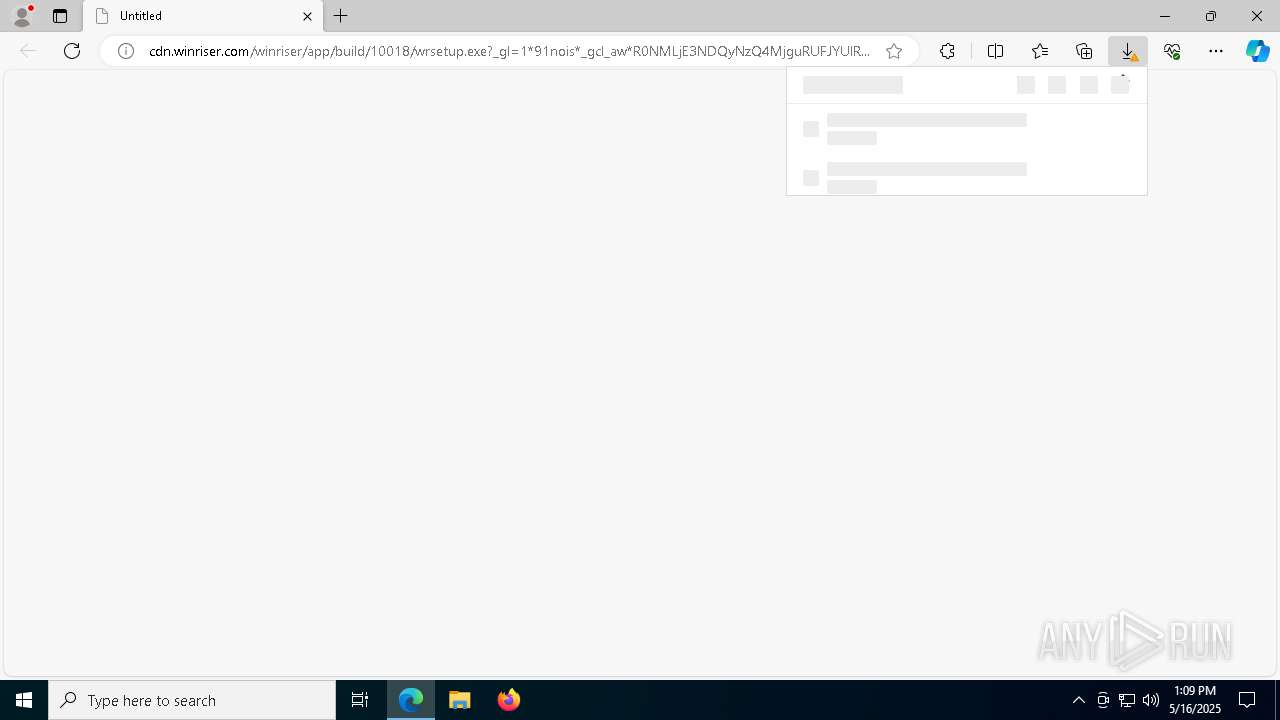
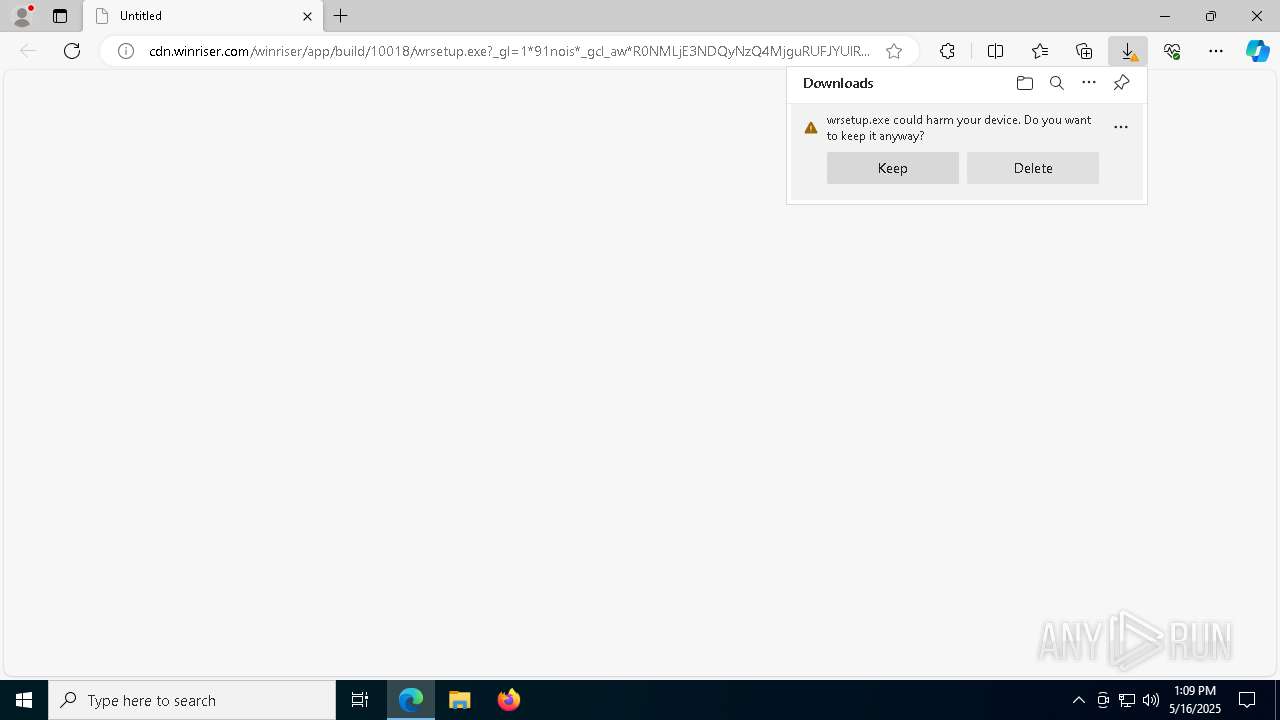
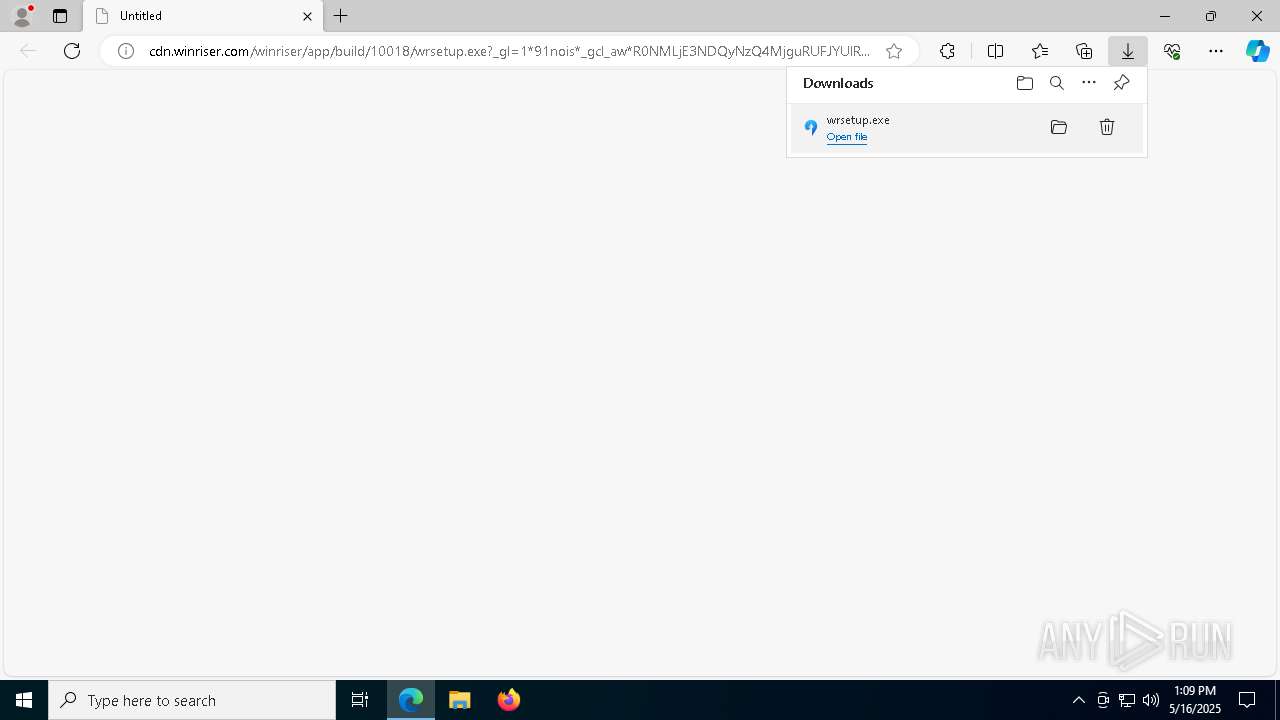
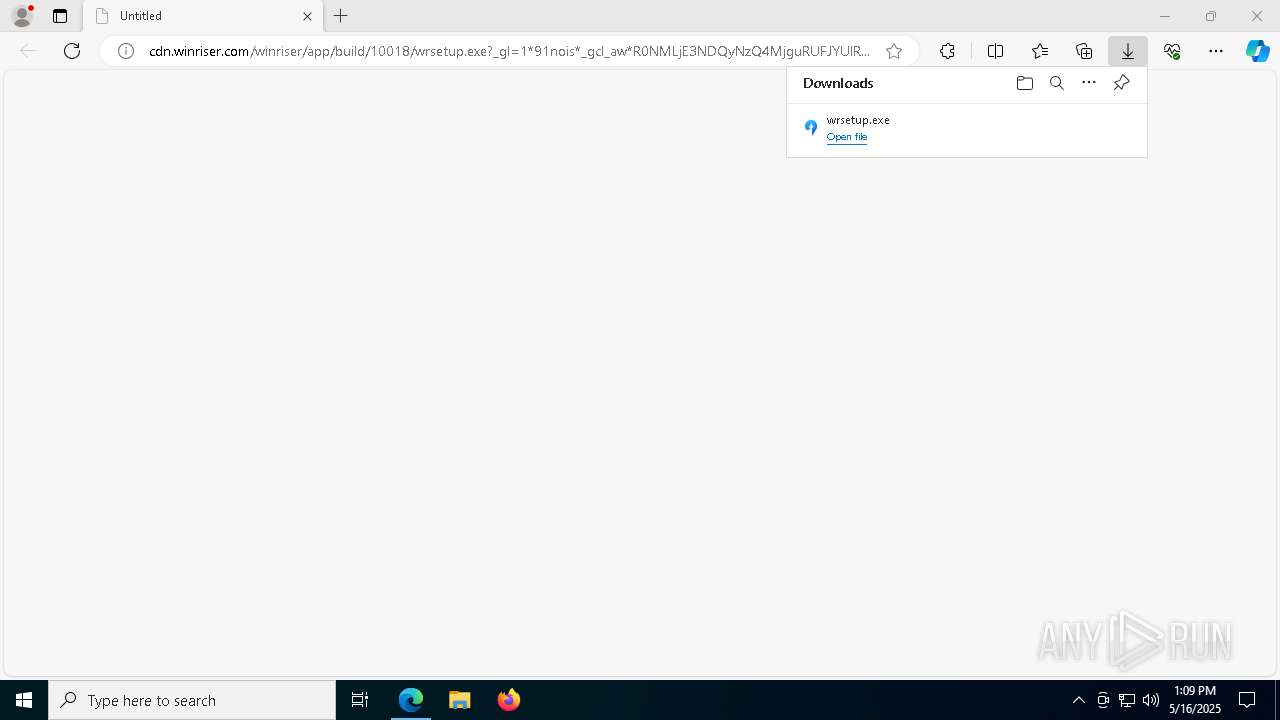
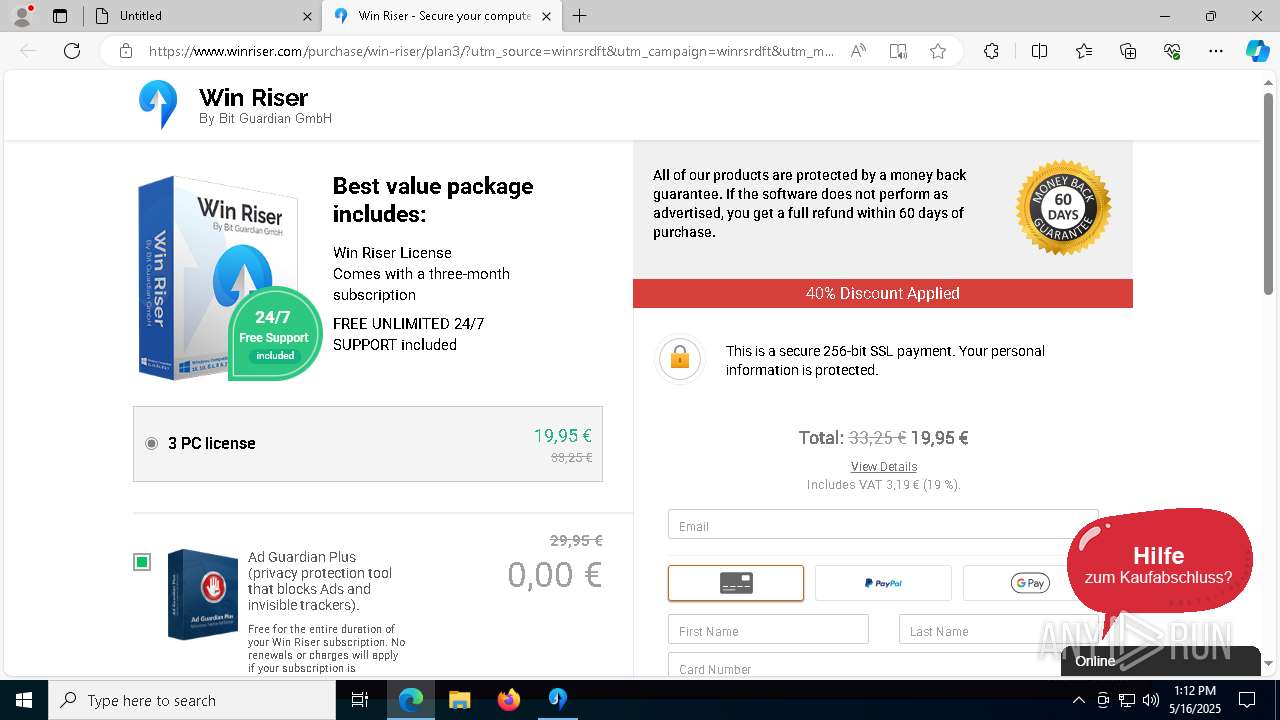
| URL: | cdn.winriser.com/winriser/app/build/10018/wrsetup.exe?_gl=1*91nois*_gcl_aw*R0NMLjE3NDQyNzQ4MjguRUFJYUlRb2JDaE1JcnRMczFZbk5qQU1WckNNR0FCM2Y3Uk5MRUFFWUFTQUFFZ0l2UVBEX0J3RQ..*_gcl_au*NDY0NDU2MDQwLjE3NDQyNzQ4Mjg. |
| Full analysis: | https://app.any.run/tasks/fe81b3d6-bd8d-46fb-a90b-94dcb473dbb8 |
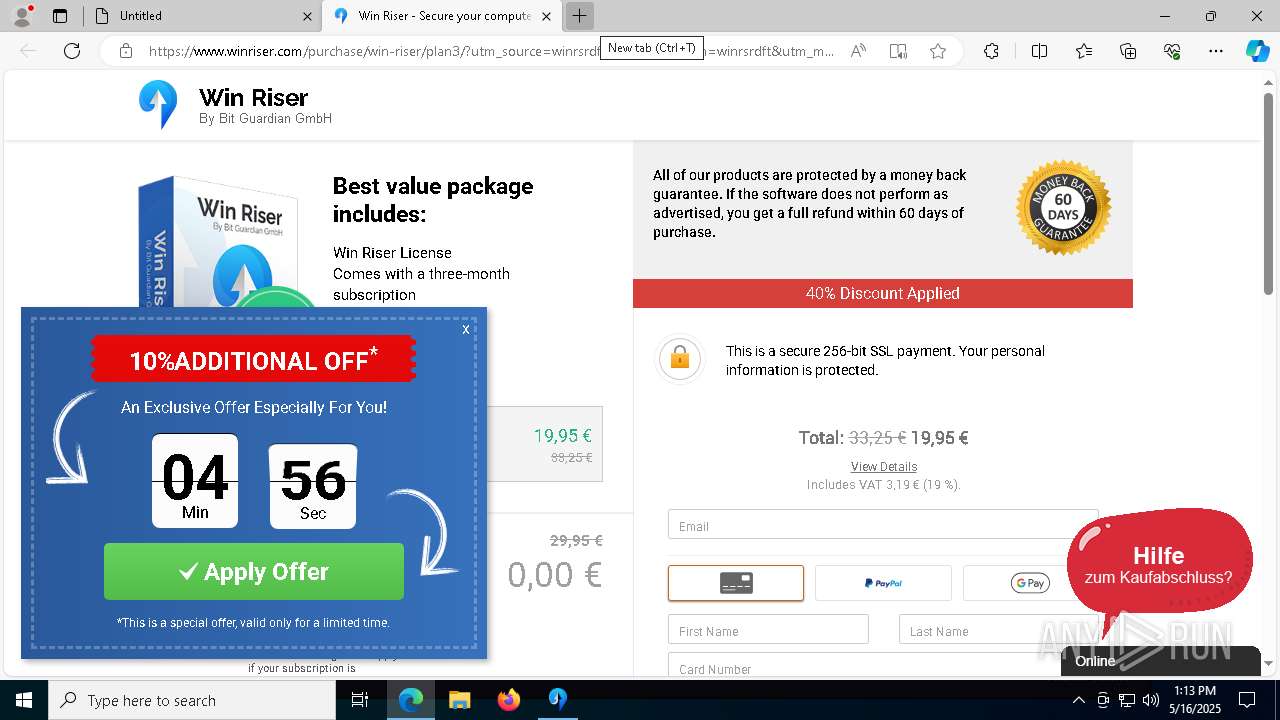
| Verdict: | Malicious activity |
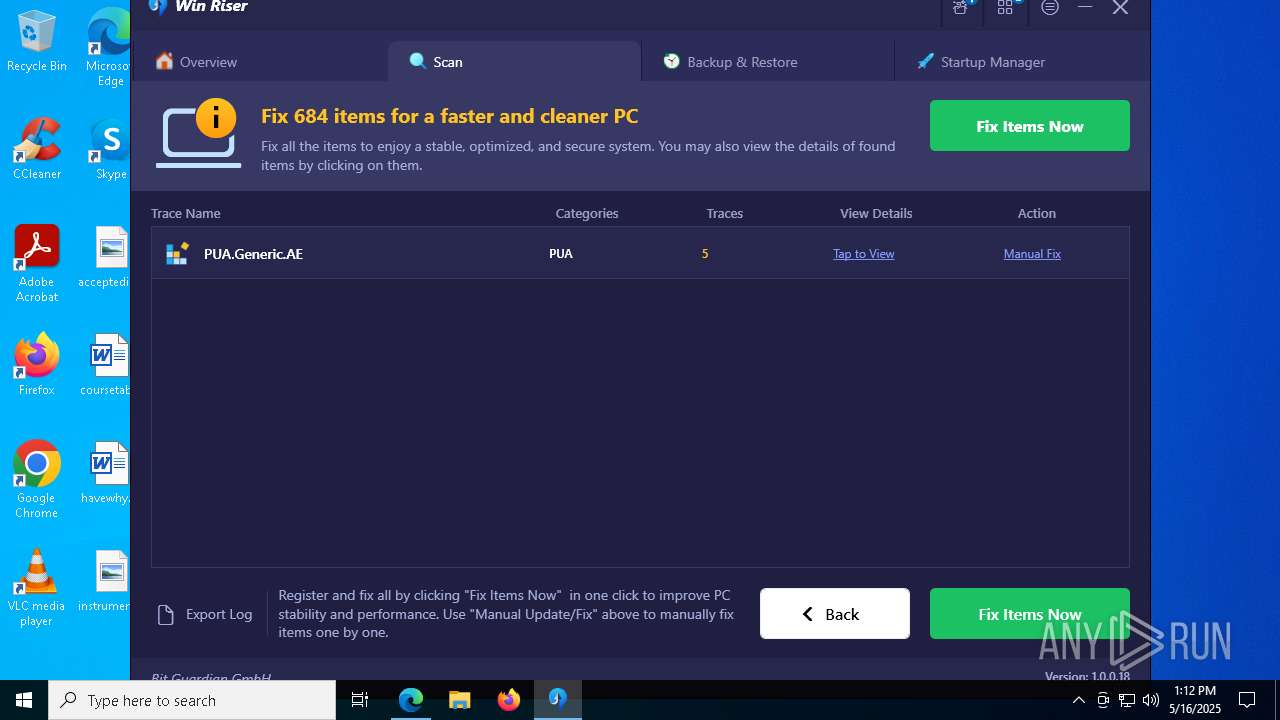
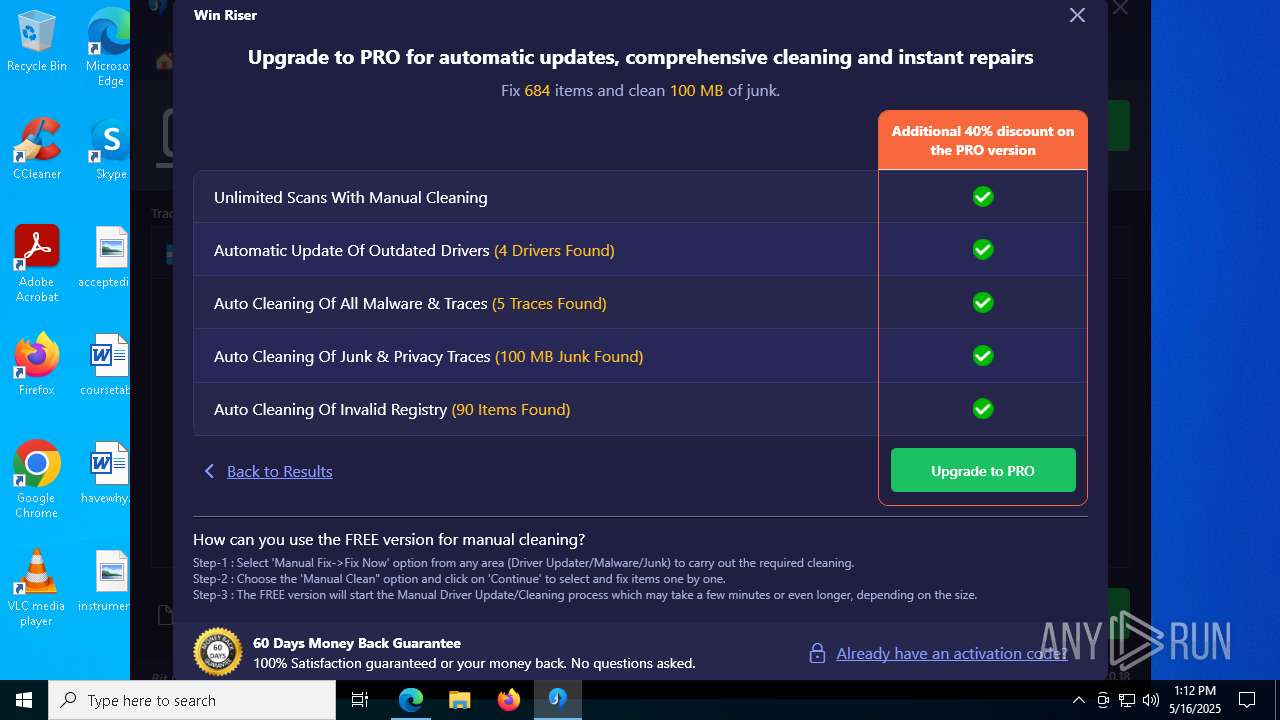
| Threats: | PureLogs is a stealer that collects a wide range of data from infected systems, including browser data, crypto wallets, PC configuration details, etc. It is delivered by PureCrypter, another malware that belongs to the Pure malware family. PureLogs is distributed based on a subscription model, allowing any threat actor to utilize it in their attacks. |
| Analysis date: | May 16, 2025, 13:09:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 21A895585253157310471578524E52C9 |
| SHA1: | A116F38255DE78B5531639300AEA91F11144308A |
| SHA256: | DC9BF1104A24712E66BAD7B014EDFA75A9FC3B3B78F34AEEE215D6A78DA42AC3 |
| SSDEEP: | 6:qQbCCFlh4/YbWJU306wMSQn9wJ0WKrf/BvBts75ZG:qQbCC7E67F9N3fJvS5ZG |
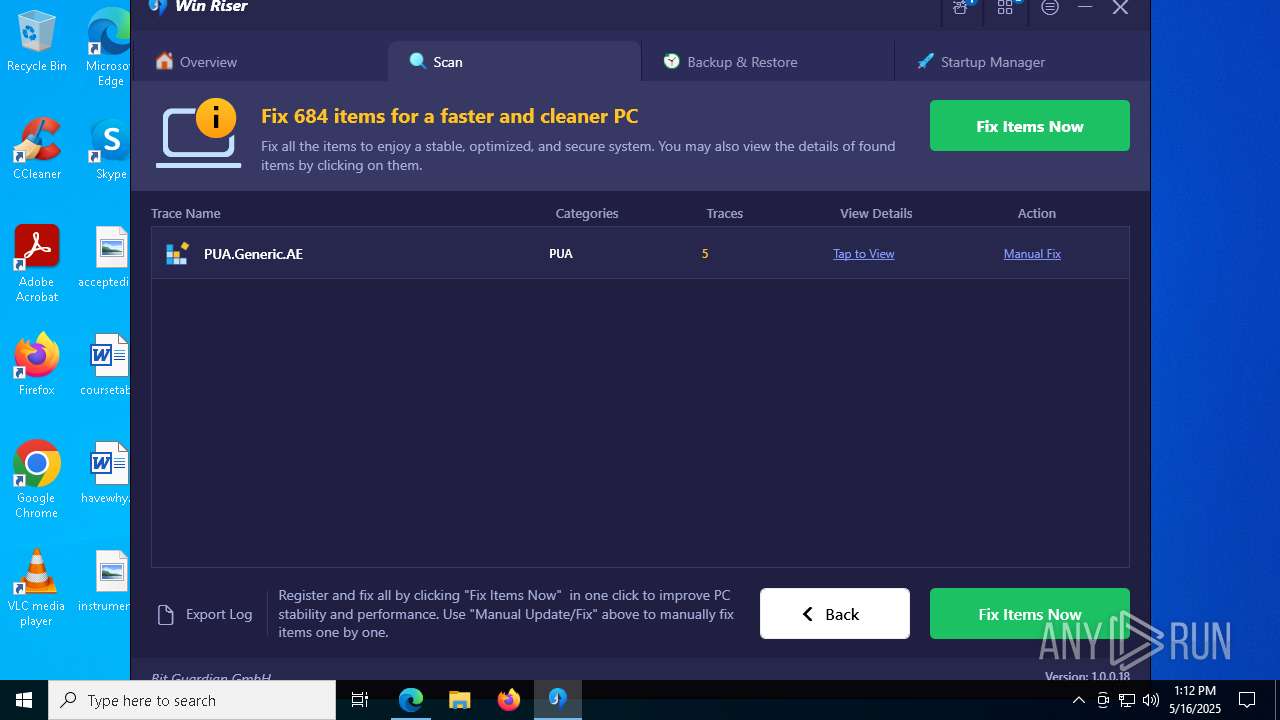
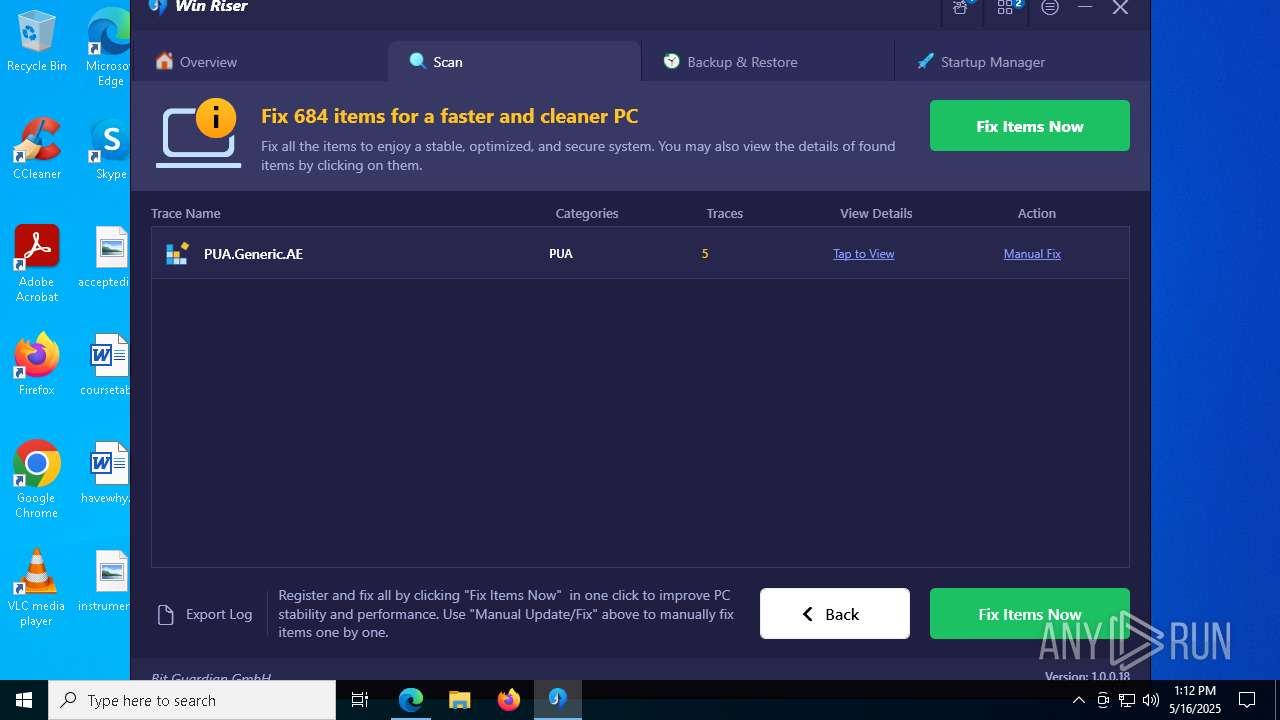
MALICIOUS
PURELOGS has been found (auto)
- msedge.exe (PID: 7328)
- msedge.exe (PID: 4996)
SUSPICIOUS
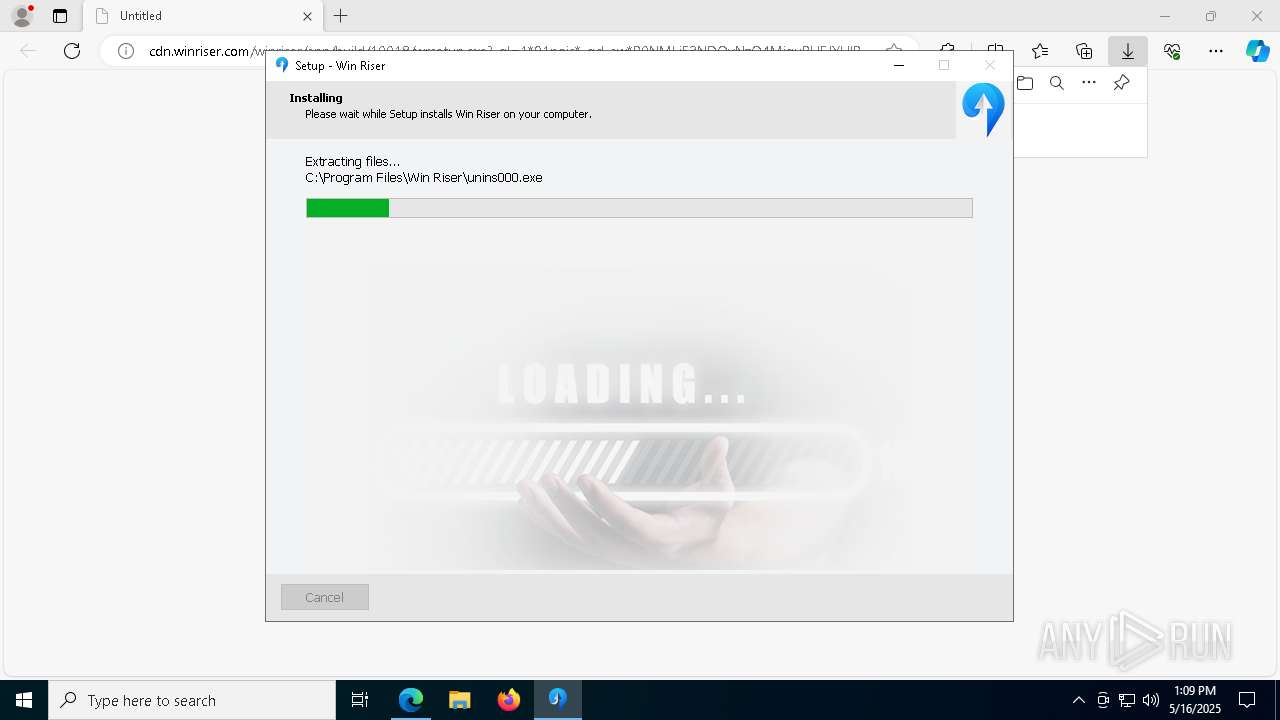
Executable content was dropped or overwritten
- wrsetup.exe (PID: 4696)
- wrsetup.exe (PID: 3676)
- wrsetup.tmp (PID: 4920)
- csc.exe (PID: 7928)
- csc.exe (PID: 2316)
- csc.exe (PID: 8120)
- csc.exe (PID: 7952)
- csc.exe (PID: 5244)
- csc.exe (PID: 8160)
- csc.exe (PID: 2980)
- csc.exe (PID: 6892)
Reads security settings of Internet Explorer
- wrsetup.tmp (PID: 2852)
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 632)
Uses TASKKILL.EXE to kill process
- wrsetup.tmp (PID: 4920)
Reads the Windows owner or organization settings
- wrsetup.tmp (PID: 4920)
Executes as Windows Service
- PresentationFontCache.exe (PID: 2564)
- VSSVC.exe (PID: 8076)
Process drops legitimate windows executable
- wrsetup.tmp (PID: 4920)
Drops 7-zip archiver for unpacking
- wrsetup.tmp (PID: 4920)
The process drops C-runtime libraries
- wrsetup.tmp (PID: 4920)
Write to the desktop.ini file (may be used to cloak folders)
- winrgr.exe (PID: 5984)
Starts POWERSHELL.EXE for commands execution
- winrgr.exe (PID: 5984)
- powershell.exe (PID: 8056)
Application launched itself
- powershell.exe (PID: 8056)
Reads browser cookies
- winrgr.exe (PID: 5984)
The process exported the data from the registry
- winrgr.exe (PID: 5984)
Starts CMD.EXE for commands execution
- winrgr.exe (PID: 5984)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 7328)
- msedge.exe (PID: 4996)
- msedge.exe (PID: 4376)
Application launched itself
- msedge.exe (PID: 4996)
Reads the computer name
- identity_helper.exe (PID: 6004)
- wrsetup.tmp (PID: 2852)
- wrsetup.exe (PID: 3676)
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
- PresentationFontCache.exe (PID: 2564)
Reads Environment values
- identity_helper.exe (PID: 6004)
- winrgr.exe (PID: 5984)
Checks supported languages
- wrsetup.exe (PID: 4696)
- wrsetup.tmp (PID: 2852)
- identity_helper.exe (PID: 6004)
- wrsetup.exe (PID: 3676)
- wrsetup.tmp (PID: 4920)
- PresentationFontCache.exe (PID: 2564)
- winrgr.exe (PID: 5984)
- csc.exe (PID: 7928)
- cvtres.exe (PID: 6972)
- csc.exe (PID: 2316)
- cvtres.exe (PID: 8132)
- cvtres.exe (PID: 2096)
- csc.exe (PID: 8120)
- csc.exe (PID: 7952)
- cvtres.exe (PID: 6740)
Create files in a temporary directory
- wrsetup.exe (PID: 4696)
- wrsetup.exe (PID: 3676)
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
- cvtres.exe (PID: 6972)
- csc.exe (PID: 2316)
- csc.exe (PID: 7928)
- cvtres.exe (PID: 2096)
- csc.exe (PID: 8120)
- cvtres.exe (PID: 8132)
- csc.exe (PID: 7952)
- cvtres.exe (PID: 6740)
Process checks computer location settings
- wrsetup.tmp (PID: 2852)
- wrsetup.tmp (PID: 4920)
Reads the machine GUID from the registry
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
- PresentationFontCache.exe (PID: 2564)
- csc.exe (PID: 7928)
- cvtres.exe (PID: 6972)
- csc.exe (PID: 2316)
- cvtres.exe (PID: 2096)
- csc.exe (PID: 8120)
- cvtres.exe (PID: 8132)
- csc.exe (PID: 7952)
- cvtres.exe (PID: 6740)
Checks proxy server information
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
Reads the software policy settings
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
Creates files or folders in the user directory
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
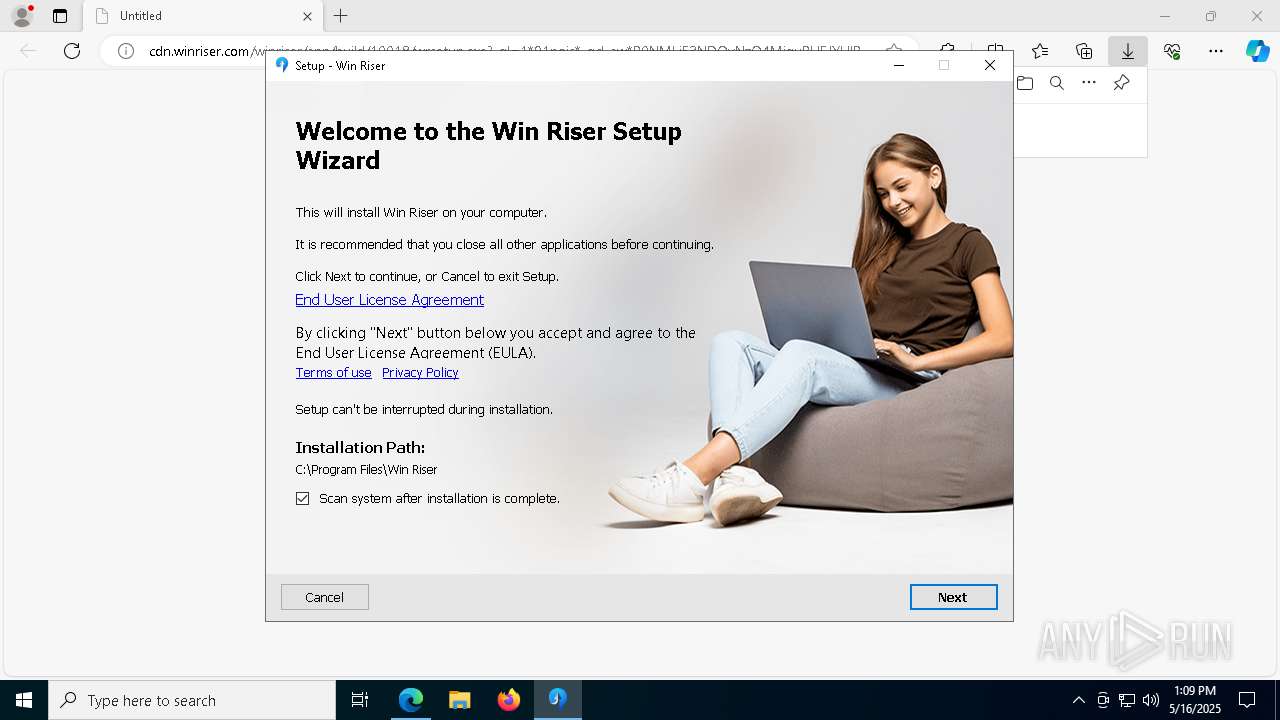
Creates files in the program directory
- wrsetup.tmp (PID: 4920)
- winrgr.exe (PID: 5984)
The sample compiled with english language support
- wrsetup.tmp (PID: 4920)
- msedge.exe (PID: 4376)
Creates a software uninstall entry
- wrsetup.tmp (PID: 4920)
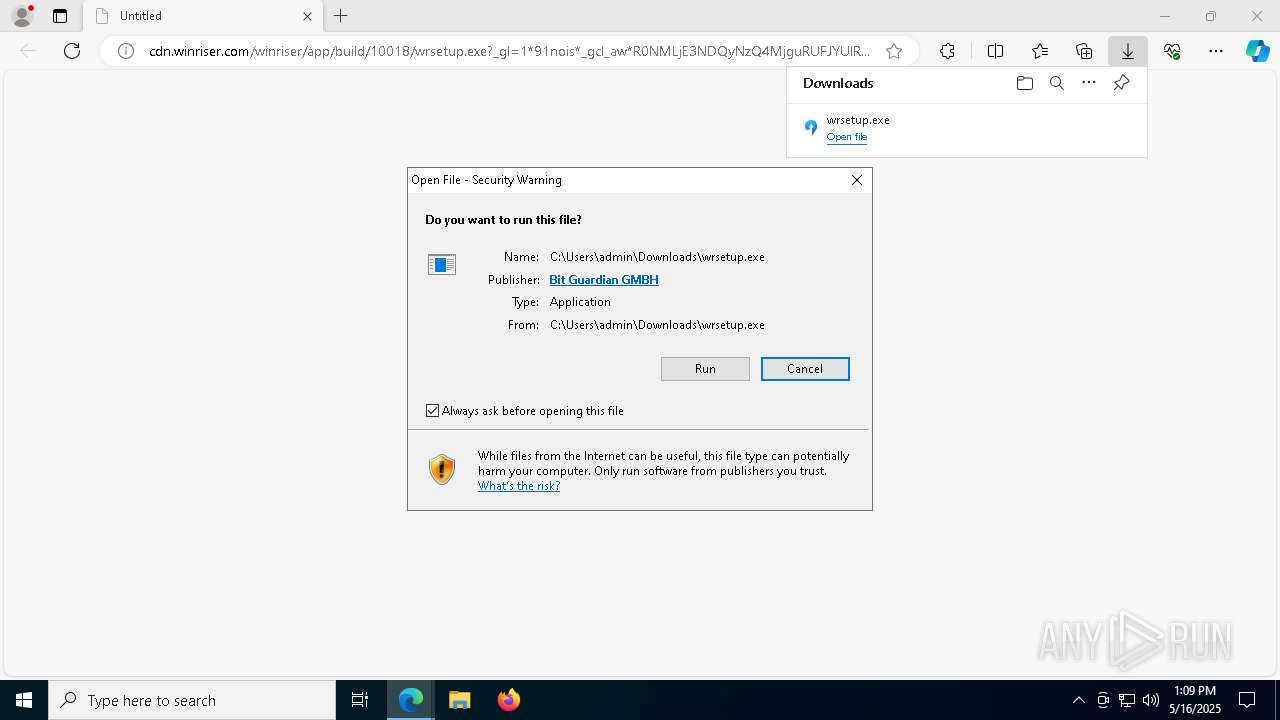
Detects InnoSetup installer (YARA)
- wrsetup.tmp (PID: 2852)
- wrsetup.exe (PID: 4696)
Compiled with Borland Delphi (YARA)
- wrsetup.tmp (PID: 2852)
- wrsetup.exe (PID: 4696)
SQLite executable
- wrsetup.tmp (PID: 4920)
.NET Reactor protector has been detected
- winrgr.exe (PID: 5984)
Reads product name
- winrgr.exe (PID: 5984)
Disables trace logs
- winrgr.exe (PID: 5984)
Manages system restore points
- SrTasks.exe (PID: 904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
259
Monitored processes
119
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7028 --field-trial-handle=2412,i,10956050472395211349,2309774571784922186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Windows\System32\schtasks.exe" /delete /tn "Win Riser_launcher" /f | C:\Windows\SysWOW64\schtasks.exe | — | wrsetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=4268 --field-trial-handle=2412,i,10956050472395211349,2309774571784922186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6620 --field-trial-handle=2412,i,10956050472395211349,2309774571784922186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3428 --field-trial-handle=2412,i,10956050472395211349,2309774571784922186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --mojo-platform-channel-handle=6044 --field-trial-handle=2412,i,10956050472395211349,2309774571784922186,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7520 --field-trial-handle=2412,i,10956050472395211349,2309774571784922186,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
790 572
Read events
790 108
Write events
442
Delete events
22
Modification events
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5D1963C6D6932F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 40566DC6D6932F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262774 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {370400F5-9177-4CFF-B7AC-C296DDCF84E1} | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262774 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9C11BC71-4F34-4A14-941A-3B20078FD8CB} | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 245D92C6D6932F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
100
Suspicious files
546
Text files
153
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b383.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b383.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b383.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b383.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b383.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
187
DNS requests
185
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
4996 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | DE | binary | 471 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
4996 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTaNXNmTHzbP9V65Wk2FQENGUmtZwQUyfwQ71DIy2t%2FvQhE7zpik%2B1bXpoCEAycMm7sE3KeDd17LH4VI84%3D | DE | binary | 727 b | whitelisted |
4996 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAeEPa0BwRXCdO5BpygiRnk%3D | DE | binary | 727 b | whitelisted |
4920 | wrsetup.tmp | GET | 200 | 18.245.38.41:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.40 Kb | whitelisted |
4920 | wrsetup.tmp | GET | 200 | 18.245.65.219:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAJTzrJHqB6JlT%2BdudvkXCw%3D | US | binary | 471 b | whitelisted |
4920 | wrsetup.tmp | GET | 200 | 154.27.69.89:80 | http://cf.winriser.com/productprice.svc/gtipinfo | US | binary | 90 b | unknown |
3192 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | — | 419 b | whitelisted |
3192 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4996 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7328 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
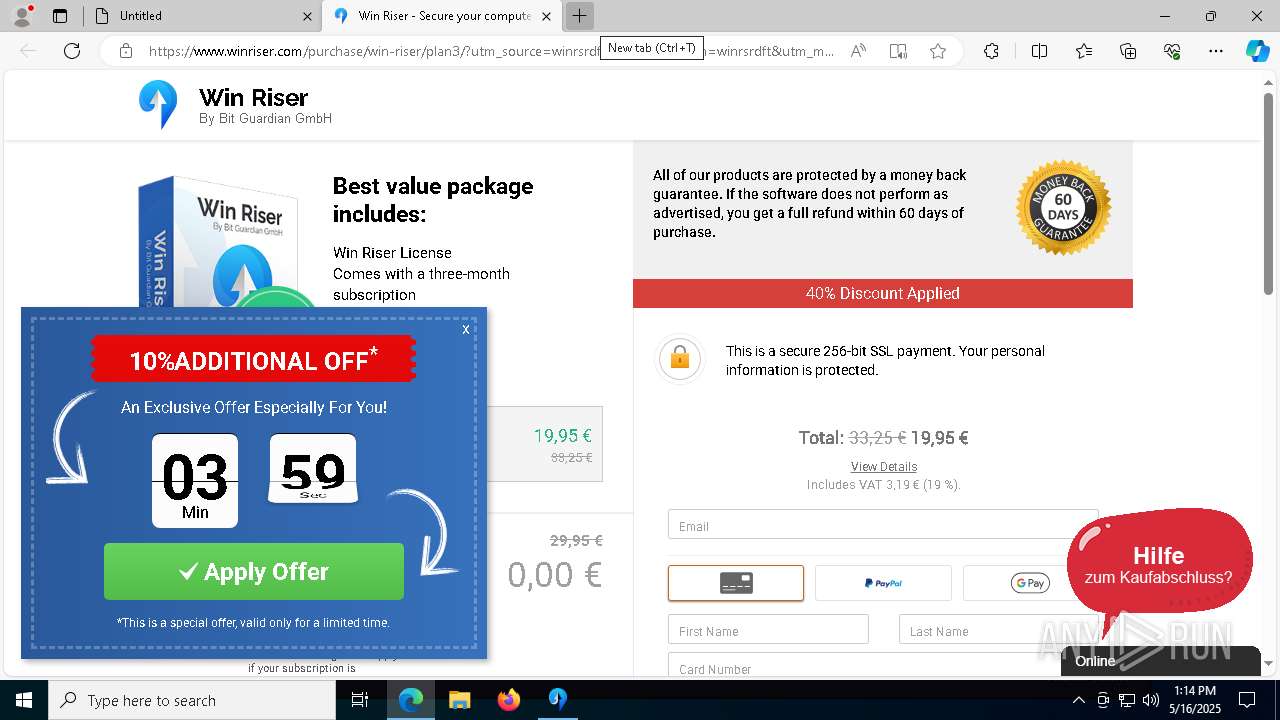
7328 | msedge.exe | 3.160.150.59:80 | cdn.winriser.com | — | US | malicious |
7328 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7328 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cdn.winriser.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |