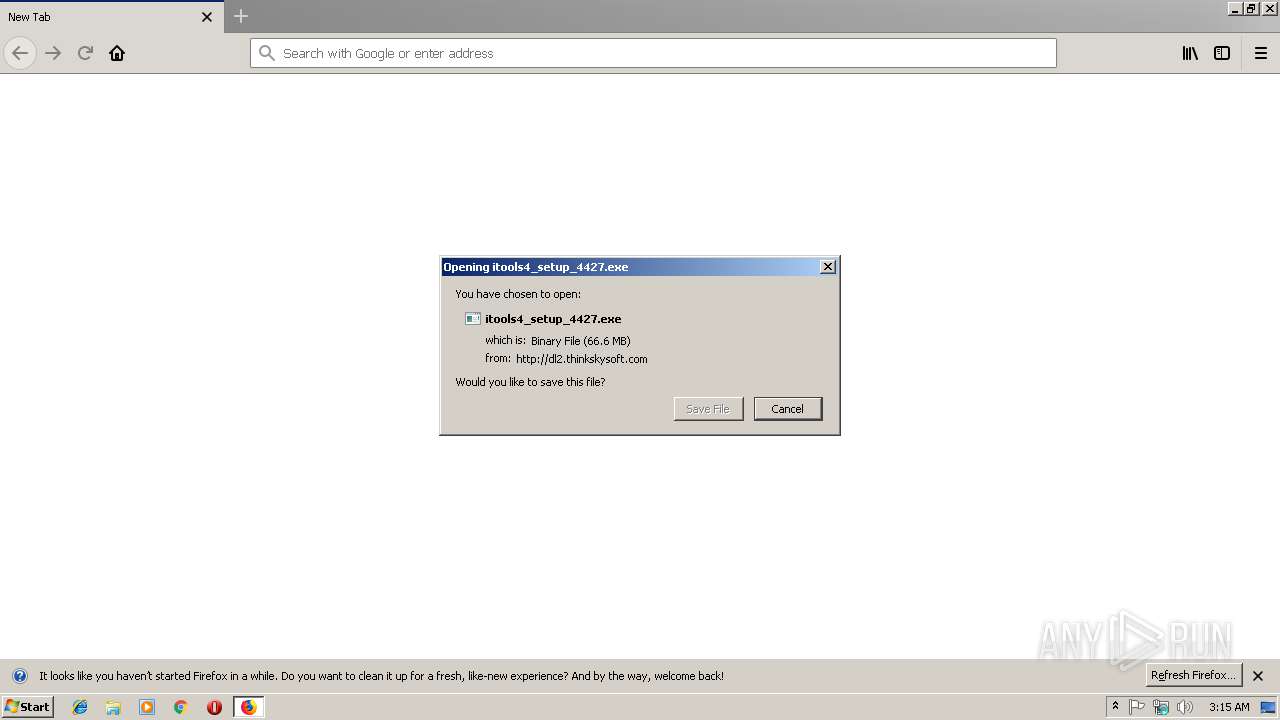
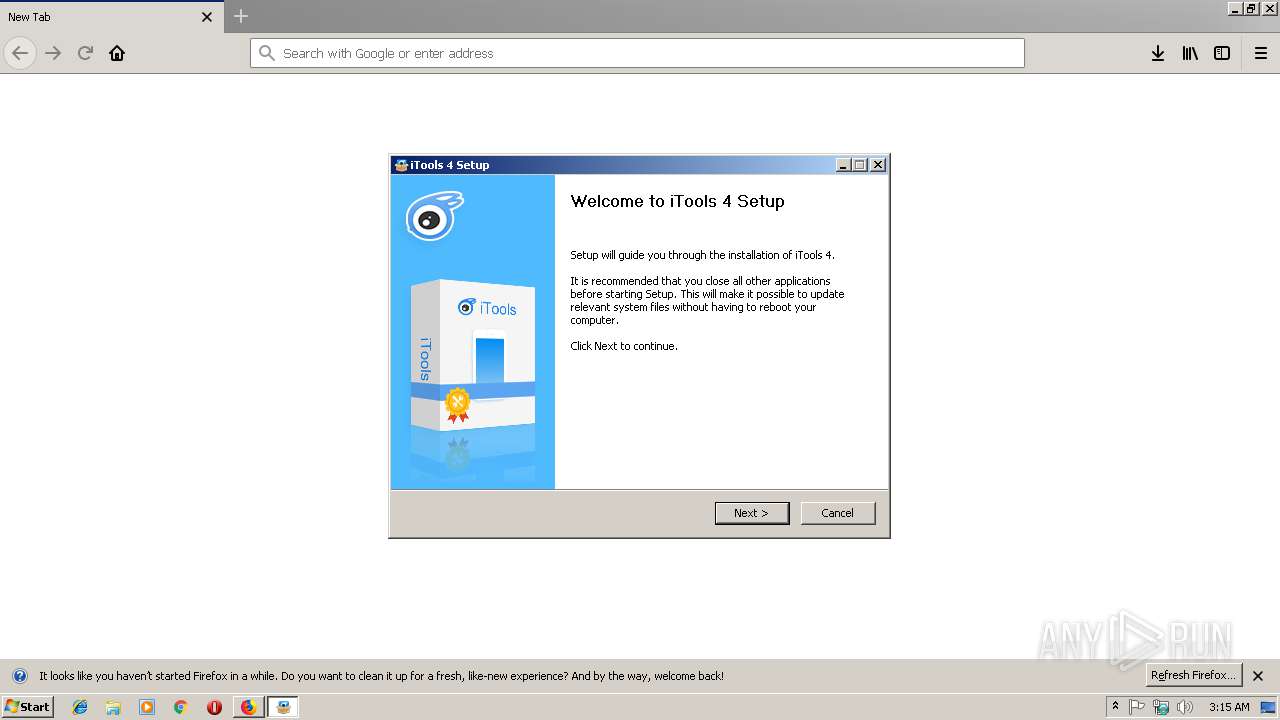
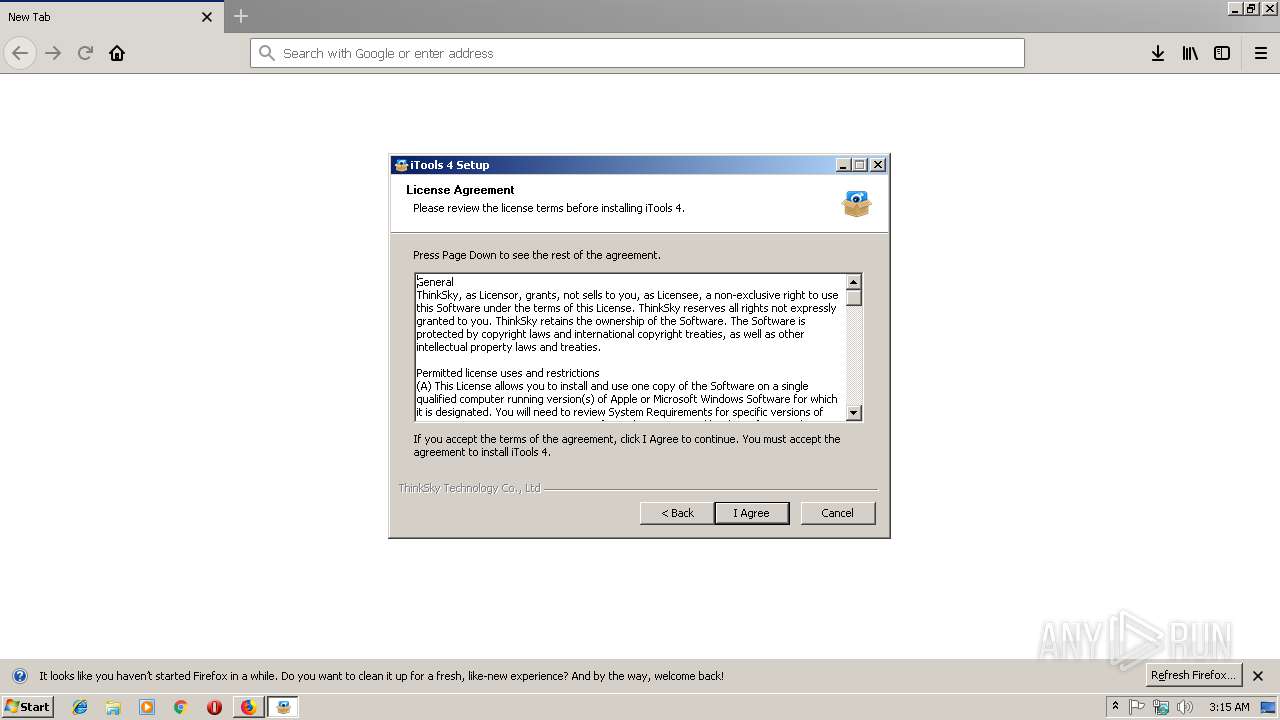
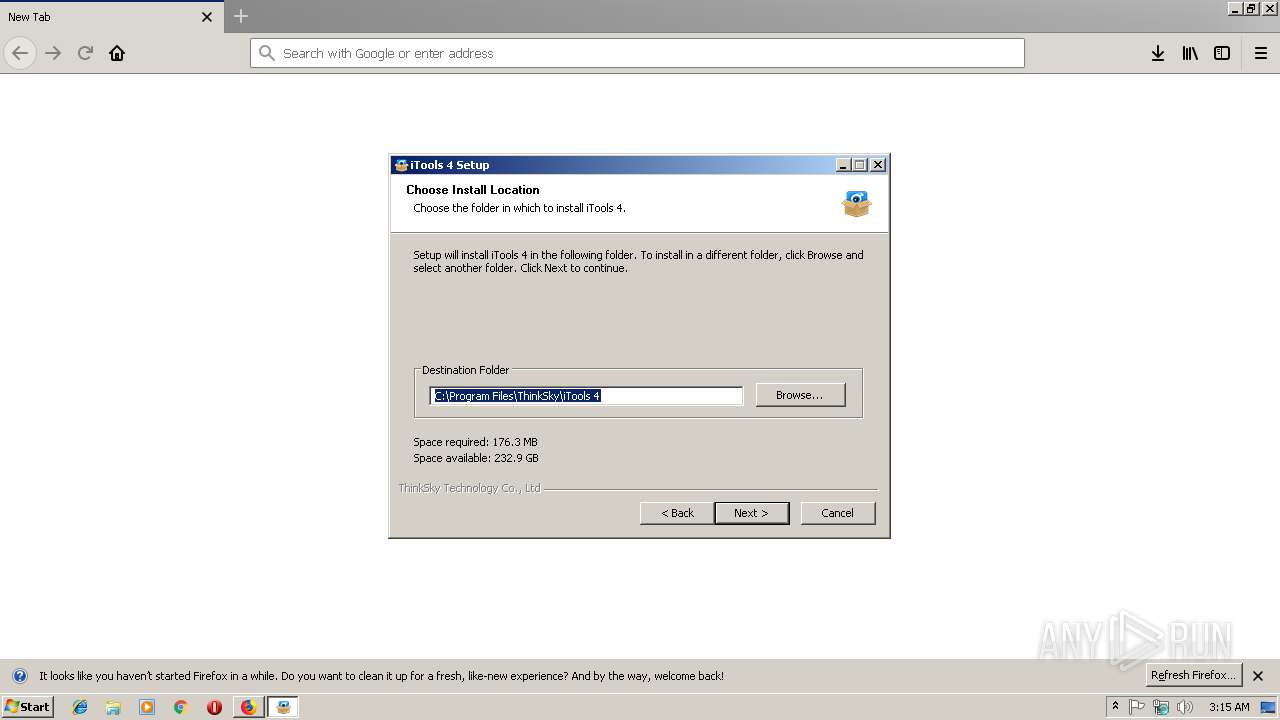
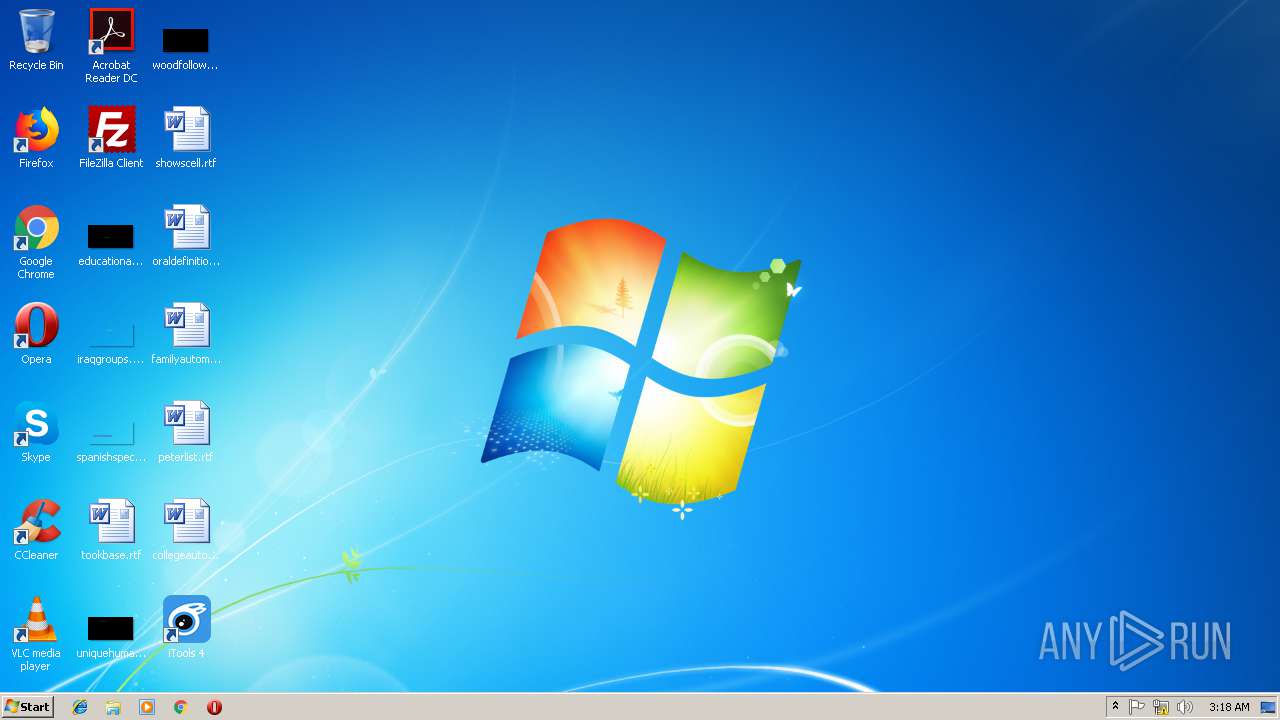
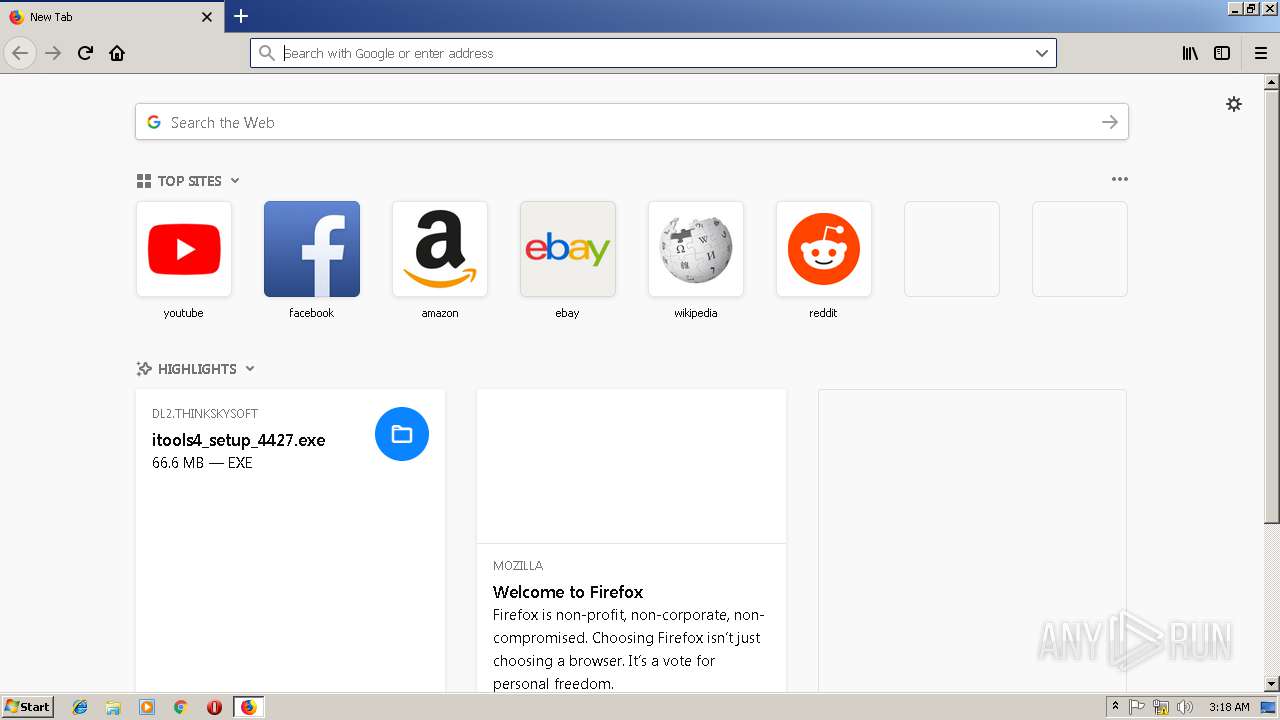
| URL: | http://dl2.thinkskysoft.com/itools/itools4_setup_4427.exe |
| Full analysis: | https://app.any.run/tasks/323000b8-c40b-4c34-b5f4-43a787eb224e |
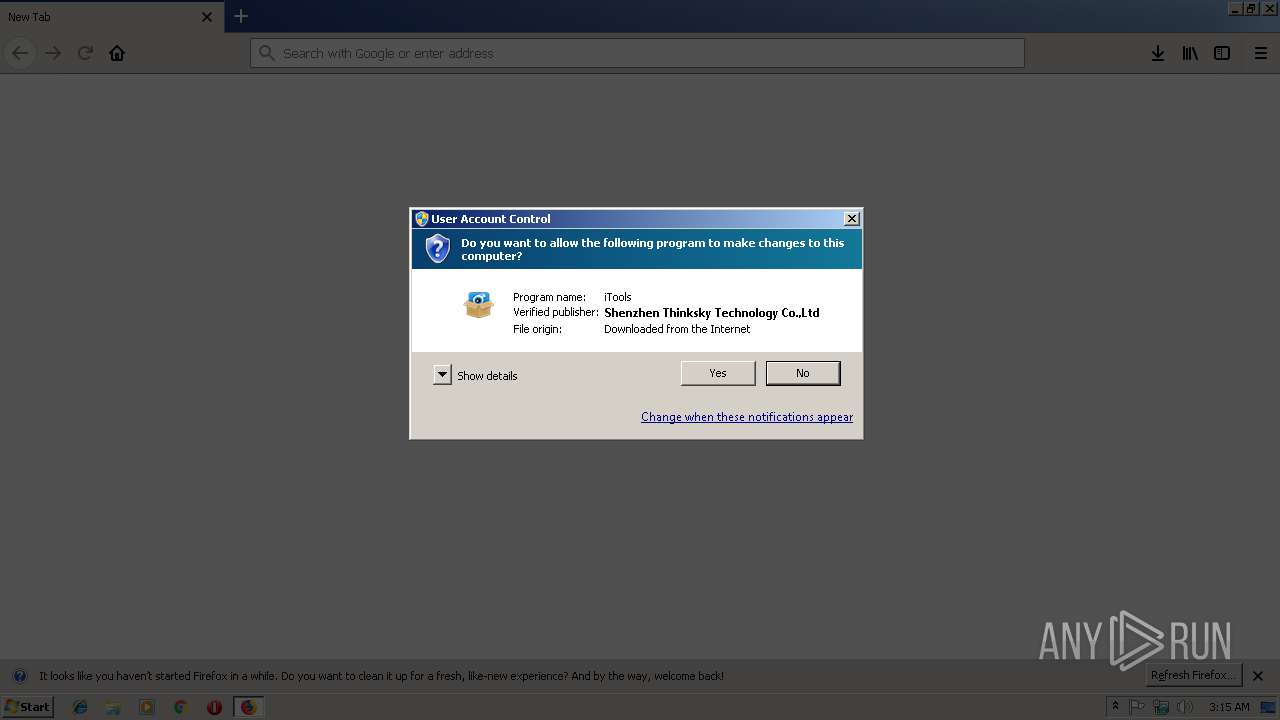
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | December 13, 2018, 03:14:49 |
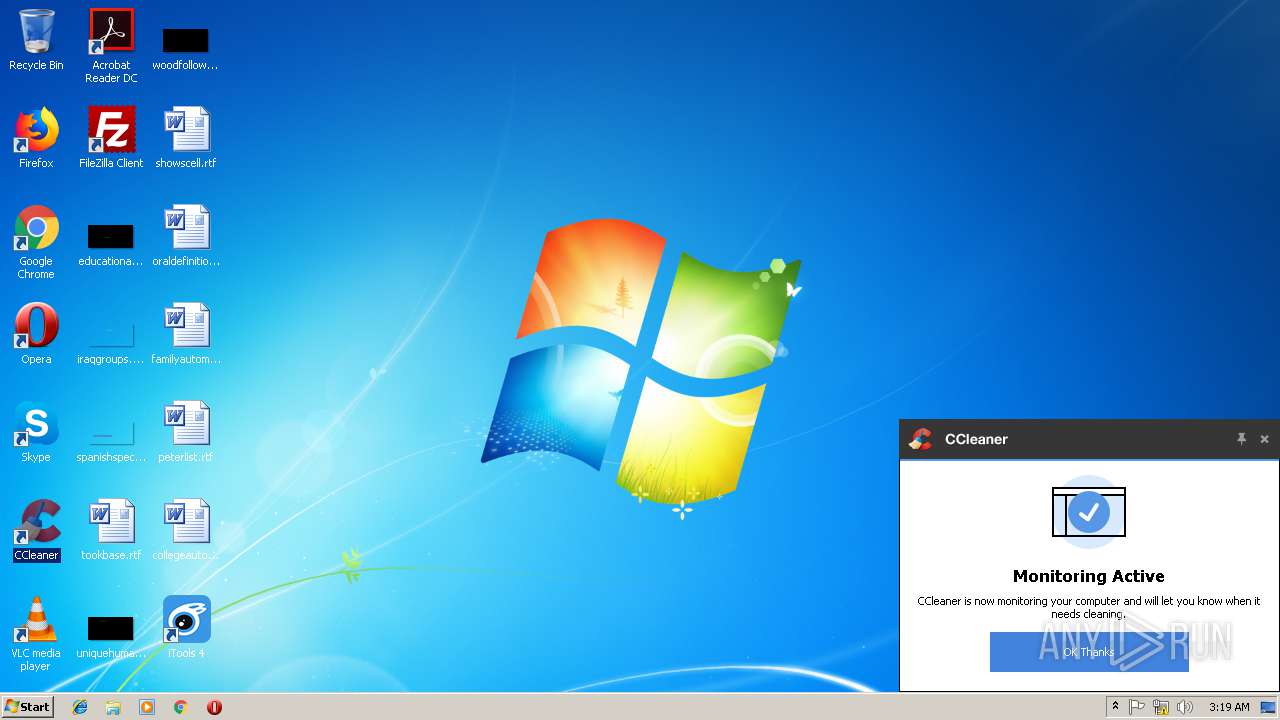
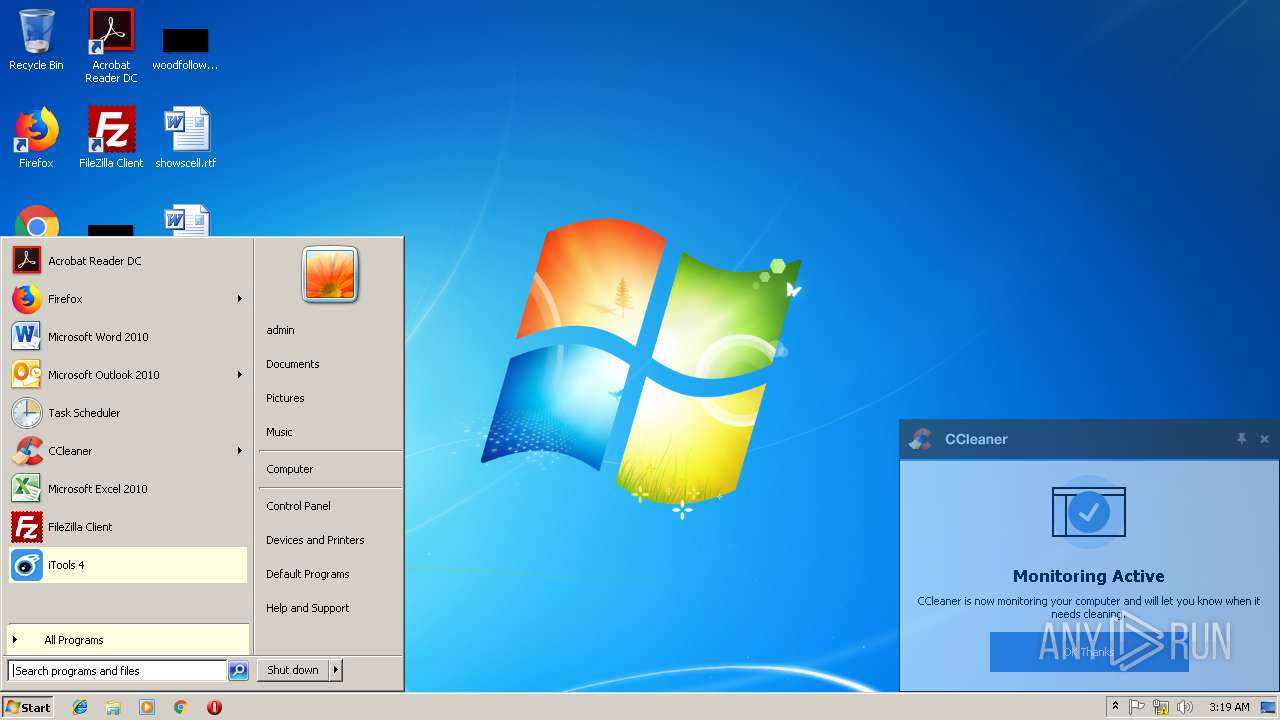
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 43DCF040D134E9F86E03C20E31F4B430 |
| SHA1: | C1717034DCB01D1283CF0CEC94C424708E1579B9 |
| SHA256: | DA9897863F7C2D7C7DF53C56BD03BDB6F8EB06AF15E3F08509F75086937E21DC |
| SSDEEP: | 3:N1KaJ1NKOWOYRtqNjyfRU0Cn:CaJ1UOWVD425U0Cn |
MALICIOUS
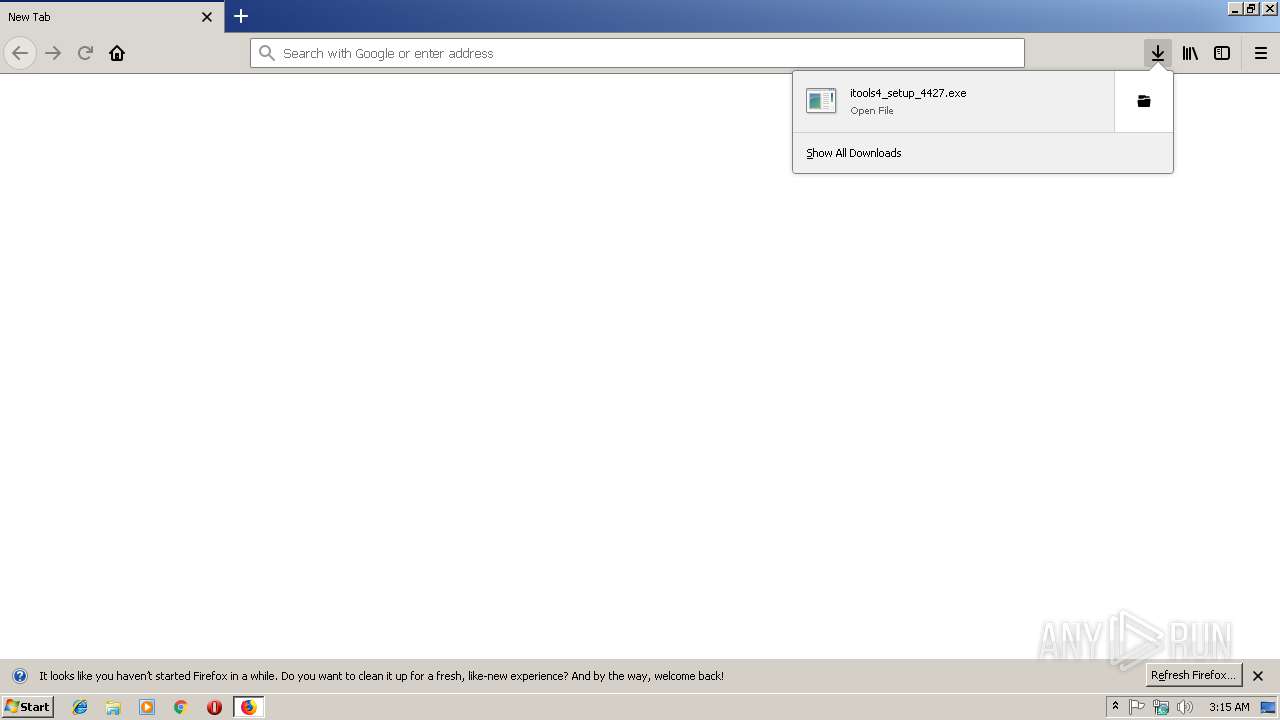
Downloads executable files from the Internet
- firefox.exe (PID: 3548)
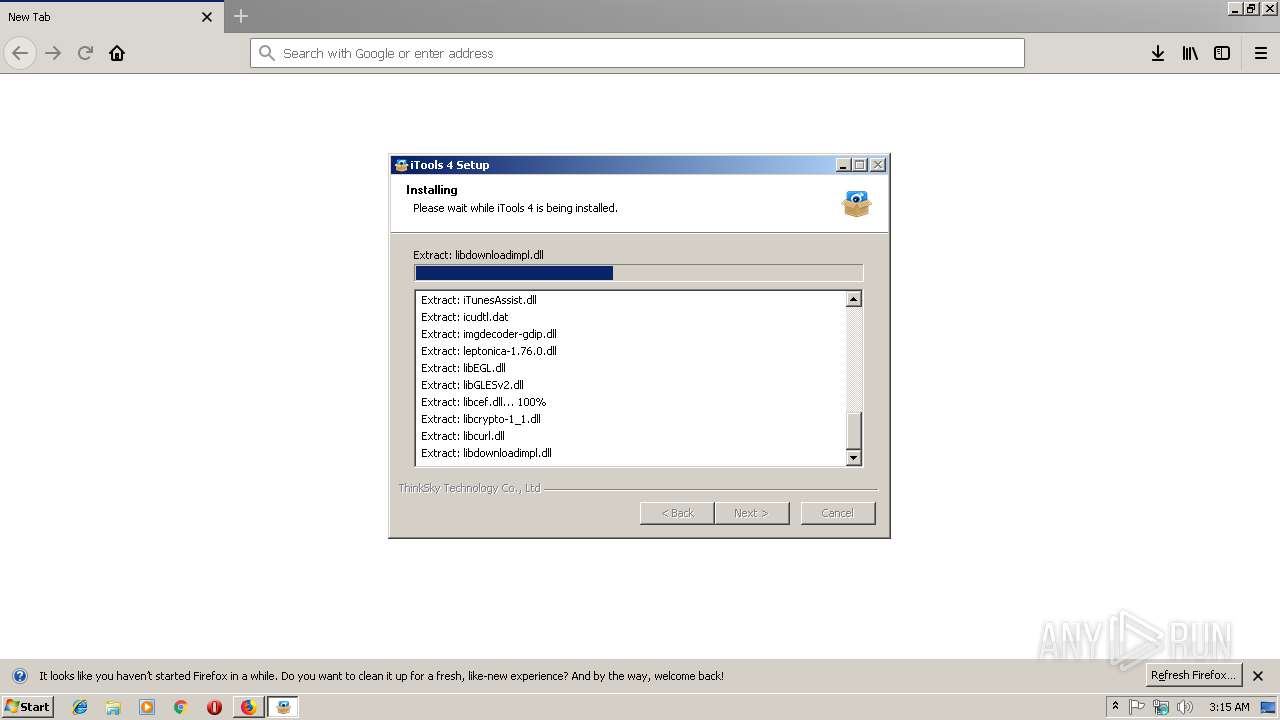
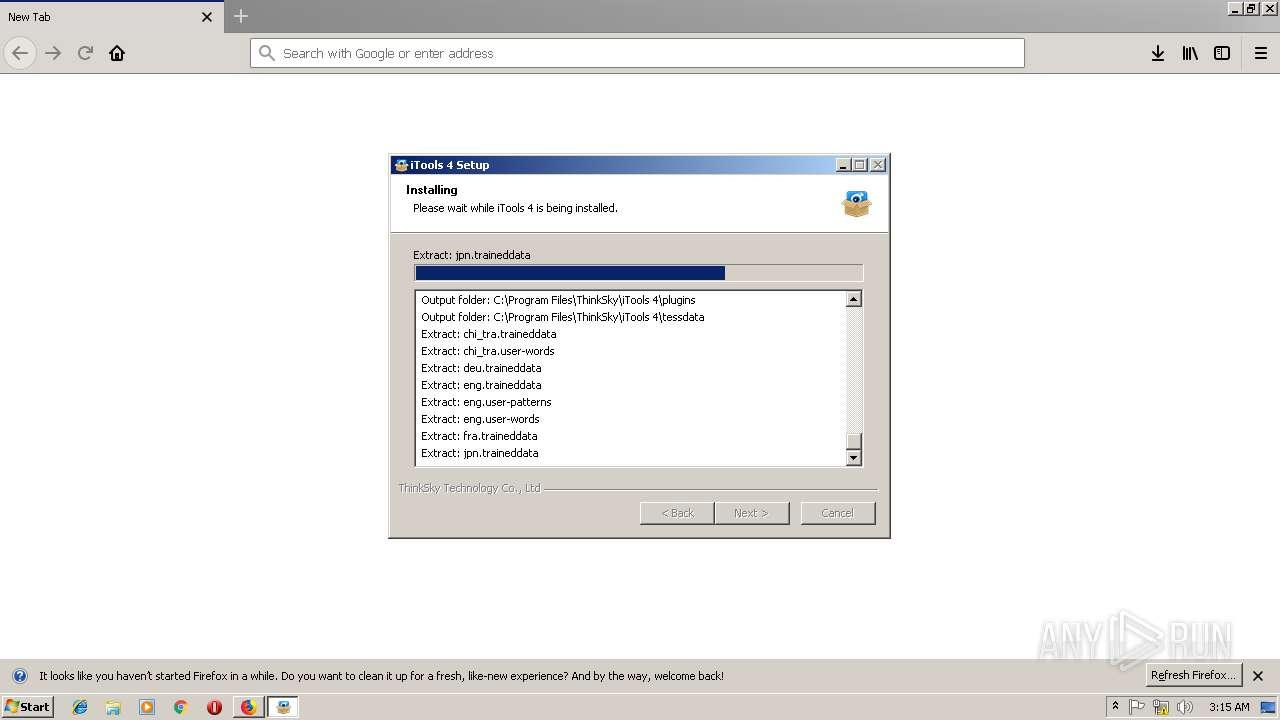
Application was dropped or rewritten from another process
- itools4_setup_4427.exe (PID: 1864)
- itools4_setup_4427.exe (PID: 792)
- CrashSender1403.exe (PID: 3004)
- iTools4.exe (PID: 2740)
- AppleMobileDeviceService.exe (PID: 2404)
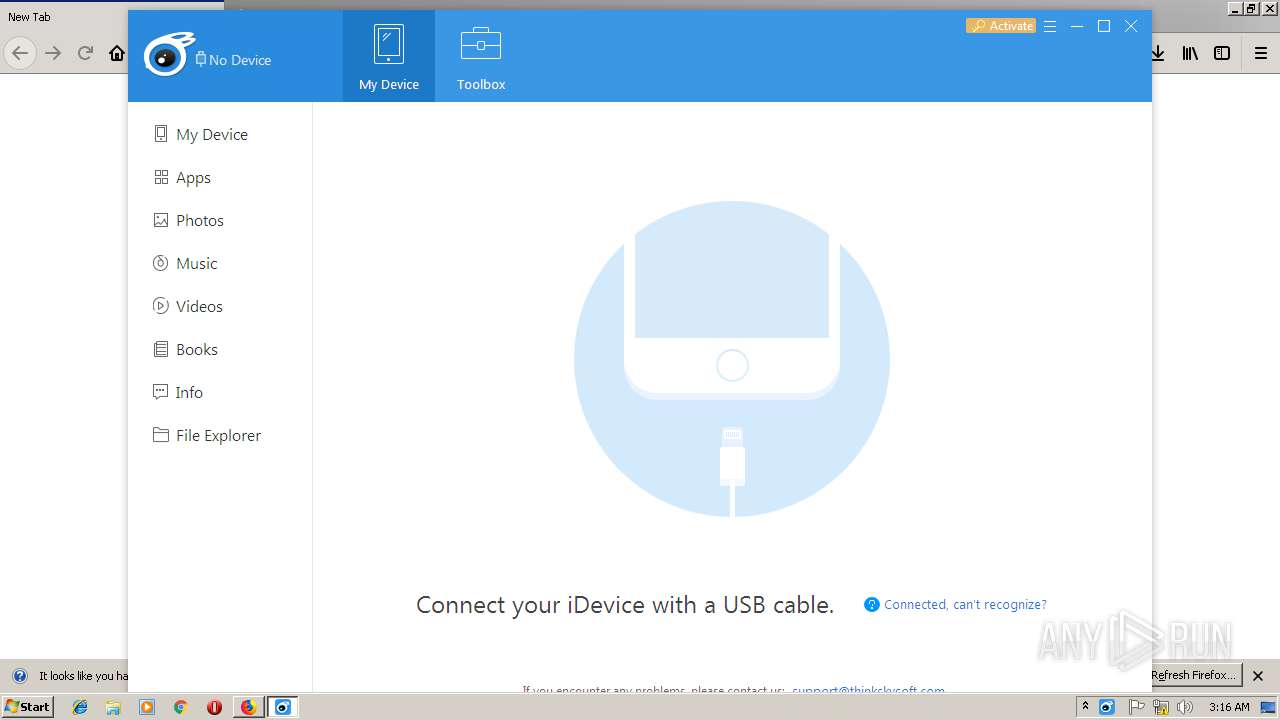
- iTools4.exe (PID: 3028)
- CrashSender1403.exe (PID: 596)
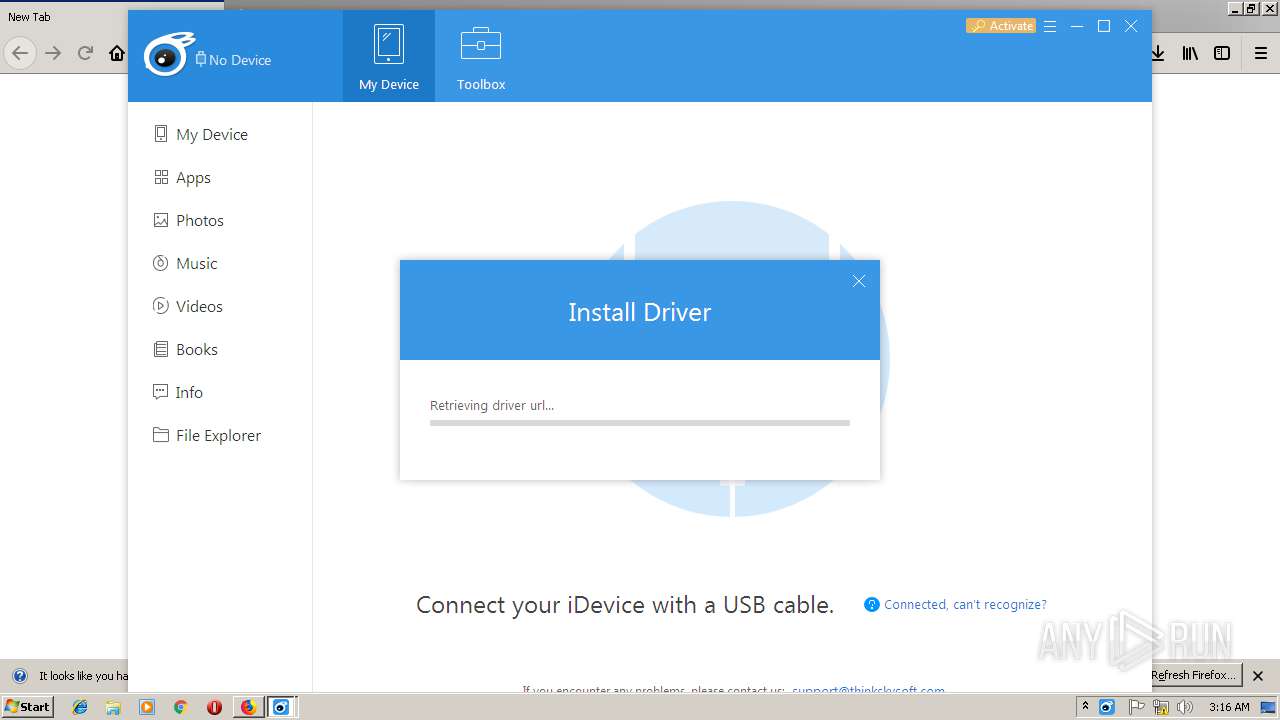
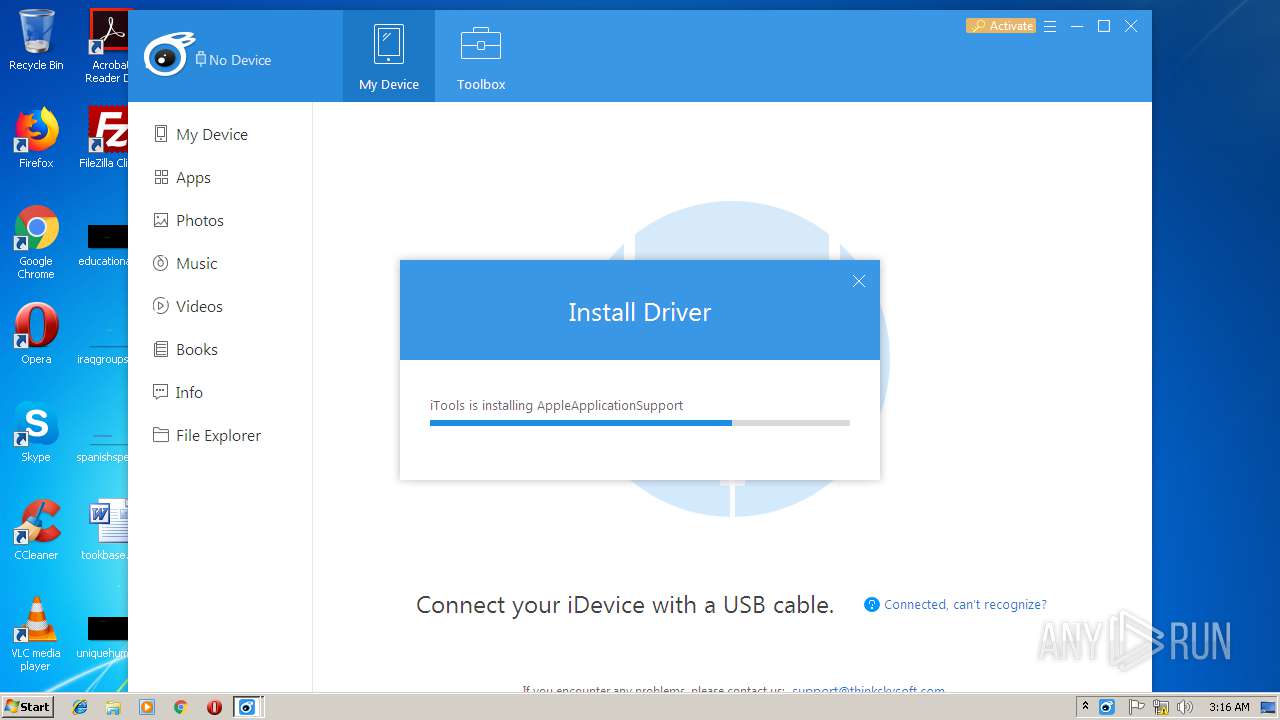
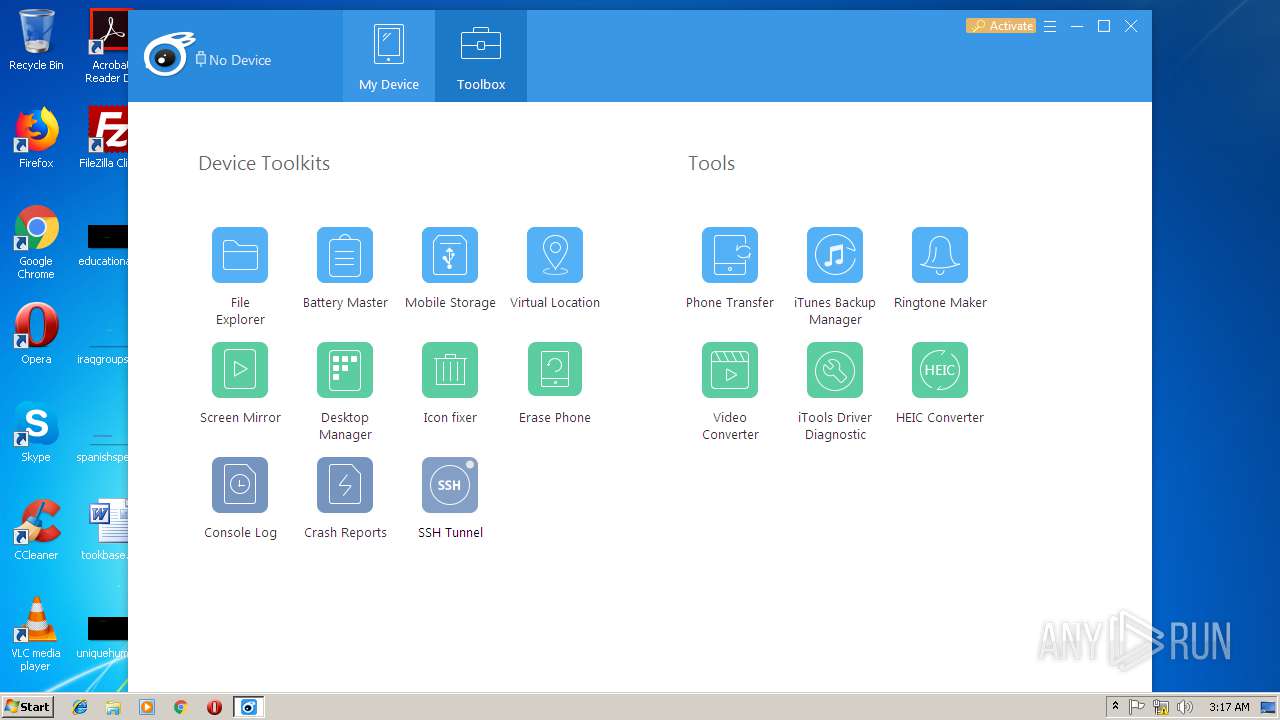
INSTALLCORE was detected
- itools4_setup_4427.exe (PID: 792)
Loads dropped or rewritten executable
- itools4_setup_4427.exe (PID: 792)
- iTools4.exe (PID: 2740)
- CrashSender1403.exe (PID: 3004)
- AppleMobileDeviceService.exe (PID: 2404)
- iTools4.exe (PID: 3028)
- CrashSender1403.exe (PID: 596)
- mmc.exe (PID: 3500)
Connects to CnC server
- itools4_setup_4427.exe (PID: 792)
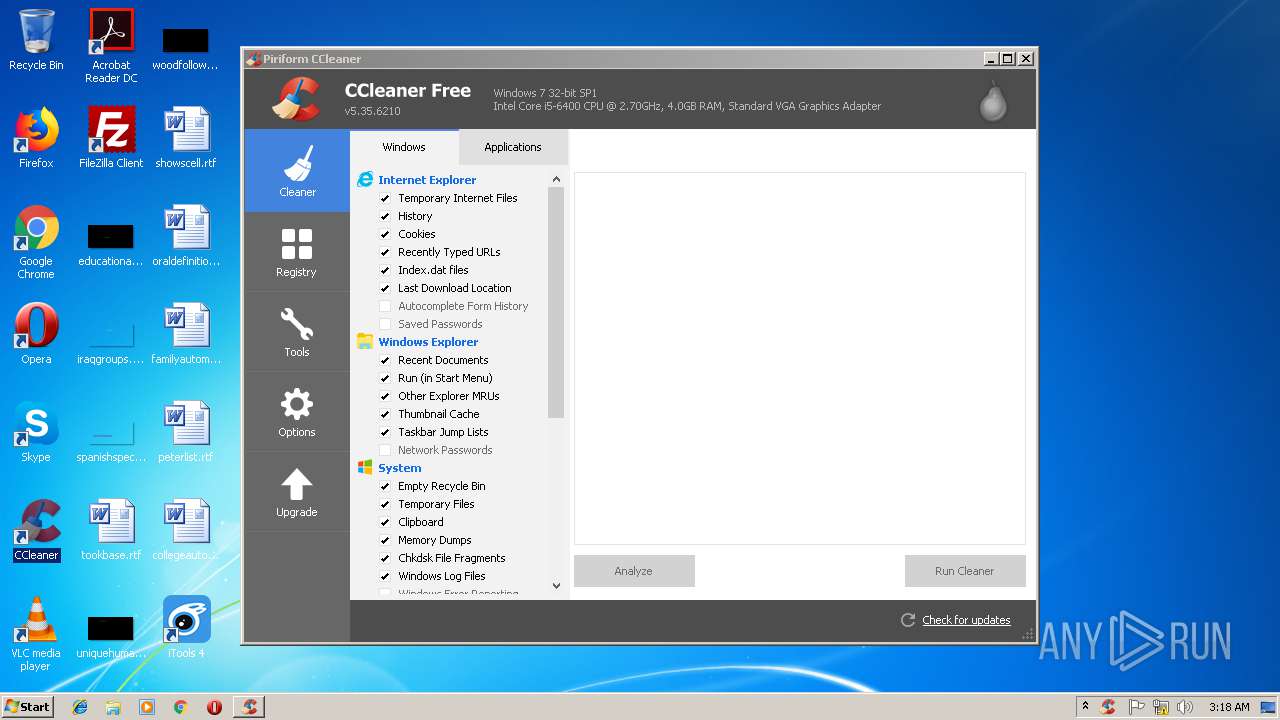
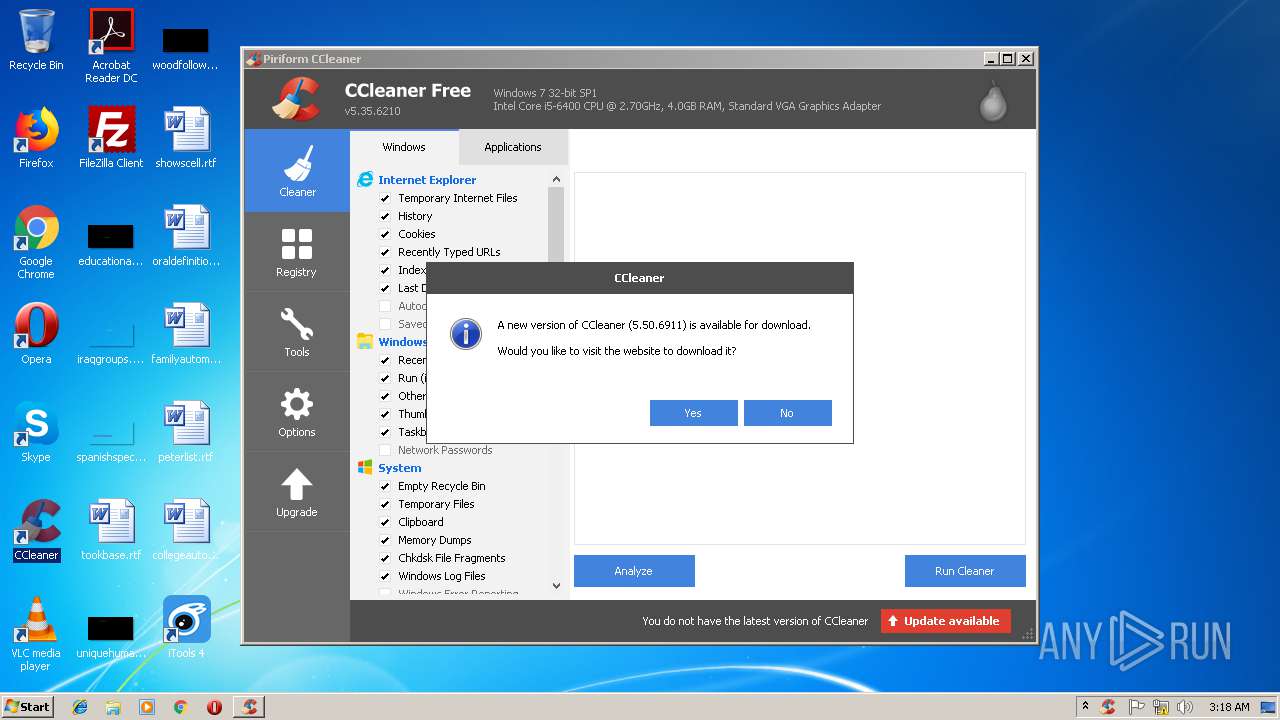
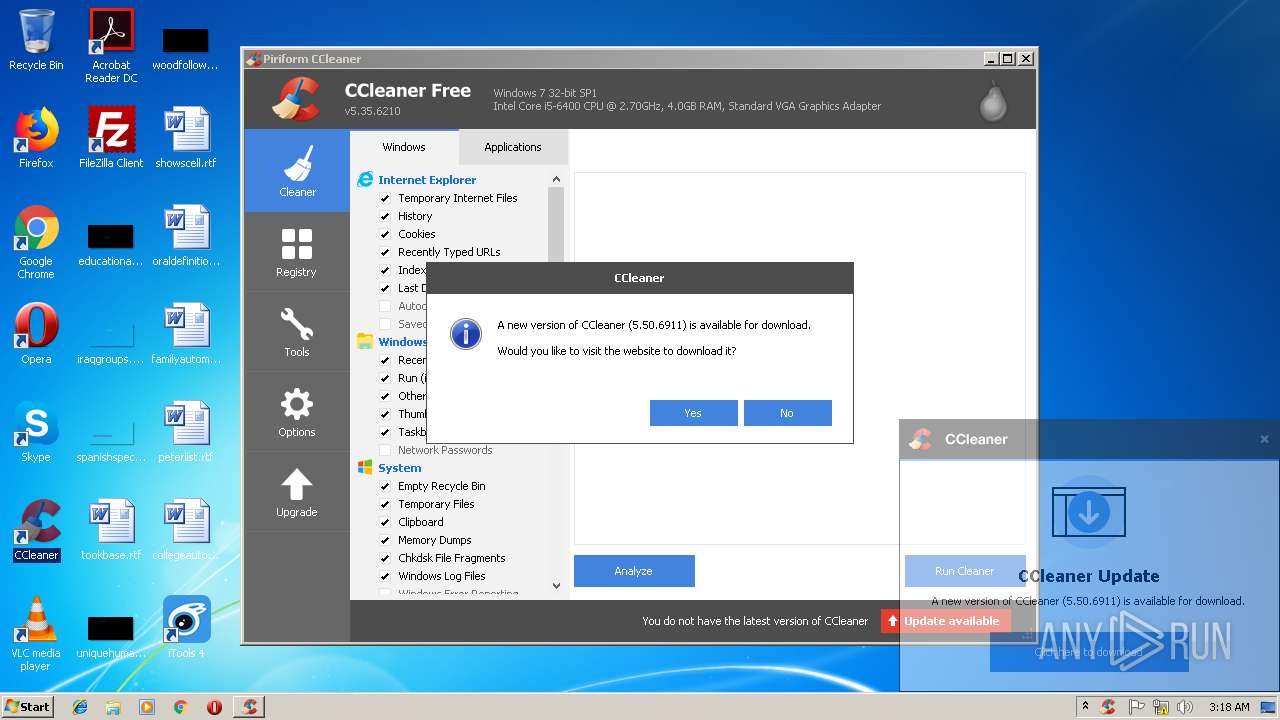
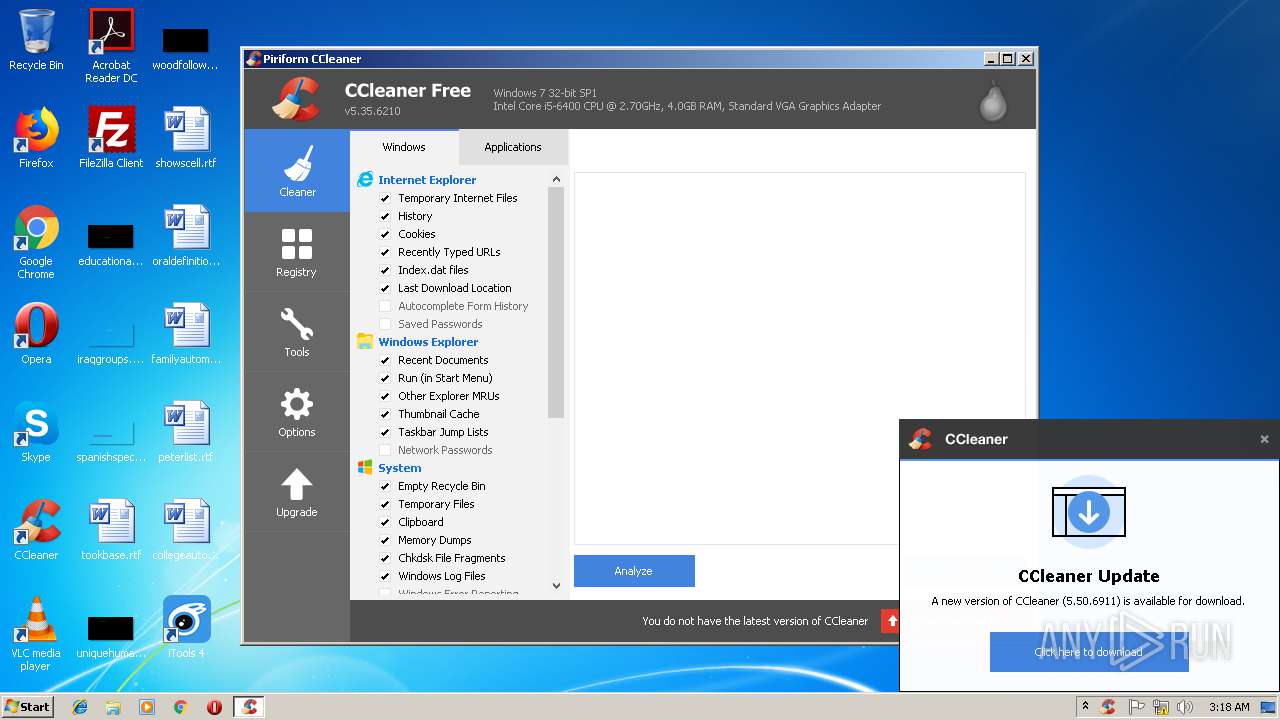
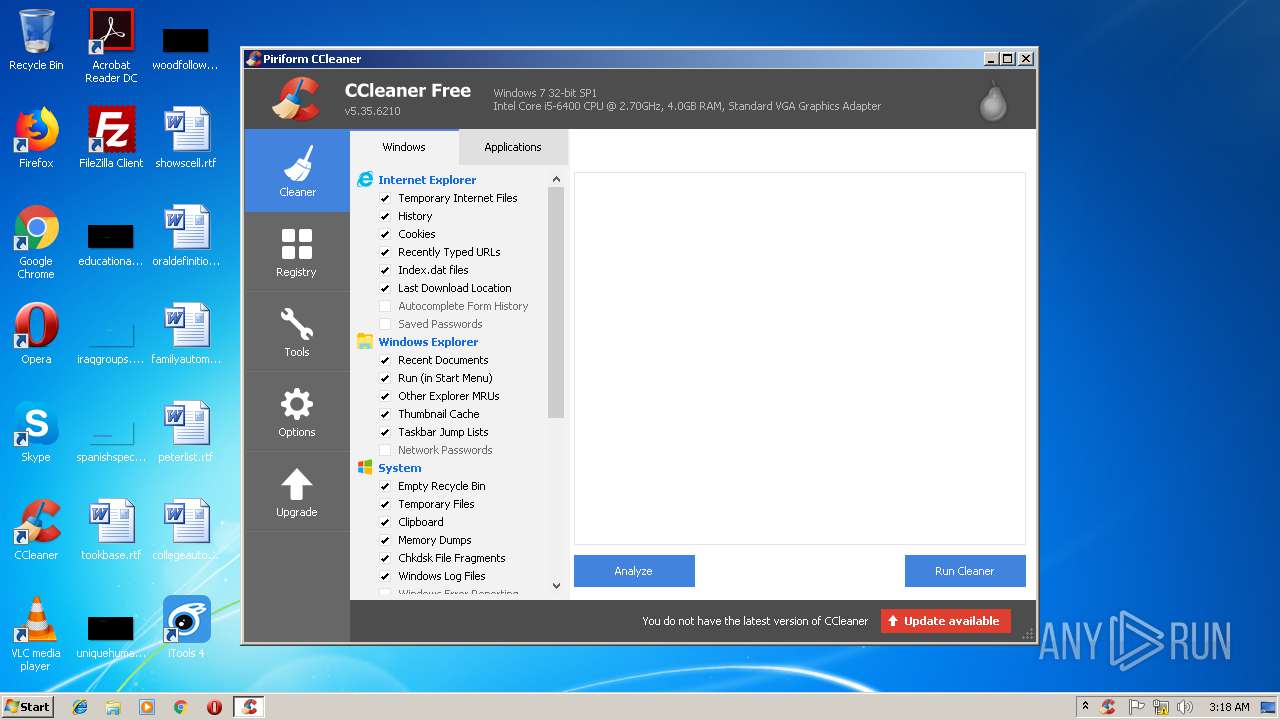
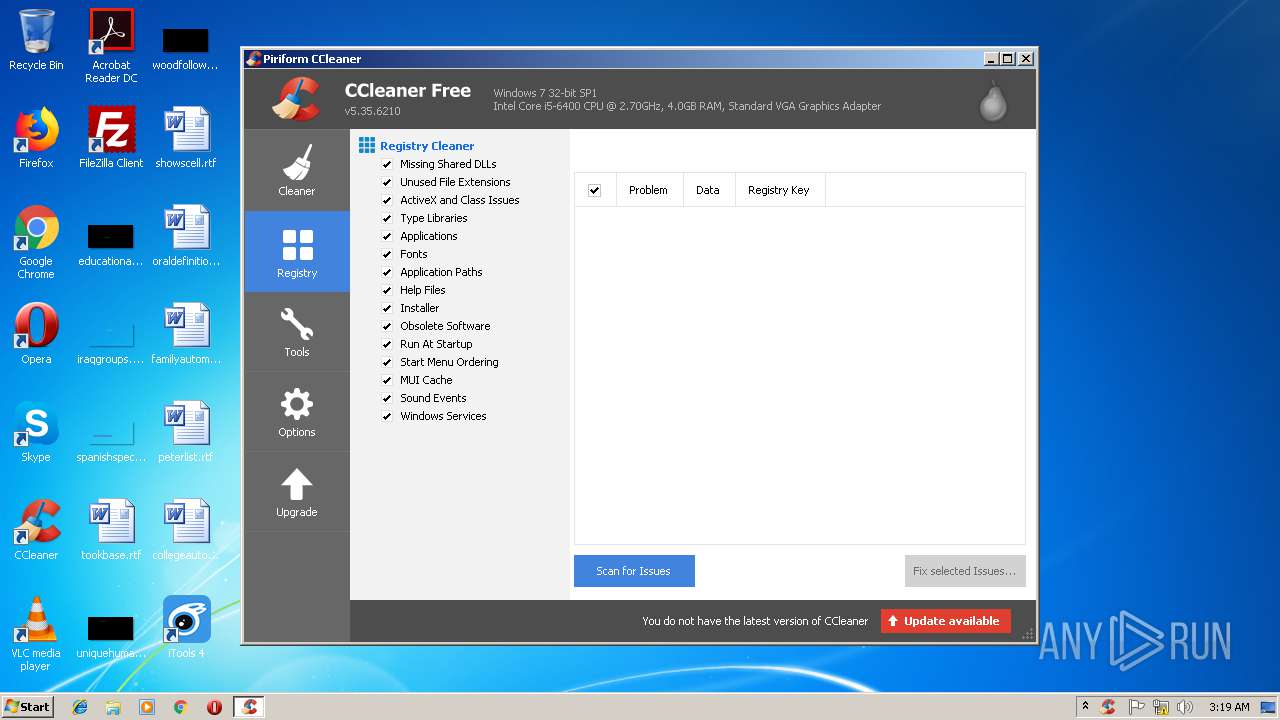
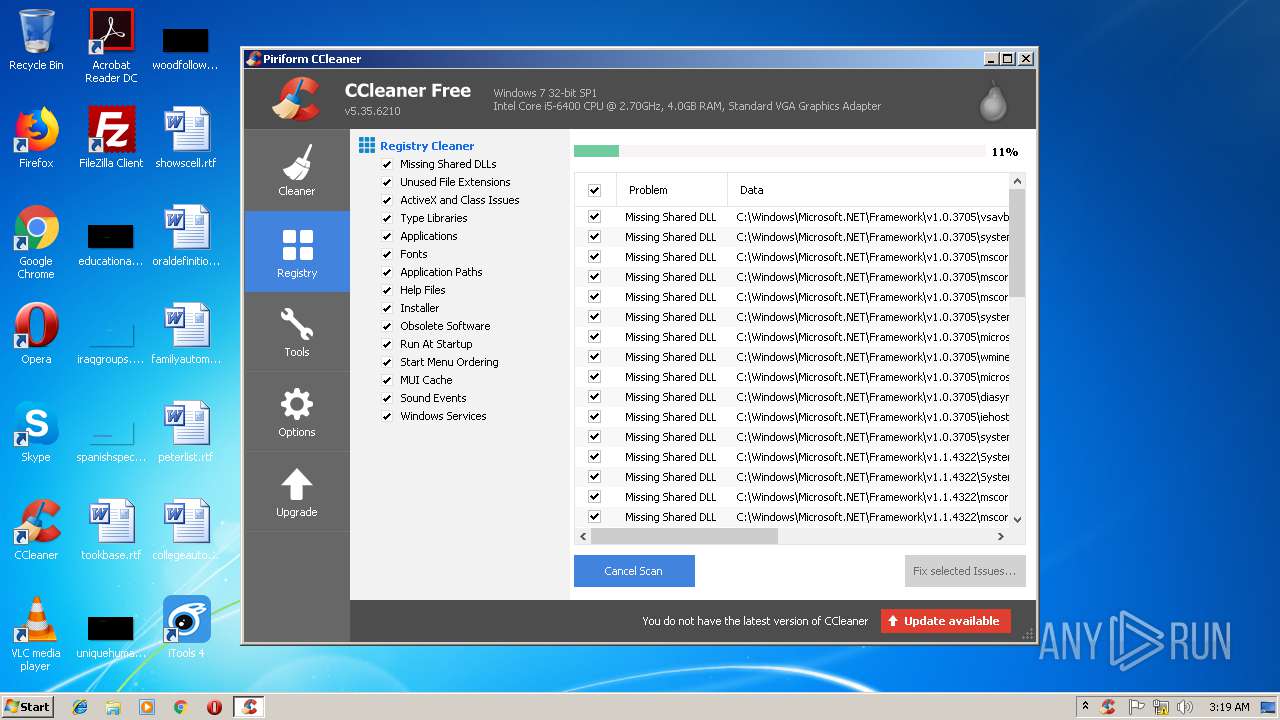
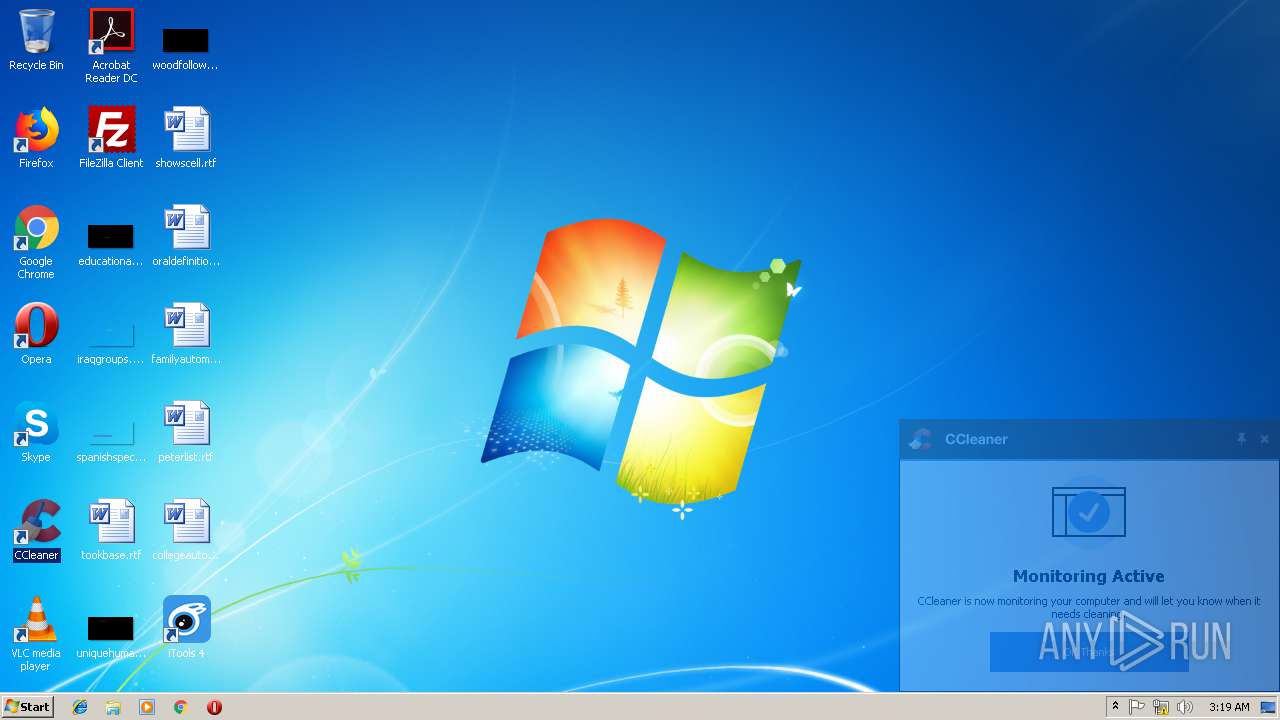
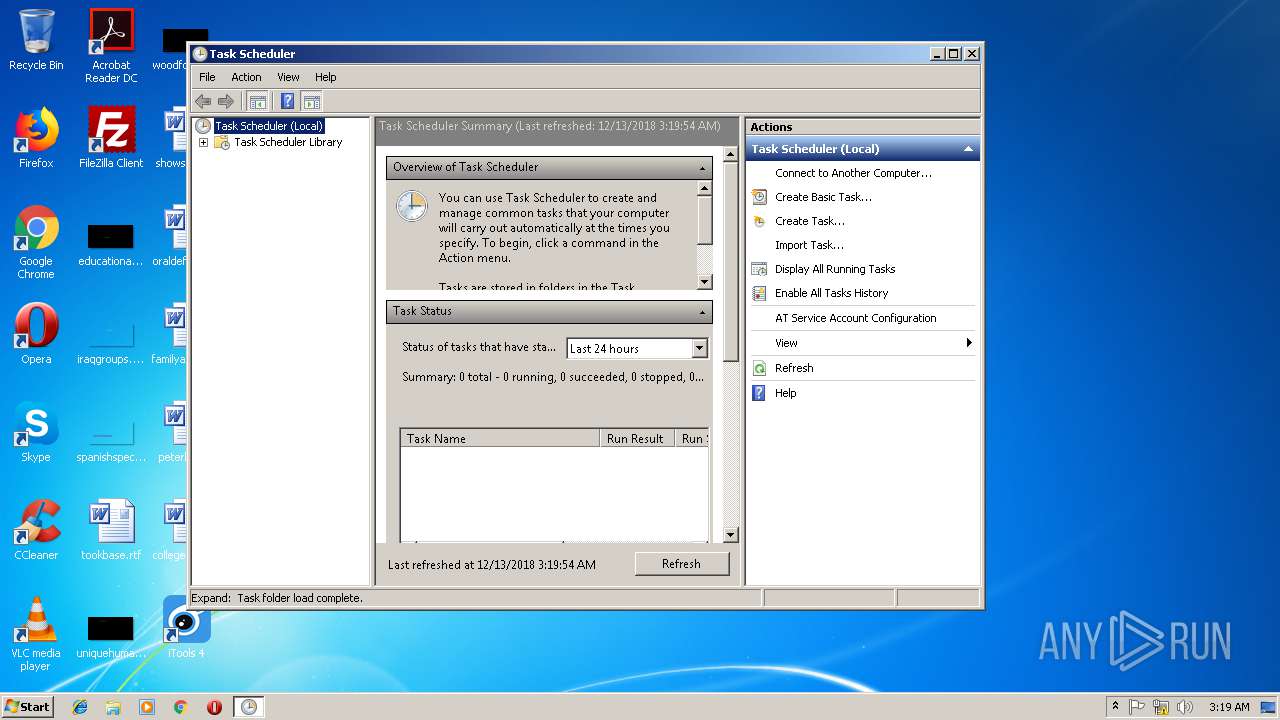
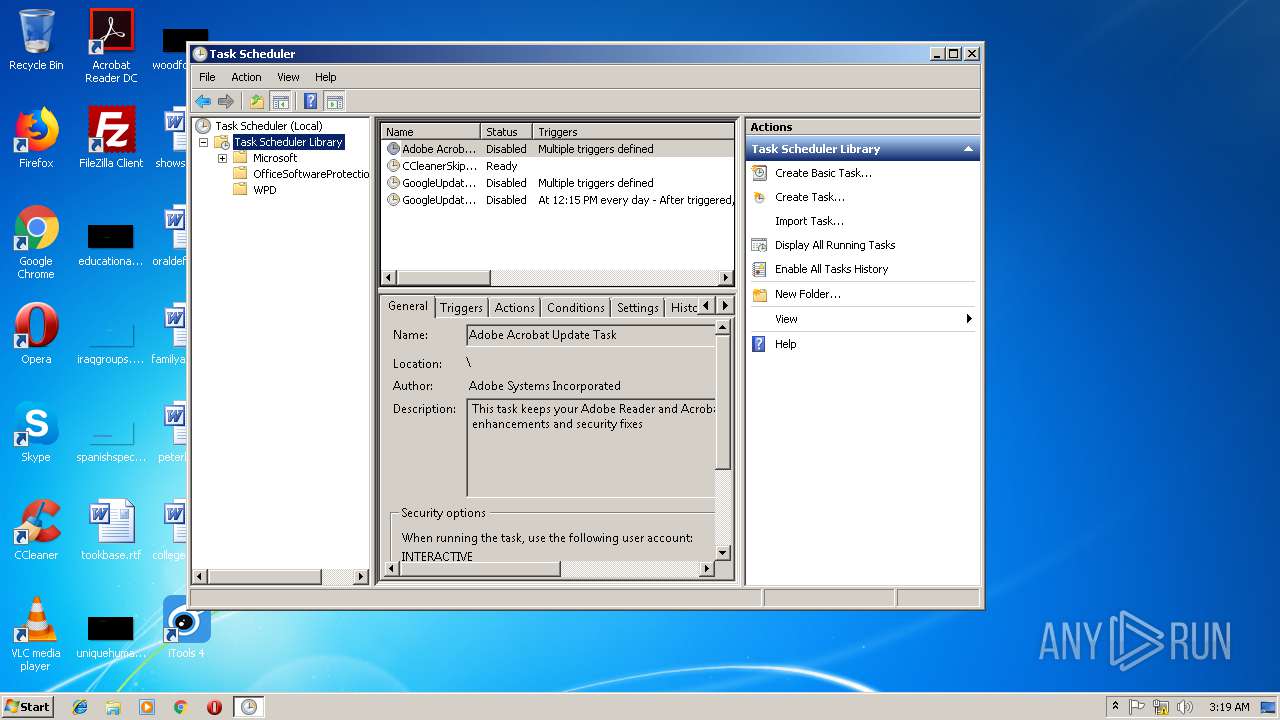
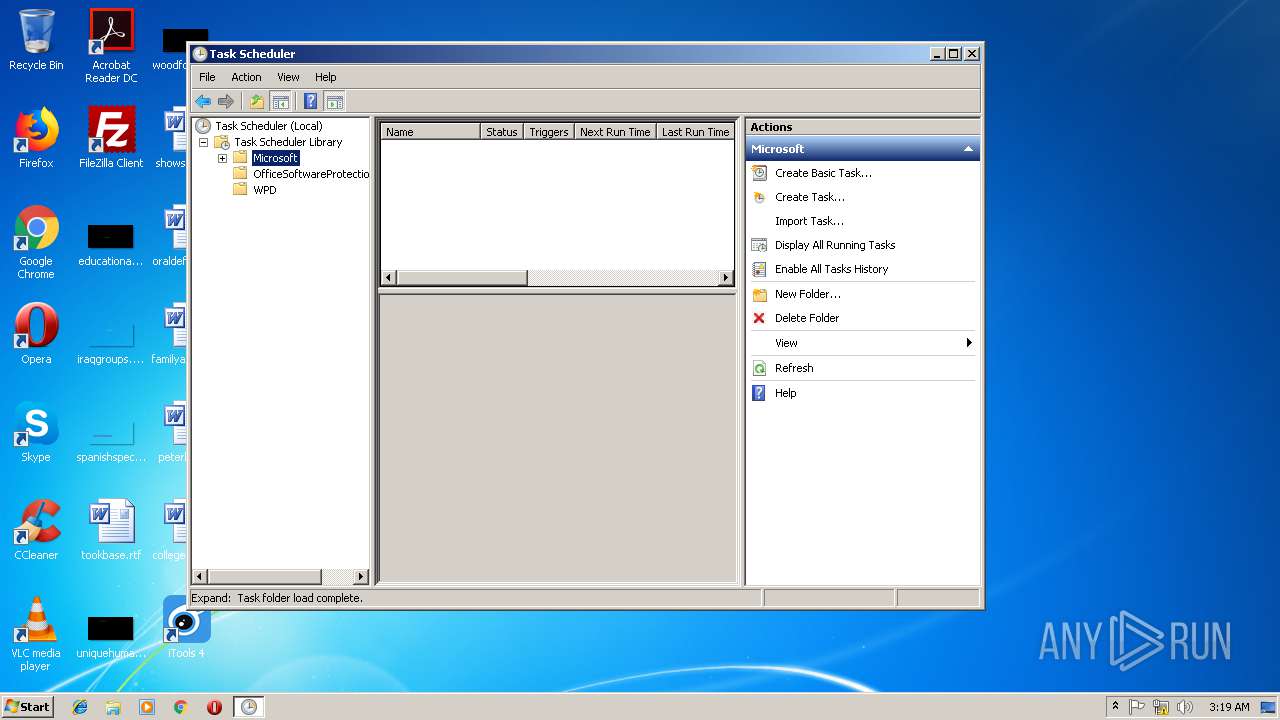
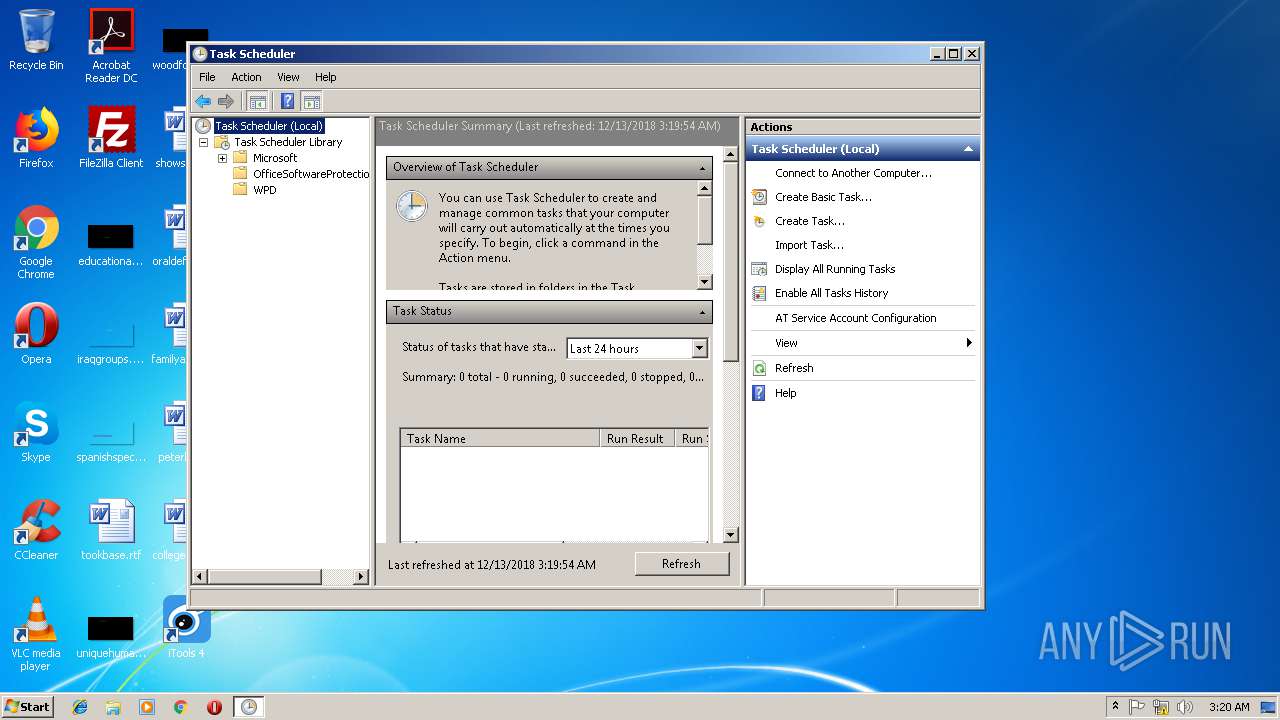
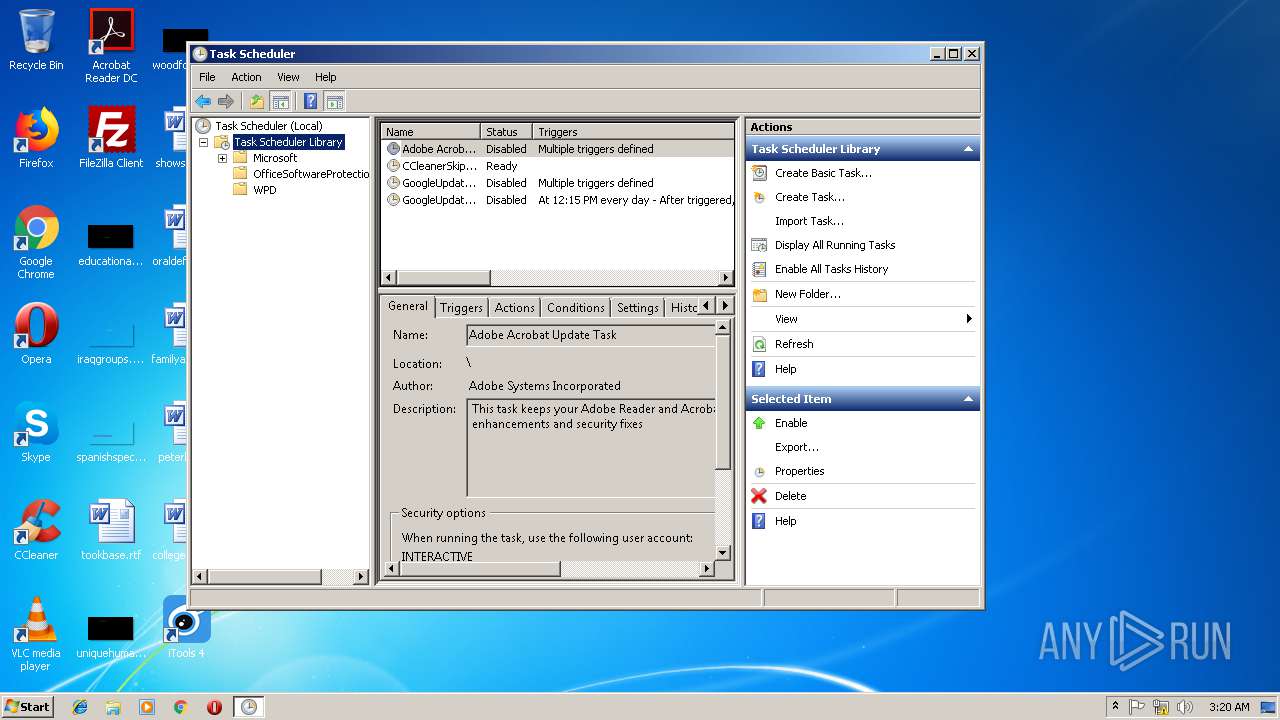
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2924)
- CCleaner.exe (PID: 2312)
- mmc.exe (PID: 3500)
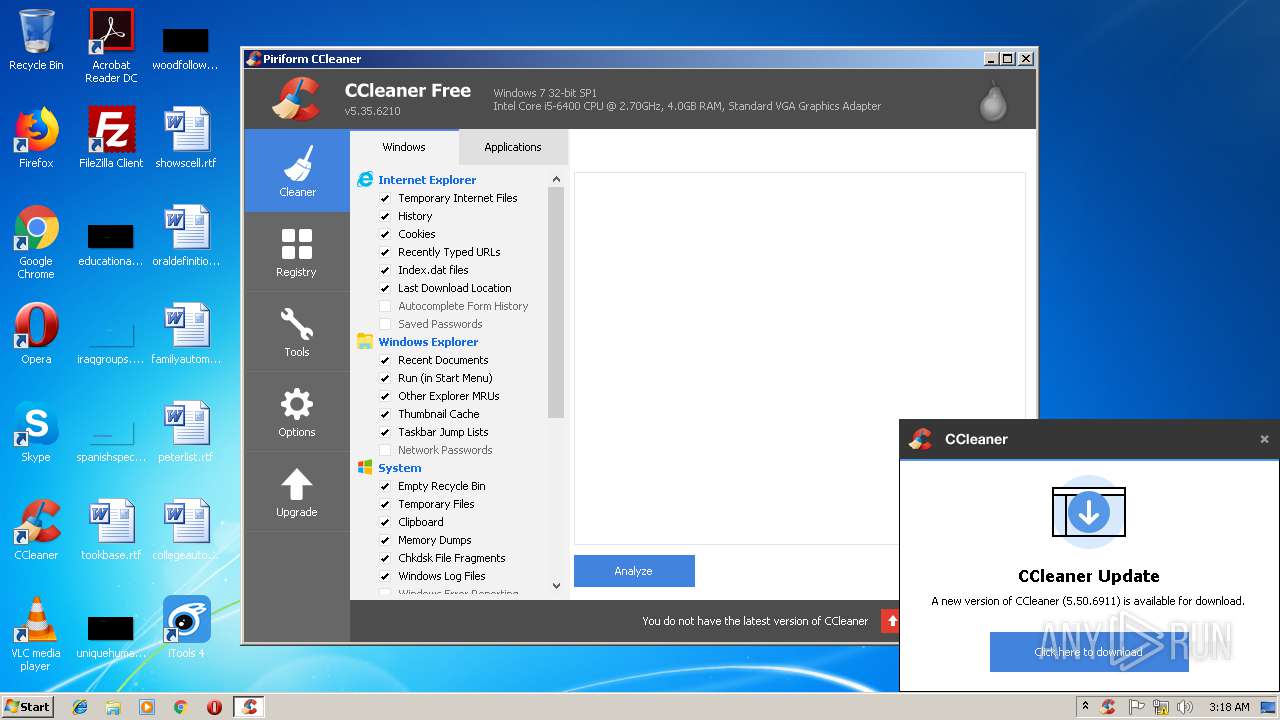
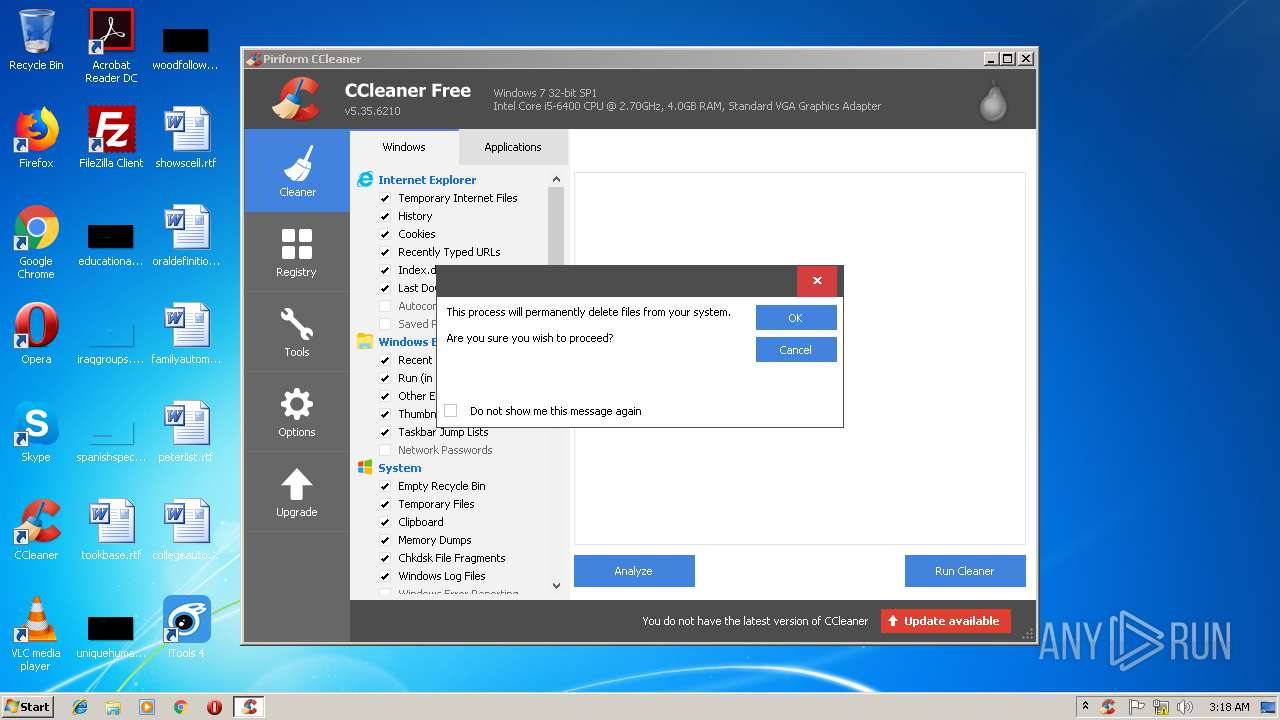
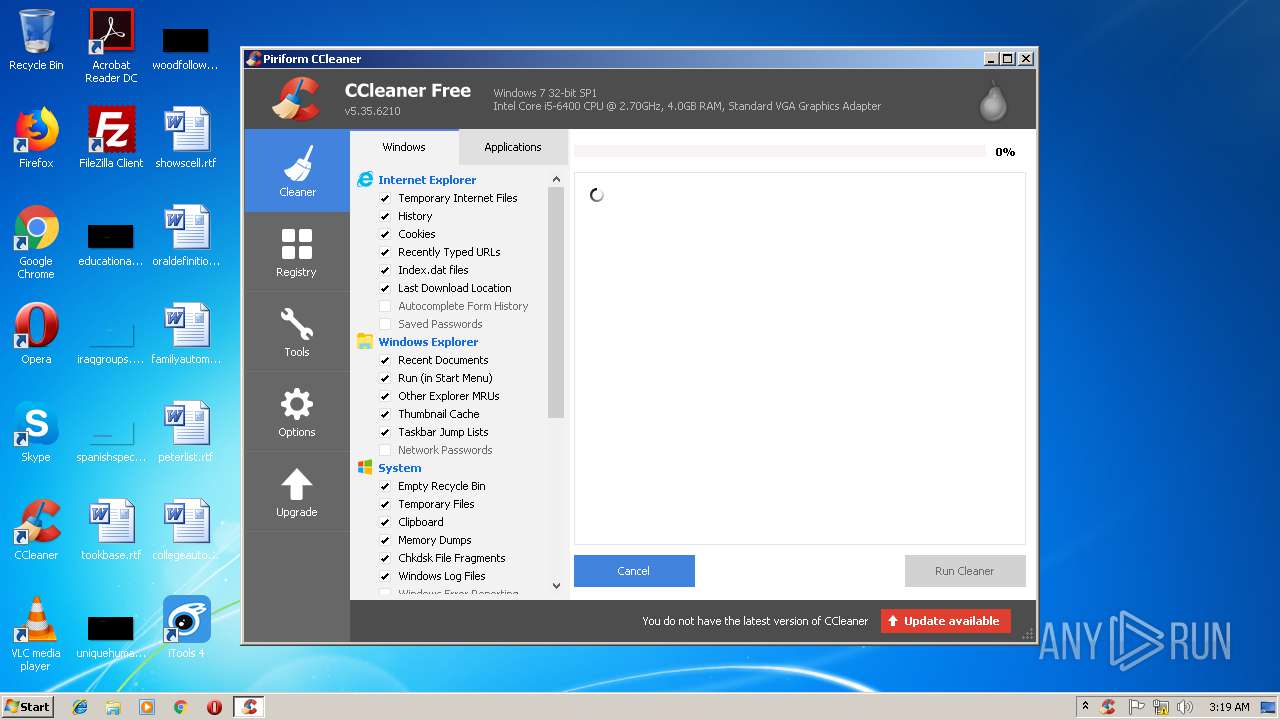
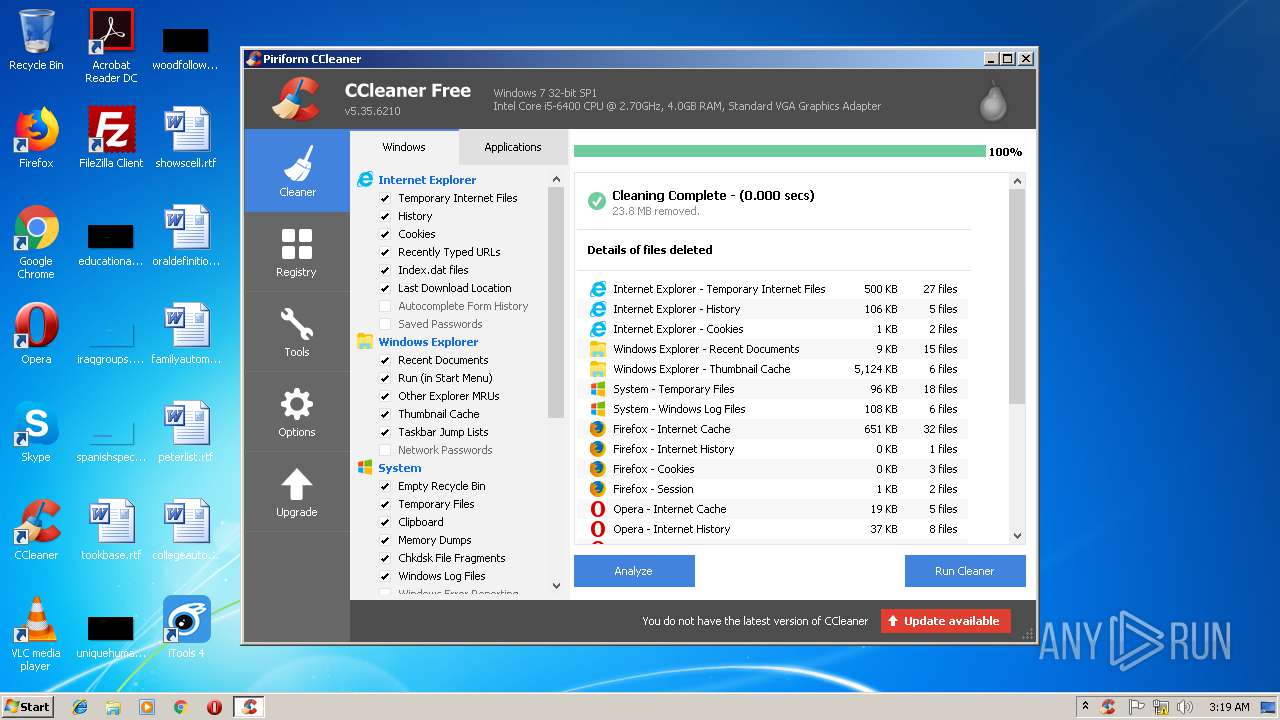
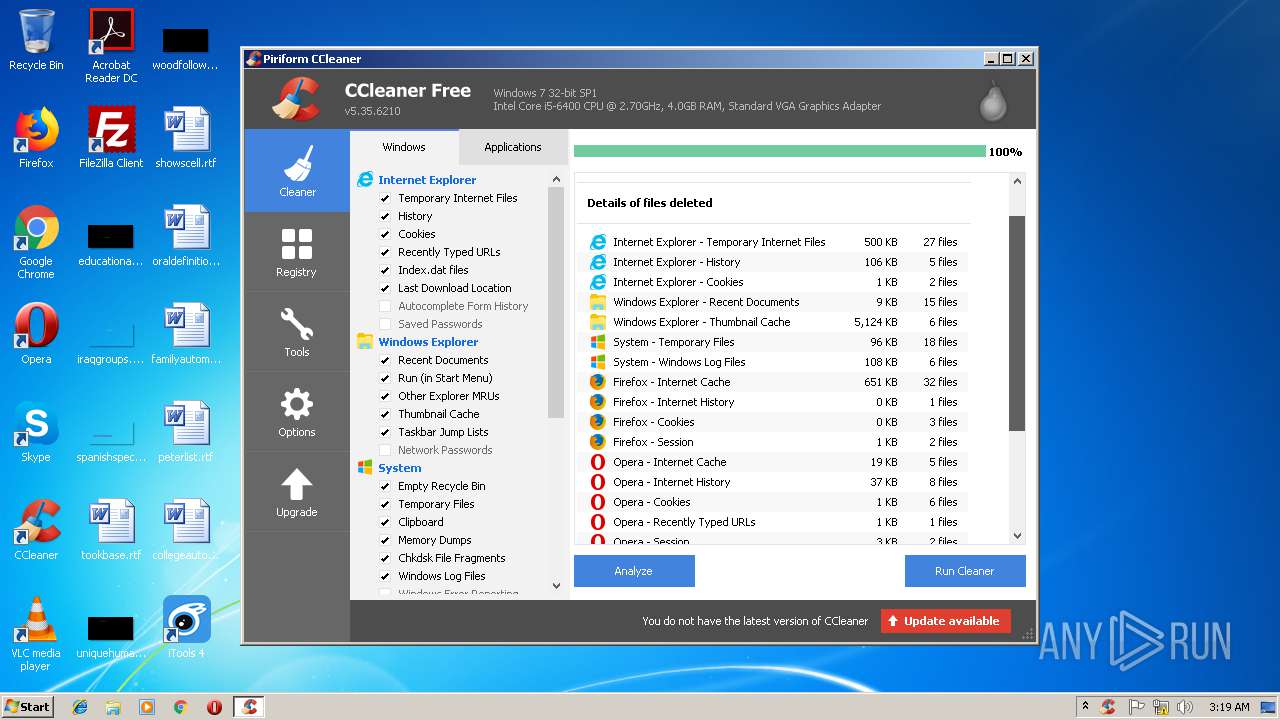
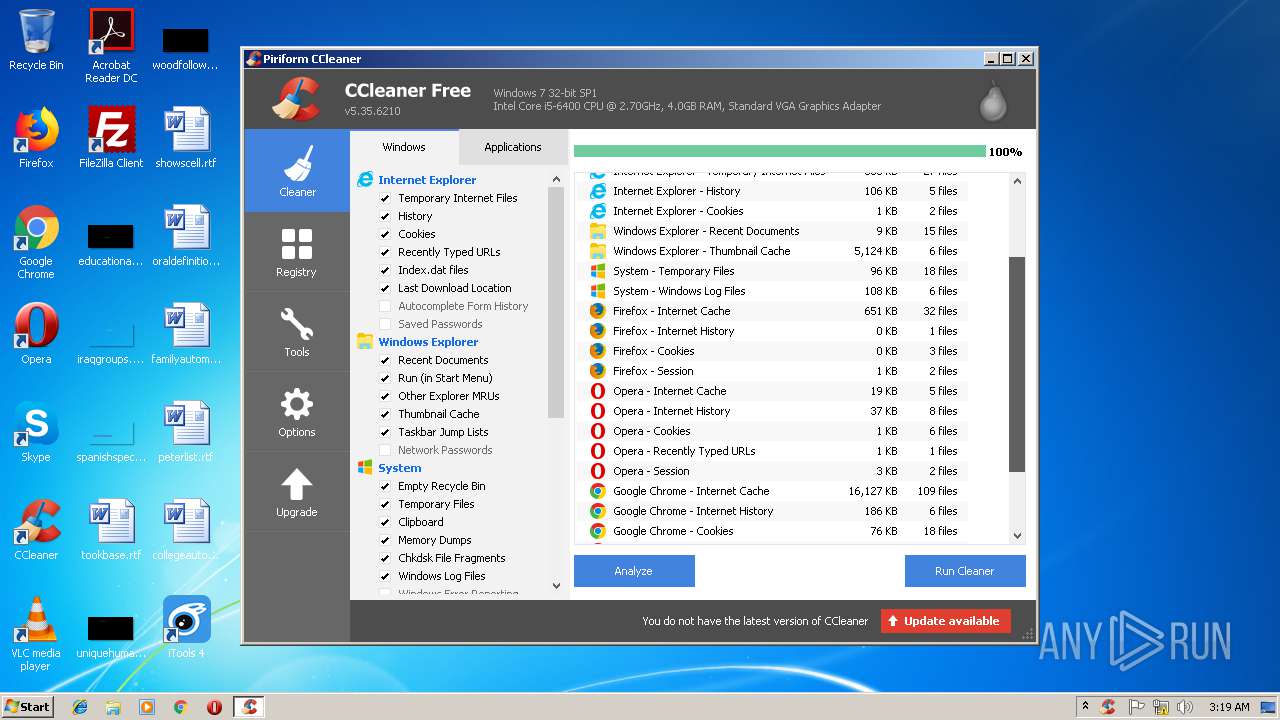
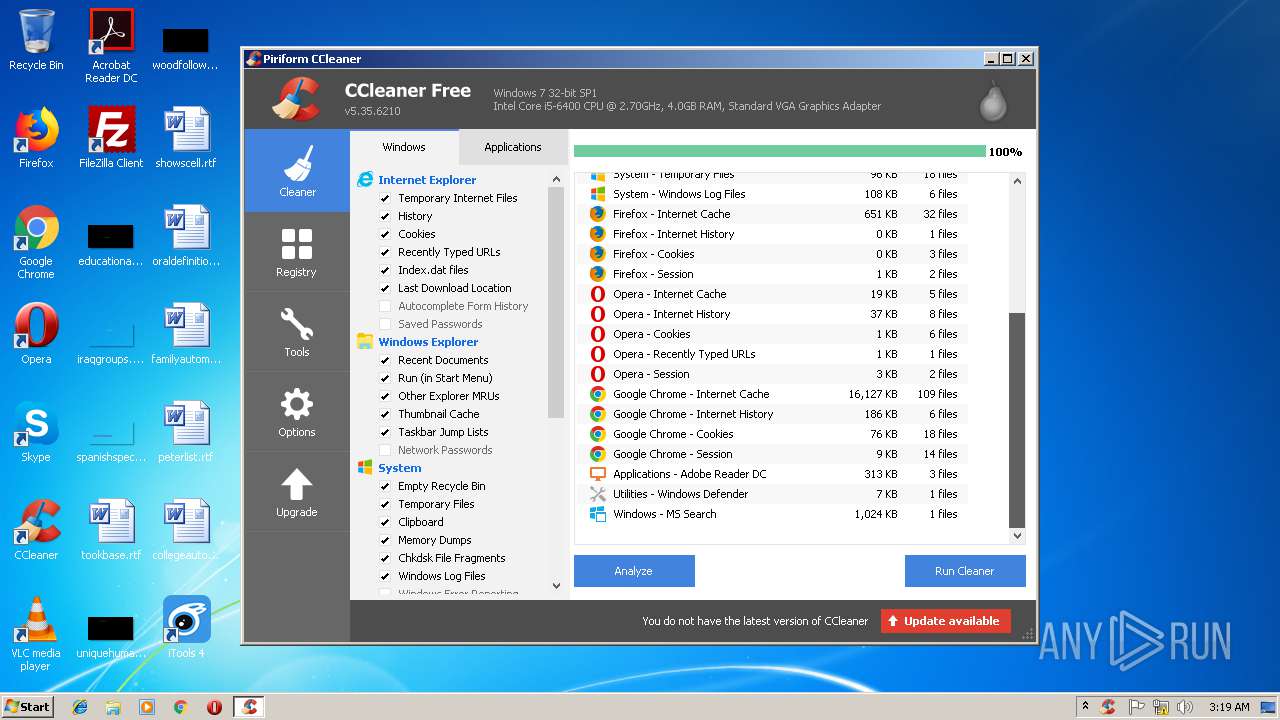
Actions looks like stealing of personal data
- CCleaner.exe (PID: 364)
- CCleaner.exe (PID: 2312)
Changes the autorun value in the registry
- CCleaner.exe (PID: 2312)
SUSPICIOUS
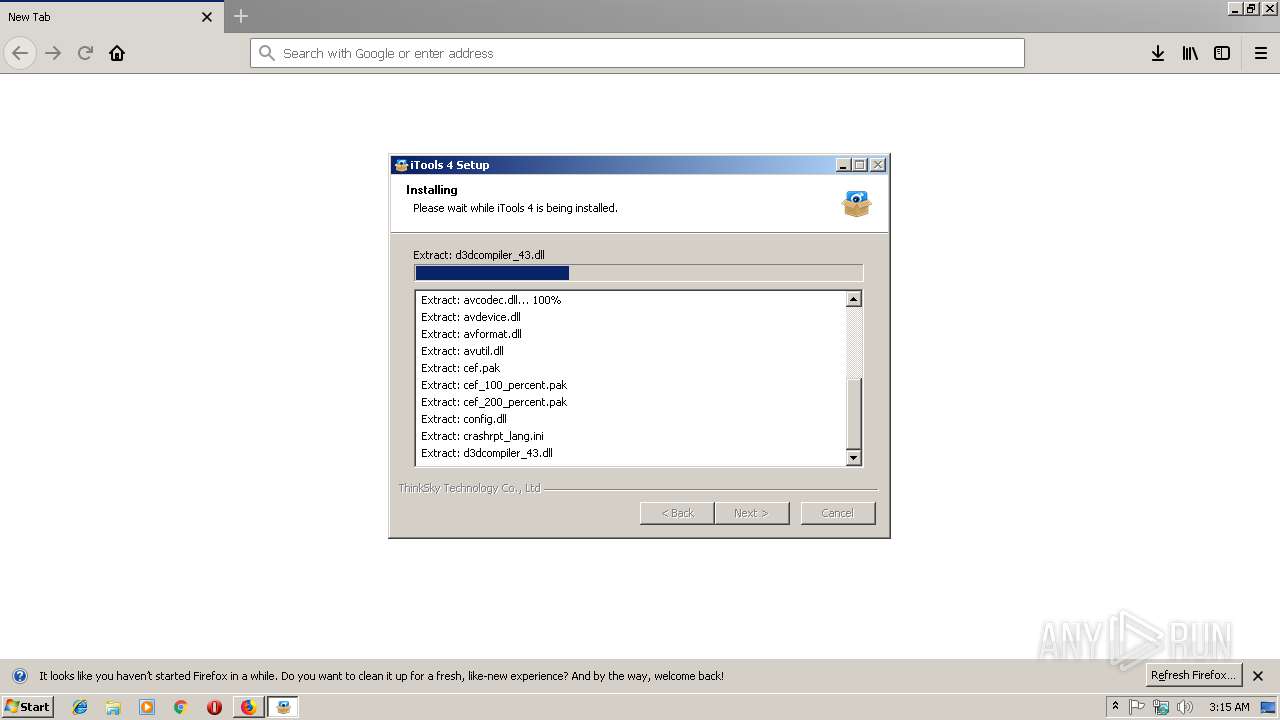
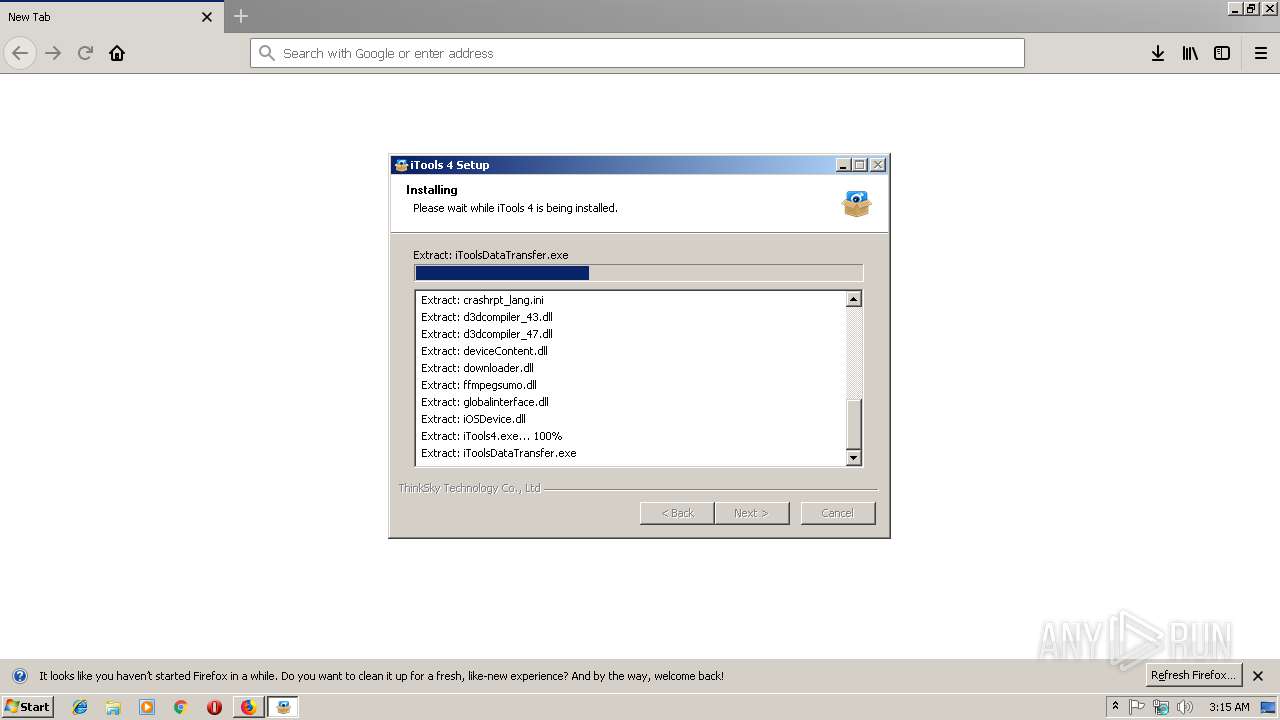
Executable content was dropped or overwritten
- itools4_setup_4427.exe (PID: 792)
- iTools4.exe (PID: 2740)
- MsiExec.exe (PID: 2208)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 3412)
- msiexec.exe (PID: 2300)
Reads the machine GUID from the registry
- itools4_setup_4427.exe (PID: 792)
Reads CPU info
- itools4_setup_4427.exe (PID: 792)
Reads Windows Product ID
- itools4_setup_4427.exe (PID: 792)
Reads Environment values
- itools4_setup_4427.exe (PID: 792)
Reads internet explorer settings
- itools4_setup_4427.exe (PID: 792)
- CCleaner.exe (PID: 364)
- CCleaner.exe (PID: 2312)
Creates a software uninstall entry
- itools4_setup_4427.exe (PID: 792)
Creates files in the program directory
- iTools4.exe (PID: 2740)
- itools4_setup_4427.exe (PID: 792)
- iTools4.exe (PID: 3028)
Creates files in the user directory
- iTools4.exe (PID: 2740)
- iTools4.exe (PID: 3028)
- CCleaner.exe (PID: 364)
Starts Microsoft Installer
- iTools4.exe (PID: 2740)
Removes files from Windows directory
- msiexec.exe (PID: 2300)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 3412)
- CCleaner.exe (PID: 364)
Creates files in the Windows directory
- msiexec.exe (PID: 2300)
- DrvInst.exe (PID: 3412)
- DrvInst.exe (PID: 4076)
Creates files in the driver directory
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 3412)
Starts CMD.EXE for commands execution
- iTools4.exe (PID: 2740)
Creates COM task schedule object
- msiexec.exe (PID: 2300)
Application launched itself
- iTools4.exe (PID: 2740)
- CCleaner.exe (PID: 364)
Reads the BIOS version
- iTools4.exe (PID: 3028)
Reads Internet Cache Settings
