| File name: | file |
| Full analysis: | https://app.any.run/tasks/415ef250-fcc6-4227-a716-a038f6eb3010 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 14, 2024, 11:54:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 986A01646E19832CD4D612C37E1AC75B |
| SHA1: | C8463240DDE522EDB3F558E542665734346D5F1B |
| SHA256: | DB29099D060B9ED6C0959E6B13A4B35C6B0893FD1870805C77F05AB6E57EEDF2 |
| SSDEEP: | 98304:M41d5FP7gDN0Sw/AtYB+KGa1gSOsLOZ99Hf/Bfvg+h2smYRjZ0khRx0vF2ZH6g0: |
MALICIOUS
Connects to the CnC server
- skotes.exe (PID: 6428)
- svchost.exe (PID: 2192)
- 1a4a33c157.exe (PID: 6192)
AMADEY has been detected (SURICATA)
- skotes.exe (PID: 6428)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- PK13K1G.exe (PID: 6864)
- d182448e91.exe (PID: 5776)
LUMMA mutex has been found
- PK13K1G.exe (PID: 6864)
- a4aeb99ac7.exe (PID: 8900)
- d182448e91.exe (PID: 5776)
Actions looks like stealing of personal data
- PK13K1G.exe (PID: 6864)
- a4aeb99ac7.exe (PID: 8900)
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
- d182448e91.exe (PID: 5776)
Steals credentials from Web Browsers
- PK13K1G.exe (PID: 6864)
- a4aeb99ac7.exe (PID: 8900)
- d182448e91.exe (PID: 5776)
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
LUMMA has been found (auto)
- skotes.exe (PID: 6428)
Possible tool for stealing has been detected
- 8c2ab5ea08.exe (PID: 5556)
- firefox.exe (PID: 6160)
StealC has been detected
- 1a4a33c157.exe (PID: 6192)
Changes the autorun value in the registry
- skotes.exe (PID: 6428)
STEALC has been detected (SURICATA)
- 1a4a33c157.exe (PID: 6192)
COINMINER has been found (auto)
- skotes.exe (PID: 6428)
Uses Task Scheduler to run other applications
- in.exe (PID: 8772)
- in.exe (PID: 8408)
VIDAR mutex has been found
- 4c32fa06c3.exe (PID: 9184)
AMADEY has been detected (YARA)
- skotes.exe (PID: 6428)
STEALC has been detected (YARA)
- 1a4a33c157.exe (PID: 6192)
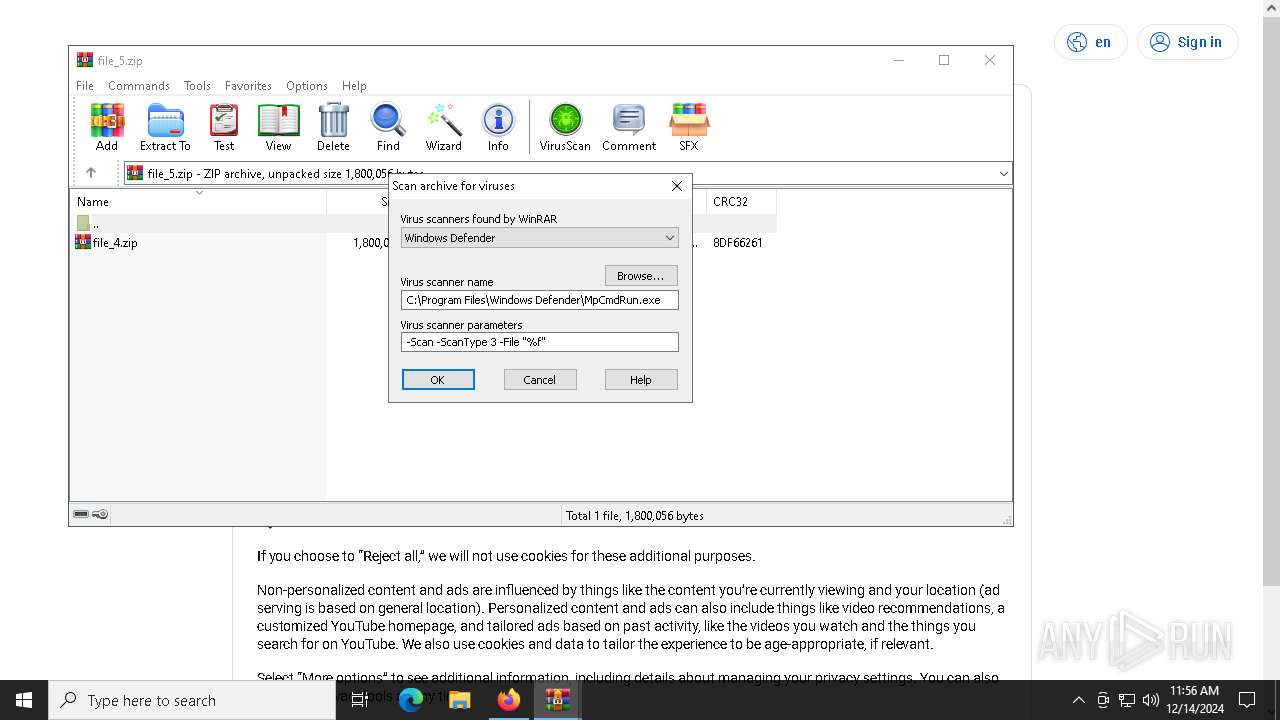
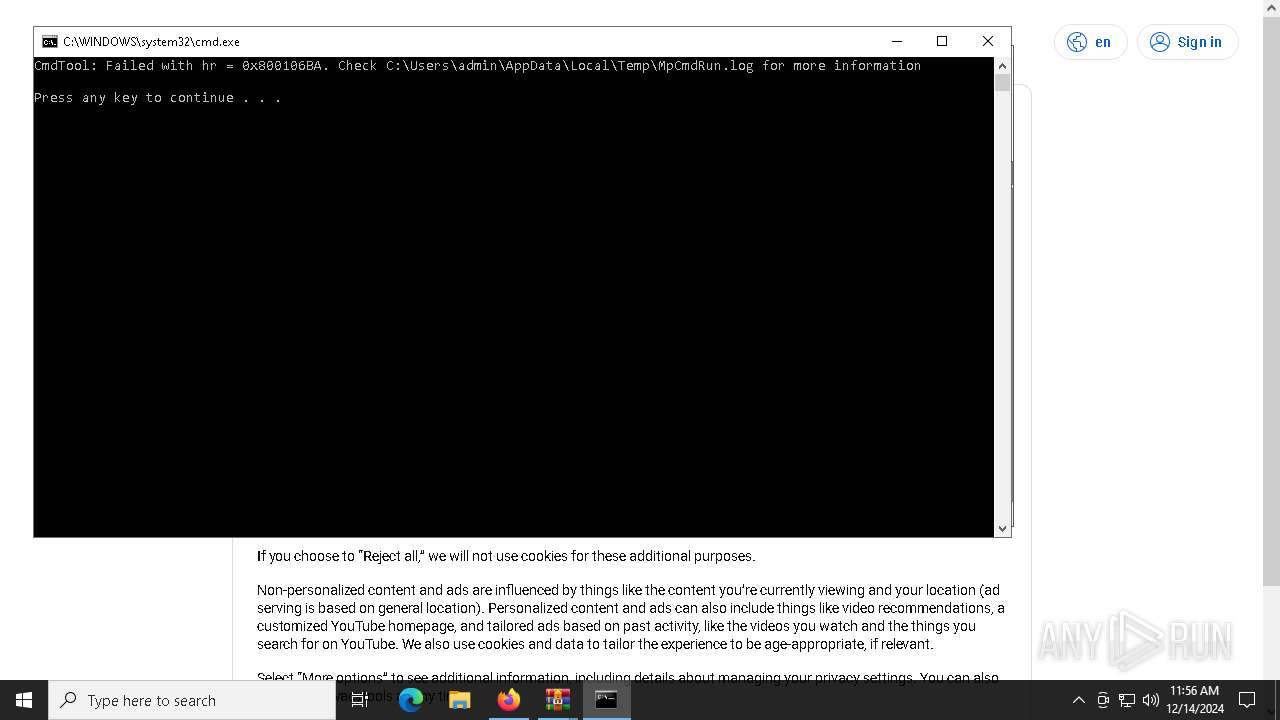
