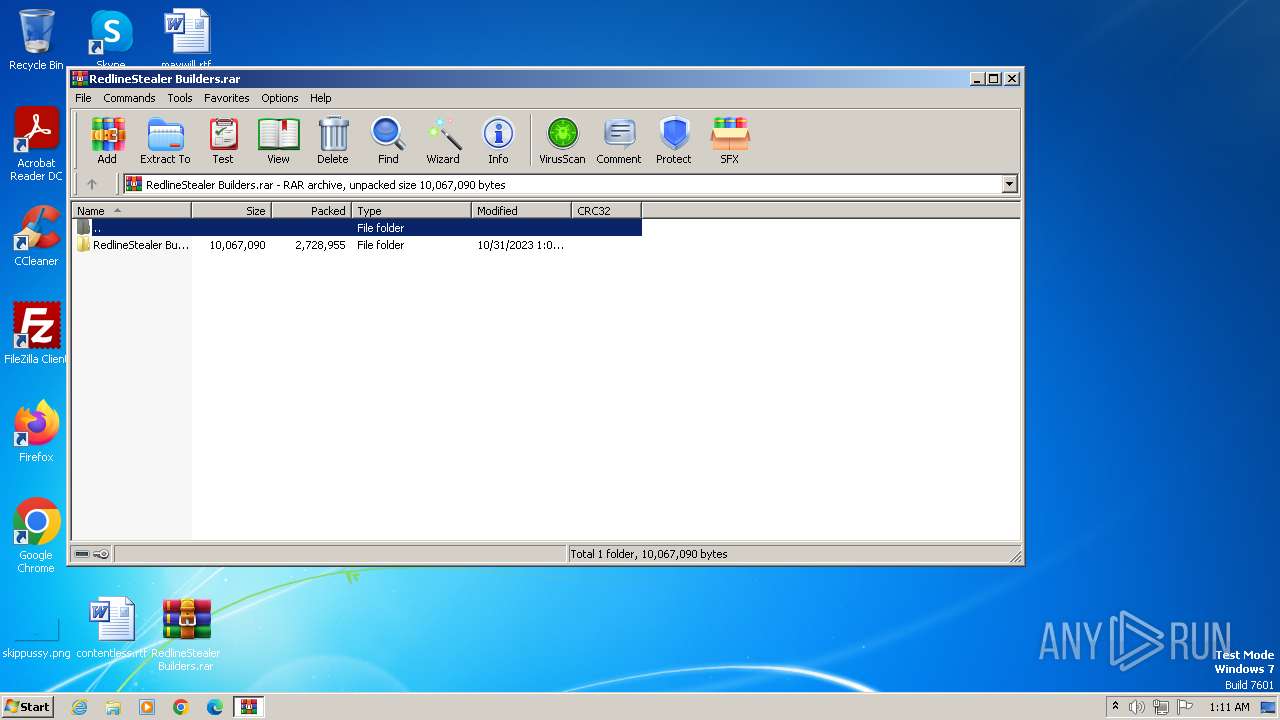
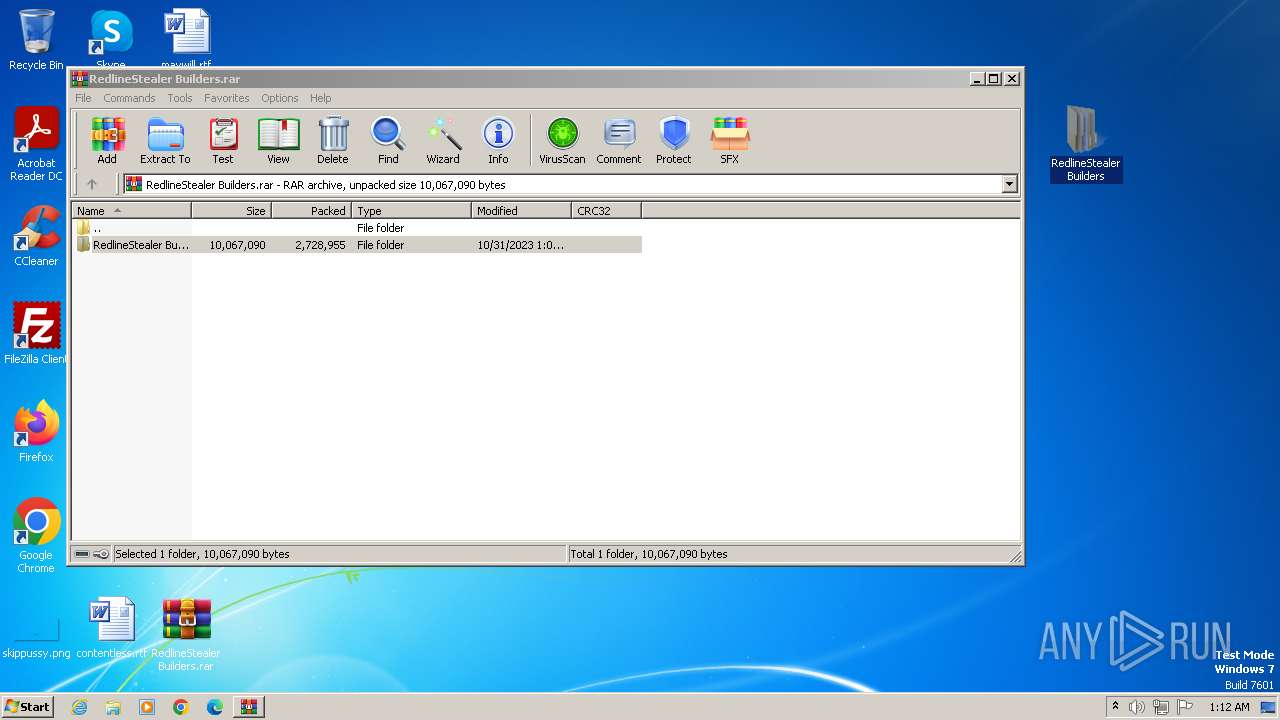
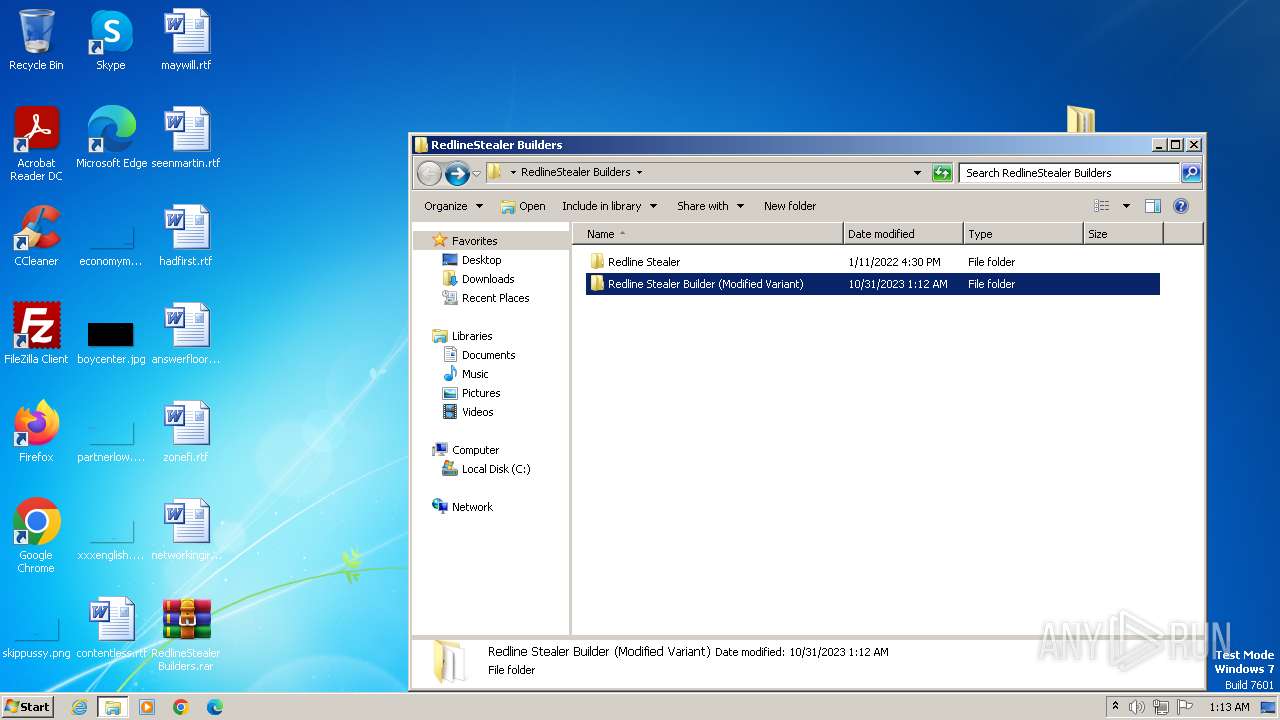
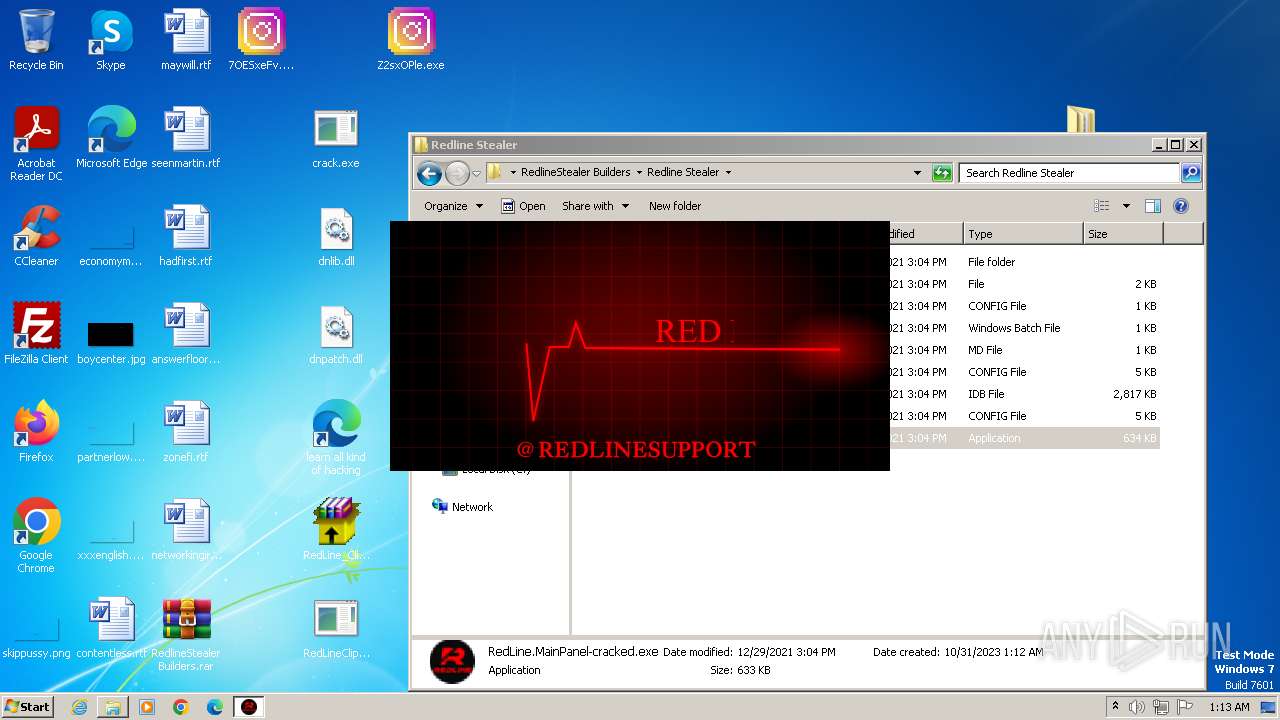
| File name: | RedlineStealer Builders.rar |
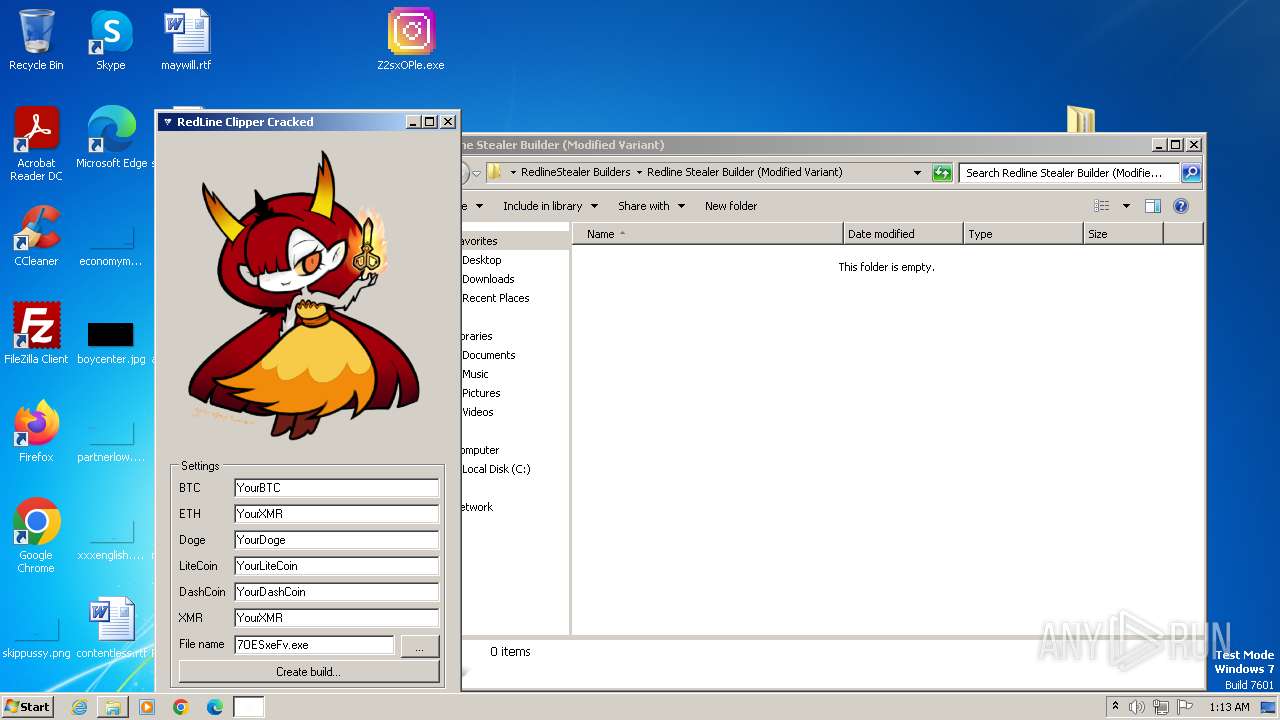
| Full analysis: | https://app.any.run/tasks/73f01445-0492-47a4-97ae-1889c0934793 |
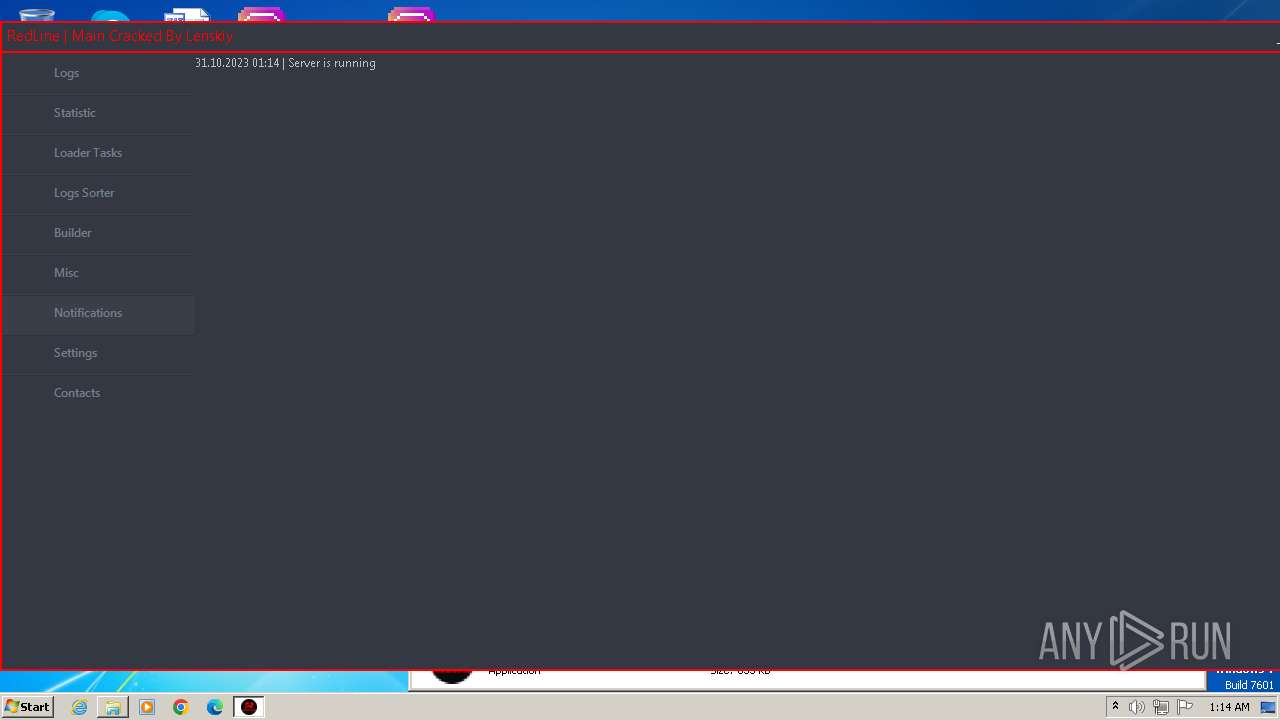
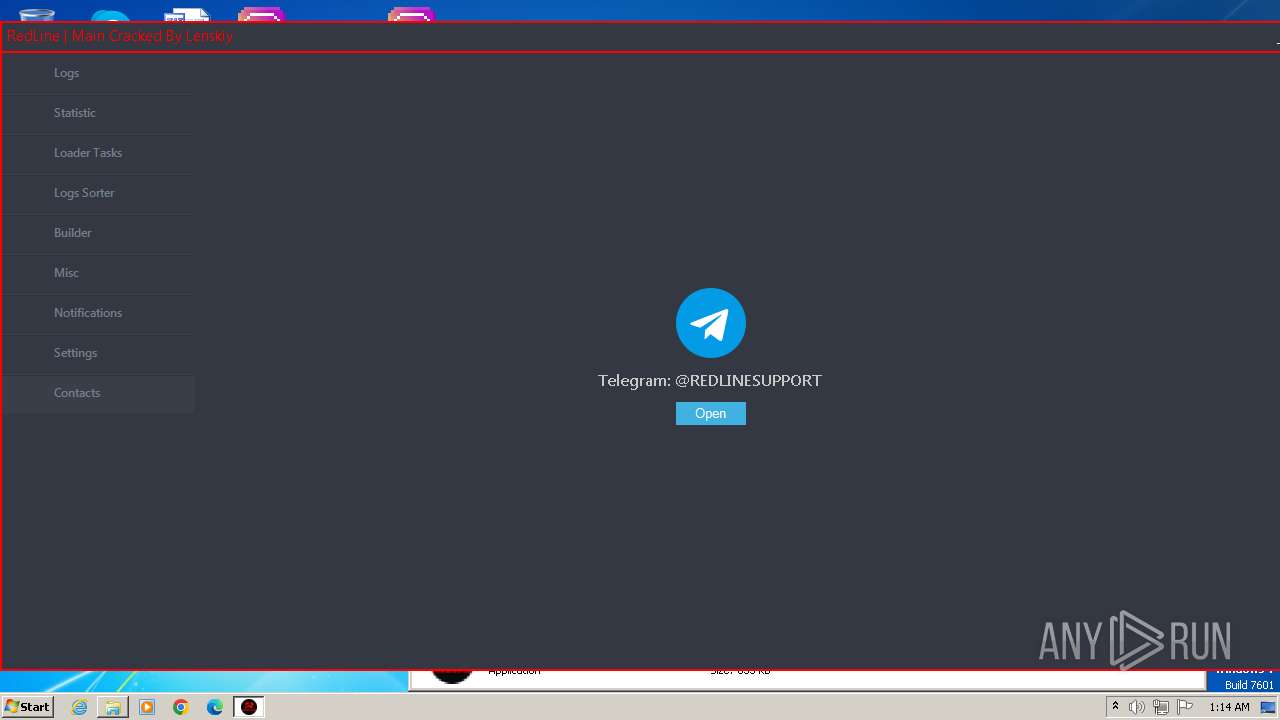
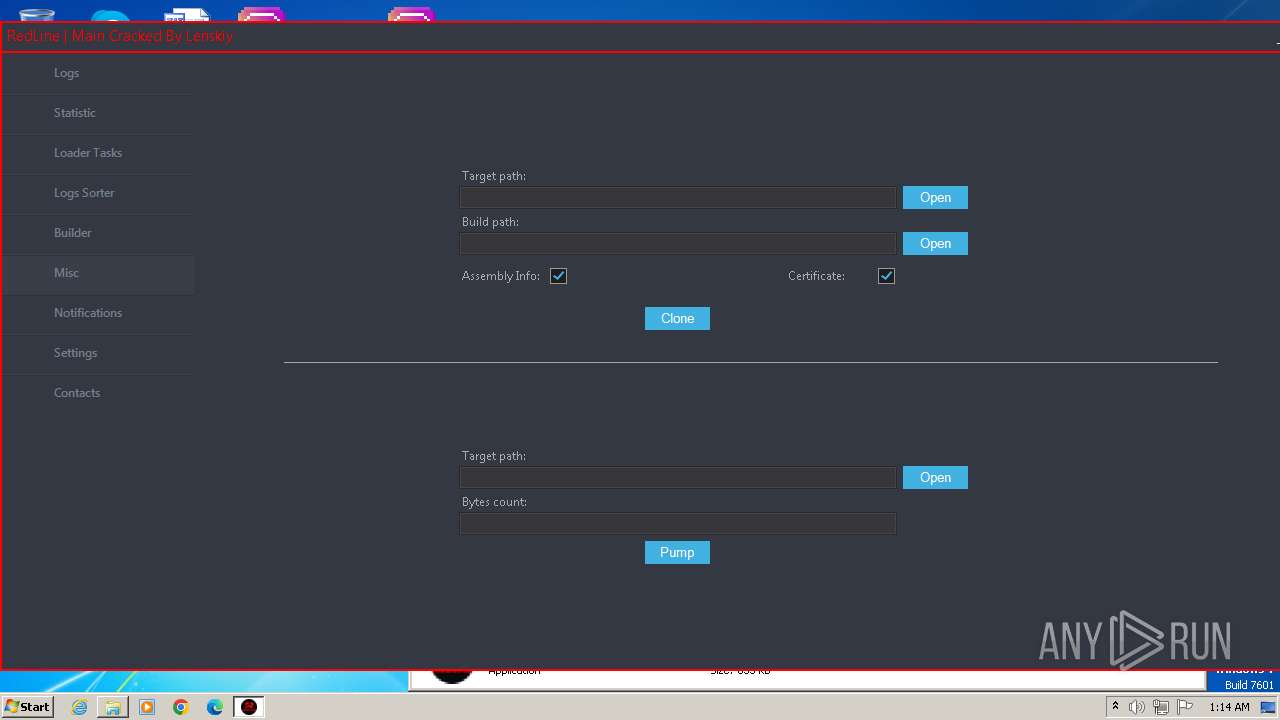
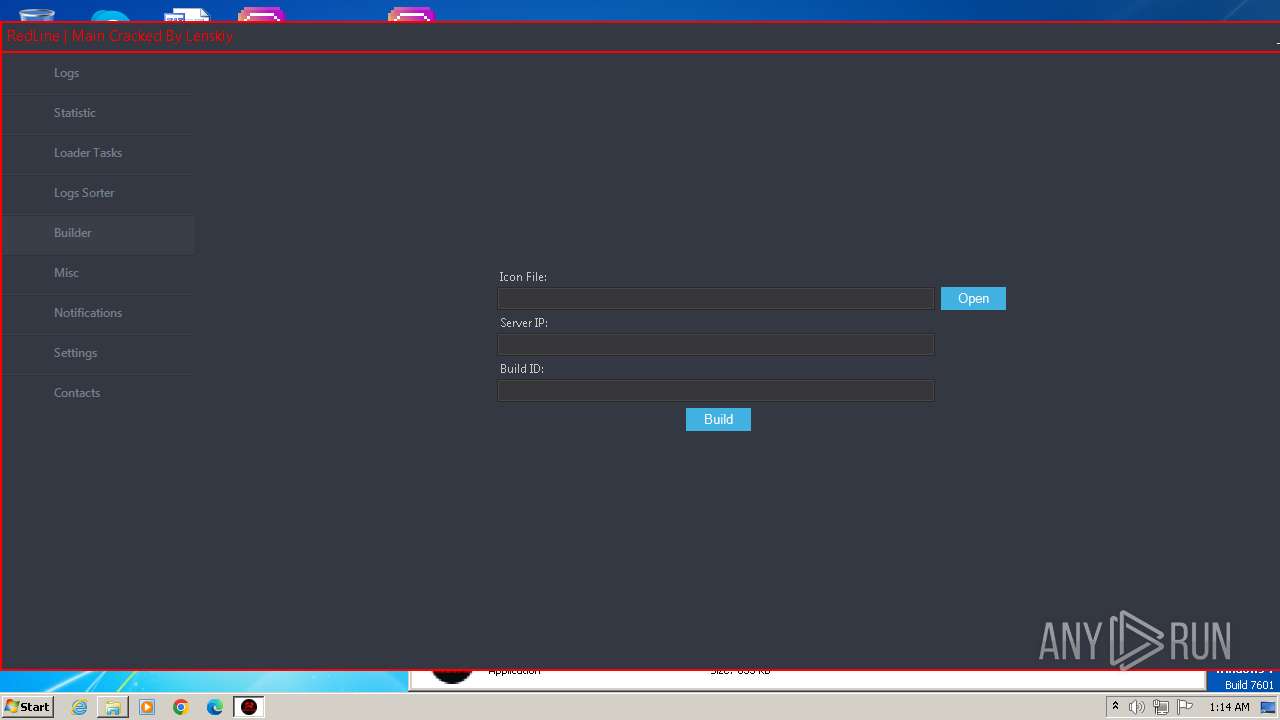
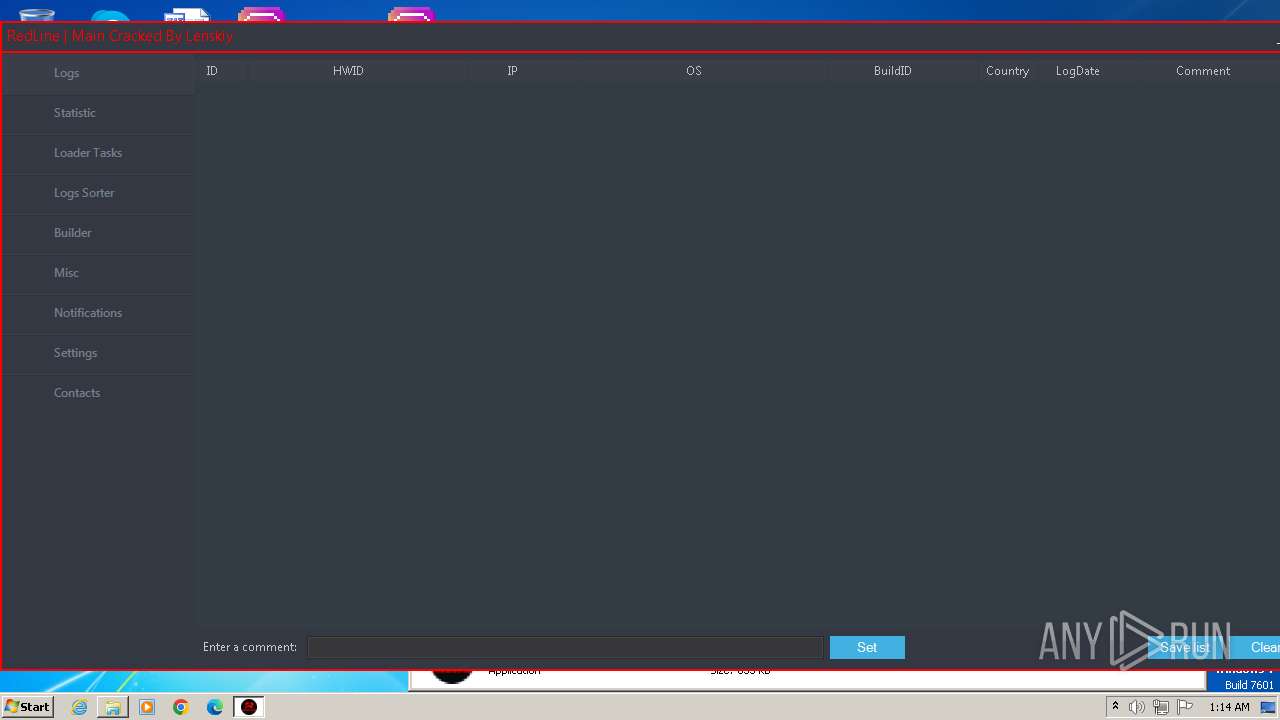
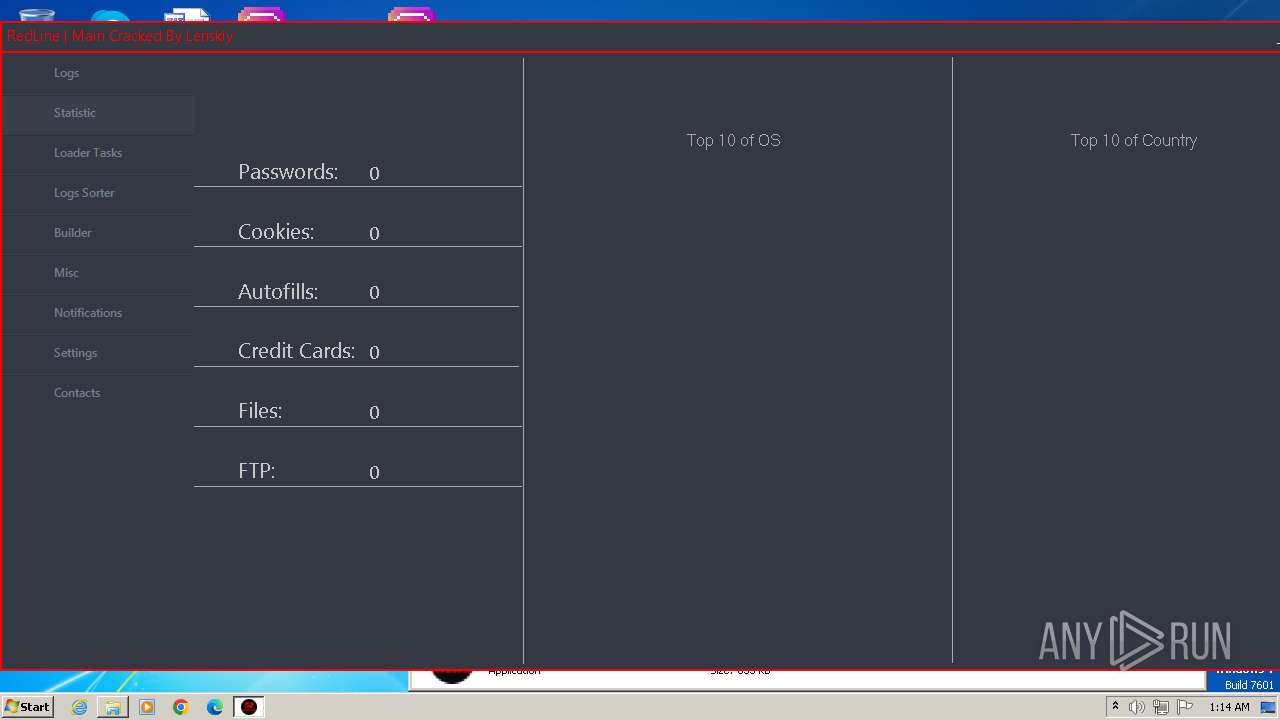
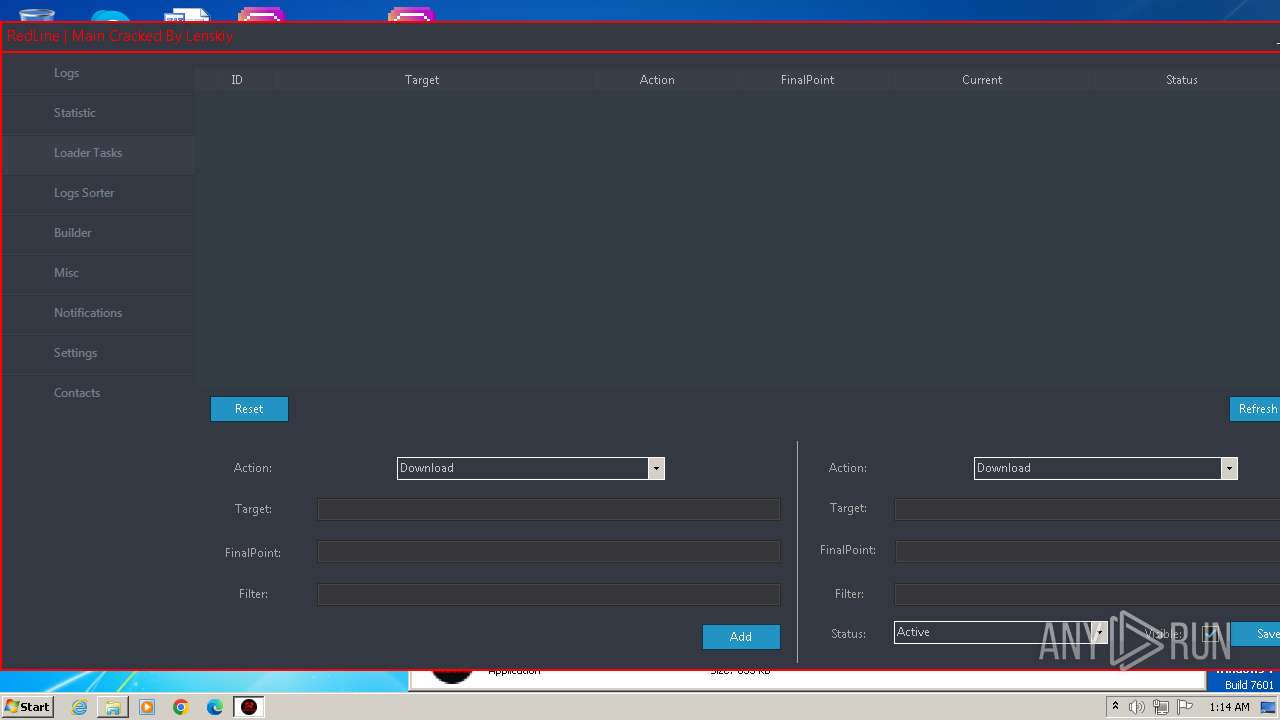
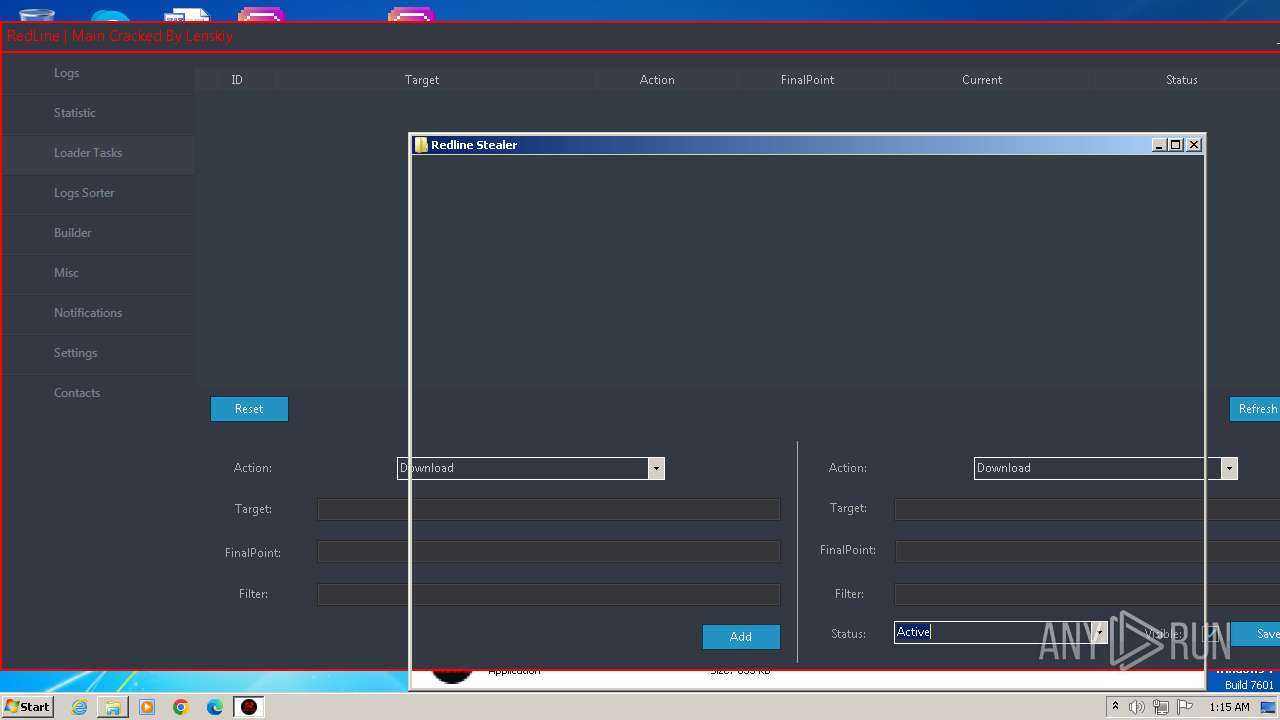
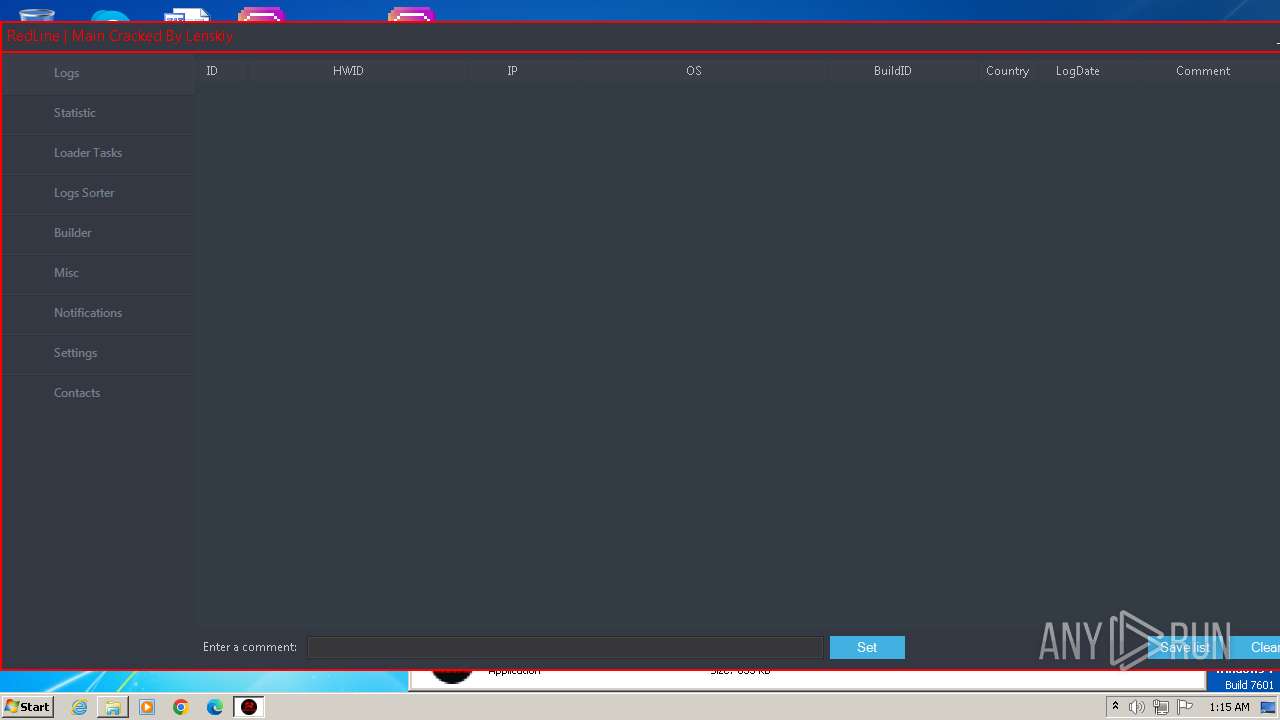
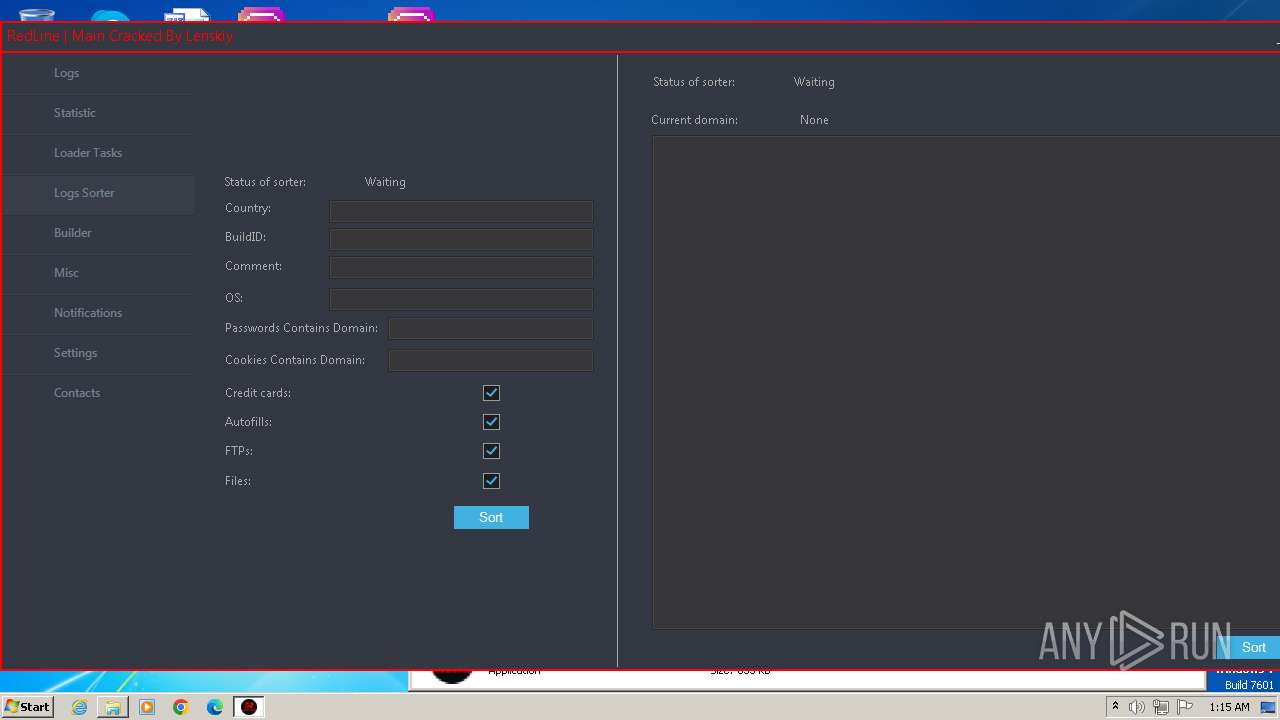
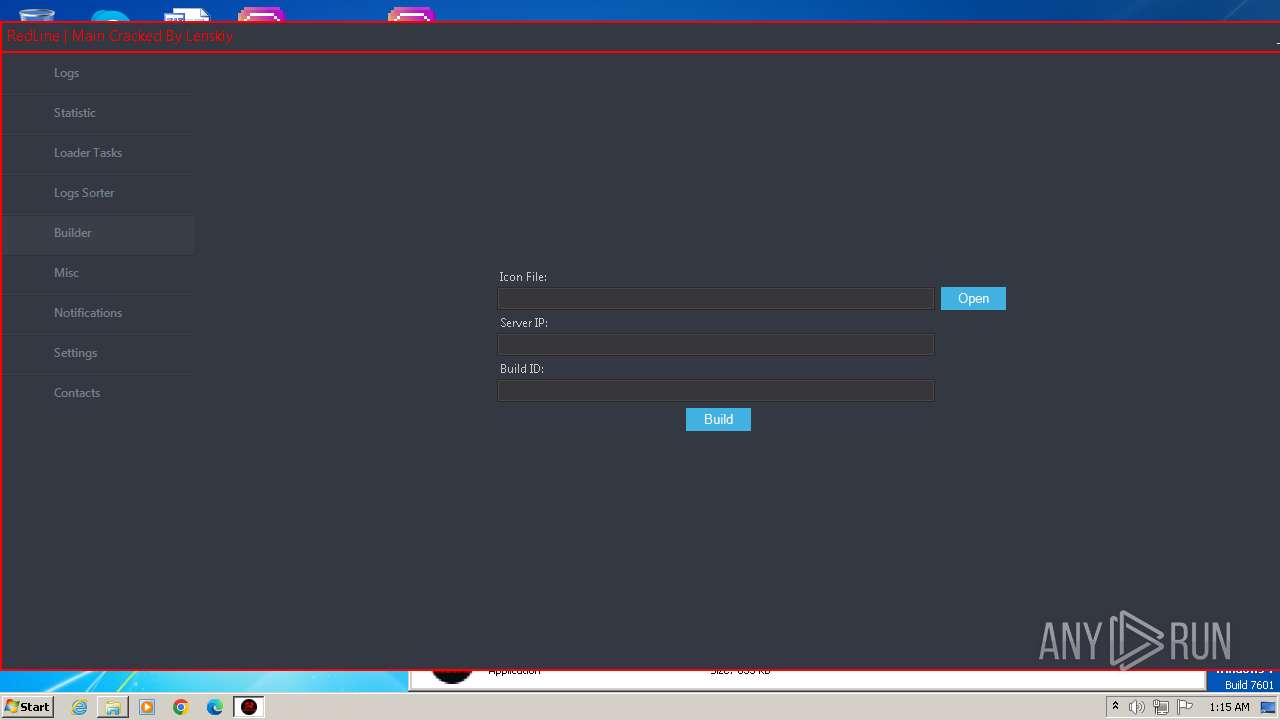
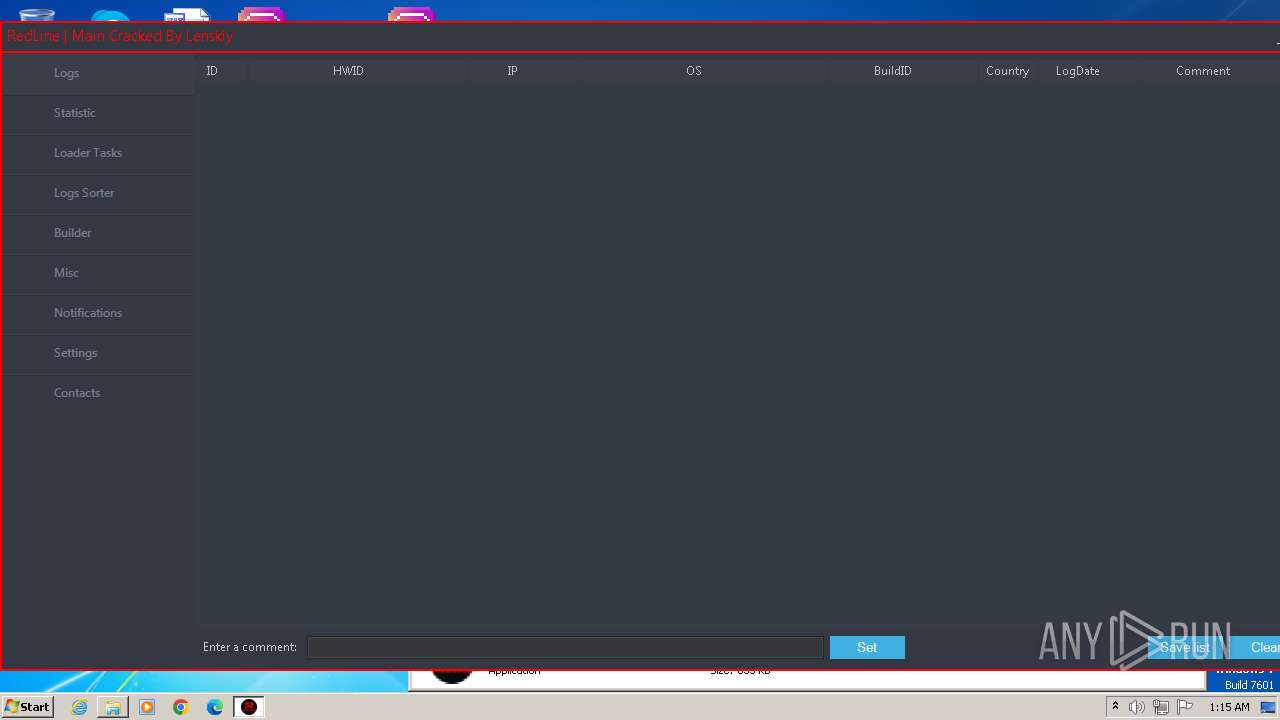
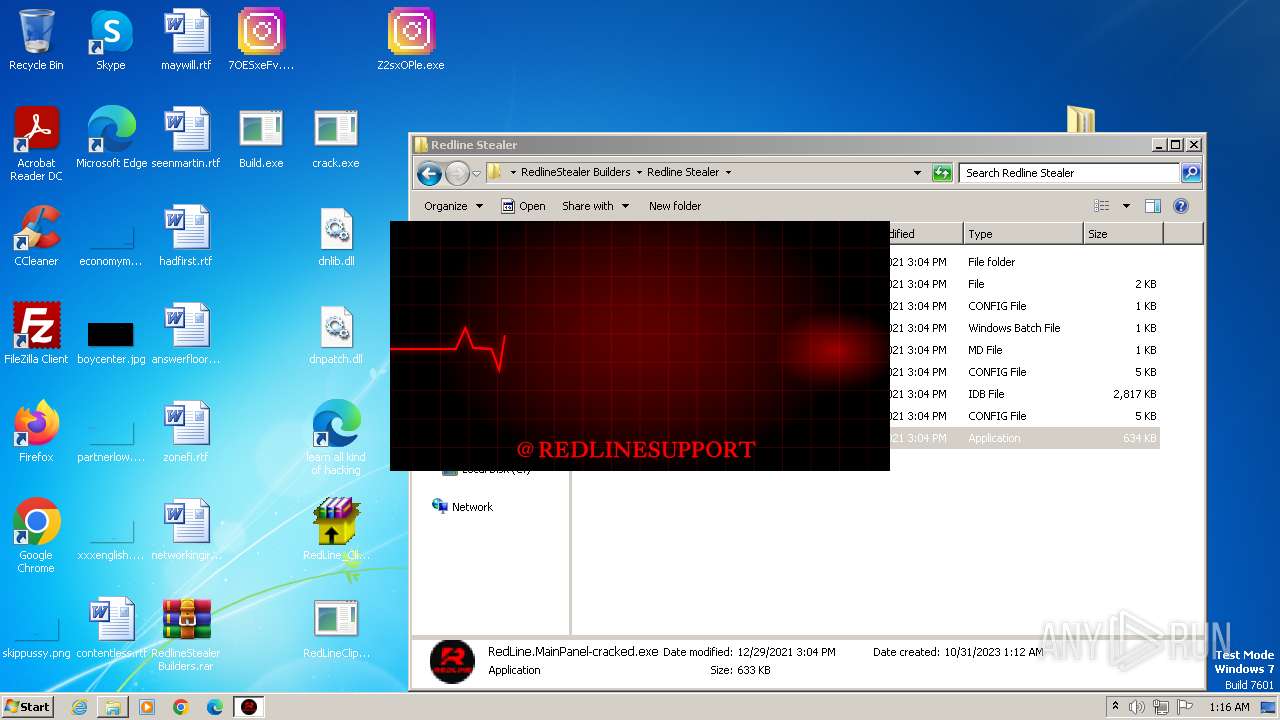
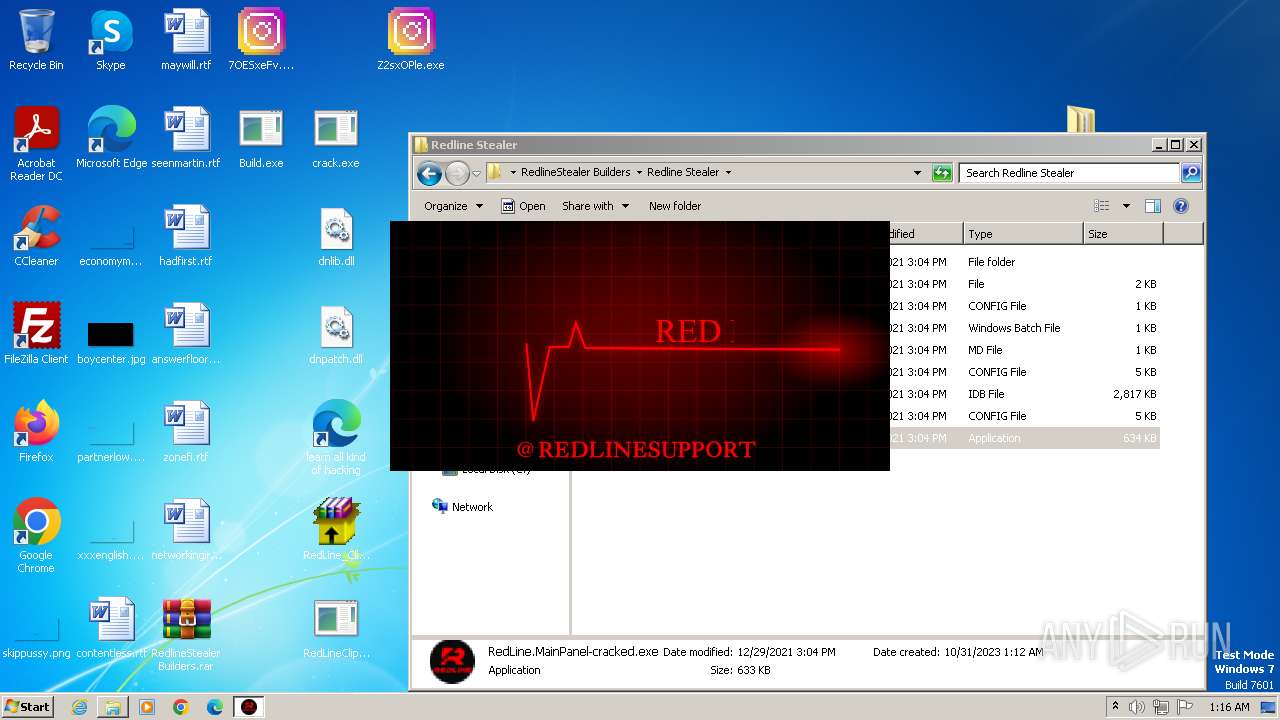
| Verdict: | Malicious activity |
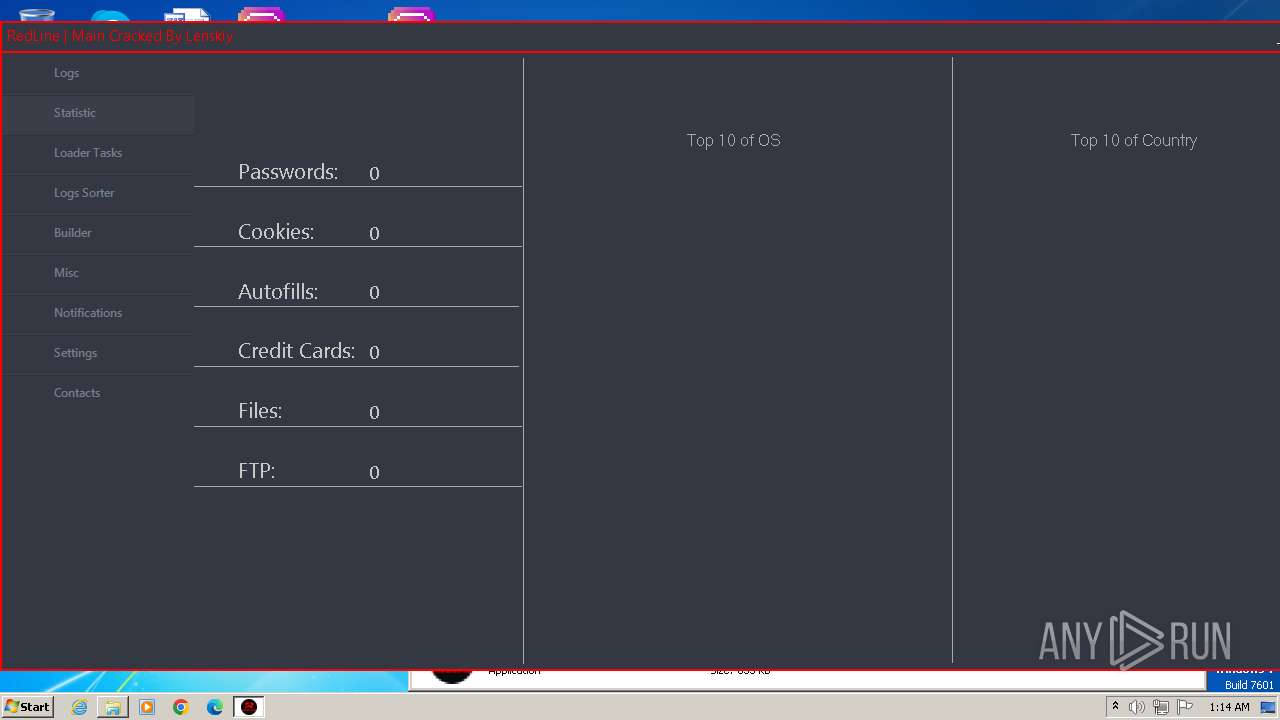
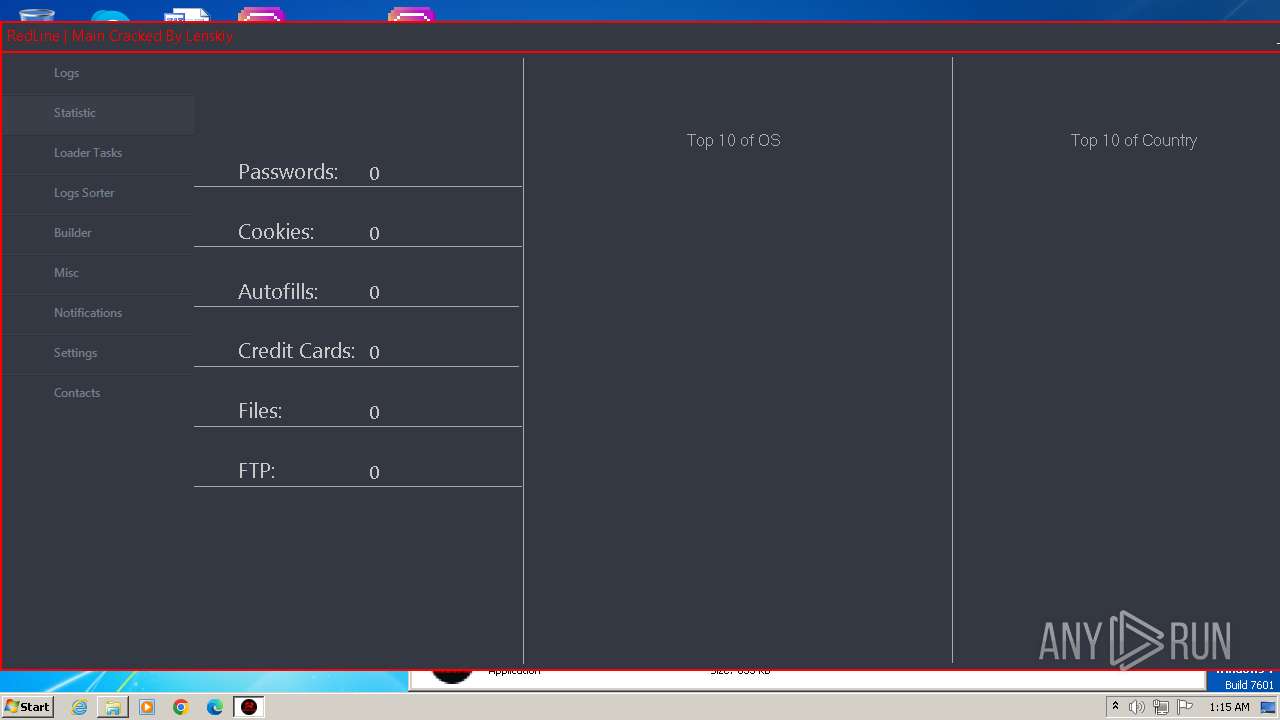
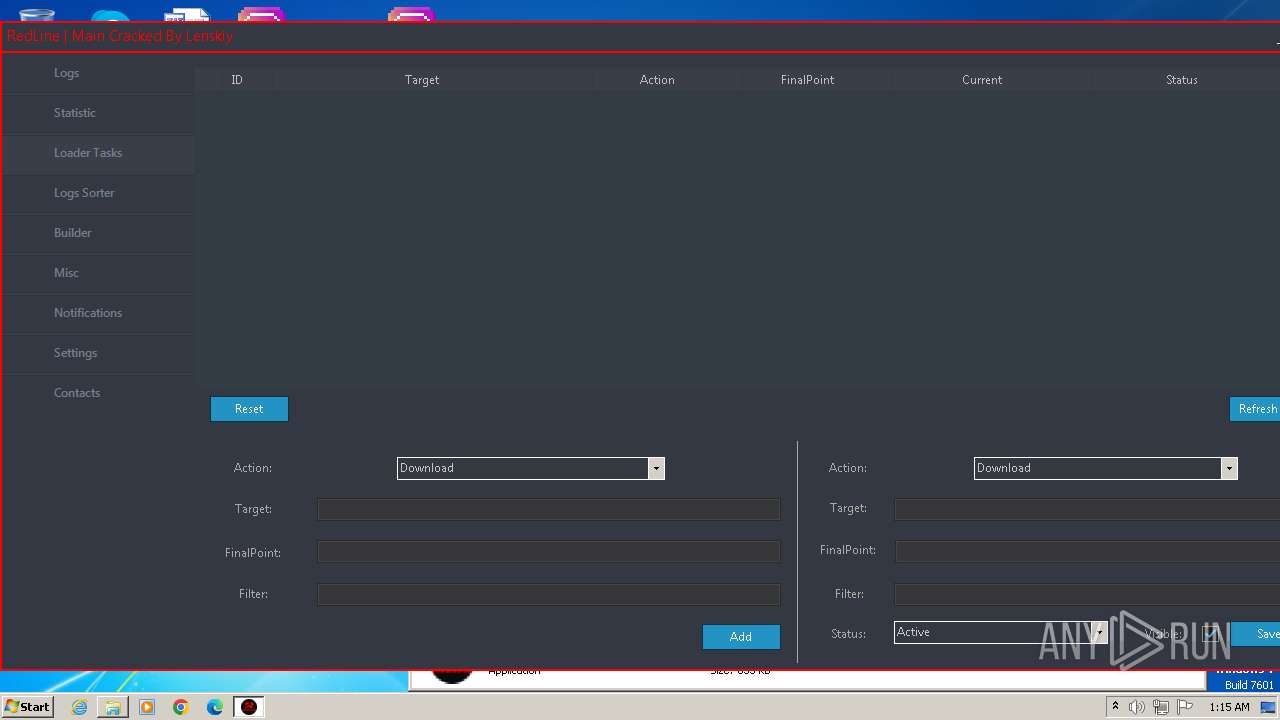
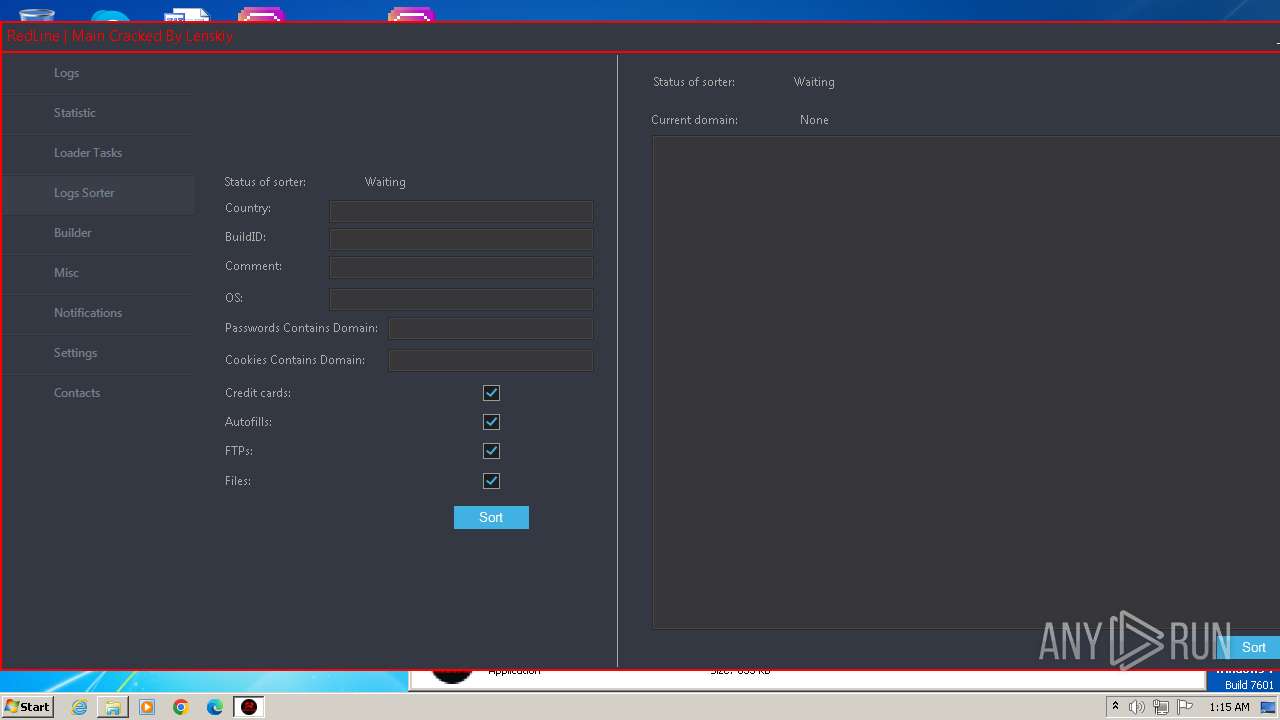
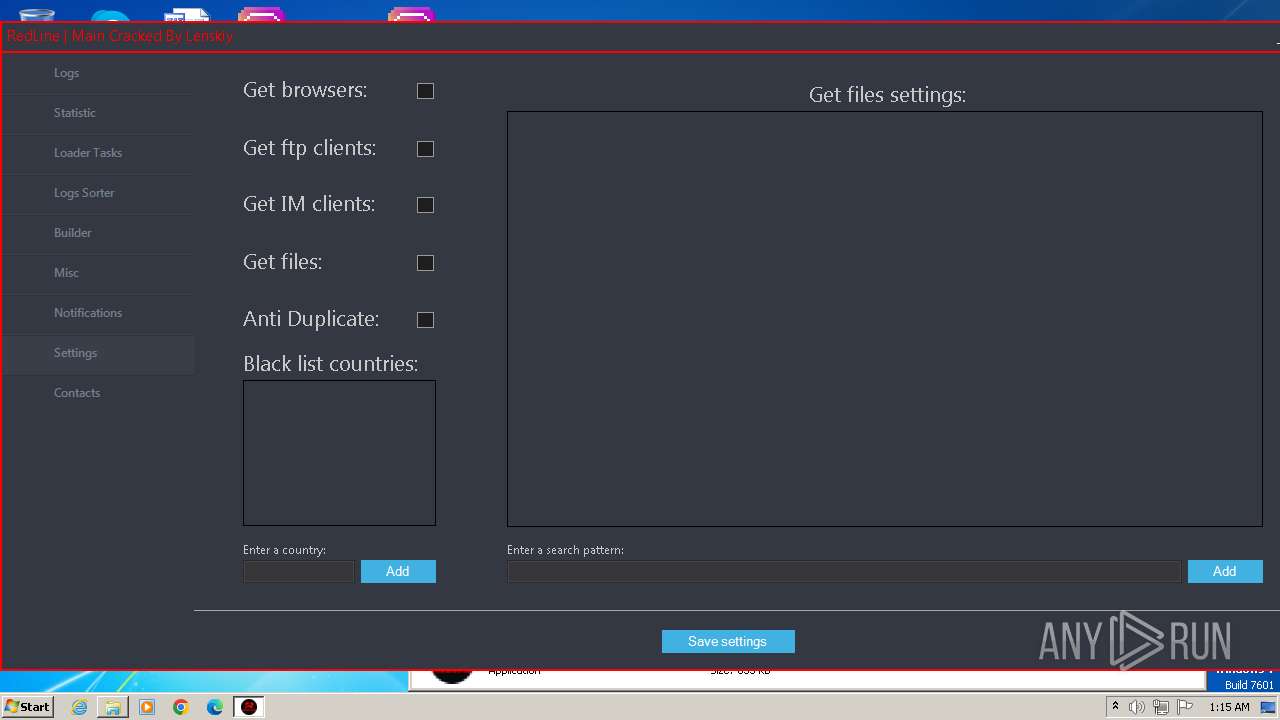
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
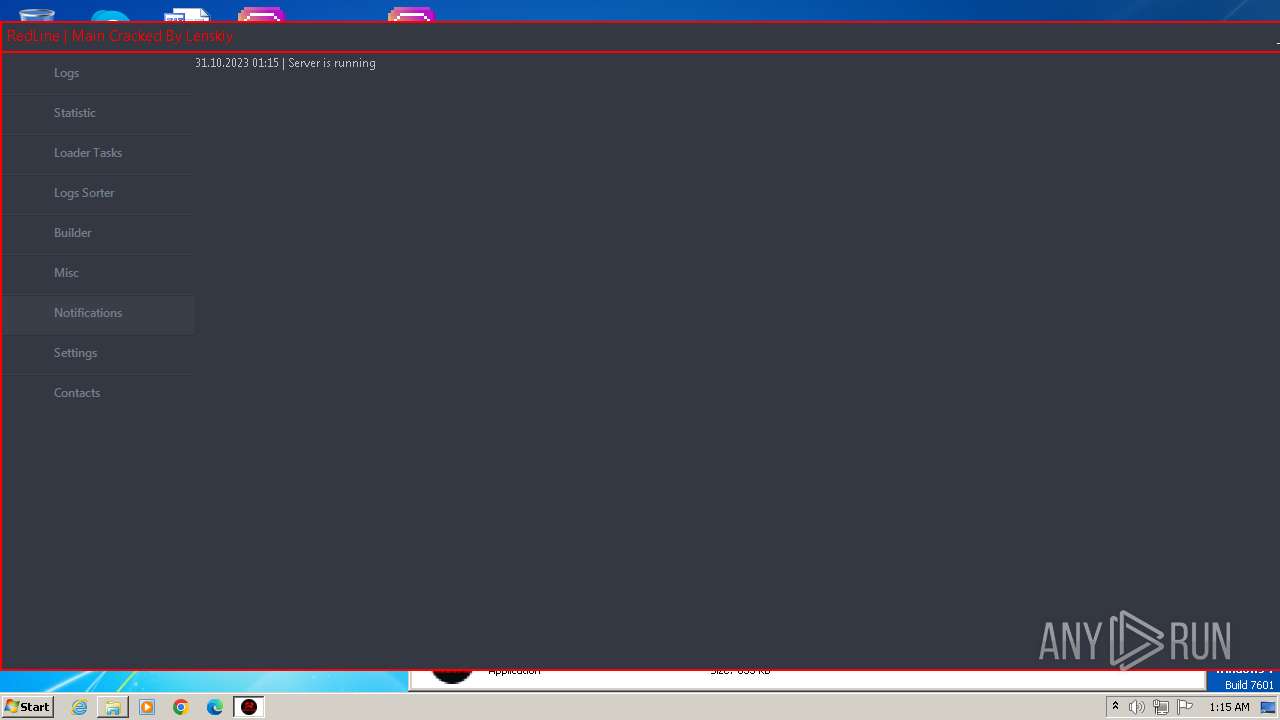
| Analysis date: | October 31, 2023, 01:11:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | BE78283A207823163C2DCC20A98D7145 |
