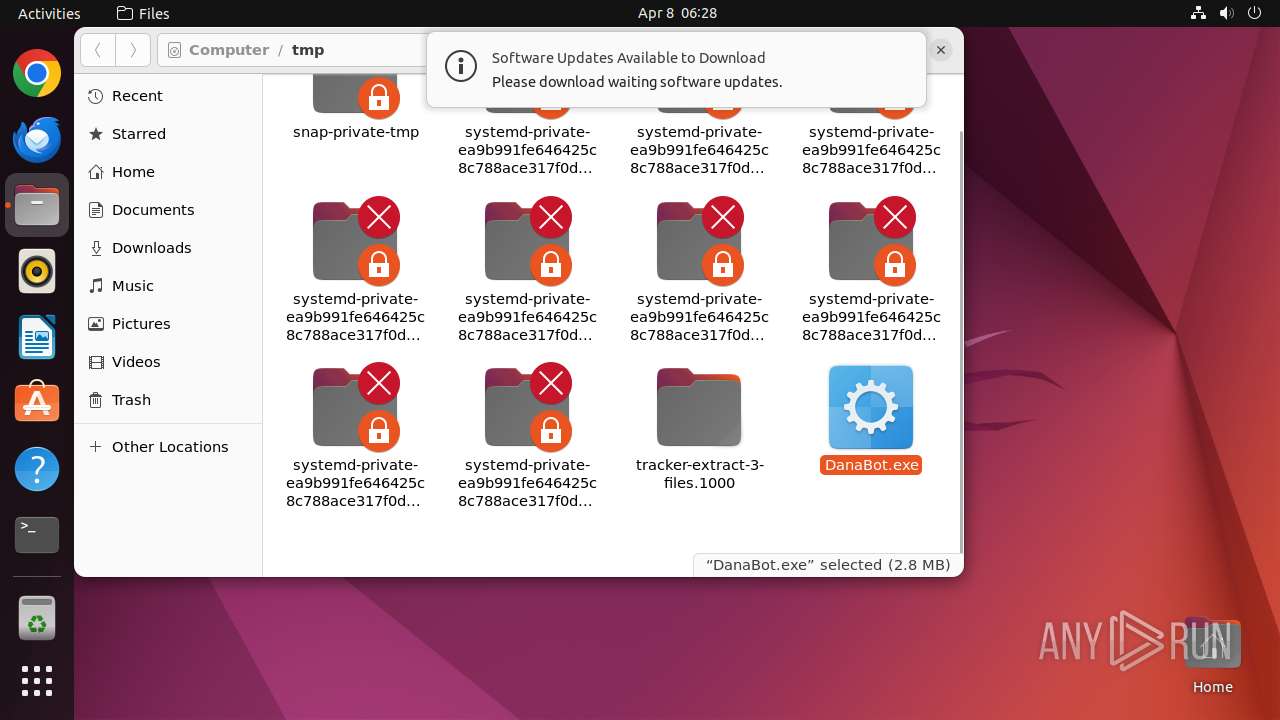
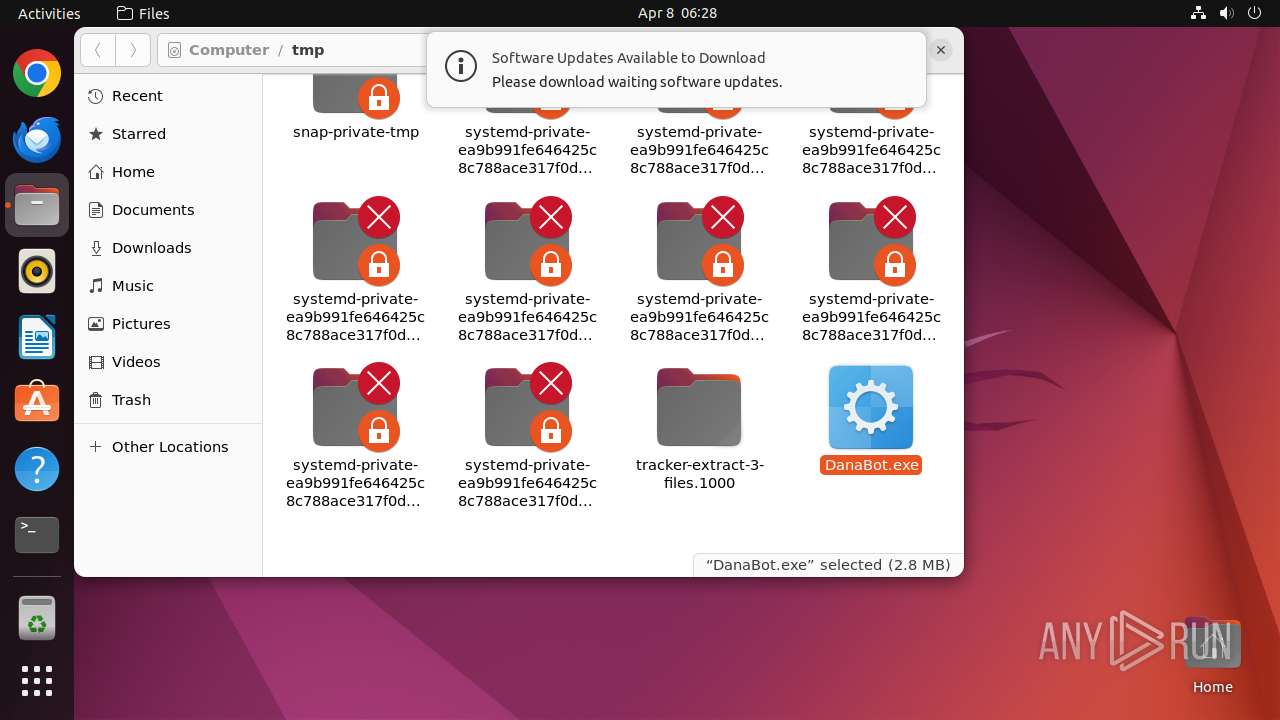
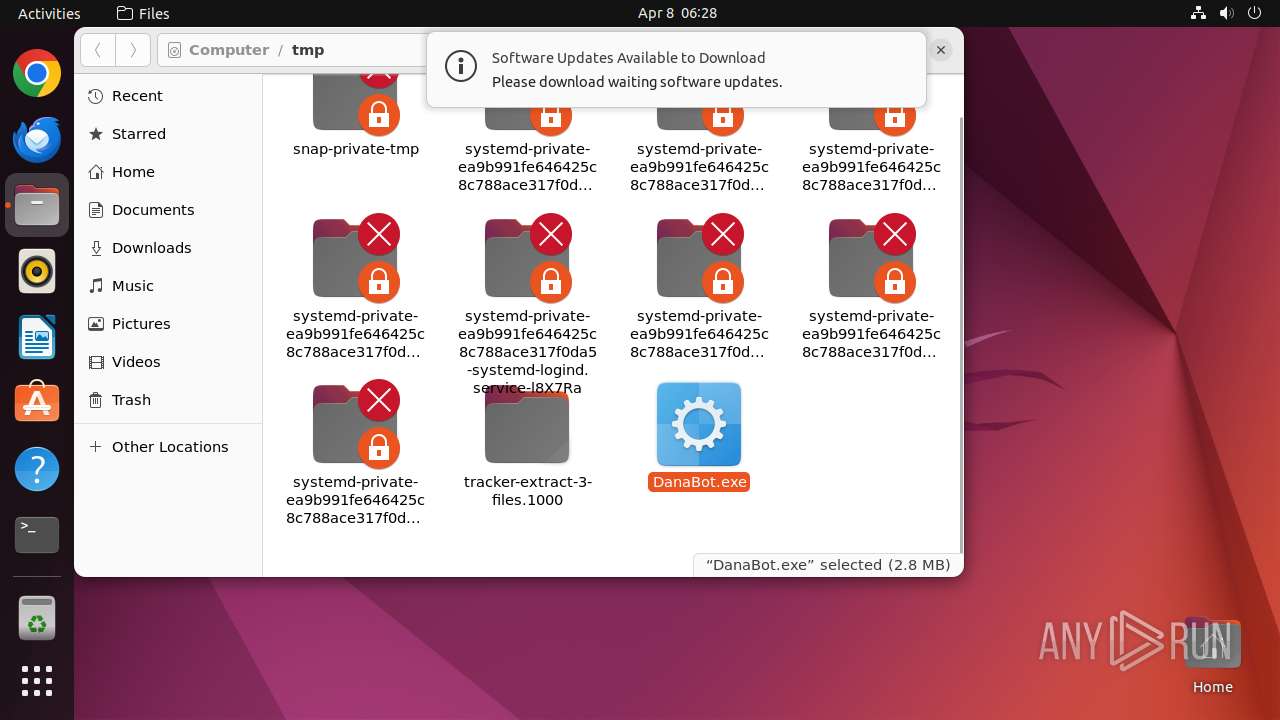
| File name: | DanaBot.exe |
| Full analysis: | https://app.any.run/tasks/c86d0817-7fab-4dcf-a353-577e81e65d95 |
| Verdict: | Malicious activity |
| Threats: | Danabot is an advanced banking Trojan malware that was designed to steal financial information from victims. Out of the Trojans in the wild, this is one of the most advanced thanks to the modular design and a complex delivery method. |
| Analysis date: | April 08, 2025, 05:27:59 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 48D8F7BBB500AF66BAA765279CE58045 |
| SHA1: | 2CDB5FDEEE4E9C7BD2E5F744150521963487EB71 |
| SHA256: | DB0D72BC7D10209F7FA354EC100D57ABBB9FE2E57CE72789F5F88257C5D3EBD1 |
| SSDEEP: | 49152:bbevayZlMTWkygVy0nQZfVY2BtZzpPL4PuQ65+6Dv7m0KXTnw:bbexZlMQcEVY2BtZzpPL4WQI9Uc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads profile file
- nautilus (PID: 39495)
Executes commands using command-line interpreter
- sudo (PID: 39494)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:14 19:36:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 63488 |
| InitializedDataSize: | 6928384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3aa3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Total processes
228
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39493 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /tmp/DanaBot\.exe " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 39494 | sudo -iu user nautilus /tmp/DanaBot.exe | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 39495 | nautilus /tmp/DanaBot.exe | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 39496 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39514 | /lib/systemd/systemd-hostnamed | /usr/lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.18:80 | http://connectivity-check.ubuntu.com/ | GB | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 169.150.255.180:443 | odrs.gnome.org | — | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
6.100.168.192.in-addr.arpa |
| unknown |