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 7188)
SUSPICIOUS
Executable content was dropped or overwritten
- file.exe (PID: 5404)
- skotes.exe (PID: 6428)
- d9868569de.exe (PID: 7832)
- 7z.exe (PID: 8732)
- cmd.exe (PID: 8512)
- in.exe (PID: 8772)
- 1a4a33c157.exe (PID: 6192)
Reads the BIOS version
- file.exe (PID: 5404)
- skotes.exe (PID: 6428)
- skotes.exe (PID: 6920)
- 1a4a33c157.exe (PID: 6192)
- 98c23c2336.exe (PID: 7764)
- AAKKFHCFIE.exe (PID: 8684)
- skotes.exe (PID: 8140)
Reads security settings of Internet Explorer
- file.exe (PID: 5404)
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
- d9868569de.exe (PID: 7832)
- 4c32fa06c3.exe (PID: 9184)
- WinRAR.exe (PID: 5776)
Contacting a server suspected of hosting an CnC
- skotes.exe (PID: 6428)
- svchost.exe (PID: 2192)
- PK13K1G.exe (PID: 6864)
- 1a4a33c157.exe (PID: 6192)
- d182448e91.exe (PID: 5776)
Starts itself from another location
- file.exe (PID: 5404)
Process requests binary or script from the Internet
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
Application launched itself
- PK13K1G.exe (PID: 6792)
- a4aeb99ac7.exe (PID: 8408)
Potential Corporate Privacy Violation
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
The process executes via Task Scheduler
- skotes.exe (PID: 6920)
- skotes.exe (PID: 8140)
- Intel_PTT_EK_Recertification.exe (PID: 7356)
Connects to the server without a host name
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
Uses TASKKILL.EXE to kill process
- 8c2ab5ea08.exe (PID: 5556)
Uses TASKKILL.EXE to kill Browsers
- 8c2ab5ea08.exe (PID: 5556)
Windows Defender mutex has been found
- 1a4a33c157.exe (PID: 6192)
Searches for installed software
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
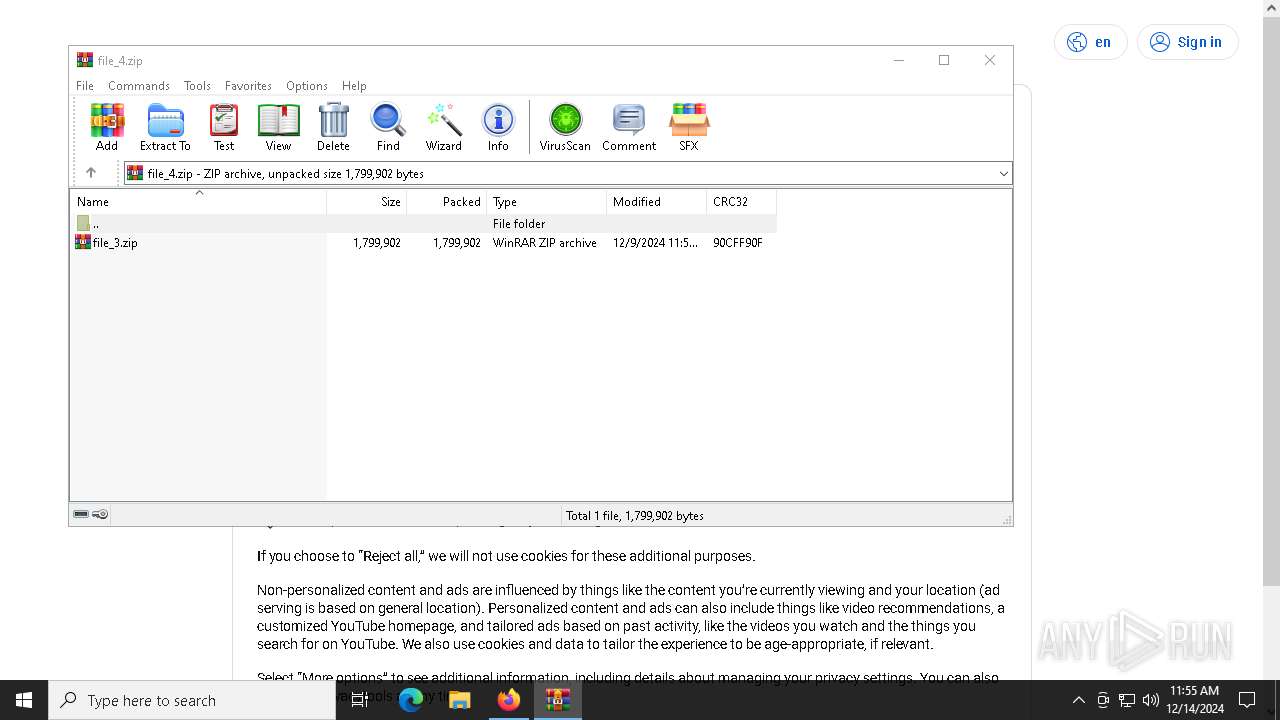
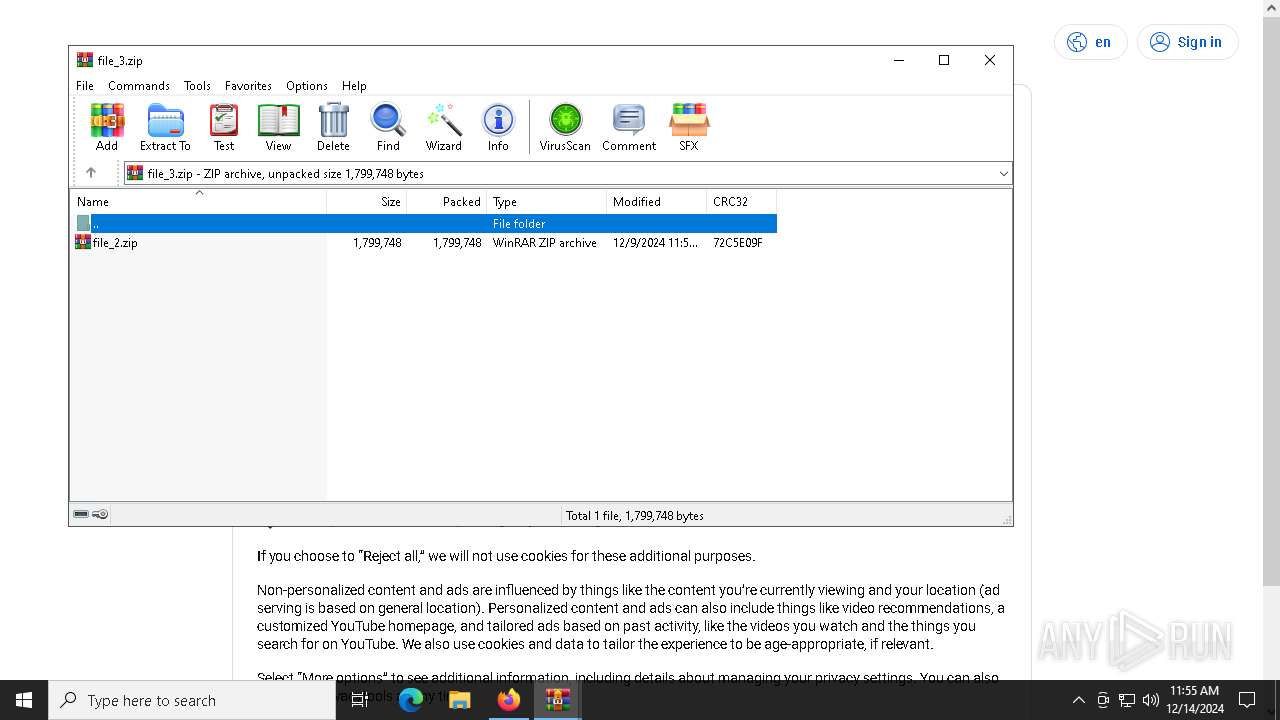
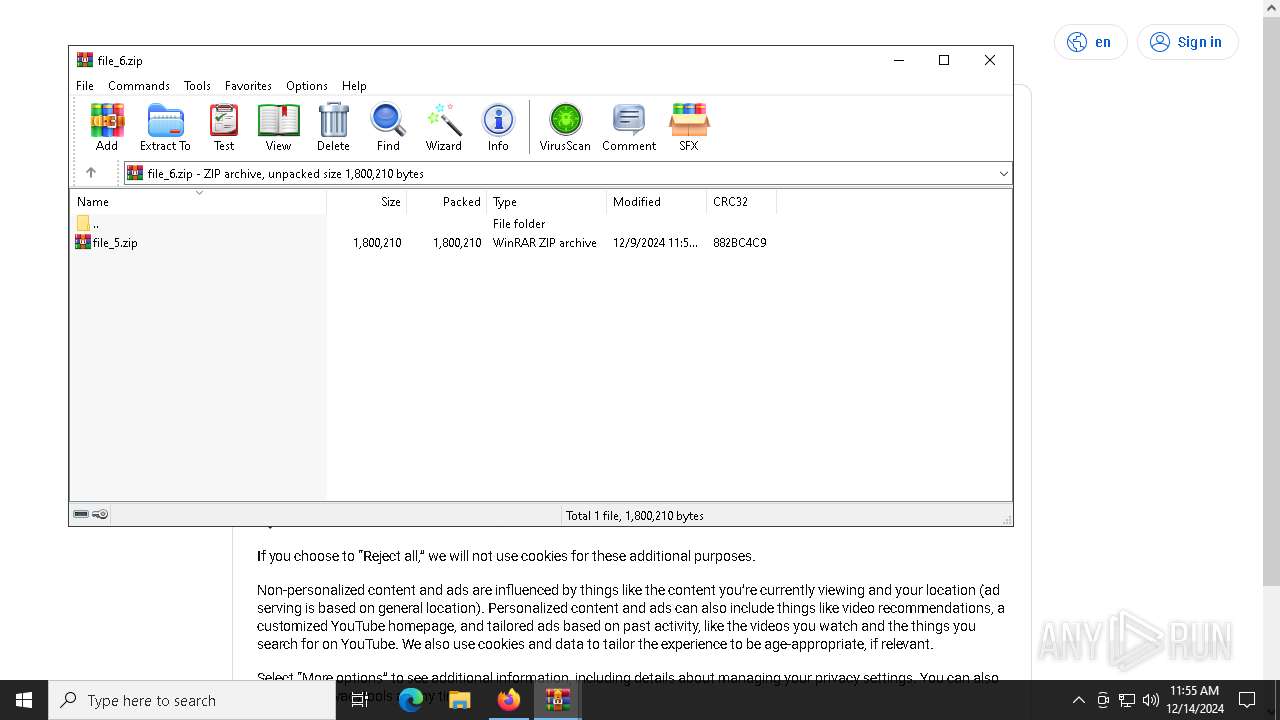
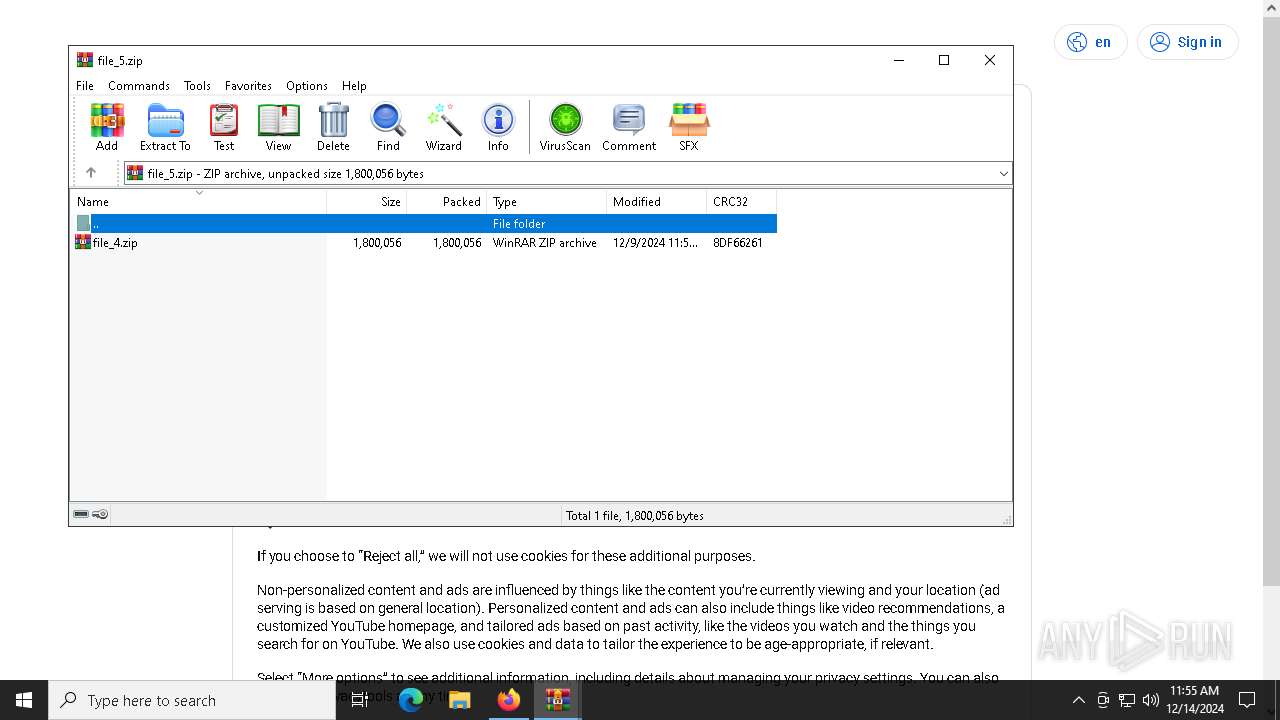
Drops 7-zip archiver for unpacking
- d9868569de.exe (PID: 7832)
