| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/bb631cba-3f6f-47bf-9960-6e0857c325e4 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 29, 2025, 11:28:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 18343F5CBF09AF16B70E4BDB87C5FC91 |
| SHA1: | 658DAA31317EE322B731BBEB60513CF7B4BDEB0B |
| SHA256: | DB3FC10F5DD5F1D577A19988E1C4E127935224CFAE35C02823F312C88CA953D8 |
| SSDEEP: | 98304:cPFKLwTEGKLaCJl7UotN5srrUK7vgyONaCr:N |
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 6640)
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
- Q6YODXZGNV558L0E.exe (PID: 5756)
LUMMA mutex has been found
- Setup.exe (PID: 6640)
Steals credentials from Web Browsers
- Setup.exe (PID: 6640)
Actions looks like stealing of personal data
- Setup.exe (PID: 6640)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 6640)
Executable content was dropped or overwritten
- Setup.exe (PID: 6640)
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Searches for installed software
- Setup.exe (PID: 6640)
Executes application which crashes
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5256)
Starts CMD.EXE for commands execution
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
INFO
Checks supported languages
- Setup.exe (PID: 6640)
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
- Q6YODXZGNV558L0E.exe (PID: 5756)
The sample compiled with russian language support
- Setup.exe (PID: 6640)
Reads the software policy settings
- Setup.exe (PID: 6640)
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Reads the computer name
- Setup.exe (PID: 6640)
- Q6YODXZGNV558L0E.exe (PID: 5756)
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Create files in a temporary directory
- Setup.exe (PID: 6640)
The sample compiled with english language support
- Setup.exe (PID: 6640)
Creates files in the program directory
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Drops encrypted JS script (Microsoft Script Encoder)
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Reads the machine GUID from the registry
- Y99OM3B4326UNPJMAMB4U.exe (PID: 6080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:06:27 10:41:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 910848 |
| InitializedDataSize: | 919552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8415f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.30.4914 |
| ProductVersionNumber: | 3.2.30.4914 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
| CompanyName: | Яндекс |
| FileDescription: | YandexDiskSetup |
| FileVersion: | 3.2.30.4914 |
| InternalName: | YandexDiskSetup |
| LegalCopyright: | © 2016-2023 ООО "ЯНДЕКС" |
| OriginalFileName: | YandexDiskSetup.exe |
| ProductName: | Яндекс.Диск |
| ProductVersion: | 3.2.30.4914 |
| Tag040904B0: | - |
| Tag041F04B0: | - |
Total processes
150
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6080 -s 736 | C:\Windows\SysWOW64\WerFault.exe | — | Y99OM3B4326UNPJMAMB4U.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6080 -s 540 | C:\Windows\SysWOW64\WerFault.exe | — | Y99OM3B4326UNPJMAMB4U.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce /v shark /t REG_SZ /d C:\ProgramData\shark.exe /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6080 -s 620 | C:\Windows\SysWOW64\WerFault.exe | — | Y99OM3B4326UNPJMAMB4U.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5124 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6080 -s 640 | C:\Windows\SysWOW64\WerFault.exe | — | Y99OM3B4326UNPJMAMB4U.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | cmd /c "reg add HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce /v shark /t REG_SZ /d C:\ProgramData\shark.exe /f" | C:\Windows\SysWOW64\cmd.exe | — | Y99OM3B4326UNPJMAMB4U.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5728 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6080 -s 608 | C:\Windows\SysWOW64\WerFault.exe | — | Y99OM3B4326UNPJMAMB4U.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
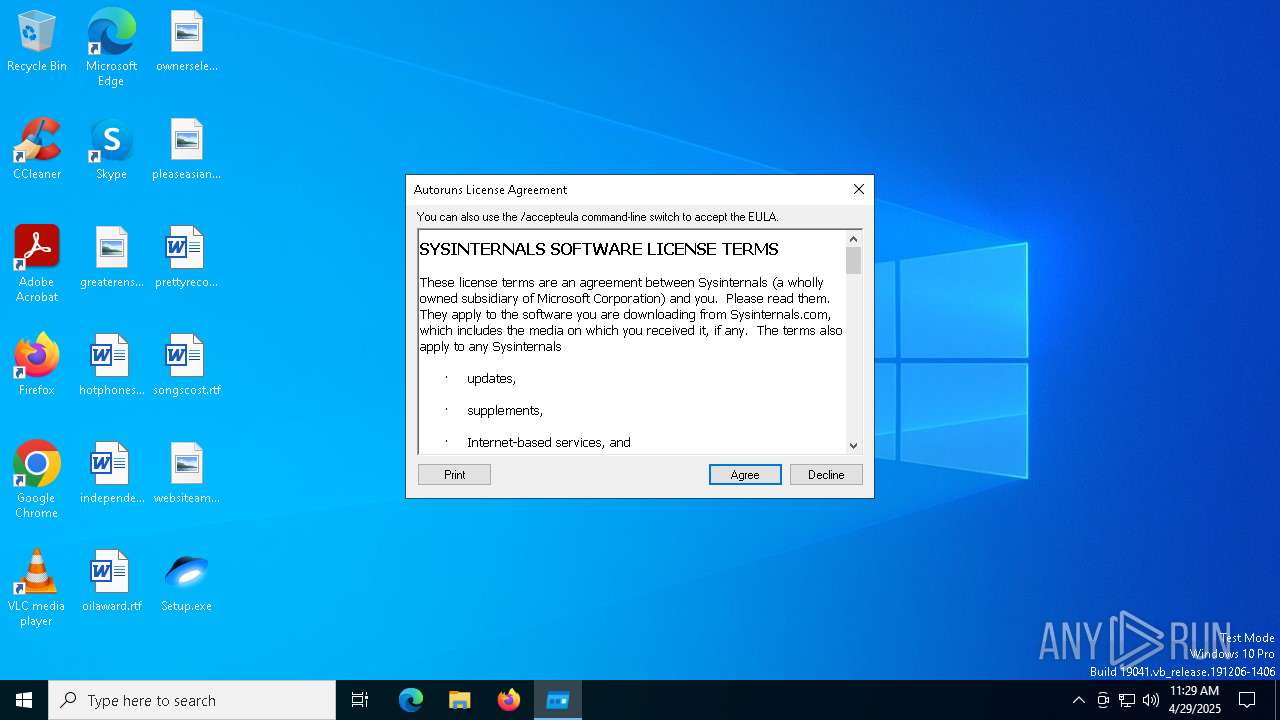
| 5756 | "C:\Users\admin\AppData\Local\Temp\Q6YODXZGNV558L0E.exe" | C:\Users\admin\AppData\Local\Temp\Q6YODXZGNV558L0E.exe | — | Setup.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Autostart program viewer Version: 14.09 Modules
| |||||||||||||||
Total events
5 895
Read events
5 894
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2516) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | shark |
Value: C:\ProgramData\shark.exe | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6080 | Y99OM3B4326UNPJMAMB4U.exe | C:\ProgramData\shark.exe | executable | |
MD5:6C9F00DC3B5E5F4BA983856E3127FE5A | SHA256:9B779FD1067255BDC612A797CAA8536276BC78A37BDE7EF068ABDF726FC79011 | |||
| 6640 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Q6YODXZGNV558L0E.exe | executable | |
MD5:7AFD388B65B41E842D7FF34FDE825CCE | SHA256:96C666F2AFE4D60BB18412B675416CFA9FA10C113C8185BC2CA55F7396C3EFC6 | |||
| 6640 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Y99OM3B4326UNPJMAMB4U.exe | executable | |
MD5:6C9F00DC3B5E5F4BA983856E3127FE5A | SHA256:9B779FD1067255BDC612A797CAA8536276BC78A37BDE7EF068ABDF726FC79011 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
27
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6068 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6068 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
nodepathr.run |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES DNS Query to Commonly Actor Abused Online Service (data-seed-prebsc-2-s1 .binance .org) |
6080 | Y99OM3B4326UNPJMAMB4U.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (data-seed-prebsc-2-s1 .binance .org in TLS SNI) |