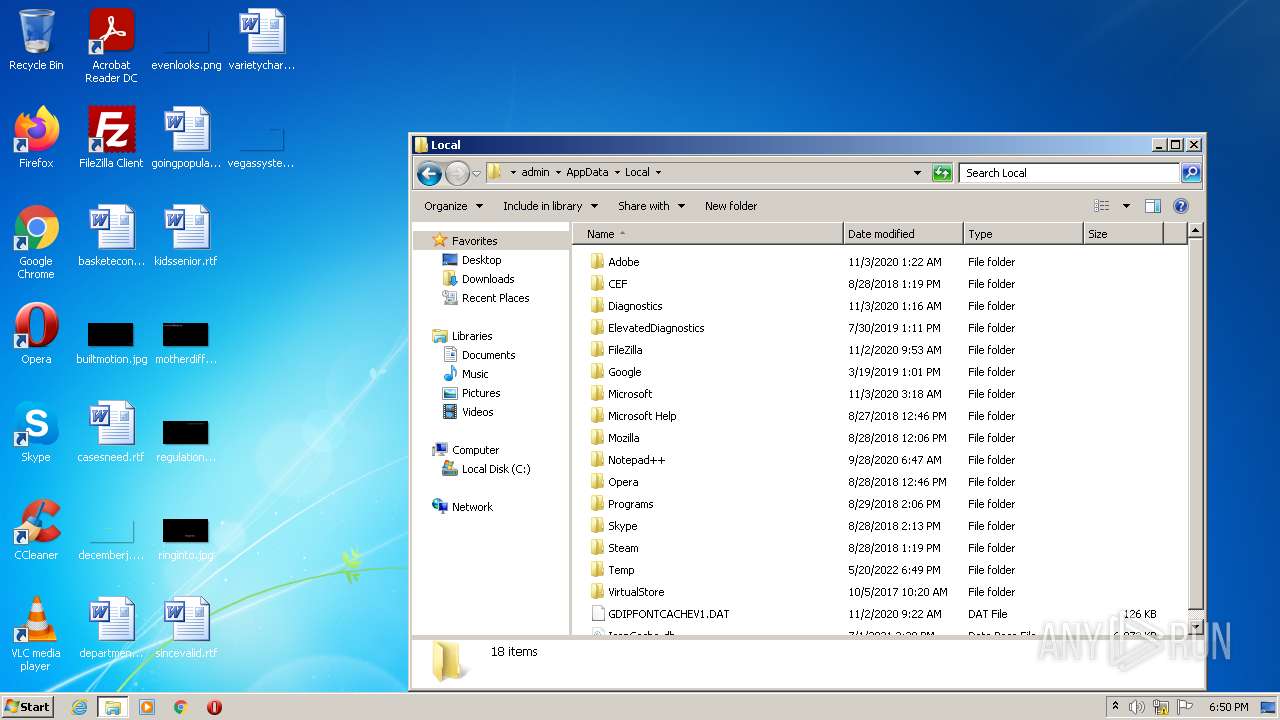
Creates files in the user directory
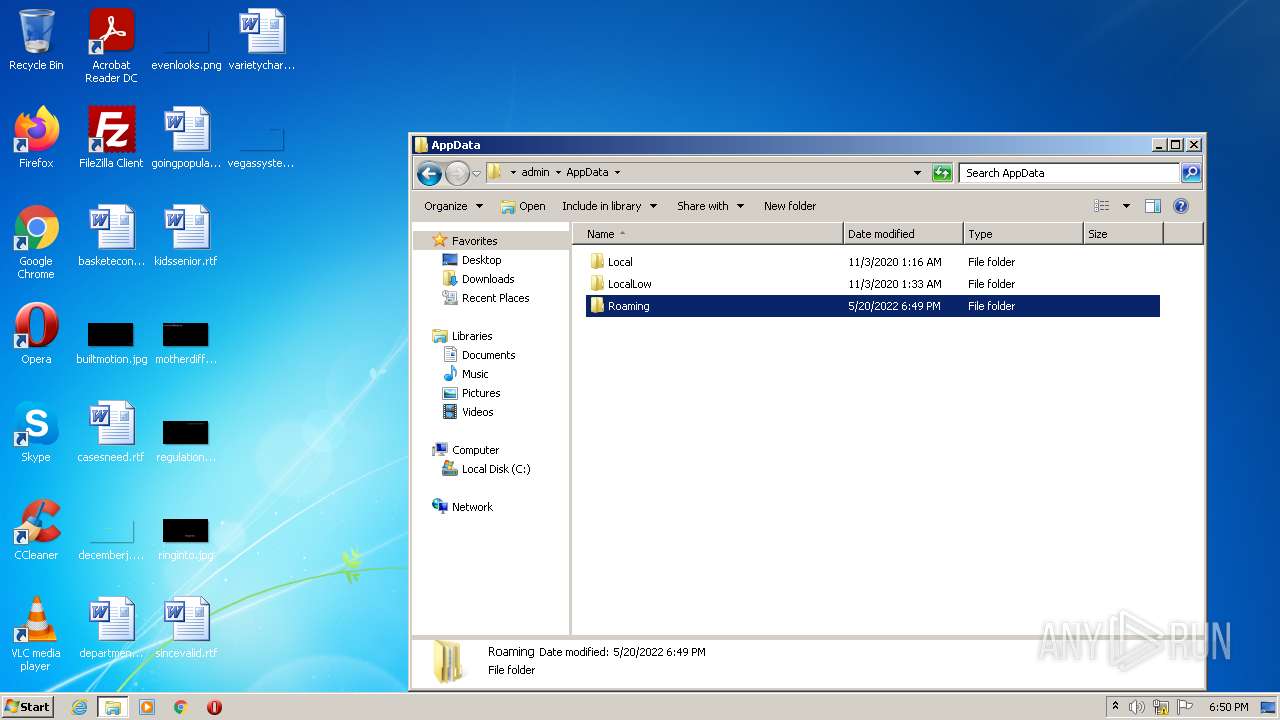
- iexplore.exe (PID: 3480)
Reads the hosts file
- chrome.exe (PID: 1828)
- chrome.exe (PID: 2772)
Application launched itself
- chrome.exe (PID: 1828)
Reads settings of System Certificates
- chrome.exe (PID: 2772)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DarkComet
(PID) Process(3480) iexplore.exe
C2 (1)seguridadsocial.ddns.net:1604
Version#KCMDDC51#
MutexDC_MUTEX-MKHPJPY
sidFOTOVERANO15
FWB1
gencodelsBsa7lPZ9Fu
InstallTrue
COMBOPATH7
Install pathMSDCSC\msdcsc.exe
Registry keyMicroUpdate
Edit date2007-04-16
PersistanceTrue
MELT1
Change Date1
Directory attributesFalse
File attrubutesFalse
SH51
SH61
PERS1
Offline keyloggerTrue
BIND1
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| ProductVersion: | 4, 0, 0, 0 |
|---|---|