- CCleaner.exe (PID: 364)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 364)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 364)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 364)
Searches for installed software
- CCleaner.exe (PID: 364)
INFO
Reads CPU info
- firefox.exe (PID: 4008)
- firefox.exe (PID: 2204)
- firefox.exe (PID: 3548)
- firefox.exe (PID: 1136)
- firefox.exe (PID: 2676)
- firefox.exe (PID: 3644)
- firefox.exe (PID: 3972)
- firefox.exe (PID: 3120)
Creates files in the user directory
- firefox.exe (PID: 3548)
- firefox.exe (PID: 2676)
Application launched itself
- firefox.exe (PID: 3548)
- msiexec.exe (PID: 2300)
- chrome.exe (PID: 2080)
- firefox.exe (PID: 2676)
Reads settings of System Certificates
- firefox.exe (PID: 3548)
- pingsender.exe (PID: 2584)
- CCleaner.exe (PID: 364)
Loads dropped or rewritten executable
- msiexec.exe (PID: 2300)
Creates a software uninstall entry
- msiexec.exe (PID: 2300)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2080)
Creates files in the program directory
- msiexec.exe (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
43
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6e1000b0,0x6e1000c0,0x6e1000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 596 | "C:\Program Files\ThinkSky\iTools 4\CrashSender1403.exe" "c5f851ea-0d97-4a00-ad16-4b6effcc9d75-tmp" | C:\Program Files\ThinkSky\iTools 4\CrashSender1403.exe | — | iTools4.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Crash Report Delivery Module Exit code: 0 Version: 1.4.0.3 Modules
| |||||||||||||||
| 792 | "C:\Users\admin\Downloads\itools4_setup_4427.exe" | C:\Users\admin\Downloads\itools4_setup_4427.exe | firefox.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,16730664619584815270,10513581399880405053,131072 --enable-features=PasswordImport --service-pipe-token=3B3FA4833EAED508DDAE20F09AE84438 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3B3FA4833EAED508DDAE20F09AE84438 --renderer-client-id=3 --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3548.0.301713799\1741005666" -childID 1 -isForBrowser -prefsHandle 1360 -prefsLen 8310 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3548 "\\.\pipe\gecko-crash-server-pipe.3548" 1480 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 1240 | msiexec /i "C:\Users\admin\AppData\Local\Temp\ThinkSky\iTools_Temp_415401B188FF4006\\AppleMobileDeviceSupport.msi" /qn REBOOT=ReallySuppress /le C:\Users\admin\AppData\Local\Temp\ThinkSky\\15065126520183455203.txt | C:\Windows\system32\msiexec.exe | — | iTools4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | msiexec /x "C:\Users\admin\AppData\Local\Temp\ThinkSky\iTools_Temp_415401B188FF4006\AppleApplicationSupport.msi" /qn /quiet | C:\Windows\system32\msiexec.exe | — | iTools4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1605 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\Downloads\itools4_setup_4427.exe" | C:\Users\admin\Downloads\itools4_setup_4427.exe | — | firefox.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,16730664619584815270,10513581399880405053,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A25D08ED413AF66AE5A3F82264AA26E7 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A25D08ED413AF66AE5A3F82264AA26E7 --renderer-client-id=6 --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
6 099
Read events
2 974
Write events
3 058
Delete events
67
Modification events
| (PID) Process: | (3548) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3548) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3548) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3548) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3548) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (792) itools4_setup_4427.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (792) itools4_setup_4427.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (792) itools4_setup_4427.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (792) itools4_setup_4427.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\itools4_setup_4427_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (792) itools4_setup_4427.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\itools4_setup_4427_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
311
Suspicious files
242
Text files
1 654
Unknown types
127
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\6B45131DFE936988C8E43AAC528138B53844E907 | der | |
MD5:— | SHA256:— | |||
| 3548 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\google4\goog-badbinurl-proto.metadata | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
58
DNS requests
87
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2740 | iTools4.exe | GET | — | 104.27.94.32:80 | http://dl2.thinkskysoft.com/itunes_lite/vista_1260/iTunesOL_Lite_32_12.9.0.167.zip | US | — | — | suspicious |
792 | itools4_setup_4427.exe | POST | 200 | 54.154.255.147:80 | http://os.tenaranerweh.com/itools_Pub_FS/ | IE | binary | 164 Kb | malicious |
3548 | firefox.exe | POST | 200 | 172.217.168.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3548 | firefox.exe | GET | 200 | 104.27.94.32:80 | http://dl2.thinkskysoft.com/itools/itools4_setup_4427.exe | US | executable | 66.5 Mb | suspicious |
2740 | iTools4.exe | GET | 206 | 104.27.94.32:80 | http://dl2.thinkskysoft.com/itunes_lite/vista_1260/iTunesOL_Lite_32_12.9.0.167.zip | US | binary | 2.00 Mb | suspicious |
2740 | iTools4.exe | GET | 206 | 104.27.94.32:80 | http://dl2.thinkskysoft.com/itunes_lite/vista_1260/iTunesOL_Lite_32_12.9.0.167.zip | US | binary | 7.00 Mb | suspicious |
792 | itools4_setup_4427.exe | POST | 200 | 54.194.149.175:80 | http://rp.tenaranerweh.com/ | IE | — | — | malicious |
3548 | firefox.exe | POST | 200 | 172.217.168.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2740 | iTools4.exe | GET | 206 | 104.27.94.32:80 | http://dl2.thinkskysoft.com/itunes_lite/vista_1260/iTunesOL_Lite_32_12.9.0.167.zip | US | binary | 2.11 Mb | suspicious |
3548 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3548 | firefox.exe | 104.27.94.32:80 | dl2.thinkskysoft.com | Cloudflare Inc | US | shared |
3548 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3548 | firefox.exe | 34.216.89.123:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3548 | firefox.exe | 93.184.220.29:80 | cs9.wac.phicdn.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3548 | firefox.exe | 52.34.90.23:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3548 | firefox.exe | 34.209.108.219:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3548 | firefox.exe | 172.217.168.14:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3548 | firefox.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3548 | firefox.exe | 172.217.168.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2740 | iTools4.exe | 104.27.94.32:80 | dl2.thinkskysoft.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
dl2.thinkskysoft.com |
| suspicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3548 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3548 | firefox.exe | unknown | SURICATA IPv4 invalid checksum |
792 | itools4_setup_4427.exe | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M2 |
792 | itools4_setup_4427.exe | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M1 |
792 | itools4_setup_4427.exe | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M3 |
792 | itools4_setup_4427.exe | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M4 |
2740 | iTools4.exe | unknown | SURICATA IPv4 invalid checksum |
364 | CCleaner.exe | A Network Trojan was detected | SC MINER Miner Possible Bitcoin Miner Windows |
5 ETPRO signatures available at the full report
Process | Message |
|---|---|
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect item of type:1 in SOUI!! |
iTools4.exe | Warning: no ojbect popupstyle of type:1 in SOUI!! |
AppleMobileDeviceService.exe | ASL checking for logging parameters in environment variable "AppleMobileDeviceService.exe.log"
|