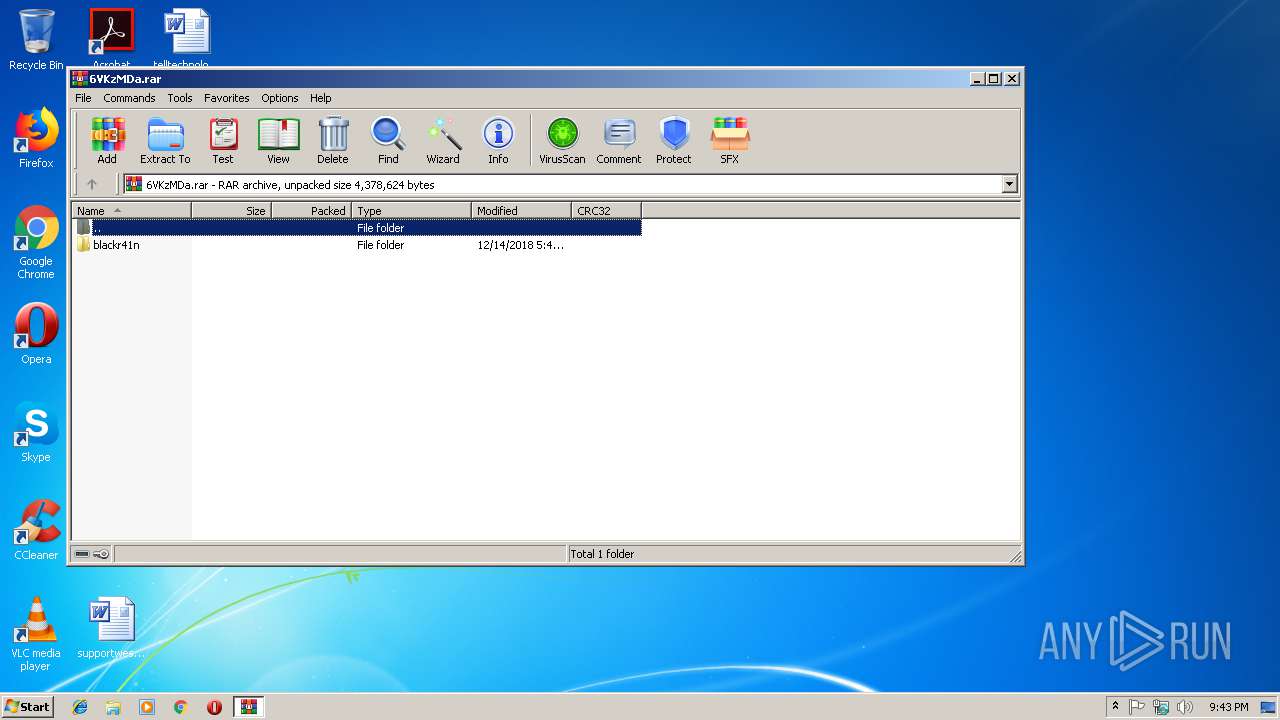
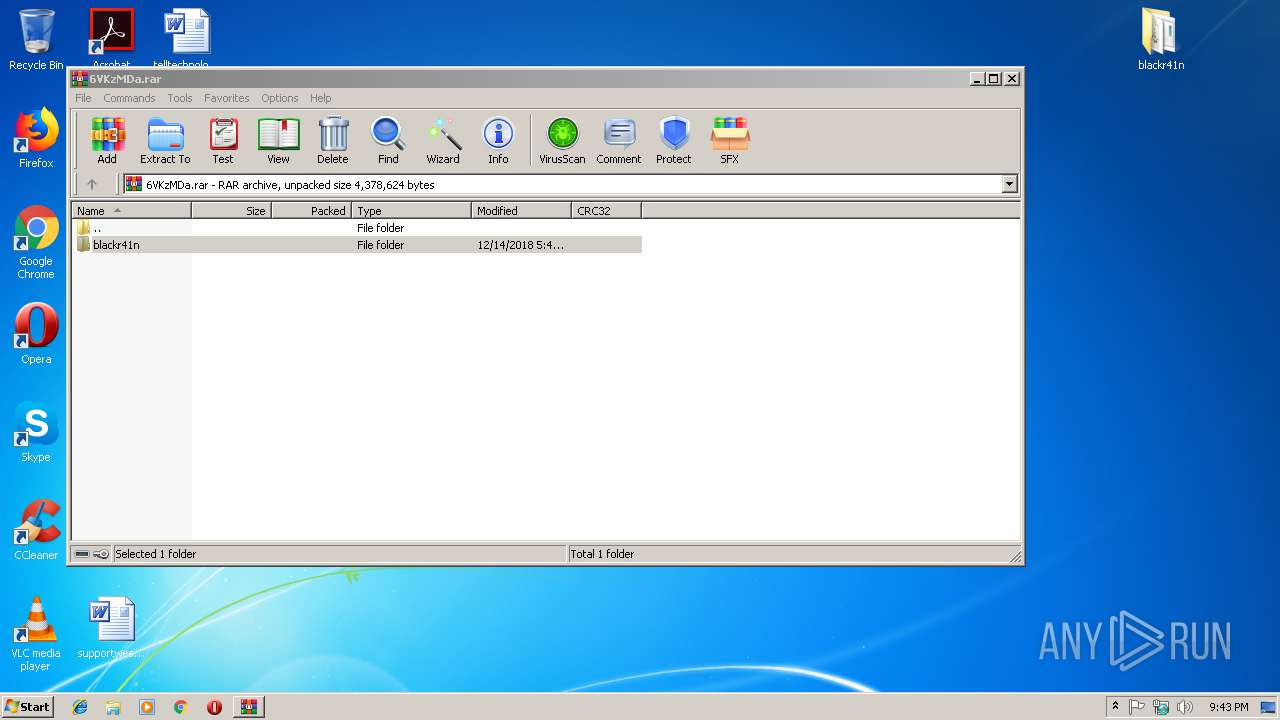
| File name: | 6VKzMDa.rar |
| Full analysis: | https://app.any.run/tasks/d90bb5dc-8ab7-44c8-8d33-8414f7edcf52 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | December 14, 2018, 21:43:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 076728C8745E78F4CEEF2E9A389BD46A |
| SHA1: | 1285FFB3D25E6600CBC11F097B06464090E6D421 |
| SHA256: | DD20C9220B1A26B0C98CAC348FBE3D0220A33981F3C8AC42F6AB0C05770D3577 |
| SSDEEP: | 49152:nMmKXqcvSTF8TB+pY9IMtXNR5GVjqHe0/7YEupEf15/XzGZWP:nPzc6R8TuYXNR5GNqHH/9bjGgP |
MALICIOUS
Orcus was detected
- Regasm.exe (PID: 2840)
- Regasm.exe (PID: 3020)
- Regasm.exe (PID: 3212)
- Regasm.exe (PID: 1376)
- Regasm.exe (PID: 4076)
- Regasm.exe (PID: 1084)
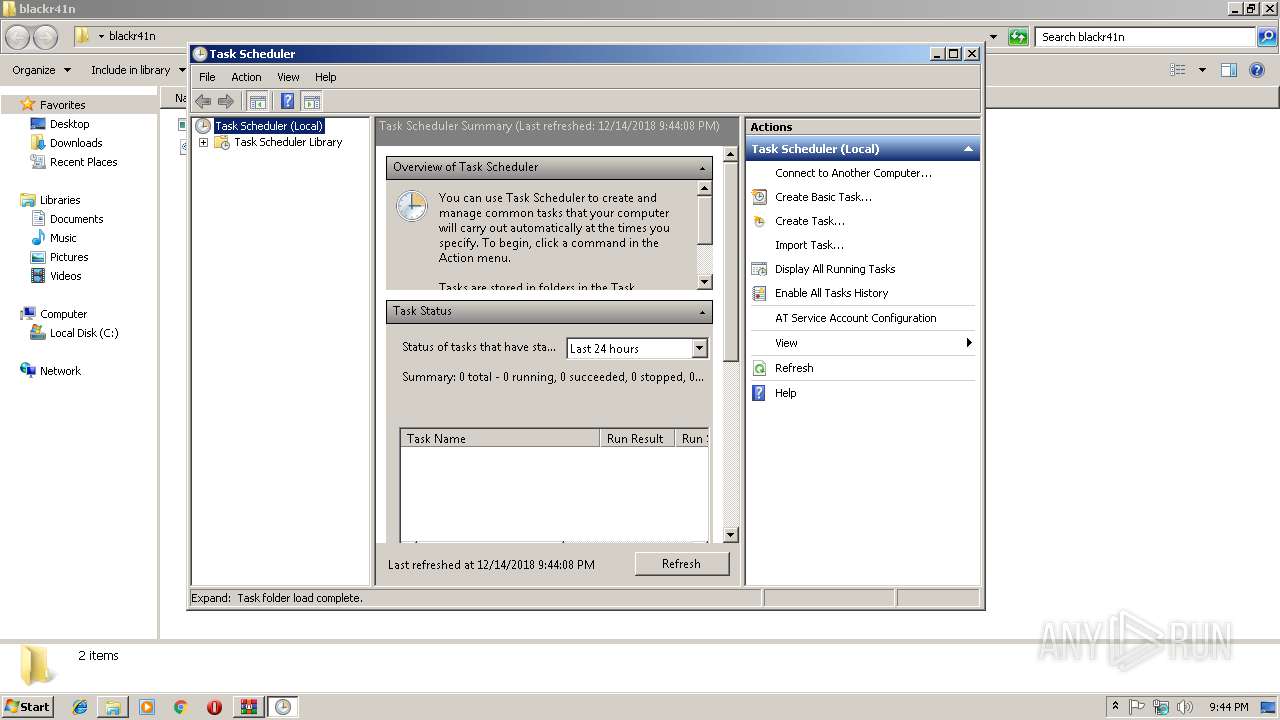
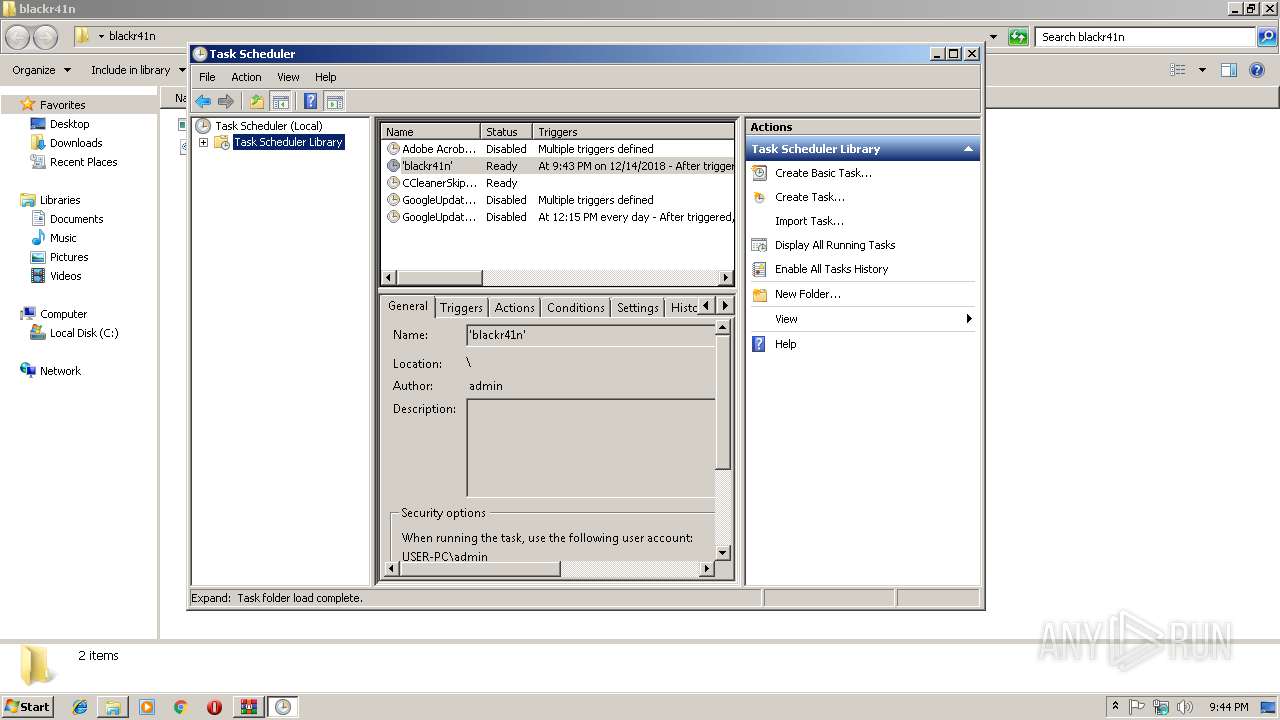
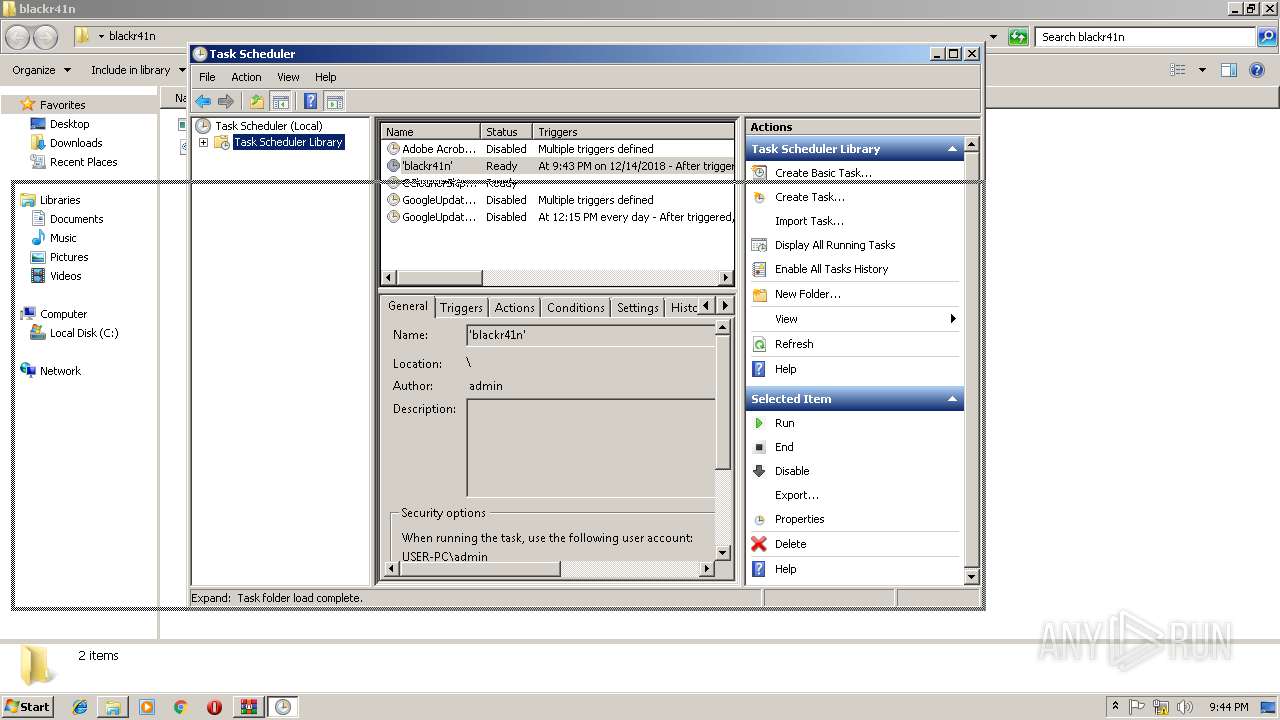
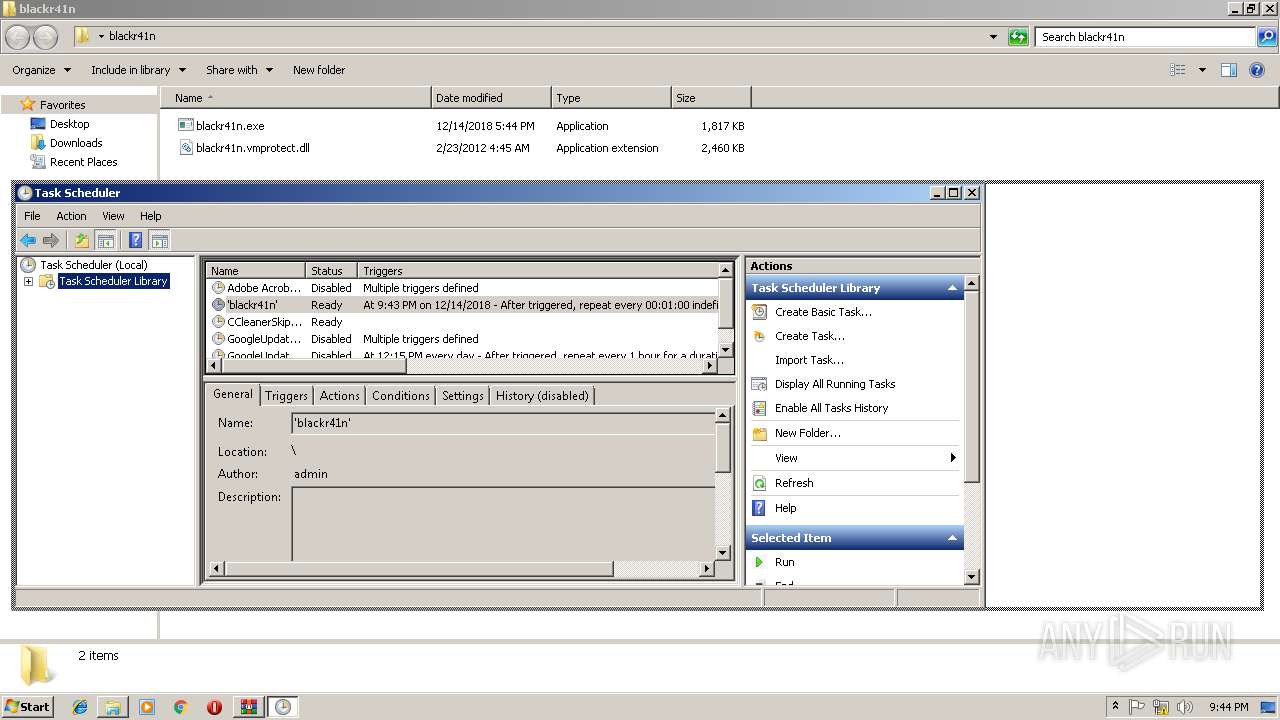
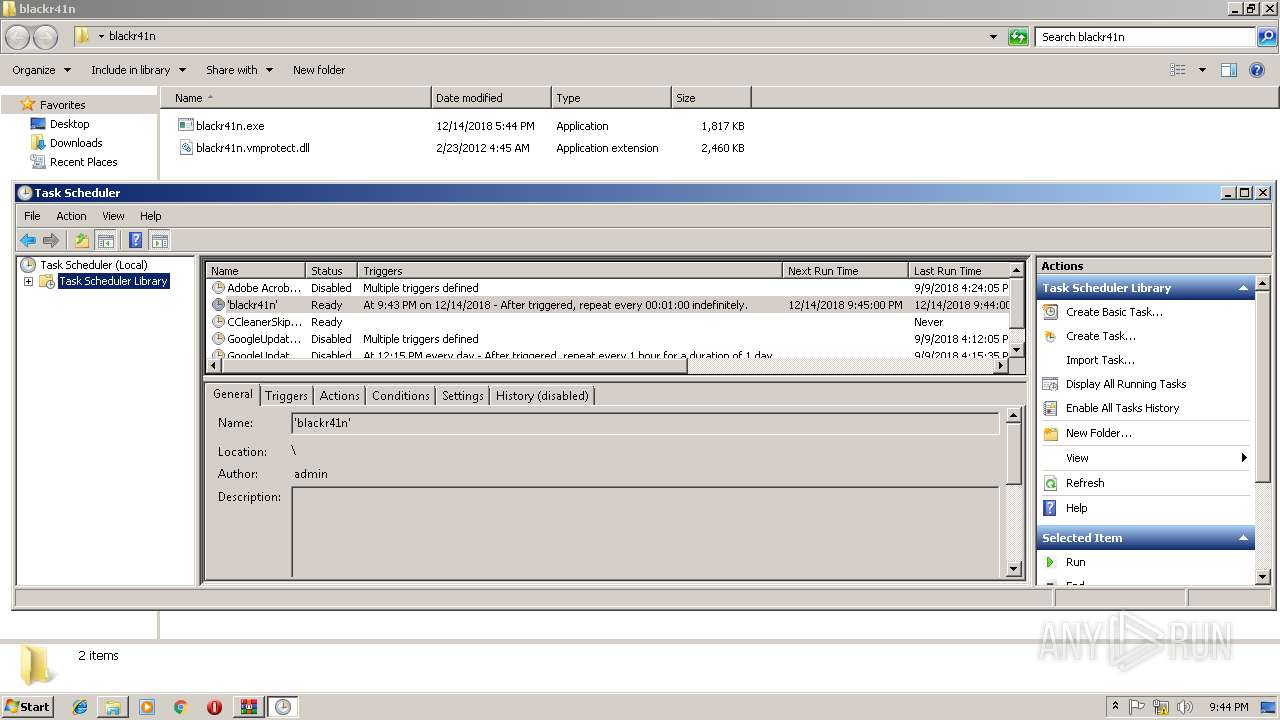
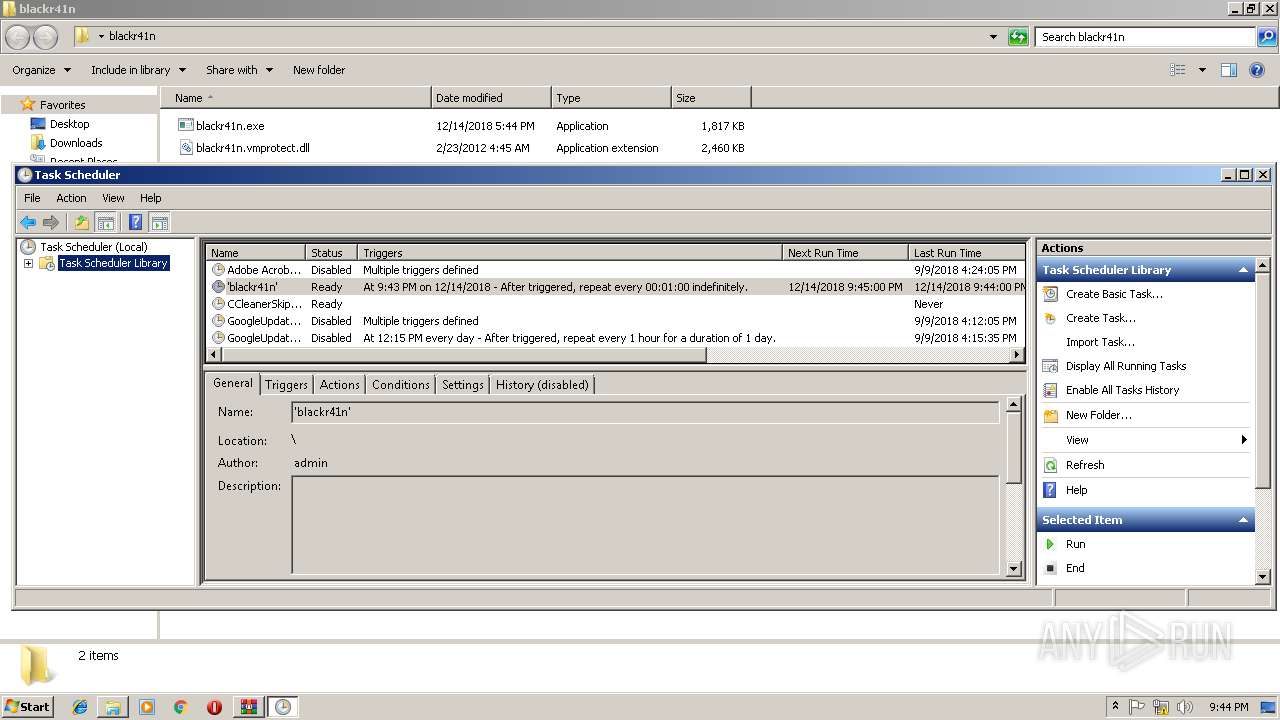
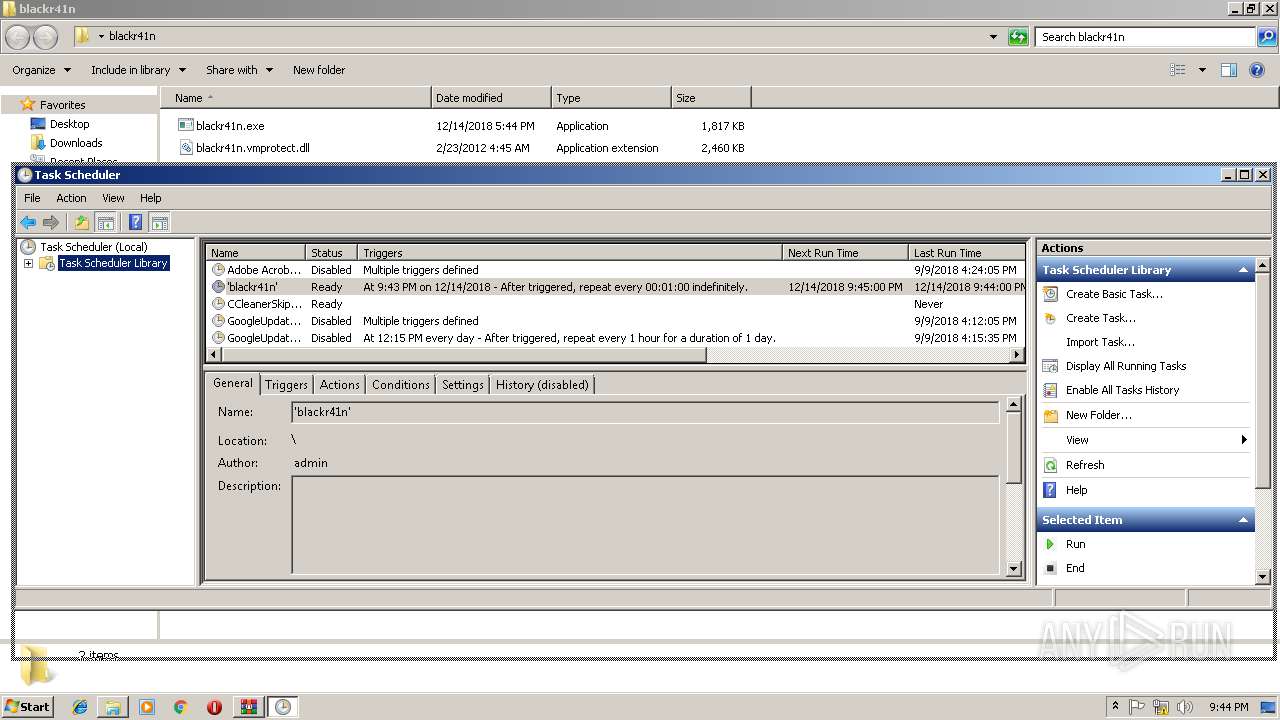
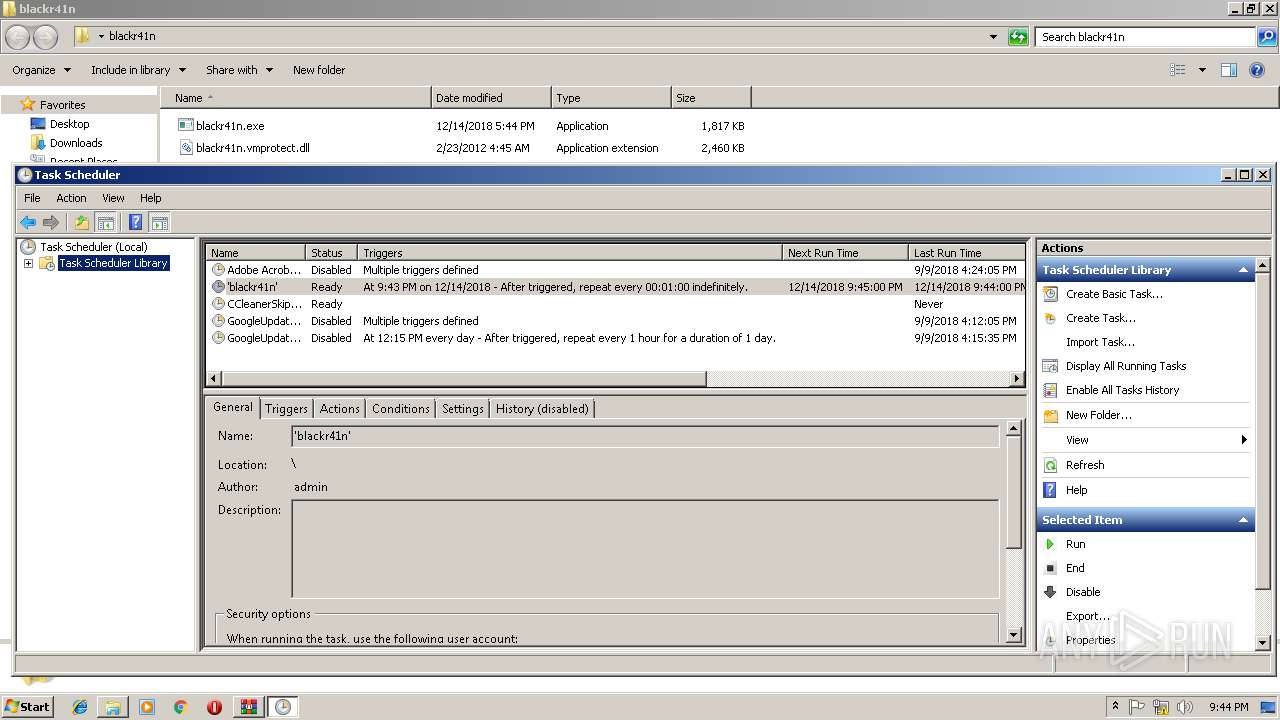
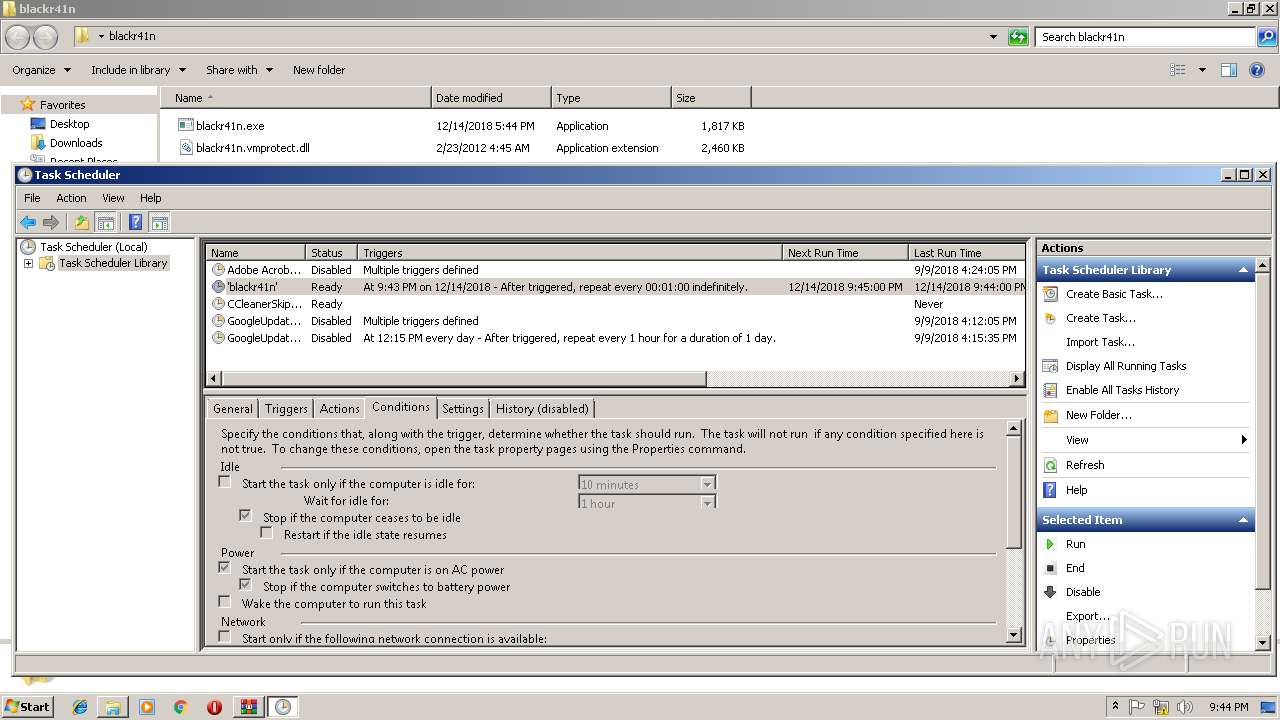
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3668)
- mmc.exe (PID: 3068)
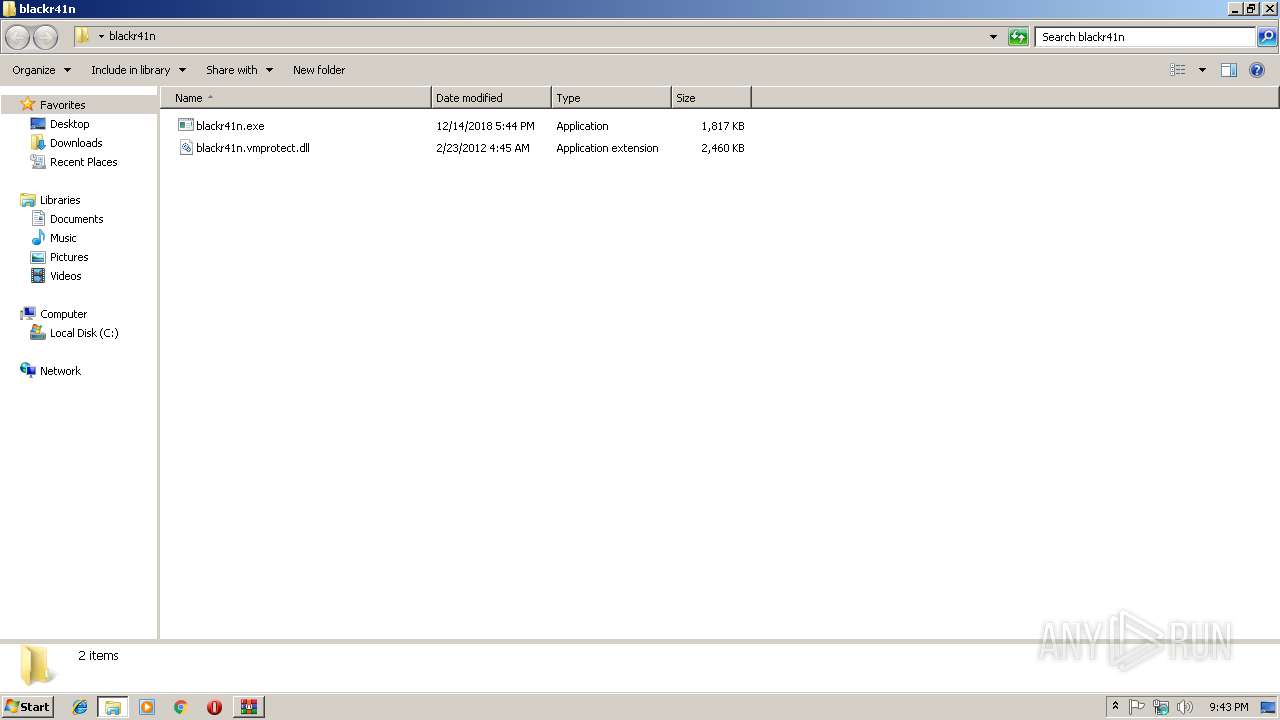
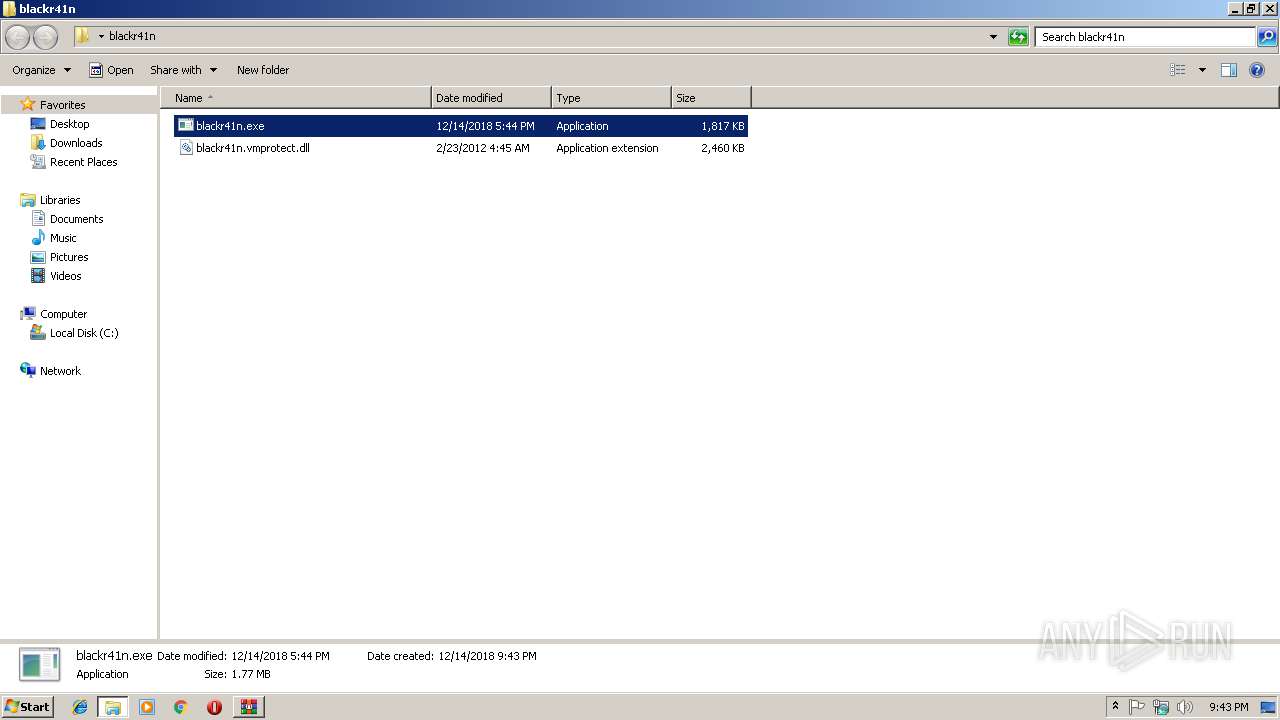
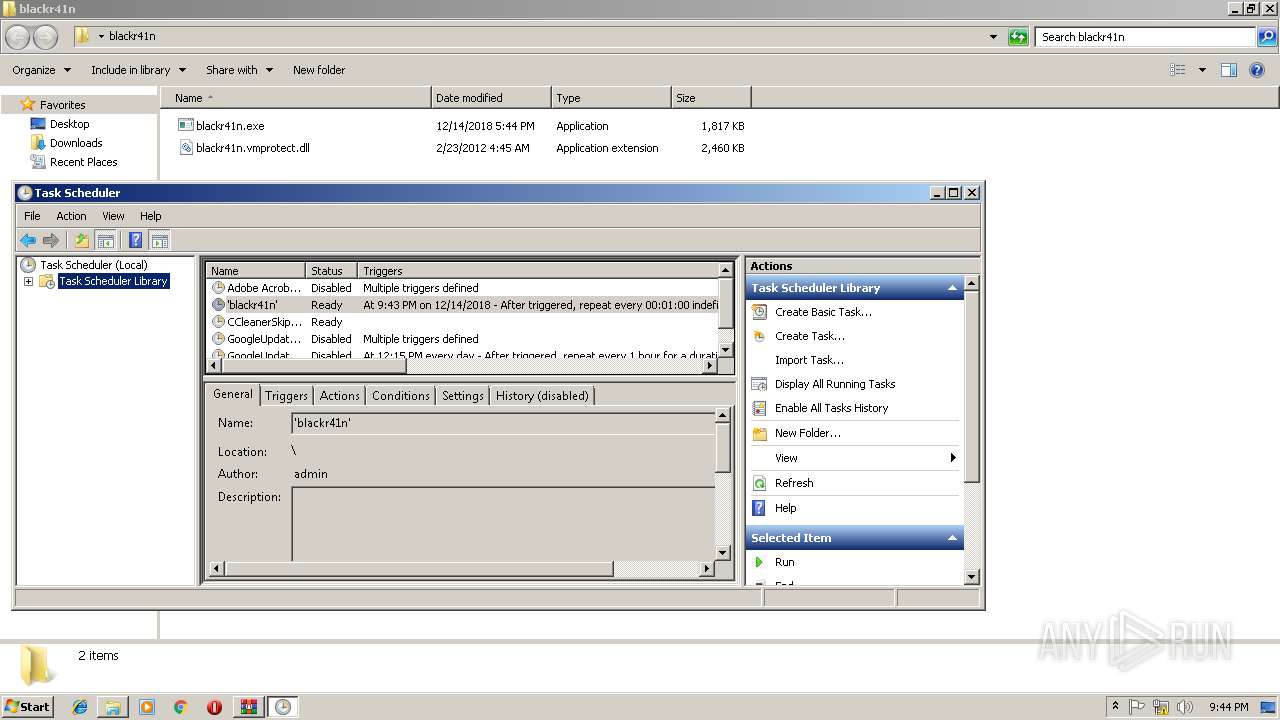
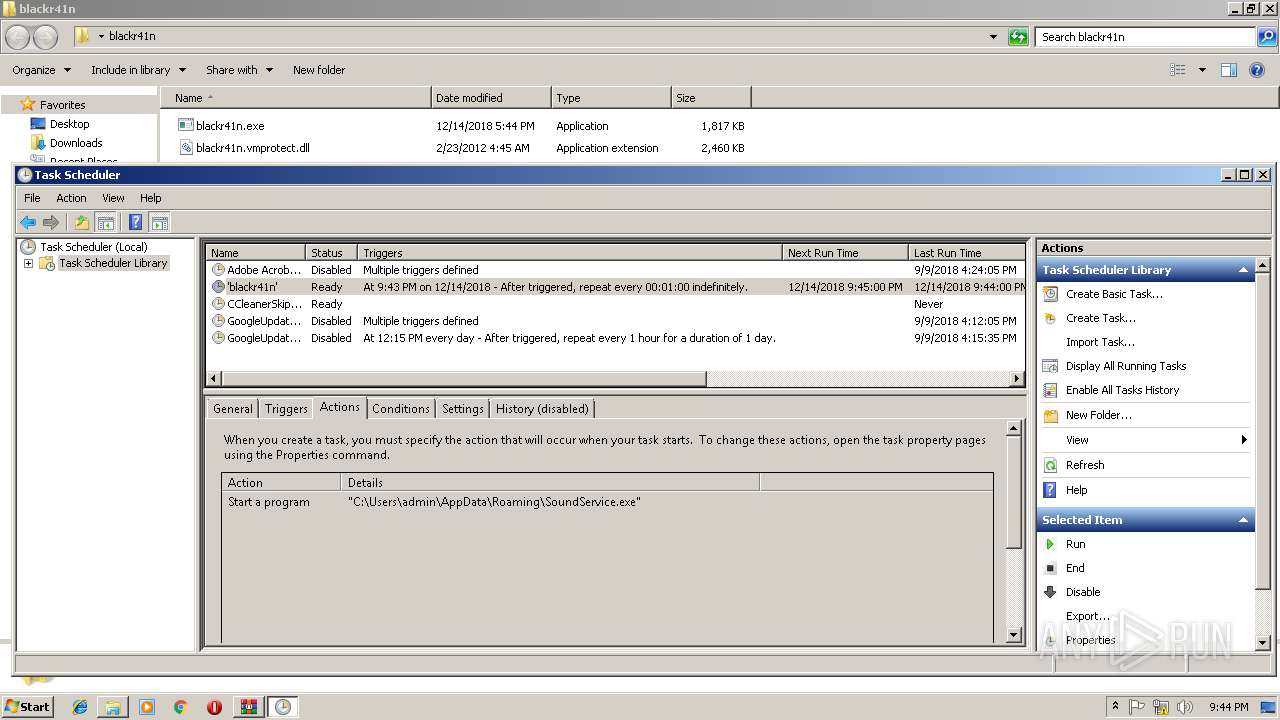
Application was dropped or rewritten from another process
- blackr41n.exe (PID: 2376)
- SoundService.exe (PID: 3156)
- SoundService.exe (PID: 3928)
- SoundService.exe (PID: 960)
- SoundService.exe (PID: 4000)
- SoundService.exe (PID: 3280)
- SoundService.exe (PID: 3708)
Uses Task Scheduler to run other applications
- blackr41n.exe (PID: 2376)
SUSPICIOUS
Creates files in the user directory
- blackr41n.exe (PID: 2376)
Starts itself from another location
- blackr41n.exe (PID: 2376)
Executable content was dropped or overwritten
- blackr41n.exe (PID: 2376)
Connects to unusual port
- Regasm.exe (PID: 2840)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
55
Monitored processes
17
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | C:\Users\admin\AppData\Roaming\SoundService.exe | C:\Users\admin\AppData\Roaming\SoundService.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1084 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | SoundService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1376 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | SoundService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\Desktop\blackr41n\blackr41n.exe" | C:\Users\admin\Desktop\blackr41n\blackr41n.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2840 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | SoundService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\6VKzMDa.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3020 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | SoundService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 3068 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3156 | "C:\Users\admin\AppData\Roaming\SoundService.exe" | C:\Users\admin\AppData\Roaming\SoundService.exe | — | blackr41n.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3212 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | SoundService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
951
Read events
920
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\6VKzMDa.rar | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2376) blackr41n.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2376) blackr41n.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.31434\blackr41n\blackr41n.exe | — | |
MD5:— | SHA256:— | |||
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.31434\blackr41n\blackr41n.vmprotect.dll | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Cab2571.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Tar2572.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Cab2582.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Tar2583.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Cab2640.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Tar2641.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | Regasm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 2376 | blackr41n.exe | C:\Users\admin\AppData\Roaming\SoundService.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | Regasm.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | Regasm.exe | 103.1.184.108:54984 | — | TPG Telecom Limited | AU | malicious |
2840 | Regasm.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2840 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
2840 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
2840 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) pkt checker #1 |
2840 | Regasm.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
2840 | Regasm.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|