| ProductName: | Remote Service Application |
| OriginalFileName: | MSRSAAP.EXE |
| LegalCopyright: | Copyright (C) 1999 |
| InternalName: | MSRSAAPP |
| FileVersion: | 1, 0, 0, 1 |
| FileDescription: | Remote Service Application |
| CompanyName: | Microsoft Corp. |
| Comments: | Remote Service Application |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.0.0.0 |
| FileVersionNumber: | 4.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x8f888 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 307200 |
| CodeSize: | 586752 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2012:06:07 17:59:53+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jun-2012 15:59:53 |
| Detected languages: |
|
| Comments: | Remote Service Application |
| CompanyName: | Microsoft Corp. |
| FileDescription: | Remote Service Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | MSRSAAPP |
| LegalCopyright: | Copyright (C) 1999 |
| OriginalFilename: | MSRSAAP.EXE |
| ProductName: | Remote Service Application |
| ProductVersion: | 4, 0, 0, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 07-Jun-2012 15:59:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008D8F0 | 0x0008DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55342 |
.itext | 0x0008F000 | 0x00001954 | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95375 |
.data | 0x00091000 | 0x00003D3C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.83487 |
.bss | 0x00095000 | 0x00007404 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0009D000 | 0x00004140 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.26814 |
.tls | 0x000A2000 | 0x00000038 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000A3000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x000A4000 | 0x00008ADC | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72501 |
.rsrc | 0x000AD000 | 0x0003A01C | 0x0003A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.40206 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34616 | 856 | Latin 1 / Western European | French - France | RT_VERSION |
2 | 2.80231 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
50 | 5.50662 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
128 | 2.16096 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
4083 | 3.16951 | 524 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
AVICAP32.DLL |
SHELL32.DLL |
SHFolder.dll |
URLMON.DLL |
WS2_32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
gdiplus.dll |
kernel32.dll |
Total processes
70
Monitored processes
34
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Users\admin\AppData\Local\Temp\FOTOVERANO15.scr.exe" | C:\Users\admin\AppData\Local\Temp\FOTOVERANO15.scr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,2602247931059493679,8735685933768009181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,2602247931059493679,8735685933768009181,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6cf5d988,0x6cf5d998,0x6cf5d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,2602247931059493679,8735685933768009181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | FOTOVERANO15.scr.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,2602247931059493679,8735685933768009181,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,2602247931059493679,8735685933768009181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3288 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2304 | notepad | C:\Windows\system32\notepad.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 630
Read events
7 557
Write events
73
Delete events
0
Modification events
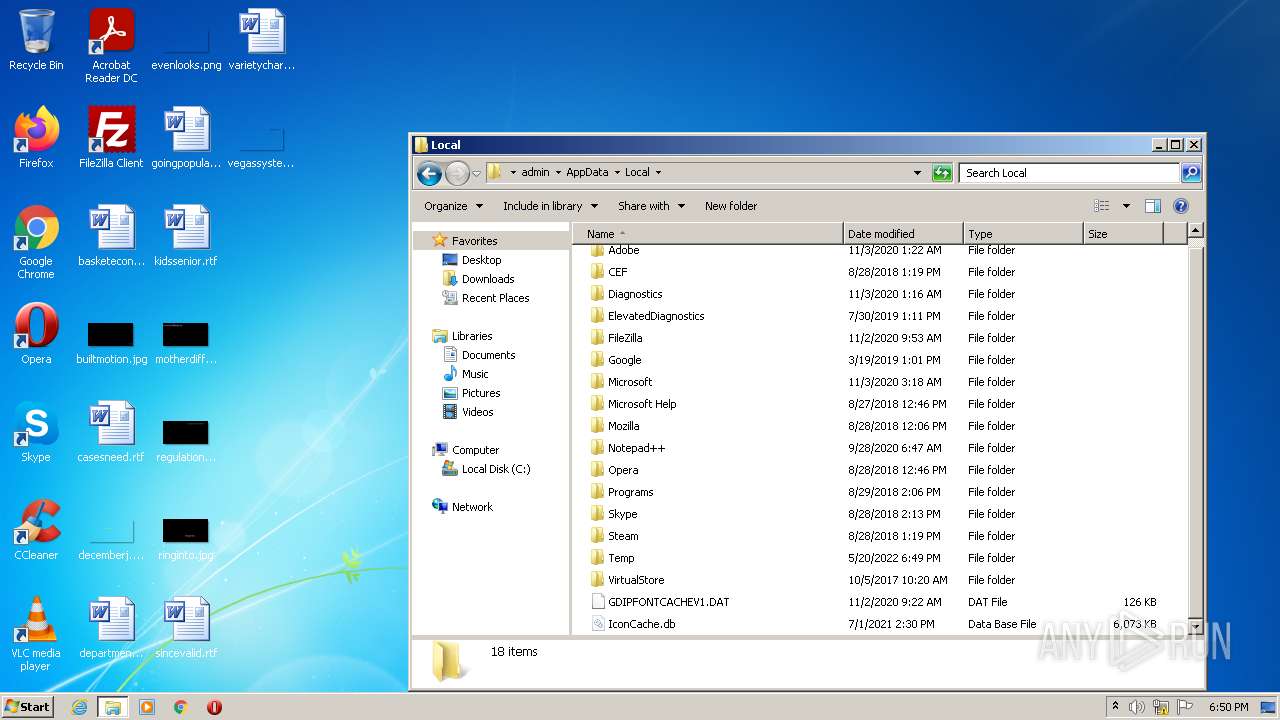
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
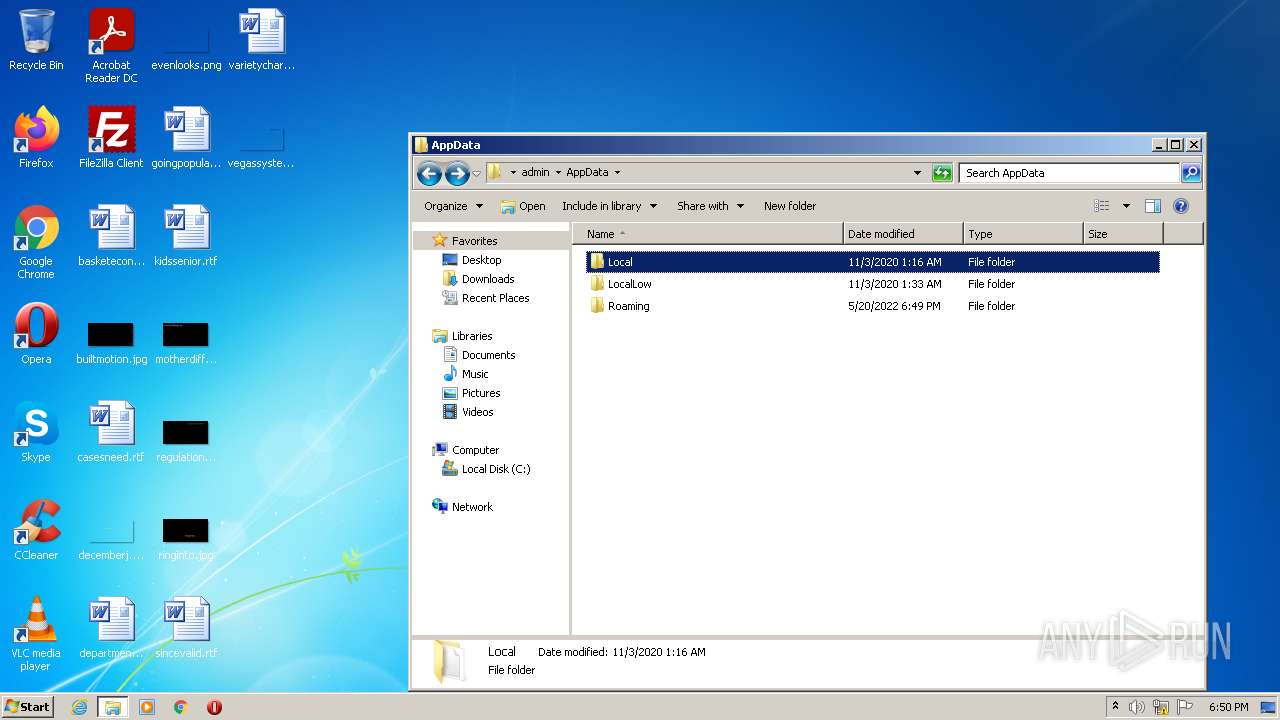
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000002EE9A502726CD801 | |||
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: FOTOVERANO15.scr.exe | |||
| (PID) Process: | (2360) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (240) FOTOVERANO15.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1828) msdcsc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
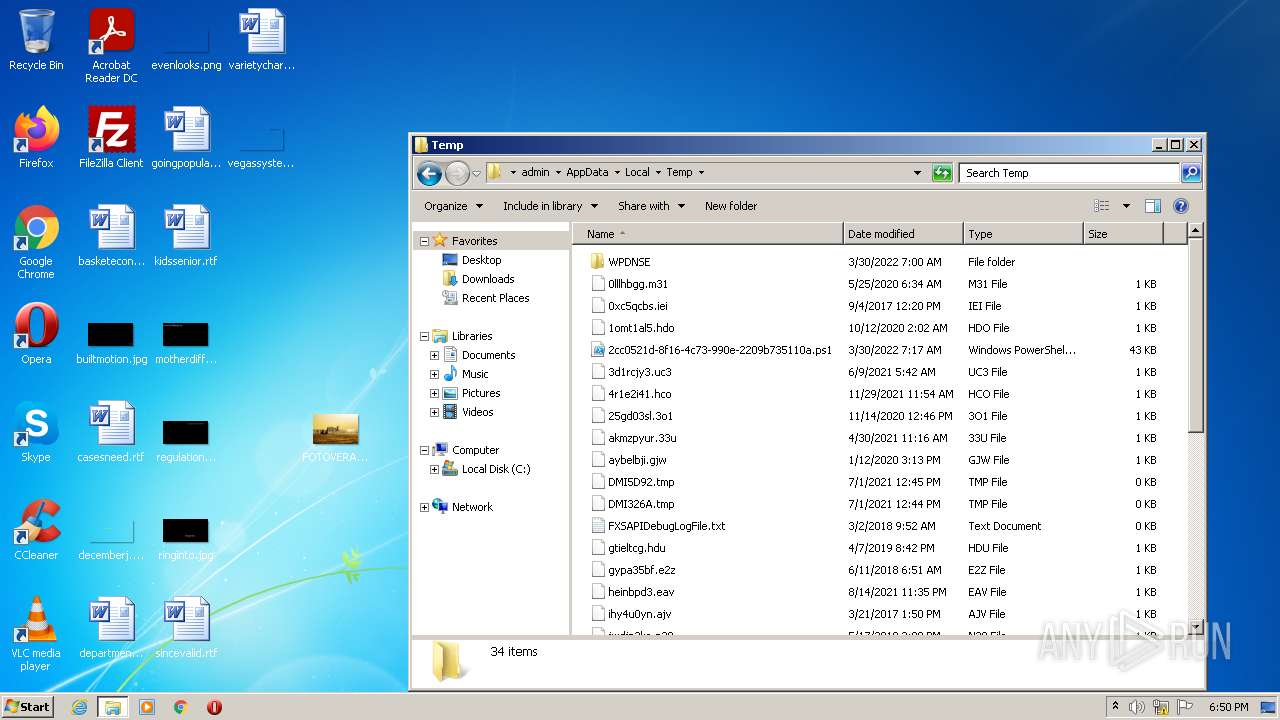
Executable files
1
Suspicious files
152
Text files
76
Unknown types
6
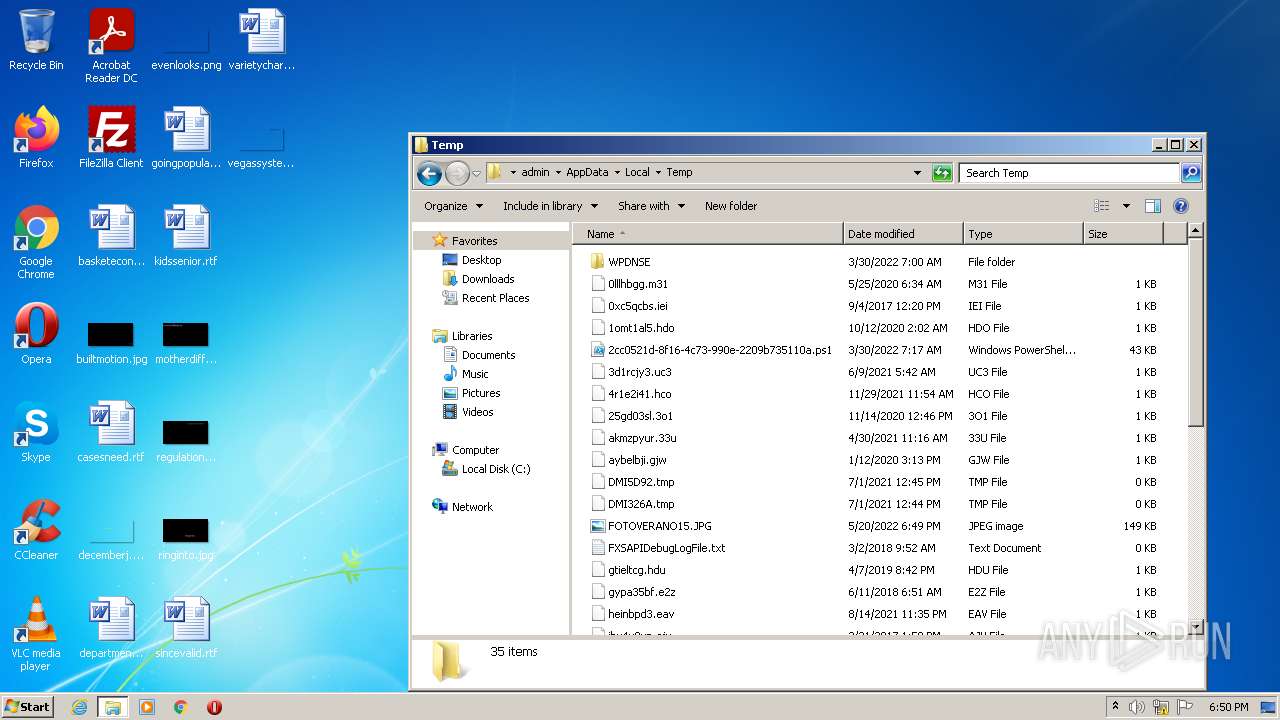
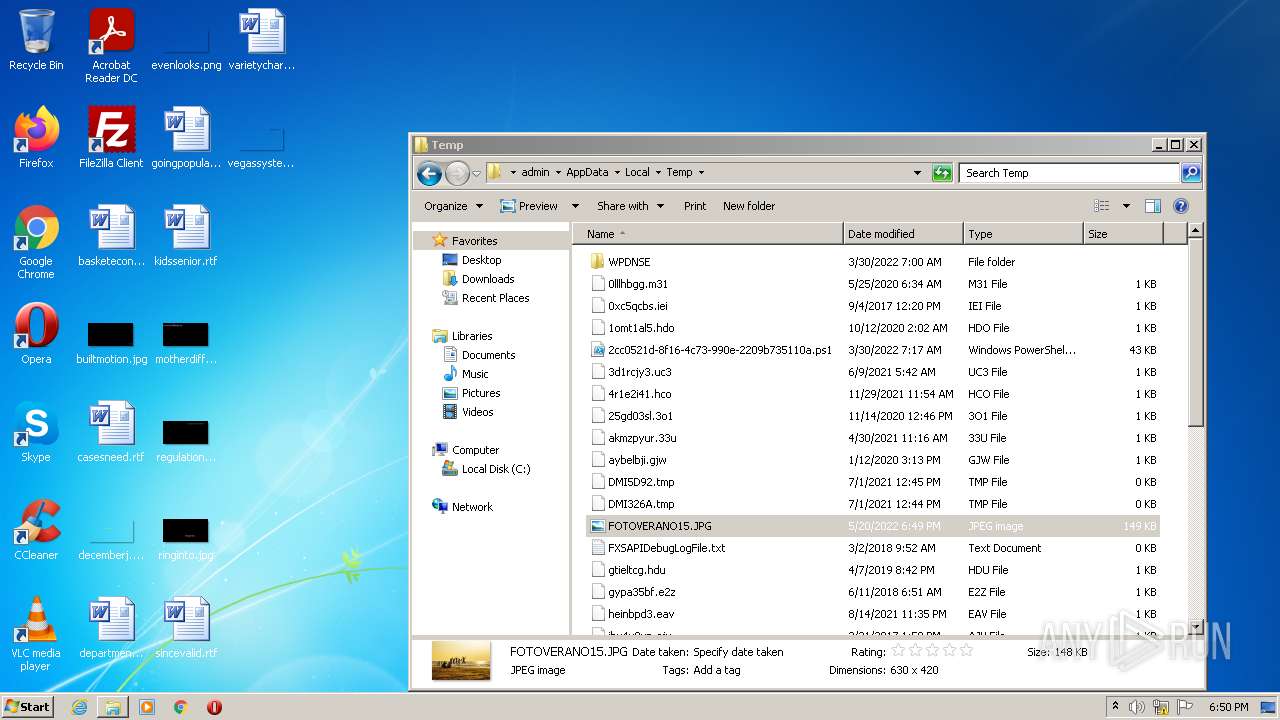
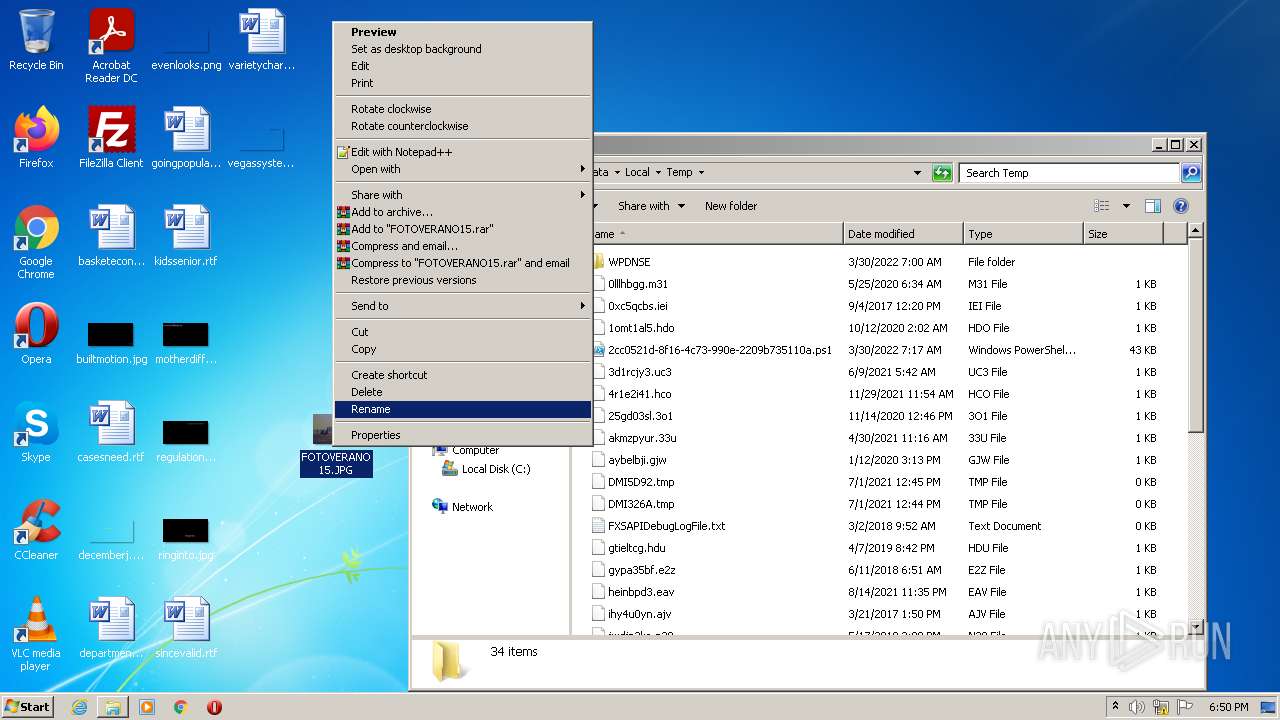
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287D4E7-724.pma | — | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Roaming\dclogs\2022-05-20-6.dc | text | |
MD5:— | SHA256:— | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\df997760-a975-4480-b254-8ef08e56e13c.tmp | text | |
MD5:— | SHA256:— | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 240 | FOTOVERANO15.scr.exe | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | executable | |
MD5:EC692BDE91AD1C6E182843BC0A5C7E81 | SHA256:DE19D8EA2911FF7E337823576E214151AD4426206DB8E9EA9880778F2592F935 | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1128c2.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1129eb.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
42
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
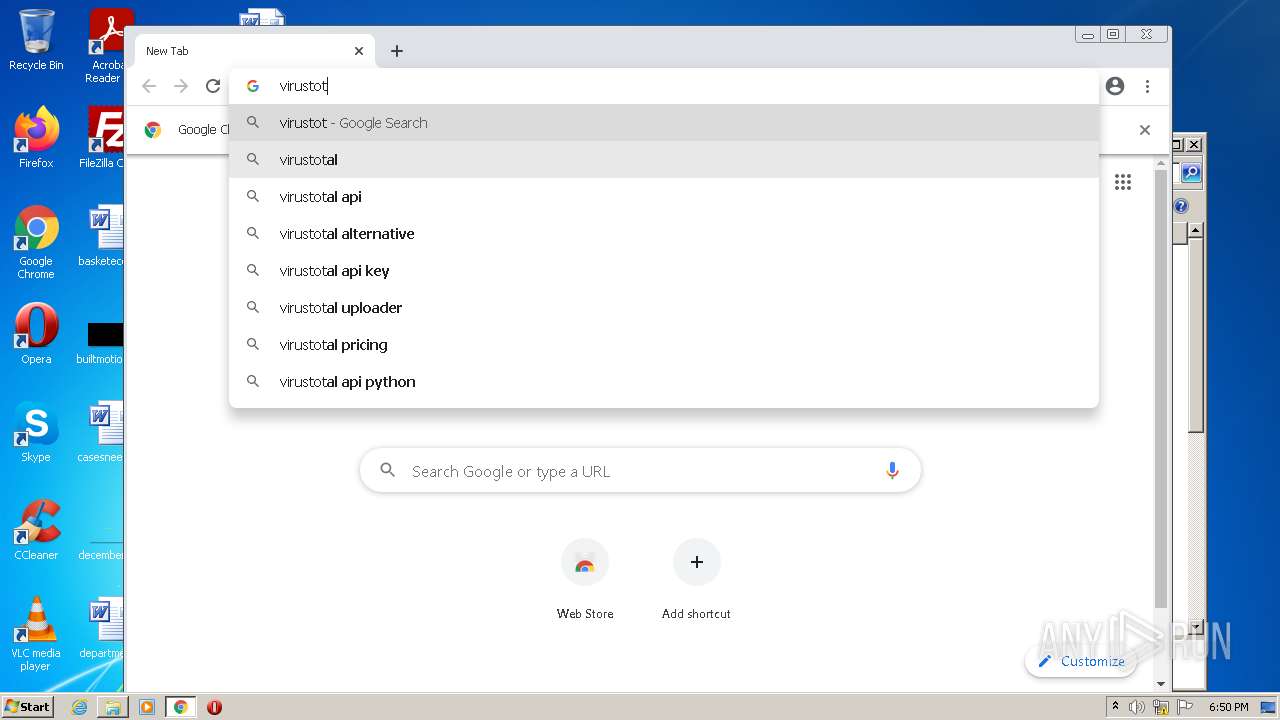
2772 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2772 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | iexplore.exe | 195.77.152.5:1604 | seguridadsocial.ddns.net | Telefonica De Espana | ES | unknown |
2772 | chrome.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 195.77.152.5:1604 | seguridadsocial.ddns.net | Telefonica De Espana | ES | unknown |
2772 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2772 | chrome.exe | 142.250.186.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 142.250.186.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 142.250.185.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 216.239.32.21:80 | virustotal.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seguridadsocial.ddns.net |
| malicious |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |