| File name: | dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin |
| Full analysis: | https://app.any.run/tasks/ce6f6922-4d11-4979-b930-11e5697d31eb |
| Verdict: | Malicious activity |
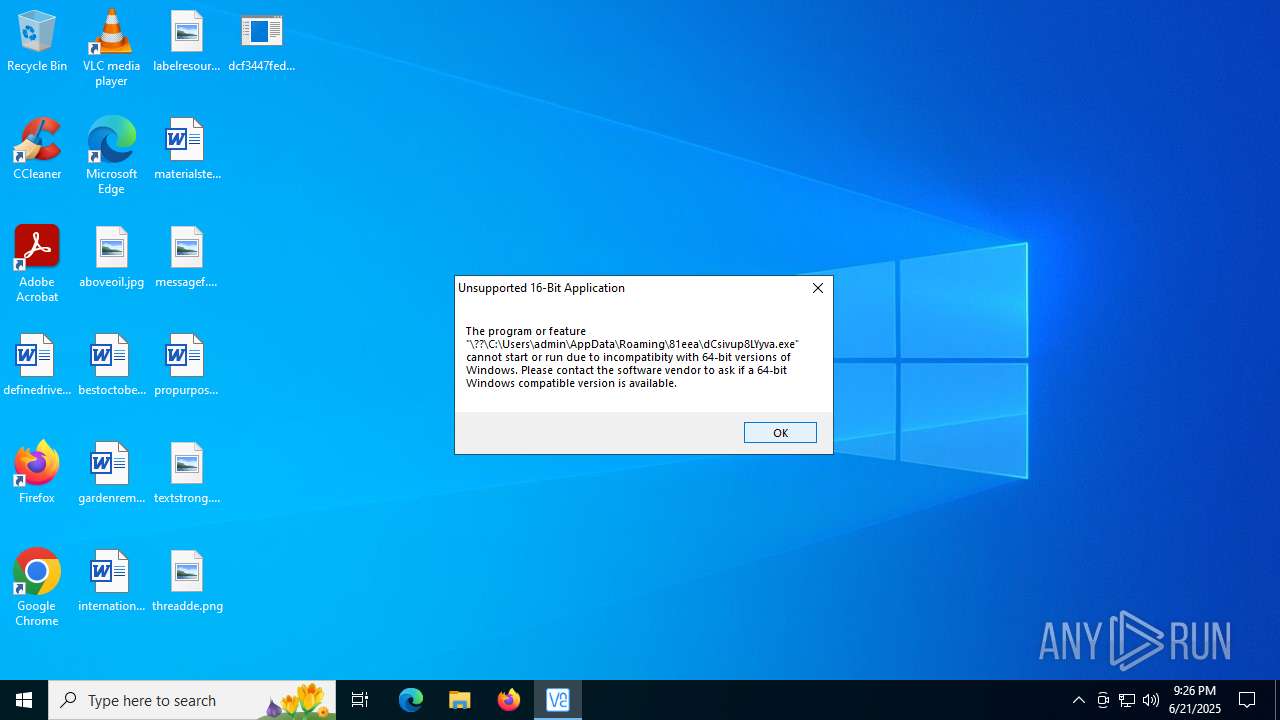
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 21, 2025, 21:23:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 101358C866BAFED0818099C30CEA5E40 |
| SHA1: | 02BA255828F940291ABA7E41B9652D2E887BD4B0 |
| SHA256: | DCF3447FED604475229DBBFA219E6447511382E1EE0505709087CB1497D5E1FF |
| SSDEEP: | 98304:SxwcbSU+063DX0RgUU6YQL/zs5uj0UF2np9zsATjj1jPxd95csupkz33JjJeQtM+:0oA |
MALICIOUS
LUMMA mutex has been found
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
LUMMA has been detected (YARA)
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
Steals credentials from Web Browsers
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
Actions looks like stealing of personal data
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
AMADEY mutex has been found
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- ramez.exe (PID: 1564)
- O1BXVWZVTU6EQ0EY18HYH259H.exe (PID: 6220)
- ramez.exe (PID: 4664)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 2232)
Connects to the CnC server
- ramez.exe (PID: 2232)
Changes the autorun value in the registry
- ramez.exe (PID: 2232)
AMADEY has been detected (YARA)
- ramez.exe (PID: 2232)
Executing a file with an untrusted certificate
- ed8cd81207.exe (PID: 7316)
- svchost015.exe (PID: 8012)
- wphS74bnKOMN.exe (PID: 4864)
- bo29vqzNRx8.exe (PID: 4312)
- bo29vqzNRx8.exe (PID: 7276)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 8012)
GCLEANER has been detected (YARA)
- svchost015.exe (PID: 8012)
Registers / Runs the DLL via REGSVR32.EXE
- bo29vqzNRx8.tmp (PID: 7720)
SUSPICIOUS
Reads the BIOS version
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- ramez.exe (PID: 1564)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
- O1BXVWZVTU6EQ0EY18HYH259H.exe (PID: 6220)
- ramez.exe (PID: 4664)
Searches for installed software
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
Process requests binary or script from the Internet
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- ramez.exe (PID: 2232)
- aca318cff1.exe (PID: 4944)
Potential Corporate Privacy Violation
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- ramez.exe (PID: 2232)
- svchost015.exe (PID: 8012)
- aca318cff1.exe (PID: 4944)
Executable content was dropped or overwritten
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- ed8cd81207.exe (PID: 7316)
- svchost015.exe (PID: 8012)
- ndtNTxq18tY.exe (PID: 7936)
- ndtNTxq18tY.tmp (PID: 8020)
- openfilesviewer.exe (PID: 7840)
- aca318cff1.exe (PID: 4944)
- bo29vqzNRx8.exe (PID: 4312)
- bo29vqzNRx8.tmp (PID: 3568)
- bo29vqzNRx8.exe (PID: 7276)
- bo29vqzNRx8.tmp (PID: 7720)
Connects to the server without a host name
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- ramez.exe (PID: 2232)
- svchost015.exe (PID: 8012)
- aca318cff1.exe (PID: 4944)
Reads security settings of Internet Explorer
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- svchost015.exe (PID: 8012)
- openfilesviewer.exe (PID: 7840)
- wphS74bnKOMN.exe (PID: 4864)
- bo29vqzNRx8.tmp (PID: 3568)
Starts itself from another location
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 2232)
The process executes via Task Scheduler
- ramez.exe (PID: 1564)
- updater.exe (PID: 7528)
- ramez.exe (PID: 4664)
There is functionality for enable RDP (YARA)
- ramez.exe (PID: 2232)
There is functionality for taking screenshot (YARA)
- ramez.exe (PID: 2232)
- ed8cd81207.exe (PID: 7316)
- svchost015.exe (PID: 8012)
- wphS74bnKOMN.exe (PID: 4864)
Application launched itself
- updater.exe (PID: 7528)
The process drops C-runtime libraries
- ndtNTxq18tY.tmp (PID: 8020)
Reads the Windows owner or organization settings
- ndtNTxq18tY.tmp (PID: 8020)
- bo29vqzNRx8.tmp (PID: 3568)
- bo29vqzNRx8.tmp (PID: 7720)
Process drops legitimate windows executable
- ndtNTxq18tY.tmp (PID: 8020)
Starts POWERSHELL.EXE for commands execution
- openfilesviewer.exe (PID: 7840)
- regsvr32.exe (PID: 6192)
Starts CMD.EXE for commands execution
- wphS74bnKOMN.exe (PID: 4864)
Get information on the list of running processes
- cmd.exe (PID: 6868)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6868)
The executable file from the user directory is run by the CMD process
- Oc.com (PID: 5644)
Starts application with an unusual extension
- cmd.exe (PID: 6868)
Starts the AutoIt3 executable file
- cmd.exe (PID: 6868)
Executing commands from a ".bat" file
- wphS74bnKOMN.exe (PID: 4864)
The process hide an interactive prompt from the user
- regsvr32.exe (PID: 6192)
The process bypasses the loading of PowerShell profile settings
- regsvr32.exe (PID: 6192)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Oc.com (PID: 5644)
INFO
Checks supported languages
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- ramez.exe (PID: 1564)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
- ed8cd81207.exe (PID: 7316)
- svchost015.exe (PID: 8012)
- updater.exe (PID: 7528)
- updater.exe (PID: 4680)
- ndtNTxq18tY.exe (PID: 7936)
- ndtNTxq18tY.tmp (PID: 8020)
- openfilesviewer.exe (PID: 7840)
- O1BXVWZVTU6EQ0EY18HYH259H.exe (PID: 6220)
- wphS74bnKOMN.exe (PID: 4864)
- OpenFilesViewer.exe (PID: 7308)
- extrac32.exe (PID: 8180)
- ramez.exe (PID: 4664)
- bo29vqzNRx8.exe (PID: 4312)
- bo29vqzNRx8.tmp (PID: 3568)
- Oc.com (PID: 5644)
- bo29vqzNRx8.exe (PID: 7276)
- bo29vqzNRx8.tmp (PID: 7720)
Reads the machine GUID from the registry
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
- svchost015.exe (PID: 8012)
- Oc.com (PID: 5644)
Reads the computer name
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
- svchost015.exe (PID: 8012)
- updater.exe (PID: 7528)
- ndtNTxq18tY.tmp (PID: 8020)
- openfilesviewer.exe (PID: 7840)
- wphS74bnKOMN.exe (PID: 4864)
- OpenFilesViewer.exe (PID: 7308)
- extrac32.exe (PID: 8180)
- bo29vqzNRx8.tmp (PID: 3568)
- Oc.com (PID: 5644)
- bo29vqzNRx8.tmp (PID: 7720)
Reads the software policy settings
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
- svchost015.exe (PID: 8012)
- slui.exe (PID: 6356)
- Oc.com (PID: 5644)
Application launched itself
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 6292)
- chrome.exe (PID: 2680)
- msedge.exe (PID: 5712)
- msedge.exe (PID: 1380)
- msedge.exe (PID: 2120)
- msedge.exe (PID: 6980)
- msedge.exe (PID: 1564)
- msedge.exe (PID: 6016)
- chrome.exe (PID: 6936)
- chrome.exe (PID: 7396)
- chrome.exe (PID: 8164)
- chrome.exe (PID: 2448)
- msedge.exe (PID: 8160)
- msedge.exe (PID: 1712)
- msedge.exe (PID: 7760)
- msedge.exe (PID: 7968)
- msedge.exe (PID: 4100)
- msedge.exe (PID: 7532)
- msedge.exe (PID: 5444)
- msedge.exe (PID: 8064)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 7376)
- chrome.exe (PID: 7760)
- chrome.exe (PID: 2144)
- msedge.exe (PID: 1560)
Themida protector has been detected
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- ramez.exe (PID: 2232)
- aca318cff1.exe (PID: 4944)
- aca318cff1.exe (PID: 3608)
Create files in a temporary directory
- dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe (PID: 5952)
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- ed8cd81207.exe (PID: 7316)
- ndtNTxq18tY.exe (PID: 7936)
- ndtNTxq18tY.tmp (PID: 8020)
- aca318cff1.exe (PID: 4944)
- wphS74bnKOMN.exe (PID: 4864)
- extrac32.exe (PID: 8180)
- bo29vqzNRx8.exe (PID: 4312)
- bo29vqzNRx8.tmp (PID: 3568)
- bo29vqzNRx8.tmp (PID: 7720)
- bo29vqzNRx8.exe (PID: 7276)
Process checks computer location settings
- FUFI1A8NFD7L8GM7TEY19QSFDU7787.exe (PID: 3196)
- ramez.exe (PID: 2232)
- openfilesviewer.exe (PID: 7840)
- wphS74bnKOMN.exe (PID: 4864)
- svchost015.exe (PID: 8012)
- bo29vqzNRx8.tmp (PID: 3568)
Checks proxy server information
- ramez.exe (PID: 2232)
- svchost015.exe (PID: 8012)
- slui.exe (PID: 6356)
Creates files or folders in the user directory
- ramez.exe (PID: 2232)
- svchost015.exe (PID: 8012)
- ndtNTxq18tY.tmp (PID: 8020)
- bo29vqzNRx8.tmp (PID: 7720)
Launching a file from a Registry key
- ramez.exe (PID: 2232)
Manual execution by a user
- aca318cff1.exe (PID: 3608)
- OpenFilesViewer.exe (PID: 7308)
The sample compiled with chinese language support
- ramez.exe (PID: 2232)
Compiled with Borland Delphi (YARA)
- ed8cd81207.exe (PID: 7316)
- ndtNTxq18tY.tmp (PID: 8020)
The sample compiled with english language support
- ed8cd81207.exe (PID: 7316)
- ndtNTxq18tY.tmp (PID: 8020)
- openfilesviewer.exe (PID: 7840)
Process checks whether UAC notifications are on
- updater.exe (PID: 7528)
Creates files in the program directory
- openfilesviewer.exe (PID: 7840)
Creates a software uninstall entry
- ndtNTxq18tY.tmp (PID: 8020)
Changes the registry key values via Powershell
- openfilesviewer.exe (PID: 7840)
Reads mouse settings
- Oc.com (PID: 5644)
Detects InnoSetup installer (YARA)
- ndtNTxq18tY.exe (PID: 7936)
- ndtNTxq18tY.tmp (PID: 8020)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 1096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(5952) dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe
C2 (9)ropyi.xyz/zadf
skjgx.xyz/riuw
gewgb.xyz/axgh
baviip.xyz/twiw
equidn.xyz/xapq
spjeo.xyz/axka
firddy.xyz/yhbc
shaeb.xyz/ikxz
trqqe.xyz/xudu
(PID) Process(4944) aca318cff1.exe
C2 (9)ropyi.xyz/zadf
skjgx.xyz/riuw
gewgb.xyz/axgh
baviip.xyz/twiw
equidn.xyz/xapq
spjeo.xyz/axka
firddy.xyz/yhbc
shaeb.xyz/ikxz
trqqe.xyz/xudu
(PID) Process(3608) aca318cff1.exe
C2 (9)ropyi.xyz/zadf
skjgx.xyz/riuw
gewgb.xyz/axgh
baviip.xyz/twiw
equidn.xyz/xapq
spjeo.xyz/axka
firddy.xyz/yhbc
shaeb.xyz/ikxz
trqqe.xyz/xudu
Amadey
(PID) Process(2232) ramez.exe
C2185.156.72.96
URLhttp://185.156.72.96/te4h2nus/index.php
Version5.34
Options
Drop directoryd610cf342e
Drop nameramez.exe
Strings (125)Powershell.exe
/te4h2nus/index.php
ramez.exe
bi:
185.156.72.96
AVAST Software
/Plugins/
------
id:
\0000
wb
Programs
-%lu
.jpg
AVG
r=
dm:
-executionpolicy remotesigned -File "
SOFTWARE\Microsoft\Windows NT\CurrentVersion
\
ProgramData\
Avira
e2
os:
http://
vs:
<c>
2025
ComputerName
og:
00000419
rb
2022
Content-Type: application/x-www-form-urlencoded
shell32.dll
https://
Main
Sophos
Norton
GET
#
S-%lu-
st=s
cmd /C RMDIR /s/q
lv:
msi
Content-Disposition: form-data; name="data"; filename="
5.34
d1
2016
ar:
cred.dll|clip.dll|
rundll32
WinDefender
Content-Type: multipart/form-data; boundary=----
Rem
CurrentBuild
0123456789
&& Exit"
un:
Kaspersky Lab
d610cf342e
Bitdefender
+++
av:
rundll32.exe
random
<d>
Keyboard Layout\Preload
shutdown -s -t 0
DefaultSettings.XResolution
/quiet
--
0000043f
Startup
e1
Doctor Web
2019
GetNativeSystemInfo
VideoID
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
:::
ESET
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
" && ren
abcdefghijklmnopqrstuvwxyz0123456789-_
cmd
"taskkill /f /im "
00000423
-unicode-
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
cred.dll
360TotalSecurity
"
exe
00000422
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
&&
Comodo
"
Content-Type: application/octet-stream
------
?scr=1
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
zip
dll
/k
&unit=
ps1
" && timeout 1 && del
kernel32.dll
ProductName
%-lu
clip.dll
%USERPROFILE%
\App
SYSTEM\ControlSet001\Services\BasicDisplay\Video
pc:
sd:
POST
Panda Security
e3
|
=
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:16 14:51:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 311296 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4c0000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
364
Monitored processes
226
Malicious processes
18
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3624,i,3373017487071204935,15369809094628712111,262144 --variations-seed-version --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 360 | choice /d n /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=2952,i,9204373351843225946,9860194867536987952,262144 --variations-seed-version --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3480,i,9204373351843225946,9860194867536987952,262144 --variations-seed-version --mojo-platform-channel-handle=3608 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2396,i,15466084266343360243,11839085369195743561,262144 --variations-seed-version --mojo-platform-channel-handle=2404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=2828,i,921988187171847434,16775599357825142199,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3860 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=1924,i,5628532023408711957,15188011227863674919,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2108 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3176,i,5814212539732313958,4088598972493429702,262144 --variations-seed-version --mojo-platform-channel-handle=3328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | aca318cff1.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2028,i,5632632749765521803,13452715903753167736,262144 --variations-seed-version --mojo-platform-channel-handle=2020 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
88 370
Read events
88 202
Write events
164
Delete events
4
Modification events
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
96
Suspicious files
310
Text files
513
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF178647.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF178647.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF178656.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF178656.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF178666.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF178637.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
368
TCP/UDP connections
418
DNS requests
345
Threats
34
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.25.50.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2368 | RUXIMICS.exe | GET | 200 | 184.25.50.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.25.50.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2368 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 142.250.184.195:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | unknown | compressed | 59.2 Kb | whitelisted |
— | — | GET | 200 | 142.250.185.74:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
— | — | POST | 200 | 85.90.196.155:443 | https://equidn.xyz/xapq | unknown | binary | 32.7 Kb | unknown |
— | — | GET | 200 | 142.250.185.68:443 | https://www.google.com/complete/search?client=chrome-omni&gs_ri=chrome-ext-ansg&xssi=t&q=&oit=0&oft=1&pgcl=20&gs_rn=42&sugkey=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | text | 7.57 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2368 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.25.50.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.25.50.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2368 | RUXIMICS.exe | 184.25.50.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2368 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
equidn.xyz |
| unknown |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5952 | dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5952 | dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5952 | dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5952 | dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe | Misc activity | ET INFO Packed Executable Download |
5952 | dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2232 | ramez.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
2232 | ramez.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
2232 | ramez.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2232 | ramez.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2232 | ramez.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
Process | Message |
|---|---|
dcf3447fed604475229dbbfa219e6447511382e1ee0505709087cb1497d5e1ff.bin.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
aca318cff1.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
aca318cff1.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|