Executing commands from a ".bat" file
- d9868569de.exe (PID: 7832)
- WinRAR.exe (PID: 5776)
Starts CMD.EXE for commands execution
- d9868569de.exe (PID: 7832)
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
- WinRAR.exe (PID: 5776)
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 8608)
- 7z.exe (PID: 8580)
- 7z.exe (PID: 8628)
- 7z.exe (PID: 8648)
- 7z.exe (PID: 8672)
- 7z.exe (PID: 8692)
- 7z.exe (PID: 8712)
- 7z.exe (PID: 8732)
- in.exe (PID: 8772)
- AAKKFHCFIE.exe (PID: 8684)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8512)
- in.exe (PID: 8772)
- in.exe (PID: 8408)
Checks Windows Trust Settings
- 4c32fa06c3.exe (PID: 9184)
Found IP address in command line
- powershell.exe (PID: 8828)
- powershell.exe (PID: 8836)
- powershell.exe (PID: 8040)
Starts POWERSHELL.EXE for commands execution
- in.exe (PID: 8772)
- in.exe (PID: 8408)
- Intel_PTT_EK_Recertification.exe (PID: 7356)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- 4c32fa06c3.exe (PID: 9184)
The process drops Mozilla's DLL files
- 1a4a33c157.exe (PID: 6192)
Process drops legitimate windows executable
- 1a4a33c157.exe (PID: 6192)
The process drops C-runtime libraries
- 1a4a33c157.exe (PID: 6192)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8152)
Executes application which crashes
- 4c32fa06c3.exe (PID: 9184)
INFO
Reads the computer name
- file.exe (PID: 5404)
- skotes.exe (PID: 6428)
- PK13K1G.exe (PID: 6864)
- 8c2ab5ea08.exe (PID: 5556)
- 1a4a33c157.exe (PID: 6192)
- 98c23c2336.exe (PID: 7764)
- d9868569de.exe (PID: 7832)
- 7z.exe (PID: 8580)
- 7z.exe (PID: 8608)
- 7z.exe (PID: 8628)
- 7z.exe (PID: 8672)
- 7z.exe (PID: 8648)
- 7z.exe (PID: 8692)
- 7z.exe (PID: 8712)
- 7z.exe (PID: 8732)
- 4c32fa06c3.exe (PID: 9184)
- a4aeb99ac7.exe (PID: 8900)
- d182448e91.exe (PID: 5776)
- MpCmdRun.exe (PID: 7188)
Create files in a temporary directory
- file.exe (PID: 5404)
- skotes.exe (PID: 6428)
- d9868569de.exe (PID: 7832)
- 7z.exe (PID: 8580)
- 7z.exe (PID: 8608)
- 7z.exe (PID: 8628)
- 7z.exe (PID: 8648)
- 7z.exe (PID: 8672)
- 7z.exe (PID: 8692)
- 7z.exe (PID: 8712)
- 7z.exe (PID: 8732)
- MpCmdRun.exe (PID: 7188)
Process checks computer location settings
- file.exe (PID: 5404)
- skotes.exe (PID: 6428)
- d9868569de.exe (PID: 7832)
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
Checks proxy server information
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
- WerFault.exe (PID: 1412)
Sends debugging messages
- skotes.exe (PID: 6428)
- file.exe (PID: 5404)
- skotes.exe (PID: 6920)
- 1a4a33c157.exe (PID: 6192)
- 98c23c2336.exe (PID: 7764)
- AAKKFHCFIE.exe (PID: 8684)
- skotes.exe (PID: 8140)
Checks supported languages
- skotes.exe (PID: 6428)
- file.exe (PID: 5404)
- PK13K1G.exe (PID: 6864)
- PK13K1G.exe (PID: 6792)
- skotes.exe (PID: 6920)
- d182448e91.exe (PID: 5776)
- 8c2ab5ea08.exe (PID: 5556)
- 1a4a33c157.exe (PID: 6192)
- 98c23c2336.exe (PID: 7764)
- a4aeb99ac7.exe (PID: 8408)
- d9868569de.exe (PID: 7832)
- mode.com (PID: 8556)
- 7z.exe (PID: 8580)
- 7z.exe (PID: 8628)
- 7z.exe (PID: 8608)
- 7z.exe (PID: 8648)
- 7z.exe (PID: 8672)
- 7z.exe (PID: 8692)
- 7z.exe (PID: 8712)
- 7z.exe (PID: 8732)
- in.exe (PID: 8772)
- a4aeb99ac7.exe (PID: 8900)
- 4c32fa06c3.exe (PID: 9184)
- in.exe (PID: 8408)
- AAKKFHCFIE.exe (PID: 8684)
- skotes.exe (PID: 8140)
- Intel_PTT_EK_Recertification.exe (PID: 7356)
- MpCmdRun.exe (PID: 7188)
Creates files or folders in the user directory
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
- in.exe (PID: 8772)
- 4c32fa06c3.exe (PID: 9184)
- WerFault.exe (PID: 1412)
The process uses the downloaded file
- skotes.exe (PID: 6428)
- d9868569de.exe (PID: 7832)
- 1a4a33c157.exe (PID: 6192)
- WinRAR.exe (PID: 5776)
- 4c32fa06c3.exe (PID: 9184)
Reads the software policy settings
- PK13K1G.exe (PID: 6864)
- a4aeb99ac7.exe (PID: 8900)
- 4c32fa06c3.exe (PID: 9184)
- d182448e91.exe (PID: 5776)
- WerFault.exe (PID: 1412)
The sample compiled with english language support
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
- d9868569de.exe (PID: 7832)
Reads mouse settings
- 8c2ab5ea08.exe (PID: 5556)
Application launched itself
- firefox.exe (PID: 6160)
- firefox.exe (PID: 6180)
- chrome.exe (PID: 7928)
- msedge.exe (PID: 8268)
- chrome.exe (PID: 8188)
- msedge.exe (PID: 2092)
Reads product name
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
Reads CPU info
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
Reads Environment values
- 1a4a33c157.exe (PID: 6192)
- 4c32fa06c3.exe (PID: 9184)
Starts MODE.COM to configure console settings
- mode.com (PID: 8556)
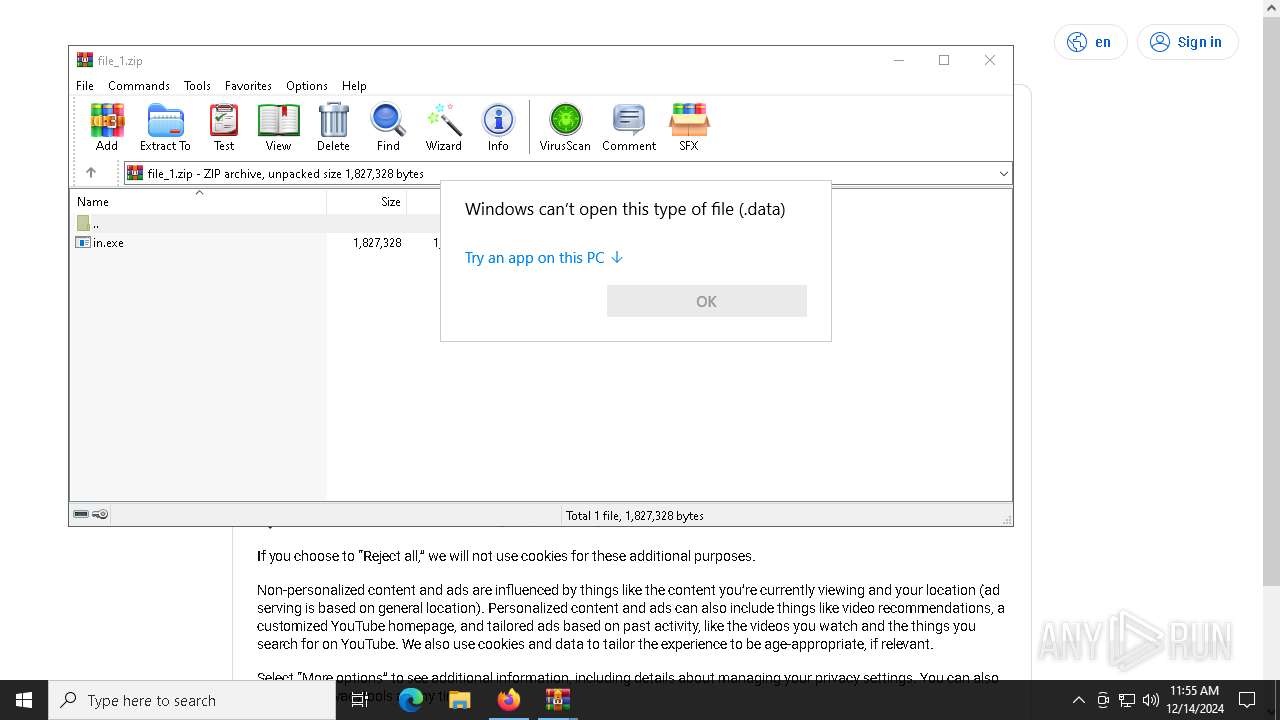
Manual execution by a user
- WinRAR.exe (PID: 8716)
- in.exe (PID: 8408)
- WinRAR.exe (PID: 8868)
- WinRAR.exe (PID: 9128)
- OpenWith.exe (PID: 8120)
- WinRAR.exe (PID: 8932)
- WinRAR.exe (PID: 1356)
- WinRAR.exe (PID: 5776)
Reads the machine GUID from the registry
- 4c32fa06c3.exe (PID: 9184)
Themida protector has been detected
- skotes.exe (PID: 6428)
- 1a4a33c157.exe (PID: 6192)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8828)
- powershell.exe (PID: 8836)
- powershell.exe (PID: 8040)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 8120)
Executable content was dropped or overwritten
- firefox.exe (PID: 6180)
Creates files in the program directory
- 4c32fa06c3.exe (PID: 9184)
- 1a4a33c157.exe (PID: 6192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:22 17:40:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 322048 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x310000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
259
Monitored processes
129
Malicious processes
15
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
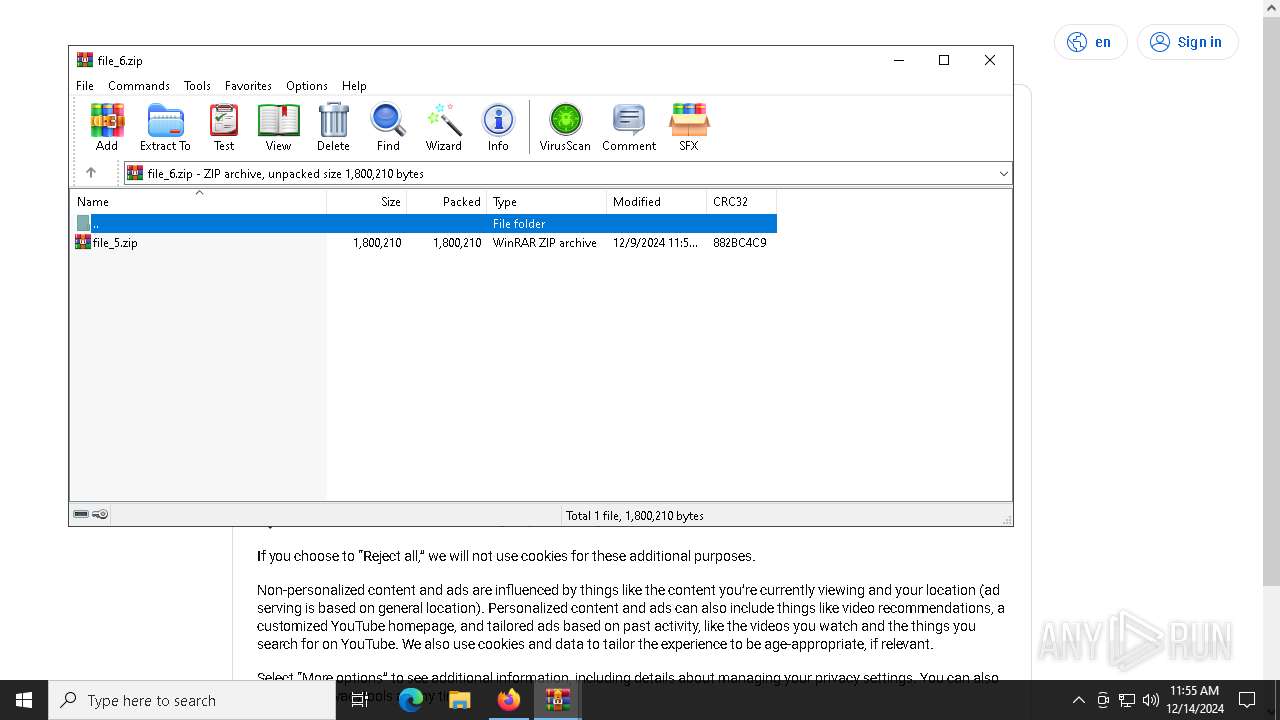
| 1356 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\file_2.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1412 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 9184 -s 2844 | C:\Windows\SysWOW64\WerFault.exe | 4c32fa06c3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --remote-debugging-port=9223 --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3680 --field-trial-handle=1964,i,7648953490937583370,8350221897437114672,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --remote-debugging-port=9229 --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3600 --field-trial-handle=1960,i,3117584816817967683,14265497474254398783,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2752 --field-trial-handle=2420,i,9692622775204129301,530129374465936743,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --remote-debugging-port=9223 --profile-directory="Default" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | 4c32fa06c3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "C:\Windows\system32\cmd.exe" /c start "" "C:\Users\admin\Documents\AAKKFHCFIE.exe" | C:\Windows\SysWOW64\cmd.exe | — | 1a4a33c157.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3540 | taskkill /F /IM firefox.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | 8c2ab5ea08.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
56 188
Read events
56 098
Write events
90
Delete events
0
Modification events
| (PID) Process: | (6428) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6428) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6428) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6428) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 8c2ab5ea08.exe |
Value: C:\Users\admin\AppData\Local\Temp\1015166001\8c2ab5ea08.exe | |||
| (PID) Process: | (6180) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6192) 1a4a33c157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6192) 1a4a33c157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6192) 1a4a33c157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6428) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 1a4a33c157.exe |
Value: C:\Users\admin\AppData\Local\Temp\1015167001\1a4a33c157.exe | |||
| (PID) Process: | (7928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
65
Suspicious files
391
Text files
167
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6180 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5404 | file.exe | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | executable | |
MD5:986A01646E19832CD4D612C37E1AC75B | SHA256:DB29099D060B9ED6C0959E6B13A4B35C6B0893FD1870805C77F05AB6E57EEDF2 | |||
| 6428 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1015146001\PK13K1G.exe | executable | |
MD5:15A1CAF203C034ACFF6EB99EB66C5CF9 | SHA256:AD0025FF91B8339B11EF619BB57A2F1EFCACAAF0CCC16A0A0DC704AD0C18DCA3 | |||
| 6428 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1015165001\d182448e91.exe | executable | |
MD5:2A78CE9F3872F5E591D643459CABE476 | SHA256:21A2AC44ACD7A640735870EEBFD04B8DC57BC66877CB5BE3B929299E86A43DAE | |||
| 6428 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\random[1].exe | executable | |
MD5:2A78CE9F3872F5E591D643459CABE476 | SHA256:21A2AC44ACD7A640735870EEBFD04B8DC57BC66877CB5BE3B929299E86A43DAE | |||
| 6428 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\random[1].exe | executable | |
MD5:9BA5A9284F9E89843B0D21B2B2027B5E | SHA256:6D9D77738D9B5CBB78A8833F30664C96908C6101AA0B2757EBD829FD3904F668 | |||
| 6428 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:B355C3C7B4A5F5B7549D18FE732849D6 | SHA256:39F2838FD920FC9B46C4DA04494257050F1898BB6BD8C4E101F5012F75BD5CD2 | |||
| 6180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6428 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1015167001\1a4a33c157.exe | executable | |
MD5:B355C3C7B4A5F5B7549D18FE732849D6 | SHA256:39F2838FD920FC9B46C4DA04494257050F1898BB6BD8C4E101F5012F75BD5CD2 | |||
| 5404 | file.exe | C:\Windows\Tasks\skotes.job | binary | |
MD5:20A031A4F73CCFB0820FDFA4B3FAFC0F | SHA256:97DA73D1428DB84C964779230436849EE6470EC4EBCAE9C5F441F8ADA1D76297 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
76
TCP/UDP connections
222
DNS requests
205
Threats
78
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6428 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6428 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6180 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6428 | skotes.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/off/random.exe | unknown | — | — | malicious |
6192 | 1a4a33c157.exe | POST | 200 | 185.215.113.206:80 | http://185.215.113.206/c4becf79229cb002.php | unknown | — | — | malicious |
6180 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6180 | firefox.exe | POST | — | 142.250.181.227:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
440 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.38.73.129:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6060 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.80.89:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
bellflamre.click |
| malicious |
youtube.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6428 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
6428 | skotes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6428 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6428 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 2 |
6428 | skotes.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6428 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6428 | skotes.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6428 | skotes.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
6864 | PK13K1G.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (bellflamre .click in TLS SNI) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (bellflamre .click) |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
1a4a33c157.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
98c23c2336.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
AAKKFHCFIE.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|