| File name: | dccdf0e0a479d7abd0c87f717d993cb833cfb9fc8f96c49d7dcc65ae3704d218 |
| Full analysis: | https://app.any.run/tasks/56d49dc0-6e97-4cbb-b67d-d7266dd51c35 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | January 11, 2019, 04:24:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | A5D0B8DCFDAB608227EBC26A4C572341 |
| SHA1: | 076038F9E6F401C04AB29AC9B2A8EDAA45E0FC8E |
| SHA256: | DCCDF0E0A479D7ABD0C87F717D993CB833CFB9FC8F96C49D7DCC65AE3704D218 |
| SSDEEP: | 12288:bh6jIdvQByarOdnMl6YfoytsBHhoubsJex6oEMePKzIXz1L+9uPQabF:dfdvUyaidnMVoytkZbsAEMoRDwMI0F |
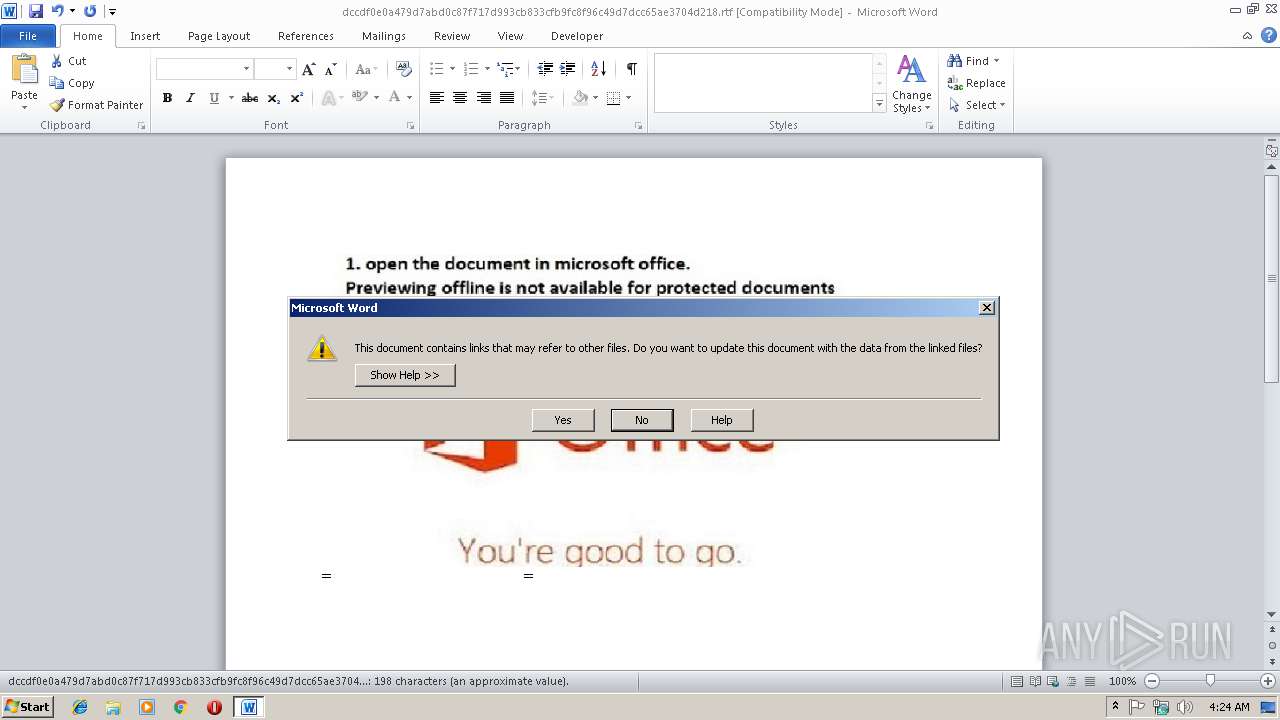
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2924)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2924)
Runs app for hidden code execution
- cmd.exe (PID: 2704)
- cmd.exe (PID: 3300)
Application was dropped or rewritten from another process
- saver.scr (PID: 3096)
Detected artifacts of LokiBot
- saver.scr (PID: 3096)
LOKIBOT was detected
- saver.scr (PID: 3096)
Connects to CnC server
- saver.scr (PID: 3096)
Actions looks like stealing of personal data
- saver.scr (PID: 3096)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2704)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 3300)
- cmd.exe (PID: 3440)
Executes scripts
- cmd.exe (PID: 3440)
Executable content was dropped or overwritten
- cscript.exe (PID: 2572)
- saver.scr (PID: 3096)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3440)
- cmd.exe (PID: 3468)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 2400)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 3440)
Application launched itself
- cmd.exe (PID: 3440)
Starts application with an unusual extension
- cmd.exe (PID: 3440)
Starts Microsoft Office Application
- cmd.exe (PID: 3440)
Loads DLL from Mozilla Firefox
- saver.scr (PID: 3096)
Creates files in the user directory
- saver.scr (PID: 3096)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2924)
- WINWORD.EXE (PID: 3108)
Creates files in the user directory
- WINWORD.EXE (PID: 2924)
- WINWORD.EXE (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
70
Monitored processes
36
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | TIMEOUT /T 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\12.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2024 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\14.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\11.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | CmD | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2288 | REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\12.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | TIMEOUT /T 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | C:\Windows\system32\cmd.exe /c REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\12.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2400 | C:\Windows\system32\cmd.exe /c REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 068
Read events
1 697
Write events
355
Delete events
16
Modification events
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3'% |
Value: 332725006C0B0000010000000000000000000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311440926 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311441040 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311441041 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 6C0B0000E862629065A9D40100000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d)% |
Value: 642925006C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | d)% |
Value: 642925006C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
16
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9783.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB694.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3096 | saver.scr | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\Desktop\~$cdf0e0a479d7abd0c87f717d993cb833cfb9fc8f96c49d7dcc65ae3704d218.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\a.ScT | xml | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\itnqknf5.cmd | text | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0F986474-99CF-4613-8AA1-73642B733781}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | saver.scr | POST | — | 200.63.40.2:80 | http://umbra-diego.com/wp-content/file/log/Panel/five/fre.php | PA | — | — | malicious |
3096 | saver.scr | POST | — | 200.63.40.2:80 | http://umbra-diego.com/wp-content/file/log/Panel/five/fre.php | PA | — | — | malicious |
3096 | saver.scr | POST | — | 200.63.40.2:80 | http://umbra-diego.com/wp-content/file/log/Panel/five/fre.php | PA | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | saver.scr | 200.63.40.2:80 | umbra-diego.com | Panamaserver.com | PA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
umbra-diego.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3096 | saver.scr | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3096 | saver.scr | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3096 | saver.scr | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3 ETPRO signatures available at the full report