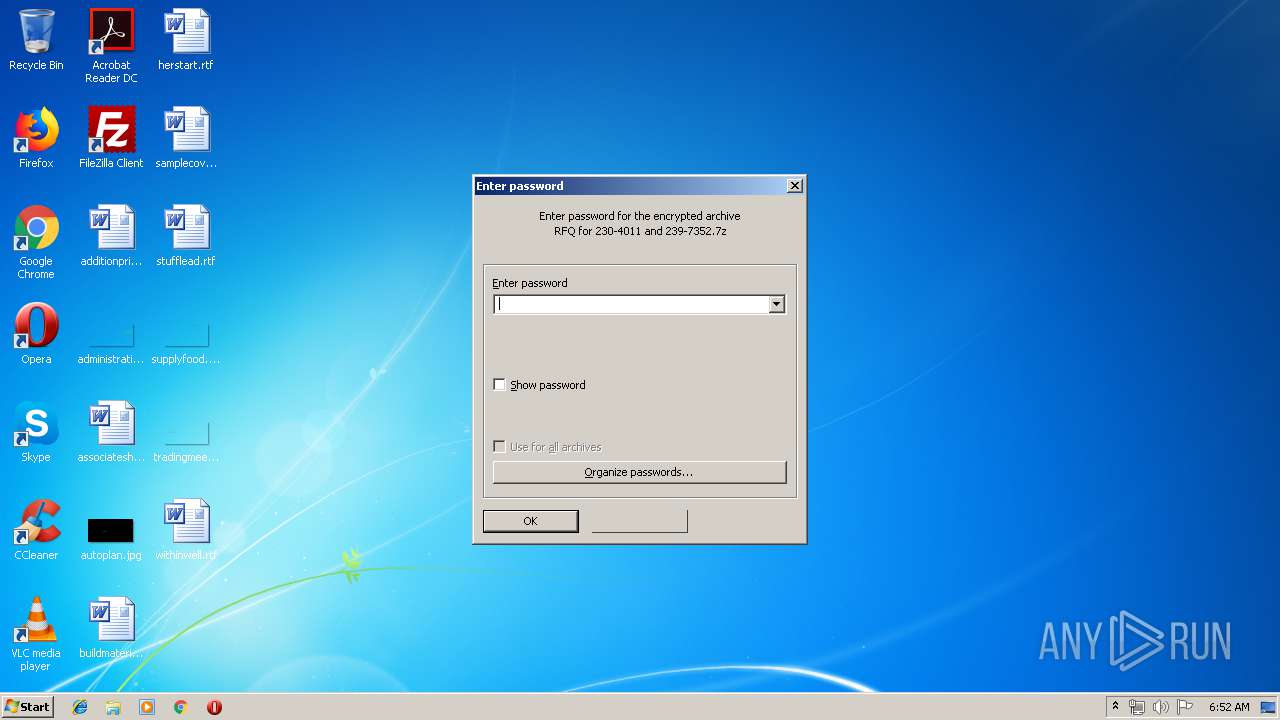
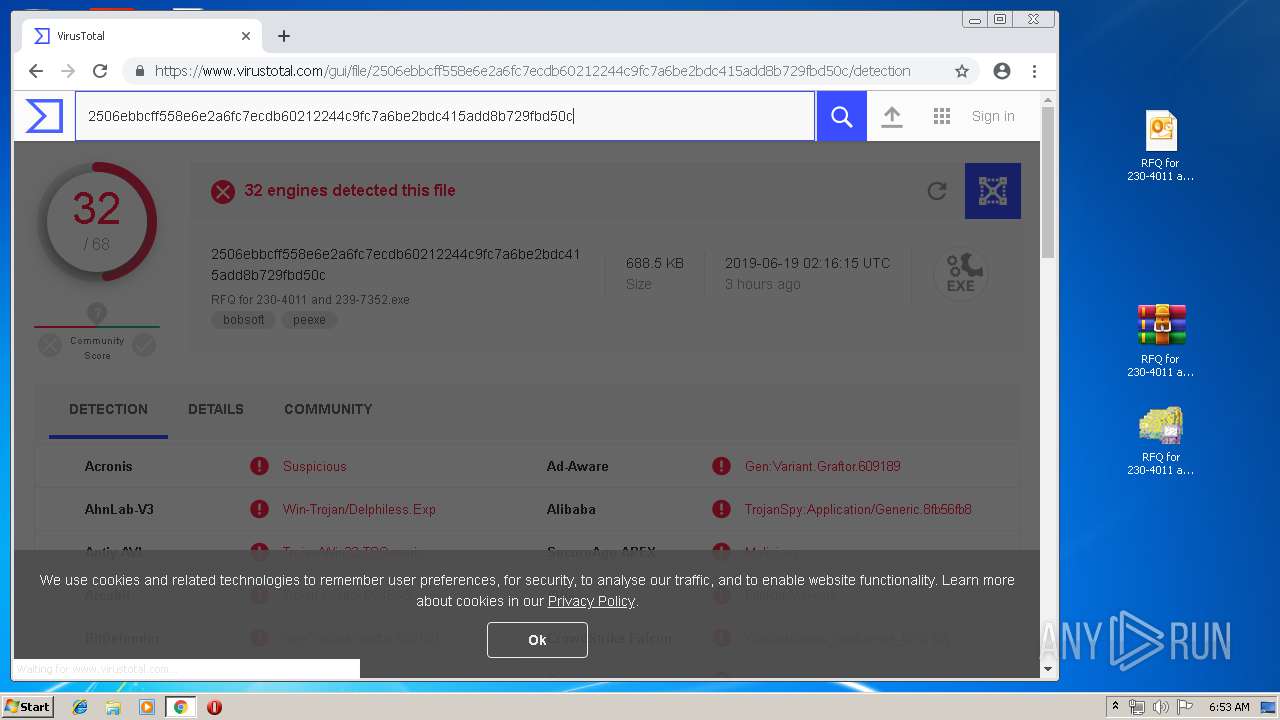
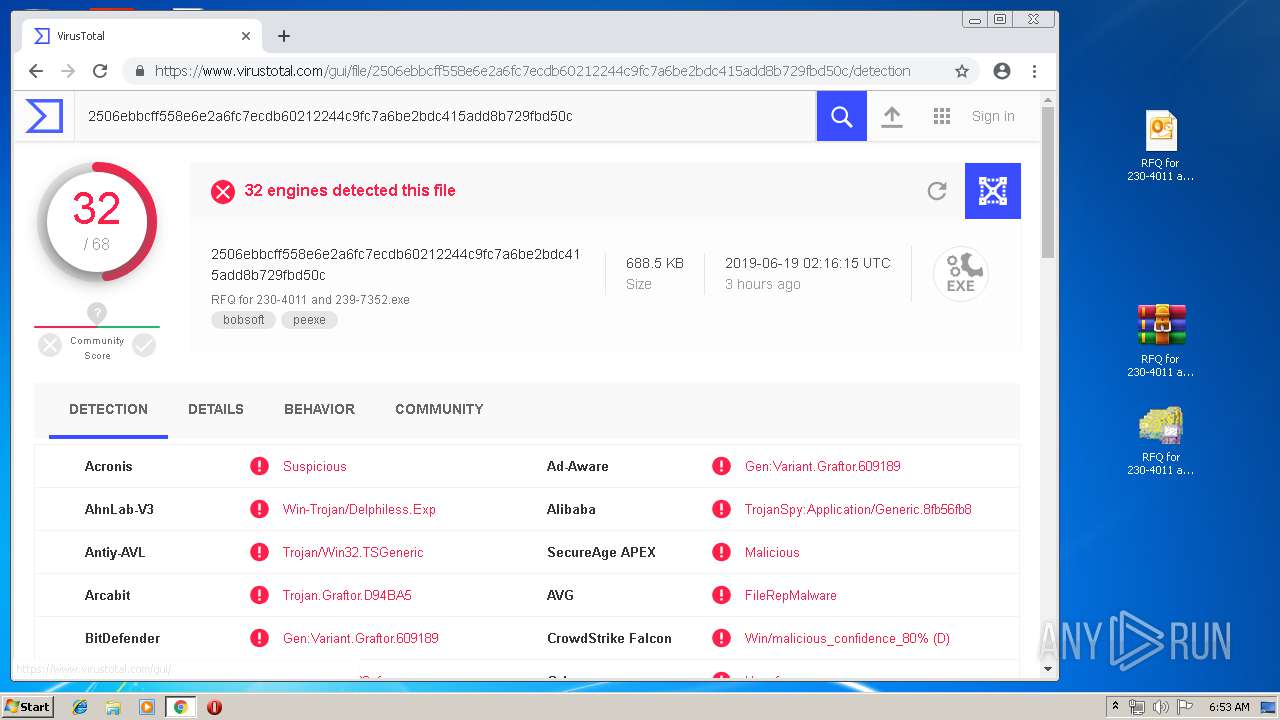
| File name: | RFQ for 230-4011 and 239-7352.7z |
| Full analysis: | https://app.any.run/tasks/509ed4a6-7d6a-4734-afea-1e756a3d4aad |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 19, 2019, 05:52:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | DD01DBDE4F92C020AEFC1BDF5236CC41 |
| SHA1: | 14F10DDF27E916CB9FE786F8F6D24E9A7A1406DE |
| SHA256: | DAE048F10756EFA1FAA3017F428539EDEDB3420BC6BD206B0D37D1DAA1423933 |
| SSDEEP: | 24576:qN78ROuhgrOqeoMYq1lbfUAI9rb83uwg1KuBAcn:0JrbAngAWH83uVTn |
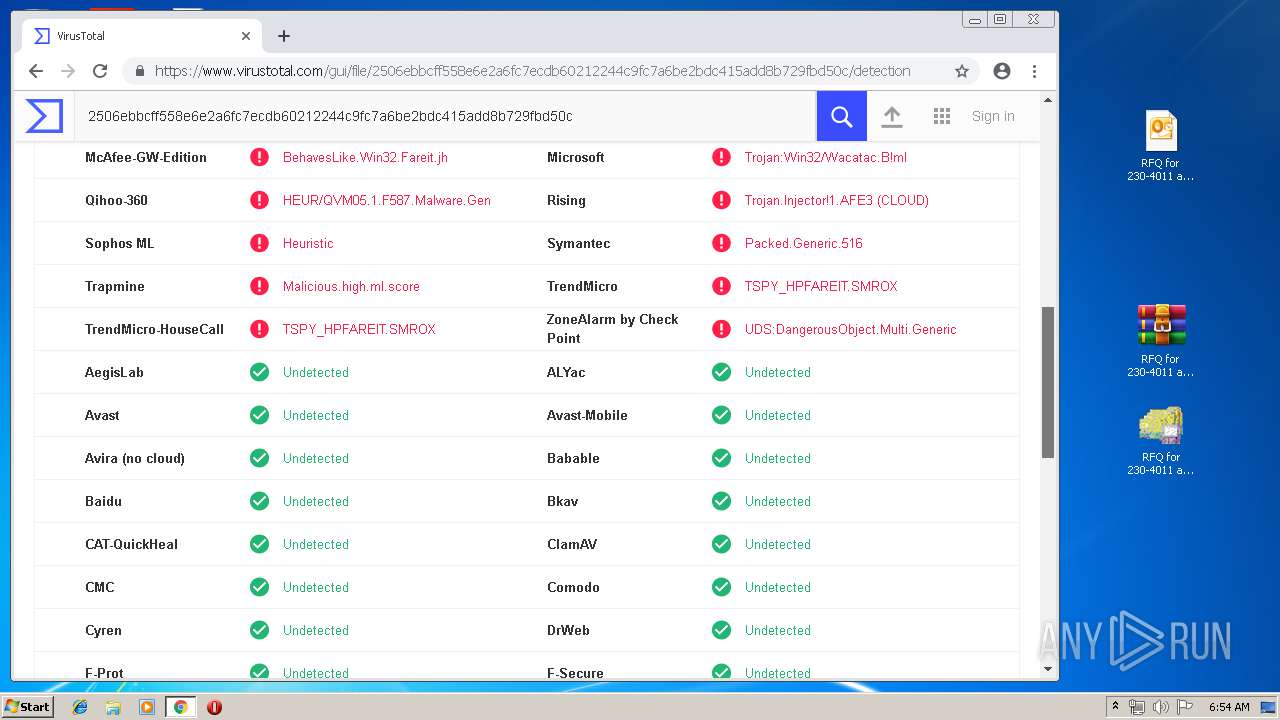
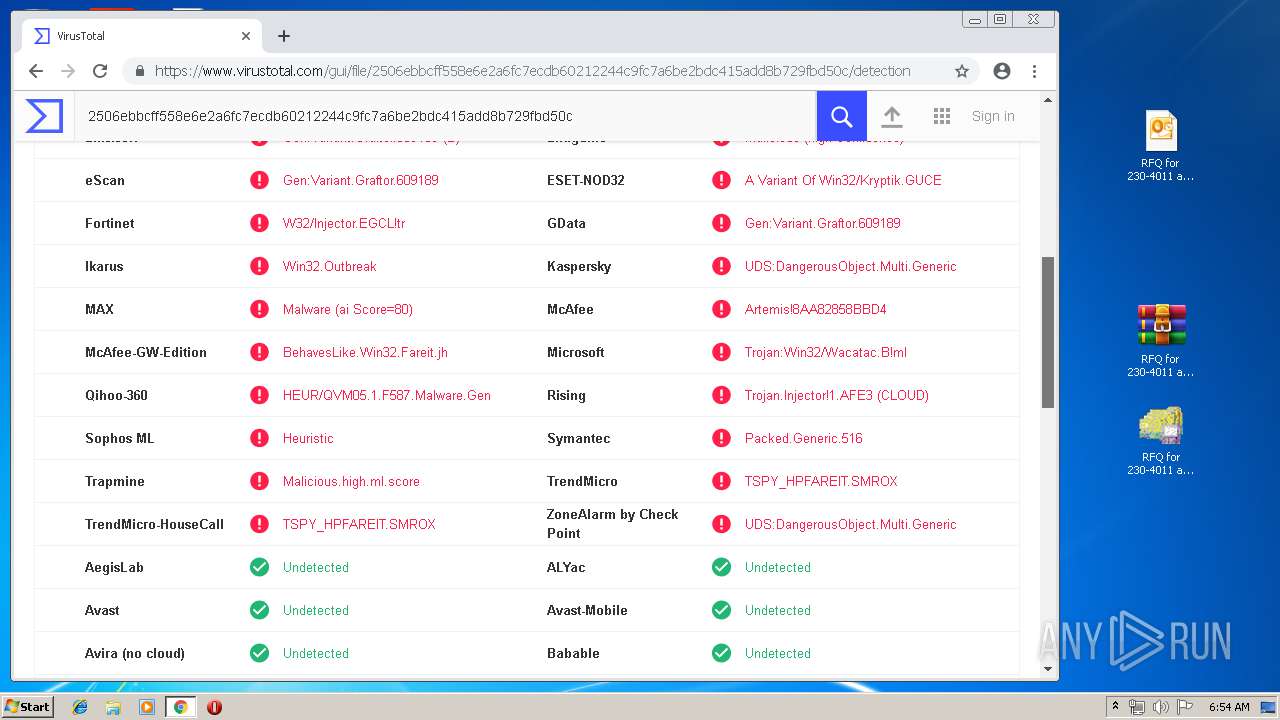
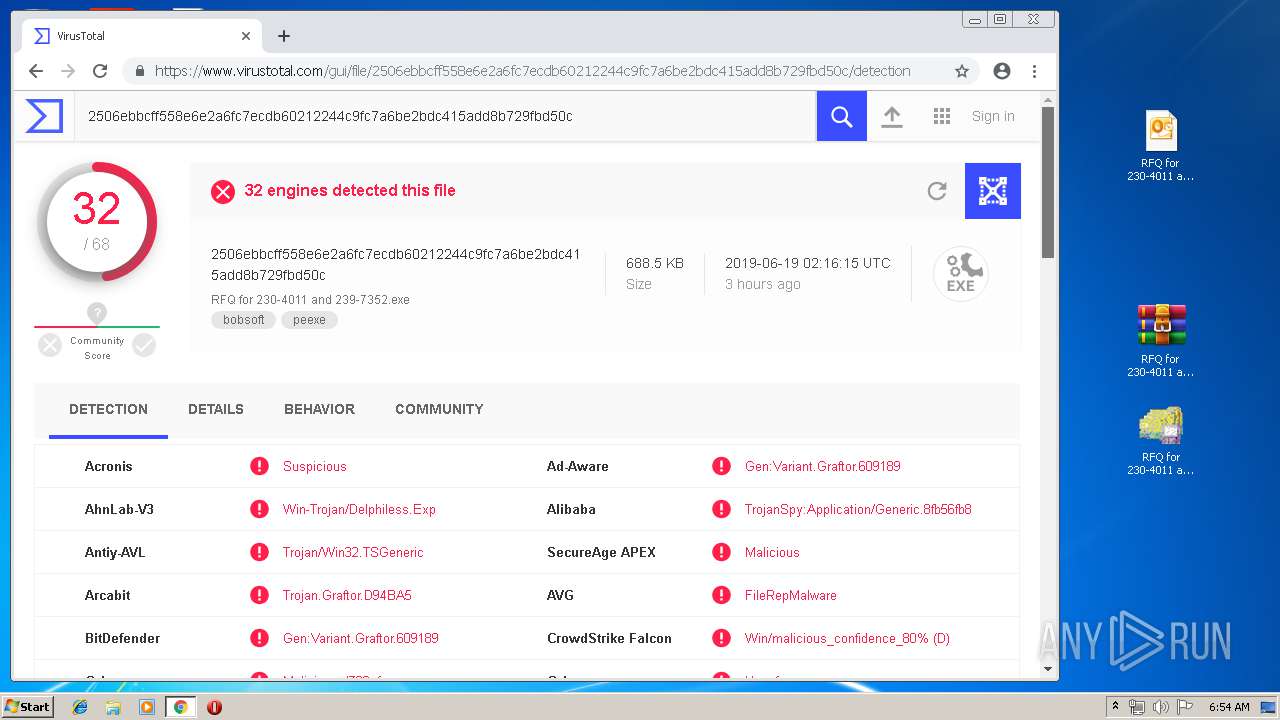
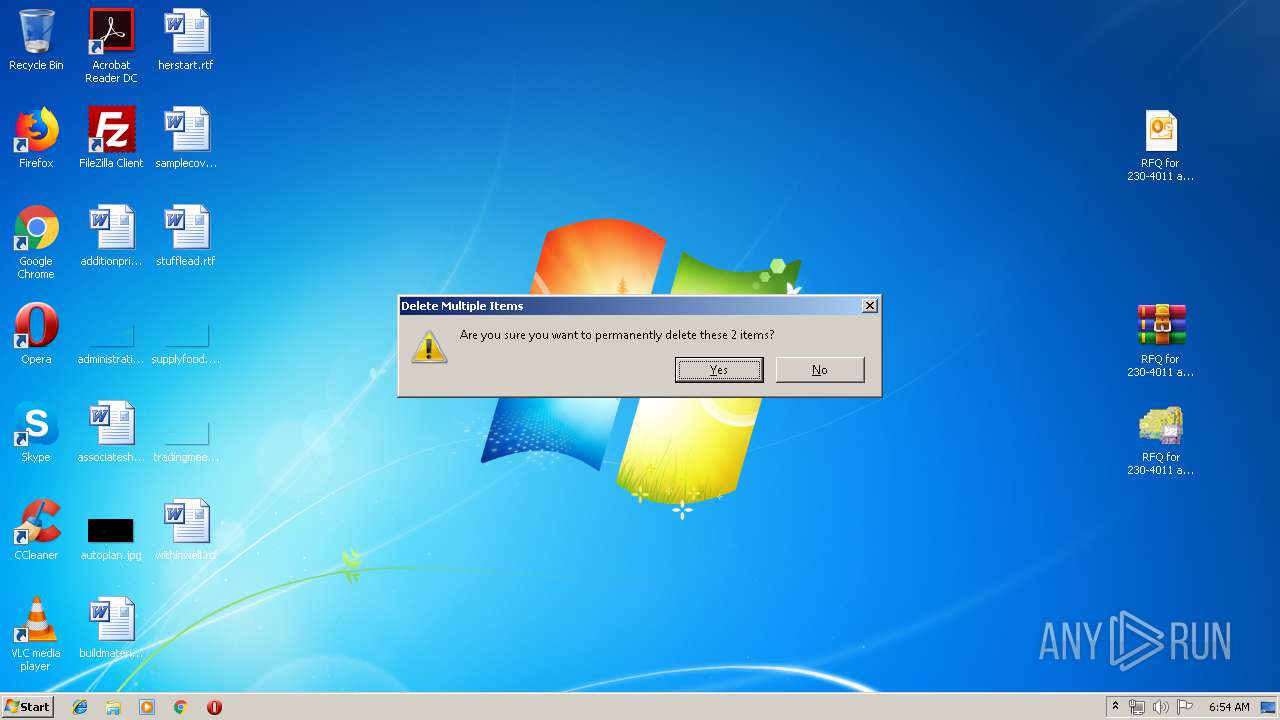
MALICIOUS
Application was dropped or rewritten from another process
- RFQ for 230-4011 and 239-7352.exe (PID: 596)
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
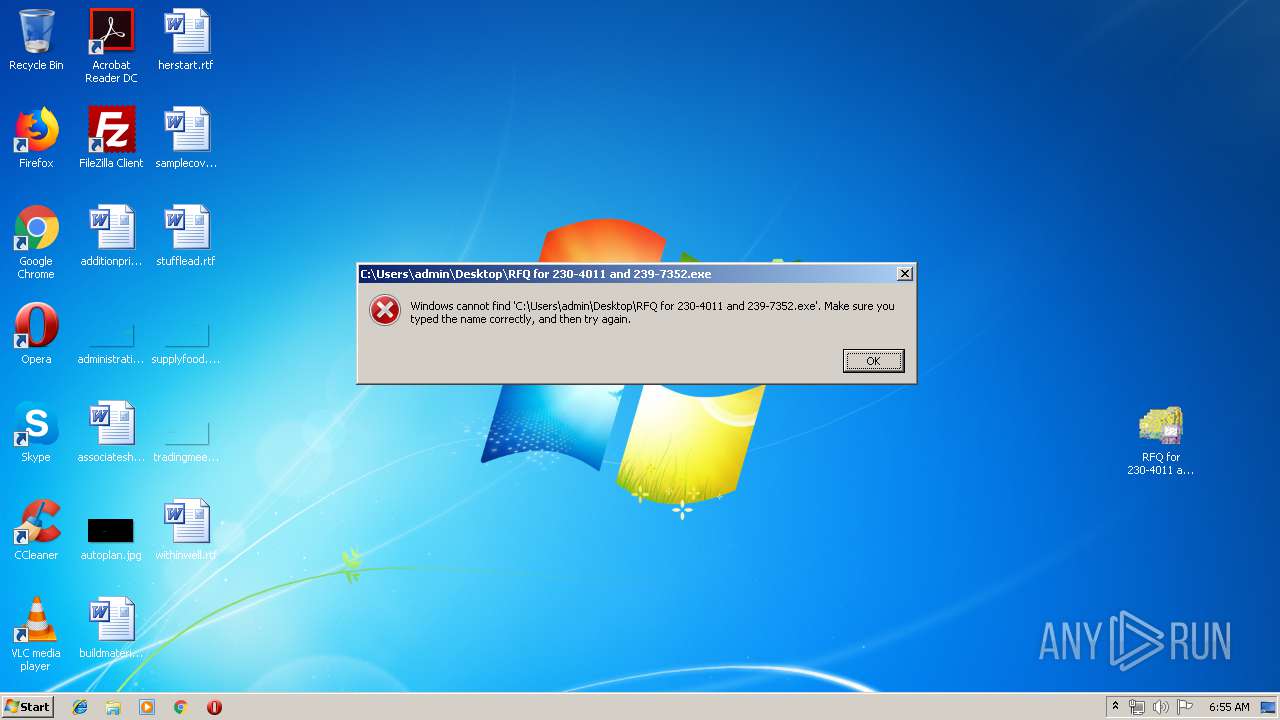
LokiBot was detected
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
LOKIBOT was detected
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
Actions looks like stealing of personal data
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
Connects to CnC server
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3660)
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3660)
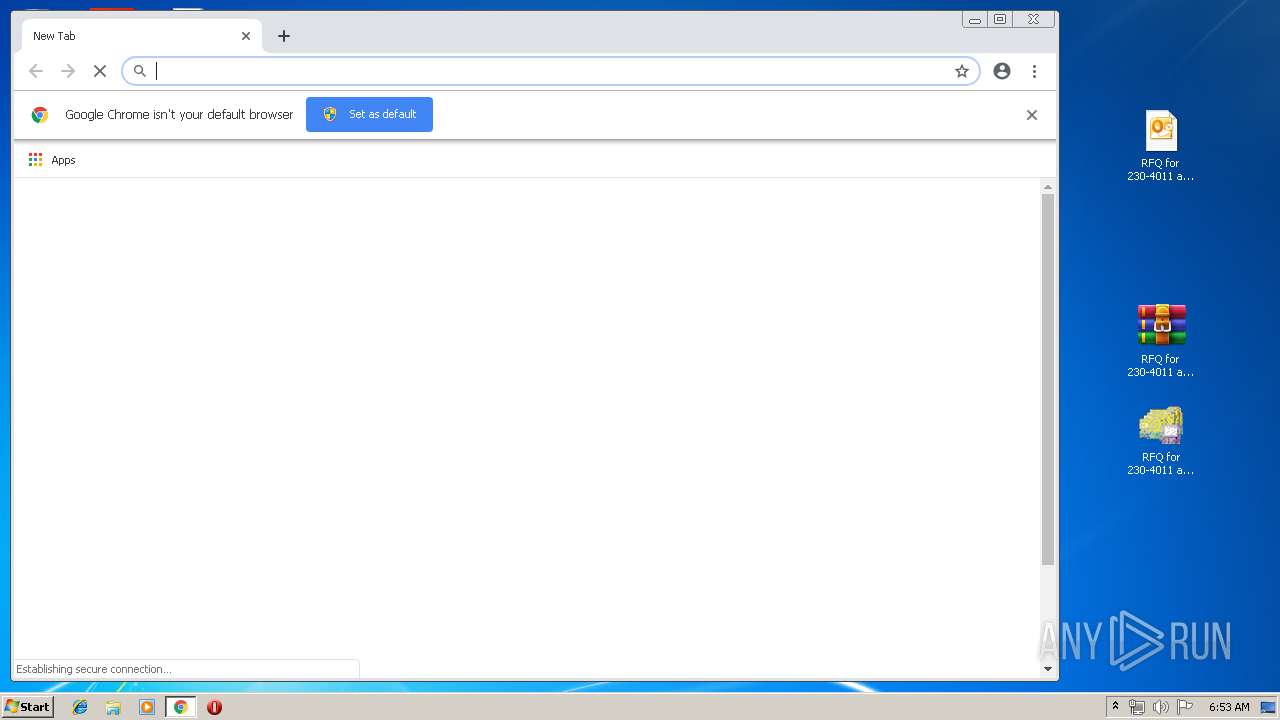
Modifies files in Chrome extension folder
- chrome.exe (PID: 2772)
Loads DLL from Mozilla Firefox
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
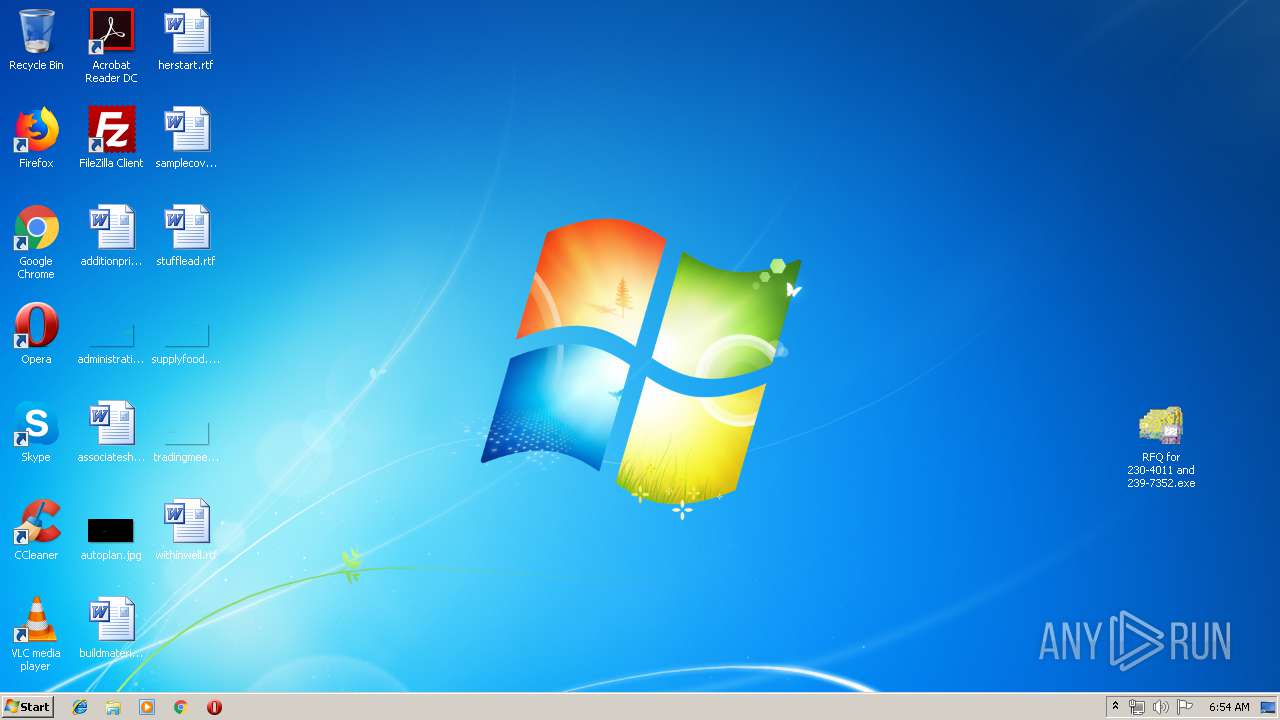
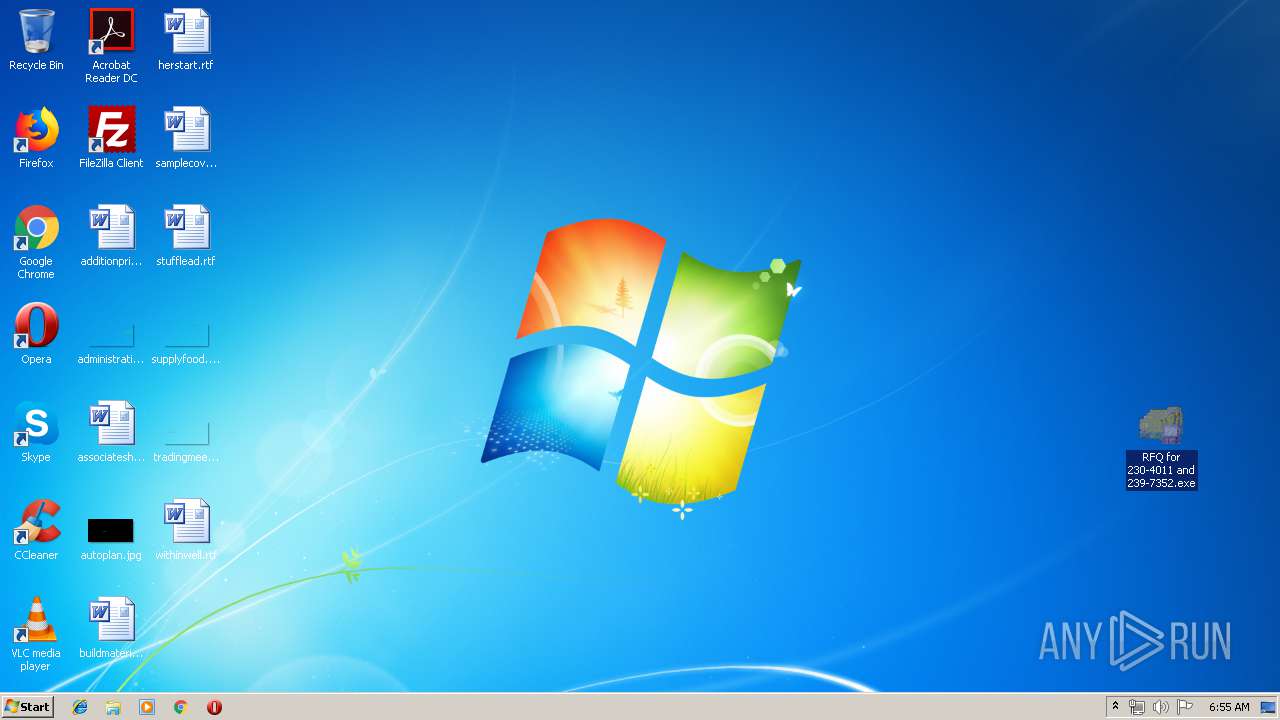
Application launched itself
- RFQ for 230-4011 and 239-7352.exe (PID: 596)
Executable content was dropped or overwritten
- RFQ for 230-4011 and 239-7352.exe (PID: 2896)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3948)
- chrome.exe (PID: 2772)
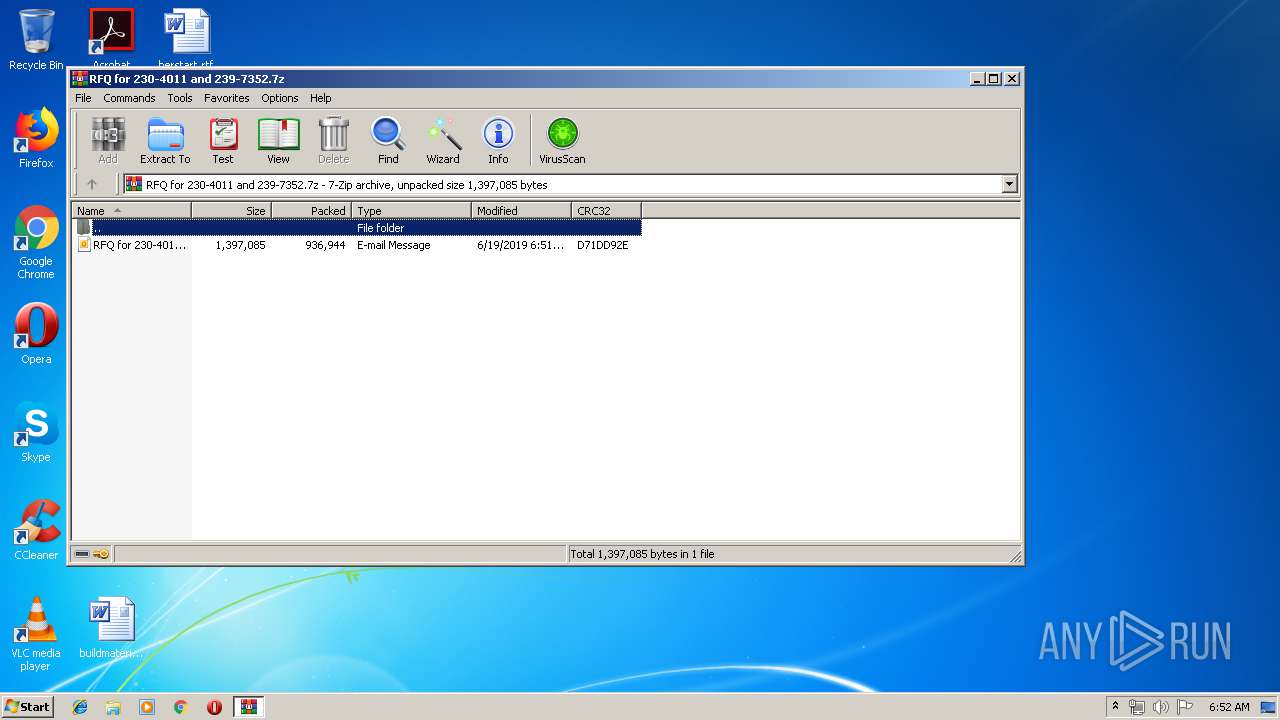
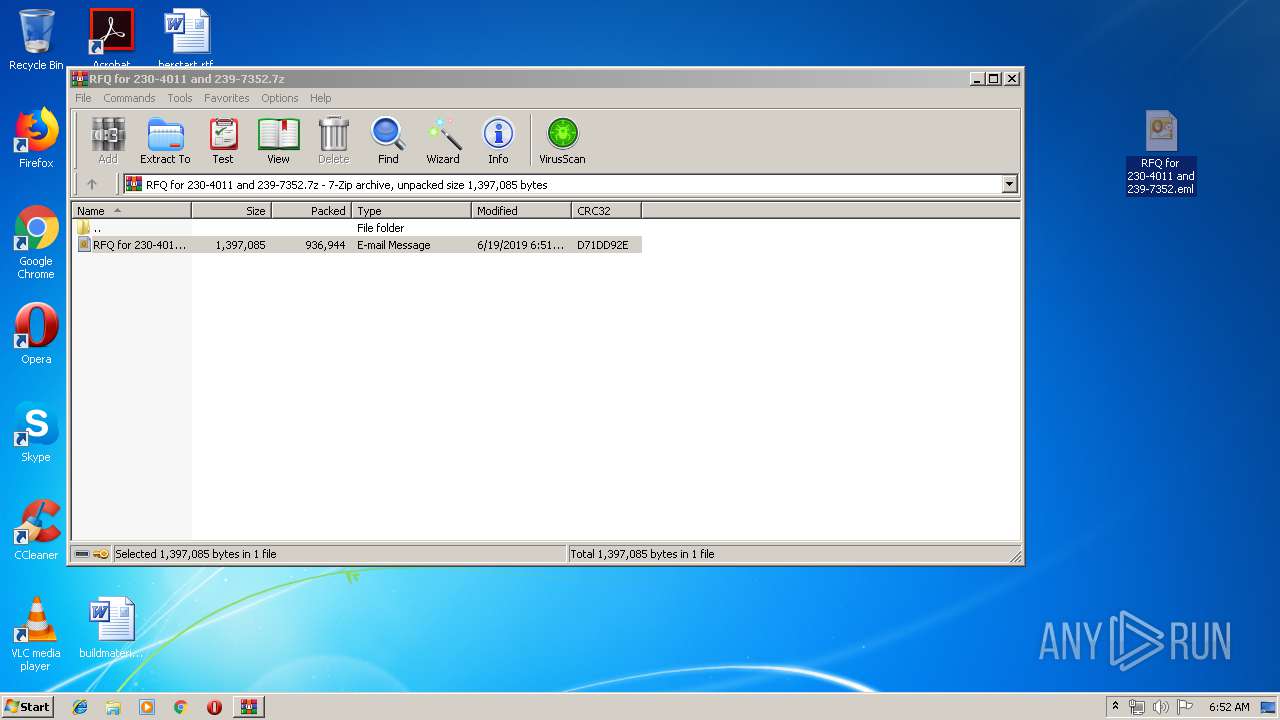
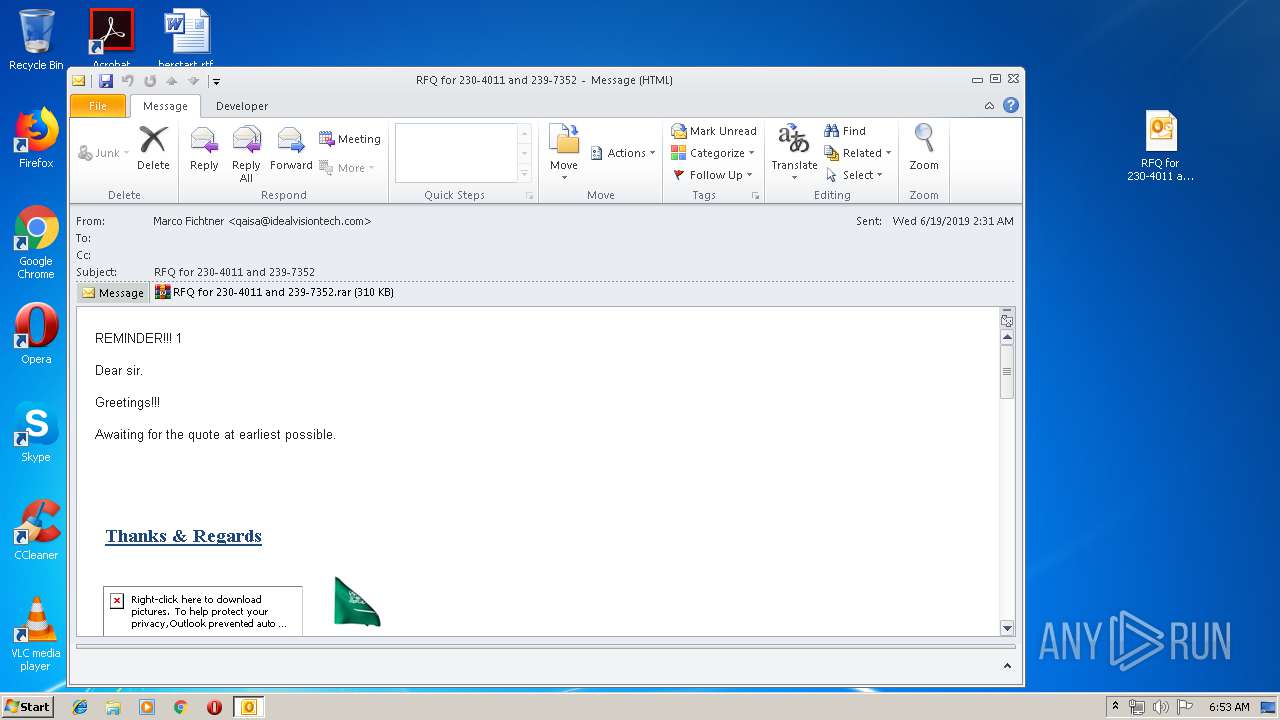
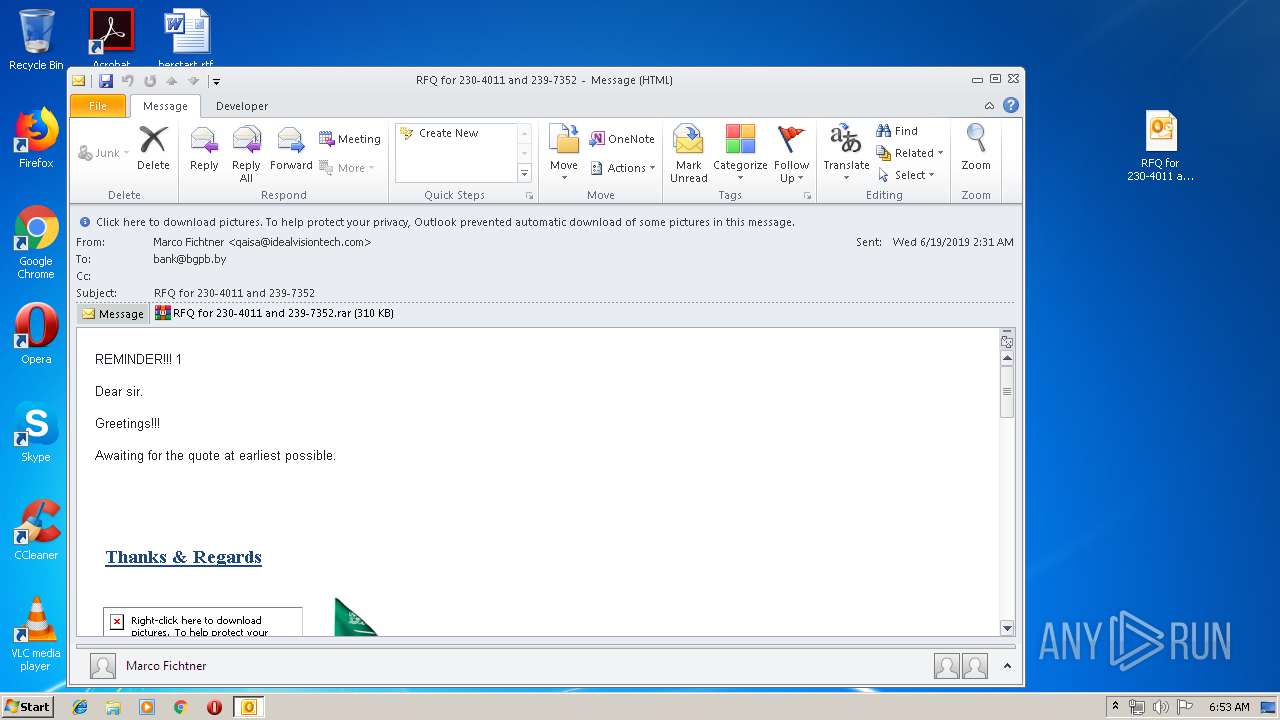
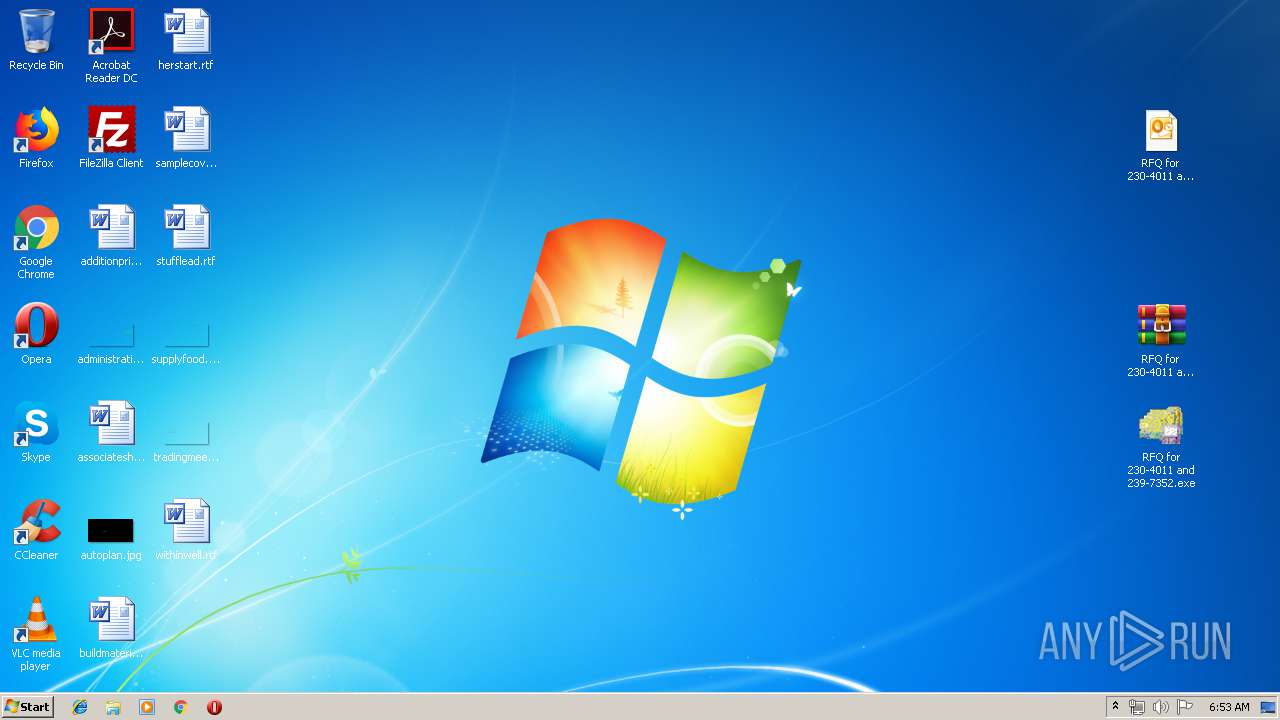
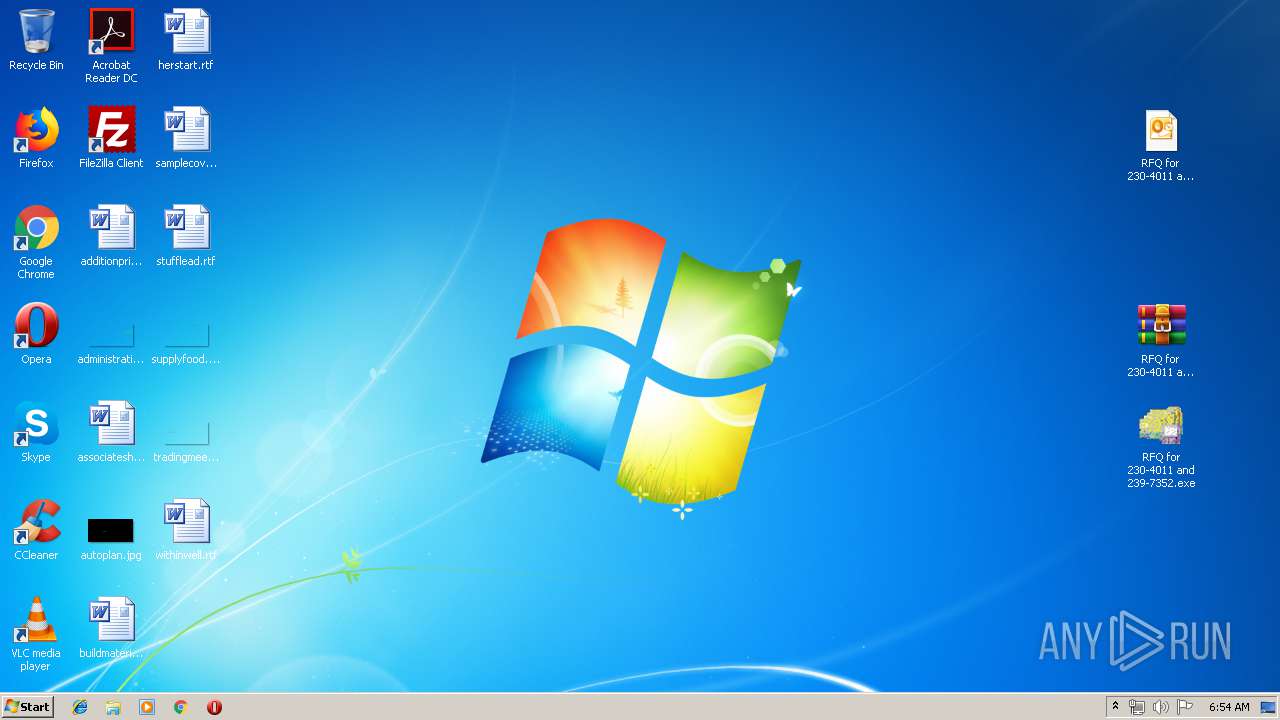
Manual execution by user
- WinRAR.exe (PID: 2072)
- chrome.exe (PID: 2772)
- OUTLOOK.EXE (PID: 3660)
- RFQ for 230-4011 and 239-7352.exe (PID: 596)
Reads settings of System Certificates
- chrome.exe (PID: 2772)
Application launched itself
- chrome.exe (PID: 2772)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
68
Monitored processes
31
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --service-pipe-token=10946701167002926408 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10946701167002926408 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 596 | "C:\Users\admin\Desktop\RFQ for 230-4011 and 239-7352.exe" | C:\Users\admin\Desktop\RFQ for 230-4011 and 239-7352.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18259004890884641502 --mojo-platform-channel-handle=4652 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7345278316368072876 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7345278316368072876 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14381717721372863837 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14381717721372863837 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6679610604442357772 --mojo-platform-channel-handle=4736 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16758371063028237887 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16758371063028237887 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
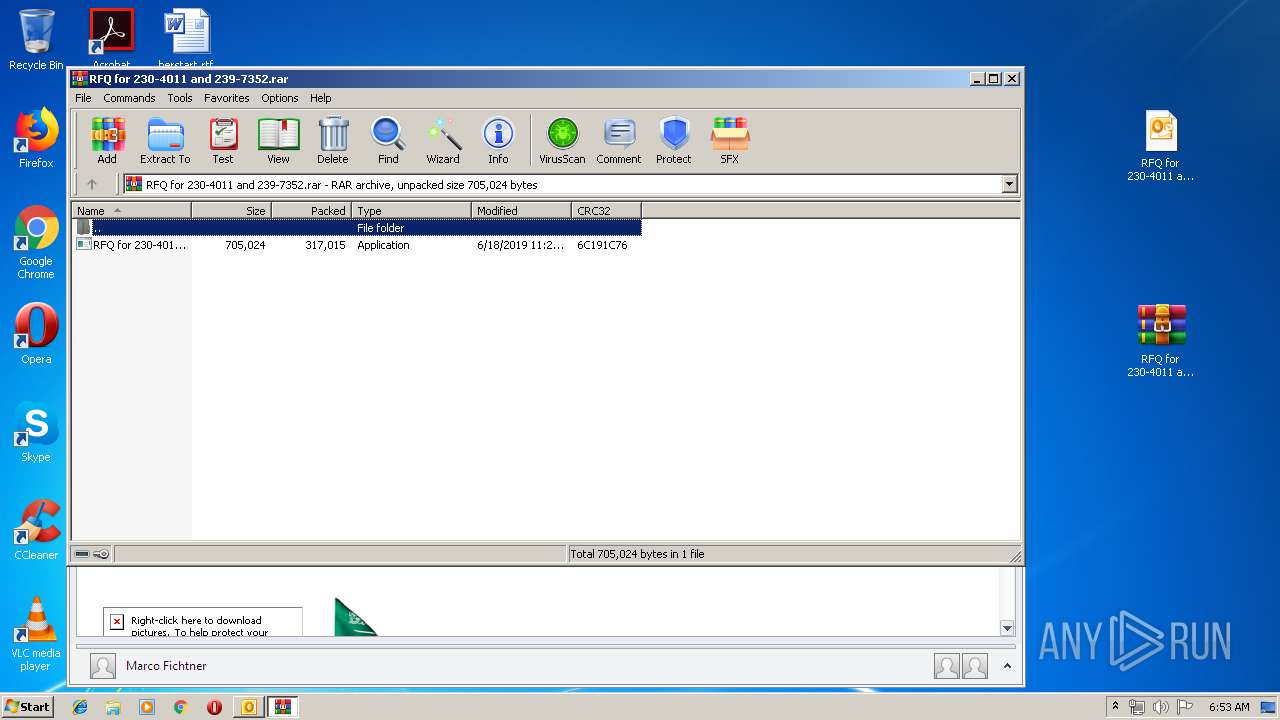
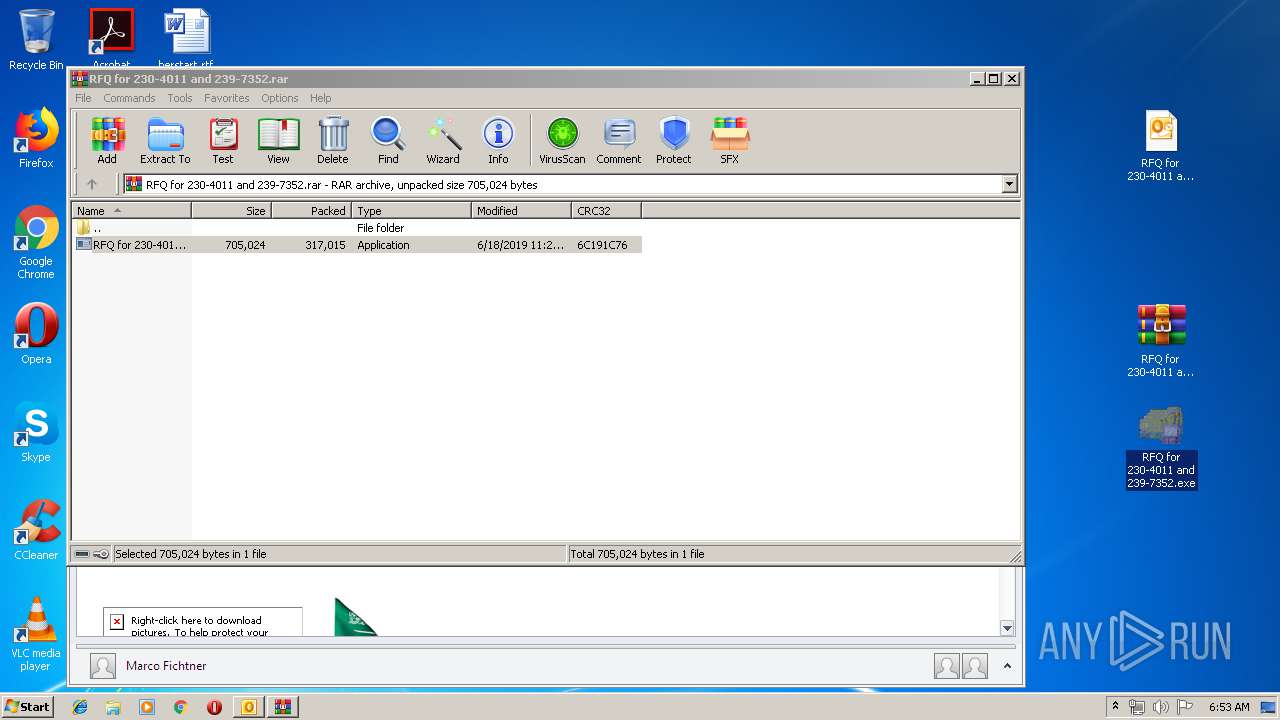
| 2072 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\RFQ for 230-4011 and 239-7352.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15825625509947678373 --mojo-platform-channel-handle=2620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2316465615877973793 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 730
Read events
2 173
Write events
532
Delete events
25
Modification events
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RFQ for 230-4011 and 239-7352.7z | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
256
Text files
198
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR805E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp82E0.tmp | — | |
MD5:— | SHA256:— | |||
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp82F1.tmp | — | |
MD5:— | SHA256:— | |||
| 2072 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2072.11007\RFQ for 230-4011 and 239-7352.exe | — | |
MD5:— | SHA256:— | |||
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{708204CC-D21B-4507-9794-0FC19089CA9C}.tmp | — | |
MD5:— | SHA256:— | |||
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF0B0BCA205B73F8D5.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF64404D0CC12BCD69.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{DF428005-1571-400F-A1D7-491F9541BDCC}.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
25
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3660 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2772 | chrome.exe | GET | 200 | 185.48.9.77:80 | http://r2---sn-x2pm-3ufd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=31.204.154.118&mm=28&mn=sn-x2pm-3ufd&ms=nvh&mt=1560922509&mv=u&pl=23&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
2772 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 507 b | whitelisted |
2896 | RFQ for 230-4011 and 239-7352.exe | POST | 404 | 37.120.146.118:80 | http://freecaps.top/81167/logs/fre.php | RO | text | 15 b | malicious |
2896 | RFQ for 230-4011 and 239-7352.exe | POST | 404 | 37.120.146.118:80 | http://freecaps.top/81167/logs/fre.php | RO | text | 15 b | malicious |
2896 | RFQ for 230-4011 and 239-7352.exe | POST | 404 | 37.120.146.118:80 | http://freecaps.top/81167/logs/fre.php | RO | binary | 23 b | malicious |
2772 | chrome.exe | GET | 302 | 74.125.34.46:80 | http://www.virustotal.com/nl/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2772 | chrome.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3660 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2772 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2772 | chrome.exe | 172.217.23.163:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2896 | RFQ for 230-4011 and 239-7352.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2896 | RFQ for 230-4011 and 239-7352.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3 ETPRO signatures available at the full report