| SHA1: | 207B43F5019F78AC019C60C2654E1BBF26F95219 |
| SHA256: | DBB87E72A26F96371CDBE93CA24E7E6A1DBF33F08243A956F2F8344D4E20E2EB |
| SSDEEP: | 98304:EzLqGxpzLeLGg1PuyF/av3FNS7hBn2Kl3Mxin8dDRxdNc/I5J4It/APNsRG9aRS7:av/Sbl |
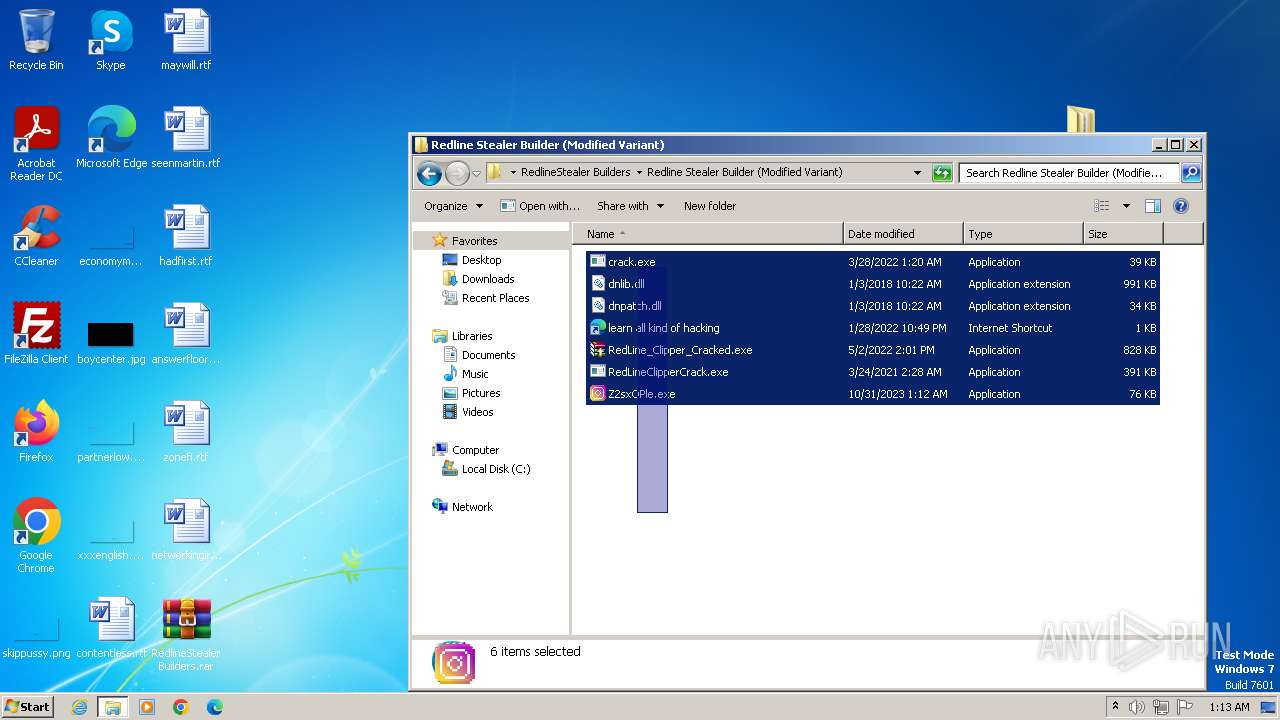
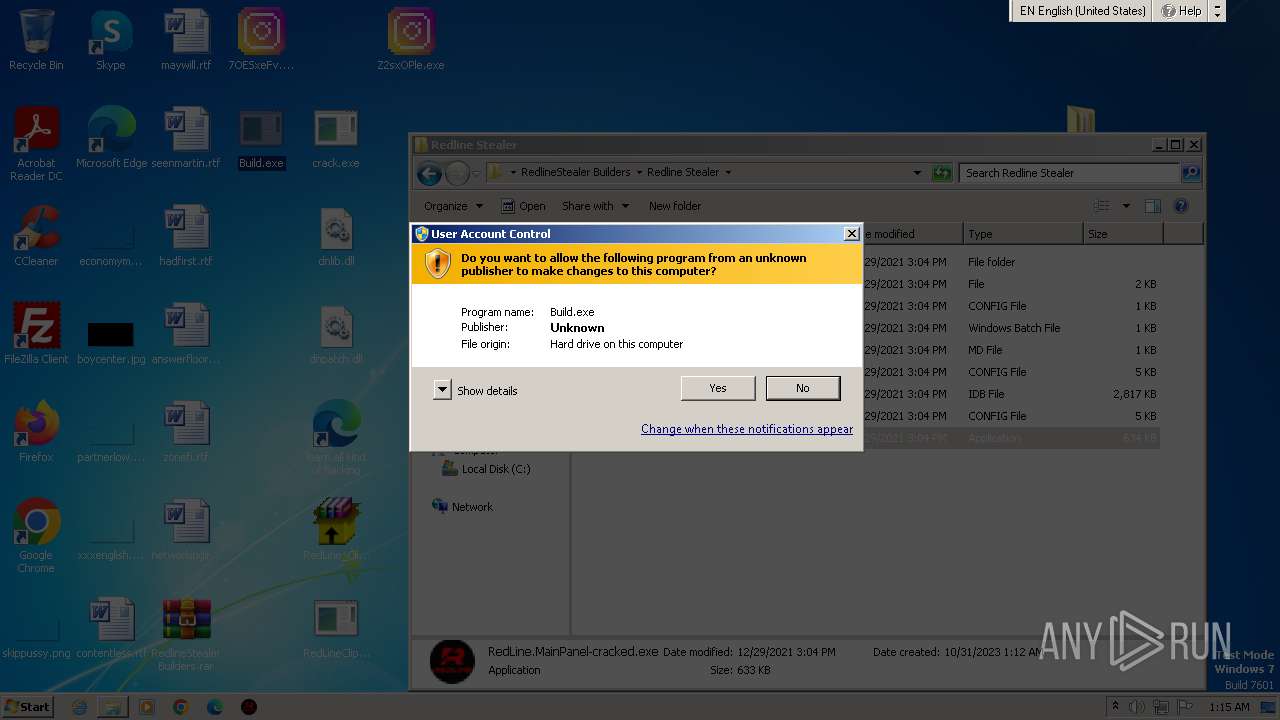
MALICIOUS
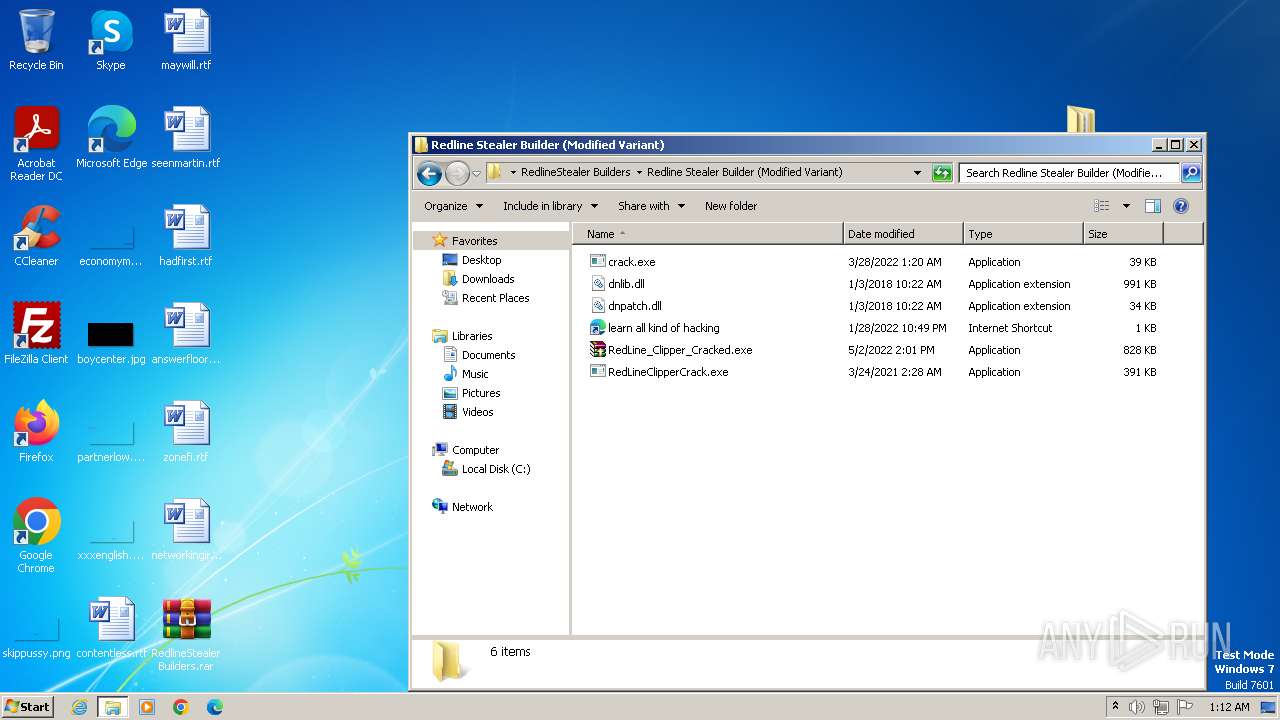
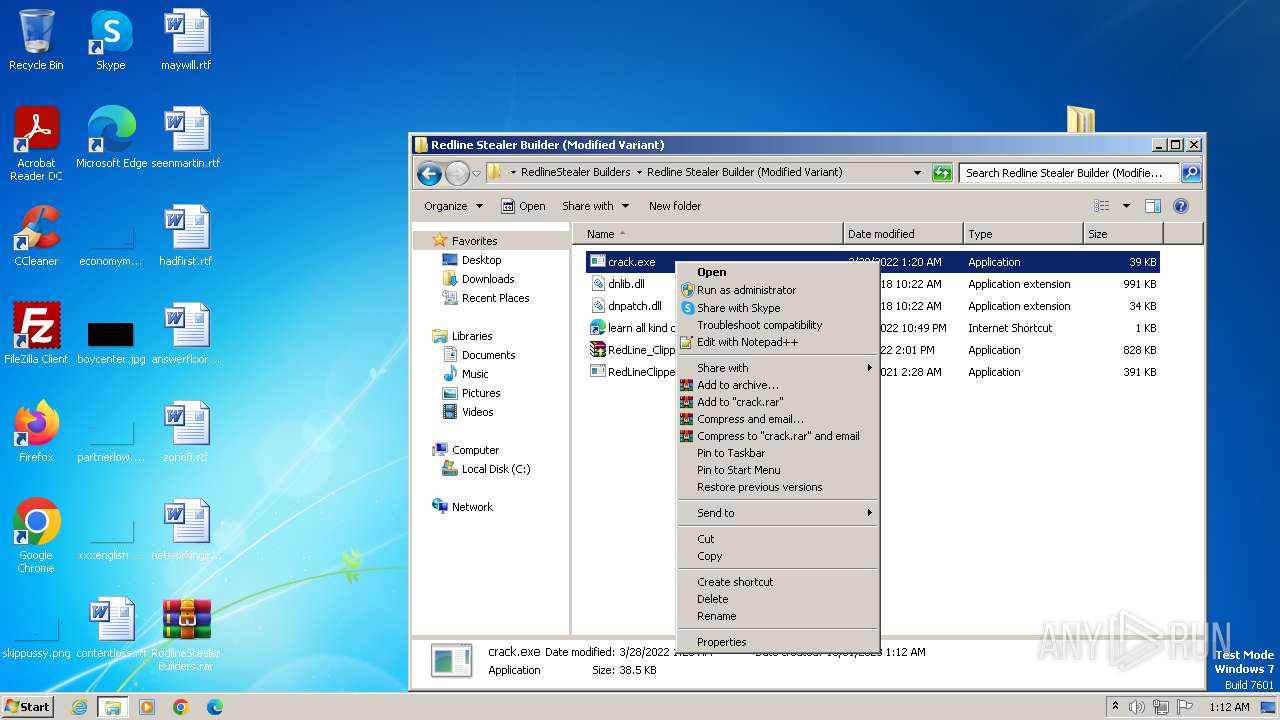
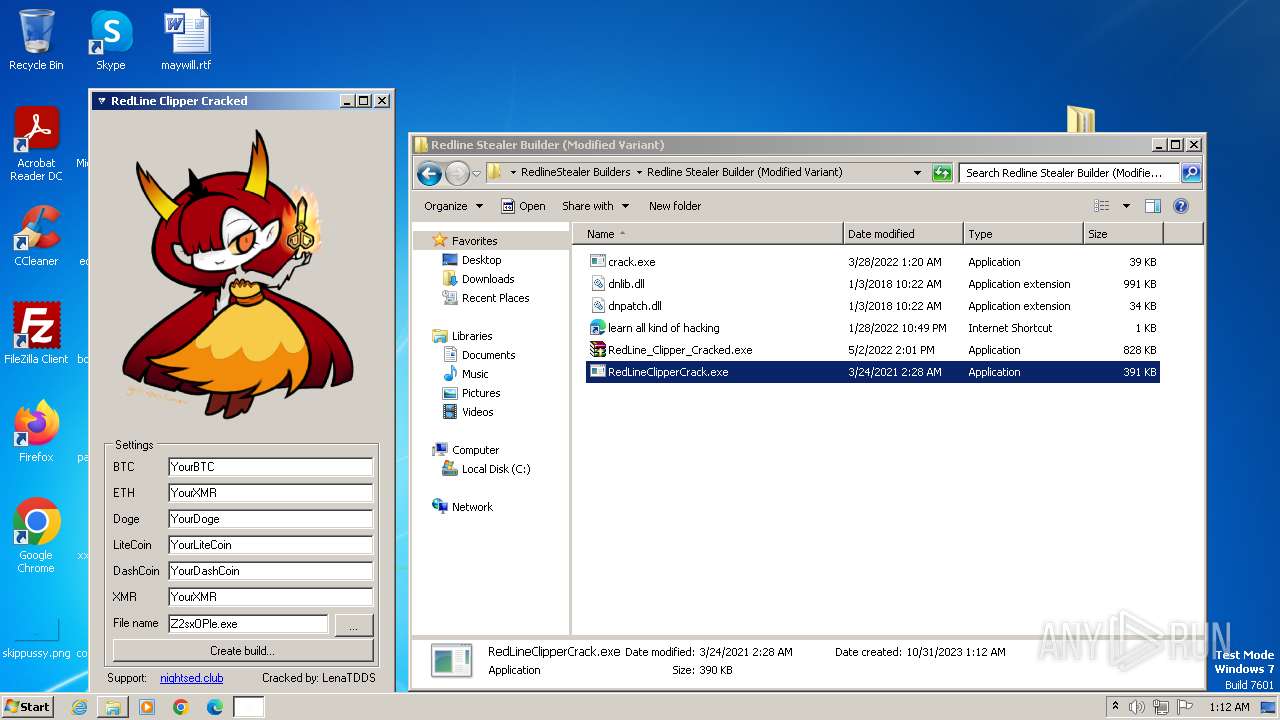
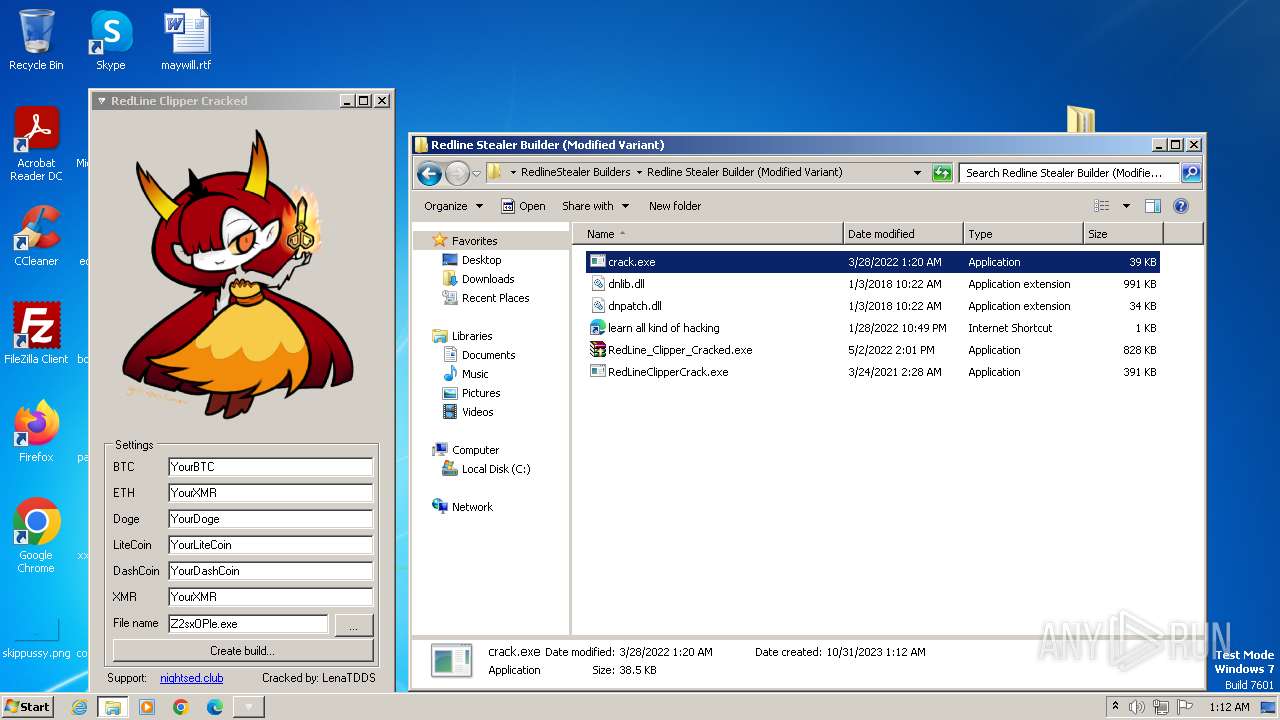
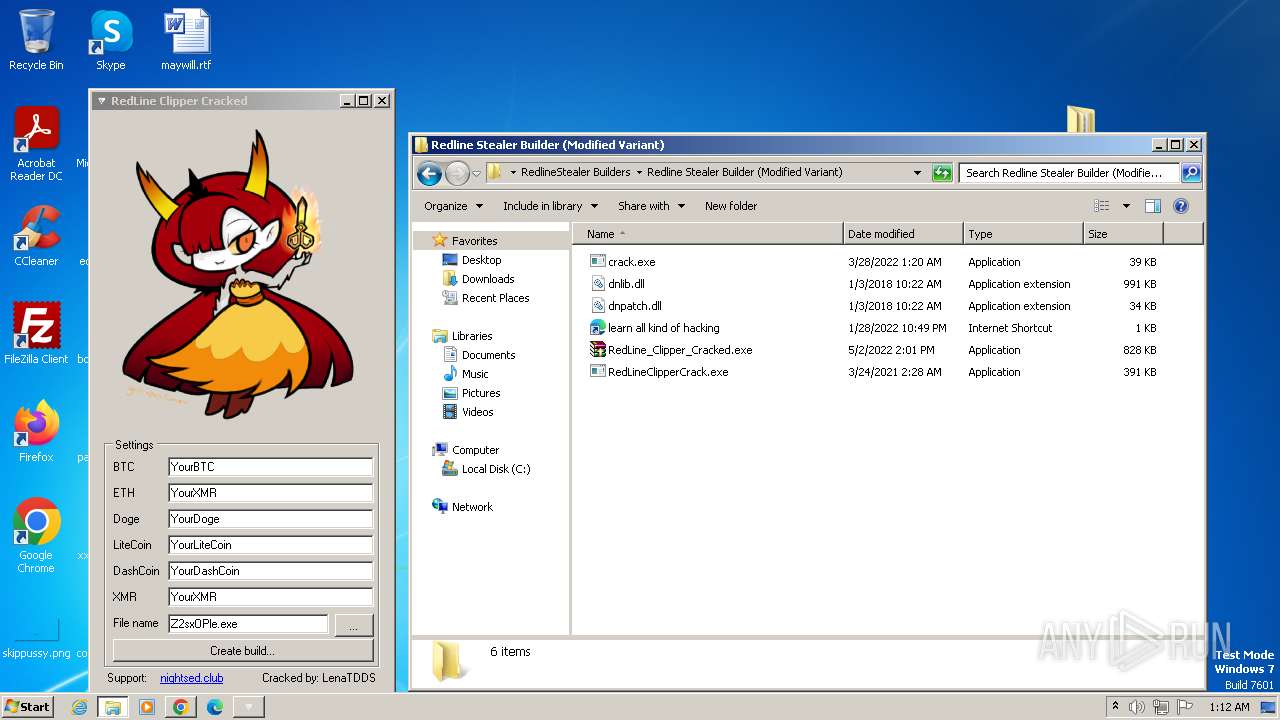
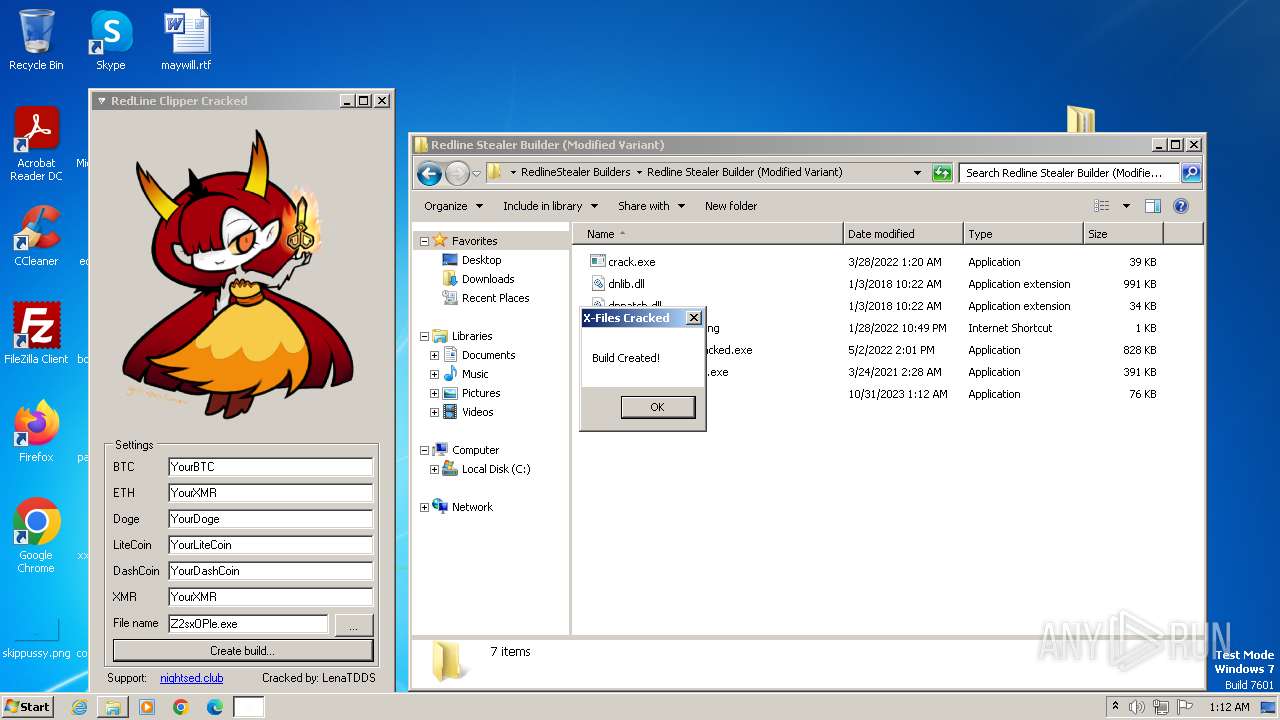
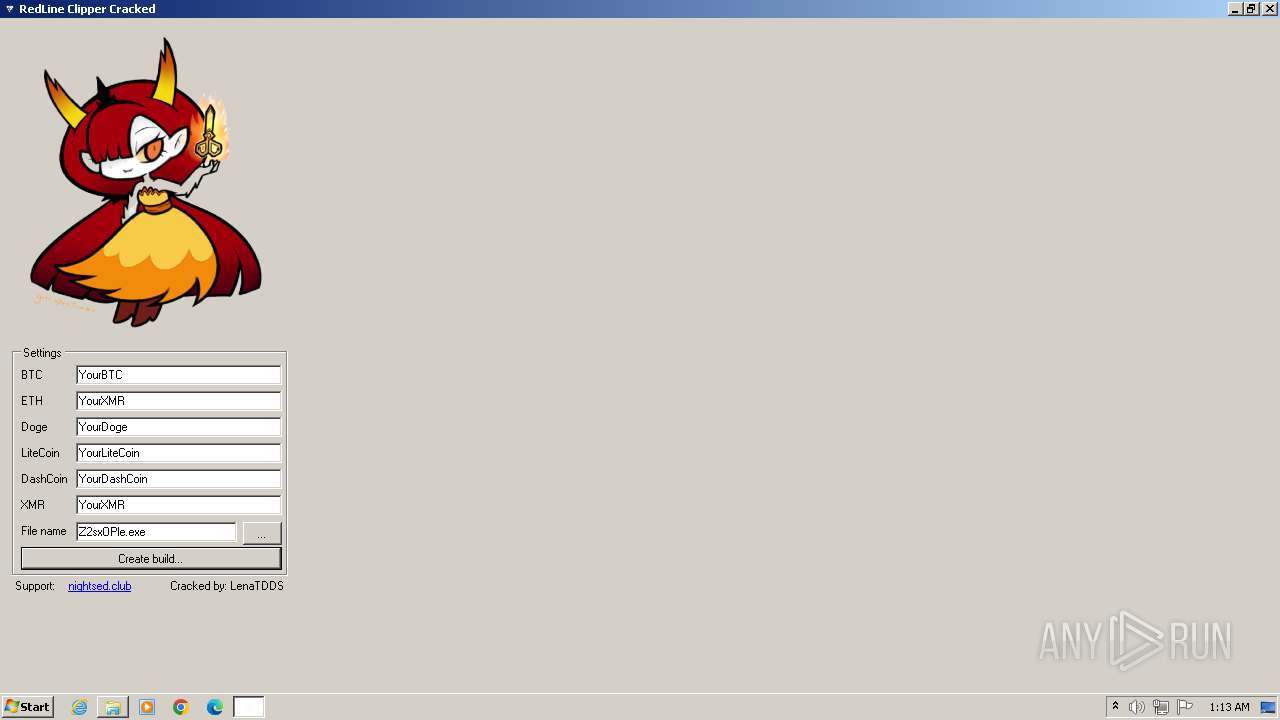
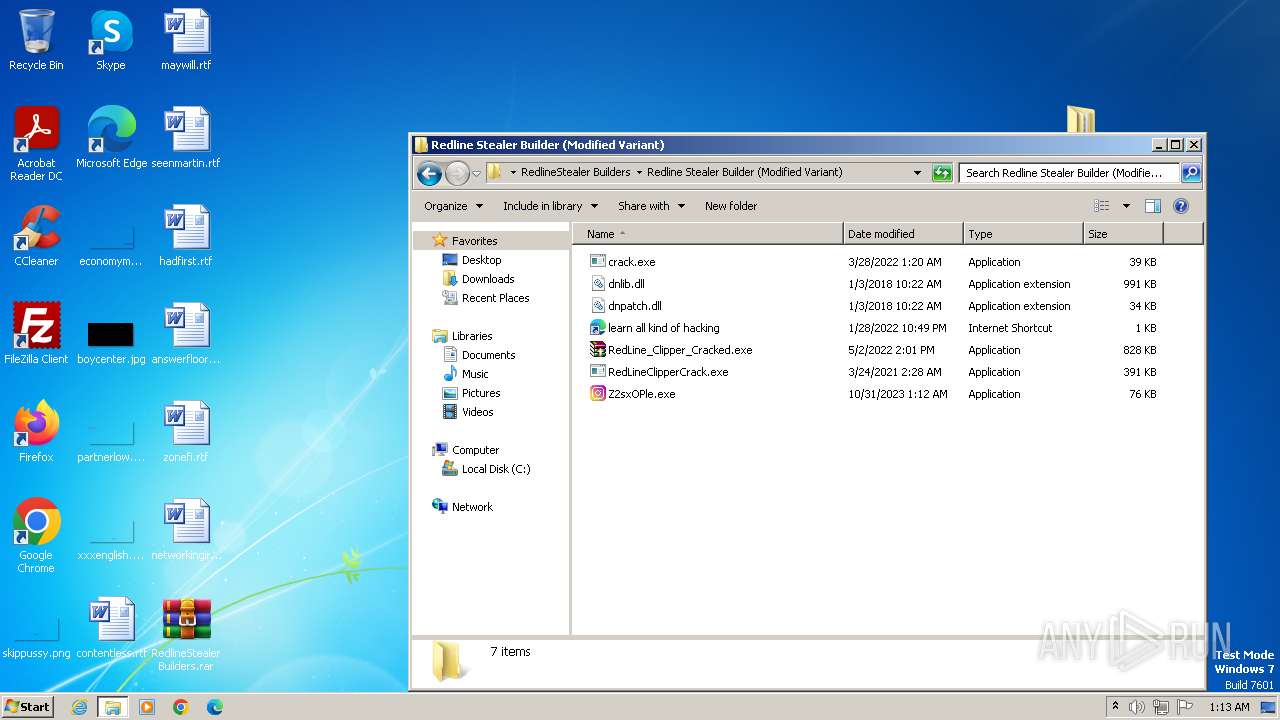
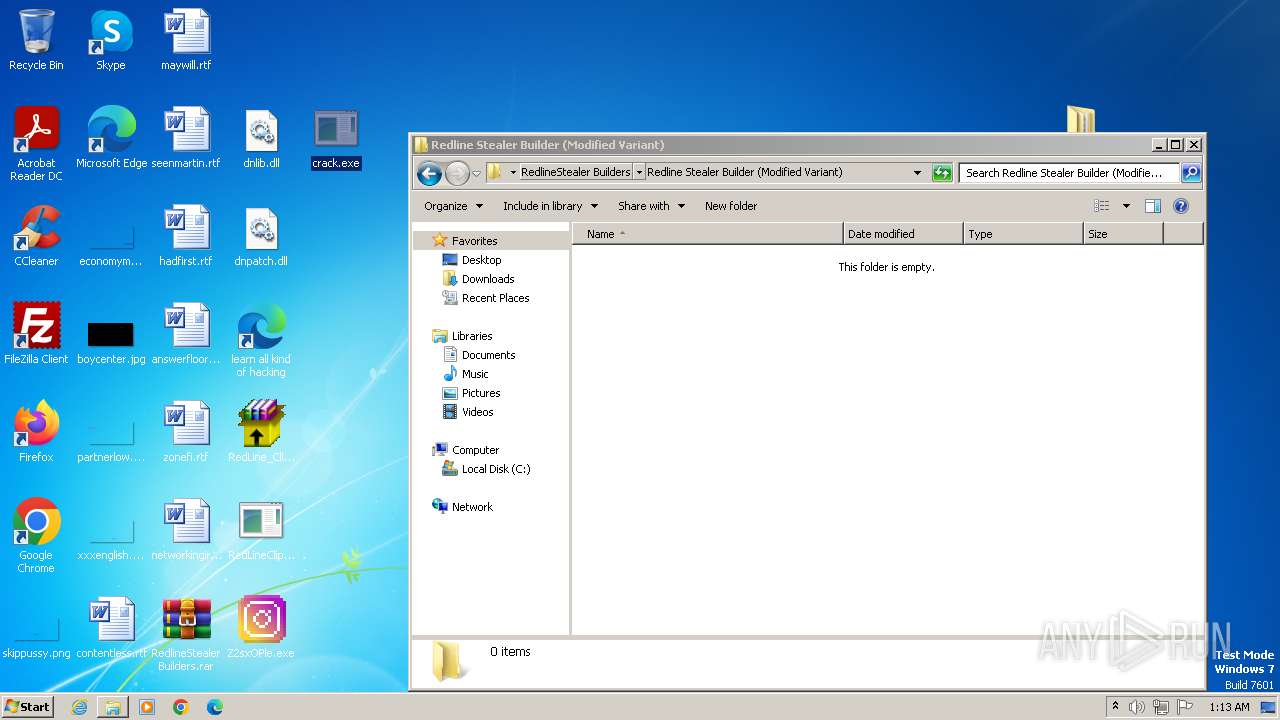
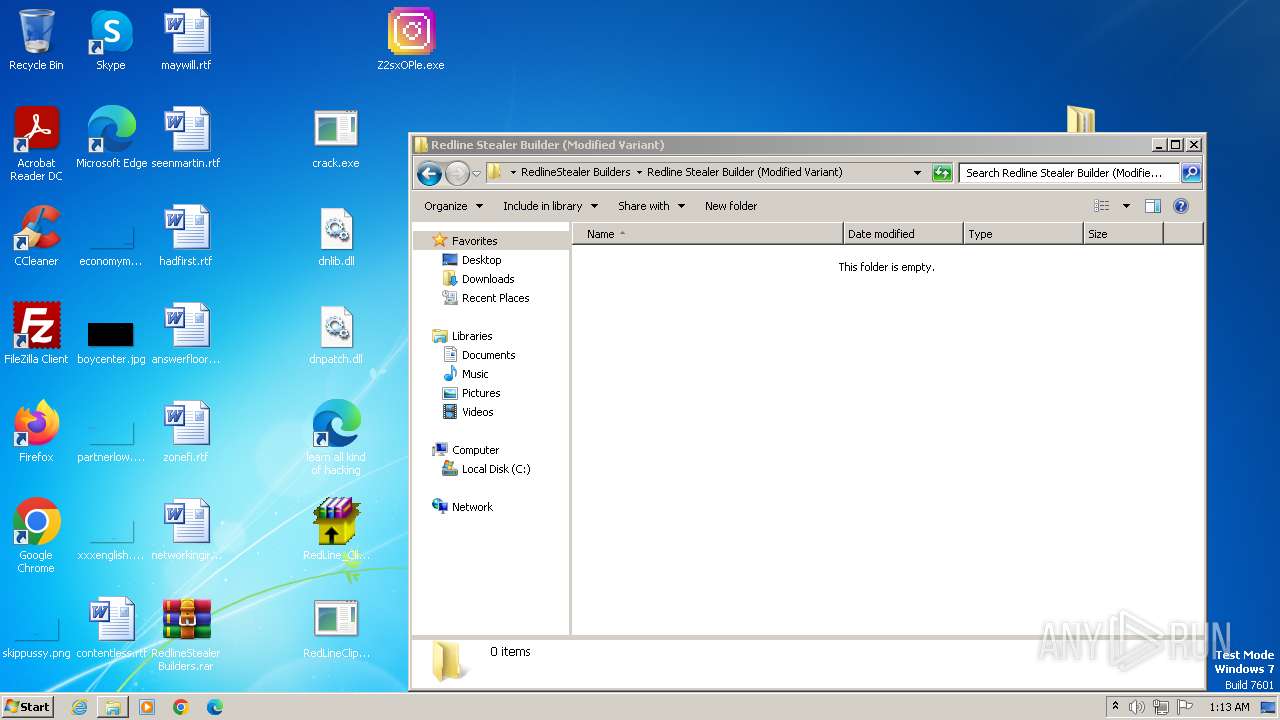
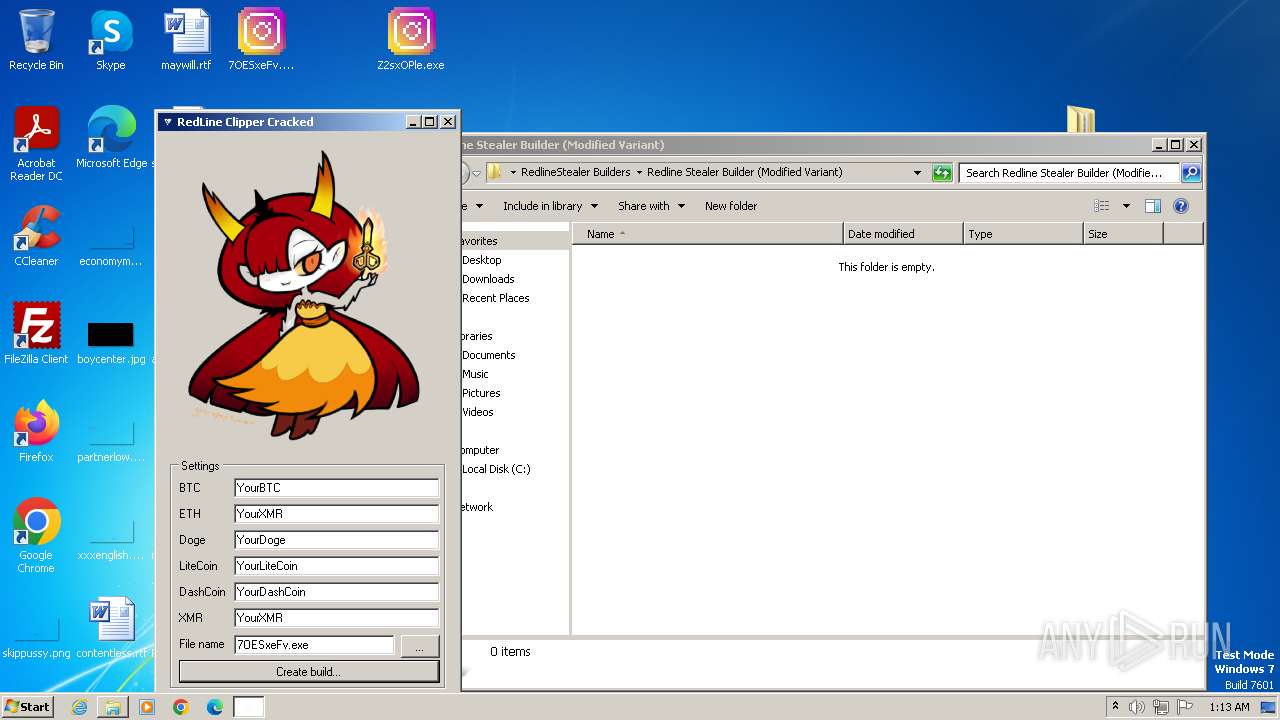
Application was dropped or rewritten from another process
- RedLine_Clipper_Cracked.exe (PID: 1956)
- crack.exe (PID: 3504)
- RedLineClipperCrack.exe (PID: 2520)
- crack.exe (PID: 2428)
Drops the executable file immediately after the start
- RedLine_Clipper_Cracked.exe (PID: 1956)
- crack.exe (PID: 3504)
- RedLineClipperCrack.exe (PID: 2520)
- builder.exe (PID: 1304)
- RedLineClipperCrack.exe (PID: 3896)
Create files in the Startup directory
- crack.exe (PID: 3504)
Loads dropped or rewritten executable
