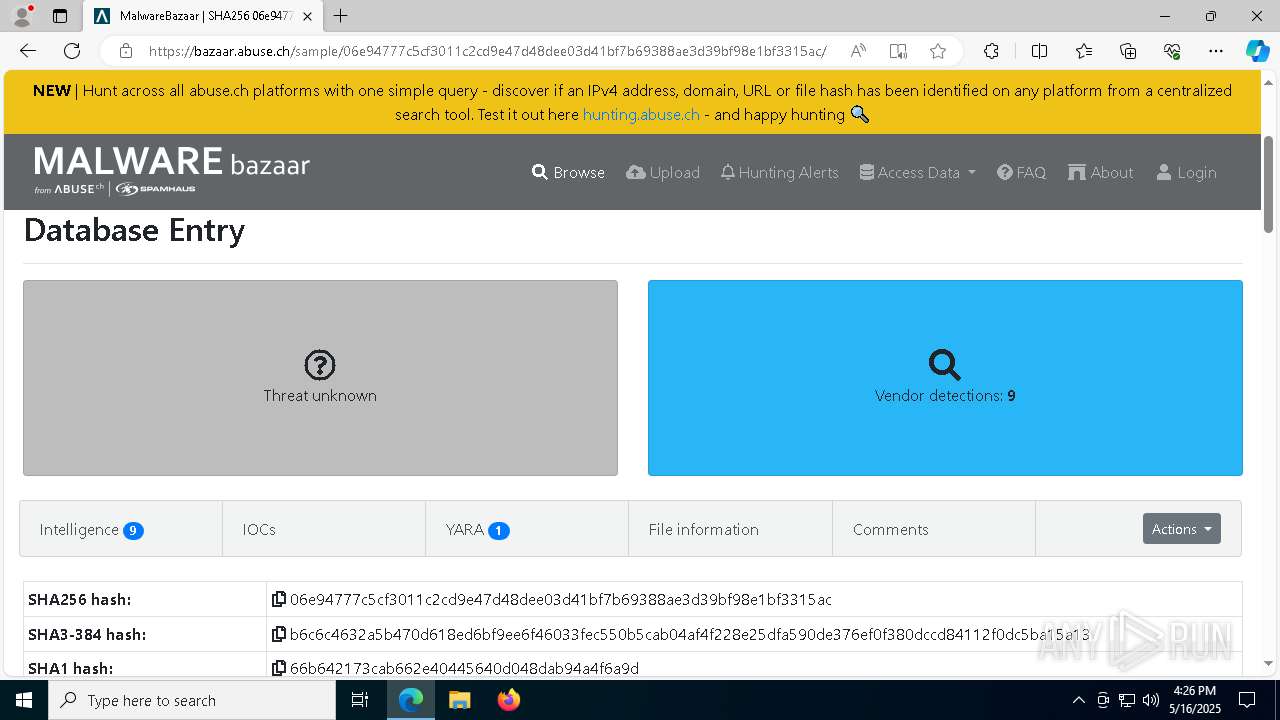
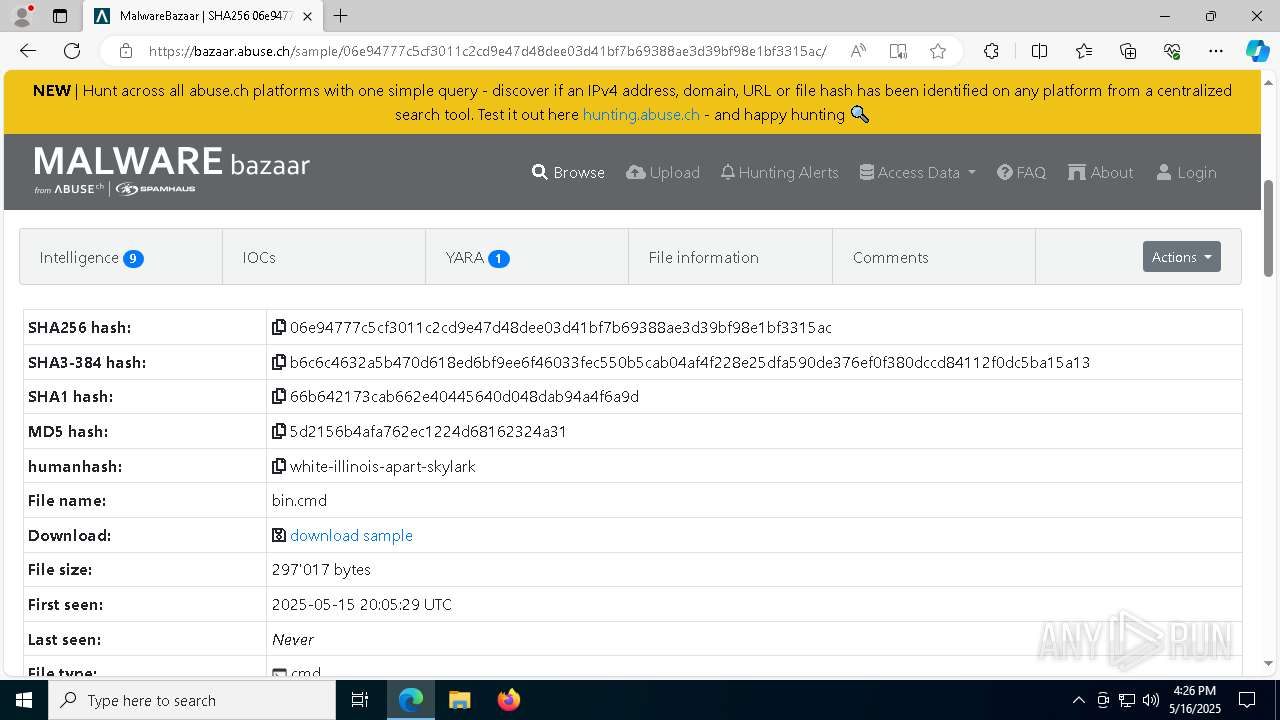
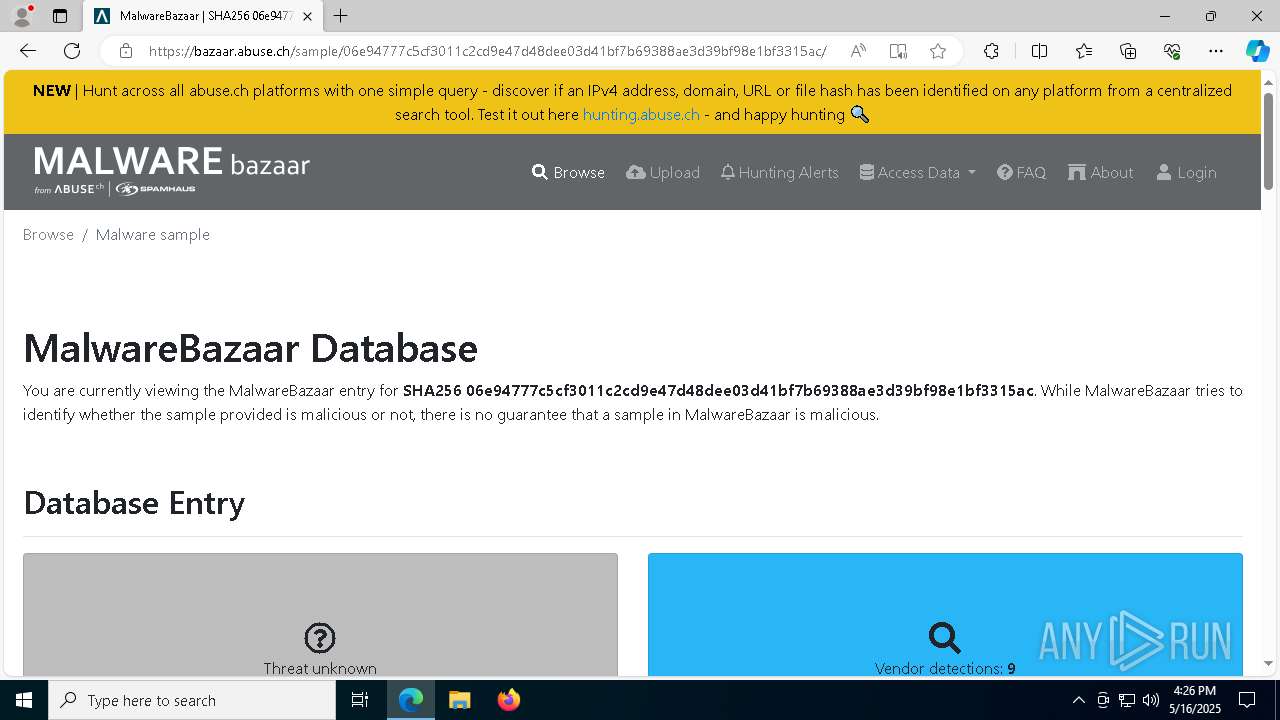
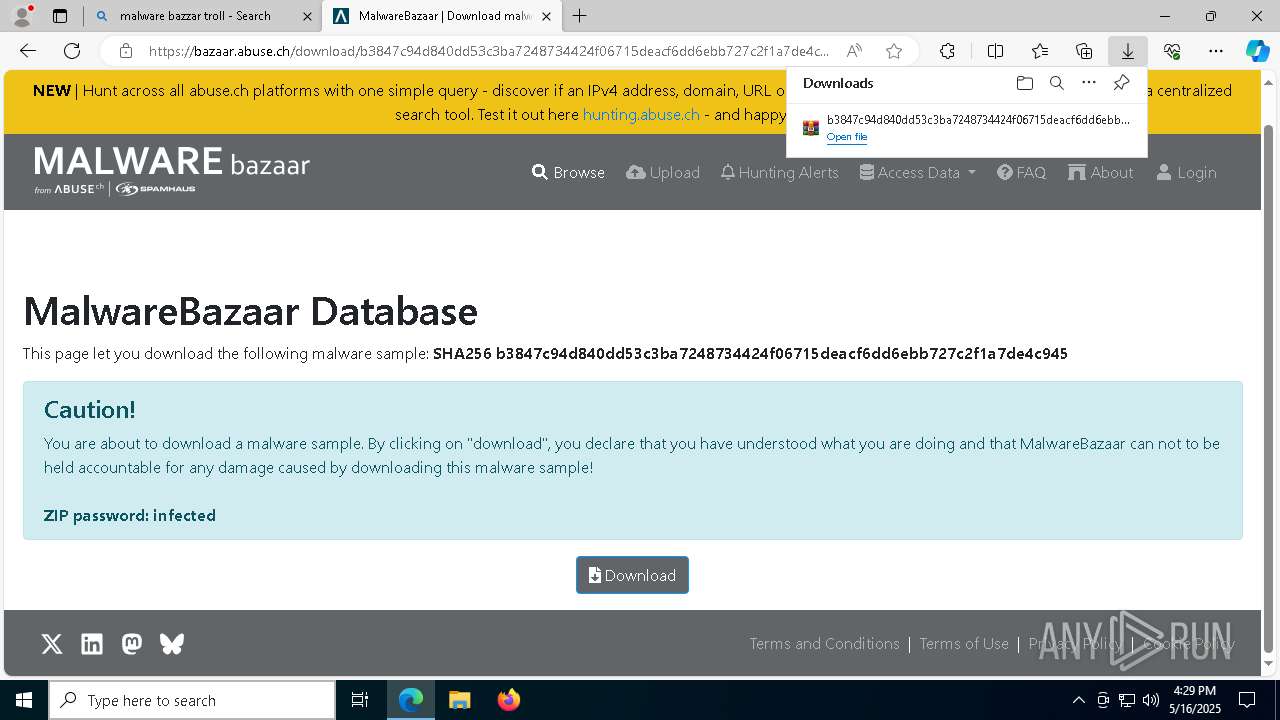
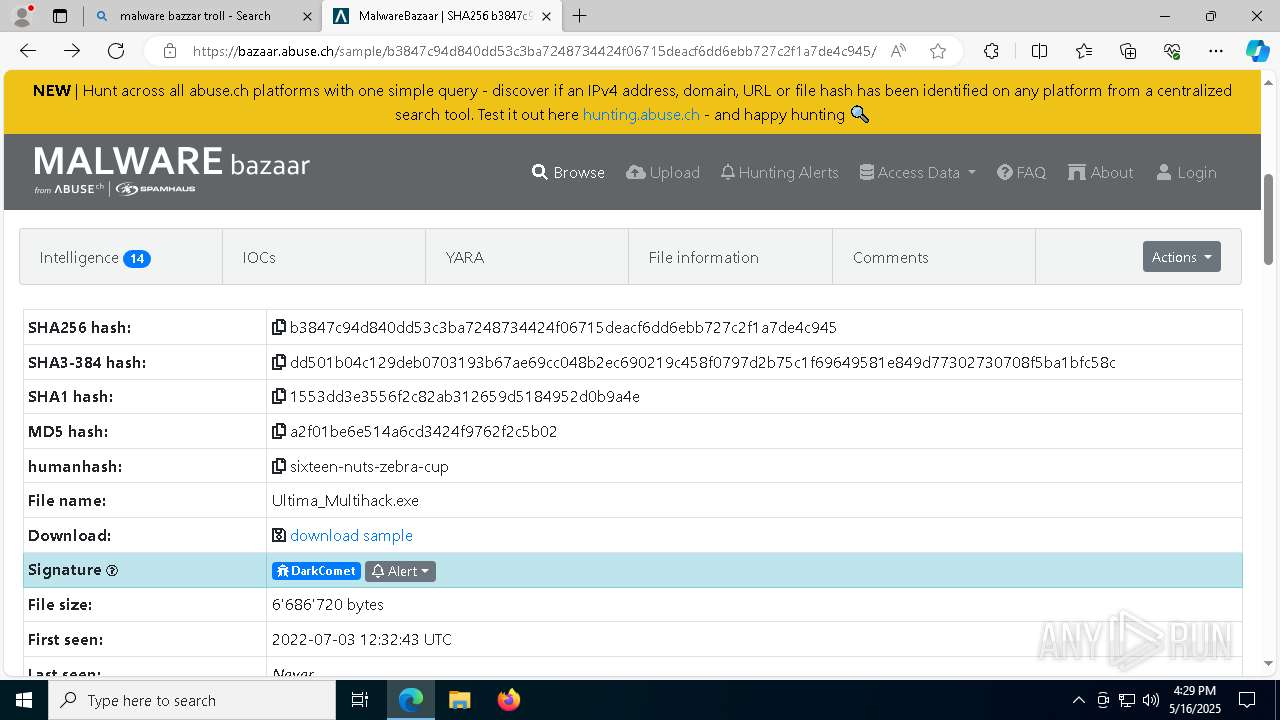
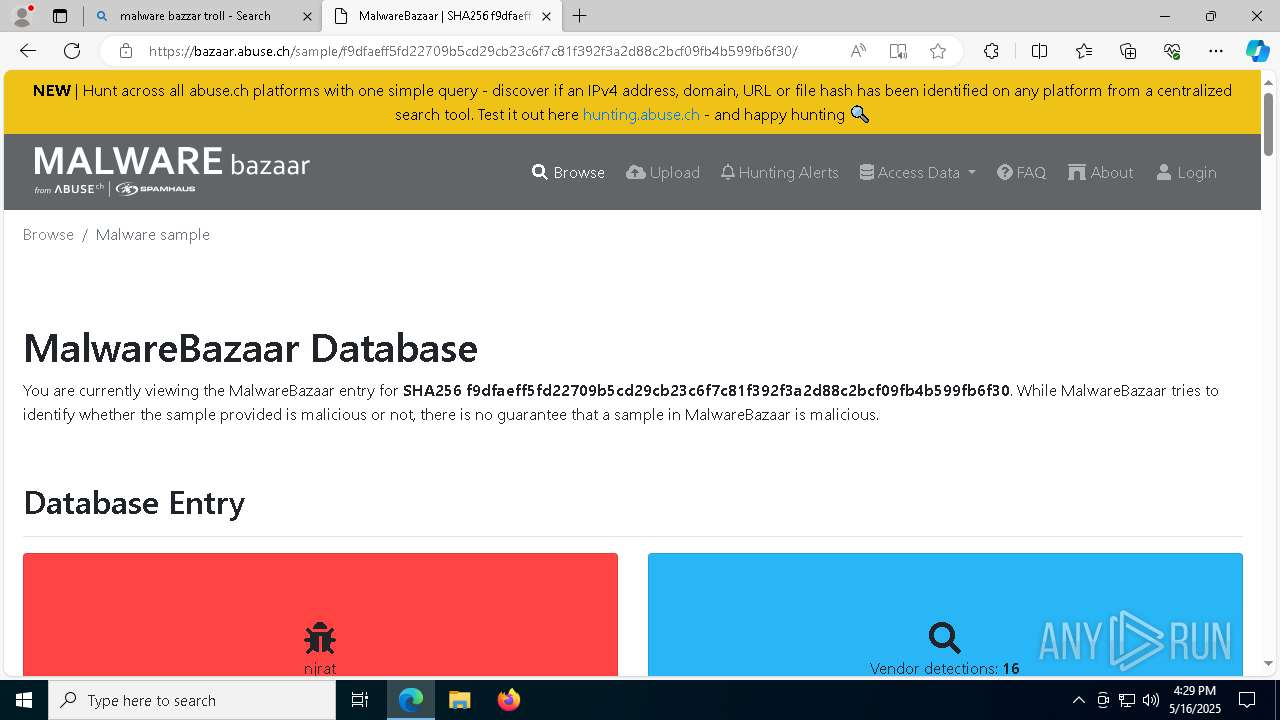
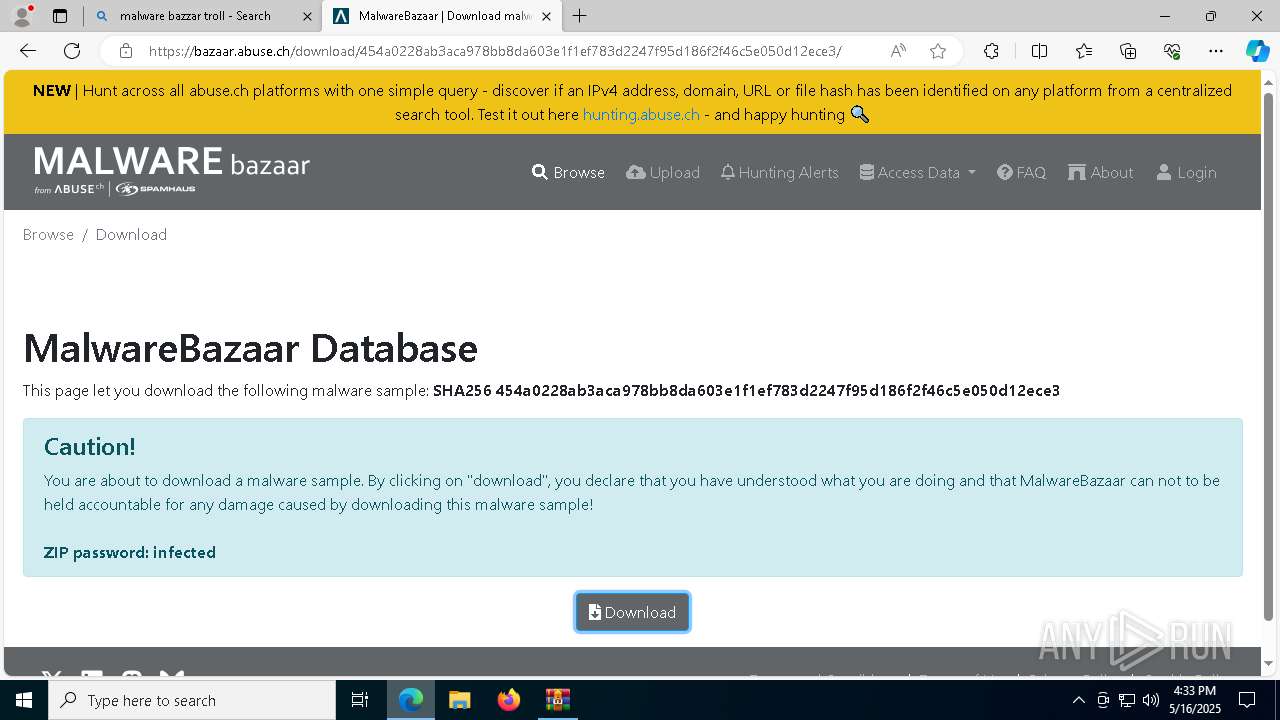
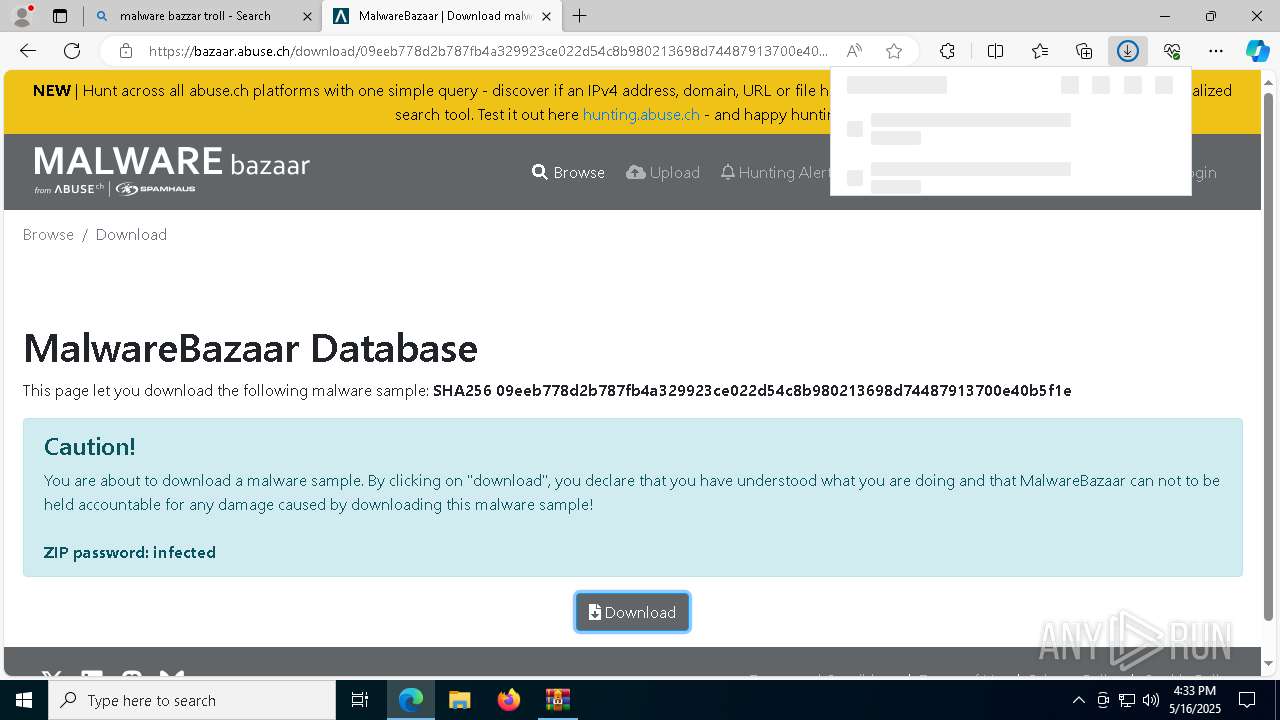
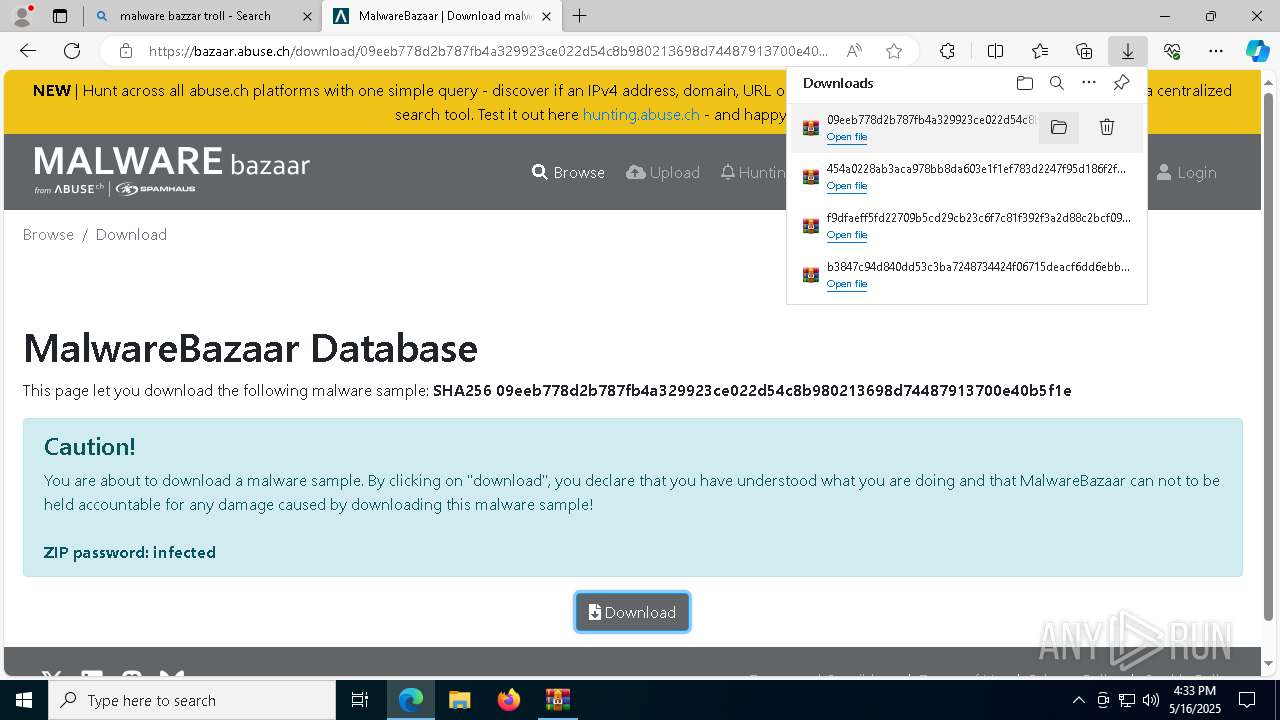
| URL: | https://bazaar.abuse.ch/sample/06e94777c5cf3011c2cd9e47d48dee03d41bf7b69388ae3d39bf98e1bf3315ac/ |
| Full analysis: | https://app.any.run/tasks/6850d060-6f1b-4afd-88dd-f09e6f68b4de |
| Verdict: | Malicious activity |
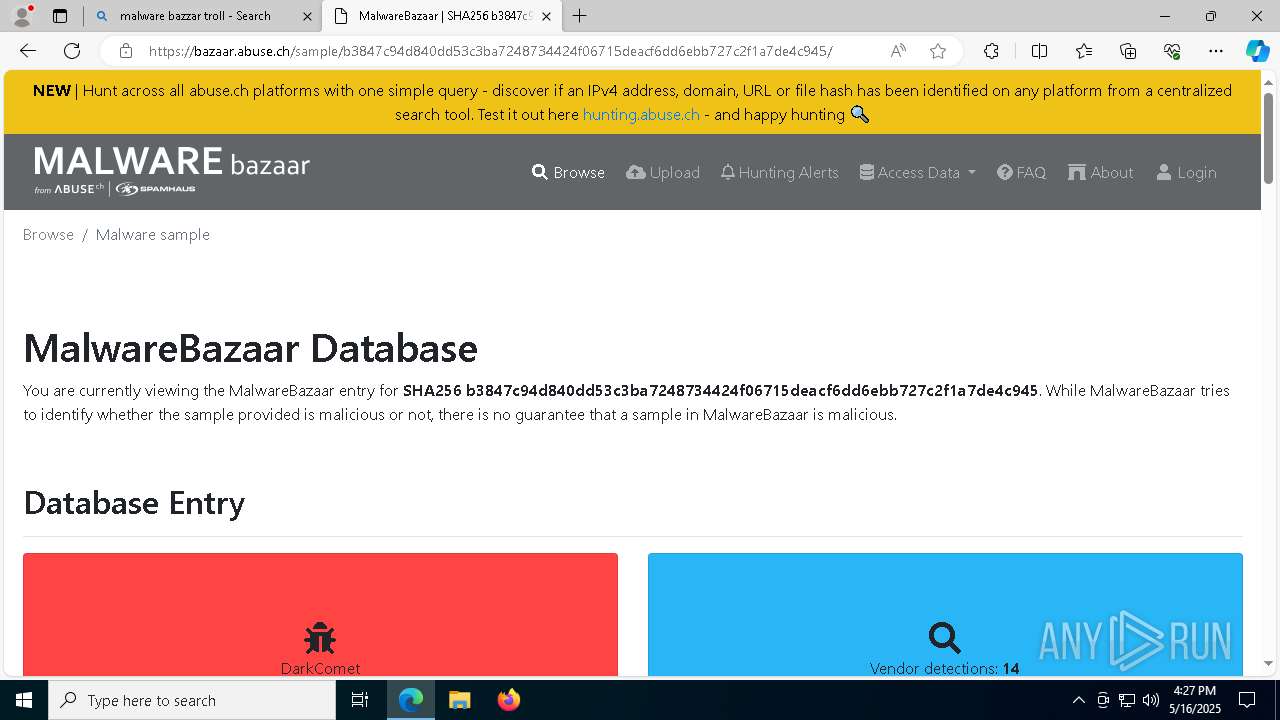
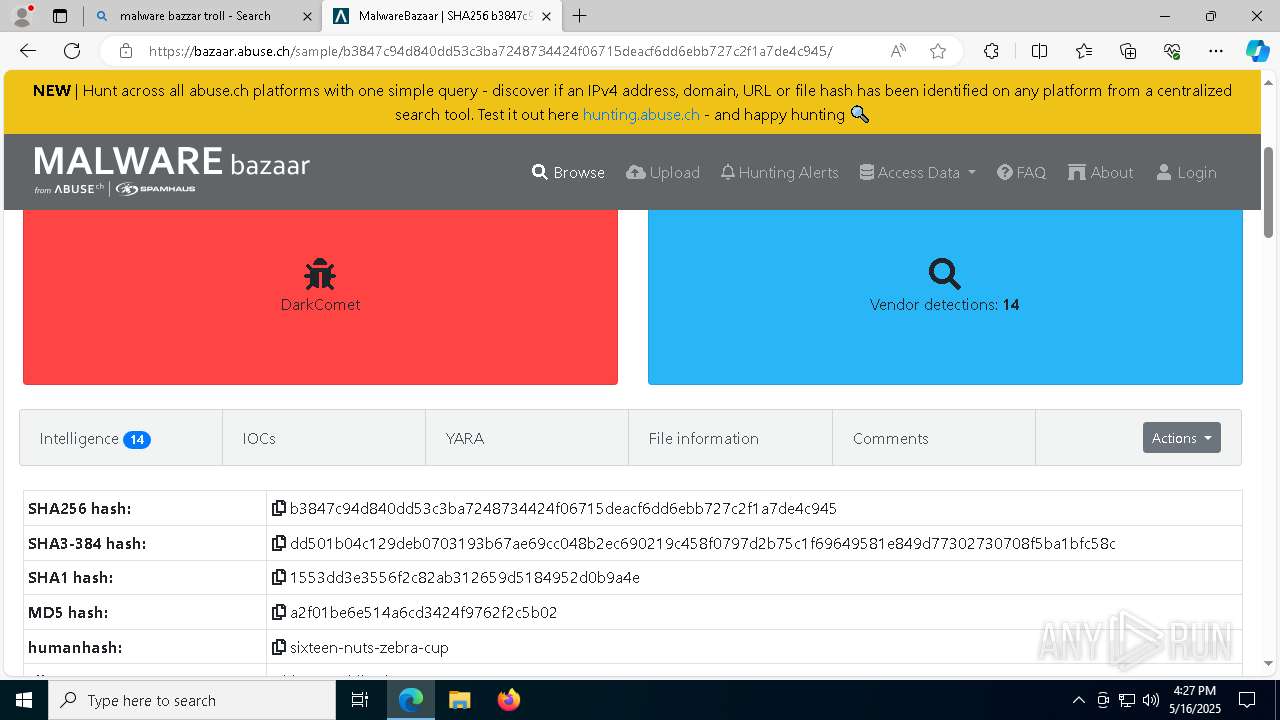
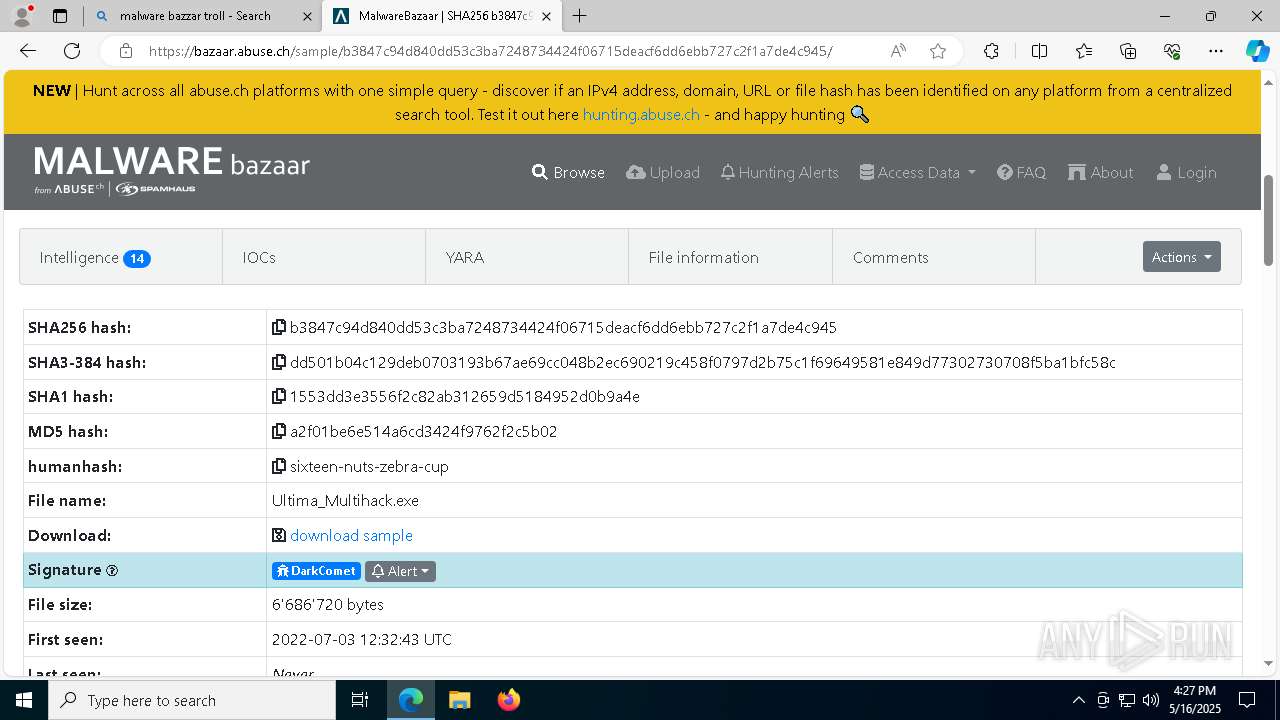
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | May 16, 2025, 16:26:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C9223108479B220EF16EE8BC841A1EDF |
| SHA1: | 5C80F87CC50C79DD2E1EF7CD2B578756B43C3FB9 |
| SHA256: | DD3C8029E11292461C533F385F29224661FC4B204EB0133497D9659C774C8F1C |
| SSDEEP: | 3:N8N0uDWWhRSUfXJRxVSjdGAW5GSn:23nRSOfTcWgS |
MALICIOUS
GENERIC has been found (auto)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
Changes Security Center notification settings
- msdcsc.exe (PID: 536)
- iexplore.exe (PID: 5740)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Changes the autorun value in the registry
- msdcsc.exe (PID: 536)
- loader.exe (PID: 2288)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Changes firewall settings
- msdcsc.exe (PID: 536)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- iexplore.exe (PID: 5740)
- loader.exe (PID: 3008)
Disables Windows firewall
- msdcsc.exe (PID: 536)
- iexplore.exe (PID: 5740)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
UAC/LUA settings modification
- msdcsc.exe (PID: 536)
- iexplore.exe (PID: 5740)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Creates or modifies Windows services
- msdcsc.exe (PID: 536)
- loader.exe (PID: 7724)
- iexplore.exe (PID: 5740)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
DARKCOMET mutex has been found
- msdcsc.exe (PID: 536)
- iexplore.exe (PID: 5740)
- notepad.exe (PID: 6416)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Modify registry editing tools (regedit)
- iexplore.exe (PID: 5740)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Changes the login/logoff helper path in the registry
- loader.exe (PID: 2288)
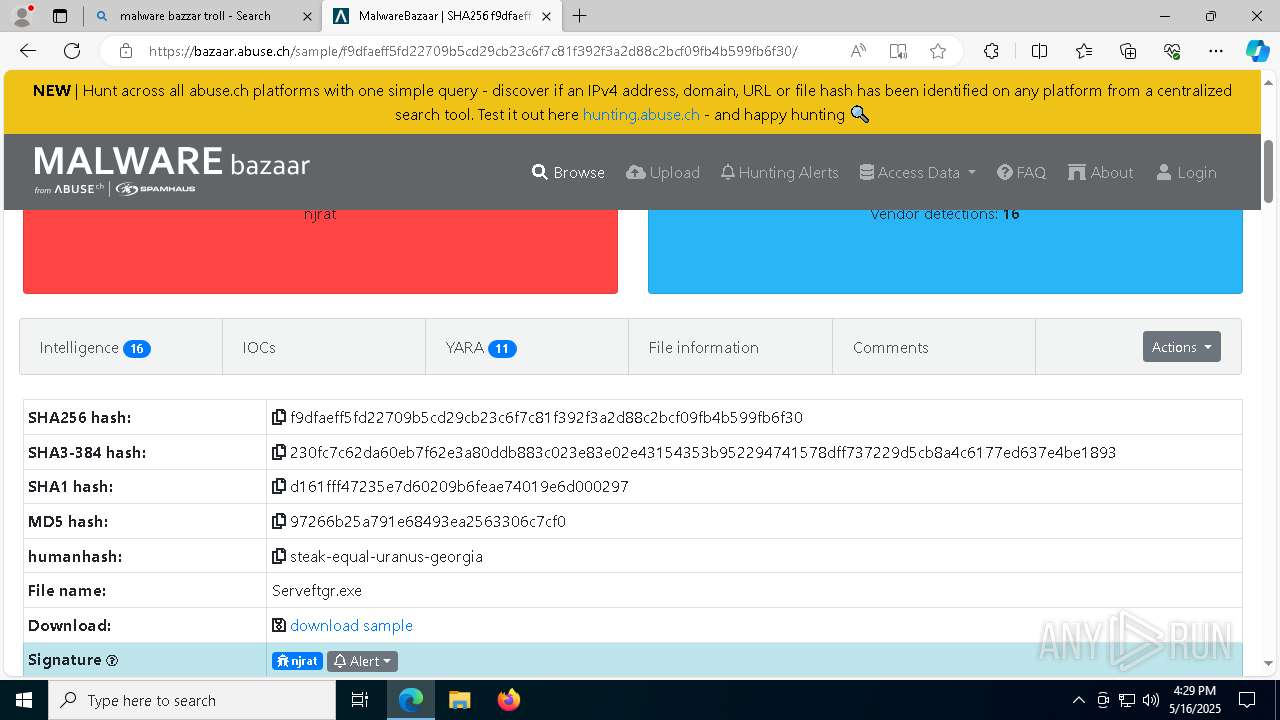
NJRAT has been detected (YARA)
- server.exe (PID: 4692)
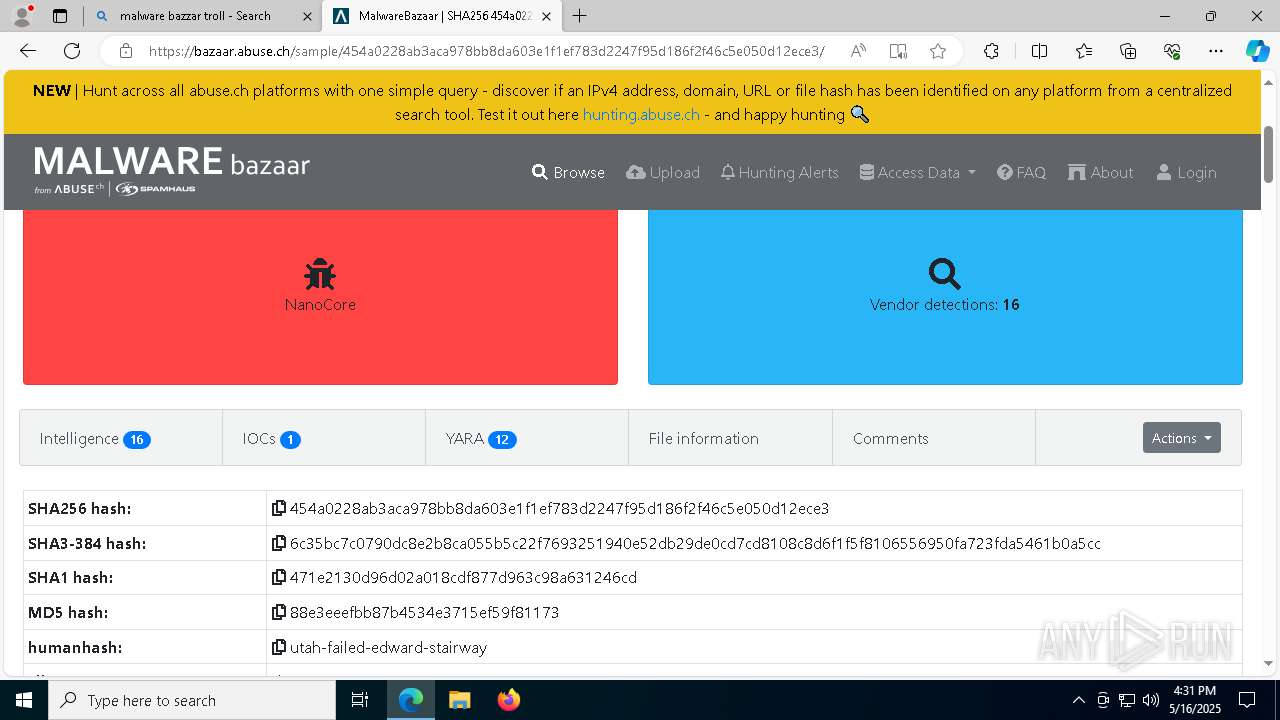
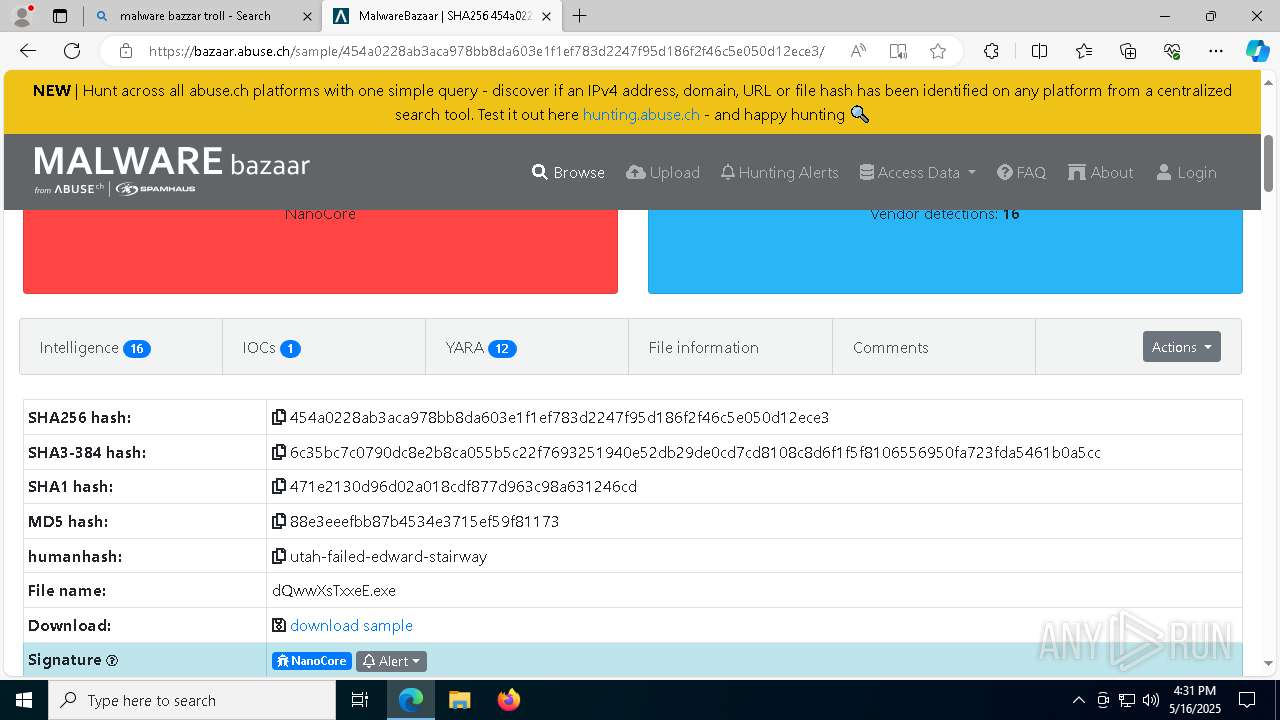
NANOCORE has been detected (YARA)
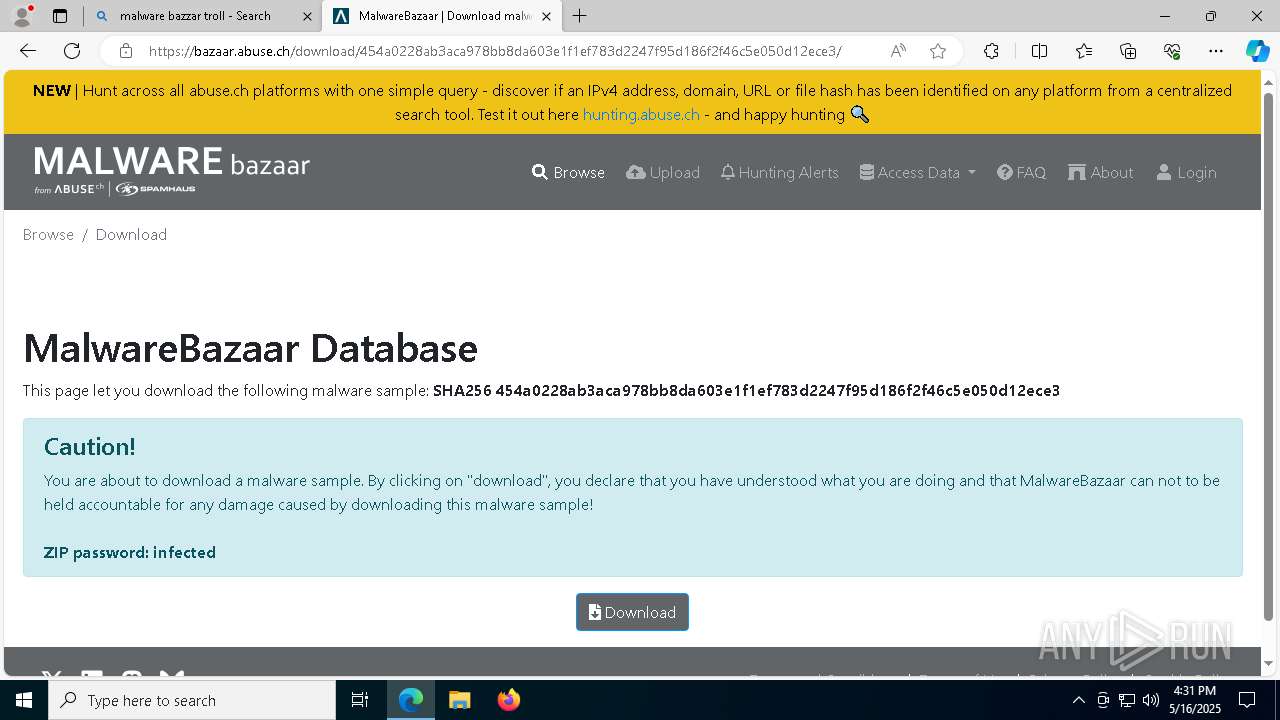
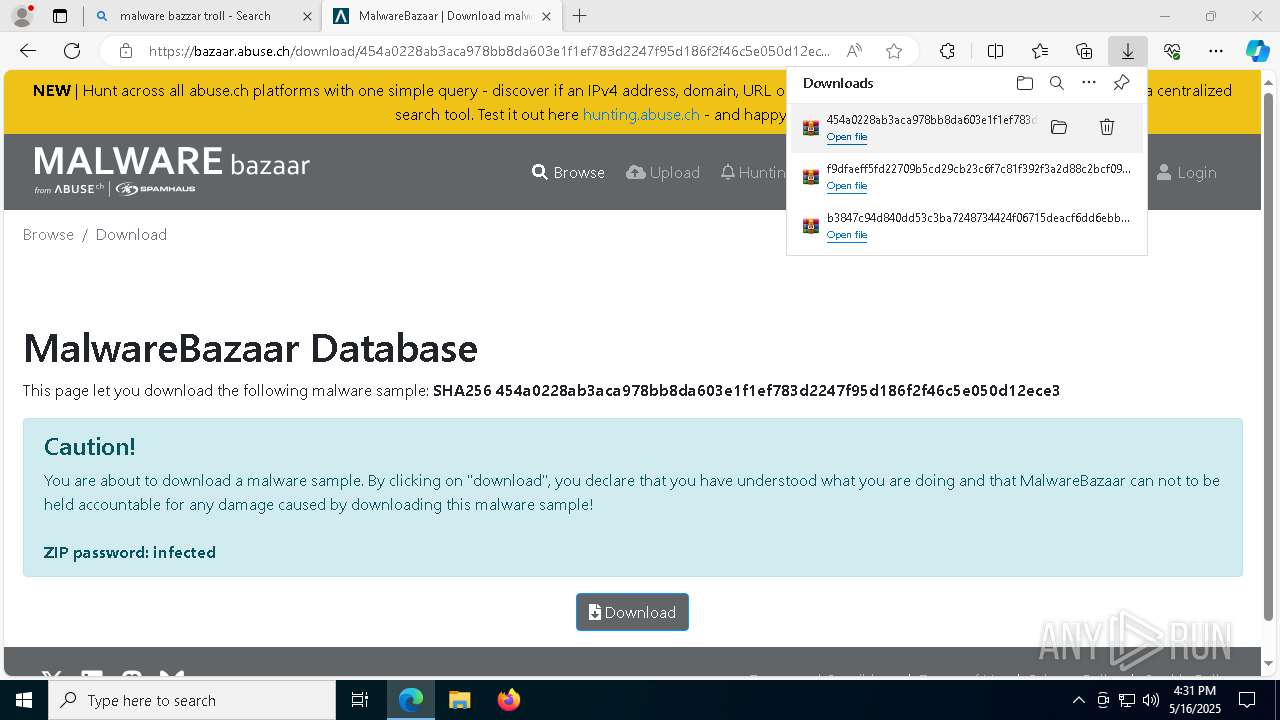
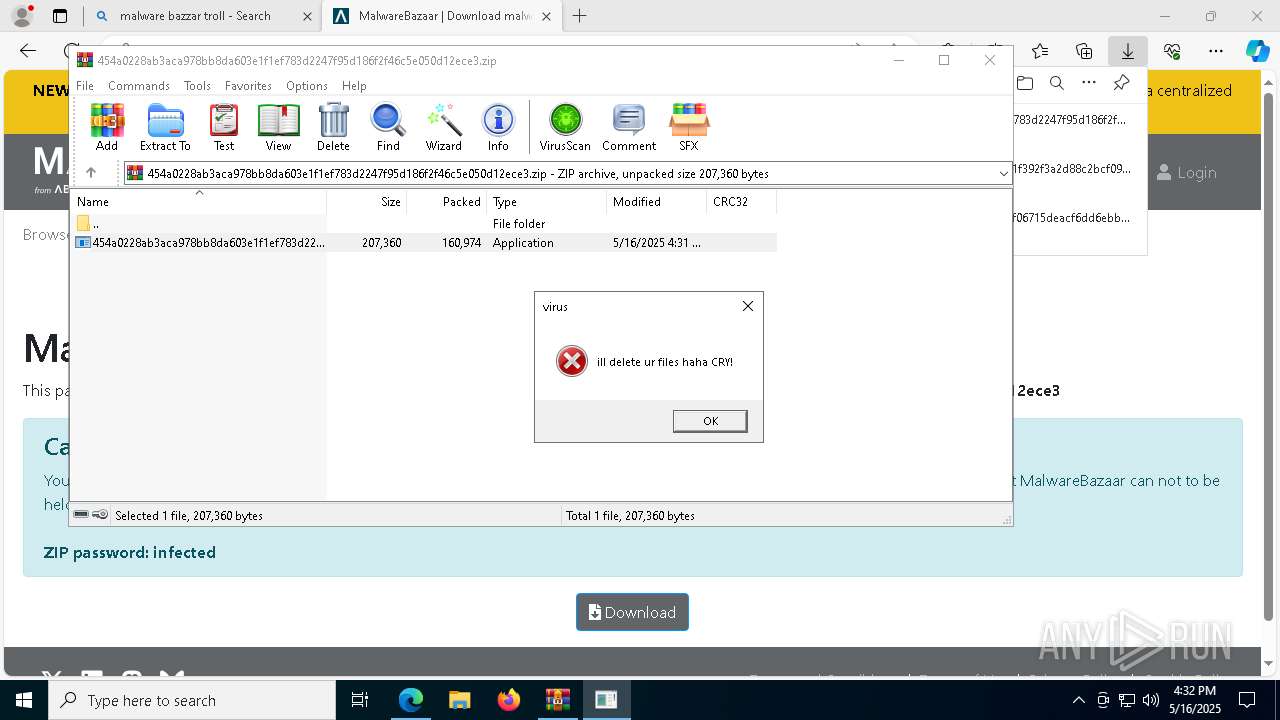
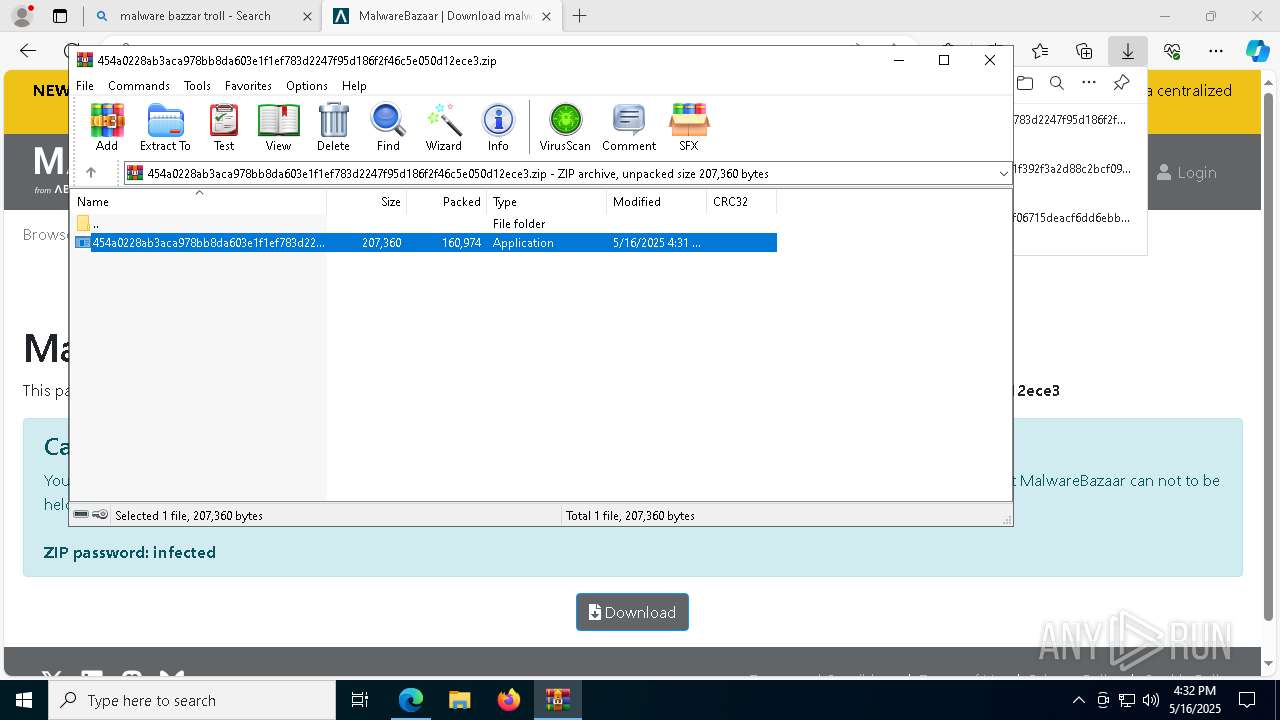
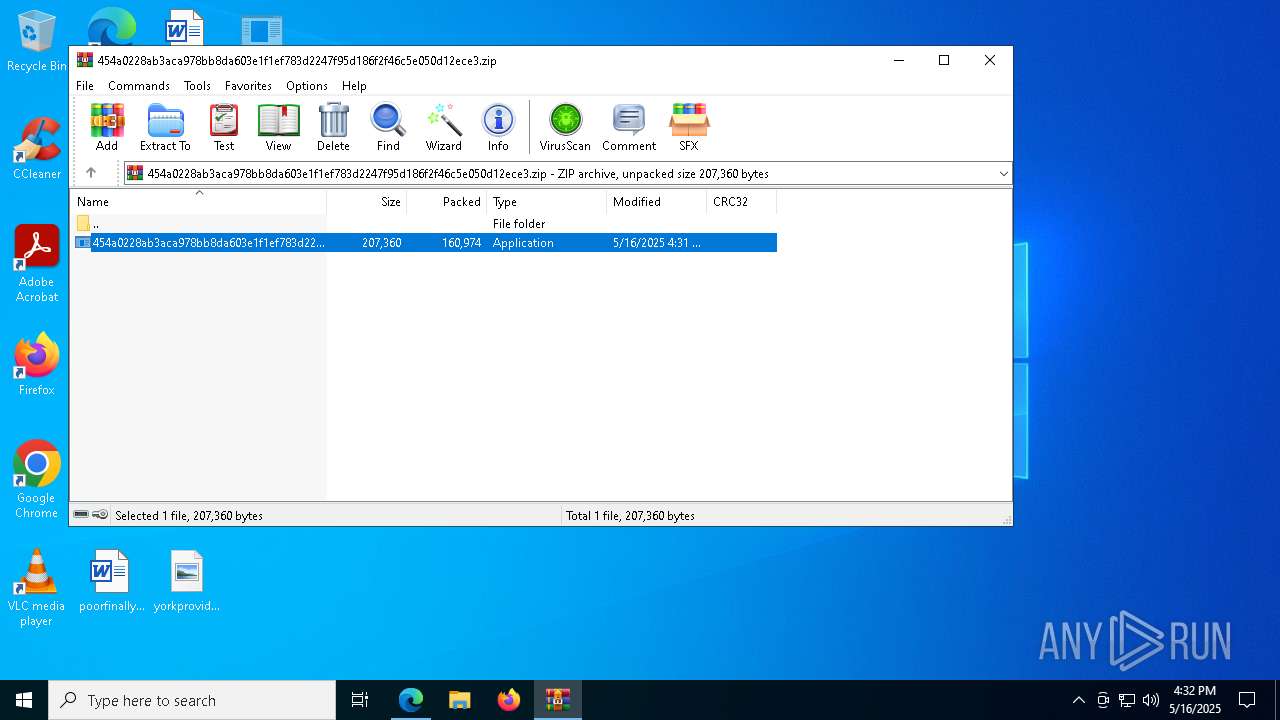
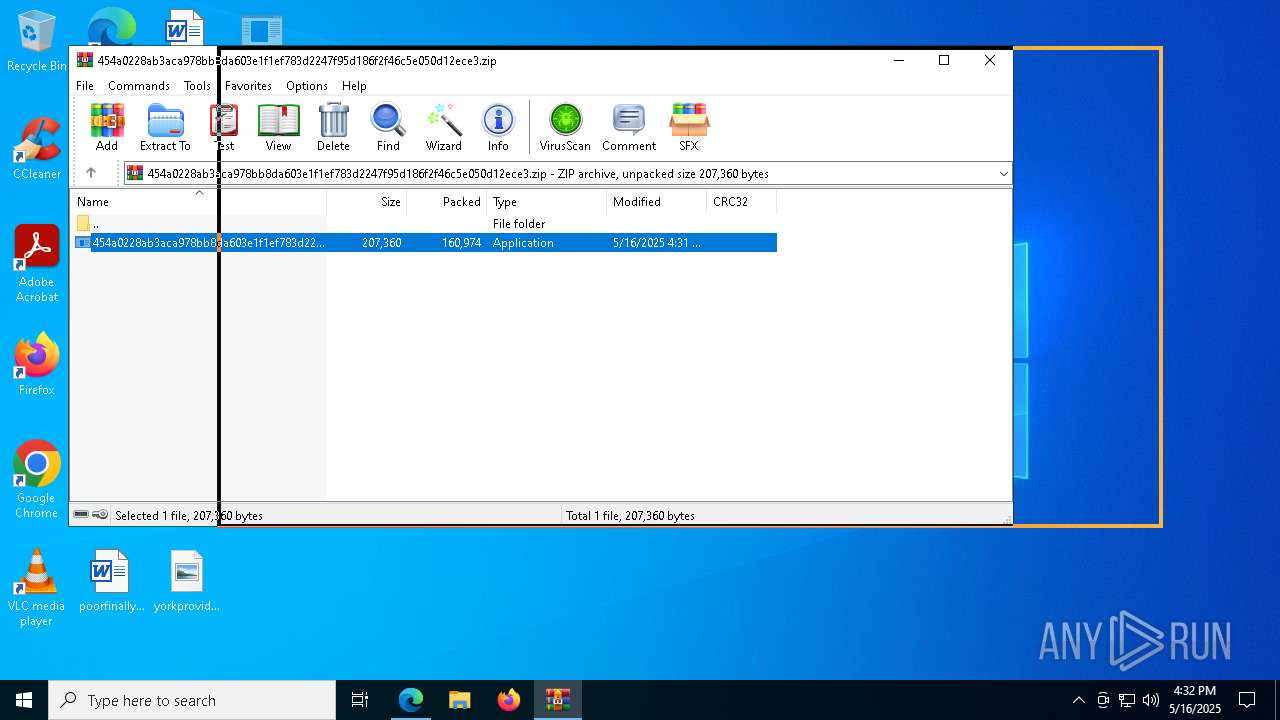
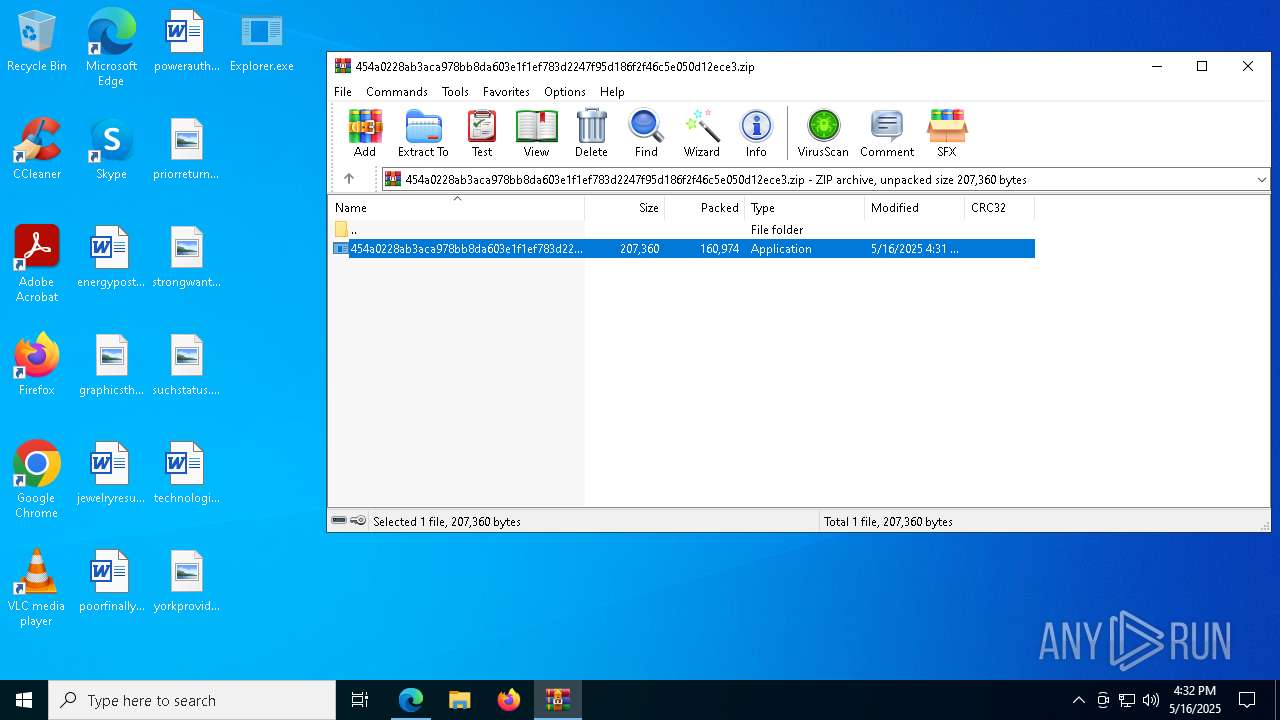
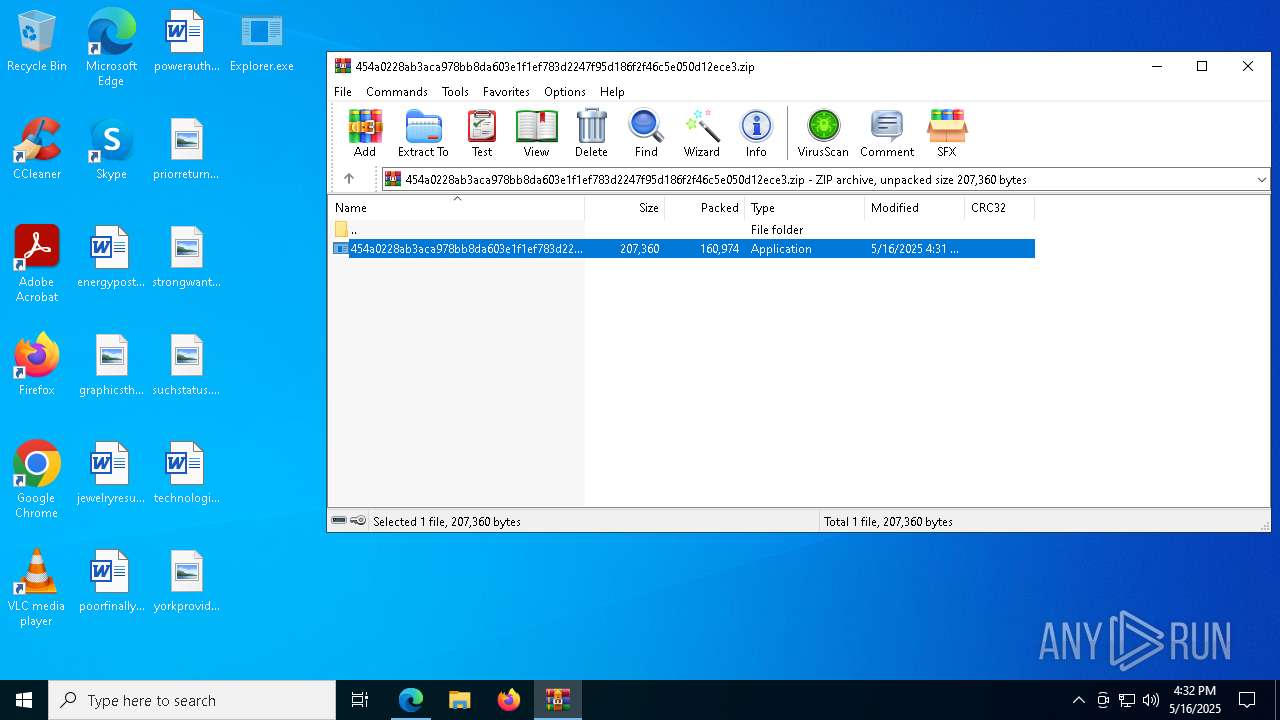
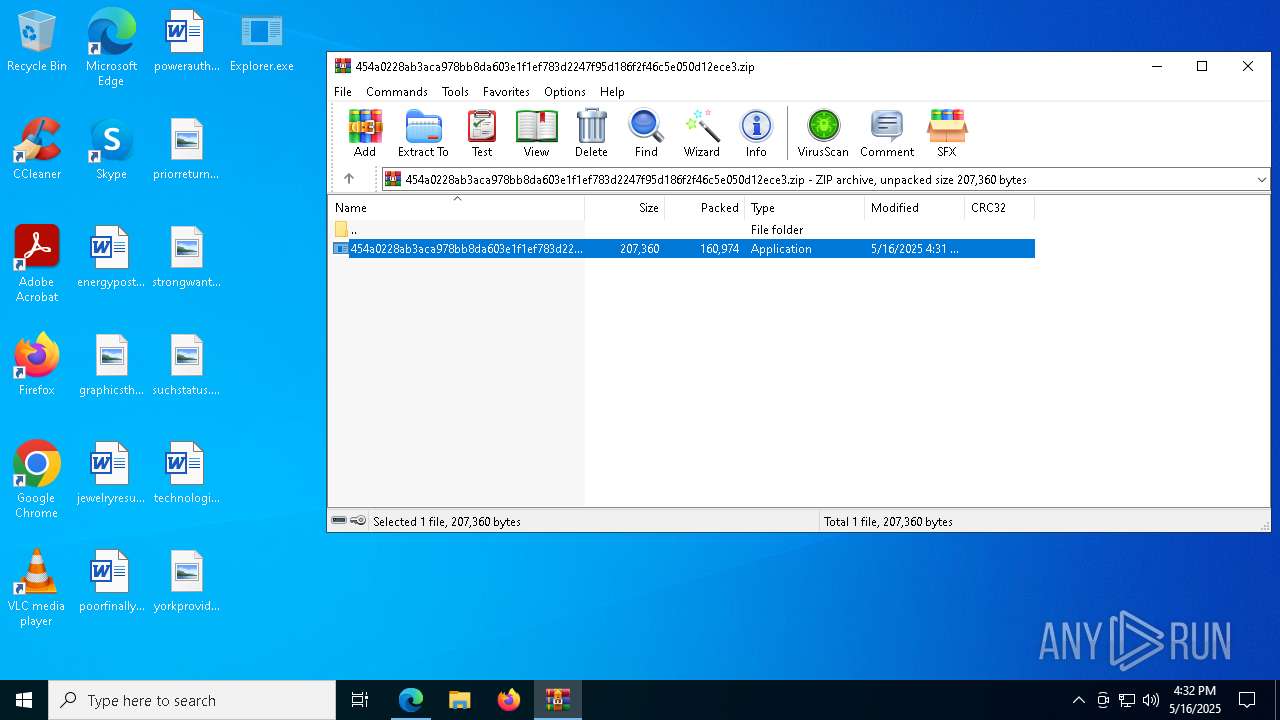
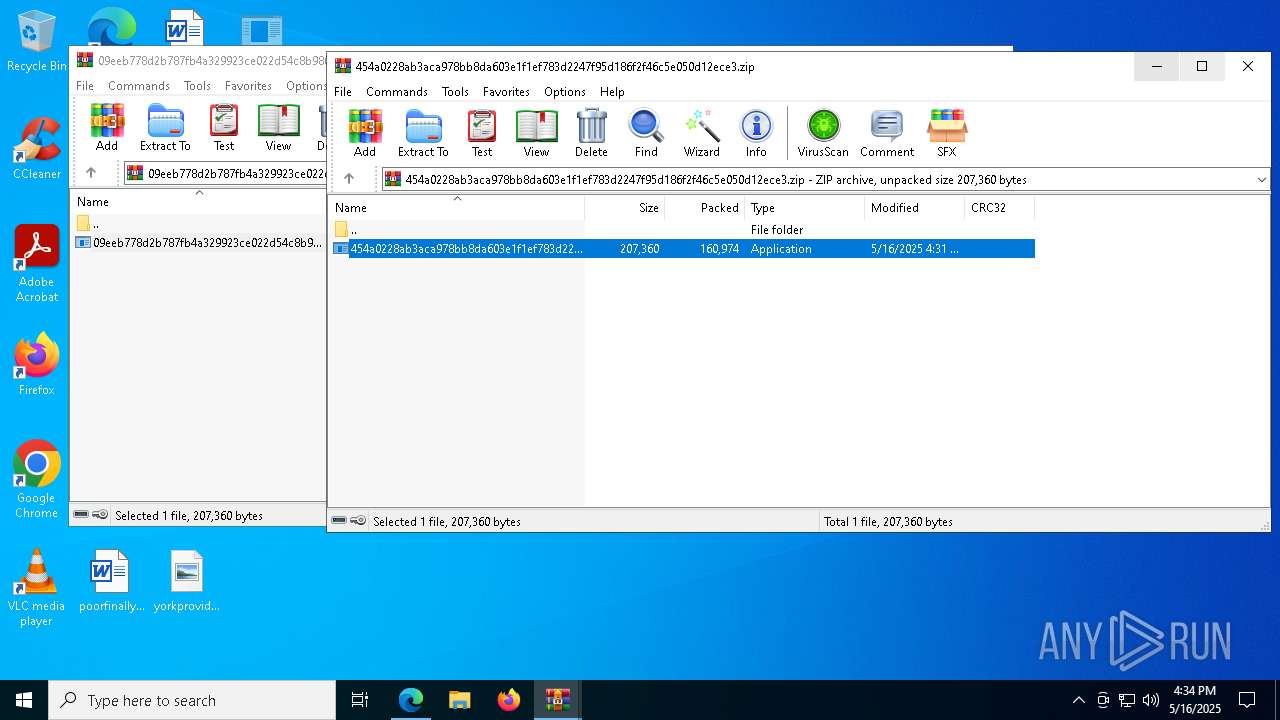
- 454a0228ab3aca978bb8da603e1f1ef783d2247f95d186f2f46c5e050d12ece3.exe (PID: 6036)
SUSPICIOUS
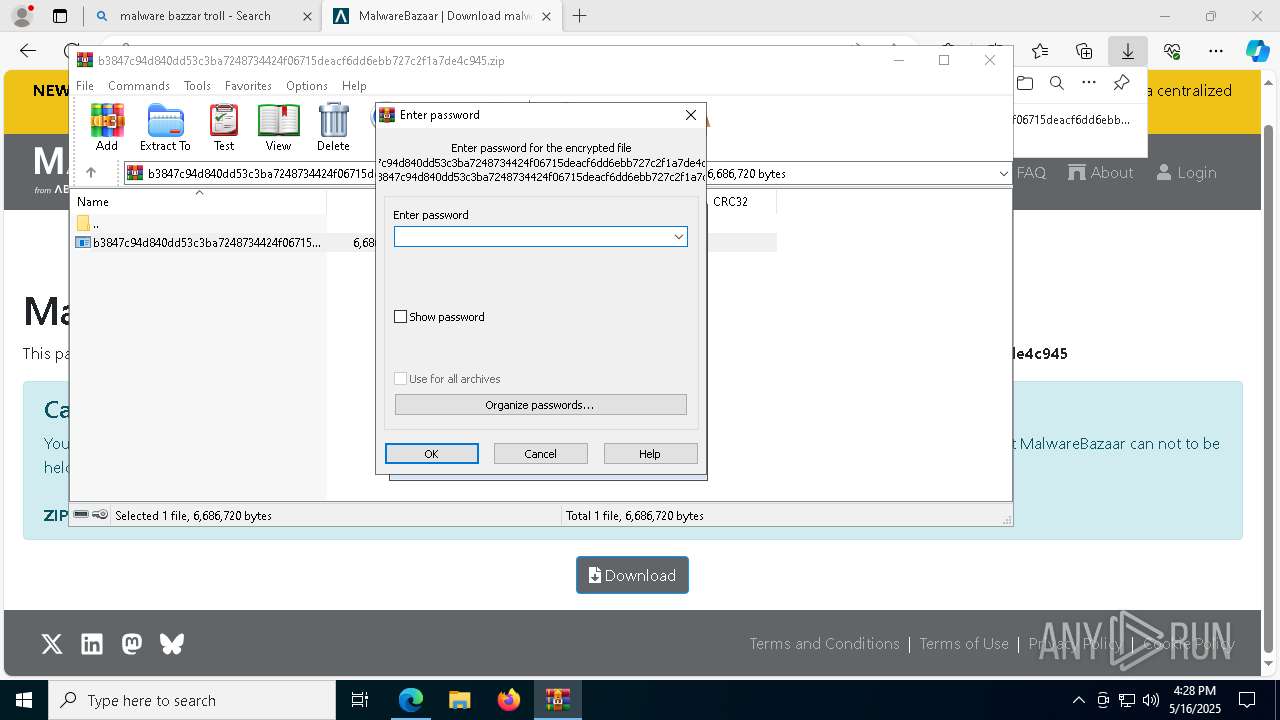
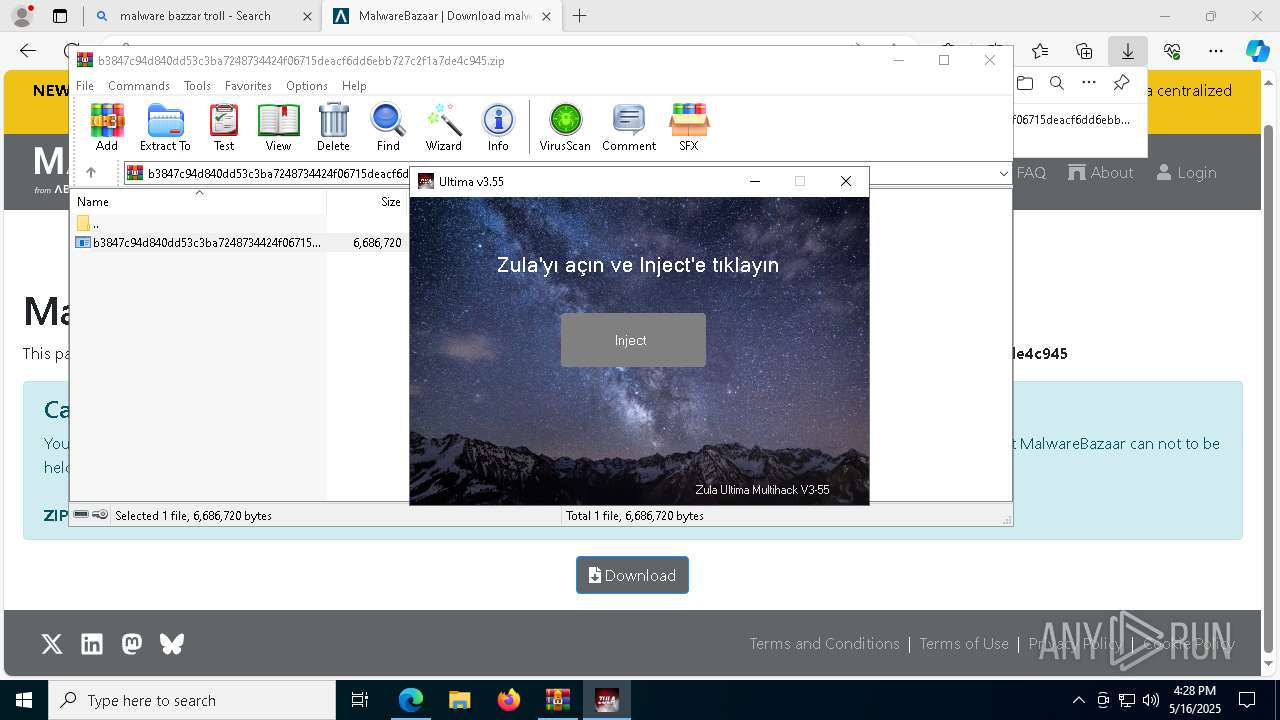
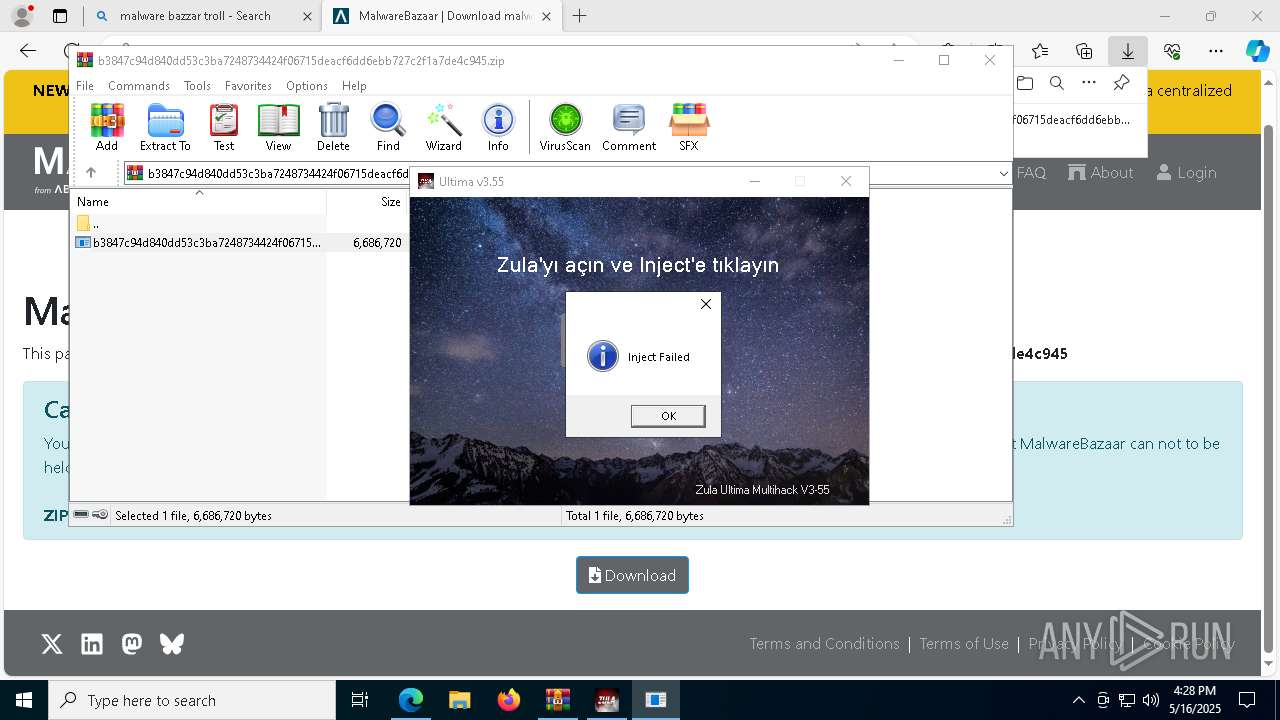
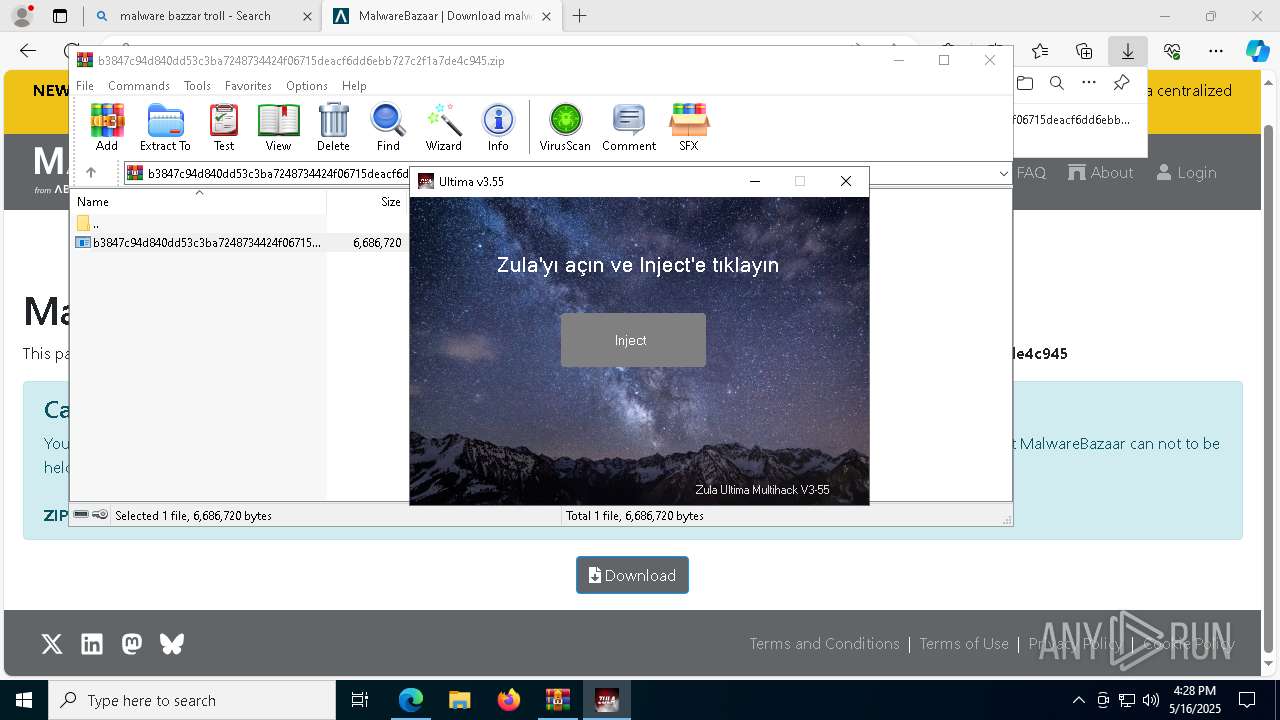
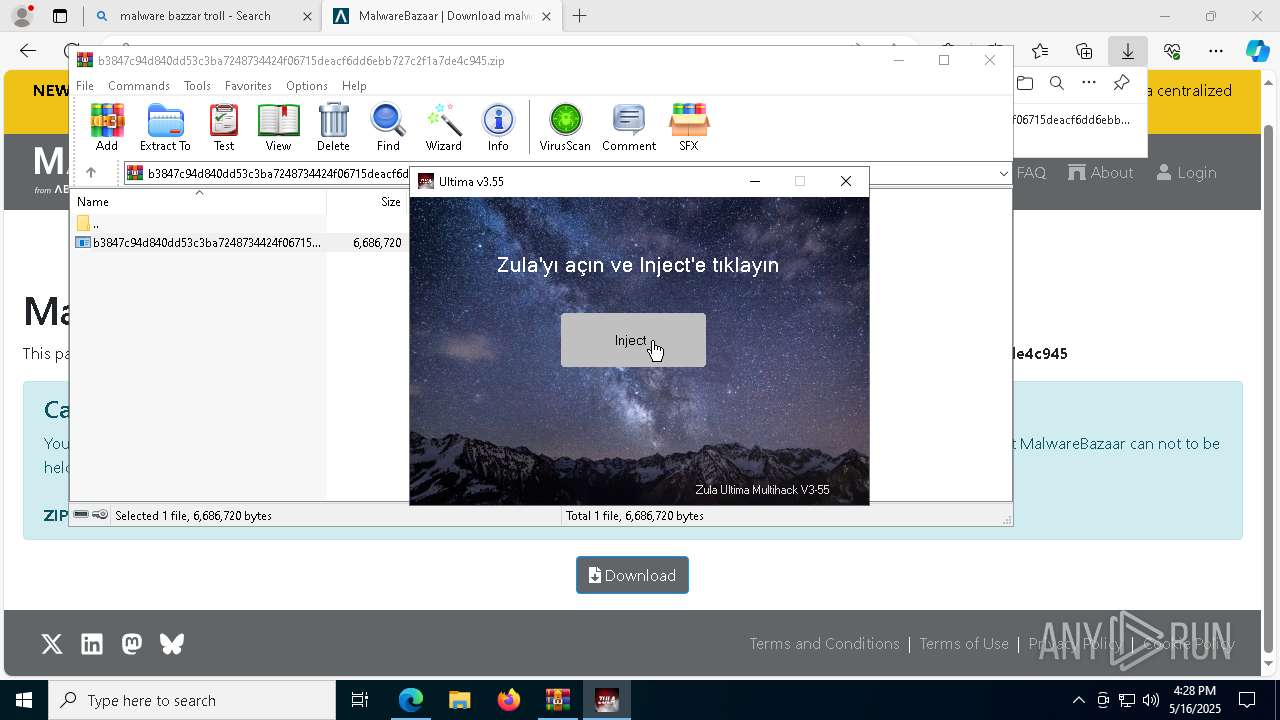
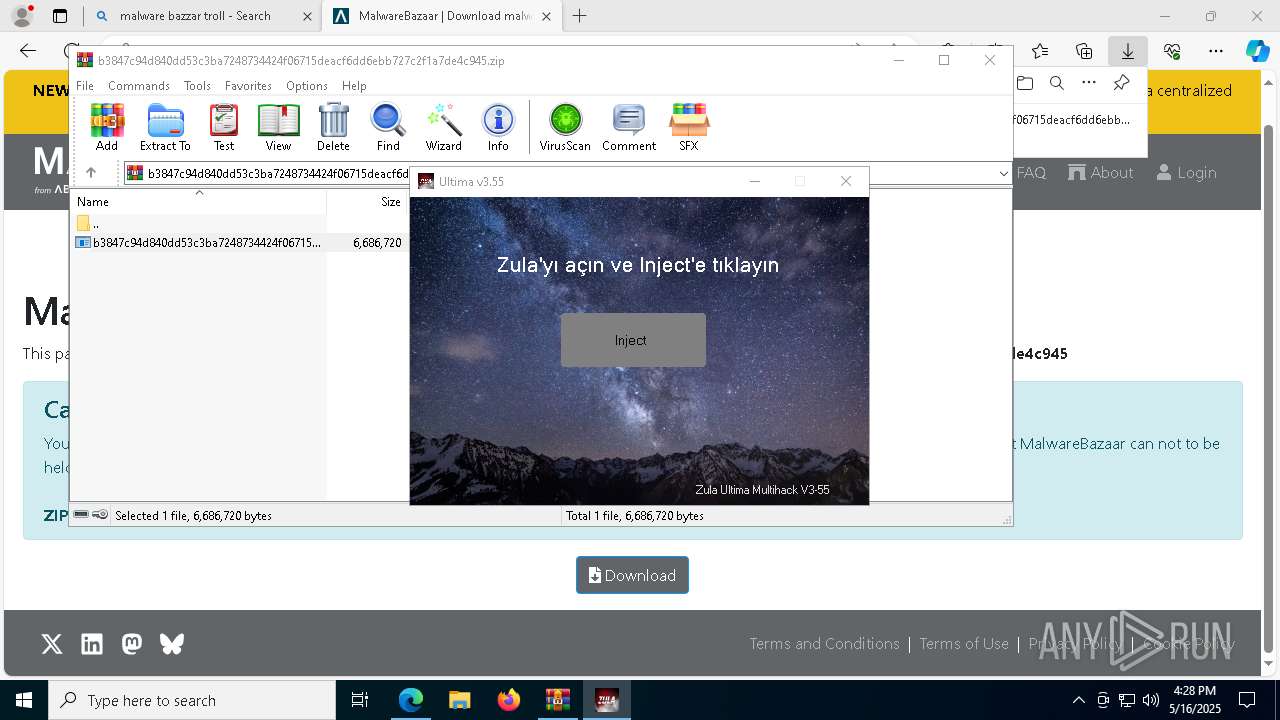
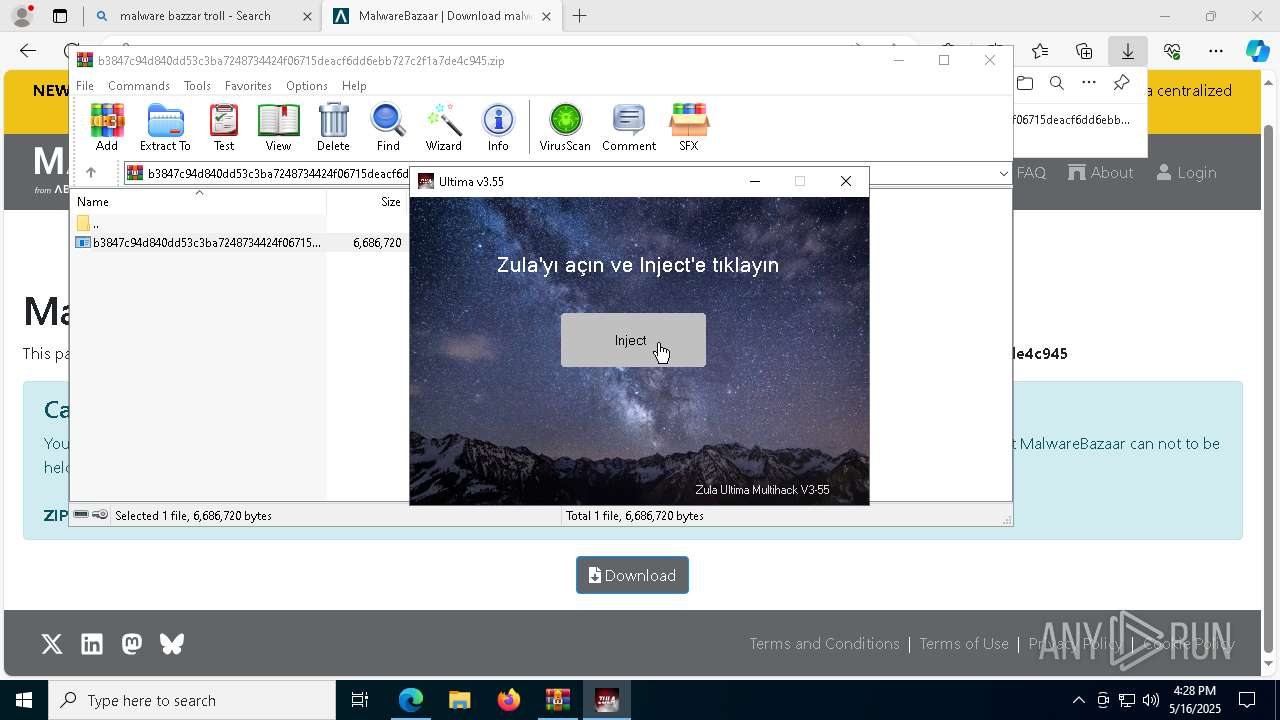
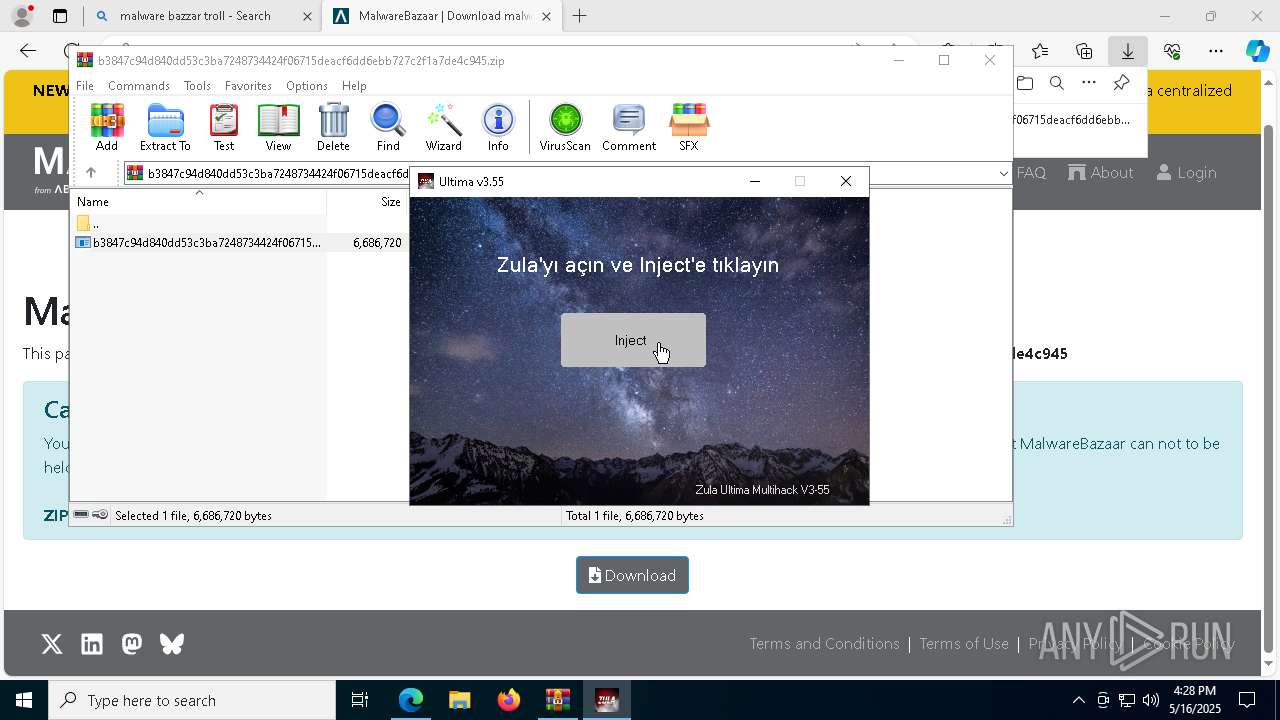
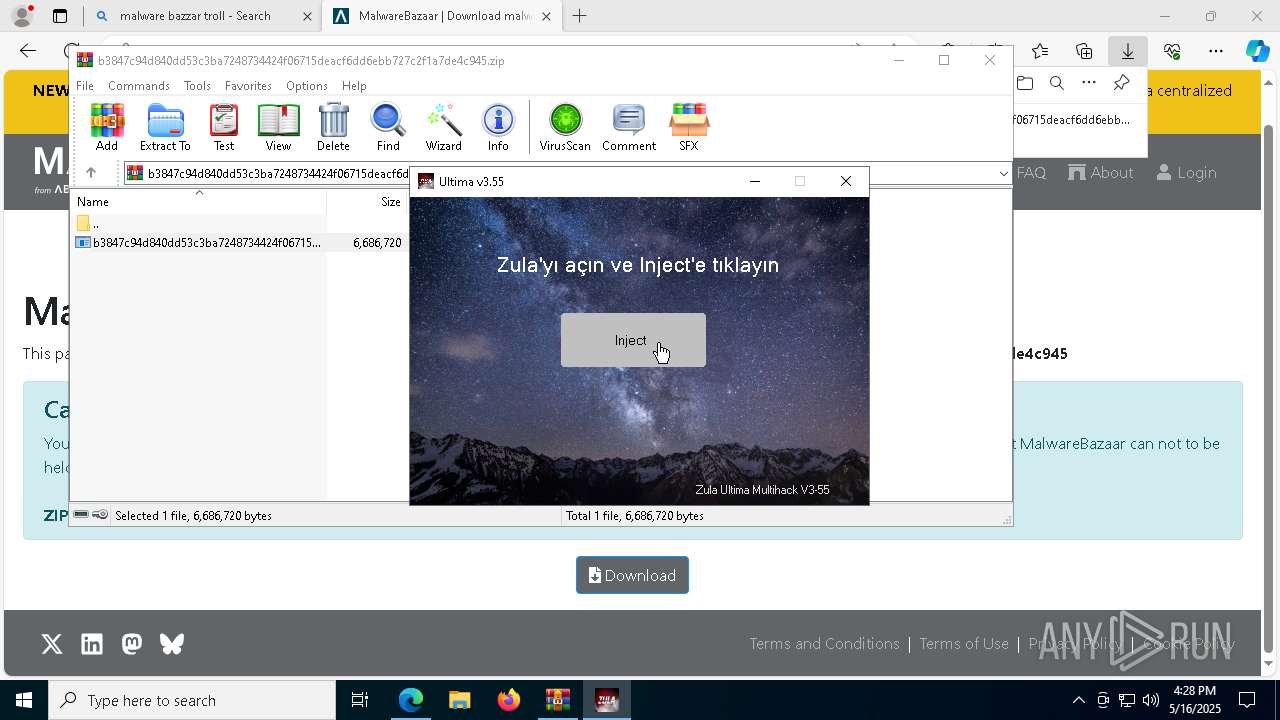
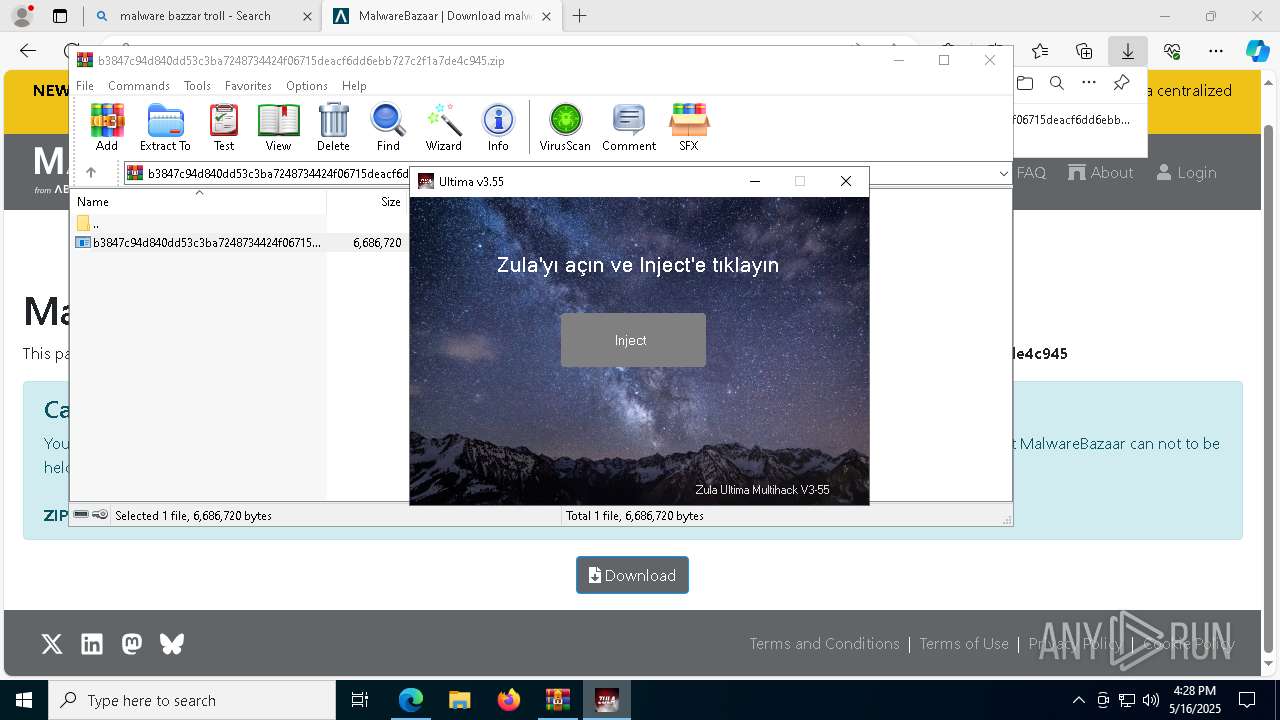
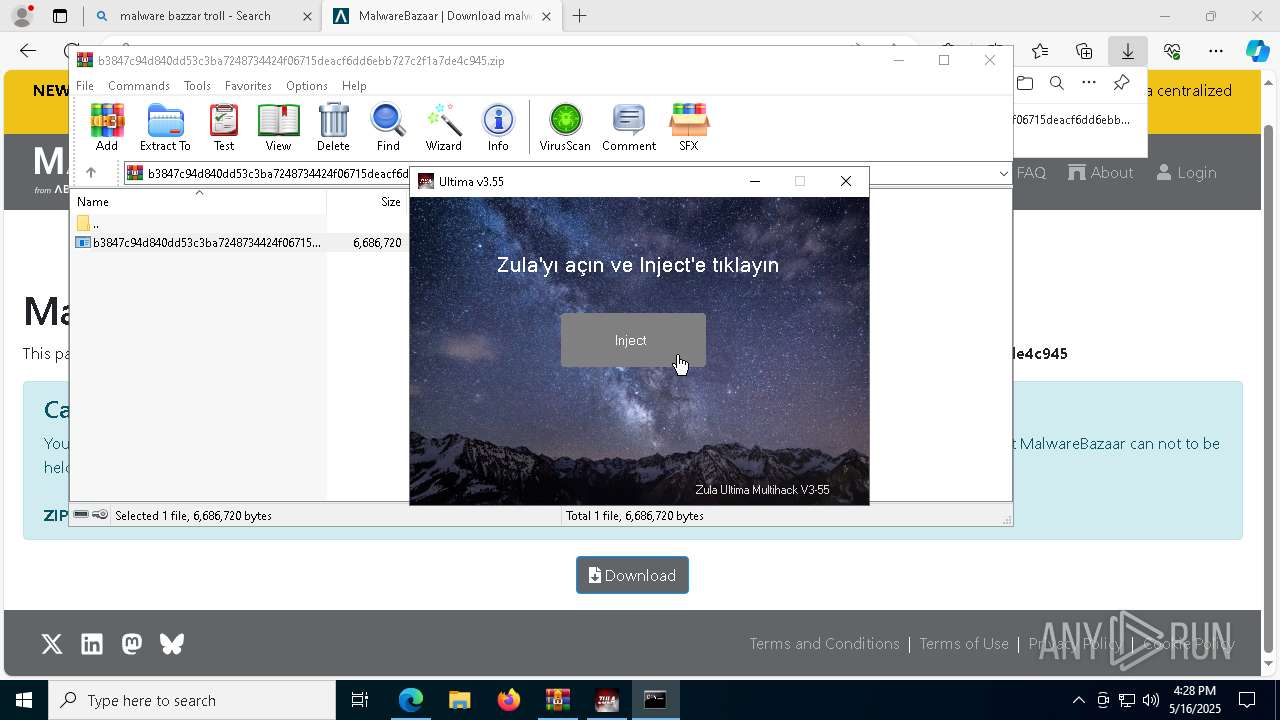
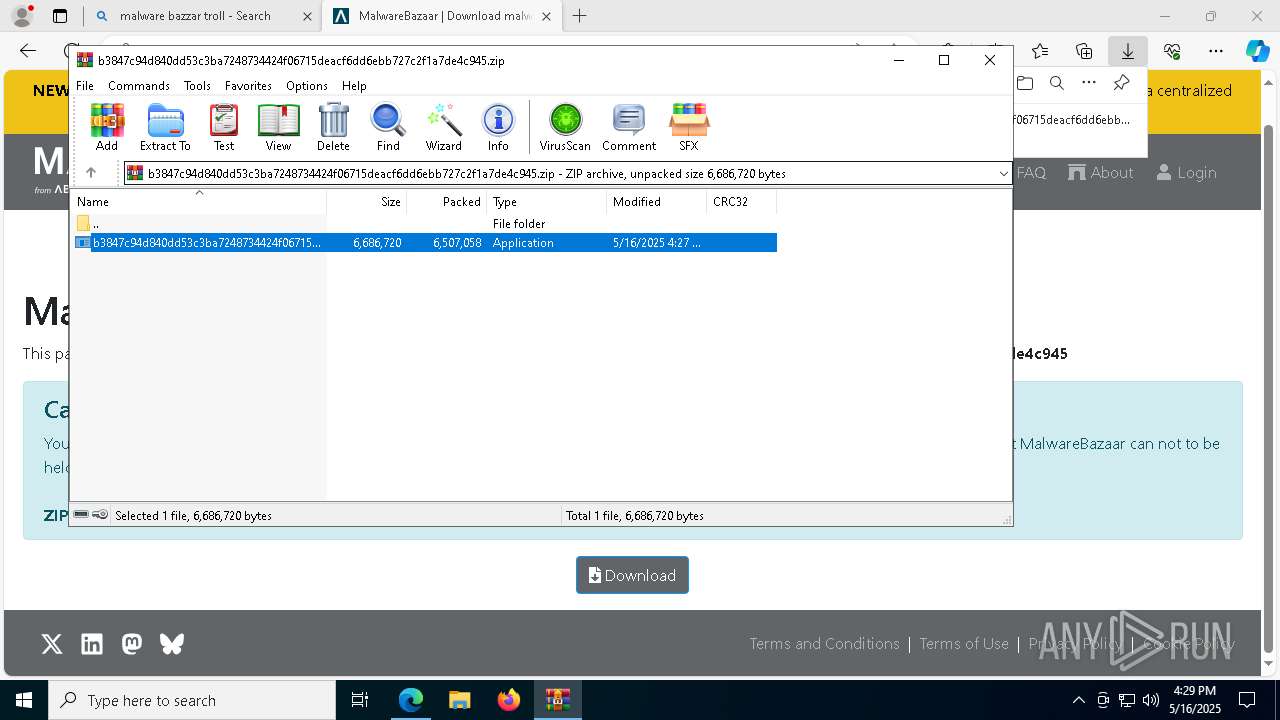
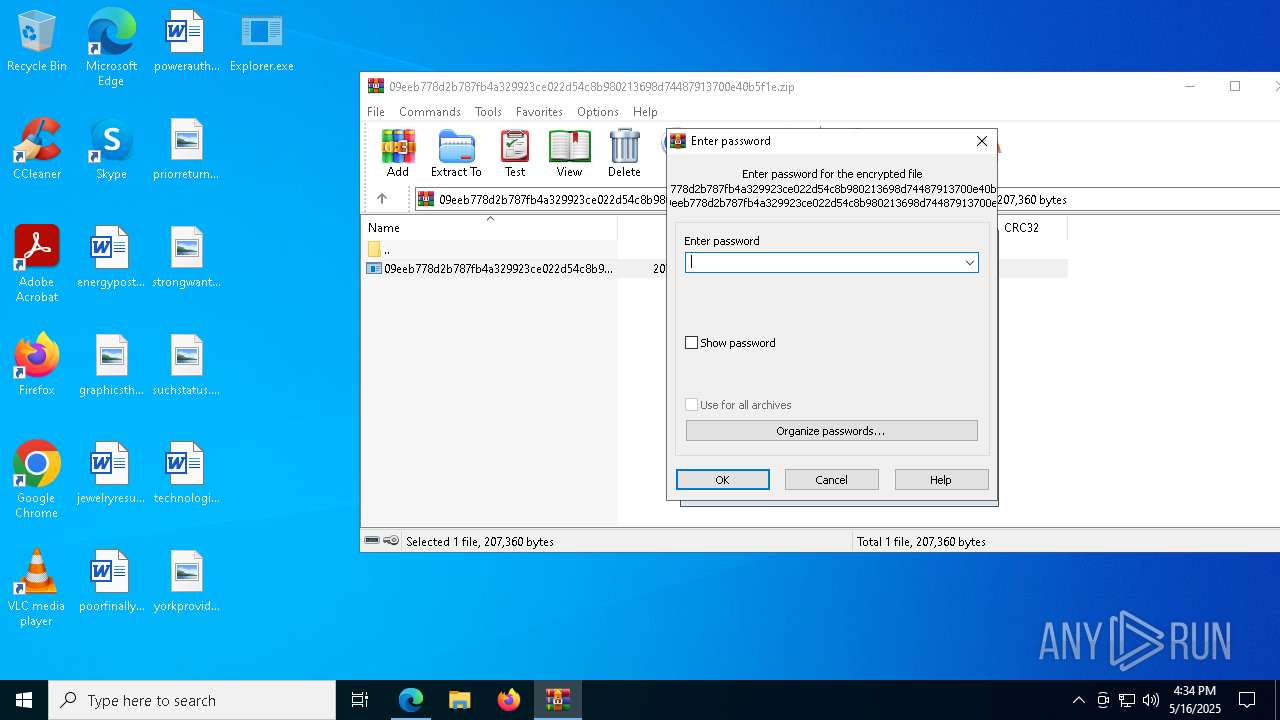
Reads security settings of Internet Explorer
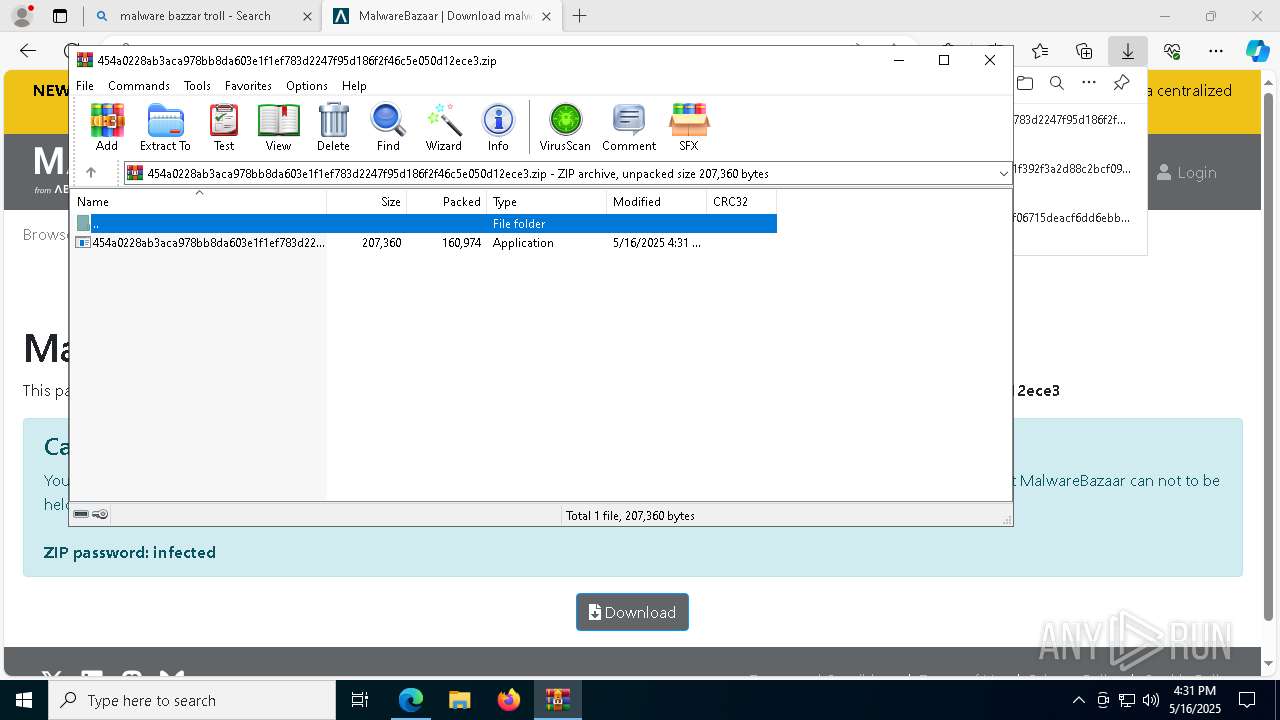
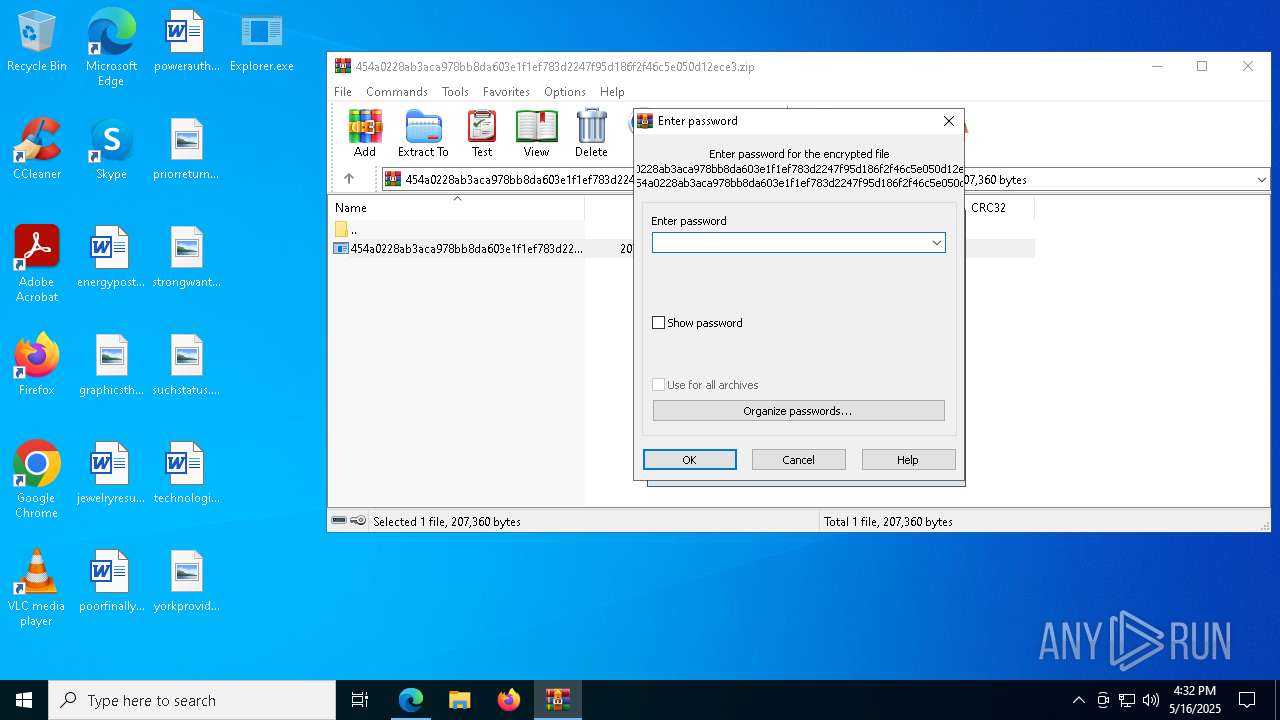
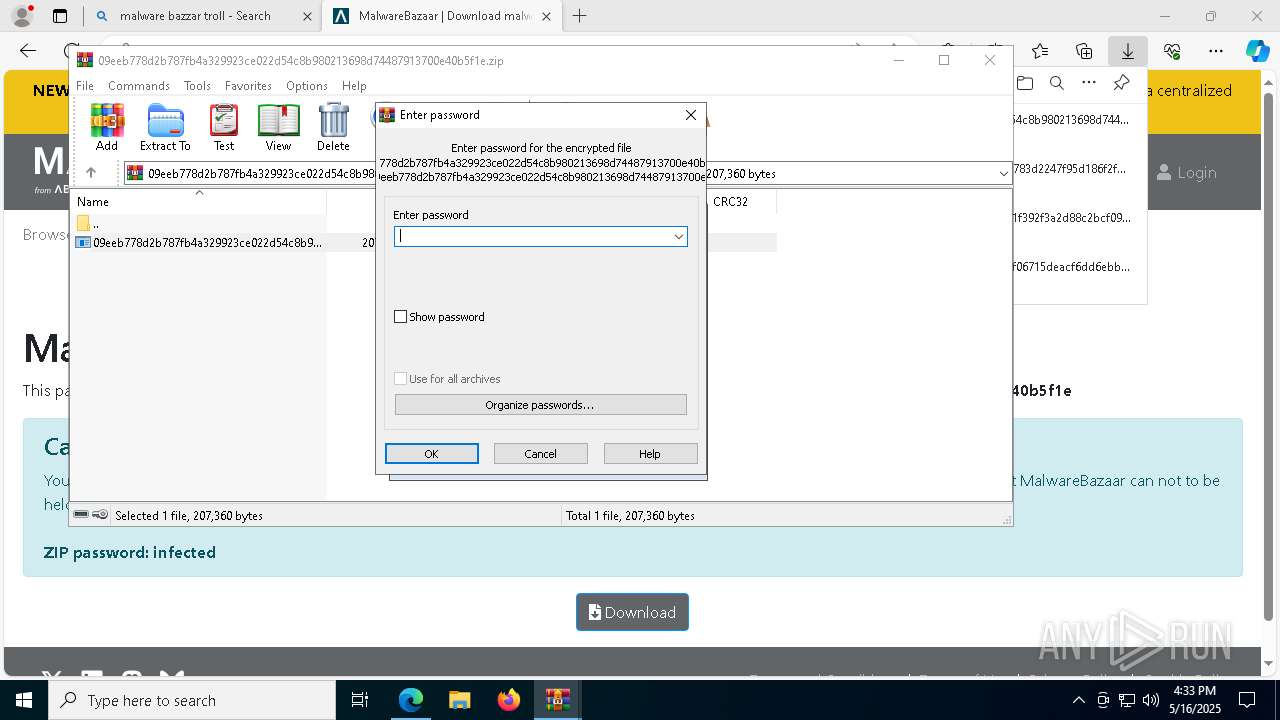
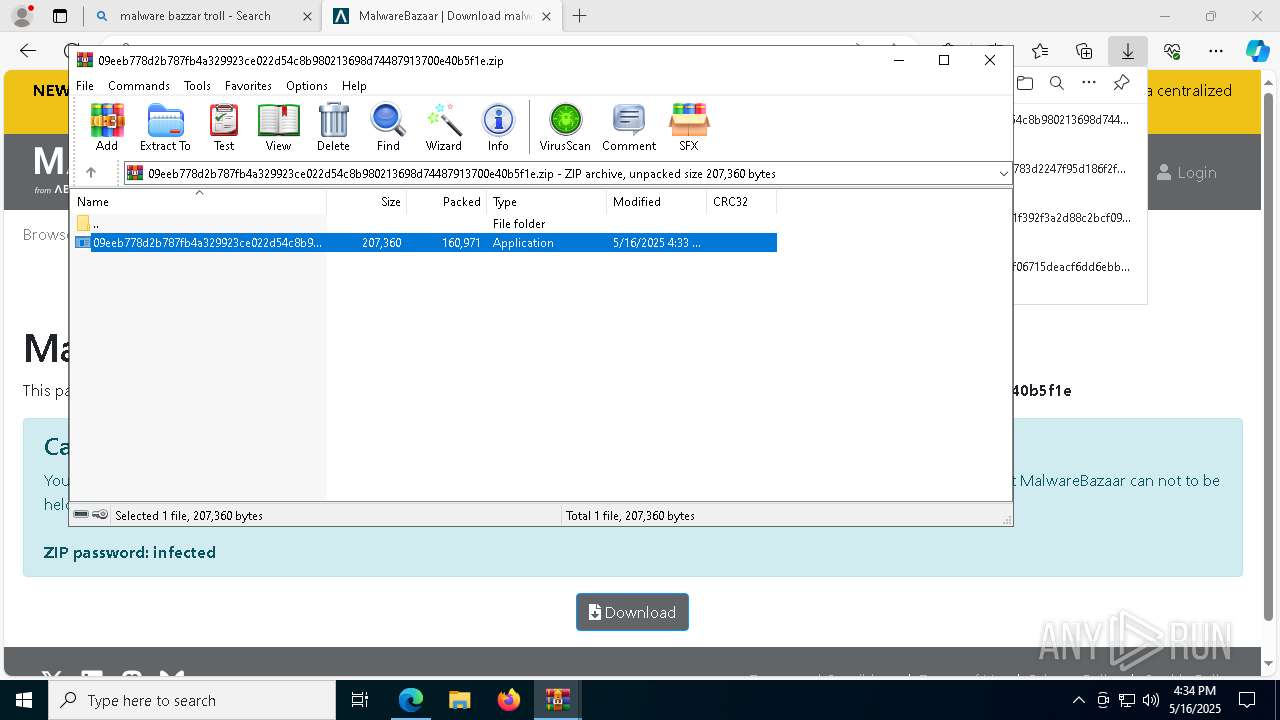
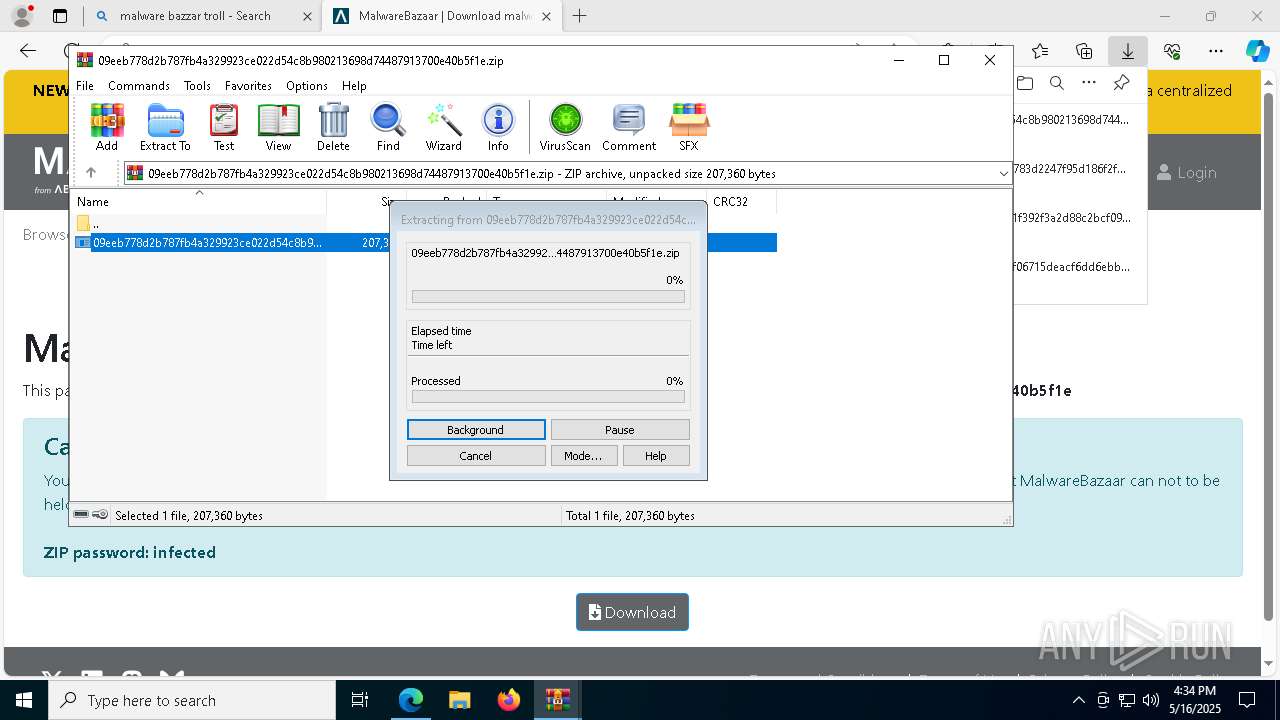
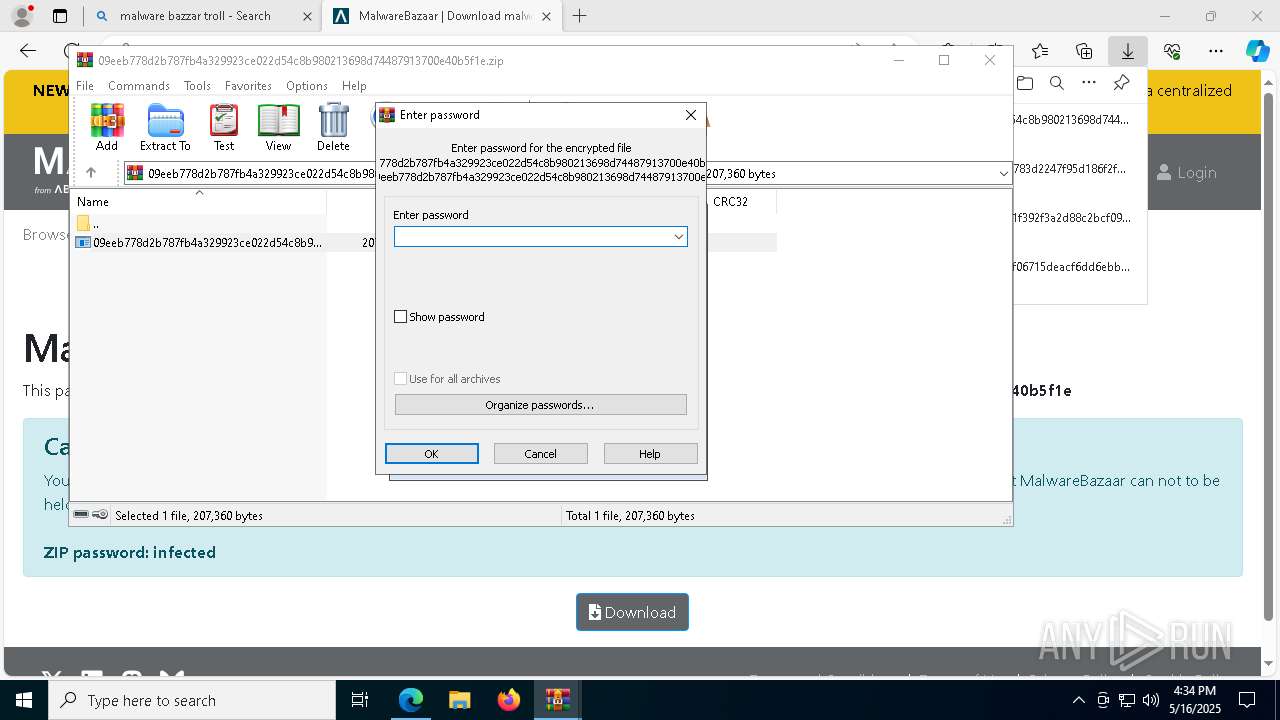
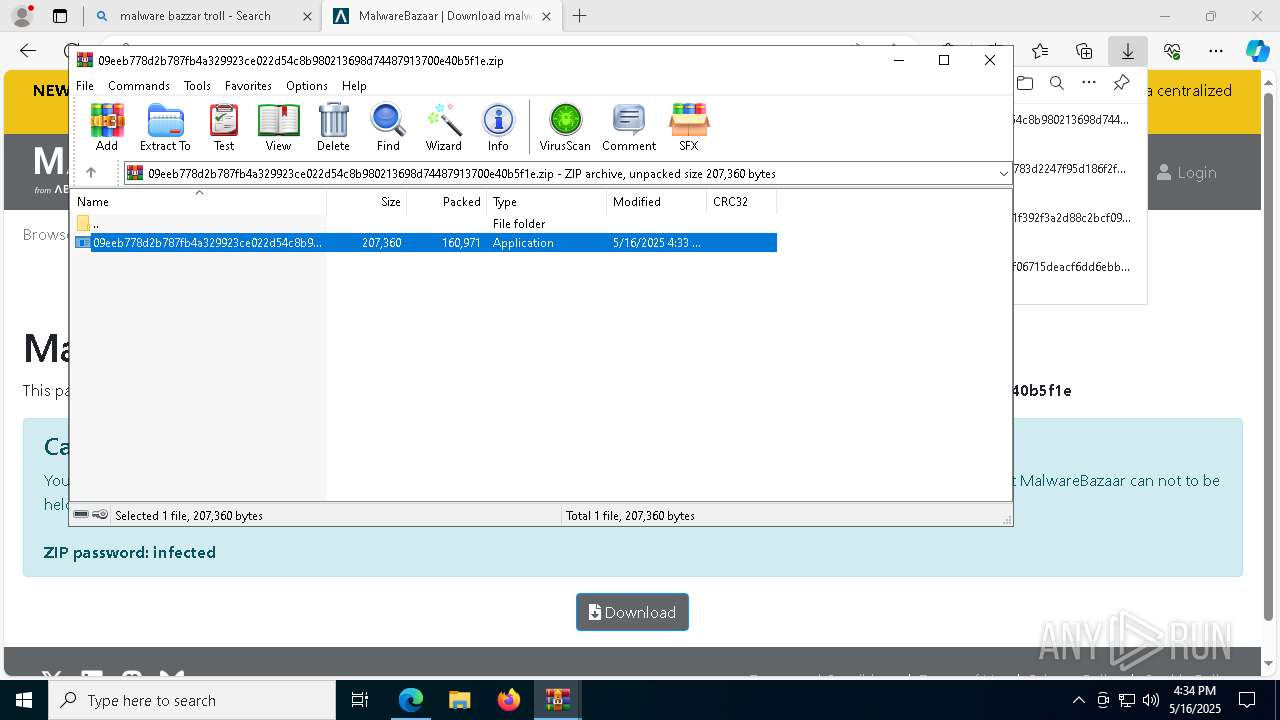
- WinRAR.exe (PID: 7828)
- ultima.exe (PID: 8628)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
- loader.exe (PID: 2288)
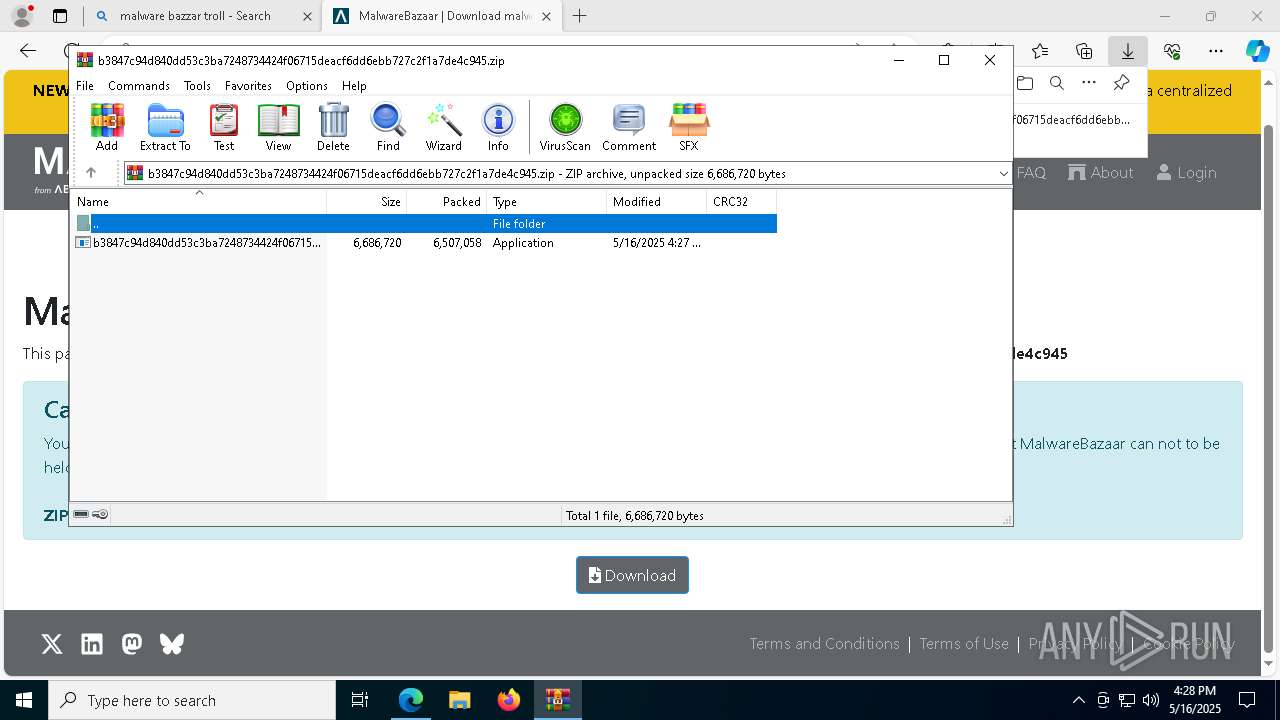
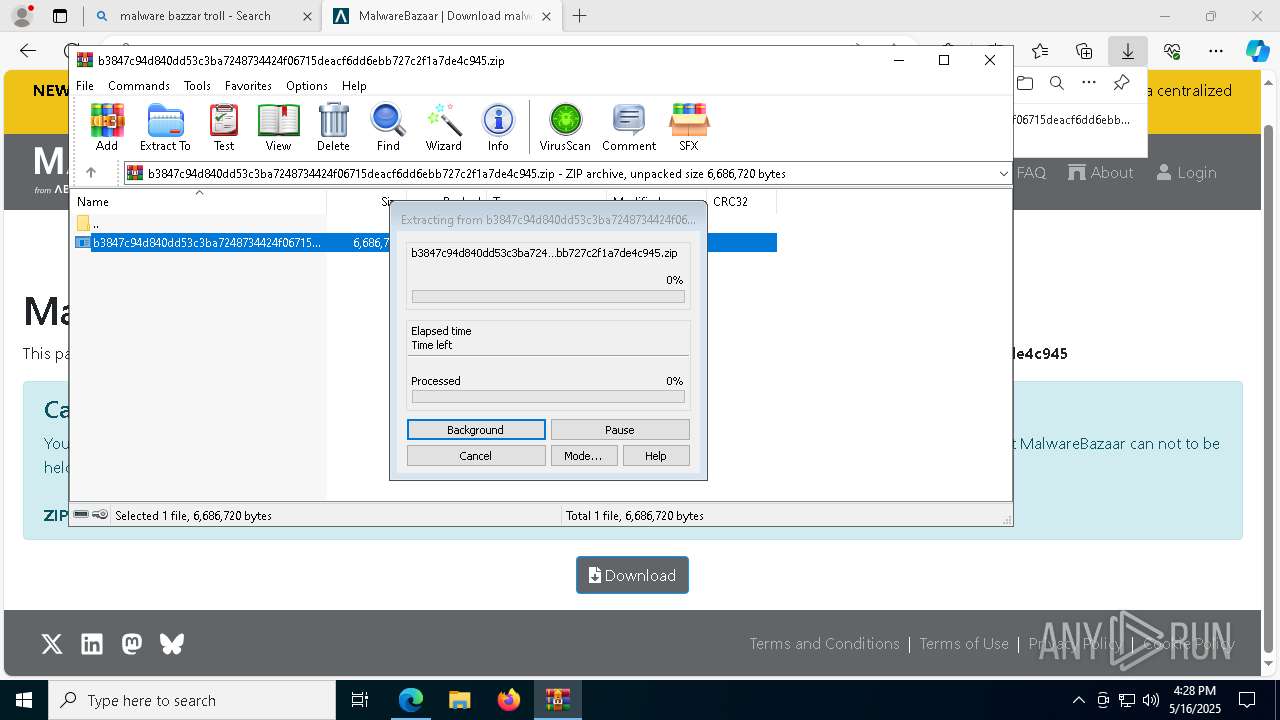
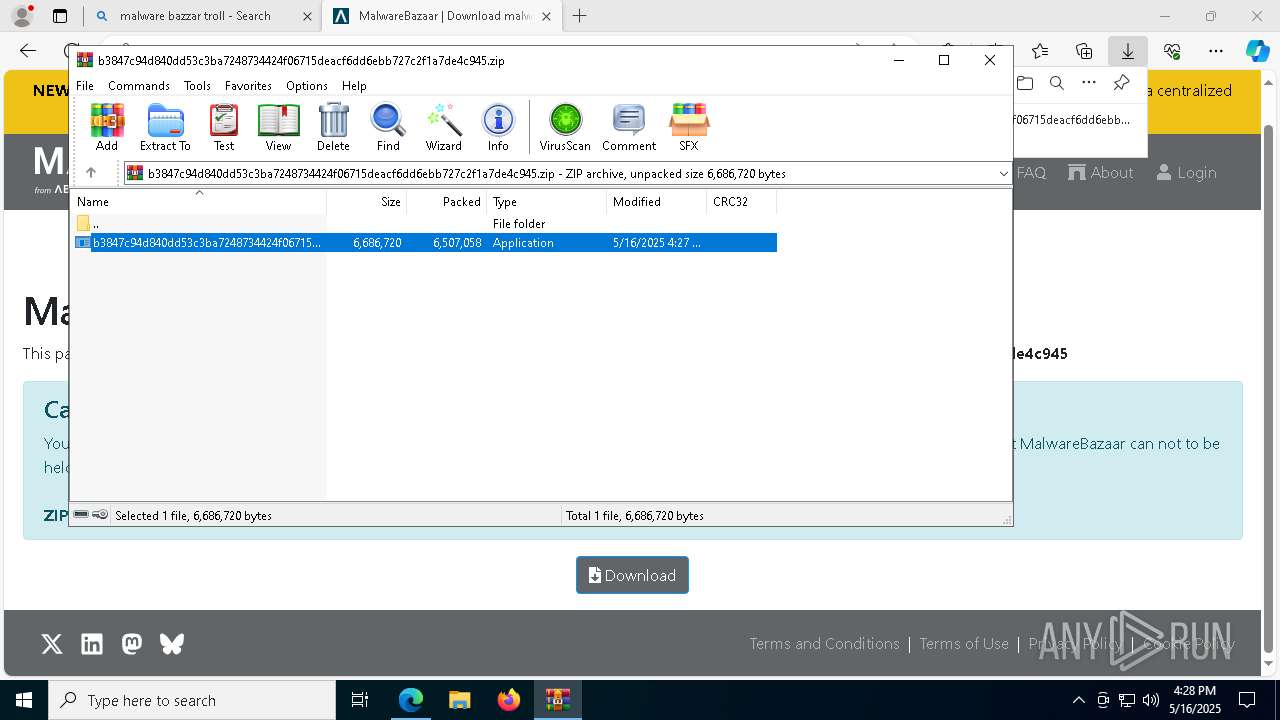
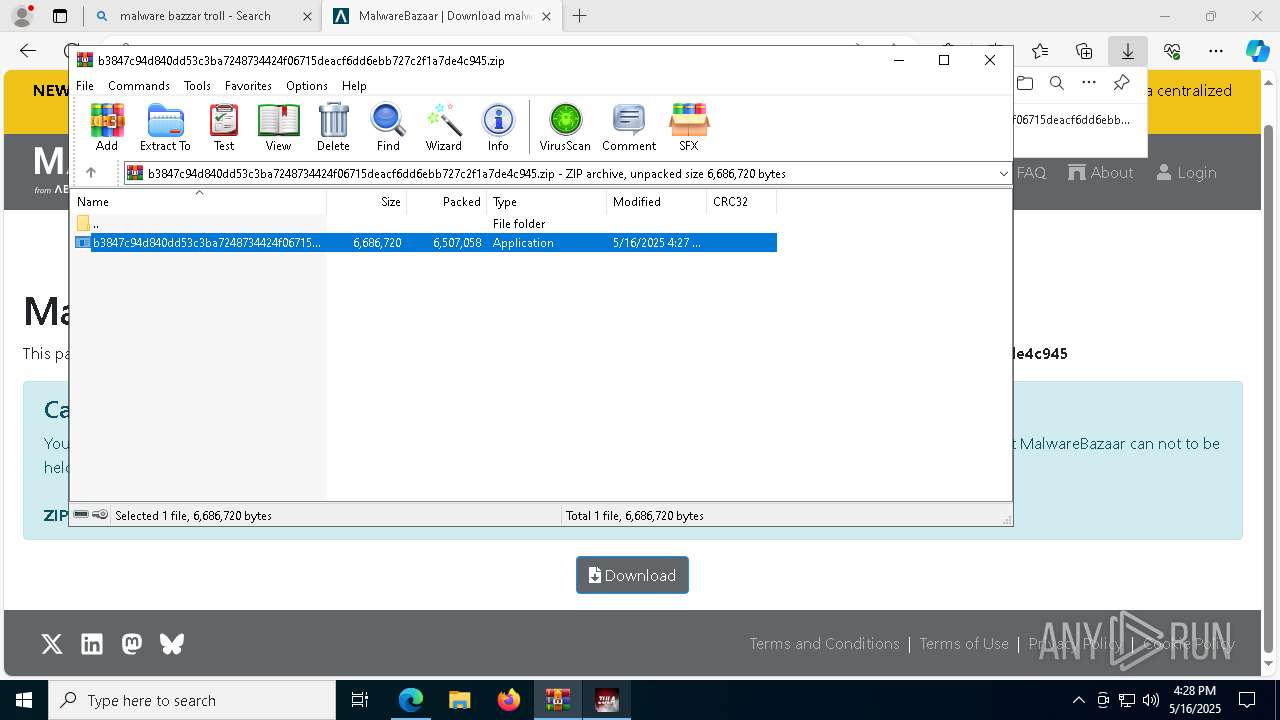
Executable content was dropped or overwritten
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
- loader.exe (PID: 2288)
- 454a0228ab3aca978bb8da603e1f1ef783d2247f95d186f2f46c5e050d12ece3.exe (PID: 6036)
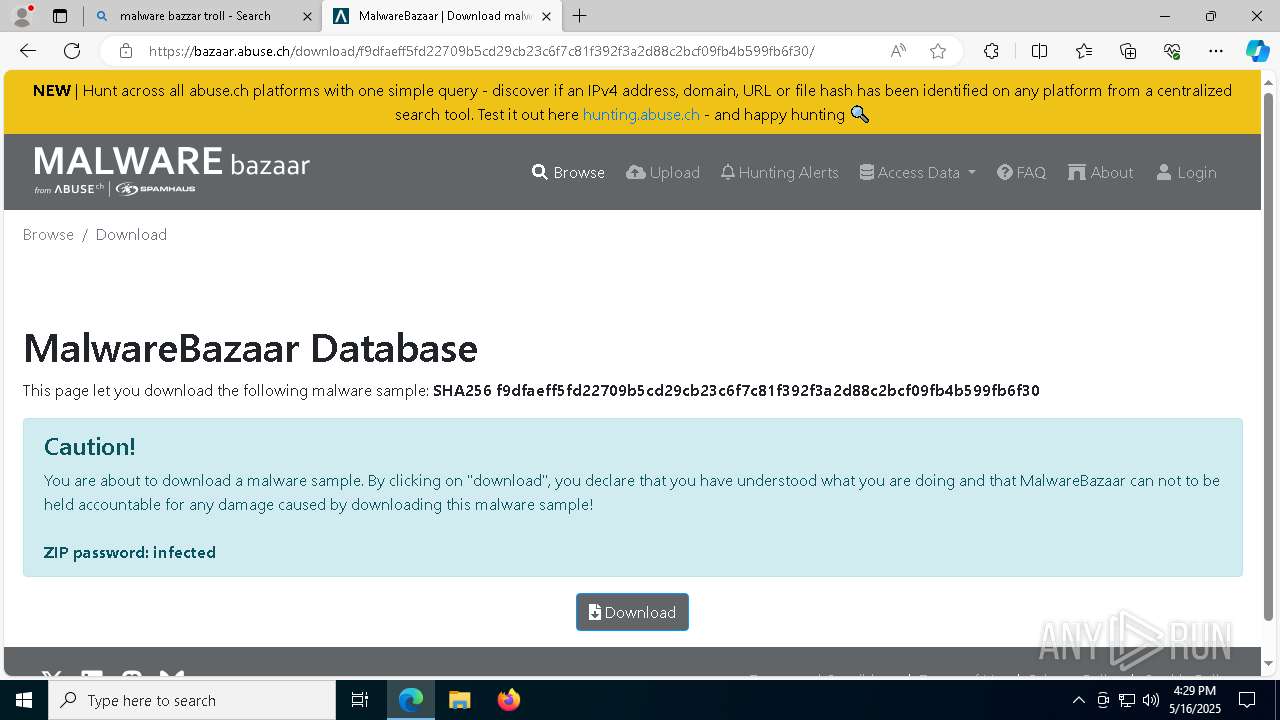
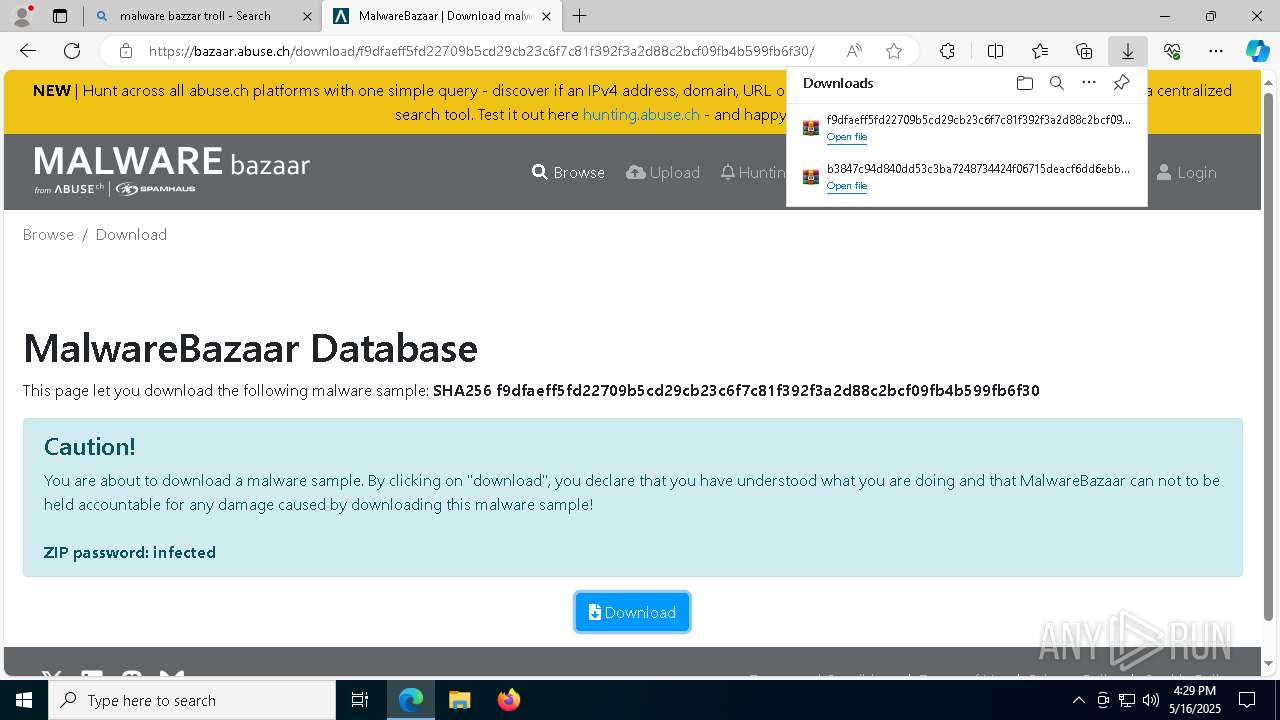
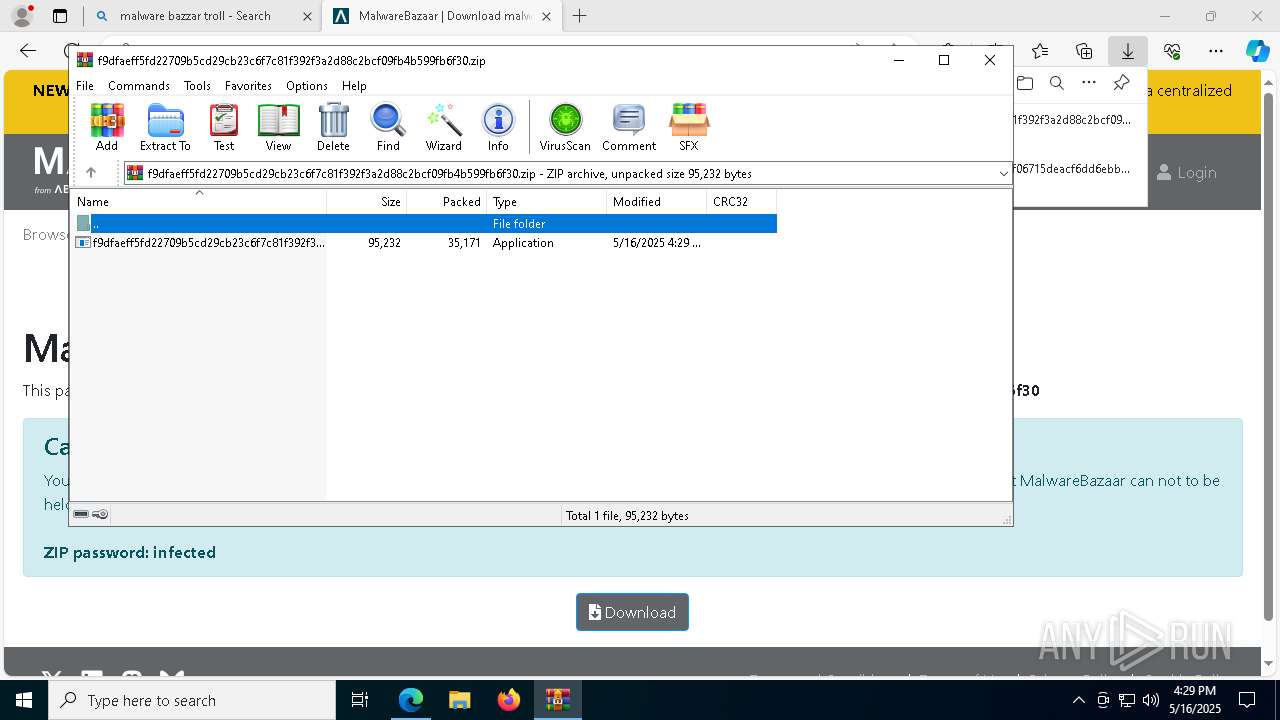
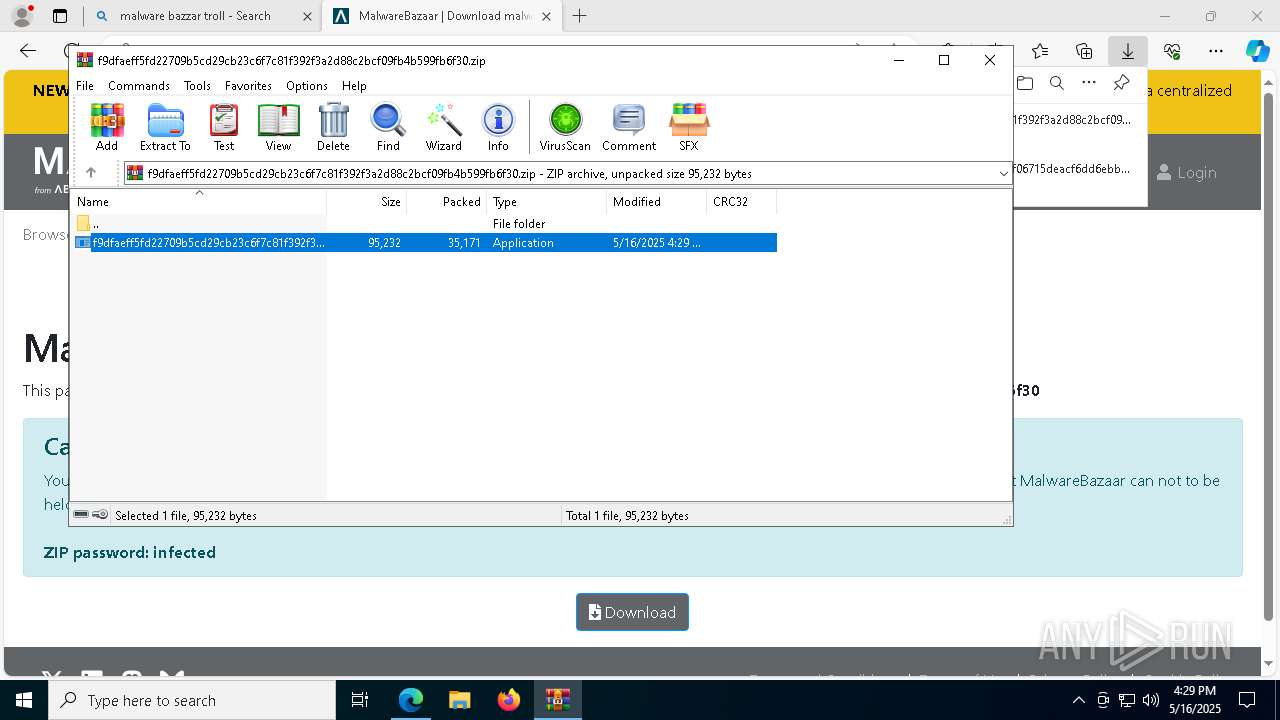
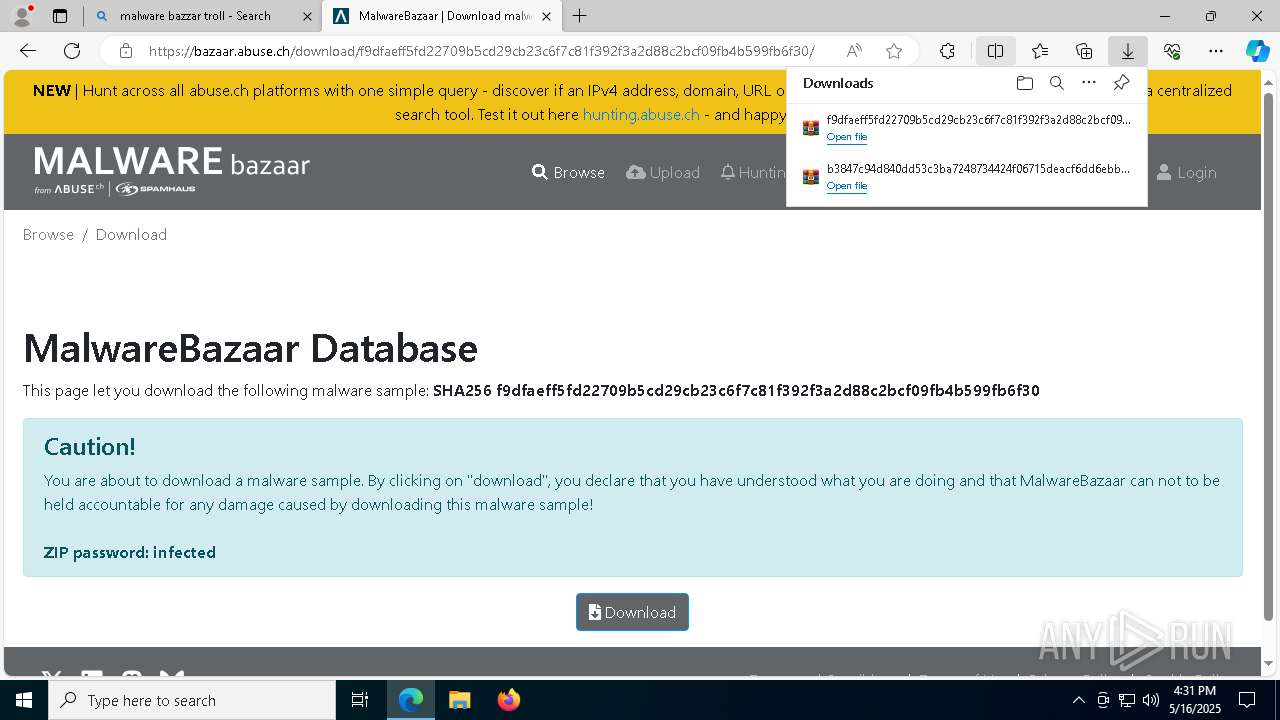
- f9dfaeff5fd22709b5cd29cb23c6f7c81f392f3a2d88c2bcf09fb4b599fb6f30.exe (PID: 1300)
- server.exe (PID: 4692)
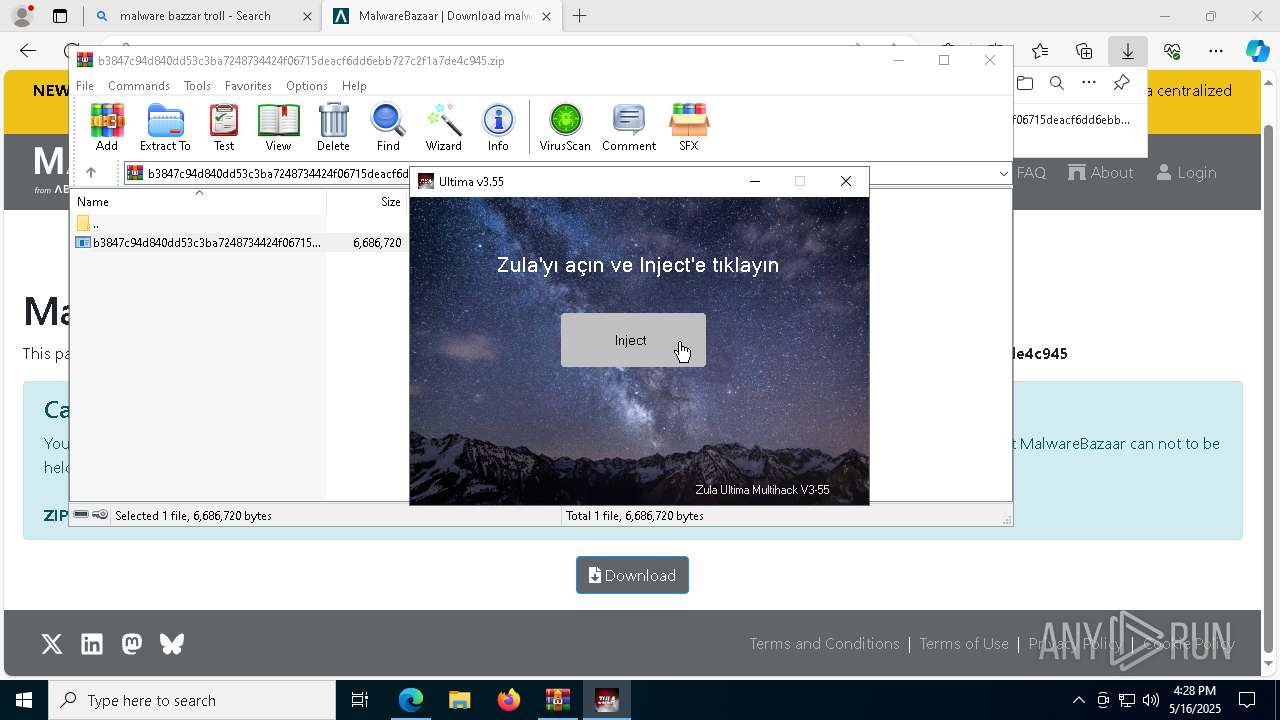
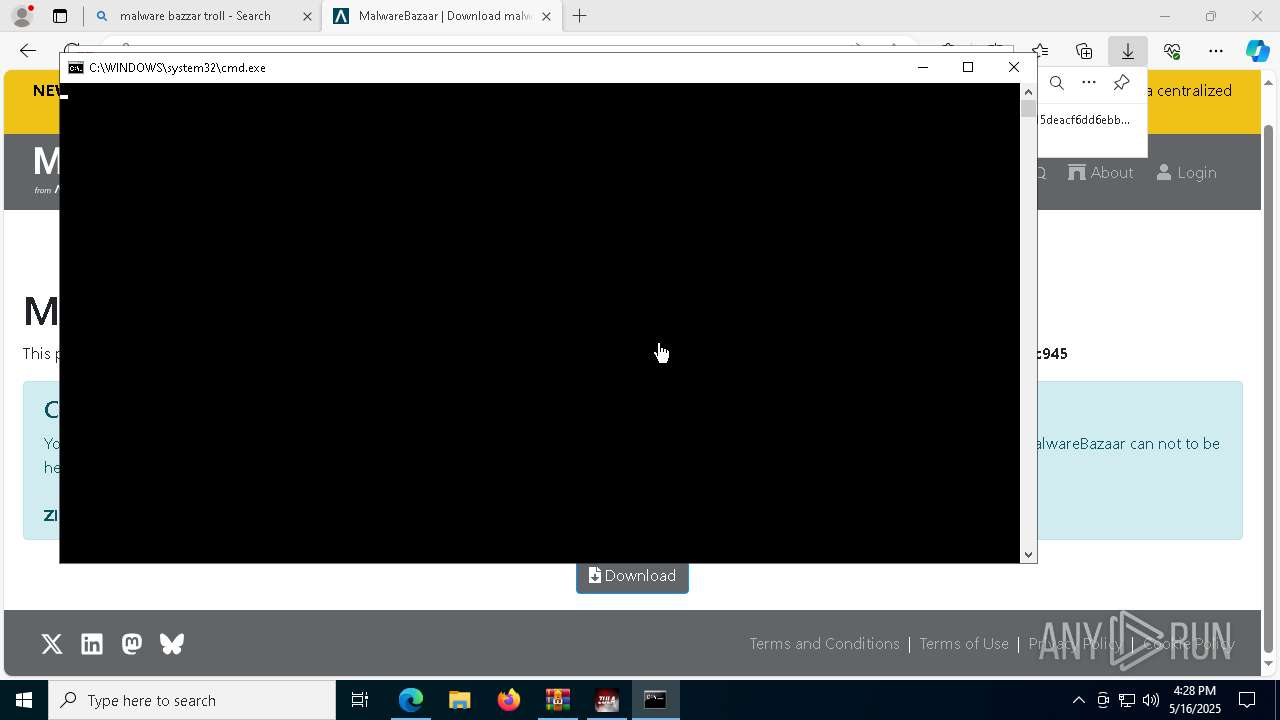
The executable file from the user directory is run by the CMD process
- loader.exe (PID: 2288)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Starts CMD.EXE for commands execution
- ultima.exe (PID: 8628)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
Executing commands from a ".bat" file
- ultima.exe (PID: 8628)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
Starts itself from another location
- loader.exe (PID: 2288)
- f9dfaeff5fd22709b5cd29cb23c6f7c81f392f3a2d88c2bcf09fb4b599fb6f30.exe (PID: 1300)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- server.exe (PID: 4692)
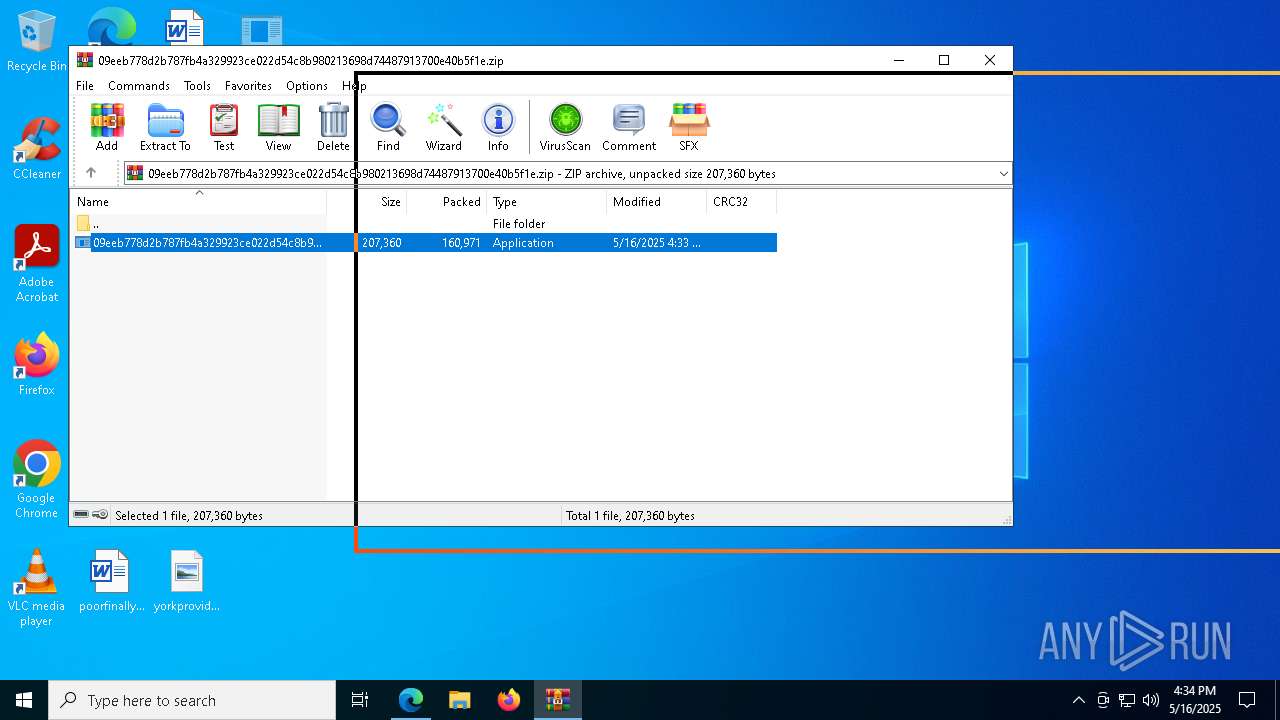
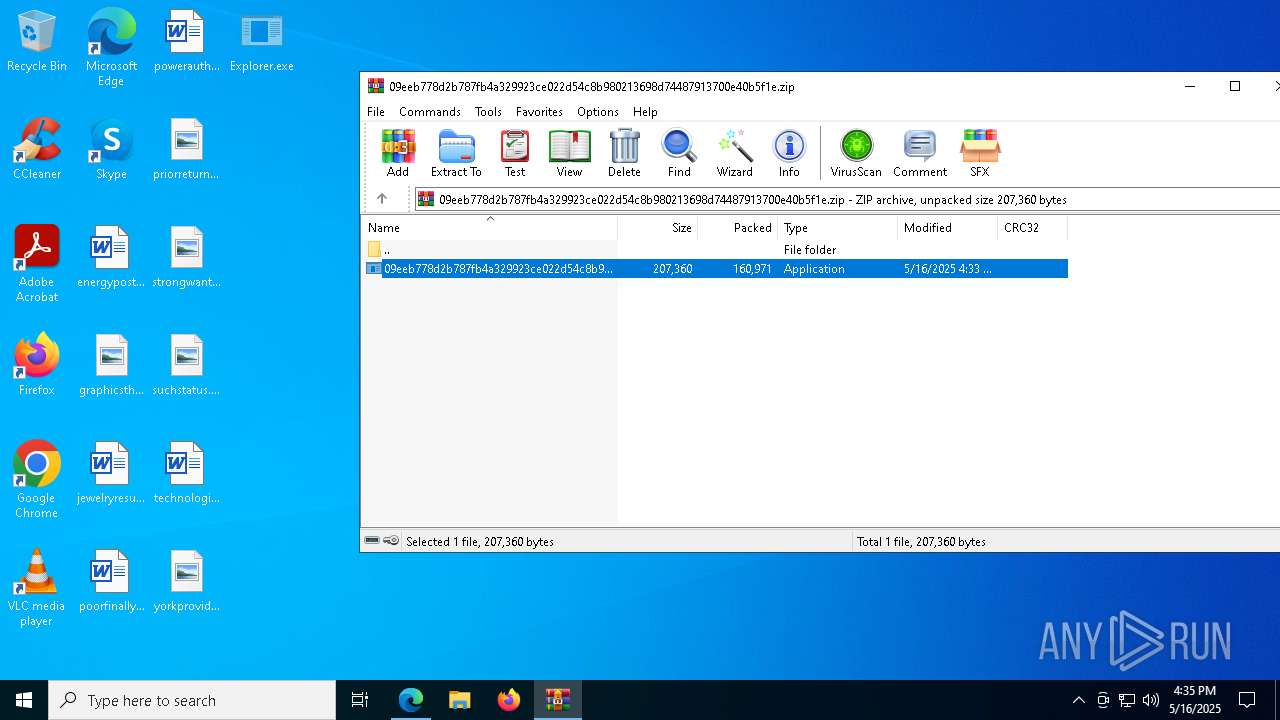
Application launched itself
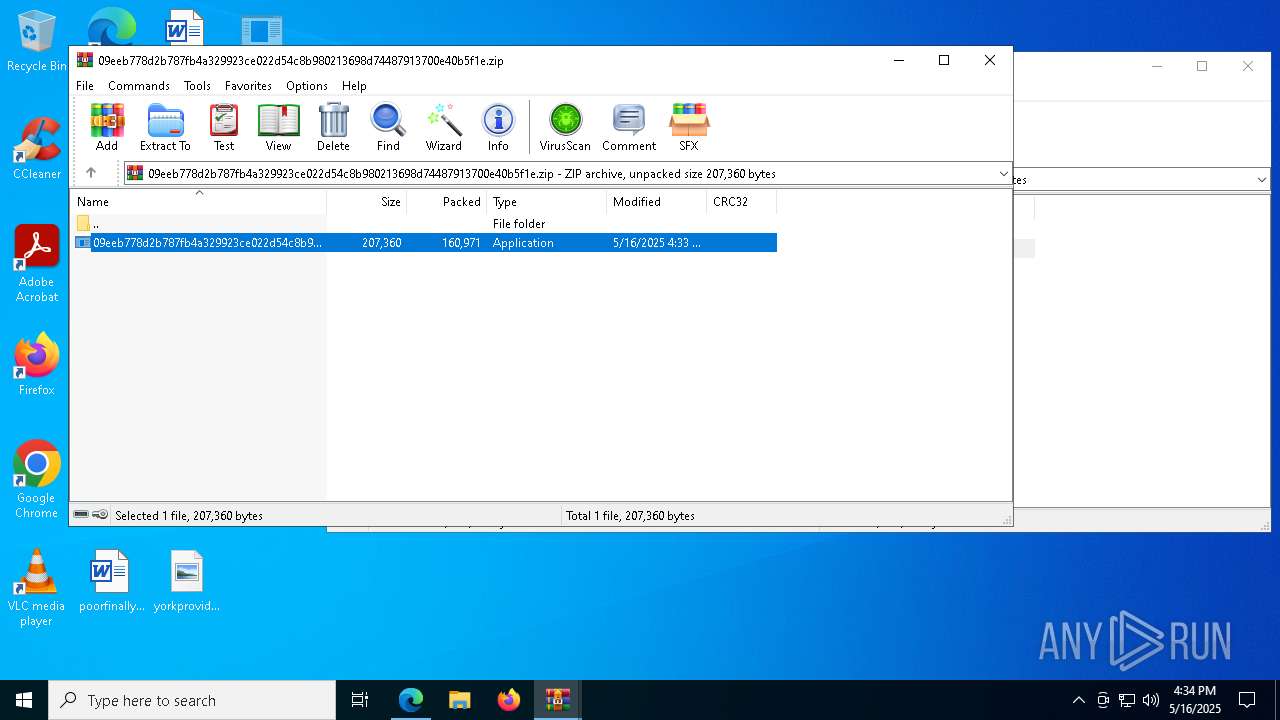
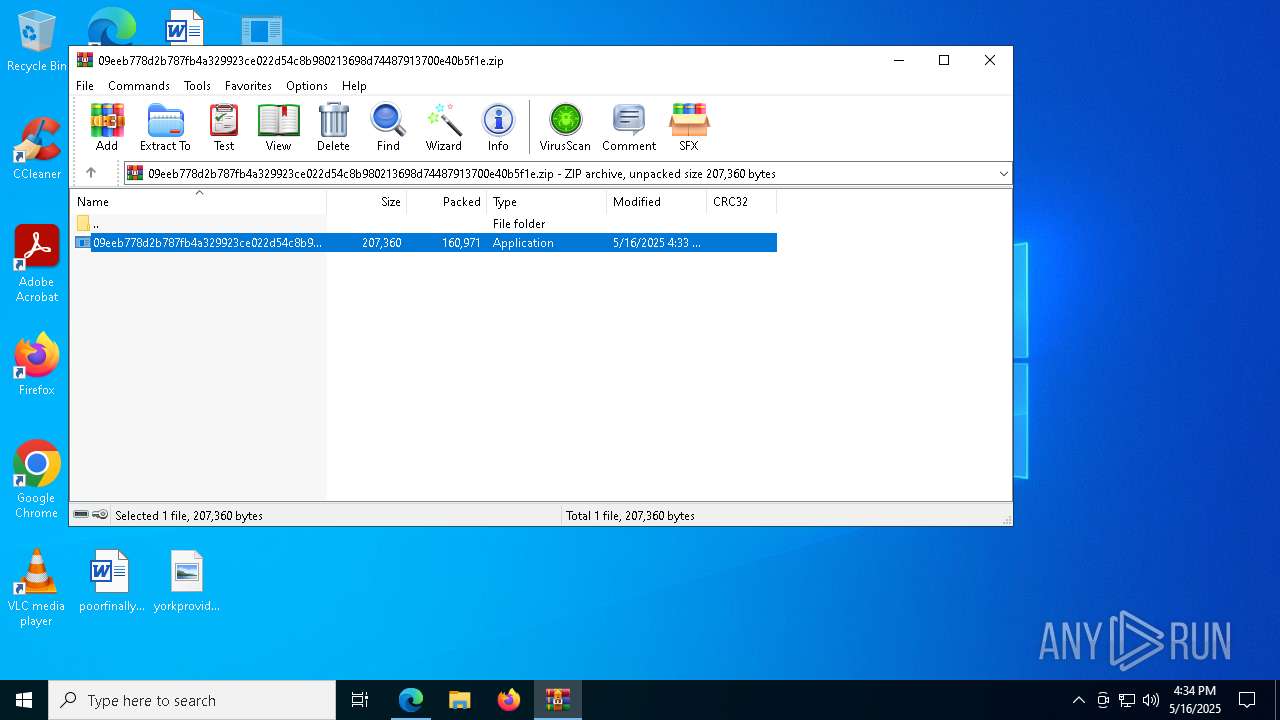
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 4980)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7944)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8024)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 3884)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5452)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7948)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8948)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 2236)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8896)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7000)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6644)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 4280)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 1504)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6516)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 908)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 3016)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8056)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8956)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8644)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5800)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 1680)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6004)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 2420)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 2968)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7684)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8328)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6792)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8348)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 3888)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5344)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5548)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8852)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8544)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6876)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 1676)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5404)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 4476)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7988)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8988)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6768)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6904)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 2192)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5044)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8340)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6676)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5980)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7728)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 3708)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8944)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8928)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8872)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5944)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5360)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 3744)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 4052)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5348)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8064)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8664)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 7468)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8624)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 6800)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 8568)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 4376)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 1128)
- 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe (PID: 5952)
Uses NETSH.EXE to add a firewall rule or allowed programs
- server.exe (PID: 4692)
Probably fake Windows Update file has been dropped
- server.exe (PID: 4692)
Connects to unusual port
- 454a0228ab3aca978bb8da603e1f1ef783d2247f95d186f2f46c5e050d12ece3.exe (PID: 6036)
INFO
Application launched itself
- msedge.exe (PID: 6044)
Checks supported languages
- identity_helper.exe (PID: 5892)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
- loader.exe (PID: 2288)
- ultima.exe (PID: 8628)
- msdcsc.exe (PID: 536)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
Reads Environment values
- identity_helper.exe (PID: 5892)
Reads the software policy settings
- slui.exe (PID: 8180)
- slui.exe (PID: 7012)
Reads the computer name
- identity_helper.exe (PID: 5892)
- ultima.exe (PID: 8628)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
- loader.exe (PID: 2288)
- msdcsc.exe (PID: 536)
- loader.exe (PID: 7724)
- loader.exe (PID: 7720)
- loader.exe (PID: 7656)
- loader.exe (PID: 4016)
- loader.exe (PID: 3992)
- loader.exe (PID: 1128)
- loader.exe (PID: 3008)
The sample compiled with english language support
- msedge.exe (PID: 6044)
- WinRAR.exe (PID: 7828)
- msedge.exe (PID: 7784)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6044)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7828)
- msedge.exe (PID: 7784)
- WinRAR.exe (PID: 5244)
- WinRAR.exe (PID: 744)
- WinRAR.exe (PID: 8624)
Create files in a temporary directory
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
Checks proxy server information
- slui.exe (PID: 7012)
Reads the machine GUID from the registry
- ultima.exe (PID: 8628)
Process checks computer location settings
- ultima.exe (PID: 8628)
- b3847c94d840dd53c3ba7248734424f06715deacf6dd6ebb727c2f1a7de4c945.exe (PID: 8472)
- loader.exe (PID: 2288)
Connects to unusual port
- iexplore.exe (PID: 5740)
Manual execution by a user
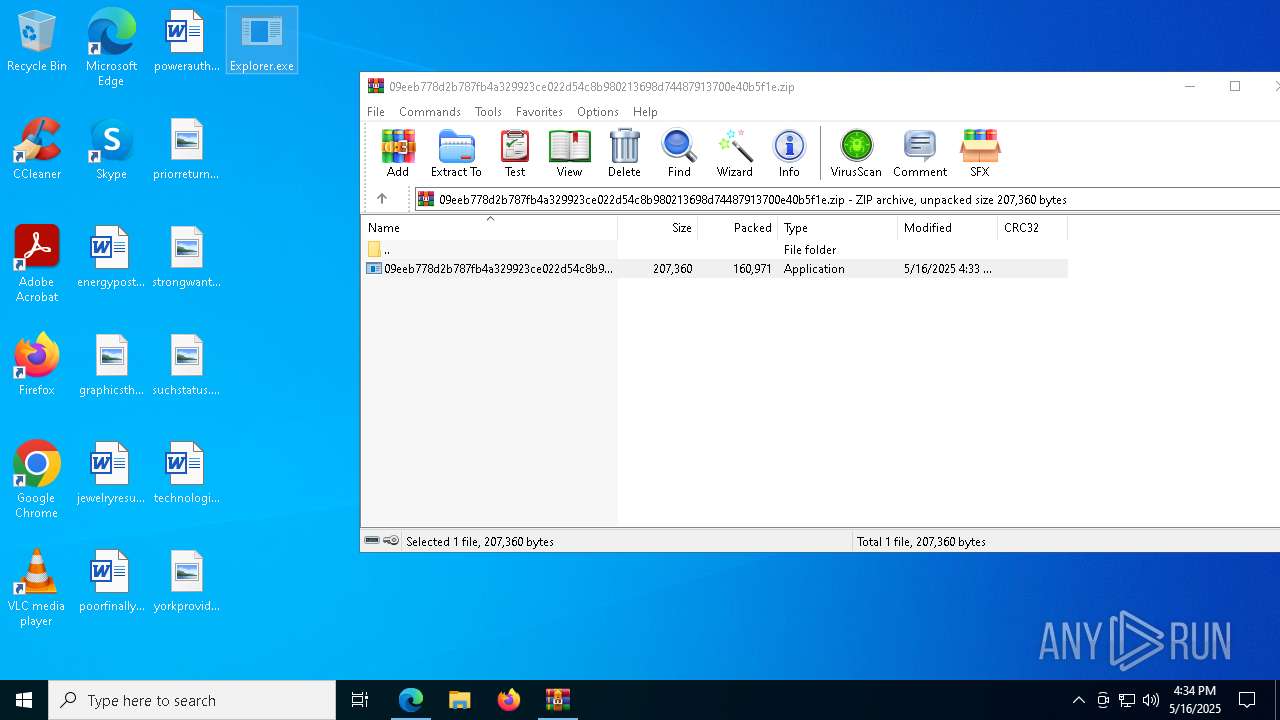
- Explorer.exe (PID: 1856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(4692) server.exe
C2susiahat24199a.ddns.net
Ports5552
BotnetHacKed
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\a8f08fa23dbc544d76787e679872404a
Splitter|'|'|
Version0.7d
Total processes
334
Monitored processes
194
Malicious processes
28
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc87fa5fd8,0x7ffc87fa5fe4,0x7ffc87fa5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | loader.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: HIGH Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7912 --field-trial-handle=2416,i,744362438227571896,8038634636045042728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
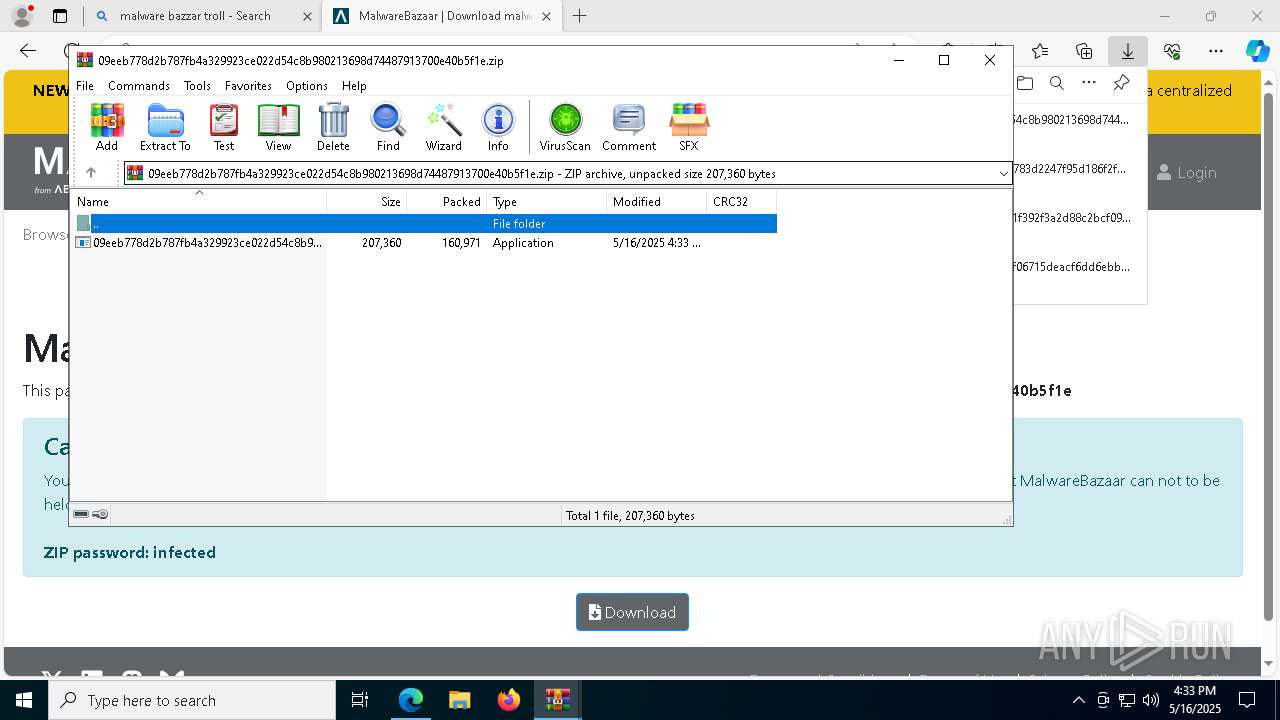
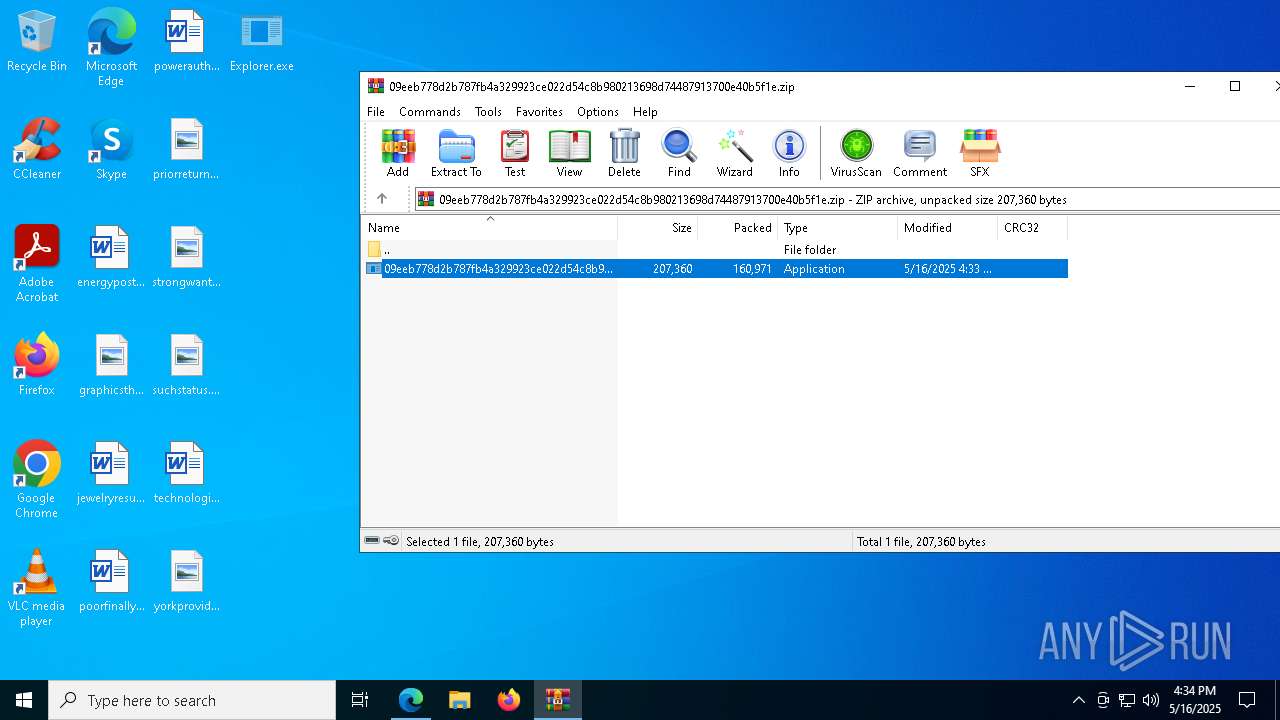
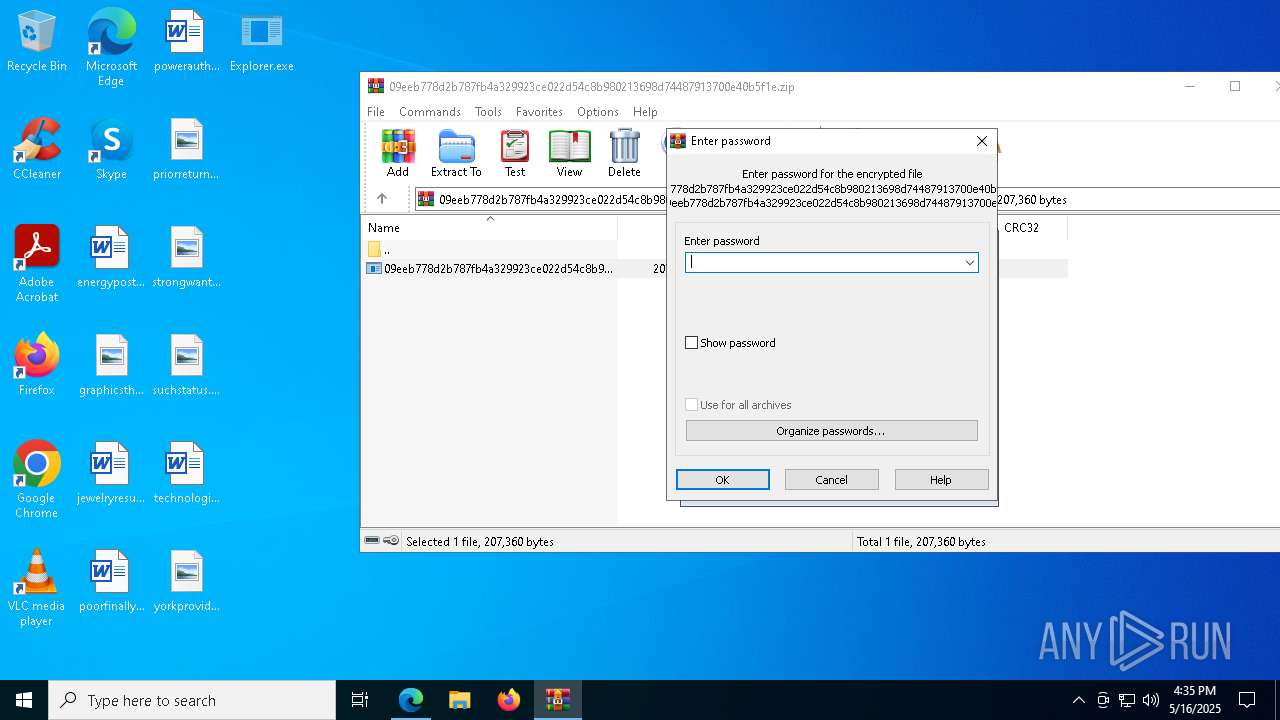
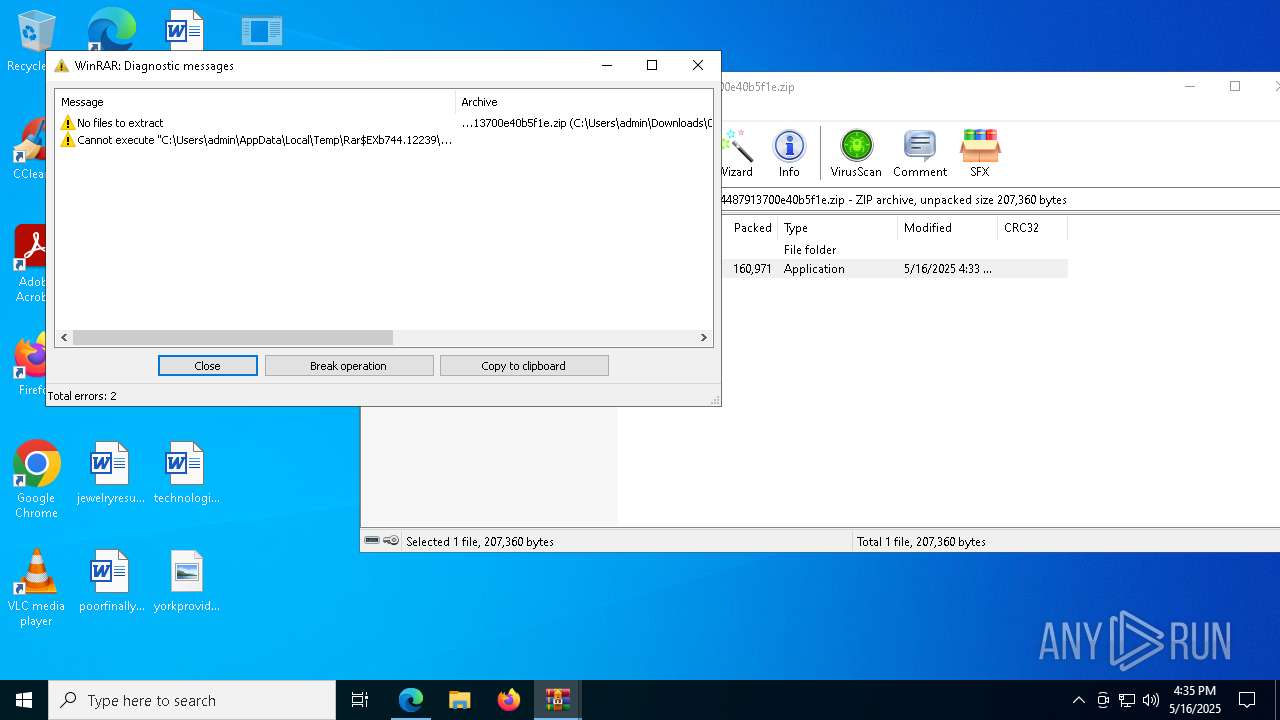
| 744 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6304 --field-trial-handle=2416,i,744362438227571896,8038634636045042728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6560 --field-trial-handle=2416,i,744362438227571896,8038634636045042728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4332 --field-trial-handle=2416,i,744362438227571896,8038634636045042728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=8780 --field-trial-handle=2416,i,744362438227571896,8038634636045042728,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 908 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb744.4449\09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb744.4449\09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe | — | 09eeb778d2b787fb4a329923ce022d54c8b980213698d74487913700e40b5f1e.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
51 193
Read events
50 886
Write events
289
Delete events
18
Modification events
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4769FD85D9932F00 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C204A16F-030D-4C29-AD85-680D63045151} | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {684DCF87-D521-4197-9058-A0E154A3064D} | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6EFFF185D9932F00 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DF393186D9932F00 | |||
| (PID) Process: | (6044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {396ABC90-CE37-4451-B5CA-D0F028CE58C0} | |||
Executable files
47
Suspicious files
637
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bd85.TMP | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
1 176
DNS requests
237
Threats
125
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8472 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2852 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747693644&P2=404&P3=2&P4=LHul8Q2oWb5mY3HwdW13RHYP%2bqy0tbPCMwFREOsgGbEKCN5M8pOsktoZF7ovZObPVSf386u9ErRiXvB6%2fugbQA%3d%3d | unknown | — | — | whitelisted |
8472 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2852 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747693644&P2=404&P3=2&P4=LHul8Q2oWb5mY3HwdW13RHYP%2bqy0tbPCMwFREOsgGbEKCN5M8pOsktoZF7ovZObPVSf386u9ErRiXvB6%2fugbQA%3d%3d | unknown | — | — | whitelisted |
2852 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747693644&P2=404&P3=2&P4=LHul8Q2oWb5mY3HwdW13RHYP%2bqy0tbPCMwFREOsgGbEKCN5M8pOsktoZF7ovZObPVSf386u9ErRiXvB6%2fugbQA%3d%3d | unknown | — | — | whitelisted |
2852 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747693644&P2=404&P3=2&P4=UtpAbIvCQ11Oedorgs7x4rT%2bRhfWMA9PupC9TyNybZBanRYuR1b19AMySNsDbPGaexMo1WI8YjmoMql2ikxhTw%3d%3d | unknown | — | — | whitelisted |
2852 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747693644&P2=404&P3=2&P4=UtpAbIvCQ11Oedorgs7x4rT%2bRhfWMA9PupC9TyNybZBanRYuR1b19AMySNsDbPGaexMo1WI8YjmoMql2ikxhTw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7368 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6044 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7368 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7368 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7368 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
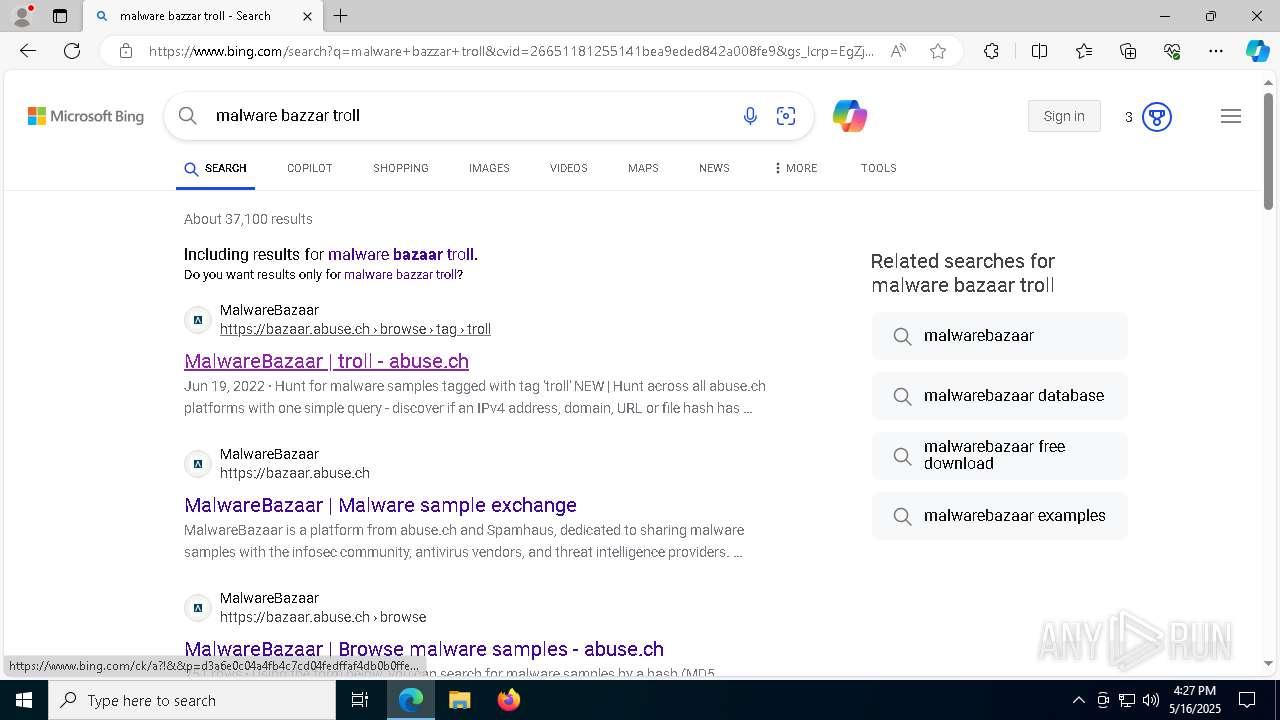
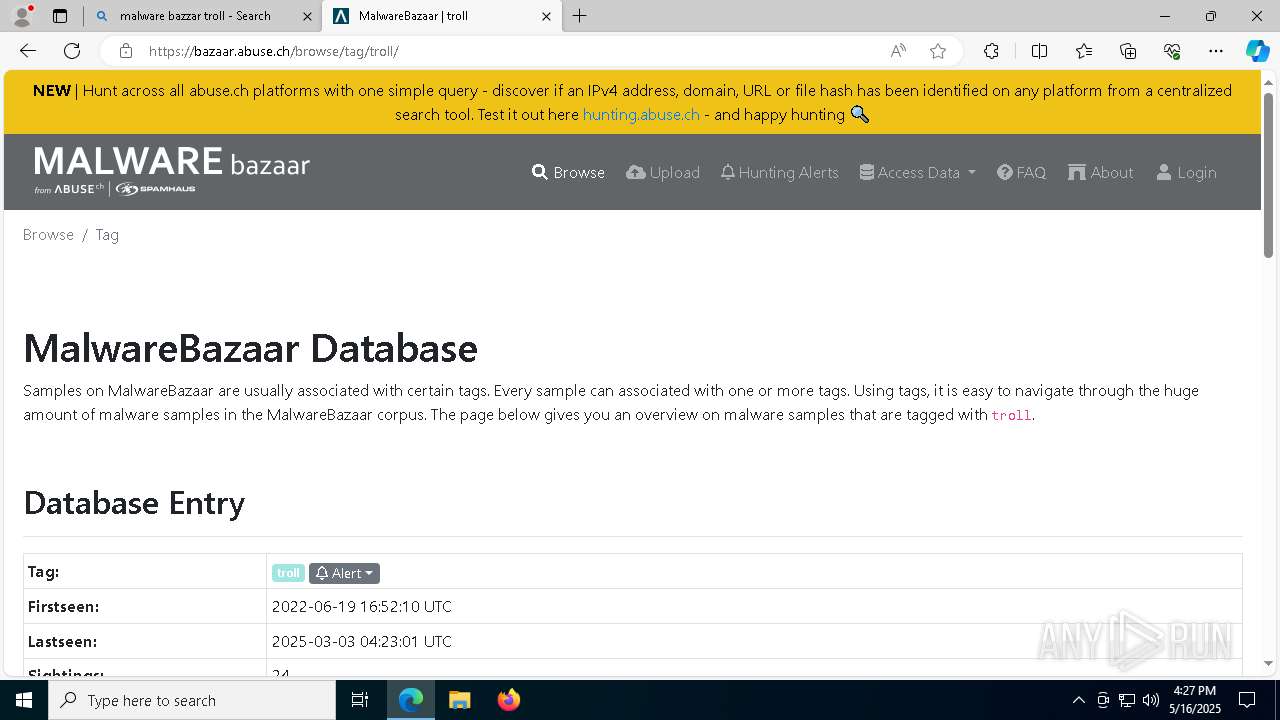
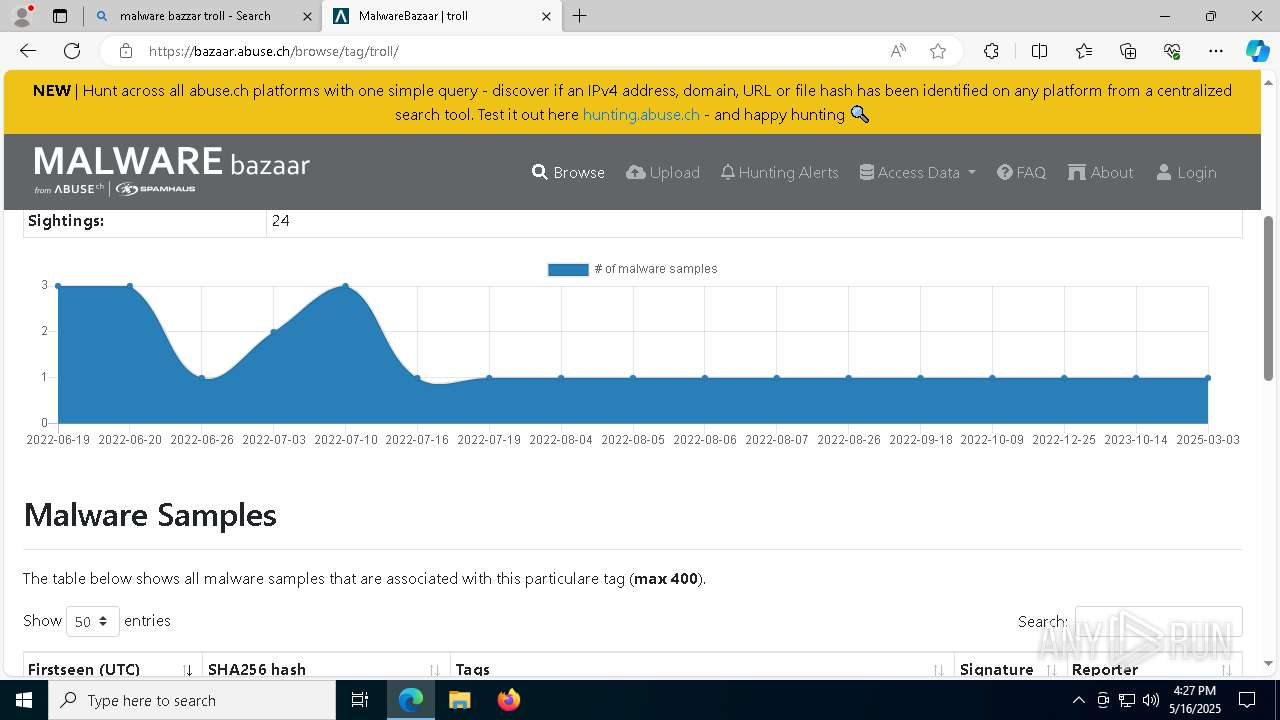
bazaar.abuse.ch |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7368 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |