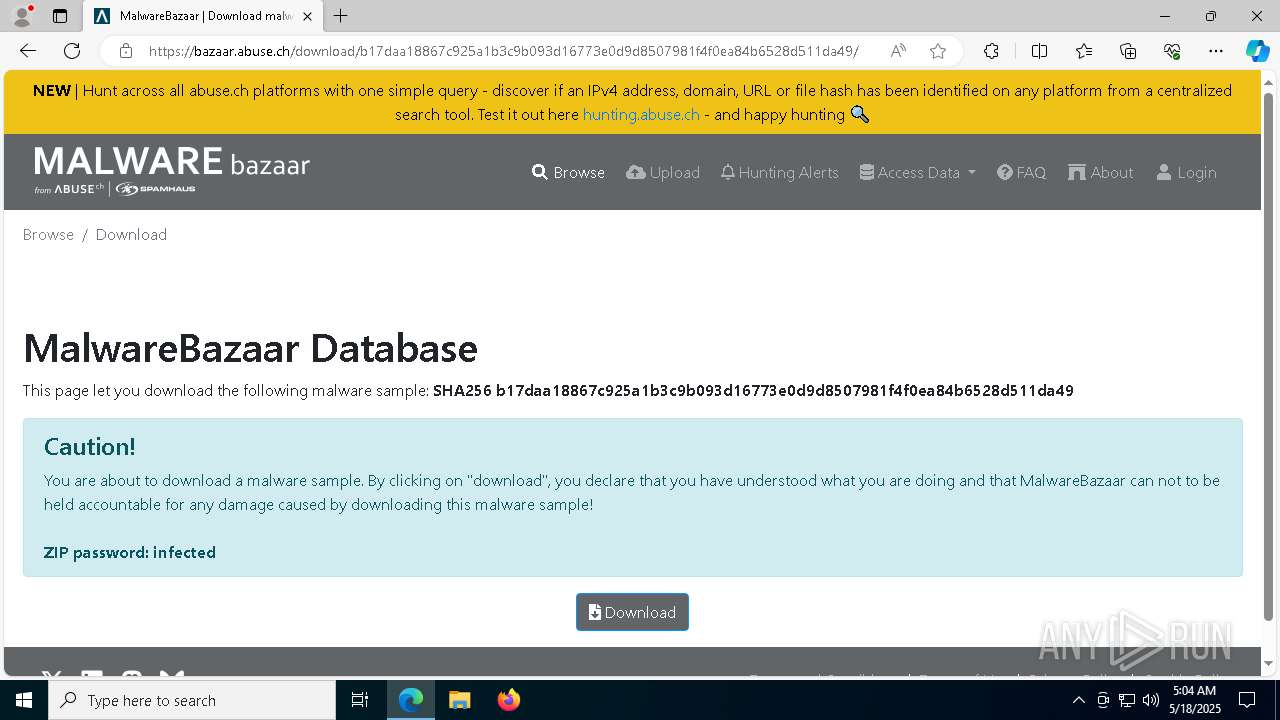
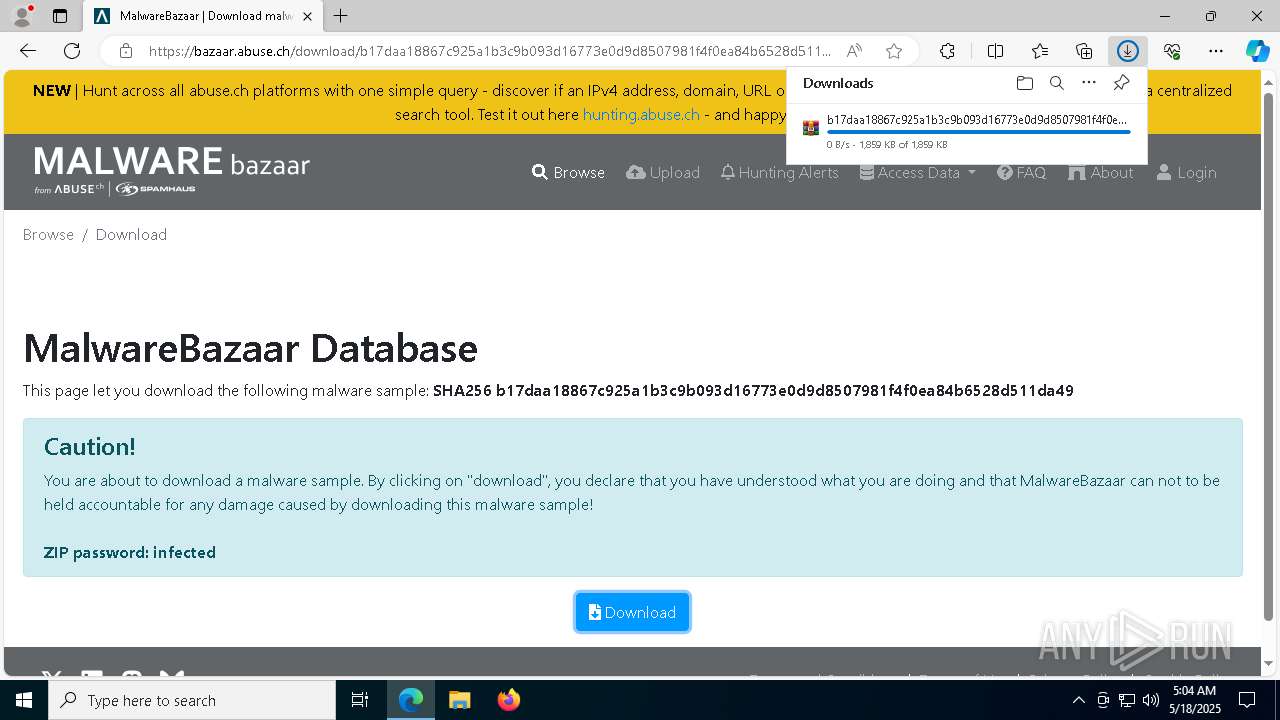
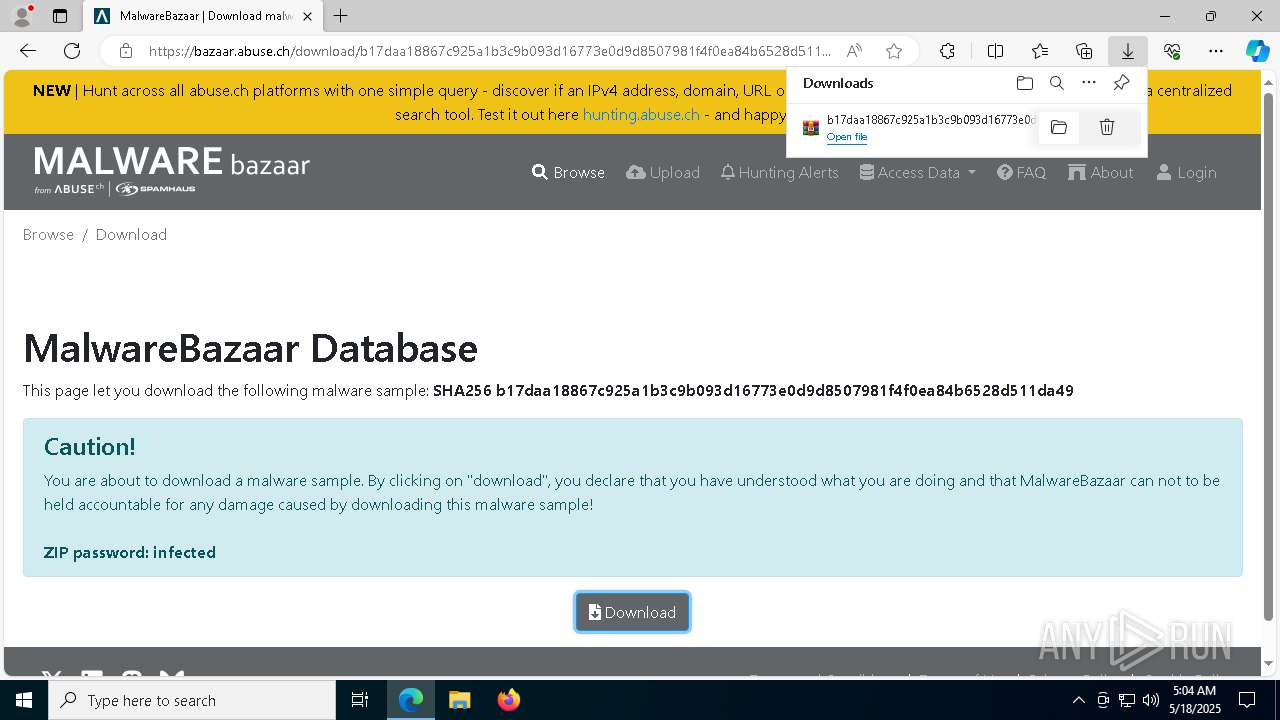
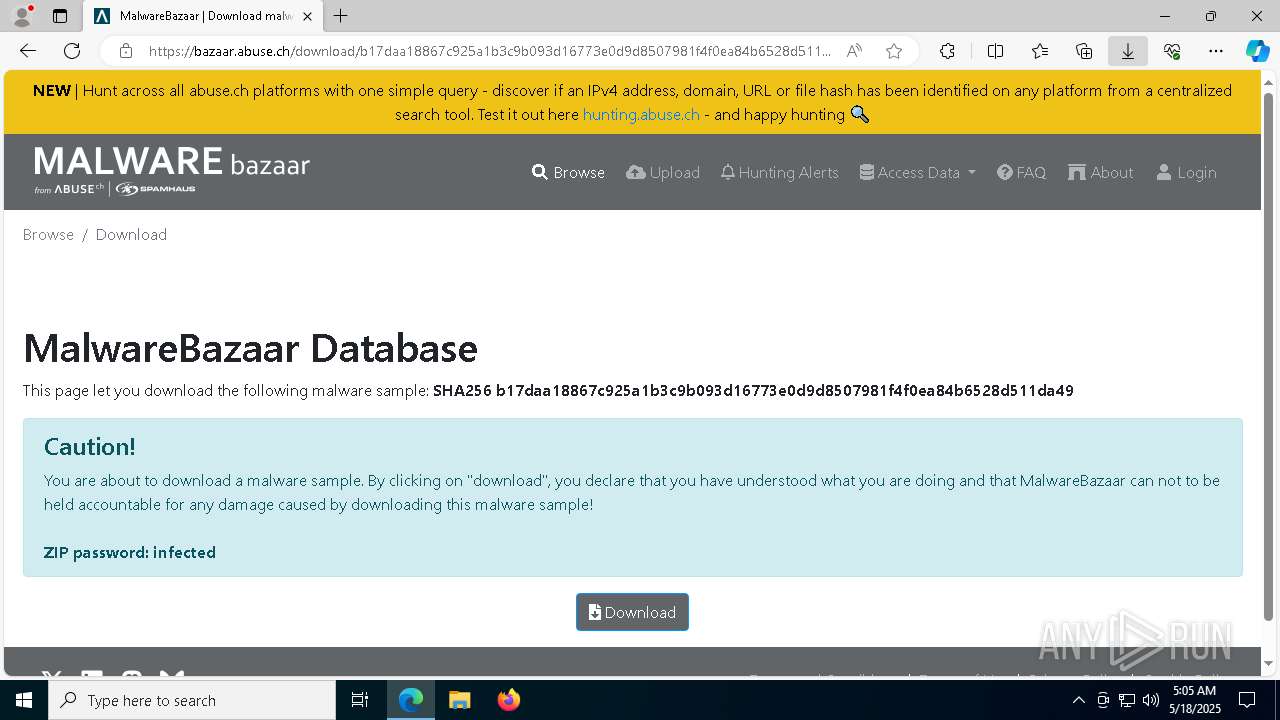
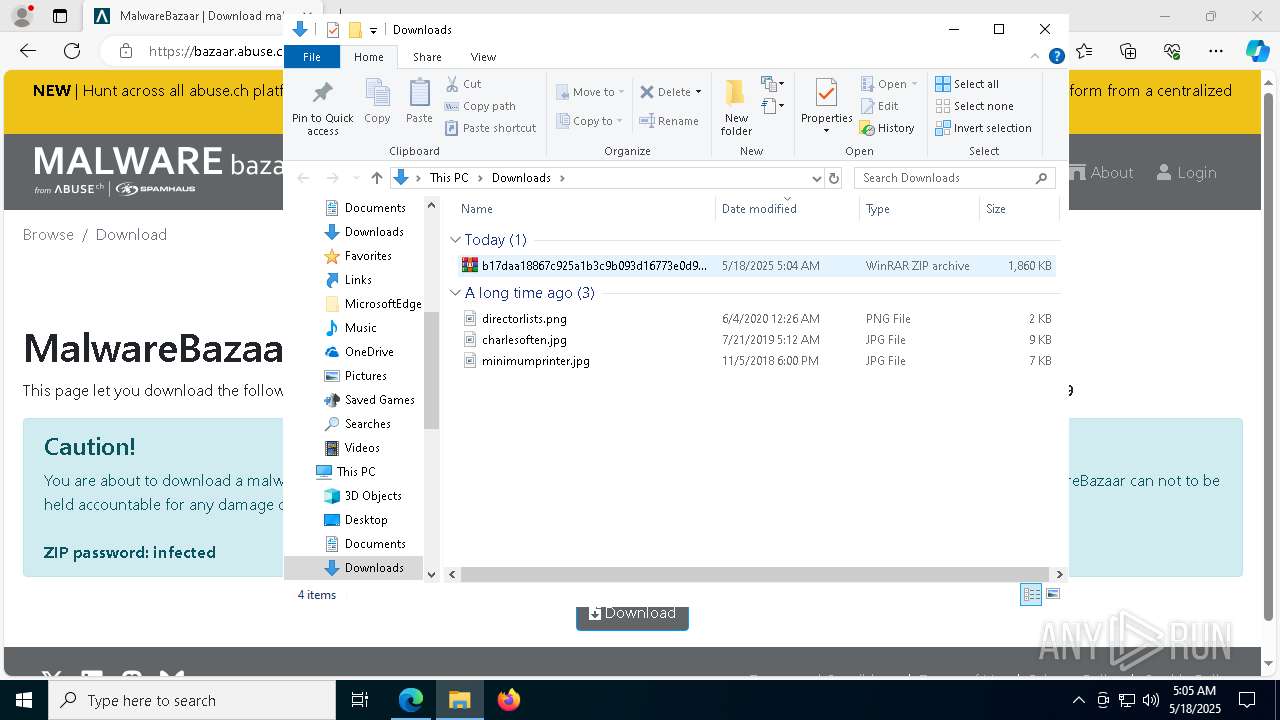
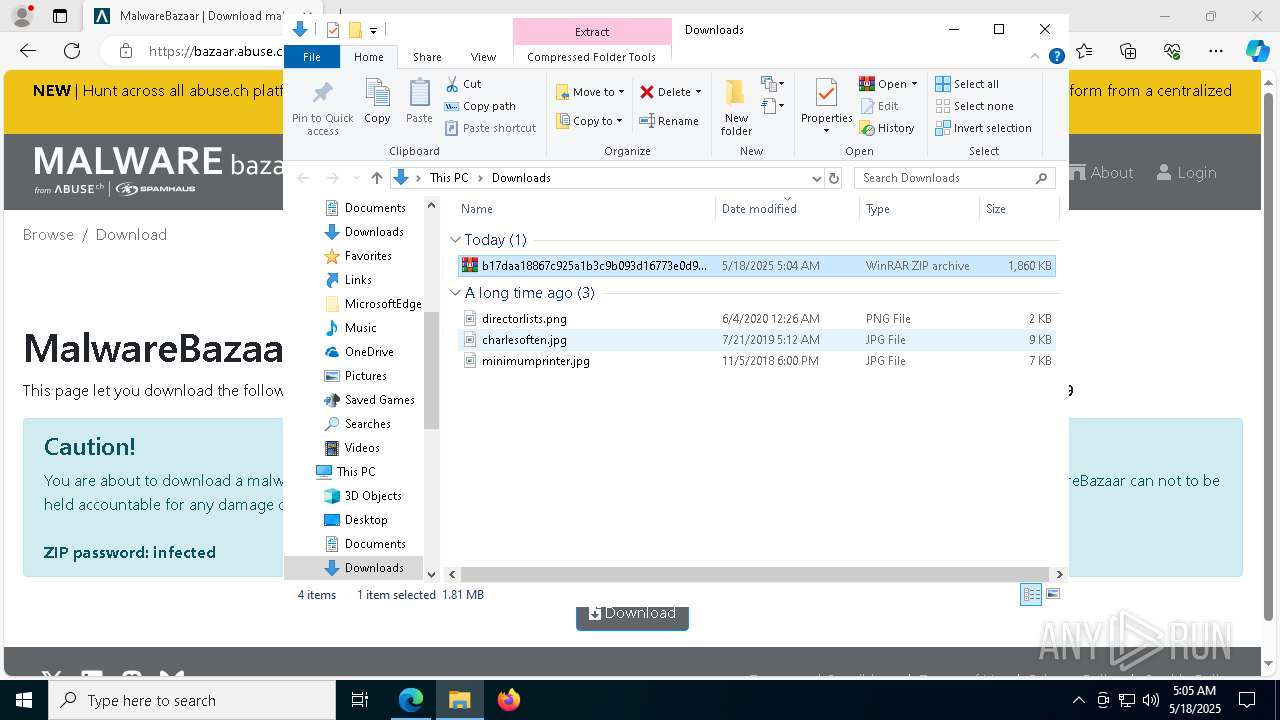
| URL: | https://bazaar.abuse.ch/download/b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49/ |
| Full analysis: | https://app.any.run/tasks/bdd1f1b9-d259-4324-a53d-85b39319a0be |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 18, 2025, 05:04:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B6DB09FC63AE840375C5ADF8B9065CA6 |
| SHA1: | 2F816C9CFCD9E584BF805F5DF5CD1C1F36F96BD7 |
| SHA256: | DC0951B1EB891B42AC3752B47086260464B5ED14DEBF9AF53EF8F8D8C5215FE0 |
| SSDEEP: | 3:N8N0uDWB4VE971EIc1cGUeaIBdQVScWlT8XVUB47:23G6E9B81cKrAvWxGV/7 |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
Connects to the CnC server
- svchost.exe (PID: 2196)
- ramez.exe (PID: 1096)
AMADEY mutex has been found
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- ramez.exe (PID: 1096)
LUMMA mutex has been found
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
Steals credentials from Web Browsers
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
Actions looks like stealing of personal data
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 1096)
SUSPICIOUS
Reads the BIOS version
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- ramez.exe (PID: 1096)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- ramez.exe (PID: 1096)
Potential Corporate Privacy Violation
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- ramez.exe (PID: 1096)
Connects to the server without a host name
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- ramez.exe (PID: 1096)
Process requests binary or script from the Internet
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- ramez.exe (PID: 1096)
Executable content was dropped or overwritten
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- ramez.exe (PID: 1096)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- 4989c876fb.exe (PID: 7904)
Searches for installed software
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
Reads security settings of Internet Explorer
- ramez.exe (PID: 1096)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- 4989c876fb.exe (PID: 7904)
Starts itself from another location
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
Drops 7-zip archiver for unpacking
- 4989c876fb.exe (PID: 7904)
The process creates files with name similar to system file names
- 4989c876fb.exe (PID: 7904)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7804)
- 4989c876fb.exe (PID: 7904)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 6136)
- NSudoLG.exe (PID: 1180)
- nircmd.exe (PID: 8256)
- cmd.exe (PID: 4452)
Executing commands from a ".bat" file
- 4989c876fb.exe (PID: 7904)
- cmd.exe (PID: 7804)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 6136)
- nircmd.exe (PID: 8256)
- NSudoLG.exe (PID: 1180)
Application launched itself
- cmd.exe (PID: 7804)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 4452)
Starts application with an unusual extension
- cmd.exe (PID: 6712)
- cmd.exe (PID: 8284)
- cmd.exe (PID: 4452)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8284)
- cmd.exe (PID: 4452)
The executable file from the user directory is run by the CMD process
- NSudoLG.exe (PID: 1180)
- nircmd.exe (PID: 8256)
Get information on the list of running processes
- cmd.exe (PID: 9008)
- cmd.exe (PID: 4452)
INFO
Reads the computer name
- identity_helper.exe (PID: 8752)
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- ramez.exe (PID: 1096)
- 4989c876fb.exe (PID: 7904)
Checks supported languages
- identity_helper.exe (PID: 8752)
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- ramez.exe (PID: 1096)
- 4989c876fb.exe (PID: 7904)
Application launched itself
- msedge.exe (PID: 2560)
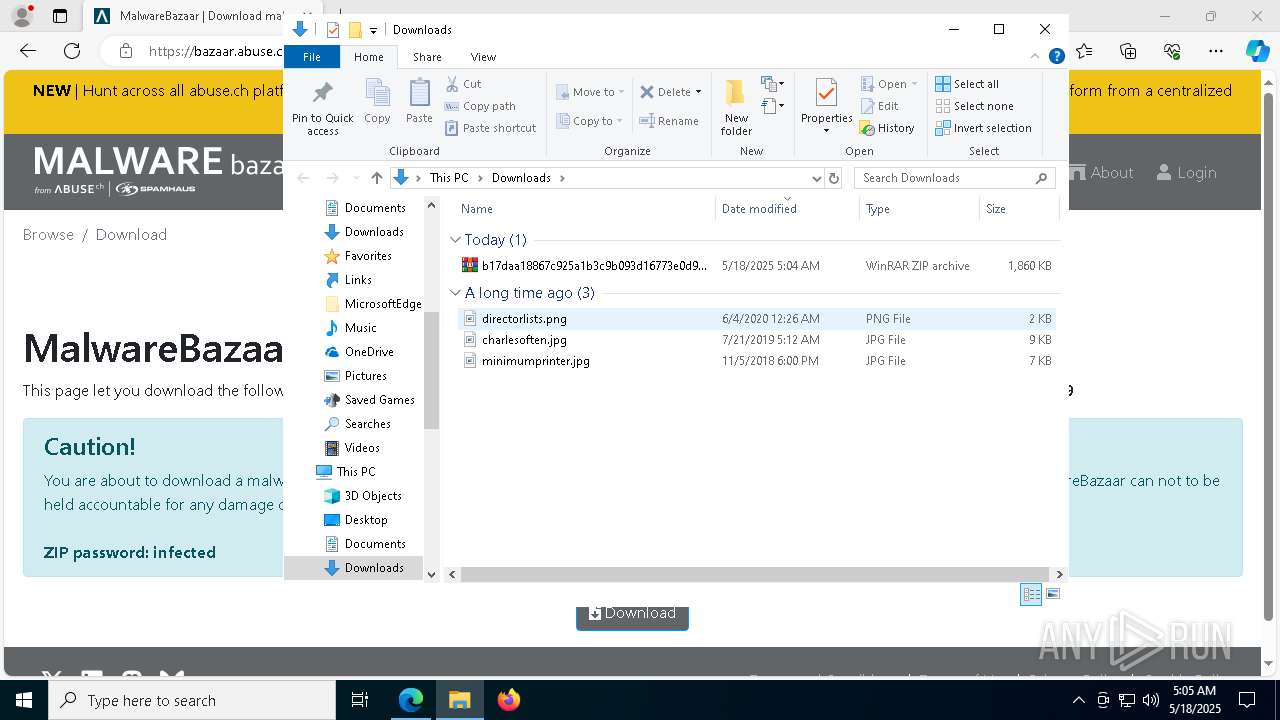
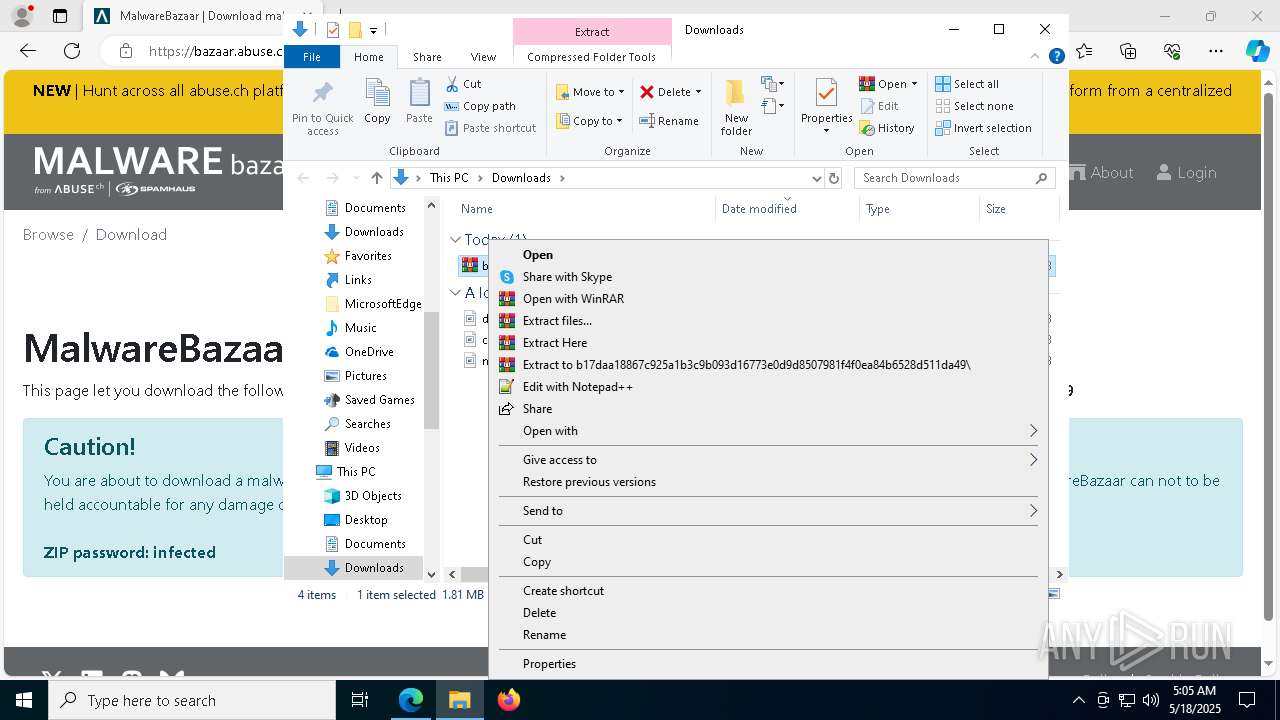
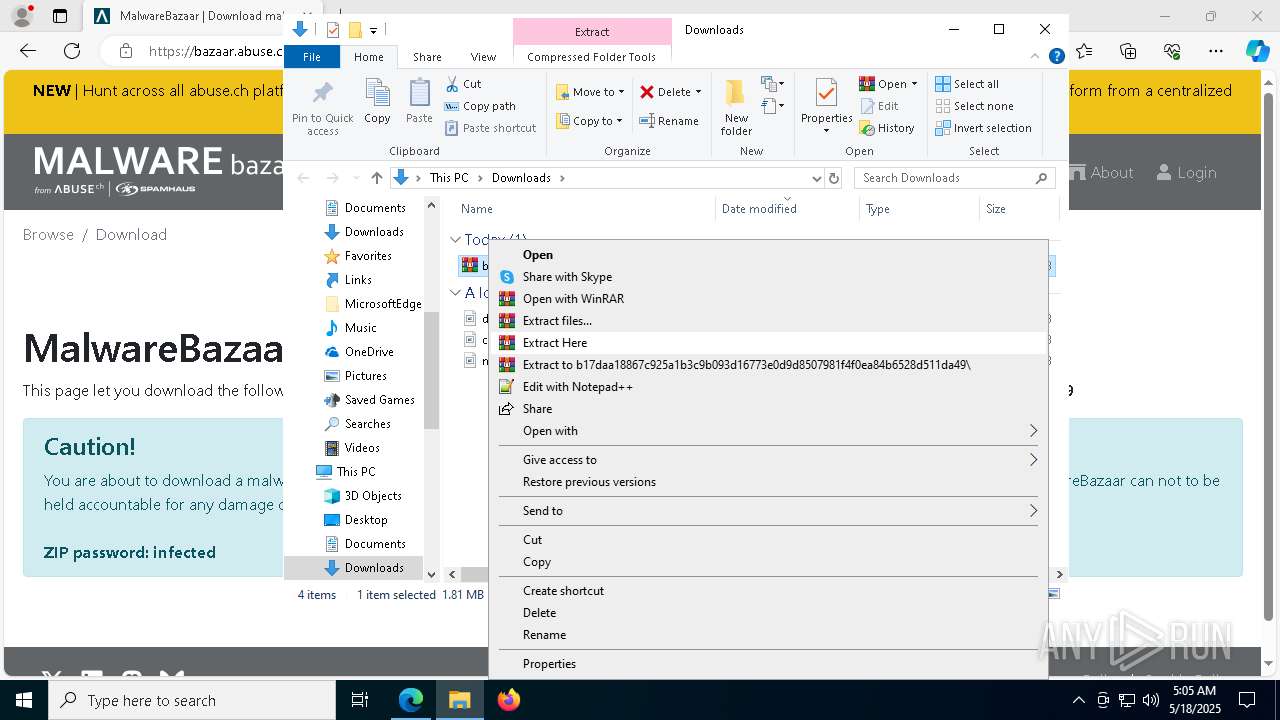
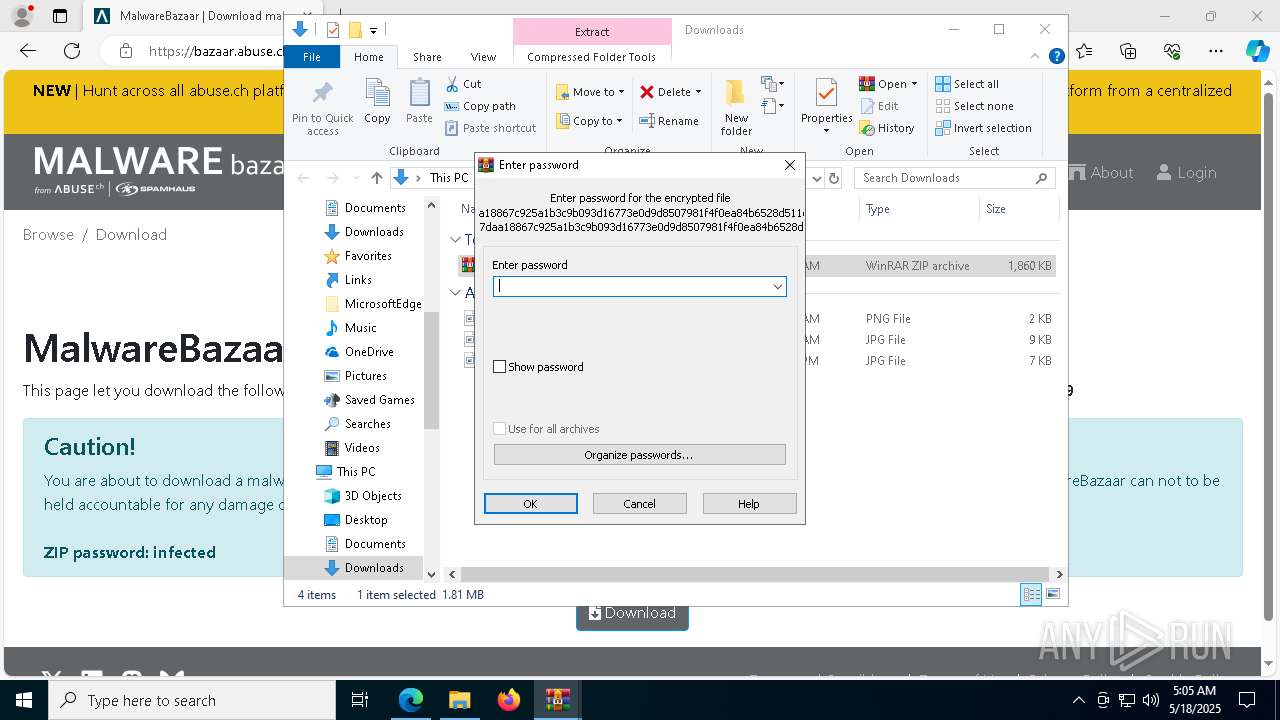
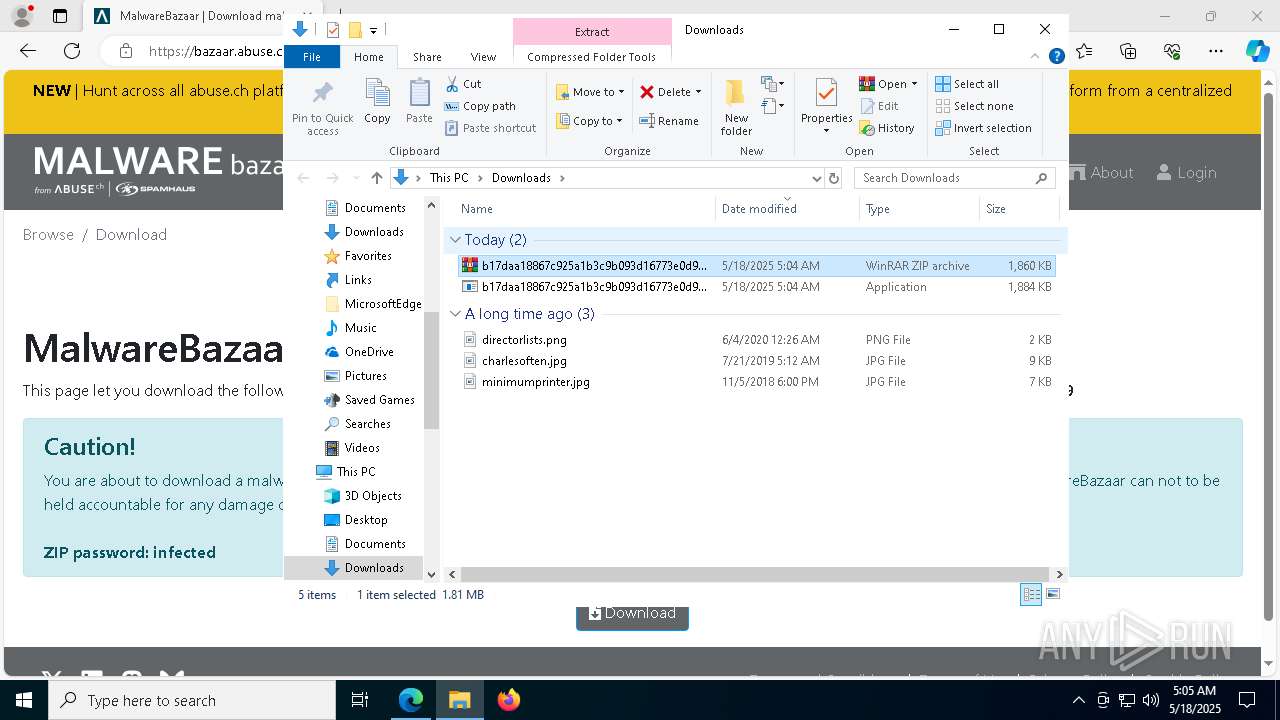
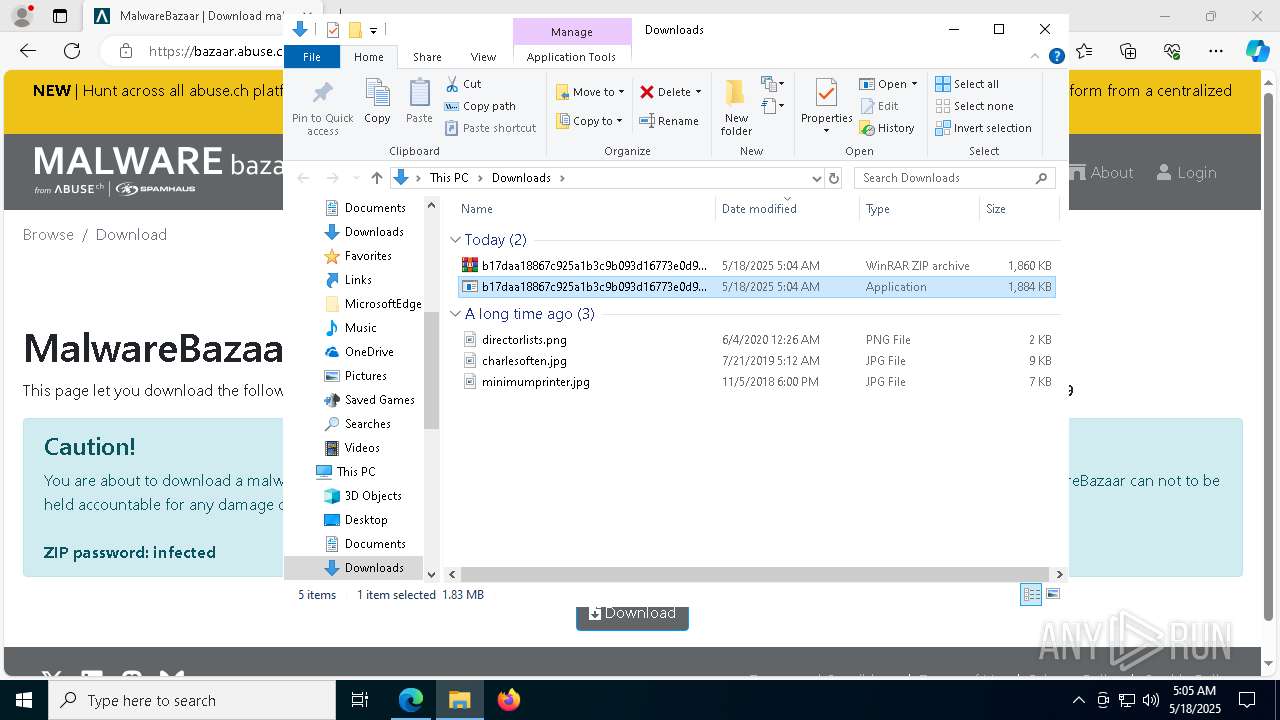
Manual execution by a user
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- WinRAR.exe (PID: 780)
Reads Environment values
- identity_helper.exe (PID: 8752)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 780)
Reads the software policy settings
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
Create files in a temporary directory
- b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe (PID: 8952)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- ramez.exe (PID: 1096)
- 4989c876fb.exe (PID: 7904)
Checks proxy server information
- ramez.exe (PID: 1096)
Process checks computer location settings
- ramez.exe (PID: 1096)
- H733BZGAQ3HYP01BOBS7YK21.exe (PID: 9180)
- 4989c876fb.exe (PID: 7904)
Creates files or folders in the user directory
- ramez.exe (PID: 1096)
The sample compiled with english language support
- 4989c876fb.exe (PID: 7904)
Changes the display of characters in the console
- cmd.exe (PID: 6712)
- cmd.exe (PID: 8284)
- cmd.exe (PID: 4452)
NirSoft software is detected
- nircmd.exe (PID: 8256)
Starts MODE.COM to configure console settings
- mode.com (PID: 7976)
Checks operating system version
- cmd.exe (PID: 4452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
205
Monitored processes
73
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Local\Temp\d610cf342e\ramez.exe" | C:\Users\admin\AppData\Local\Temp\d610cf342e\ramez.exe | H733BZGAQ3HYP01BOBS7YK21.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1180 | NSudoLG -U:T -P:E -UseCurrentConsole C:\Users\admin\AppData\Local\Temp\RG6I9Lo.bat | C:\Users\admin\AppData\Local\Temp\Work\NSudoLG.exe | — | cmd.exe | |||||||||||
User: admin Company: M2-Team Integrity Level: HIGH Description: NSudo Launcher Exit code: 0 Version: 9.0.2676.0 Modules
| |||||||||||||||
| 1660 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://bazaar.abuse.ch/download/b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3020 | reg query "HKU\S-1-5-19" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7388 --field-trial-handle=2412,i,14576224336276097396,3021366606454880394,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4108 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 859
Read events
8 828
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0B005D3CF8932F00 | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9101673CF8932F00 | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459410 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {014688BF-3DEA-497C-8E0F-5A732A40E110} | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459410 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C6DE20C4-2AB7-416F-893E-4E3C71ACE751} | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459410 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6FD48455-04F1-438F-A234-C22B039C8703} | |||
| (PID) Process: | (2560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459410 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D4E5C75C-D593-44A8-9F0F-5F86C9EDB3D6} | |||
Executable files
17
Suspicious files
90
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba2a.TMP | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba68.TMP | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba68.TMP | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bad6.TMP | — | |
MD5:— | SHA256:— | |||
| 2560 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
57
DNS requests
58
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8952 | b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/mine/random.exe | unknown | — | — | unknown |
1096 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
1096 | ramez.exe | POST | 200 | 185.156.72.96:80 | http://185.156.72.96/te4h2nus/index.php | unknown | — | — | malicious |
1096 | ramez.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/newdef/random.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7376 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2560 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7376 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7376 | msedge.exe | 151.101.130.49:443 | bazaar.abuse.ch | FASTLY | US | whitelisted |
7376 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bazaar.abuse.ch |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
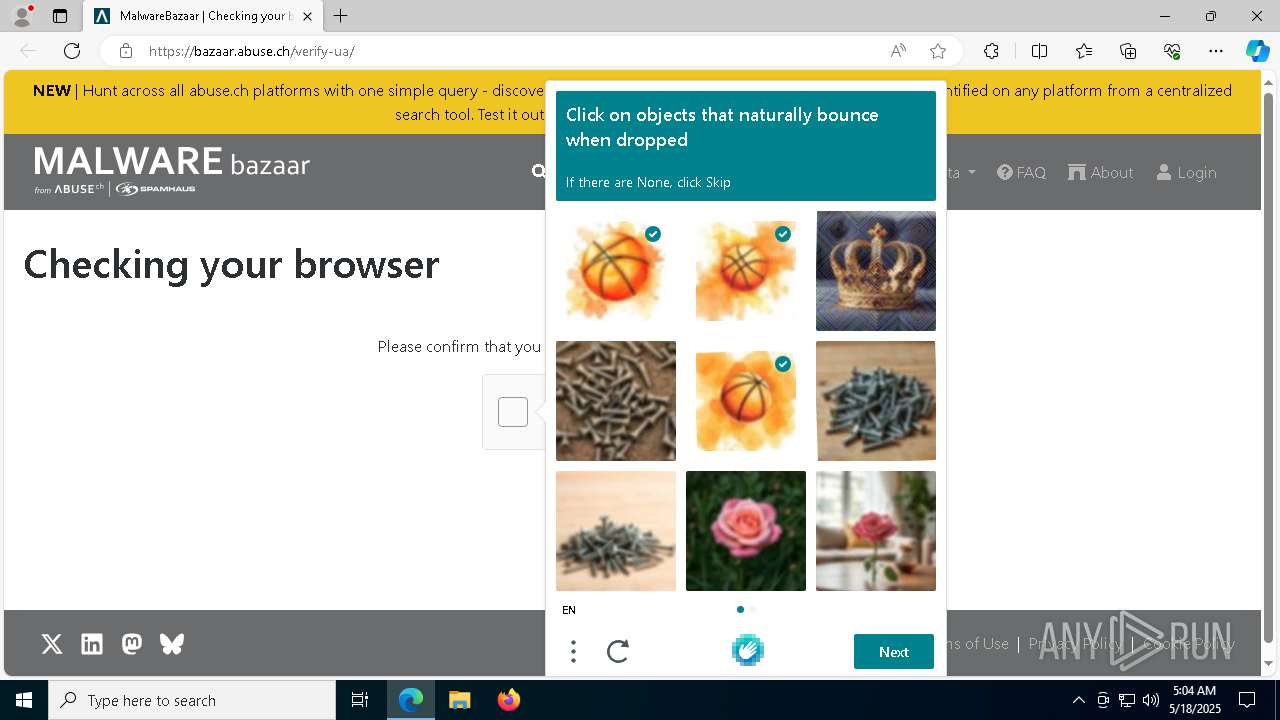
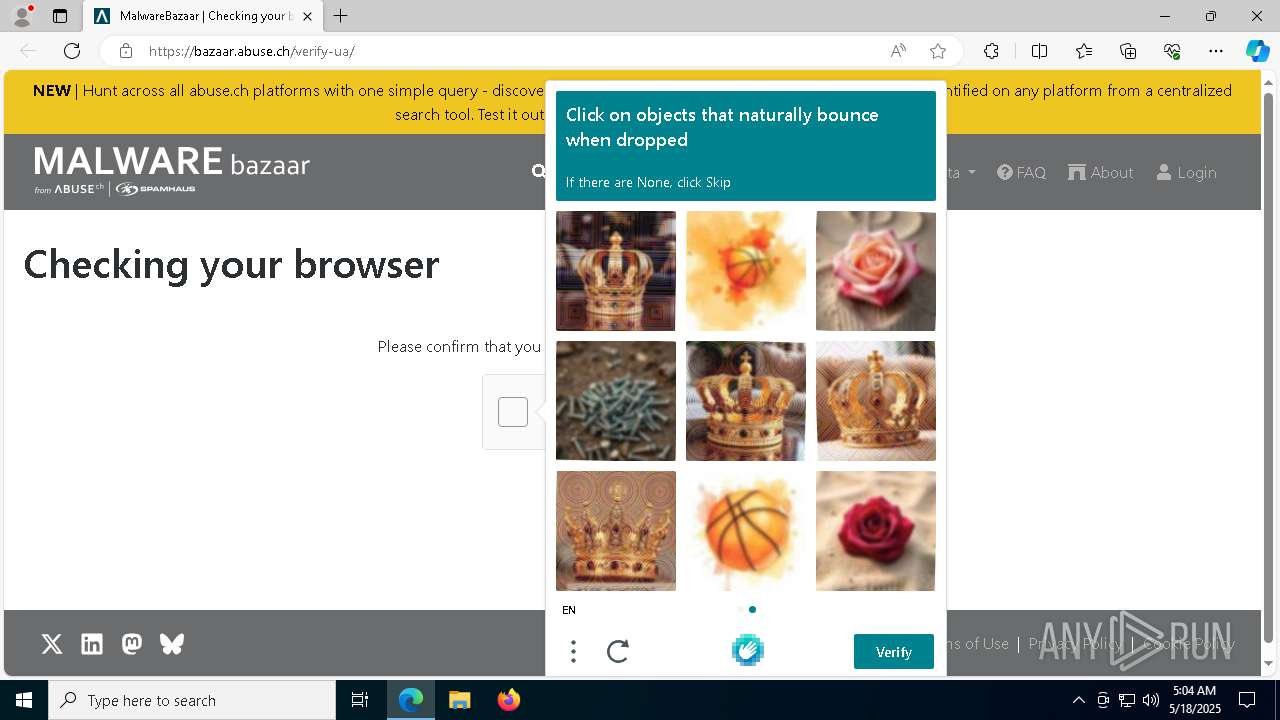
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7376 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (cornerdurv .top) |
8952 | b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (cornerdurv .top) in TLS SNI |
8952 | b17daa18867c925a1b3c9b093d16773e0d9d8507981f4f0ea84b6528d511da49.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (cornerdurv .top) in TLS SNI |