- RedLineClipperCrack.exe (PID: 2520)
Changes the autorun value in the registry
- crack.exe (PID: 2428)
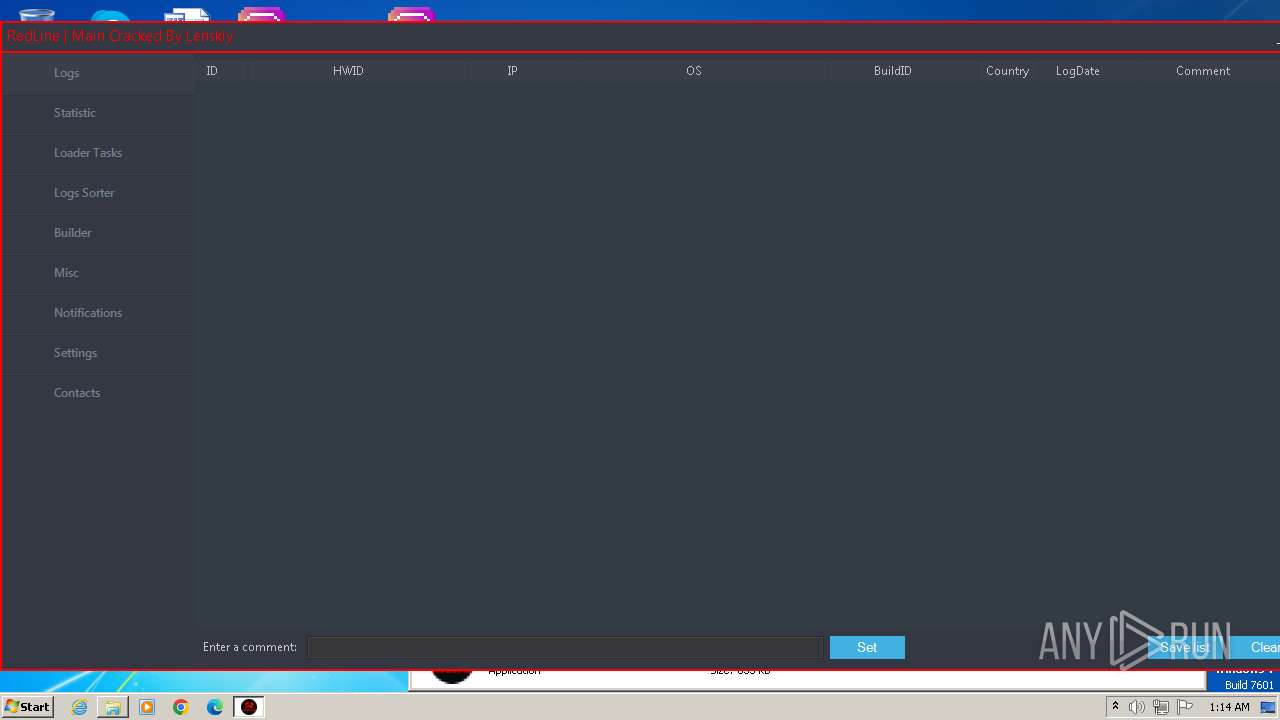
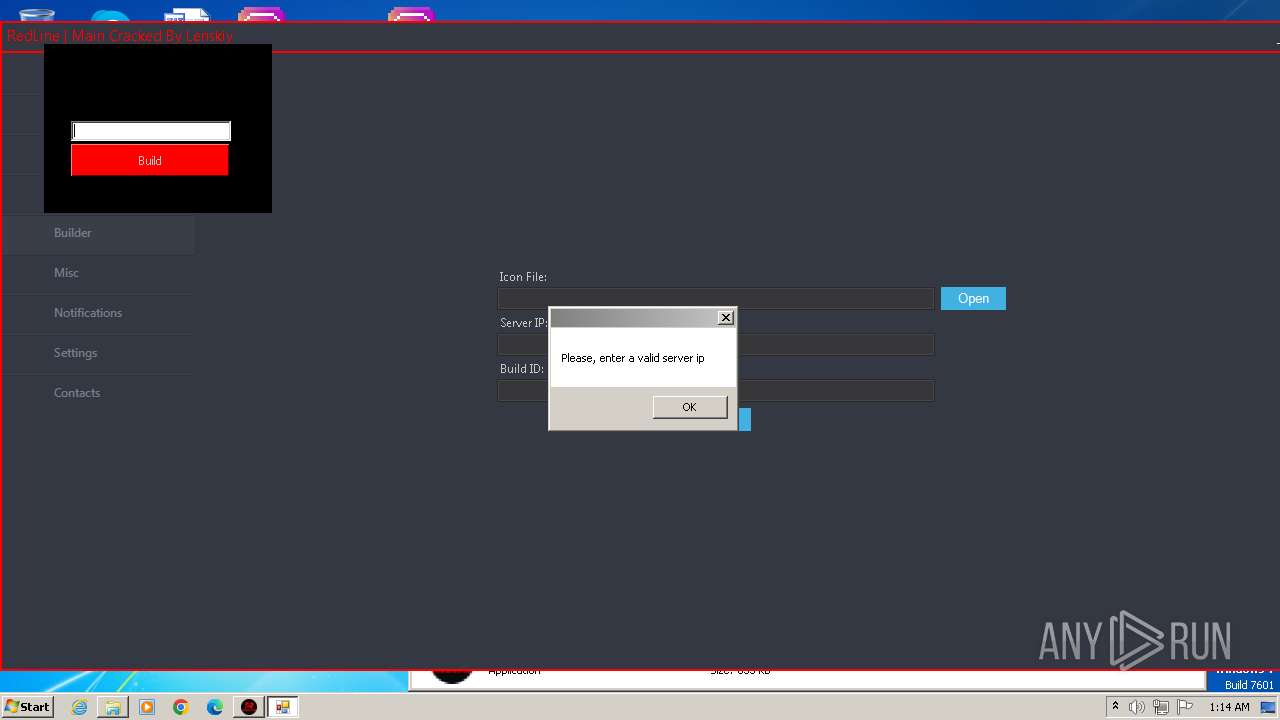
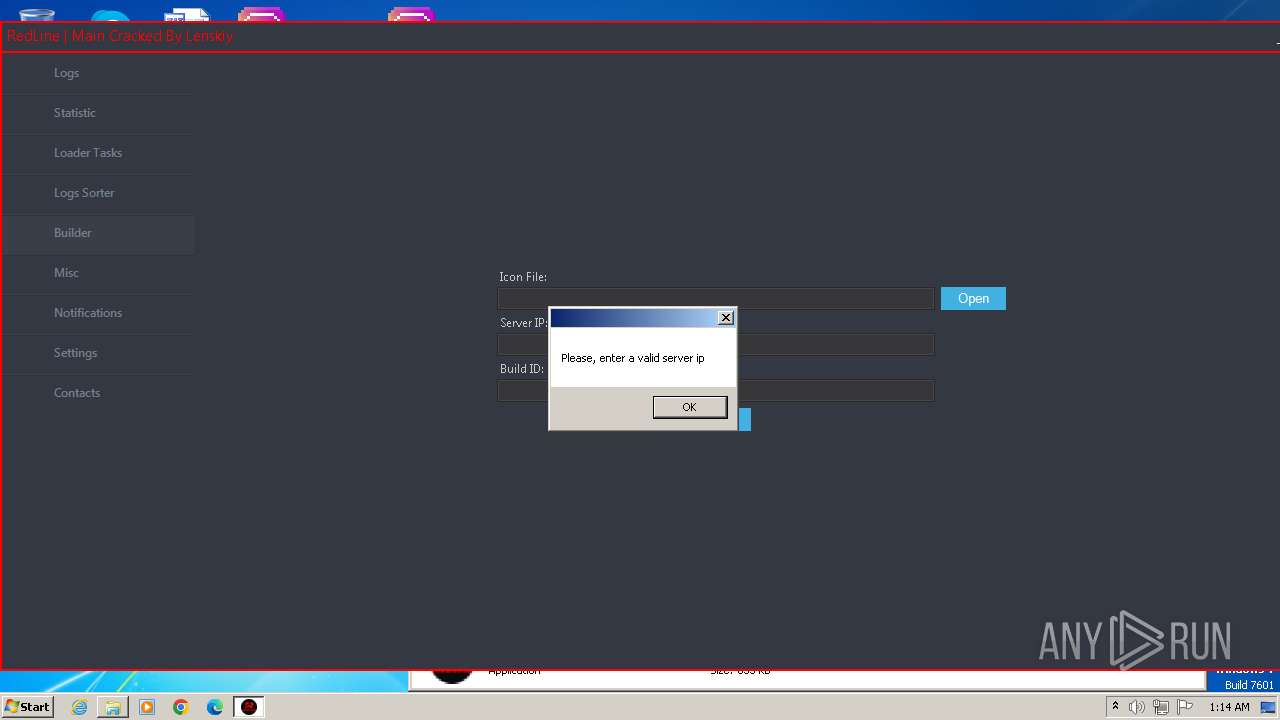
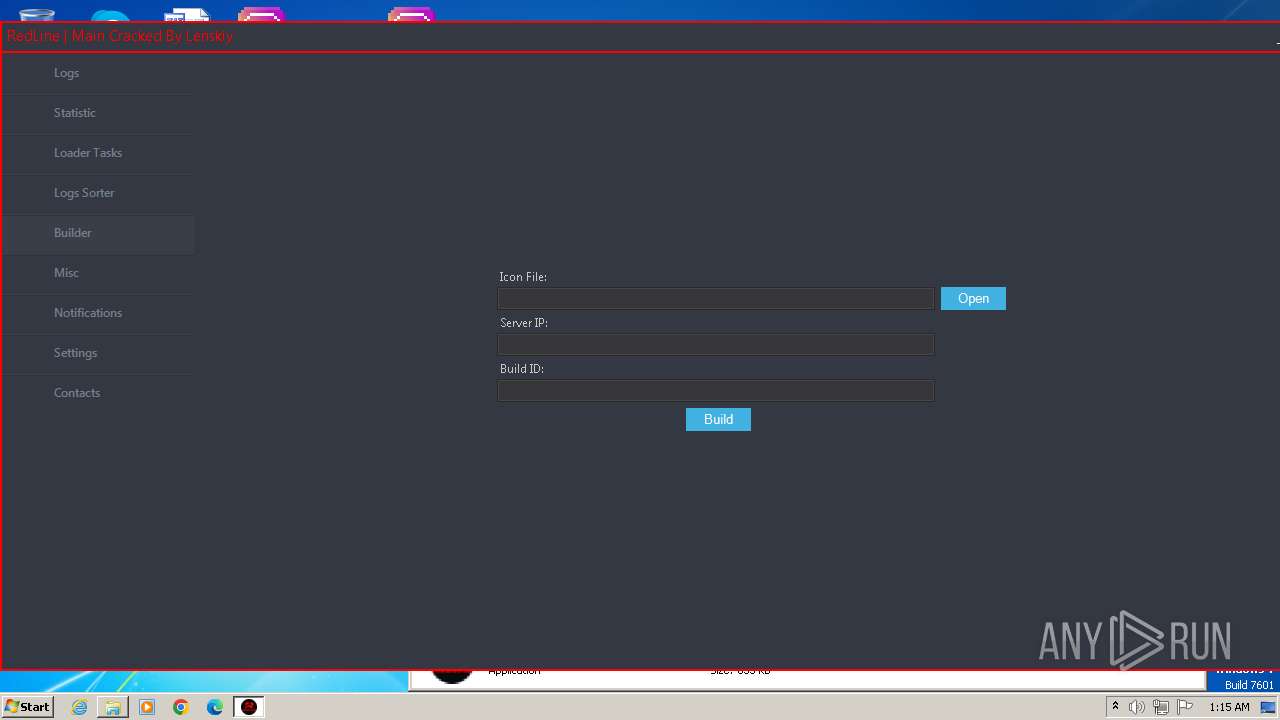
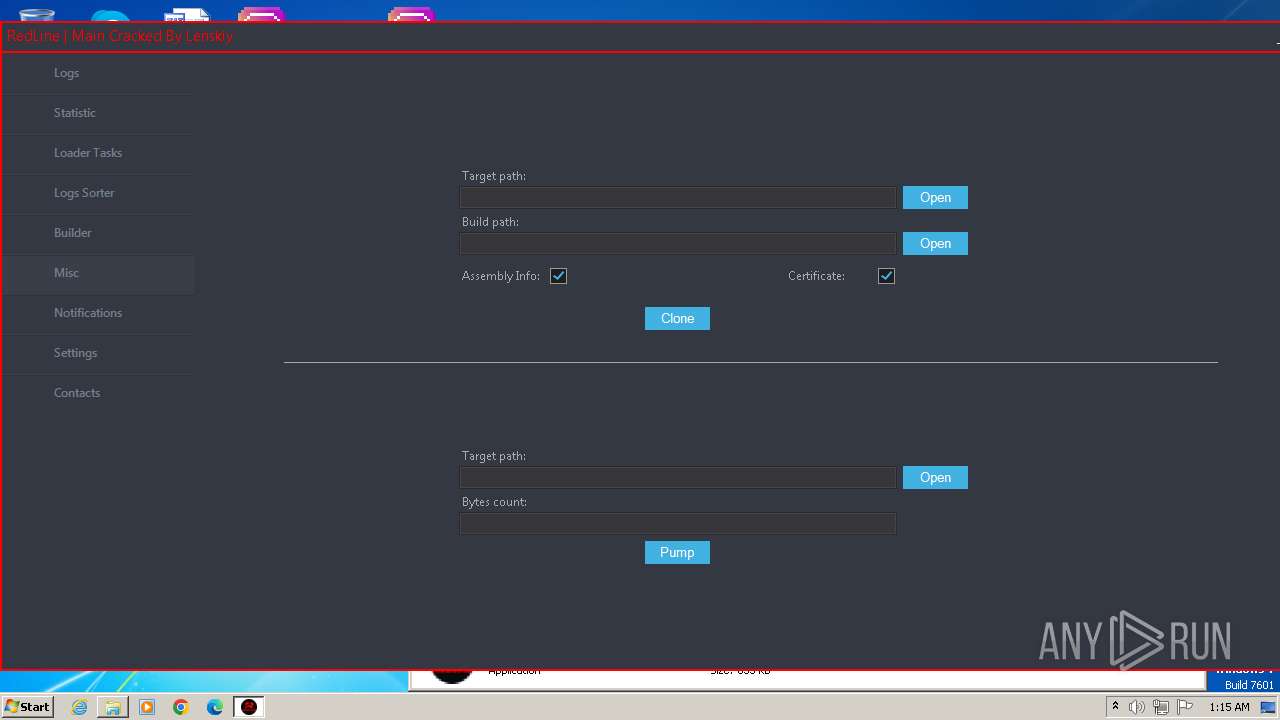
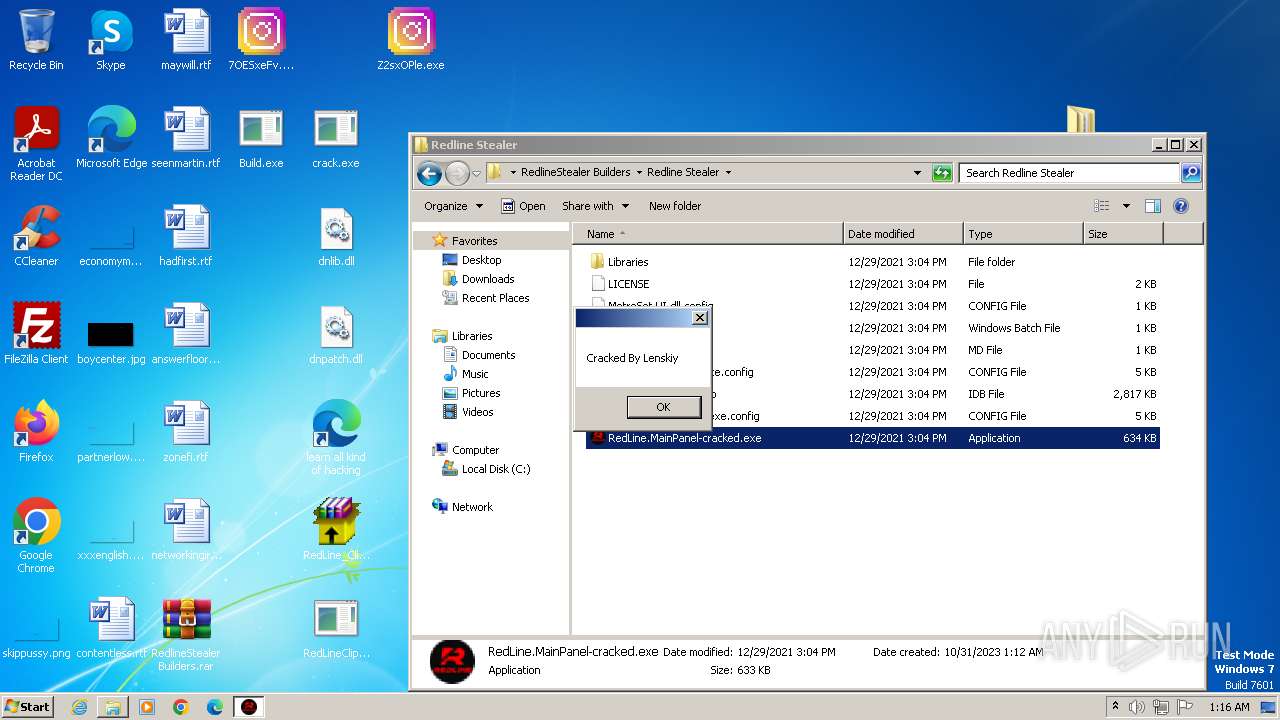
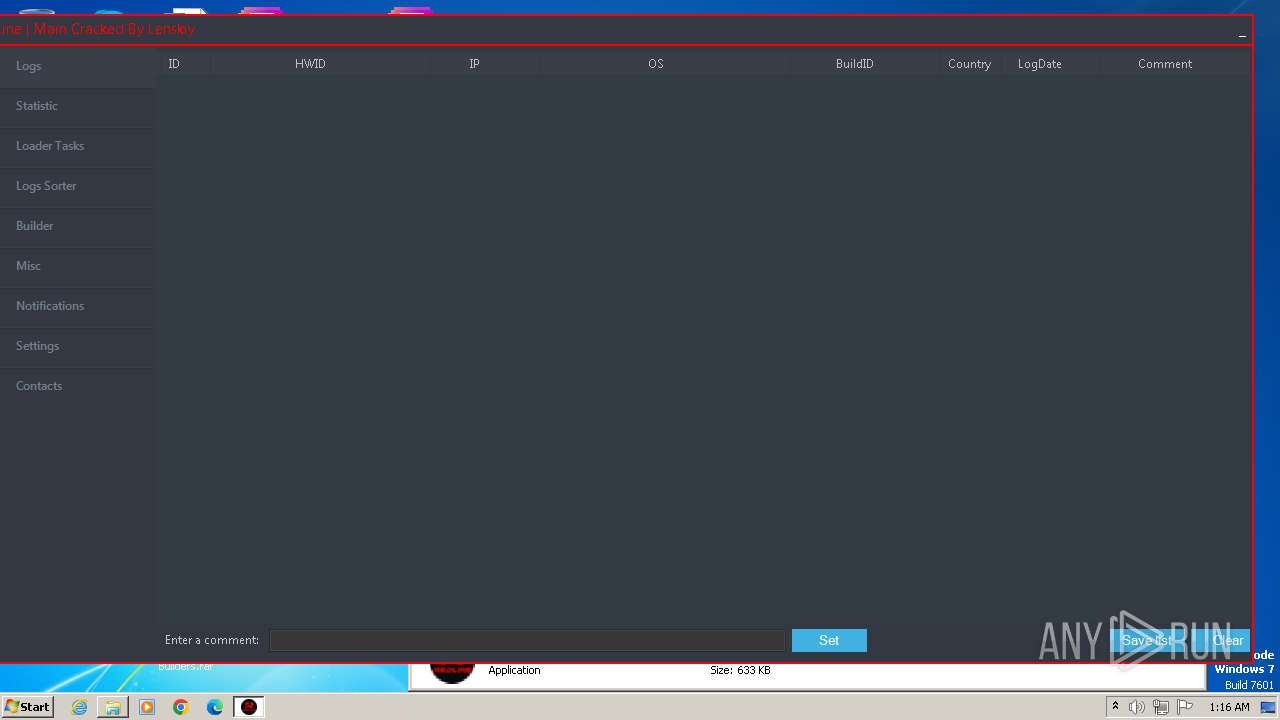
REDLINE has been detected (YARA)
- builder.exe (PID: 1304)
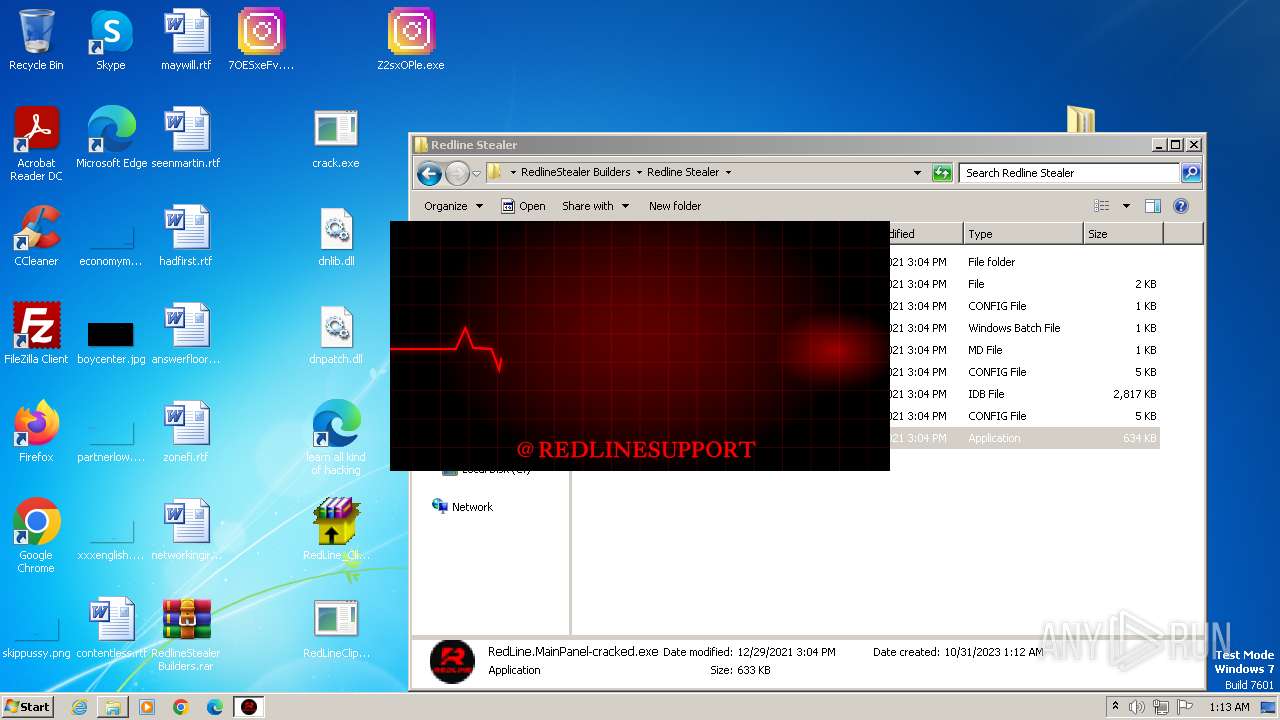
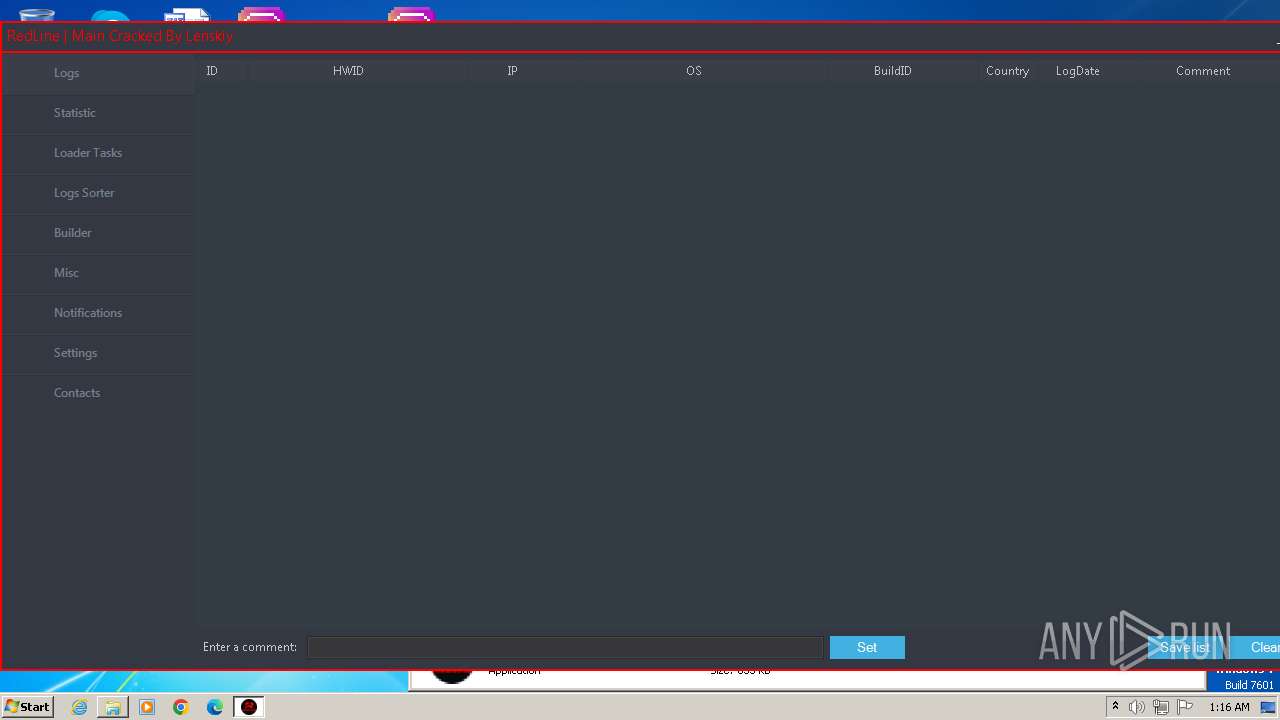
- RedLine.MainPanel-cracked.exe (PID: 3808)
- RedLine.MainPanel-cracked.exe (PID: 2808)
- RedLine.MainPanel-cracked.exe (PID: 1688)
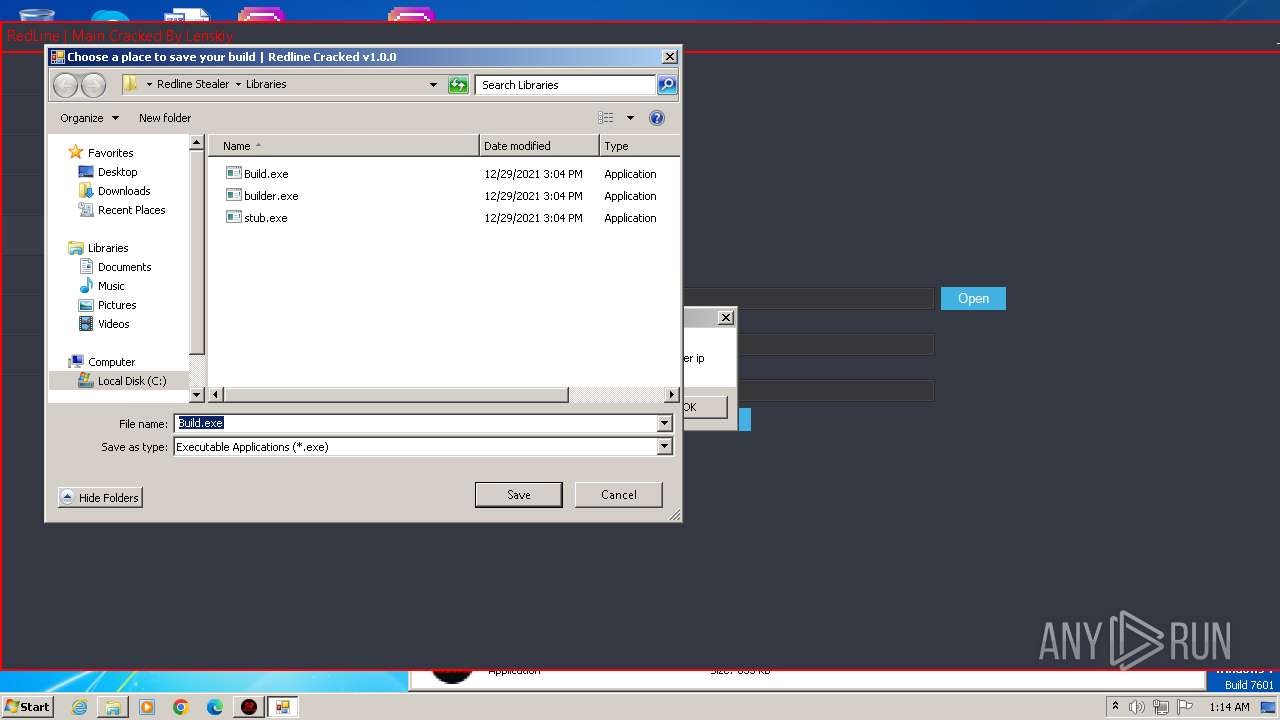
Starts CMD.EXE for self-deleting
- Build.exe (PID: 3064)
SUSPICIOUS
Reads the Internet Settings
- RedLine_Clipper_Cracked.exe (PID: 1956)
- crack.exe (PID: 3504)
- crack.exe (PID: 2428)
Reads Microsoft Outlook installation path
- RedLine_Clipper_Cracked.exe (PID: 1956)
Reads Internet Explorer settings
- RedLine_Clipper_Cracked.exe (PID: 1956)
- RedLineClipperCrack.exe (PID: 2520)
Starts CMD.EXE for commands execution
- Build.exe (PID: 3064)
- explorer.exe (PID: 1400)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1592)
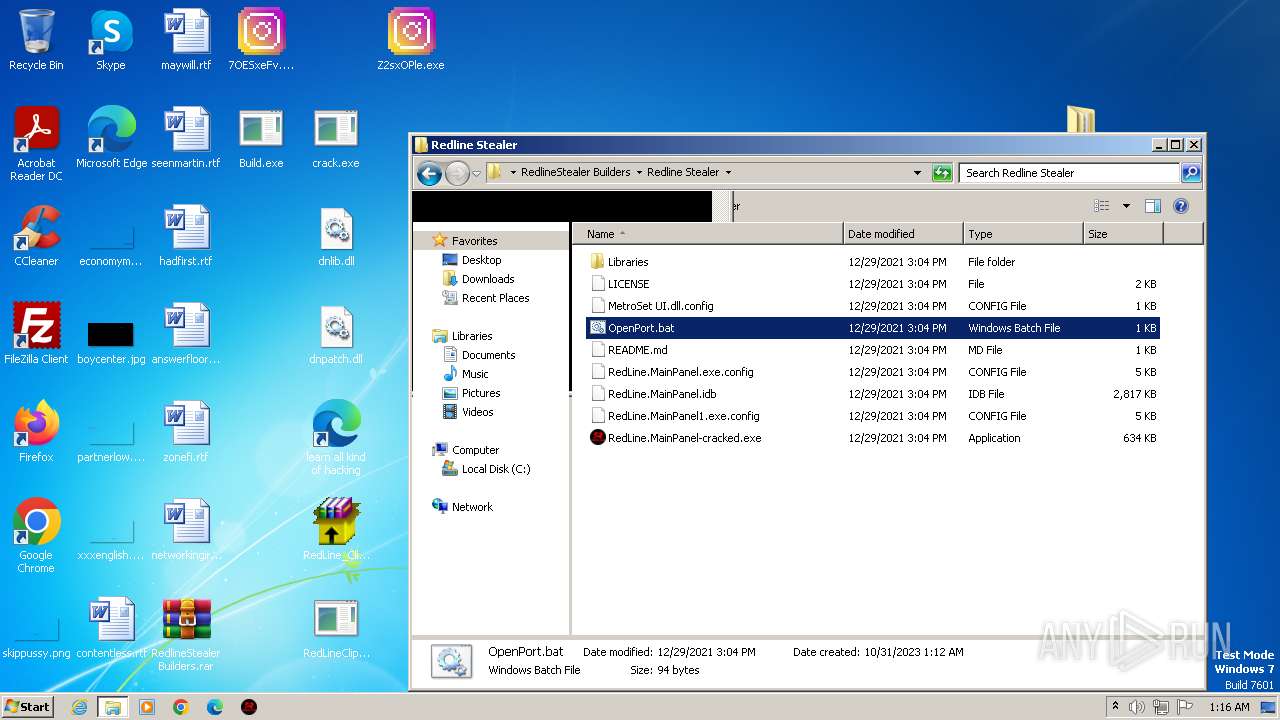
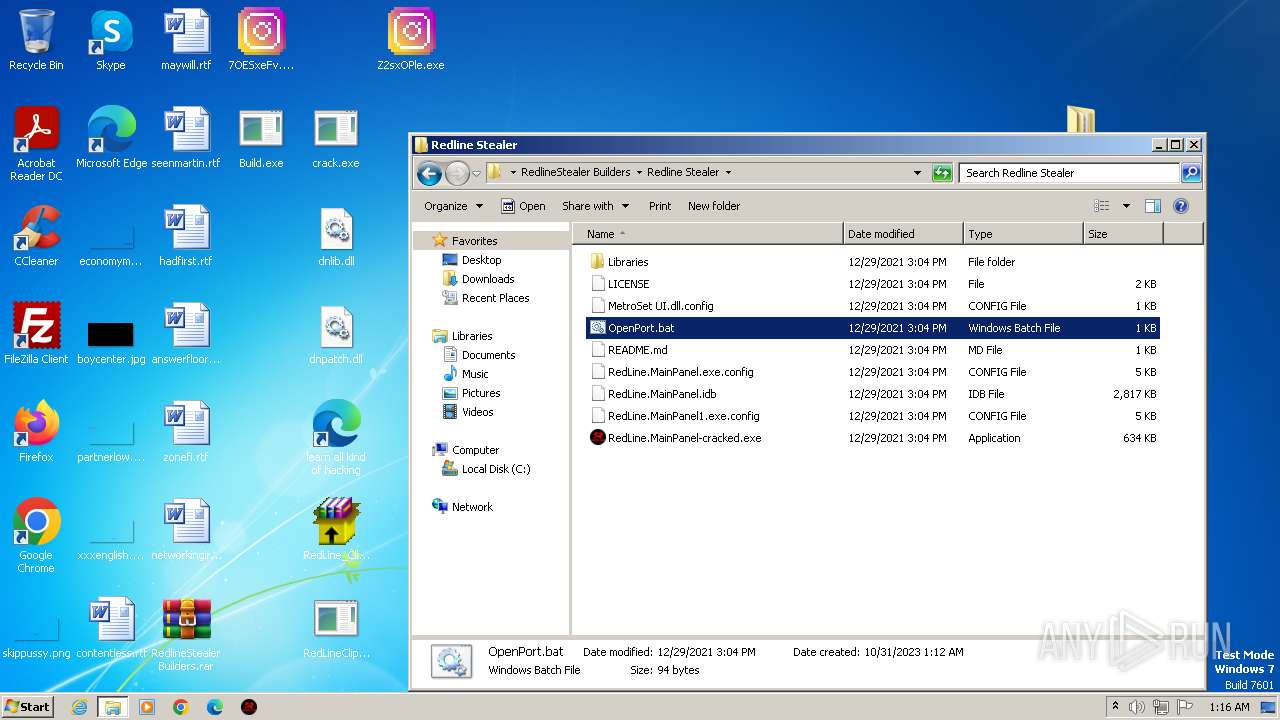
Executing commands from a ".bat" file
- explorer.exe (PID: 1400)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2372)
INFO
Reads the computer name
- RedLine_Clipper_Cracked.exe (PID: 1956)
- crack.exe (PID: 3504)
- RedLineClipperCrack.exe (PID: 2520)
- crack.exe (PID: 2428)
Reads the Internet Settings
- explorer.exe (PID: 1400)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1796)
- explorer.exe (PID: 1400)
Checks supported languages
- RedLine_Clipper_Cracked.exe (PID: 1956)
- crack.exe (PID: 3504)
- crack.exe (PID: 2428)
- RedLineClipperCrack.exe (PID: 2520)
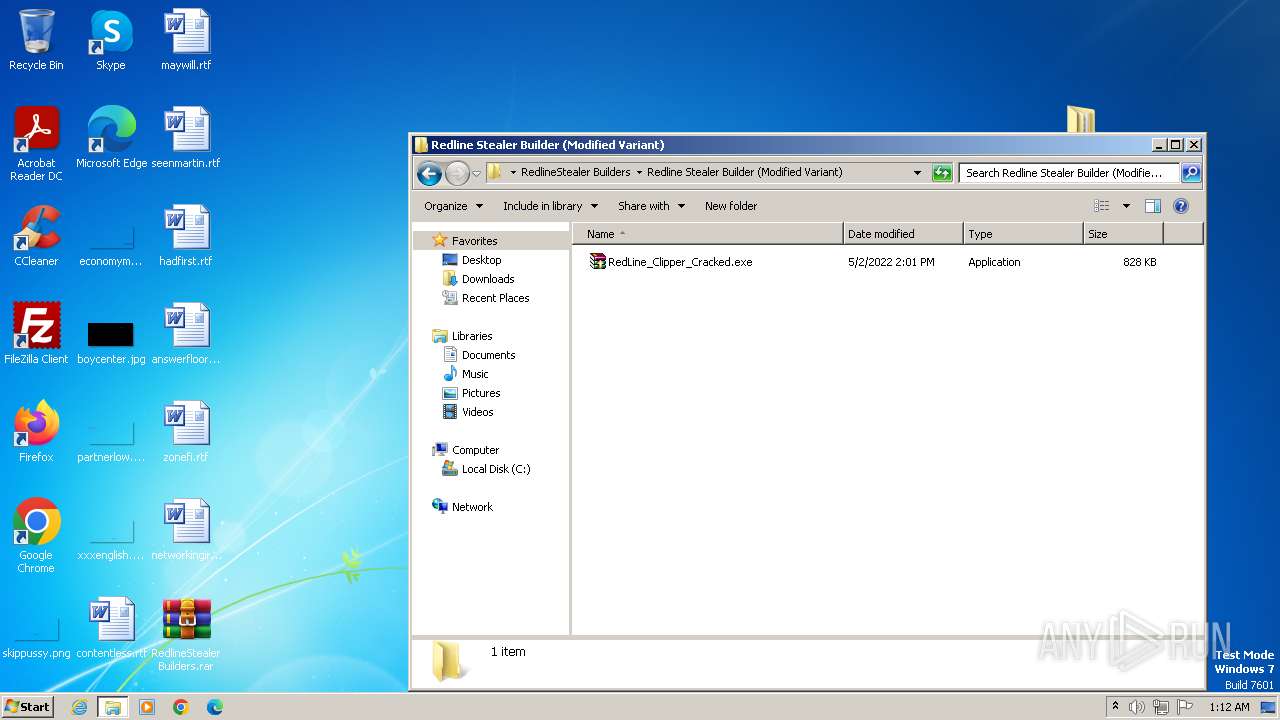
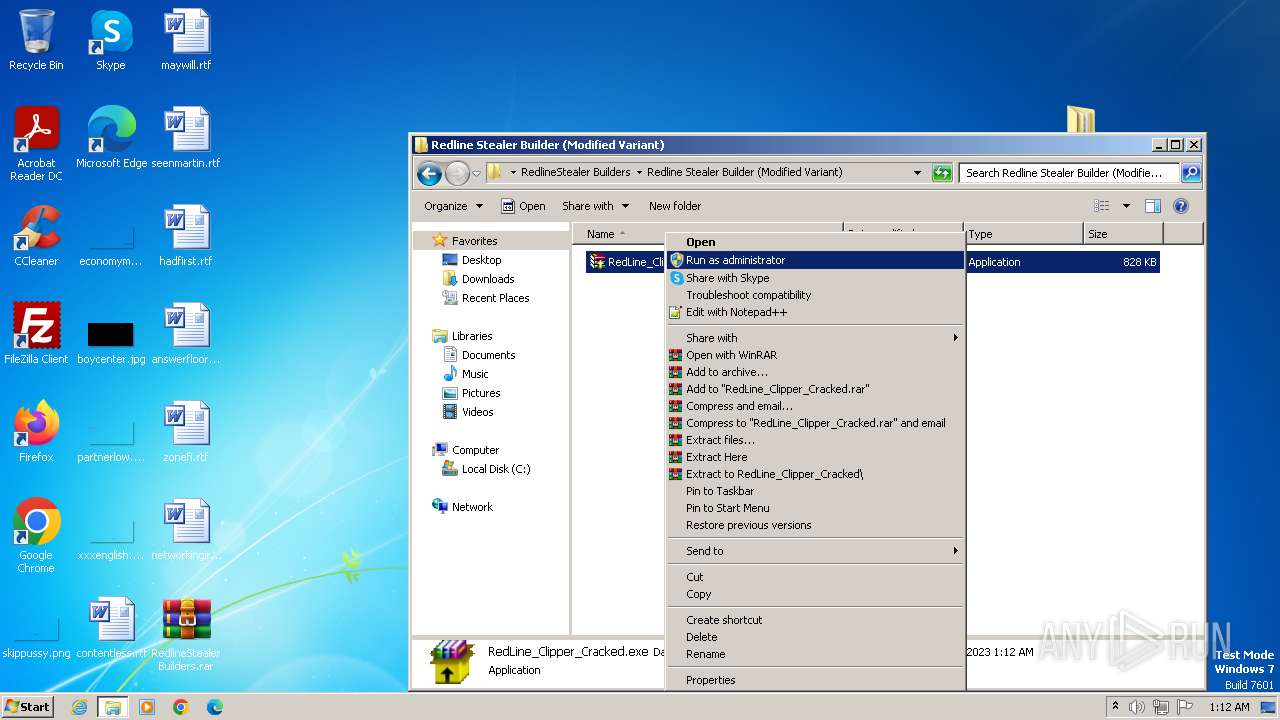
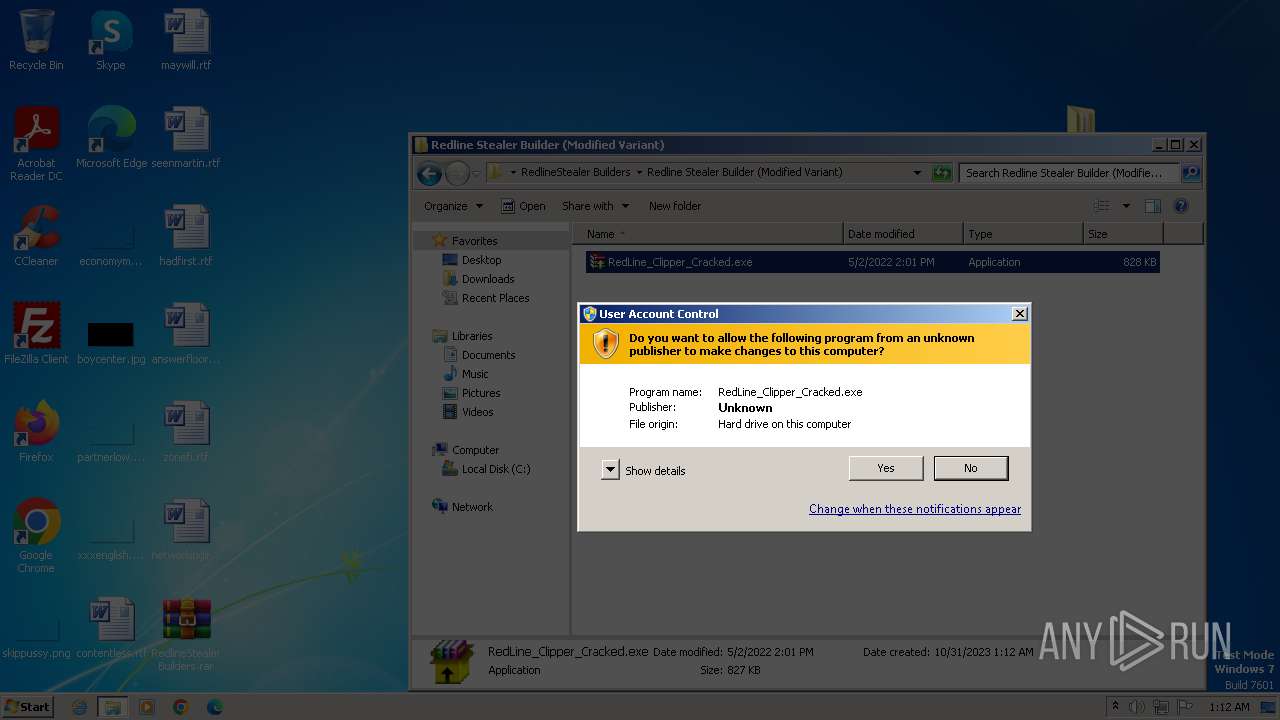
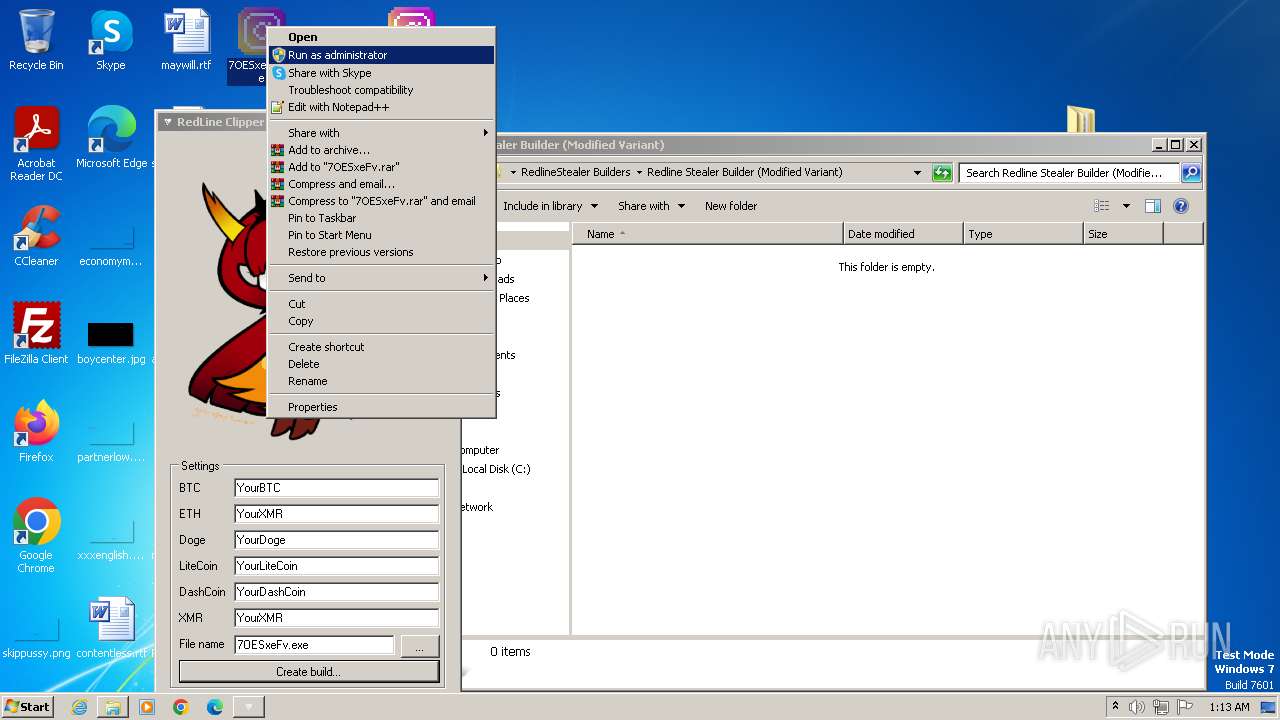
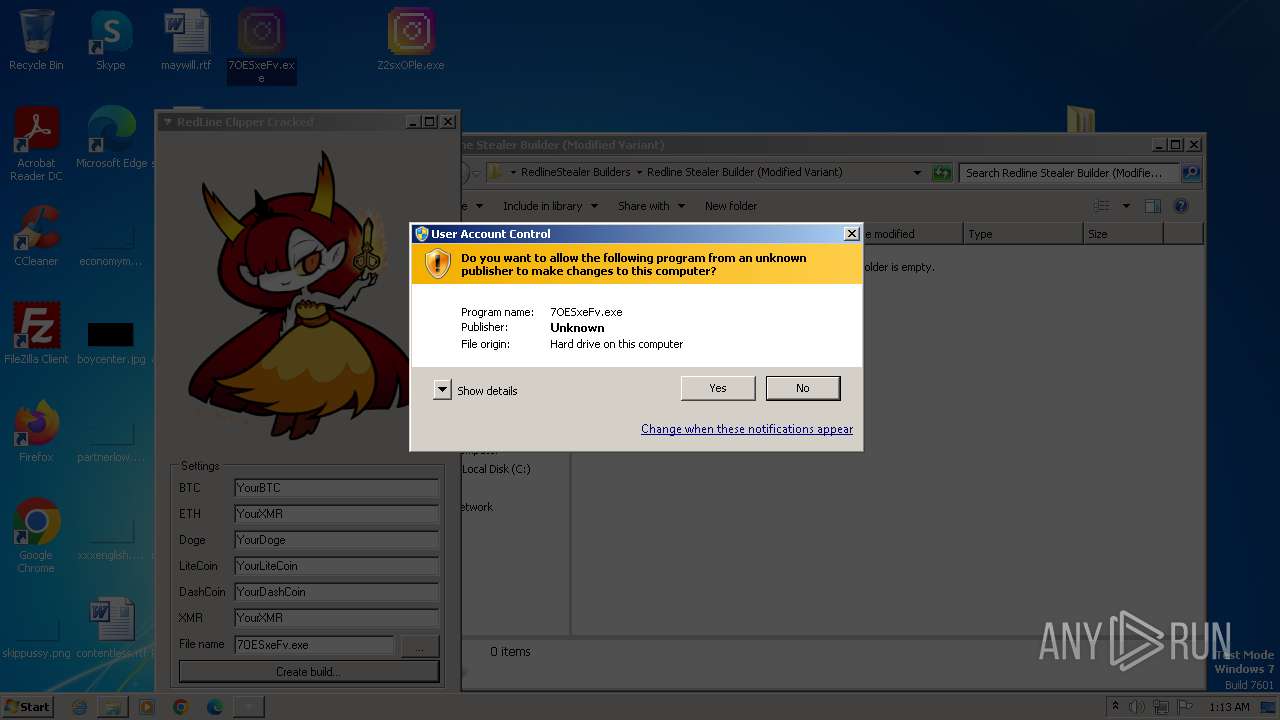
Manual execution by a user
- RedLine_Clipper_Cracked.exe (PID: 1956)
- RedLineClipperCrack.exe (PID: 2520)
- crack.exe (PID: 2428)
Checks proxy server information
- RedLine_Clipper_Cracked.exe (PID: 1956)
Reads the machine GUID from the registry
- RedLine_Clipper_Cracked.exe (PID: 1956)
- crack.exe (PID: 3504)
- RedLineClipperCrack.exe (PID: 2520)
- crack.exe (PID: 2428)
Create files in a temporary directory
- crack.exe (PID: 3504)
Creates files or folders in the user directory
- crack.exe (PID: 3504)
- crack.exe (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
77
Monitored processes
19
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
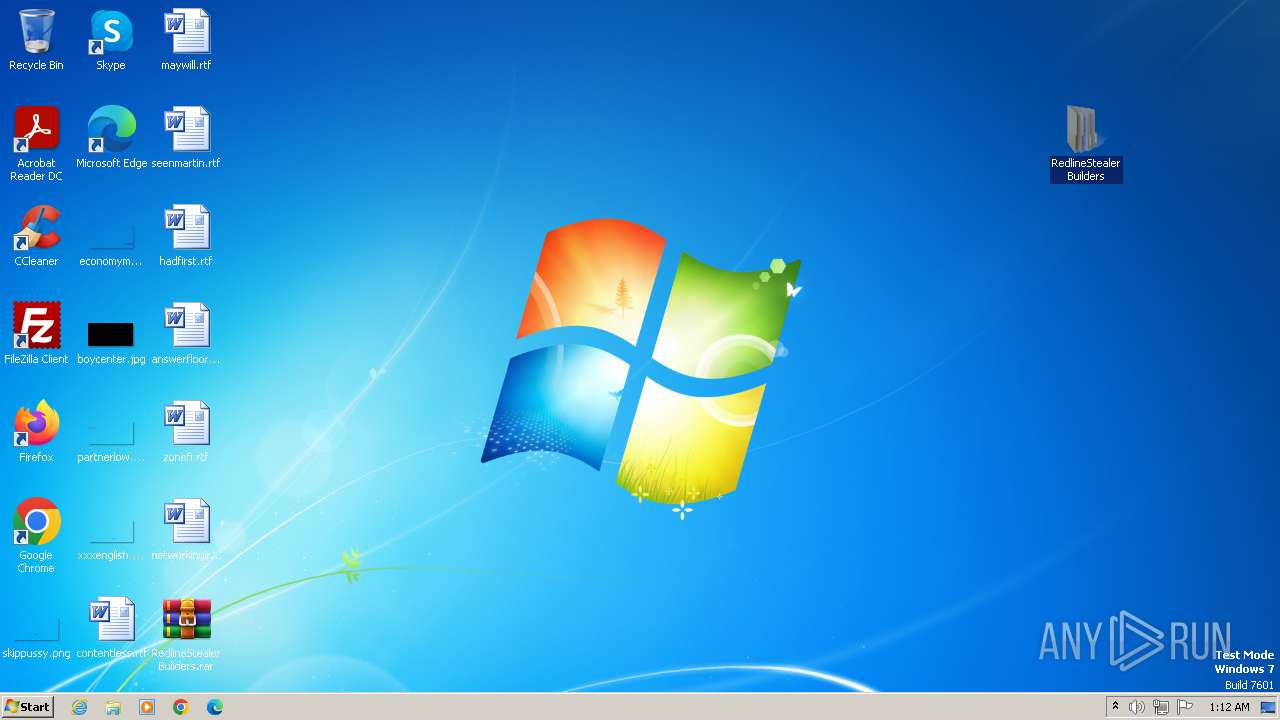
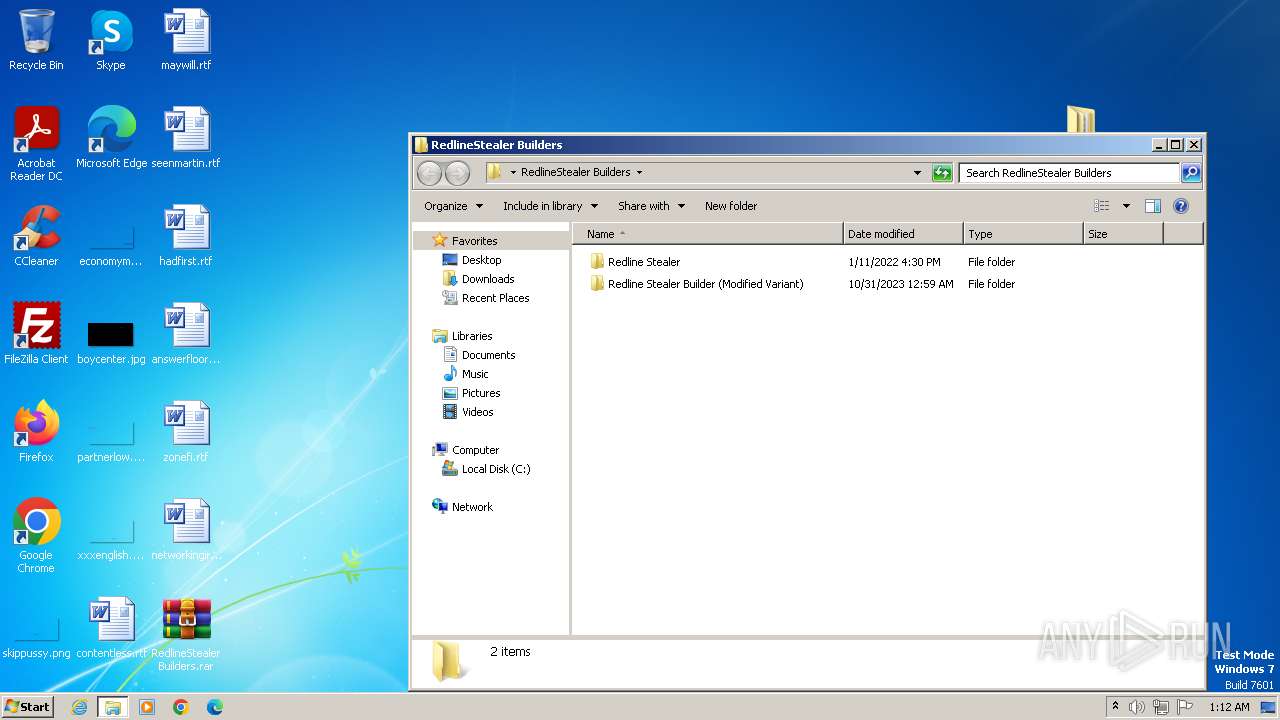
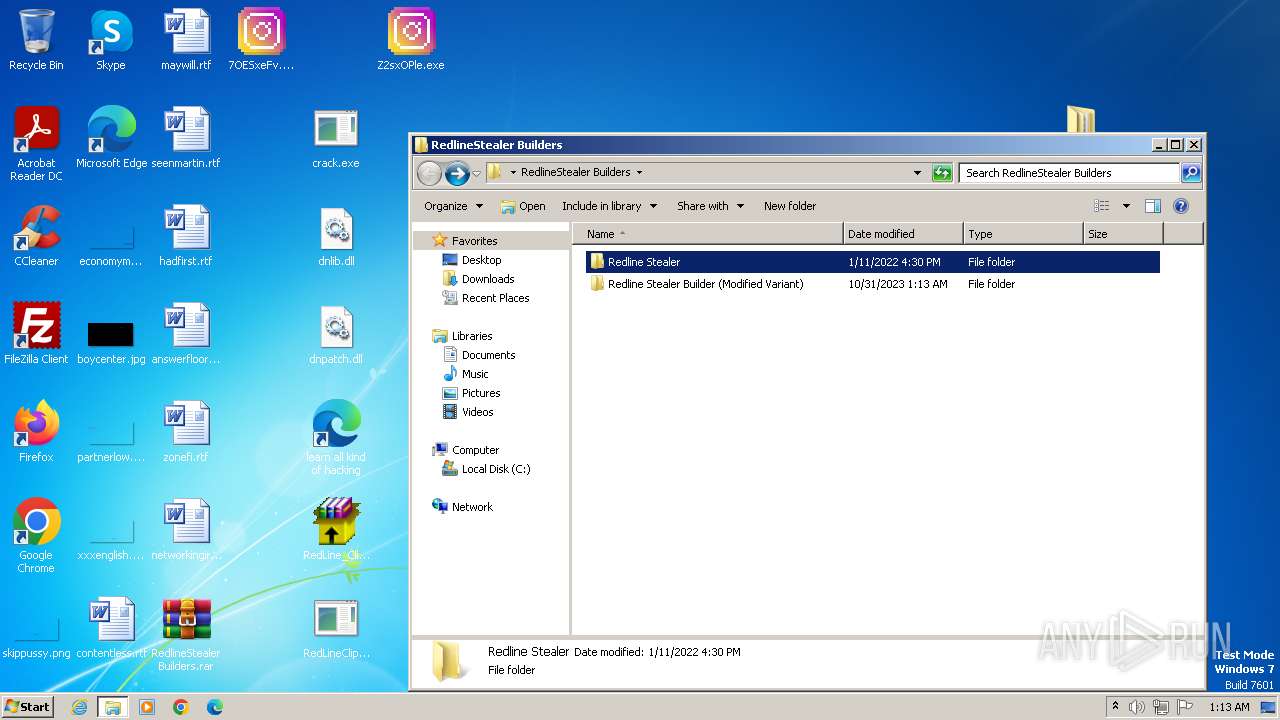
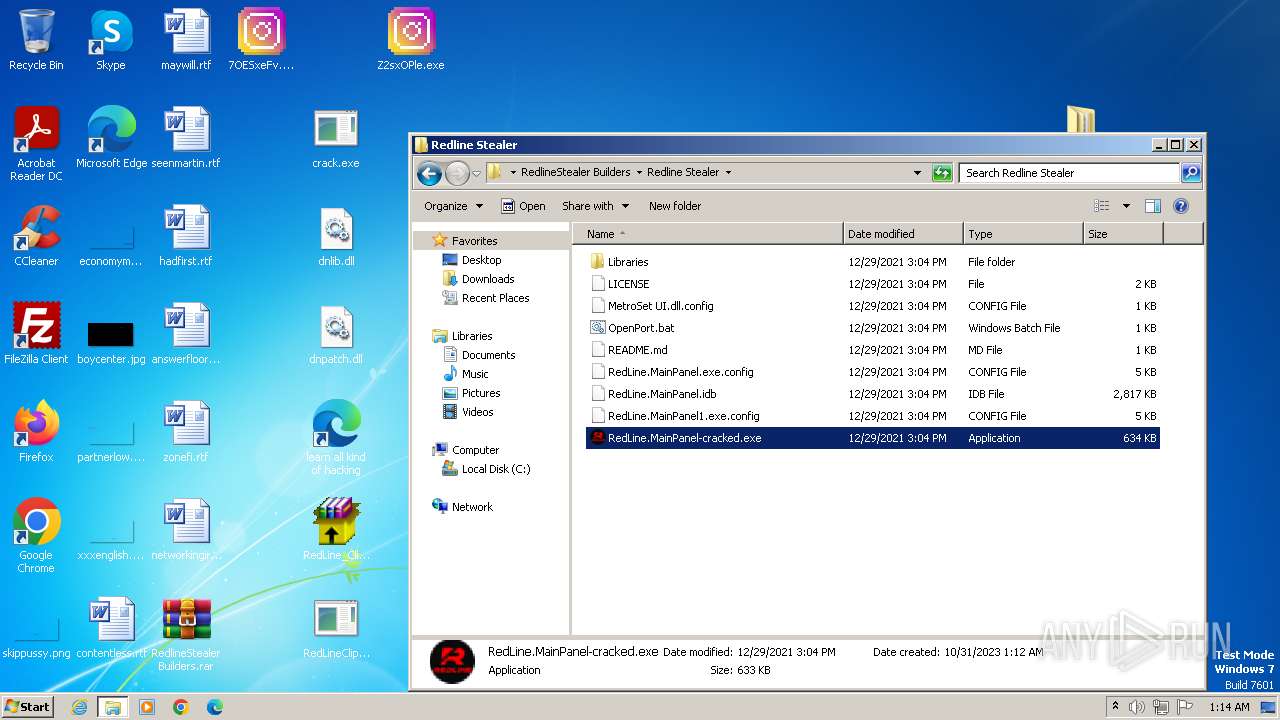
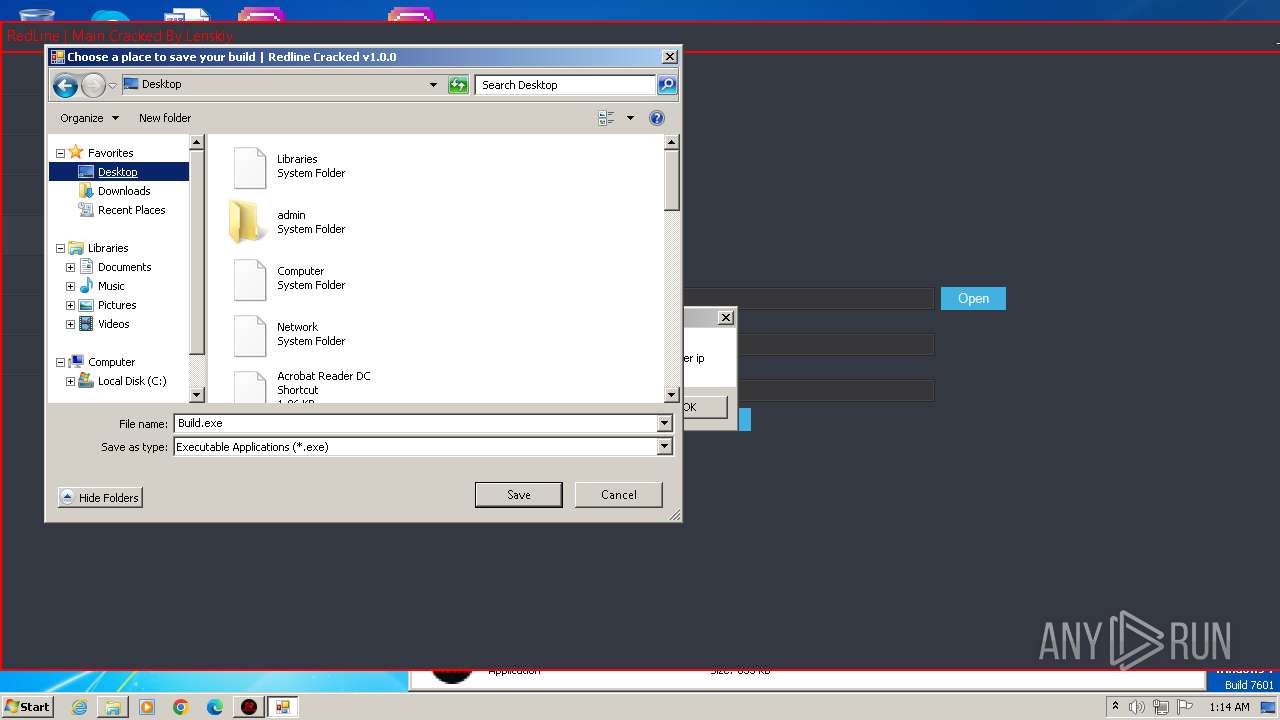
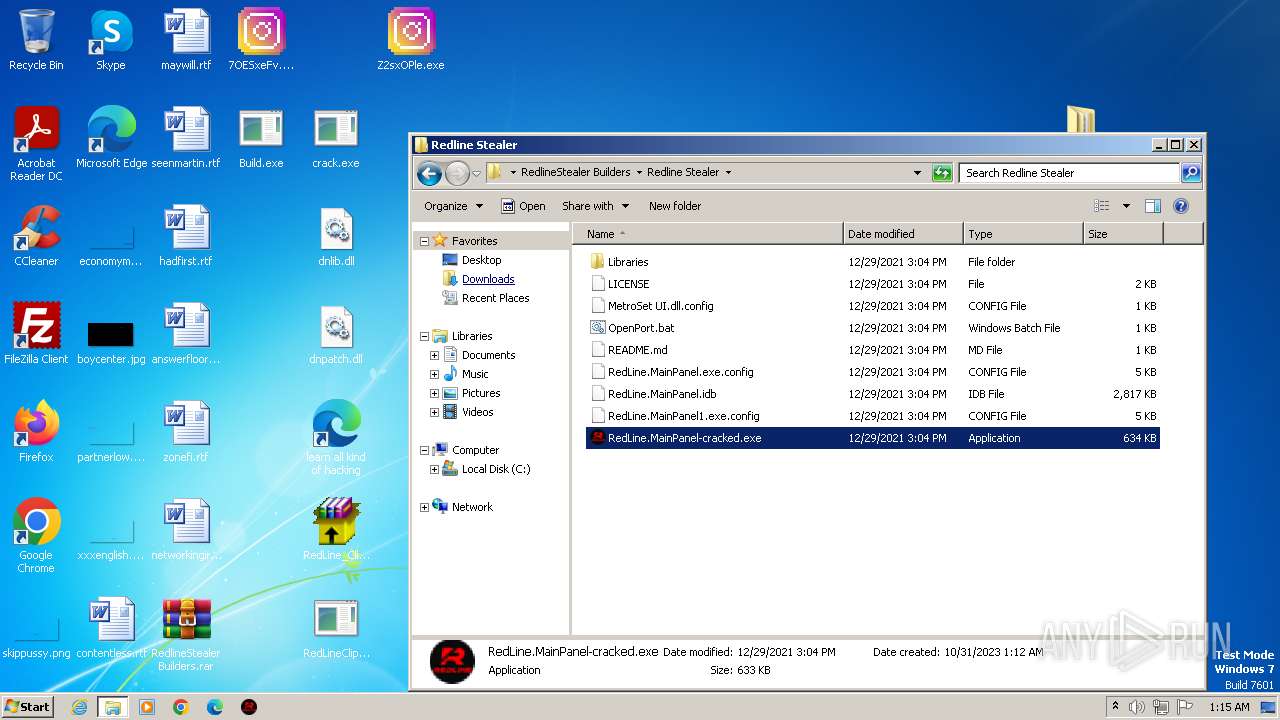
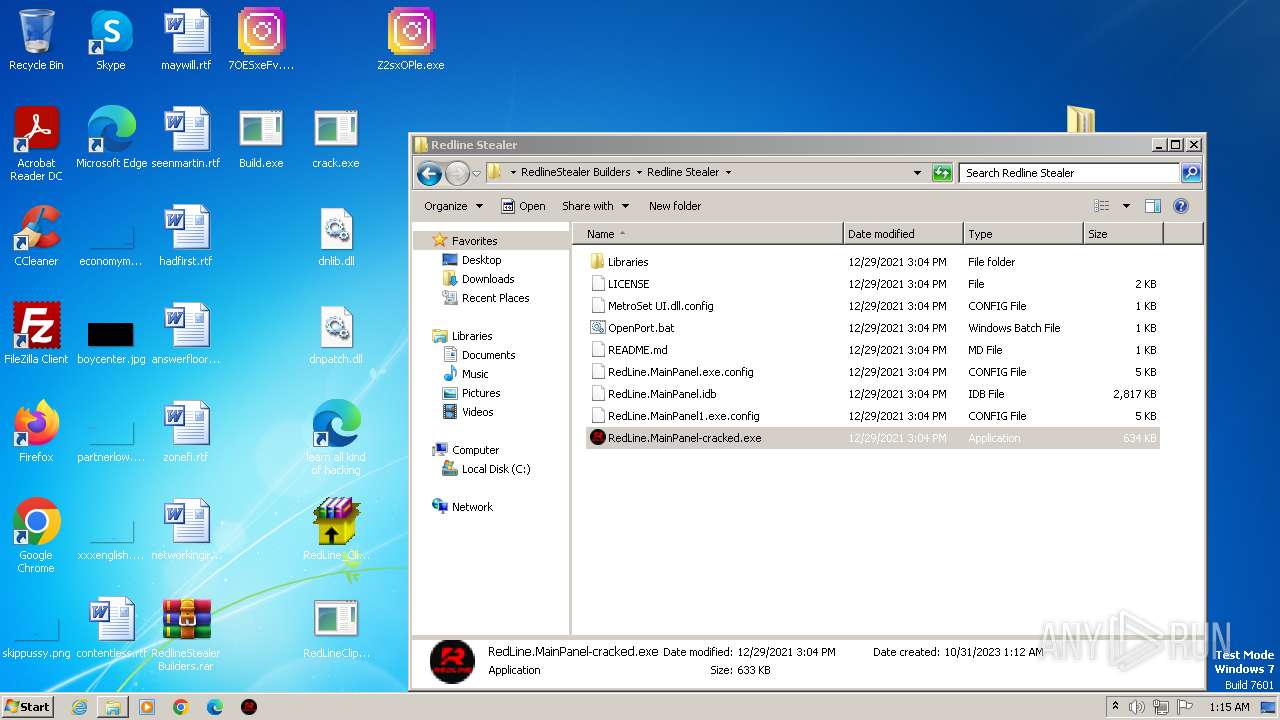
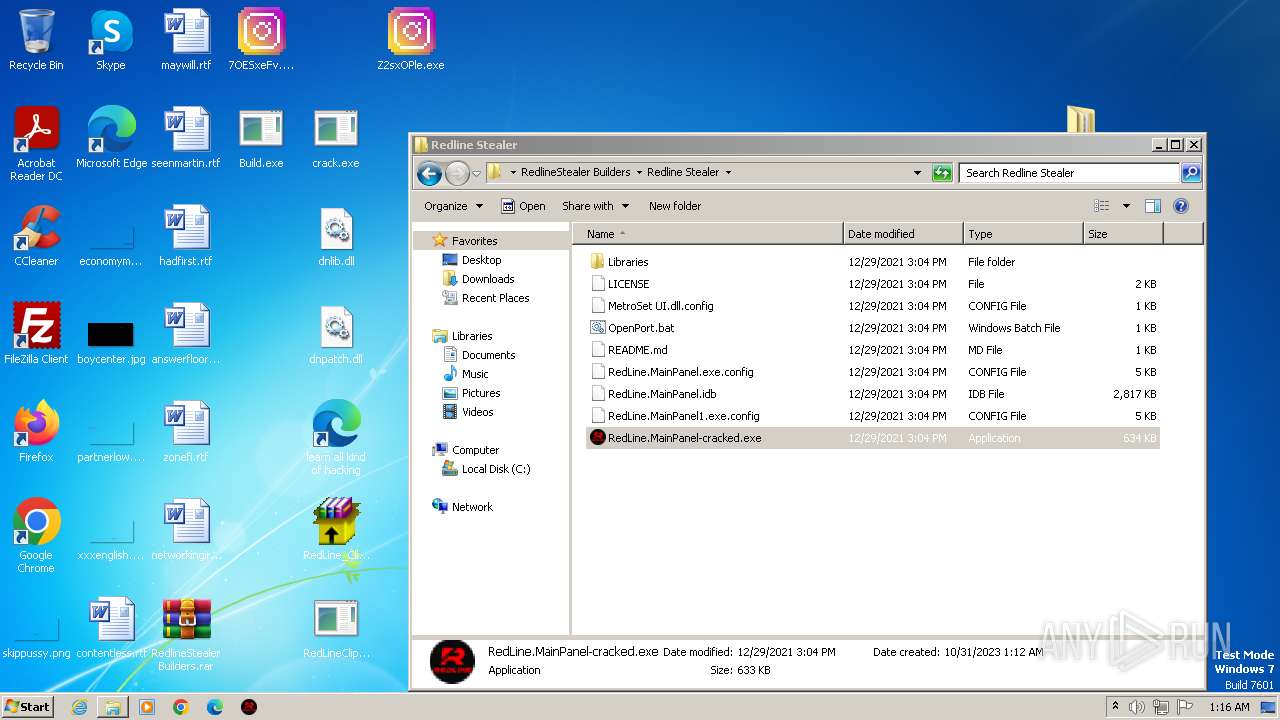
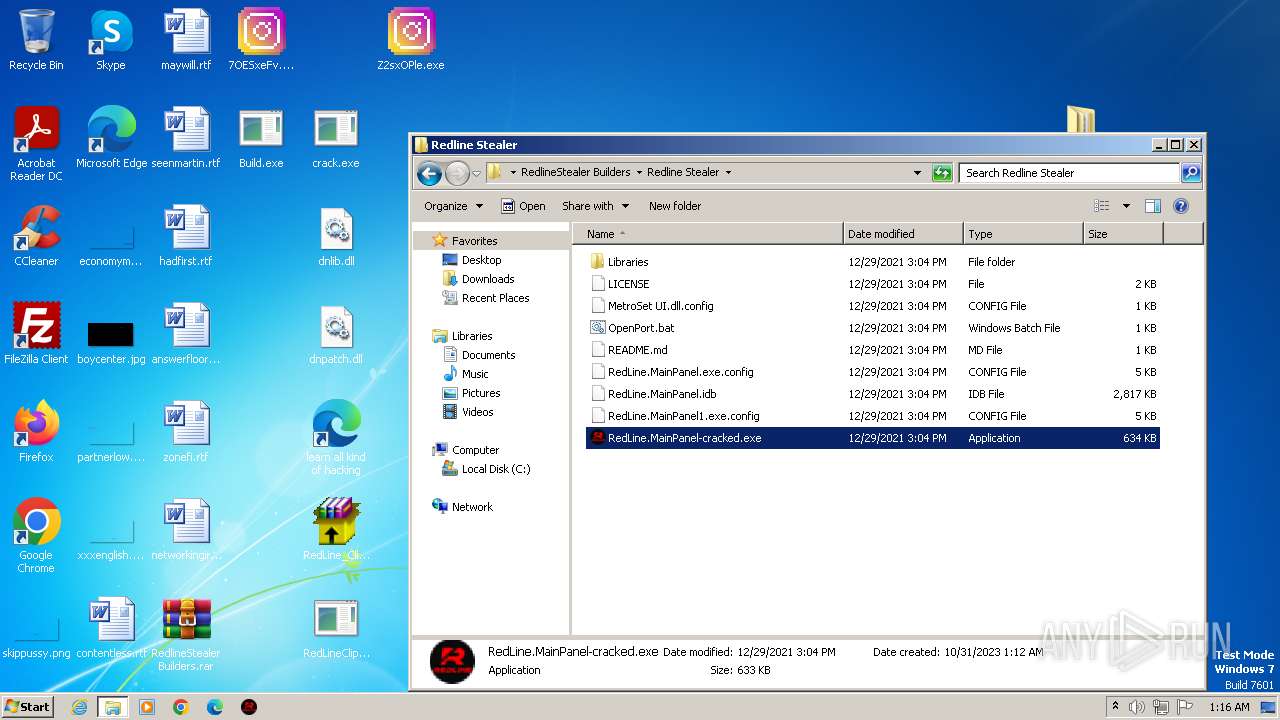
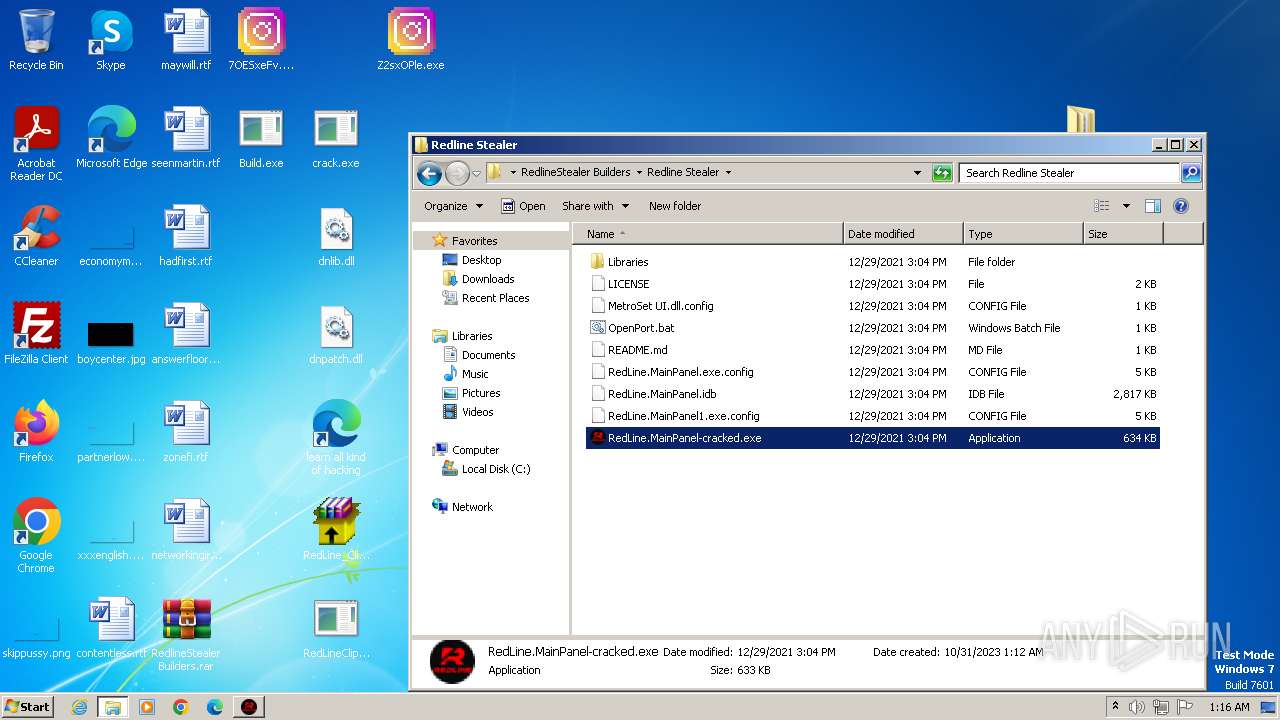
| 1304 | "C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer\Libraries\builder.exe" | C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer\Libraries\builder.exe | RedLine.MainPanel-cracked.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: builder Exit code: 0 Version: 1.0.0.0 | |||||||||||||||
| 1400 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "cmd.exe" /C taskkill /F /PID 3064 && choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\Desktop\Build.exe" | C:\Windows\System32\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
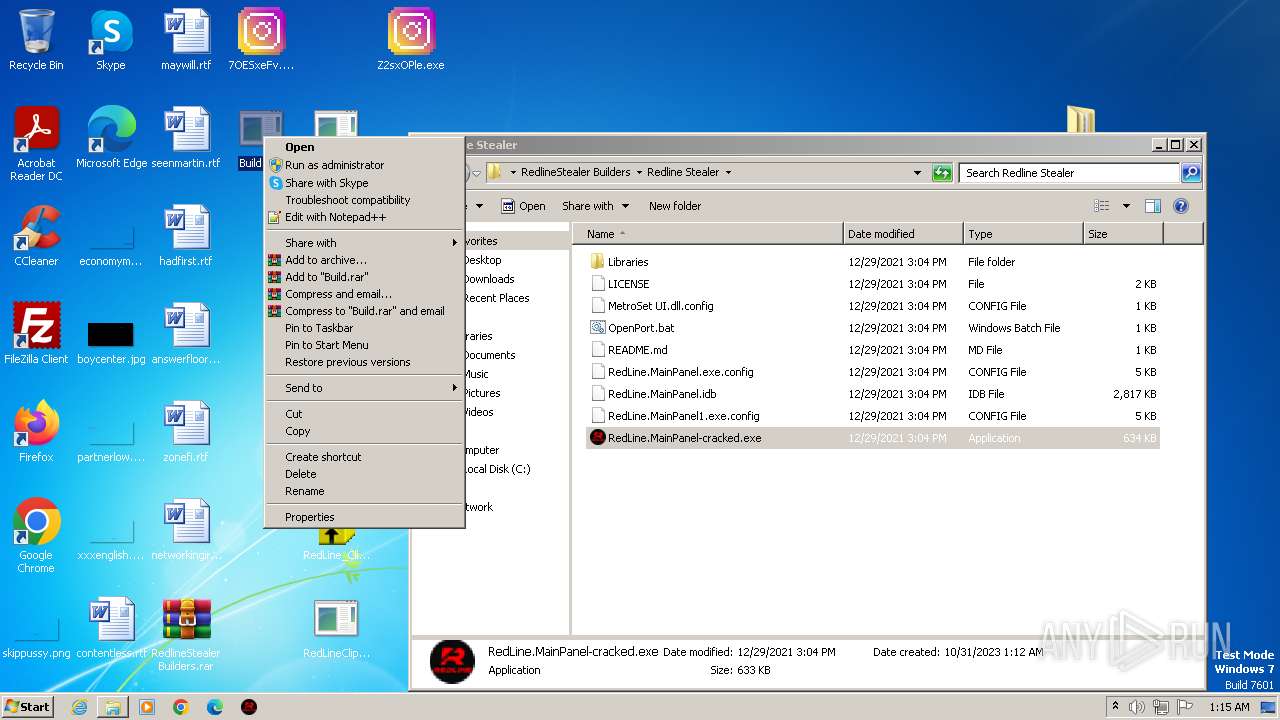
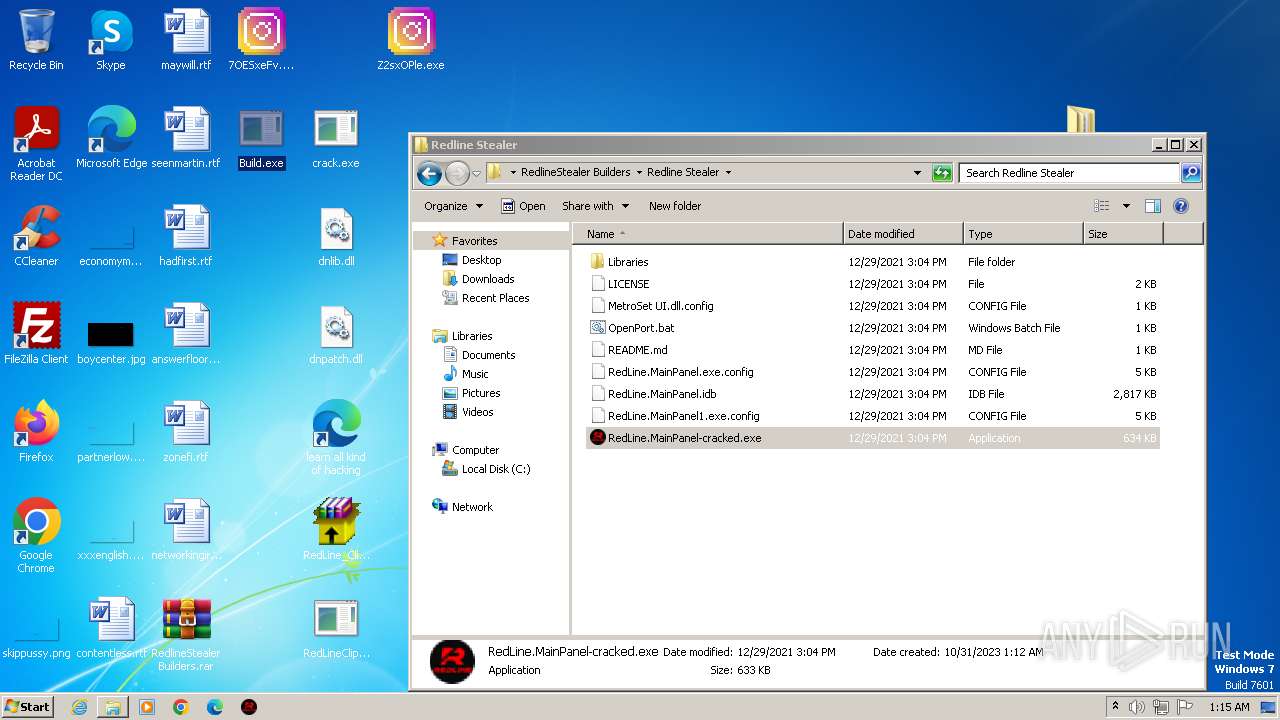
| 1688 | "C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer\RedLine.MainPanel-cracked.exe" | C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer\RedLine.MainPanel-cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RedLinePanel Exit code: 0 Version: 1.0.0.0 | |||||||||||||||
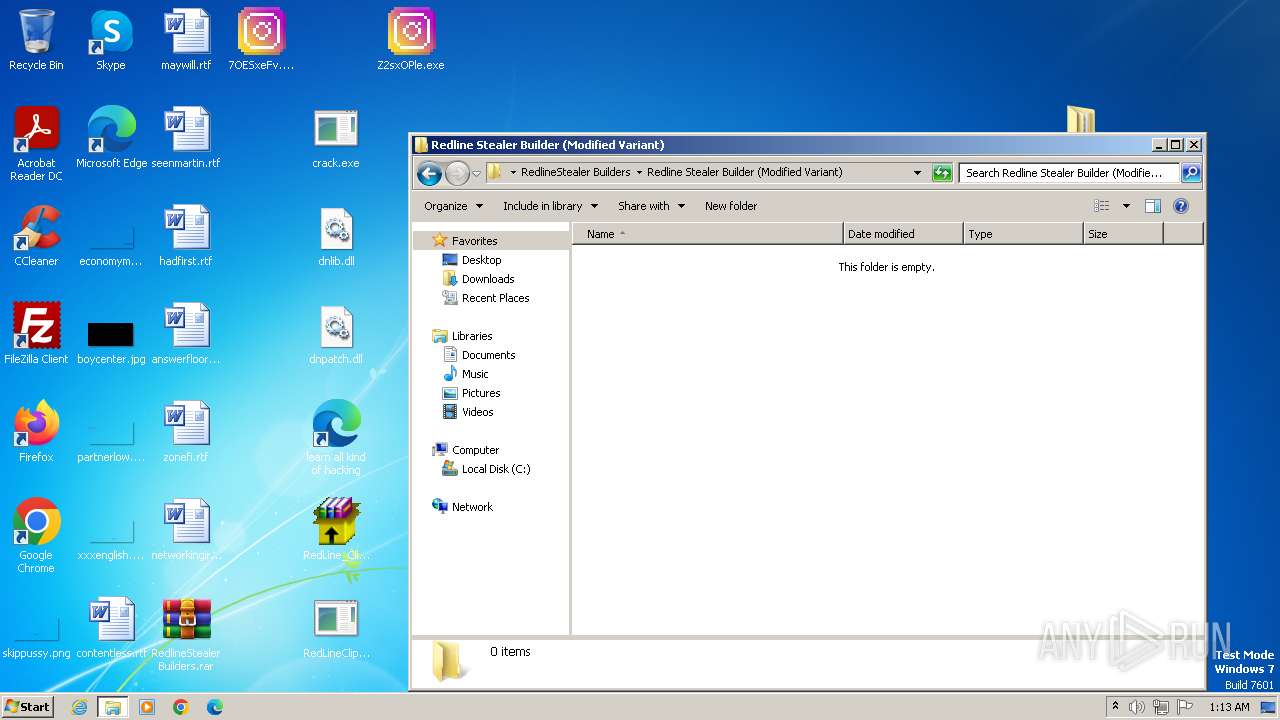
| 1796 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\RedlineStealer Builders.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
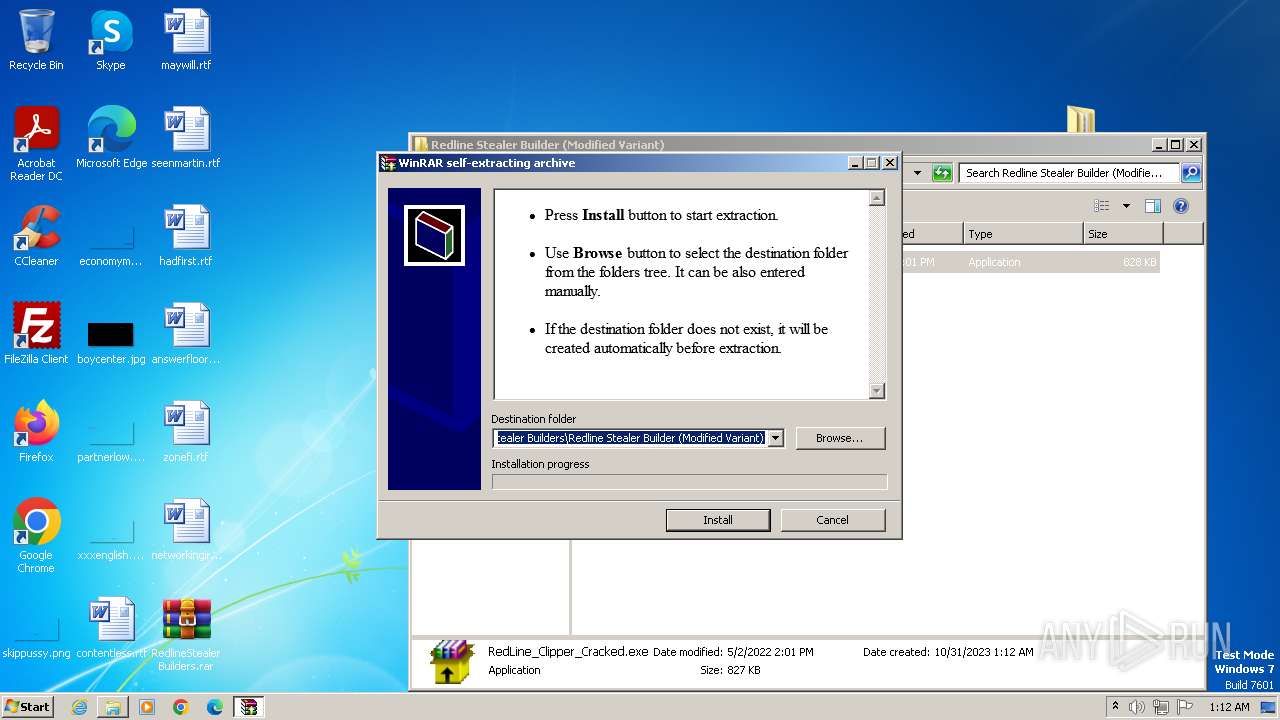
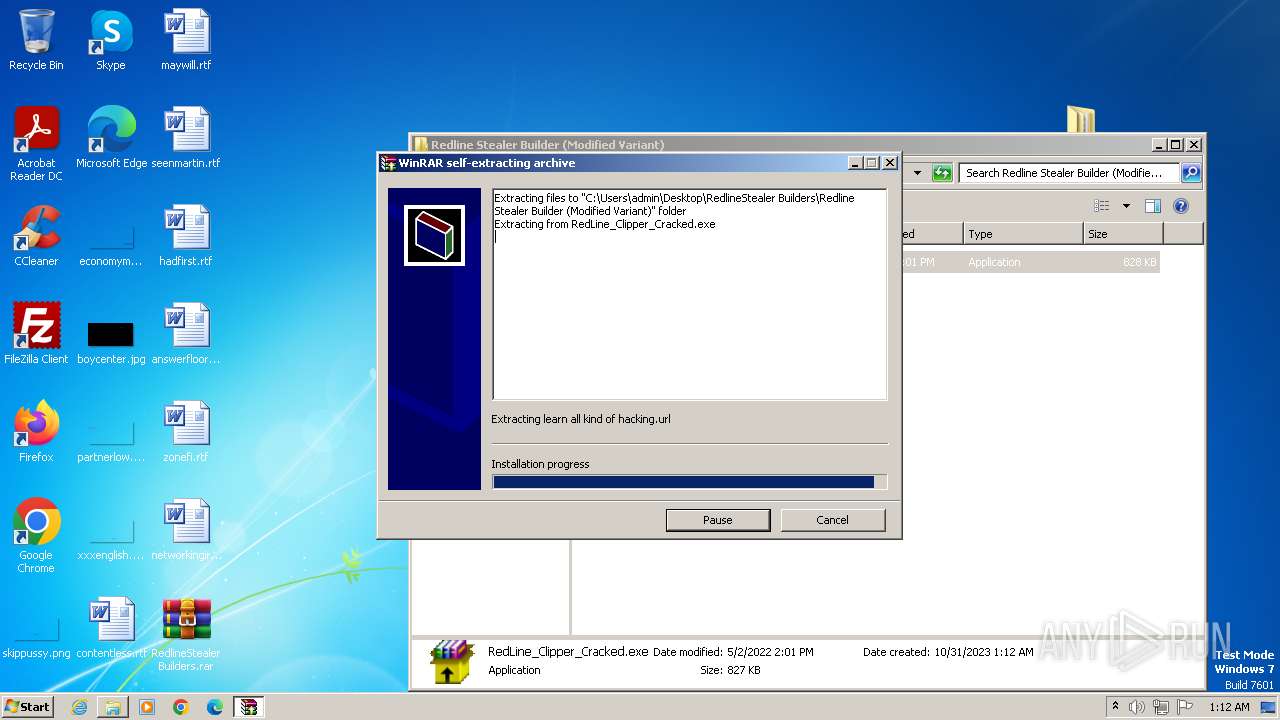
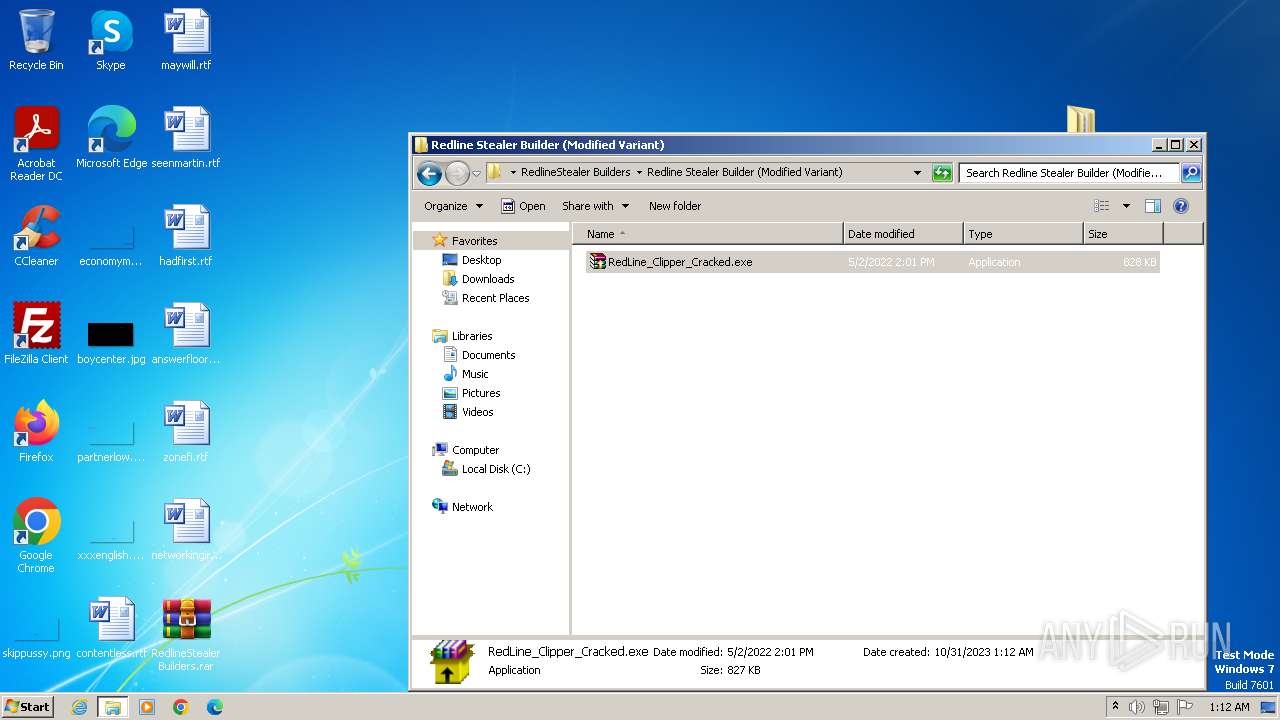
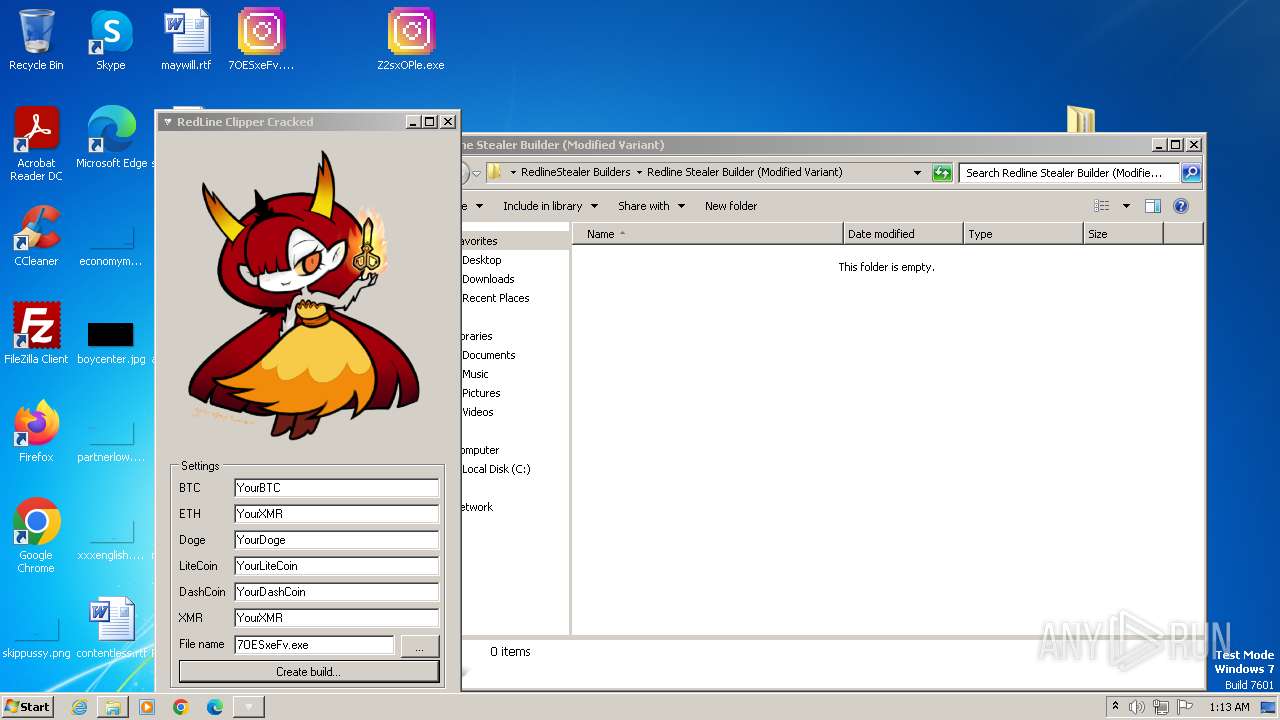
| 1956 | "C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer Builder (Modified Variant)\RedLine_Clipper_Cracked.exe" | C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer Builder (Modified Variant)\RedLine_Clipper_Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2216 | taskkill /F /PID 3064 | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2372 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer\OpenPort.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 2428 | "C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer Builder (Modified Variant)\crack.exe" | C:\Users\admin\Desktop\RedlineStealer Builders\Redline Stealer Builder (Modified Variant)\crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Get Cliboard Address Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
10 435
Read events
10 210
Write events
224
Delete events
1
Modification events
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1400) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | write | Name: | MRUListEx |
Value: 020000001E0000001D0000001C0000001B0000001A000000000000001900000003000000180000001600000017000000150000001400000013000000120000000F00000011000000100000000E0000000D0000000C0000000B0000000A00000009000000080000000700000006000000050000000400000001000000FFFFFFFF | |||
| (PID) Process: | (1400) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
35
Suspicious files
14
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1400 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | binary | |
MD5:DAAAC49C6DECA37836E023F49CD165E0 | SHA256:5E7622B3F3DE106303DBB87003AEB7704EE8670EA132AD8D189AB2D345CF3B12 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Build.exe | executable | |
MD5:1035BBF6B782B7A8819FA9BC616A9657 | SHA256:4060699BE22D52CD3753FA0BB8D3147A7B14B4EE9769013F2F0AD284586911CB | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\builder.pdb | binary | |
MD5:418DC008EF956465E179EC29D3C3C245 | SHA256:8C7E21B37540211D56C5FDBB7E731655A96945AA83F2988E33D5ADB8AA7C8DF1 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\builder.exe | executable | |
MD5:DE6F68CDF350FCE9BE13803D84BE98C4 | SHA256:51BBC69942823B84C2A1F0EFDB9D63FB04612B223E86AF8A83B4B307DD15CD24 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Mono.Cecil.dll | executable | |
MD5:7546ACEBC5A5213DEE2A5ED18D7EBC6C | SHA256:7744C9C84C28033BC3606F4DFCE2ADCD6F632E2BE7827893C3E2257100F1CF9E | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Bunifu_UI_v1.52.dll | executable | |
MD5:5ECA94D909F1BA4C5F3E35AC65A49076 | SHA256:DE0E530D46C803D85B8AEB6D18816F1B09CB3DAFEFB5E19FDFA15C9F41E0F474 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Mono.Cecil.Pdb.dll | executable | |
MD5:6CD3ED3DB95D4671B866411DB4950853 | SHA256:D67EBD49241041E6B6191703A90D89E68D4465ADCE02C595218B867DF34581A3 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Mono.Cecil.Mdb.pdb | binary | |
MD5:0BA762B6B5FBDA000E51D66722A3BB2C | SHA256:D18EB89421D50F079291B78783408CEE4BAB6810E4C5A4B191849265BDD5BA7C | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Mono.Cecil.Mdb.dll | executable | |
MD5:DC80F588F513D998A5DF1CA415EDB700 | SHA256:90CFC73BEFD43FC3FD876E23DCC3F5CE6E9D21D396BBB346513302E2215DB8C9 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1796.20378\RedlineStealer Builders\Redline Stealer\Libraries\Mono.Cecil.pdb | binary | |
MD5:C0A69F1B0C50D4F133CD0B278AC2A531 | SHA256:A4F79C99D8923BD6C30EFAFA39363C18BABE95F6609BBAD242BCA44342CCC7BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |