| URL: | https://pdfupload.io/docs/c10821c5 |
| Full analysis: | https://app.any.run/tasks/879941c3-4b00-4996-8b10-316846e7b234 |
| Verdict: | Malicious activity |
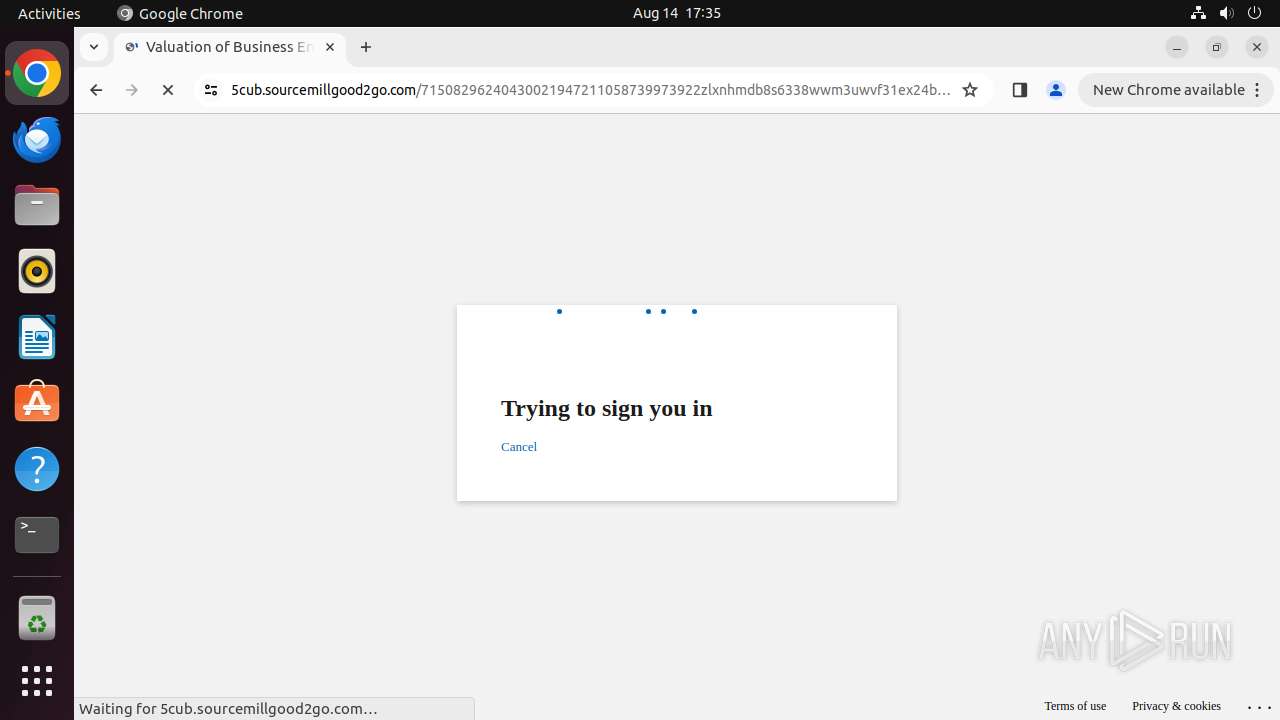
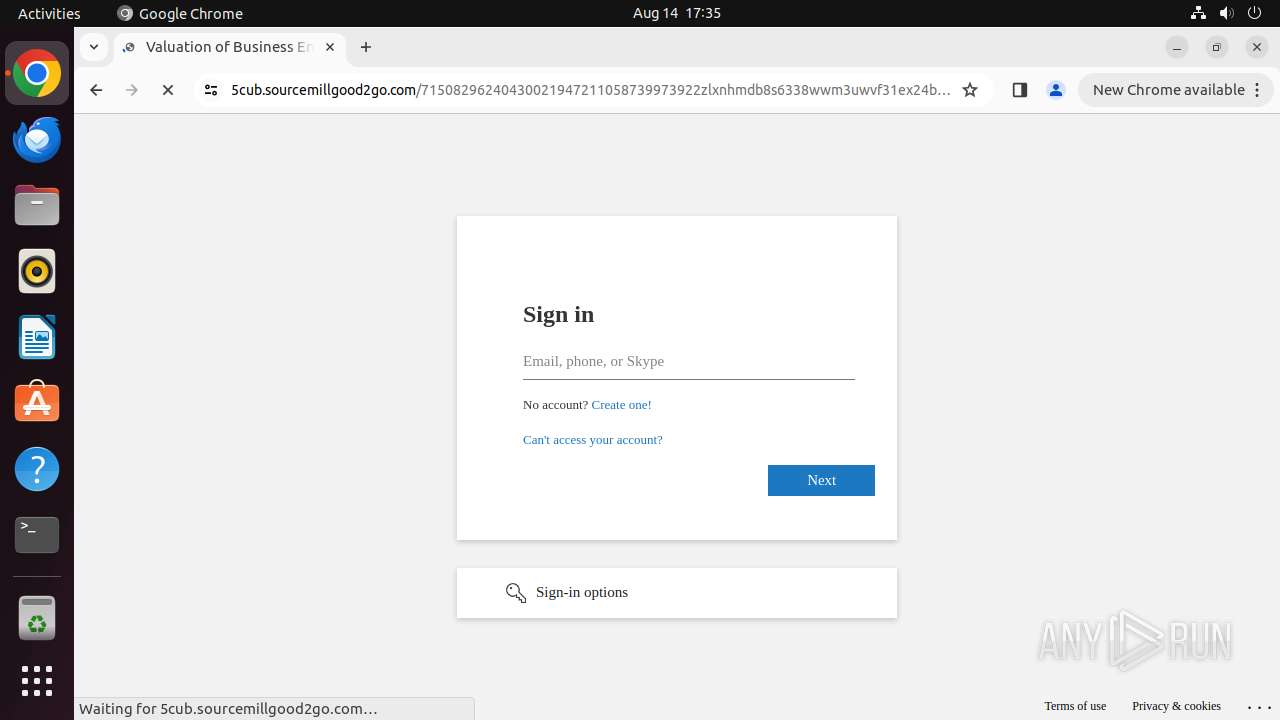
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | August 14, 2024, 16:34:48 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 257824765AD2645F108E7ACAB06AA1A8 |
| SHA1: | 89D6769587152D393C986D9D19DCD8E0098B45A1 |
| SHA256: | DE093977BD7A283514EE0B37E78419125308AB6046723D9B87ADEFAFC9D07EC4 |
| SSDEEP: | 3:N8FMjwEMVUGQn:2jEM5Q |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 425)
SUSPICIOUS
Executes commands using command-line interpreter
- update-notifier (PID: 13302)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13304)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
321
Monitored processes
109
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 425 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 12930 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://pdfupload\.io/docs/c10821c5 " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12931 | sudo -iu user google-chrome https://pdfupload.io/docs/c10821c5 | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12932 | /usr/bin/google-chrome https://pdfupload.io/docs/c10821c5 | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12933 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12934 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12935 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12936 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12937 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12938 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
1
Suspicious files
186
Text files
38
Unknown types
168
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12932 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12932 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13075 | chrome | /home/user/.cache/mesa_shader_cache/index | koa | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
65
DNS requests
77
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.17:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acu4ycdzikqvldkjno6ksqtjzt5a_9030/hfnkpimlhhgieaddgfemjhofmfblmnib_9030_all_m7fsjuj7f45cqnobg5msqhypoa.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/myyvyry7kskkpb7gzyvhfrkohm_1044/efniojlnjndmcbiieegkicadnoecjjef_1044_all_adx4v7kqqvkdbmpqe5sgerij3y7a.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.1994e34393325afdff0c90ac370065028be66ba9f7c8991b0cf425a0ae494611/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/2cd022aaefa46340fa30bfa48c6cdb4f6d5d0b3e8bd5e5d4c990531b9964bf32 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnlb63r4ejlzzg47leq44ofux7a_2024.8.13.1/jflhchccmppkfebkiaminageehmchikm_2024.08.13.01_all_bcl3rsba4wuw3pqnrn4mgxr3uq.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/e6xlmsu5i2bokri3w4cyuhv4nq_2024.8.10.0/gonpemdgkjcecdgbnaabipppbmgfggbe_2024.08.10.00_all_ngbcdbf23y5deox6qfrqcyni5e.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/advy5jo626rsoyhmpt3vxe2fwamq_2024.8.14.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.08.14.01_all_he6tjokbqldqyde6usssa2t37y.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 185.125.190.17:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 138.199.37.38:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
— | — | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
— | — | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
12932 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 66.241.124.20:443 | pdfupload.io | FLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
pdfupload.io |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
cdn.pdfupload.io |
| unknown |
files.pdfupload.io |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
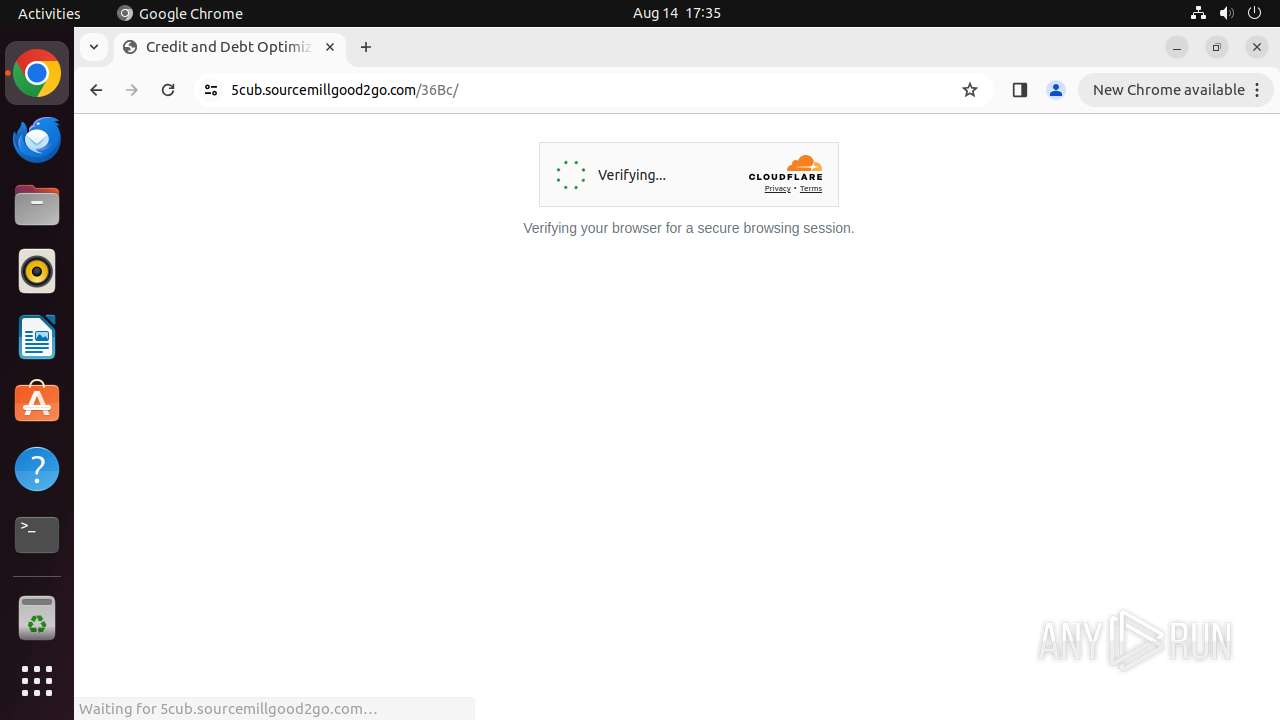
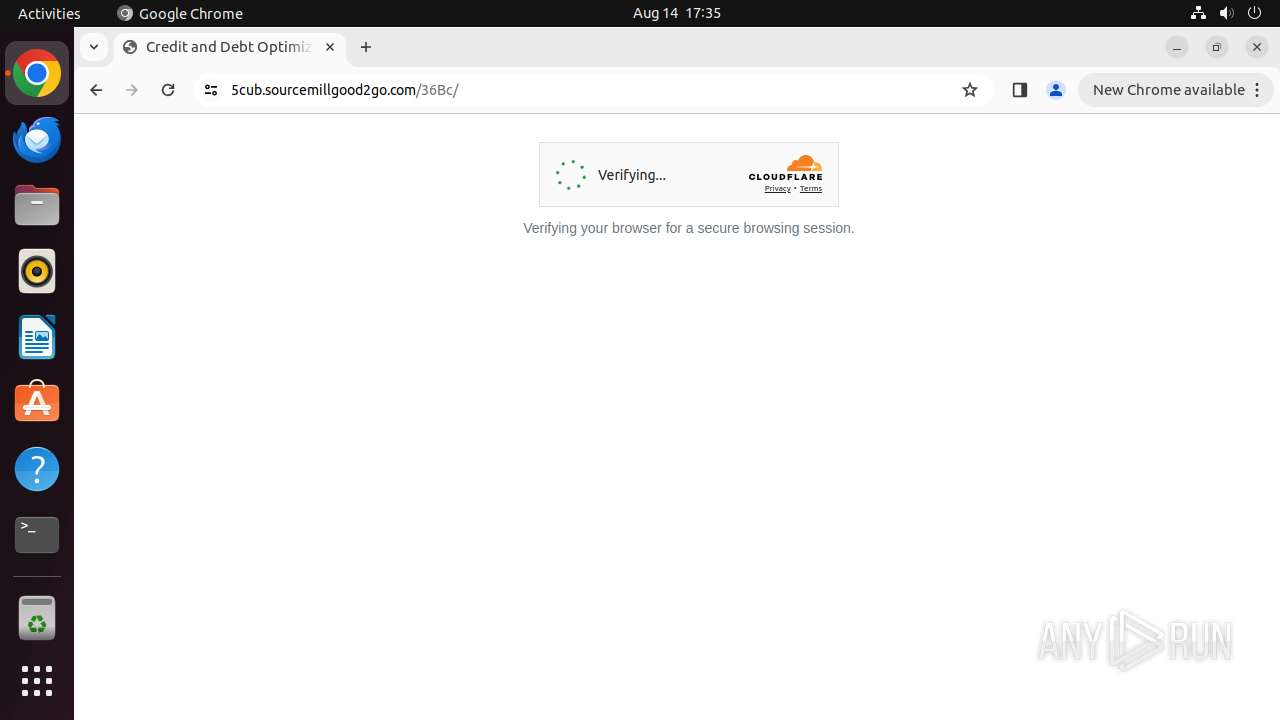
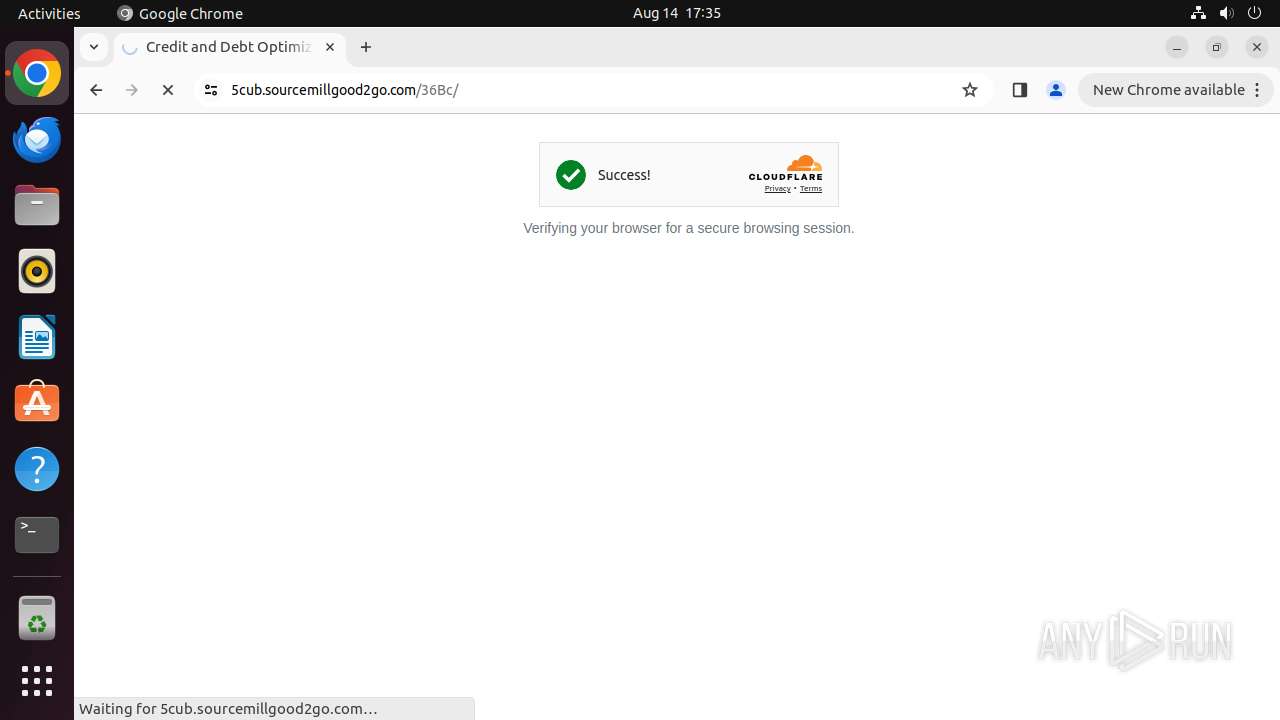
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
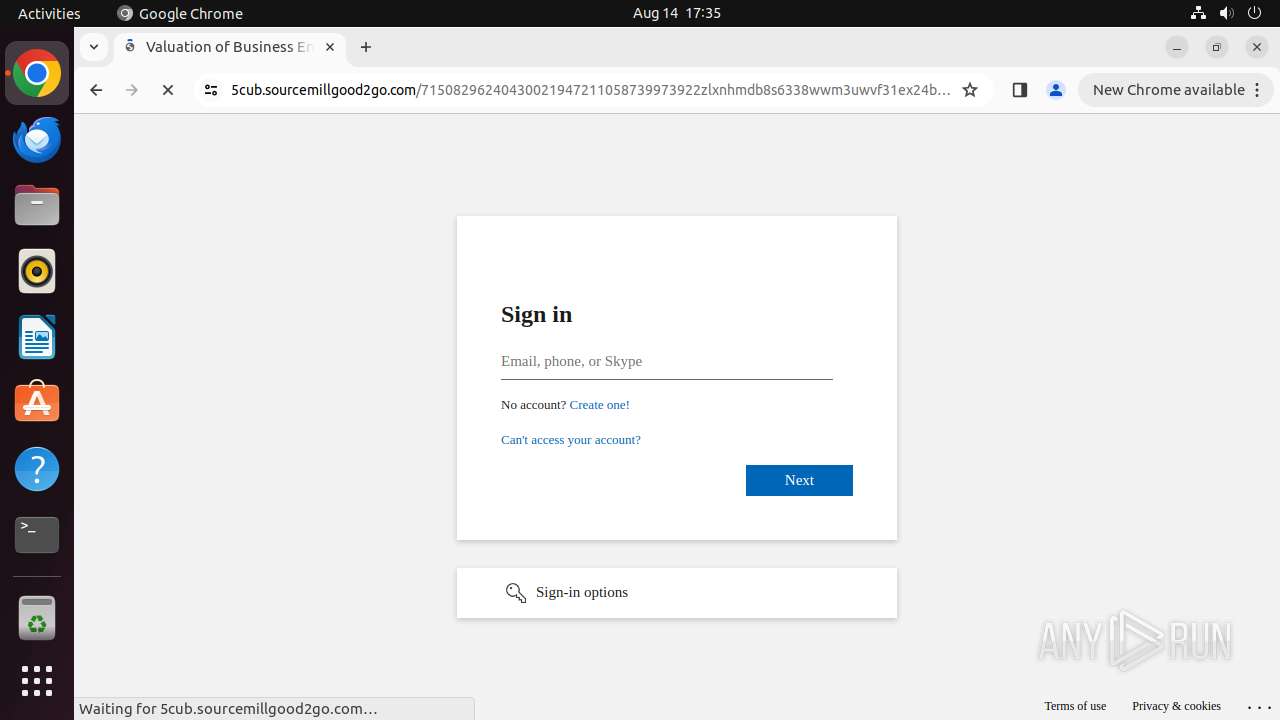
425 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (challengezone) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
425 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (challengezone) |