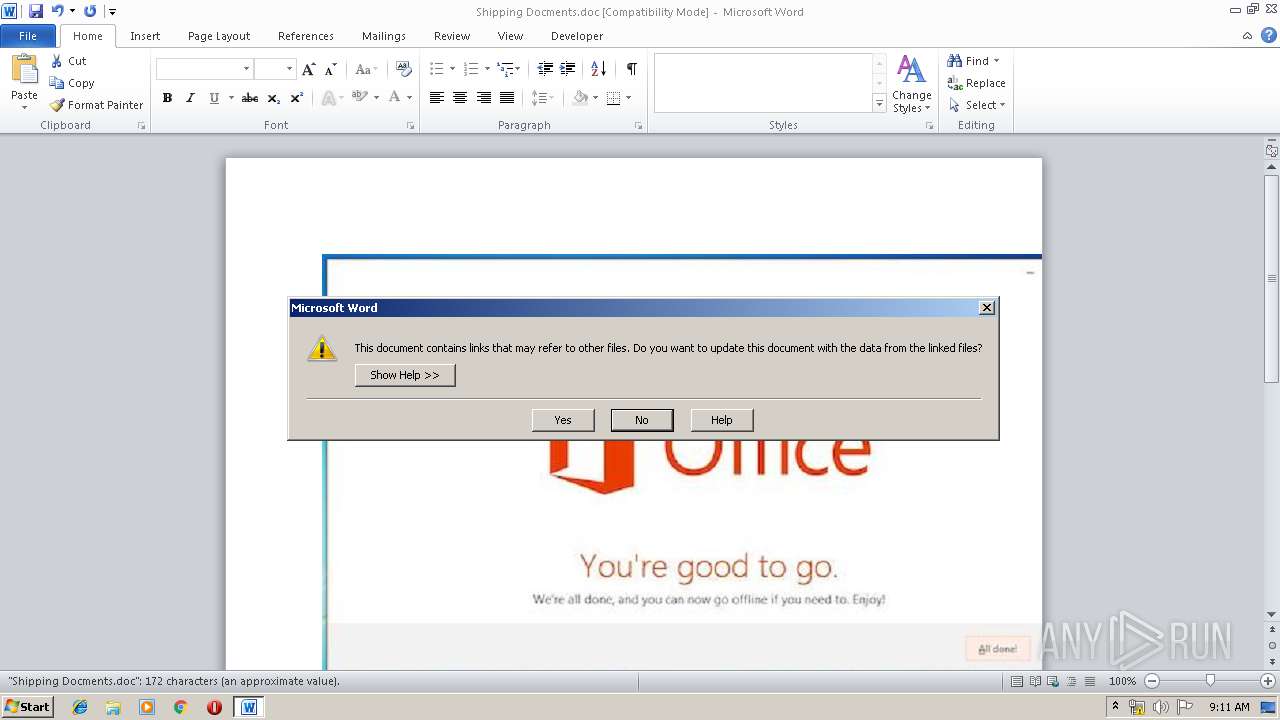
| File name: | Shipping Docments.doc |
| Full analysis: | https://app.any.run/tasks/44f08870-c0e0-45ae-a5e8-f8543e48e409 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 25, 2019, 08:10:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 9F59E5FEC0B5D5E2B98ABB2DA16EB613 |
| SHA1: | BDCF7E90BB7EC842DC4F90E6CECE5A81CC969D41 |
| SHA256: | DAD5D8DE672D29E8B5332B346E3346285FD4A6F559C125AC558038B06EBC729A |
| SSDEEP: | 24576:pd6qlMEjK5h02g0MroF1bQFGCAQf5smfohbdz1Wfbkcqo1/Ti9AuTB6AM3dB0f9f:m |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2036)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2036)
Runs app for hidden code execution
- cmd.exe (PID: 1564)
- cmd.exe (PID: 3740)
FORMBOOK was detected
- explorer.exe (PID: 116)
Application was dropped or rewritten from another process
- saver.scr (PID: 1432)
- saver.scr (PID: 3200)
- saver.scr (PID: 2676)
Formbook was detected
- Firefox.exe (PID: 1712)
- colorcpl.exe (PID: 344)
Actions looks like stealing of personal data
- colorcpl.exe (PID: 344)
Connects to CnC server
- explorer.exe (PID: 116)
Changes the autorun value in the registry
- colorcpl.exe (PID: 344)
Stealing of credential data
- colorcpl.exe (PID: 344)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3740)
- cmd.exe (PID: 1344)
- cmd.exe (PID: 1564)
- colorcpl.exe (PID: 344)
- cmd.exe (PID: 300)
Application launched itself
- cmd.exe (PID: 1564)
- cmd.exe (PID: 300)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3688)
- cmd.exe (PID: 300)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 388)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 3620)
Executes scripts
- cmd.exe (PID: 300)
Executable content was dropped or overwritten
- cscript.exe (PID: 2592)
Starts application with an unusual extension
- saver.scr (PID: 3200)
- cmd.exe (PID: 300)
- saver.scr (PID: 1432)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 300)
Creates files in the user directory
- colorcpl.exe (PID: 344)
Loads DLL from Mozilla Firefox
- colorcpl.exe (PID: 344)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2036)
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Creates files in the user directory
- WINWORD.EXE (PID: 2036)
- Firefox.exe (PID: 1712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
78
Monitored processes
45
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 300 | C:\Windows\system32\cmd.exe /K mt6nzqofd.CMD | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 344 | "C:\Windows\System32\colorcpl.exe" | C:\Windows\System32\colorcpl.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | C:\Windows\system32\cmd.exe /c REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\15.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 596 | REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\15.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | TIMEOUT /T 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | TIMEOUT /T 1 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\11.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | CmD | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Temp\saVER.scR" | C:\Users\admin\AppData\Local\Temp\saver.scr | — | cmd.exe | |||||||||||
User: admin Company: vmwAre Integrity Level: MEDIUM Description: cUrofencEen Exit code: 0 Version: 9.04.0005 Modules
| |||||||||||||||
Total events
1 117
Read events
1 077
Write events
37
Delete events
3
Modification events
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | wr4 |
Value: 77723400F4070000010000000000000000000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318649886 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650001 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F407000060DAD46C3EFBD40100000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | zt4 |
Value: 7A743400F407000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | zt4 |
Value: 7A743400F407000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
76
Text files
13
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6657.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mt6nzqofd.cmd | text | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2592 | cscript.exe | C:\Users\admin\AppData\Local\Temp\saver.scr | executable | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ipping Docments.doc | pgc | |
MD5:— | SHA256:— | |||
| 300 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_.vbs | text | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\kulebiaka.ZiP | compressed | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{B747B07D-ED20-49FC-9D8F-7A110389F885}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2592 | cscript.exe | C:\Users\admin\AppData\Local\Temp\gondi.doc | text | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{8958EB77-5789-4E51-AC00-001F8B24A7C2}.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | explorer.exe | GET | — | 184.168.221.44:80 | http://www.routecars.com/st/?OrpDKZ=4GU6NhSDsPSxkLrGHeja8EkadlosHUETC2YyrLefukXERaeAJQka7sK0QKoW4DInPNaXEg==&CXG=chUxZlTP2 | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | explorer.exe | 184.168.221.44:80 | www.routecars.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.routecars.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1 ETPRO signatures available at the full report