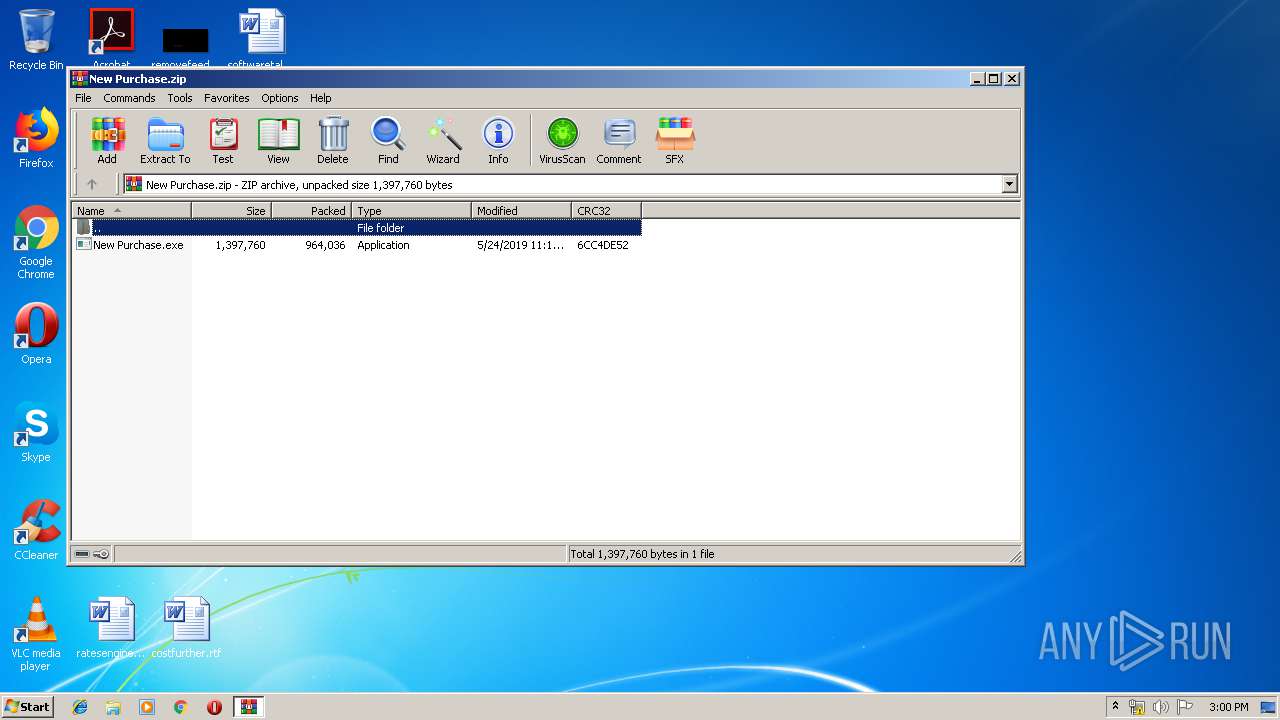
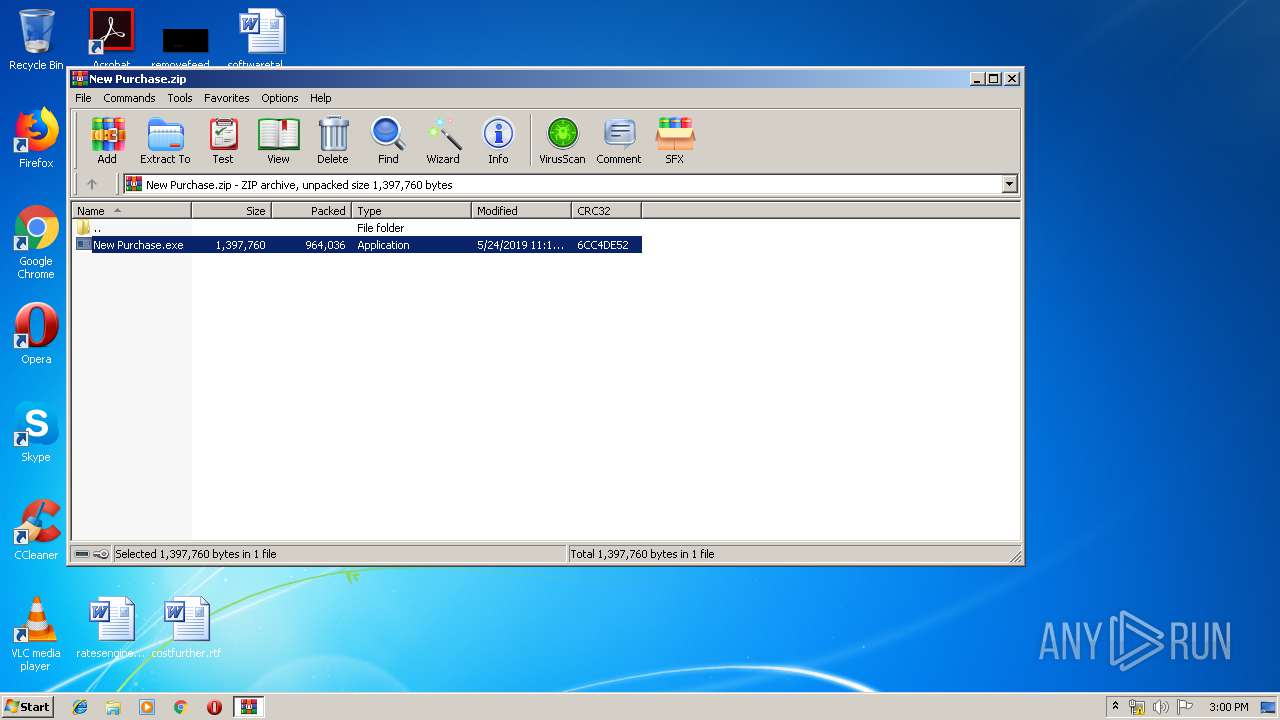
| File name: | New Purchase.zip |
| Full analysis: | https://app.any.run/tasks/afdf53b1-c424-4847-b5c3-c98023750c9c |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 24, 2019, 14:00:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E6BC30B452AEE17C094A32E529337F39 |
| SHA1: | 124E5384C4826DC7F02B9C96AC8D5D30B9295041 |
| SHA256: | DC9D583E9362D42682E5753A3D701918694669AF41A73C3AAF0C009D566F90FD |
| SSDEEP: | 24576:0t+TbYfl0H2GEma8AubOcCwBT1jGRLdudCC0tqzsMZuj:ioboGEibqcCwN1SdCDRC |
MALICIOUS
Application was dropped or rewritten from another process
- New Purchase.exe (PID: 2812)
- Latest-server.exe (PID: 1232)
- RegSvcs.exe (PID: 2628)
Writes to a start menu file
- New Purchase.exe (PID: 2812)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 2628)
- Latest-server.exe (PID: 1232)
NanoCore was detected
- Latest-server.exe (PID: 1232)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 2628)
AGENTTESLA was detected
- RegSvcs.exe (PID: 2628)
Connects to CnC server
- Latest-server.exe (PID: 1232)
SUSPICIOUS
Executable content was dropped or overwritten
- New Purchase.exe (PID: 2812)
- WinRAR.exe (PID: 3276)
- RegSvcs.exe (PID: 2628)
- Latest-server.exe (PID: 1232)
Creates files in the user directory
- New Purchase.exe (PID: 2812)
- RegSvcs.exe (PID: 2628)
- Latest-server.exe (PID: 1232)
Checks for external IP
- RegSvcs.exe (PID: 2628)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:24 17:12:28 |
| ZipCRC: | 0x6cc4de52 |
| ZipCompressedSize: | 964036 |
| ZipUncompressedSize: | 1397760 |
| ZipFileName: | New Purchase.exe |
Total processes
36
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1232 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Latest-server.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Latest-server.exe | RegSvcs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2628 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe | New Purchase.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2812 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3276.45948\New Purchase.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3276.45948\New Purchase.exe | WinRAR.exe | ||||||||||||
User: admin Company: PrintBrmEngine Integrity Level: MEDIUM Description: conhost Exit code: 0 Version: 753.254.685.736 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\New Purchase.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
904
Read events
864
Write events
40
Delete events
0
Modification events
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\New Purchase.zip | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3276) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
3
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1232 | Latest-server.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\settings.bak | — | |
MD5:— | SHA256:— | |||
| 2812 | New Purchase.exe | C:\Users\admin\AppData\Local\Temp\DsmUserTask\avicap32.vbs | text | |
MD5:— | SHA256:— | |||
| 3276 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3276.45948\New Purchase.exe | executable | |
MD5:— | SHA256:— | |||
| 2628 | RegSvcs.exe | C:\Users\admin\AppData\Local\Temp\dude\dude.exe | executable | |
MD5:— | SHA256:— | |||
| 1232 | Latest-server.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\TCP Monitor\tcpmon.exe | executable | |
MD5:— | SHA256:— | |||
| 2628 | RegSvcs.exe | C:\Users\admin\AppData\Local\Temp\636943068799691250_8983642e-48e1-425d-8829-263e8643ba8a.db | sqlite | |
MD5:— | SHA256:— | |||
| 1232 | Latest-server.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\run.dat | text | |
MD5:— | SHA256:— | |||
| 2812 | New Purchase.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\avicap32.url | text | |
MD5:— | SHA256:— | |||
| 2812 | New Purchase.exe | C:\Users\admin\AppData\Local\Temp\DsmUserTask\aeevts.exe | executable | |
MD5:— | SHA256:— | |||
| 2628 | RegSvcs.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Latest-server.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
71
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | RegSvcs.exe | GET | 200 | 18.211.215.84:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1232 | Latest-server.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
1232 | Latest-server.exe | 188.72.95.39:1122 | starlucky.dynu.net | Voxility S.R.L. | GB | malicious |
2628 | RegSvcs.exe | 87.250.250.38:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
2628 | RegSvcs.exe | 18.211.215.84:80 | checkip.amazonaws.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
starlucky.dynu.net |
| unknown |
smtp.yandex.com |
| malicious |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1232 | Latest-server.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 60B |
1232 | Latest-server.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
1232 | Latest-server.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
1232 | Latest-server.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
1232 | Latest-server.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
1232 | Latest-server.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
1232 | Latest-server.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
1232 | Latest-server.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
1232 | Latest-server.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
1232 | Latest-server.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 64B |
40 ETPRO signatures available at the full report